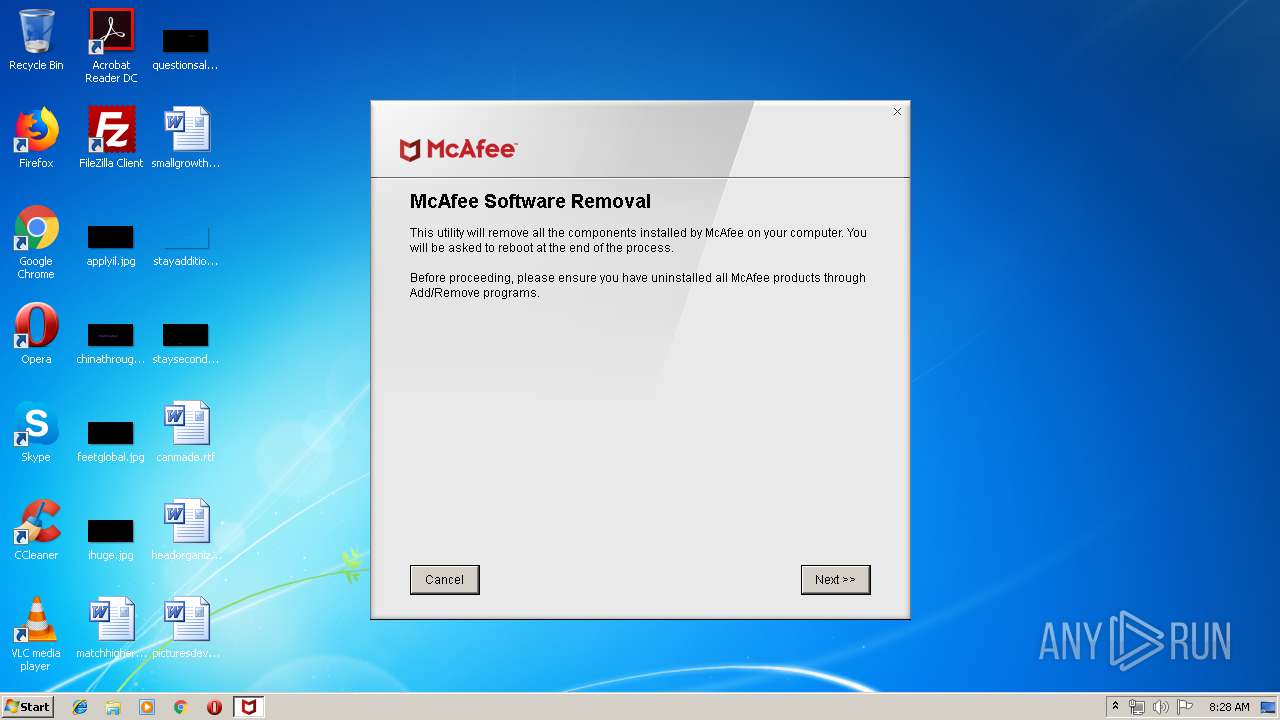
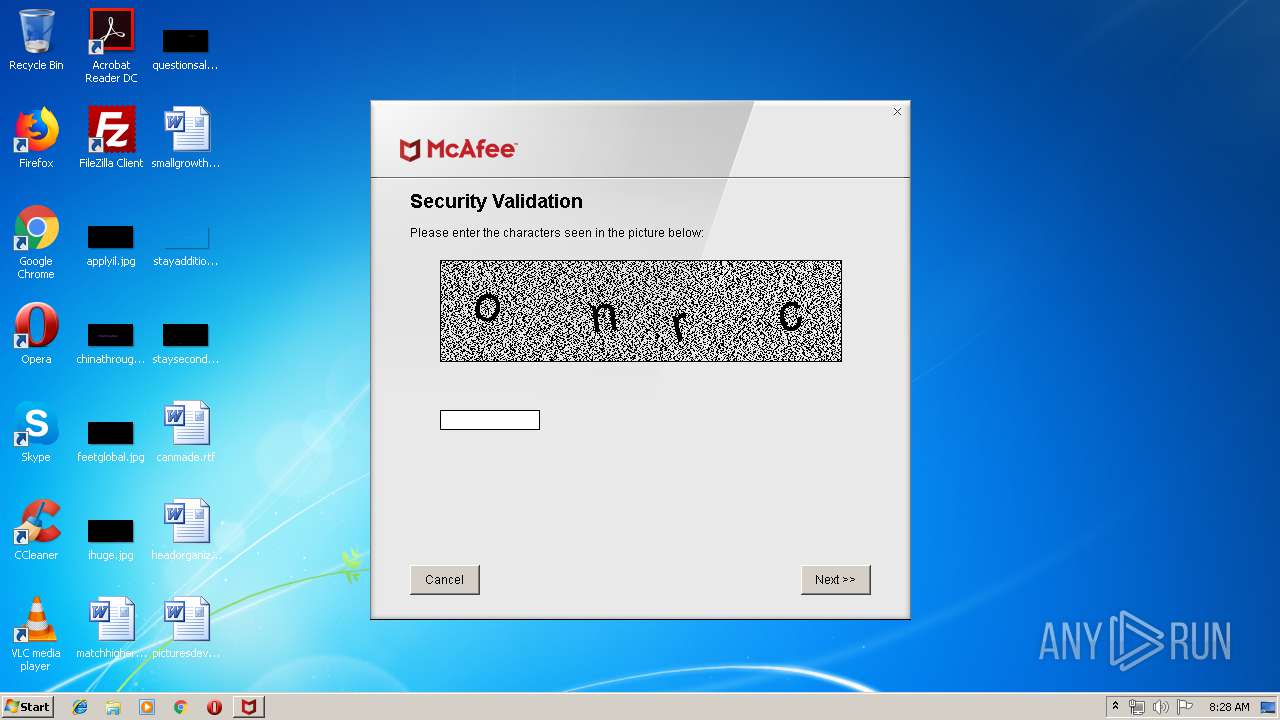
| File name: | MCPR.exe |
| Full analysis: | https://app.any.run/tasks/76344bc8-c3f5-4041-9516-0801842b1fc1 |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2019, 07:28:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 12A889049EFBA4253F88E408360DB335 |
| SHA1: | 18D24100BA5C4CEBF5A3FF02ADDA0C2BFE74A4B6 |
| SHA256: | FC9E46FC6A022A8D647419955B3E14D15183E20FF72C55C8100B4D6B455EF09B |
| SSDEEP: | 196608:H0v73NH39AejbER1PrYnAZd6V+ZZbd8TeUEQHD7qg0t0AJ1SzSnAy:HE3VMR1PrmAZd6V4Zbdpt0hzSnl |
MALICIOUS
Loads dropped or rewritten executable
- MCPR.exe (PID: 2288)
- mccleanup.exe (PID: 2308)
- mfputil_x86.exe (PID: 2824)
Application was dropped or rewritten from another process
- mccleanup.exe (PID: 2616)
- McClnUI.exe (PID: 828)
- mccleanup.exe (PID: 2308)
- sediag.exe (PID: 2032)
- firesvc.exe (PID: 2828)
- sediag.exe (PID: 3816)
- mfputil_x86.exe (PID: 2824)
Loads the Task Scheduler DLL interface
- mccleanup.exe (PID: 2616)
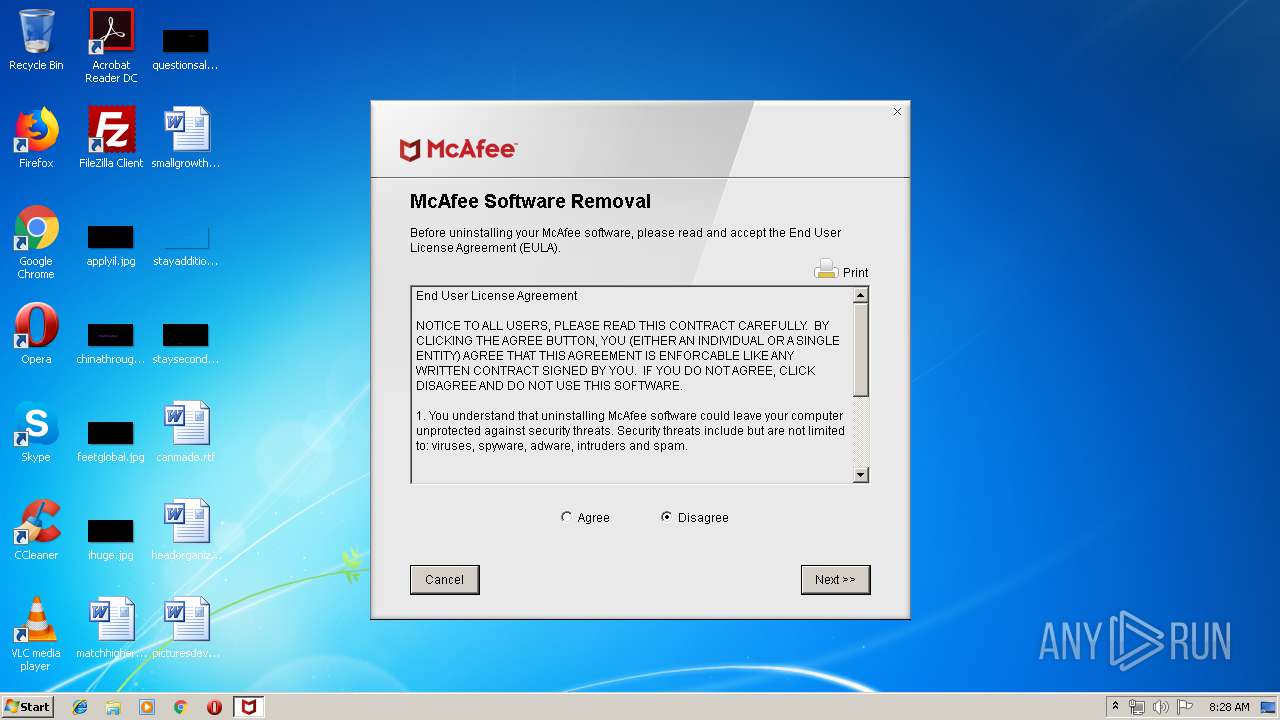
Changes settings of System certificates
- McClnUI.exe (PID: 828)
Starts NET.EXE for service management
- cmd.exe (PID: 2132)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 2068)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 2748)
- cmd.exe (PID: 2000)
- cmd.exe (PID: 3104)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 300)
- cmd.exe (PID: 572)
- cmd.exe (PID: 3556)
- cmd.exe (PID: 1008)
- cmd.exe (PID: 2768)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 1476)
- cmd.exe (PID: 2440)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 760)
- cmd.exe (PID: 920)
- cmd.exe (PID: 3792)
- cmd.exe (PID: 3512)
- cmd.exe (PID: 1360)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 2448)
- mccleanup.exe (PID: 2308)
- cmd.exe (PID: 3208)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 3552)
- cmd.exe (PID: 1892)
- cmd.exe (PID: 2596)
- cmd.exe (PID: 1076)
- cmd.exe (PID: 1020)
- cmd.exe (PID: 2248)
- cmd.exe (PID: 3212)
- cmd.exe (PID: 1420)
- cmd.exe (PID: 312)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 3168)
SUSPICIOUS
Executable content was dropped or overwritten
- MCPR.exe (PID: 2288)
Adds / modifies Windows certificates
- McClnUI.exe (PID: 828)
Creates files in the Windows directory
- mccleanup.exe (PID: 2616)
- mccleanup.exe (PID: 2308)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2712)
Creates COM task schedule object
- mccleanup.exe (PID: 2308)
Starts SC.EXE for service management
- cmd.exe (PID: 2656)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 608)
- cmd.exe (PID: 2448)
- cmd.exe (PID: 252)
- cmd.exe (PID: 2228)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 4016)
