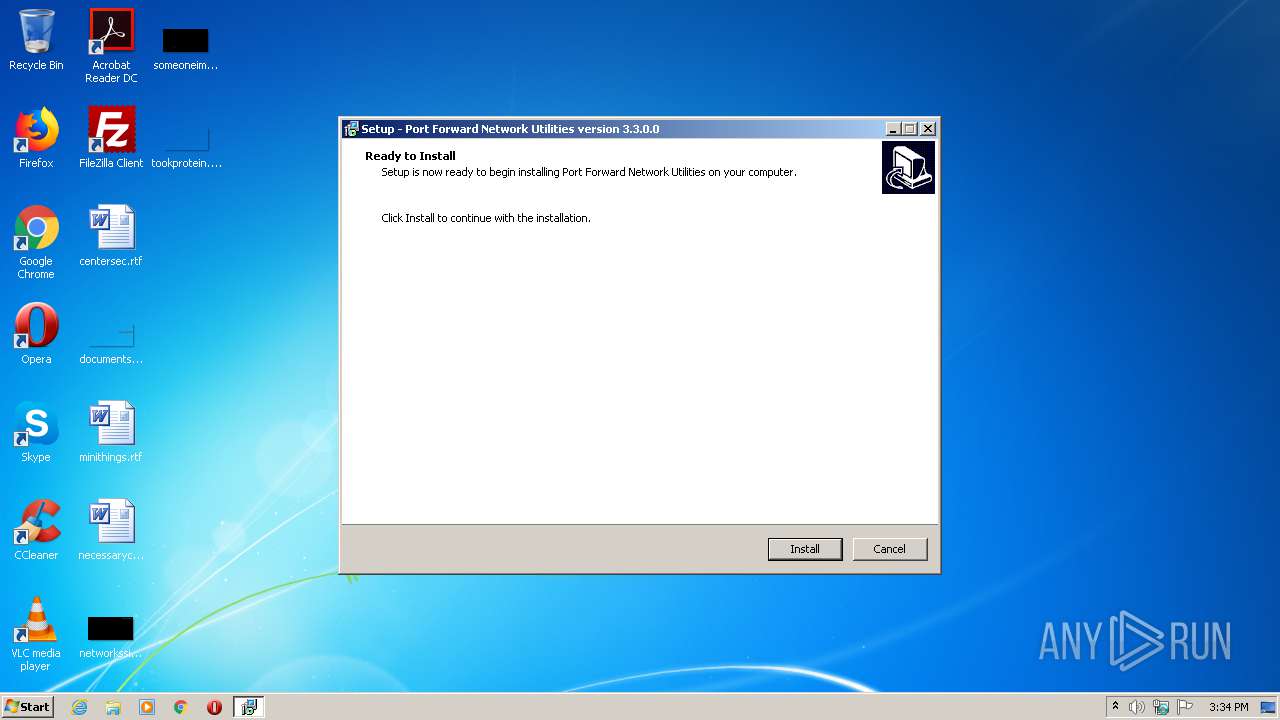
| File name: | SetupPortForwardNetworkUtilities.exe |
| Full analysis: | https://app.any.run/tasks/b737328e-996e-4d72-be2a-1951dc5ea730 |
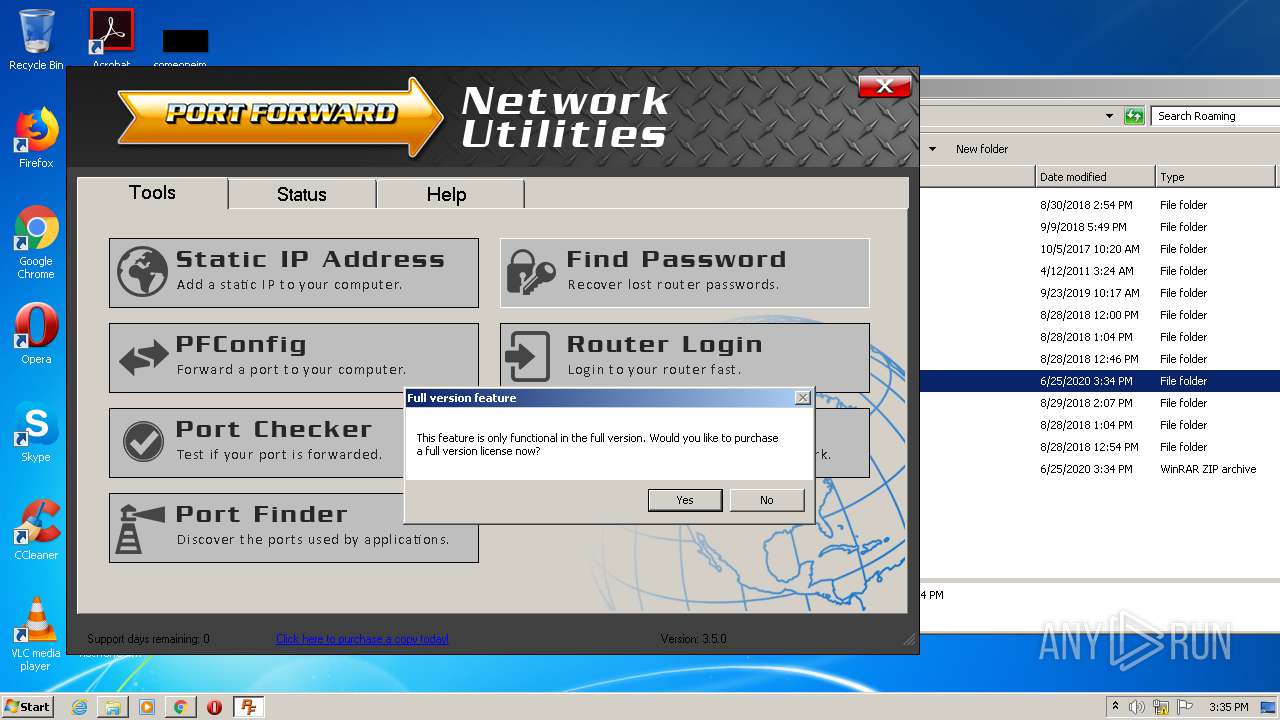
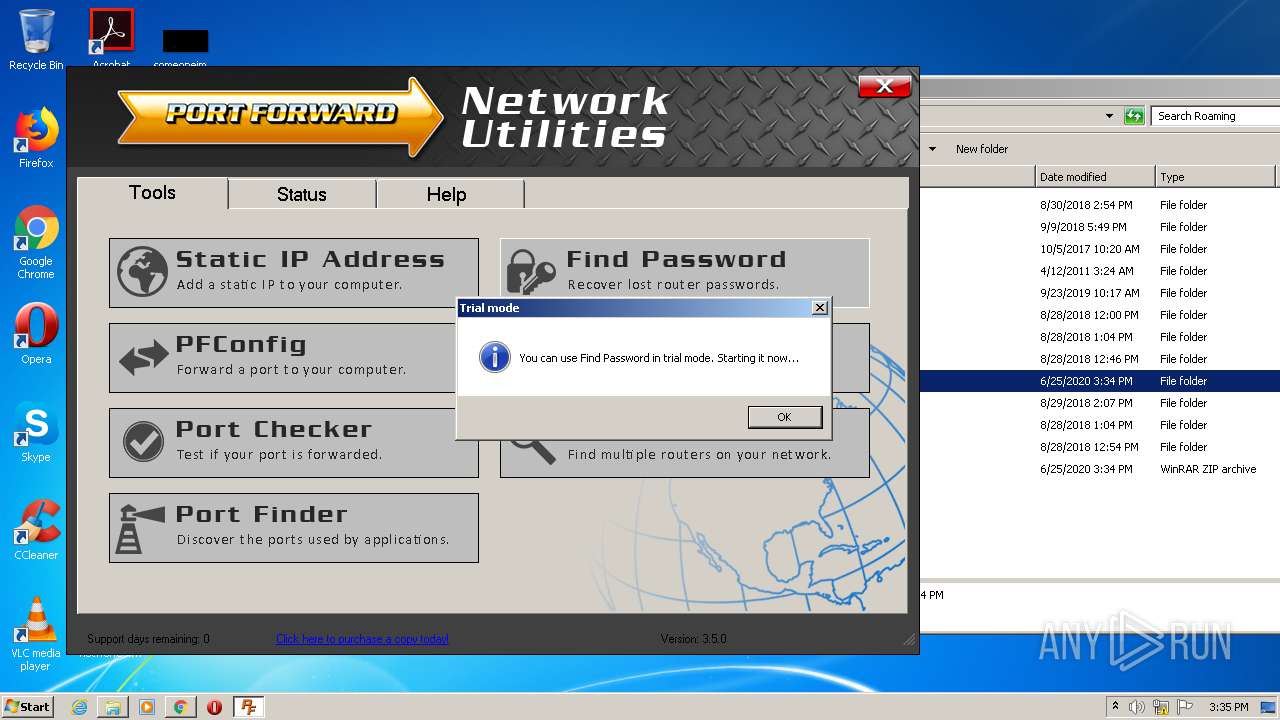
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2020, 14:33:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F173C344B00B26AC42756404DFD5B3B9 |
| SHA1: | 21C5EBC09E378B6D7EDA6F4FDE5685C3813875B5 |
| SHA256: | FC3C7E07734E2EC24BCB7F0AED7BD64071C3F3CD556A2DC650B63178BB8710C6 |
| SSDEEP: | 49152:KcsQ6QVYXDixKe95XCMwWrOJ8+7dnzqMmwN0o:K1QTiXDc/95XCM8d4D2h |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2040)
- regsvr32.exe (PID: 2660)
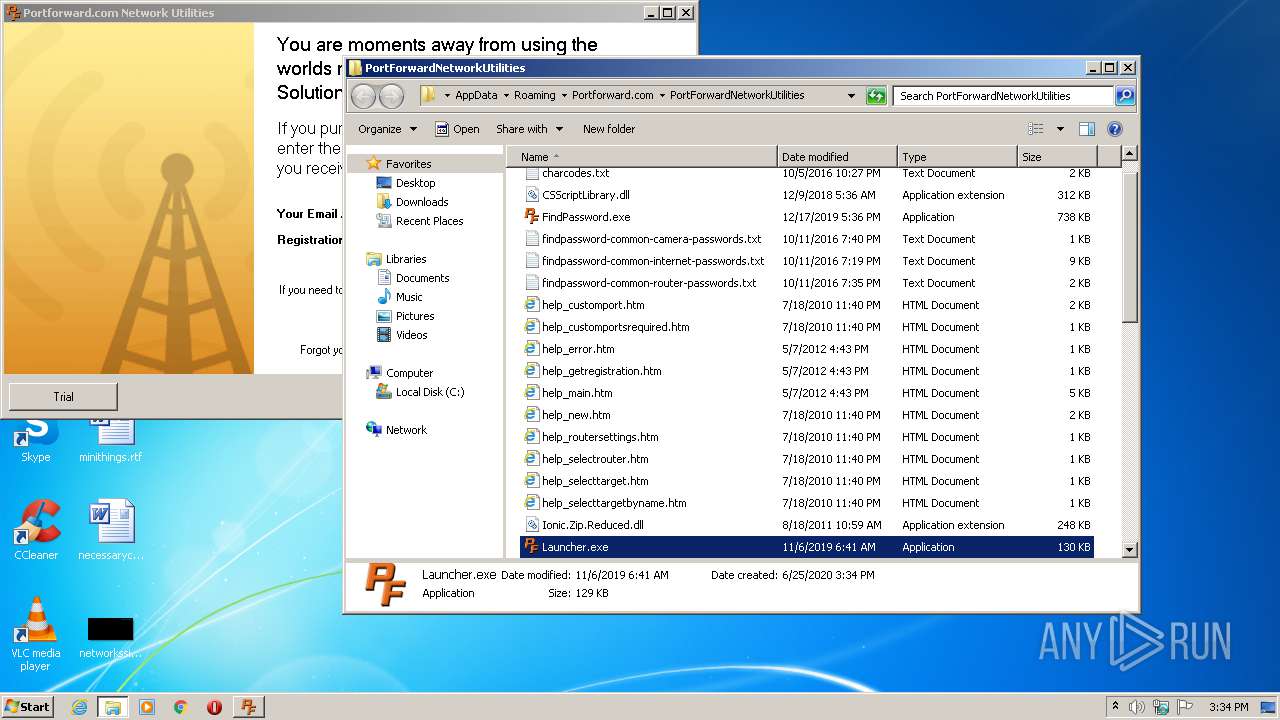
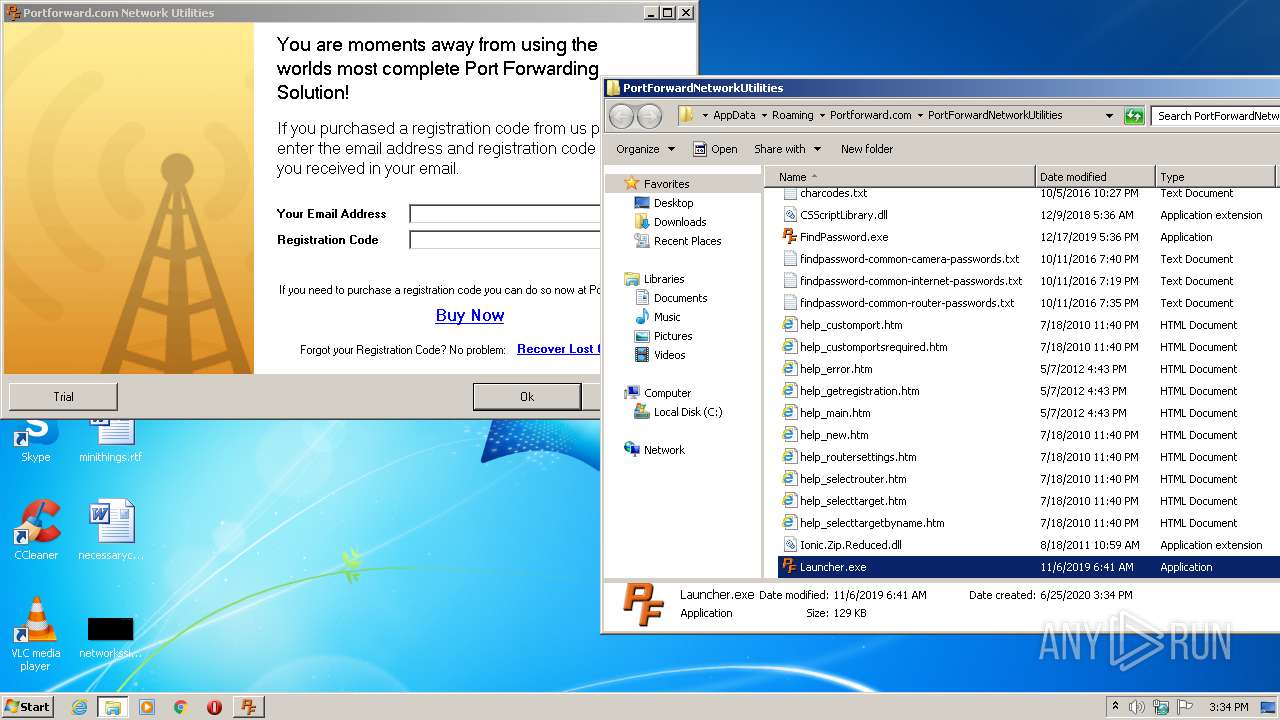
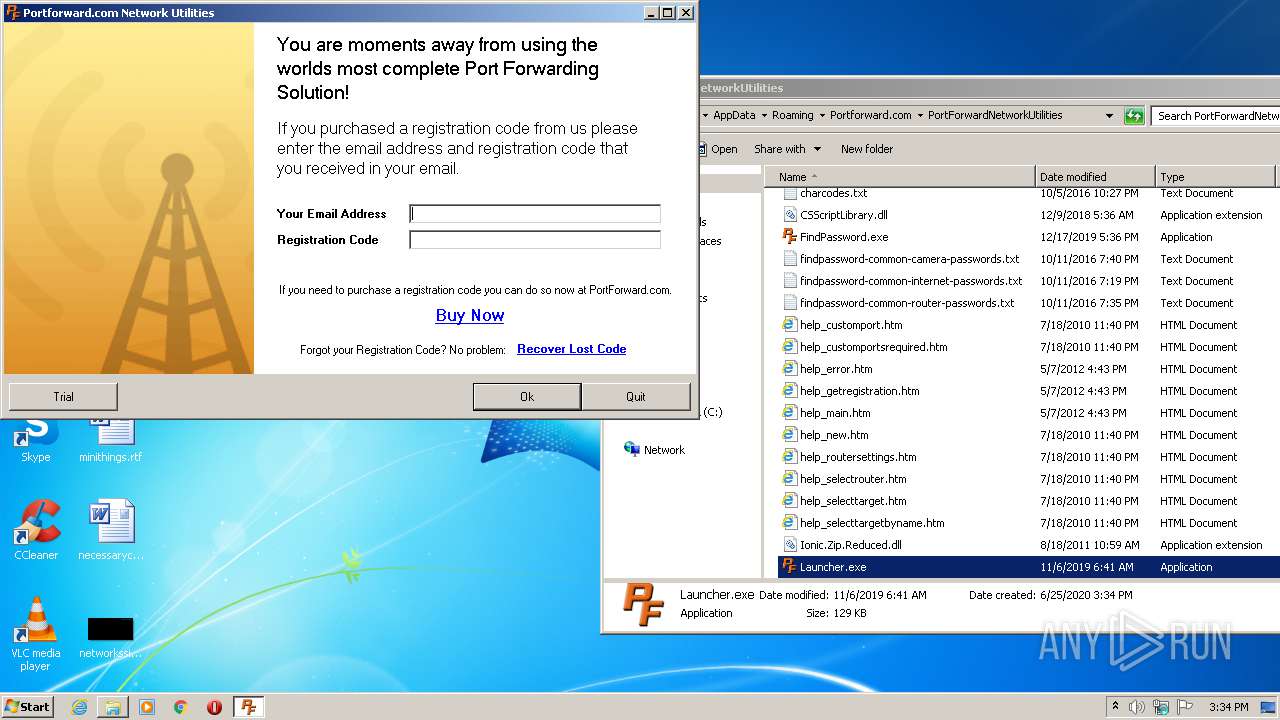
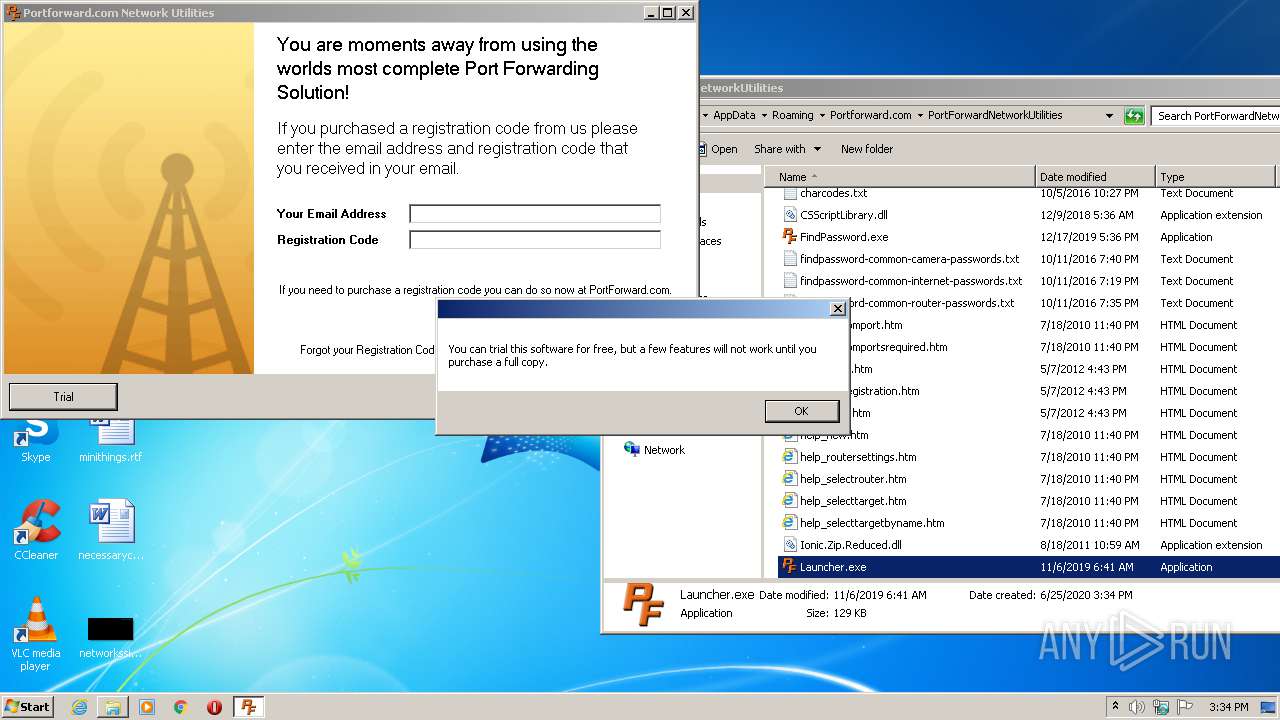
- Launcher.exe (PID: 2692)
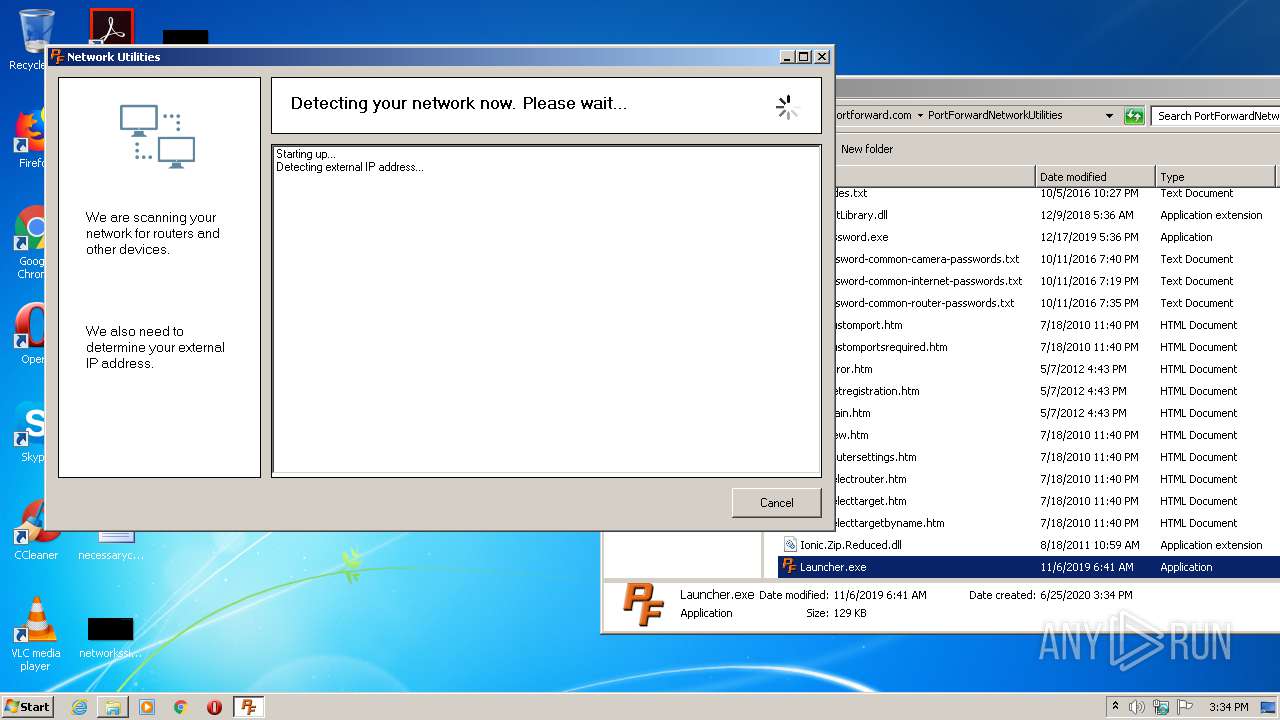
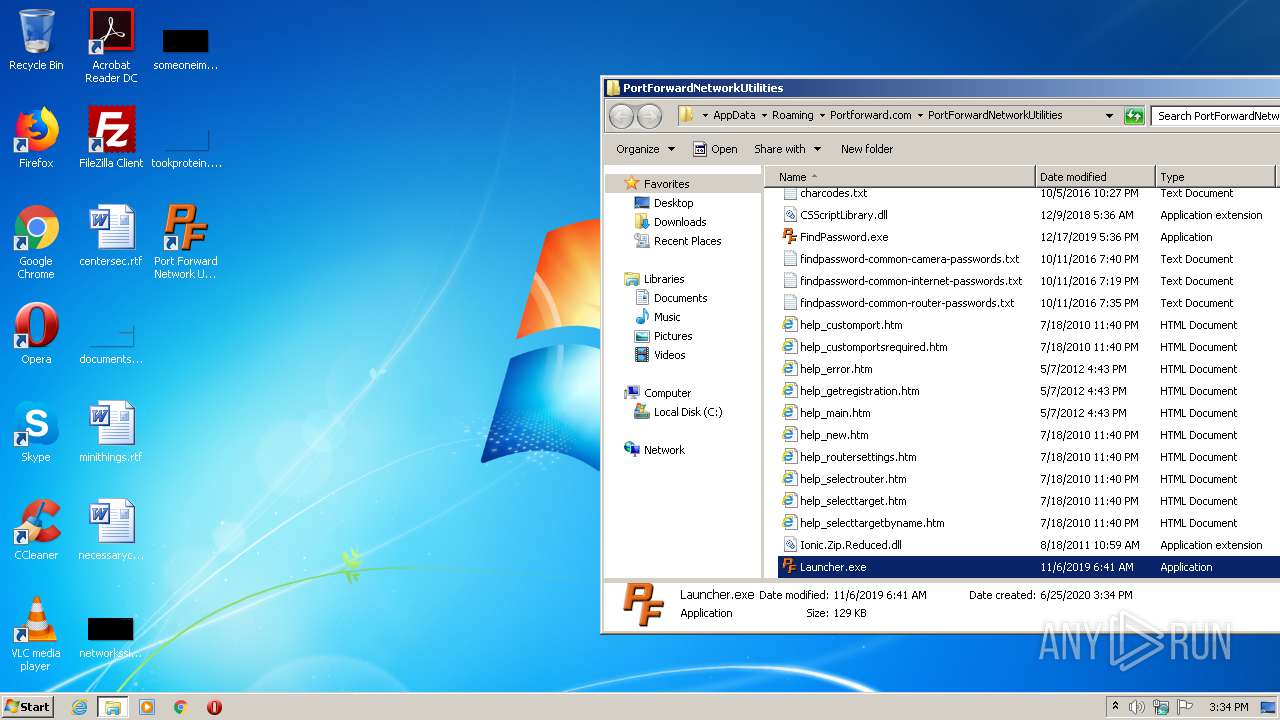
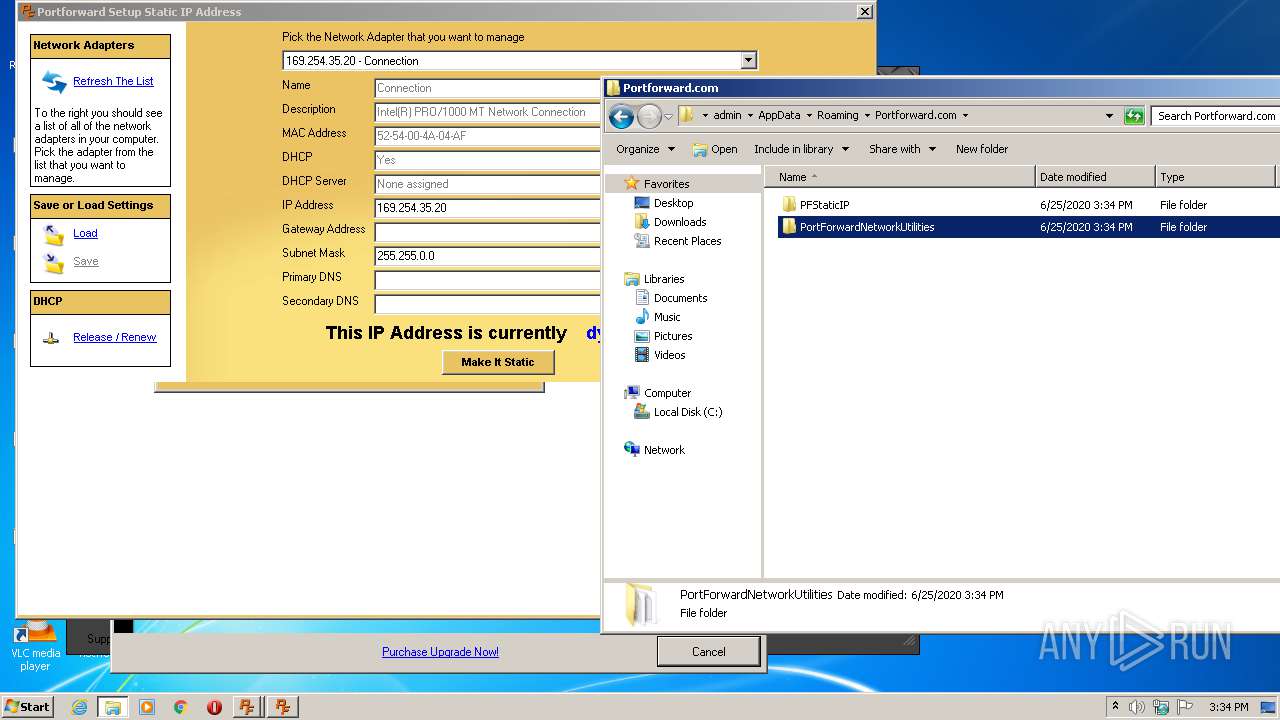
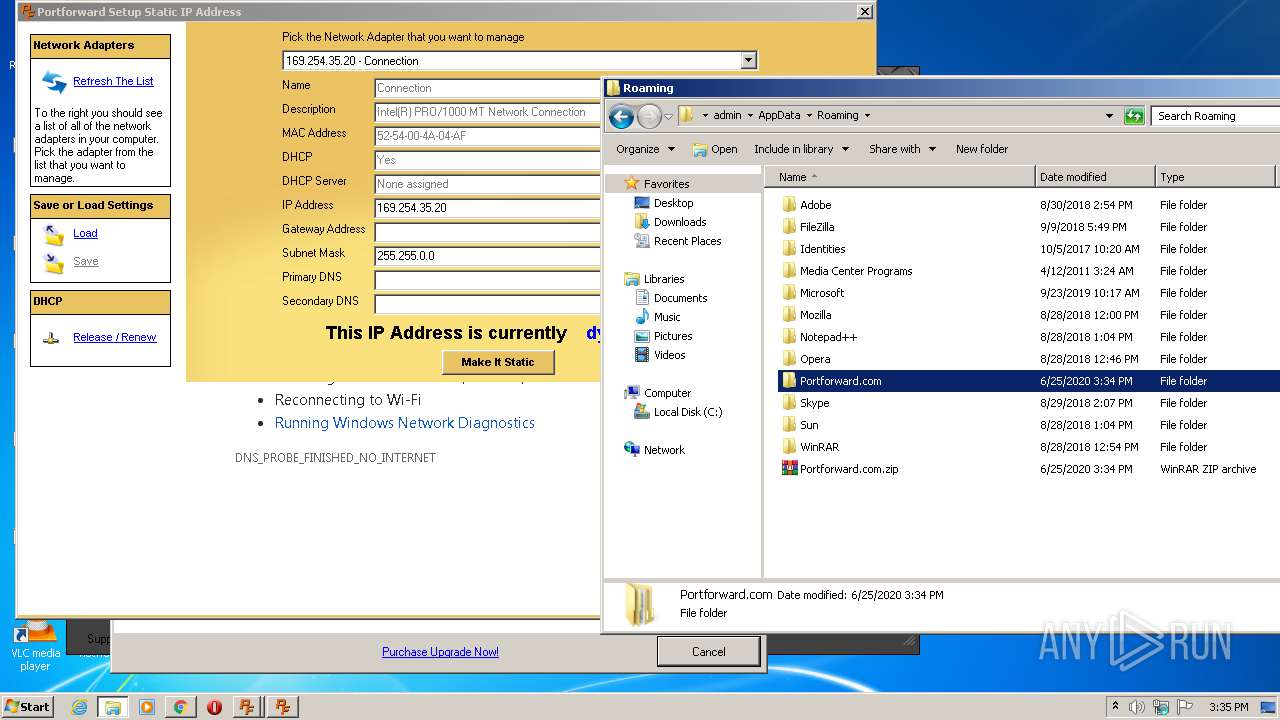
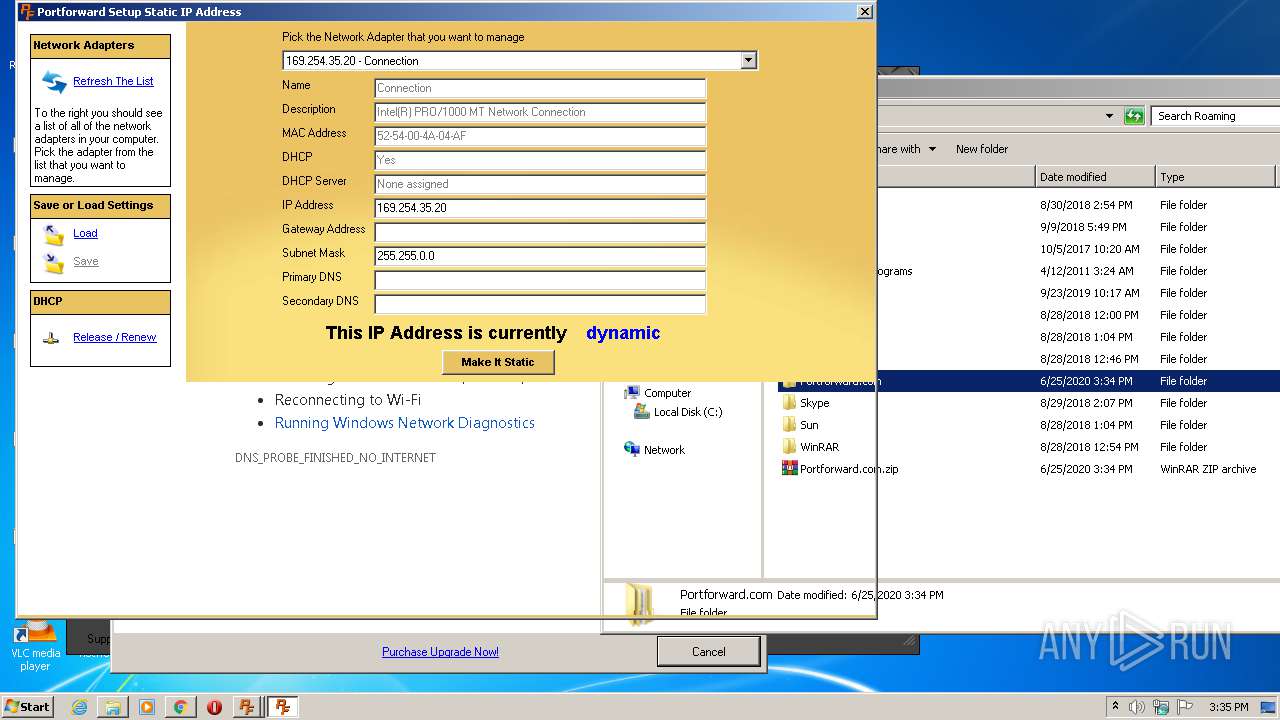
Application was dropped or rewritten from another process
- Launcher.exe (PID: 2692)
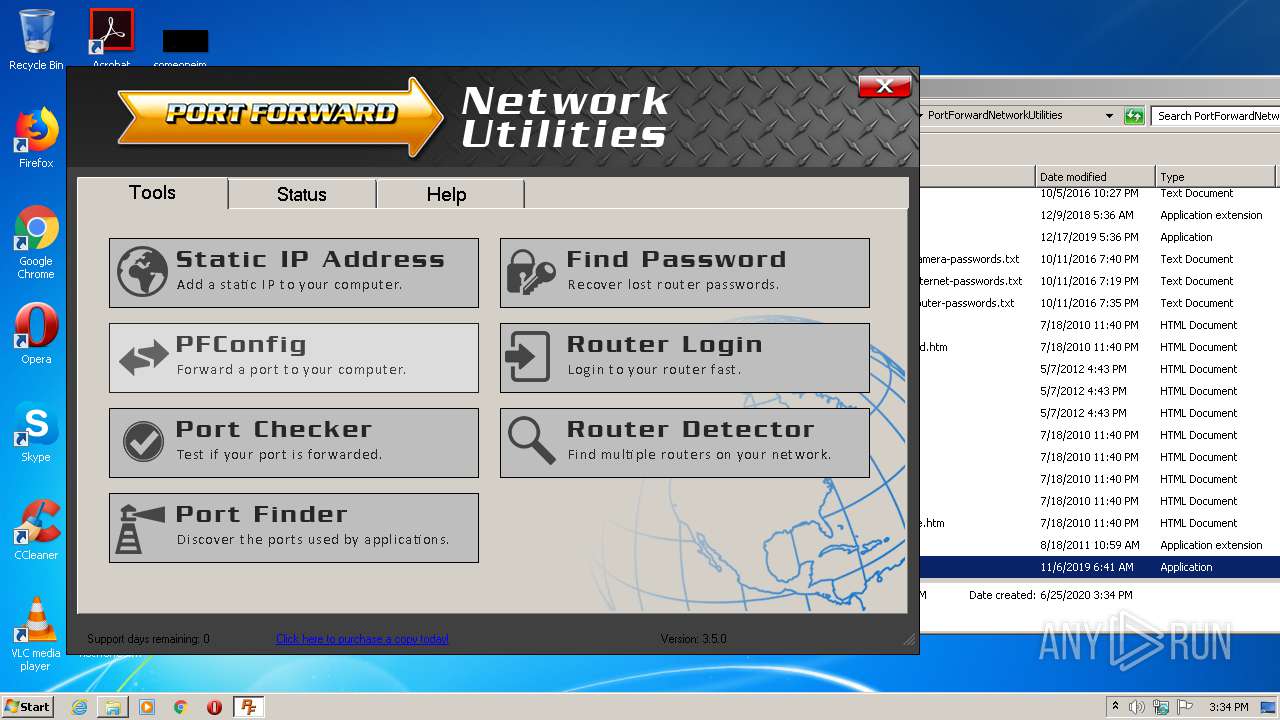
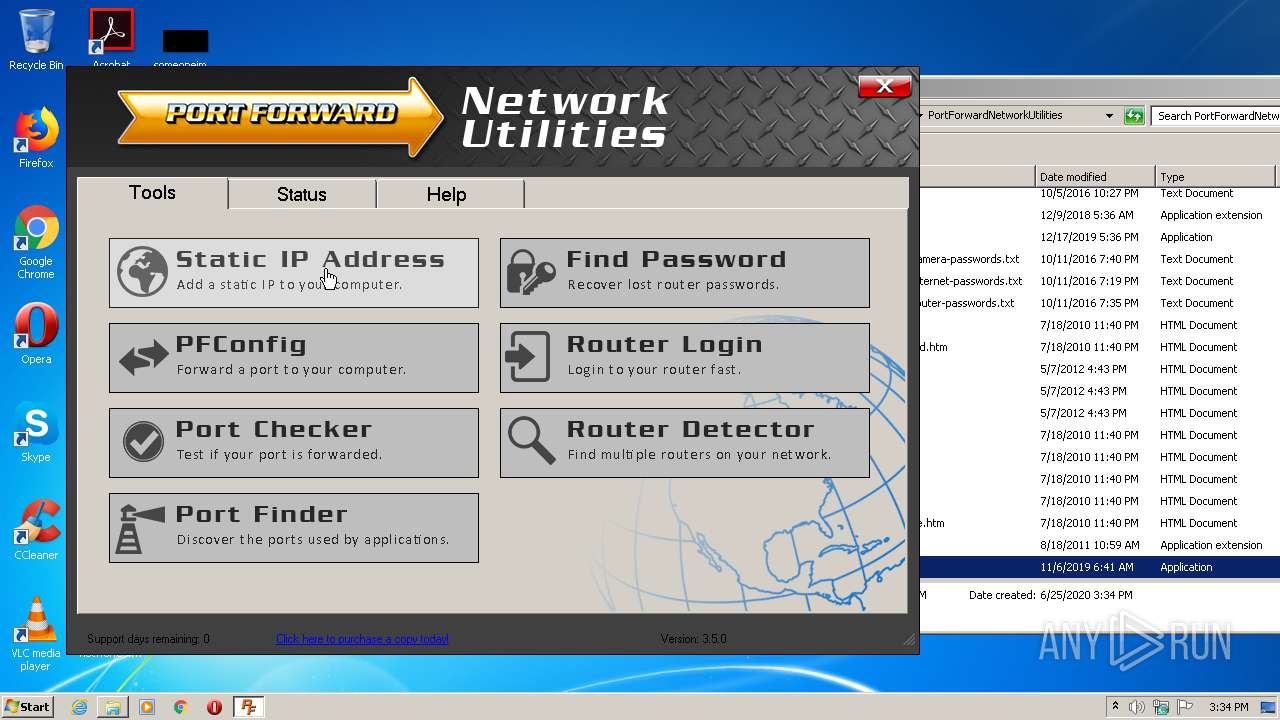
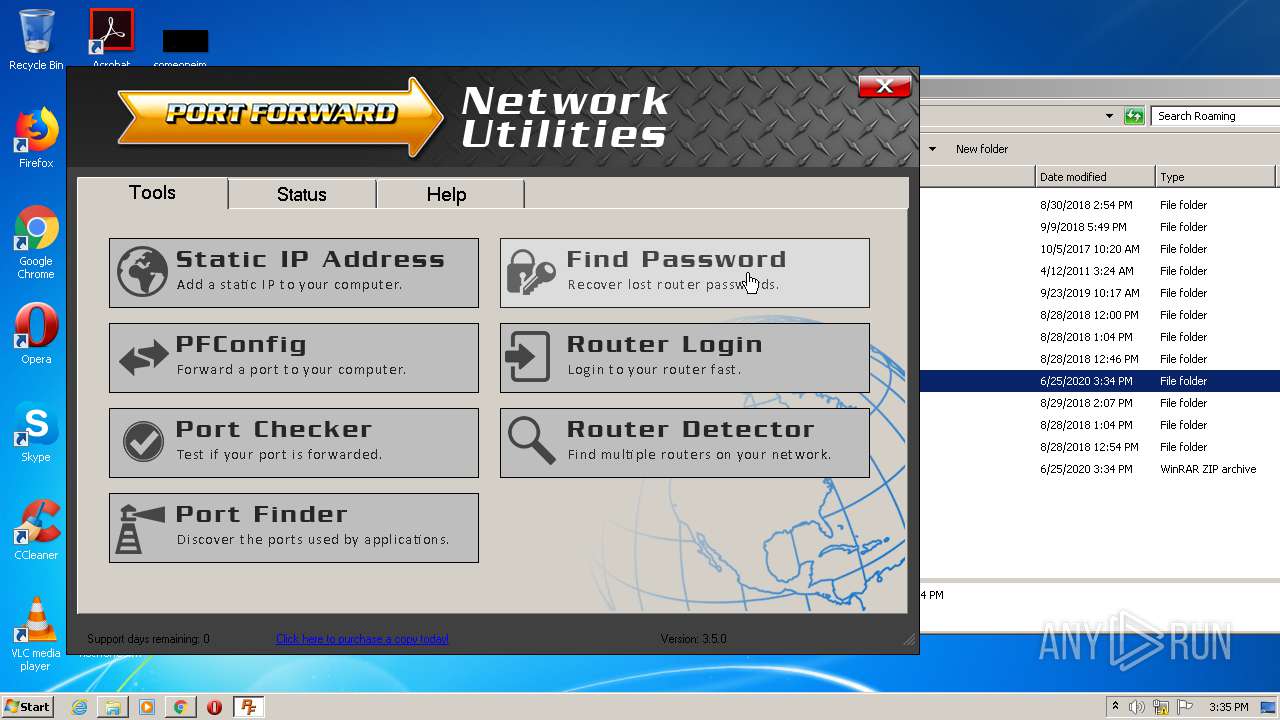
- PortForwardNetworkUtilities.exe (PID: 1572)
- PFStaticIP.exe (PID: 2148)
- PFStaticIP.exe (PID: 4020)
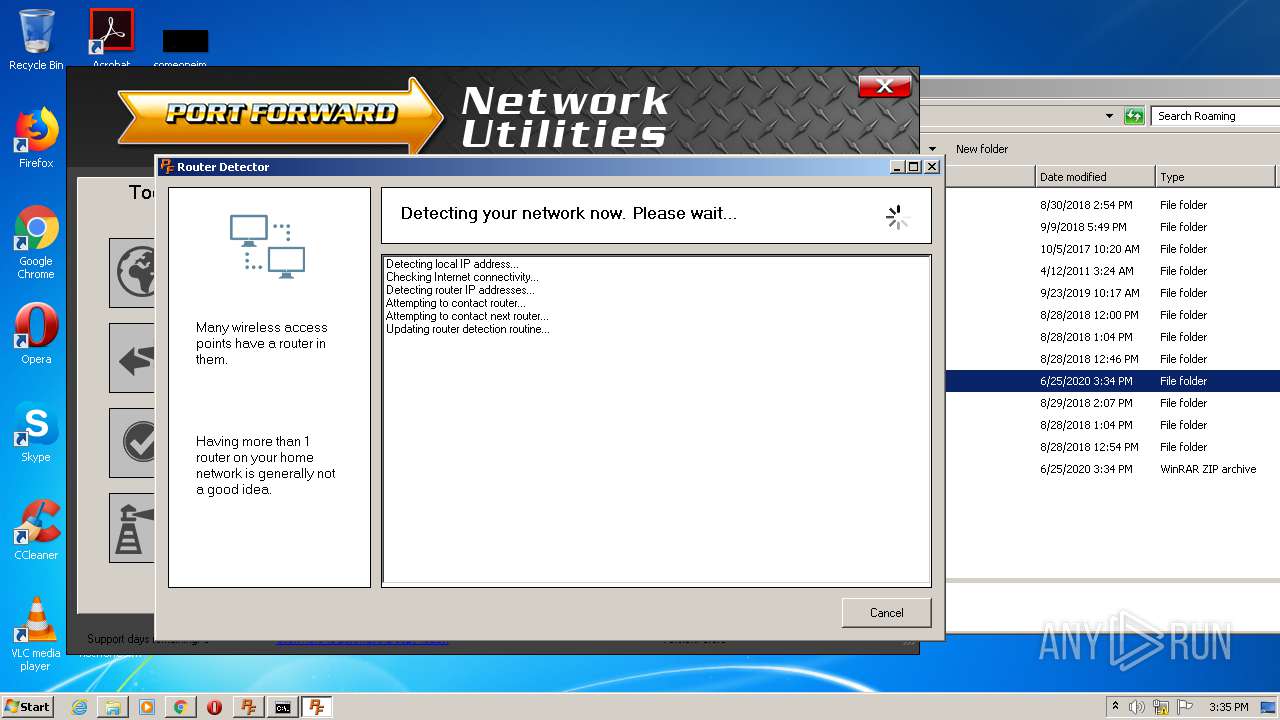
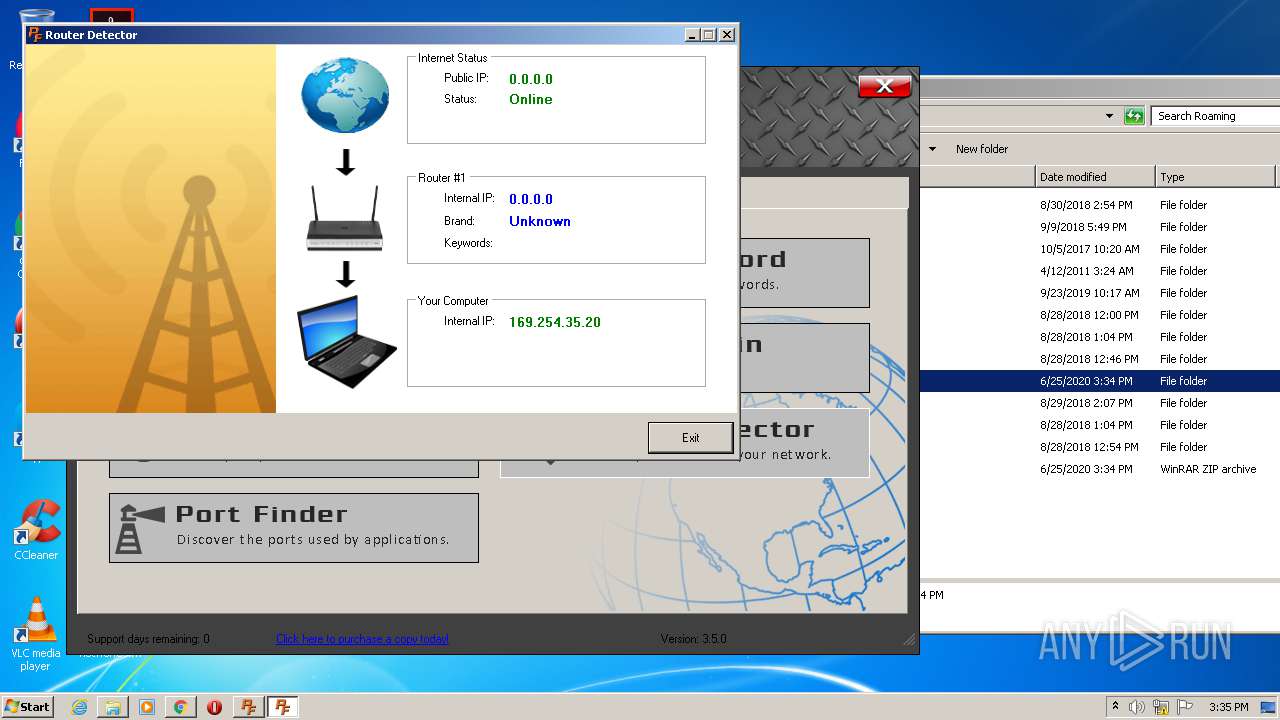
- PFRouterDetector.exe (PID: 3540)
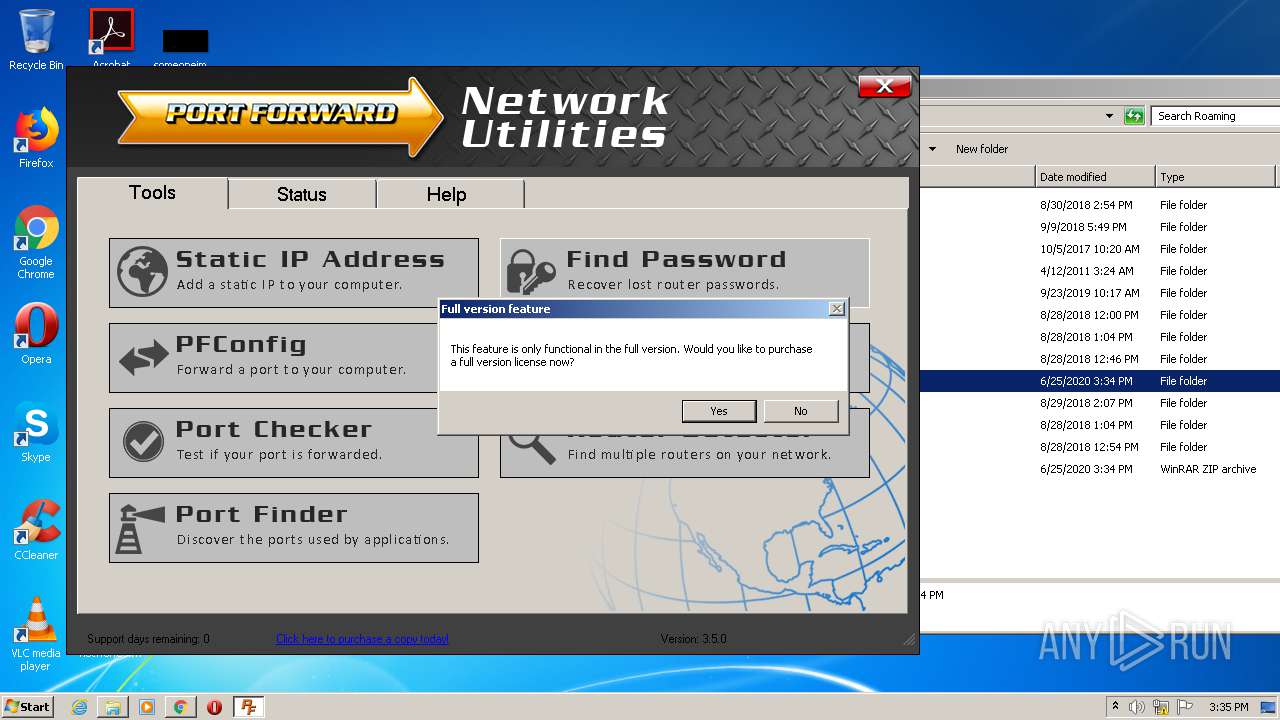
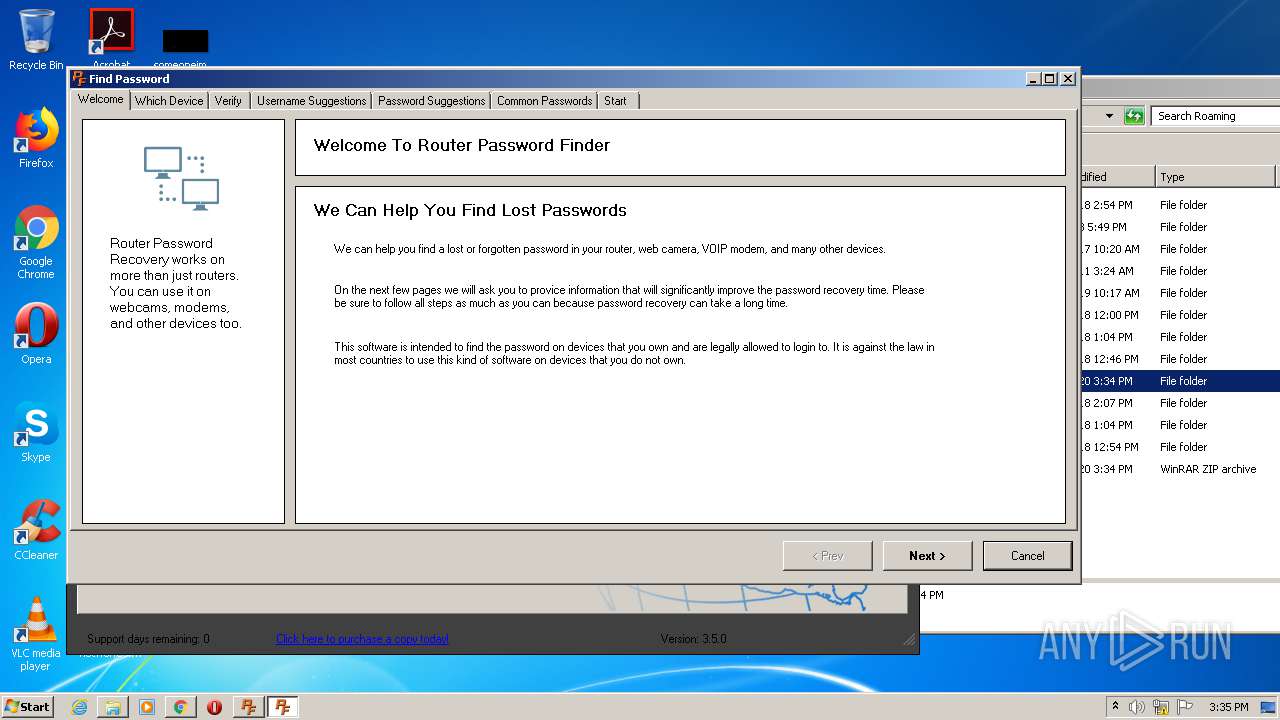
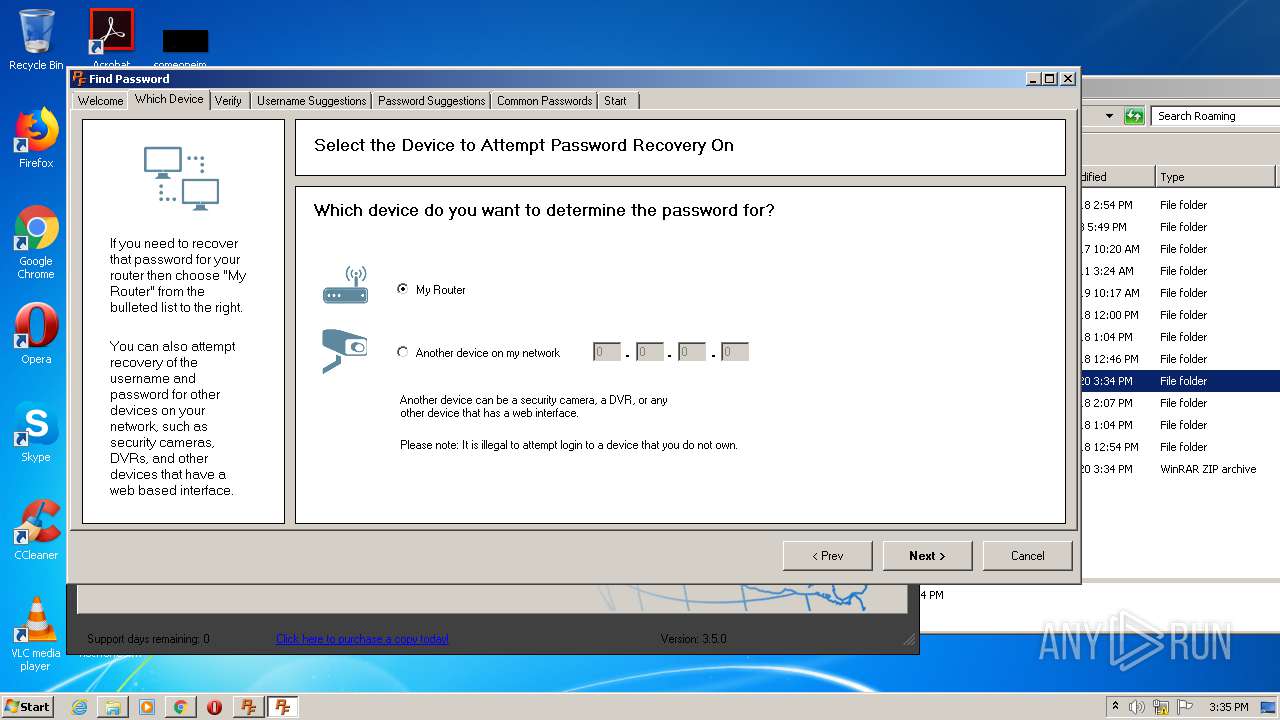
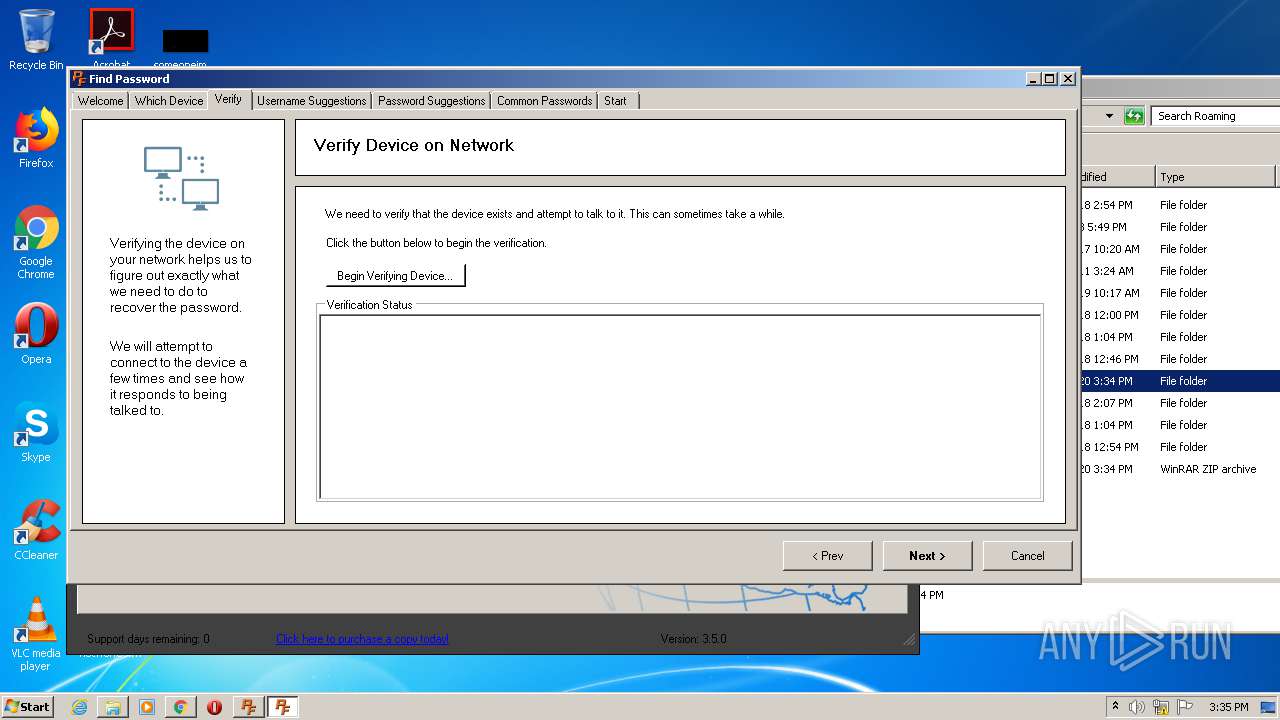
- FindPassword.exe (PID: 3440)
Changes settings of System certificates
- PFStaticIP.exe (PID: 4020)
SUSPICIOUS
Executable content was dropped or overwritten
- SetupPortForwardNetworkUtilities.exe (PID: 2720)
- SetupPortForwardNetworkUtilities.exe (PID: 4012)
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
- Launcher.exe (PID: 2692)
Reads the Windows organization settings
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
Reads Windows owner or organization settings
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
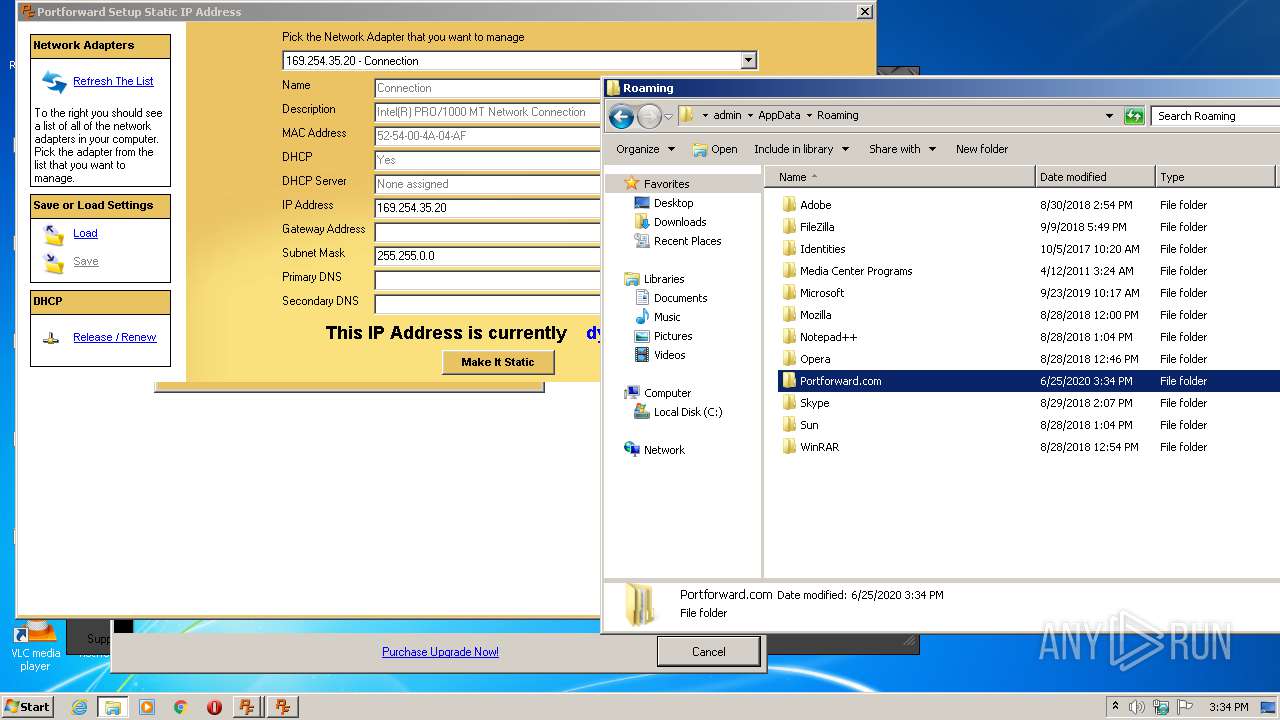
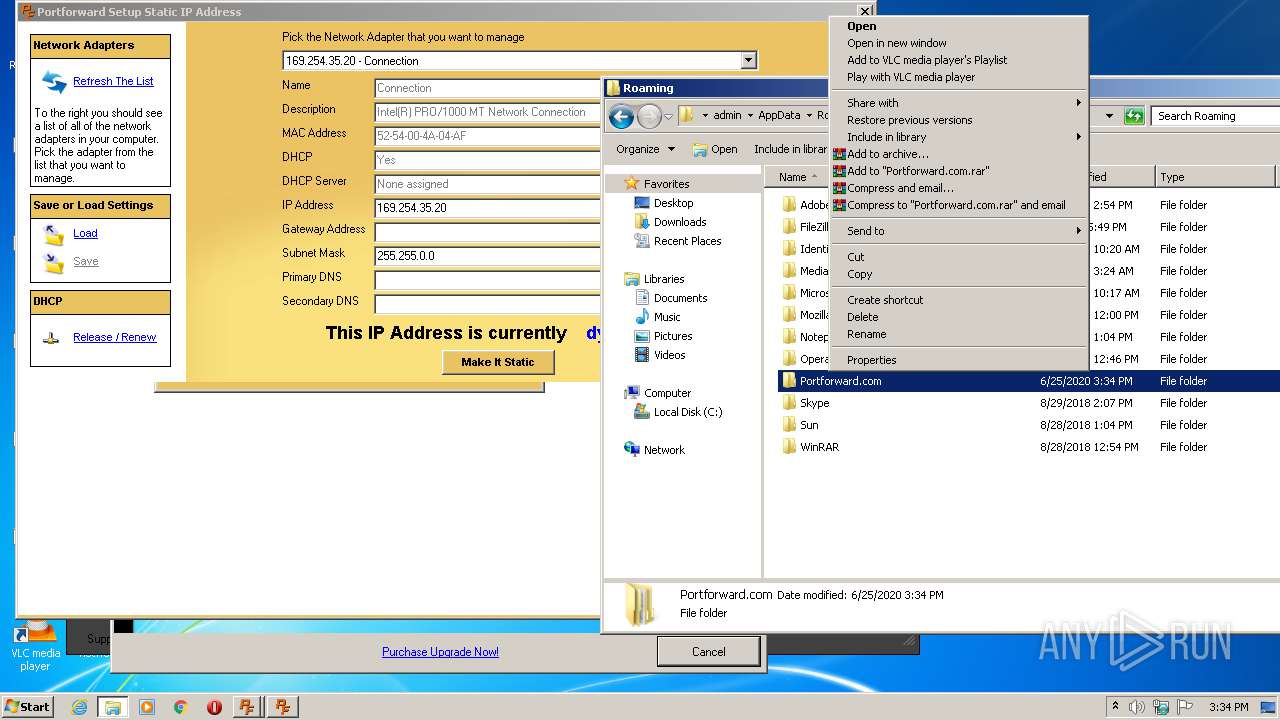
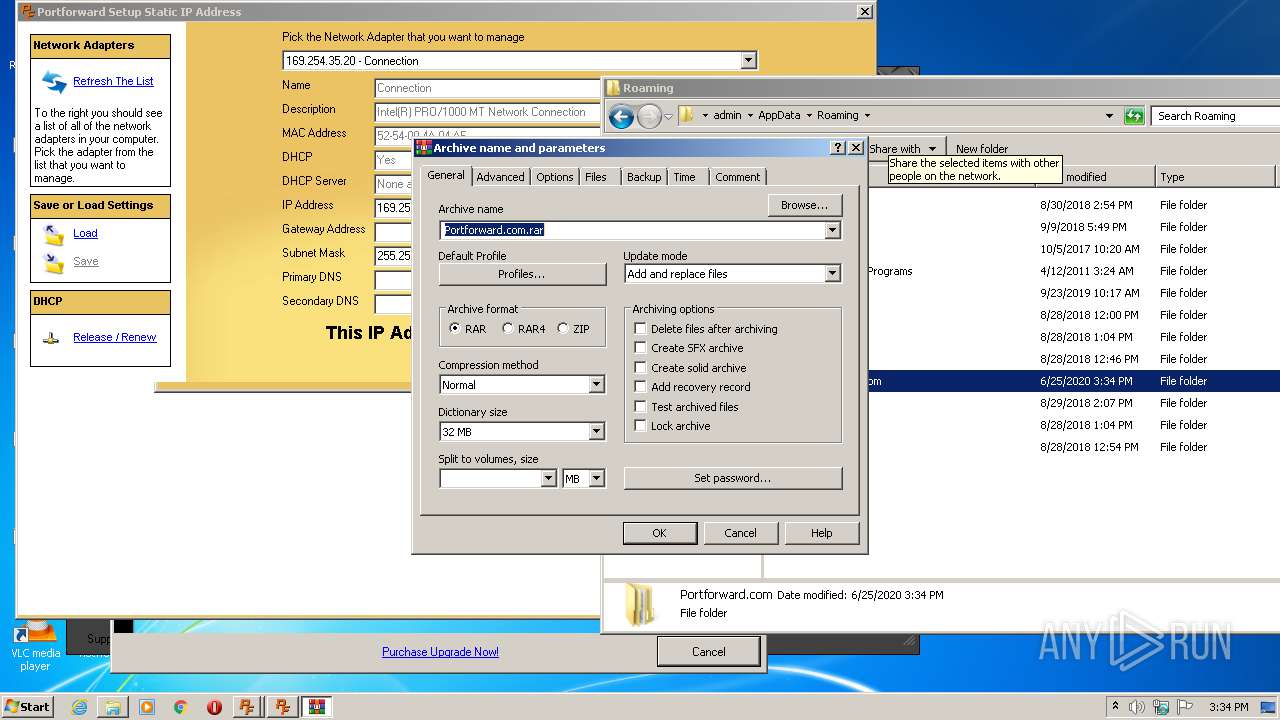
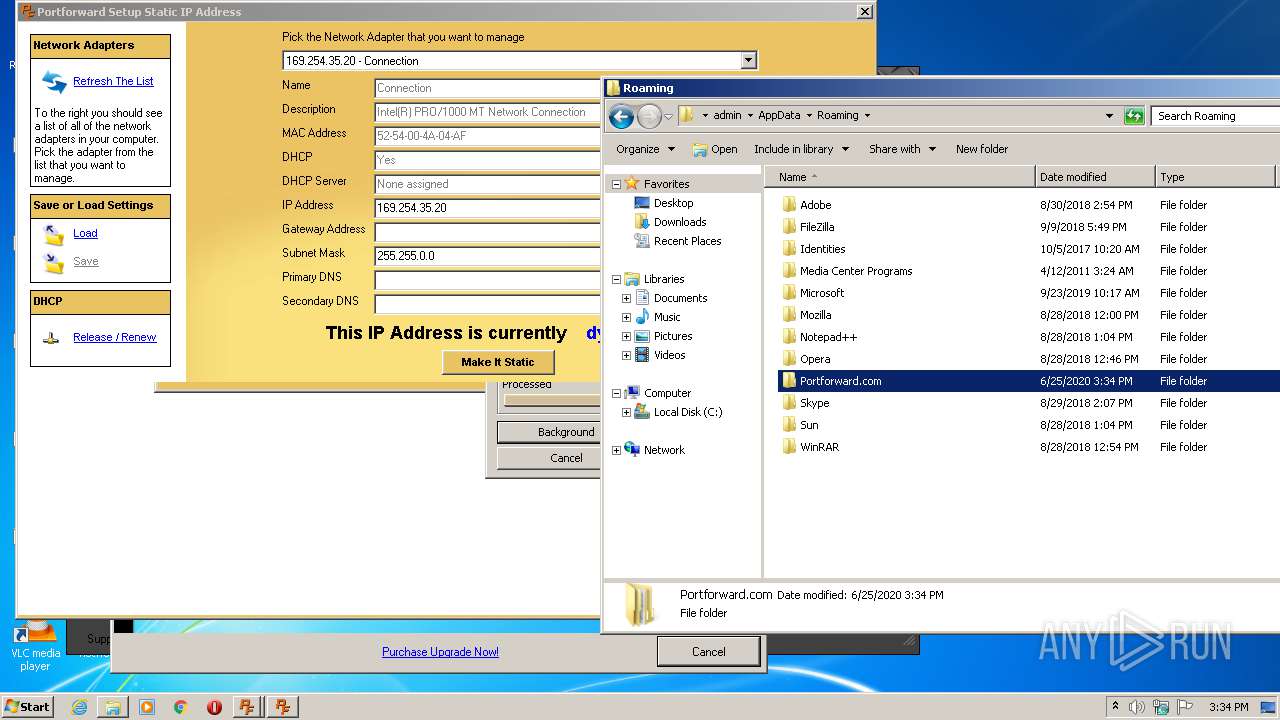
Creates files in the user directory
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
- Launcher.exe (PID: 2692)
- PortForwardNetworkUtilities.exe (PID: 1572)
- cmd.exe (PID: 3704)
- PFStaticIP.exe (PID: 4020)
- WinRAR.exe (PID: 2356)
- PFRouterDetector.exe (PID: 3540)
- cmd.exe (PID: 692)
- cmd.exe (PID: 1532)
- FindPassword.exe (PID: 3440)
- cmd.exe (PID: 2696)
- cmd.exe (PID: 2496)
Creates files in the Windows directory
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
Changes IE settings (feature browser emulation)
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
Reads Environment values
- Launcher.exe (PID: 2692)
- PortForwardNetworkUtilities.exe (PID: 1572)
- PFRouterDetector.exe (PID: 3540)
- FindPassword.exe (PID: 3440)
Reads internet explorer settings
- PortForwardNetworkUtilities.exe (PID: 1572)
- PFStaticIP.exe (PID: 4020)
Reads Internet Cache Settings
- PortForwardNetworkUtilities.exe (PID: 1572)
- PFStaticIP.exe (PID: 4020)
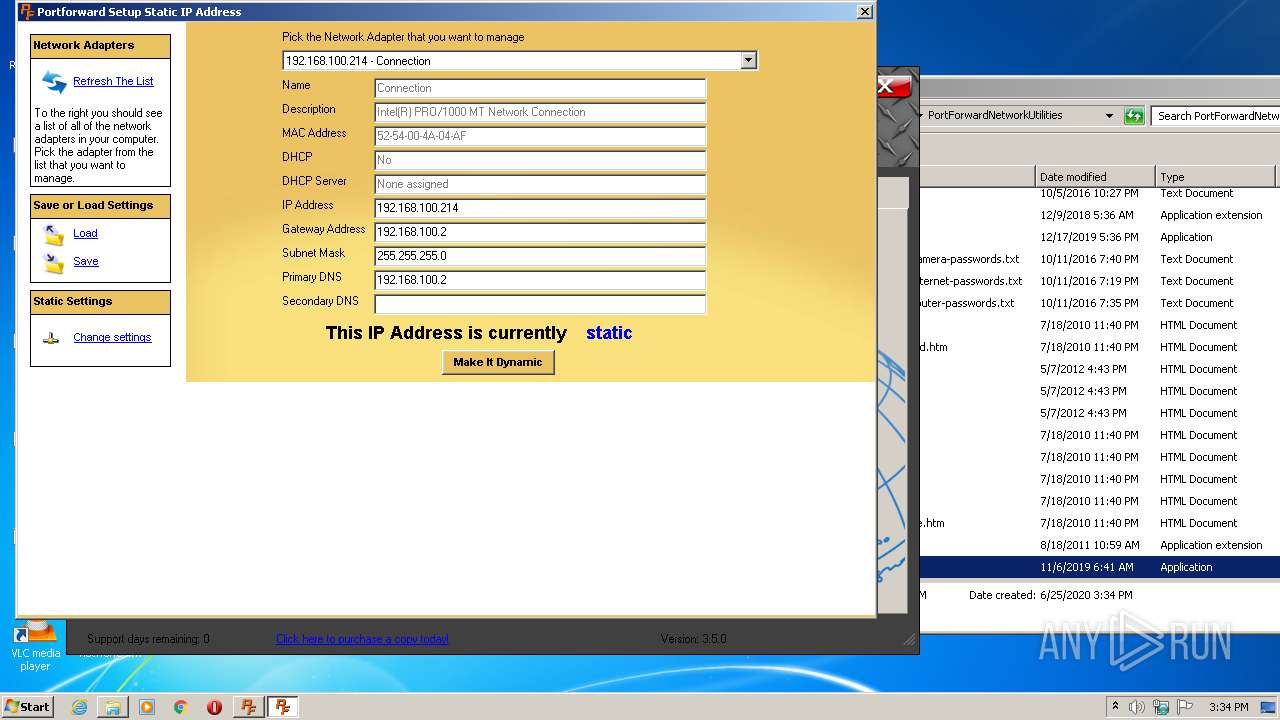
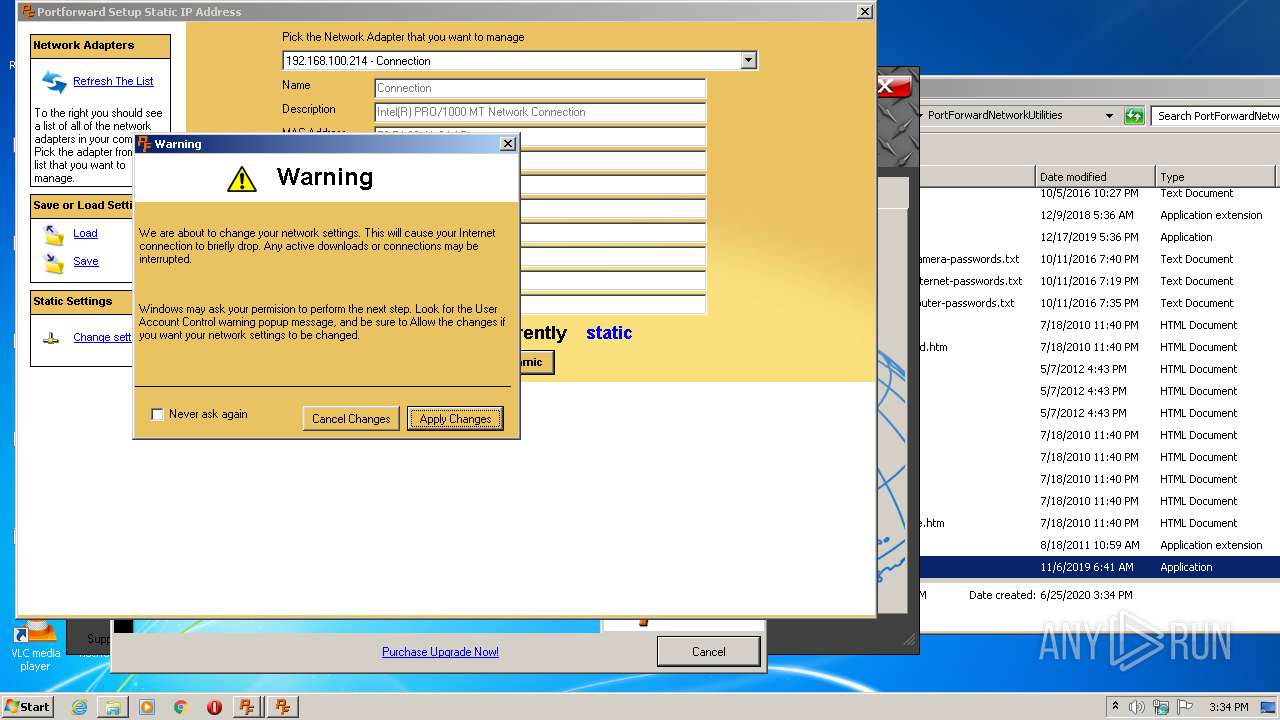
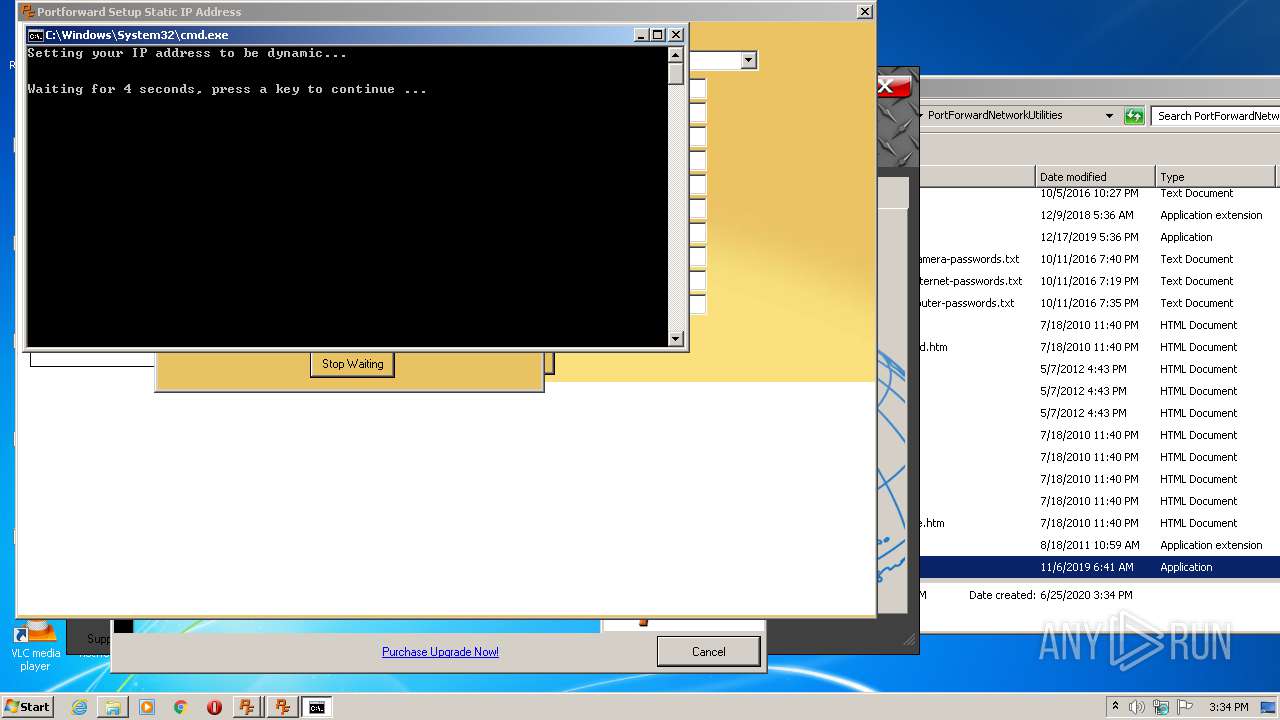
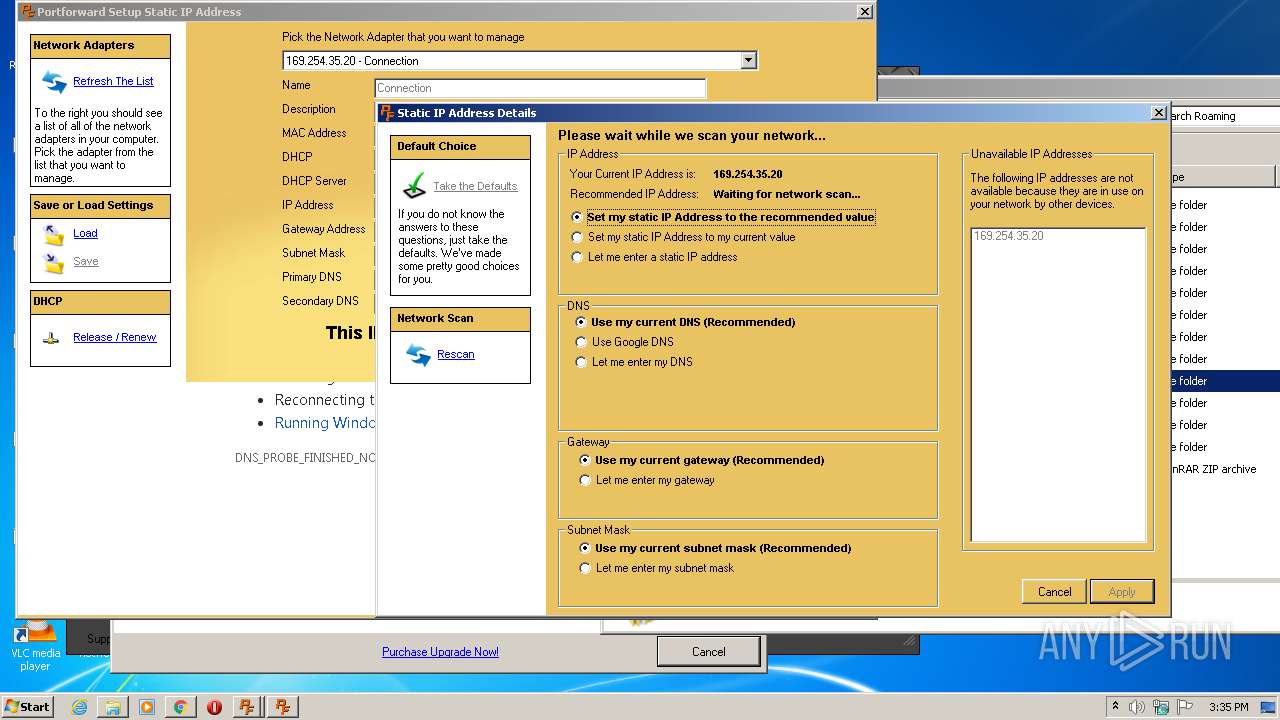
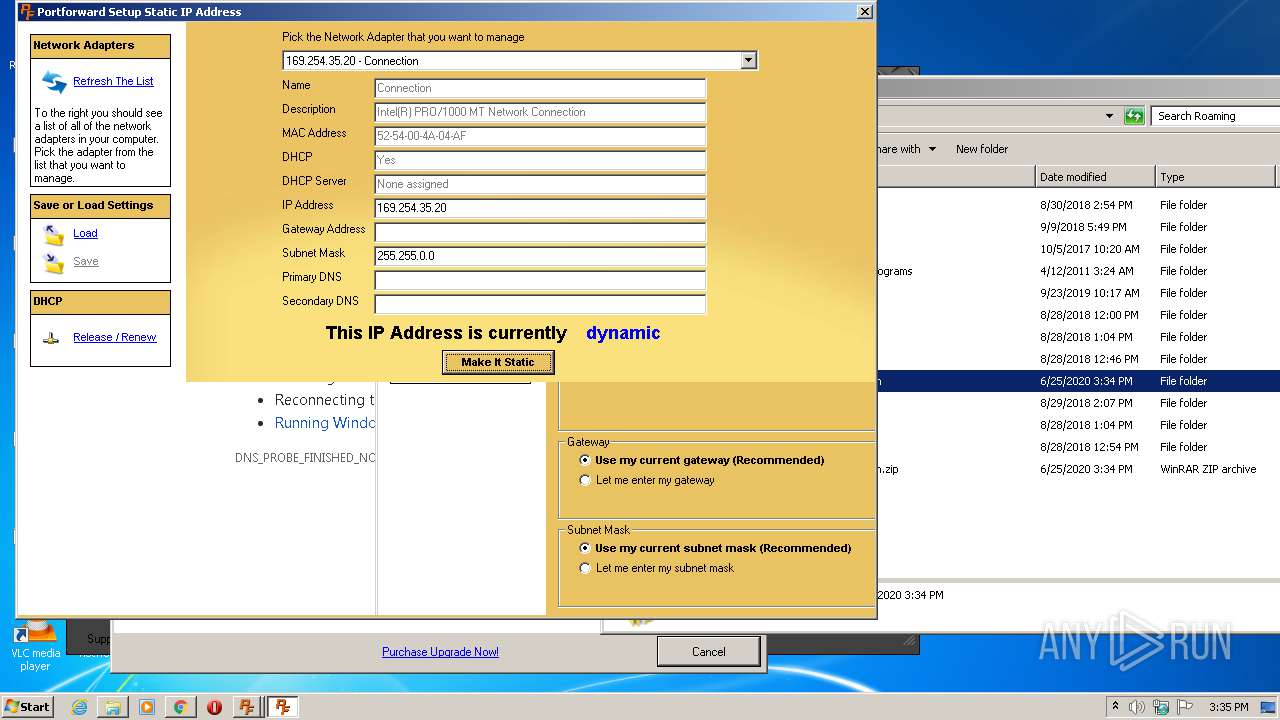
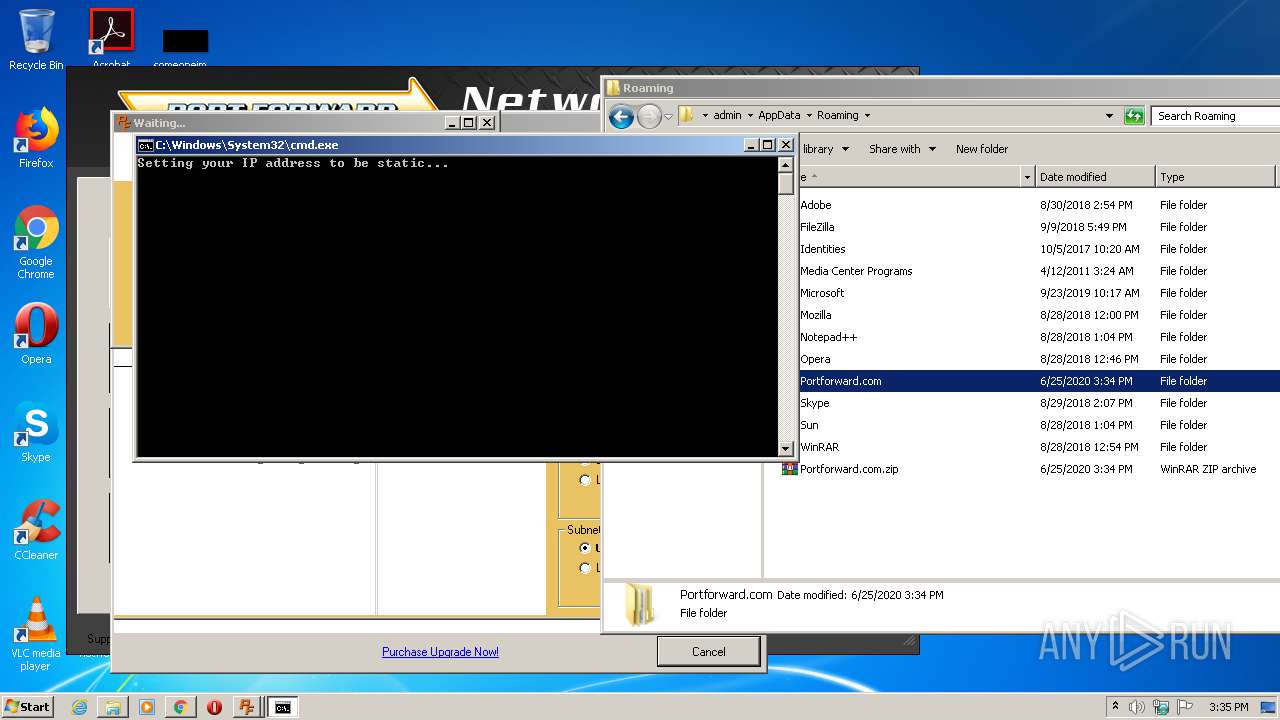
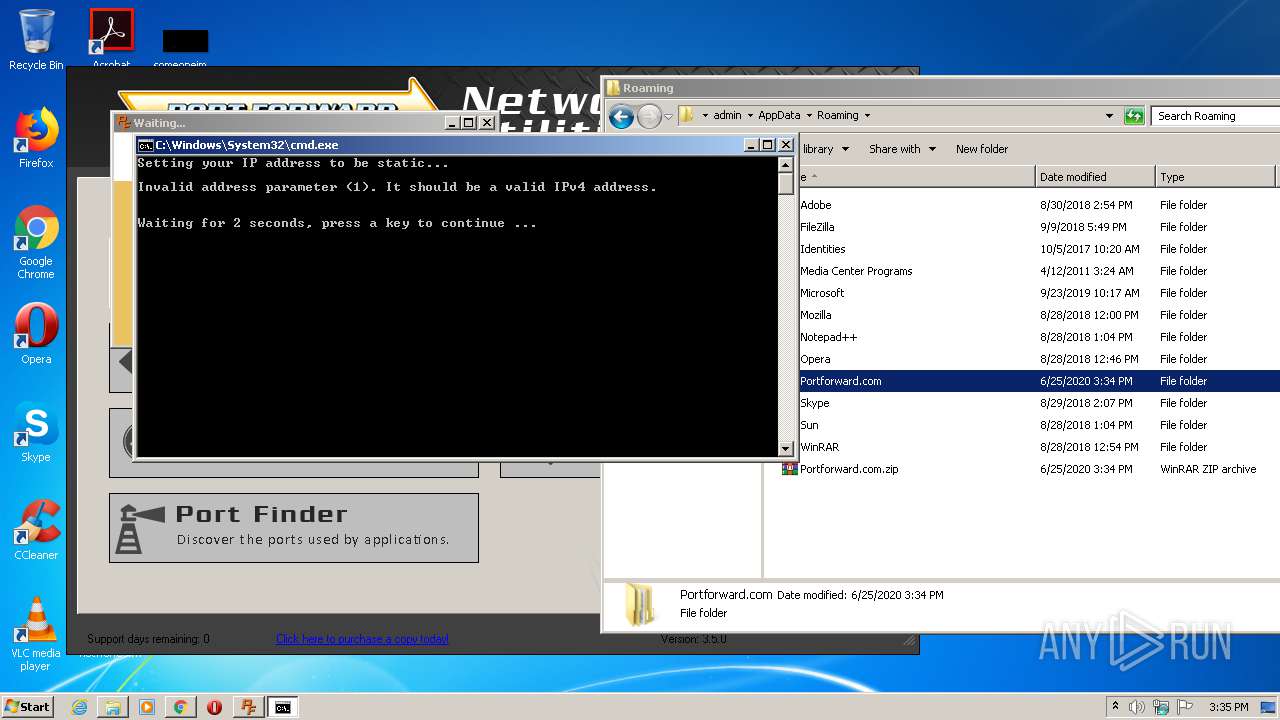
Starts CMD.EXE for commands execution
- PFStaticIP.exe (PID: 4020)
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3704)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 2496)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2696)
- cmd.exe (PID: 692)
Adds / modifies Windows certificates
- PFStaticIP.exe (PID: 4020)
INFO
Application was dropped or rewritten from another process
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
- SetupPortForwardNetworkUtilities.tmp (PID: 4036)
Creates files in the program directory
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
Creates a software uninstall entry
- SetupPortForwardNetworkUtilities.tmp (PID: 180)
Reads settings of System Certificates
- PFStaticIP.exe (PID: 4020)
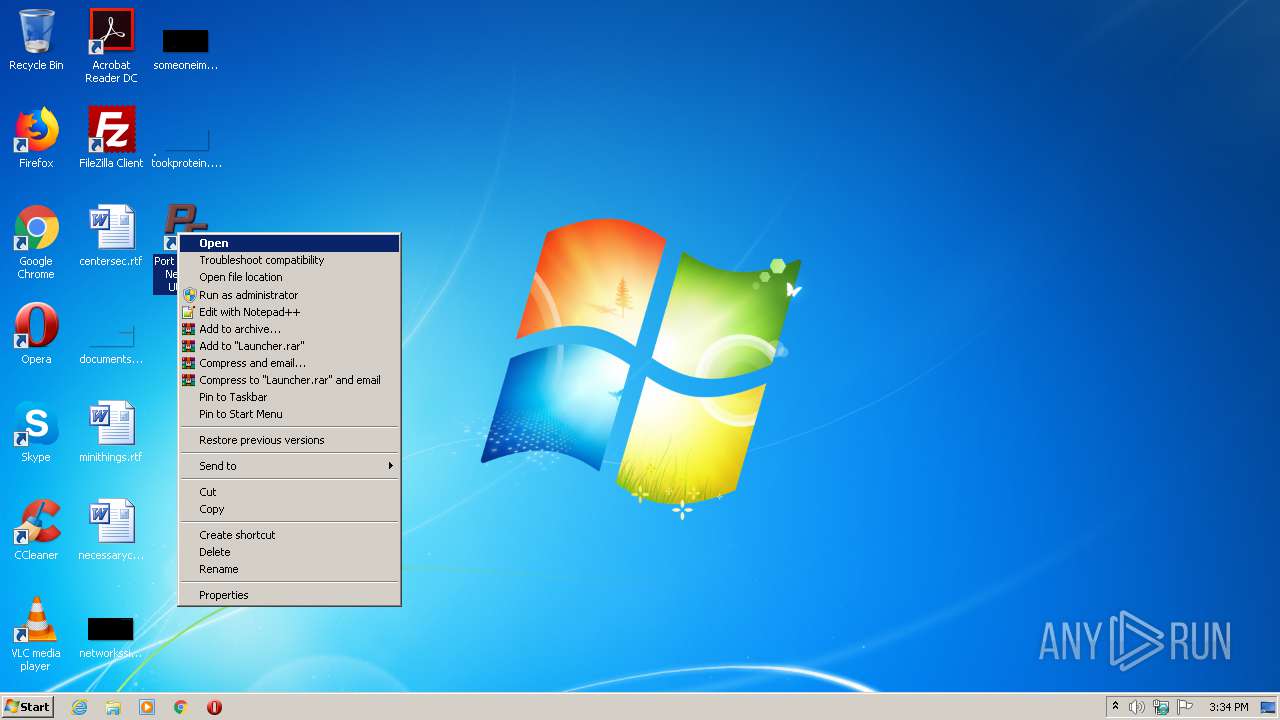
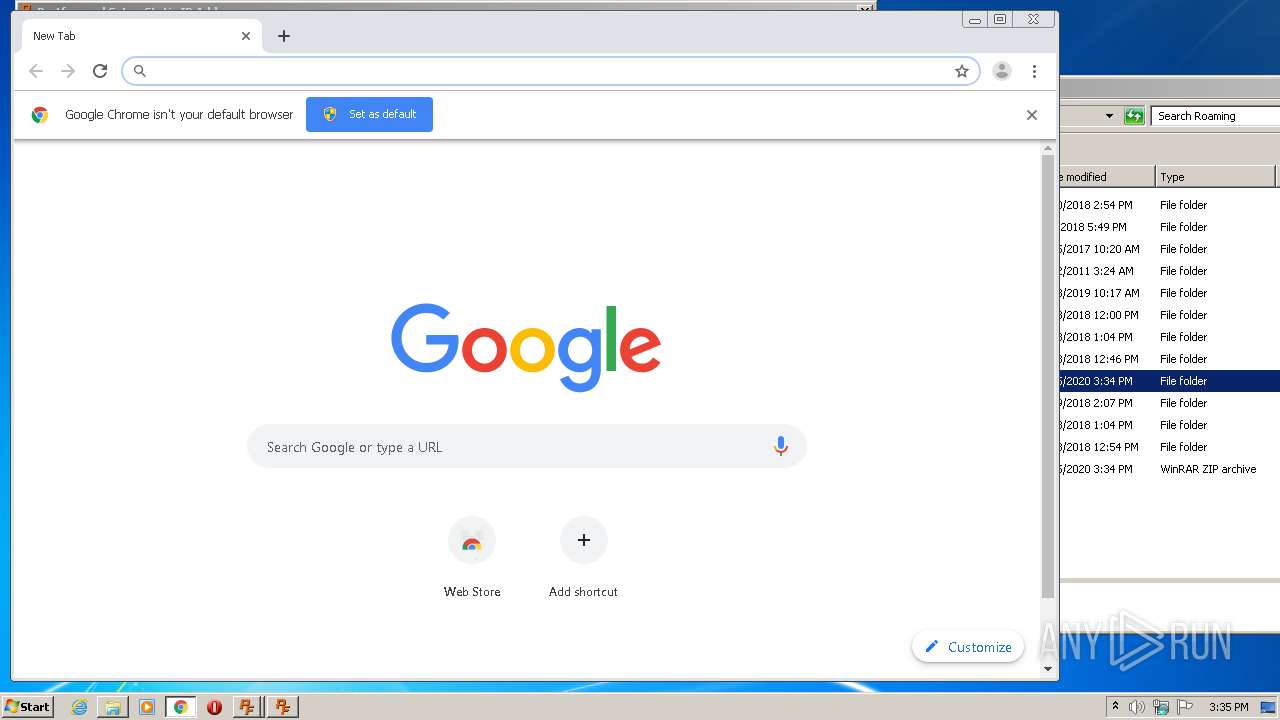
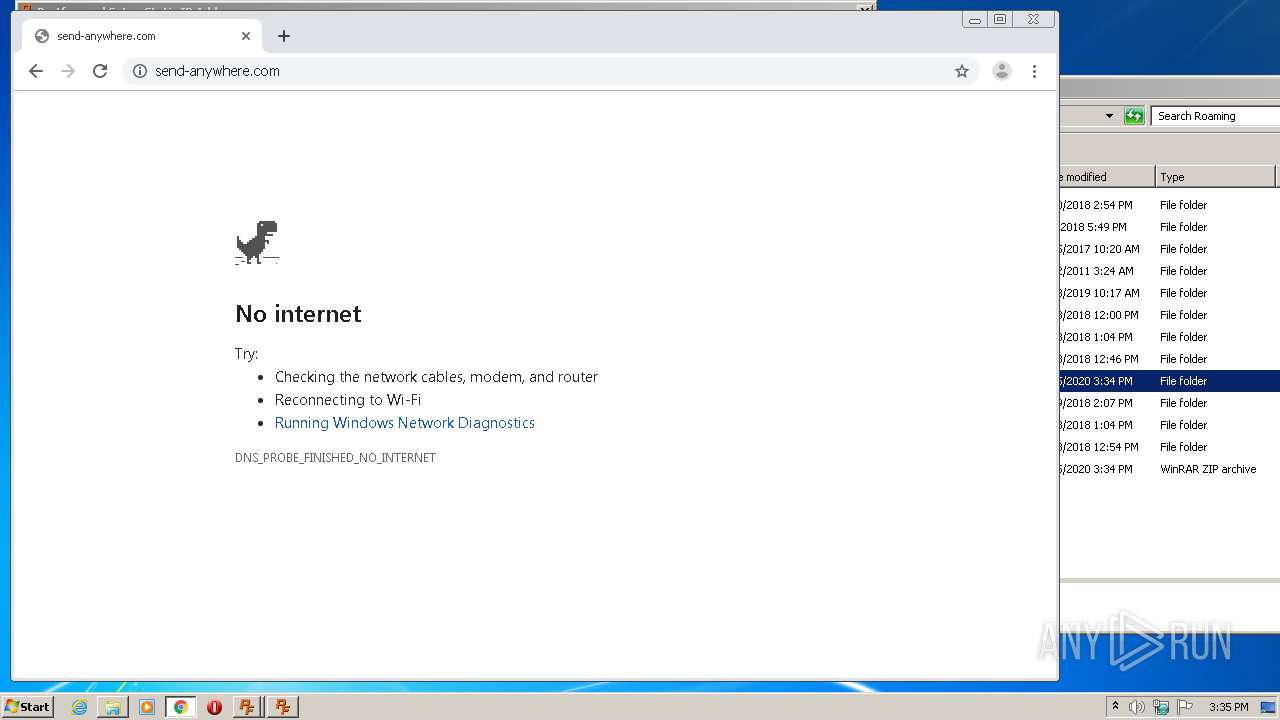
Manual execution by user
- WinRAR.exe (PID: 2356)
- chrome.exe (PID: 3152)
Reads the hosts file
- chrome.exe (PID: 3152)
- chrome.exe (PID: 3992)
Application launched itself
- chrome.exe (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:12 13:15:57+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 37888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Portforward, LLC |
| FileDescription: | Port Forward Network Utilities Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | Port Forward Network Utilities |
| ProductVersion: | 3.3.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Oct-2019 11:15:57 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Portforward, LLC |
| FileDescription: | Port Forward Network Utilities Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | Port Forward Network Utilities |
| ProductVersion: | 3.3.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 12-Oct-2019 11:15:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A50E8 | 0x000A5200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36928 |
.itext | 0x000A7000 | 0x00001668 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95181 |
.data | 0x000A9000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.03517 |
.bss | 0x000AD000 | 0x00006778 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000B4000 | 0x00000F1C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.79161 |
.didata | 0x000B5000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74582 |
.edata | 0x000B6000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.88107 |
.tls | 0x000B7000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000B8000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.37999 |
.rsrc | 0x000B9000 | 0x00004600 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43659 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4086 | 3.16547 | 864 | UNKNOWN | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | UNKNOWN | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | UNKNOWN | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000B063C |
__dbk_fcall_wrapper | 2 | 0x0000D3DC |
TMethodImplementationIntercept | 3 | 0x00053AC0 |
Total processes
94
Monitored processes
45
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,8541260012301034680,3714162340891568161,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4971530788139724804 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 180 | "C:\Users\admin\AppData\Local\Temp\is-S0IBO.tmp\SetupPortForwardNetworkUtilities.tmp" /SL5="$3013C,2669572,721408,C:\Users\admin\AppData\Local\Temp\SetupPortForwardNetworkUtilities.exe" /SPAWNWND=$20132 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-S0IBO.tmp\SetupPortForwardNetworkUtilities.tmp | SetupPortForwardNetworkUtilities.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,8541260012301034680,3714162340891568161,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4830481651344280197 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,8541260012301034680,3714162340891568161,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1957953457627125361 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 688 | netsh interface ip set dns "Connection" static | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\AppData\Roaming\Portforward.com\PFStaticIP\set_to_static.bat" | C:\Windows\System32\cmd.exe | — | PFStaticIP.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,8541260012301034680,3714162340891568161,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18337580307120920684 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | netsh interface ip set address name="Connection" static 1 | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,8541260012301034680,3714162340891568161,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4532864043178970473 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | C:\Windows\system32\cmd.exe /C "C:\Users\admin\AppData\Roaming\Portforward.com\PFStaticIP\runipconfig.bat" | C:\Windows\system32\cmd.exe | — | PFStaticIP.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
5 055
Read events
3 053
Write events
1 935
Delete events
67
Modification events
| (PID) Process: | (180) SetupPortForwardNetworkUtilities.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B4000000E47B00ACFD4AD601 | |||
| (PID) Process: | (180) SetupPortForwardNetworkUtilities.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 437638A3D084F6FA51431CEFEEB452D038252D9409143A82E125D98513D3C083 | |||
| (PID) Process: | (180) SetupPortForwardNetworkUtilities.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (180) SetupPortForwardNetworkUtilities.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\Launcher.exe | |||
| (PID) Process: | (180) SetupPortForwardNetworkUtilities.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 4B3AD316D19DD8431E448DDF0A3EB9D464783856F97F377A0E7EA55EBDAEAC8A | |||
| (PID) Process: | (2552) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{996BF5E0-8044-4650-ADEB-0B013914E99C} |
| Operation: | write | Name: | |
Value: Microsoft ListView Control 6.0 (SP6) | |||
| (PID) Process: | (2552) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{996BF5E0-8044-4650-ADEB-0B013914E99C}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Windows\system32\MSCOMCTL.OCX | |||
| (PID) Process: | (2552) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{996BF5E0-8044-4650-ADEB-0B013914E99C}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (2552) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComctlLib.ListViewCtrl |
| Operation: | write | Name: | |
Value: Microsoft ListView Control 6.0 (SP6) | |||
| (PID) Process: | (2552) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\MSComctlLib.ListViewCtrl\CLSID |
| Operation: | write | Name: | |
Value: {996BF5E0-8044-4650-ADEB-0B013914E99C} | |||
Executable files
23
Suspicious files
15
Text files
211
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 180 | SetupPortForwardNetworkUtilities.tmp | C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\is-6818B.tmp | — | |
MD5:— | SHA256:— | |||
| 180 | SetupPortForwardNetworkUtilities.tmp | C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\is-KRE3B.tmp | — | |
MD5:— | SHA256:— | |||
| 180 | SetupPortForwardNetworkUtilities.tmp | C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\is-IR9PK.tmp | — | |
MD5:— | SHA256:— | |||
| 180 | SetupPortForwardNetworkUtilities.tmp | C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\is-GC5LA.tmp | — | |
MD5:— | SHA256:— | |||
| 180 | SetupPortForwardNetworkUtilities.tmp | C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\is-BCFSU.tmp | — | |
MD5:— | SHA256:— | |||
| 180 | SetupPortForwardNetworkUtilities.tmp | C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\is-7F5LC.tmp | — | |
MD5:— | SHA256:— | |||
| 180 | SetupPortForwardNetworkUtilities.tmp | C:\Windows\system32\is-LS7AO.tmp | — | |
MD5:— | SHA256:— | |||
| 180 | SetupPortForwardNetworkUtilities.tmp | C:\Windows\system32\is-BUVTS.tmp | — | |
MD5:— | SHA256:— | |||
| 2692 | Launcher.exe | C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\version | — | |
MD5:— | SHA256:— | |||
| 2692 | Launcher.exe | C:\Users\admin\AppData\Roaming\Portforward.com\PortForwardNetworkUtilities\PortForwardNetworkUtilities.exe.pls | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1572 | PortForwardNetworkUtilities.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAwjODFPn3Ye7EY4D9W39qs%3D | US | der | 279 b | whitelisted |
1572 | PortForwardNetworkUtilities.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2692 | Launcher.exe | 172.67.68.62:443 | portforward.com | — | US | unknown |
1572 | PortForwardNetworkUtilities.exe | 65.112.29.35:443 | secure.portforward.com | Computer Country | US | unknown |
1572 | PortForwardNetworkUtilities.exe | 172.67.68.62:443 | portforward.com | — | US | unknown |
1572 | PortForwardNetworkUtilities.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4020 | PFStaticIP.exe | 172.67.68.62:80 | portforward.com | — | US | unknown |
4020 | PFStaticIP.exe | 172.67.68.62:443 | portforward.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
portforward.com |
| whitelisted |
secure.portforward.com |
| unknown |
ocsp.digicert.com |
| whitelisted |