| File name: | 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer |
| Full analysis: | https://app.any.run/tasks/ab86e175-3a5b-4610-a6de-f2b2fbdcafce |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 23:13:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | EE9252DA4BF46C5980A48C39922B0E9C |
| SHA1: | 9DE86C24BC3F4FAB92F19A279DF7E60914C58975 |
| SHA256: | FC1907033697C1849B52105AE19CD05B2D45FC510EE38C5F0638ED3C418386A8 |
| SSDEEP: | 12288:lcZPh4EcnEE3ej4NDgZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZE:oMEE3ej4NDx |
MALICIOUS
Changes the autorun value in the registry
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
TOFSEE has been detected (YARA)
- svchost.exe (PID: 5164)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
Reads security settings of Internet Explorer
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
Executes application which crashes
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
- npitaiwm.exe (PID: 8000)
- npitaiwm.exe (PID: 2140)
Connects to SMTP port
- svchost.exe (PID: 8072)
- svchost.exe (PID: 5164)
Detected use of alternative data streams (AltDS)
- svchost.exe (PID: 8072)
- svchost.exe (PID: 5164)
INFO
Create files in a temporary directory
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
Reads the computer name
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
- npitaiwm.exe (PID: 8000)
- npitaiwm.exe (PID: 2140)
Process checks computer location settings
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
Checks supported languages
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
- npitaiwm.exe (PID: 8000)
- npitaiwm.exe (PID: 2140)
Auto-launch of the file from Registry key
- 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe (PID: 7772)
Manual execution by a user
- npitaiwm.exe (PID: 2140)
Checks proxy server information
- slui.exe (PID: 4120)
Reads the software policy settings
- slui.exe (PID: 4120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:10 13:01:49+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 68096 |
| InitializedDataSize: | 248832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x130b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
143
Monitored processes
11
Malicious processes
4
Suspicious processes
1
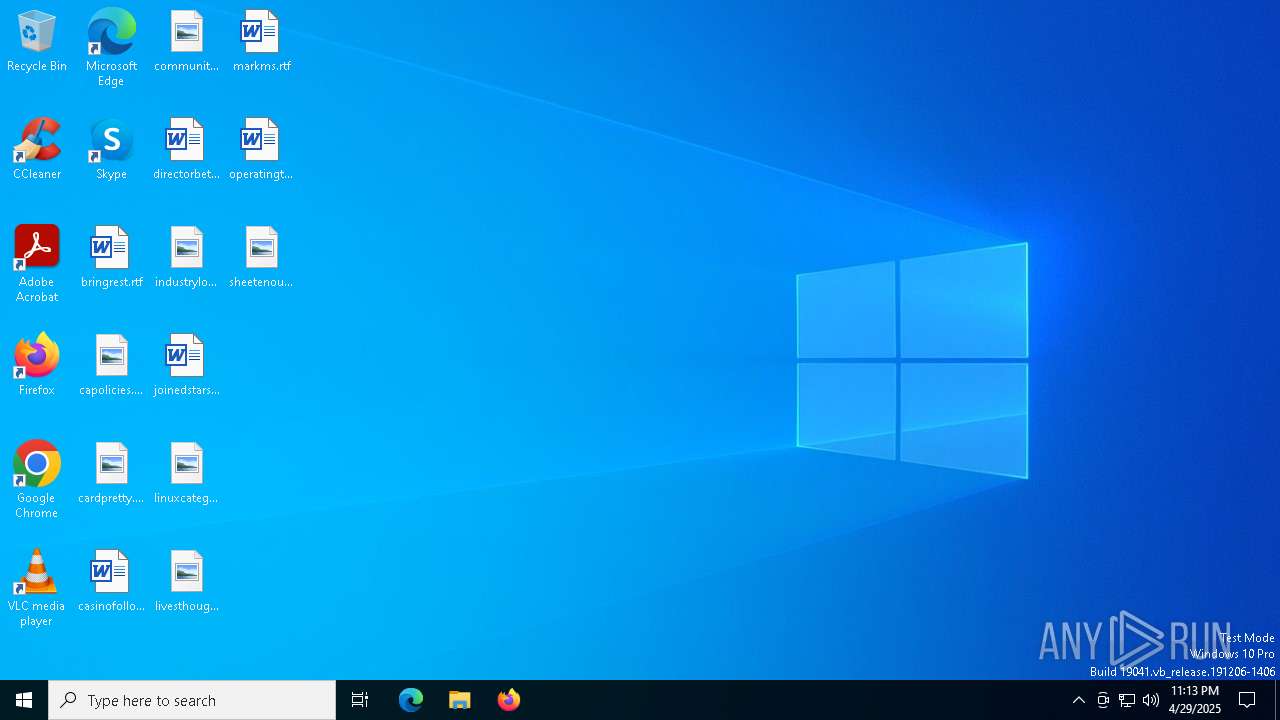
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | "C:\Users\admin\npitaiwm.exe" | C:\Users\admin\npitaiwm.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 4120 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5164 | svchost.exe | C:\Windows\SysWOW64\svchost.exe | npitaiwm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7584 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 2140 -s 524 | C:\Windows\SysWOW64\WerFault.exe | — | npitaiwm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7772 | "C:\Users\admin\Desktop\2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe" | C:\Users\admin\Desktop\2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 7876 | "C:\Windows\System32\wusa.exe" | C:\Windows\SysWOW64\wusa.exe | — | 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7972 | "C:\WINDOWS\SysWOW64\wusa.exe" | C:\Windows\SysWOW64\wusa.exe | 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8000 | "C:\Users\admin\npitaiwm.exe" /d"C:\Users\admin\Desktop\2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe" /e550302100000007F | C:\Users\admin\npitaiwm.exe | 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 8072 | svchost.exe | C:\Windows\SysWOW64\svchost.exe | npitaiwm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8144 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7772 -s 1032 | C:\Windows\SysWOW64\WerFault.exe | — | 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 319
Read events
5 316
Write events
2
Delete events
1
Modification events
| (PID) Process: | (7772) 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | xyhgwiar |
Value: "C:\Users\admin\npitaiwm.exe" | |||
| (PID) Process: | (8072) svchost.exe | Key: | HKEY_CURRENT_USER\Control Panel\Buses |
| Operation: | write | Name: | Config0 |
Value: 008D603D98F01F3D24EDB47D450DD49D084297DCE82E72BAA4943BFDE422031D8FF0089C48CD945D24EDB47D470DD49D024195DAF71261ADC06D04FDA6E22673BBC9154961CDA56B15D4834E7C3DE5AF644490BDB57B26EB925D05CFF0BA54758DF21D5904E0AD6B1CD88D4E7234E59D084295D9E13F4BB4C06D07FD | |||
| (PID) Process: | (8072) svchost.exe | Key: | HKEY_CURRENT_USER\Control Panel\Buses |
| Operation: | delete value | Name: | Config1 |
Value: | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7772 | 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe | C:\Users\admin\AppData\Local\Temp\plddapoc.exe | executable | |
MD5:1FFAD3CB25F632F574C746FC1DCB870E | SHA256:1A758B481142C1E477934FFFF00CC1A18E21FE03D58D073F6EEA9F15AF06E311 | |||
| 8072 | svchost.exe | C:\Users\admin:.repos | binary | |
MD5:9CB0AC090780F28F1DE45A844BD87A09 | SHA256:384089A7BF041EC54AE6EEA3636CA0A93BFC648B7A81CCE5C948EB82C9B36393 | |||
| 7772 | 2025-04-29_ee9252da4bf46c5980a48c39922b0e9c_black-basta_elex_luca-stealer.exe | C:\Users\admin\npitaiwm.exe | executable | |
MD5:0F816EE0614E8CA5DB162AE34263444A | SHA256:9916B5C9D73B9202A20A8D4B4C21BBC97304B1BFF5095968B2D23794FE705DA1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
58
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4108 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
1276 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
1276 | SIHClient.exe | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.85.23.206:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
1276 | SIHClient.exe | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
1276 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1276 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4108 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4108 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
8072 | svchost.exe | 13.107.246.59:80 | microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
microsoft.com |
| whitelisted |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |