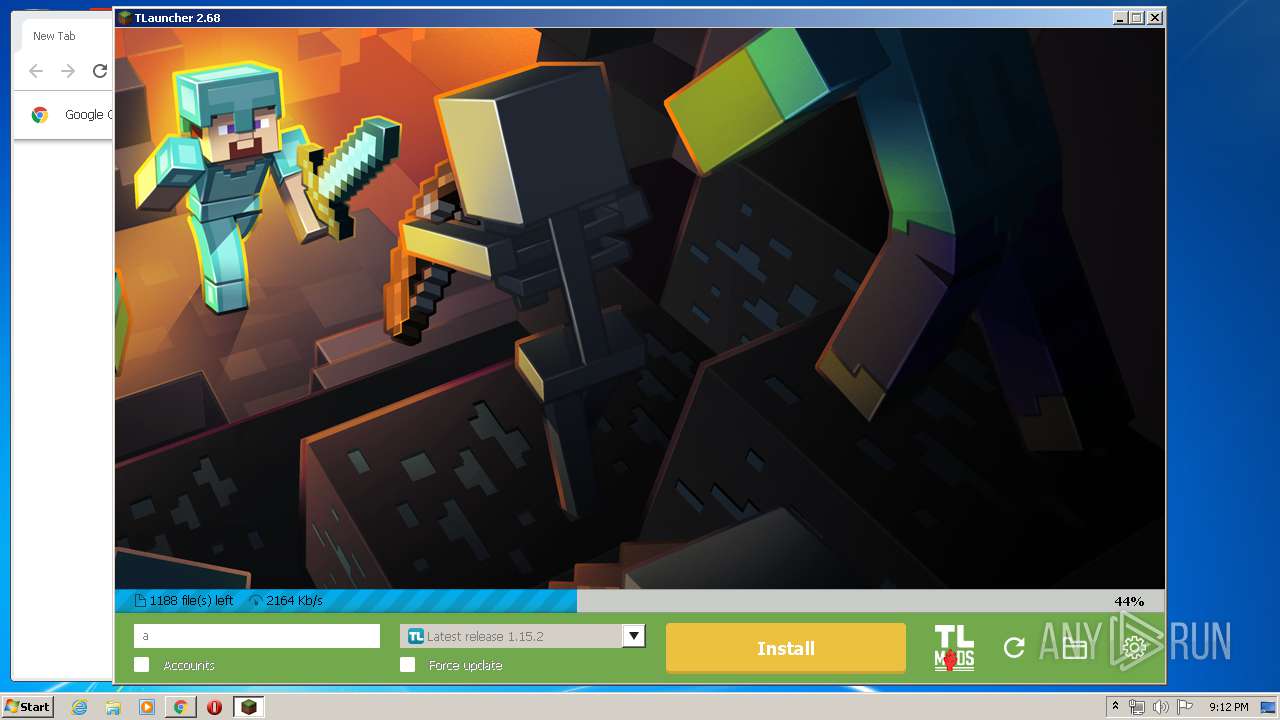
| File name: | TLauncher.exe |
| Full analysis: | https://app.any.run/tasks/3ee45cf7-23d7-4496-af69-83f3abb054dd |
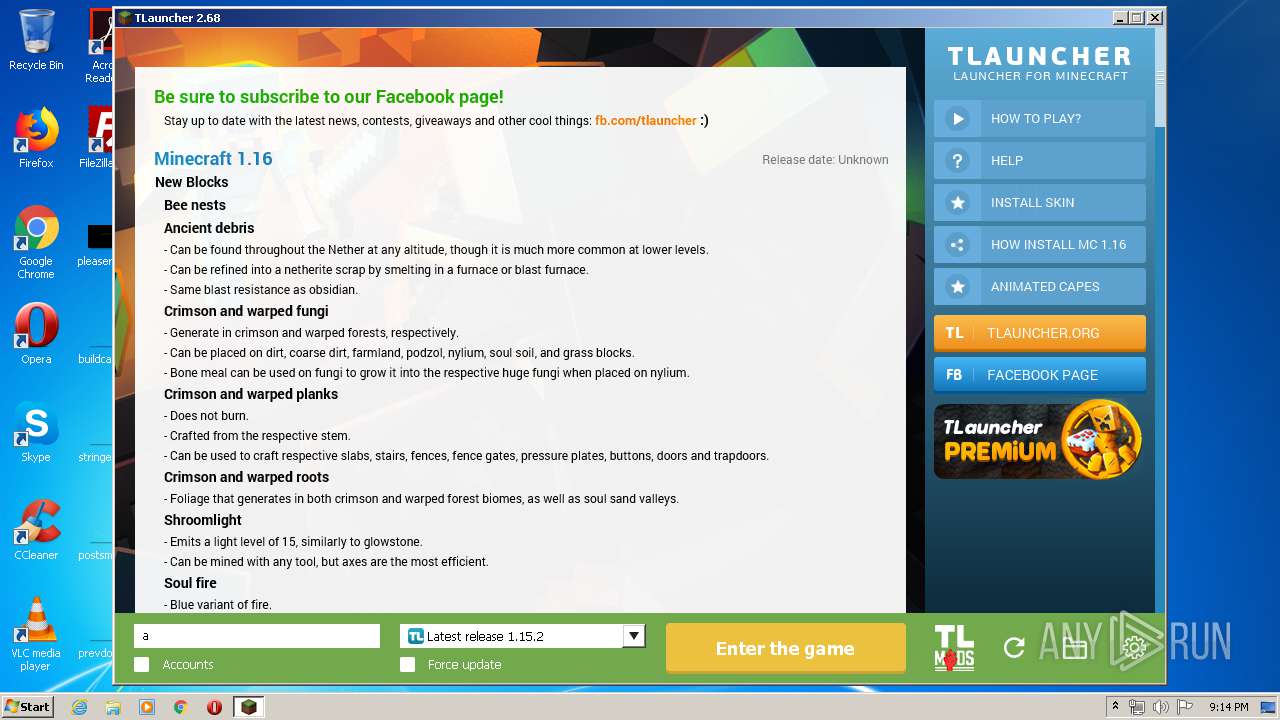
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2020, 20:10:27 |
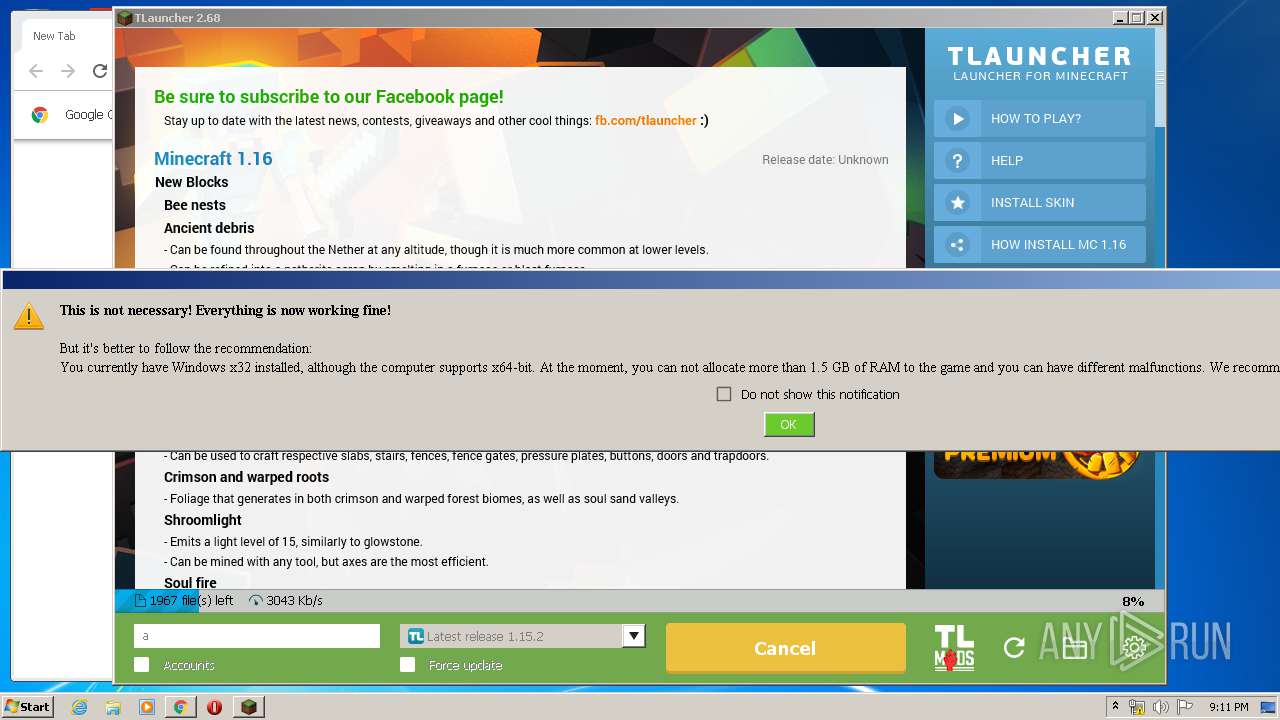
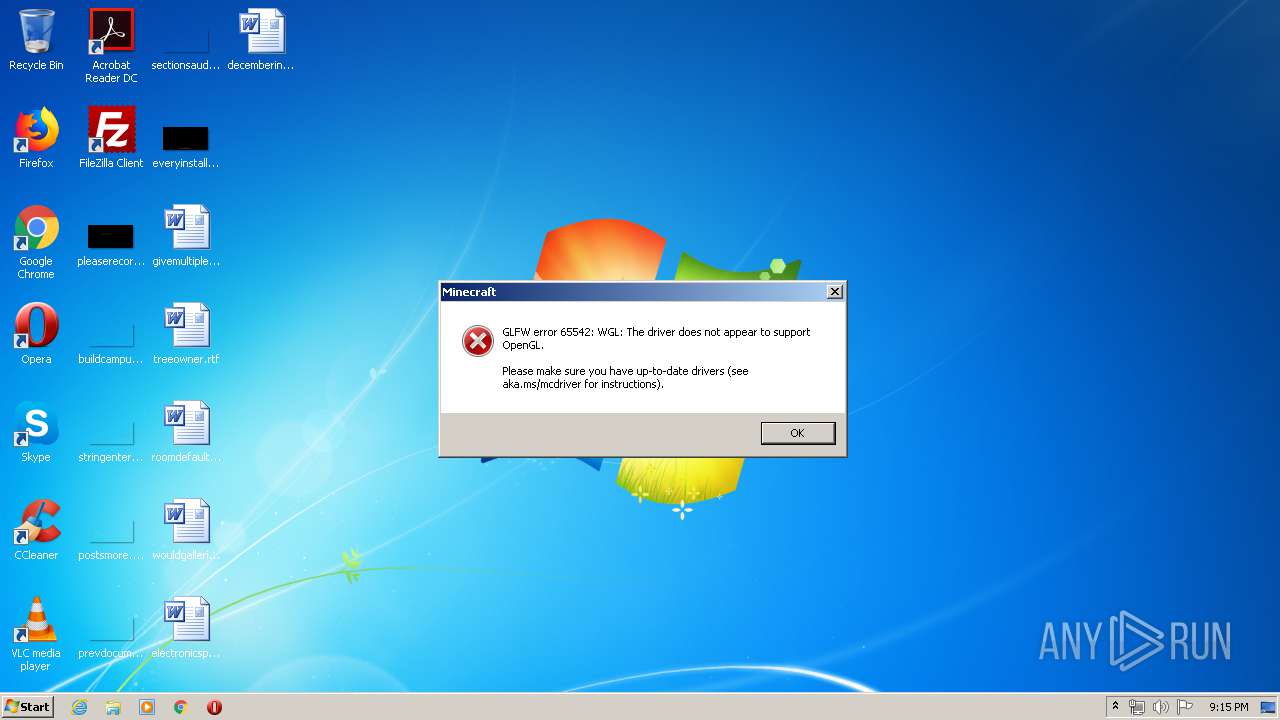
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | B4C85FACB1BA9B726675BC7F8E9DC8BB |
| SHA1: | DAAF287AD2BE511C99260E57C98575740EB65AB2 |
| SHA256: | FCFB649A92BC918B5A211B8CFA07F2930BC727B144CF2CC259E9E1697C3F44C1 |
| SSDEEP: | 49152:t3ONBK350OU1otFj/HziCePD0kEjAhX/WyjORRFW:ZONBK350OU1QJHWX74LlW |
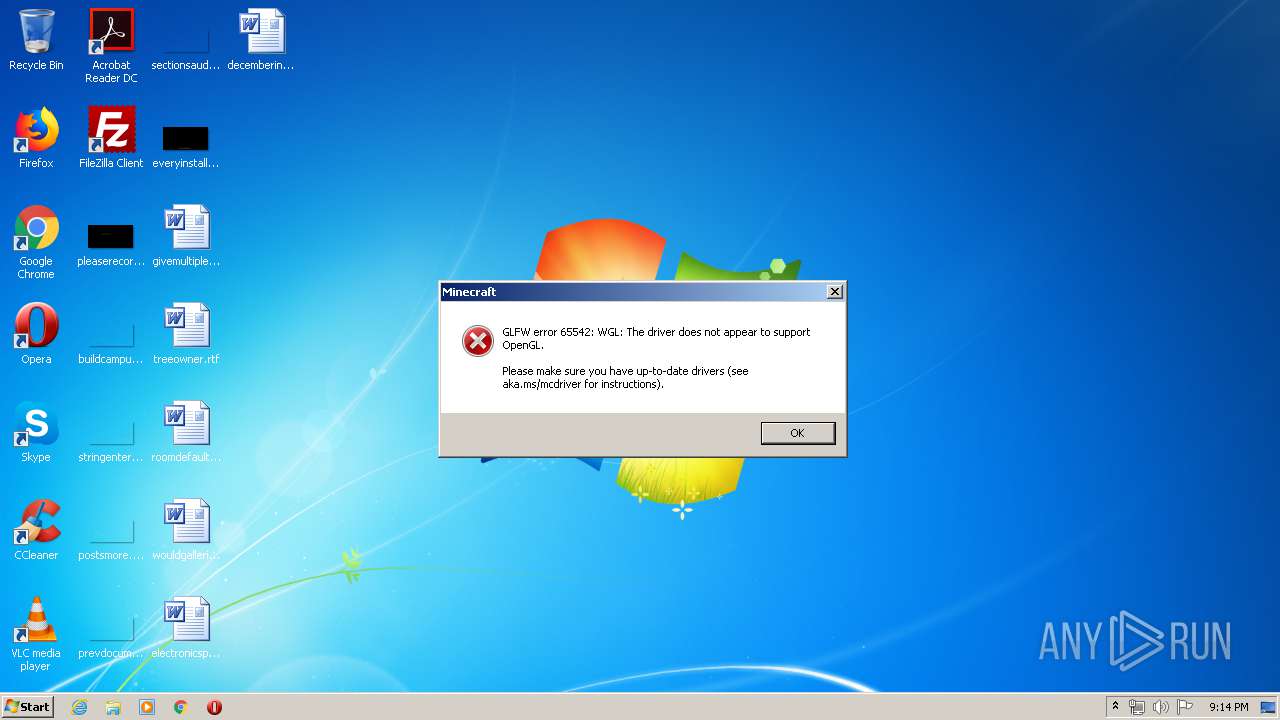
MALICIOUS
Actions looks like stealing of personal data
- javaw.exe (PID: 2744)
- DllHost.exe (PID: 3380)
Loads dropped or rewritten executable
- javaw.exe (PID: 1908)
- javaw.exe (PID: 2732)
SUSPICIOUS
Starts CMD.EXE for commands execution
- javaw.exe (PID: 740)
- javaw.exe (PID: 2744)
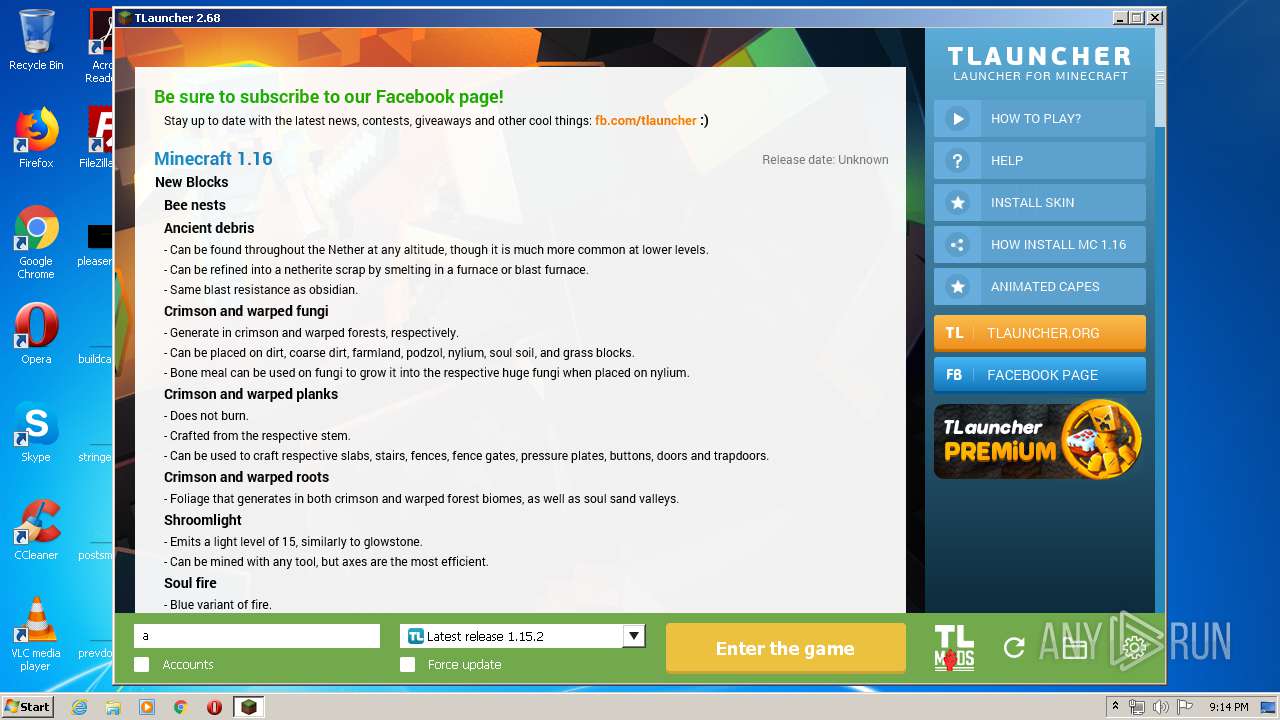
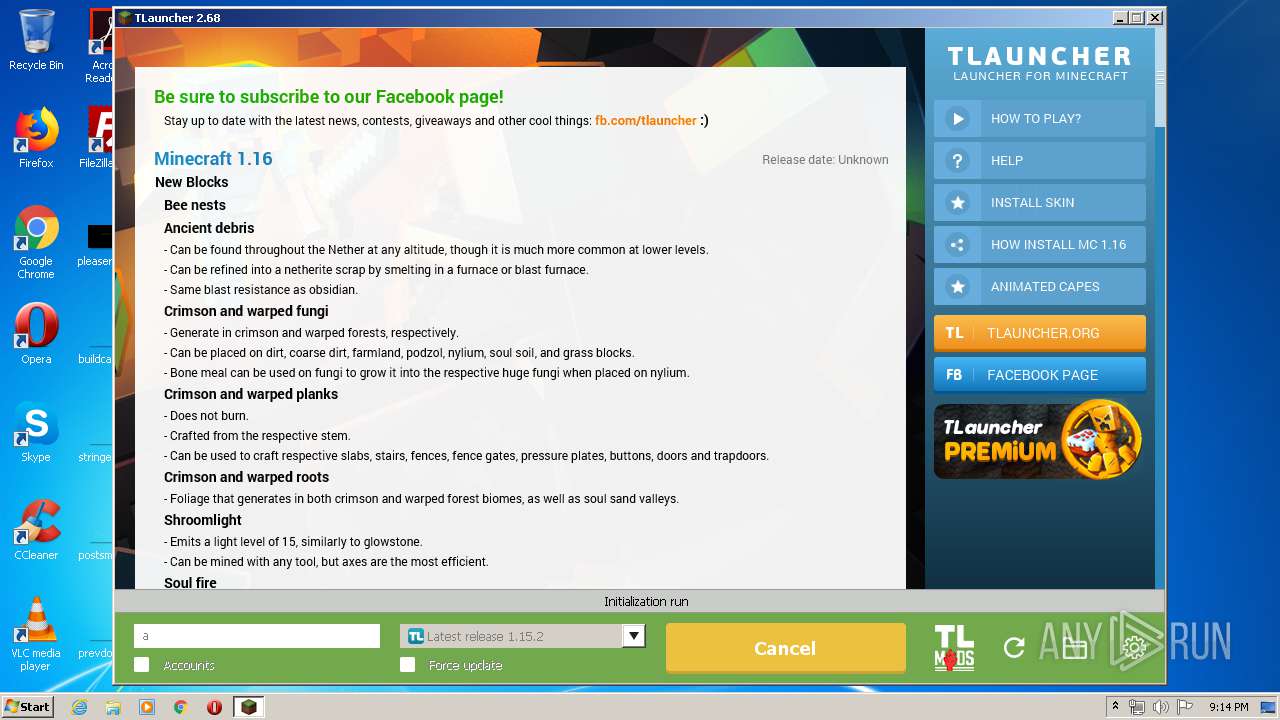
Executes JAVA applets
- TLauncher.exe (PID: 2376)
- javaw.exe (PID: 740)
- javaw.exe (PID: 2744)
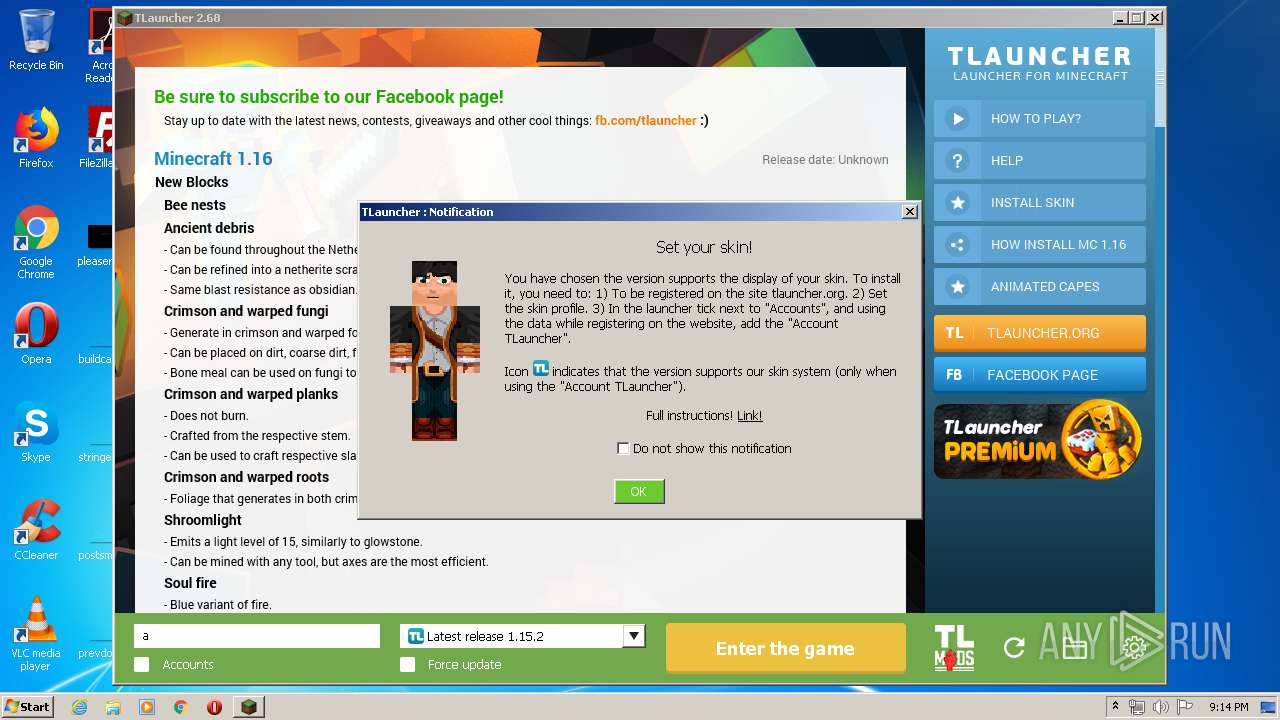
Creates files in the user directory
- javaw.exe (PID: 740)
- javaw.exe (PID: 1908)
- dxdiag.exe (PID: 4088)
- javaw.exe (PID: 2732)
- javaw.exe (PID: 2744)
Starts application with an unusual extension
- cmd.exe (PID: 3408)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 2068)
- cmd.exe (PID: 3848)
- cmd.exe (PID: 2480)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 3932)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 3408)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 2068)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 3848)
Application launched itself
- javaw.exe (PID: 740)
- javaw.exe (PID: 2744)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 2480)
Executable content was dropped or overwritten
- javaw.exe (PID: 2744)
Executed via COM
- DllHost.exe (PID: 3380)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1828)
INFO
Manual execution by user
- chrome.exe (PID: 1828)
Reads the hosts file
- chrome.exe (PID: 1828)
- chrome.exe (PID: 4064)
Application launched itself
- chrome.exe (PID: 1828)
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 2744)
Reads settings of System Certificates
- chrome.exe (PID: 4064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:15 18:13:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 25088 |
| InitializedDataSize: | 16896 |
| UninitializedDataSize: | 36864 |
| EntryPoint: | 0x1290 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
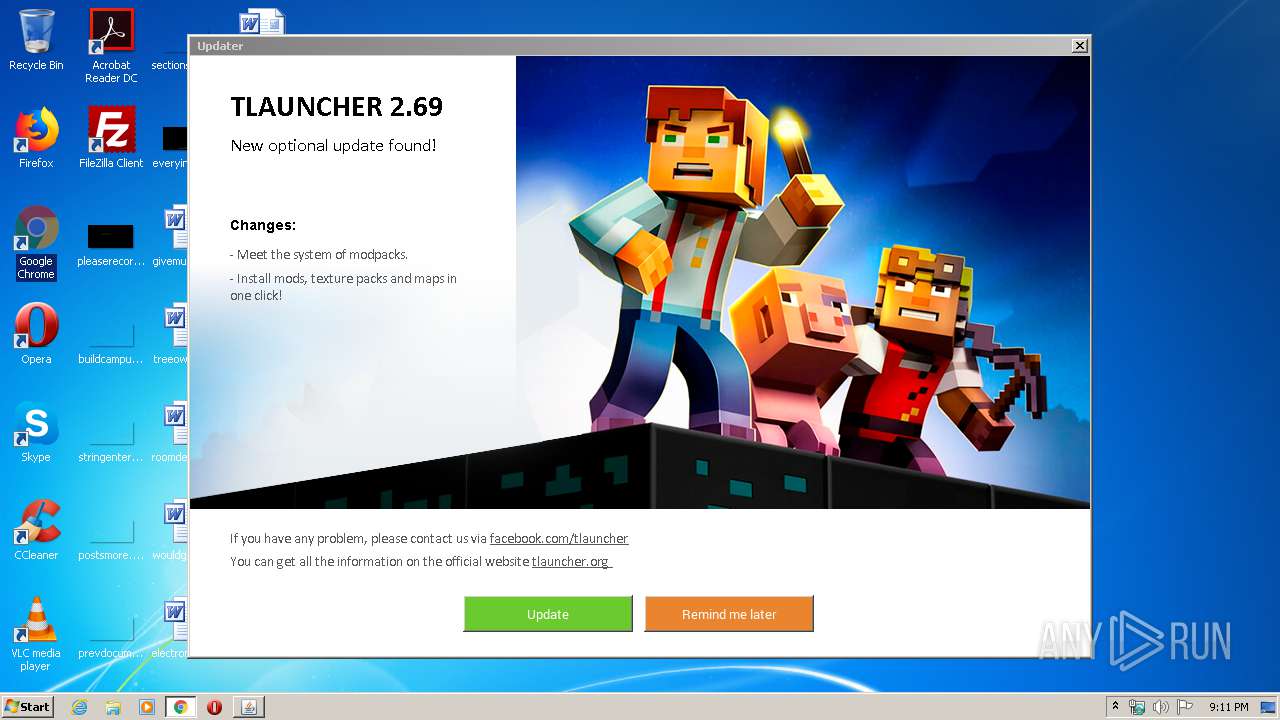
| FileVersionNumber: | 2.68.0.0 |
| ProductVersionNumber: | 2.68.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Windows NT |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher |
| FileVersion: | 2.68 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Inc. |
| LegalTrademarks: | - |
| OriginalFileName: | TLauncher.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.68.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2019 17:13:27 |
| Detected languages: |
|
| CompanyName: | TLauncher Inc. |
| FileDescription: | TLauncher |
| FileVersion: | 2.68 |
| InternalName: | TLauncher |
| LegalCopyright: | TLauncher Inc. |
| LegalTrademarks: | - |
| OriginalFilename: | TLauncher.exe |
| ProductName: | TLauncher |
| ProductVersion: | 2.68.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 15-Dec-2019 17:13:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006080 | 0x00006200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.98243 |
.data | 0x00008000 | 0x00000040 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.163808 |
.rdata | 0x00009000 | 0x00000510 | 0x00000600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01355 |
.bss | 0x0000A000 | 0x00008E30 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00013000 | 0x00000AA8 | 0x00000C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.65264 |
.rsrc | 0x00014000 | 0x00002D9C | 0x00002E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.52768 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.24996 | 728 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.25163 | 6 | UNKNOWN | Process Default Language | RT_RCDATA |
10 | 3.39275 | 13 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 4.10695 | 31 | UNKNOWN | Process Default Language | RT_RCDATA |
30 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
101 | 4.04307 | 50 | UNKNOWN | Process Default Language | RT_RCDATA |
102 | 4.26779 | 115 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
msvcrt.dll |
Total processes
114
Monitored processes
62
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4629789112213147899,14490072297711839695,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=586704747097534460 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4629789112213147899,14490072297711839695,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16947649307422319481 --mojo-platform-channel-handle=3408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4629789112213147899,14490072297711839695,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14872271354627509699 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 540 | wmic os get osarchitecture | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4629789112213147899,14490072297711839695,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10793358305740029890 --mojo-platform-channel-handle=3568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 740 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\TLauncher.