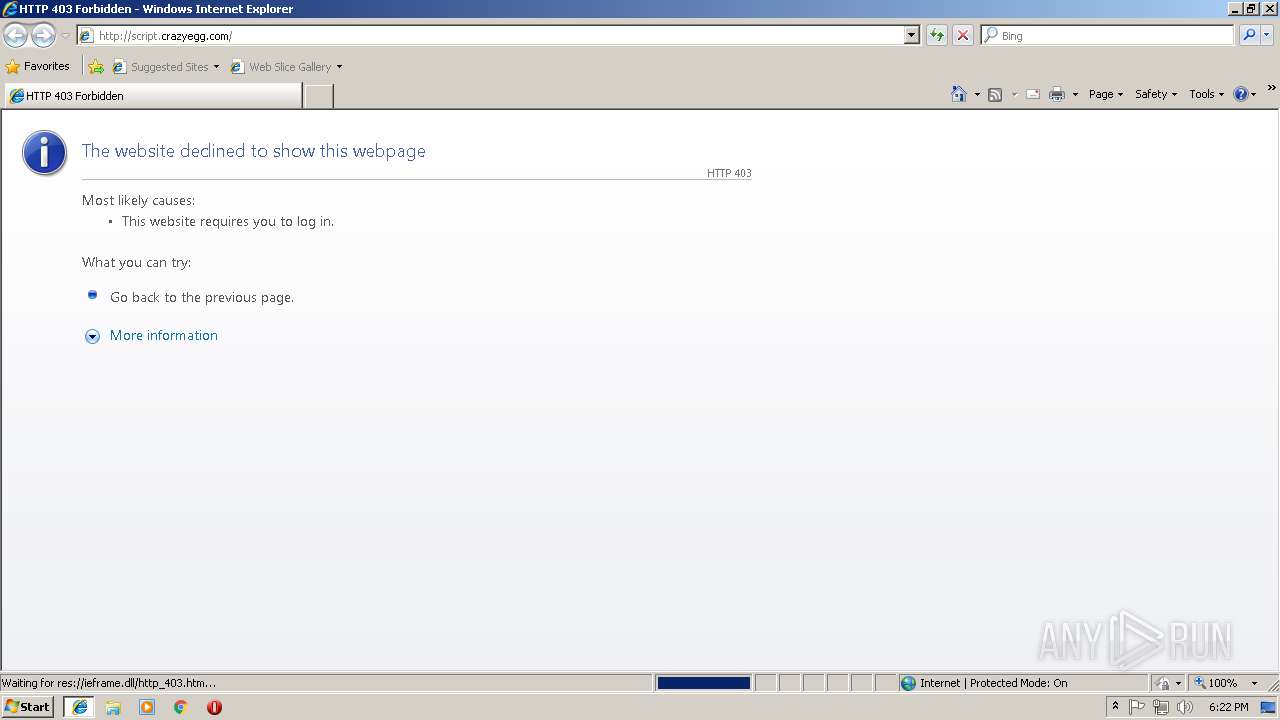
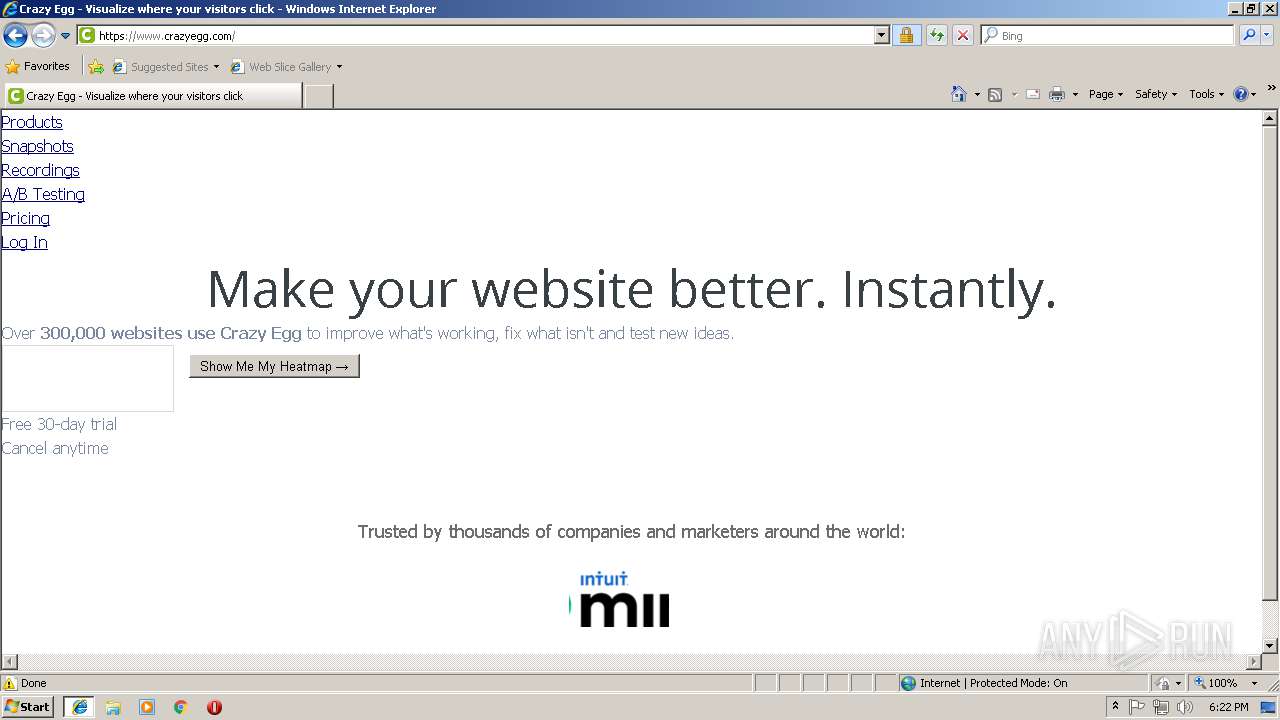
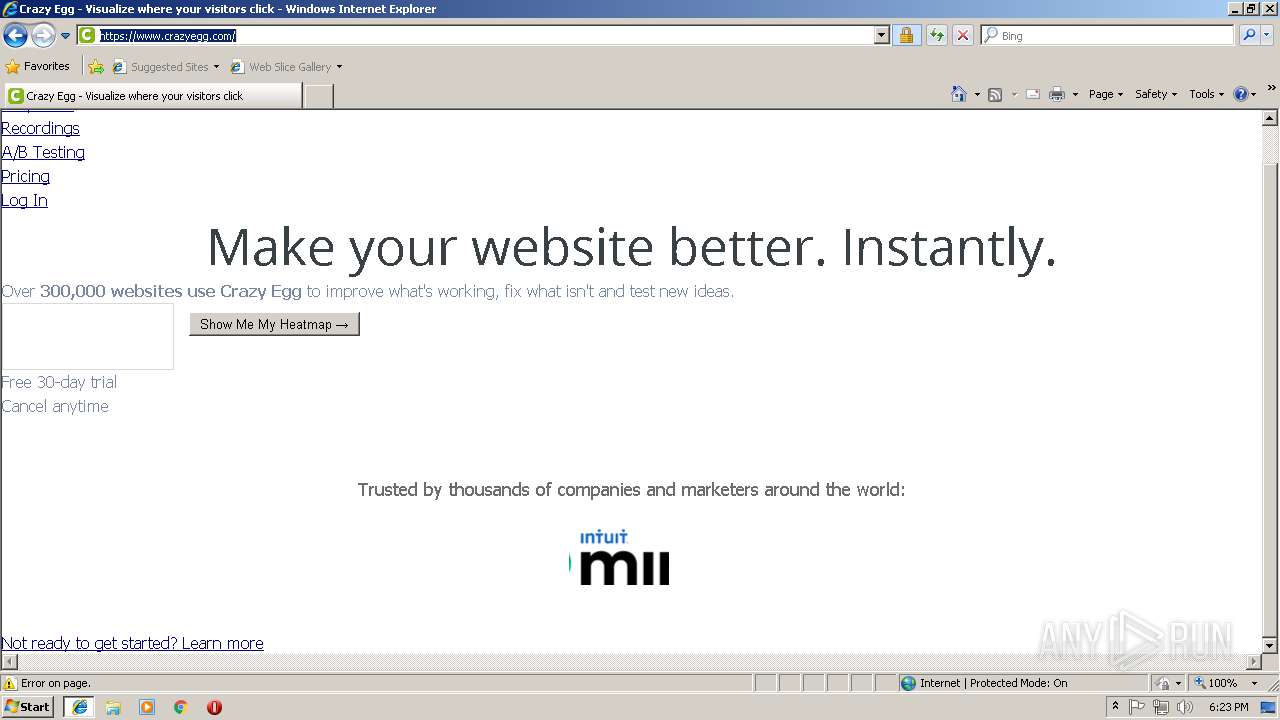
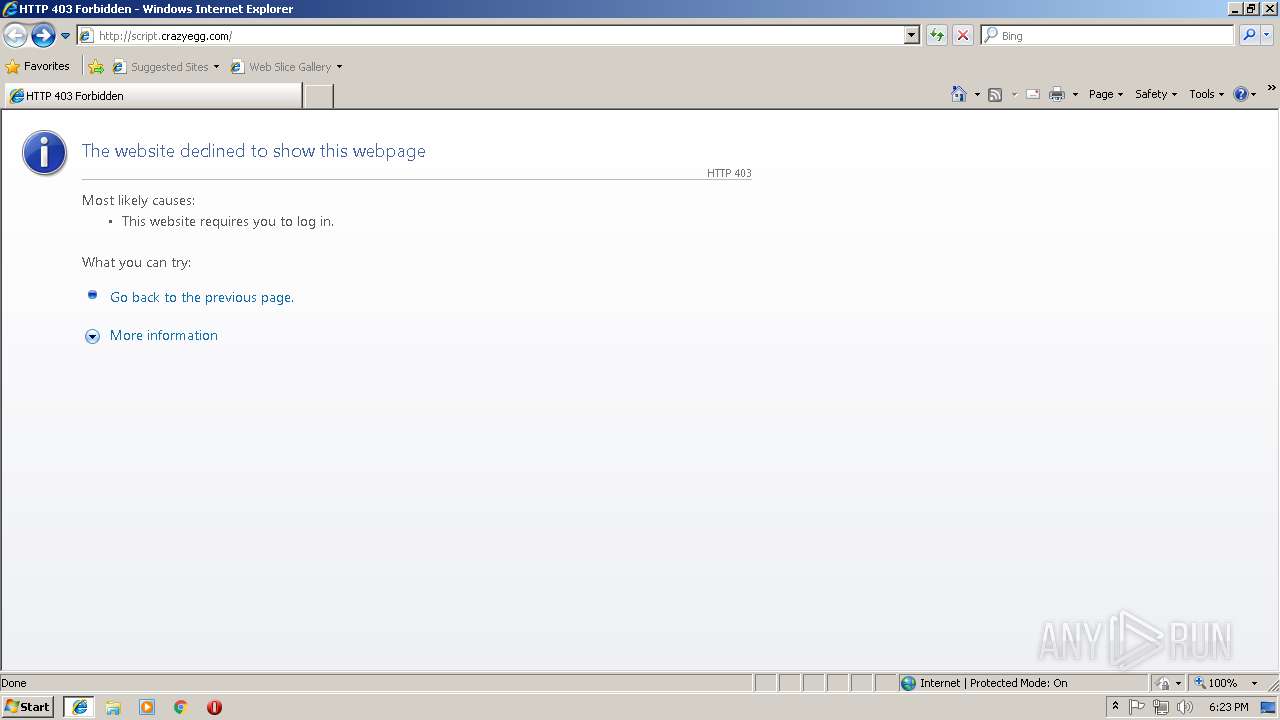
| URL: | http://script.crazyegg.com |
| Full analysis: | https://app.any.run/tasks/76dbc37c-d8e1-4423-a3be-053bca4b1b6f |
| Verdict: | Suspicious activity |
| Analysis date: | September 12, 2018, 17:22:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3381C3383BD1E7899EEDAE8F318B573C |
| SHA1: | 8E6E424D8314E7C3F32DAA99AC783C8F291CA05E |
| SHA256: | FC6DEEF8CC5311BBFCAA3B33A88C947341FA0D9244E0ACC9954D58C925FA2466 |
| SSDEEP: | 3:N1KNGYtfcACC2:CUYt0n |
MALICIOUS
Loads dropped or rewritten executable
- software_reporter_tool.exe (PID: 1836)
SUSPICIOUS
Executable content was dropped or overwritten
- software_reporter_tool.exe (PID: 1836)
Application launched itself
- software_reporter_tool.exe (PID: 1336)
- software_reporter_tool.exe (PID: 2540)
Searches for installed software
- software_reporter_tool.exe (PID: 1836)
INFO
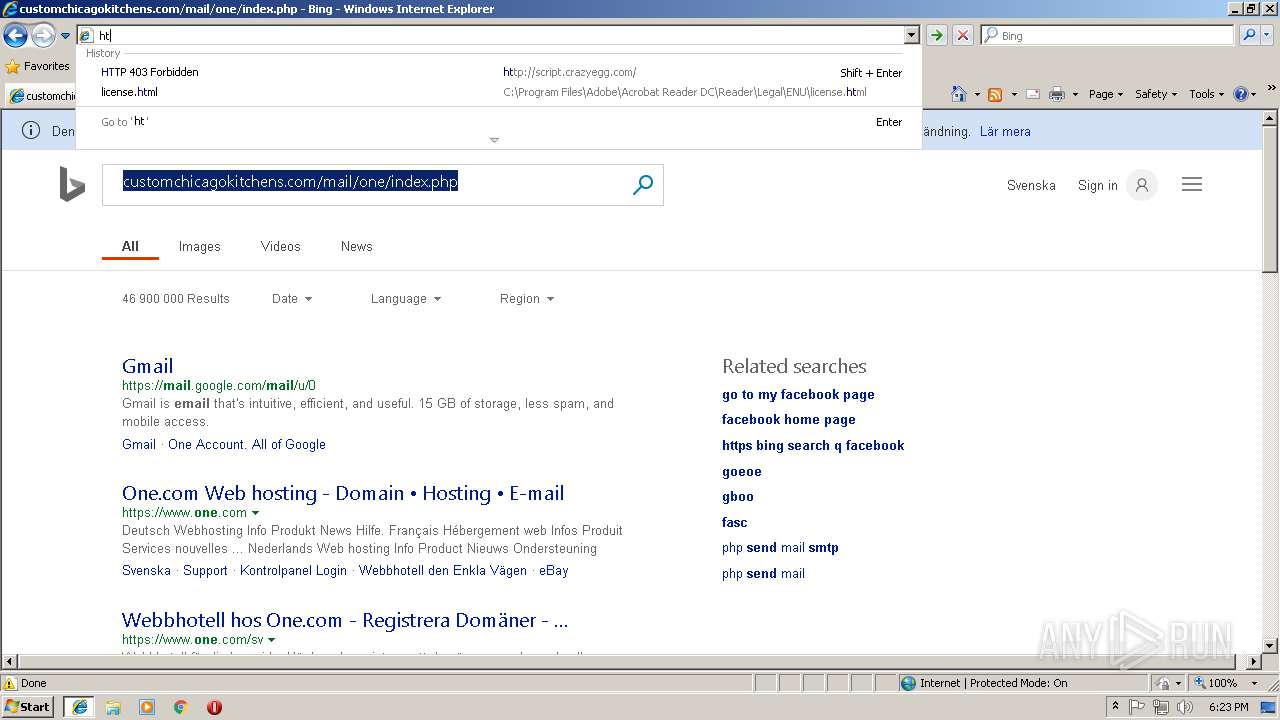
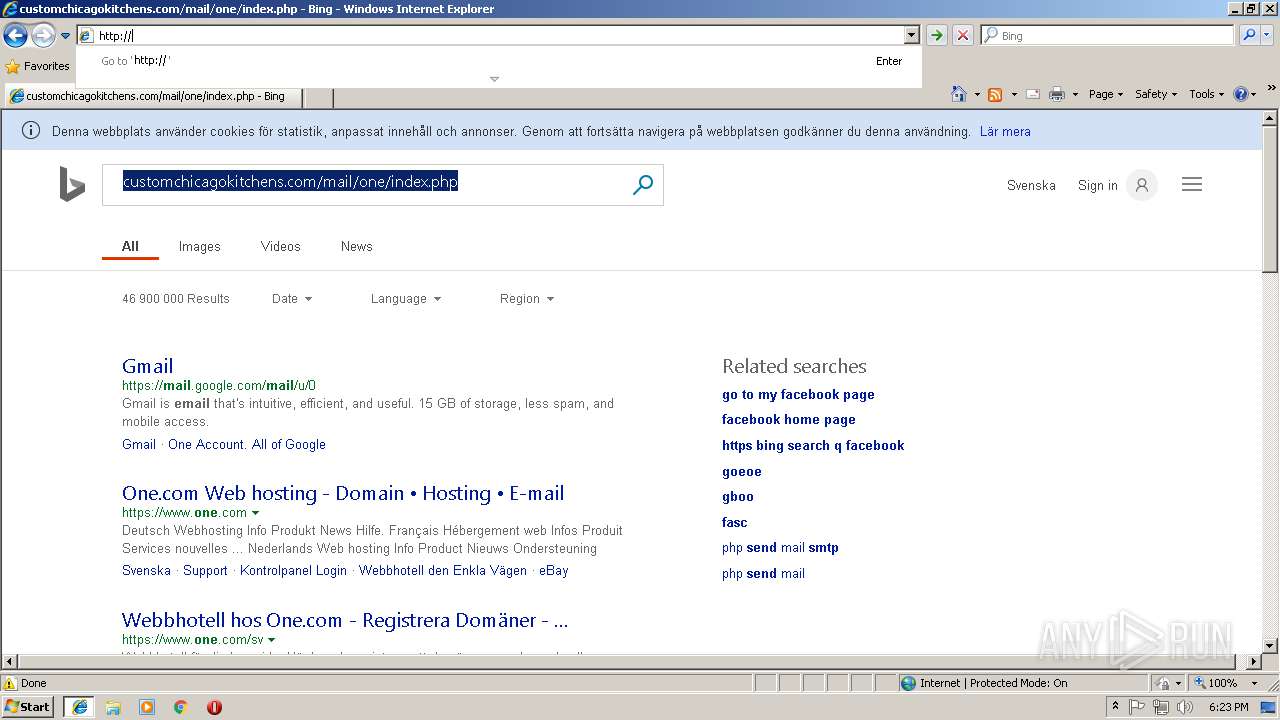
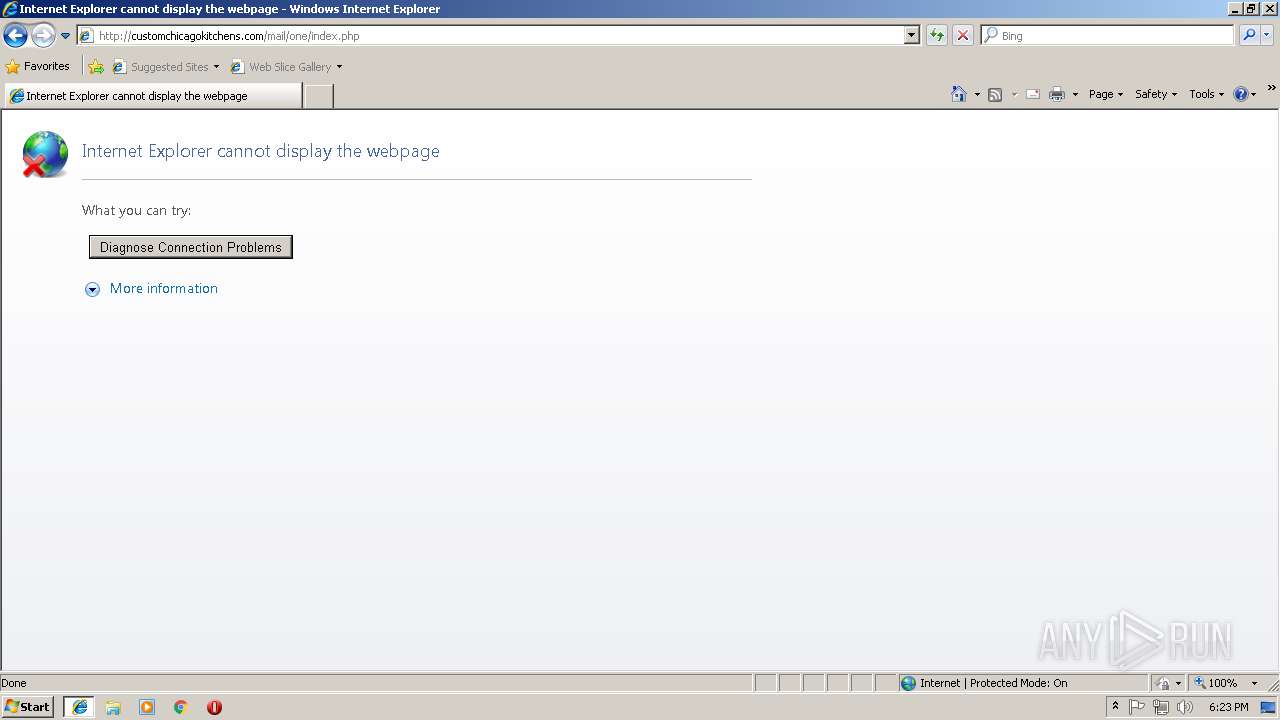
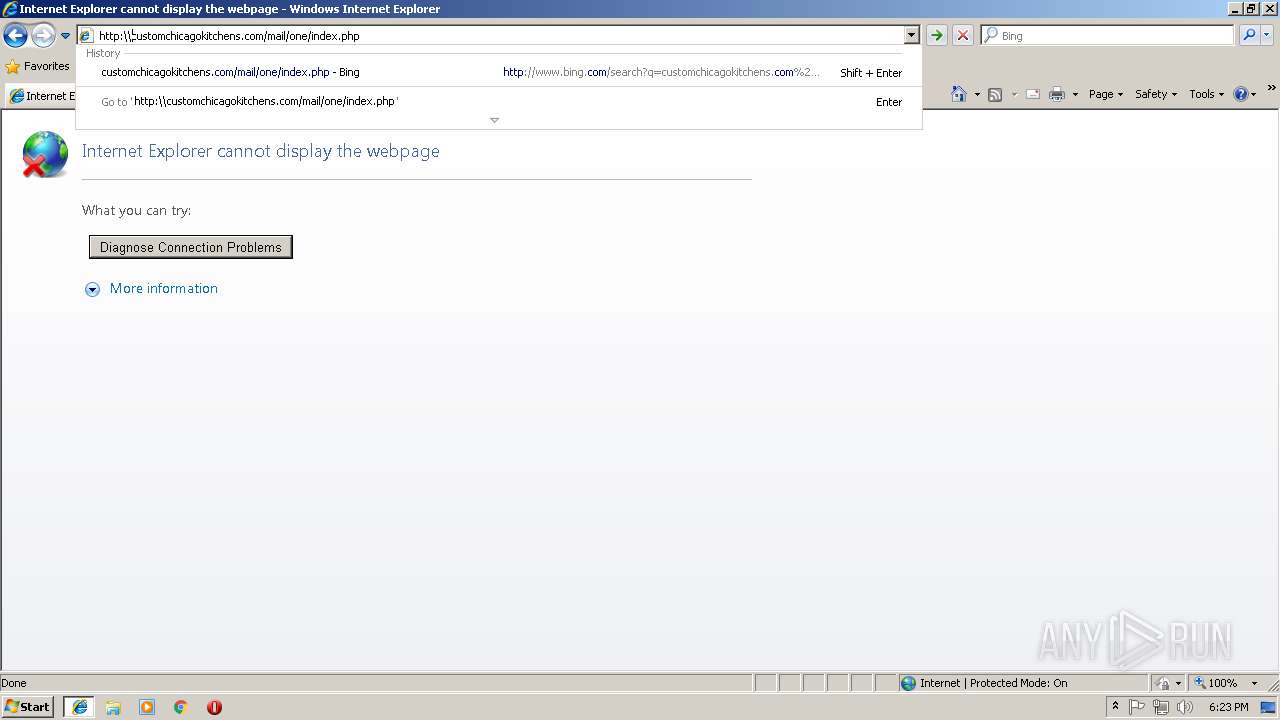
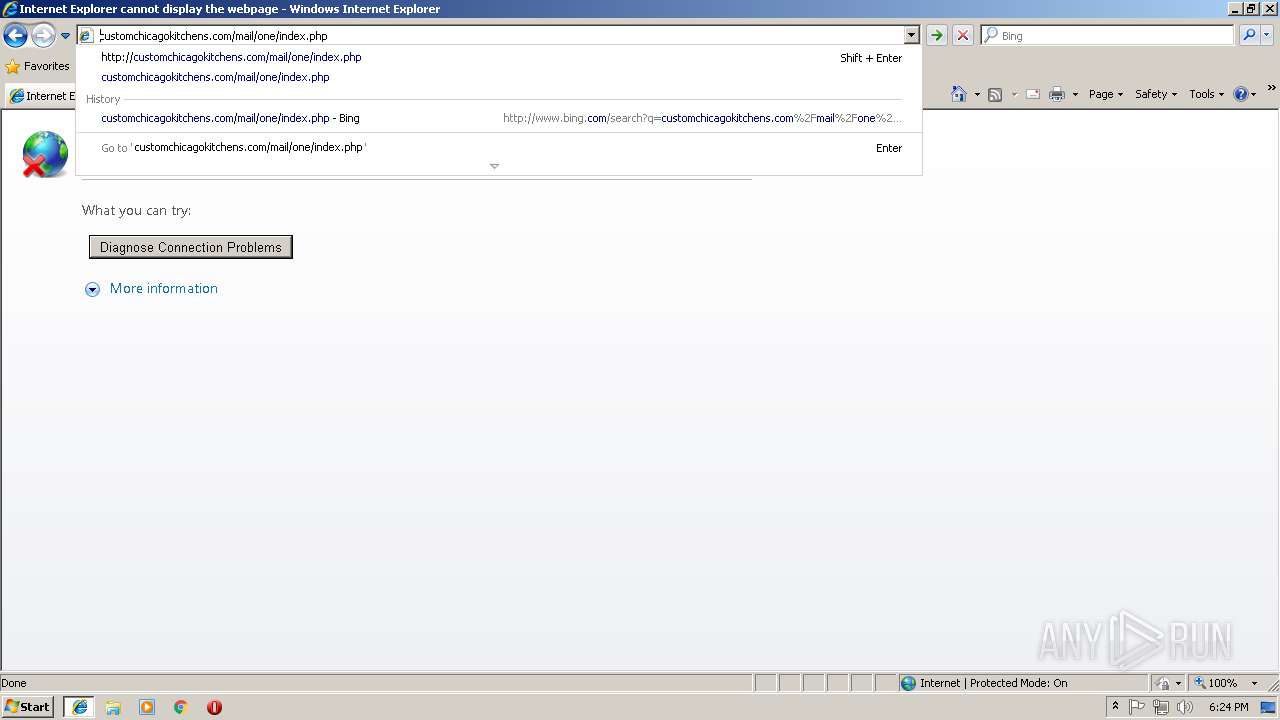
Reads internet explorer settings
- iexplore.exe (PID: 384)
Reads settings of System Certificates
- iexplore.exe (PID: 504)
- chrome.exe (PID: 2696)
Changes internet zones settings
- iexplore.exe (PID: 504)
Reads Internet Cache Settings
- iexplore.exe (PID: 384)
Creates files in the user directory
- iexplore.exe (PID: 384)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 1336)
- software_reporter_tool.exe (PID: 2540)
Application launched itself
- chrome.exe (PID: 2696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
26
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,3714814882143961386,7118574184173306221,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=EAE0635D2F52D9D4FA6C08AA0981AEC7 --mojo-platform-channel-handle=4248 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,3714814882143961386,7118574184173306221,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=CA09787FF60C4FF125DD7D255F47F1CA --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CA09787FF60C4FF125DD7D255F47F1CA --renderer-client-id=14 --mojo-platform-channel-handle=4760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 384 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:504 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 504 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | "C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\33.170.201\software_reporter_tool.exe" --session-id=PdECwCh1JlLfEv1dsYupRURZ/ty1MVFKHXHKfpFv --registry-suffix=URZA --srt-field-trial-group-name=NewCleanerUIExperiment | C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\33.170.201\software_reporter_tool.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 2 Version: 33.170.201 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,3714814882143961386,7118574184173306221,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=0D772D71F612CDD956A04A5935573B97 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0D772D71F612CDD956A04A5935573B97 --renderer-client-id=12 --mojo-platform-channel-handle=4376 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,3714814882143961386,7118574184173306221,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=F2EBC837DC765477777FD9C2653CE0C5 --mojo-platform-channel-handle=3276 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,3714814882143961386,7118574184173306221,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2D394A366EDE4A9DCD2A73C52746BD9B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2D394A366EDE4A9DCD2A73C52746BD9B --renderer-client-id=11 --mojo-platform-channel-handle=4052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1836 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe" --use-crash-handler-with-id="\\.\pipe\crashpad_2540_GWJVCMJSBTNFISYP" --sandboxed-process-id=2 --init-done-notifier=344 --sandbox-mojo-pipe-token=53858F87FCF2289A4AE5724A27D9D2B4 --mojo-platform-channel-handle=280 --engine=2 | c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe | software_reporter_tool.exe | ||||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 33.170.201 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,3714814882143961386,7118574184173306221,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=95AA76026A06842EB0CCCB069BB30427 --mojo-platform-channel-handle=2740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 706
Read events
1 364
Write events
321
Delete events
21
Modification events
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {6F9B0F97-B6B0-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207090003000C001100160023003600 | |||
Executable files
7
Suspicious files
45
Text files
168
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
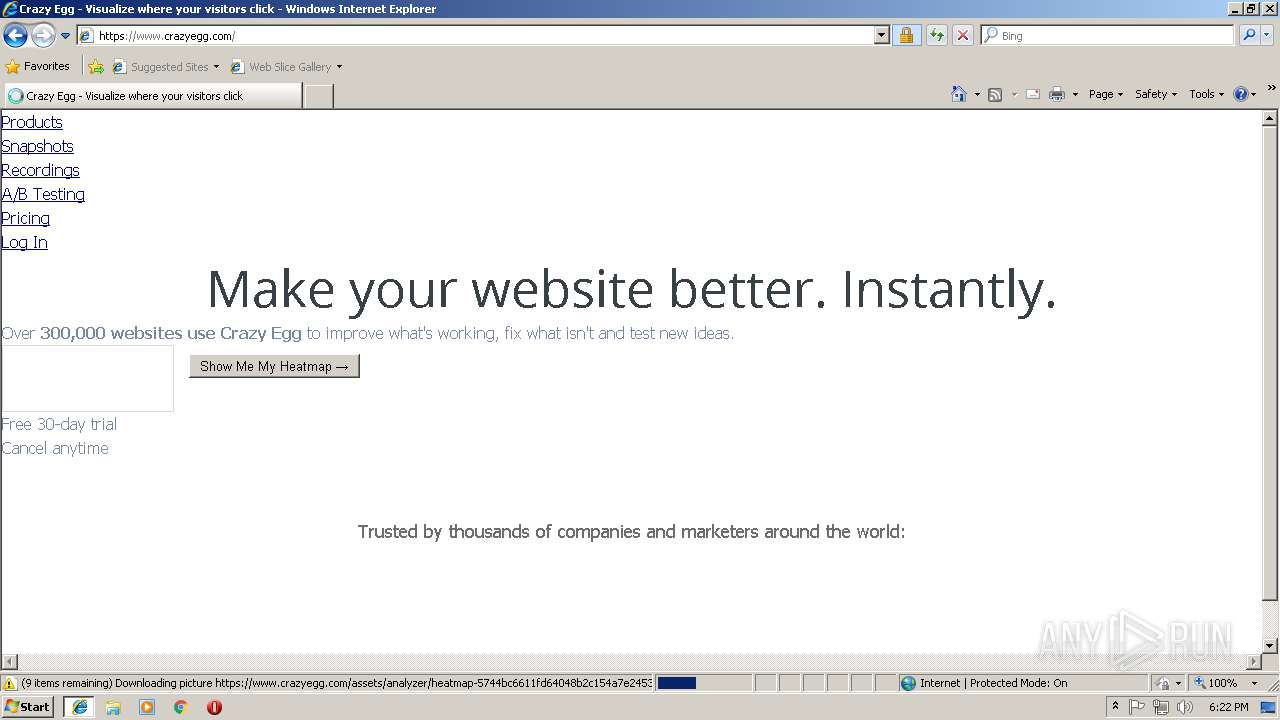
| 384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\crazyegg_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\api[1].js | text | |
MD5:— | SHA256:— | |||
| 384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\crazyegg_com[1].htm | html | |
MD5:— | SHA256:— | |||
| 384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\application-524176fa169751ecfefb060eadde31e141ec6bc4b6f3c8951dd6167242d0b6ce[1].css | text | |
MD5:— | SHA256:— | |||
| 384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\application-b263d862e7ab16e1cce9[1].js | text | |
MD5:— | SHA256:— | |||
| 384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\application-42d635d1c57d1ab9a00f13a44c6746408d6d5845c50cca43ee4146a6b6dbe840[1].js | text | |
MD5:— | SHA256:— | |||
| 384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\abtesting-507229f8be7985292eefcc9c80076e4f53a967f5aa969f06ec7d84ca04815093[1].png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
105
TCP/UDP connections
96
DNS requests
46
Threats
0
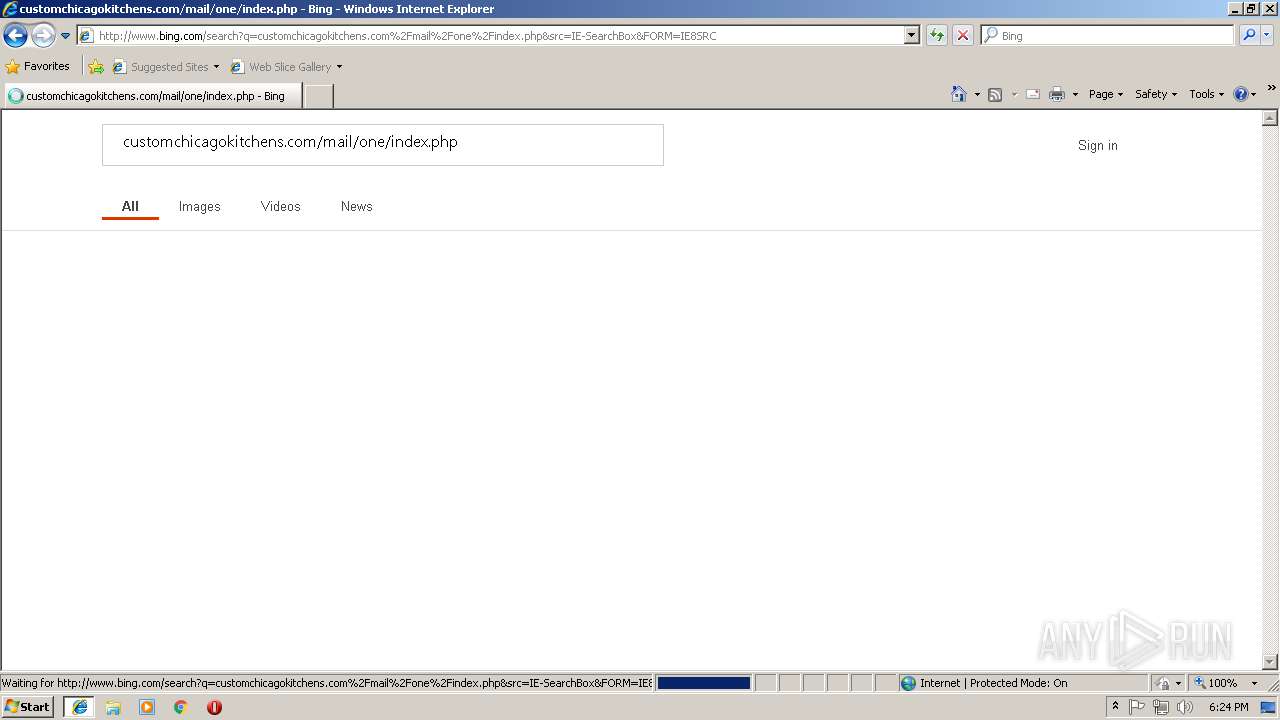
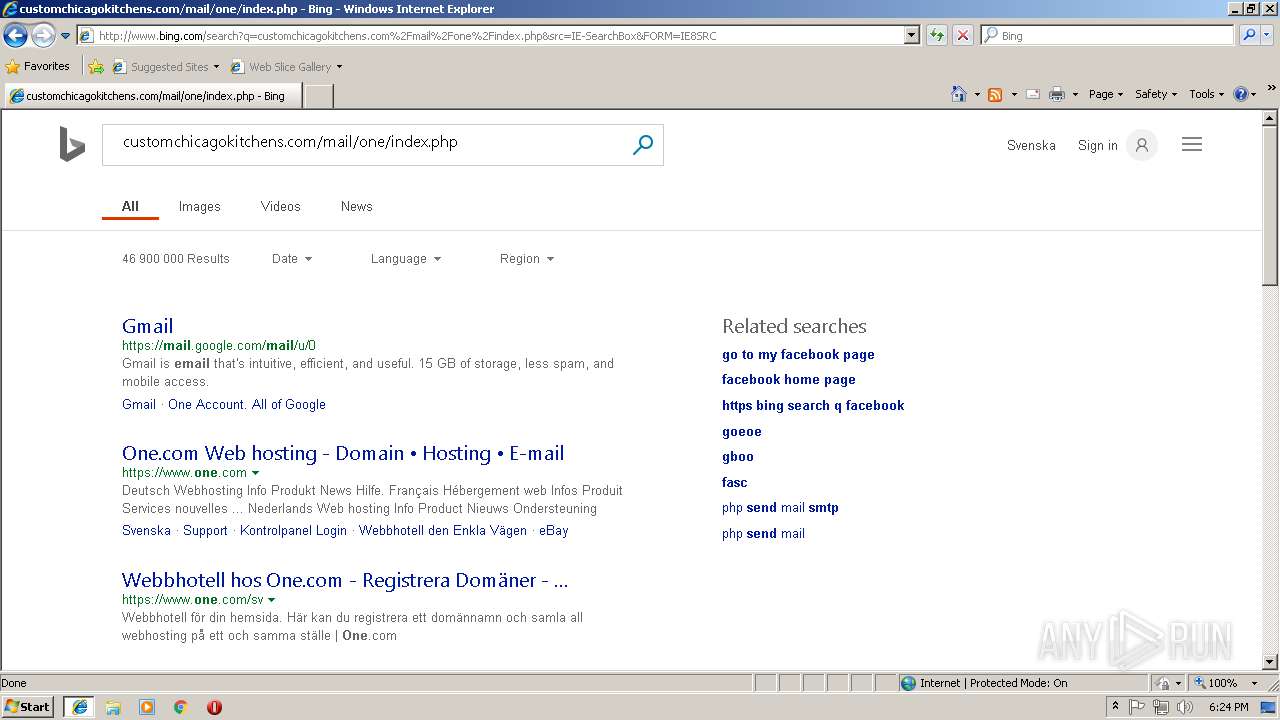
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
384 | iexplore.exe | GET | 403 | 143.204.93.232:80 | http://script.crazyegg.com/ | US | xml | 243 b | whitelisted |
384 | iexplore.exe | GET | 200 | 131.253.33.200:80 | http://www.bing.com/sa/simg/SharedSpriteDesktopRewards_022118.png | US | image | 5.73 Kb | whitelisted |
384 | iexplore.exe | GET | 200 | 131.253.33.200:80 | http://www.bing.com/fd/ls/l?IG=689907A51414459482F4895431DCB415&CID=0495151E5BCD64D43CFA19765A1265FC&Type=Event.ClientInst&DATA=[{"T":"CI.GetError","FID":"CI","Name":"JSGetError","Text":"Member%20not%20found.%0D%0A","Meta":"http%3A//www.bing.com/rb/12/cj%2Cnj/dfbe5368/a11e6044.js%3Fbu%3DDSkuWWltcWVdYaYBqgEumgE","Line":2,"Char":%20undefined}] | US | compressed | 837 b | whitelisted |
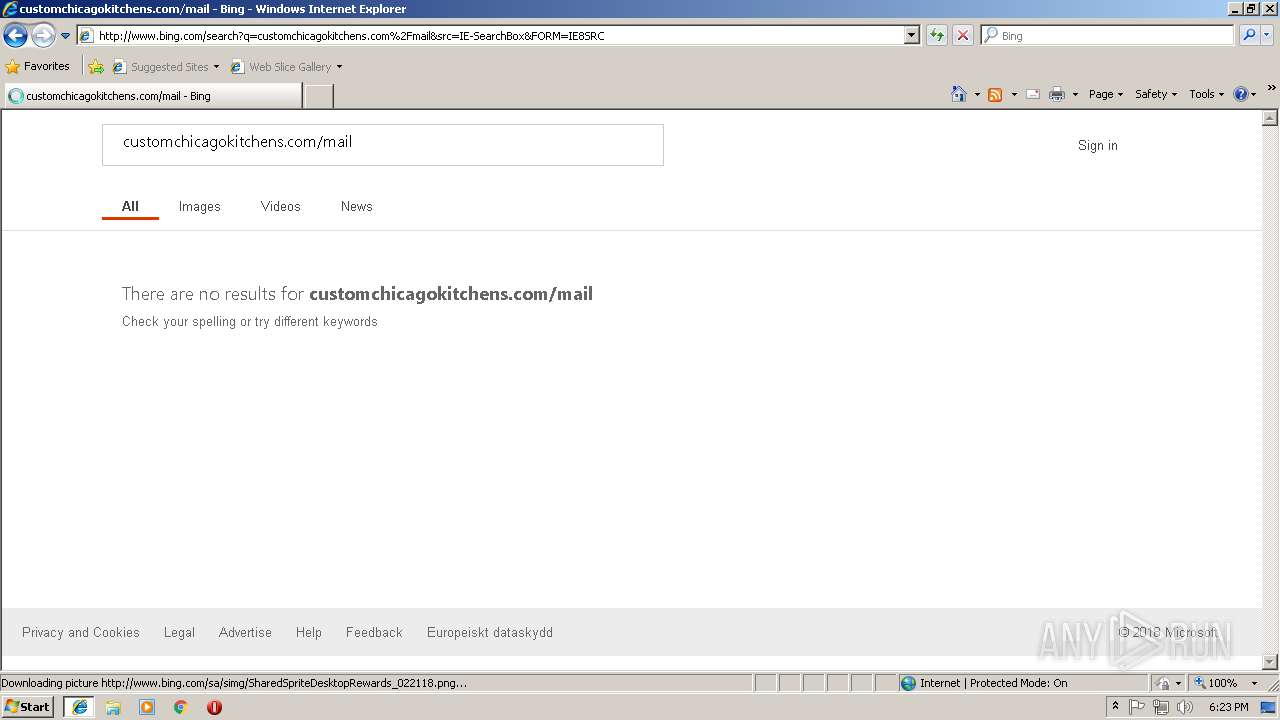
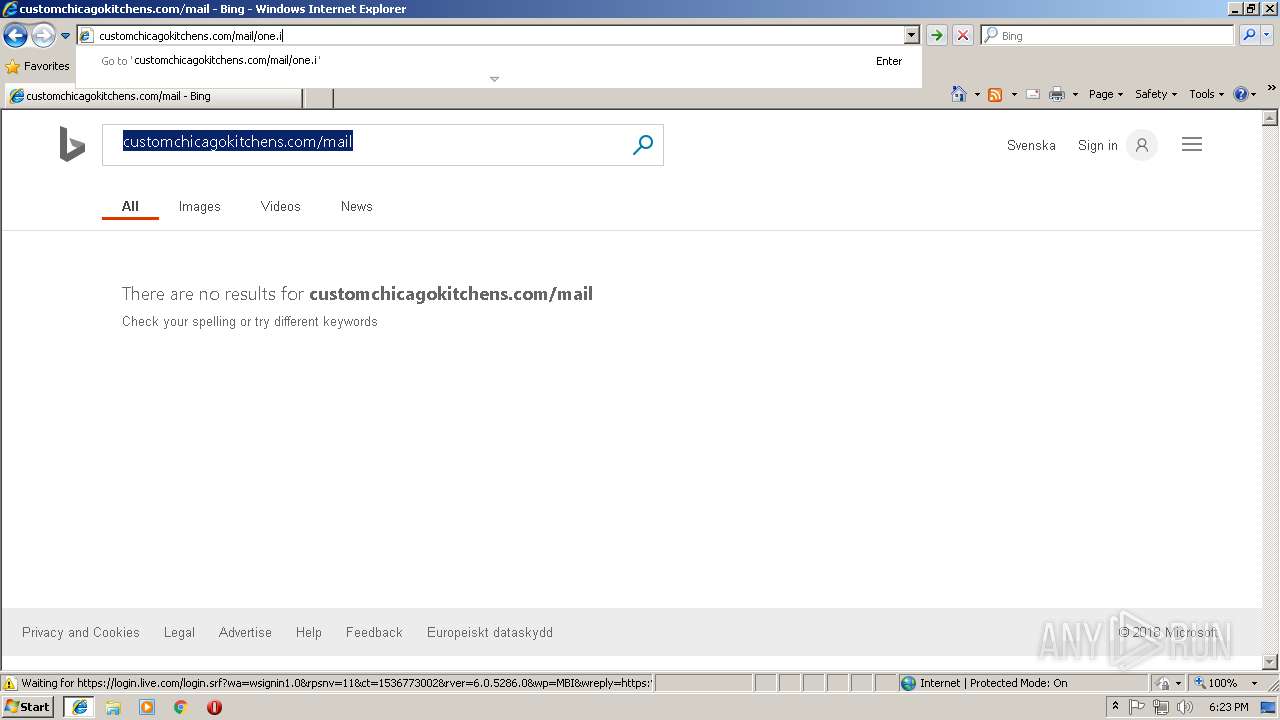
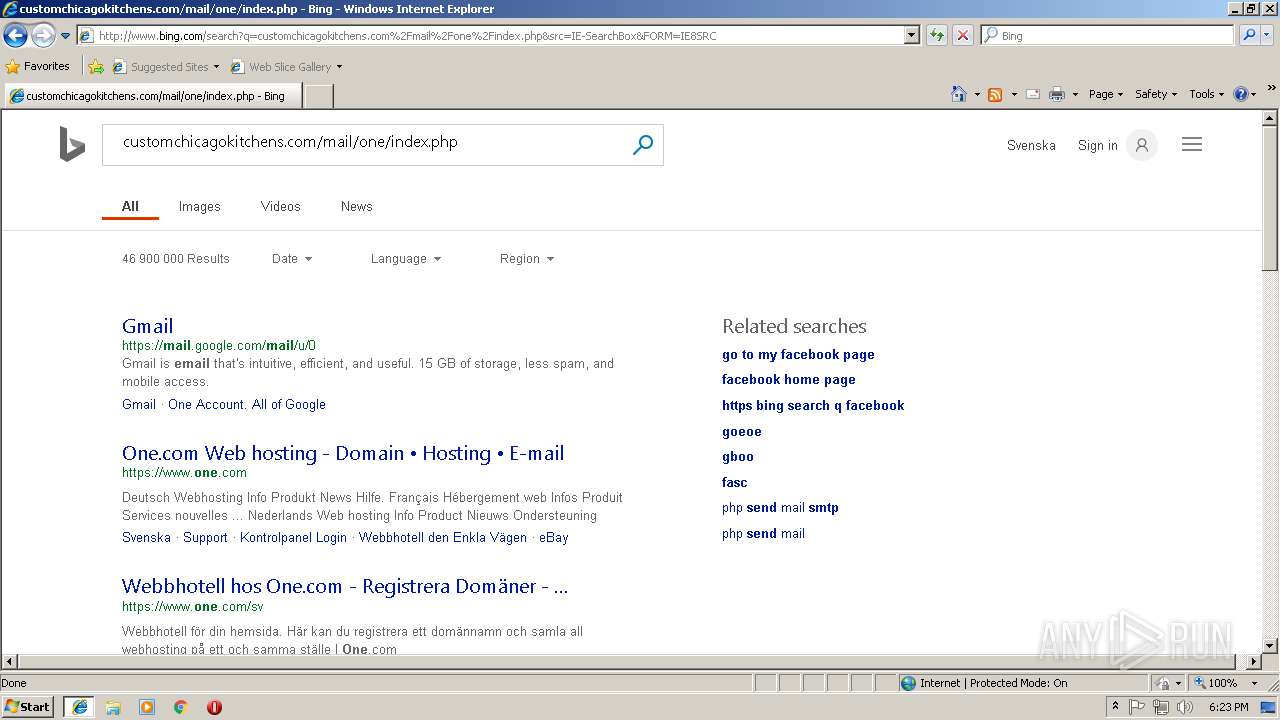
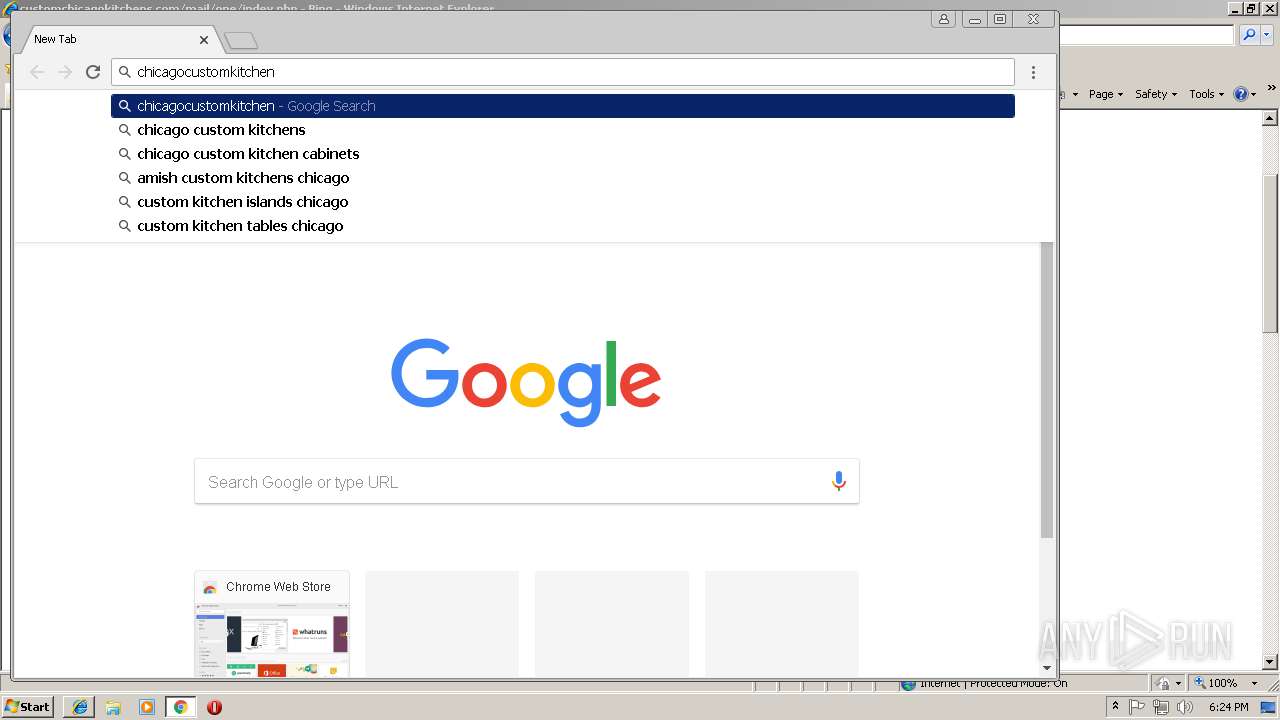
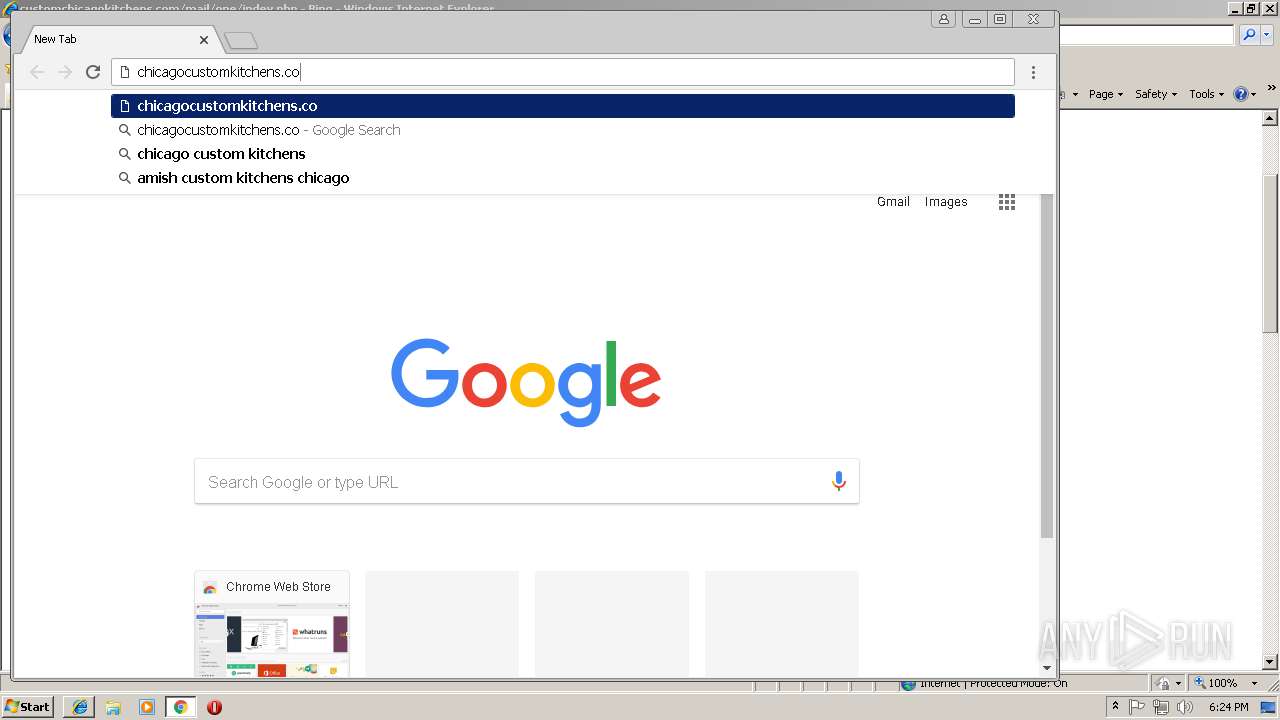
384 | iexplore.exe | GET | 200 | 131.253.33.200:80 | http://www.bing.com/search?q=customchicagokitchens.com%2Fmail&src=IE-SearchBox&FORM=IE8SRC | US | html | 21.6 Kb | whitelisted |
384 | iexplore.exe | GET | 200 | 131.253.33.200:80 | http://www.bing.com/rb/12/cj,nj/dfbe5368/a11e6044.js?bu=DSkuWWltcWVdYaYBqgEumgE | US | text | 7.54 Kb | whitelisted |
384 | iexplore.exe | GET | 200 | 131.253.33.200:80 | http://www.bing.com/rms/AutoSug/cj,nj/41818034/0beb16f3.js?bu=rms+answers+AutoSuggest+Service*Web%24Utils*Web%24EventRegisterer*Web%24EventRegistration*Empty*Empty*Empty*Empty*Web%24WebCore*Web%24DataProvider*Empty*Empty*Empty*Web%24Canvas*Empty*Web%24Layout*Web%24SearchForm*Web%24Ghosting*Empty*Empty*Empty*Empty*Empty*Empty*Web%24DeleteHistorySuggestionHandler*Web%24Init | US | text | 13.3 Kb | whitelisted |
384 | iexplore.exe | POST | 204 | 131.253.33.200:80 | http://www.bing.com/fd/ls/lsp.aspx | US | compressed | 174 b | whitelisted |
384 | iexplore.exe | GET | 200 | 131.253.33.200:80 | http://www.bing.com/rs/2S/2d/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
384 | iexplore.exe | POST | 204 | 131.253.33.200:80 | http://www.bing.com/fd/ls/lsp.aspx | US | compressed | 816 b | whitelisted |
384 | iexplore.exe | POST | 204 | 131.253.33.200:80 | http://www.bing.com/fd/ls/lsp.aspx | US | compressed | 7.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
504 | iexplore.exe | 131.253.33.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
384 | iexplore.exe | 143.204.93.232:80 | script.crazyegg.com | — | US | unknown |
384 | iexplore.exe | 52.72.156.183:80 | crazyegg.com | Amazon.com, Inc. | US | unknown |
384 | iexplore.exe | 52.200.95.92:443 | crazyegg.com | Amazon.com, Inc. | US | unknown |
384 | iexplore.exe | 23.23.199.152:443 | app.crazyegg.com | Amazon.com, Inc. | US | unknown |
384 | iexplore.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
384 | iexplore.exe | 108.177.119.95:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
384 | iexplore.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
504 | iexplore.exe | 143.204.93.232:80 | script.crazyegg.com | — | US | unknown |
504 | iexplore.exe | 52.200.95.92:443 | crazyegg.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
script.crazyegg.com |
| whitelisted |
crazyegg.com |
| whitelisted |
www.crazyegg.com |
| suspicious |
www.google.com |
| malicious |
app.crazyegg.com |
| suspicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
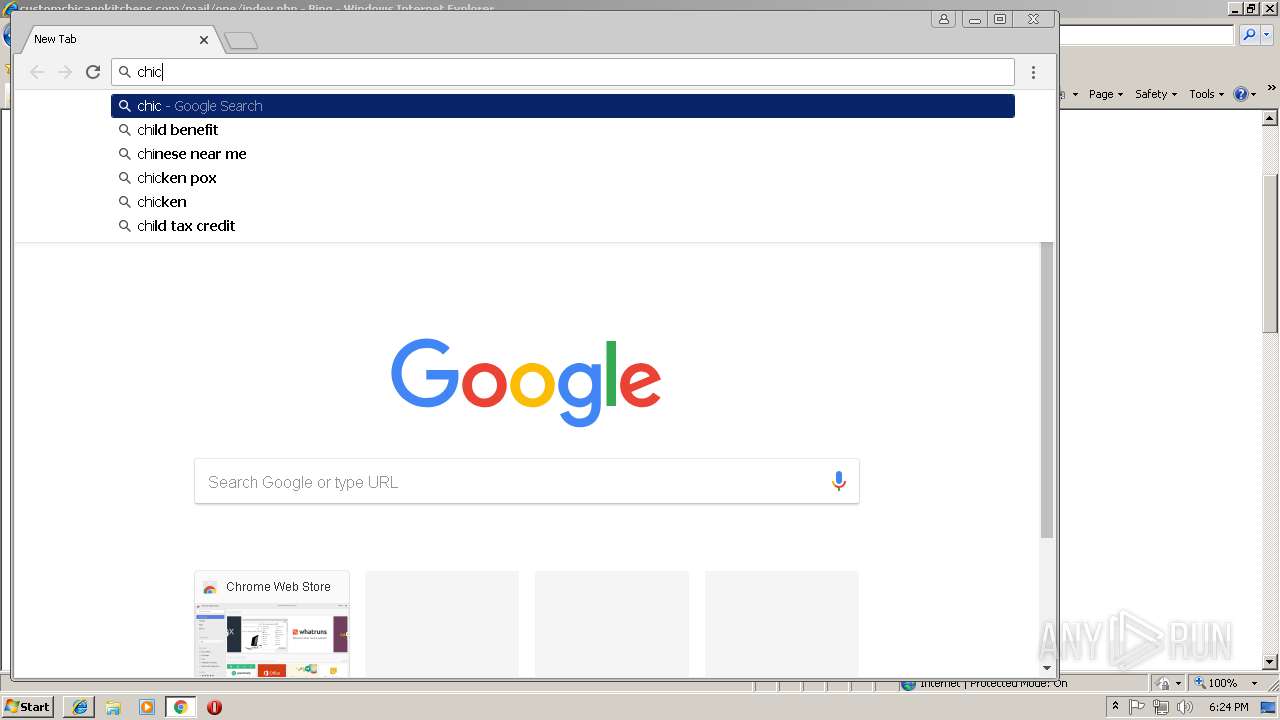
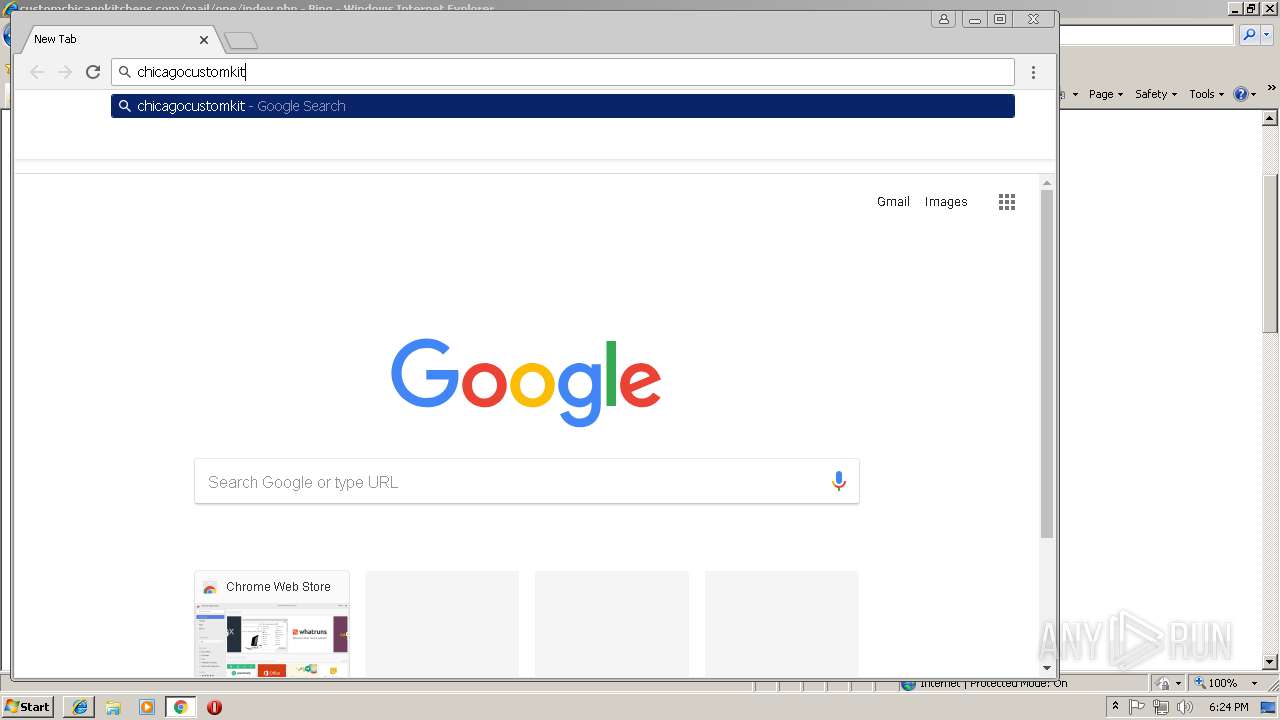
customchicagokitchens.com |
| unknown |