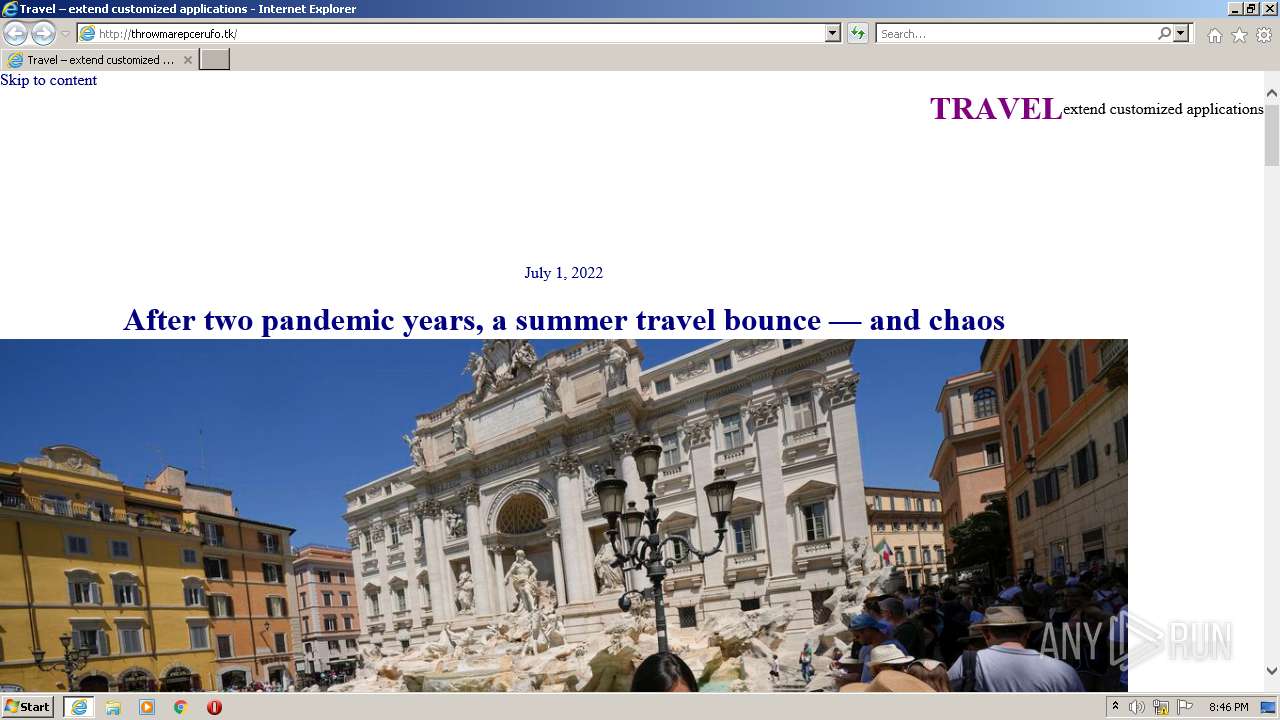
| URL: | http://throwmarepcerufo.tk |
| Full analysis: | https://app.any.run/tasks/166430ea-1d70-425f-a81c-45ea672cc4c3 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 19:45:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A200CE6EB787054118F7C12A0892D3F5 |
| SHA1: | F2BC5B34039EF4084763FB7BAA4301B02E9C81A5 |
| SHA256: | FCAA0BB4559EAA4C50F01F9F8624993AF060D0D2E18DA21D0352258D50C6CA96 |
| SSDEEP: | 3:N1KKNZ5XAV5RO:CKNZ5QV5o |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2484)
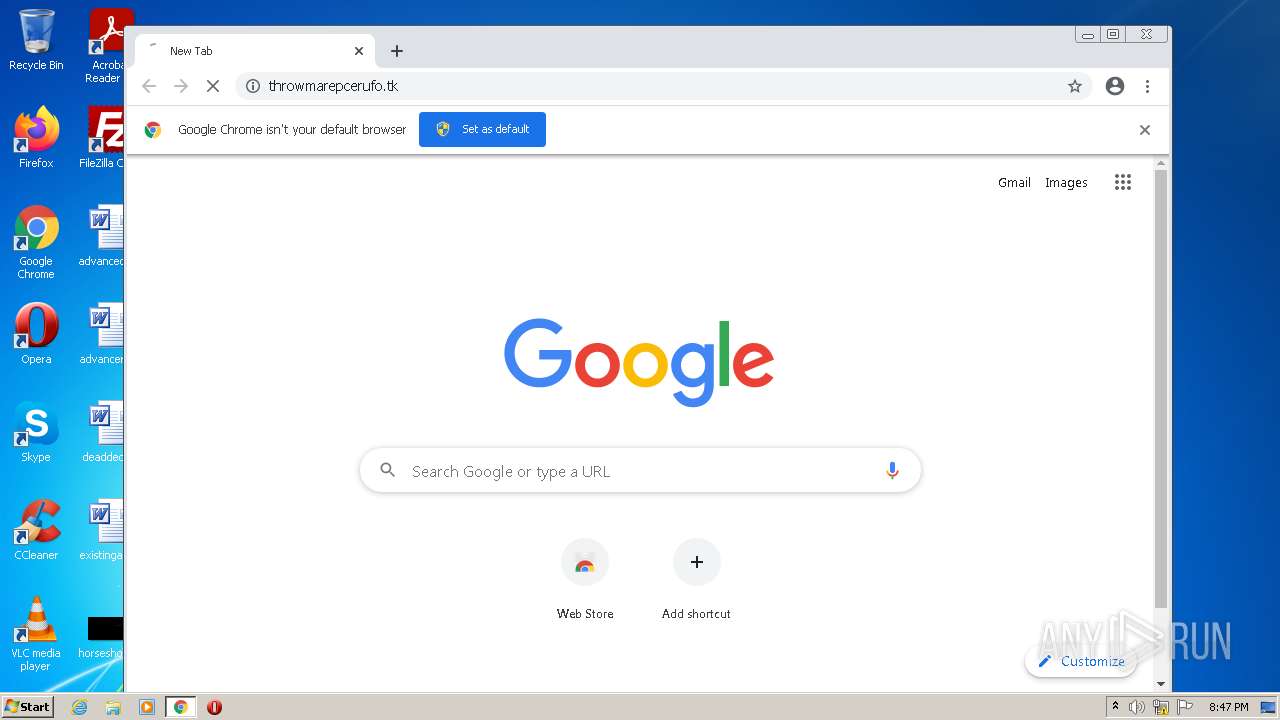
Modifies files in Chrome extension folder
- chrome.exe (PID: 4020)
INFO
Reads the computer name
- iexplore.exe (PID: 1448)
- iexplore.exe (PID: 2484)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 1308)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 2980)
Checks supported languages
- iexplore.exe (PID: 1448)
- chrome.exe (PID: 4020)
- iexplore.exe (PID: 2484)
- chrome.exe (PID: 1308)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1296)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 3100)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 508)
- chrome.exe (PID: 3904)
- chrome.exe (PID: 2980)
Changes internet zones settings
- iexplore.exe (PID: 1448)
Manual execution by user
- chrome.exe (PID: 4020)
Reads internet explorer settings
- iexplore.exe (PID: 2484)
Application launched itself
- chrome.exe (PID: 4020)
- iexplore.exe (PID: 1448)
Checks Windows Trust Settings
- iexplore.exe (PID: 1448)
Reads settings of System Certificates
- iexplore.exe (PID: 1448)
- chrome.exe (PID: 3232)
Reads the date of Windows installation
- iexplore.exe (PID: 1448)
- chrome.exe (PID: 2980)
Changes default file association
- chrome.exe (PID: 4020)
Changes settings of System certificates
- iexplore.exe (PID: 1448)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,6712105327734025716,12558157188902849727,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,6712105327734025716,12558157188902849727,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3376 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,6712105327734025716,12558157188902849727,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,6712105327734025716,12558157188902849727,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://throwmarepcerufo.tk" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,6712105327734025716,12558157188902849727,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,6712105327734025716,12558157188902849727,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3180 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1448 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1052,6712105327734025716,12558157188902849727,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2956 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,6712105327734025716,12558157188902849727,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
18 637
Read events
18 374
Write events
253
Delete events
10
Modification events
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 675114272 | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977668 | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 975271772 | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977668 | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
149
Text files
154
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\thumb10[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\EHPLLYM8.htm | html | |
MD5:— | SHA256:— | |||
| 2484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\thumb14[1].jpg | image | |
MD5:— | SHA256:— | |||
| 1448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 2484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\thumb12[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\theme[1].css | text | |
MD5:— | SHA256:— | |||
| 2484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\thumb18[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\thumb16[1].jpg | image | |
MD5:— | SHA256:— | |||
| 1448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
59
DNS requests
31
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2484 | iexplore.exe | GET | — | 172.67.220.31:80 | http://throwmarepcerufo.tk/wp-content/uploads/2022/06/thumb10.jpg | US | — | — | suspicious |
2484 | iexplore.exe | GET | — | 172.67.220.31:80 | http://throwmarepcerufo.tk/wp-content/uploads/2022/05/thumb14.jpg | US | — | — | suspicious |
2484 | iexplore.exe | GET | — | 172.67.220.31:80 | http://throwmarepcerufo.tk/wp-content/themes/quadrat-green-wpcom/assets/theme.css?ver=1.1.42 | US | — | — | suspicious |
2484 | iexplore.exe | GET | — | 172.67.220.31:80 | http://throwmarepcerufo.tk/wp-includes/blocks/navigation/view.min.js?ver=009e29110e016c14bac4ba0ecc809fcd | US | — | — | suspicious |
2484 | iexplore.exe | GET | — | 172.67.220.31:80 | http://throwmarepcerufo.tk/wp-content/uploads/2022/03/thumb18.jpg | US | — | — | suspicious |
2484 | iexplore.exe | GET | 200 | 172.67.220.31:80 | http://throwmarepcerufo.tk/ | US | html | 10.0 Kb | suspicious |
2484 | iexplore.exe | GET | 200 | 172.67.220.31:80 | http://throwmarepcerufo.tk/wp-content/uploads/2022/03/thumb16.jpg | US | image | 117 Kb | suspicious |
1448 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1448 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
1448 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2484 | iexplore.exe | 104.21.24.194:80 | throwmarepcerufo.tk | Cloudflare Inc | US | unknown |
1448 | iexplore.exe | 8.249.61.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1448 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1448 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2484 | iexplore.exe | 172.67.220.31:80 | throwmarepcerufo.tk | — | US | suspicious |
— | — | 172.67.220.31:80 | throwmarepcerufo.tk | — | US | suspicious |
1448 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1448 | iexplore.exe | 104.21.24.194:80 | throwmarepcerufo.tk | Cloudflare Inc | US | unknown |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1448 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
throwmarepcerufo.tk |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2484 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |