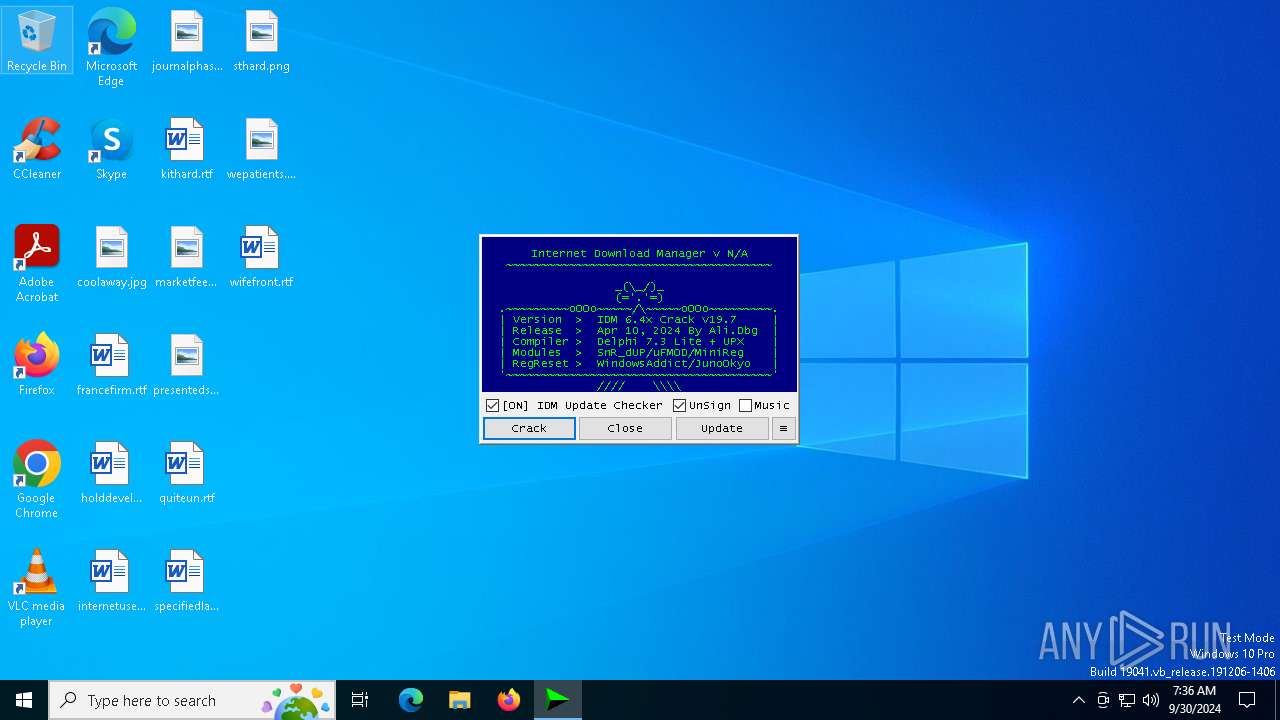
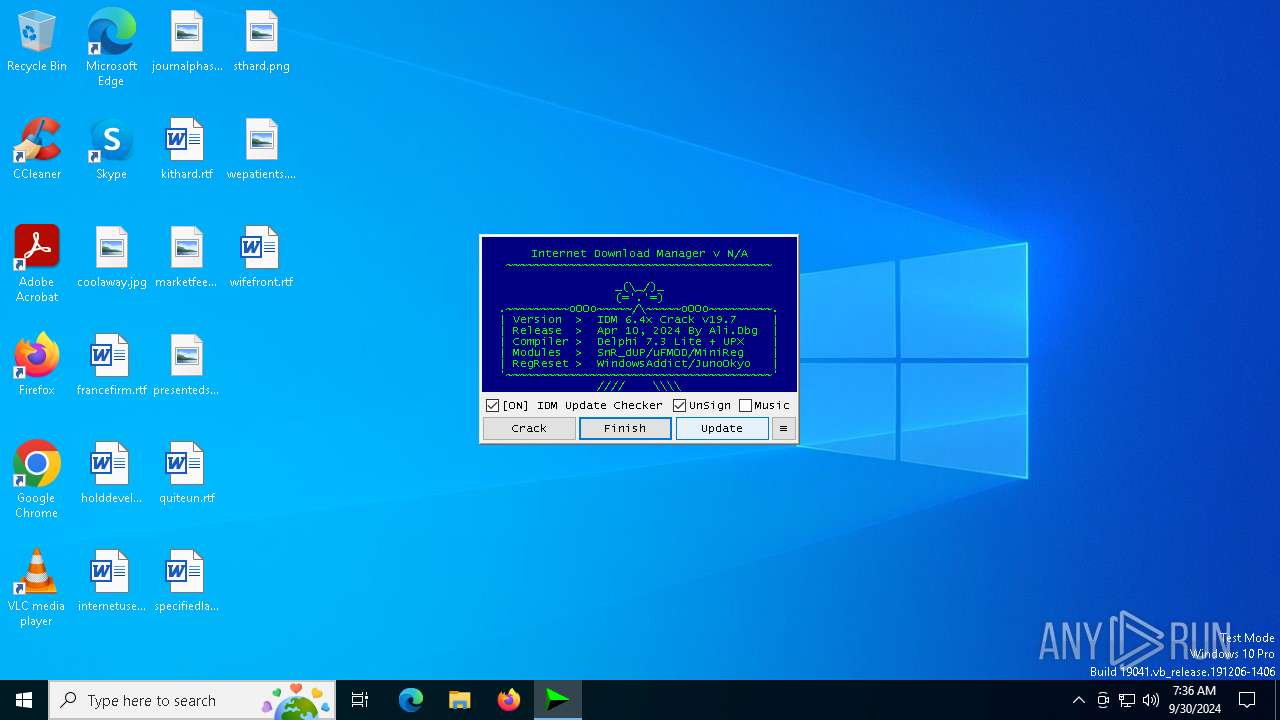
| File name: | IDM_6.4x_Crack_v19.7.exe |
| Full analysis: | https://app.any.run/tasks/ffe369d7-d0c1-4786-a879-beb7b786cedc |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2024, 07:36:40 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 27016937B5781C4F84B6B3432170F4D0 |
| SHA1: | BC812A8C4D44A3503FFD6A46E4FDAB925C622344 |
| SHA256: | FC1A02B509B8F351AC45BD45EFD4E7296B365545A48FFD6A14E8E07BC7189155 |
| SSDEEP: | 1536:kaaR+ChjLjFnDrpfBzftBr20ezIL6bFwNA5fufSiaAx:khRdHjNDrpfdfjr20xUH9uKdAx |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v19.7.exe (PID: 1488)
- cmd.exe (PID: 3076)
- cmd.exe (PID: 2424)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v19.7.exe (PID: 1488)
- cmd.exe (PID: 2424)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v19.7.exe (PID: 1488)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 2660)
Application launched itself
- cmd.exe (PID: 3076)
- cmd.exe (PID: 2424)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2424)
Hides command output
- cmd.exe (PID: 2660)
- cmd.exe (PID: 7124)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 188)
- cmd.exe (PID: 2424)
- cmd.exe (PID: 7124)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2424)
INFO
Reads the computer name
- IDM_6.4x_Crack_v19.7.exe (PID: 1488)
Checks supported languages
- IDM_6.4x_Crack_v19.7.exe (PID: 1488)
Create files in a temporary directory
- IDM_6.4x_Crack_v19.7.exe (PID: 1488)
- reg.exe (PID: 420)
Checks operating system version
- cmd.exe (PID: 2424)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 57344 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 184320 |
| EntryPoint: | 0x3b700 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
182
Monitored processes
50
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | reg query "HKCU\Software\DownloadManager" "/v" "radxcnt" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | C:\WINDOWS\system32\cmd.exe /c powershell.exe "(Get-Date).ToString('yyyyMMdd-HHmmssfff')" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 376 | "C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v19.7.exe" | C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v19.7.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 420 | reg export HKCU\Software\Classes\Wow6432Node\CLSID "C:\WINDOWS\Temp\_Backup_HKCU_CLSID_20240930-073713474.reg" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | reg delete HKCU\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | powershell.exe "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\BATCLEN.bat') -split ':PowerShellTest:\s*';iex ($f[1])" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1308 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1336 | reg delete HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\Classes\Wow6432Node\CLSID\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1488 | "C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v19.7.exe" | C:\Users\admin\AppData\Local\Temp\IDM_6.4x_Crack_v19.7.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1768 | reg query "HKCU\Software\DownloadManager" "/v" "LastCheckQU" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 407
Read events
21 373
Write events
19
Delete events
15
Modification events
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
| (PID) Process: | (1488) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\PowerShell\1\ShellIds\ScriptedDiagnostics |
| Operation: | write | Name: | ExecutionPolicy |
Value: Bypass | |||
Executable files
0
Suspicious files
3
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ja2ccjqc.51g.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 420 | reg.exe | C:\Windows\Temp\_Backup_HKCU_CLSID_20240930-073713474.reg | text | |
MD5:345823A0BDDB596A43415D67C9880B8A | SHA256:D9CB0467BD3FC677837C380F3A7D5C69291E001B210907FD302B3CE61FF98682 | |||
| 6672 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tphjsn2z.nm1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 420 | reg.exe | C:\Users\admin\AppData\Local\Temp\REGD28F.tmp | text | |
MD5:345823A0BDDB596A43415D67C9880B8A | SHA256:D9CB0467BD3FC677837C380F3A7D5C69291E001B210907FD302B3CE61FF98682 | |||
| 6020 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_atn0rfzo.dqh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5044 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:AE6D5D9FF77D0828C515BDAFA52A0B99 | SHA256:— | |||
| 1488 | IDM_6.4x_Crack_v19.7.exe | C:\Users\admin\AppData\Local\Temp\IDMRegClean.reg | text | |
MD5:73C023B1480CC88BE4D7761EF11A7703 | SHA256:9C7F6CE7CE6FA4093A20CFA3C1A6D2CDD7D5307AFF7405830C898A21F154ED68 | |||
| 1488 | IDM_6.4x_Crack_v19.7.exe | C:\Users\admin\AppData\Local\Temp\BATCLEN.bat | text | |
MD5:9FE22C4AD624881F8F0977CC7614346F | SHA256:12B47C1949CC555C2F68F9FD4677ED5266F25C4DA4630BEC36E303629B133225 | |||
| 6044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lk1z4iuq.umo.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_w41ayzzy.v2r.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
39
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2208 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2132 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2208 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2208 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5676 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
4324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2456 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |