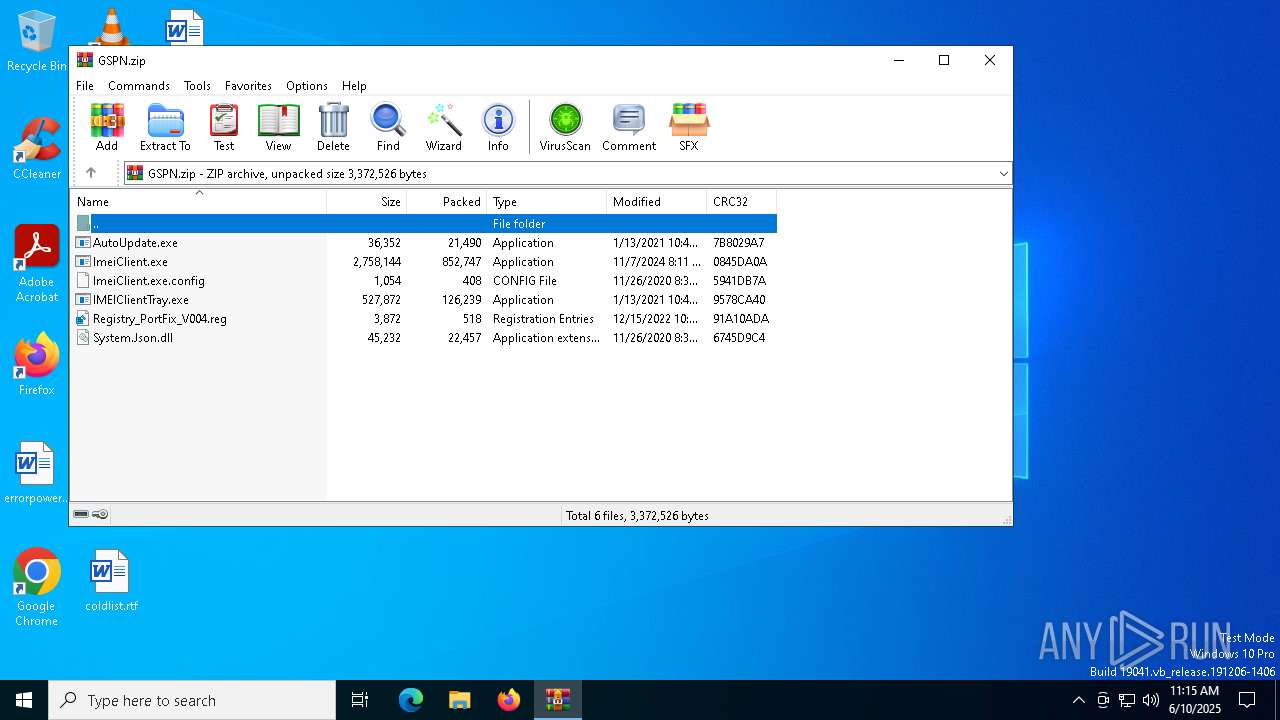
| File name: | GSPN.zip |
| Full analysis: | https://app.any.run/tasks/25fbcc42-60d6-4c7e-a4de-ffade03d63a9 |
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2025, 11:15:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E15A19B1D8CFCDF645F9FED49D5812F4 |
| SHA1: | 08A53707C45D14C28C70083E40ADCF66DBD22EFD |
| SHA256: | FCECADC6C900F9960BDE2F7BB618FFF0FE9BDB00F28D1DBED94B7B73ADF1C2D4 |
| SSDEEP: | 49152:Ax9lfuRNnHTxJsmzTPQVkZVFv/ACdlxlk70ds72uE3pGm5fAllE:29lGNnHTxJsoTmkrFwC9S7l7TE3pGmKM |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 1348)
Changes the autorun value in the registry
- IMEIClientTray.exe (PID: 208)
- IMEIClientTray.exe (PID: 7348)
Renames files like ransomware
- AutoUpdate.exe (PID: 672)
SUSPICIOUS
Reads security settings of Internet Explorer
- ImeiClient.exe (PID: 6820)
- AutoUpdate.exe (PID: 672)
- ImeiClient.exe (PID: 2908)
Process drops legitimate windows executable
- AutoUpdate.exe (PID: 672)
- WinRAR.exe (PID: 1348)
Executable content was dropped or overwritten
- AutoUpdate.exe (PID: 672)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1348)
Manual execution by a user
- ImeiClient.exe (PID: 3872)
- ImeiClient.exe (PID: 6820)
Creates files in the program directory
- ImeiClient.exe (PID: 6820)
Reads the computer name
- ImeiClient.exe (PID: 6820)
- IMEIClientTray.exe (PID: 208)
- AutoUpdate.exe (PID: 672)
- ImeiClient.exe (PID: 2908)
- IMEIClientTray.exe (PID: 7348)
Checks supported languages
- IMEIClientTray.exe (PID: 208)
- ImeiClient.exe (PID: 6820)
- AutoUpdate.exe (PID: 672)
- ImeiClient.exe (PID: 2908)
- IMEIClientTray.exe (PID: 7348)
Process checks computer location settings
- ImeiClient.exe (PID: 6820)
- AutoUpdate.exe (PID: 672)
- ImeiClient.exe (PID: 2908)
Reads the machine GUID from the registry
- ImeiClient.exe (PID: 6820)
- IMEIClientTray.exe (PID: 208)
- AutoUpdate.exe (PID: 672)
- ImeiClient.exe (PID: 2908)
- IMEIClientTray.exe (PID: 7348)
Checks proxy server information
- ImeiClient.exe (PID: 6820)
- AutoUpdate.exe (PID: 672)
- ImeiClient.exe (PID: 2908)
- slui.exe (PID: 8052)
Launching a file from a Registry key
- IMEIClientTray.exe (PID: 208)
- IMEIClientTray.exe (PID: 7348)
Reads the software policy settings
- ImeiClient.exe (PID: 6820)
- AutoUpdate.exe (PID: 672)
- slui.exe (PID: 2040)
- ImeiClient.exe (PID: 2908)
- slui.exe (PID: 8052)
Disables trace logs
- AutoUpdate.exe (PID: 672)
- ImeiClient.exe (PID: 2908)
- ImeiClient.exe (PID: 6820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2021:01:13 10:49:58 |
| ZipCRC: | 0x9578ca40 |
| ZipCompressedSize: | 126239 |
| ZipUncompressedSize: | 527872 |
| ZipFileName: | IMEIClientTray.exe |
Total processes
139
Monitored processes
10
Malicious processes
2
Suspicious processes
2
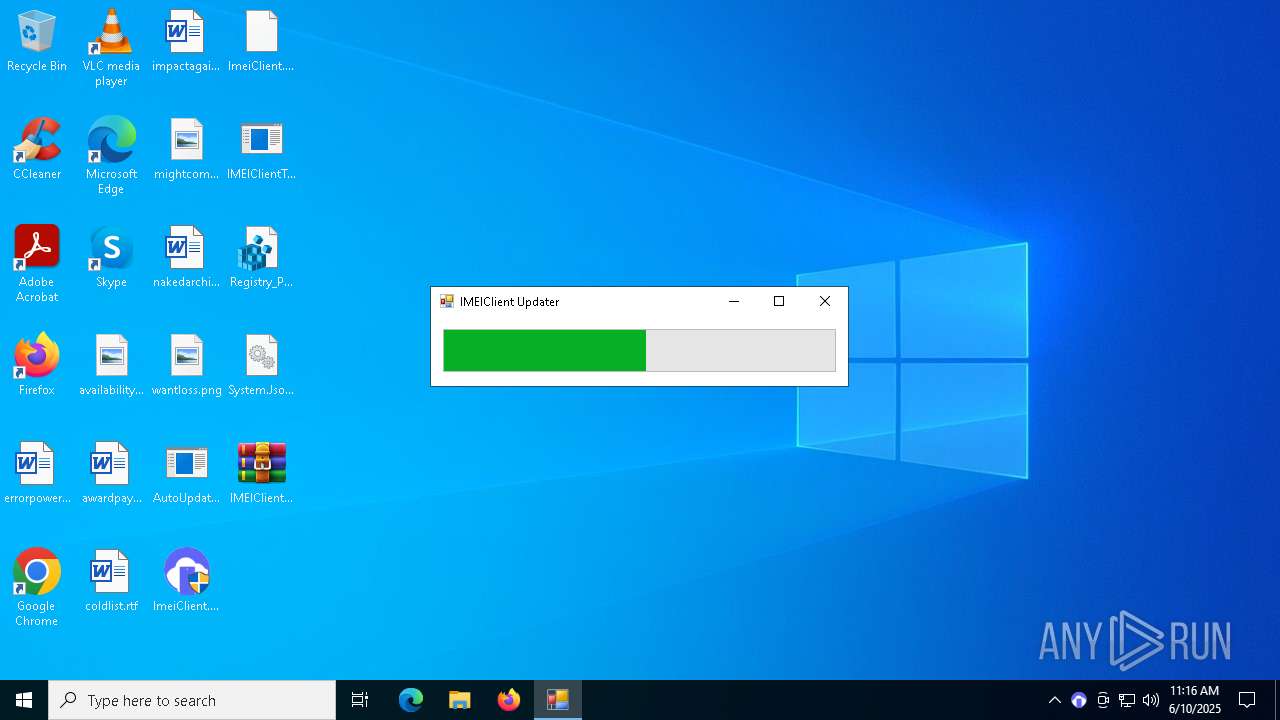
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\Desktop\IMEIClientTray.exe" IMEICLIENT_GSPN | C:\Users\admin\Desktop\IMEIClientTray.exe | ImeiClient.exe | ||||||||||||
User: admin Company: SAMSUNG SDS GUMI Integrity Level: HIGH Description: IMEIClientTray Exit code: 4294967295 Version: 1.0.1.0 Modules
| |||||||||||||||
| 672 | "AutoUpdate.exe" IMEICLIENT_GSPN | C:\Users\admin\Desktop\AutoUpdate.exe | ImeiClient.exe | ||||||||||||
User: admin Company: SAMSUNG SDS GUMI Integrity Level: HIGH Description: AutoUpdate Exit code: 0 Version: 1.0.1.0 Modules
| |||||||||||||||
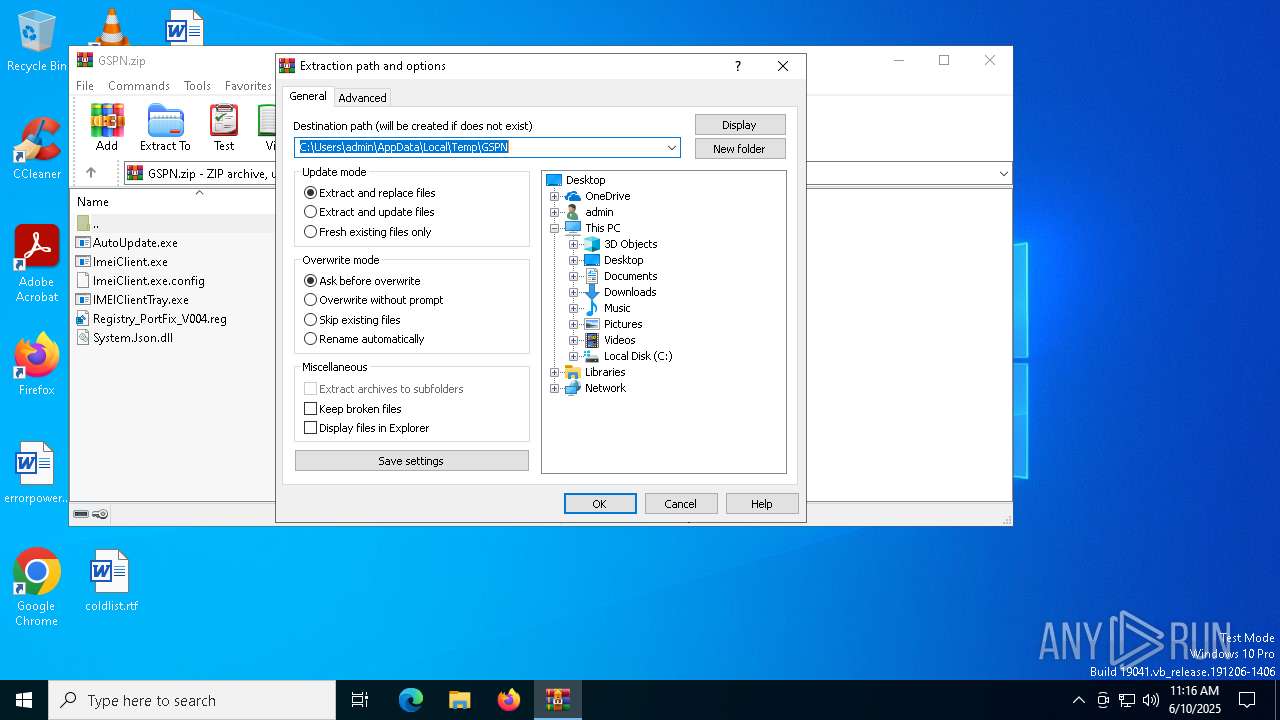
| 1348 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\GSPN.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2040 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
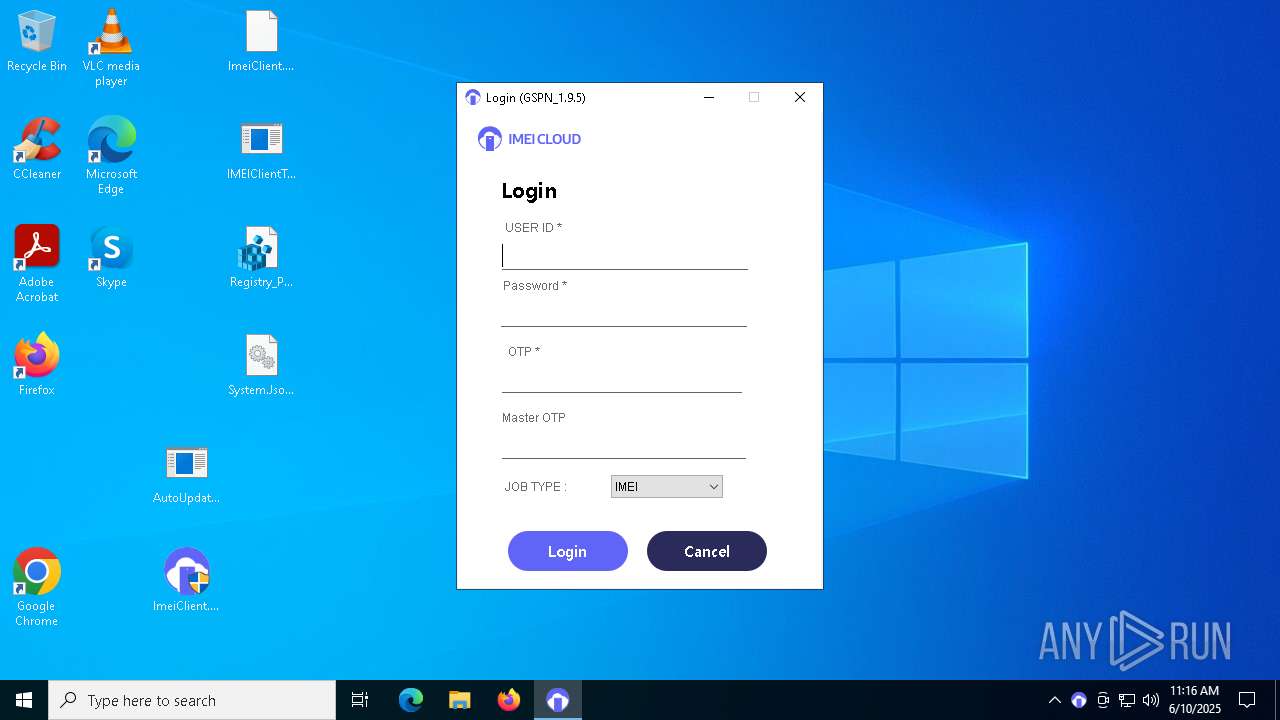
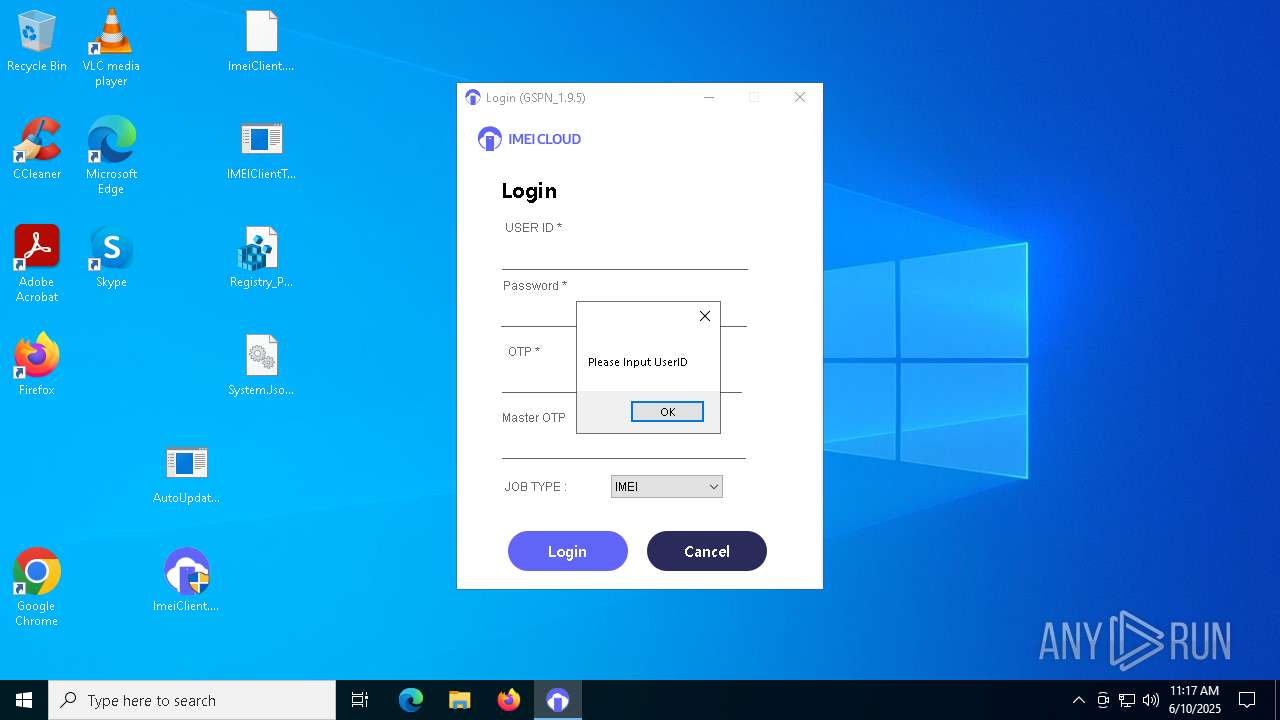
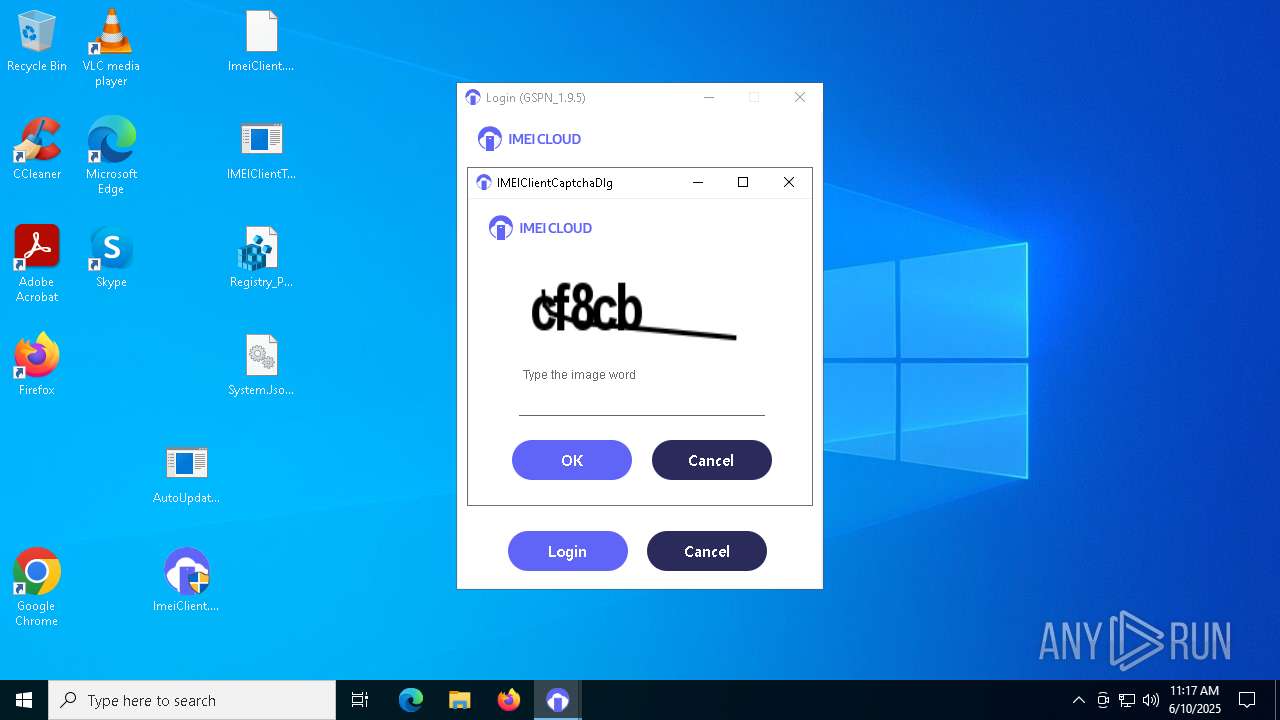
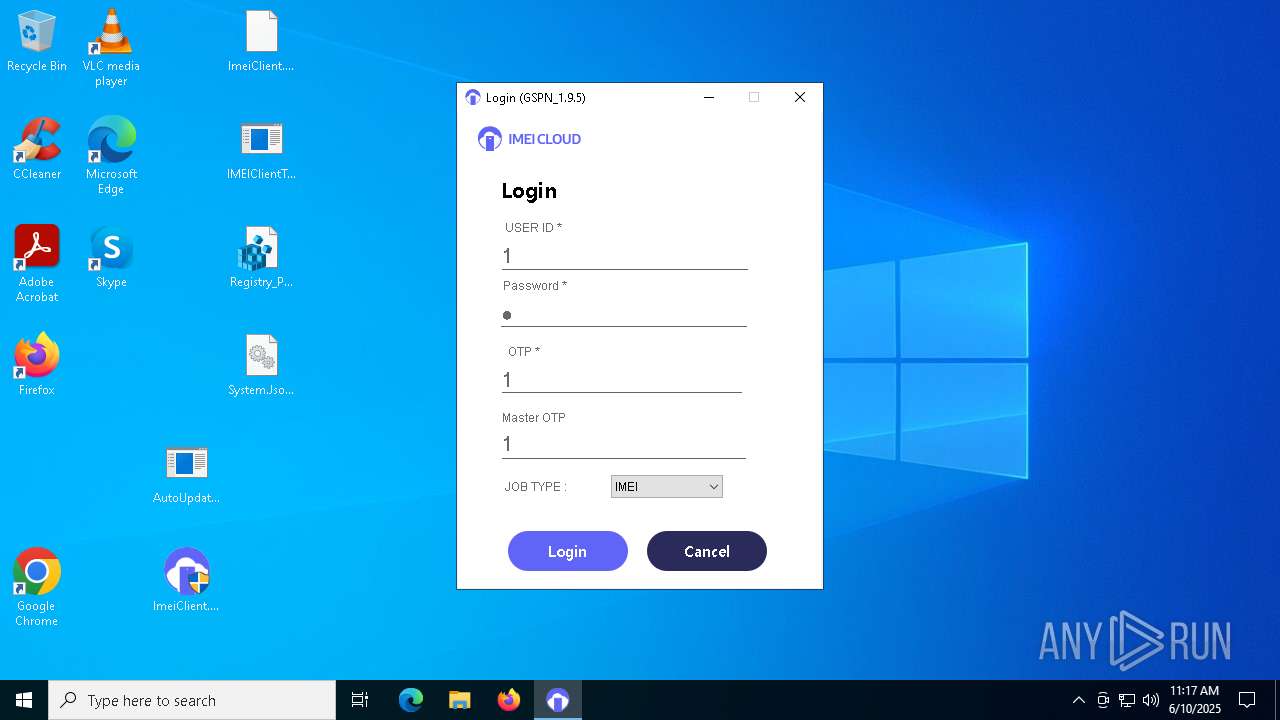
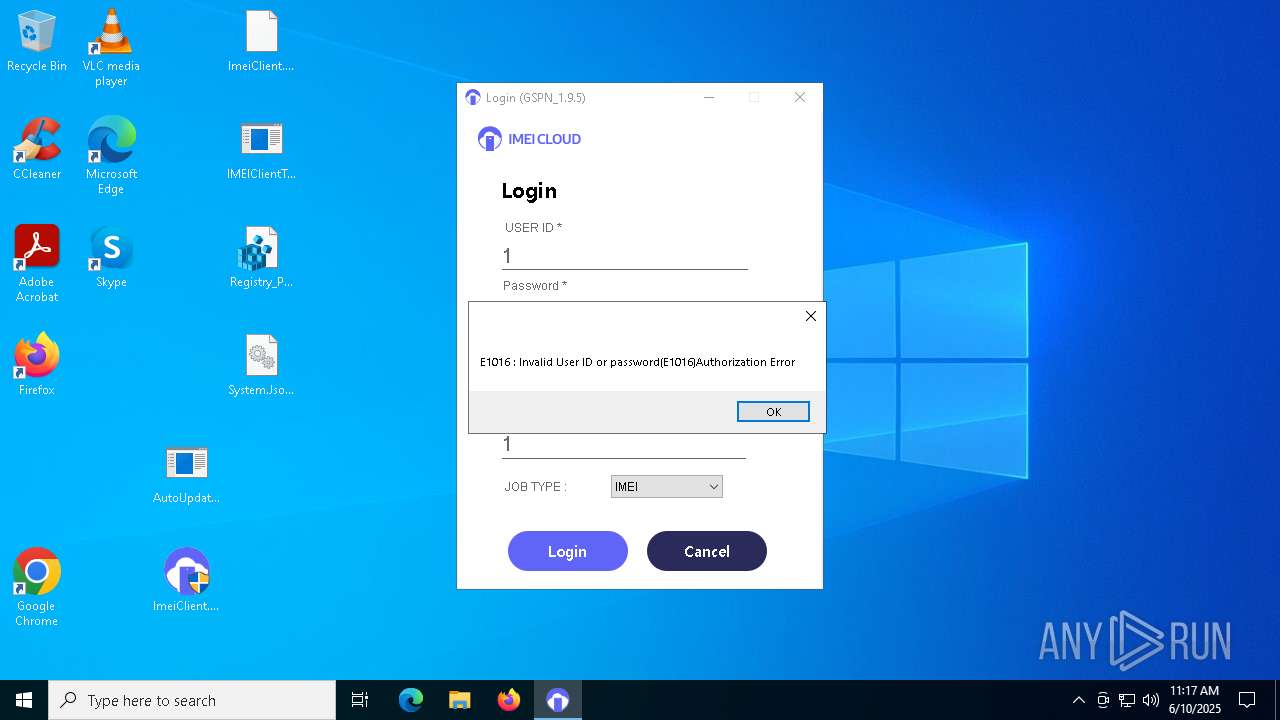
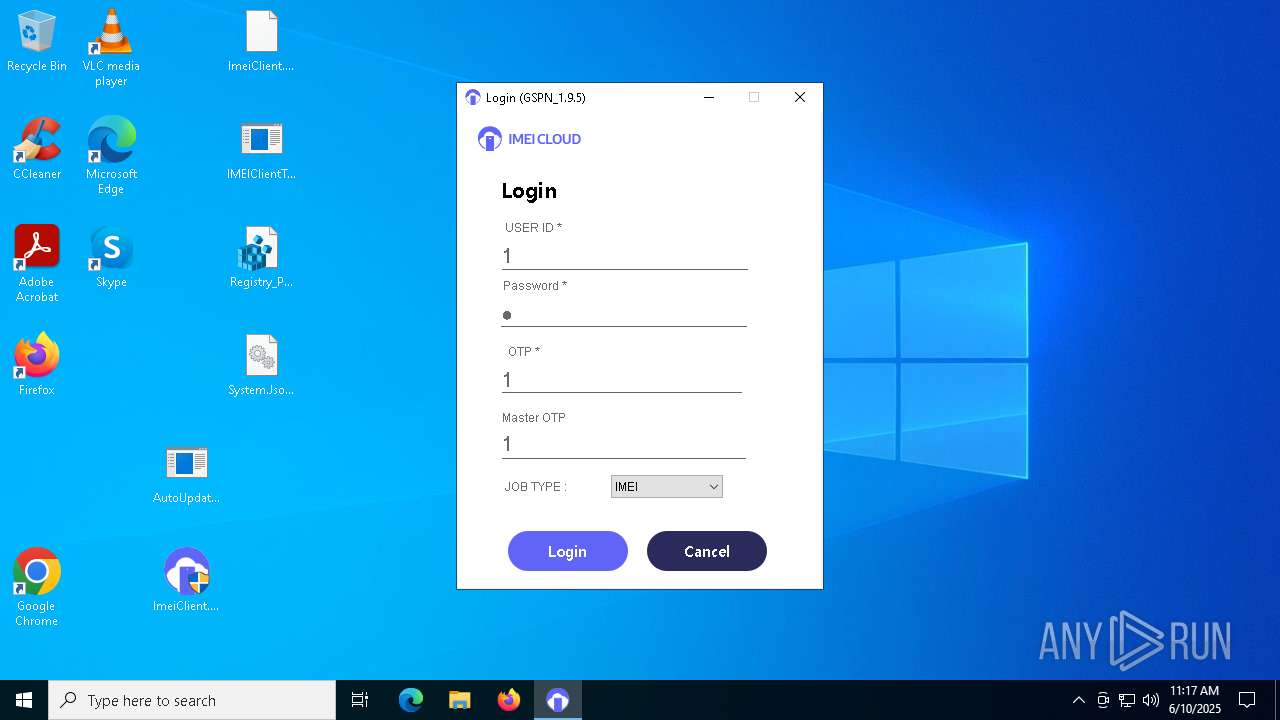
| 2908 | "C:\Users\admin\Desktop\ImeiClient.exe" | C:\Users\admin\Desktop\ImeiClient.exe | AutoUpdate.exe | ||||||||||||
User: admin Company: SAMSUNG Integrity Level: HIGH Description: ImeiClient_IMEICLIENT_GSPN Version: 1.9.5.0 Modules
| |||||||||||||||
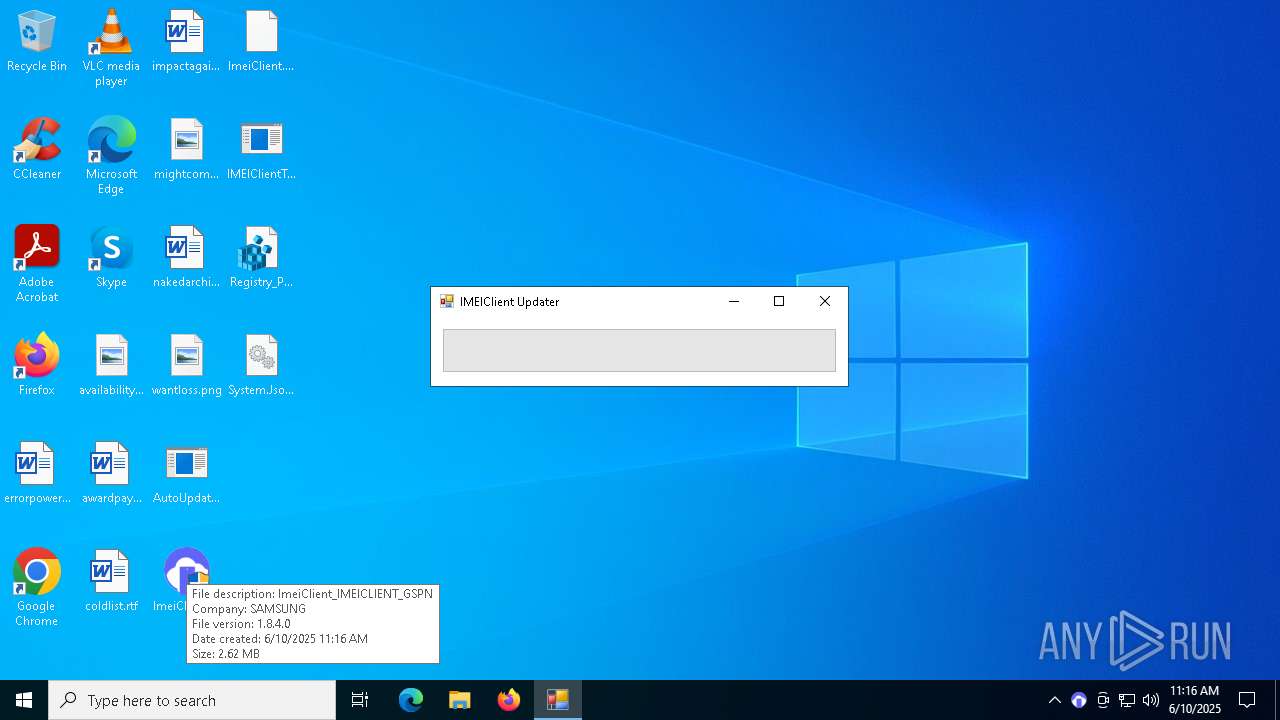
| 3872 | "C:\Users\admin\Desktop\ImeiClient.exe" | C:\Users\admin\Desktop\ImeiClient.exe | — | explorer.exe | |||||||||||
User: admin Company: SAMSUNG Integrity Level: MEDIUM Description: ImeiClient_IMEICLIENT_GSPN Exit code: 3221226540 Version: 1.8.4.0 Modules
| |||||||||||||||
| 6820 | "C:\Users\admin\Desktop\ImeiClient.exe" | C:\Users\admin\Desktop\ImeiClient.exe | explorer.exe | ||||||||||||
User: admin Company: SAMSUNG Integrity Level: HIGH Description: ImeiClient_IMEICLIENT_GSPN Exit code: 0 Version: 1.8.4.0 Modules
| |||||||||||||||
| 7348 | "C:\Users\admin\Desktop\IMEIClientTray.exe" IMEICLIENT_GSPN | C:\Users\admin\Desktop\IMEIClientTray.exe | ImeiClient.exe | ||||||||||||
User: admin Company: SAMSUNG SDS GUMI Integrity Level: HIGH Description: IMEIClientTray Version: 1.0.1.0 Modules
| |||||||||||||||
| 7376 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8052 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 302
Read events
21 238
Write events
51
Delete events
13
Modification events
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GSPN.zip | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (1348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
12
Suspicious files
1
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 672 | AutoUpdate.exe | C:\Users\admin\Desktop\availabilityincrease.jpg.old | image | |
MD5:B30DDAFE5B4B3979B03739C823DE8917 | SHA256:79C146C0252AE40466B4CD085D2C6259B2BA618C4C66358CA4092AB69748ABF0 | |||
| 1348 | WinRAR.exe | C:\Users\admin\Desktop\ImeiClient.exe | executable | |
MD5:236D95FE4274929A246A333405F789B9 | SHA256:10FD46C5447FFE5E1979CF2452E4F141FA8F01F351B3485E2E1CD1F9DA8B4FAA | |||
| 1348 | WinRAR.exe | C:\Users\admin\Desktop\AutoUpdate.exe | executable | |
MD5:C2BFC73AD4D0702BE1DEEFC295E6A989 | SHA256:041D2B62450C3DE3BC5BAA42DCF80A814AF23A457A6181C781851CFC70527737 | |||
| 672 | AutoUpdate.exe | C:\Users\admin\Desktop\errorpowered.rtf.old | text | |
MD5:F6941DDF388CF1121954BF8E73FB6156 | SHA256:1316B86BD172777CE437B55926B7C74913020326E141214BE5F9B523B2D8C29A | |||
| 672 | AutoUpdate.exe | C:\Users\admin\Desktop\awardpayment.rtf.old | text | |
MD5:85C820A0AA3BC70195142FEE6EB91219 | SHA256:B99D3F0B33BCBB4A1743726D19FF180D8910DE565431331E847A4F07125910D1 | |||
| 672 | AutoUpdate.exe | C:\Users\admin\Desktop\coldlist.rtf.old | text | |
MD5:A562D1A9725F4EC7F7FDE9620604EA78 | SHA256:05EA2EB6F54EA153AC1CC9010C42558C3D93EB247E56F7BDCB20A5FC1E59D770 | |||
| 672 | AutoUpdate.exe | C:\Users\admin\Desktop\desktop.ini.old | text | |
MD5:9E36CC3537EE9EE1E3B10FA4E761045B | SHA256:4B9D687AC625690FD026ED4B236DAD1CAC90EF69E7AD256CC42766A065B50026 | |||
| 672 | AutoUpdate.exe | C:\Users\admin\Desktop\mightcompleted.png.old | image | |
MD5:470066ECE1167CBE82331BB1A2BC231D | SHA256:EAA79A5AC2C4957D332DF4F2A74364492F76714ECD3A6CFE2F87B960729B71C9 | |||
| 672 | AutoUpdate.exe | C:\Users\admin\Desktop\ImeiClient.exe.old | executable | |
MD5:236D95FE4274929A246A333405F789B9 | SHA256:10FD46C5447FFE5E1979CF2452E4F141FA8F01F351B3485E2E1CD1F9DA8B4FAA | |||
| 672 | AutoUpdate.exe | C:\Users\admin\Desktop\impactagain.rtf.old | text | |
MD5:CC33455414734BE60B630560E0196D26 | SHA256:95D22F2C6944D5030823941A4D285D6576A2F1DBC4E24684C2E111CB756CB674 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7420 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7420 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5608 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6960 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7420 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
api.secmobilesvc.com |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |