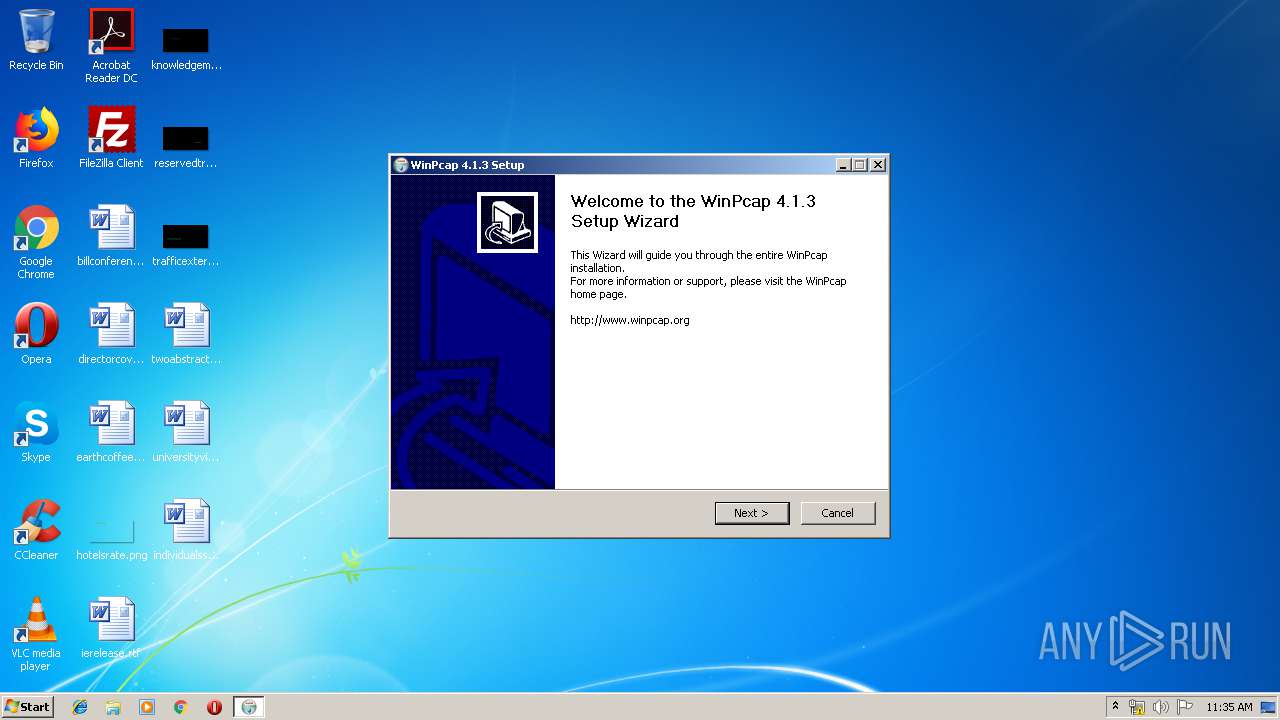
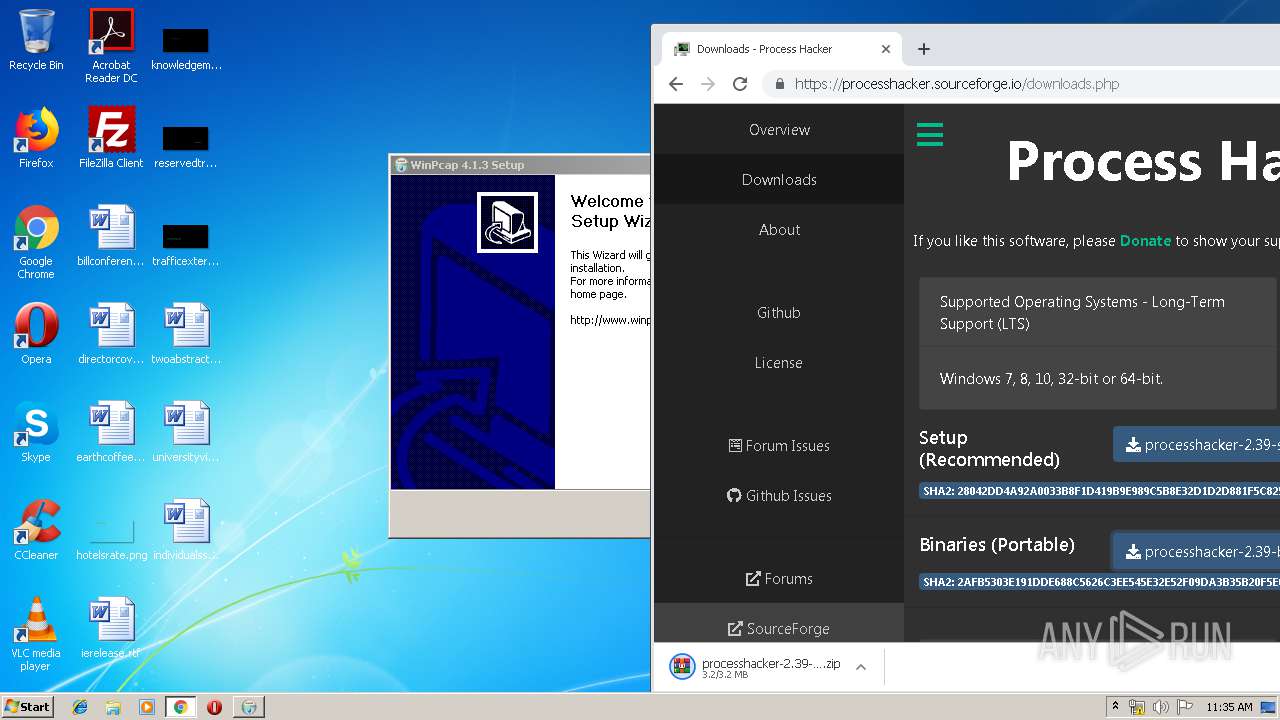
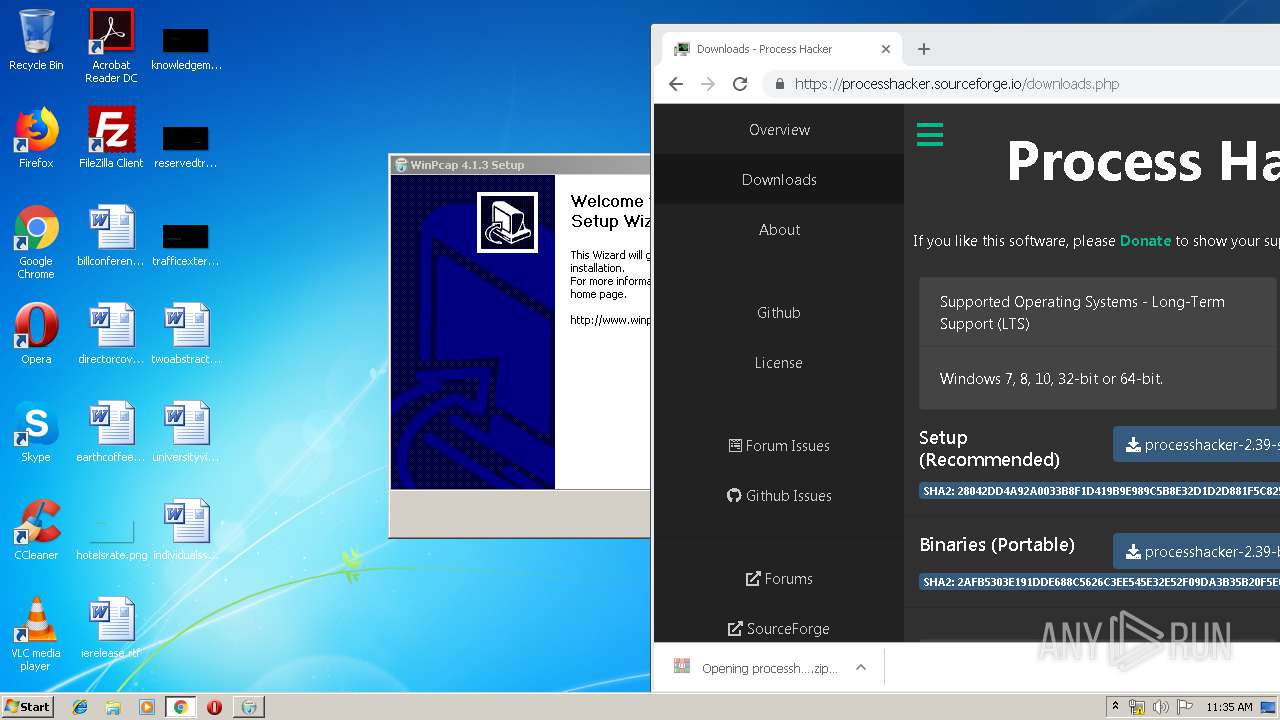
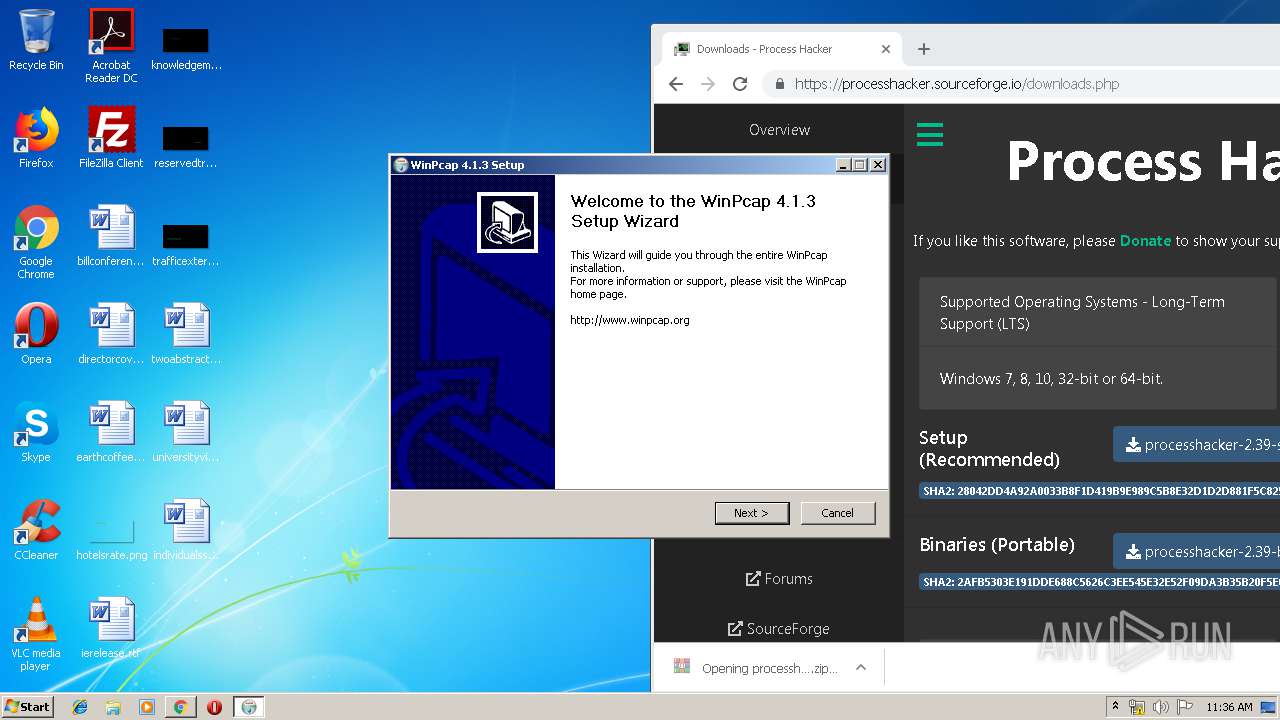
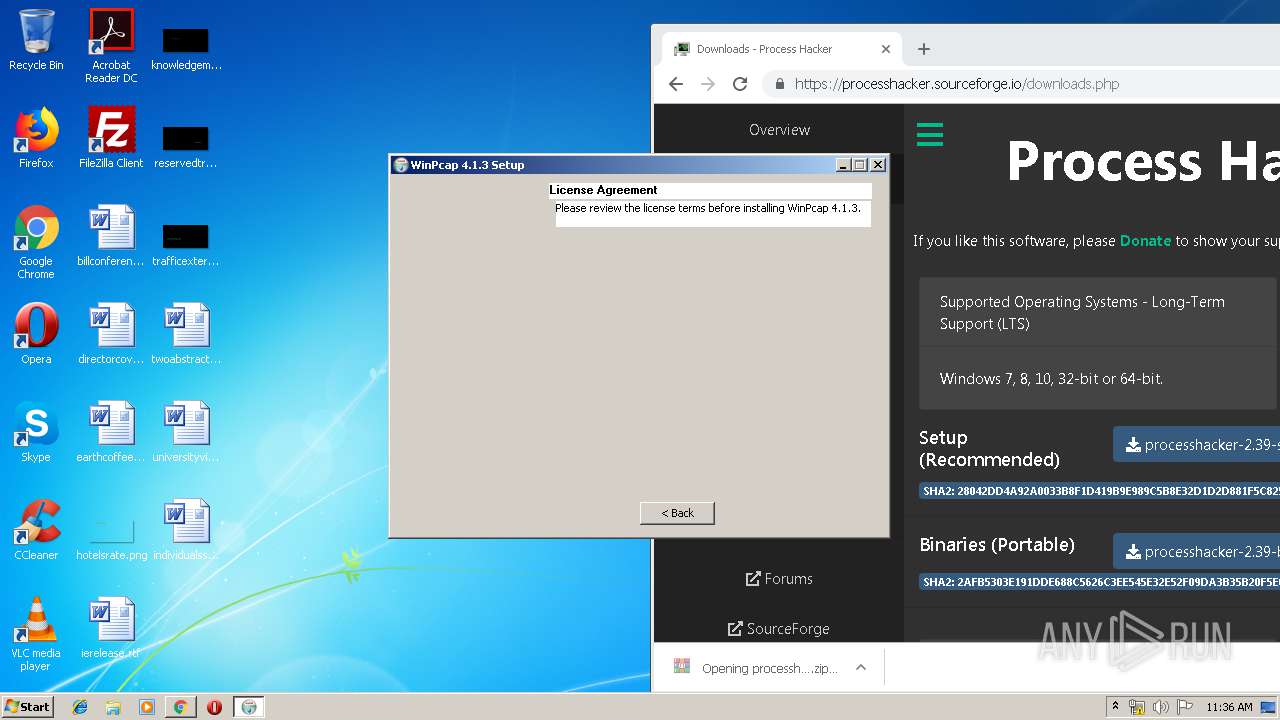
| File name: | WinPcap_4_1_3.exe |
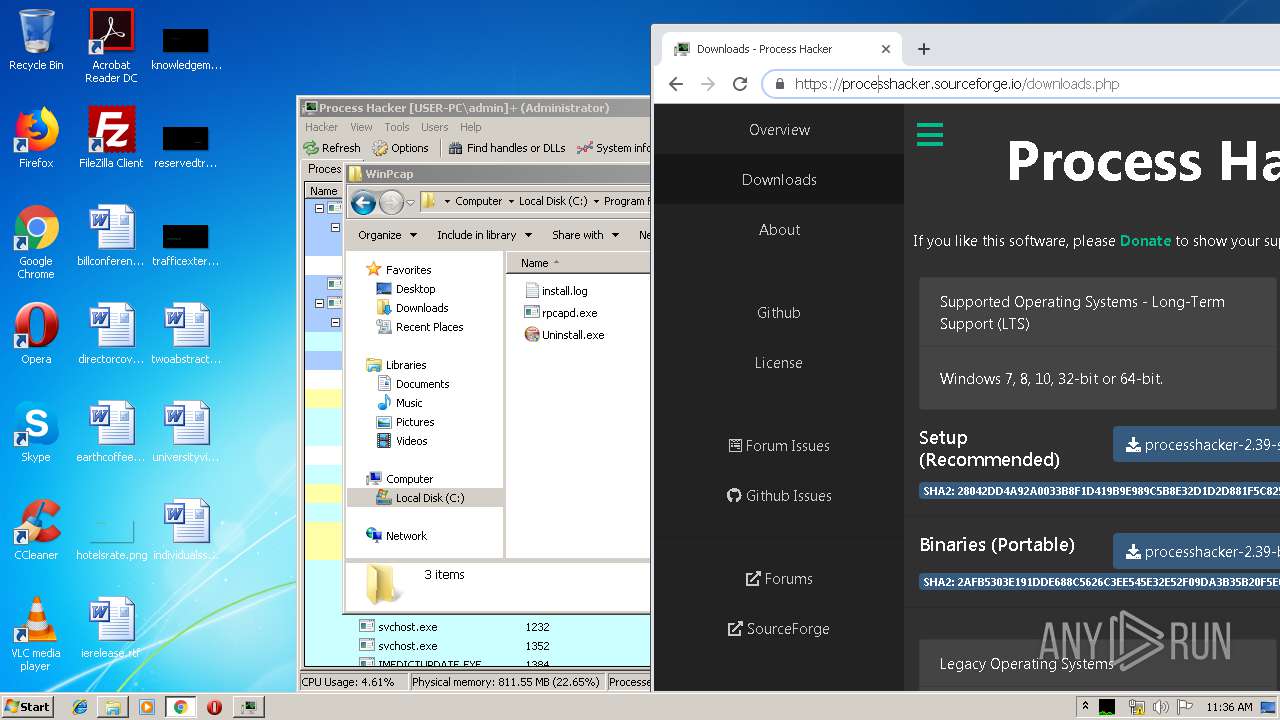
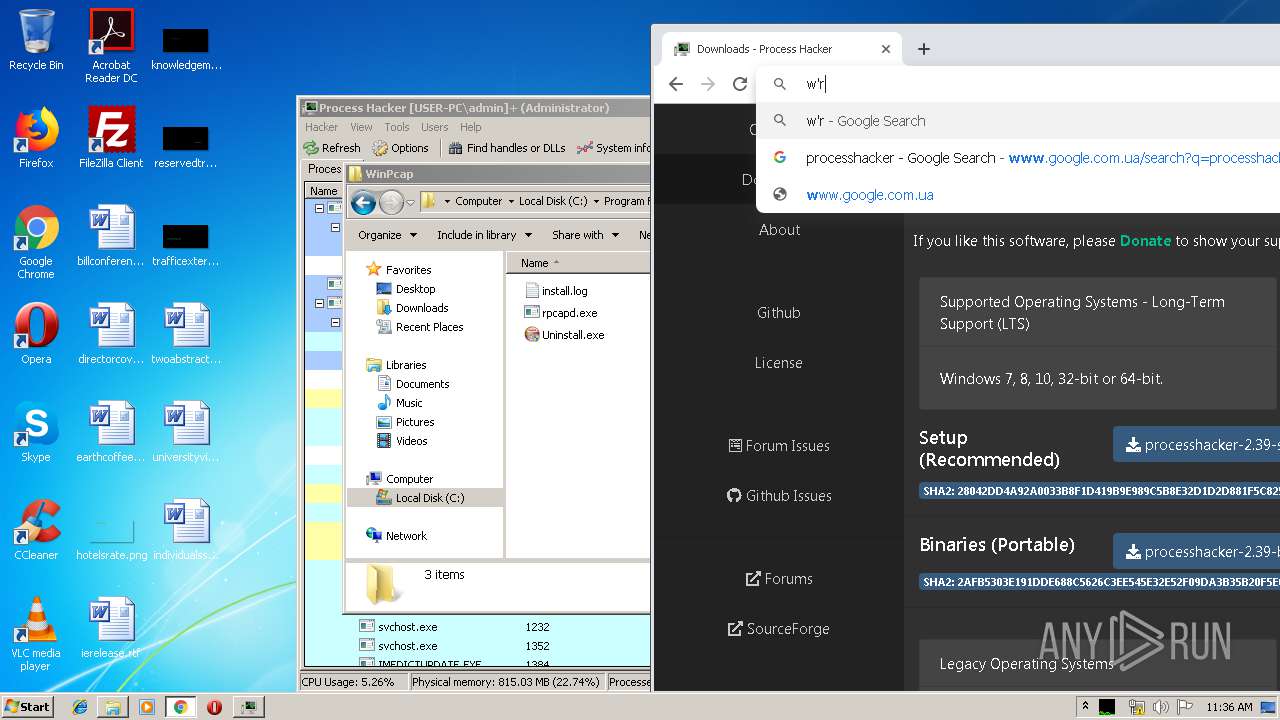
| Full analysis: | https://app.any.run/tasks/fab30c10-2a5f-40b9-9ad9-7f39913eb62d |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2020, 11:35:11 |
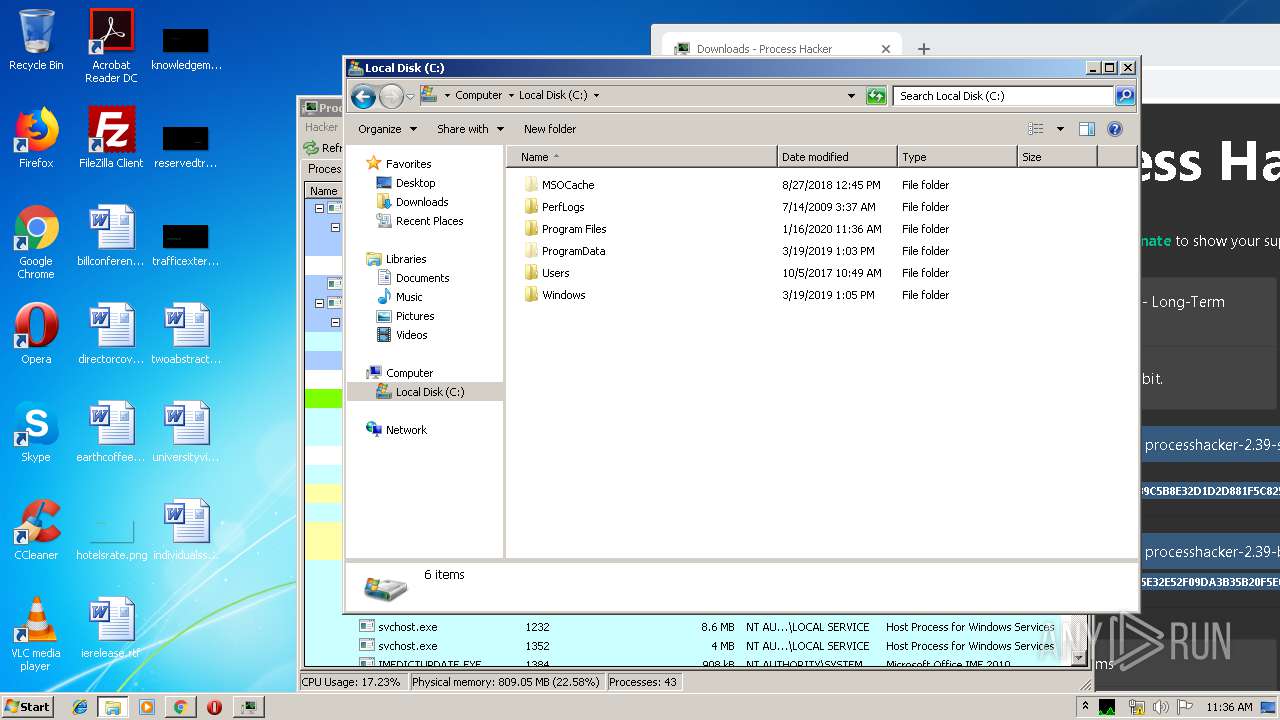
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A11A2F0CFE6D0B4C50945989DB6360CD |
| SHA1: | E2516FCD1573E70334C8F50BEE5241CDFDF48A00 |
| SHA256: | FC4623B113A1F603C0D9AD5F83130BD6DE1C62B973BE9892305132389C8588DE |
| SSDEEP: | 24576:UBOldyR6ORWsaM2QROxa6jsqUENfJjNK/CG6niqiL:2KzqWsayROxa6QDENuaG+ifL |
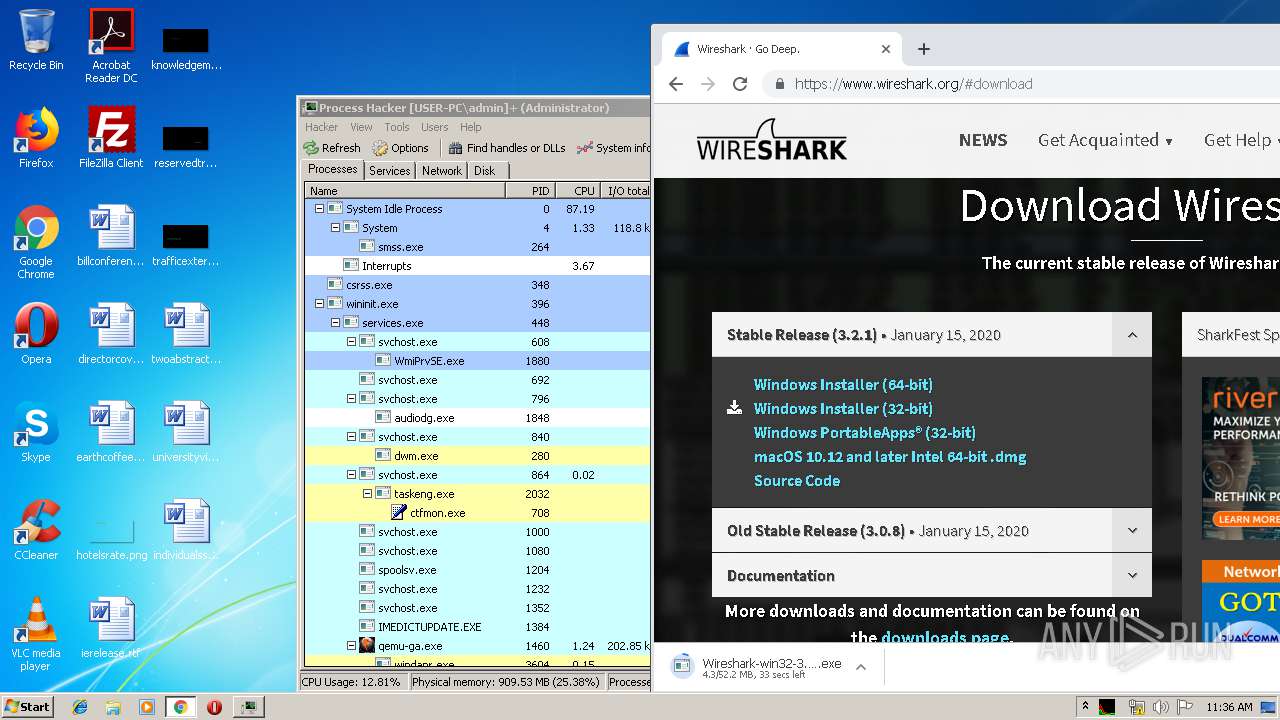
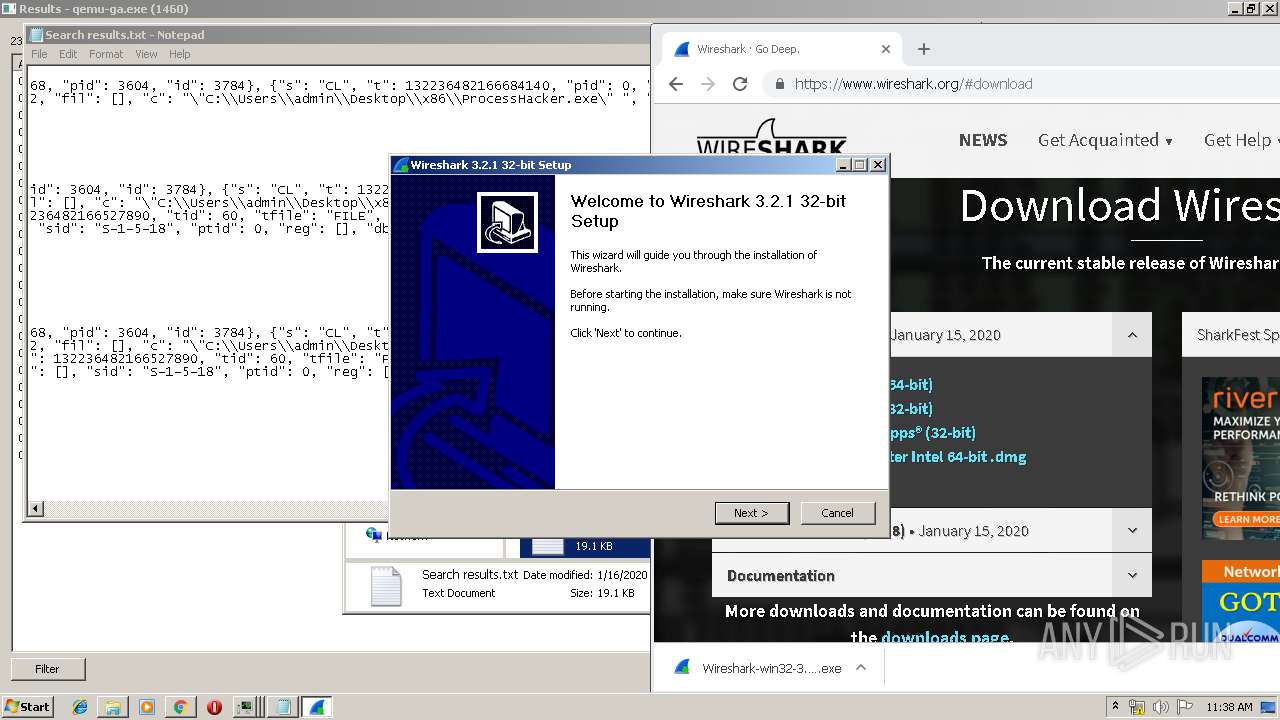
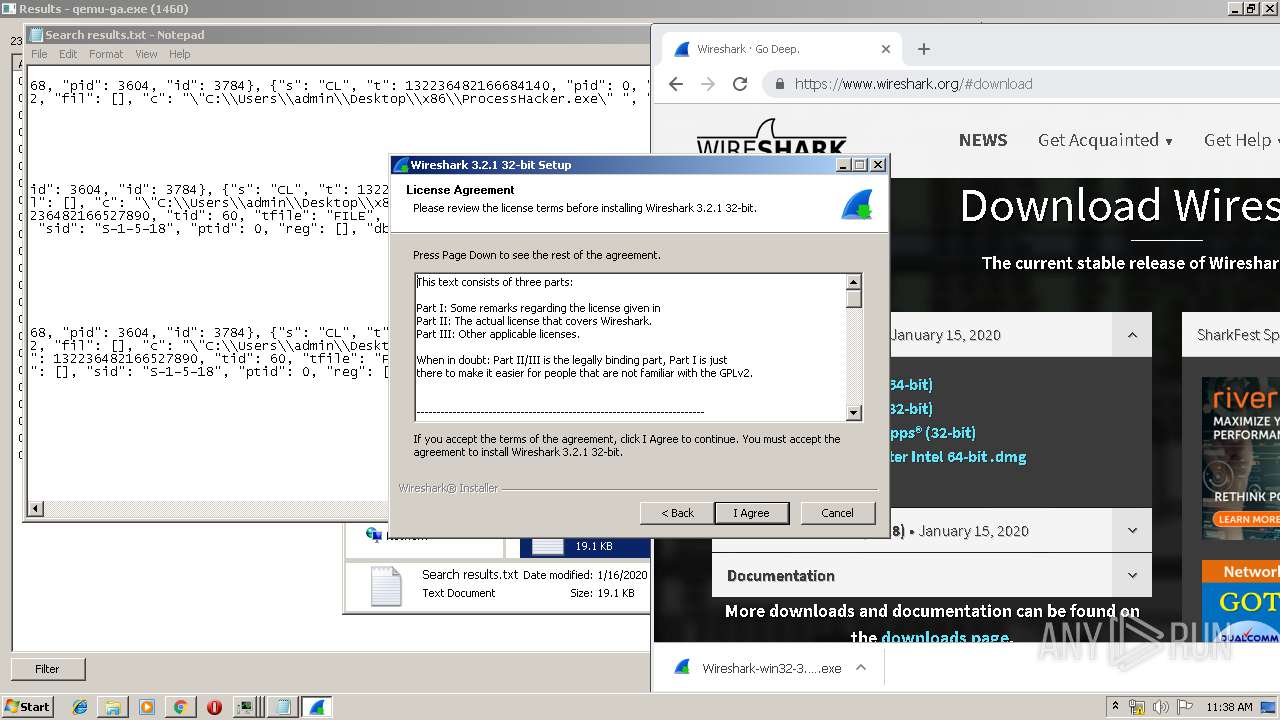
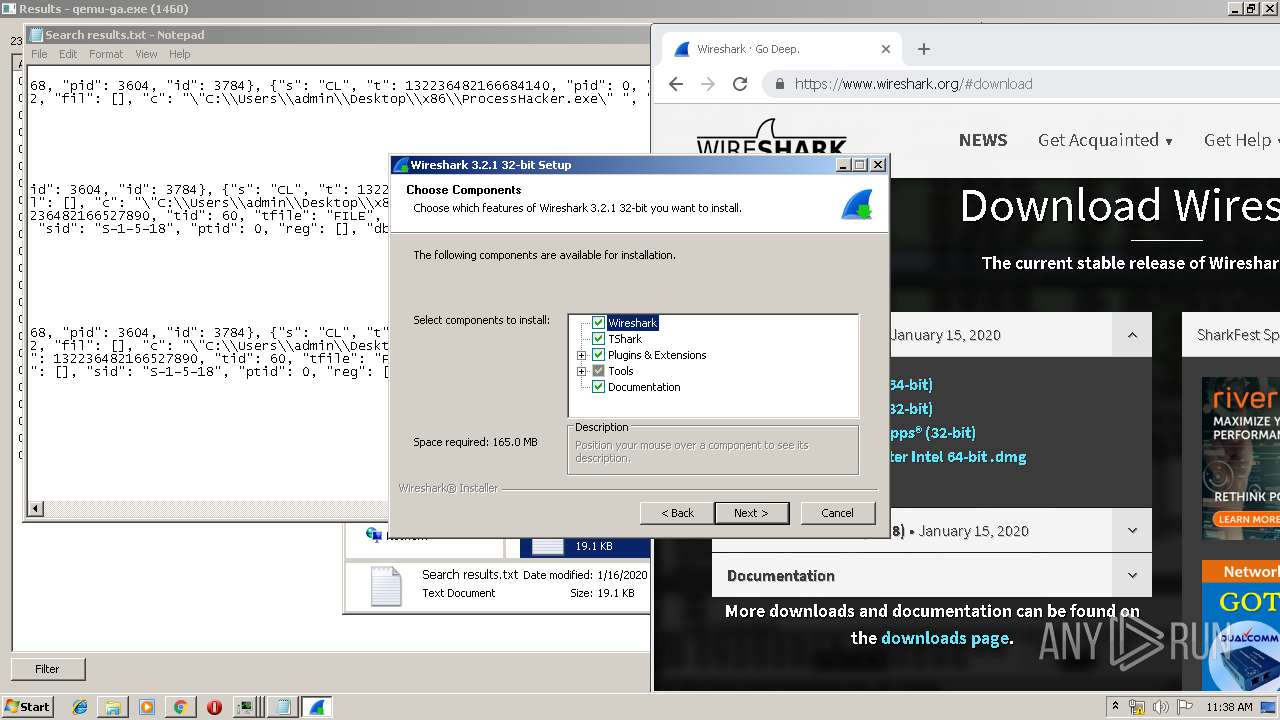
MALICIOUS
Loads dropped or rewritten executable
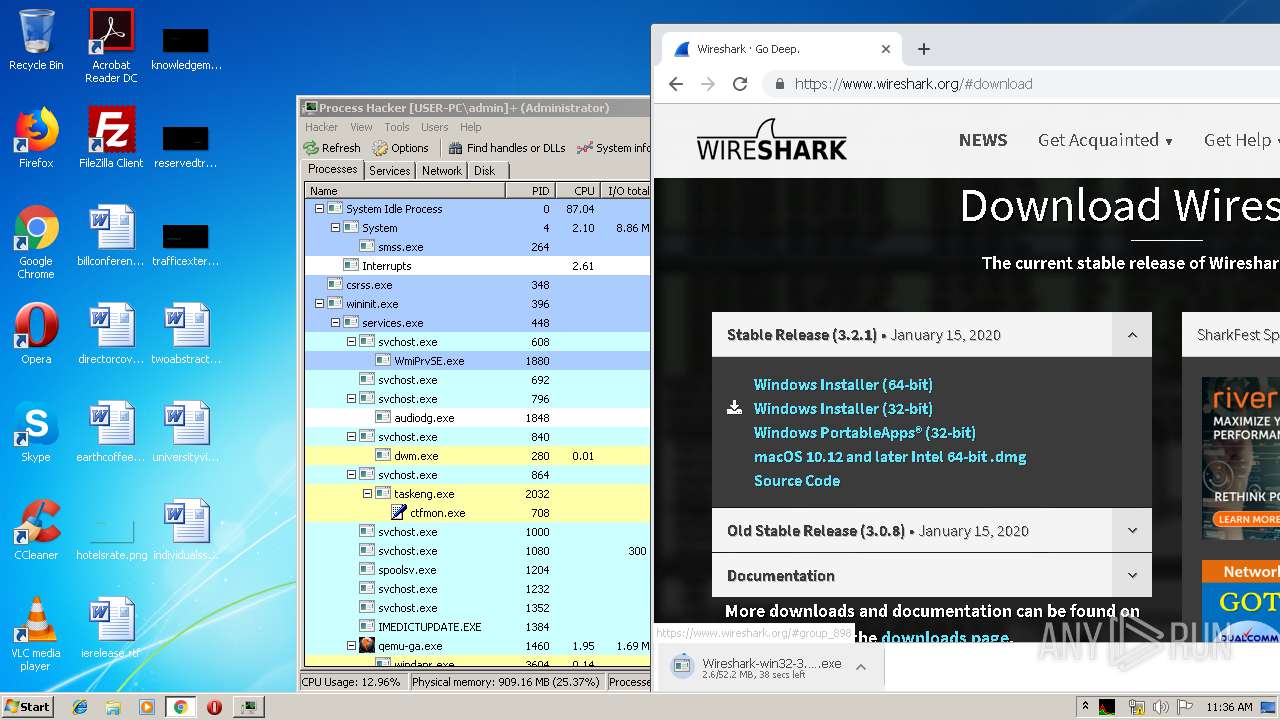
- WinPcap_4_1_3.exe (PID: 3564)
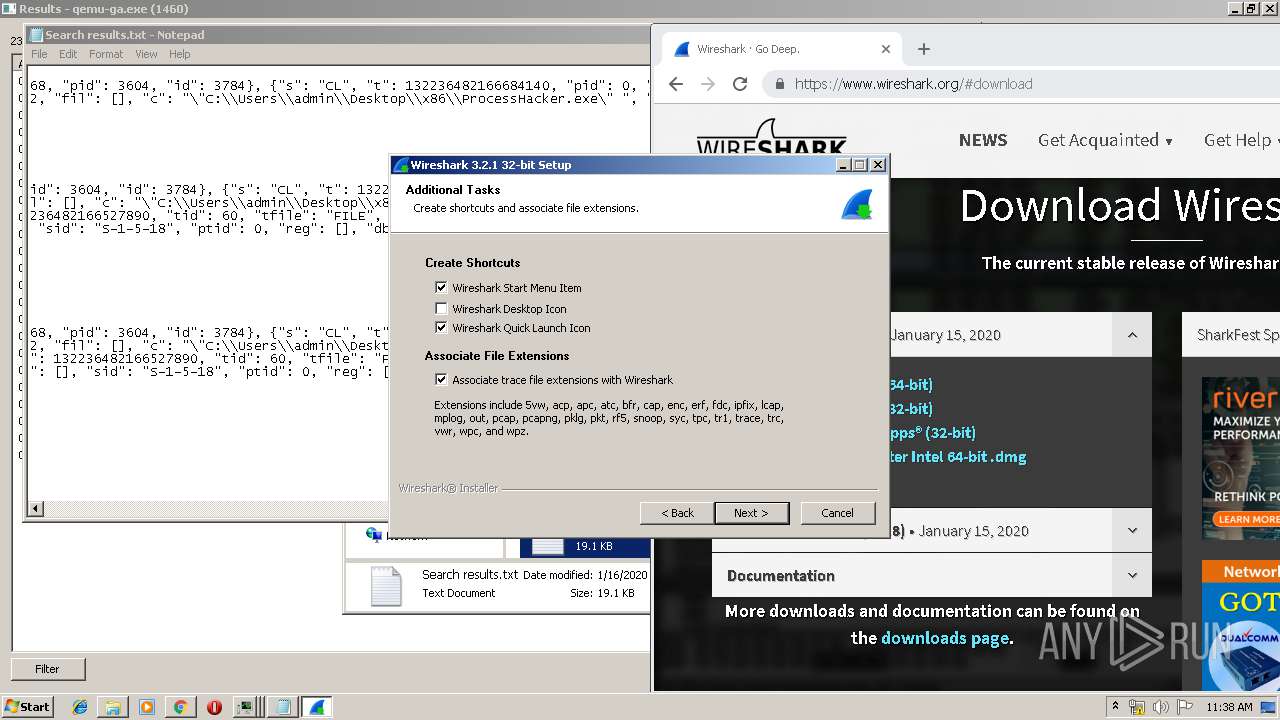
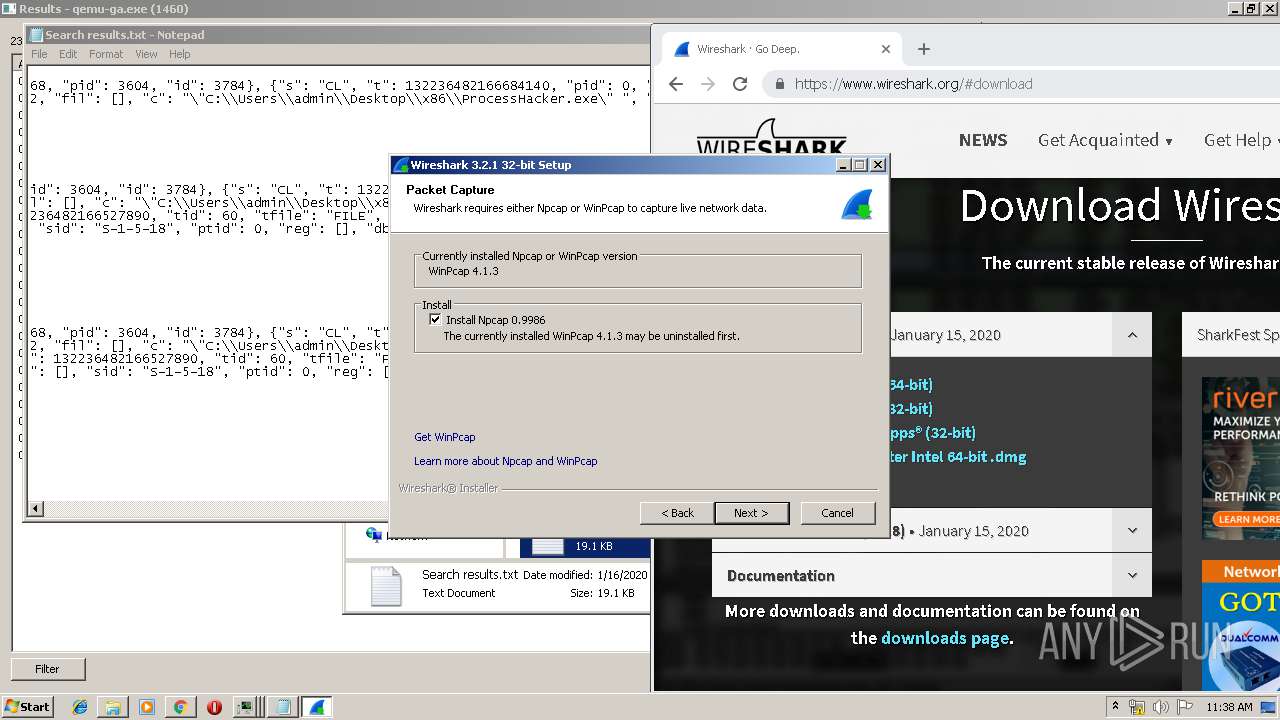
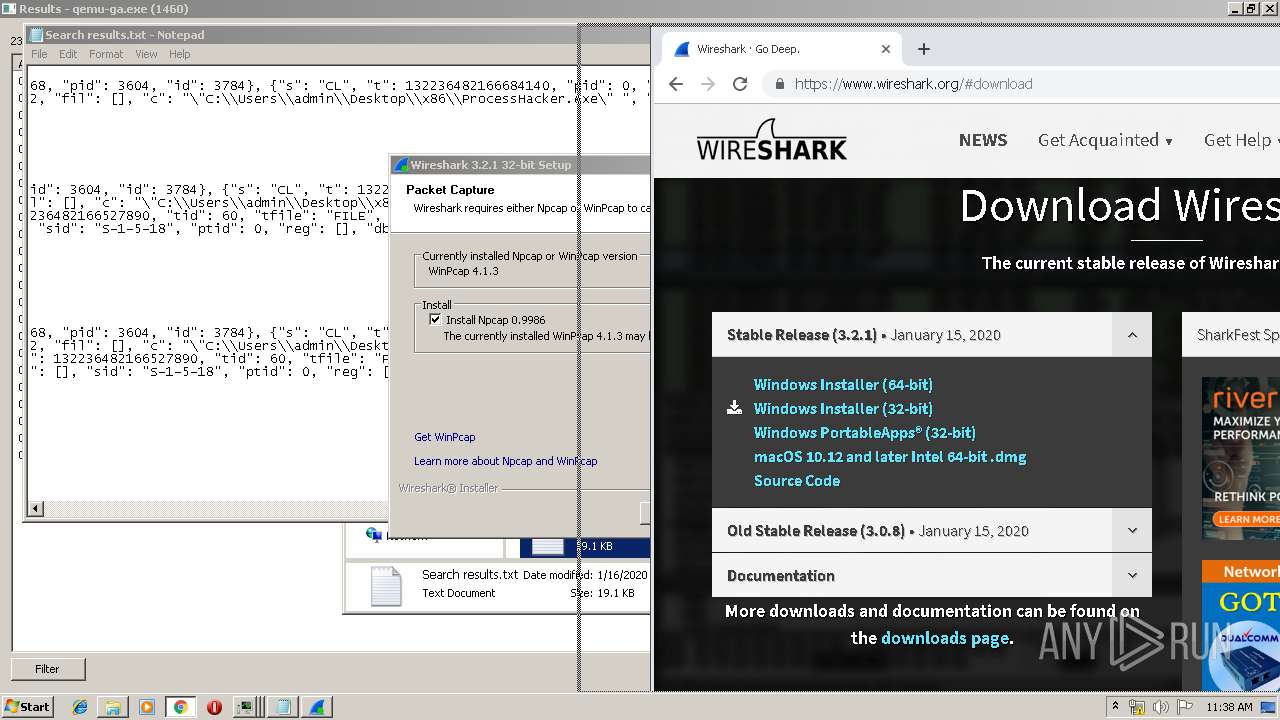
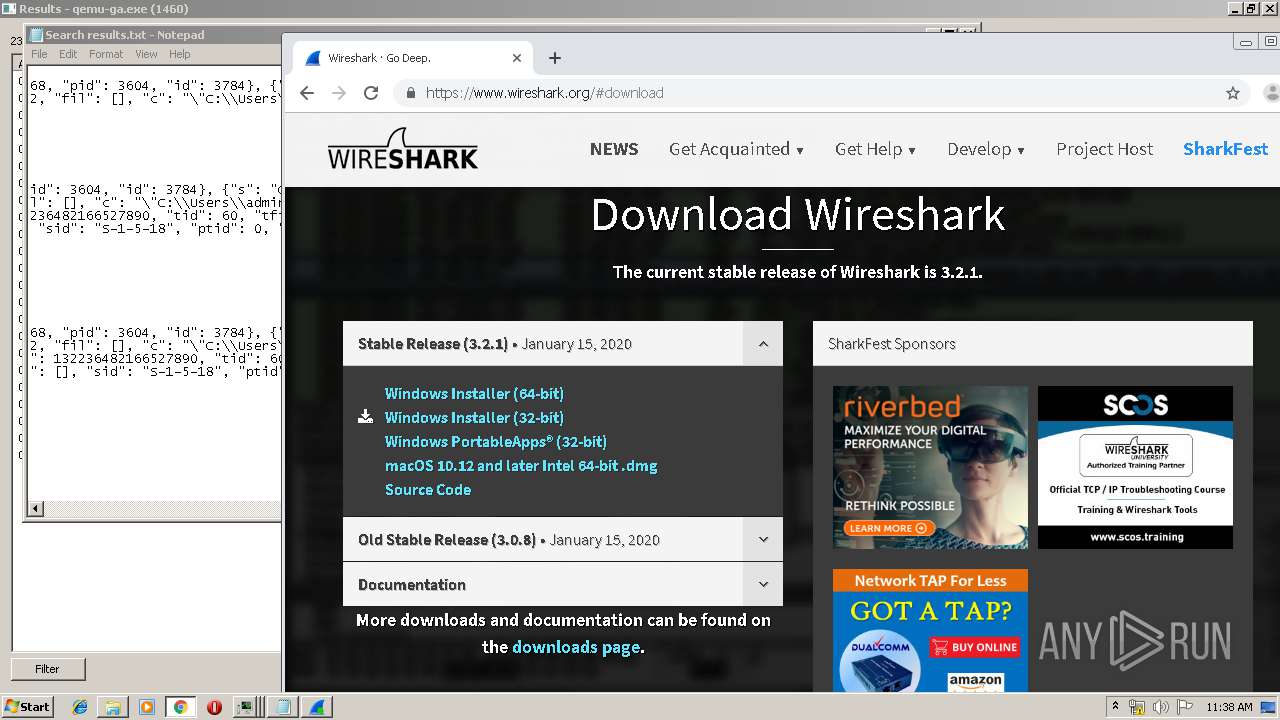
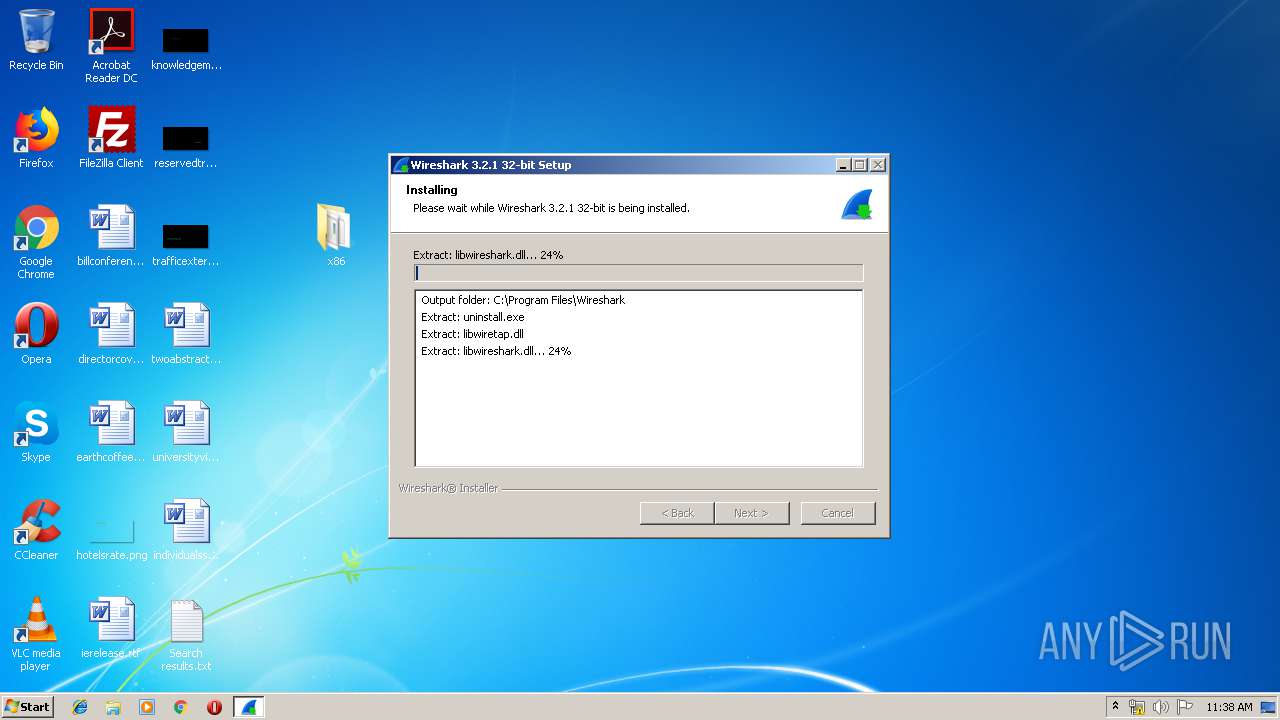
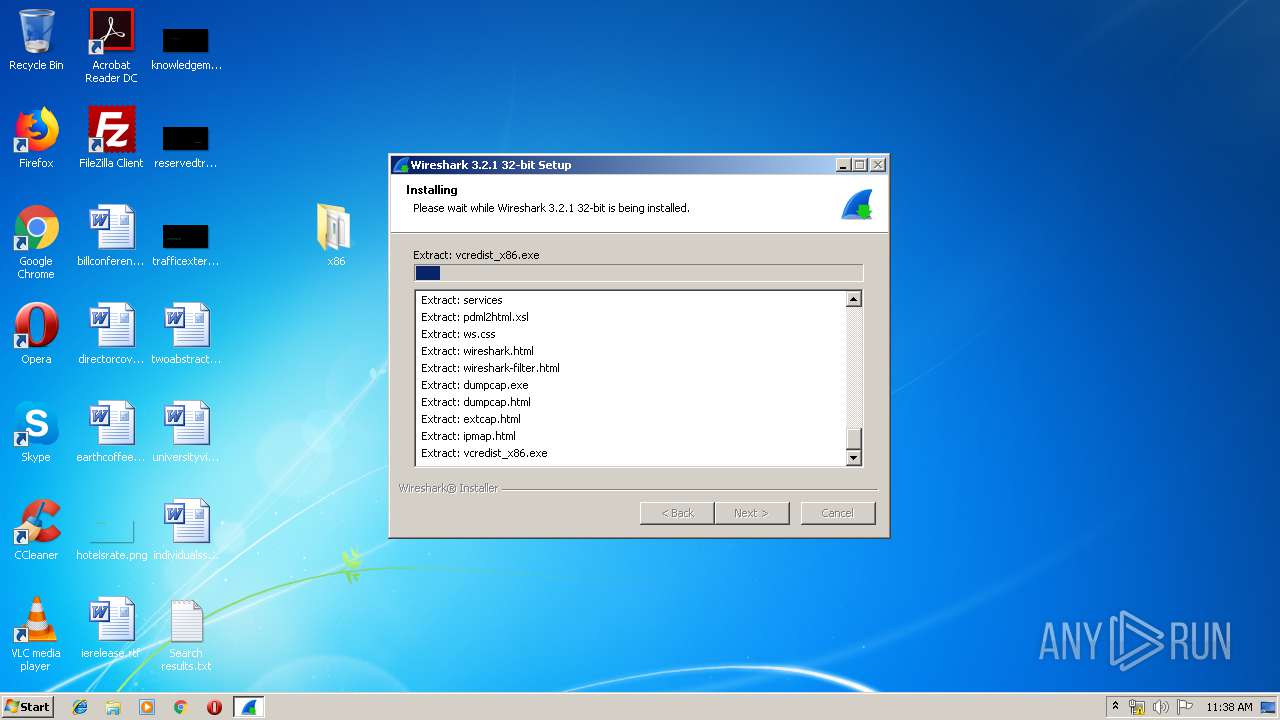
- Wireshark-win32-3.2.1.exe (PID: 1608)
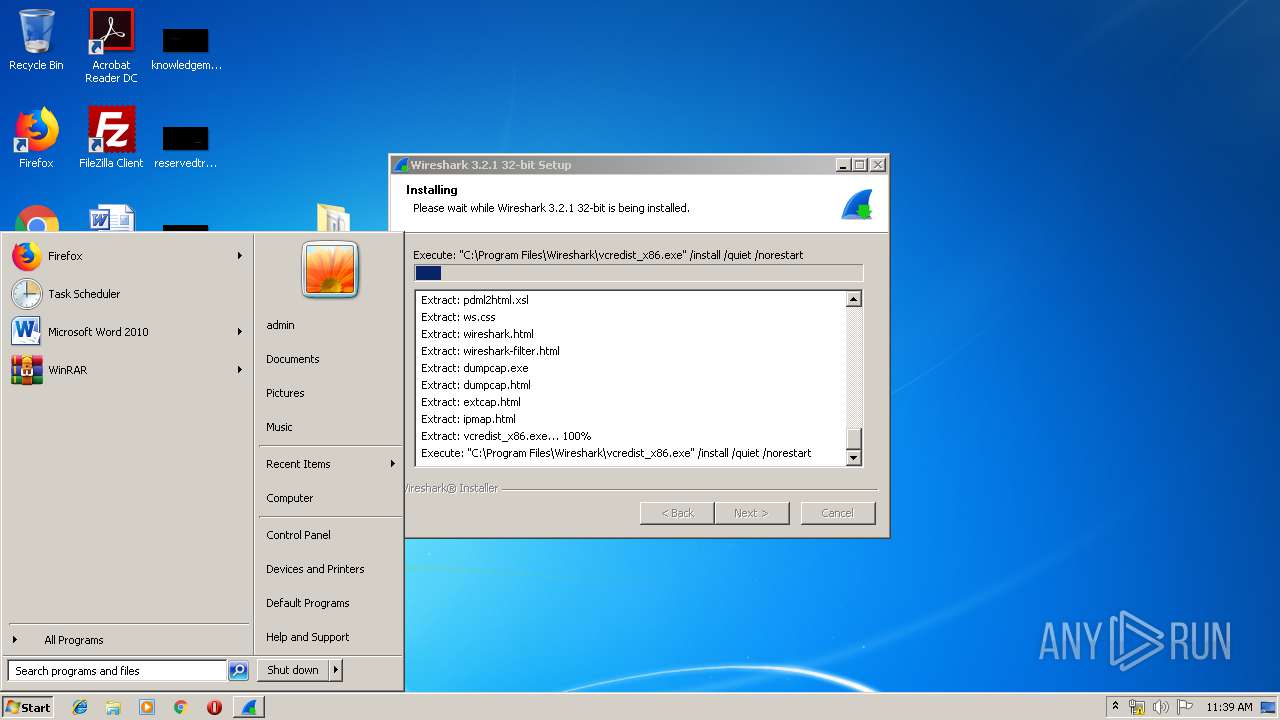
- vcredist_x86.exe (PID: 3808)
- VC_redist.x86.exe (PID: 2856)
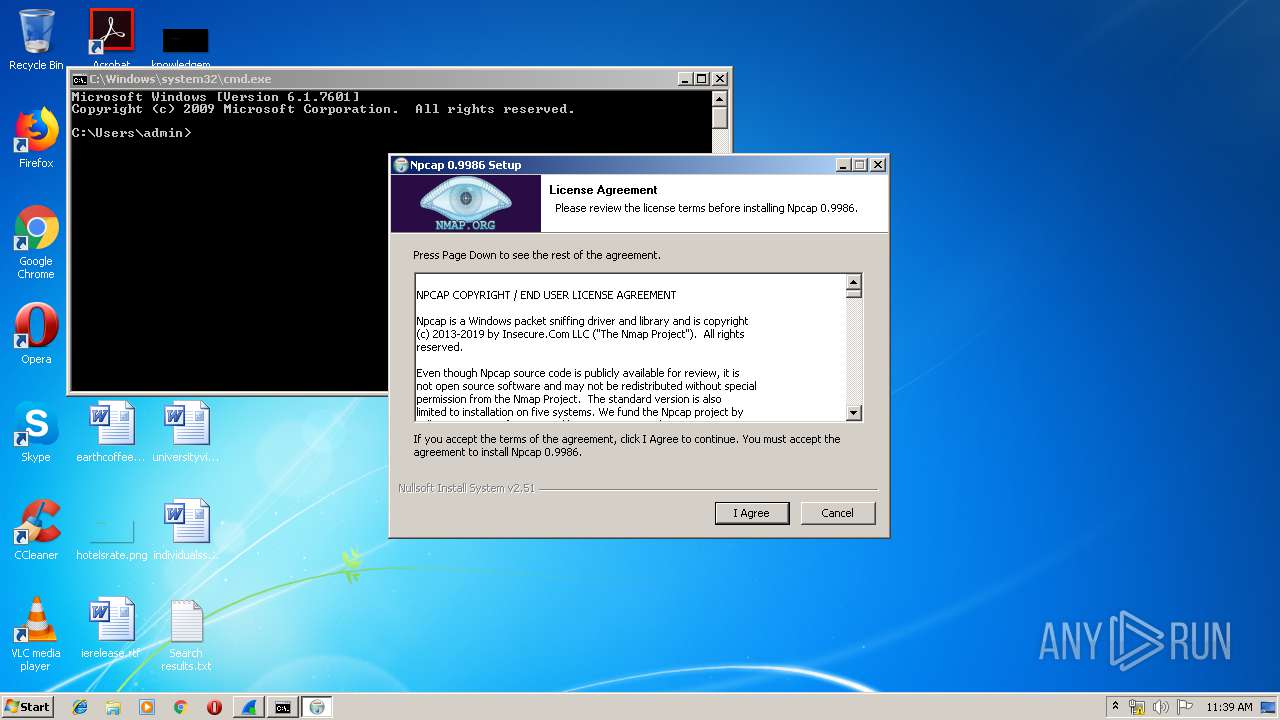
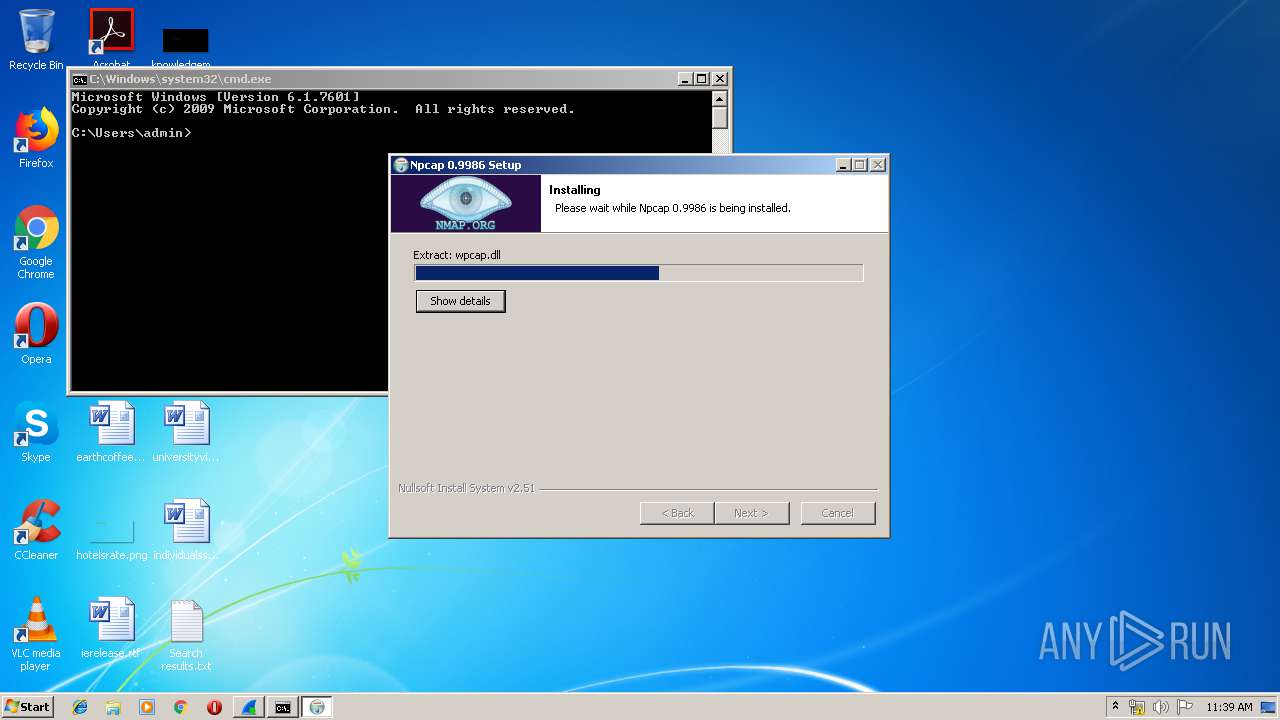
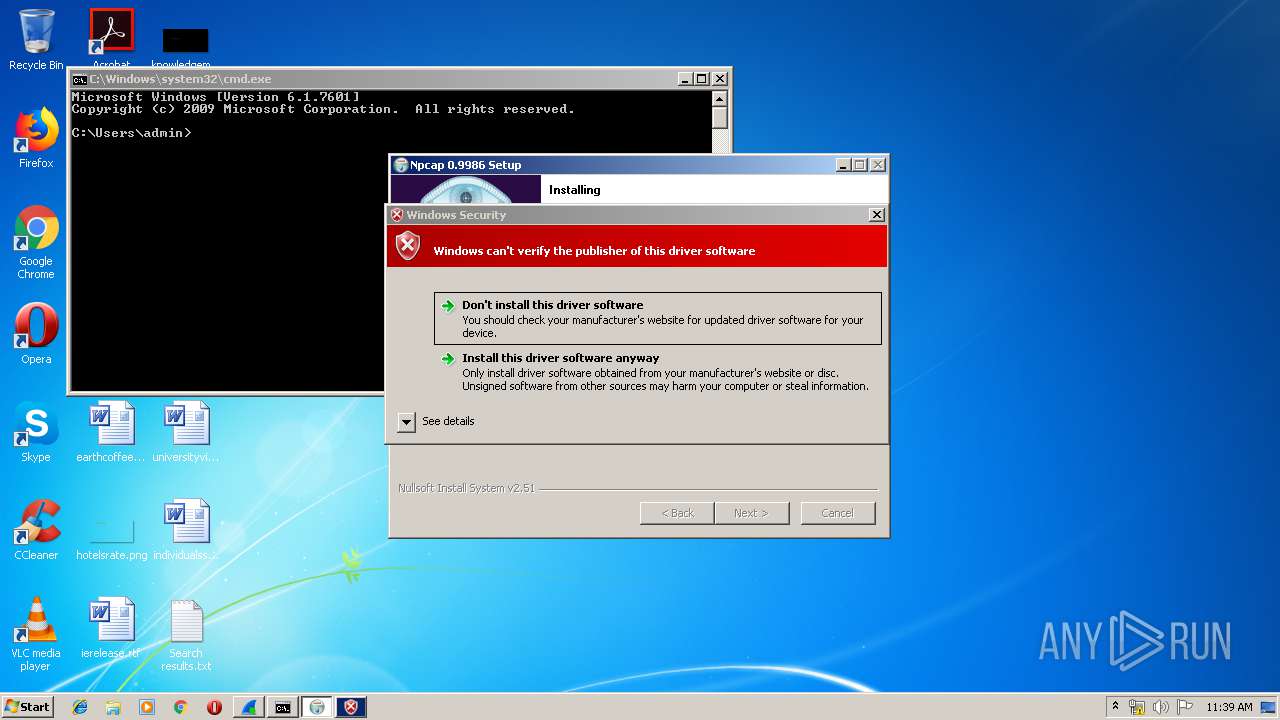
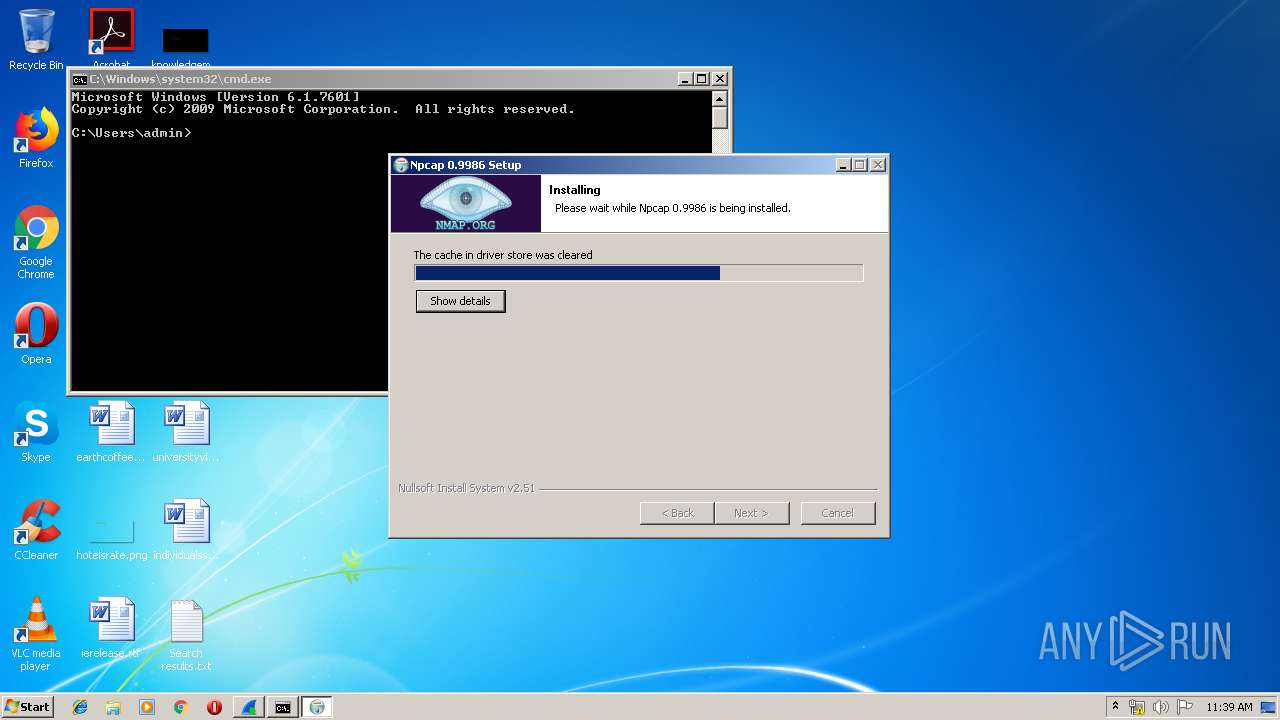
- npcap-0.9986.exe (PID: 788)
- dumpcap.exe (PID: 2884)
- Wireshark.exe (PID: 444)
- dumpcap.exe (PID: 2136)
- dumpcap.exe (PID: 3004)
- dumpcap.exe (PID: 2356)
Starts NET.EXE for service management
- WinPcap_4_1_3.exe (PID: 3564)
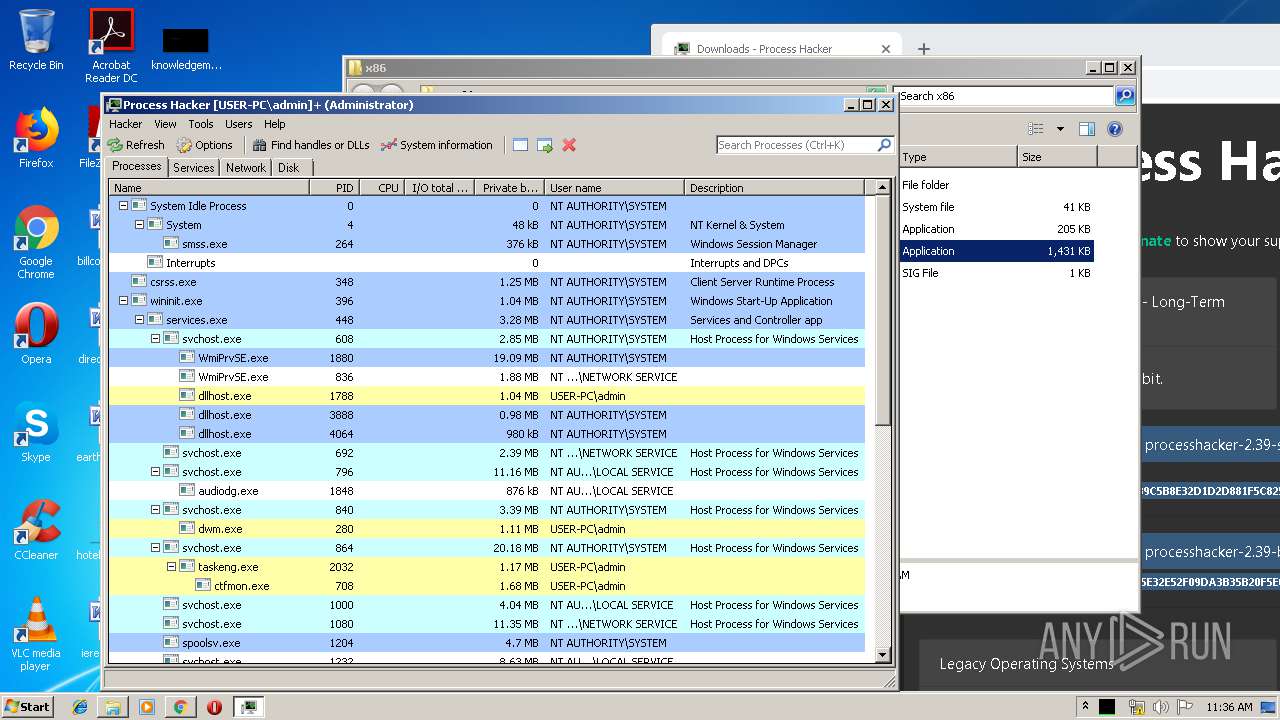
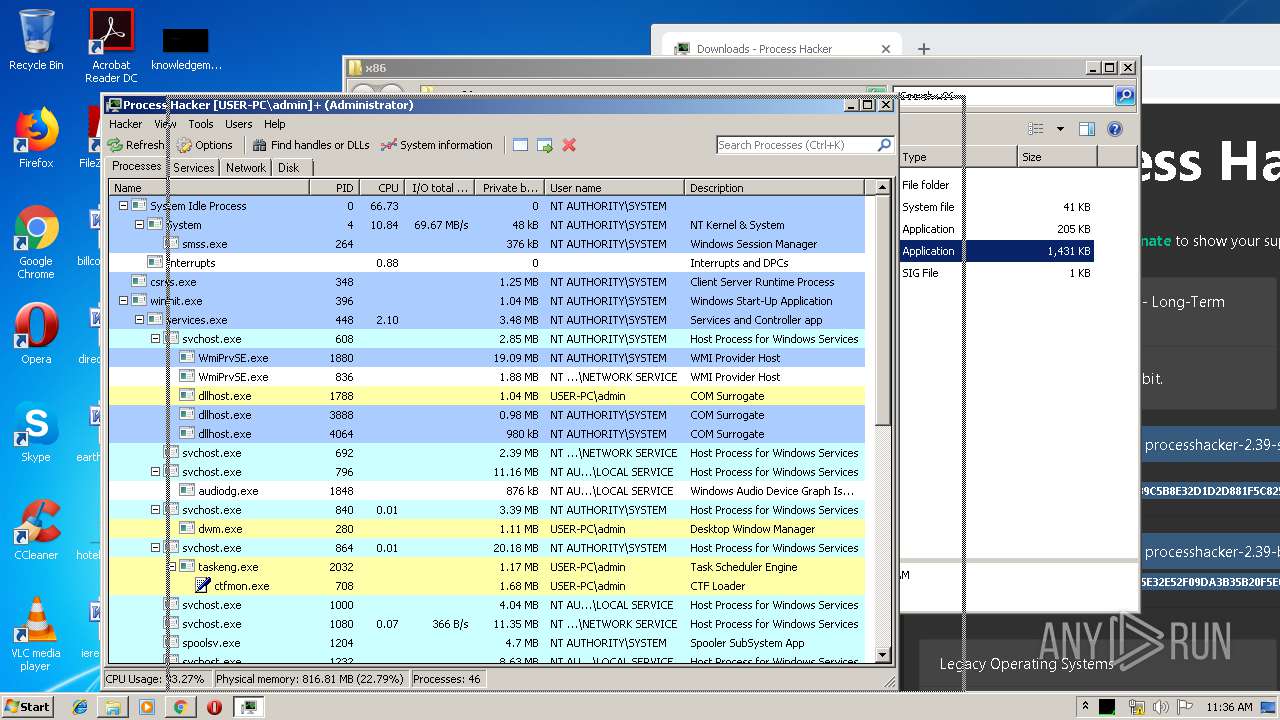
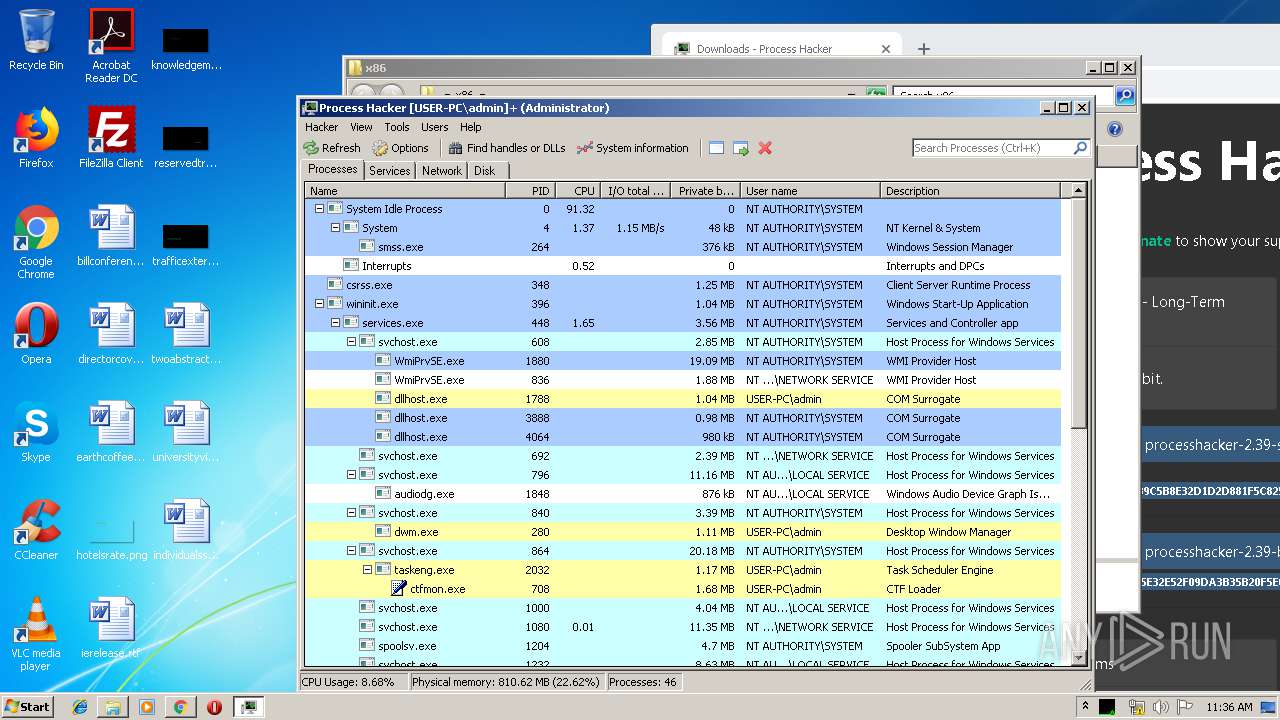
Changes settings of System certificates
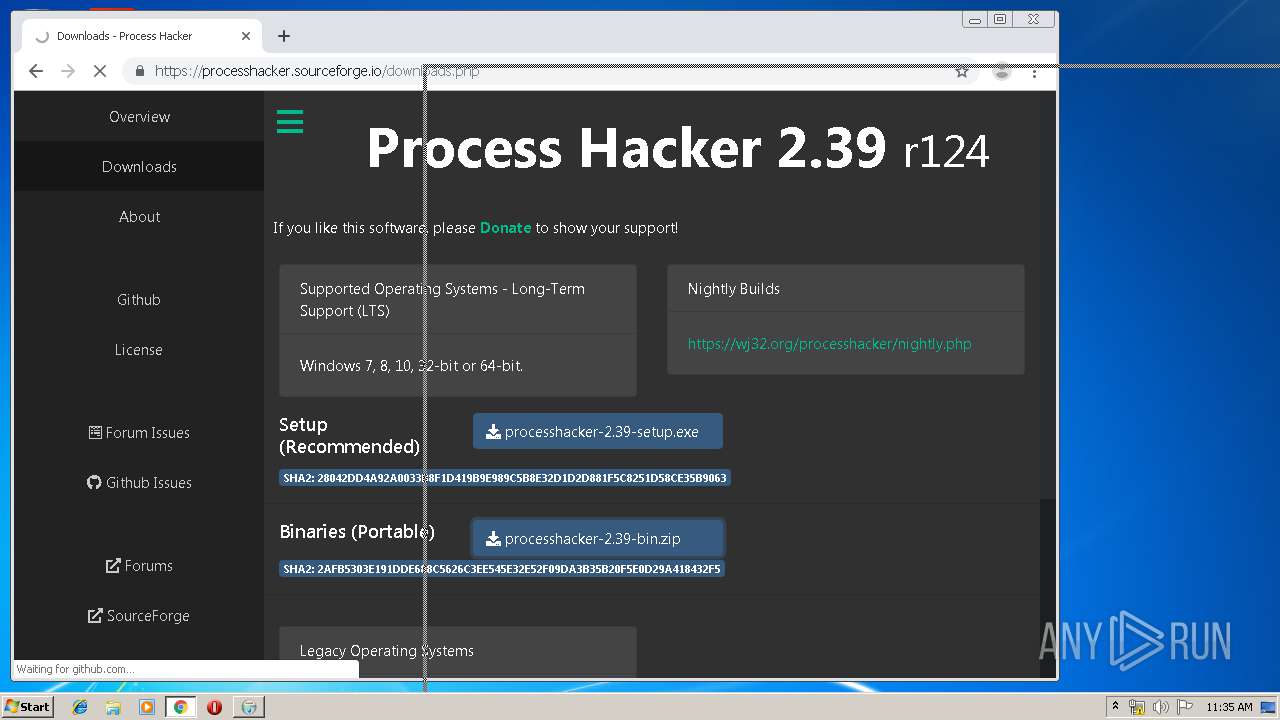
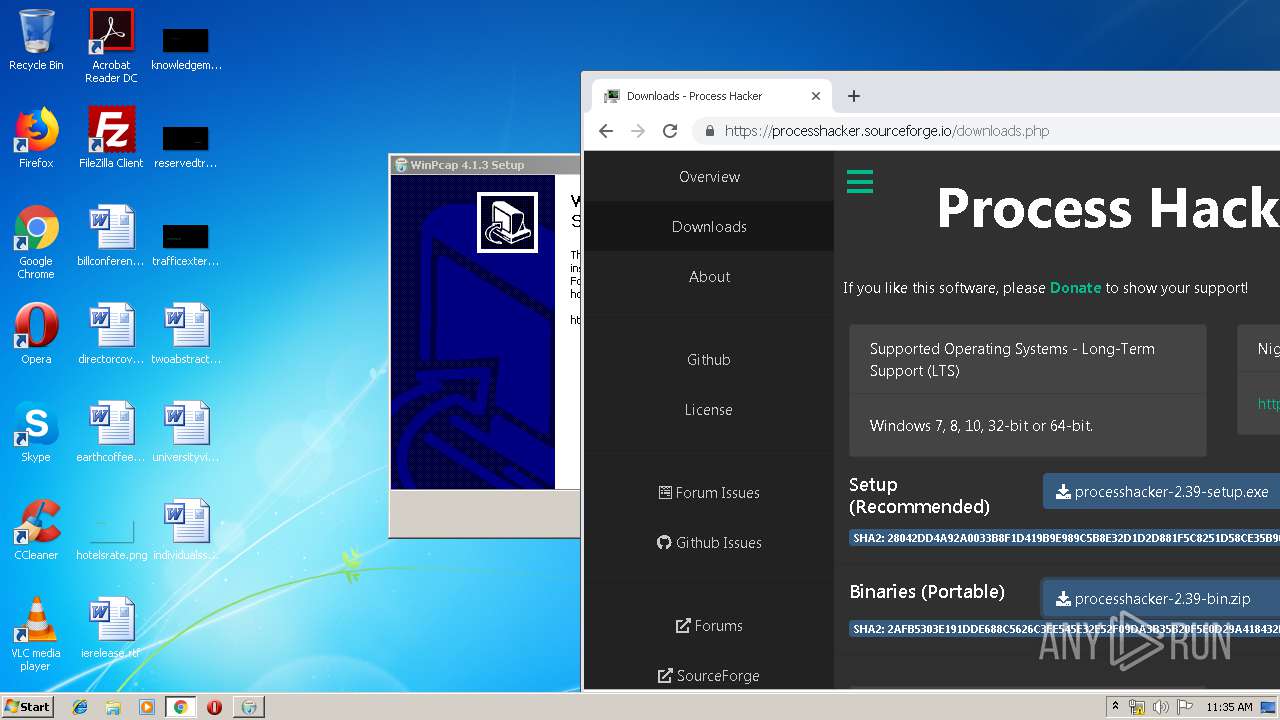
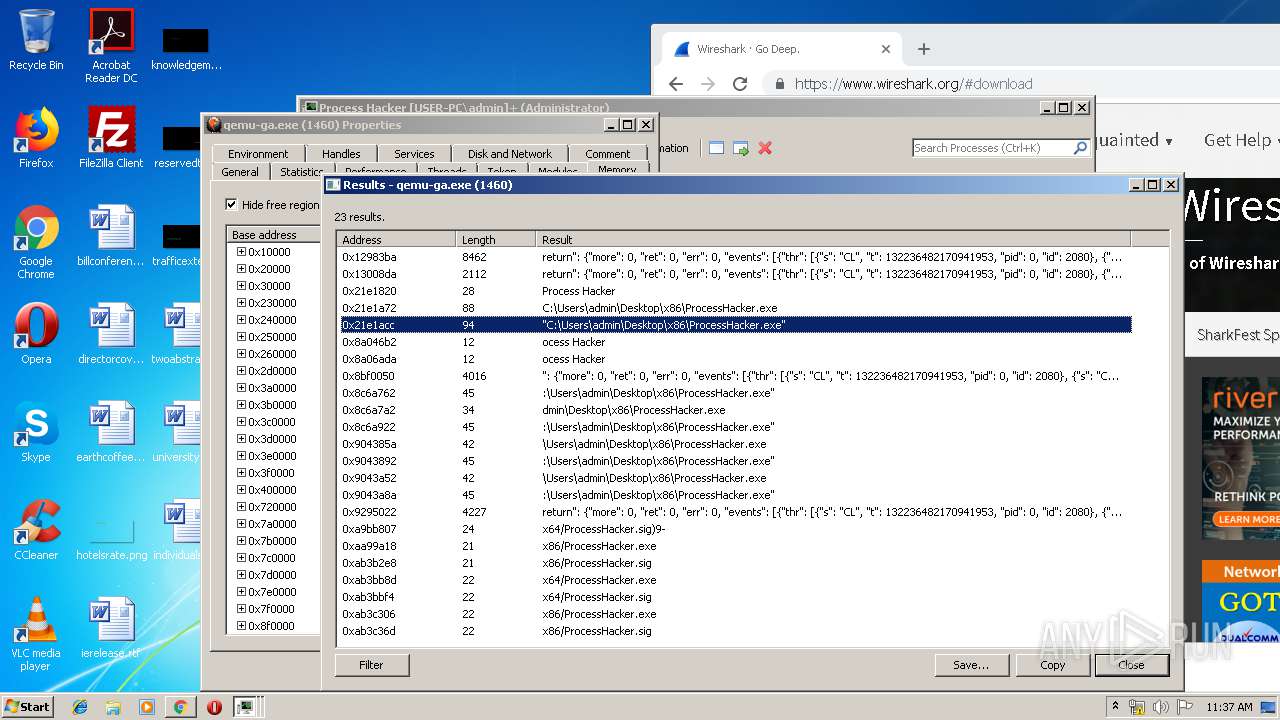
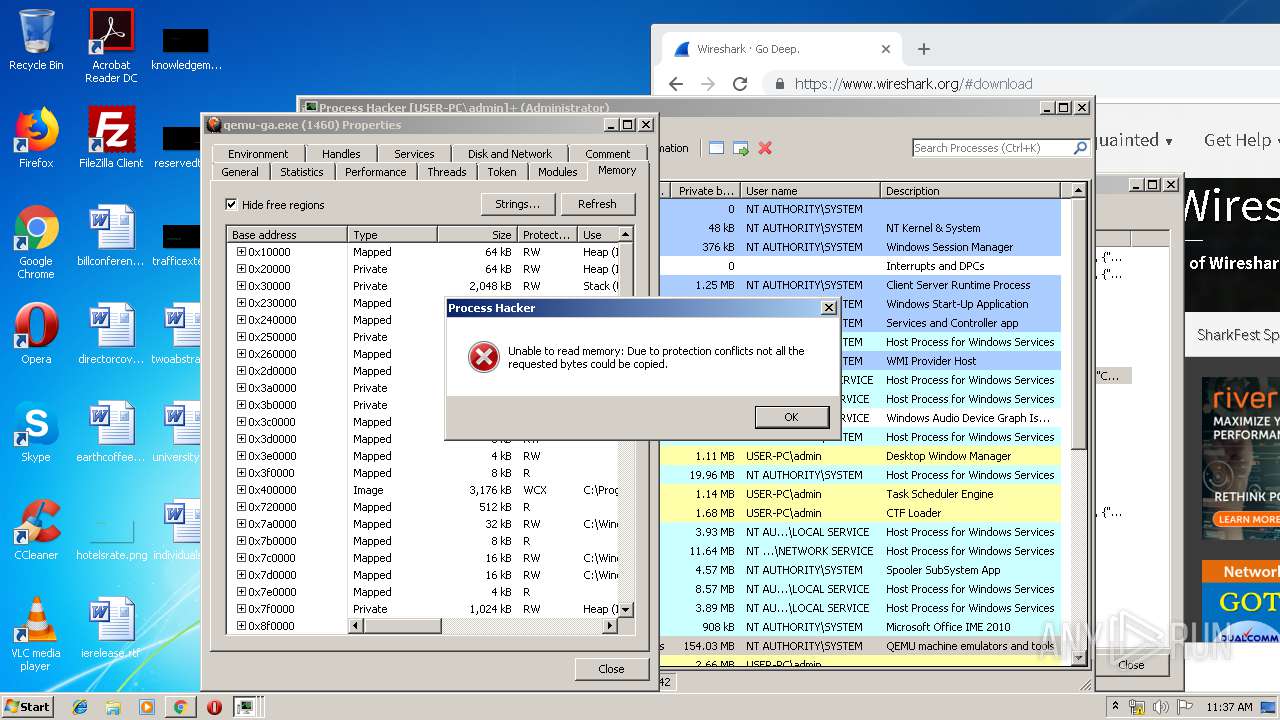
- ProcessHacker.exe (PID: 1944)
- msiexec.exe (PID: 1536)
- certutil.exe (PID: 3916)
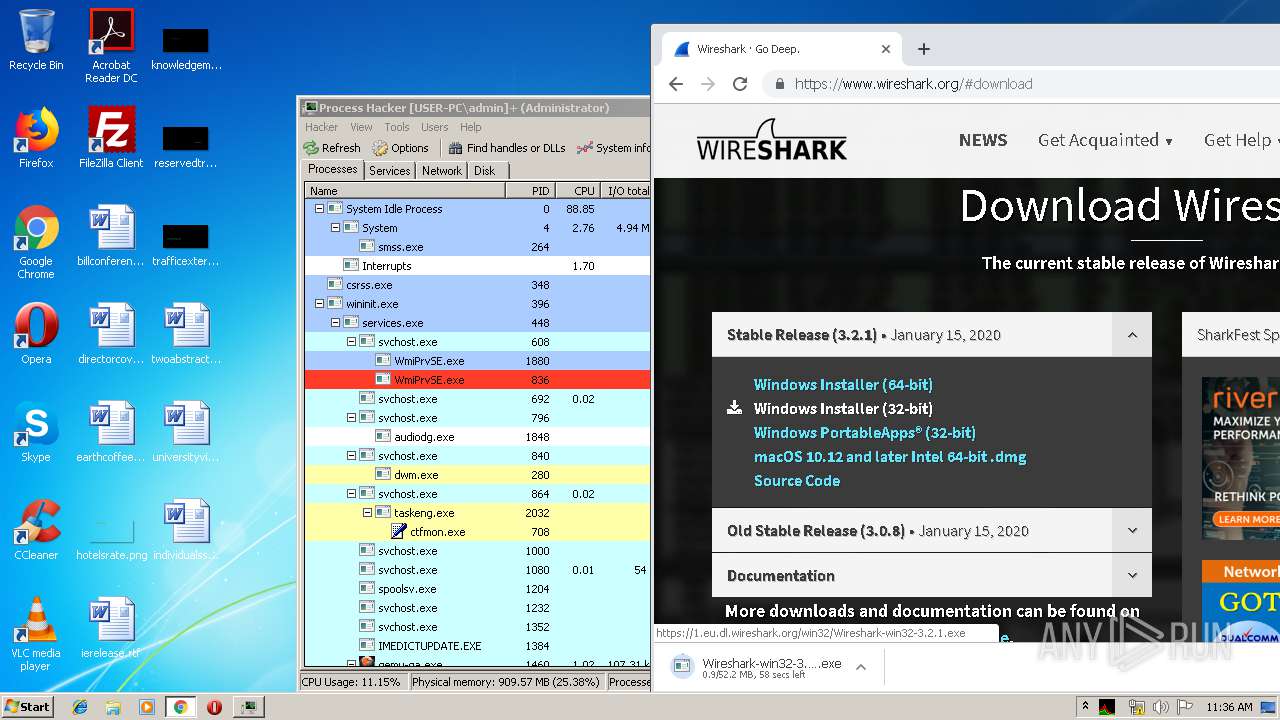
Application was dropped or rewritten from another process
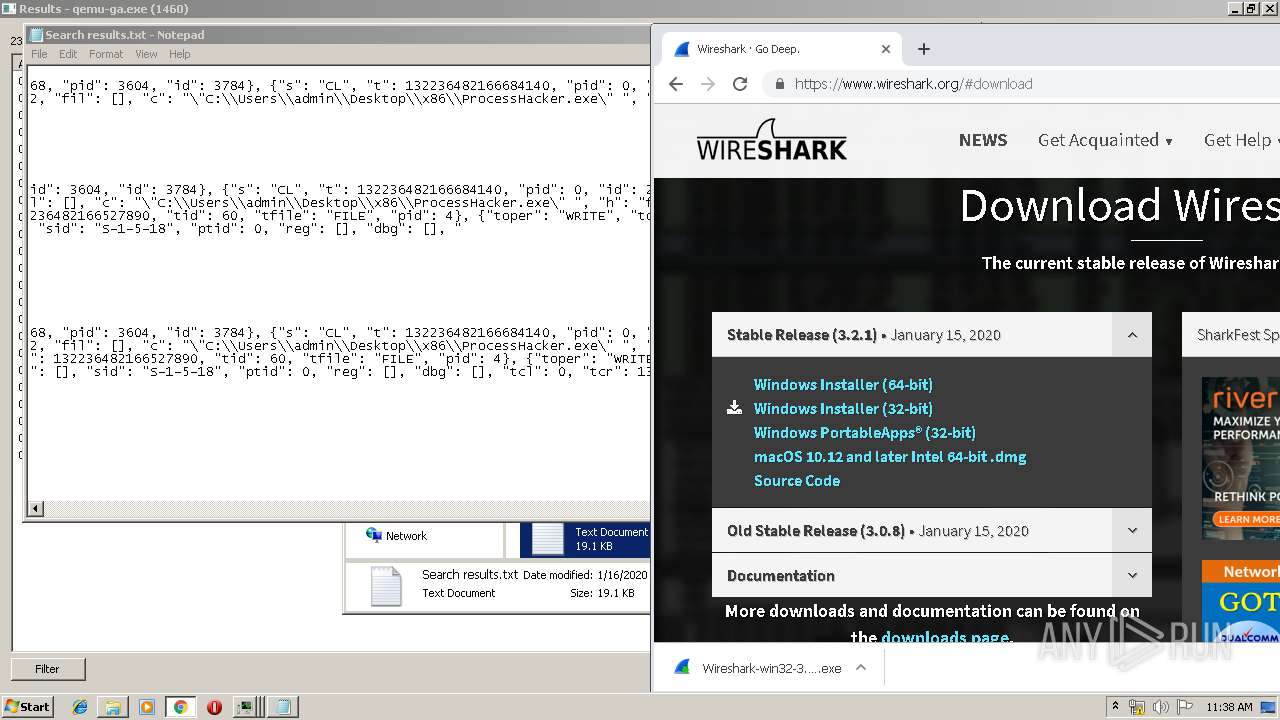
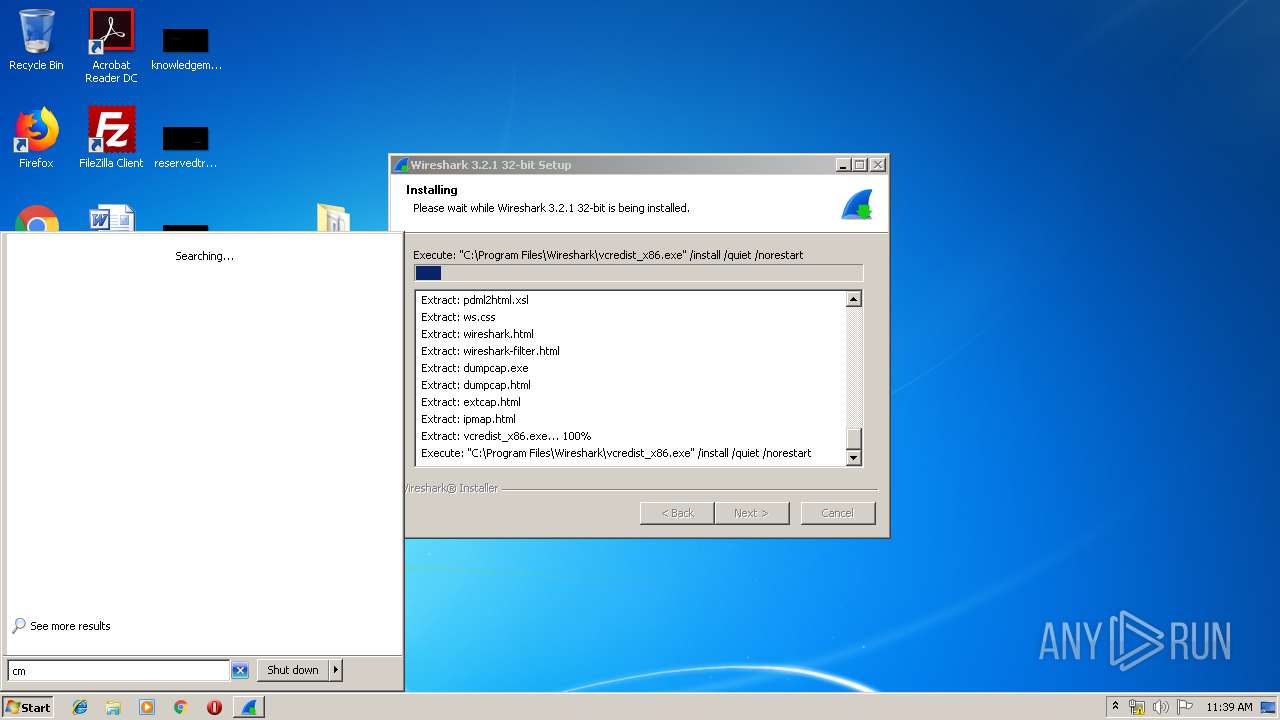
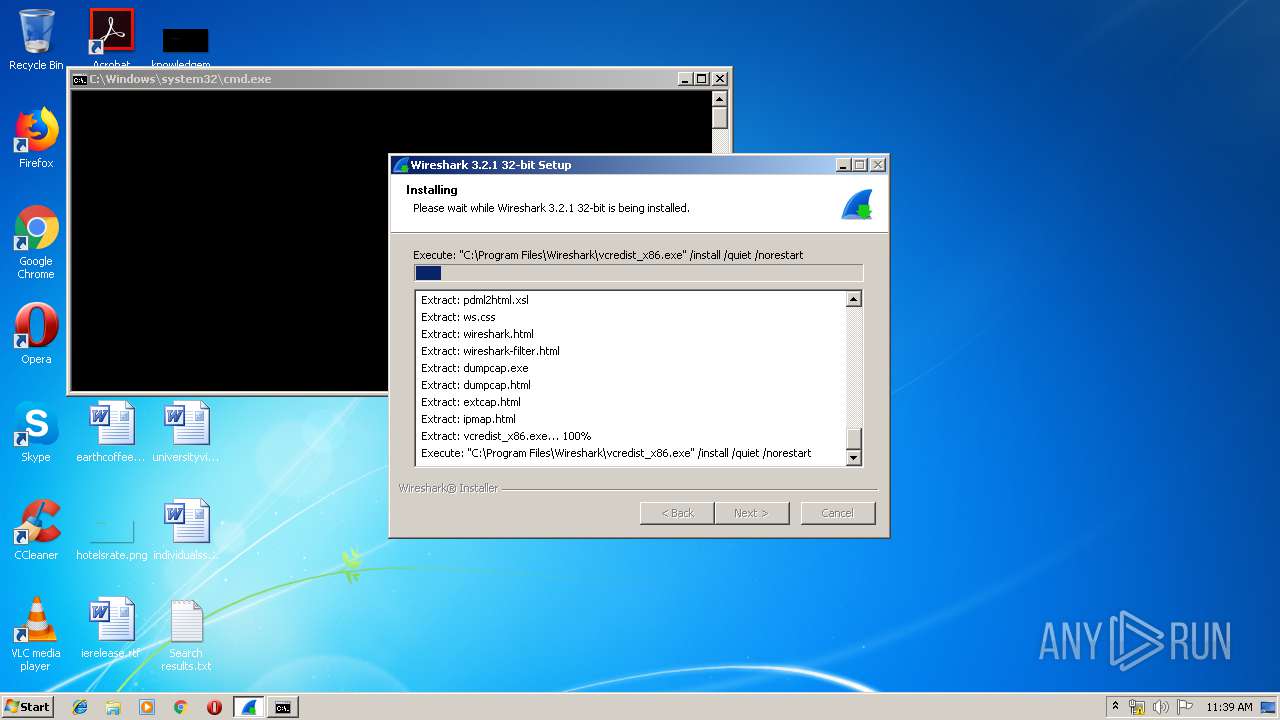
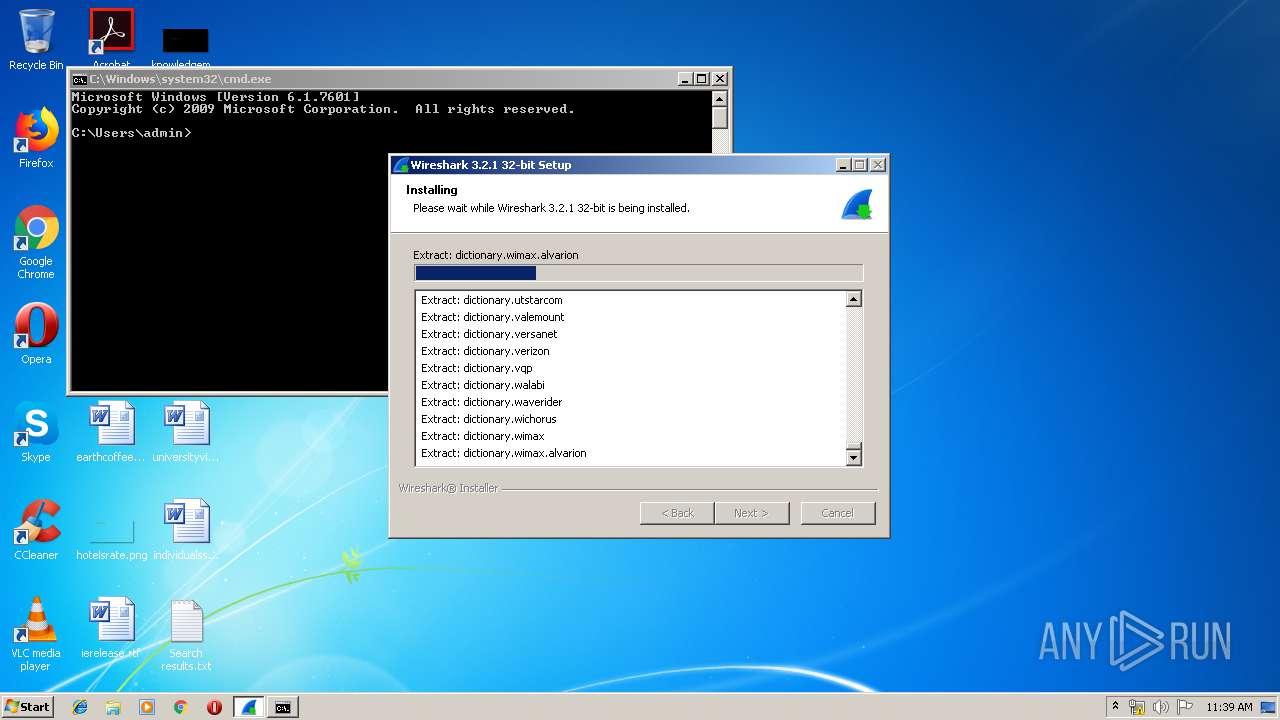
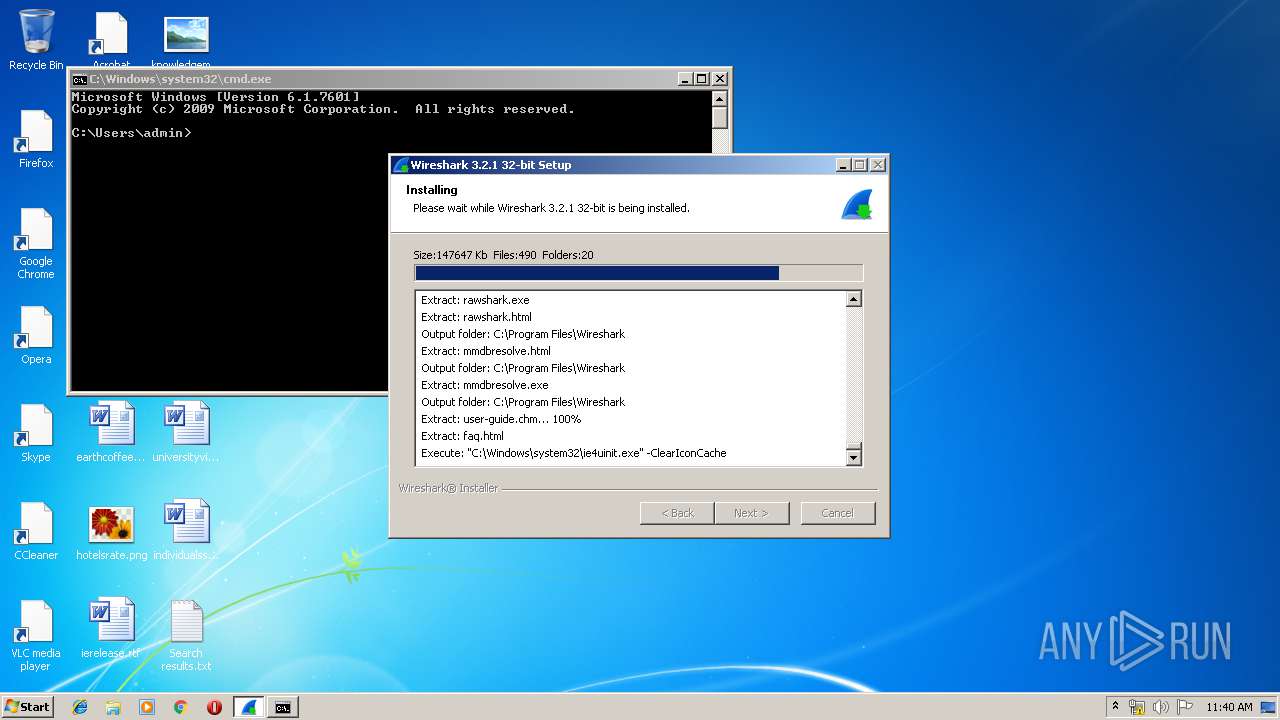
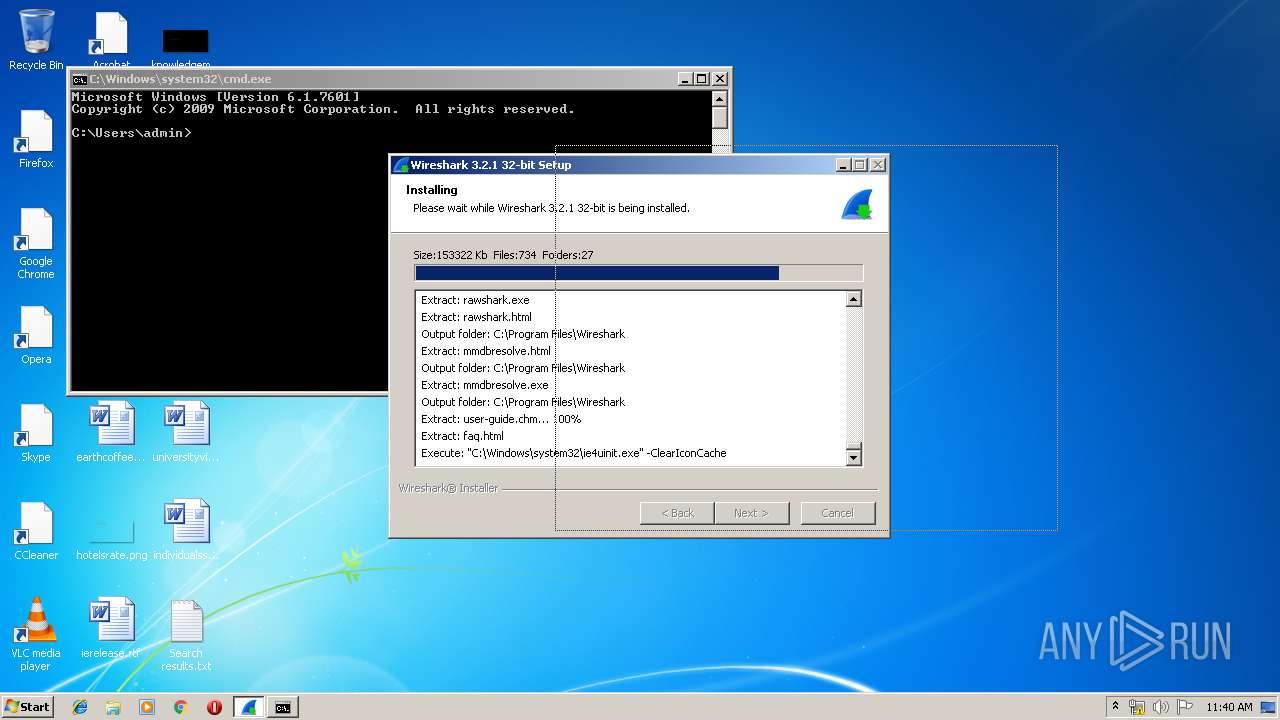
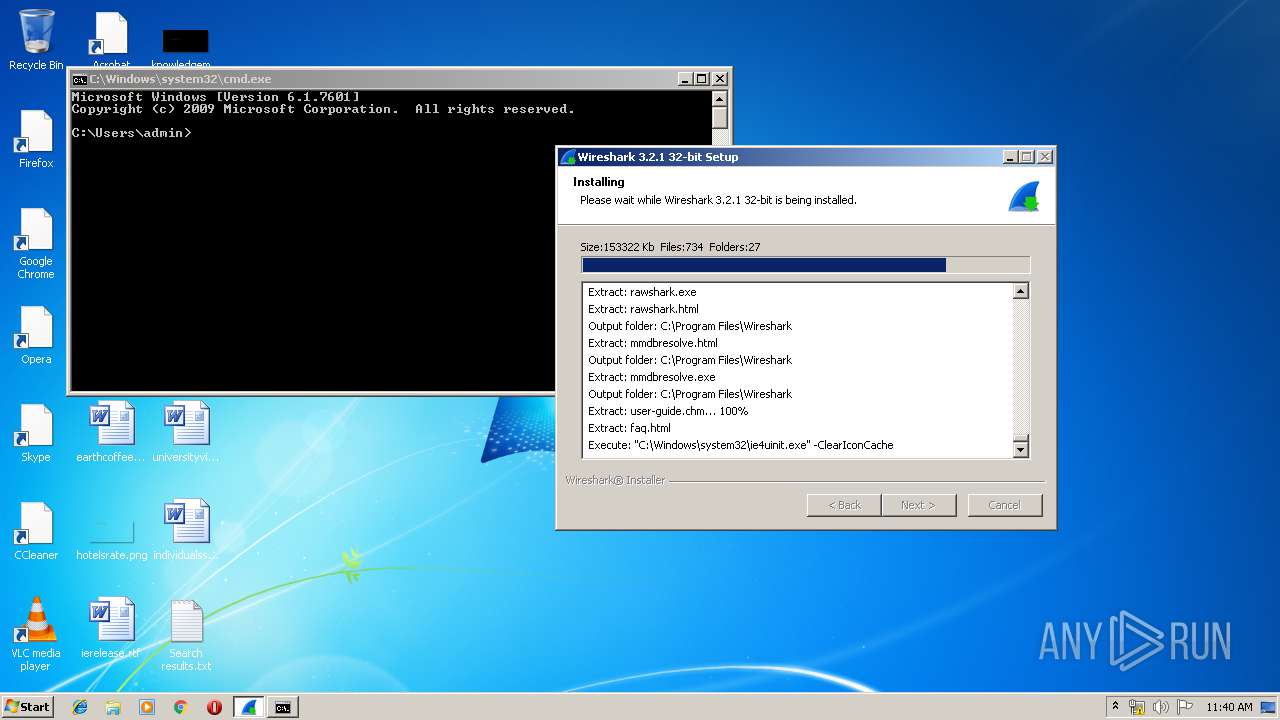
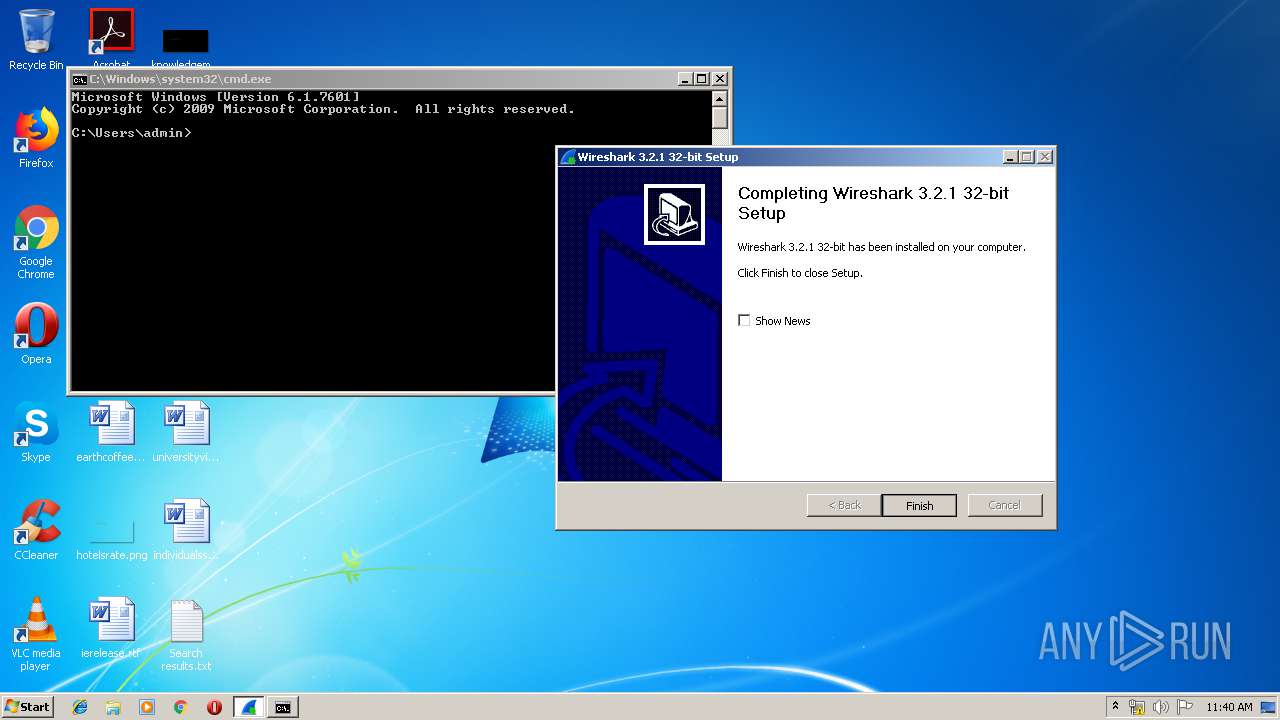
- Wireshark-win32-3.2.1.exe (PID: 1608)
- Wireshark-win32-3.2.1.exe (PID: 3632)
- vcredist_x86.exe (PID: 3568)
- vcredist_x86.exe (PID: 3808)
- VC_redist.x86.exe (PID: 2348)
- VC_redist.x86.exe (PID: 3228)
- VC_redist.x86.exe (PID: 2856)
- VC_redist.x86.exe (PID: 856)
- npcap-0.9986.exe (PID: 788)
- NPFInstall.exe (PID: 1600)
- NPFInstall.exe (PID: 2532)
- NPFInstall.exe (PID: 3948)
- ns9A2C.tmp (PID: 2616)
- ns9D3B.tmp (PID: 2640)
- ns9E26.tmp (PID: 3184)
- ns9B84.tmp (PID: 2244)
- dumpcap.exe (PID: 2884)
- nsEF54.tmp (PID: 2080)
- Wireshark.exe (PID: 444)
- dumpcap.exe (PID: 2136)
- dumpcap.exe (PID: 3004)
- dumpcap.exe (PID: 2356)
Changes the autorun value in the registry
- VC_redist.x86.exe (PID: 2348)
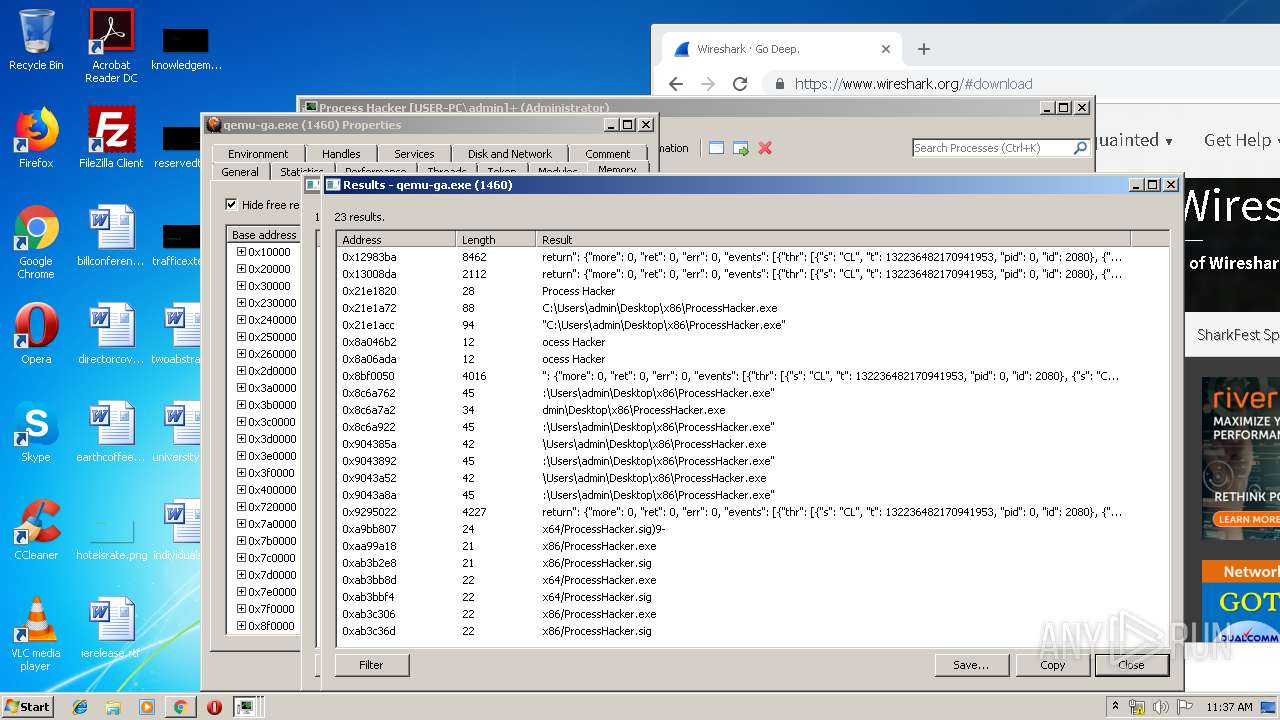
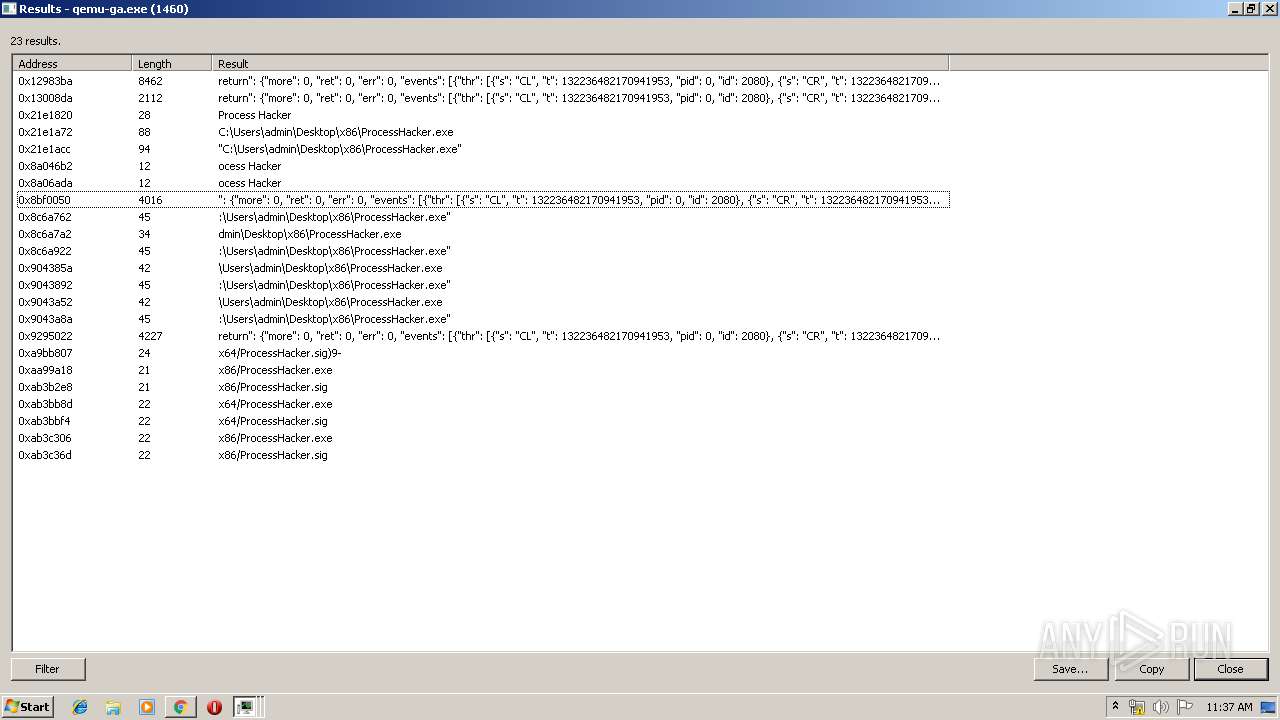
Uses Task Scheduler to run other applications
- nsEF54.tmp (PID: 2080)
Loads the Task Scheduler COM API
- SCHTASKS.EXE (PID: 3656)
SUSPICIOUS
Executable content was dropped or overwritten
- WinPcap_4_1_3.exe (PID: 3564)
- chrome.exe (PID: 1012)
- vcredist_x86.exe (PID: 3568)
- VC_redist.x86.exe (PID: 2348)
- Wireshark-win32-3.2.1.exe (PID: 1608)
- vcredist_x86.exe (PID: 3808)
- msiexec.exe (PID: 1536)
- VC_redist.x86.exe (PID: 2856)
- VC_redist.x86.exe (PID: 856)
- npcap-0.9986.exe (PID: 788)
- NPFInstall.exe (PID: 3948)
- DrvInst.exe (PID: 2380)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1012)
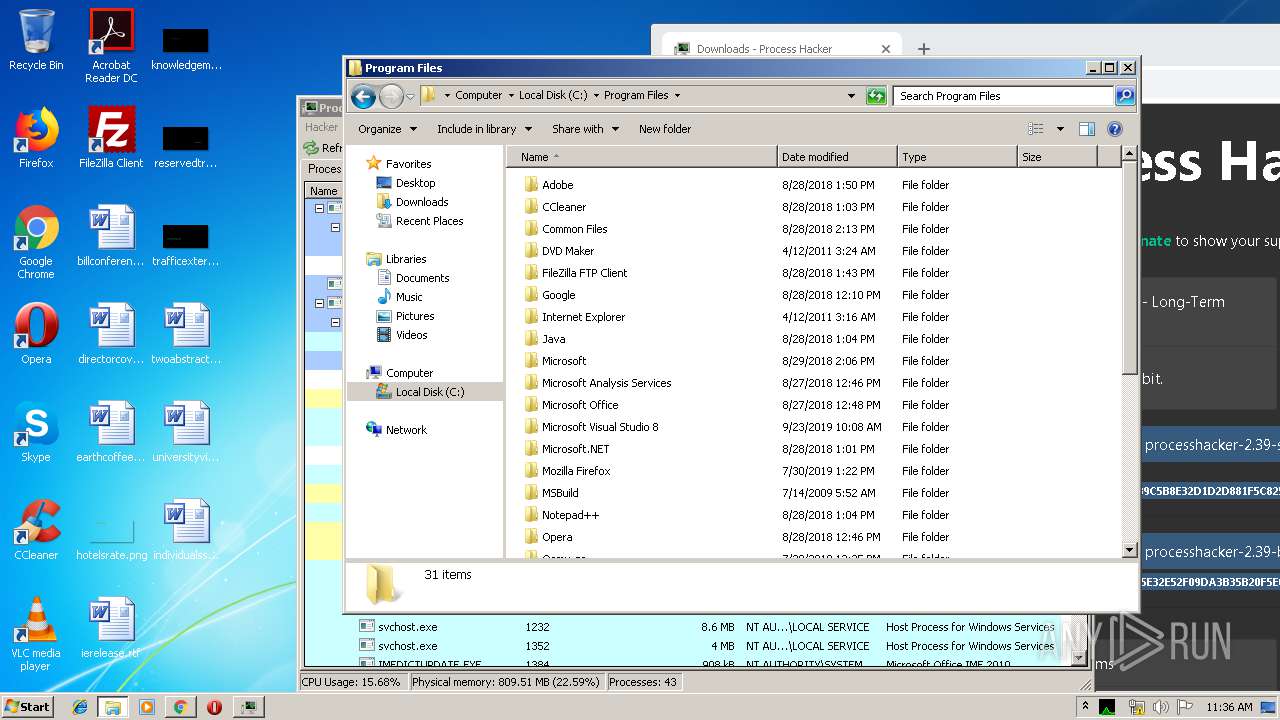
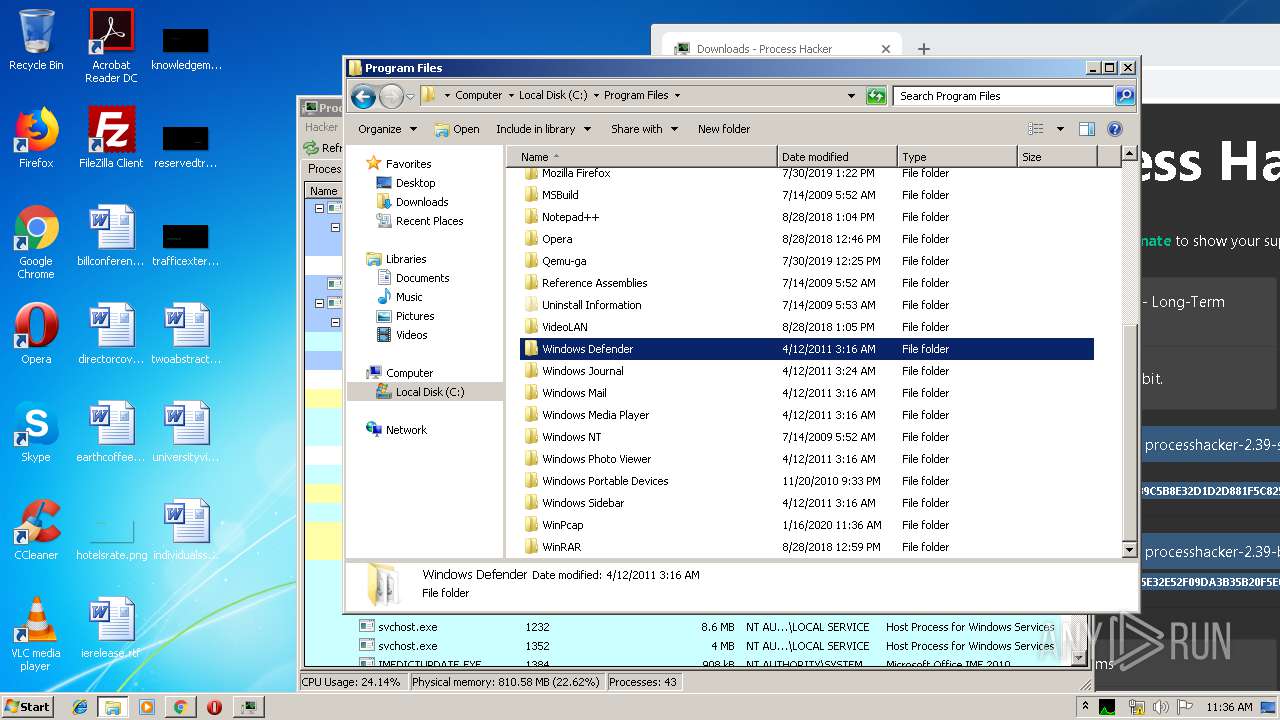
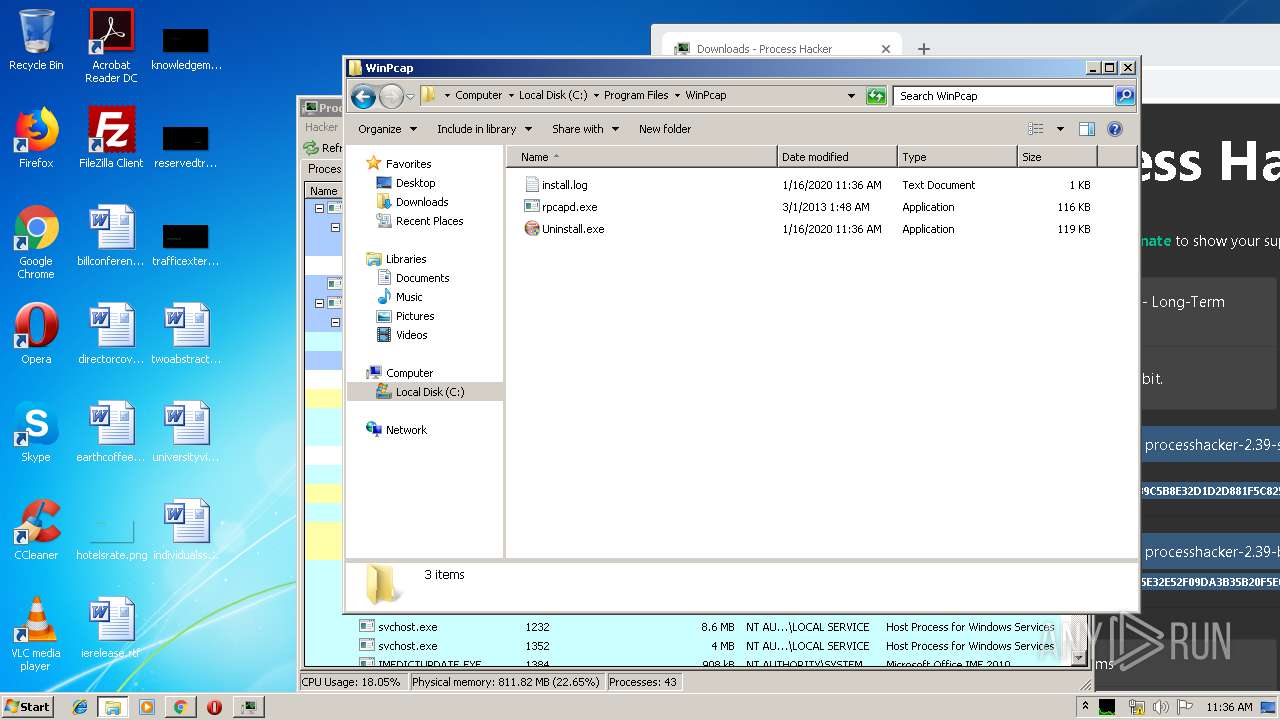
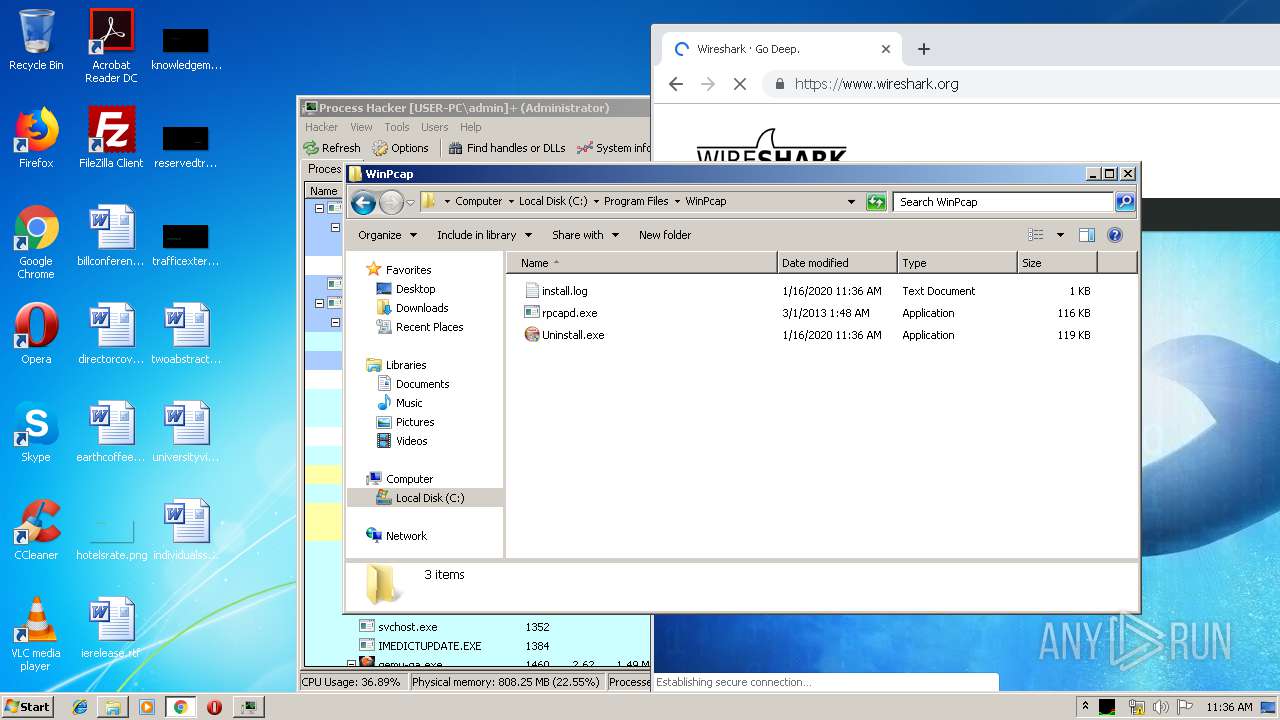
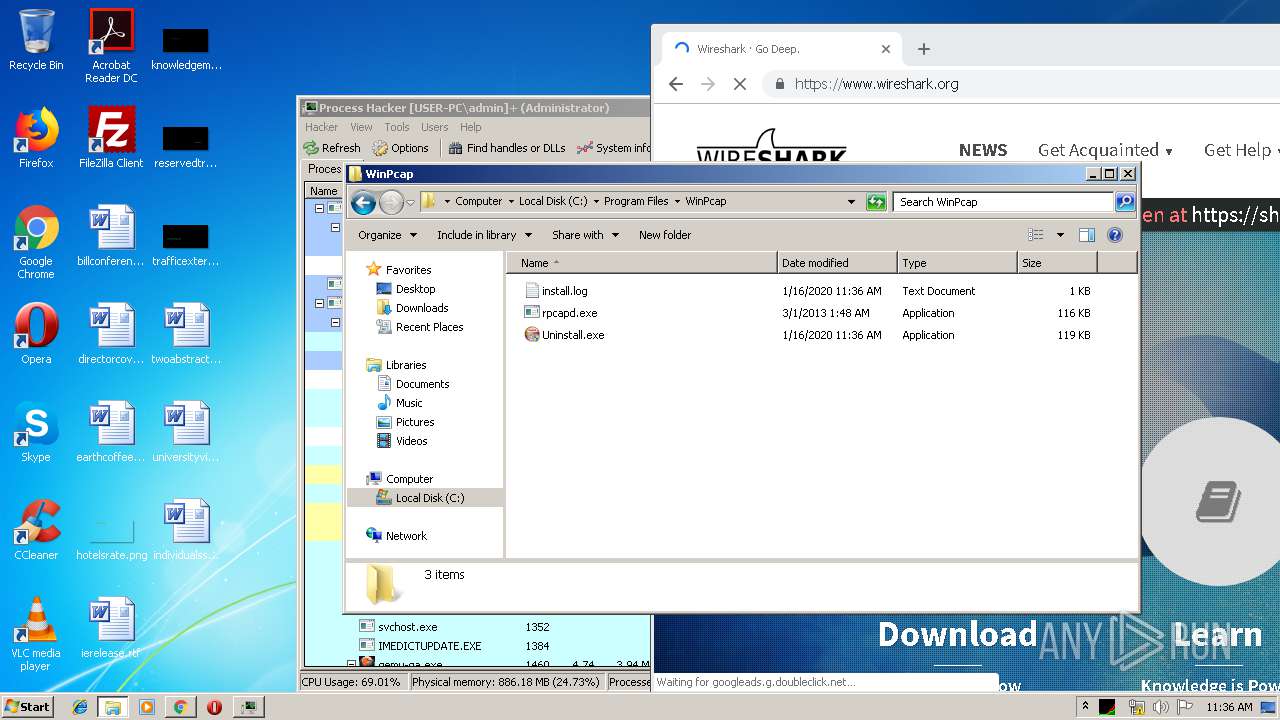
Creates files in the program directory
- WinPcap_4_1_3.exe (PID: 3564)
- VC_redist.x86.exe (PID: 2348)
- Wireshark-win32-3.2.1.exe (PID: 1608)
- npcap-0.9986.exe (PID: 788)
- NPFInstall.exe (PID: 1600)
Creates files in the Windows directory
- WinPcap_4_1_3.exe (PID: 3564)
- vcredist_x86.exe (PID: 3568)
- vcredist_x86.exe (PID: 3808)
- msiexec.exe (PID: 1536)
- VC_redist.x86.exe (PID: 2856)
- npcap-0.9986.exe (PID: 788)
- certutil.exe (PID: 3916)
- pnputil.exe (PID: 3872)
- DrvInst.exe (PID: 2380)
- NPFInstall.exe (PID: 3948)
Creates or modifies windows services
- WinPcap_4_1_3.exe (PID: 3564)
- npcap-0.9986.exe (PID: 788)
Creates files in the driver directory
- WinPcap_4_1_3.exe (PID: 3564)
- DrvInst.exe (PID: 2380)
- NPFInstall.exe (PID: 3948)
Creates a software uninstall entry
- WinPcap_4_1_3.exe (PID: 3564)
- VC_redist.x86.exe (PID: 2348)
- VC_redist.x86.exe (PID: 856)
- Wireshark-win32-3.2.1.exe (PID: 1608)
