| File name: | ROP2.exe |
| Full analysis: | https://app.any.run/tasks/7c025beb-24ba-43d2-a2c1-4a445fc41599 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2024, 14:27:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8F5A2B3154ABA26ACF5440FD3034326C |
| SHA1: | B4D508EE783DC1F1A2CF9147CC1E5729470E773B |
| SHA256: | FC7E799742A1C64361A8A9C3FECDF44F9DB85F0BF57F4FB5712519D12BA4C5AC |
| SSDEEP: | 393216:l2iLiU7VXd6AKprP7iJx4J20cQ3qpalJZfhxGWqIcckC:l2iNObp4x820AS7nj |
MALICIOUS
Drops the executable file immediately after the start
- ROP2.exe (PID: 2892)
- cmd.exe (PID: 696)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 2908)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2908)
Disables Windows Defender
- gdifuncs.exe (PID: 2660)
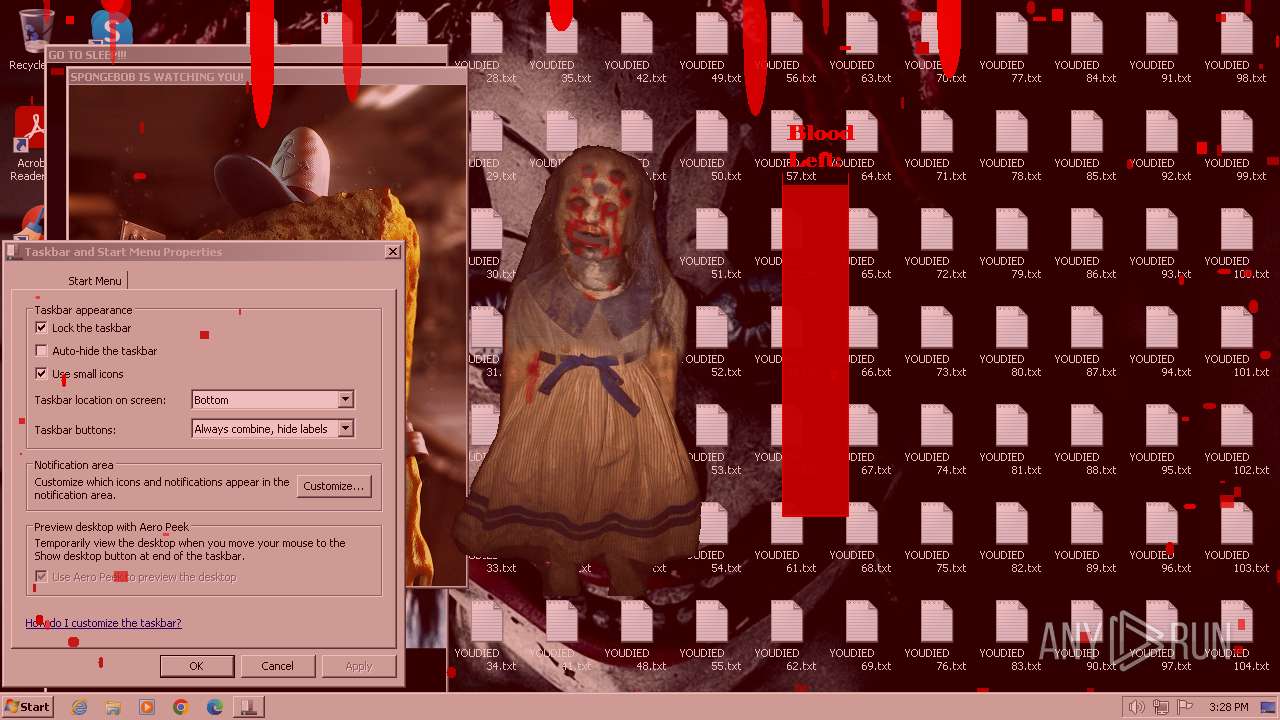
Task Manager has been disabled (taskmgr)
- gdifuncs.exe (PID: 2660)
Changes the login/logoff helper path in the registry
- gdifuncs.exe (PID: 2660)
Disables the Run the Start menu
- gdifuncs.exe (PID: 2660)
SUSPICIOUS
Runs WScript without displaying logo
- wscript.exe (PID: 2908)
The process executes VB scripts
- ROP2.exe (PID: 2892)
Reads security settings of Internet Explorer
- ROP2.exe (PID: 2892)
Reads the Internet Settings
- ROP2.exe (PID: 2892)
- wscript.exe (PID: 2908)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2908)
Blank space has been found in the path
- wscript.exe (PID: 2908)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 2908)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2908)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 696)
Creates file in the systems drive root
- rundll32.exe (PID: 2060)
- rundll32.exe (PID: 2968)
- rundll32.exe (PID: 3680)
- rundll32.exe (PID: 1816)
- cmd.exe (PID: 696)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2908)
Executing commands from ".cmd" file
- wscript.exe (PID: 2908)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 696)
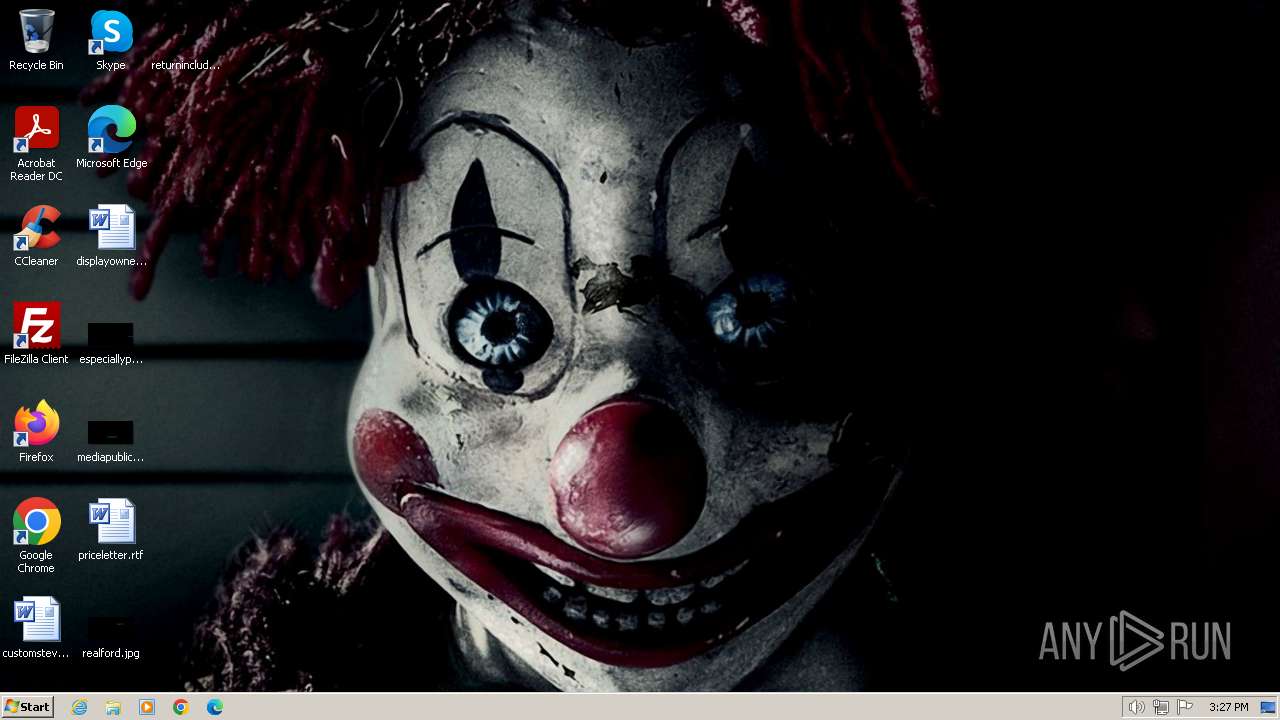
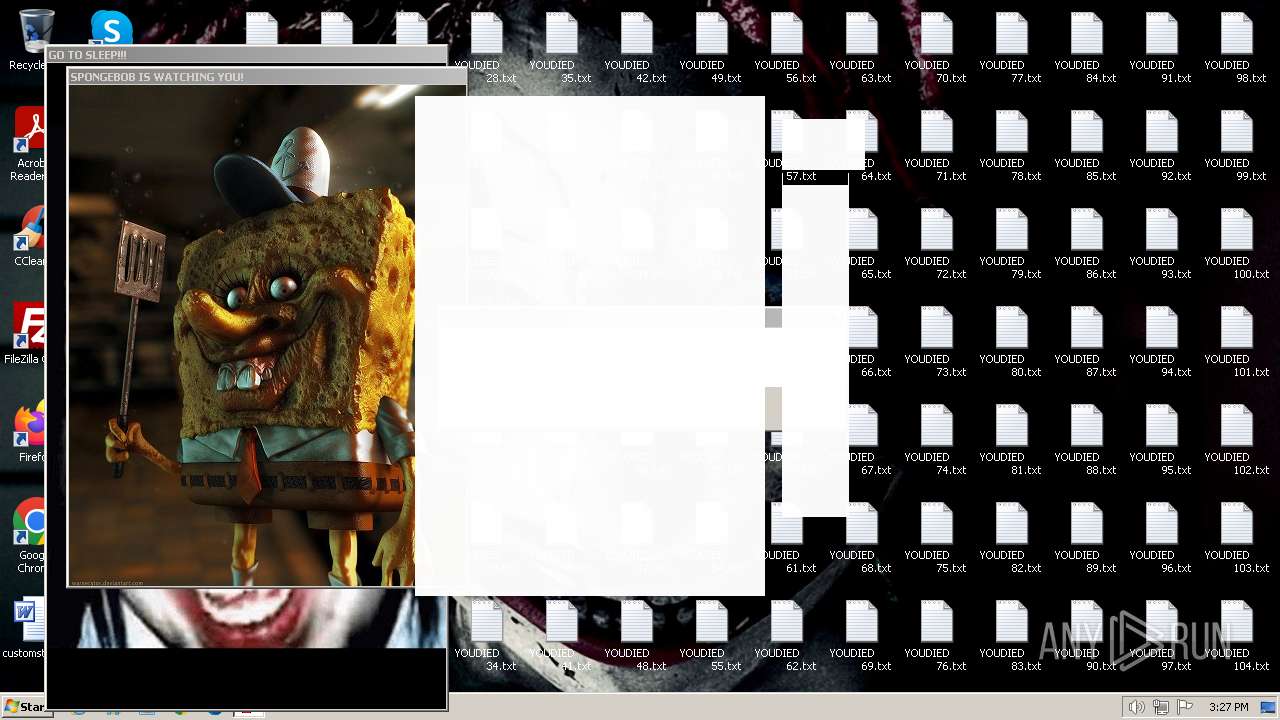
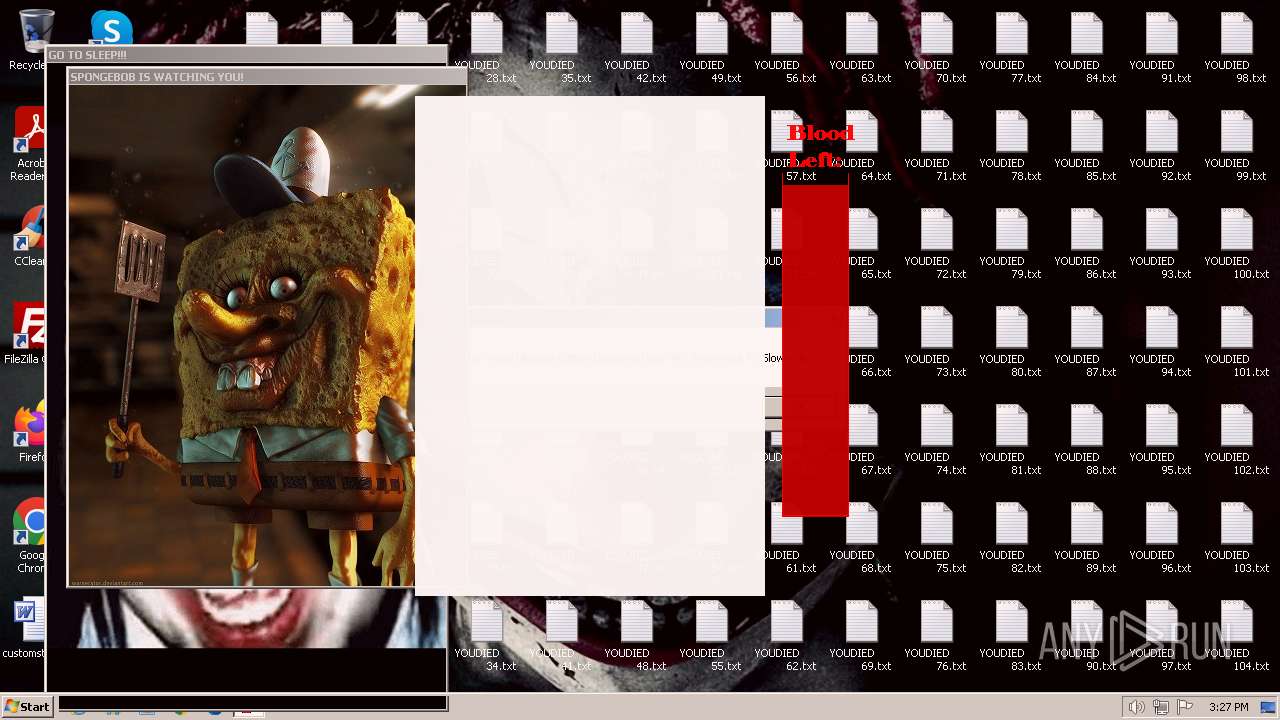
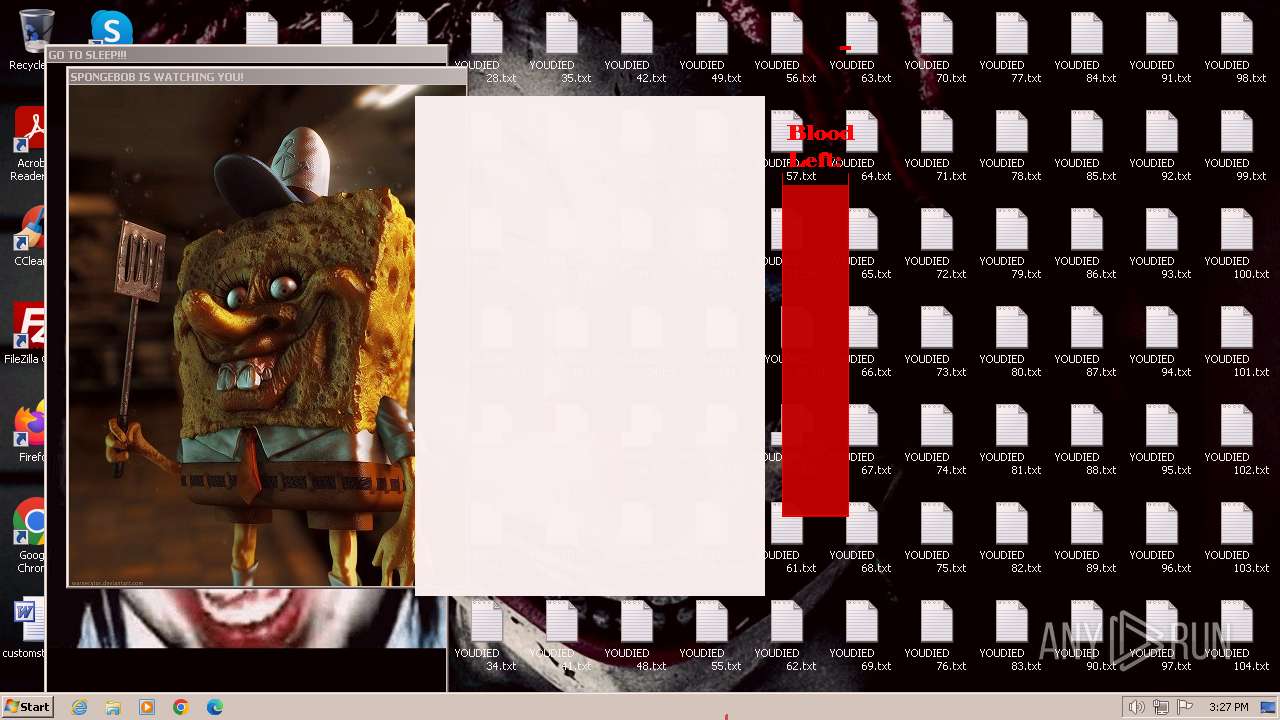
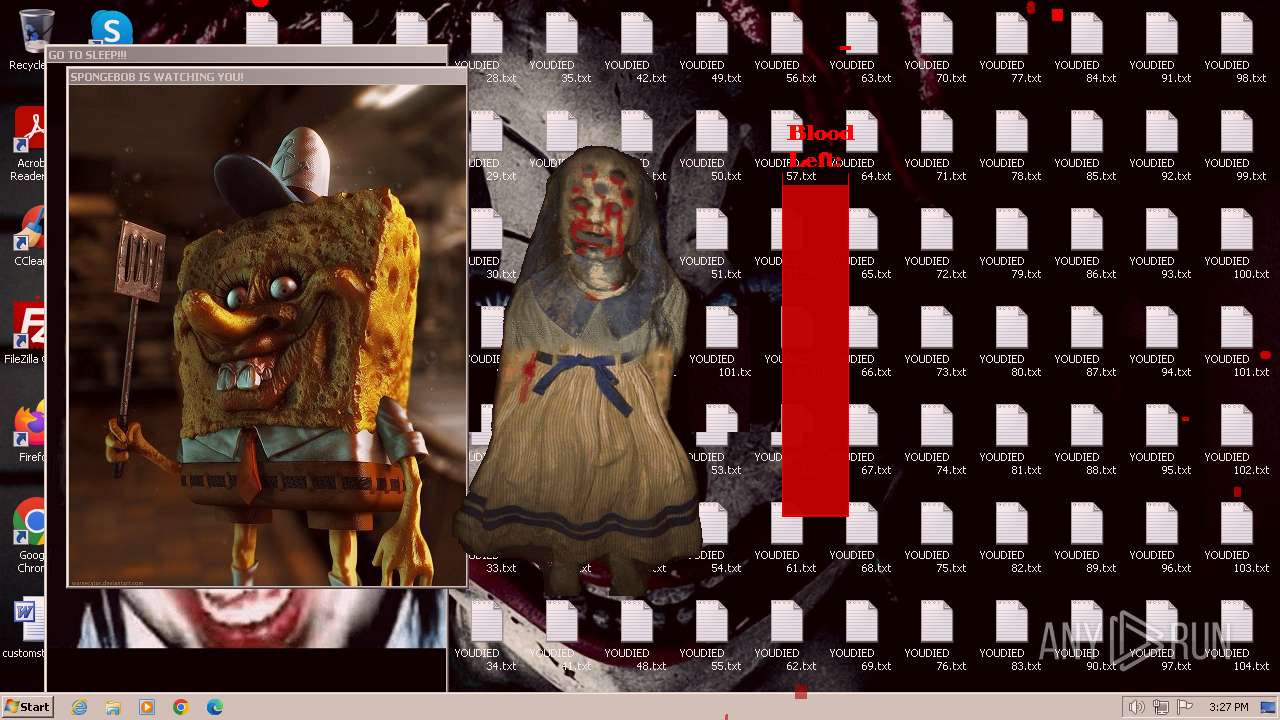
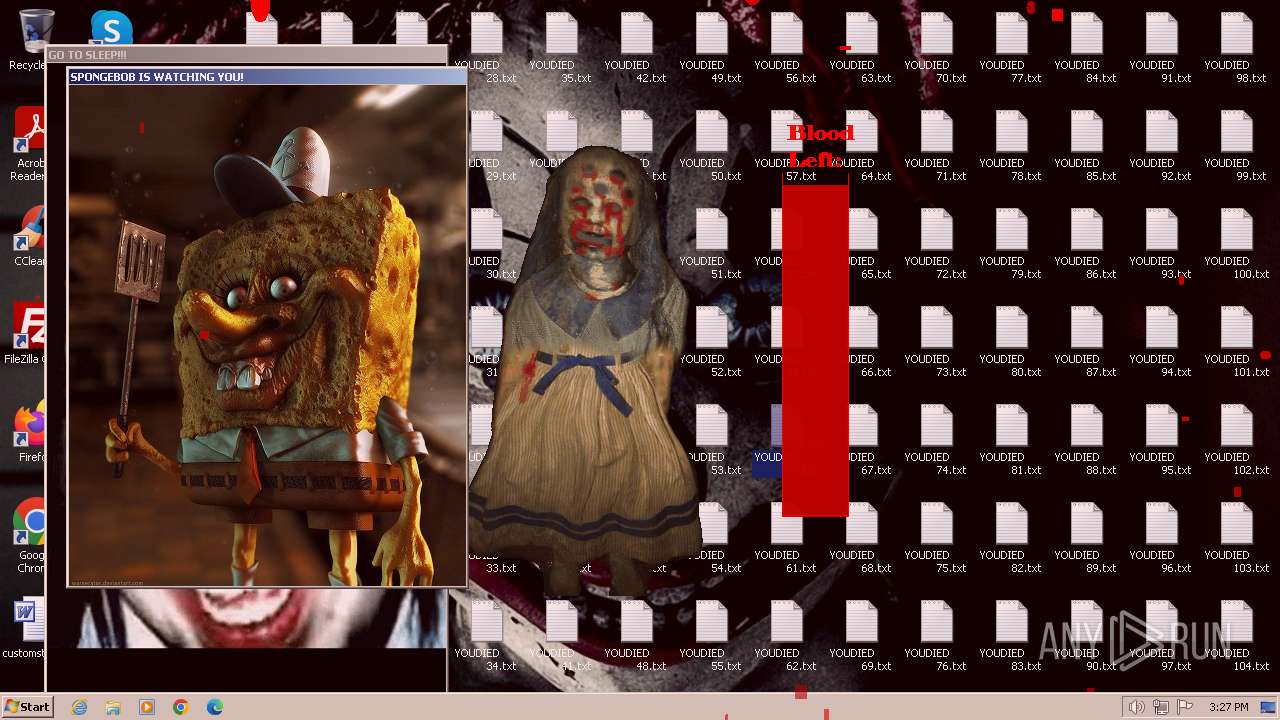
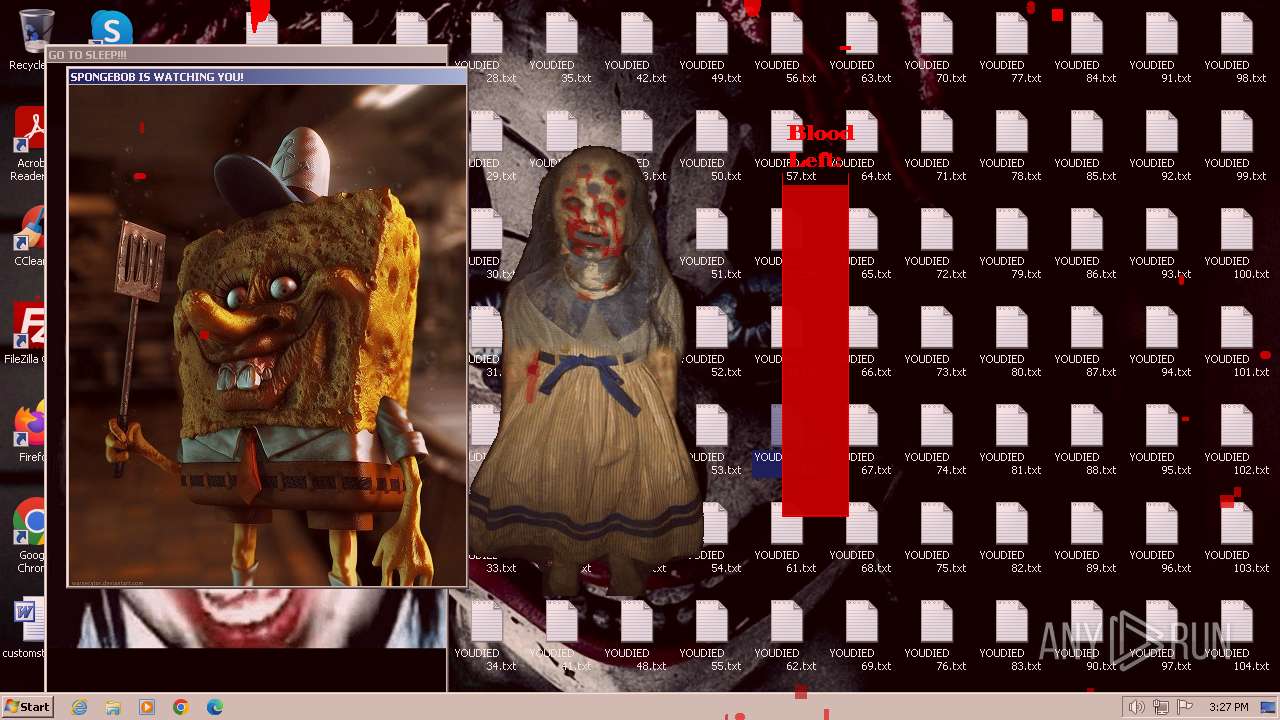
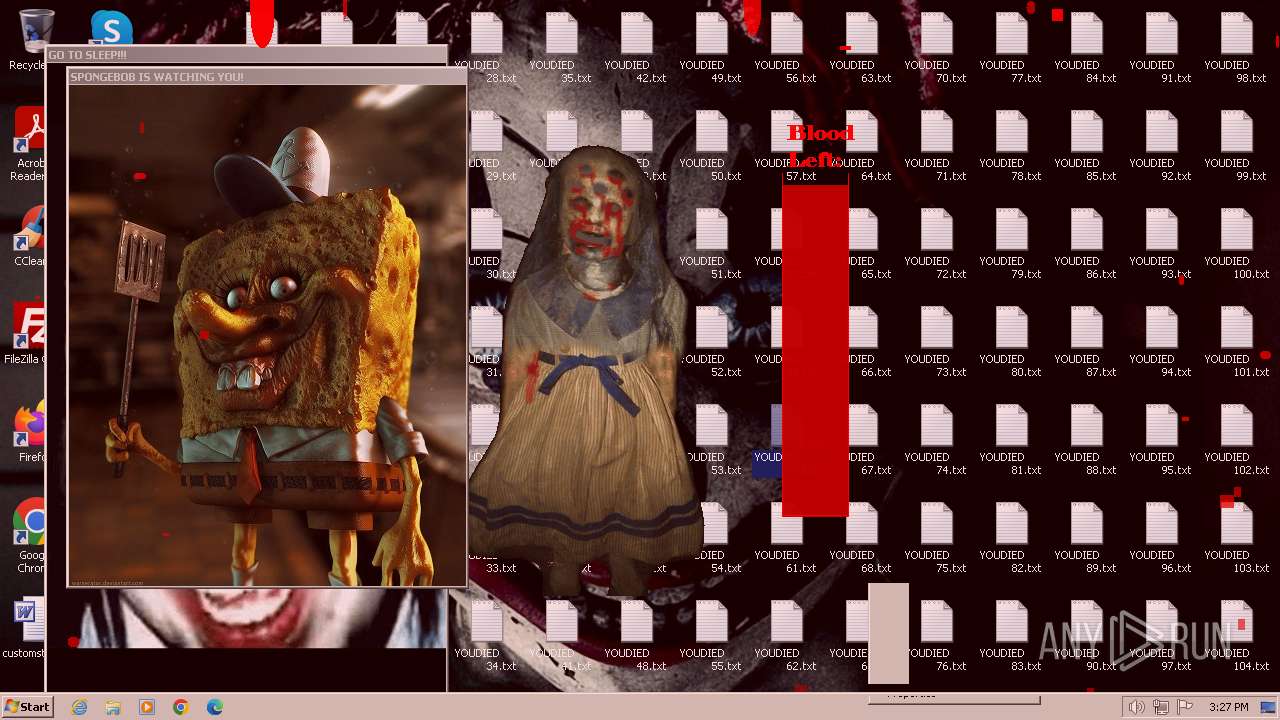
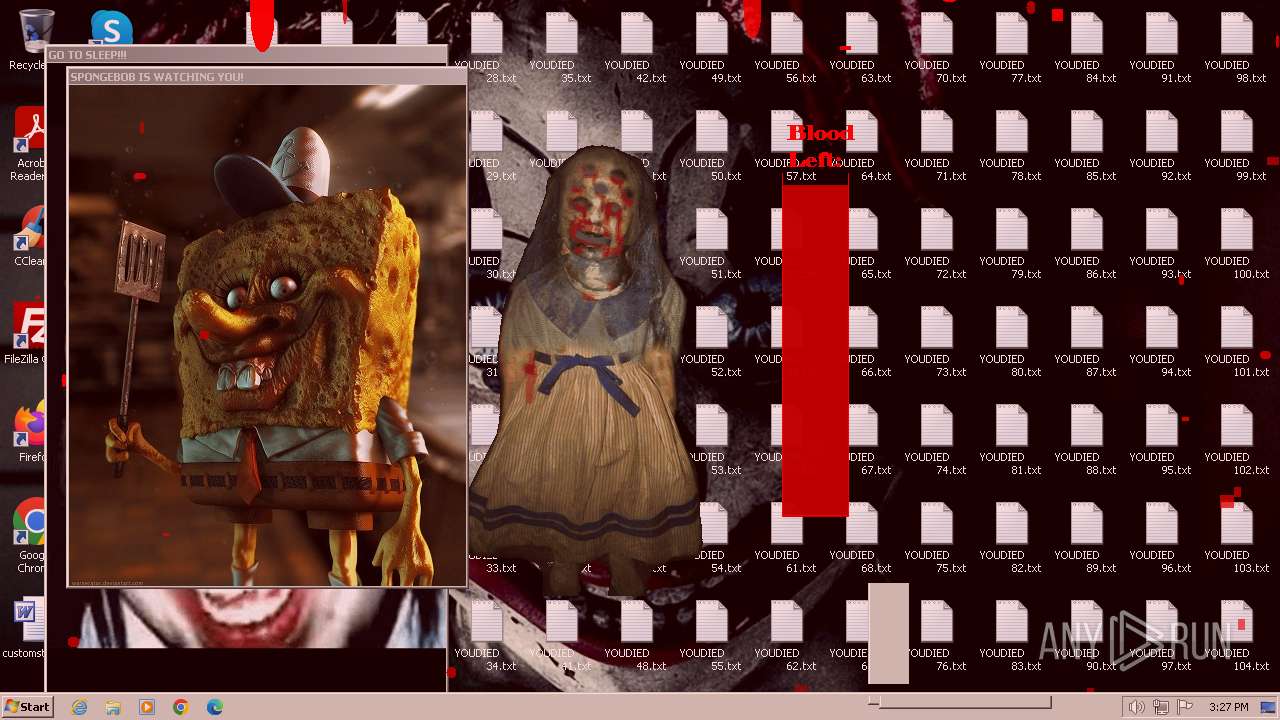
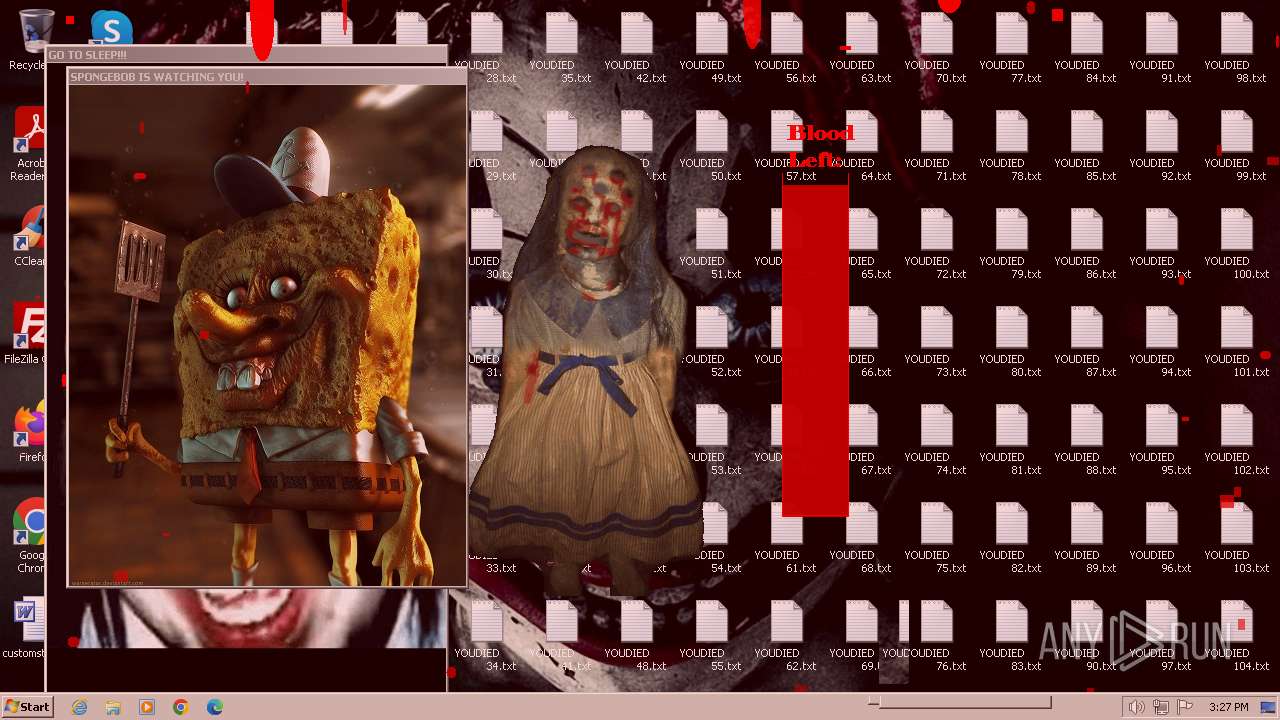
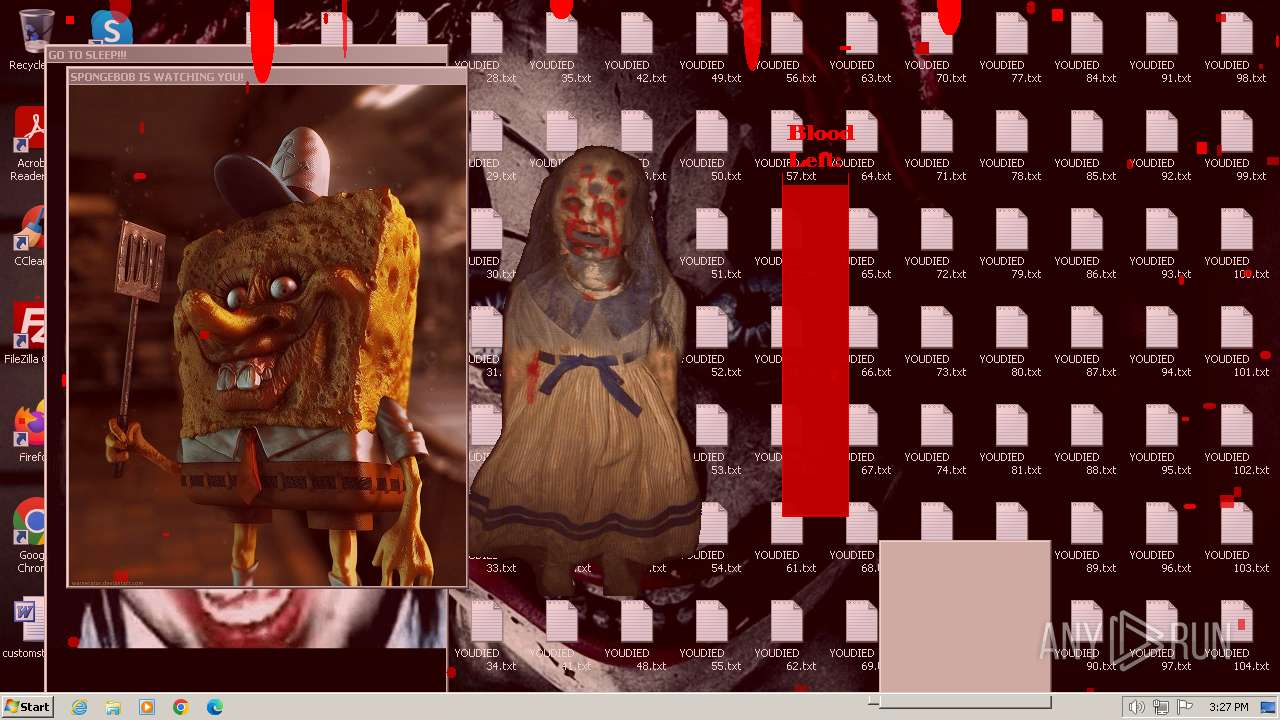
Changes the desktop background image
- reg.exe (PID: 3516)
Creates or modifies Windows services
- gdifuncs.exe (PID: 2660)
INFO
Checks supported languages
- ROP2.exe (PID: 2892)
- mbr.exe (PID: 1824)
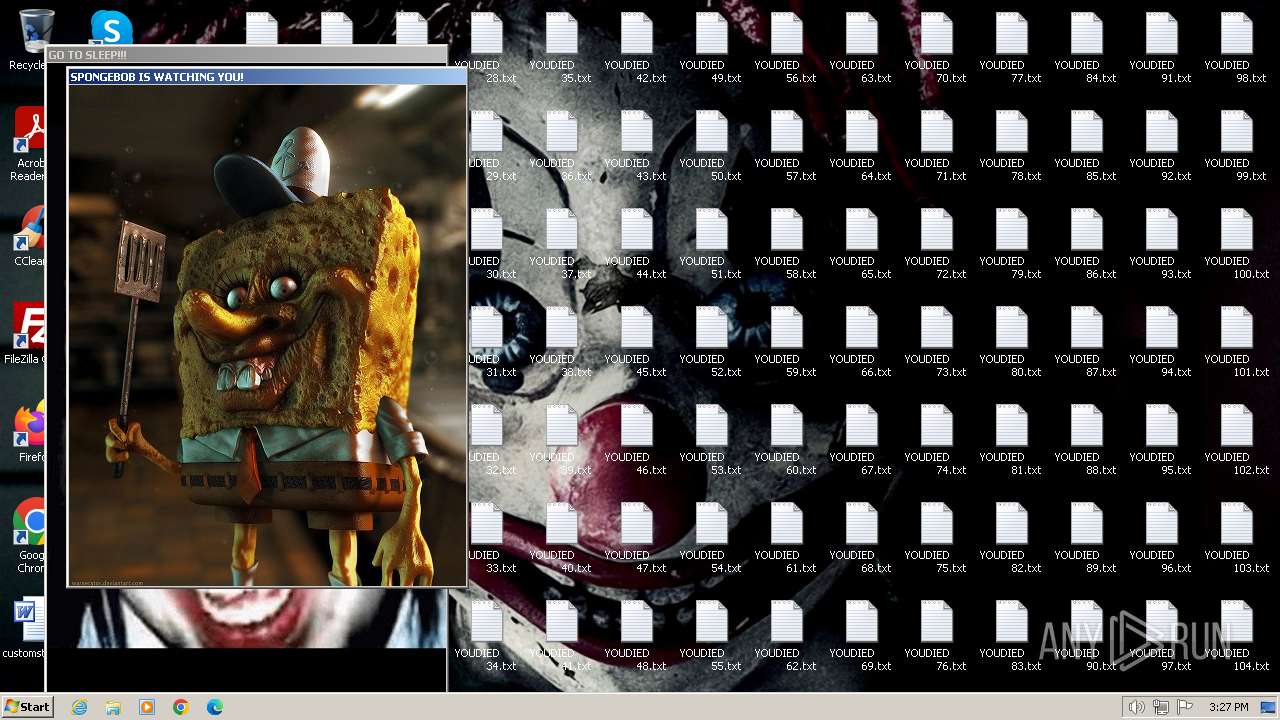
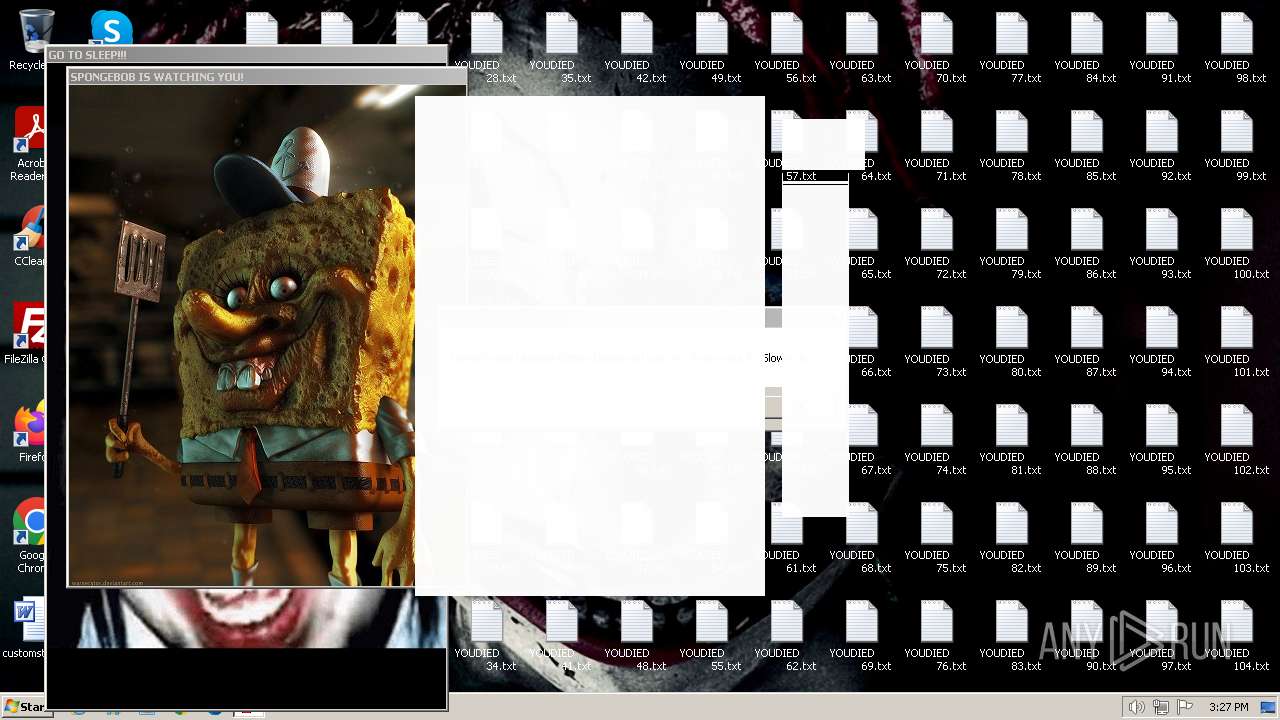
- bobcreep.exe (PID: 2620)
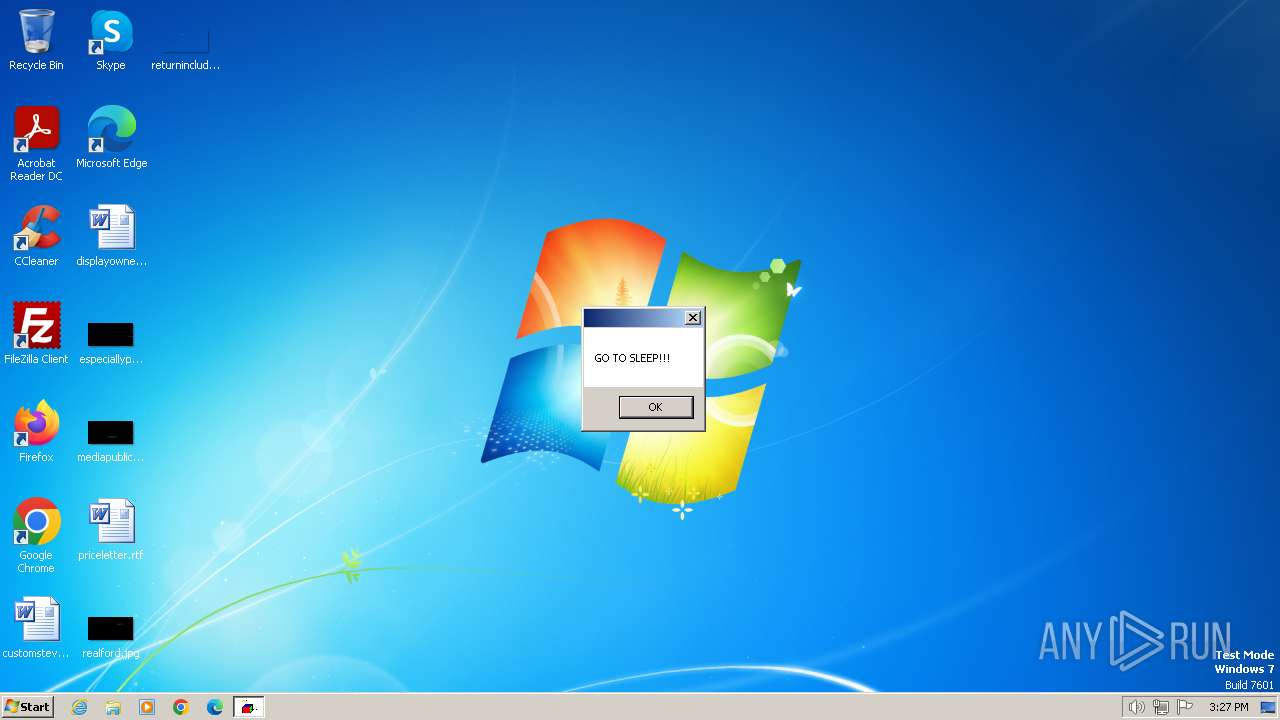
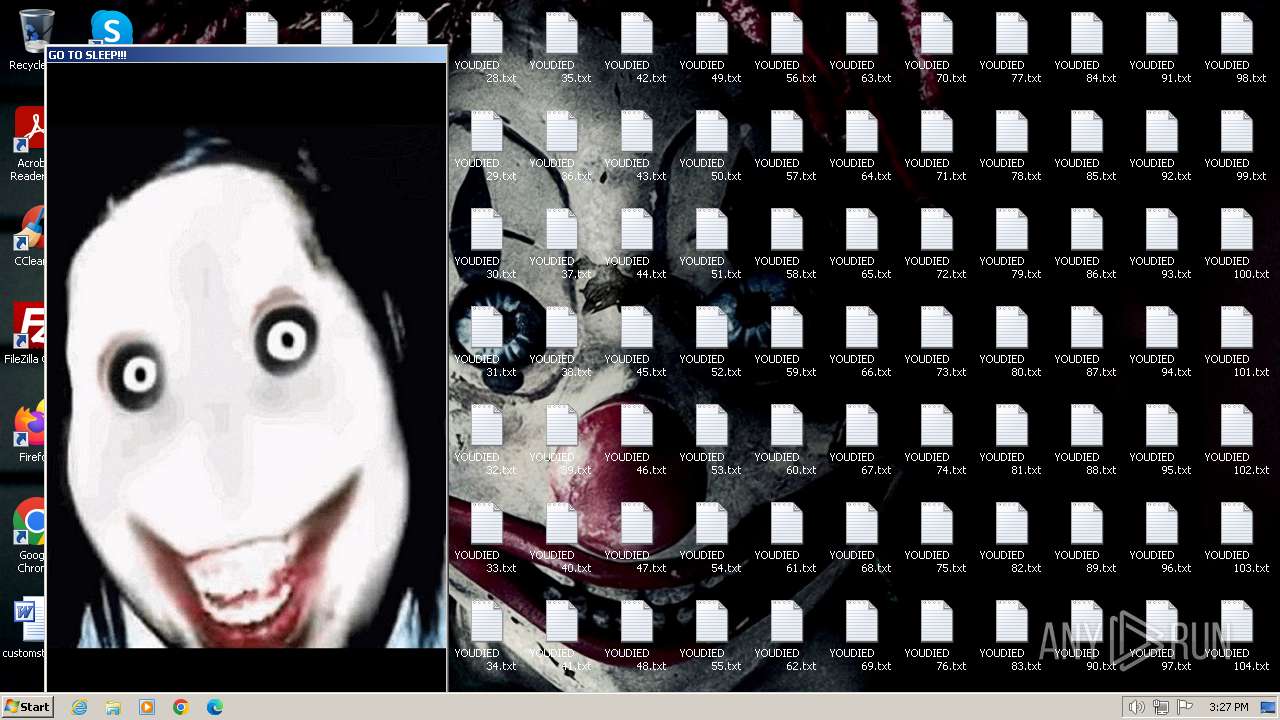
- jeffpopup.exe (PID: 3444)
- gdifuncs.exe (PID: 2660)
Create files in a temporary directory
- ROP2.exe (PID: 2892)
Reads the computer name
- ROP2.exe (PID: 2892)
- gdifuncs.exe (PID: 2660)
Reads the machine GUID from the registry
- gdifuncs.exe (PID: 2660)
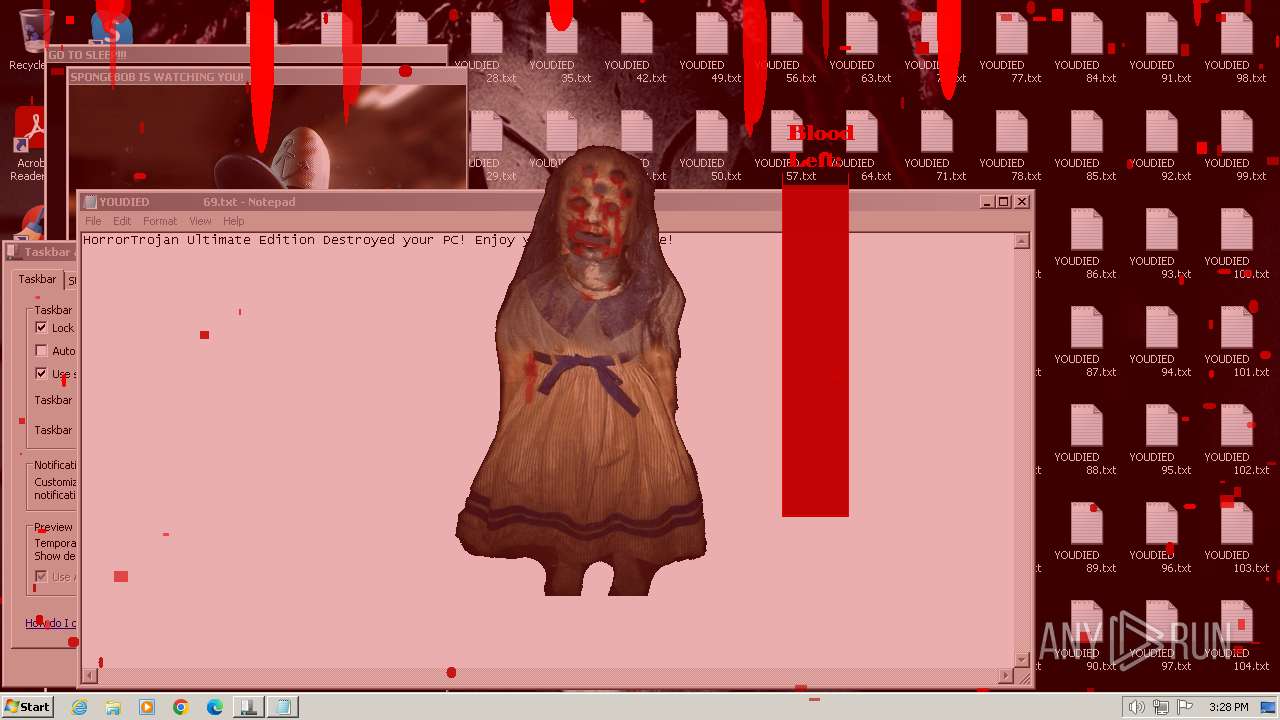
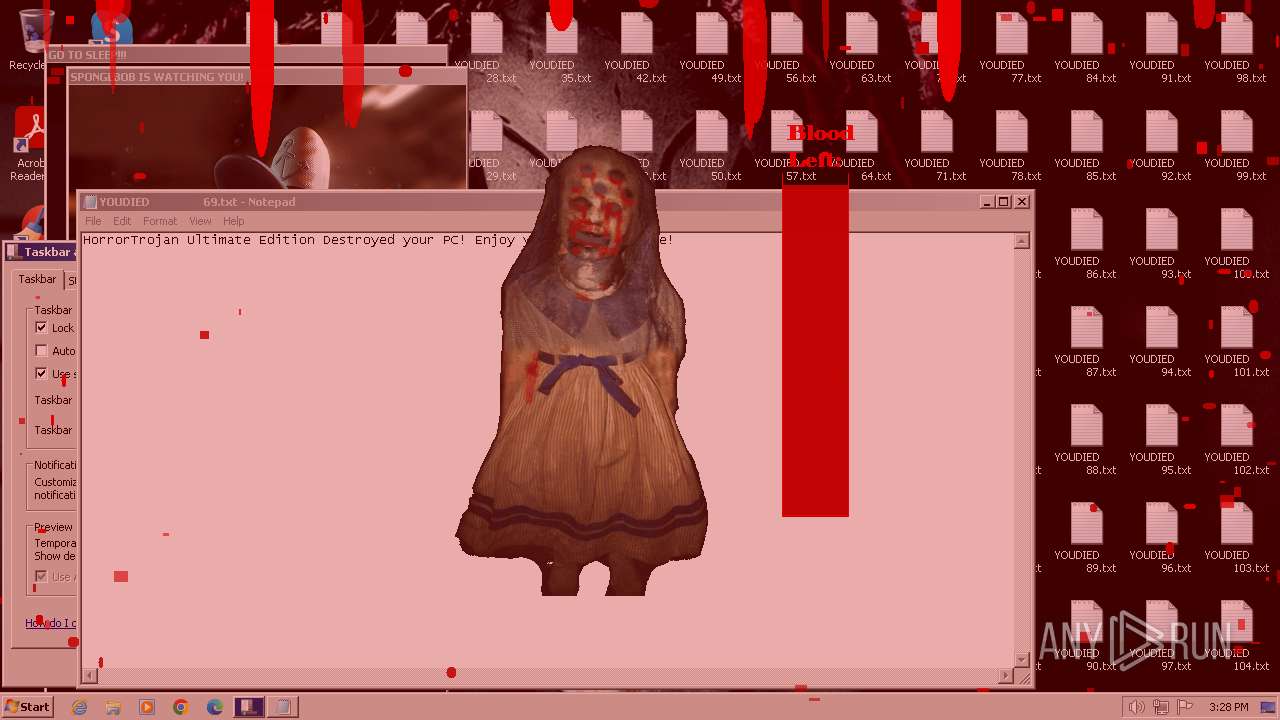
Manual execution by a user
- notepad.exe (PID: 2616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 20:46:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 66048 |
| InitializedDataSize: | 15667200 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.6.6.6 |
| ProductVersionNumber: | 6.6.6.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 6.6.6.6 |
| ProductVersion: | 6.6.6.6 |
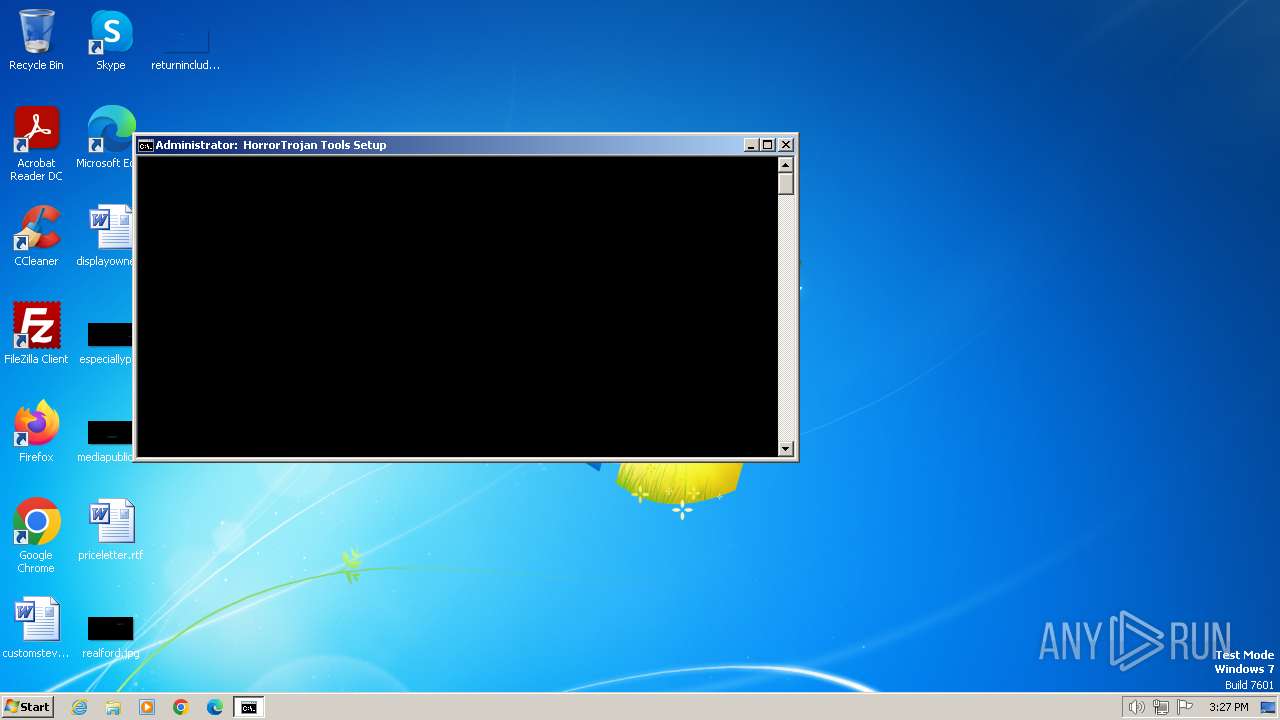
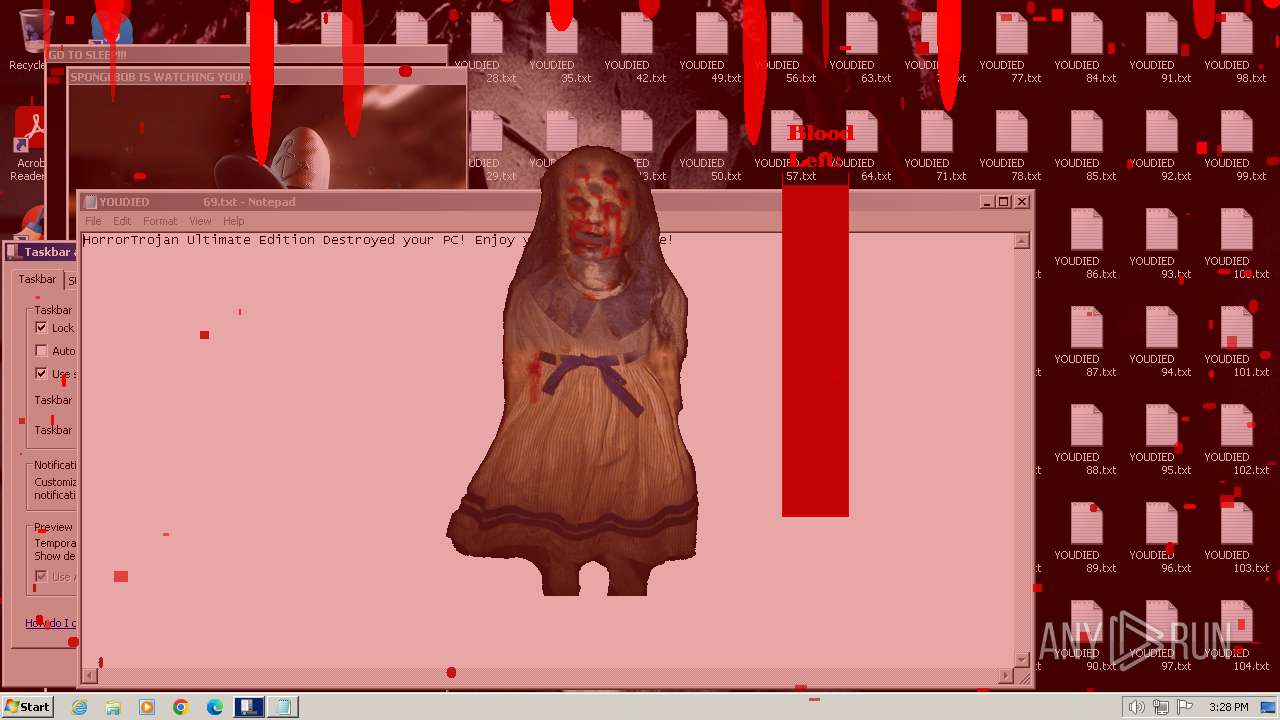
| FileDescription: | HorrorTrojan Ultimate Edition Destructive |
| CompanyName: | HorrorTrojans (pankoza) |
Total processes
85
Monitored processes
45
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 696 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\2E8D.tmp\tools.cmd" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 748 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1368 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1644 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1656 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 800
Read events
6 563
Write events
237
Delete events
0
Modification events
| (PID) Process: | (2892) ROP2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2892) ROP2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2892) ROP2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2892) ROP2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2908) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2908) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2908) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2908) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3516) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: c:\bg.bmp | |||
| (PID) Process: | (2660) gdifuncs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe, wscript.exe "C:\windows\winbase_base_procid_none\secureloc0x65\WinRapistI386.vbs" | |||
Executable files
5
Suspicious files
0
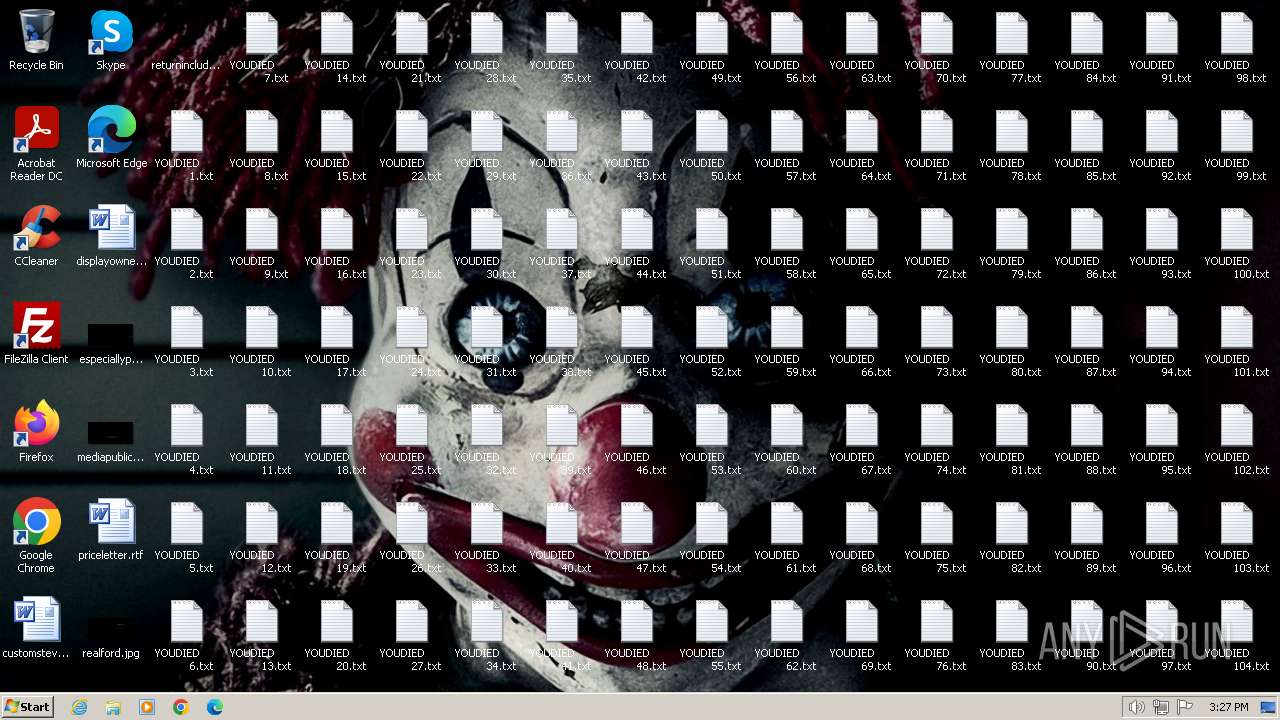
Text files
202
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\2E8E.tmp\2E8F.vbs | binary | |
MD5:— | SHA256:— | |||
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\bg.bmp | — | |
MD5:— | SHA256:— | |||
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\bobcreep.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\gdifuncs.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\jeffpopup.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\mainbgtheme.wav | — | |
MD5:— | SHA256:— | |||
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\mbr.cpp | text | |
MD5:— | SHA256:— | |||
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\mbr.exe | executable | |
MD5:— | SHA256:— | |||
| 2892 | ROP2.exe | C:\Users\admin\AppData\Local\Temp\2E8D.tmp\tools.cmd | text | |
MD5:— | SHA256:— | |||
| 2908 | wscript.exe | C:\Users\admin\Desktop\YOUDIED 1.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |