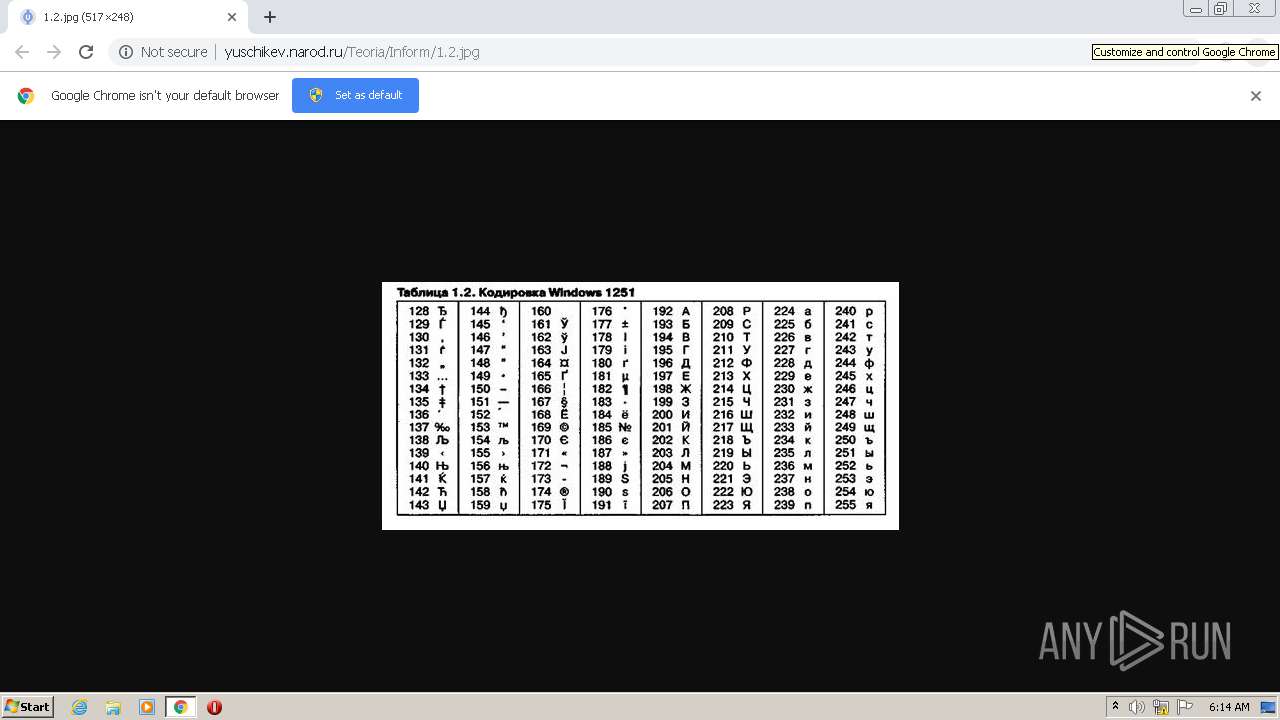
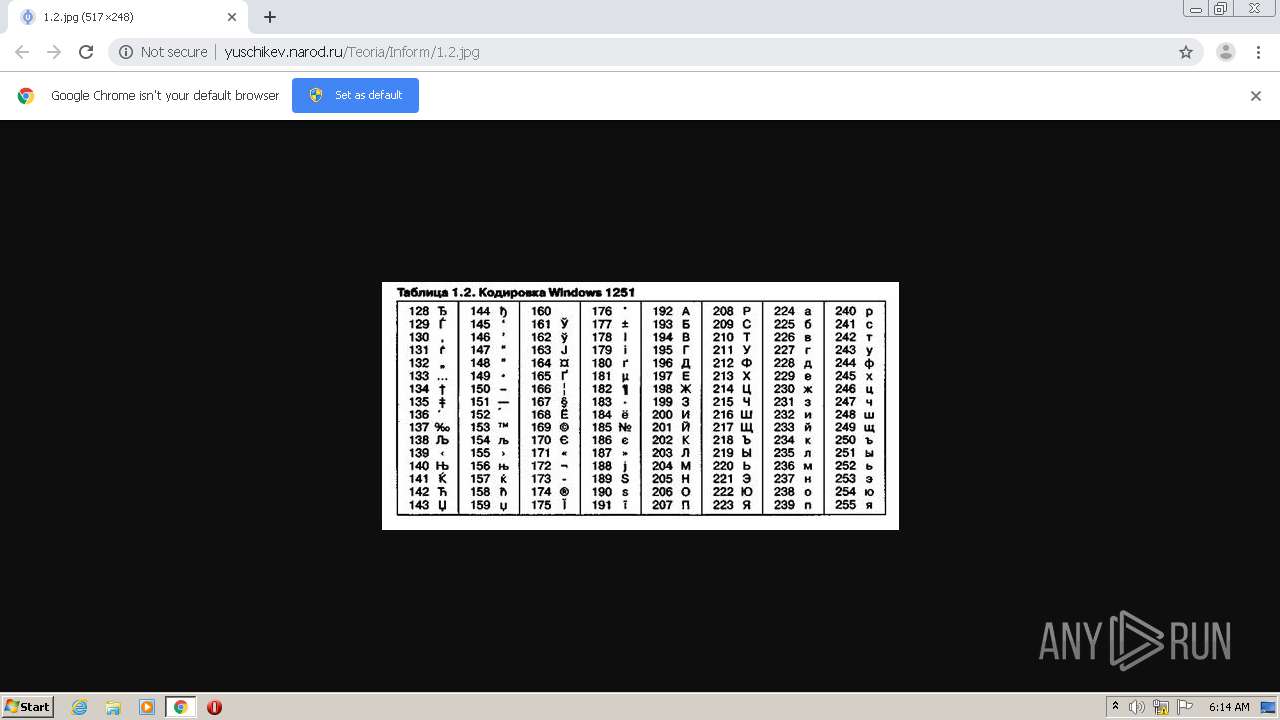
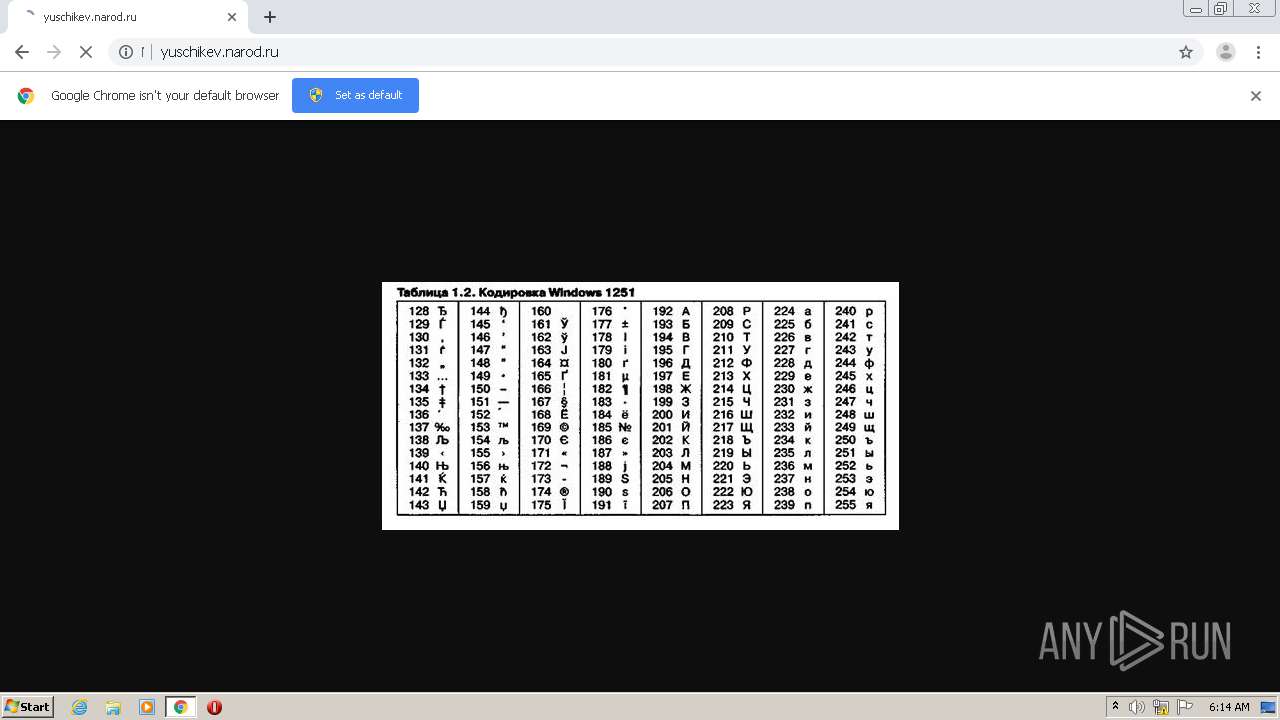
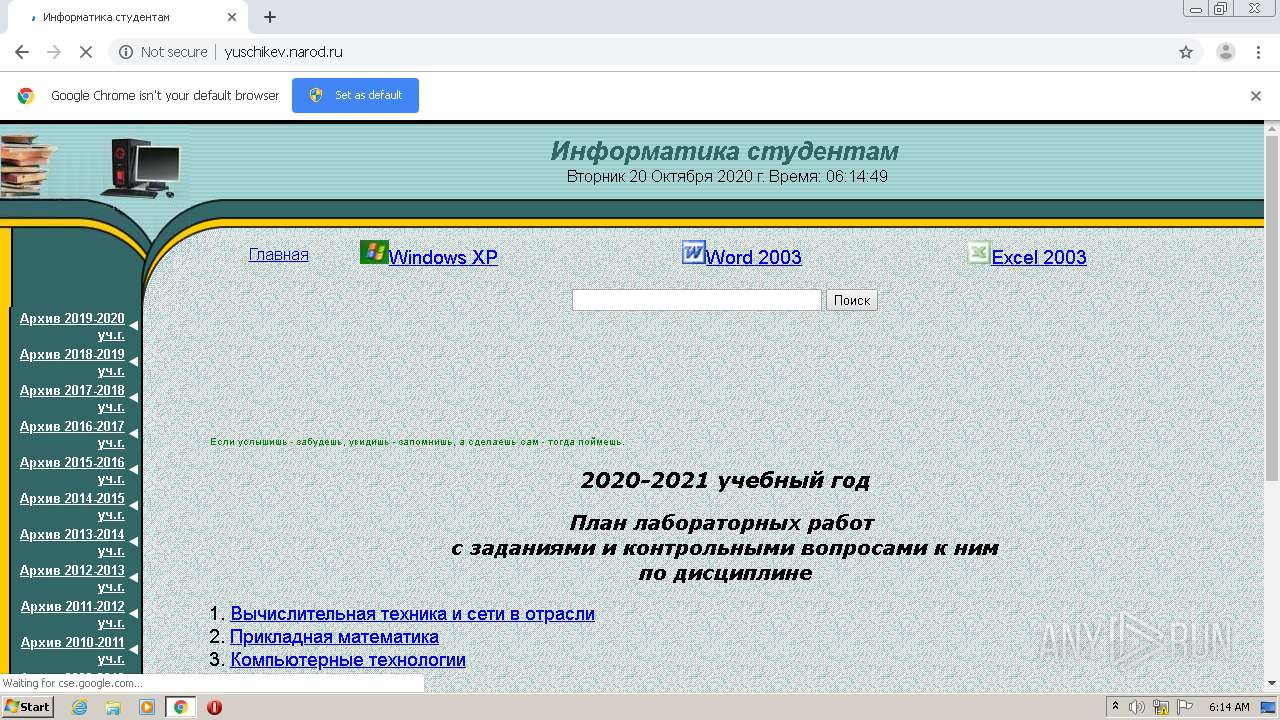
| URL: | http://yuschikev.narod.ru/Teoria/Inform/1.2.jpg |
| Full analysis: | https://app.any.run/tasks/02df1306-c6fd-4eb6-a7d5-a2defbed72d1 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 05:14:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AB9F7BBA492ECD1CB18D082CB05C10FB |
| SHA1: | 55BF96D5B167C69F7922ED796047E162BDFA95EB |
| SHA256: | FC382E9ED8CBB25FB1640B513CABDA8399C46E322A3CA381D51BA4C2A604620F |
| SSDEEP: | 3:N1KHm0WXkLbPVC:C2SrVC |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2724)
- chrome.exe (PID: 2528)
Application launched itself
- chrome.exe (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7771102432448668304 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12627905532902995957 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13395535296433753502 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14485629105362860036 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2814385648690011333 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13950546774663814712 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7215425548151016034 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9781713157737731636 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17779630727074401332 --mojo-platform-channel-handle=3824 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,13782686663574252339,14059243353447214084,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7404682131210274119 --mojo-platform-channel-handle=1624 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
219
Read events
141
Write events
74
Delete events
4
Modification events
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2724-13247644480236750 |
Value: 259 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2724-13247644480236750 |
Value: 259 | |||
Executable files
0
Suspicious files
30
Text files
78
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E7240-AA4.pma | — | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\524ad718-2bf4-4f3c-b16b-4b1e1ef37686.tmp | — | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d41d0.TMP | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d41e0.TMP | text | |
MD5:— | SHA256:— | |||
| 2724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
52
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2528 | chrome.exe | GET | 302 | 217.69.133.145:80 | http://db.c1.b8.a1.top.mail.ru/counter?id=1579886;t=170;l=1 | RU | — | — | suspicious |
2528 | chrome.exe | GET | 200 | 193.109.247.247:80 | http://yuschikev.narod.ru/Teoria/Inform/1.2.jpg | RU | image | 71.5 Kb | suspicious |
2528 | chrome.exe | GET | 200 | 216.58.210.2:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 44.6 Kb | whitelisted |
2528 | chrome.exe | GET | 200 | 193.109.247.247:80 | http://yuschikev.narod.ru/Image.files/data1.js | RU | text | 501 b | suspicious |
2528 | chrome.exe | GET | 200 | 193.109.247.247:80 | http://s203.ucoz.net/cgi/uutils.fcg?a=uSD&ca=2&ug=999&isp=1&r=0.723353937744065 | RU | text | 345 b | suspicious |
2528 | chrome.exe | GET | 200 | 216.58.210.2:80 | http://pagead2.googlesyndication.com/pagead/show_ads.js | US | text | 32.5 Kb | whitelisted |
2528 | chrome.exe | GET | 200 | 193.109.247.247:80 | http://yuschikev.narod.ru/Teoria.files/corner.gif | RU | image | 1.26 Kb | suspicious |
2528 | chrome.exe | GET | 200 | 193.109.247.247:80 | http://yuschikev.narod.ru/Image.files/bk1.GIF | RU | image | 25.8 Kb | suspicious |
2528 | chrome.exe | GET | 200 | 193.109.247.247:80 | http://yuschikev.narod.ru/Teoria.files/top.jpg | RU | image | 15.2 Kb | suspicious |
2528 | chrome.exe | GET | 200 | 193.109.247.247:80 | http://yuschikev.narod.ru/Image.files/arrow.gif | RU | image | 119 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2528 | chrome.exe | 172.217.23.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2528 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2528 | chrome.exe | 193.109.247.247:80 | yuschikev.narod.ru | Filanco, ltd. | RU | suspicious |
2528 | chrome.exe | 172.217.21.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2528 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
2528 | chrome.exe | 216.58.210.2:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2528 | chrome.exe | 185.15.208.118:80 | r1.wmlink.ru | Innovation IT Solutions LTD | RU | unknown |
2528 | chrome.exe | 216.58.210.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2528 | chrome.exe | 217.69.133.145:80 | db.c1.b8.a1.top.mail.ru | Limited liability company Mail.Ru | RU | suspicious |
2528 | chrome.exe | 88.212.201.198:80 | counter.yadro.ru | United Network LLC | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yuschikev.narod.ru |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
s203.ucoz.net |
| suspicious |
pagead2.googlesyndication.com |
| whitelisted |
r1.wmlink.ru |
| unknown |
counter.yadro.ru |
| whitelisted |
db.c1.b8.a1.top.mail.ru |
| suspicious |