- npcap-0.9986.exe (PID: 788)
Adds / modifies Windows certificates
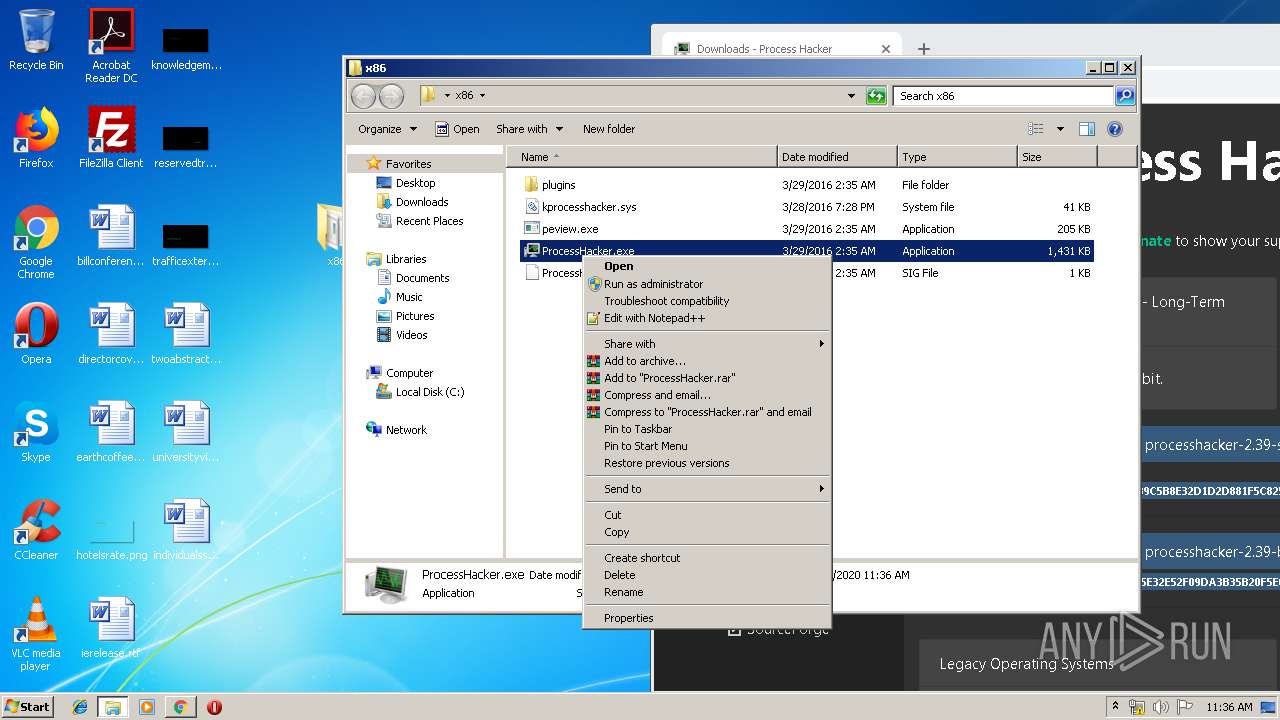
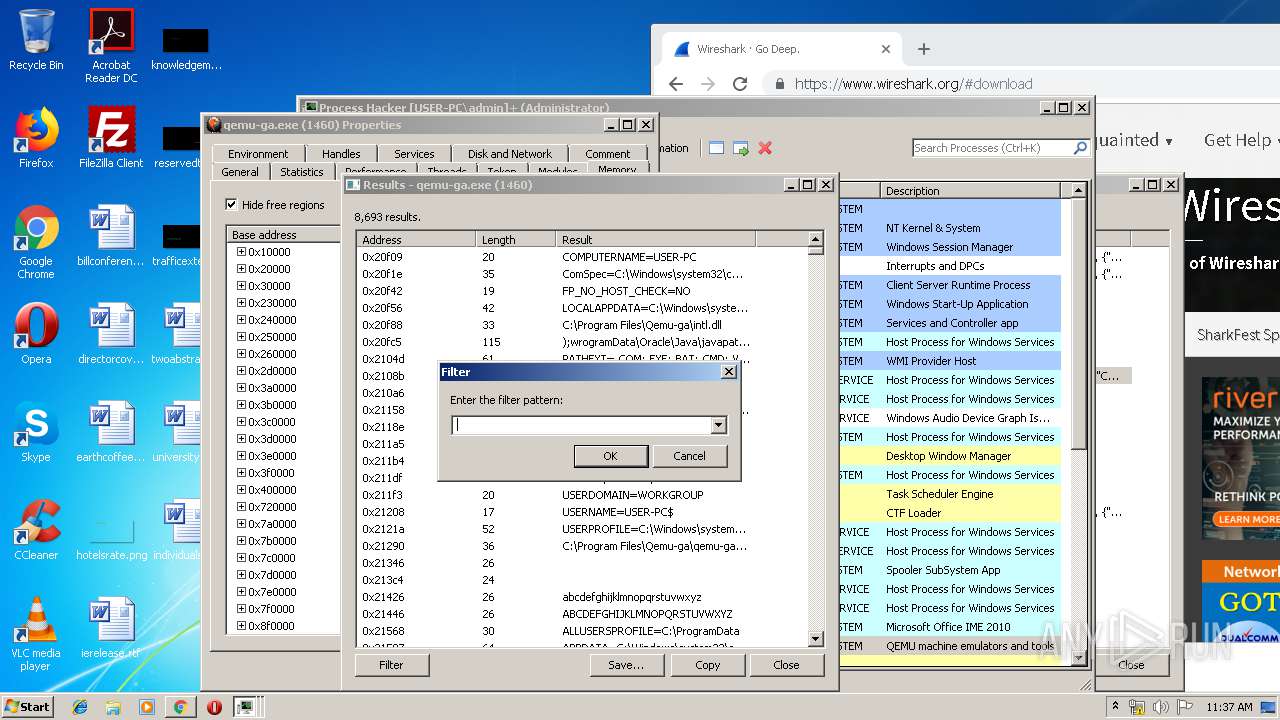
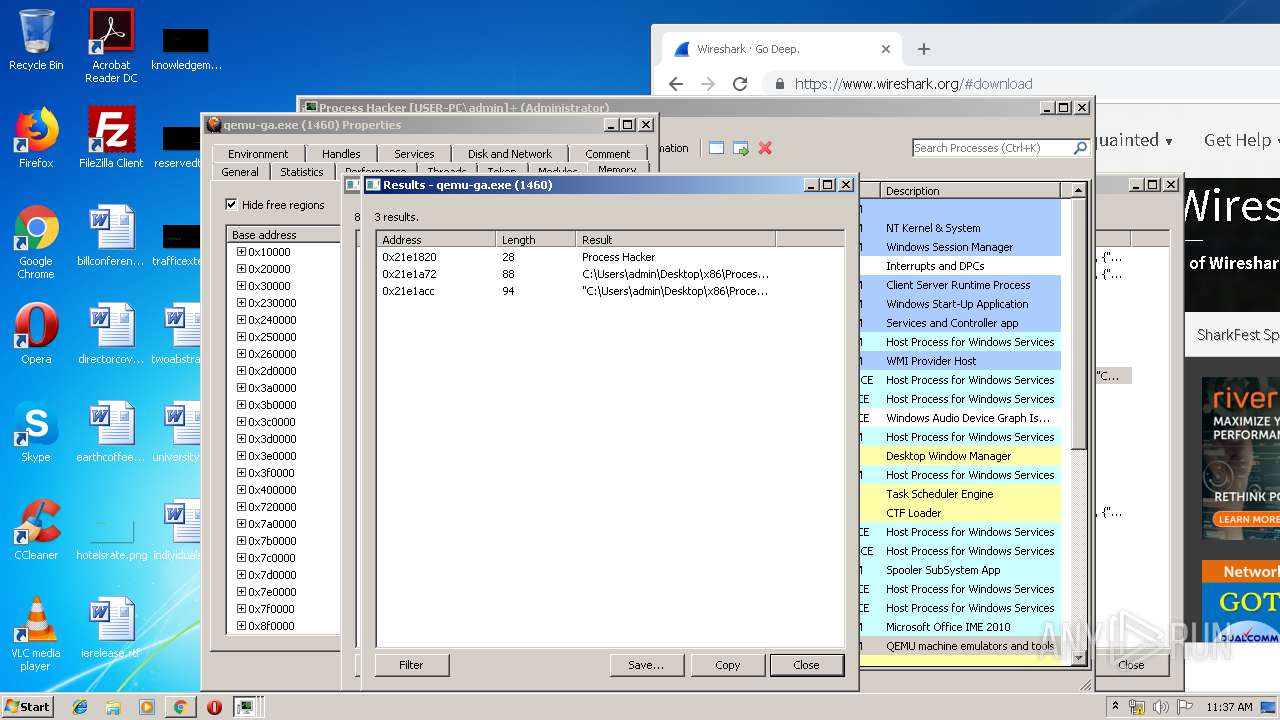
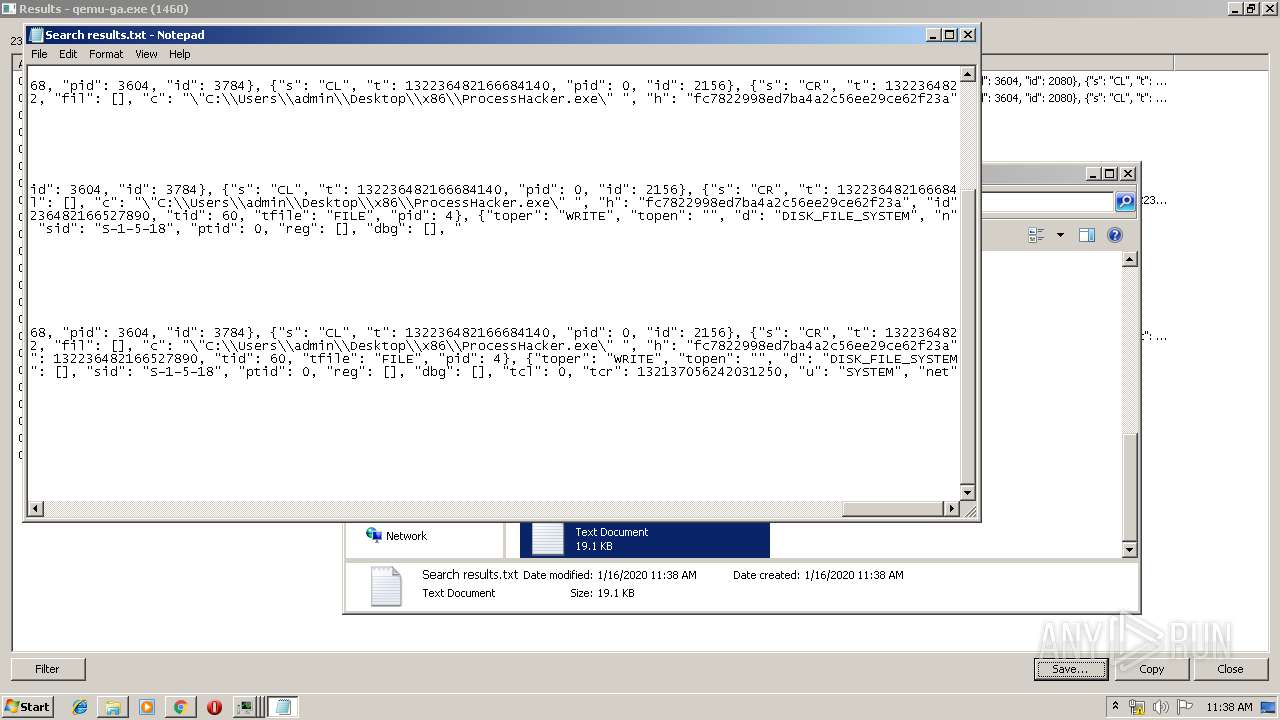
- ProcessHacker.exe (PID: 1944)
- msiexec.exe (PID: 1536)
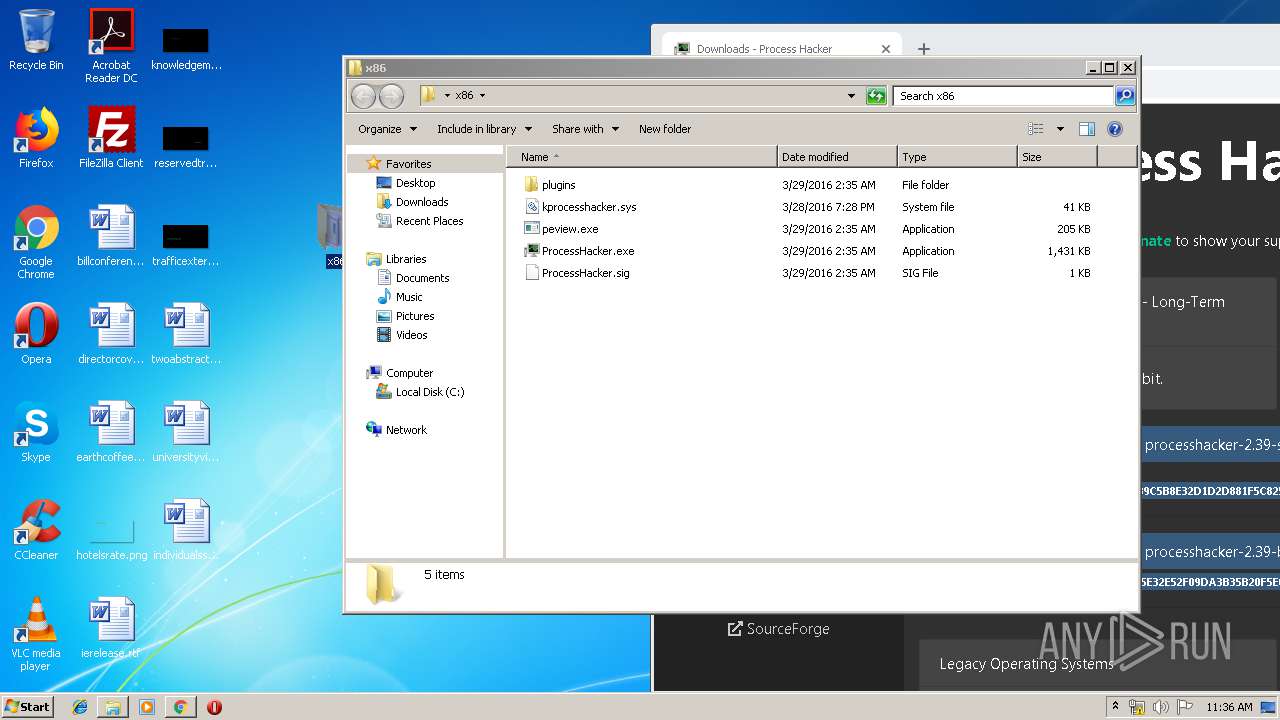
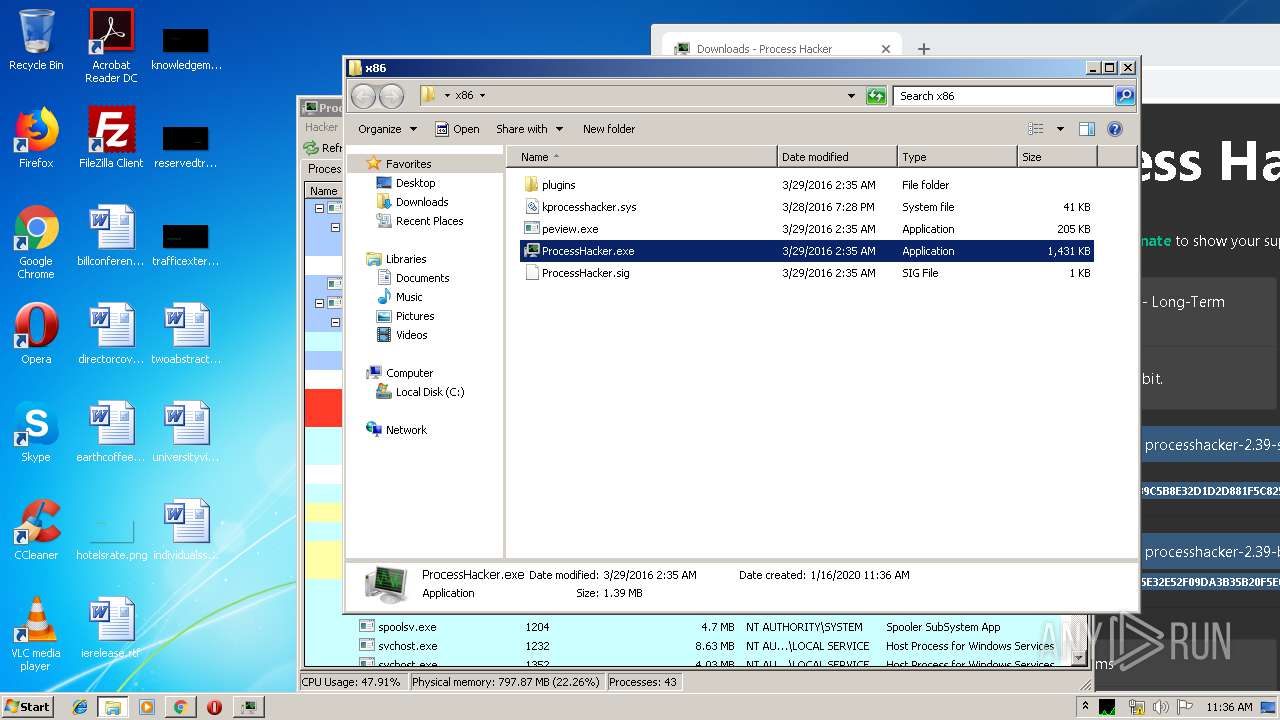
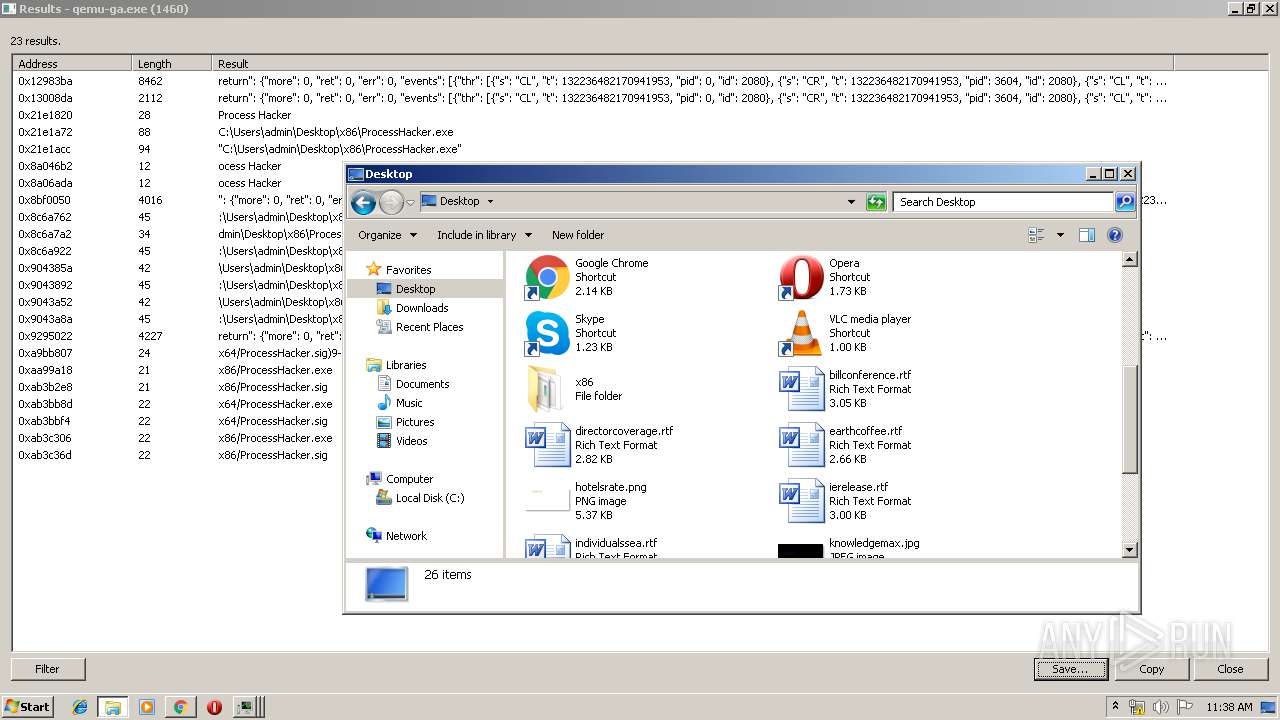
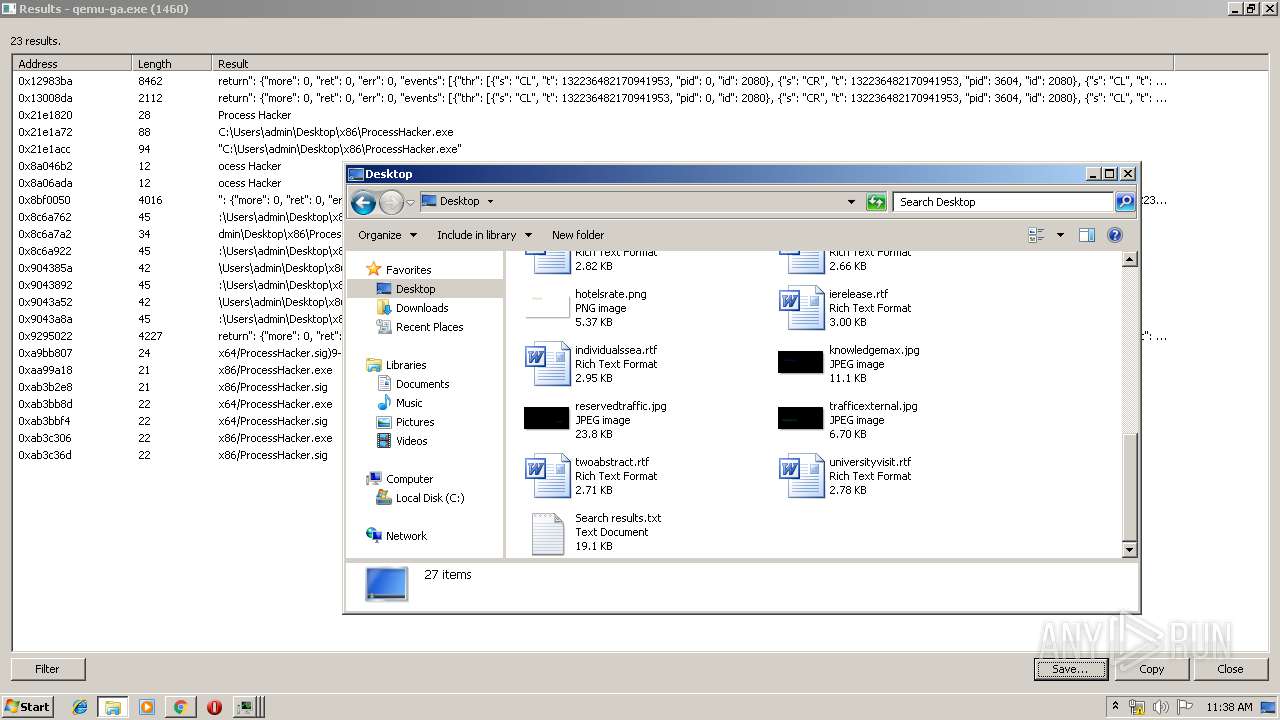
Creates files in the user directory
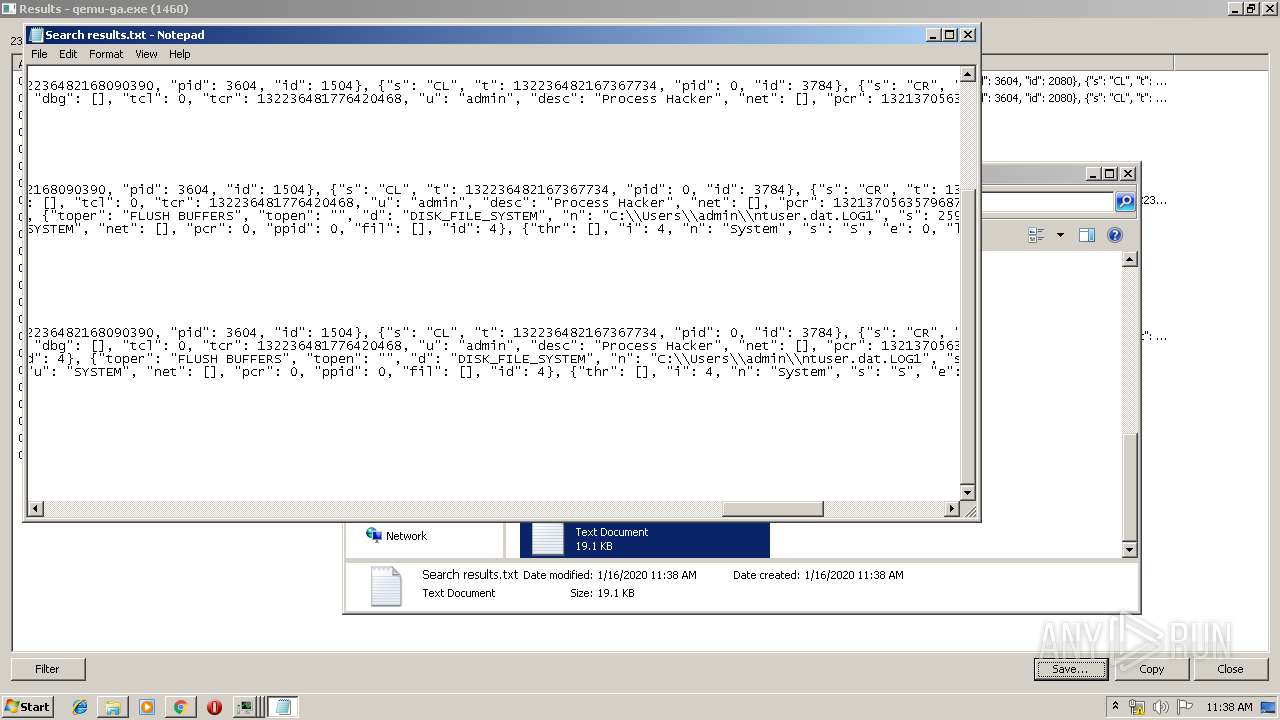
- ProcessHacker.exe (PID: 1944)
- Wireshark-win32-3.2.1.exe (PID: 1608)
Searches for installed software
- VC_redist.x86.exe (PID: 2348)
Executed as Windows Service
- vssvc.exe (PID: 2344)
Starts itself from another location
- vcredist_x86.exe (PID: 3808)
Application launched itself
- VC_redist.x86.exe (PID: 3228)
- VC_redist.x86.exe (PID: 2856)
Removes files from Windows directory
- vcredist_x86.exe (PID: 3808)
- vcredist_x86.exe (PID: 3568)
- VC_redist.x86.exe (PID: 2856)
- certutil.exe (PID: 3916)
- DrvInst.exe (PID: 2380)
- NPFInstall.exe (PID: 3948)
Modifies the open verb of a shell class
- Wireshark-win32-3.2.1.exe (PID: 1608)
Starts application with an unusual extension
- npcap-0.9986.exe (PID: 788)
Executed via COM
- DrvInst.exe (PID: 2380)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2380)
INFO
Reads the hosts file
- chrome.exe (PID: 3736)
- chrome.exe (PID: 1012)
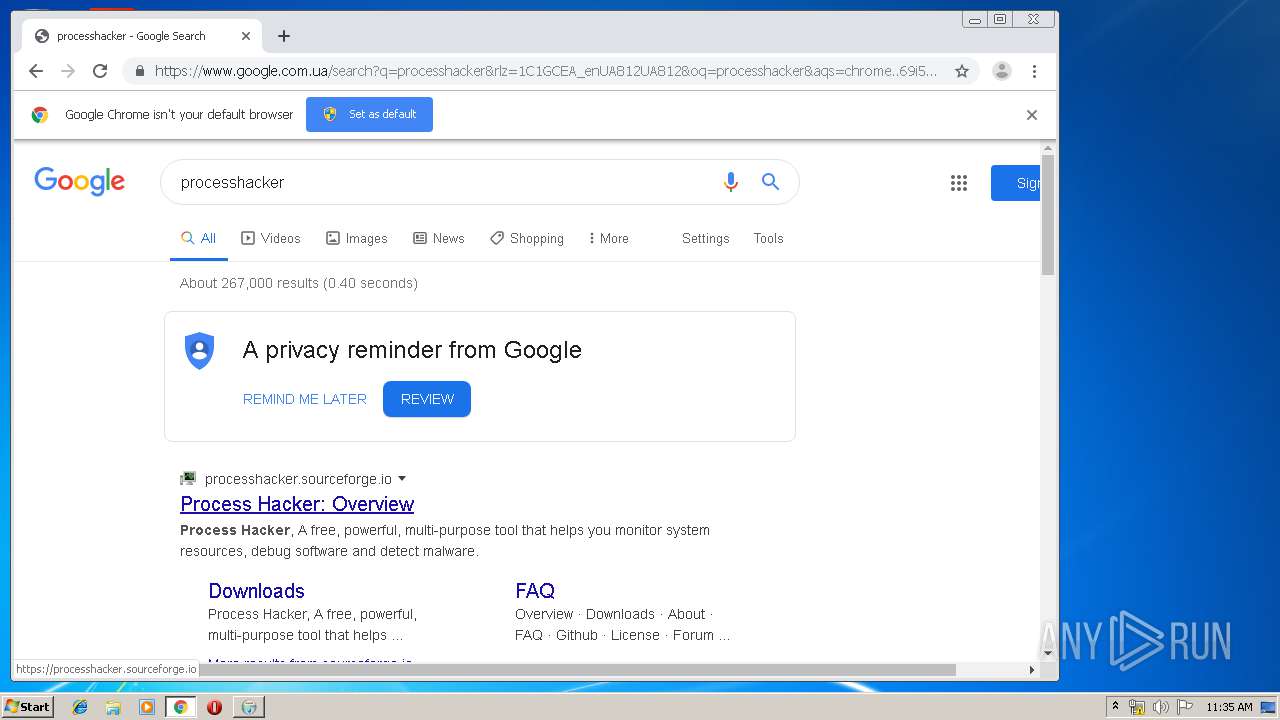
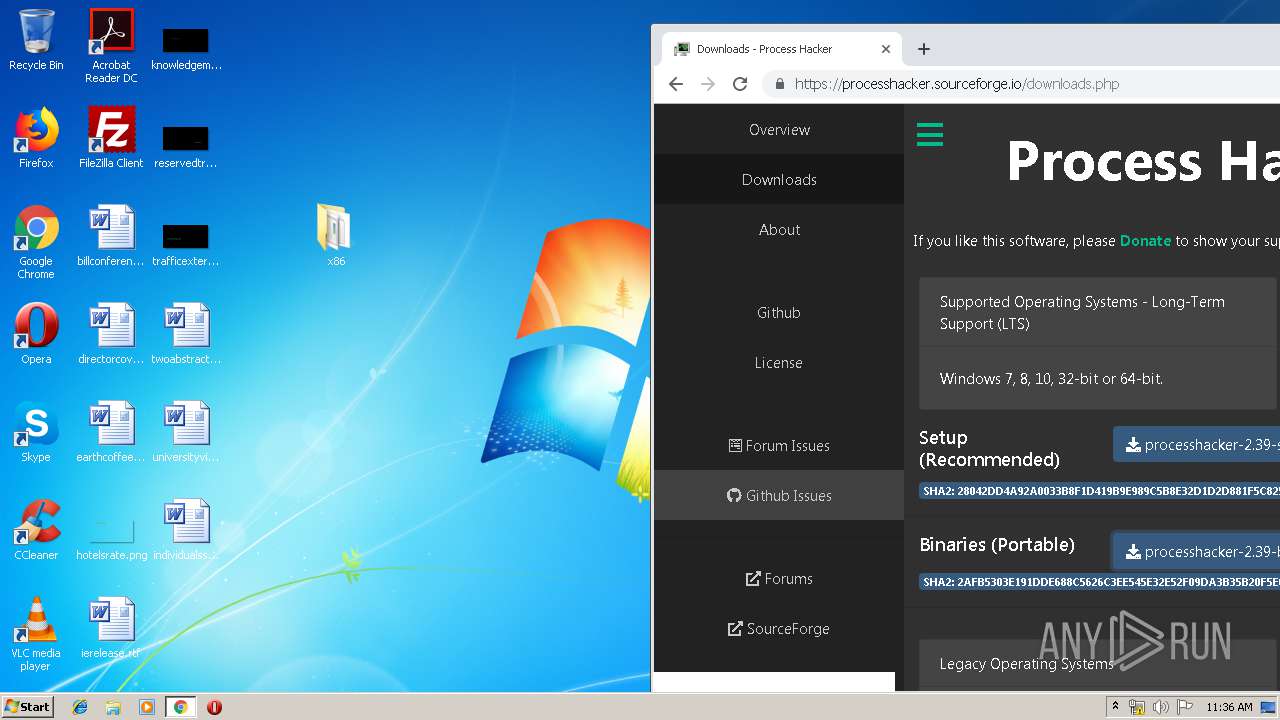
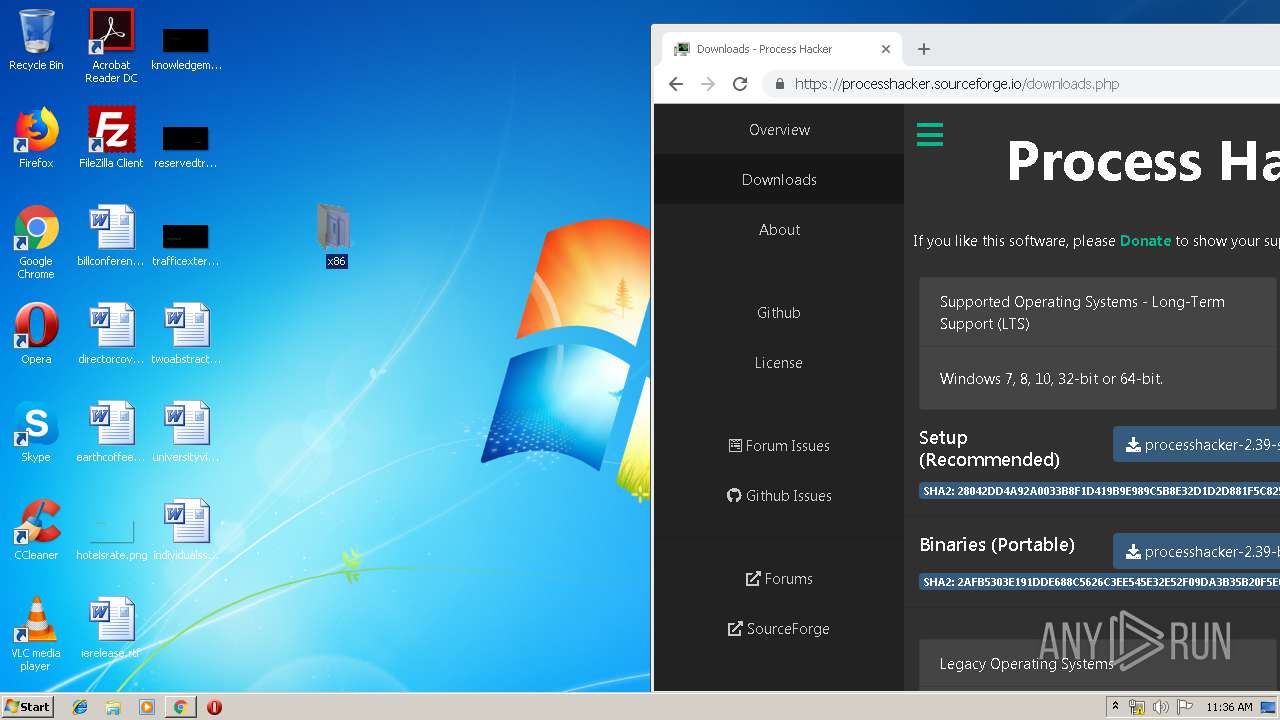
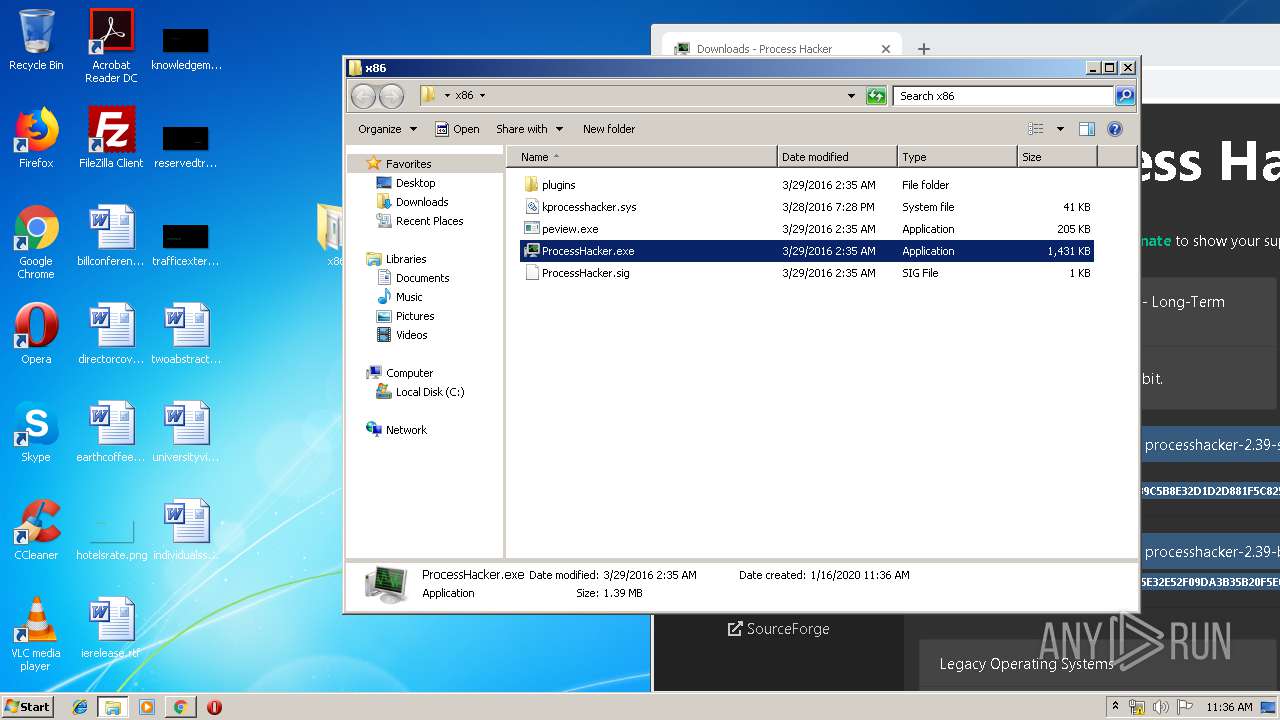
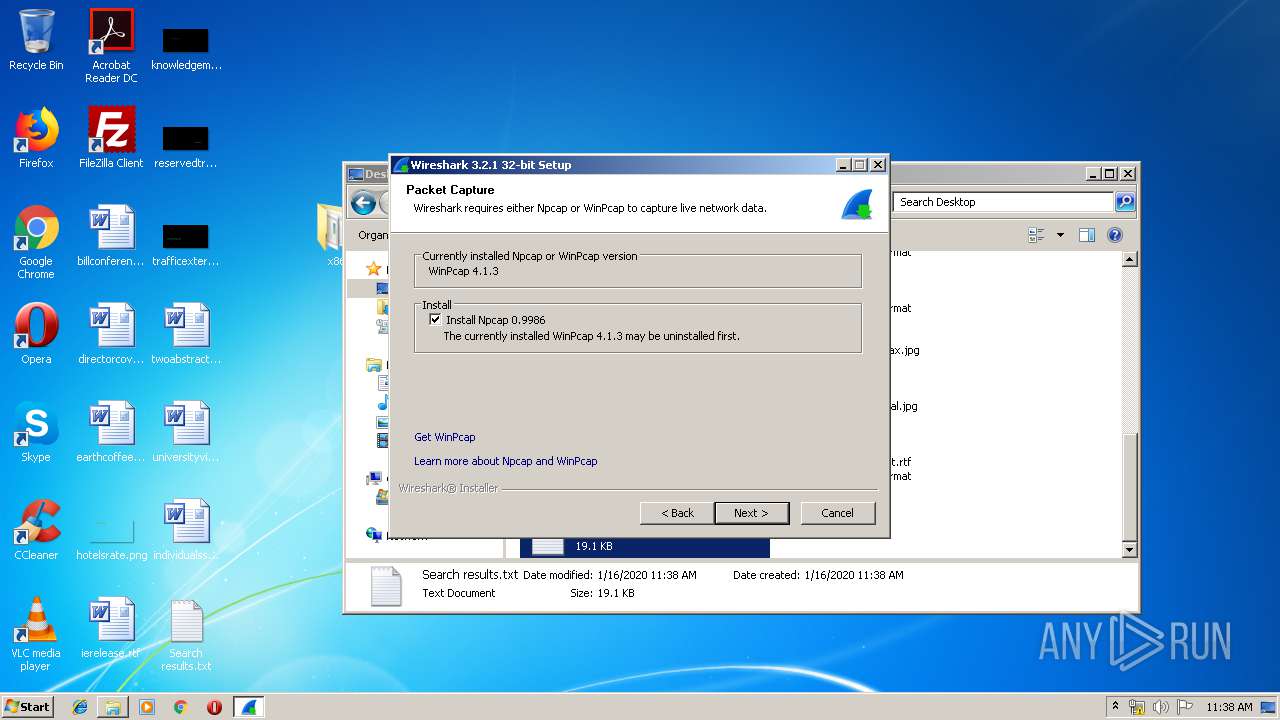
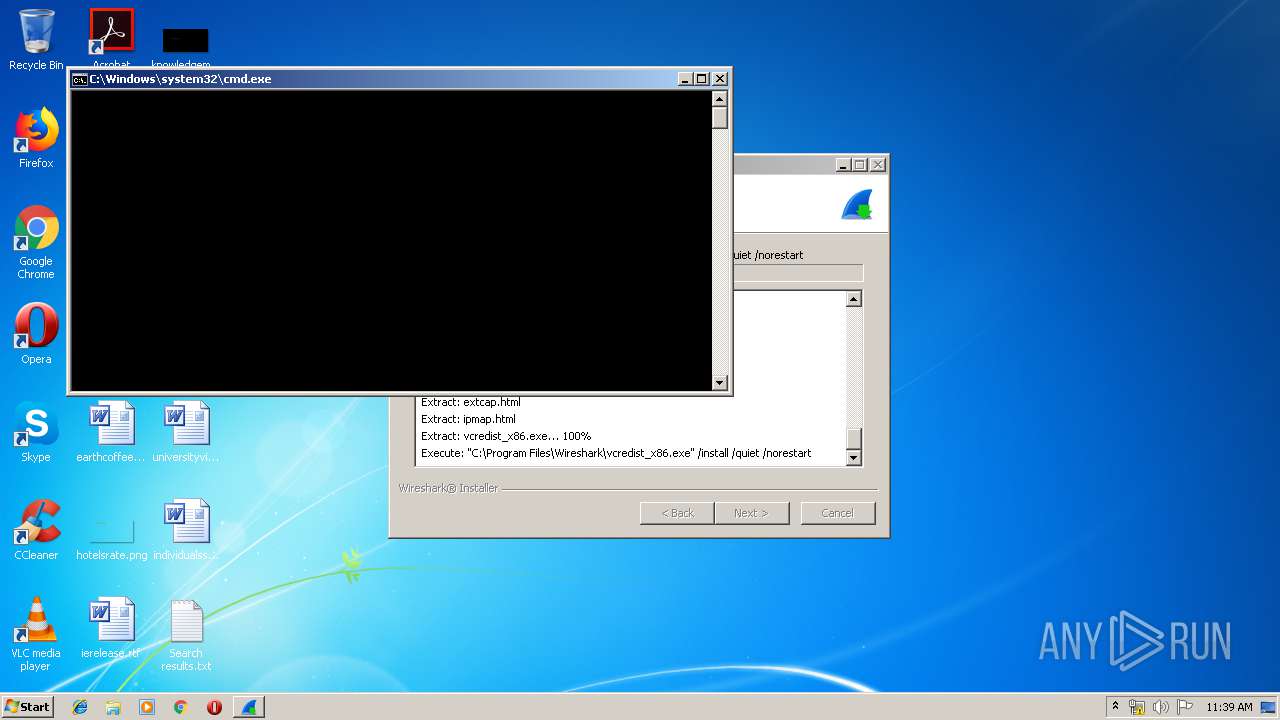
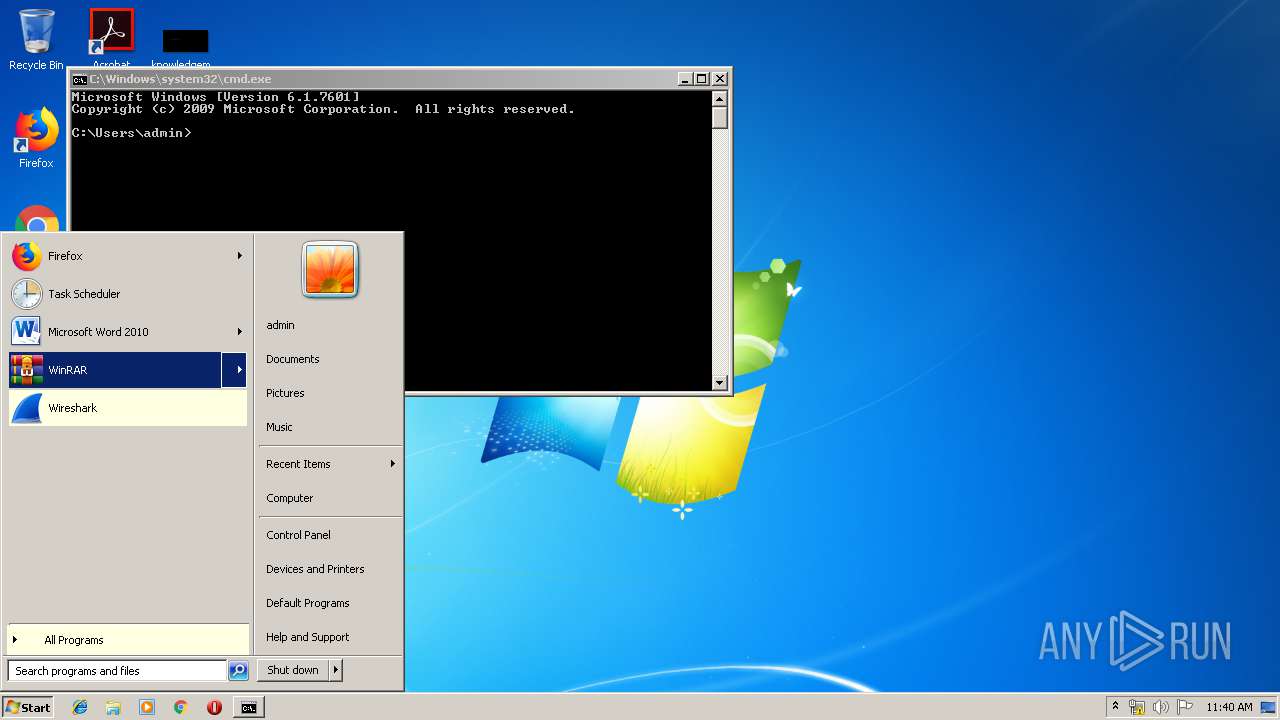
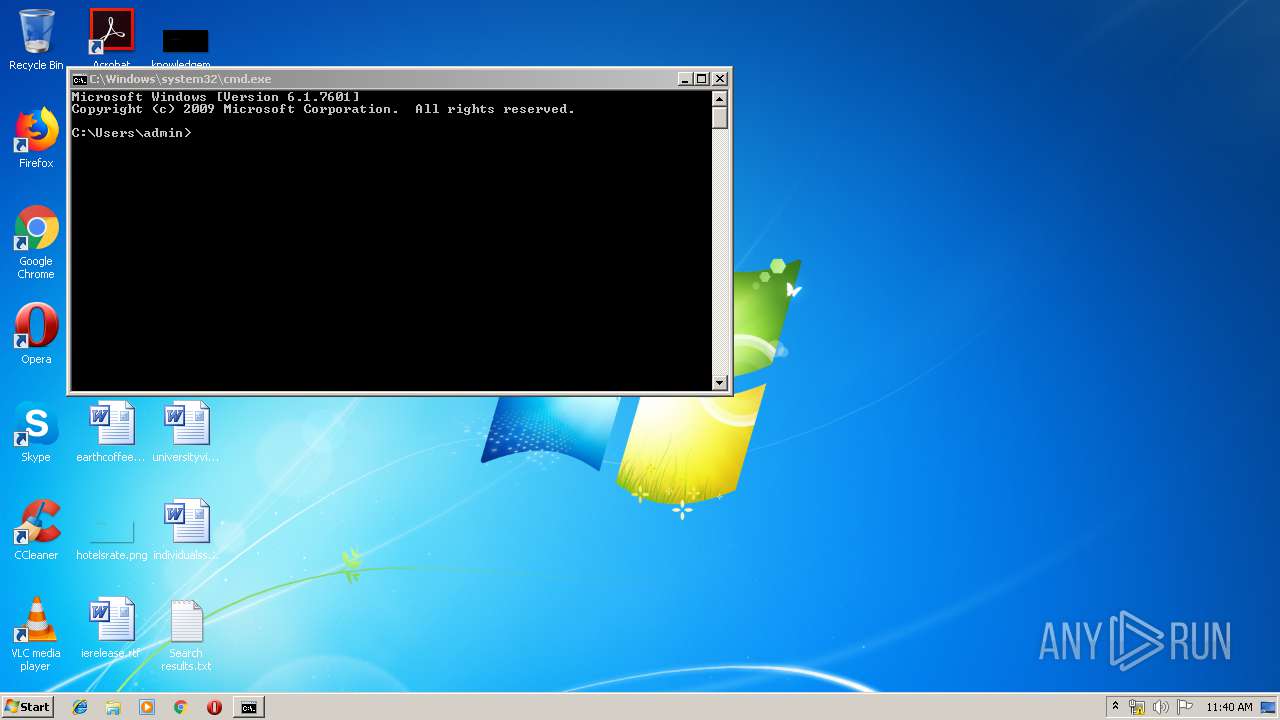
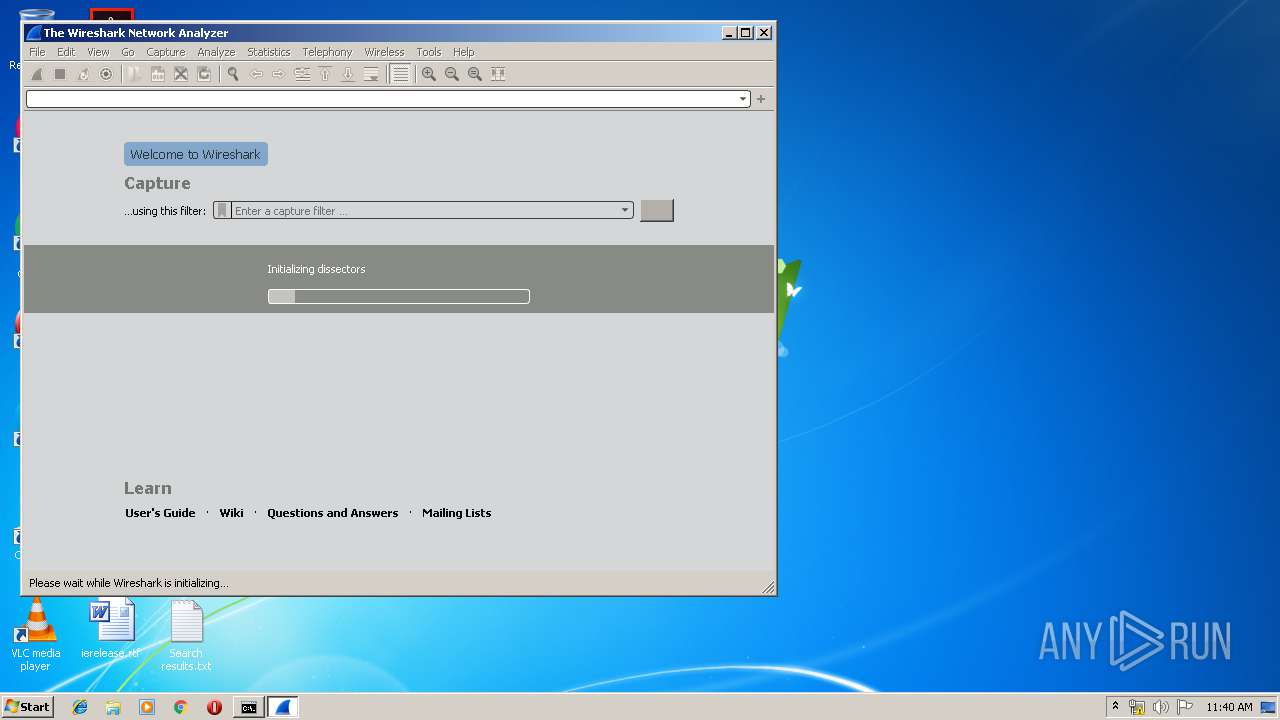
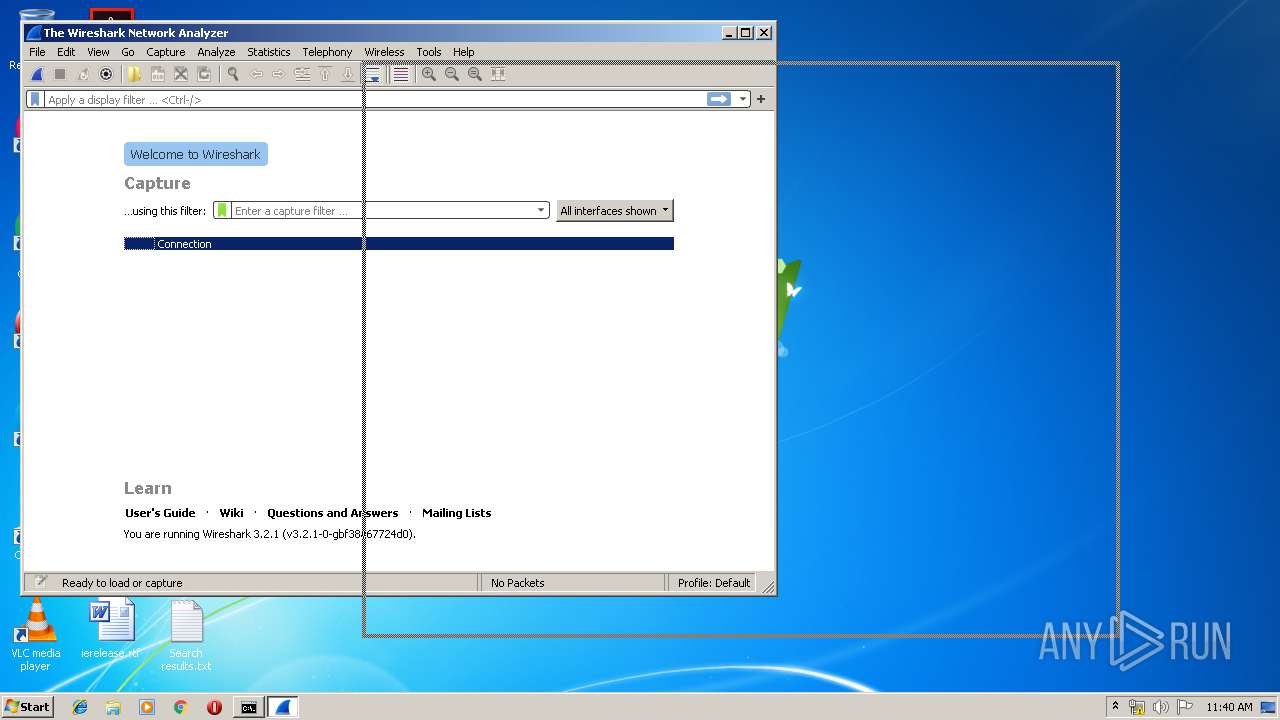
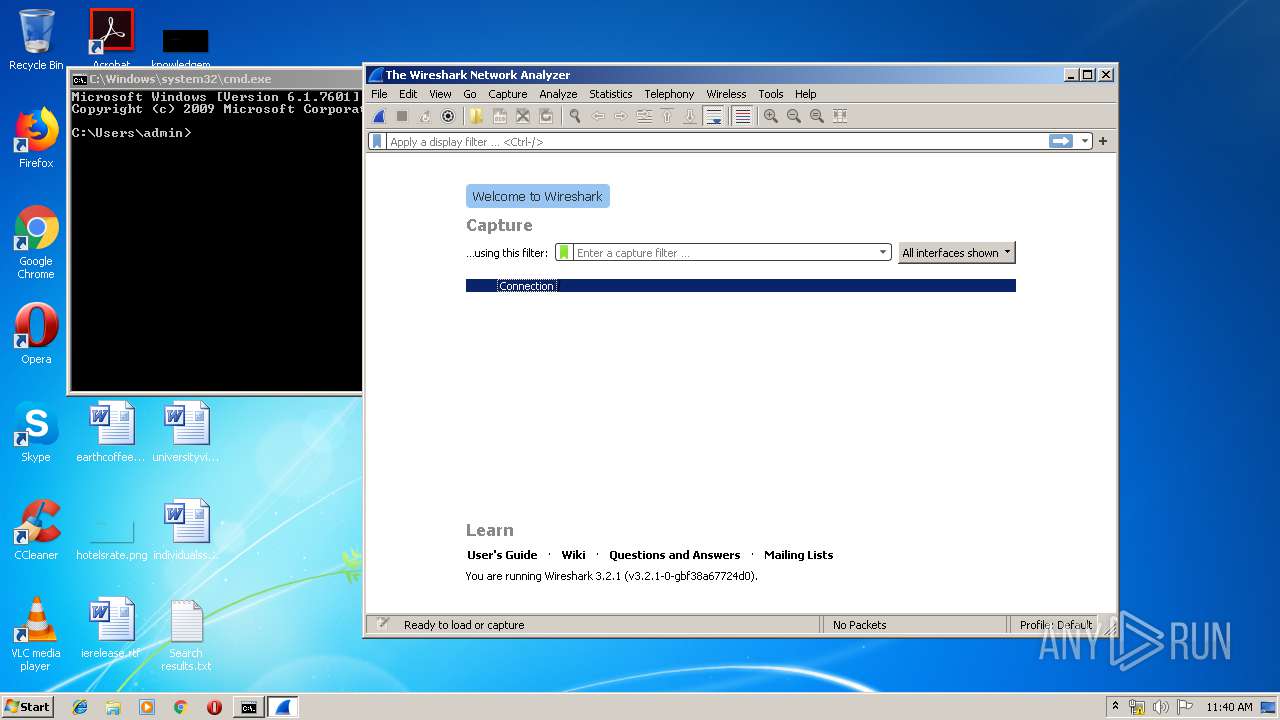
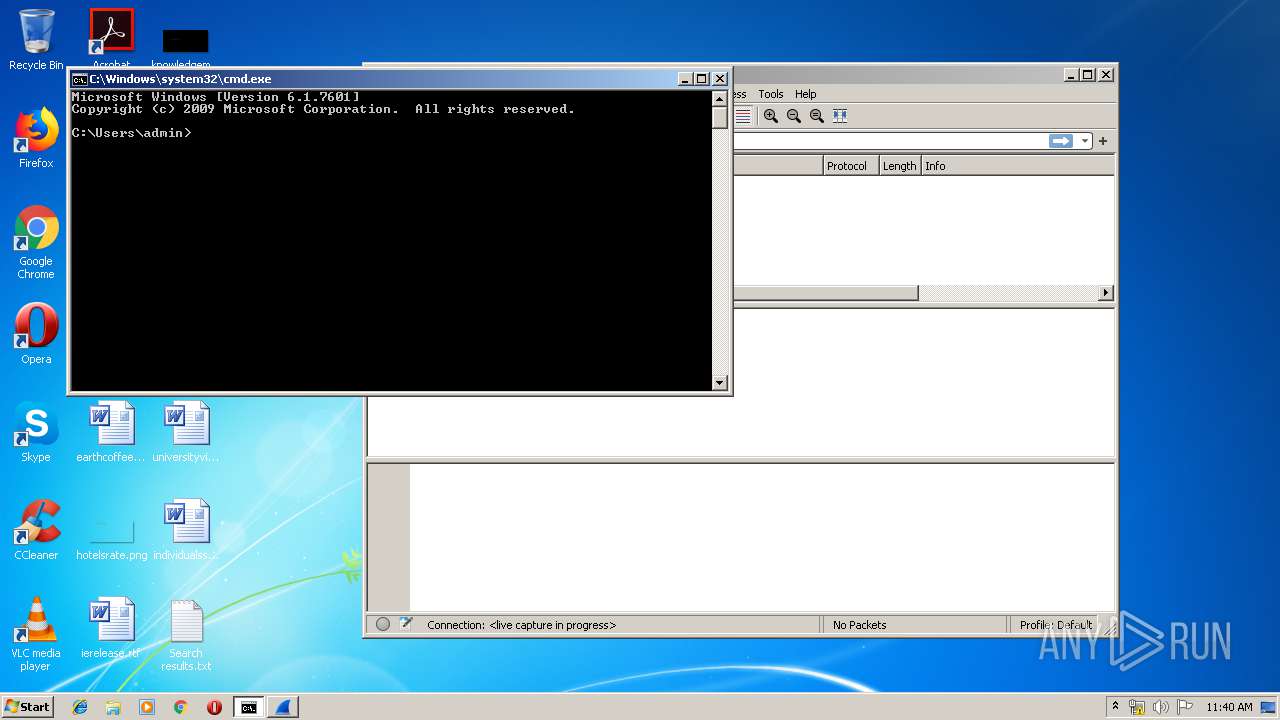
Manual execution by user
- chrome.exe (PID: 1012)
- ProcessHacker.exe (PID: 1944)
- NOTEPAD.EXE (PID: 2152)
- explorer.exe (PID: 3148)
- opera.exe (PID: 4056)
- cmd.exe (PID: 3128)
- Wireshark.exe (PID: 444)
Reads Internet Cache Settings
- chrome.exe (PID: 1012)
Creates files in the user directory
- chrome.exe (PID: 1012)
- opera.exe (PID: 4056)
Application launched itself
- chrome.exe (PID: 1012)
Reads settings of System Certificates
- chrome.exe (PID: 3736)
- chrome.exe (PID: 1012)
- ProcessHacker.exe (PID: 1944)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1012)
- Wireshark-win32-3.2.1.exe (PID: 1608)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2344)
Creates a software uninstall entry
- msiexec.exe (PID: 1536)
Searches for installed software
- DrvInst.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.0.2980 |
| ProductVersionNumber: | 4.1.0.2980 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | - |
| CompanyName: | Riverbed Technology, Inc. |
| FileDescription: | WinPcap 4.1.3 installer |
| FileVersion: | 4.1.0.2980 |
| LegalCopyright: | © 2005 - 2013 Riverbed Technology, Inc. |
| LegalTrademarks: | - |
| ProductName: | WinPcap 4.1.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Riverbed Technology, Inc. |
| FileDescription: | WinPcap 4.1.3 installer |
| FileVersion: | 4.1.0.2980 |
| LegalCopyright: | © 2005 - 2013 Riverbed Technology, Inc. |
| LegalTrademarks: | - |
| ProductName: | WinPcap 4.1.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003F000 | 0x000043A8 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.84643 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
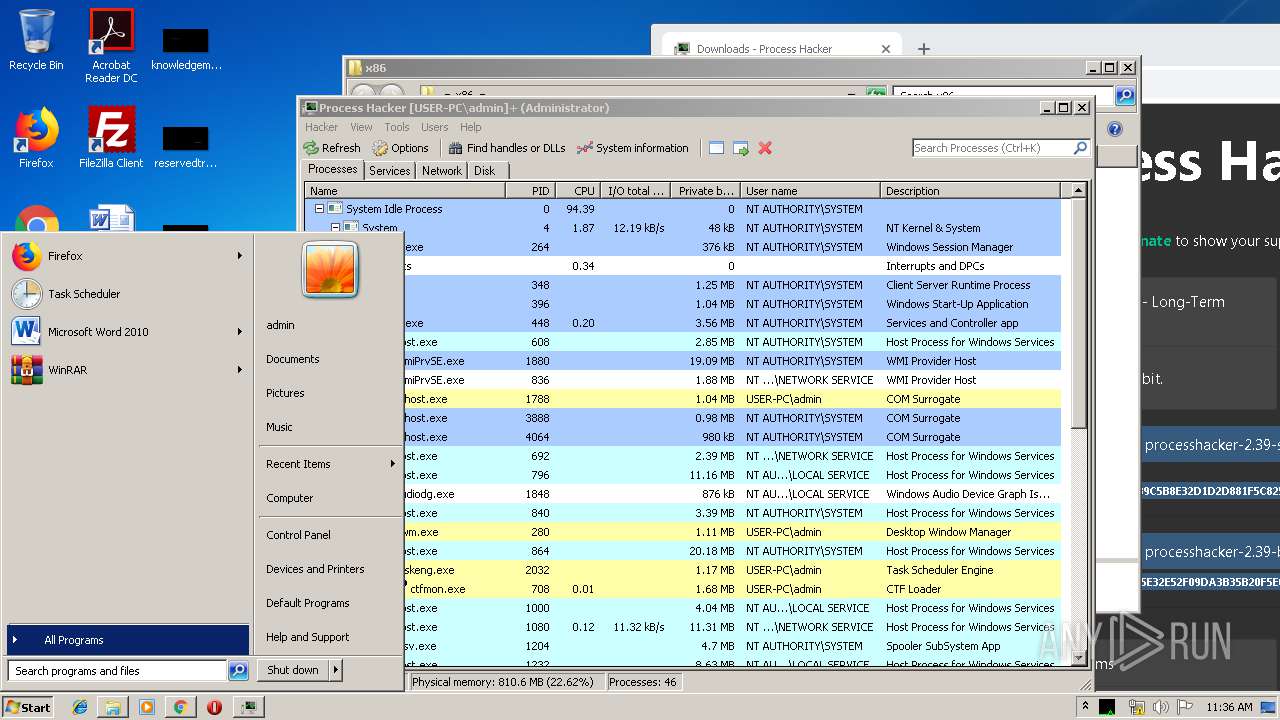
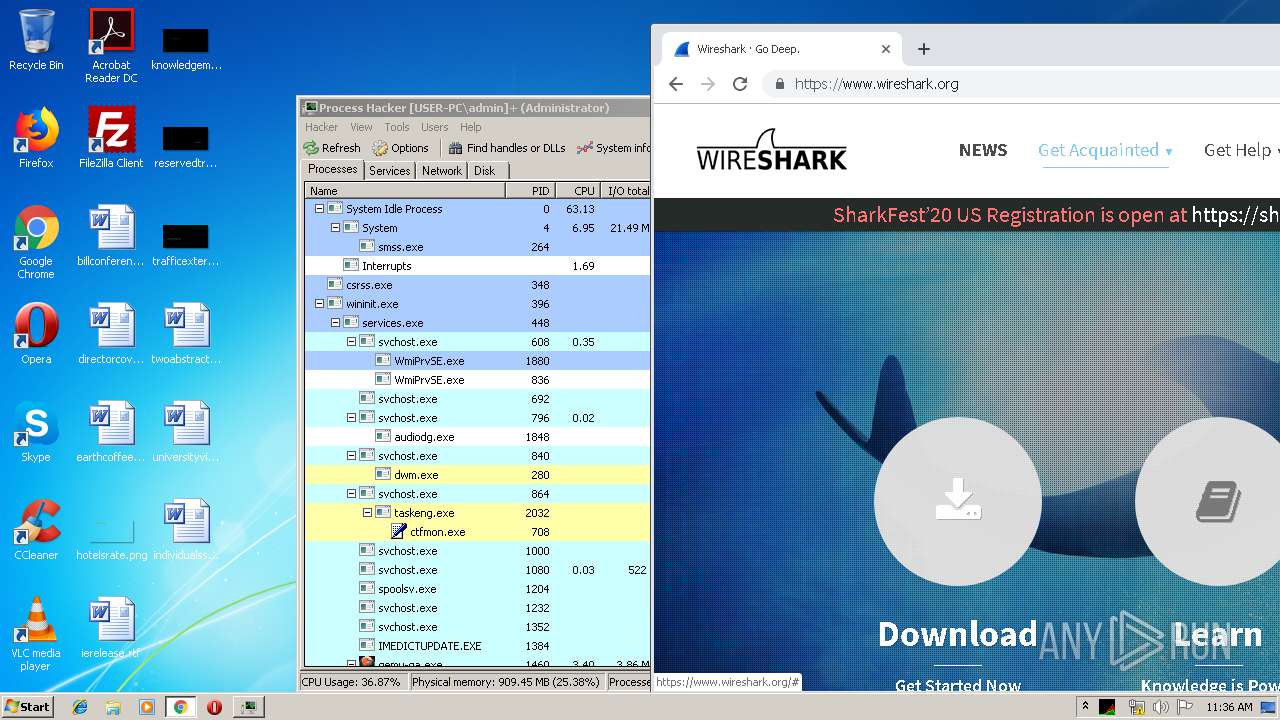
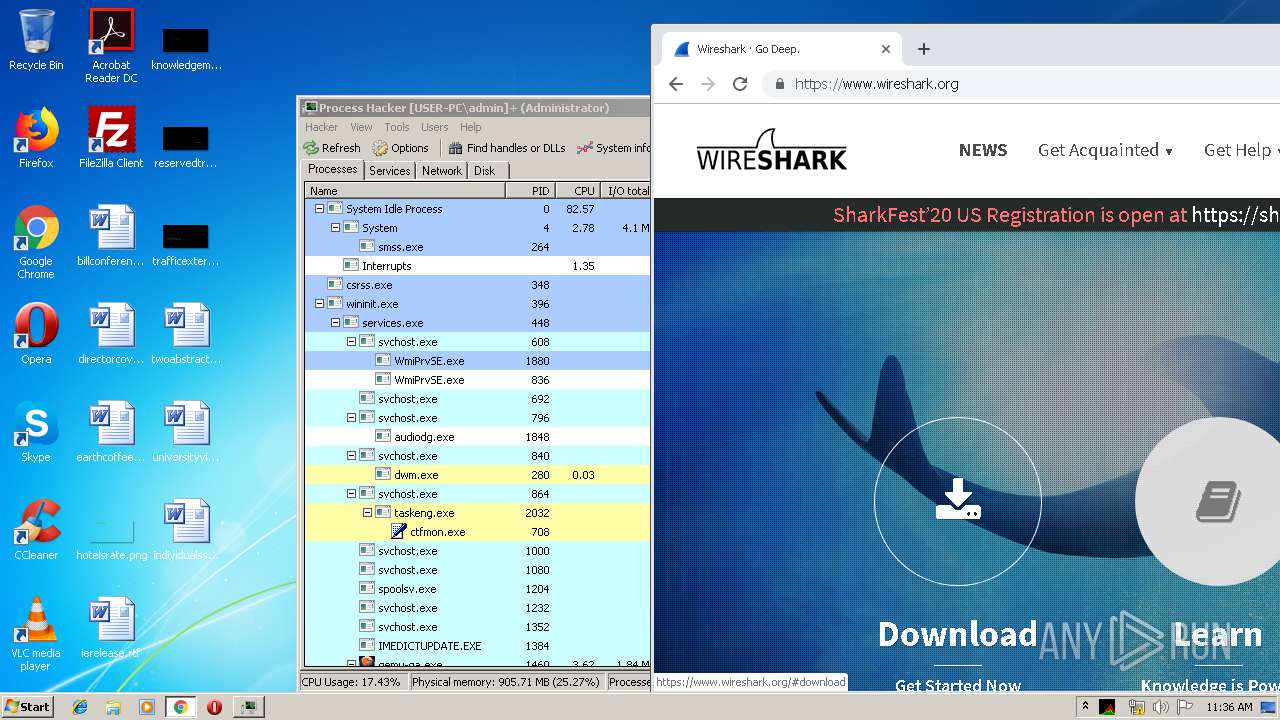
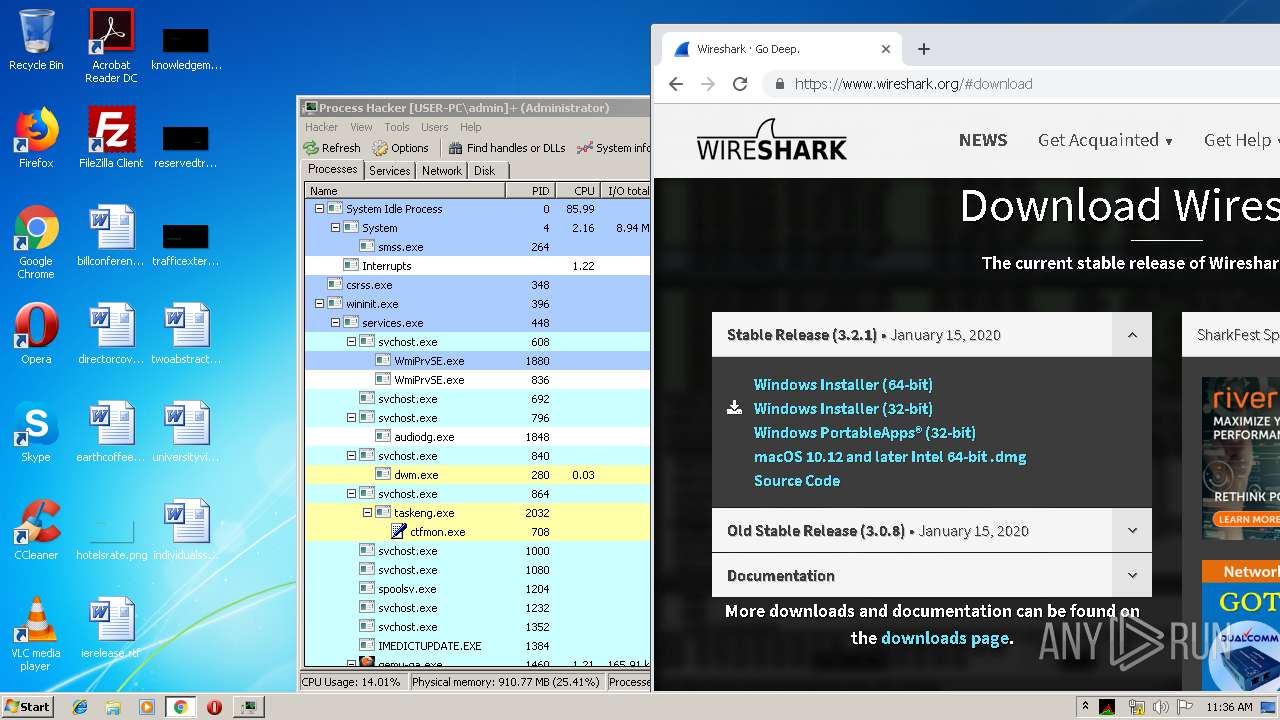
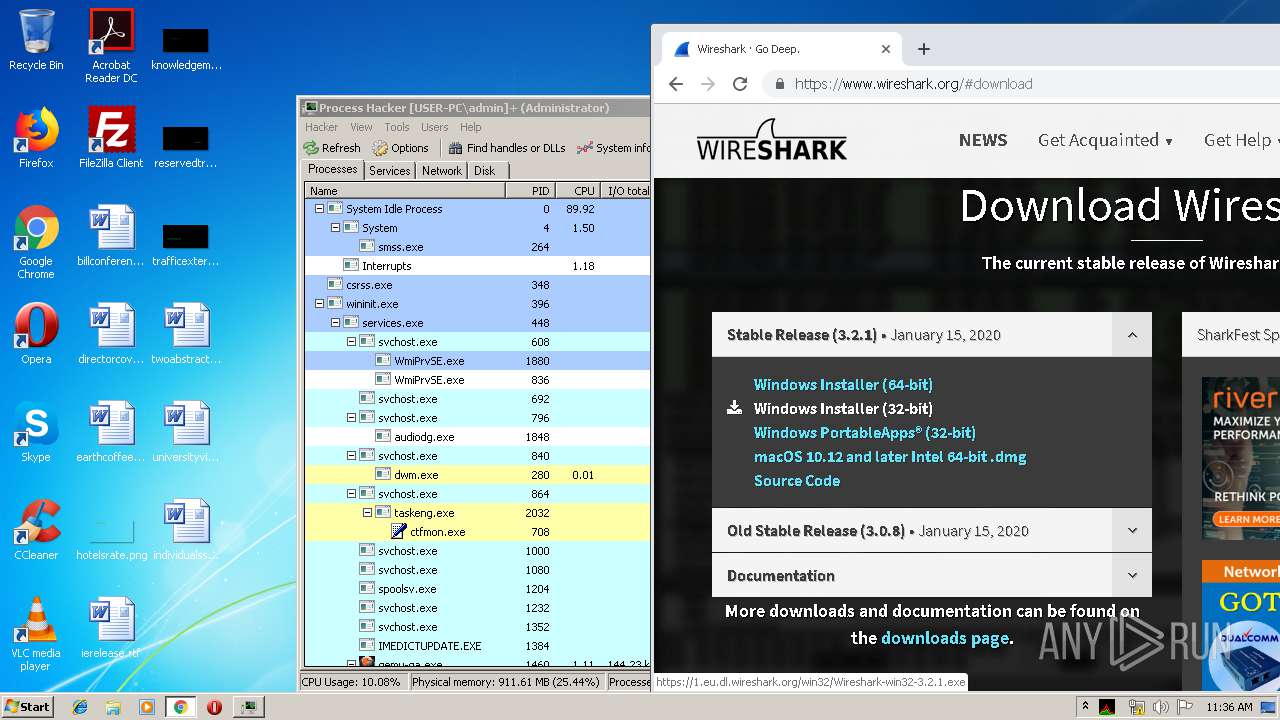
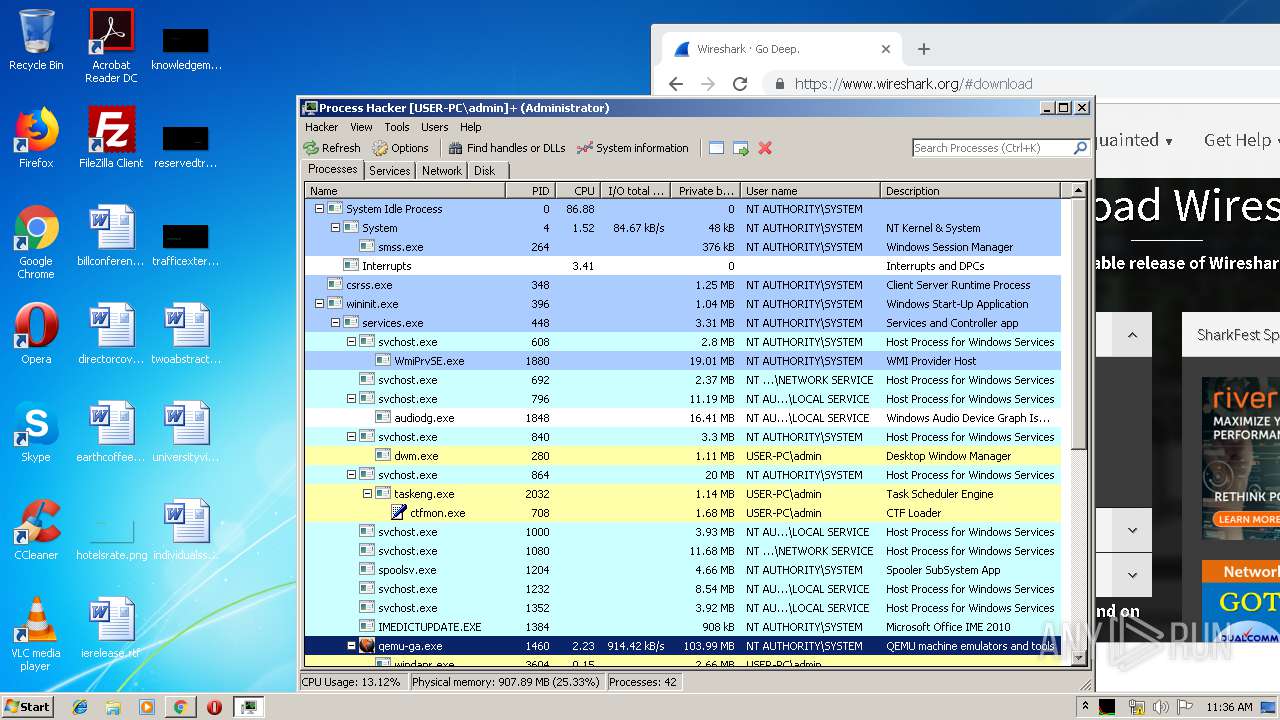
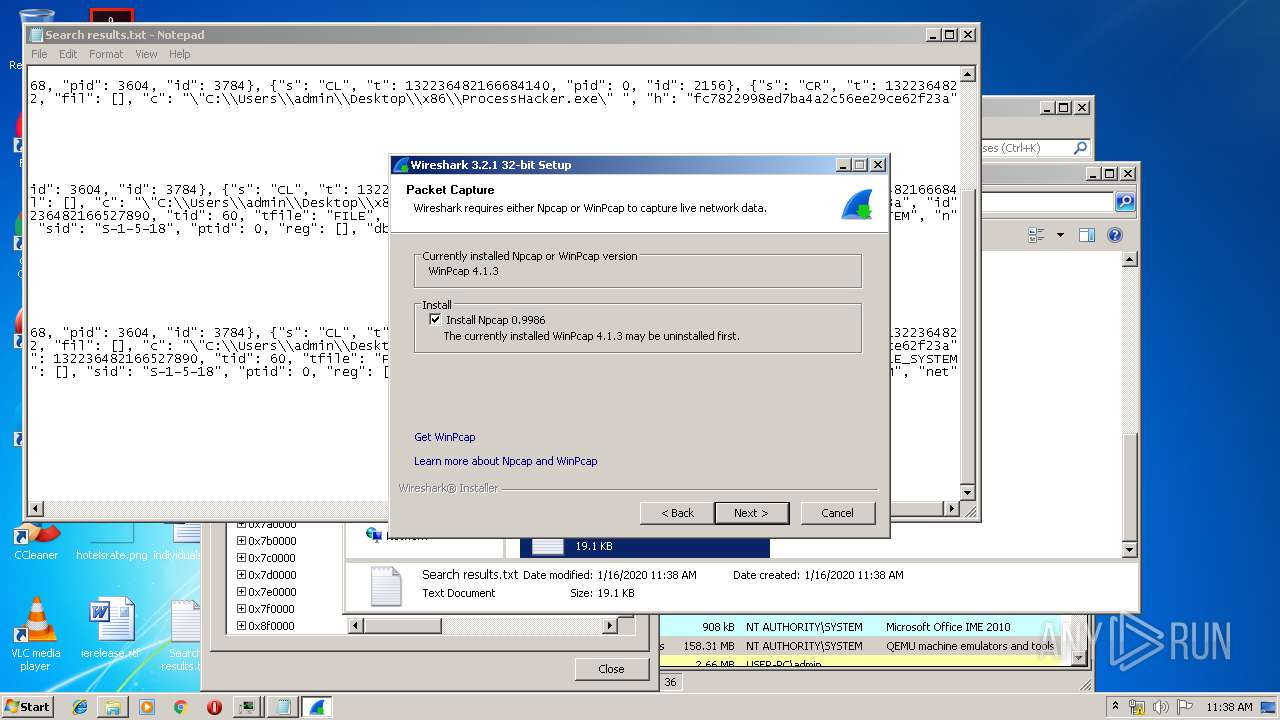
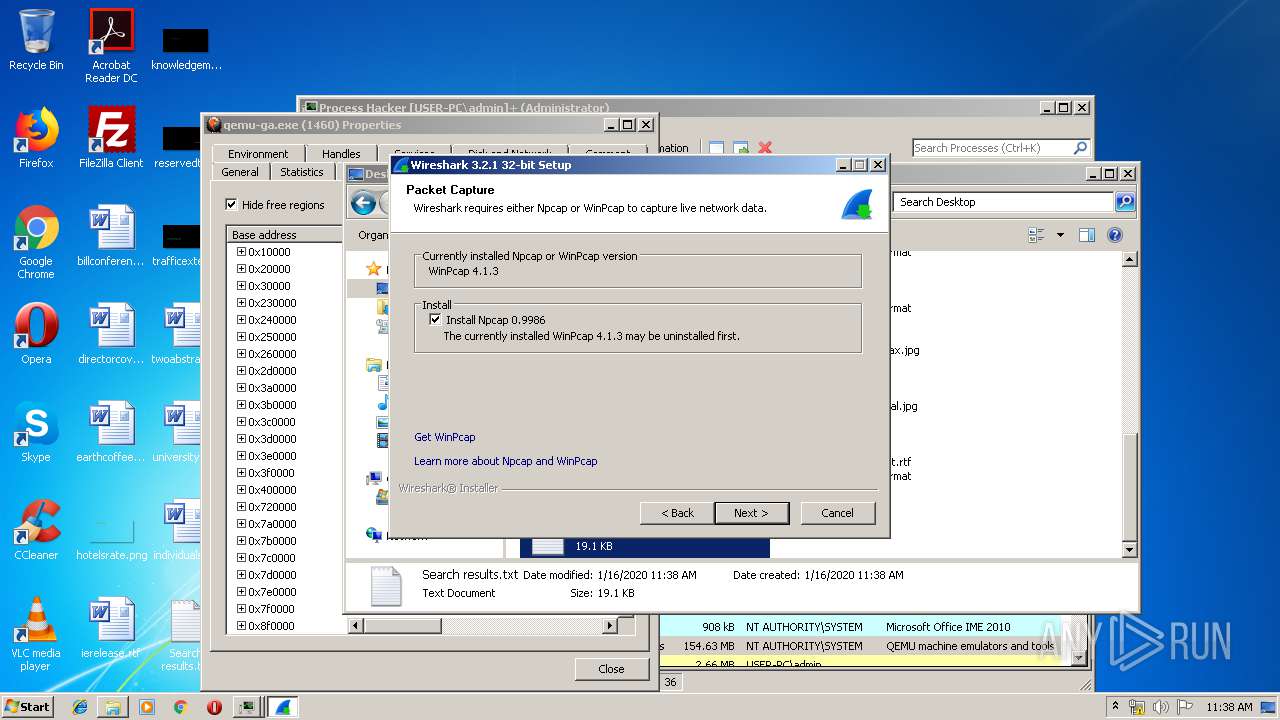
Total processes
149
Monitored processes
85
Malicious processes
18
Suspicious processes
2
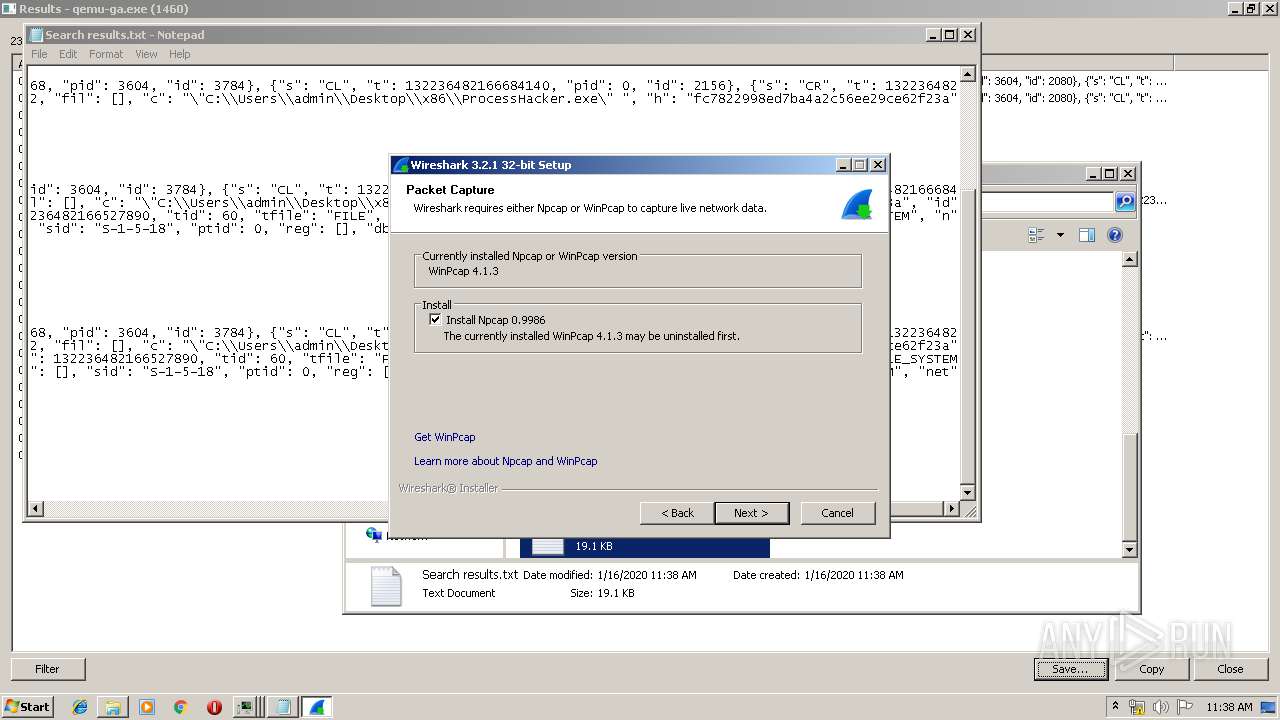
Behavior graph
Click at the process to see the details
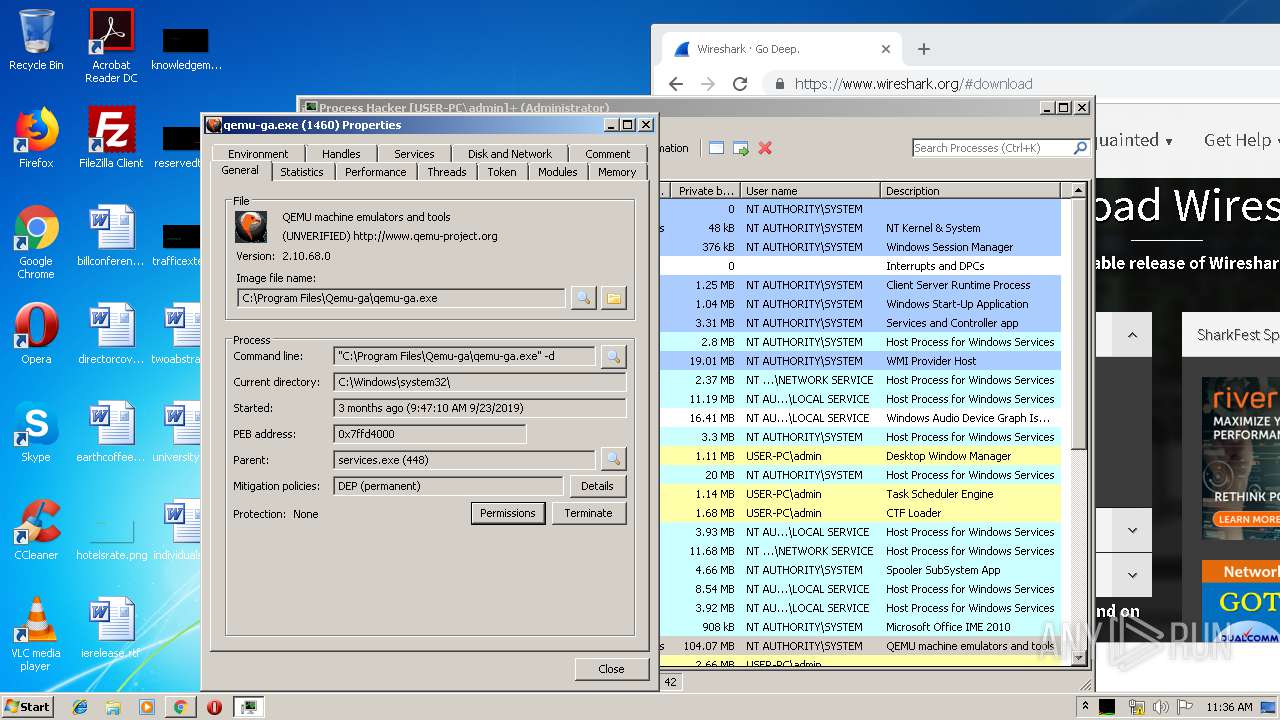
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Wireshark\Wireshark.exe" | C:\Program Files\Wireshark\Wireshark.exe | — | explorer.exe | |||||||||||
User: admin Company: The Wireshark developer community, https://www.wireshark.org/ Integrity Level: MEDIUM Description: Wireshark Exit code: 0 Version: 3.2.1 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6414856957941930827,15623237768712109949,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9772120073748570242 --mojo-platform-channel-handle=3616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
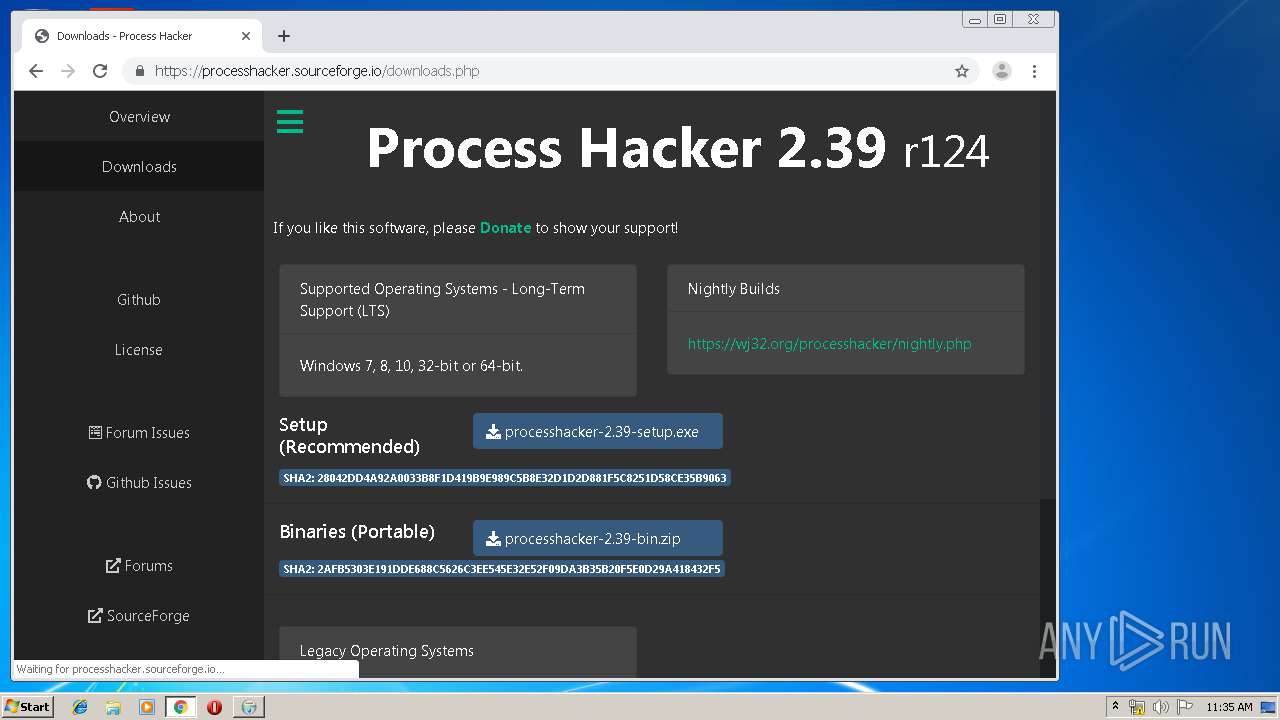
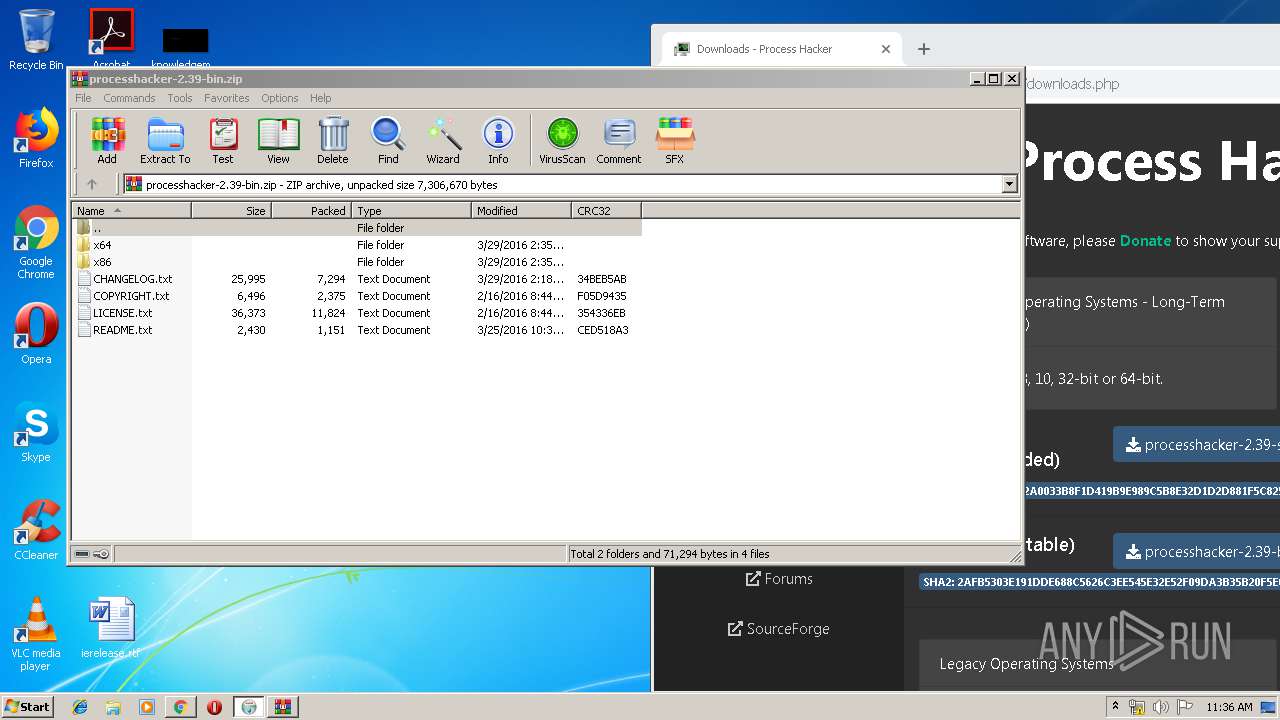
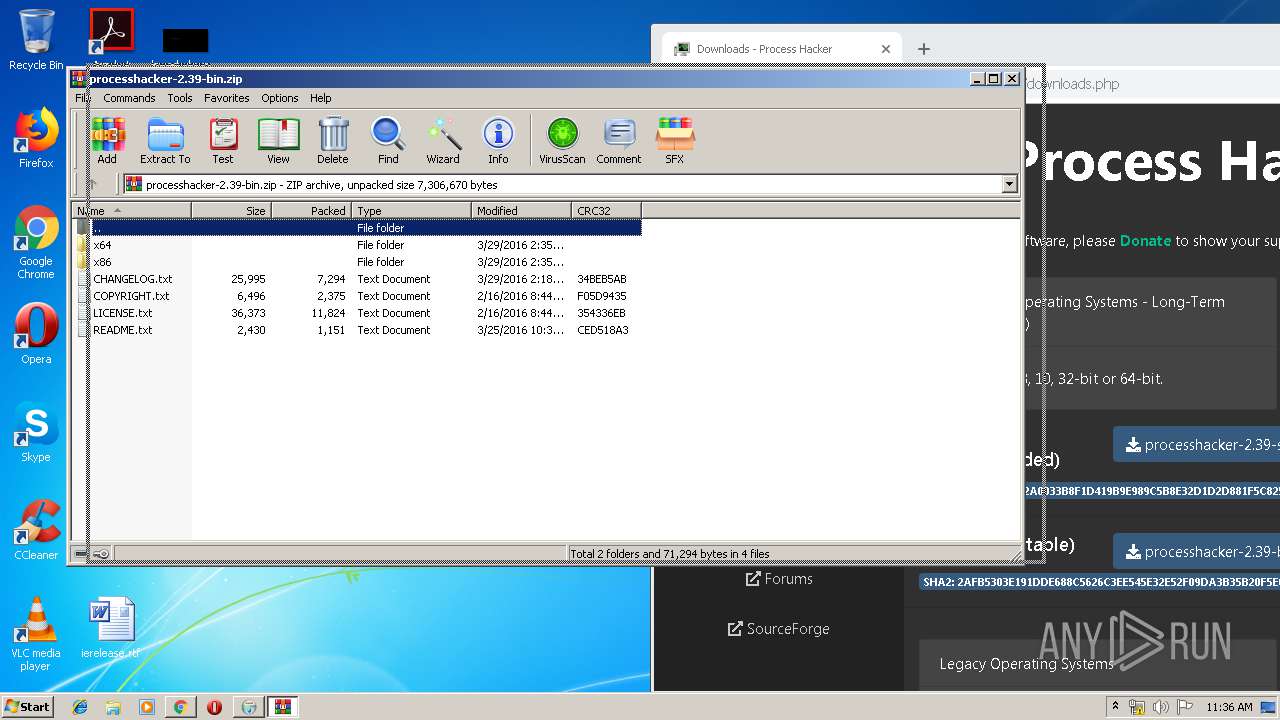
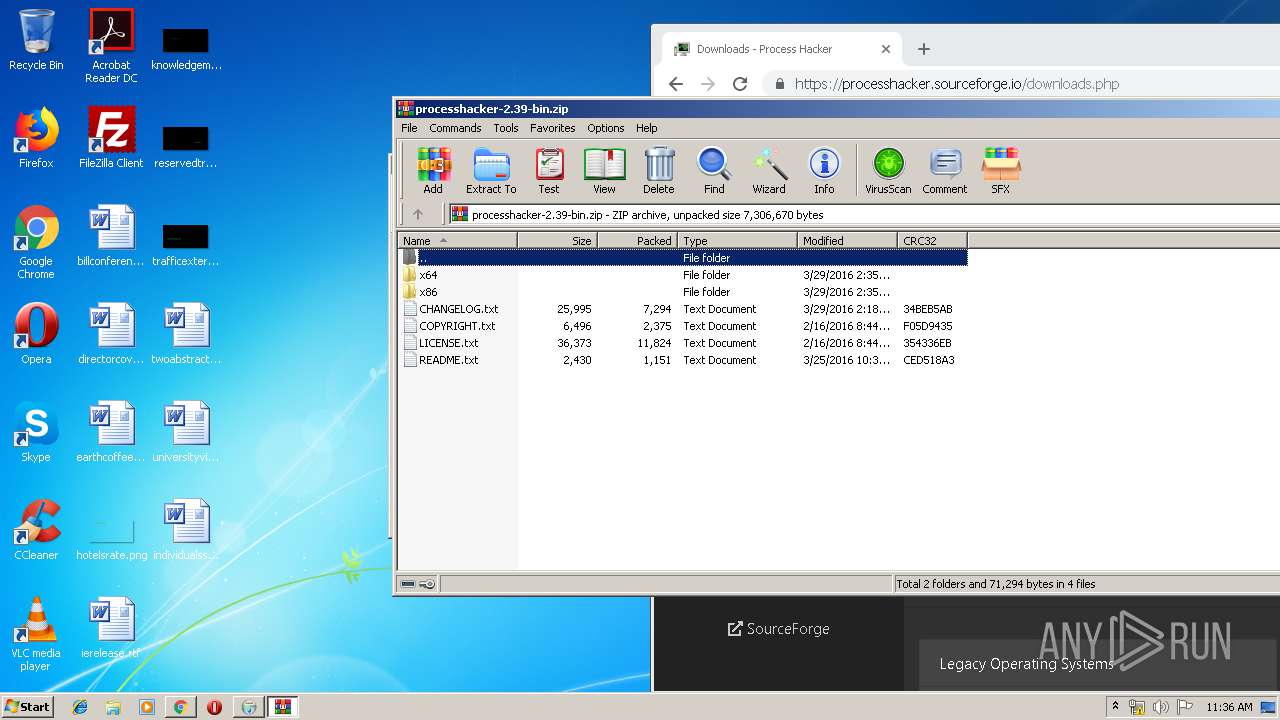
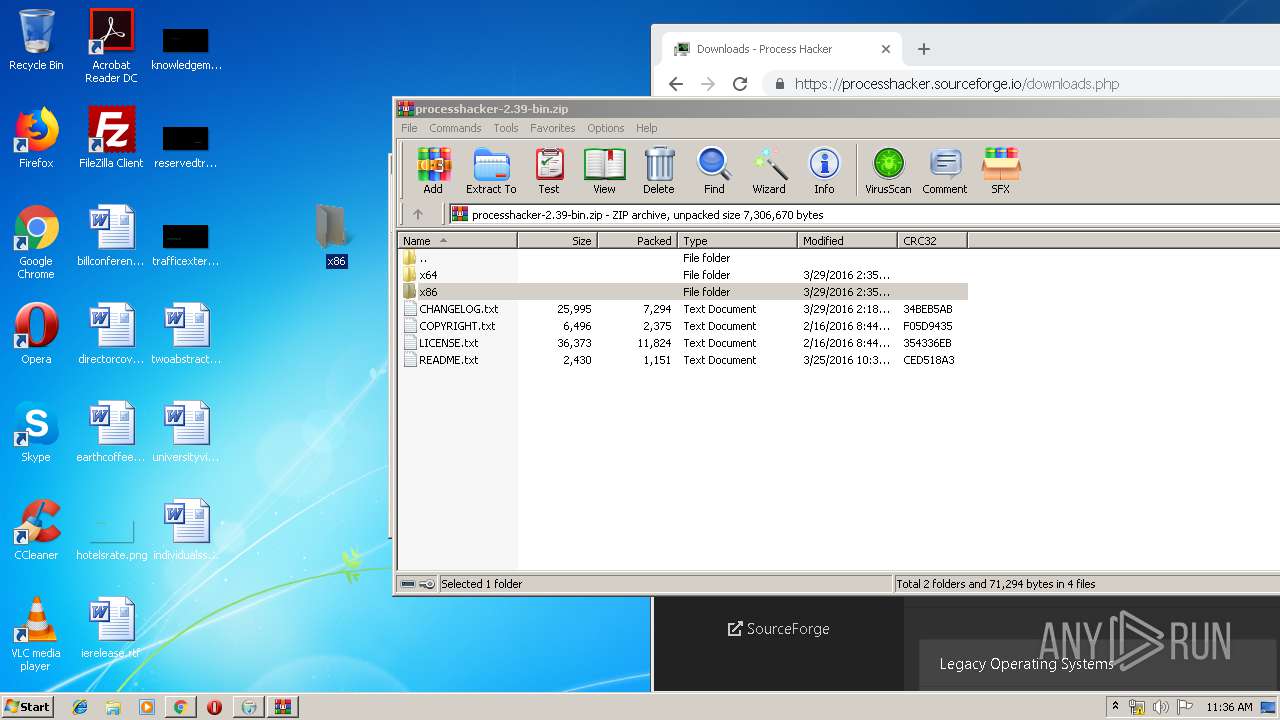
| 504 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\processhacker-2.39-bin.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1636 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
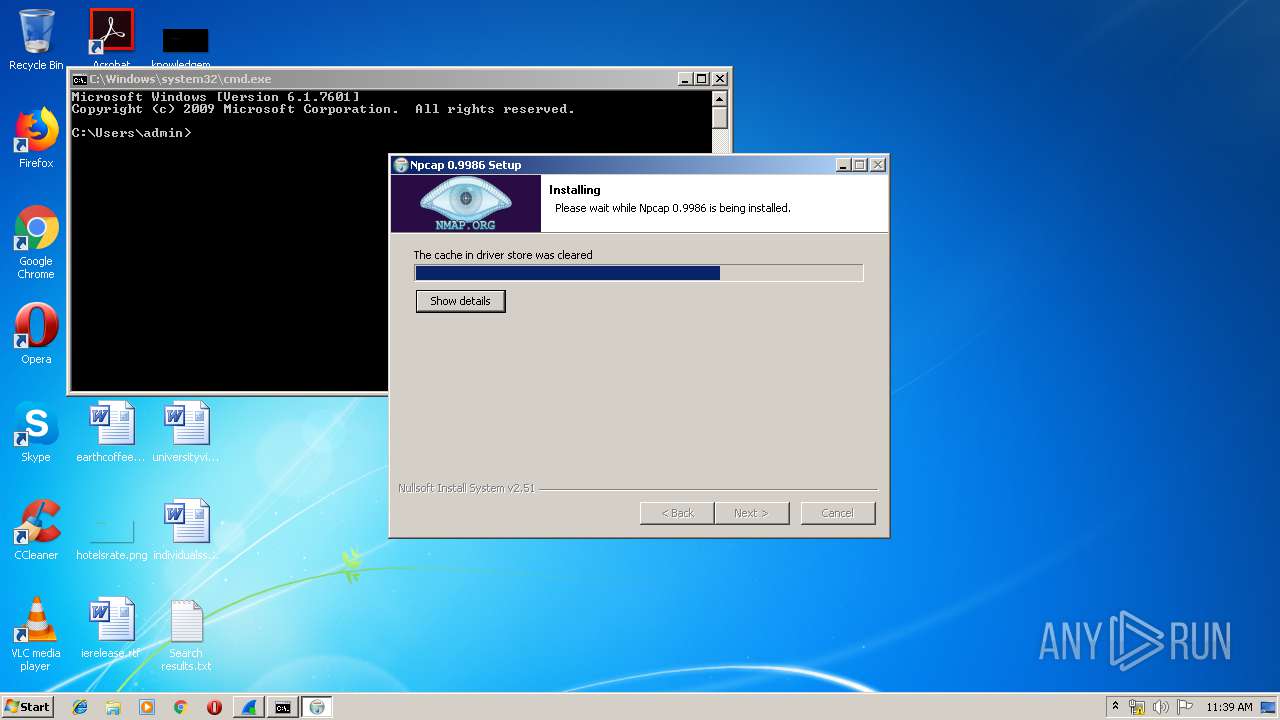
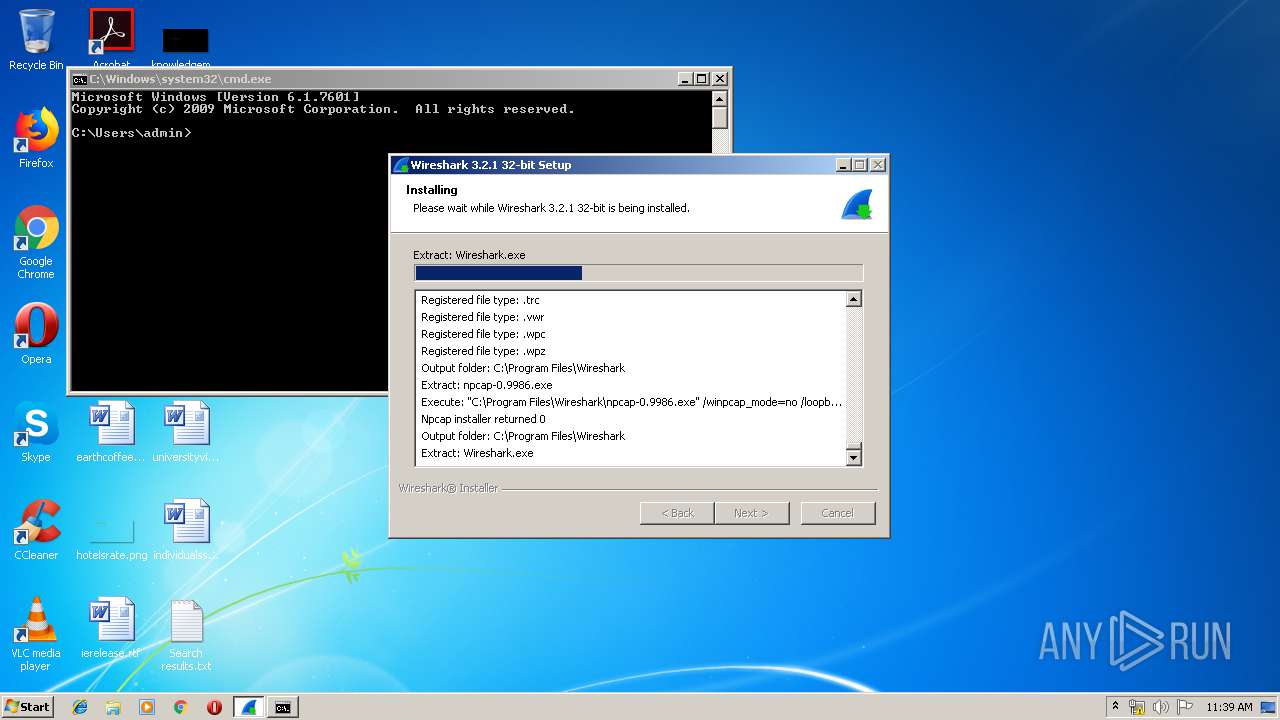
| 788 | "C:\Program Files\Wireshark\npcap-0.9986.exe" /winpcap_mode=no /loopback_support=no | C:\Program Files\Wireshark\npcap-0.9986.exe | Wireshark-win32-3.2.1.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Npcap 0.9986 installer Exit code: 0 Version: 0.9986 Modules
| |||||||||||||||
| 856 | "C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{E4E0B566-7F74-49F7-BF07-6DA09632FEE6} {7C013625-3289-4510-A09F-73EA47D8B2B2} 2856 | C:\ProgramData\Package Cache\{49697869-be8e-427d-81a0-c334d1d14950}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,6414856957941930827,15623237768712109949,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8311255494285674104 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6414856957941930827,15623237768712109949,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2856155536678988508 --mojo-platform-channel-handle=3480 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,6414856957941930827,15623237768712109949,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11931705186195743432 --mojo-platform-channel-handle=2976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 330
Read events
3 856
Write events
1 175
Delete events
299
Modification events
| (PID) Process: | (716) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1012-13223648136894000 |
Value: 259 | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
198
Suspicious files
187
Text files
1 382
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3904dc.TMP | — | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\00b62705-dacc-4128-86ea-00c9b77bed30.tmp | — | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3904dc.TMP | text | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3904dc.TMP | text | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF390559.TMP | text | |
MD5:— | SHA256:— | |||
| 1012 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
58
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3736 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
3736 | chrome.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
4056 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
3736 | chrome.exe | GET | 200 | 173.194.5.216:80 | http://r2---sn-aigl6n7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=78.157.214.134&mm=28&mn=sn-aigl6n7d&ms=nvh&mt=1579174477&mv=m&mvi=1&pl=19&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3736 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3736 | chrome.exe | GET | 200 | 52.222.149.168:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3736 | chrome.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3736 | chrome.exe | GET | 200 | 95.101.72.145:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.4 Kb | whitelisted |
3736 | chrome.exe | GET | 200 | 173.194.183.168:80 | http://r3---sn-aigl6ney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.157.214.134&mm=28&mn=sn-aigl6ney&ms=nvh&mt=1579174477&mv=m&mvi=2&pl=19&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3736 | chrome.exe | 216.58.205.227:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3736 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3736 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3736 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3736 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
3736 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3736 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3736 | chrome.exe | 173.194.5.216:80 | r2---sn-aigl6n7d.gvt1.com | Google Inc. | US | whitelisted |
3736 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3736 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |