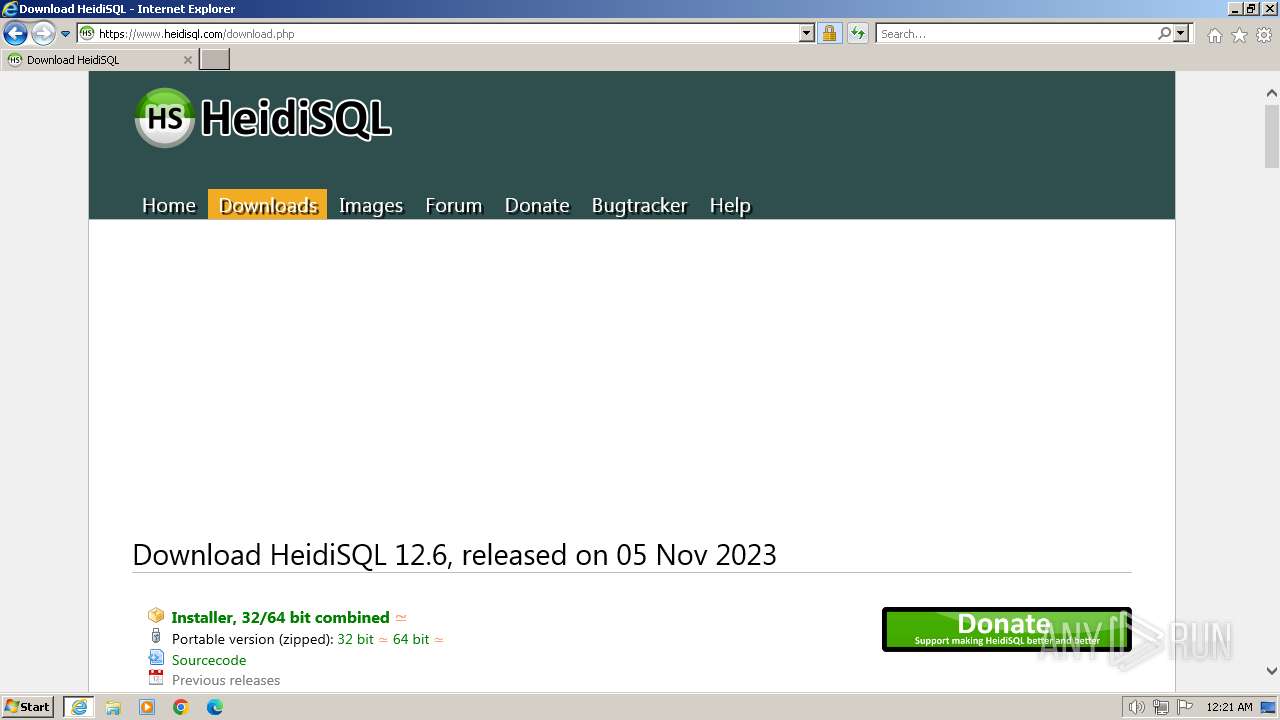
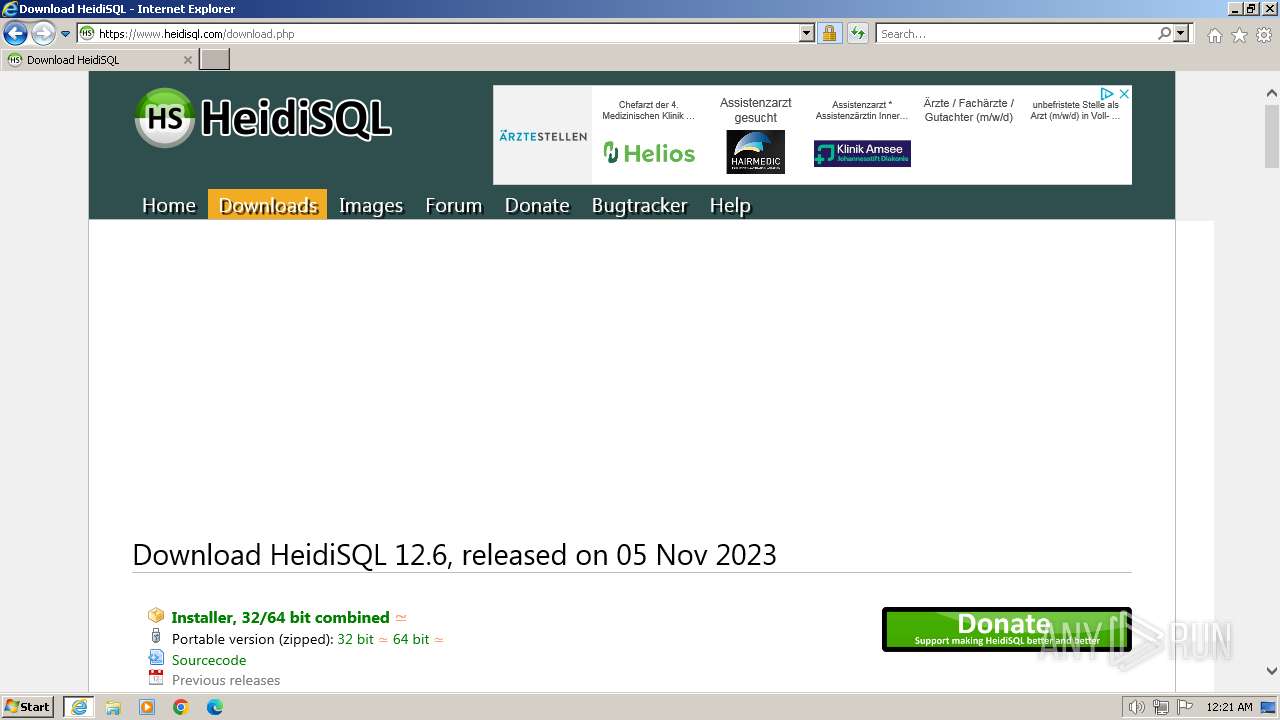
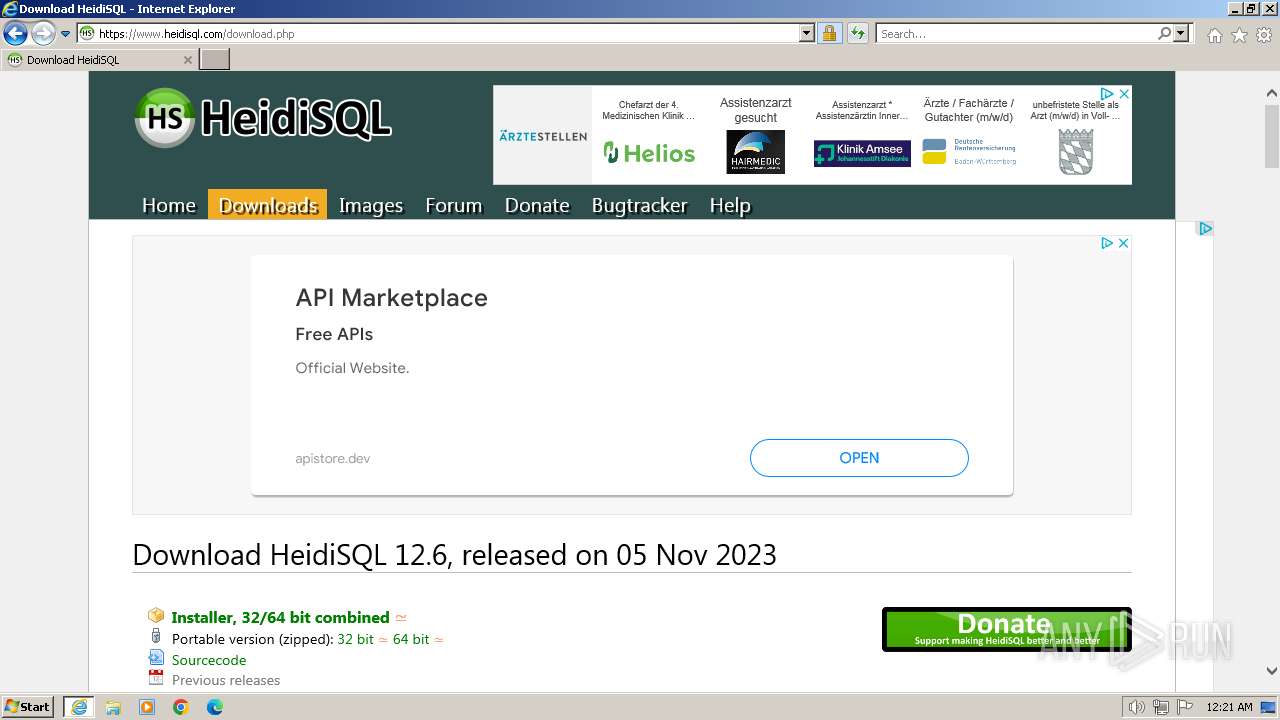
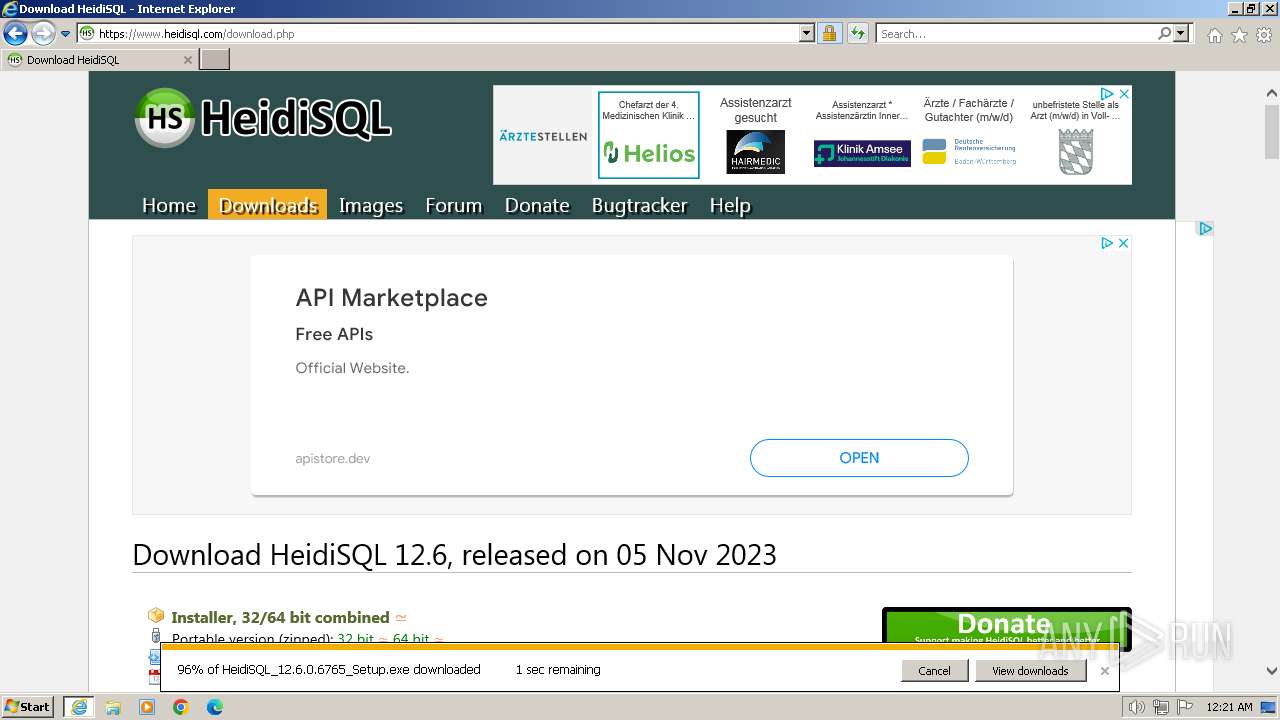
| URL: | https://www.heidisql.com |
| Full analysis: | https://app.any.run/tasks/8516cbcd-09c5-4b0a-b919-5edc3c41f97e |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2024, 00:20:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 17B713AFA71C447E44AE4463F98AE20F |
| SHA1: | 0CEABDE7F2F1CD7B5091CBFB6E52294C7676D218 |
| SHA256: | FCAAF8816095D0A5B49E5577CCF28A4665DE73A93D43406804AD94140DA18D2C |
| SSDEEP: | 3:N8DSLCWZT:2OLVZT |
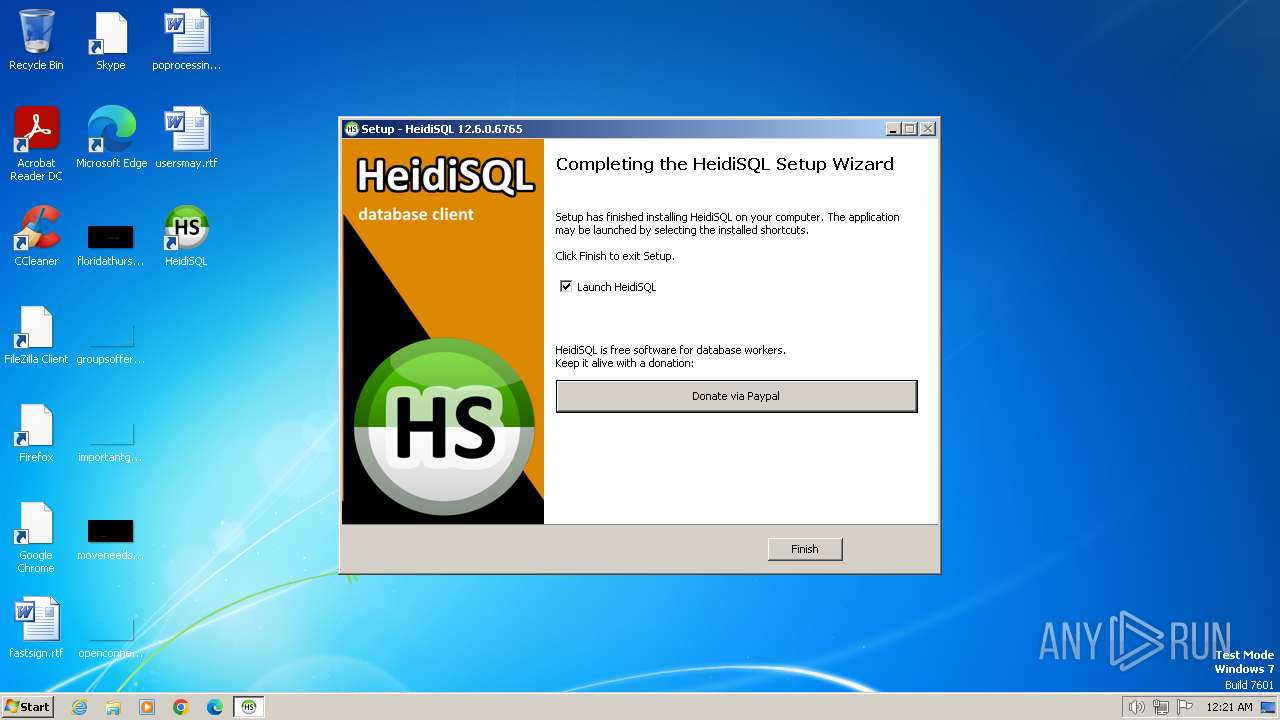
MALICIOUS
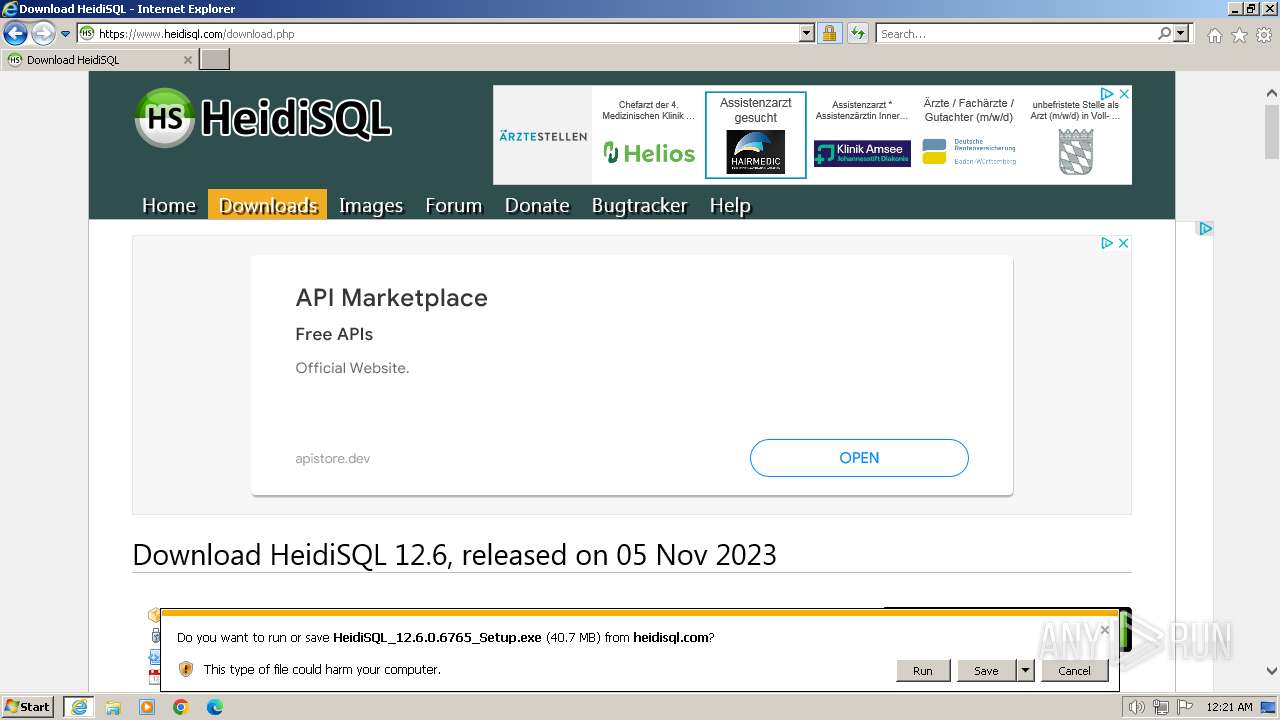
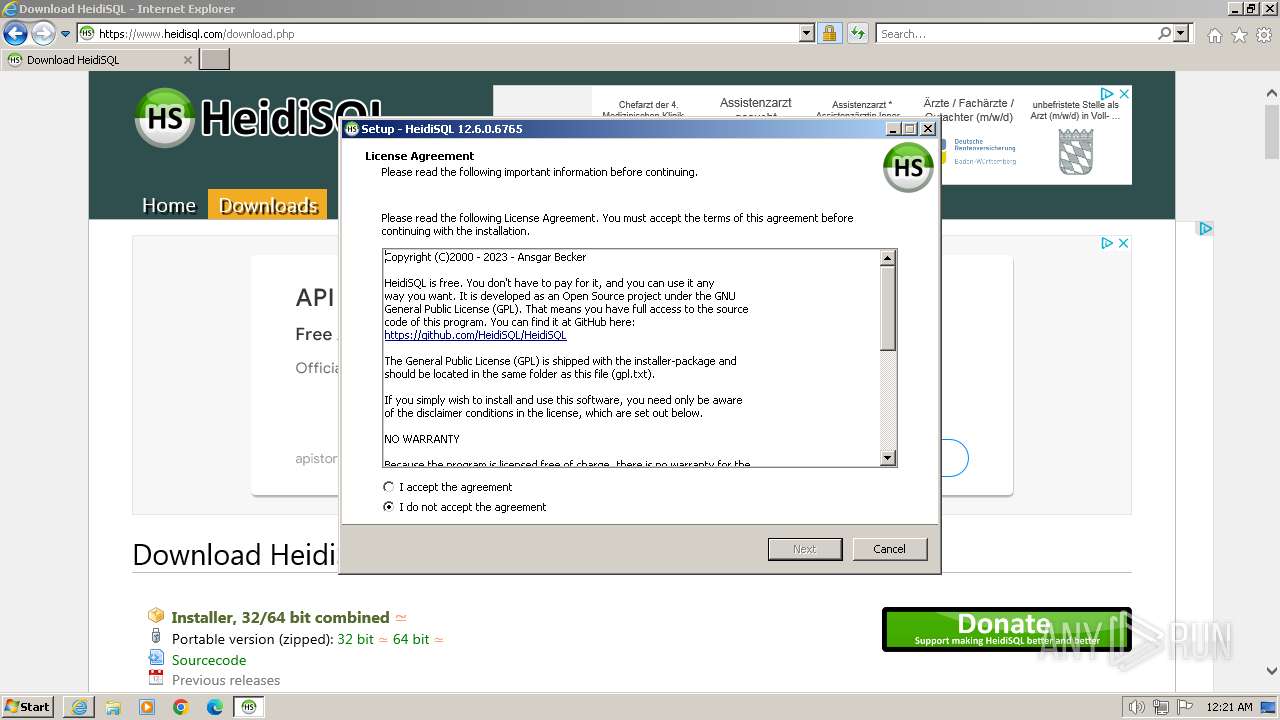
Drops the executable file immediately after the start
- HeidiSQL_12.6.0.6765_Setup.exe (PID: 240)
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
- VC_redist.x86.exe (PID: 2060)
- VC_redist.x86.exe (PID: 2100)
SUSPICIOUS
Executable content was dropped or overwritten
- HeidiSQL_12.6.0.6765_Setup.exe (PID: 240)
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
- VC_redist.x86.exe (PID: 2060)
- VC_redist.x86.exe (PID: 2100)
Reads the Windows owner or organization settings
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
Process drops SQLite DLL files
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
Process drops legitimate windows executable
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
- VC_redist.x86.exe (PID: 2060)
Reads settings of System Certificates
- heidisql.exe (PID: 2968)
Starts a Microsoft application from unusual location
- VC_redist.x86.exe (PID: 2100)
Reads the Internet Settings
- heidisql.exe (PID: 2968)
Reads security settings of Internet Explorer
- heidisql.exe (PID: 2968)
Checks Windows Trust Settings
- heidisql.exe (PID: 2968)
Searches for installed software
- VC_redist.x86.exe (PID: 2100)
Non-standard symbols in registry
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
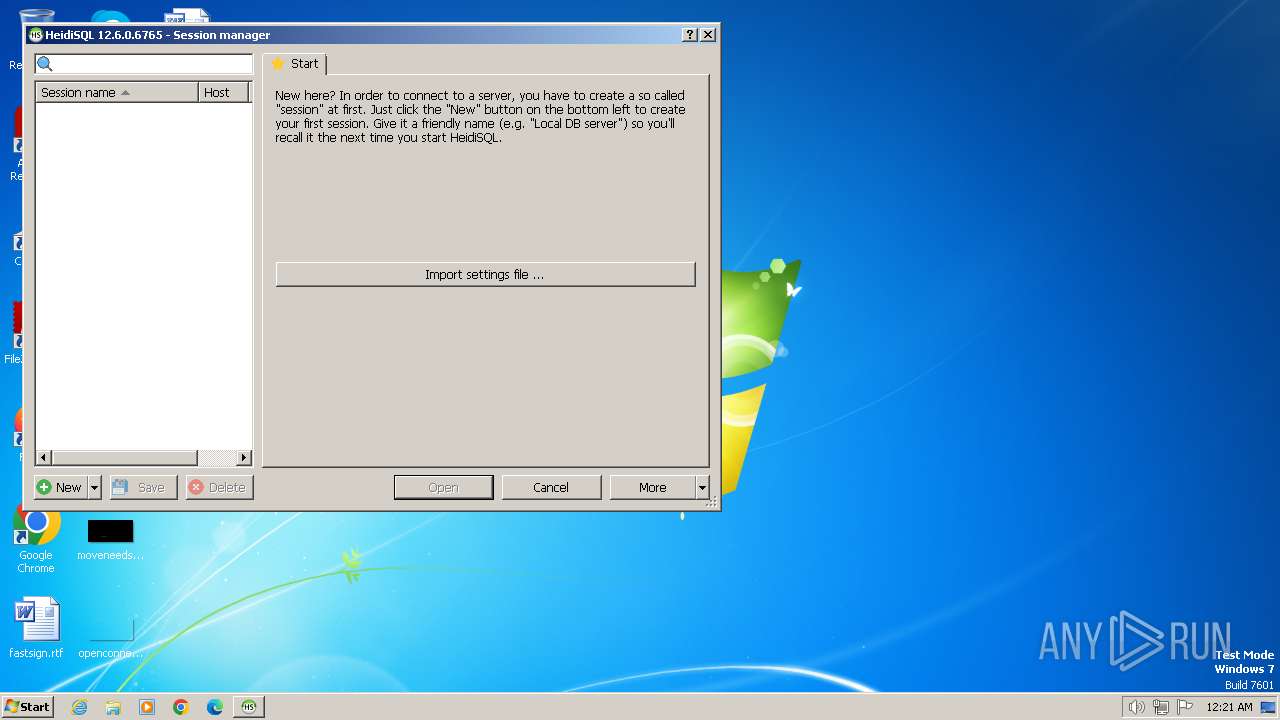
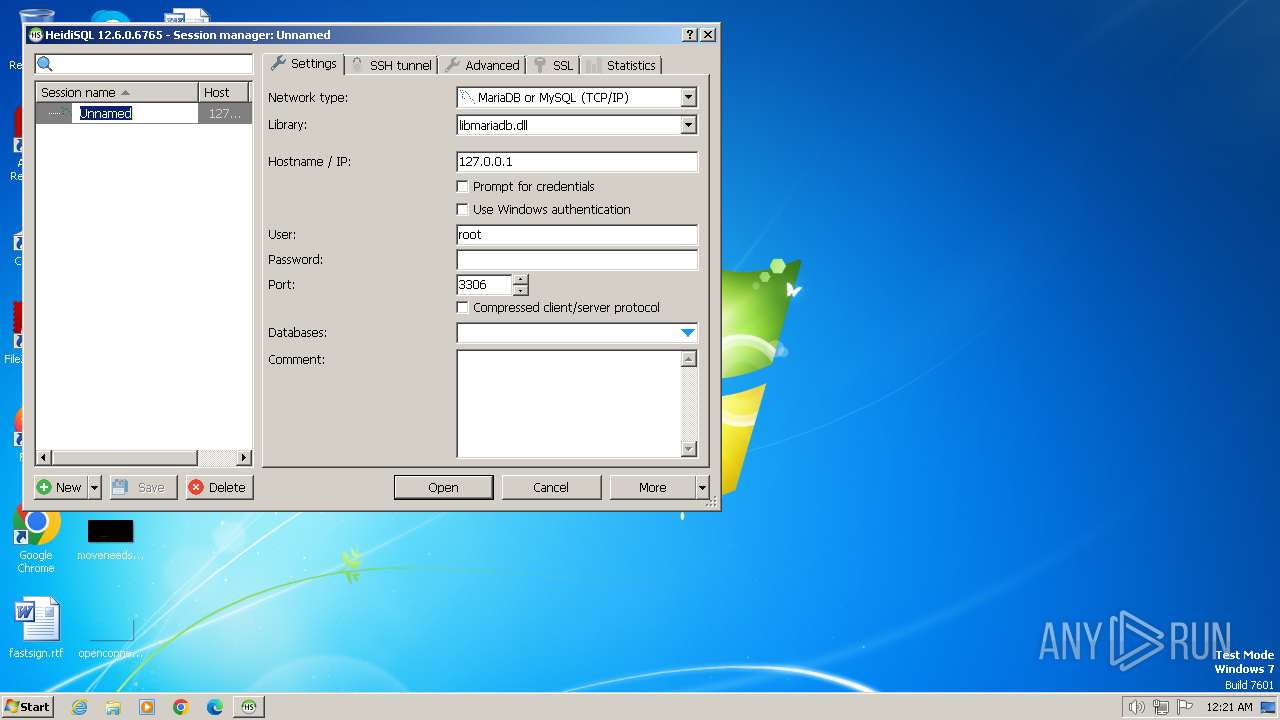
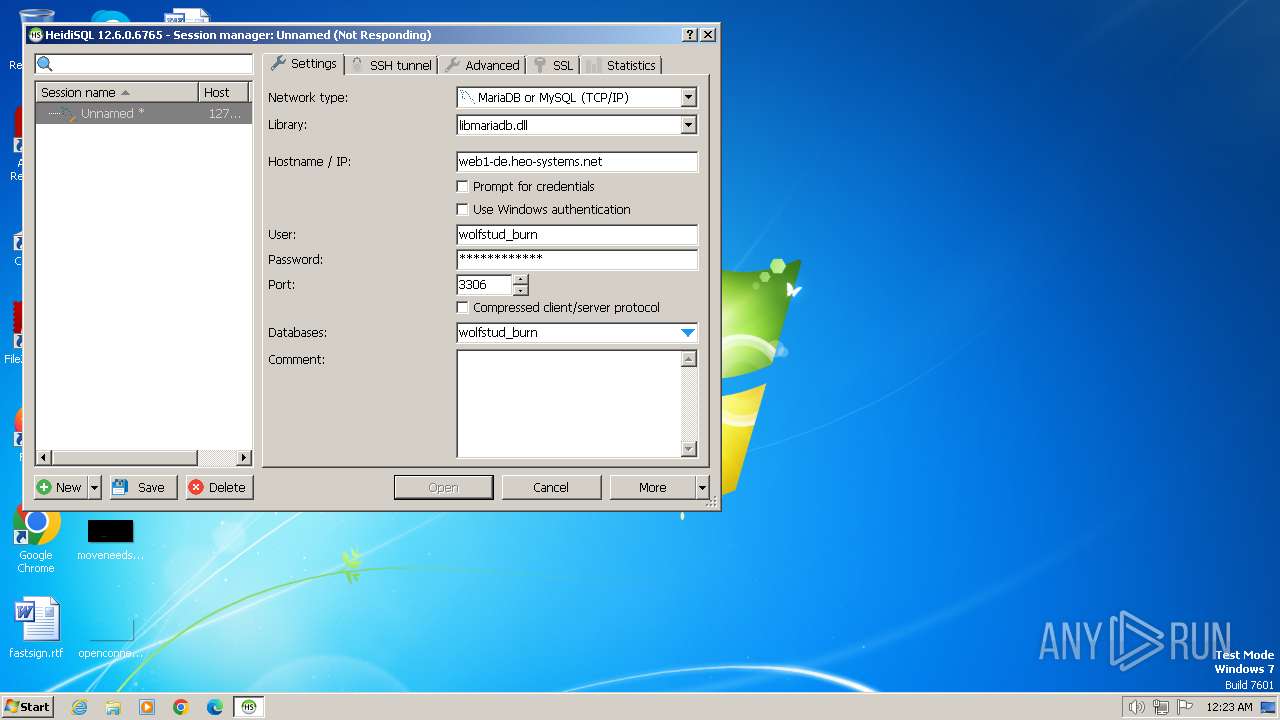
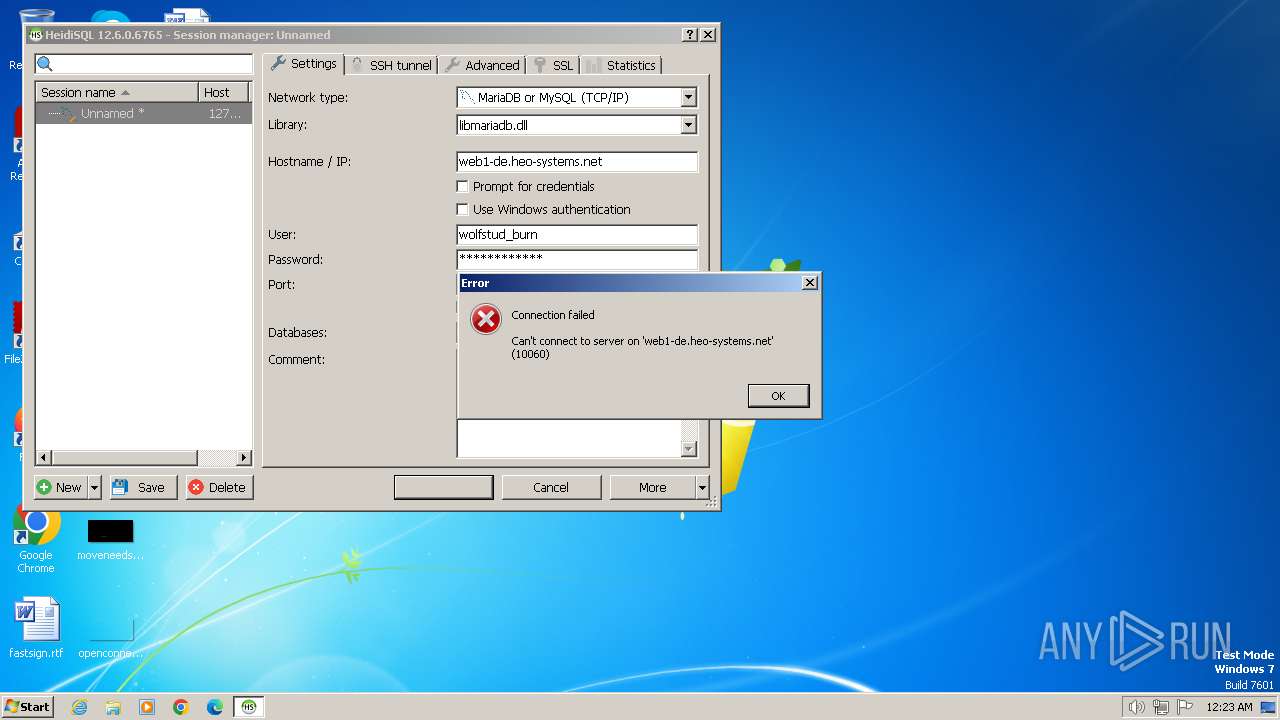
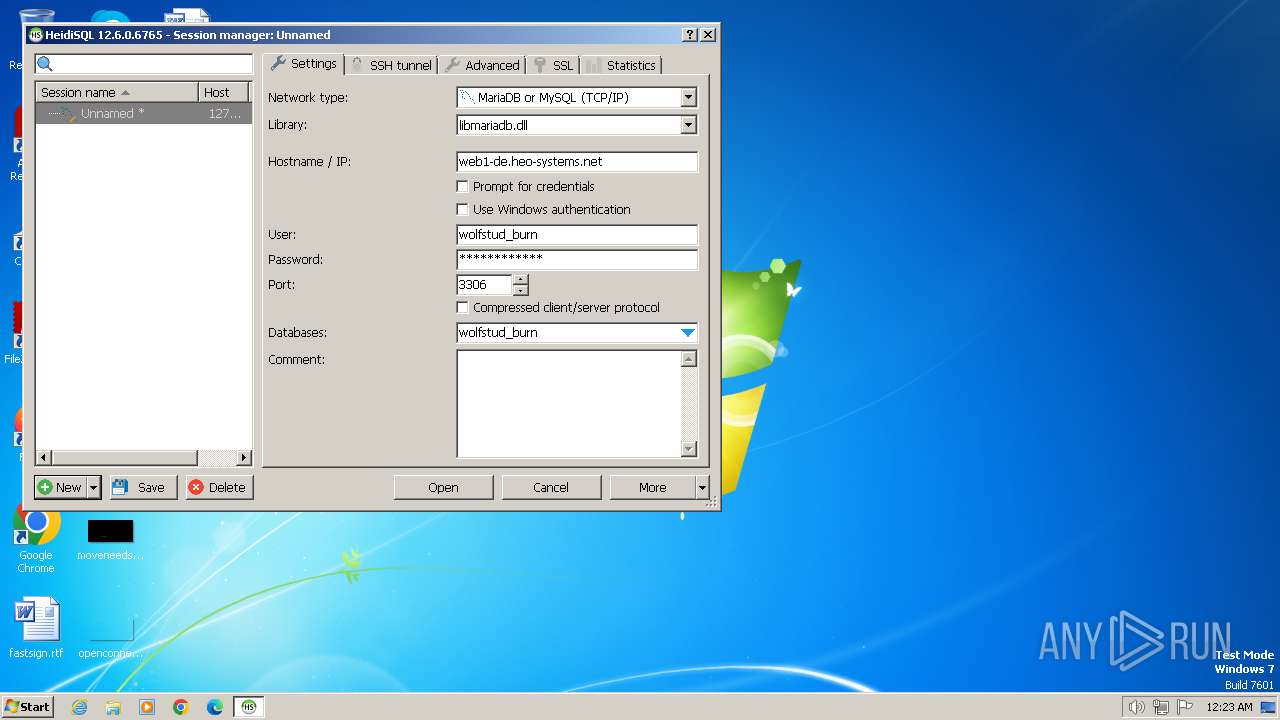
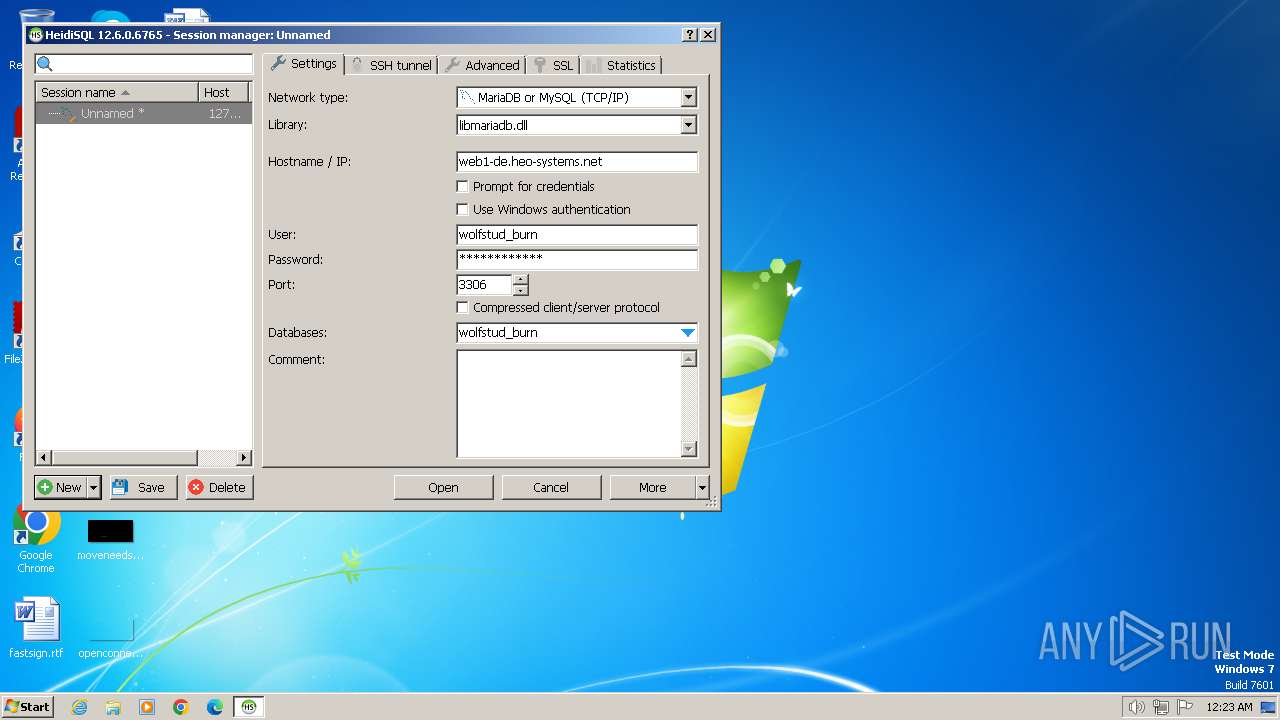
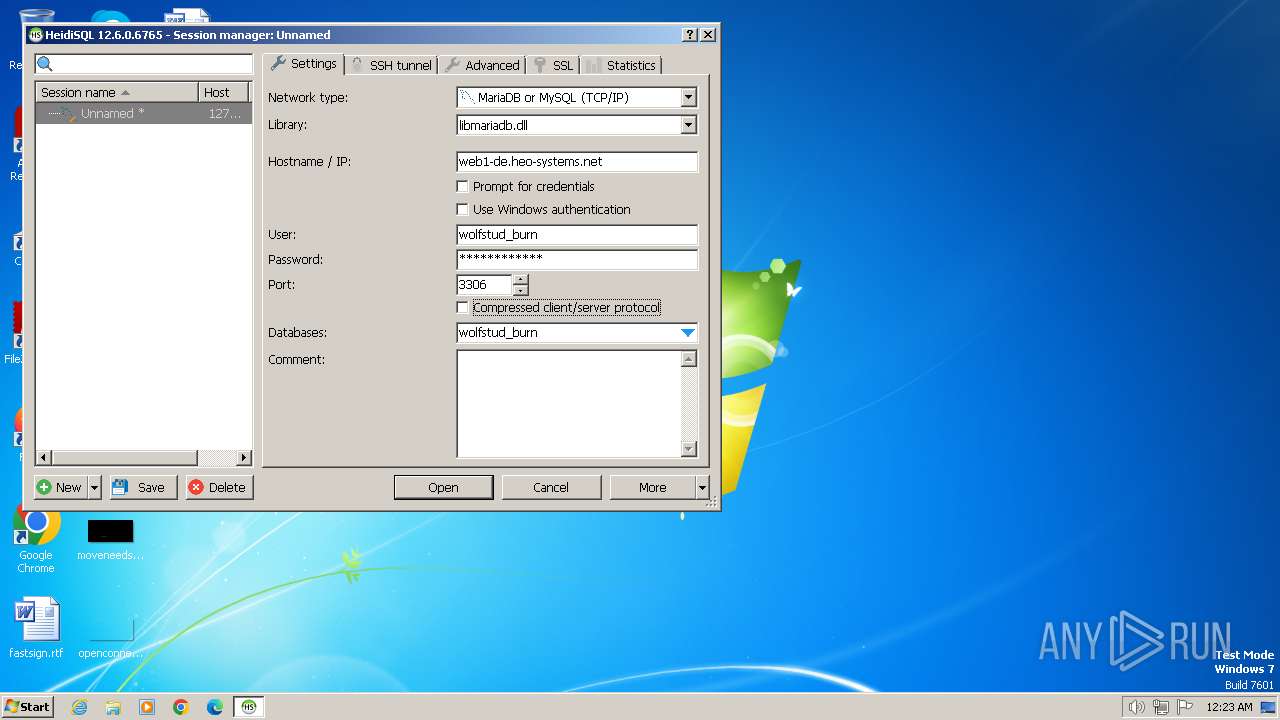
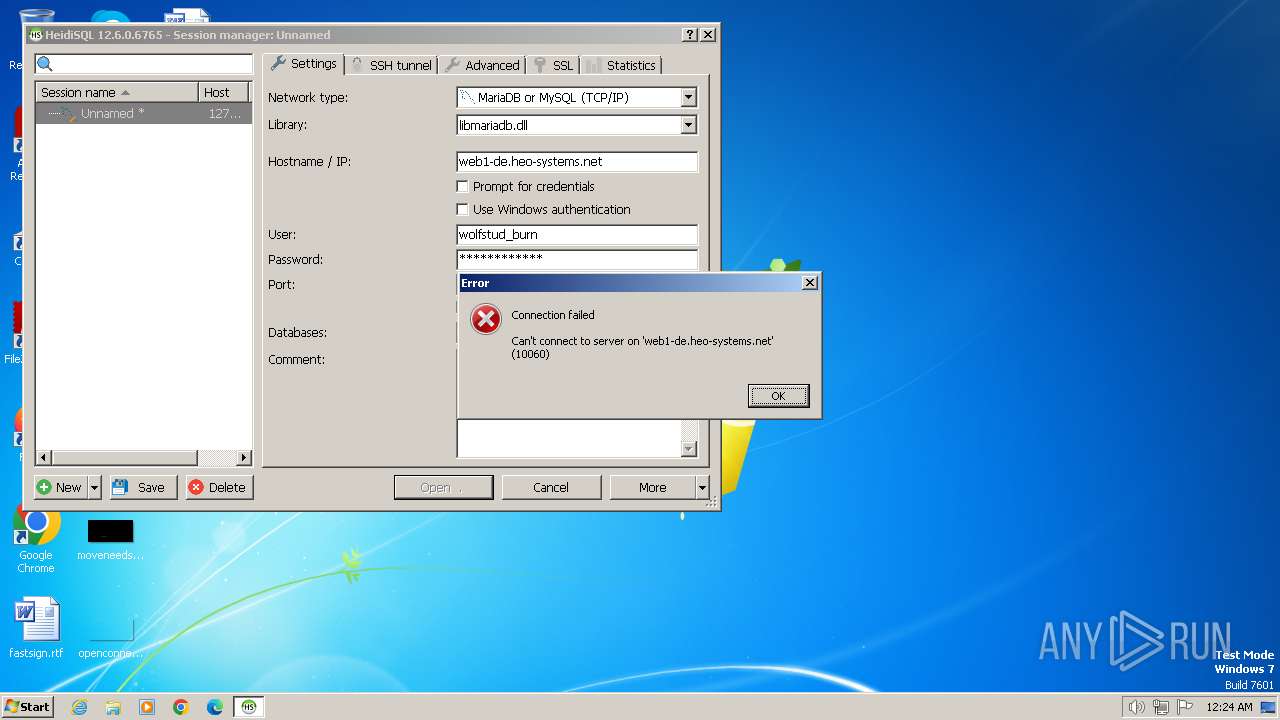
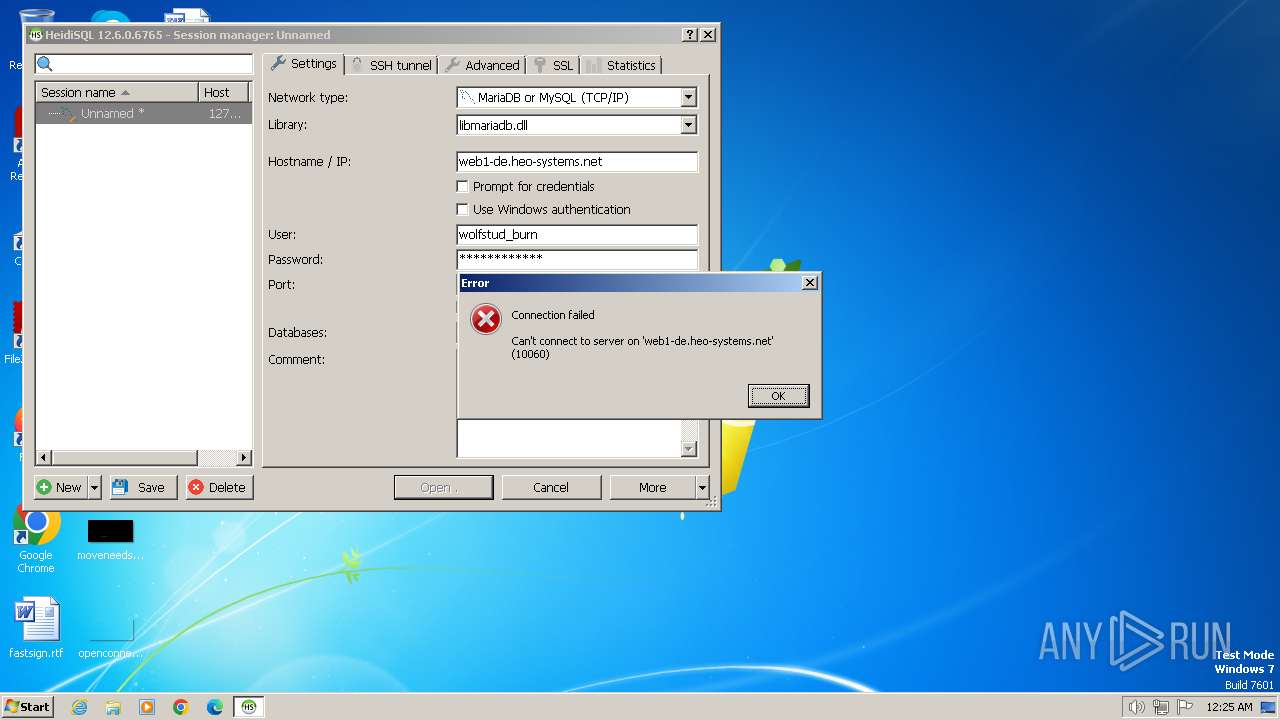
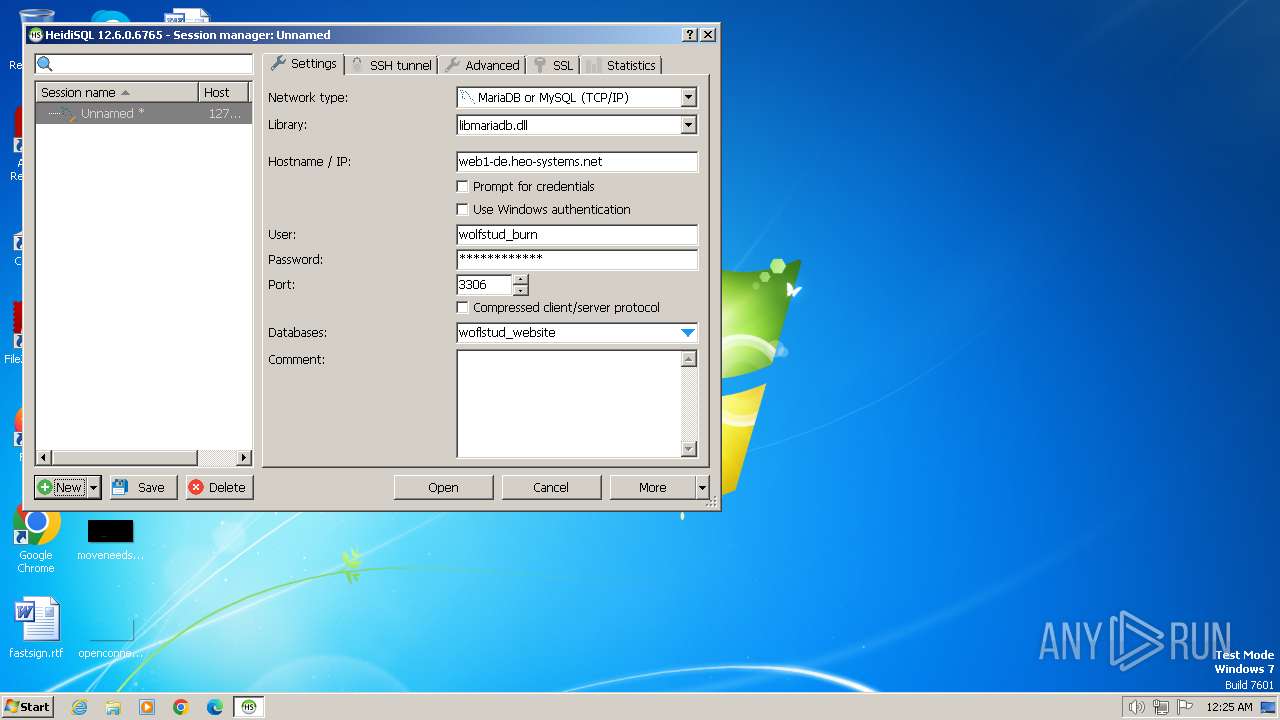
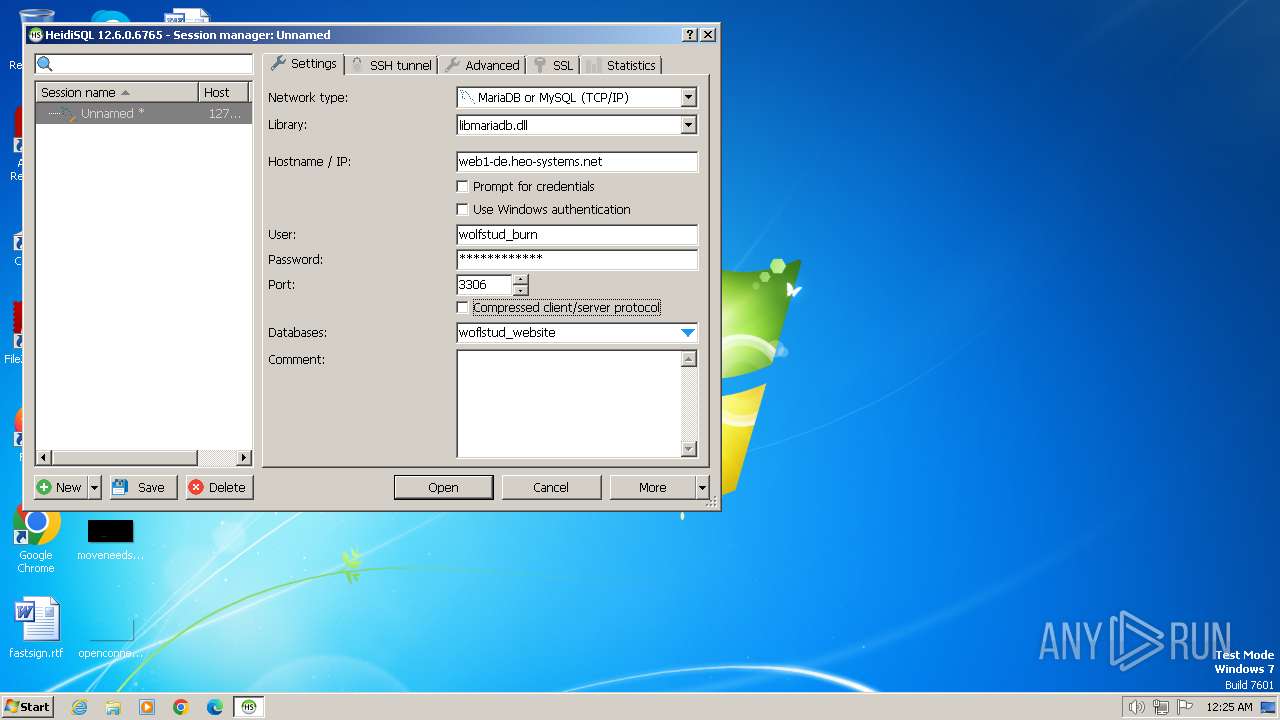
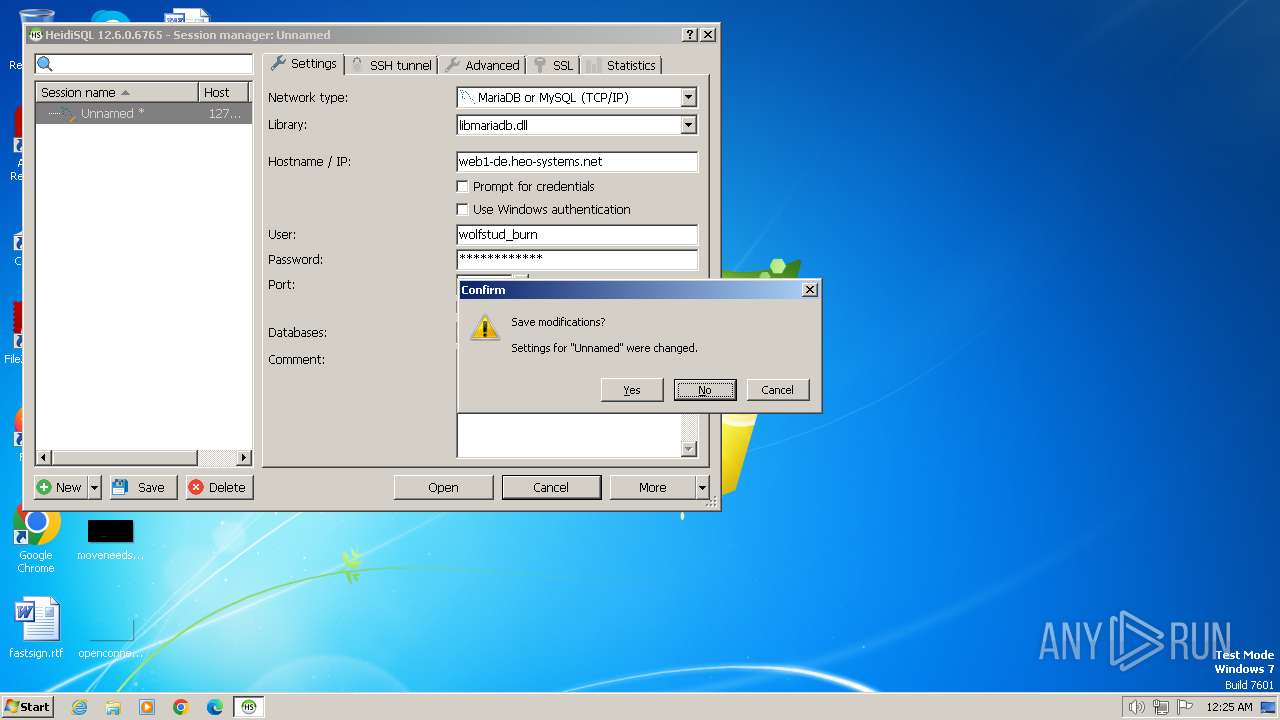
Connects to unusual port
- heidisql.exe (PID: 2968)
INFO
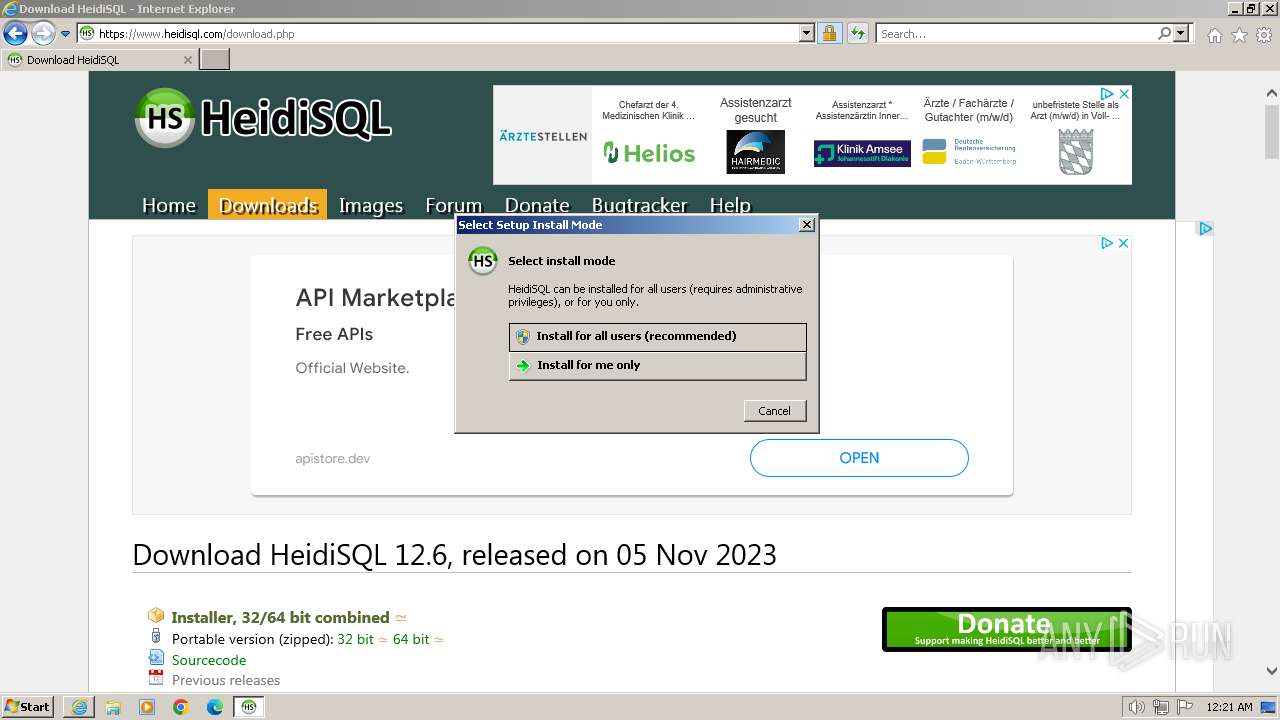
Application launched itself
- iexplore.exe (PID: 3700)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2920)
Checks supported languages
- HeidiSQL_12.6.0.6765_Setup.exe (PID: 240)
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
- VC_redist.x86.exe (PID: 2060)
- heidisql.exe (PID: 2968)
- VC_redist.x86.exe (PID: 2100)
Create files in a temporary directory
- HeidiSQL_12.6.0.6765_Setup.exe (PID: 240)
- VC_redist.x86.exe (PID: 2060)
- VC_redist.x86.exe (PID: 2100)
- heidisql.exe (PID: 2968)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3700)
Reads the computer name
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
- heidisql.exe (PID: 2968)
- VC_redist.x86.exe (PID: 2100)
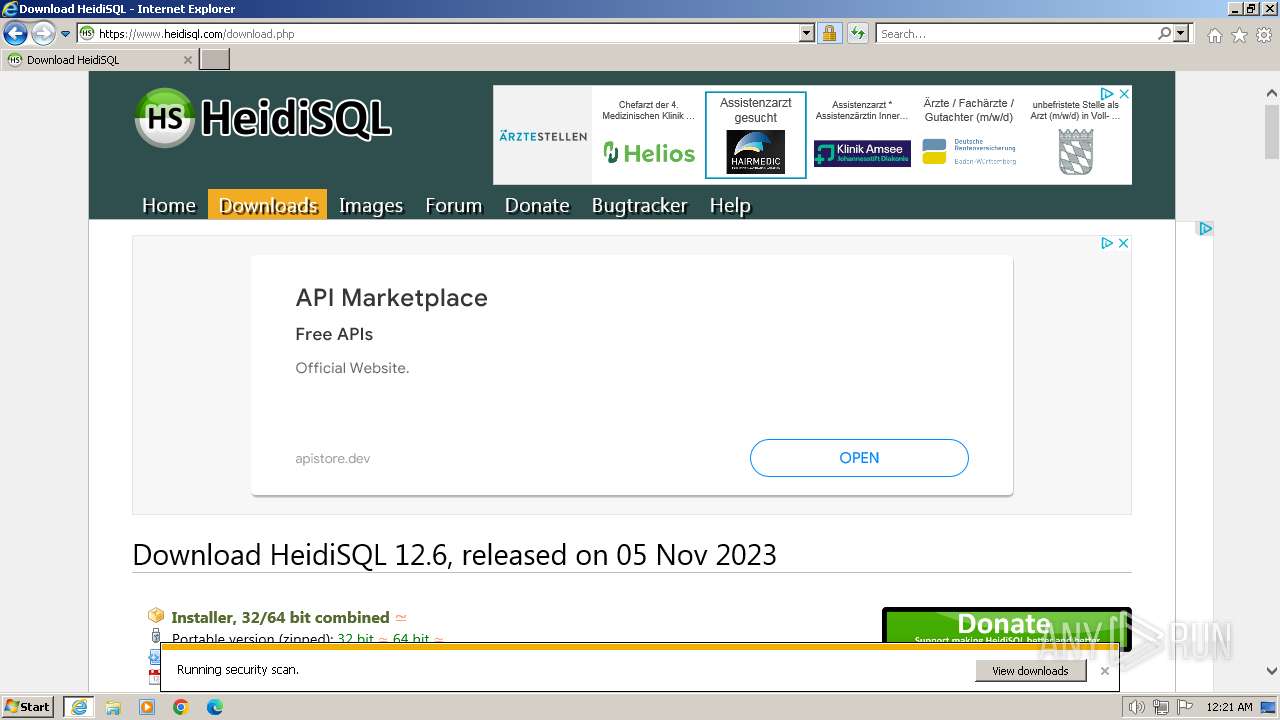
The process uses the downloaded file
- iexplore.exe (PID: 3700)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2920)
Creates files or folders in the user directory
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
- heidisql.exe (PID: 2968)
Creates a software uninstall entry
- HeidiSQL_12.6.0.6765_Setup.tmp (PID: 1860)
Reads the machine GUID from the registry
- heidisql.exe (PID: 2968)
Checks proxy server information
- heidisql.exe (PID: 2968)
Reads the software policy settings
- heidisql.exe (PID: 2968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
7
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
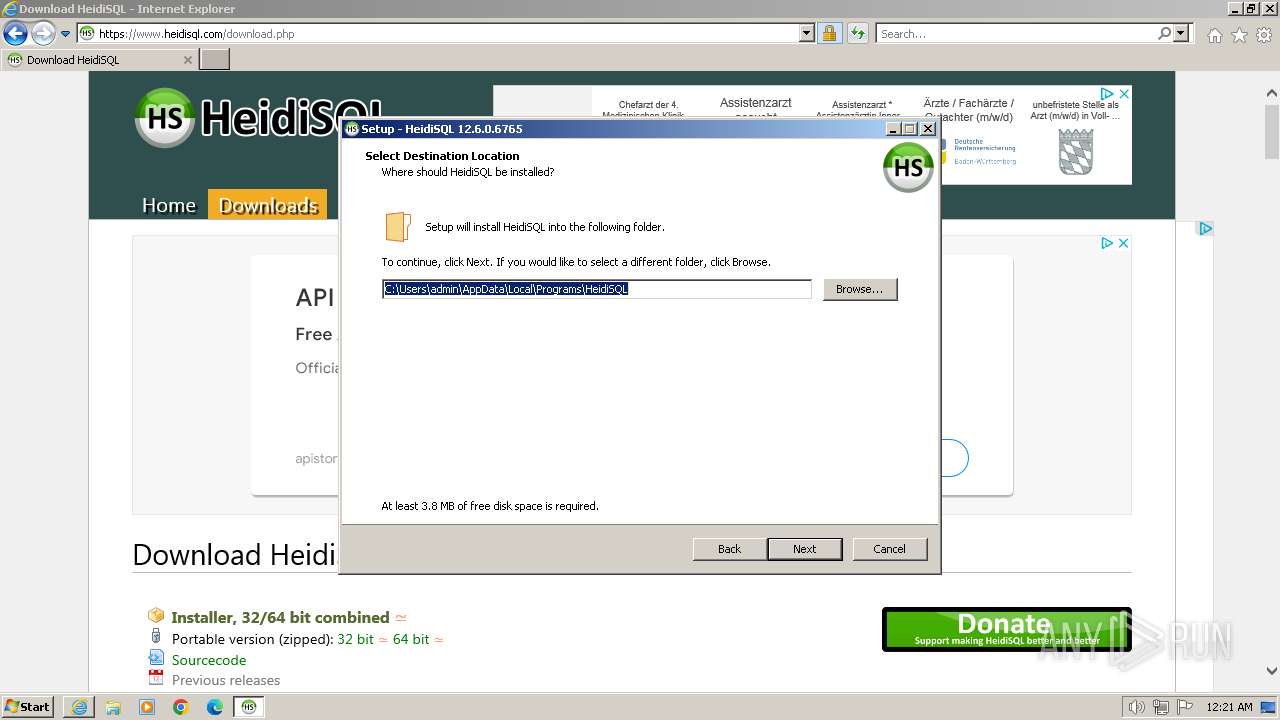
| 240 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\HeidiSQL_12.6.0.6765_Setup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\HeidiSQL_12.6.0.6765_Setup.exe | iexplore.exe | ||||||||||||
User: admin Company: Ansgar Becker Integrity Level: MEDIUM Description: HeidiSQL Setup Exit code: 0 Version: 12.6.0.6765 Modules
| |||||||||||||||
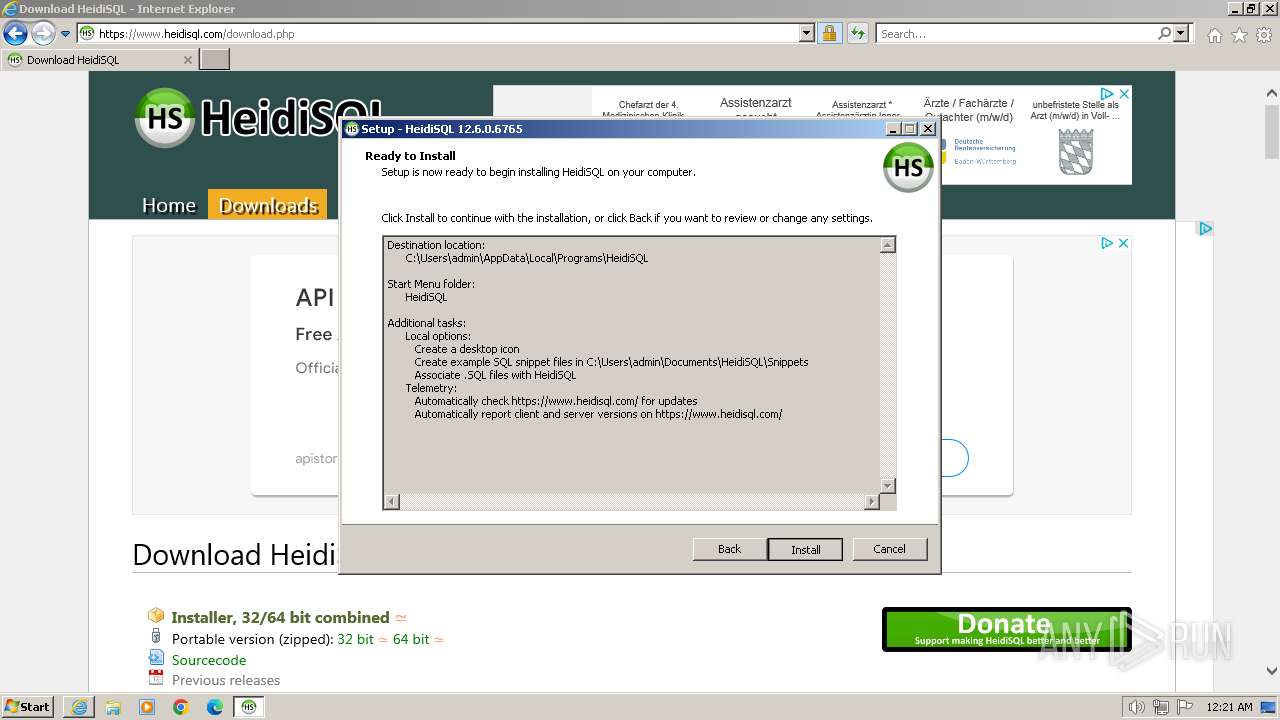
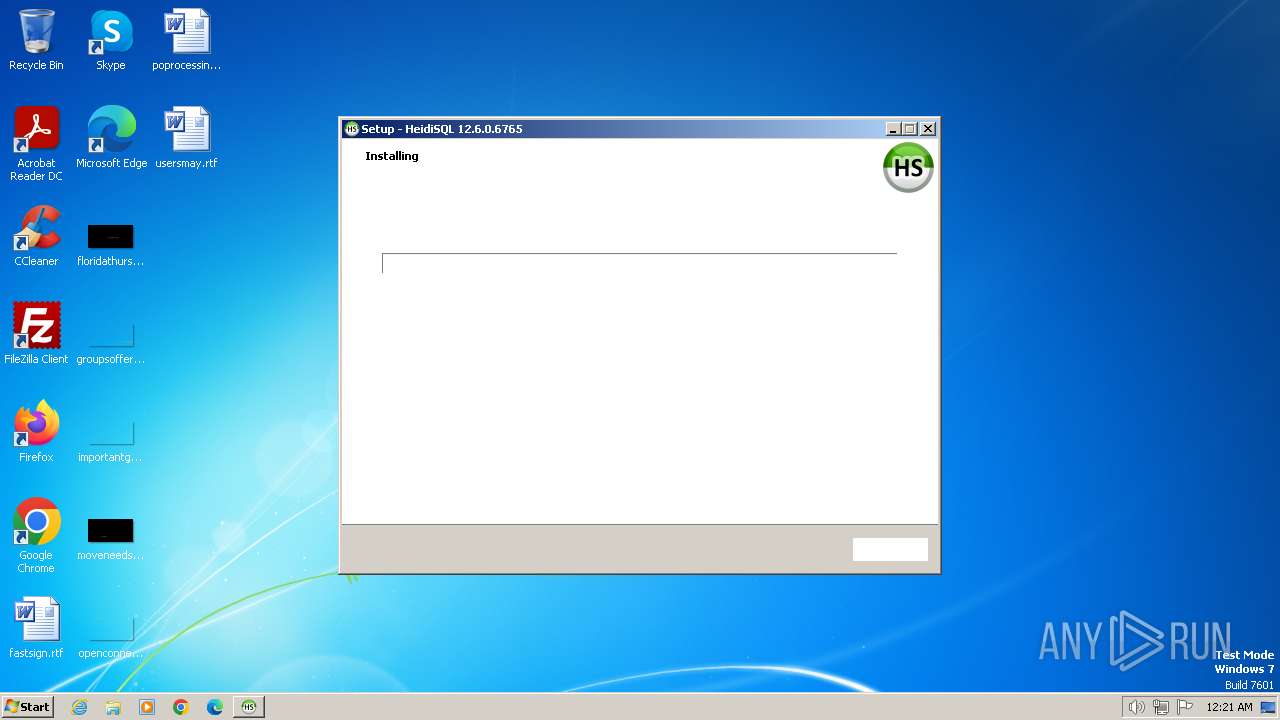
| 1860 | "C:\Users\admin\AppData\Local\Temp\is-36K9E.tmp\HeidiSQL_12.6.0.6765_Setup.tmp" /SL5="$160138,41713096,893952,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\HeidiSQL_12.6.0.6765_Setup.exe" | C:\Users\admin\AppData\Local\Temp\is-36K9E.tmp\HeidiSQL_12.6.0.6765_Setup.tmp | HeidiSQL_12.6.0.6765_Setup.exe | ||||||||||||
User: admin Company: Ansgar Becker Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
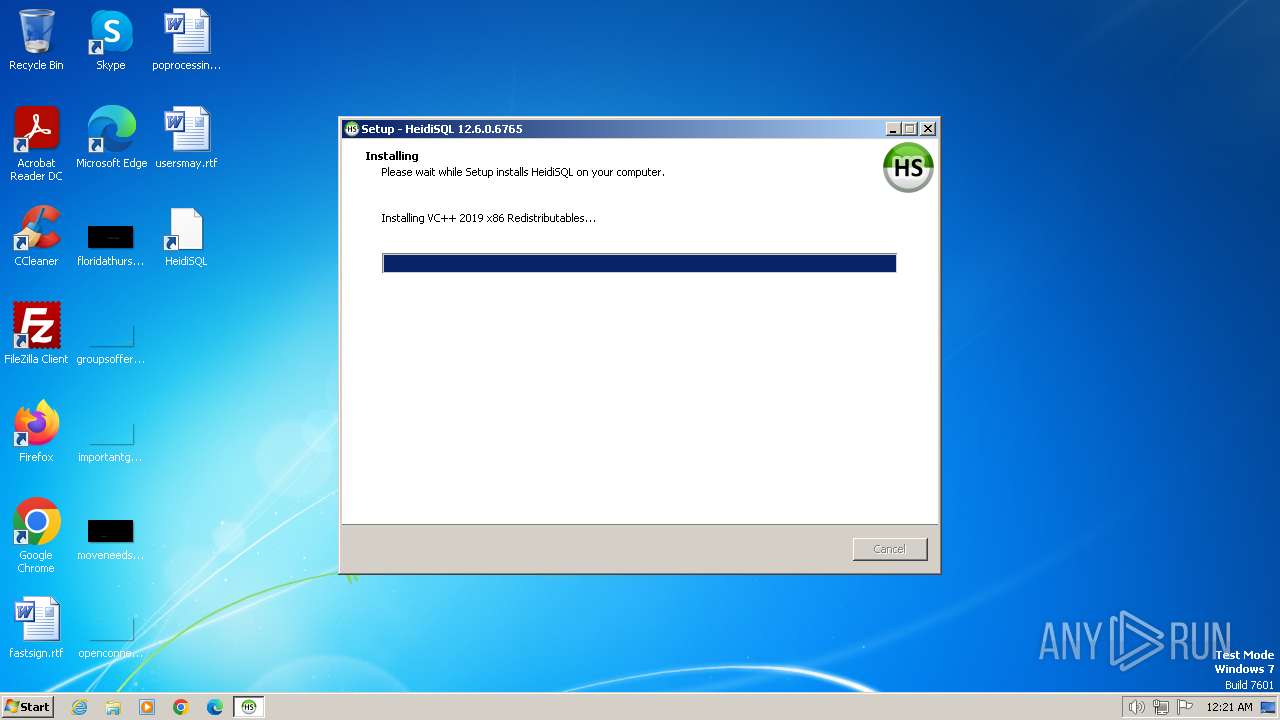
| 2060 | "C:\Users\admin\AppData\Local\Programs\HeidiSQL\VC_redist.x86.exe" /q /norestart /q:a /c:"VC_RED~1.EXE /q:a /c:""msiexec /i vcredist.msi /qn"" " | C:\Users\admin\AppData\Local\Programs\HeidiSQL\VC_redist.x86.exe | HeidiSQL_12.6.0.6765_Setup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.28.29914 Exit code: 1638 Version: 14.28.29914.0 Modules
| |||||||||||||||
| 2100 | "C:\Users\admin\AppData\Local\Temp\{C8561273-6980-4AD5-9BE8-79EF7F30CAA5}\.cr\VC_redist.x86.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Programs\HeidiSQL\VC_redist.x86.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 /q /norestart /q:a /c:"VC_RED~1.EXE /q:a /c:""msiexec /i vcredist.msi /qn"" " | C:\Users\admin\AppData\Local\Temp\{C8561273-6980-4AD5-9BE8-79EF7F30CAA5}\.cr\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.28.29914 Exit code: 1638 Version: 14.28.29914.0 Modules
| |||||||||||||||
| 2920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3700 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
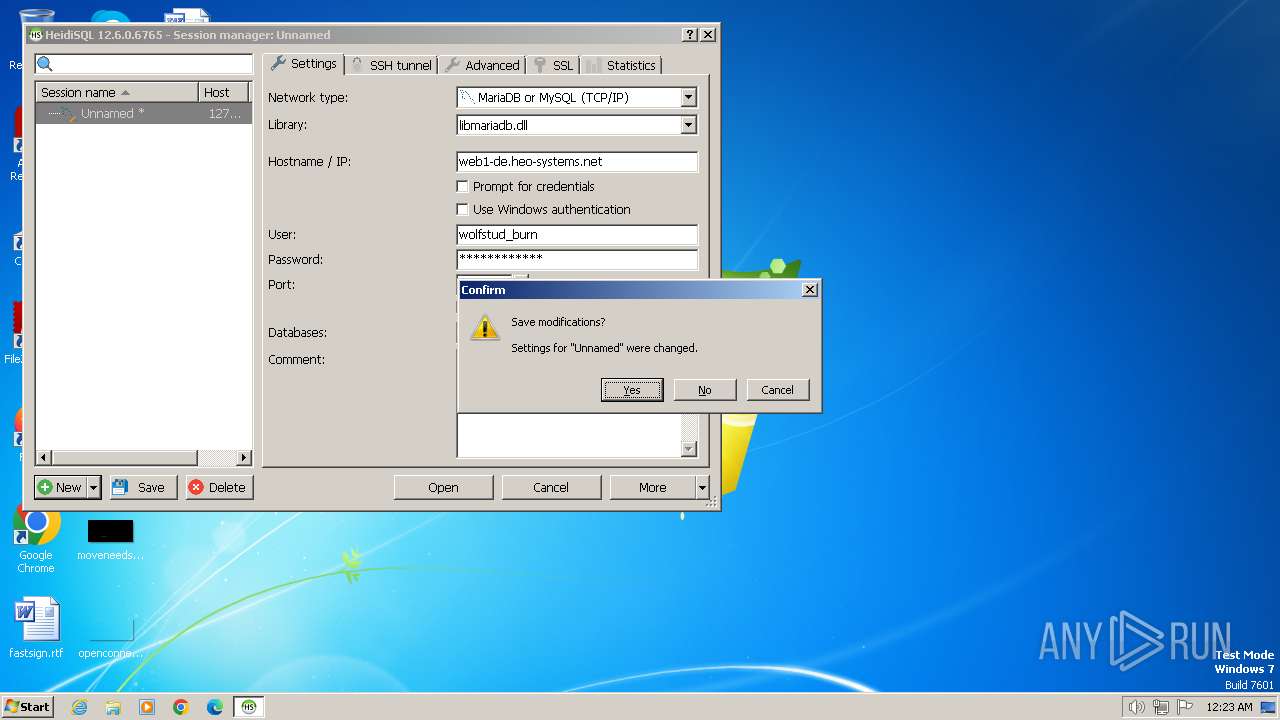
| 2968 | "C:\Users\admin\AppData\Local\Programs\HeidiSQL\heidisql.exe" | C:\Users\admin\AppData\Local\Programs\HeidiSQL\heidisql.exe | HeidiSQL_12.6.0.6765_Setup.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Description: HeidiSQL 12.6.0.6765 32 Bit Exit code: 0 Modules
| |||||||||||||||
| 3700 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.heidisql.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
38 253
Read events
37 887
Write events
290
Delete events
76
Modification events
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 24864912 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31093578 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 325028662 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31093578 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
65
Suspicious files
59
Text files
248
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:B743B3CAFF59ED593602C1CD1BBC79B3 | SHA256:793047C8A0AC8B52E347FE69790C2C76A623642B6CE6C298693BD462DE094C1B | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\create_db[1].png | image | |
MD5:CD1BCFF80D340698B5A10D685ABBDB41 | SHA256:232B3F1C681B426D4B757589537EAC2D0BED1A75AF59BC204D7EFE11F9744853 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E41285A173160E7DDF7CF1AD9E6968C2_848781681684DA374D15312DACB4A3F1 | binary | |
MD5:602797227D192DEF56D1D52761AC15E7 | SHA256:85826CA128A17E464402C9E5482E22244E8E9536BE1CDBC59E37675B272B07D6 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\heidisql_logo[1].png | image | |
MD5:650E091AAA8547BF48B9E6699F9A5393 | SHA256:329B9DC077119AD3E93891DA5DA3BBD6E717B21B3BB9B7C01894AFF7FBC20CDE | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery.selection[1].js | text | |
MD5:D5C2BC705B5BFBF43475DB5C6E863DB1 | SHA256:16C1157BB2712E6A4645A64C1B65C3DA997AC456A347A7C83BA1763DAE261BB5 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\helpers[1].js | text | |
MD5:040B6B75E0B1BB105888C3E514A58B5F | SHA256:EF4A508FAD12FFAD1EB8F7A340044B6D9F8CBA3C36E81E3F12B9B1290E026BE5 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\instagram-icon[1].png | image | |
MD5:52F8A980DDF262F8A5A64E2E2C7F51A5 | SHA256:E44F07283830D60A2FFF2B541998C002AC0427B2106B2127D4E2CC86E234398E | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E41285A173160E7DDF7CF1AD9E6968C2_848781681684DA374D15312DACB4A3F1 | der | |
MD5:AD2937B31E6CB907092B8D9A2527F7E4 | SHA256:5E437173B4EE3585C4D5B0F963BD1D50A1A25B8BAEE0FFA3727EB2BD8B1A3881 | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\facebook-icon[1].png | image | |
MD5:AB52461DF9FBAF75FAC2F3DBEB427E5D | SHA256:C2F95EB22E656D3451B76FF63CAF80D4889D5F6A76F30876667C09243421F66A | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\84AFE219AEC53B0C9251F5E19EF019BD_2C9D5E6D83DF507CBE6C15521D5D3562 | der | |
MD5:EDA45DFE3932BF8661CFB3E41B5BB789 | SHA256:AAF6A74785C2CA4B49BEDD454B8950F8C02FEDC185D6C8BFC3C155EA56E44027 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
109
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2920 | iexplore.exe | GET | 304 | 92.123.48.145:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | IT | — | — | unknown |
2920 | iexplore.exe | GET | 304 | 92.122.225.235:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f78d505714a595e3 | IT | — | — | unknown |
2920 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | US | binary | 2.05 Kb | unknown |
2920 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.starfieldtech.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT1ZqtwV0O1KcYi0gdzcFkHM%2BuArAQUJUWBaFAmOD07LSy%2BzWrZtj2zZmMCCF7FjMX8rTw9 | US | binary | 2.10 Kb | unknown |
2920 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
2920 | iexplore.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | binary | 978 b | unknown |
2920 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDbVdzMVsELUBBnL7Zp8PpU | US | binary | 472 b | unknown |
3700 | iexplore.exe | GET | 304 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?70d85e3b0e586cab | US | — | — | unknown |
2920 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAhflMAthXvozBT%2FU%2B2iPio%3D | US | binary | 471 b | unknown |
2920 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEmjnEcAcBIRCdkf7NhadAI%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2920 | iexplore.exe | 5.175.26.196:443 | www.heidisql.com | Host Europe GmbH | FR | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2920 | iexplore.exe | 92.122.225.235:80 | ctldl.windowsupdate.com | TELECOM ITALIA SPARKLE S.p.A. | IT | unknown |
2920 | iexplore.exe | 92.123.48.145:80 | ctldl.windowsupdate.com | TELECOM ITALIA SPARKLE S.p.A. | IT | unknown |
2920 | iexplore.exe | 192.124.249.23:80 | ocsp.starfieldtech.com | SUCURI-SEC | US | unknown |
2920 | iexplore.exe | 142.250.185.68:443 | www.google.com | GOOGLE | US | whitelisted |
2920 | iexplore.exe | 192.0.73.2:443 | www.gravatar.com | AUTOMATTIC | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.heidisql.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.starfieldtech.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.google.com |
| whitelisted |
www.gravatar.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
www.gstatic.com |
| whitelisted |