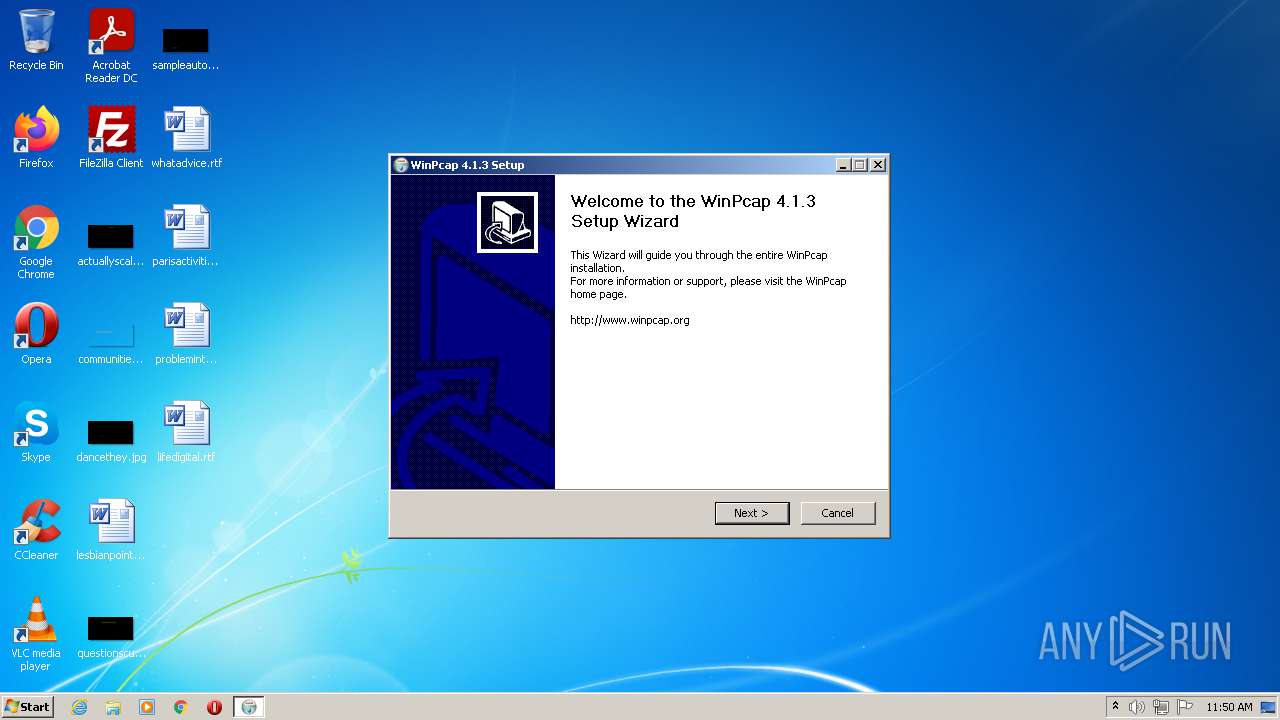
| File name: | WinPcap_4_1_3.exe |
| Full analysis: | https://app.any.run/tasks/3b855890-21d3-4eab-8151-8b85ead3ed00 |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2021, 10:50:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A11A2F0CFE6D0B4C50945989DB6360CD |
| SHA1: | E2516FCD1573E70334C8F50BEE5241CDFDF48A00 |
| SHA256: | FC4623B113A1F603C0D9AD5F83130BD6DE1C62B973BE9892305132389C8588DE |
| SSDEEP: | 24576:UBOldyR6ORWsaM2QROxa6jsqUENfJjNK/CG6niqiL:2KzqWsayROxa6QDENuaG+ifL |
MALICIOUS
Loads dropped or rewritten executable
- WinPcap_4_1_3.exe (PID: 1956)
Drops executable file immediately after starts
- WinPcap_4_1_3.exe (PID: 1956)
Starts NET.EXE for service management
- WinPcap_4_1_3.exe (PID: 1956)
SUSPICIOUS
Reads Environment values
- WinPcap_4_1_3.exe (PID: 1956)
Checks supported languages
- WinPcap_4_1_3.exe (PID: 1956)
Reads the computer name
- WinPcap_4_1_3.exe (PID: 1956)
Creates a directory in Program Files
- WinPcap_4_1_3.exe (PID: 1956)
Creates files in the program directory
- WinPcap_4_1_3.exe (PID: 1956)
Executable content was dropped or overwritten
- WinPcap_4_1_3.exe (PID: 1956)
Drops a file with too old compile date
- WinPcap_4_1_3.exe (PID: 1956)
Creates files in the Windows directory
- WinPcap_4_1_3.exe (PID: 1956)
Creates files in the driver directory
- WinPcap_4_1_3.exe (PID: 1956)
Drops a file that was compiled in debug mode
- WinPcap_4_1_3.exe (PID: 1956)
Creates or modifies windows services
- WinPcap_4_1_3.exe (PID: 1956)
Creates a software uninstall entry
- WinPcap_4_1_3.exe (PID: 1956)
INFO
Checks supported languages
- net.exe (PID: 2060)
- net1.exe (PID: 3552)
Reads the computer name
- net1.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
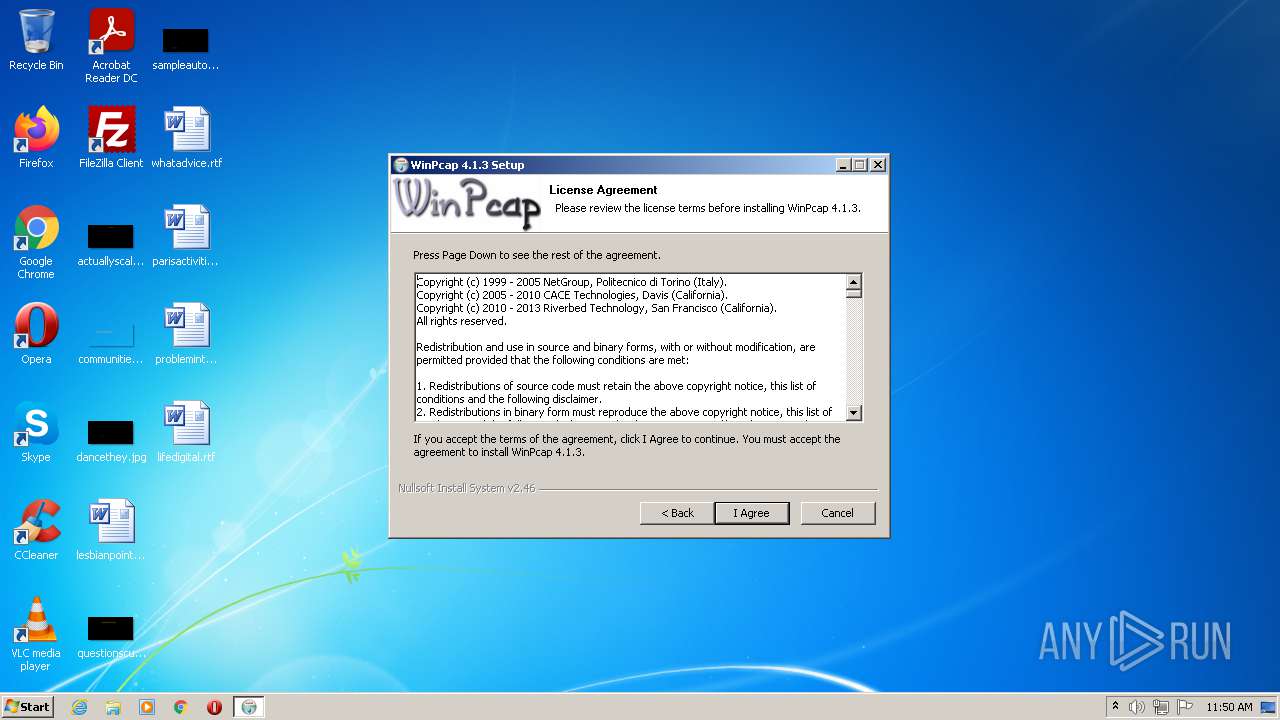
| ProductName: | WinPcap 4.1.3 |
|---|---|
| LegalTrademarks: | - |
| LegalCopyright: | © 2005 - 2013 Riverbed Technology, Inc. |
| FileVersion: | 4.1.0.2980 |
| FileDescription: | WinPcap 4.1.3 installer |
| CompanyName: | Riverbed Technology, Inc. |
| Comments: | - |
| CharacterSet: | ASCII |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 4.1.0.2980 |
| FileVersionNumber: | 4.1.0.2980 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x30fa |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 164864 |
| CodeSize: | 24064 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Riverbed Technology, Inc. |
| FileDescription: | WinPcap 4.1.3 installer |
| FileVersion: | 4.1.0.2980 |
| LegalCopyright: | © 2005 - 2013 Riverbed Technology, Inc. |
| LegalTrademarks: | - |
| ProductName: | WinPcap 4.1.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003F000 | 0x000043A8 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.84643 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1956 | "C:\Users\admin\AppData\Local\Temp\WinPcap_4_1_3.exe" | C:\Users\admin\AppData\Local\Temp\WinPcap_4_1_3.exe | Explorer.EXE | ||||||||||||
User: admin Company: Riverbed Technology, Inc. Integrity Level: HIGH Description: WinPcap 4.1.3 installer Exit code: 0 Version: 4.1.0.2980 Modules
| |||||||||||||||
| 2060 | net start npf | C:\Windows\system32\net.exe | — | WinPcap_4_1_3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3356 | "C:\Users\admin\AppData\Local\Temp\WinPcap_4_1_3.exe" | C:\Users\admin\AppData\Local\Temp\WinPcap_4_1_3.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Riverbed Technology, Inc. Integrity Level: MEDIUM Description: WinPcap 4.1.3 installer Exit code: 3221226540 Version: 4.1.0.2980 Modules
| |||||||||||||||
| 3552 | C:\Windows\system32\net1 start npf | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
756
Read events
745
Write events
11
Delete events
0
Modification events
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\NPF |
| Operation: | write | Name: | Start |
Value: 2 | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WinPcap |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\WinPcap | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinPcapInst |
| Operation: | write | Name: | DisplayName |
Value: WinPcap 4.1.3 | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinPcapInst |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\WinPcap\uninstall.exe | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinPcapInst |
| Operation: | write | Name: | Publisher |
Value: Riverbed Technology, Inc. | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinPcapInst |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.riverbed.com/ | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinPcapInst |
| Operation: | write | Name: | URLUpdateInfo |
Value: http://www.winpcap.org | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinPcapInst |
| Operation: | write | Name: | VersionMajor |
Value: 4 | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinPcapInst |
| Operation: | write | Name: | VersionMinor |
Value: 1 | |||
| (PID) Process: | (1956) WinPcap_4_1_3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WinPcapInst |
| Operation: | write | Name: | DisplayVersion |
Value: 4.1.0.2980 | |||
Executable files
11
Suspicious files
0
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1956 | WinPcap_4_1_3.exe | C:\Program Files\WinPcap\WinPcapInstall.dll | executable | |
MD5:E78291558CB803DFD091AD8FB56FEECC | SHA256:D9F4CD9F0E1BC9A138FB4DA6F83C92C3E86EB3DE4F988D5943D75C9B1DC6BB9D | |||
| 1956 | WinPcap_4_1_3.exe | C:\Users\admin\AppData\Local\Temp\nspB03C.tmp\ExecDos.dll | executable | |
MD5:A7CD6206240484C8436C66AFB12BDFBF | SHA256:69AC56D2FDF3C71B766D3CC49B33B36F1287CC2503310811017467DFCB455926 | |||
| 1956 | WinPcap_4_1_3.exe | C:\Users\admin\AppData\Local\Temp\nspB03C.tmp\bootOptions.ini | text | |
MD5:9F64B7E590B32B5BA414F4301FB8B3D5 | SHA256:F6F2E247226AB06E9B56AE2D10CCD02D9298ABCCAC85C56ABFA19E5587446D54 | |||
| 1956 | WinPcap_4_1_3.exe | C:\Program Files\WinPcap\install.log | text | |
MD5:6A69C0B7A263CDC8D261F73C406DB6BB | SHA256:30DD77859CDD3854DD387CBA3D1419F68B8D21C046D00A0F4D2619627CD90C73 | |||
| 1956 | WinPcap_4_1_3.exe | C:\Program Files\WinPcap\rpcapd.exe | executable | |
MD5:83A6C2CAFE236652D1559640594A0EA8 | SHA256:52360F17C9C70C9CEA3316560B40C4D89FD705ED7E6B6088C99FC54D4CC35EB5 | |||
| 1956 | WinPcap_4_1_3.exe | C:\Windows\system32\wpcap.dll | executable | |
MD5:4633B298D57014627831CCAC89A2C50B | SHA256:B967E4DCE952F9232592E4C1753516081438702A53424005642700522055DBC9 | |||
| 1956 | WinPcap_4_1_3.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\WinPcap\WinPcap Web Site.url | text | |
MD5:4045C586E0A52F8D15E34642A688FA3B | SHA256:66DB8411780D0E4B9C09475241E1A8578A3A26A438A0E016722DB5D174055F43 | |||
| 1956 | WinPcap_4_1_3.exe | C:\Users\admin\AppData\Local\Temp\nspB03C.tmp\InstallOptions.dll | executable | |
MD5:325B008AEC81E5AAA57096F05D4212B5 | SHA256:C9CD5C9609E70005926AE5171726A4142FFBCCCC771D307EFCD195DAFC1E6B4B | |||
| 1956 | WinPcap_4_1_3.exe | C:\Users\admin\AppData\Local\Temp\nspB03C.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 1956 | WinPcap_4_1_3.exe | C:\Windows\system32\pthreadVC.dll | executable | |
MD5:F04A90F917BA10AE2DCBE859870F4DEA | SHA256:99C61ABF41C3AEC38CAB3ED6270ADBCA9A247BBF5F9AA9D29ECB0659A5527F48 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report