Starts CMD.EXE for commands execution
- mccleanup.exe (PID: 2308)
Creates or modifies windows services
- mccleanup.exe (PID: 2308)
INFO
Dropped object may contain Bitcoin addresses
- MCPR.exe (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x32fe |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.2.257.0 |
| ProductVersionNumber: | 10.2.257.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | McAfee, Inc. |
| FileDescription: | McAfee ESD Package |
| FileVersion: | 10.2 |
| LegalCopyRight: | Copyright © 2017 McAfee, Inc |
| OriginalFileName: | coreESD.exe |
| ProductName: | McAfee ESD Package |
| ProductVersion: | 10.2.257.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:41 |
| Detected languages: |
|
| CompanyName: | McAfee, Inc. |
| FileDescription: | McAfee ESD Package |
| FileVersion: | 10.2 |
| LegalCopyRight: | Copyright © 2017 McAfee, Inc |
| OriginalFilename: | coreESD.exe |
| ProductName: | McAfee ESD Package |
| ProductVersion: | 10.2.257.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000608D | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4239 |
.rdata | 0x00008000 | 0x000013A4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16231 |
.data | 0x0000A000 | 0x000202F8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.89813 |
.ndata | 0x0002B000 | 0x00012000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003D000 | 0x00006320 | 0x00006400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.01191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28747 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.83176 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 3.49878 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.21536 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.56083 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 4.44358 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.69913 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
242
Monitored processes
148
Malicious processes
2
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Windows\system32\cmd.exe" /c "sc delete SafeFamilyService" | C:\Windows\system32\cmd.exe | — | mccleanup.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 300 | "C:\Windows\system32\cmd.exe" /c "net stop "mcproxy"" | C:\Windows\system32\cmd.exe | — | mccleanup.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 312 | sc delete "McSchedulerSvc" | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 312 | "C:\Windows\system32\cmd.exe" /c "regsvr32 /u /s "%PROGRAMFILES%\McAfee\MSK\tbirdins.dll"" | C:\Windows\system32\cmd.exe | — | mccleanup.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 404 | regsvr32 /u /s tbirdins.dll | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 456 | net stop "McAfee SiteAdvisor service" | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 476 | regsvr32 /u /s mskeuplg.dll | C:\Windows\system32\regsvr32.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | "C:\Windows\system32\cmd.exe" /c "net stop "mcpromgr"" | C:\Windows\system32\cmd.exe | — | mccleanup.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 608 | "C:\Windows\system32\cmd.exe" /c "sc delete "McOobeSv2"" | C:\Windows\system32\cmd.exe | — | mccleanup.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 676 | tskill mfp | C:\Windows\system32\tskill.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Remote Desktop Services End Process Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
879
Read events
844
Write events
34
Delete events
1
Modification events
| (PID) Process: | (828) McClnUI.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (828) McClnUI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 0F000000010000001400000085FEF11B4F47FE3952F98301C9F98976FEFEE0CE09000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030353000000010000002500000030233021060B6086480186F8450107300130123010060A2B0601040182373C0101030200C01400000001000000140000007B5B45CFAFCECB7AFD31921A6AB6F346EB5748501D00000001000000100000005B3B67000EEB80022E42605B6B3B72400B000000010000000E000000740068006100770074006500000003000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B812000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
| (PID) Process: | (828) McClnUI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\91C6D6EE3E8AC86384E548C299295C756C817B81 |
| Operation: | write | Name: | Blob |
Value: 190000000100000010000000DC73F9B71E16D51D26527D32B11A6A3D03000000010000001400000091C6D6EE3E8AC86384E548C299295C756C817B810B000000010000000E00000074006800610077007400650000001D00000001000000100000005B3B67000EEB80022E42605B6B3B72401400000001000000140000007B5B45CFAFCECB7AFD31921A6AB6F346EB57485053000000010000002500000030233021060B6086480186F8450107300130123010060A2B0601040182373C0101030200C009000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B060105050703030F000000010000001400000085FEF11B4F47FE3952F98301C9F98976FEFEE0CE2000000001000000240400003082042030820308A0030201020210344ED55720D5EDEC49F42FCE37DB2B6D300D06092A864886F70D01010505003081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F74204341301E170D3036313131373030303030305A170D3336303731363233353935395A3081A9310B300906035504061302555331153013060355040A130C7468617774652C20496E632E31283026060355040B131F43657274696669636174696F6E205365727669636573204469766973696F6E31383036060355040B132F2863292032303036207468617774652C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79311F301D06035504031316746861777465205072696D61727920526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100ACA0F0FB8059D49CC7A4CF9DA159730910450C0D2C6E68F16C5B4868495937FC0B3319C2777FCC102D95341CE6EB4D09A71CD2B8C9973602B789D4245F06C0CC4494948D02626FEB5ADD118D289A5C8490107A0DBD74662F6A38A0E2D55444EB1D079F07BA6FEEE9FD4E0B29F53E84A001F19CABF81C7E89A4E8A1D871650DA3517BEEBCD222600DB95B9DDFBAFC515B0BAF98B2E92EE904E86287DE2BC8D74EC14C641EDDCF8758BA4A4FCA68071D1C9D4AC6D52F91CC7C71721CC5C067EB32FDC9925C94DA85C09BBF537D2B09F48C9D911F976A52CBDE0936A477D87B875044D53E6E2969FB3949261E09A5807B402DEBE82785C9FE61FD7EE67C971DD59D0203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147B5B45CFAFCECB7AFD31921A6AB6F346EB574850300D06092A864886F70D010105050003820101007911C04BB391B6FCF0E967D40D6E45BE55E893D2CE033FEDDA25B01D57CB1E3A76A04CEC5076E864720CA4A9F1B88BD6D68784BB32E54111C077D9B3609DEB1BD5D16E4444A9A601EC55621D77B85C8E48497C9C3B5711ACAD73378E2F785C906847D96060E6FC073D222017C4F716E9C4D872F9C8737CDF162F15A93EFD6A27B6A1EB5ABA981FD5E34D640A9D13C861BAF5391C87BAB8BD7B227FF6FEAC4079E5AC106F3D8F1B79768BC437B3211884E53600EB632099B9E9FE3304BB41C8C102F94463209E81CE42D3D63F2C76D3639C59DD8FA6E10EA02E41F72E9547CFBCFD33F3F60B617E7E912B8147C22730EEA7105D378F5C392BE404F07B8D568C68 | |||
| (PID) Process: | (2288) MCPR.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\nsg7AEF.tmp\McSplash.dll | |||
| (PID) Process: | (2616) mccleanup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\AP\McVscIns |
| Operation: | write | Name: | APEnabled |
Value: 0 | |||
| (PID) Process: | (2616) mccleanup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\AP\McVscIns |
| Operation: | write | Name: | SOFTWARE\McAfee\SystemCore\VSCore\On Access Scanner\BehaviourBlocking |
Value: 0 | |||
| (PID) Process: | (2616) mccleanup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\SystemCore\VSCore |
| Operation: | write | Name: | LockDownEnabled |
Value: 0 | |||
| (PID) Process: | (2616) mccleanup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\Logging\Controller |
| Operation: | write | Name: | Shutdown Controller |
Value: 4D4352470100000004000000040000003827D569621FECD143ED118D7A2EA0BEA2231907 | |||
| (PID) Process: | (2308) mccleanup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\AP\McVscIns |
| Operation: | write | Name: | APEnabled |
Value: 0 | |||
| (PID) Process: | (2308) mccleanup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\AP\McVscIns |
| Operation: | write | Name: | SOFTWARE\McAfee\SystemCore\VSCore\On Access Scanner\BehaviourBlocking |
Value: 0 | |||
Executable files
31
Suspicious files
97
Text files
353
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\nsg7AEF.tmp\McSplash.bmp | image | |
MD5:4588673F6257394D3827715DFF22A6DA | SHA256:855A0E7C18A2DA2424F94869B627AD84437D00D214E309788EB1AC355B394159 | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\MCPR\StartCleanupDebug.bat | text | |
MD5:— | SHA256:— | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\MCPR\StartCleanup.bat | text | |
MD5:— | SHA256:— | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\MCPR\master.ini | text | |
MD5:— | SHA256:— | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\MCPR\McClnUI.exe | executable | |
MD5:— | SHA256:— | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\MCPR\mccleanup.exe | executable | |
MD5:— | SHA256:— | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\nsg7AEF.tmp\McSplash.dll | executable | |
MD5:B0C9D2B5B641E2C2DE6560A4258E0640 | SHA256:EA00B739C048A9B155A64342C2B6E12774DDA56F5A80C8C9FC4817843908A3DA | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\MCPR\MSKCleanUP.wse | text | |
MD5:C1F3824A5CD49FD26CEF70137178542E | SHA256:5B38BF7DB54191FAE7AC5826F079AC8CB6EBFA096B86F6C38542CEC8240CDAA8 | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\MCPR\MCPRCleanUP.wse | text | |
MD5:3B08FAE393C8BC88236C1BEA6C9995D0 | SHA256:FB2417A03DF8F10823EF6A568C8EC0F2875E96904504264B32F53DD3602CEB7A | |||
| 2288 | MCPR.exe | C:\Users\admin\AppData\Local\Temp\MCPR\MpfCleanUP.wse | text | |
MD5:133BBF94AD6260B31A42E0079679BC86 | SHA256:76308443A9BC8475879717D470F6522493CECC65E27206CA5AB71CC58C0B89BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
mccleanup.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
mccleanup.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\MCPR\mccleanup.exe loading C:\Users\admin\AppData\Local\Temp\MCPR\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
mccleanup.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
mccleanup.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\MCPR\mccleanup.exe loading C:\Users\admin\AppData\Local\Temp\MCPR\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
mccleanup.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
mccleanup.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\MCPR\mccleanup.exe loading C:\Users\admin\AppData\Local\Temp\MCPR\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
mccleanup.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
mccleanup.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\MCPR\mccleanup.exe loading C:\Users\admin\AppData\Local\Temp\MCPR\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
mccleanup.exe | NotComDllGetInterface: DLL not found in install location, looking in current directory |
mccleanup.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\MCPR\mccleanup.exe loading C:\Users\admin\AppData\Local\Temp\MCPR\mfeaaca.dll, WinVerifyTrust failed with 80092003
|