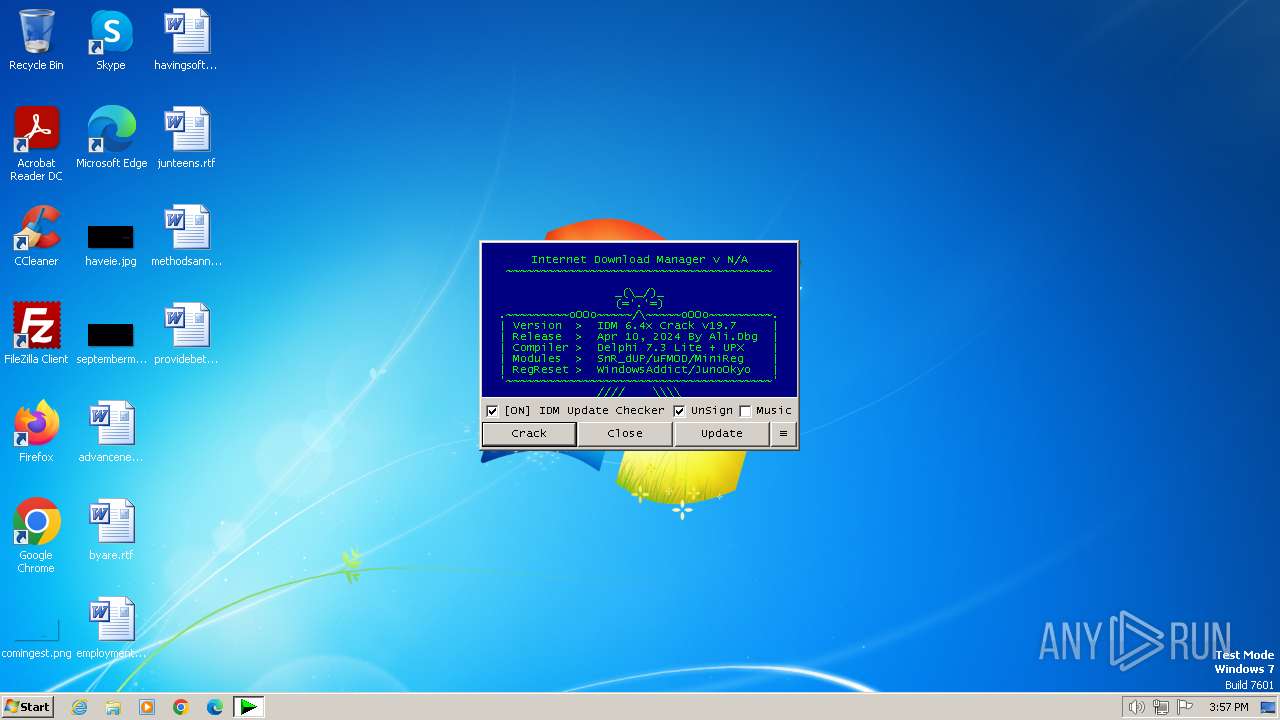
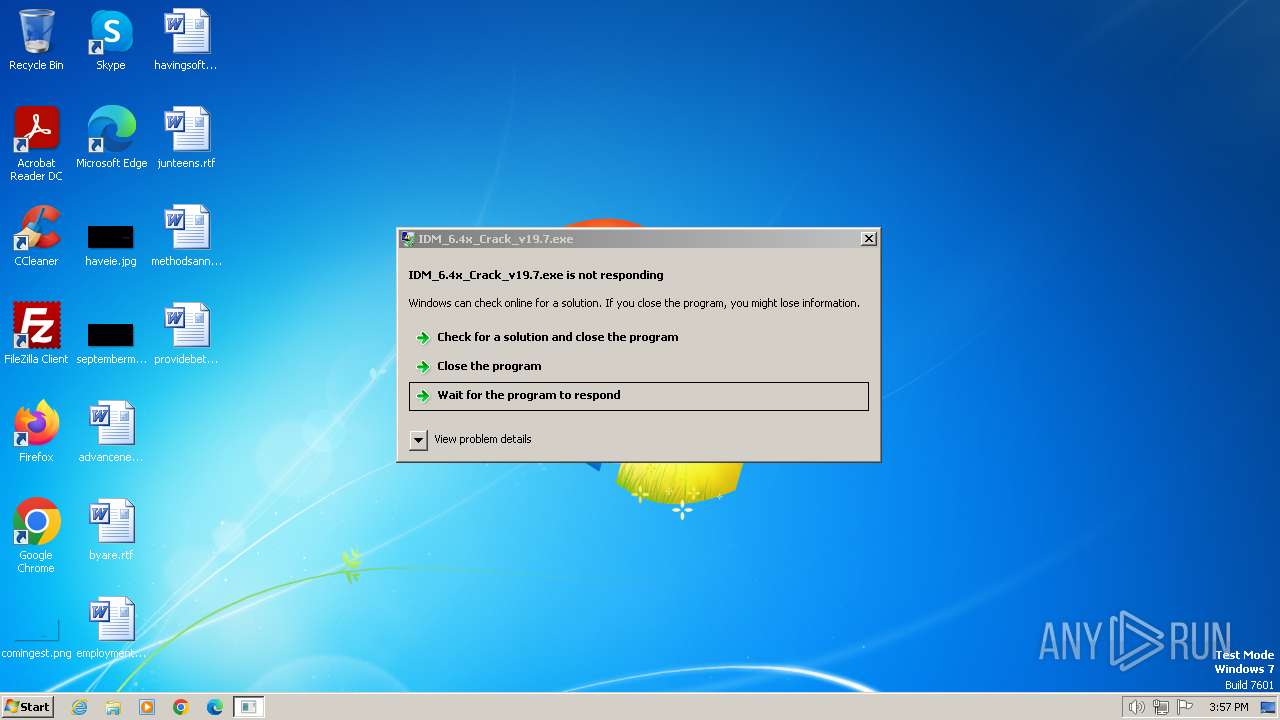
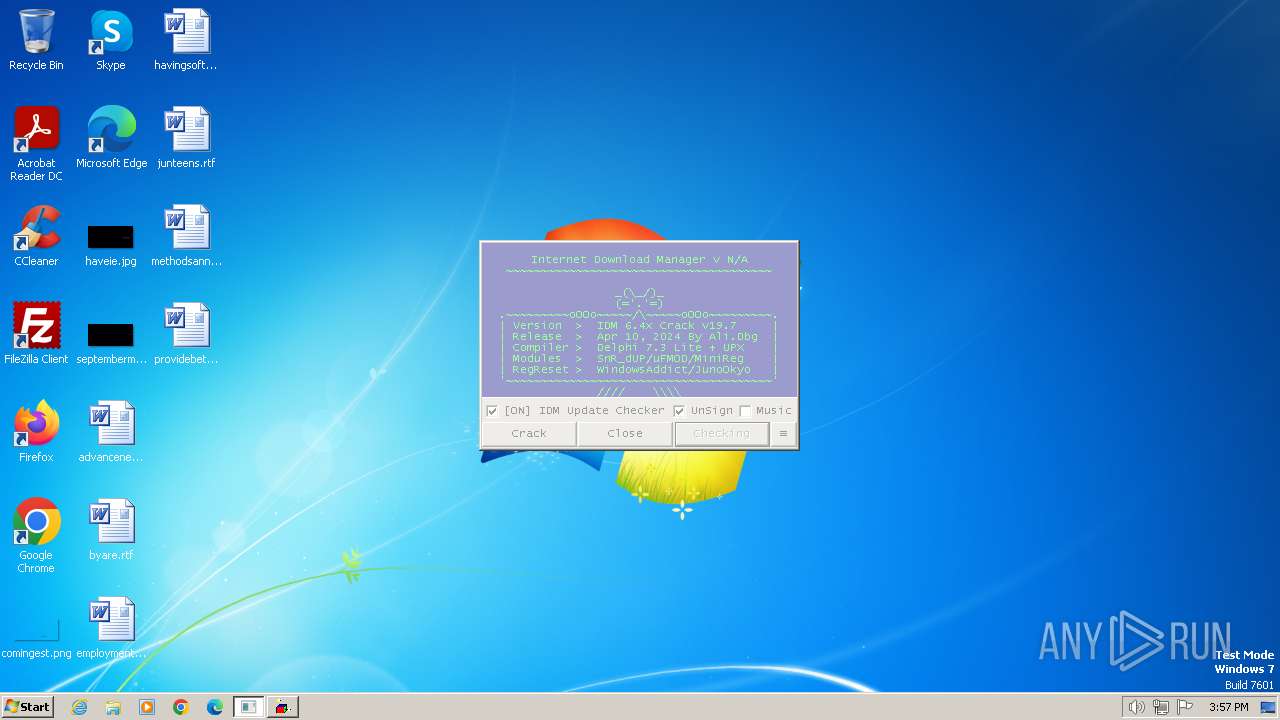
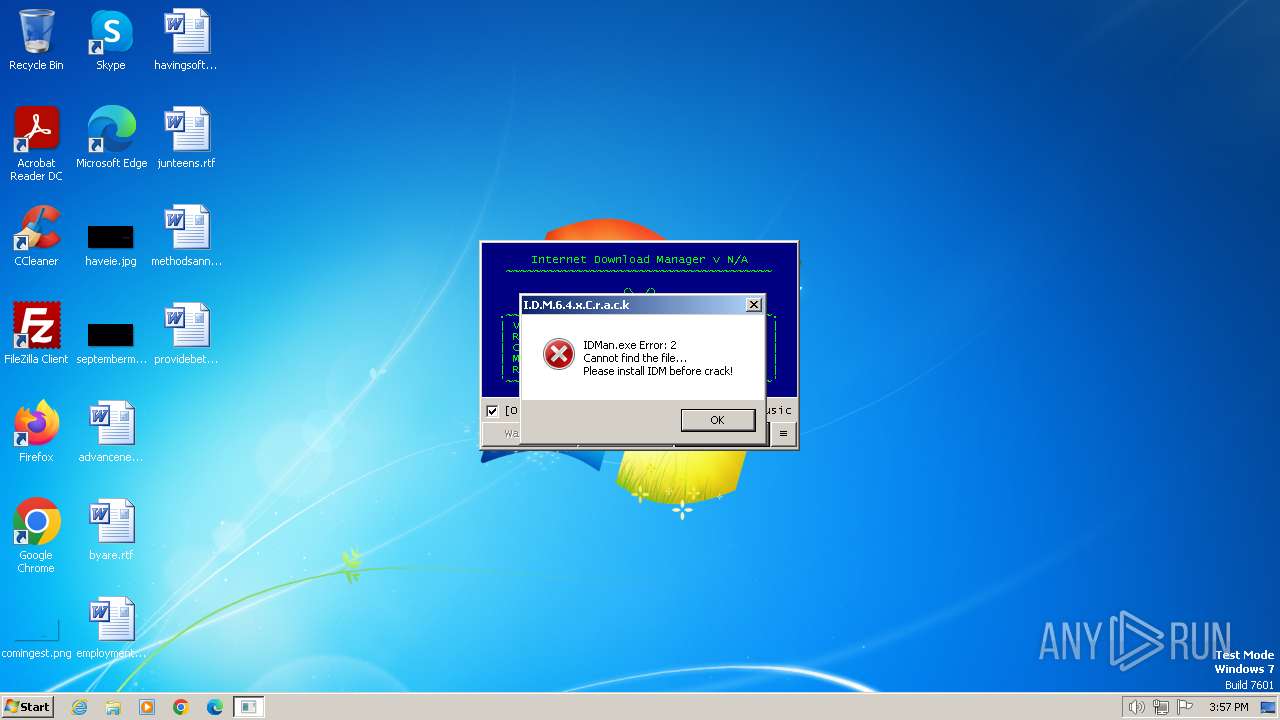
| File name: | IDM_6.4x_Crack_v19.7.exe |
| Full analysis: | https://app.any.run/tasks/f40c1da9-7b14-445f-b298-b85c53fda4c6 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2024, 14:57:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 27016937B5781C4F84B6B3432170F4D0 |
| SHA1: | BC812A8C4D44A3503FFD6A46E4FDAB925C622344 |
| SHA256: | FC1A02B509B8F351AC45BD45EFD4E7296B365545A48FFD6A14E8E07BC7189155 |
| SSDEEP: | 1536:kaaR+ChjLjFnDrpfBzftBr20ezIL6bFwNA5fufSiaAx:khRdHjNDrpfdfjr20xUH9uKdAx |
MALICIOUS
Drops the executable file immediately after the start
- IDM_6.4x_Crack_v19.7.exe (PID: 2380)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2416)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 2416)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2416)
Unusual connection from system programs
- wscript.exe (PID: 2416)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2416)
Deletes a file (SCRIPT)
- wscript.exe (PID: 2416)
SUSPICIOUS
The process executes VB scripts
- IDM_6.4x_Crack_v19.7.exe (PID: 2380)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2416)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2416)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v19.7.exe (PID: 2380)
- cmd.exe (PID: 532)
- cmd.exe (PID: 1168)
- cmd.exe (PID: 1816)
- cmd.exe (PID: 3024)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v19.7.exe (PID: 2380)
- cmd.exe (PID: 532)
- cmd.exe (PID: 1816)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v19.7.exe (PID: 2380)
- cmd.exe (PID: 532)
- cmd.exe (PID: 1816)
Application launched itself
- cmd.exe (PID: 532)
- cmd.exe (PID: 1816)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 532)
- cmd.exe (PID: 1816)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 532)
- cmd.exe (PID: 1816)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 532)
- cmd.exe (PID: 4000)
- cmd.exe (PID: 1792)
- cmd.exe (PID: 1816)
- cmd.exe (PID: 2748)
- cmd.exe (PID: 4032)
Hides command output
- cmd.exe (PID: 4000)
- cmd.exe (PID: 1168)
- cmd.exe (PID: 3024)
- cmd.exe (PID: 2748)
Starts application with an unusual extension
- cmd.exe (PID: 532)
INFO
Checks supported languages
- IDM_6.4x_Crack_v19.7.exe (PID: 2380)
- chcp.com (PID: 3112)
Create files in a temporary directory
- IDM_6.4x_Crack_v19.7.exe (PID: 2380)
- reg.exe (PID: 2572)
Reads the computer name
- IDM_6.4x_Crack_v19.7.exe (PID: 2380)
Checks operating system version
- cmd.exe (PID: 532)
- cmd.exe (PID: 1816)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3864)
- powershell.exe (PID: 3284)
- powershell.exe (PID: 1496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 57344 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 184320 |
| EntryPoint: | 0x3b700 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
124
Monitored processes
81
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | reg query HKCU\Console /v QuickEdit | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | cmd.exe /c call "C:\Users\admin\AppData\Local\Temp\BATCLEN.bat" | C:\Windows\System32\cmd.exe | — | IDM_6.4x_Crack_v19.7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 848 | reg query "HKCU\Software\DownloadManager" "/v" "ptrk_scdt" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | reg query "HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Environment" /v PROCESSOR_ARCHITECTURE | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1168 | C:\Windows\system32\cmd.exe /c reg query "HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software\DownloadManager" /v ExePath 2>nul | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1196 | reg query "HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software\DownloadManager" /v ExePath | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1288 | reg add HKU\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Classes\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1316 | powershell.exe "(Get-Date).ToString('yyyyMMdd-HHmmssfff')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1336 | powershell.exe "([System.Security.Principal.NTAccount](Get-WmiObject -Class Win32_ComputerSystem).UserName).Translate([System.Security.Principal.SecurityIdentifier]).Value" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1348 | reg query "HKLM\Software\Internet Download Manager" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
28 956
Read events
28 875
Write events
48
Delete events
33
Modification events
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\Software\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (2380) IDM_6.4x_Crack_v19.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
Executable files
0
Suspicious files
19
Text files
5
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2016 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jbfmttuz.xpb.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3864 | powershell.exe | C:\Users\admin\AppData\Local\Temp\iwt1lpnb.afa.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3864 | powershell.exe | C:\Users\admin\AppData\Local\Temp\u5k2ohdw.phg.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3864 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 2572 | reg.exe | C:\Users\admin\AppData\Local\Temp\REG6902.tmp | text | |
MD5:F58D4E5F0B6A7E69AA96964ABCDEF744 | SHA256:253D606D5060BB62CFA2411477004C8ED2ECA7925A2B0770691D485678AABF73 | |||
| 1496 | powershell.exe | C:\Users\admin\AppData\Local\Temp\f3brhj2w.qlp.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2572 | reg.exe | C:\Windows\Temp\_Backup_HKCU_CLSID_20240425-155753282.reg | text | |
MD5:F58D4E5F0B6A7E69AA96964ABCDEF744 | SHA256:253D606D5060BB62CFA2411477004C8ED2ECA7925A2B0770691D485678AABF73 | |||
| 2380 | IDM_6.4x_Crack_v19.7.exe | C:\Users\admin\AppData\Local\Temp\UPDT.vbs | text | |
MD5:7B18A872D4BE22EECF2F95CE5E63CE15 | SHA256:E64D9B855B8F02B15626C7E932C0451C07AF8E8EBB53BB17626C66E117F50CBA | |||
| 2380 | IDM_6.4x_Crack_v19.7.exe | C:\Users\admin\AppData\Local\Temp\IDMRegClean.reg | text | |
MD5:73C023B1480CC88BE4D7761EF11A7703 | SHA256:9C7F6CE7CE6FA4093A20CFA3C1A6D2CDD7D5307AFF7405830C898A21F154ED68 | |||
| 3284 | powershell.exe | C:\Users\admin\AppData\Local\Temp\h5j3noqj.dwq.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2416 | wscript.exe | 188.114.97.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idm.0dy.ir |
| unknown |