| File name: | OfficeRTool.cmd |
| Full analysis: | https://app.any.run/tasks/a6018e04-44a2-4c25-9e1d-d1c9de32b245 |
| Verdict: | Malicious activity |
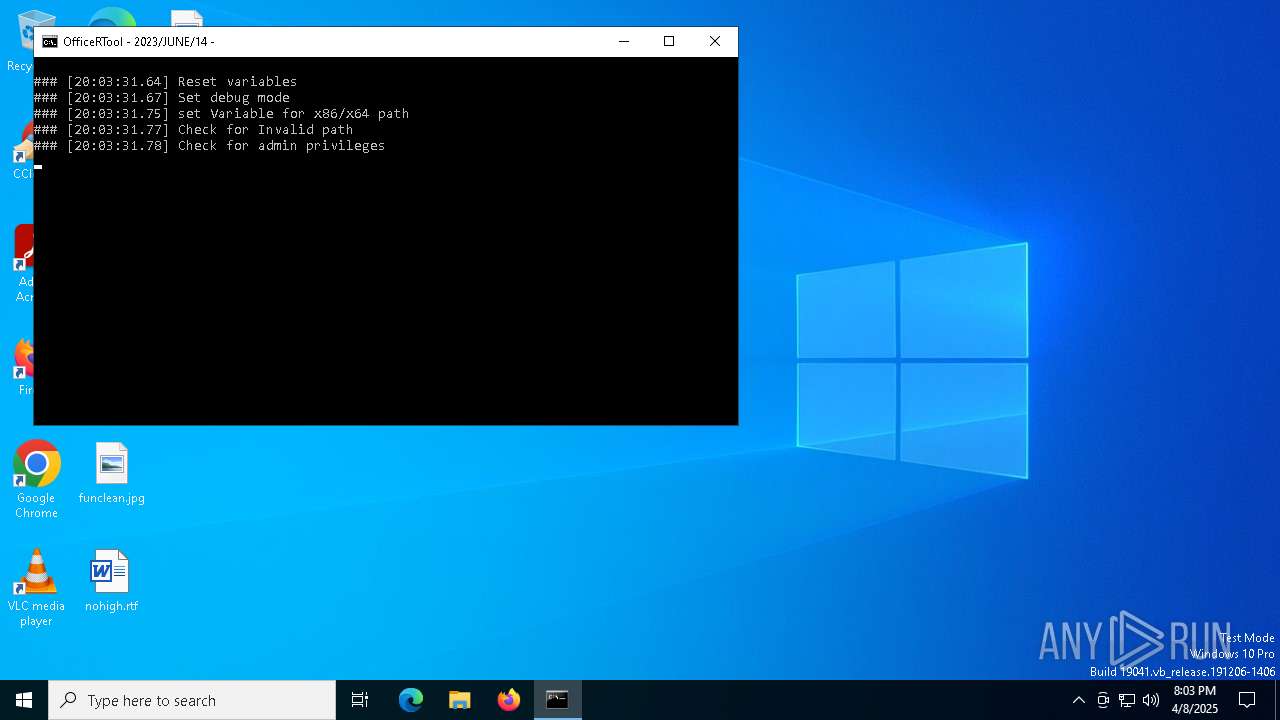
| Analysis date: | April 08, 2025, 20:03:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with very long lines (608), with CRLF line terminators, with escape sequences, with overstriking |
| MD5: | 6344F619737F291FAE73573AD05BE1CB |
| SHA1: | A8963F1A00247A7D93746CB95821427A846D6723 |
| SHA256: | FC2C173CF1A8BD82573B73DFF8C5E2155D4F6212957B13B66EBF6F372E6505E9 |
| SSDEEP: | 6144:TKLLDLjuODCLJP3ay/CPIgjMXhq6tofjRrIkmf9qmJ6NRaNLz3n:TqjuODCLJP3ay/CPIgjMX1LL |
MALICIOUS
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7756)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 720)
- cmd.exe (PID: 7756)
Application launched itself
- cmd.exe (PID: 720)
- cmd.exe (PID: 7756)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 720)
- powershell.exe (PID: 7288)
- cmd.exe (PID: 7756)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5736)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 720)
Hides command output
- cmd.exe (PID: 5736)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 7184)
Executes script without checking the security policy
- powershell.exe (PID: 7288)
- powershell.exe (PID: 7244)
Manipulates environment variables
- powershell.exe (PID: 7288)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 720)
- cmd.exe (PID: 7756)
Executing commands from ".cmd" file
- powershell.exe (PID: 7288)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7756)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7756)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7756)
- cmd.exe (PID: 720)
Executing commands from a ".bat" file
- powershell.exe (PID: 7288)
INFO
Checks supported languages
- chcp.com (PID: 4880)
- mode.com (PID: 6068)
- chcp.com (PID: 7840)
- mode.com (PID: 7864)
Changes the display of characters in the console
- cmd.exe (PID: 720)
- cmd.exe (PID: 7756)
Starts MODE.COM to configure console settings
- mode.com (PID: 6068)
- mode.com (PID: 7864)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7244)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7244)
Reads the software policy settings
- slui.exe (PID: 7396)
- slui.exe (PID: 7012)
Checks proxy server information
- slui.exe (PID: 7012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
165
Monitored processes
32
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\OfficeRTool.cmd.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | findstr "=" "C:\Users\admin\AppData\Local\Temp\Data\template.ini" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5736 | C:\WINDOWS\system32\cmd.exe /c "2>nul findstr "=" "C:\Users\admin\AppData\Local\Temp\Data\template.ini"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | reg query "HKLM\SOFTWARE\WOW6432Node\Microsoft\Office\ClickToRun\Configuration" /v "ProductReleaseIds" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6068 | mode con cols=88 lines=23 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7012 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7184 | C:\WINDOWS\system32\cmd.exe /c "2>nul findstr "=" "C:\Users\admin\AppData\Local\Temp\Data\defaults.ini"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7200 | findstr "=" "C:\Users\admin\AppData\Local\Temp\Data\defaults.ini" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 725
Read events
10 725
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7288 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_w5lq5swj.qvl.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7288 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:1C504E148174F503FDC274D825C8B4E5 | SHA256:3B8AE8477AED77AA4DCA1EE291720E514A034F64BE03E1A4BD3F35B1811C8E03 | |||
| 7244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_afsmrn50.bez.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7288 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kpt1nxsr.rsf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lv110fl5.2kh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6708 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6708 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
976 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6708 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |