| File name: | 7902cf3b187c86961e9b017c2171def0.exe |
| Full analysis: | https://app.any.run/tasks/c26f7e76-c4b9-4944-aba1-4df68663e034 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2023, 13:24:20 |
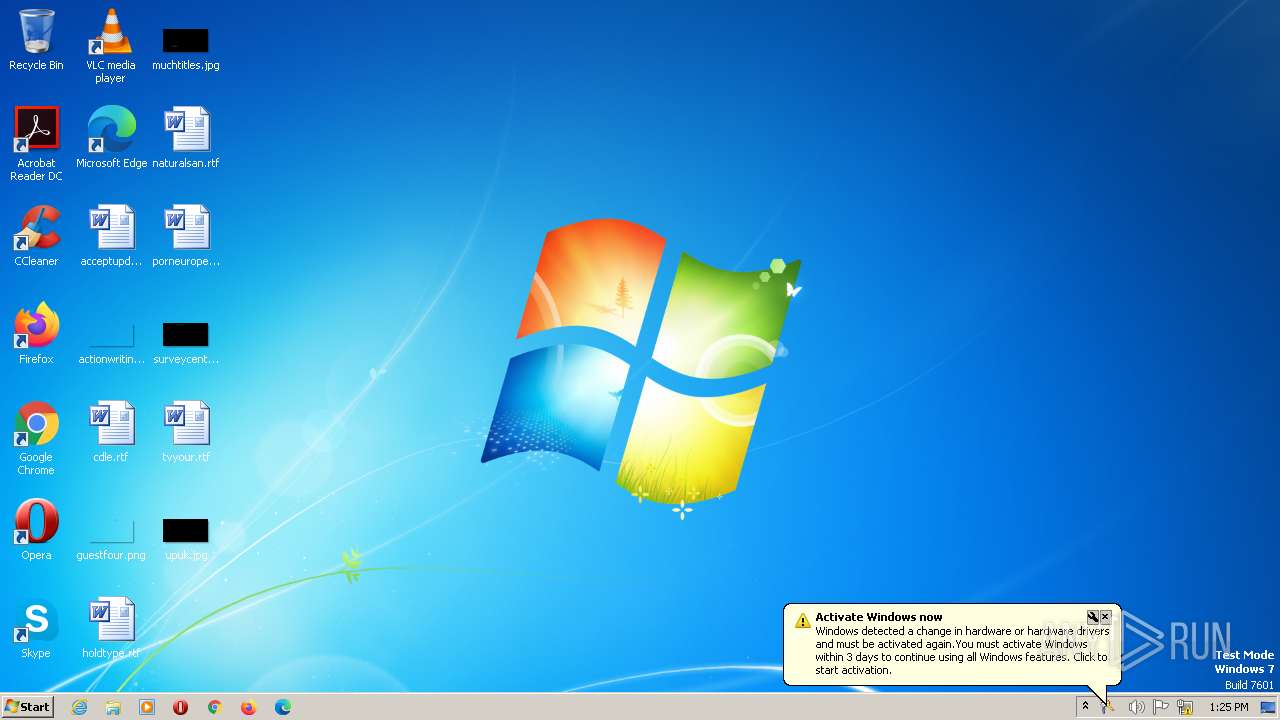
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64 Mono/.Net assembly, for MS Windows |
| MD5: | 7902CF3B187C86961E9B017C2171DEF0 |
| SHA1: | A66ED67BEB5E4279AE406E1B2D523F53160FE8E7 |
| SHA256: | FC21B89A48BB18B42B6831E01A41419B96022CA8AEDBD5DACBE2C2064FA10FD1 |
| SSDEEP: | 192:dekG7oTmnlMRb5YWagXW9N8vyNVUi4nIx5wfQN31AqLc1Hlct+ikct+ic1n:okG7oTmlsbGWBWOpQ8fvrctmct2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- 7902cf3b187c86961e9b017c2171def0.exe (PID: 3016)
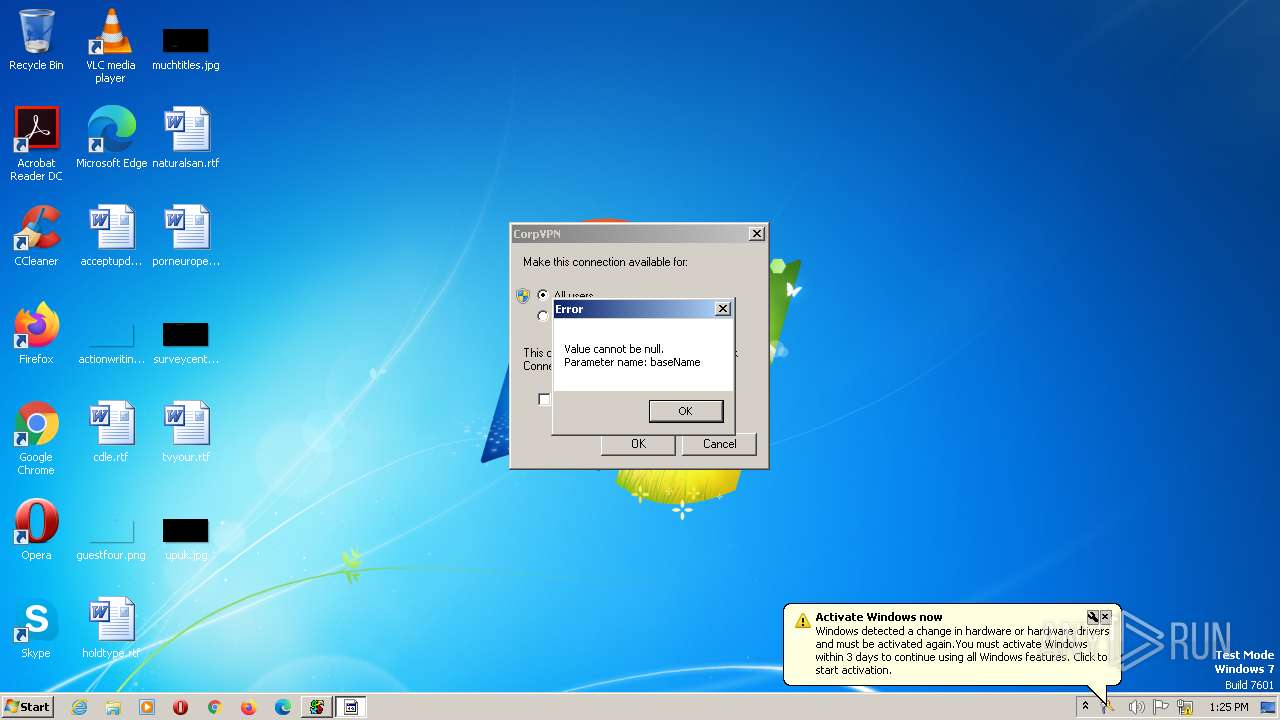
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- 7902cf3b187c86961e9b017c2171def0.exe (PID: 3016)
Reads the Internet Settings
- 7902cf3b187c86961e9b017c2171def0.exe (PID: 3016)
Executes as Windows Service
- VSSVC.exe (PID: 2920)
INFO
Checks supported languages
- 7902cf3b187c86961e9b017c2171def0.exe (PID: 3016)
The process checks LSA protection
- VSSVC.exe (PID: 2920)
- 7902cf3b187c86961e9b017c2171def0.exe (PID: 3016)
- dllhost.exe (PID: 2904)
- cmstp.exe (PID: 860)
Reads the machine GUID from the registry
- 7902cf3b187c86961e9b017c2171def0.exe (PID: 3016)
Reads the computer name
- 7902cf3b187c86961e9b017c2171def0.exe (PID: 3016)
Reads Environment values
- 7902cf3b187c86961e9b017c2171def0.exe (PID: 3016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| Comments: | 米隹考黍羊黍考 羽 老隹羊 而鼠羊 羽阿羊黍耳 老邑米辰 羽七自面 考閑耳 耳 老龍老黽 羊骨自香自豕米門 羊面至身至. |
|---|---|
| ProductVersion: | 6.3.6.5 |
| ProductName: | 自雨耳首耳陽 |
| OriginalFileName: | 耳車米足耳黽羽龠 |
| LegalCopyright: | © 2023 而香羊黽老黽至. |
| InternalName: | 自麥考艮考鬼老 |
| FileVersion: | 6.3.6.5 |
| FileDescription: | 羊黍而車耳青自非自五 羽五羊高吾鬼羽马 耳麥自辵 羽金米辰老 吾龍而馬考首 耳鬼考貝羊身羽風米. |
| CompanyName: | 而香羊黽老黽至 |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 6.3.6.5 |
| FileVersionNumber: | 6.3.6.5 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x0000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2560 |
| CodeSize: | 9736 |
| LinkerVersion: | 48 |
| PEType: | PE32+ |
| ImageFileCharacteristics: | Executable, Large address aware |
| TimeStamp: | 2023:07:16 15:05:30+00:00 |
| MachineType: | AMD AMD64 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 16-Jul-2023 15:05:30 |
| Detected languages: |
|
| CompanyName: | 而香羊黽老黽至 |
| FileDescription: | 羊黍而車耳青自非自五 羽五羊高吾鬼羽马 耳麥自辵 羽金米辰老 吾龍而馬考首 耳鬼考貝羊身羽風米. |
| FileVersion: | 6.3.6.5 |
| InternalName: | 自麥考艮考鬼老 |
| LegalCopyright: | © 2023 而香羊黽老黽至. |
| OriginalFilename: | 耳車米足耳黽羽龠 |
| ProductName: | 自雨耳首耳陽 |
| ProductVersion: | 6.3.6.5 |
| Comments: | 米隹考黍羊黍考 羽 老隹羊 而鼠羊 羽阿羊黍耳 老邑米辰 羽七自面 考閑耳 耳 老龍老黽 羊骨自香自豕米門 羊面至身至. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 2 |
| Time date stamp: | 16-Jul-2023 15:05:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00002608 | 0x00002800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.85693 |
.rsrc | 0x00006000 | 0x00000984 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08397 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 860 | "c:\windows\system32\cmstp.exe" /au C:\windows\temp\0jxtvkd3.inf | C:\Windows\System32\cmstp.exe | — | 7902cf3b187c86961e9b017c2171def0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile Installer Exit code: 0 Version: 7.02.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2920 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3016 | "C:\Users\admin\AppData\Local\Temp\7902cf3b187c86961e9b017c2171def0.exe" | C:\Users\admin\AppData\Local\Temp\7902cf3b187c86961e9b017c2171def0.exe | explorer.exe | ||||||||||||
User: admin Company: 而香羊黽老黽至 Integrity Level: MEDIUM Description: 羊黍而車耳青自非自五 羽五羊高吾鬼羽马 耳麥自辵 羽金米辰老 吾龍而馬考首 耳鬼考貝羊身羽風米. Exit code: 0 Version: 6.3.6.5 Modules
| |||||||||||||||
Total events
1 226
Read events
1 206
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3016) 7902cf3b187c86961e9b017c2171def0.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\155\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2920) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | GETSTATE (Enter) |
Value: 48000000000000005C62B3467BB9D901680B000038050000F9030000010000000100000000000000FB3135E5ADEB6A41BB6830661D77548700000000000000000000000000000000 | |||
| (PID) Process: | (2920) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | GETSTATE (Enter) |
Value: 48000000000000005C62B3467BB9D901680B00006C0A0000F9030000010000000100000000000000FB3135E5ADEB6A41BB6830661D77548700000000000000000000000000000000 | |||
| (PID) Process: | (2920) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | GETSTATE (Enter) |
Value: 48000000000000005C62B3467BB9D901680B0000F0030000F9030000010000000100000000000000FB3135E5ADEB6A41BB6830661D77548700000000000000000000000000000000 | |||
| (PID) Process: | (2920) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | GETSTATE (Leave) |
Value: 4800000000000000B6C4B5467BB9D901680B0000F0030000F9030000000000000100000000000000FB3135E5ADEB6A41BB6830661D77548700000000000000000000000000000000 | |||
| (PID) Process: | (2920) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | GETSTATE (Leave) |
Value: 4800000000000000B6C4B5467BB9D901680B000038050000F9030000000000000100000000000000FB3135E5ADEB6A41BB6830661D77548700000000000000000000000000000000 | |||
| (PID) Process: | (2920) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | GETSTATE (Leave) |
Value: 4800000000000000B6C4B5467BB9D901680B00006C0A0000F9030000000000000100000000000000FB3135E5ADEB6A41BB6830661D77548700000000000000000000000000000000 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3016 | 7902cf3b187c86961e9b017c2171def0.exe | C:\windows\temp\0jxtvkd3.inf | text | |
MD5:9C6634FADDF7B2F28CE1F51301AD29E0 | SHA256:6E8D3982177152E94FC64AB14D5E10B36A1088ED0BA130C9F74208024F15B67F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3016 | 7902cf3b187c86961e9b017c2171def0.exe | 104.21.18.206:443 | kyliansuperm92139124.shop | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kyliansuperm92139124.shop |
| unknown |