| File name: | GDI.exe |
| Full analysis: | https://app.any.run/tasks/89384cab-679b-4eac-8674-da4e5ea19346 |
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2025, 04:28:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 3C9A80A3144C5500358E88E78FD667E0 |
| SHA1: | 9AC05E028807BBA01E624571BA002B61D3978E3D |
| SHA256: | FCC1224BE8BF9B9AD75F4902DA02534E6B9C8F62708E2687FDAD83AE9B431F48 |
| SSDEEP: | 384:qLWhvaERKSiRqZqO/DDMpdbdXzU1mh4ZHEYlJjllXI5u6kYcV6qUiJFnh:qKvamJwqZqOrSdbJGHPuGYcV69izh |
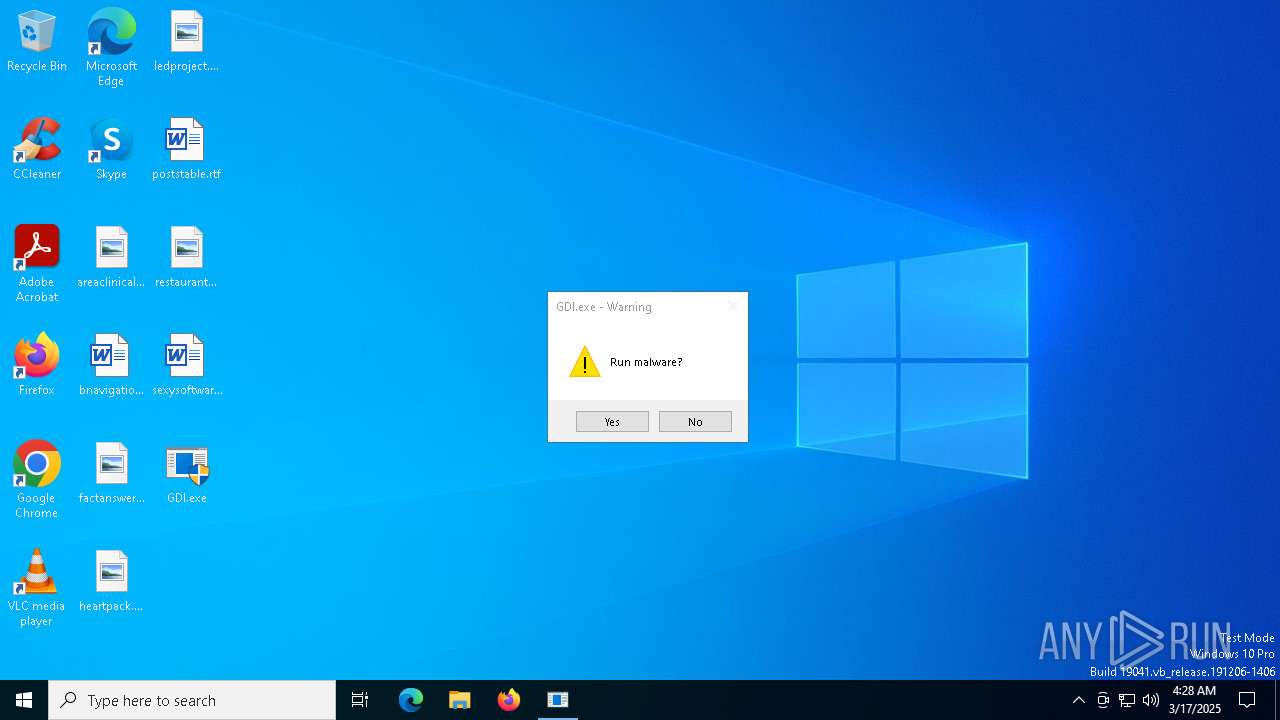
MALICIOUS
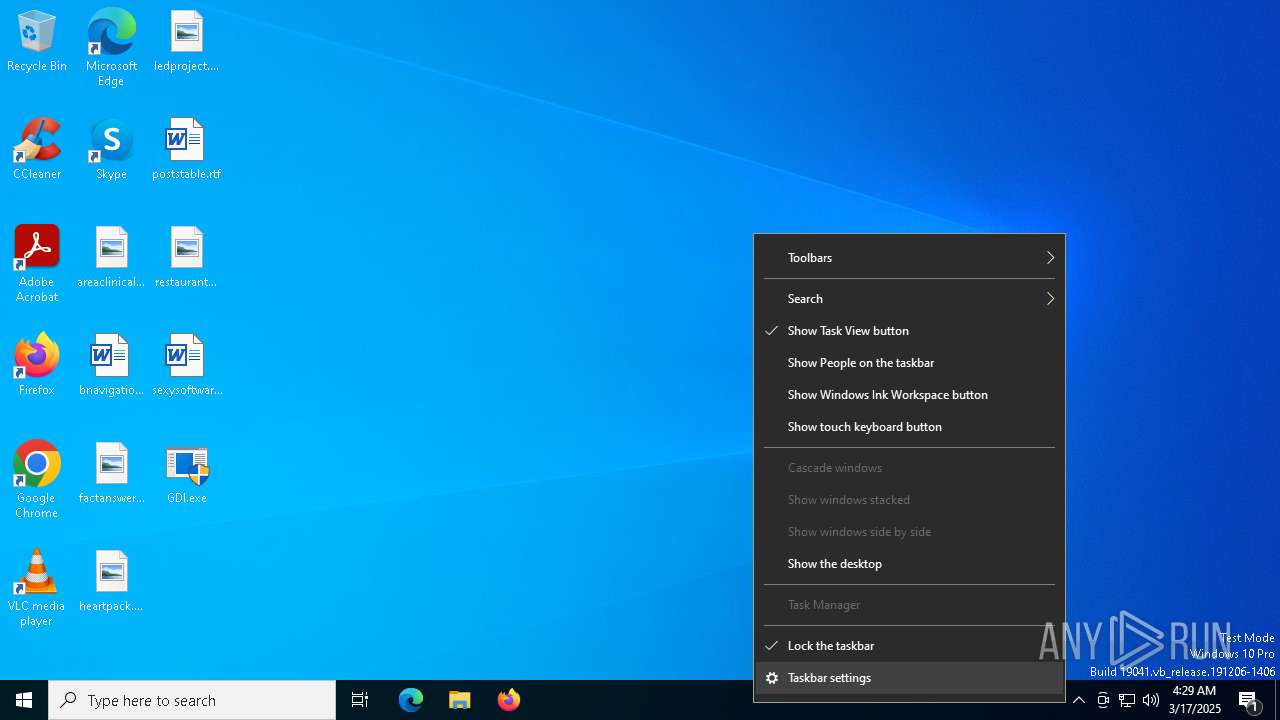
UAC/LUA settings modification
- GDI.exe (PID: 7208)
Disables task manager
- GDI.exe (PID: 7208)
SUSPICIOUS
Creates file in the systems drive root
- GDI.exe (PID: 7208)
- notepad.exe (PID: 7624)
Reads security settings of Internet Explorer
- GDI.exe (PID: 7208)
- ShellExperienceHost.exe (PID: 7616)
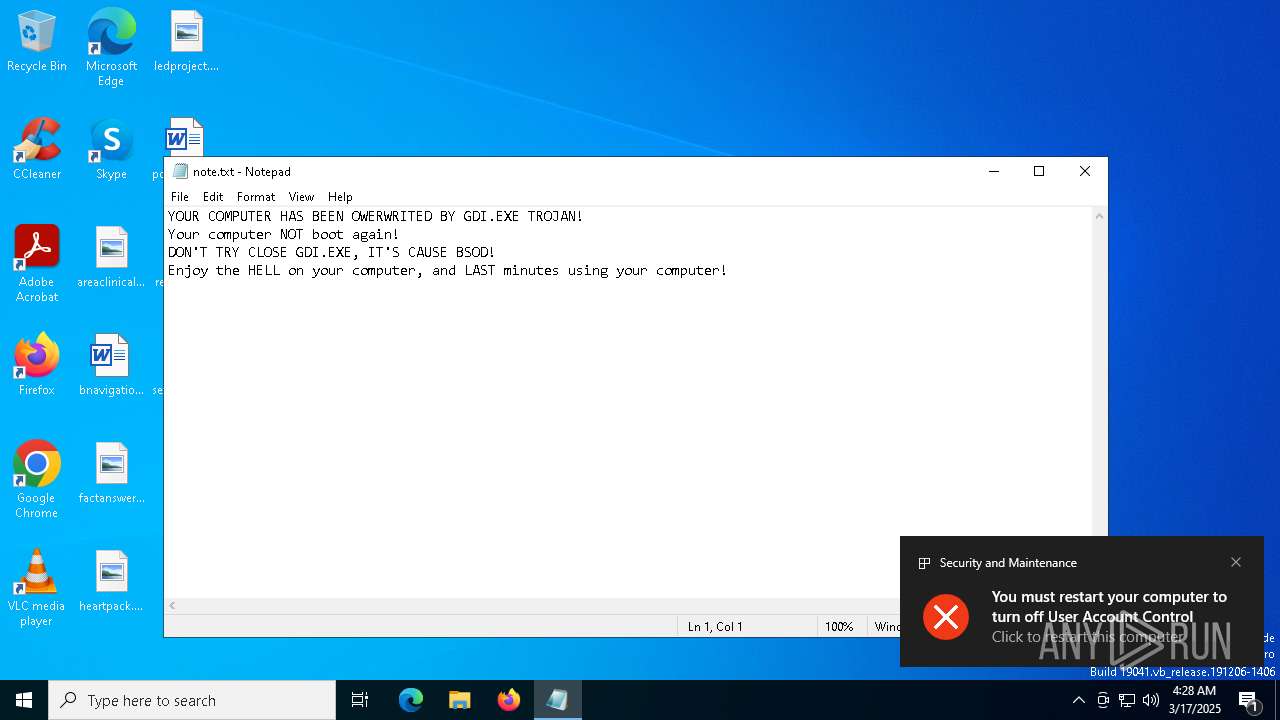
Start notepad (likely ransomware note)
- GDI.exe (PID: 7208)
There is functionality for taking screenshot (YARA)
- GDI.exe (PID: 7208)
INFO
Reads the machine GUID from the registry
- GDI.exe (PID: 7208)
Reads the computer name
- GDI.exe (PID: 7208)
- ShellExperienceHost.exe (PID: 7616)
Checks supported languages
- GDI.exe (PID: 7208)
- ShellExperienceHost.exe (PID: 7616)
Process checks whether UAC notifications are on
- GDI.exe (PID: 7208)
Process checks computer location settings
- GDI.exe (PID: 7208)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2053:12:05 01:54:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 15360 |
| InitializedDataSize: | 6144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x58ba |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | GDI |
| FileVersion: | 1.0.0.0 |
| InternalName: | GDI.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | GDI.exe |
| ProductName: | GDI |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
137
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4784 | "C:\Users\admin\Desktop\GDI.exe" | C:\Users\admin\Desktop\GDI.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GDI Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7208 | "C:\Users\admin\Desktop\GDI.exe" | C:\Users\admin\Desktop\GDI.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: GDI Version: 1.0.0.0 Modules
| |||||||||||||||
| 7252 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7284 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7616 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7624 | "C:\Windows\System32\notepad.exe" C:\note.txt | C:\Windows\SysWOW64\notepad.exe | — | GDI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 881
Read events
1 877
Write events
4
Delete events
0
Modification events
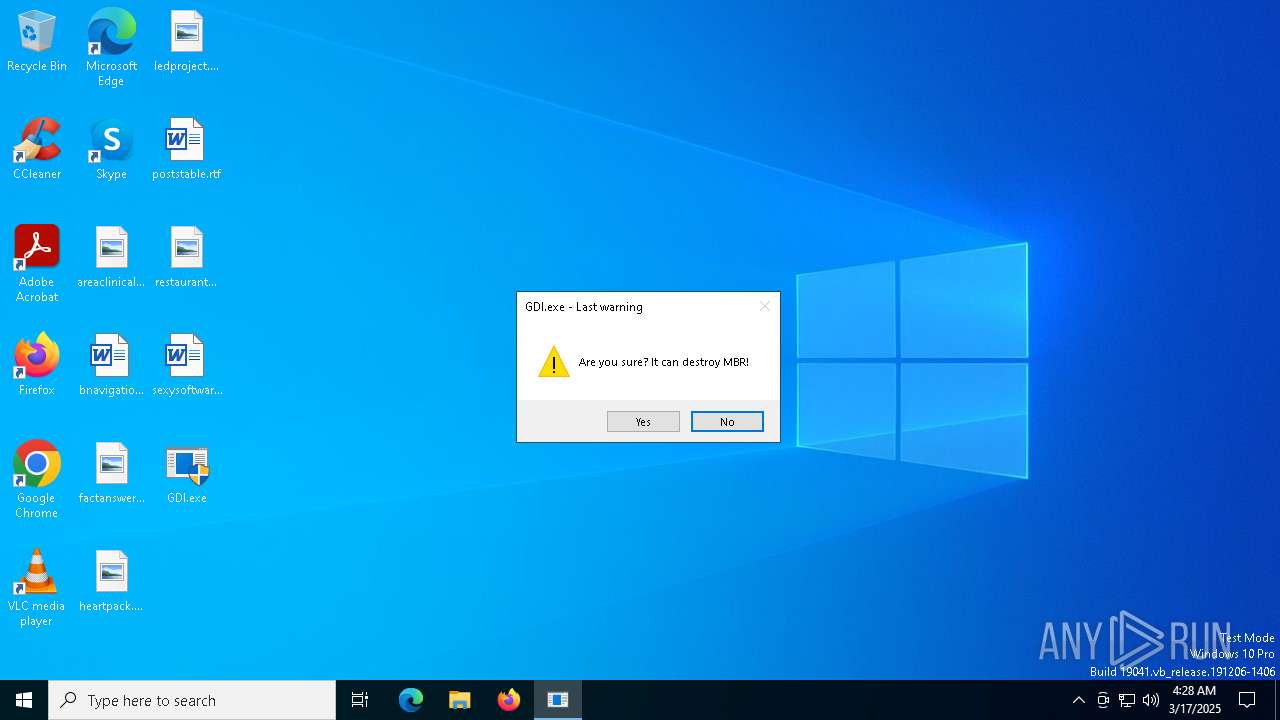
| (PID) Process: | (7208) GDI.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (7208) GDI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (7616) ShellExperienceHost.exe | Key: | \REGISTRY\A\{ee1cb6bc-54c7-79d9-9c4f-50557330e0e8}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D0000008E83B115F596DB01 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7208 | GDI.exe | C:\note.txt | text | |
MD5:E6629A967D30C2914BC3A302DCFF1C09 | SHA256:91172E4C87EFF8899DD376DD16A8651D983C36A699EA8A0F4F1151A020B65FA8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report