analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
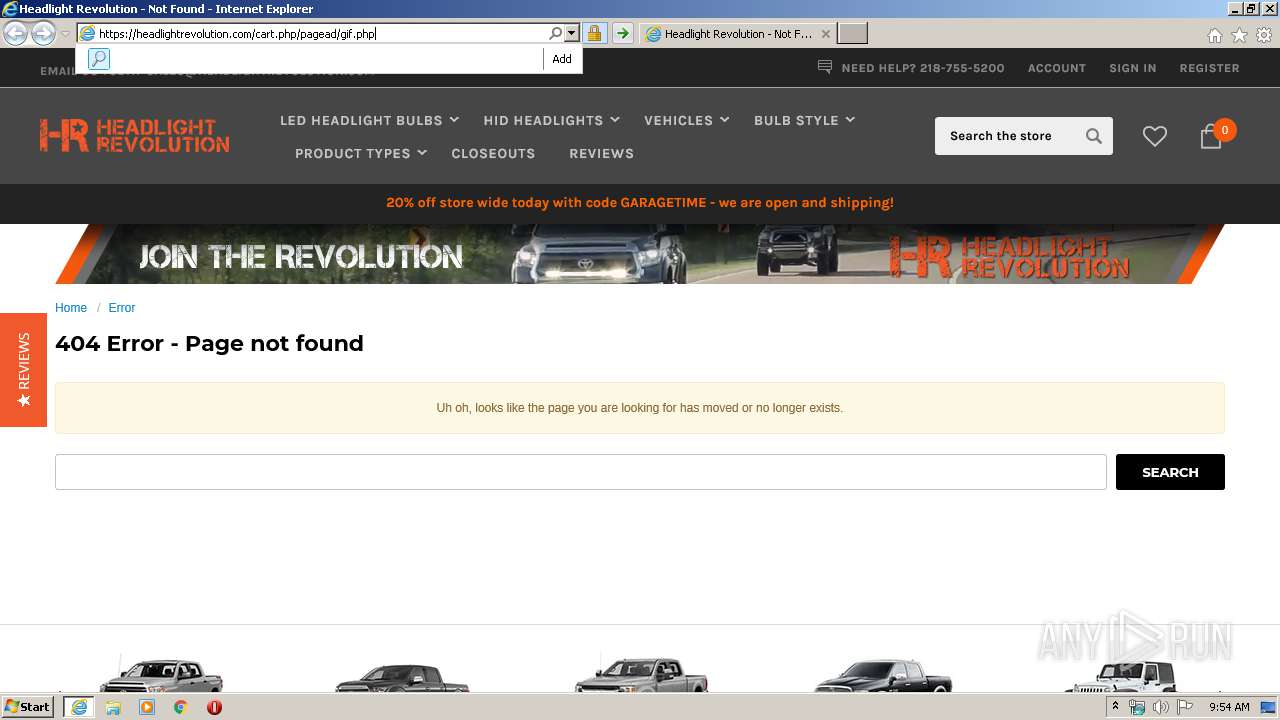
| URL: | https://headlightrevolution.com/cart.php/pagead/gif.php? |
| Full analysis: | https://app.any.run/tasks/03a9d83c-1548-4a49-b5ce-ad2a603579ea |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 08:53:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 57038D330519855533C971440D606607 |
| SHA1: | 961950F8FEF341F735111B7B8654502EBF9A0E8B |
| SHA256: | FC0E4BEE4C50967864B745F2F44CDD9D2B2C2BC77726ECBBC98E29BDCC286467 |
| SSDEEP: | 3:N88VRSUdIdEBhNK8PDh6:28nId8NBPDc |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3540)
Changes internet zones settings
- iexplore.exe (PID: 3540)
Reads Internet Cache Settings
- iexplore.exe (PID: 3540)
- iexplore.exe (PID: 3216)
Creates files in the user directory
- iexplore.exe (PID: 3216)
Reads internet explorer settings
- iexplore.exe (PID: 3216)
Reads settings of System Certificates
- iexplore.exe (PID: 3216)
- iexplore.exe (PID: 3540)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3540)
Changes settings of System certificates
- iexplore.exe (PID: 3540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3540 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://headlightrevolution.com/cart.php/pagead/gif.php?" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3216 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3540 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 772
Read events
1 411
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
106
Text files
296
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7037.tmp | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7038.tmp | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\9XO440Z8.txt | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:485769451751B235AA005A439A241DC2 | SHA256:D3CB3B2B263F929797CFEDAD54A2CA134639D586CD43E26A1D3934E9D5FFC177 | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4344B8AF97AF3A423D9EE52899963CDE_78849AF2BCA6F2FB97DE2940460ADC6A | der | |
MD5:BA634773F64FF271E7366E4930BD3068 | SHA256:C43C3E7160AEA4E752E4717948C99617CC2493BCB888AD97FED08C3C5FE97F00 | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:2F86A39384E42D175749FD0FE3E9526E | SHA256:35A49F80FEBE49410CAC94F77D88D5784C28E781EBEEC1C95183B28C78E06B1C | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:FB1DCFAD78F9693BB3A1A362365BDFD6 | SHA256:C9733E8718FE8213E3E71412B290E4DE1B8F859D2D994C8BBBC829A37E43951A | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\contivio-chat[1].js | text | |
MD5:1BED3D3F5A6C00684DFD39C6BB2BC45F | SHA256:7989A1A96A62CC7AD5F84FD40F4E293C16EDAB75CF1F8EA4E00773FA9364349D | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:63311A320518E4CA5045931F3E6ADE16 | SHA256:23B7BECCB98DAF194EF0EE6709E93CAC4632C1214F6478FCFA2A547515237D83 | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | binary | |
MD5:B1291120AC992AC2D4DCE2BE92121904 | SHA256:5C742D0EC46C3E95526E0FCC2CE563640A1F06FB4A093149E9BB3C920EF0F14E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
116
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAez3RP7hyTB6WlLwXG2xOk%3D | US | der | 471 b | whitelisted |
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3216 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3216 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3216 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3216 | iexplore.exe | 35.186.228.254:443 | — | Google Inc. | US | unknown |
3216 | iexplore.exe | 23.210.248.160:443 | cdn11.bigcommerce.com | Akamai International B.V. | NL | whitelisted |
3216 | iexplore.exe | 104.22.50.245:443 | www.powr.io | Cloudflare Inc | US | suspicious |
3216 | iexplore.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3216 | iexplore.exe | 54.241.86.195:443 | uschat3.contivio.com | Amazon.com, Inc. | US | unknown |
3216 | iexplore.exe | 143.204.94.29:443 | js.adsrvr.org | — | US | suspicious |
3216 | iexplore.exe | 216.58.208.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3216 | iexplore.exe | 23.67.141.171:443 | chimpstatic.com | Akamai International B.V. | NL | unknown |
3216 | iexplore.exe | 13.225.87.20:443 | d3ryumxhbd2uw7.cloudfront.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
headlightrevolution.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
cdn11.bigcommerce.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.powr.io |
| shared |
uschat3.contivio.com |
| unknown |
acp-magento.appspot.com |
| whitelisted |
js.adsrvr.org |
| whitelisted |
chimpstatic.com |
| whitelisted |