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | TLauncher.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4629789112213147899,14490072297711839695,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15297296158315060939 --mojo-platform-channel-handle=3688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | cmd.exe /C chcp 437 & wmic qfe get HotFixID | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1328 | cmd.exe /C chcp 437 & wmic os get osarchitecture | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1388 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 805
Read events
1 524
Write events
260
Delete events
21
Modification events
| (PID) Process: | (740) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2744) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2744) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2744) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (1828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
Executable files
45
Suspicious files
158
Text files
702
Unknown types
1 850
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\javax\inject\javax.inject\1\javax.inject-1.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\aopalliance\aopalliance\1.0\aopalliance-1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\net\sf\jopt-simple\jopt-simple\4.9\jopt-simple-4.9.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\inject\guice\4.1.0\guice-4.1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\inject\extensions\guice-assistedinject\4.1.0\guice-assistedinject-4.1.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\log4j\log4j\1.2.17\log4j-1.2.17.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\com\google\guava\guava\19.0\guava-19.0.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\apache\commons\commons-lang3\3.4\commons-lang3-3.4.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tukaani\xz\1.5\xz-1.5.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
| 740 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\tlauncher_libraries\org\tlauncher\tlauncher-resource\1.4\tlauncher-resource-1.4.jar.tlauncherdownload | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2 134
TCP/UDP connections
79
DNS requests
50
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2744 | javaw.exe | HEAD | 200 | 104.20.2.71:80 | http://page.tlauncher.org/ | US | — | — | malicious |
2744 | javaw.exe | GET | 200 | 104.20.2.71:80 | http://page.tlauncher.org/update/downloads/configs/client/eng.html | US | html | 16.7 Kb | malicious |
2744 | javaw.exe | GET | 200 | 104.20.3.71:80 | http://repo.tlauncher.org/update/lch/update_2.0.json?version=2.68&client=c44a20a1-3d3b-40c1-8640-2307592a75cf | US | text | 7.69 Kb | whitelisted |
2744 | javaw.exe | GET | 200 | 104.20.3.71:80 | http://img.tlauncher.org/update/downloads/configs/client/images/icons/btn4.png | US | image | 205 b | malicious |
2744 | javaw.exe | GET | 200 | 104.20.3.71:80 | http://repo.tlauncher.org/update/downloads/configs/inner_servers.json | US | text | 3.36 Kb | whitelisted |
2744 | javaw.exe | GET | 200 | 104.20.3.71:80 | http://img.tlauncher.org/update/downloads/configs/client/style_new_bes_fontov.css | US | text | 5.76 Kb | malicious |
2744 | javaw.exe | GET | 200 | 104.20.3.71:80 | http://repo.tlauncher.org/update/downloads/libraries/org/tlauncher/authlib/libraries-1.6.json | US | text | 86.5 Kb | whitelisted |
2744 | javaw.exe | GET | 200 | 104.20.3.71:80 | http://img.tlauncher.org/update/downloads/configs/client/images/scroll.png | US | image | 132 b | malicious |
2744 | javaw.exe | GET | 200 | 104.20.3.71:80 | http://img.tlauncher.org/update/downloads/configs/client/images/tl-en-pe-news.png | US | image | 132 Kb | malicious |
740 | javaw.exe | GET | 200 | 104.20.3.71:80 | http://repo.tlauncher.org/update/downloads/libraries/net/sf/jopt-simple/jopt-simple/4.9/jopt-simple-4.9.jar | US | java | 64.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4064 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4064 | chrome.exe | 216.58.212.174:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
740 | javaw.exe | 46.4.112.226:443 | — | Hetzner Online GmbH | DE | malicious |
740 | javaw.exe | 104.20.3.71:80 | repo.tlauncher.org | Cloudflare Inc | US | unknown |
2744 | javaw.exe | 104.20.2.71:80 | repo.tlauncher.org | Cloudflare Inc | US | suspicious |
2744 | javaw.exe | 104.20.3.71:80 | repo.tlauncher.org | Cloudflare Inc | US | unknown |
4064 | chrome.exe | 172.217.23.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2744 | javaw.exe | 99.86.1.139:443 | launchermeta.mojang.com | AT&T Services, Inc. | US | unknown |
4064 | chrome.exe | 172.217.23.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
securerepository.net |
| whitelisted |
central.maven.org |
| whitelisted |
repo.tlauncher.org |
| whitelisted |
page.tlauncher.org |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
img.tlauncher.org |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
740 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
740 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
740 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
740 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
740 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
2744 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
2744 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
2744 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
2744 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
2744 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |