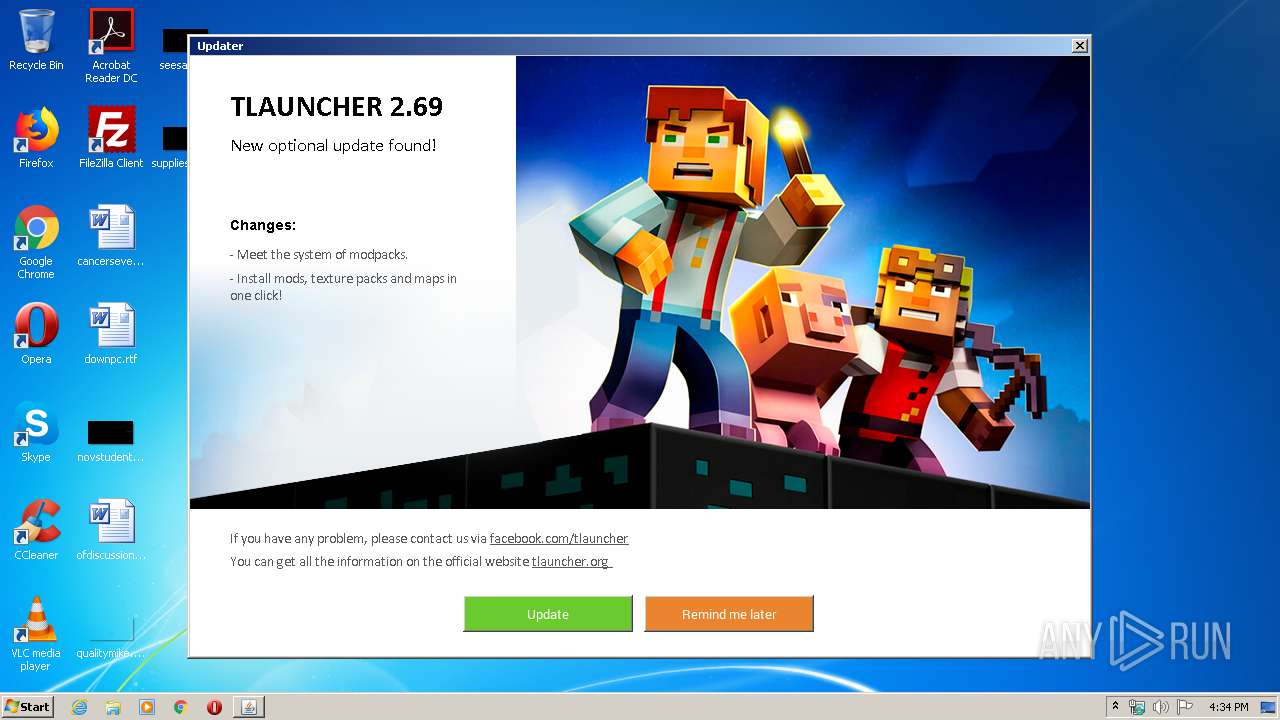
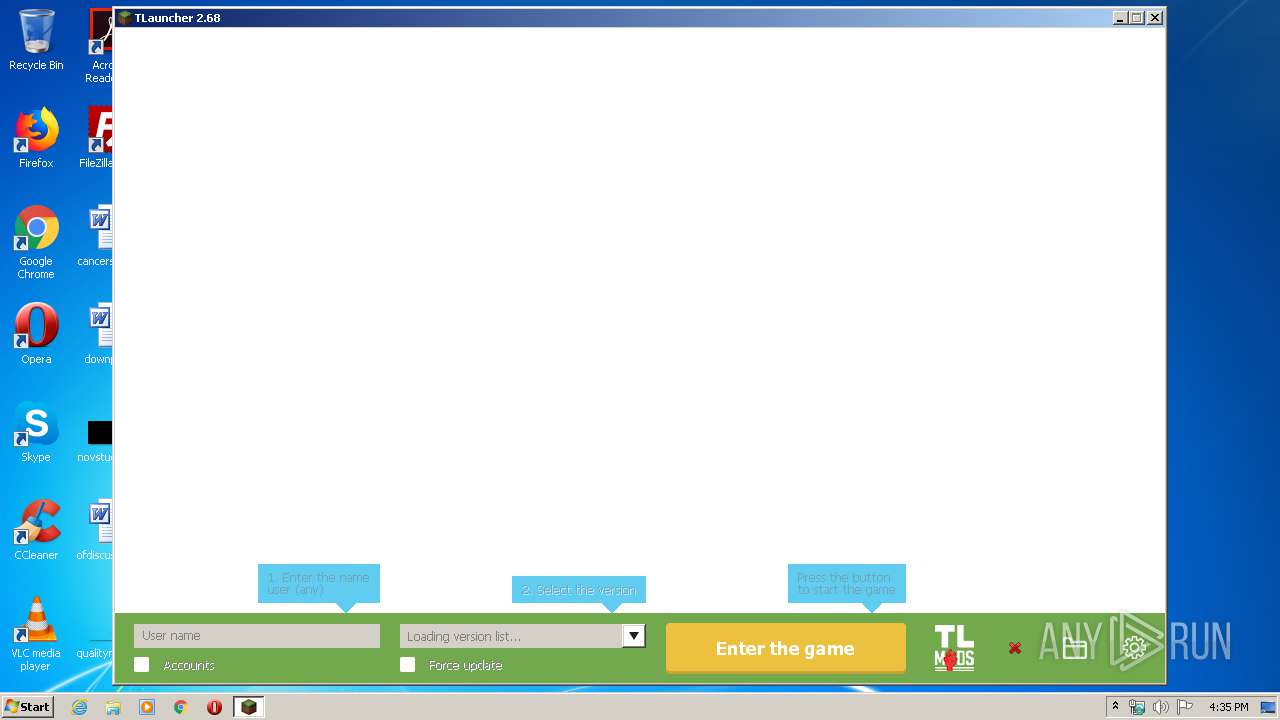
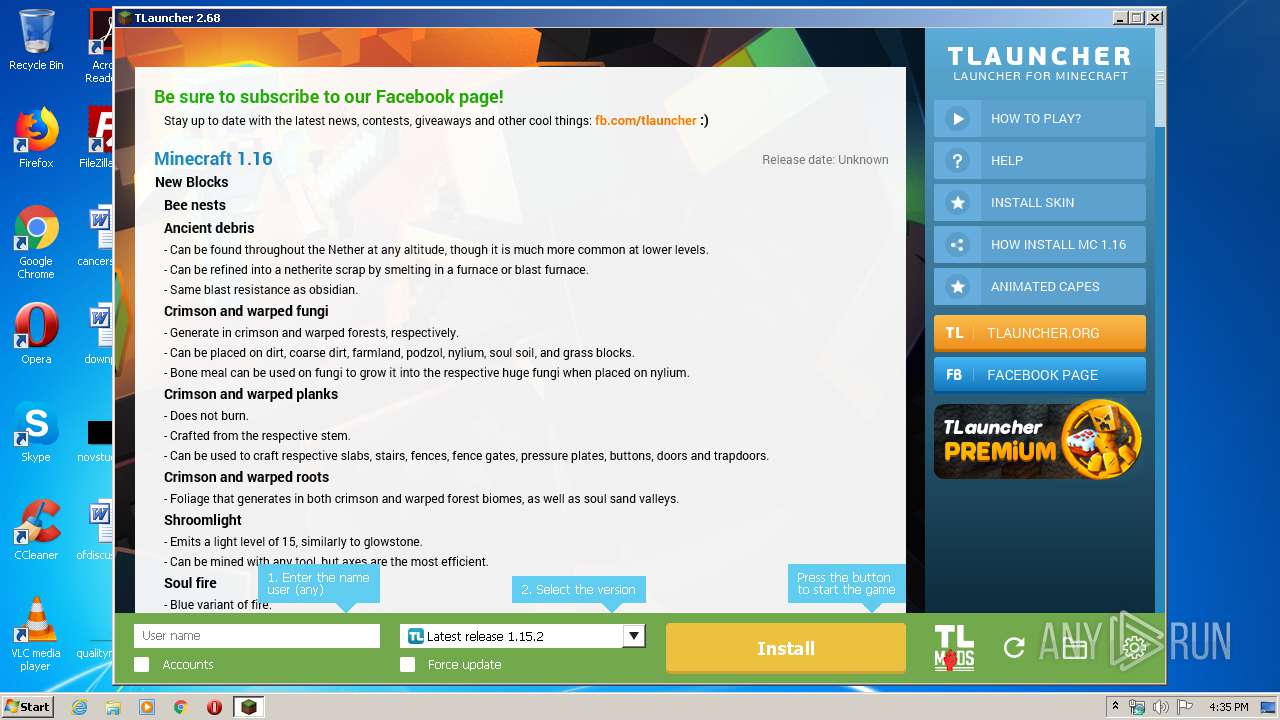
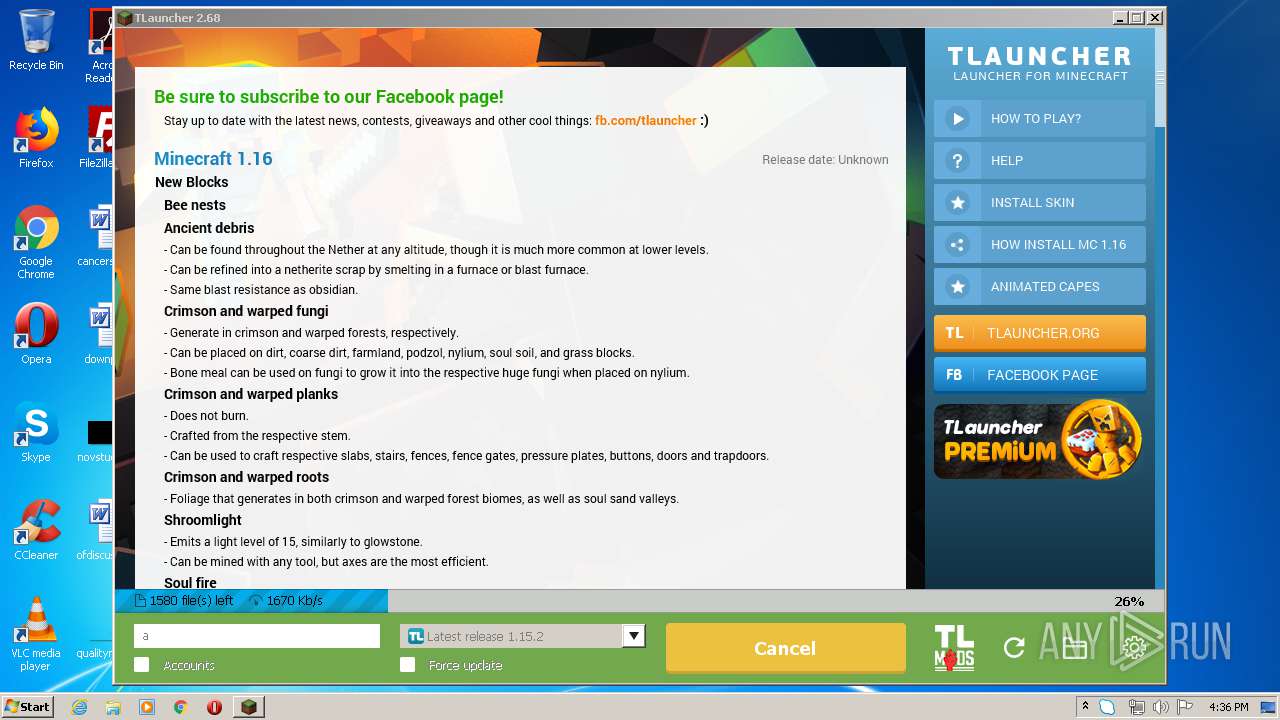
| File name: | TLauncher.exe |
| Full analysis: | https://app.any.run/tasks/95571a9f-828b-49a2-a75f-28b6f5531675 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2020, 15:34:18 |
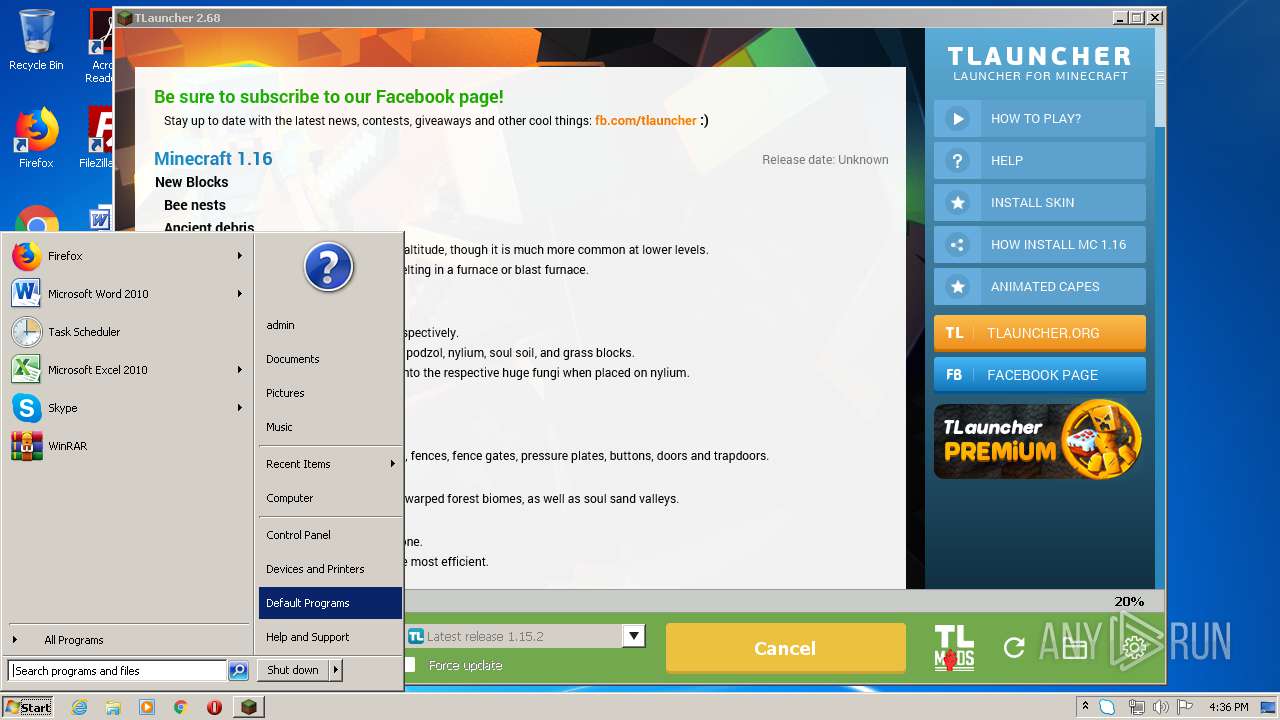
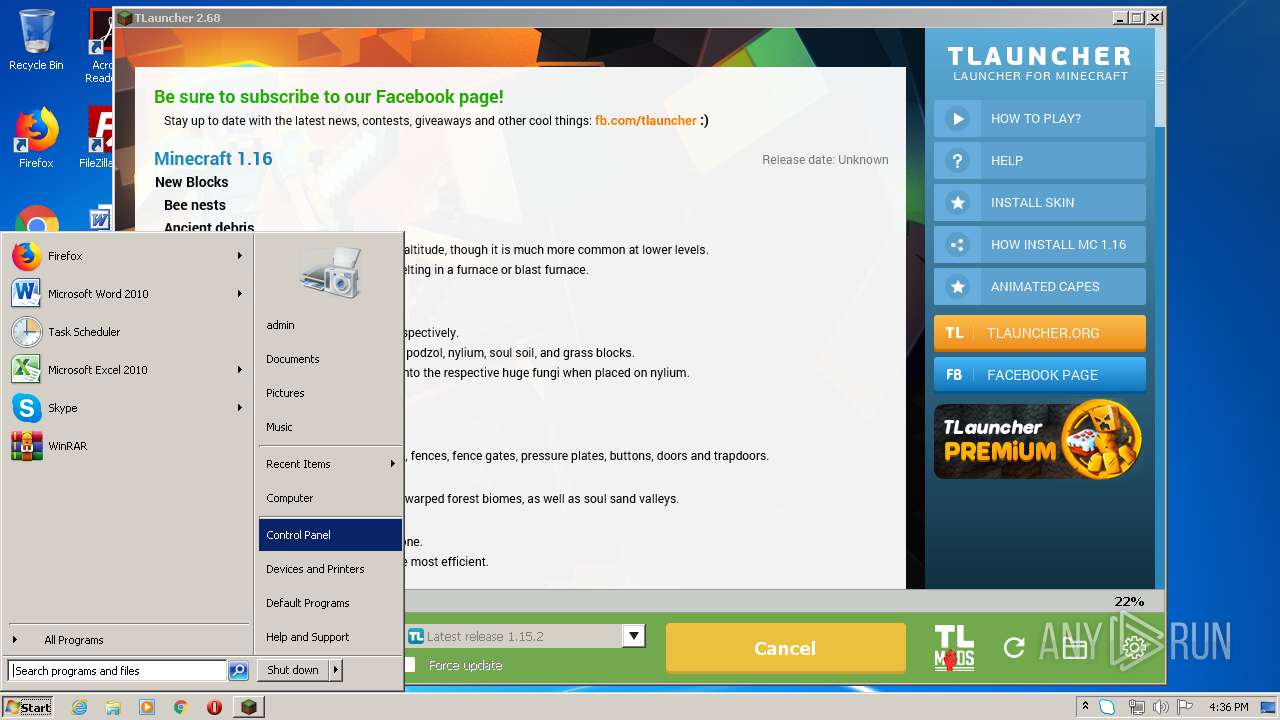
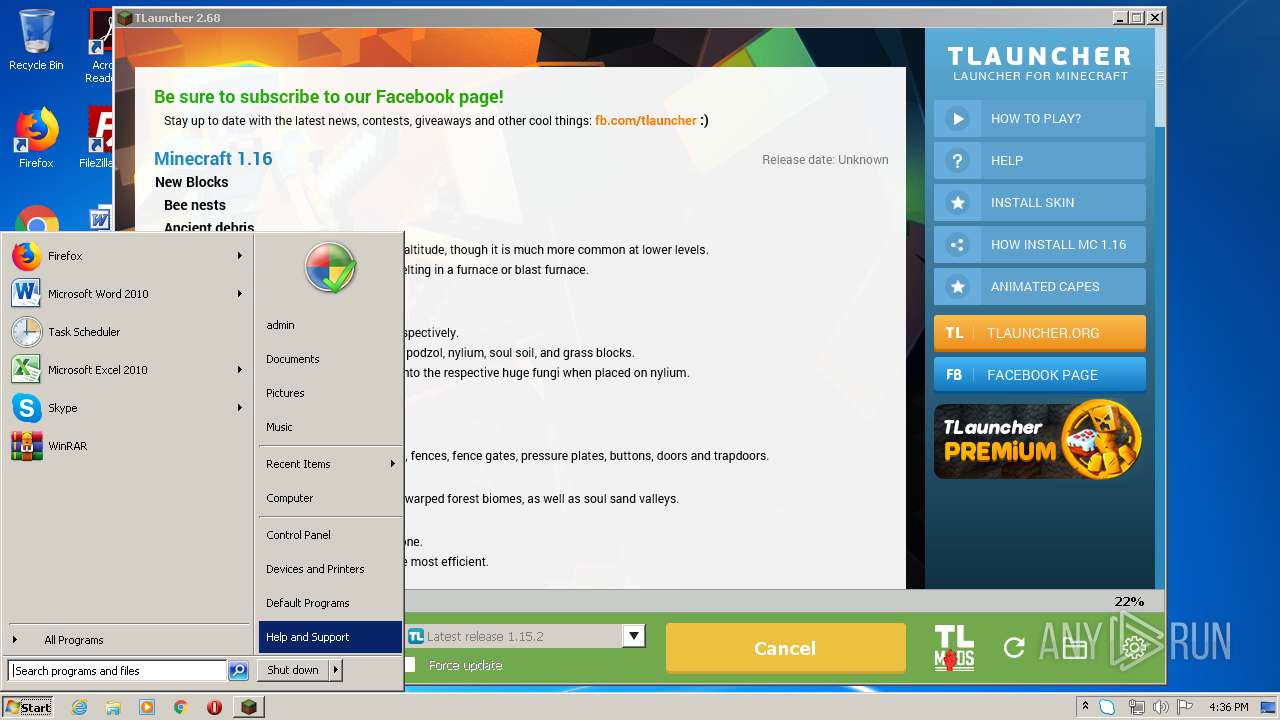
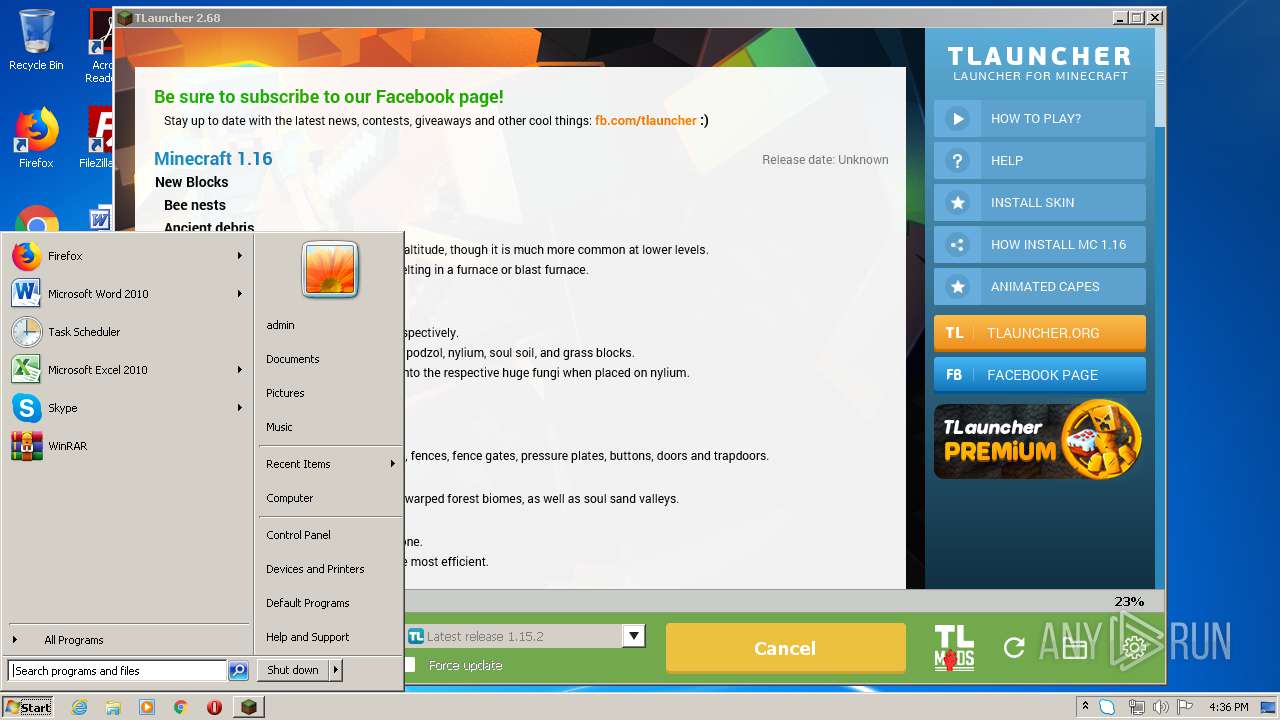
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | B4C85FACB1BA9B726675BC7F8E9DC8BB |
| SHA1: | DAAF287AD2BE511C99260E57C98575740EB65AB2 |
| SHA256: | FCFB649A92BC918B5A211B8CFA07F2930BC727B144CF2CC259E9E1697C3F44C1 |
| SSDEEP: | 49152:t3ONBK350OU1otFj/HziCePD0kEjAhX/WyjORRFW:ZONBK350OU1QJHWX74LlW |
MALICIOUS
Actions looks like stealing of personal data
- javaw.exe (PID: 2808)
Changes the autorun value in the registry
- reg.exe (PID: 404)
SUSPICIOUS
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3864)
- javaw.exe (PID: 2808)
Starts application with an unusual extension
- cmd.exe (PID: 1860)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 2900)
- cmd.exe (PID: 3432)
- cmd.exe (PID: 2824)
- cmd.exe (PID: 3748)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 1860)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 3748)
- cmd.exe (PID: 3432)
Executes JAVA applets
- javaw.exe (PID: 3864)
- TLauncher.exe (PID: 2672)
Creates files in the user directory
- dxdiag.exe (PID: 2128)
- Skype.exe (PID: 2860)
- Skype.exe (PID: 3484)
- javaw.exe (PID: 2808)
- javaw.exe (PID: 3864)
- Skype.exe (PID: 2580)
Application launched itself
- Skype.exe (PID: 2860)
- Skype.exe (PID: 2372)
- Skype.exe (PID: 2580)
- Skype.exe (PID: 3484)
- javaw.exe (PID: 3864)
- Skype.exe (PID: 3944)
Reads CPU info
- Skype.exe (PID: 3944)
- Skype.exe (PID: 2860)
- Skype.exe (PID: 2372)
Modifies the open verb of a shell class
- Skype.exe (PID: 2860)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 2900)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 2860)
INFO
Manual execution by user
- Skype.exe (PID: 2860)
- Skype.exe (PID: 3944)
- Skype.exe (PID: 2372)
Reads the hosts file
- Skype.exe (PID: 3944)
- Skype.exe (PID: 2860)
- Skype.exe (PID: 2372)
Reads settings of System Certificates
- Skype.exe (PID: 2860)
Dropped object may contain Bitcoin addresses
- Skype.exe (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:15 18:13:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 25088 |
| InitializedDataSize: | 16896 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.68.0.0 |
| ProductVersionNumber: | 2.68.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher |
| FileVersion: | 2.68 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Inc. |
| LegalTrademarks: | - |
| OriginalFileName: | TLauncher.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.68.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2019 17:13:27 |
| Detected languages: |
|
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher |
| FileVersion: | 2.68 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Inc. |
| LegalTrademarks: | - |
| OriginalFilename: | TLauncher.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.68.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 15-Dec-2019 17:13:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006080 | 0x00006200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.98243 |
.data | 0x00008000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00009000 | 0x00000510 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01355 |
.bss | 0x0000A000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00013000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65264 |
.rsrc | 0x00014000 | 0x00002D9C | 0x00002E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.52768 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.24996 | 728 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
10 | 3.39275 | 13 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 4.10695 | 31 | UNKNOWN | Process Default Language | RT_RCDATA |
30 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
101 | 4.04307 | 50 | UNKNOWN | Process Default Language | RT_RCDATA |
102 | 4.26779 | 115 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
90
Monitored processes
39
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | C:\Windows\system32\reg.exe ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "Skype for Desktop" /t REG_SZ /d "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" /f | C:\Windows\system32\reg.exe | Skype.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1428 | wmic CPU get NAME | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1452 | cmd.exe /C chcp 437 & wmic os get osarchitecture | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1860 | cmd.exe /C chcp 437 & wmic os get osarchitecture | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=2043B9A1629B13092D409DBCA6625A0F --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=1 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=2043B9A1629B13092D409DBCA6625A0F --renderer-client-id=7 --mojo-platform-channel-handle=2792 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 3221225794 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 2 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2128 | dxdiag /whql:off /t C:\Users\admin\AppData\Roaming\.minecraft\logs\tlauncher\dxdiag.txt | C:\Windows\system32\dxdiag.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2316 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2348 | wmic os get osarchitecture | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | explorer.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
Total events
1 165
Read events
982
Write events
167
Delete events
16
Modification events
| (PID) Process: | (3864) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2808) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2808) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2808) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2440) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2440) systeminfo.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\mlang.dll,-4386 |
Value: English (United States) | |||
| (PID) Process: | (2128) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | write | Name: | DxDiag In SystemInfo |
Value: 1 | |||
| (PID) Process: | (2128) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | delete value | Name: | DxDiag In SystemInfo |
Value: 1 | |||
| (PID) Process: | (2128) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | write | Name: | DxDiag In DirectDraw |
Value: 1 | |||
| (PID) Process: | (2128) dxdiag.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectX Diagnostic Tool |
| Operation: | delete value | Name: | DxDiag In DirectDraw |
Value: 1 | |||
Executable files
6
Suspicious files
27
Text files
140
Unknown types
504
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\javax\inject\javax.inject\1\javax.inject-1.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\inject\guice\4.1.0\guice-4.1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\inject\extensions\guice-assistedinject\4.1.0\guice-assistedinject-4.1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\aopalliance\aopalliance\1.0\aopalliance-1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\net\sf\jopt-simple\jopt-simple\4.9\jopt-simple-4.9.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\log4j\log4j\1.2.17\log4j-1.2.17.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\guava\guava\19.0\guava-19.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\apache\commons\commons-lang3\3.4\commons-lang3-3.4.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tukaani\xz\1.5\xz-1.5.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 3864 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tlauncher\tlauncher-resource\1.4\tlauncher-resource-1.4.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
603
TCP/UDP connections
36
DNS requests
21
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3864 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://repo.tlauncher.org/update/downloads/libraries/com/github/junrar/junrar/0.7/junrar-0.7.jar | US | compressed | 151 Kb | whitelisted |
3864 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://repo.tlauncher.org/update/downloads/libraries/com/google/guava/guava/19.0/guava-19.0.jar | US | java | 2.20 Mb | whitelisted |
3864 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://repo.tlauncher.org/update/downloads/libraries/log4j/log4j/1.2.17/log4j-1.2.17.jar | US | java | 478 Kb | whitelisted |
3864 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://repo.tlauncher.org/update/downloads/libraries/org/apache/commons/commons-lang3/3.4/commons-lang3-3.4.jar | US | compressed | 424 Kb | whitelisted |
3864 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://repo.tlauncher.org/update/downloads/libraries/org/tukaani/xz/1.5/xz-1.5.jar | US | java | 97.2 Kb | whitelisted |
2808 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://img.tlauncher.org/update/downloads/configs/client/style_new_bes_fontov.css | US | text | 5.76 Kb | malicious |
3864 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://repo.tlauncher.org/update/downloads/libraries/org/tlauncher/picture-bundle/2.8/picture-bundle-2.8.jar | US | compressed | 2.06 Mb | whitelisted |
2808 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://repo.tlauncher.org/update/lch/update_2.0.json?version=2.68&client=dfa0d279-0043-40e8-a357-02c4d9f08e0f | US | text | 7.69 Kb | whitelisted |
2808 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn2.png | US | image | 193 b | malicious |
2808 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://img.tlauncher.org/update/downloads/configs/client/images/tl-en-pe-news.png | US | image | 132 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3864 | javaw.exe | 104.20.2.71:80 | repo.tlauncher.org | Cloudflare Inc | US | suspicious |
2808 | javaw.exe | 104.20.3.71:80 | repo.tlauncher.org | Cloudflare Inc | US | unknown |
2808 | javaw.exe | 104.20.2.71:80 | repo.tlauncher.org | Cloudflare Inc | US | suspicious |
3944 | Skype.exe | 52.174.193.75:443 | get.skype.com | Microsoft Corporation | NL | whitelisted |
3864 | javaw.exe | 46.4.112.226:443 | securerepository.net | Hetzner Online GmbH | DE | malicious |
2808 | javaw.exe | 104.16.132.229:443 | ajax.cloudflare.com | Cloudflare Inc | US | suspicious |
2808 | javaw.exe | 176.9.83.82:8092 | stat.tlrepo.com | Hetzner Online GmbH | DE | suspicious |
2808 | javaw.exe | 13.225.87.58:80 | resources.download.minecraft.net | — | US | unknown |
2808 | javaw.exe | 104.20.2.71:443 | repo.tlauncher.org | Cloudflare Inc | US | suspicious |
2860 | Skype.exe | 52.174.193.75:443 | get.skype.com | Microsoft Corporation | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
repo.tlauncher.org |
| whitelisted |
central.maven.org |
| whitelisted |
securerepository.net |
| whitelisted |
page.tlauncher.org |
| malicious |
img.tlauncher.org |
| malicious |
ajax.cloudflare.com |
| whitelisted |
launchermeta.mojang.com |
| whitelisted |
stat.tlrepo.com |
| suspicious |
resources.download.minecraft.net |
| shared |
tlauncher.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3864 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3864 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3864 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3864 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3864 | javaw.exe | Potentially Bad Traffic | ET INFO JAR Size Under 30K Size - Potentially Hostile |
3864 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3864 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3864 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
Process | Message |
|---|---|
Skype.exe | [2744:880:0523/163538.293:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [2744:880:0523/163538.297:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [2744:880:0523/163538.296:VERBOSE1:crash_service.cc(145)] window handle is 000D01D0
|
Skype.exe | [2744:3240:0523/163538.299:VERBOSE1:crash_service.cc(333)] client start. pid = 2860
|
Skype.exe | [2744:880:0523/163538.299:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [2744:880:0523/163538.297:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [2744:3240:0523/163538.320:VERBOSE1:crash_service.cc(333)] client start. pid = 3944
|
Skype.exe | [2068:2840:0523/163538.761:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [2068:2840:0523/163538.762:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [2068:2840:0523/163538.762:VERBOSE1:crash_service.cc(145)] window handle is 000801CA
|