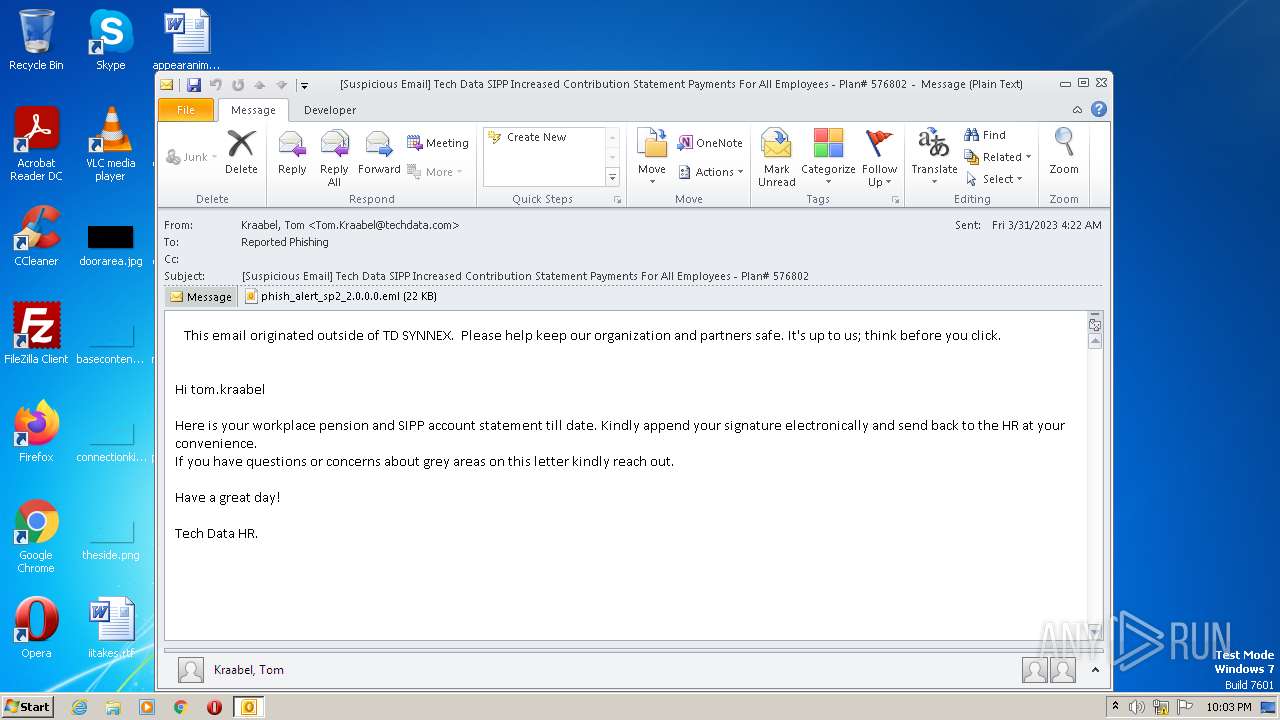
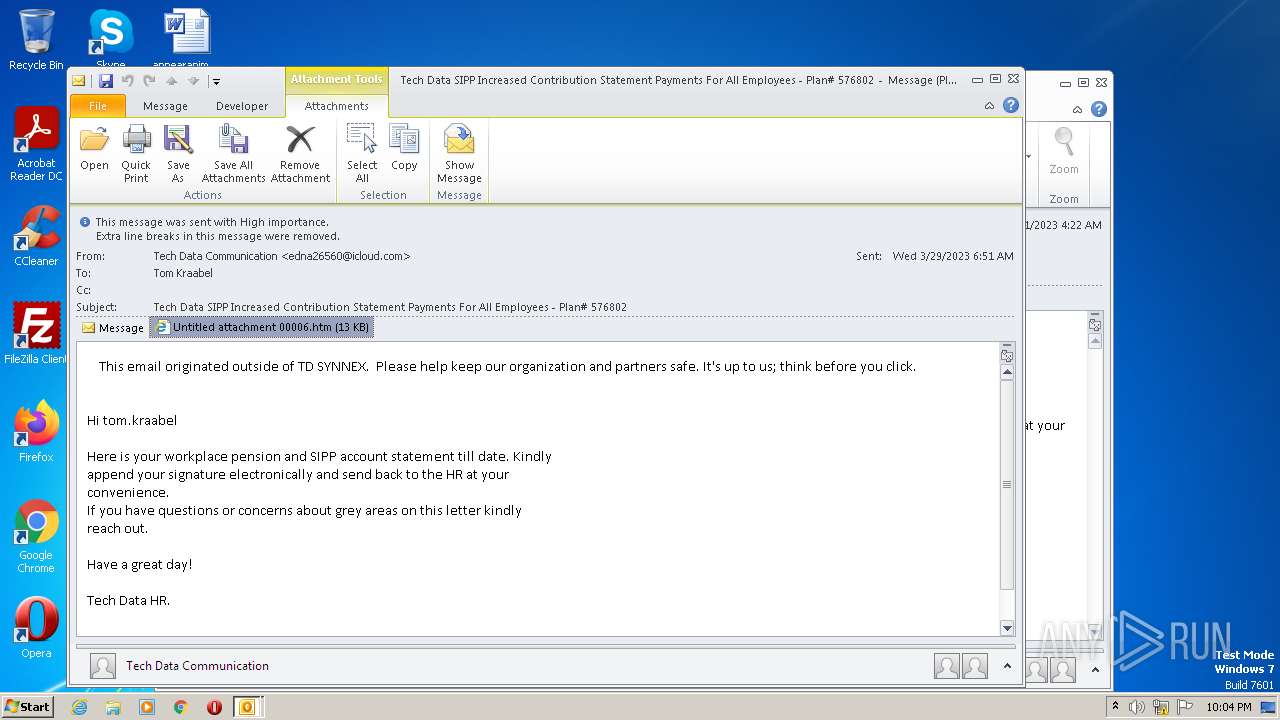
| File name: | [Suspicious Email] Tech Data SIPP Increased Contribution Statement__ Payments For All Employees - Plan# 576802.eml |
| Full analysis: | https://app.any.run/tasks/918f655b-1036-482e-b2e1-aa6b9353d5af |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2023, 21:03:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 126E87787D7F472192AE9AC2C0E4496B |
| SHA1: | 41B0F1D5E6CBA5C664467CB1B1A4D432FA1A77F3 |
| SHA256: | FC66292C5CF052FAECC16DC697FD0A2049DE9AE0E7AFB208F237295F4134B156 |
| SSDEEP: | 768:BG9sHulwKB1p0gbrRYwu2kYA65kqra58Ak6s7gh0gOoi5VZn:BG9sH4x1p0qTEqrq8AHsk4n |
MALICIOUS
Unusual execution from MS Office
- OUTLOOK.EXE (PID: 2064)
SUSPICIOUS
Reads the Internet Settings
- OUTLOOK.EXE (PID: 2064)
Searches for installed software
- OUTLOOK.EXE (PID: 2064)
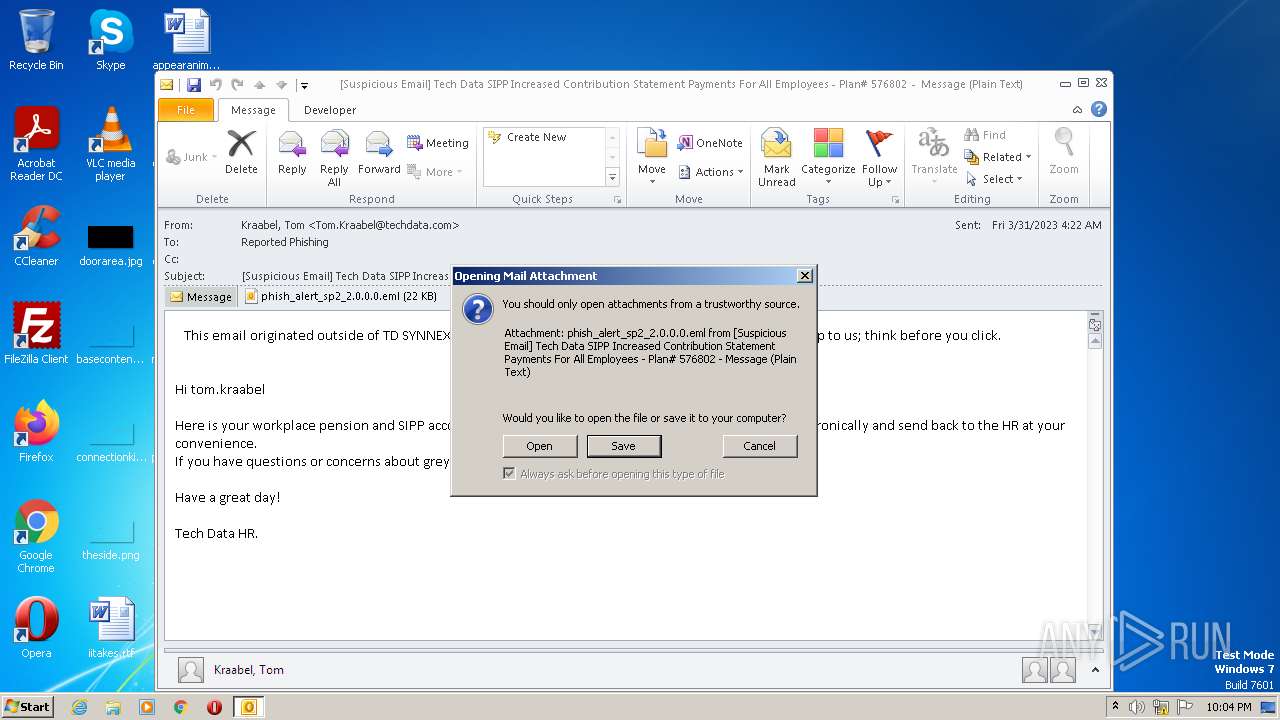
Application launched itself
- OUTLOOK.EXE (PID: 2064)
Reads Microsoft Outlook installation path
- OUTLOOK.EXE (PID: 2064)
INFO
Reads the computer name
- OUTLOOK.EXE (PID: 2064)
The process checks LSA protection
- OUTLOOK.EXE (PID: 2064)
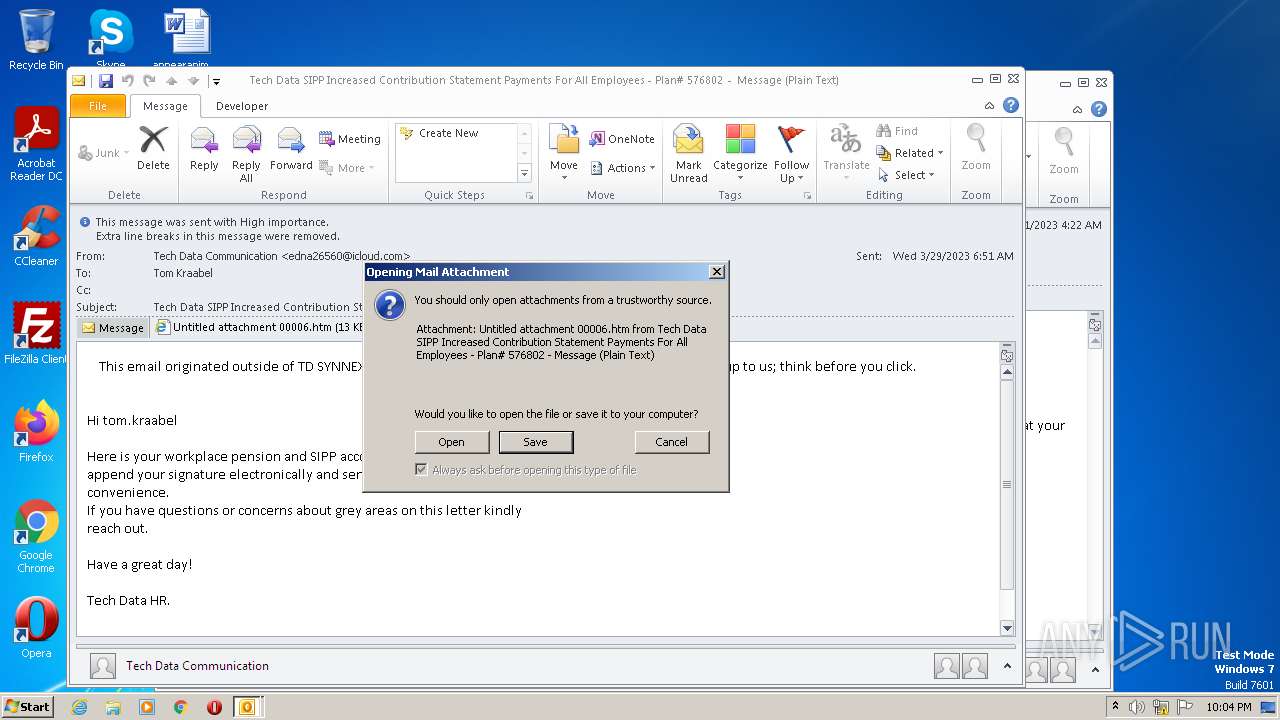
Create files in a temporary directory
- OUTLOOK.EXE (PID: 2064)
- iexplore.exe (PID: 3724)
Reads the machine GUID from the registry
- OUTLOOK.EXE (PID: 2064)
Checks supported languages
- OUTLOOK.EXE (PID: 2064)
- OUTLOOK.EXE (PID: 3016)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2064)
- OUTLOOK.EXE (PID: 3016)
Process checks computer location settings
- OUTLOOK.EXE (PID: 2064)
Checks proxy server information
- OUTLOOK.EXE (PID: 2064)
Application launched itself
- iexplore.exe (PID: 3724)
Creates files or folders in the user directory
- OUTLOOK.EXE (PID: 2064)
The process uses the downloaded file
- OUTLOOK.EXE (PID: 2064)
- iexplore.exe (PID: 3724)
- iexplore.exe (PID: 1632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
41
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1632 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3724 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2064 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\b2e6275e-bc0c-49d6-a5a2-6f37cf2c3023.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
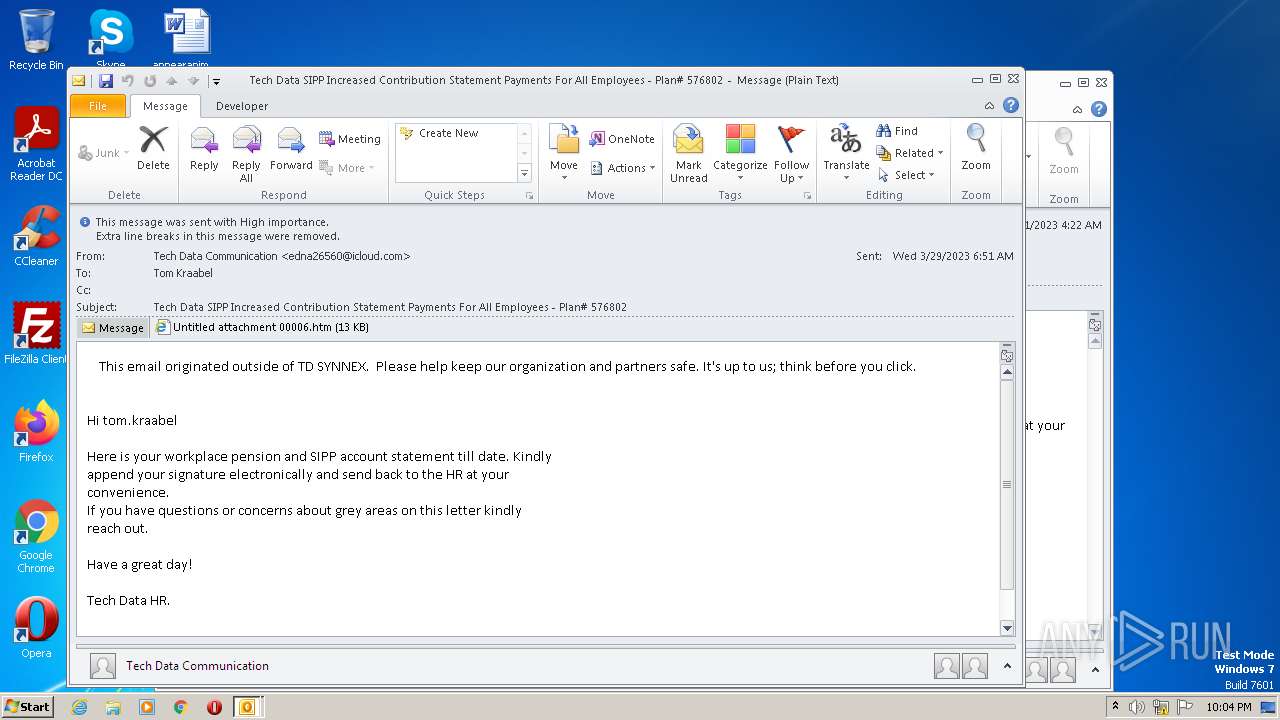
| 3016 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LABE48MP\phish_alert_sp2_2 0 0 0.eml" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3724 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LABE48MP\Untitled attachment 00006.htm | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
25 174
Read events
24 122
Write events
1 010
Delete events
42
Modification events
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
0
Suspicious files
0
Text files
32
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRFAEB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3016 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C71.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LABE48MP\phish_alert_sp2_2 0 0 0.eml | eml | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LABE48MP\Untitled attachment 00006.htm | html | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LABE48MP\phish_alert_sp2_2 0 0 0 (2).eml | eml | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\LABE48MP\Untitled attachment 00006 (2).htm | html | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | OUTLOOK.EXE | GET | 404 | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | xml | 341 b | whitelisted |
3724 | iexplore.exe | GET | 404 | 8.238.34.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8c6d1c68125615a3 | US | xml | 341 b | whitelisted |
3724 | iexplore.exe | GET | 404 | 8.238.34.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2b439f94b8e671ae | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3724 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3724 | iexplore.exe | 8.238.34.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
2064 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report