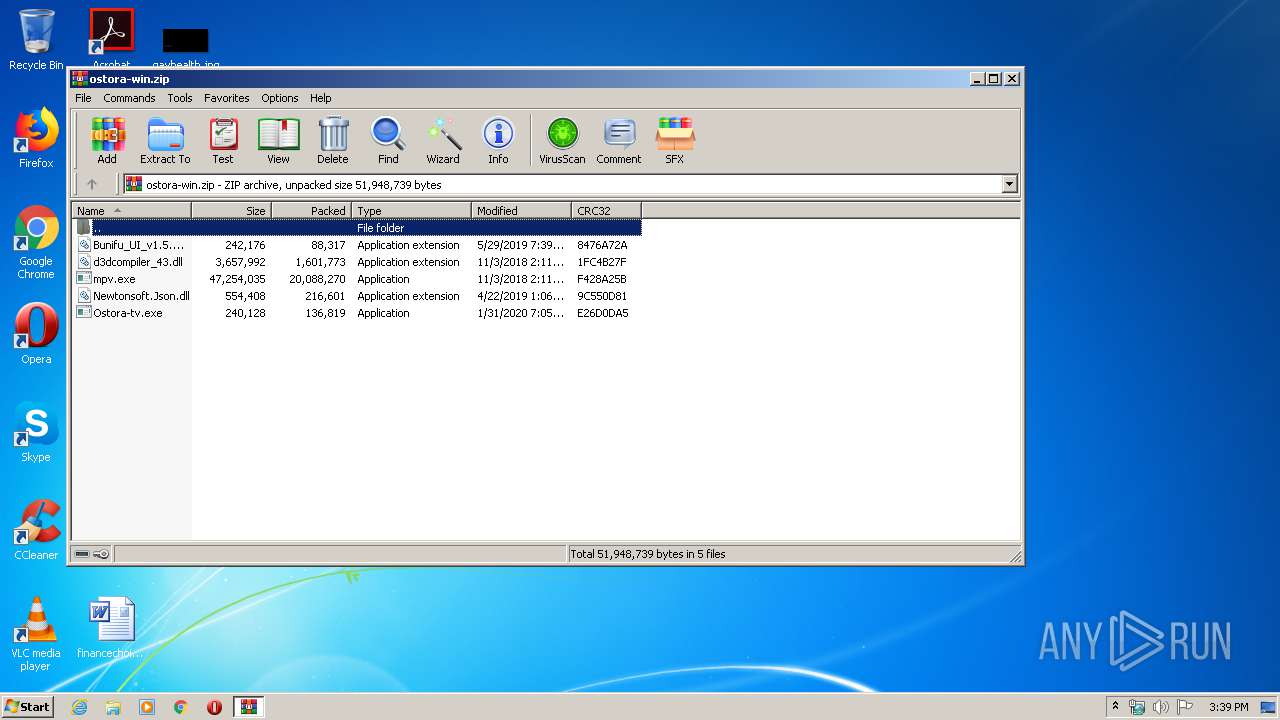
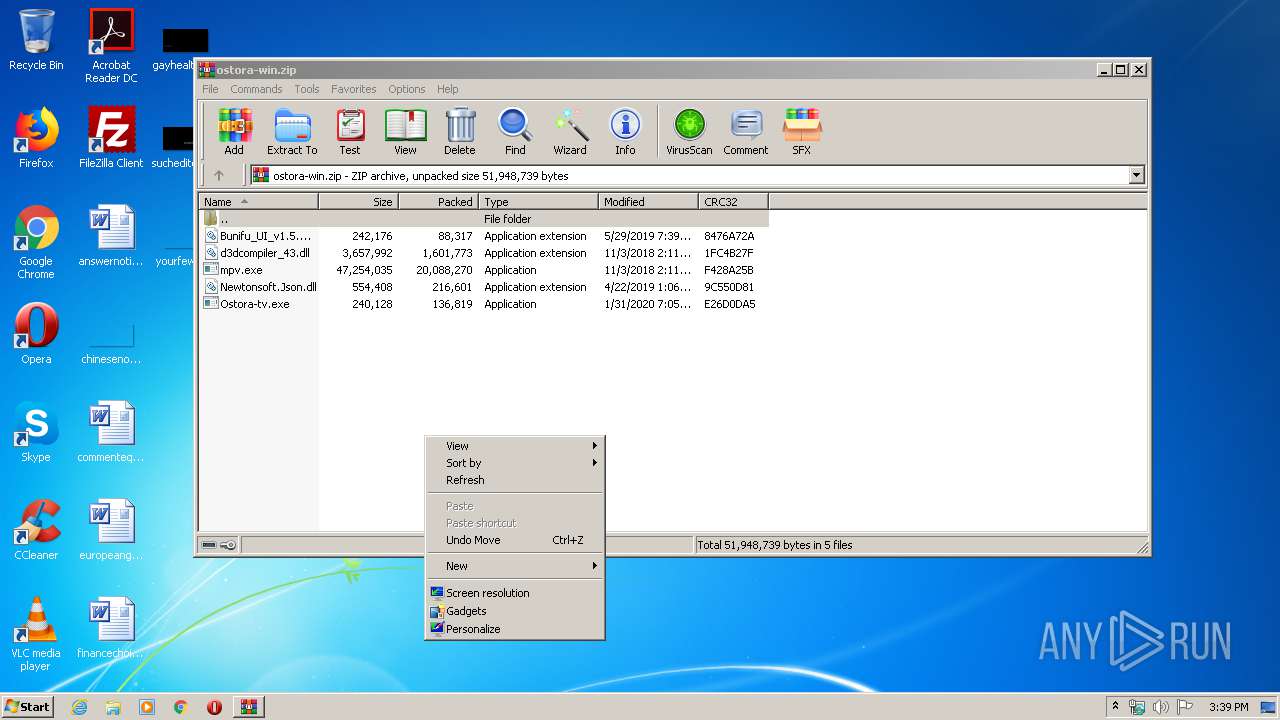
| download: | ostora-win.zip |
| Full analysis: | https://app.any.run/tasks/060a714b-a0c8-4931-aac4-967759611e97 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2020, 15:39:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E543B4079E8BFCD49616B92FFAD74D91 |
| SHA1: | 443F4760DA7F2DE808233E6D77F2195796D9F599 |
| SHA256: | FC05E929083755514AF6D74F0B48CD7C59EC2F307FA25FF1944134E2B9AD0645 |
| SSDEEP: | 393216:tb4JPjqN7mrlCvHlsunD8GyDPVKQ9zpJR8+/yEaPmF5bU6LvbrVu7znWpXBlmOv:tsJPmNwMXD8jXnXz/y5O3g8v/kroRZ |
MALICIOUS
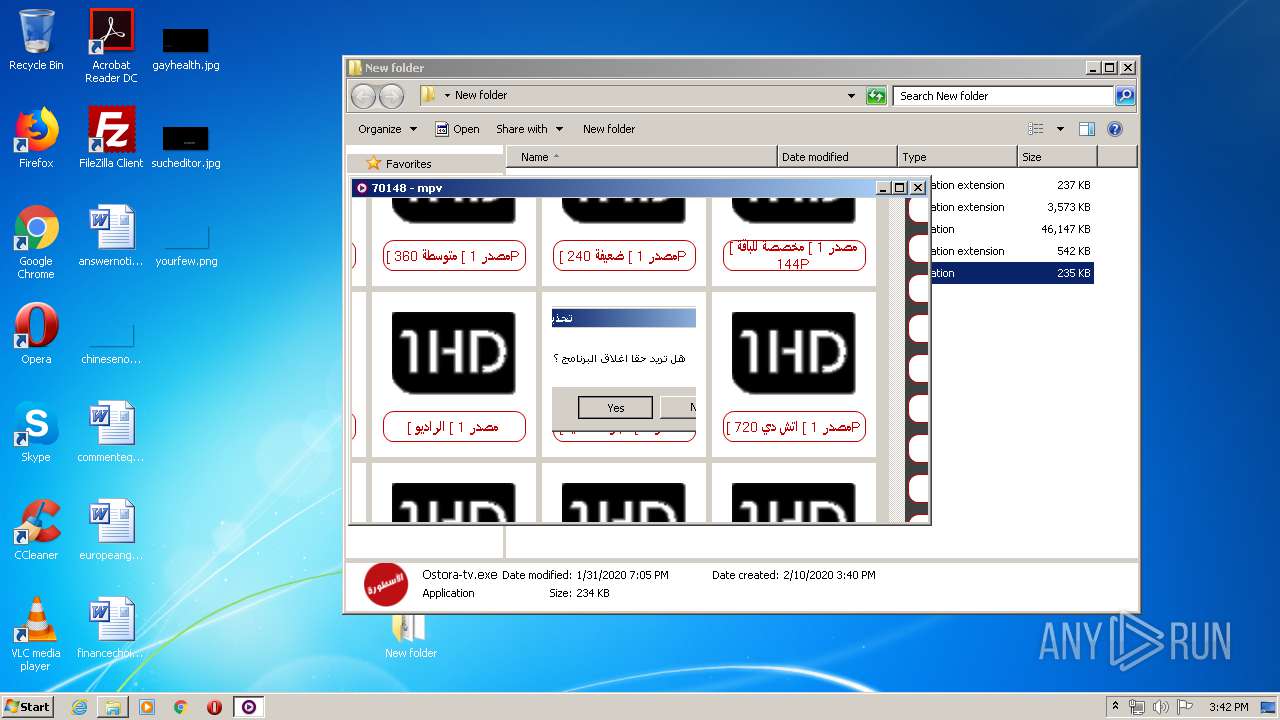
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3548)
- Ostora-tv.exe (PID: 3312)
Application was dropped or rewritten from another process
- Ostora-tv.exe (PID: 3312)
Changes settings of System certificates
- Ostora-tv.exe (PID: 3312)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2116)
Connects to unusual port
- mpv.exe (PID: 3872)
Adds / modifies Windows certificates
- Ostora-tv.exe (PID: 3312)
INFO
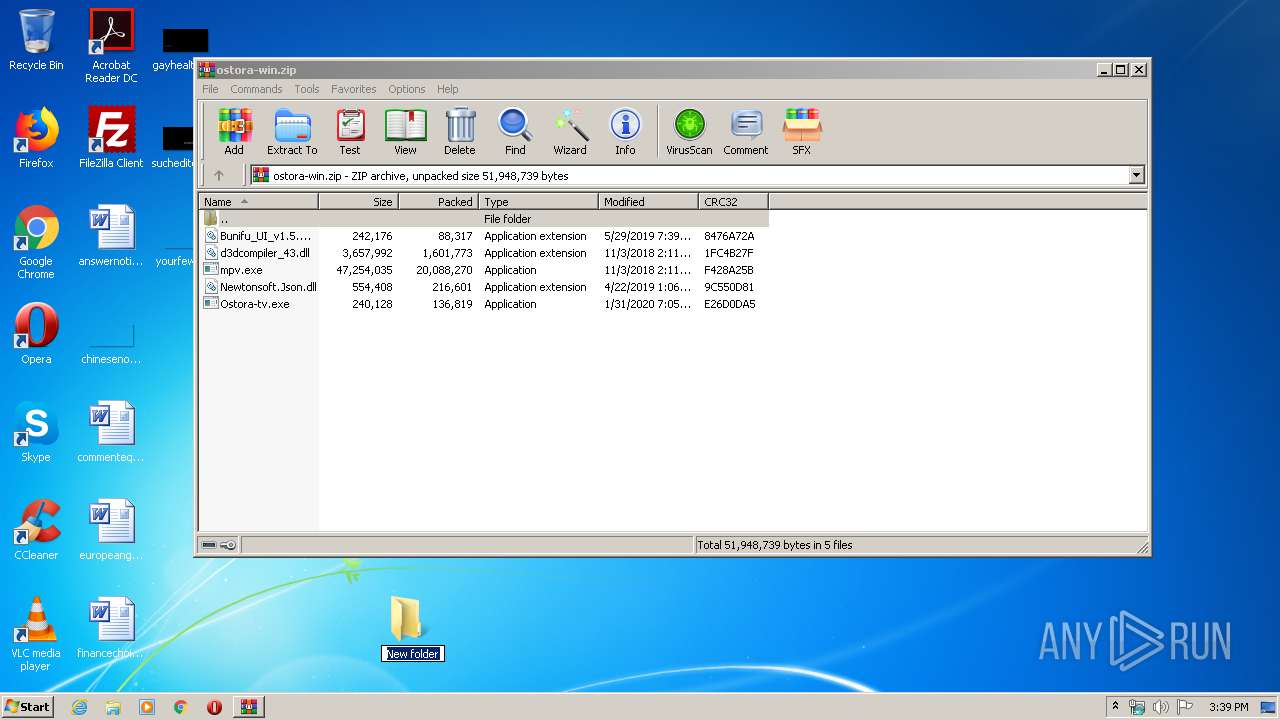
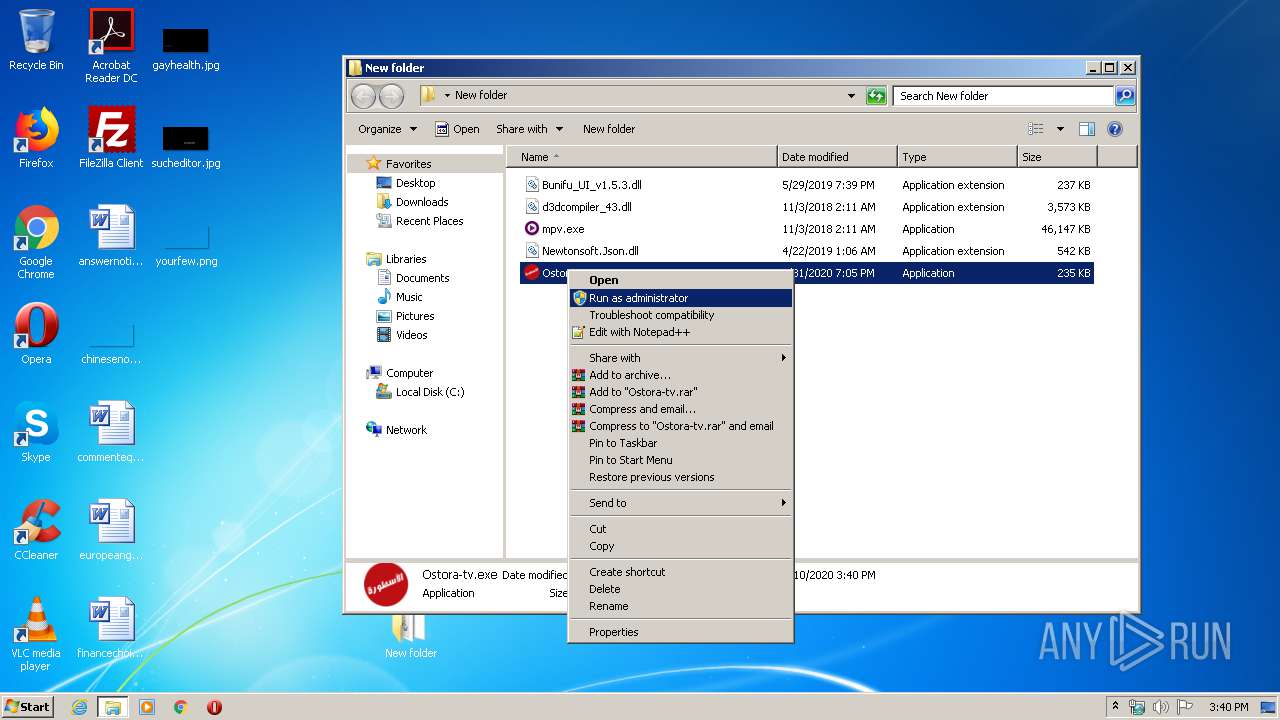
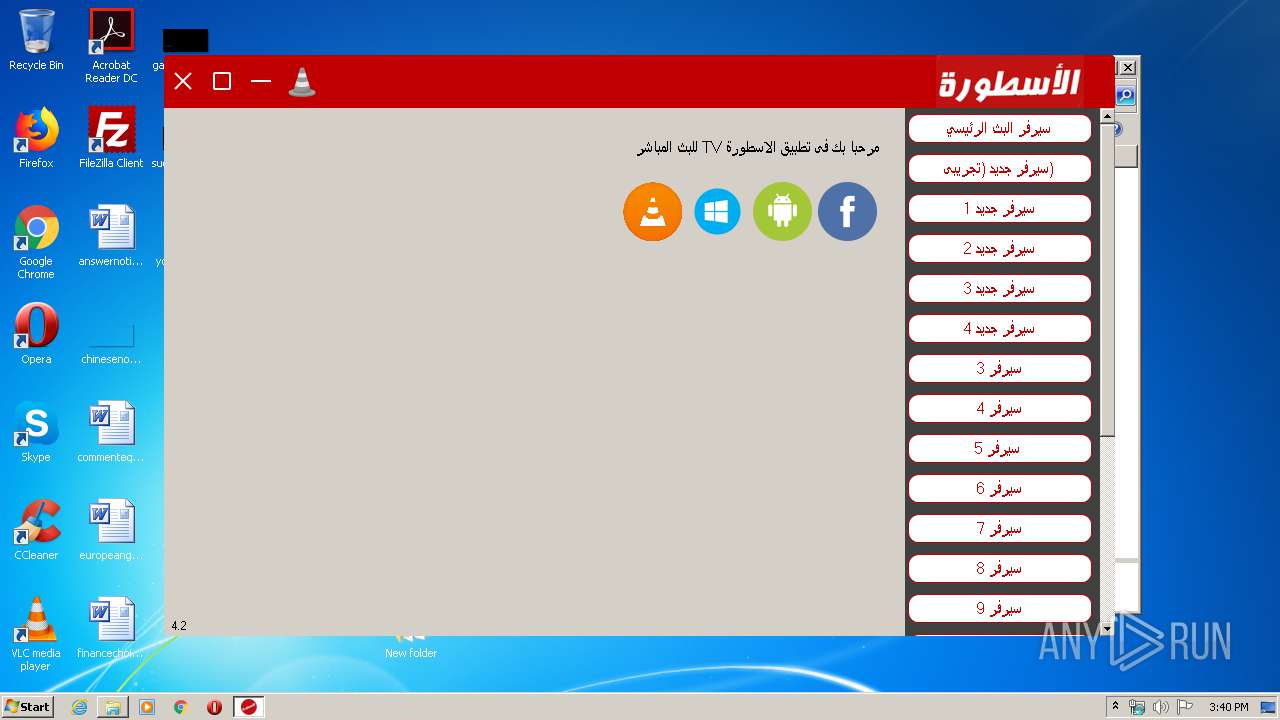
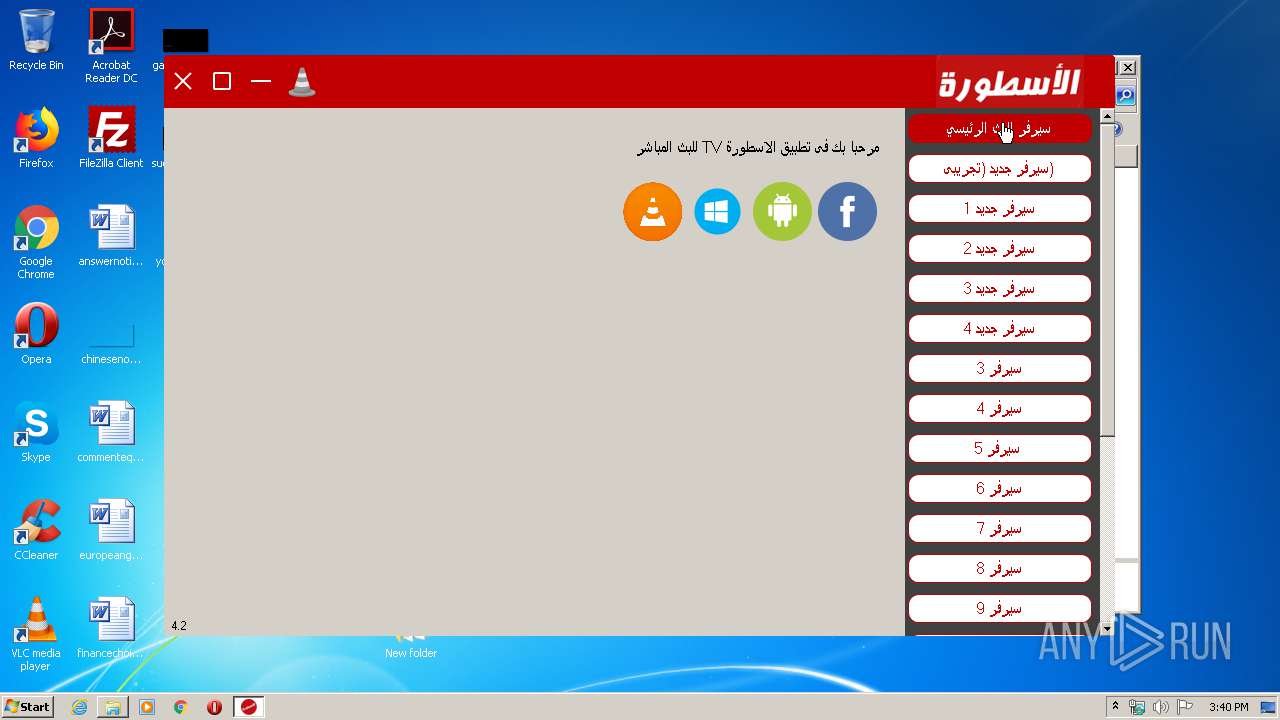
Manual execution by user
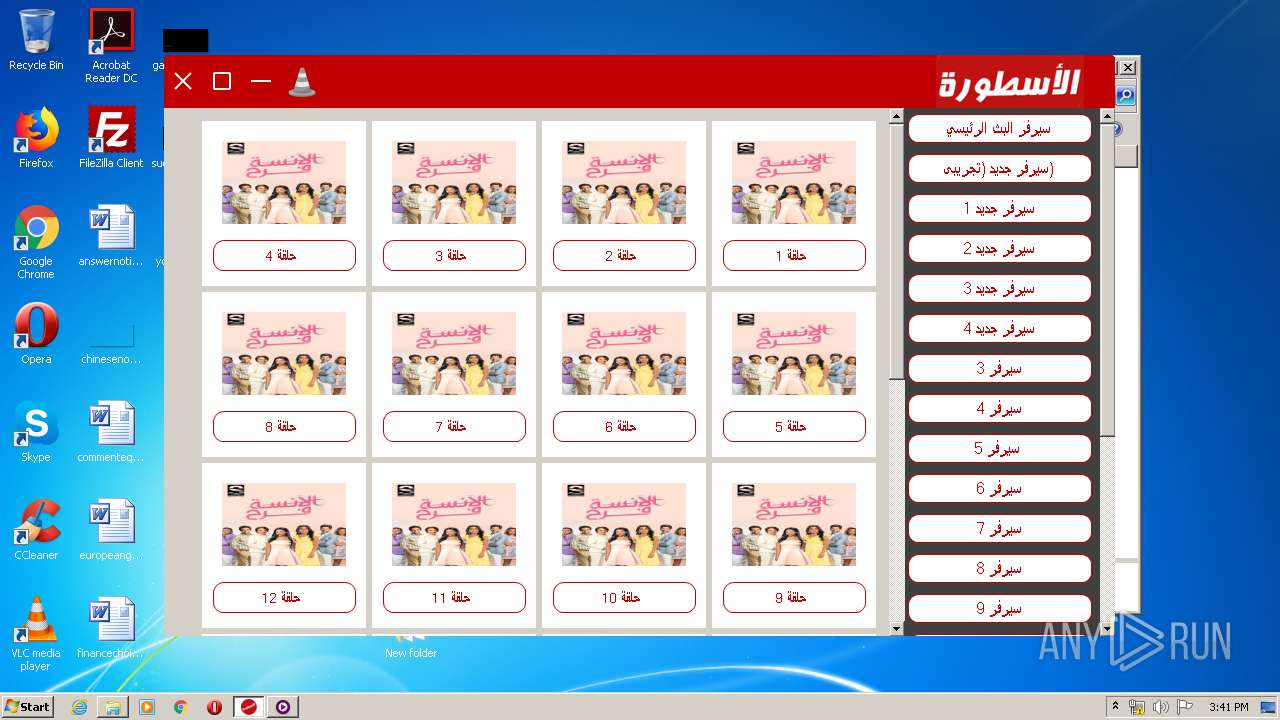
- Ostora-tv.exe (PID: 3312)
Reads settings of System Certificates
- Ostora-tv.exe (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:29 19:39:14 |
| ZipCRC: | 0x8476a72a |
| ZipCompressedSize: | 88317 |
| ZipUncompressedSize: | 242176 |
| ZipFileName: | Bunifu_UI_v1.5.3.dll |
Total processes
44
Monitored processes
6
Malicious processes
2
Suspicious processes
0
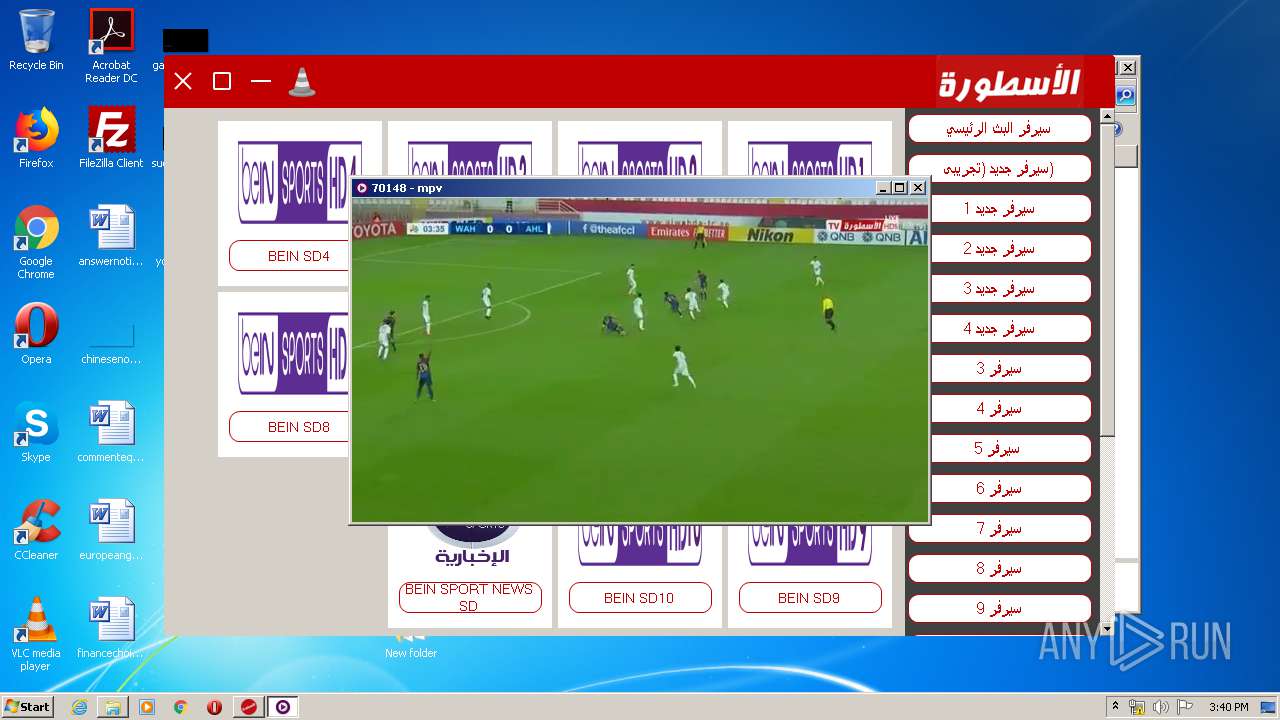
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
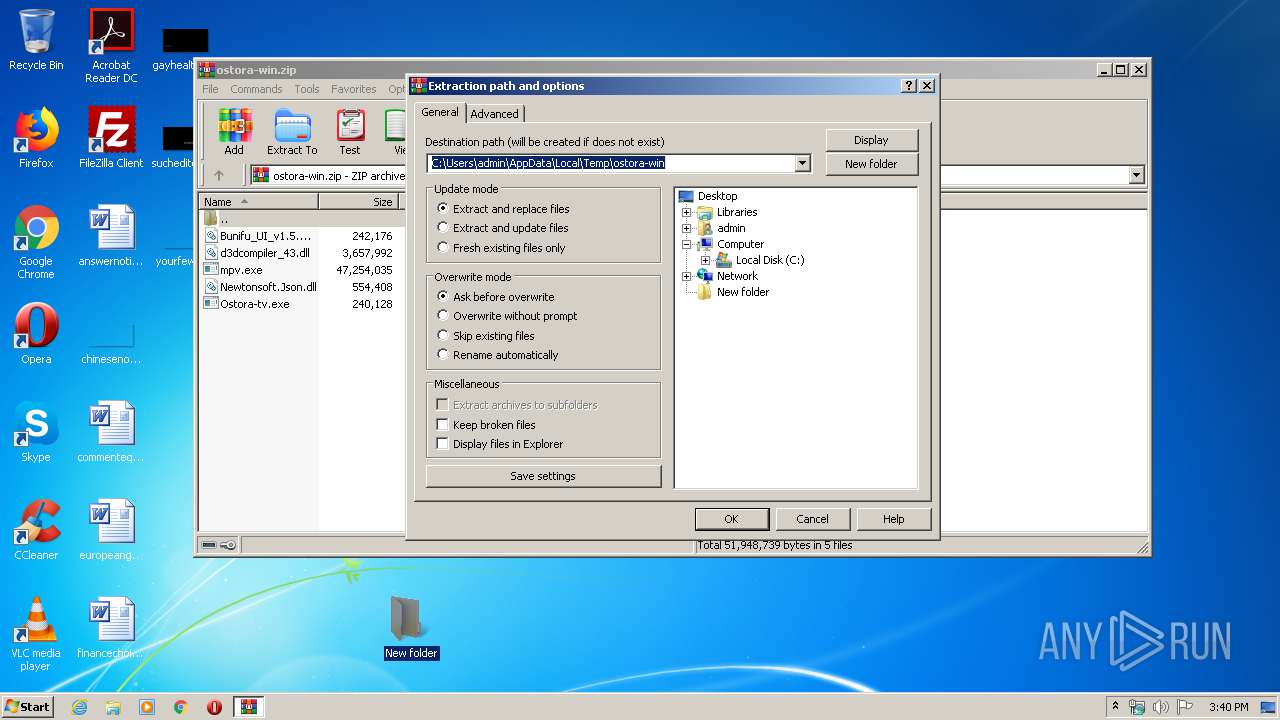
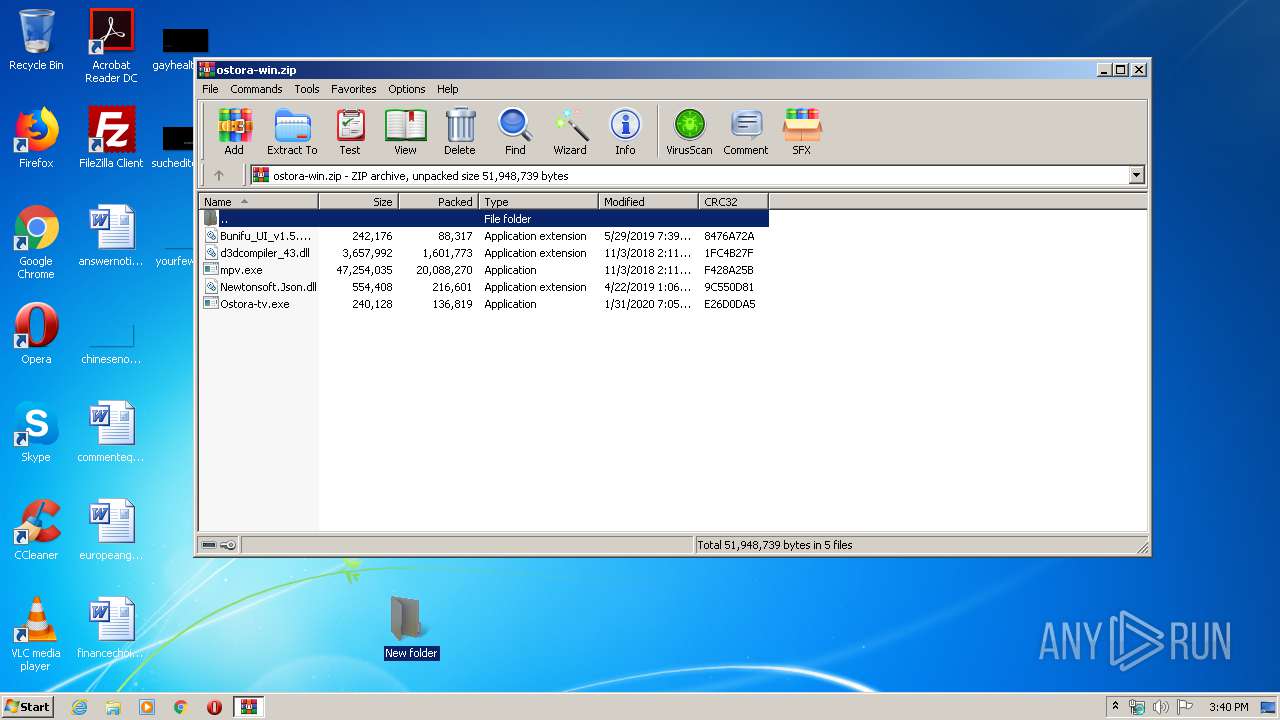
| 2116 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ostora-win.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
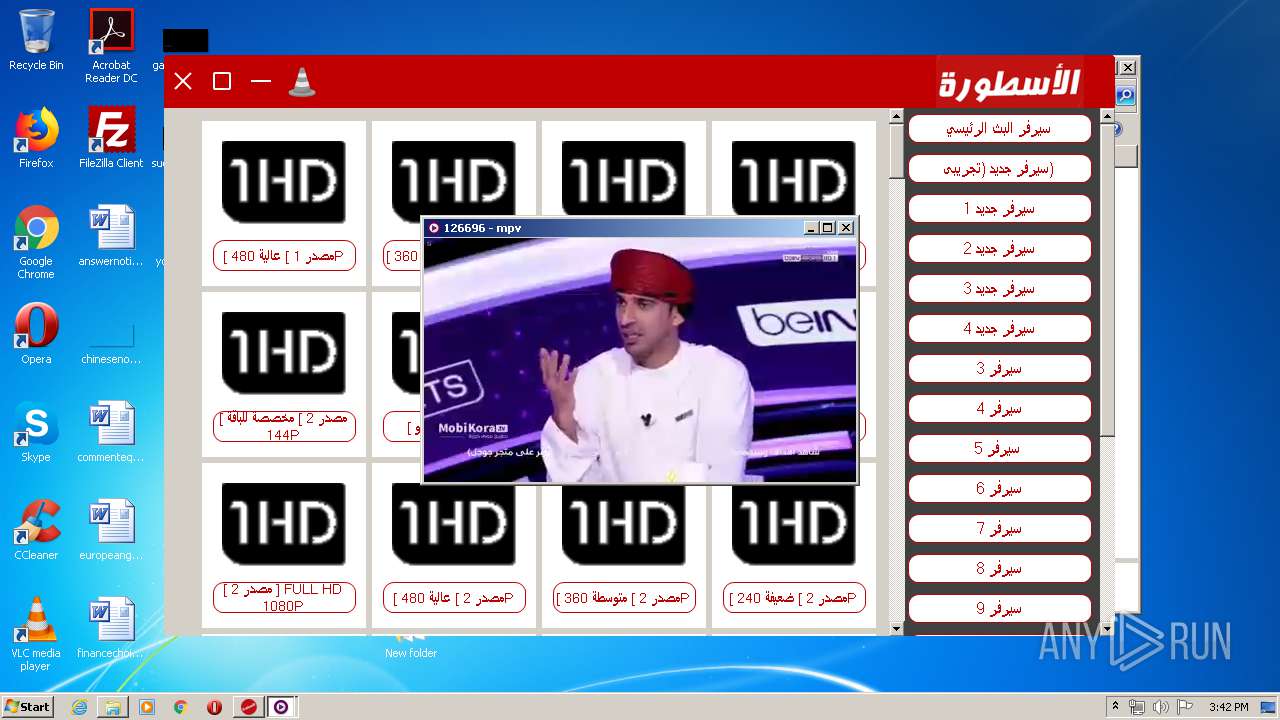
| 2708 | "C:\Users\admin\Desktop\New folder\mpv.exe" https://www.ostora-tv.com/live/20445099/1544487/70148 --fs --user-agent="Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:71.0) Gecko/20100101 Firefox/71.0" | C:\Users\admin\Desktop\New folder\mpv.exe | Ostora-tv.exe | ||||||||||||
User: admin Company: mpv Integrity Level: HIGH Description: mpv Exit code: 0 Version: 0.29.0-86-g880c59d189 Modules
| |||||||||||||||
| 3312 | "C:\Users\admin\Desktop\New folder\Ostora-tv.exe" | C:\Users\admin\Desktop\New folder\Ostora-tv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ostora-tv Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3616 | "C:\Users\admin\Desktop\New folder\mpv.exe" https://www.ostora-tv.com/live/20445099/1544487/130991 --fs --user-agent="Lavf/57.83.100" | C:\Users\admin\Desktop\New folder\mpv.exe | Ostora-tv.exe | ||||||||||||
User: admin Company: mpv Integrity Level: HIGH Description: mpv Exit code: 0 Version: 0.29.0-86-g880c59d189 Modules
| |||||||||||||||
| 3872 | "C:\Users\admin\Desktop\New folder\mpv.exe" https://www.ostora-tv.com/live/20445099/1544487/126696 --fs --user-agent="Dalvik/2.1.0 (Linux; U; Android 5.1.1; SM-G930K Build/NRD90M)" | C:\Users\admin\Desktop\New folder\mpv.exe | Ostora-tv.exe | ||||||||||||
User: admin Company: mpv Integrity Level: HIGH Description: mpv Exit code: 0 Version: 0.29.0-86-g880c59d189 Modules
| |||||||||||||||
Total events
2 146
Read events
924
Write events
1 222
Delete events
0
Modification events
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ostora-win.zip | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\New folder | |||
| (PID) Process: | (2116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFC100000039000000810400002E020000 | |||
Executable files
4
Suspicious files
0
Text files
0
Unknown types
0
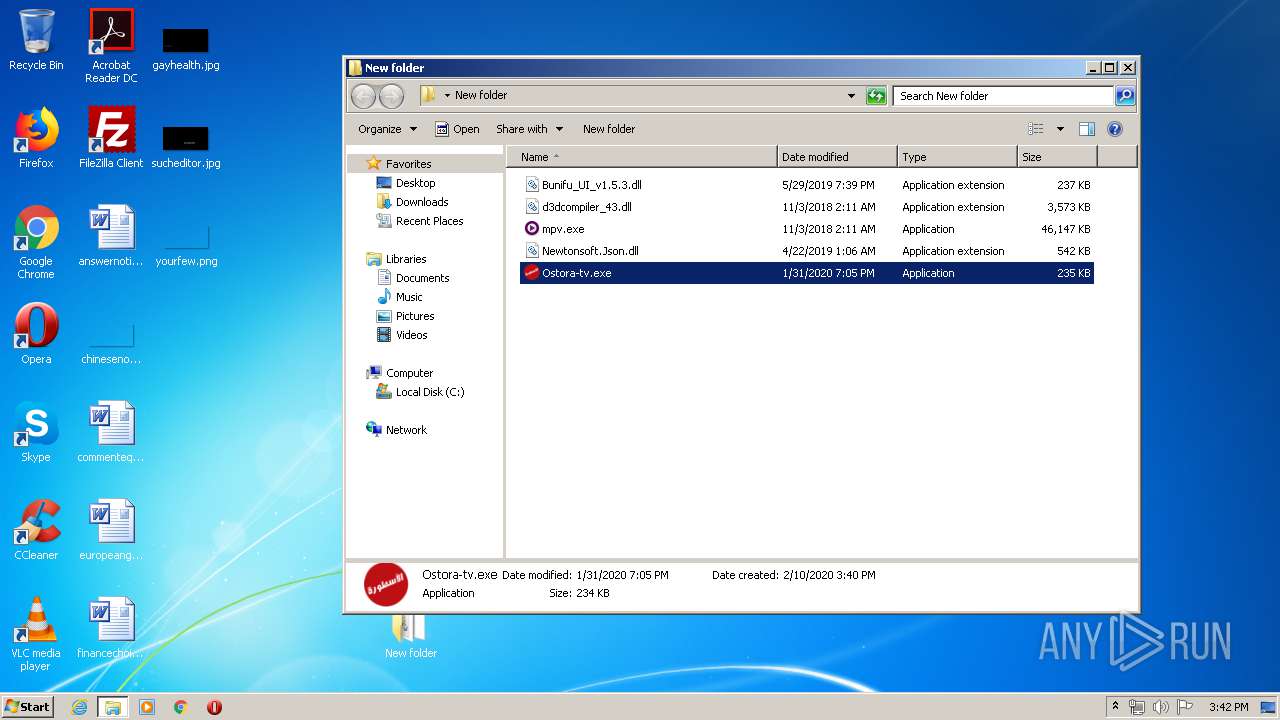
Dropped files
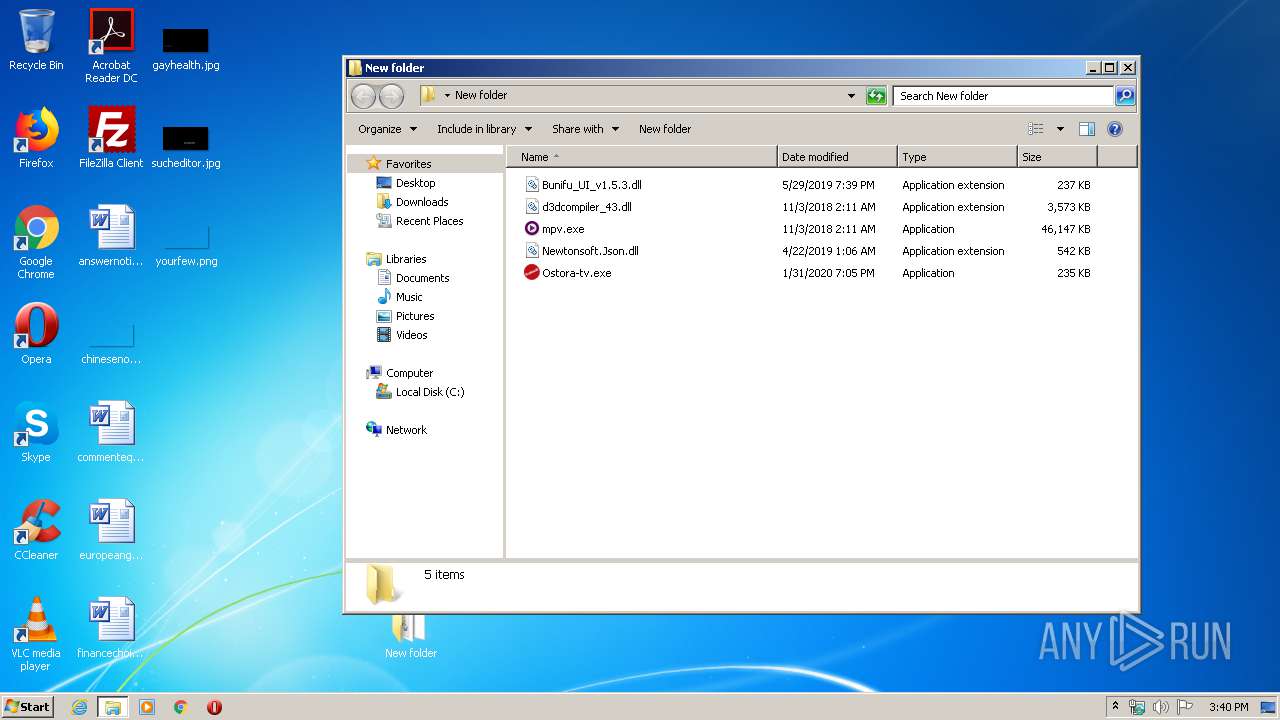
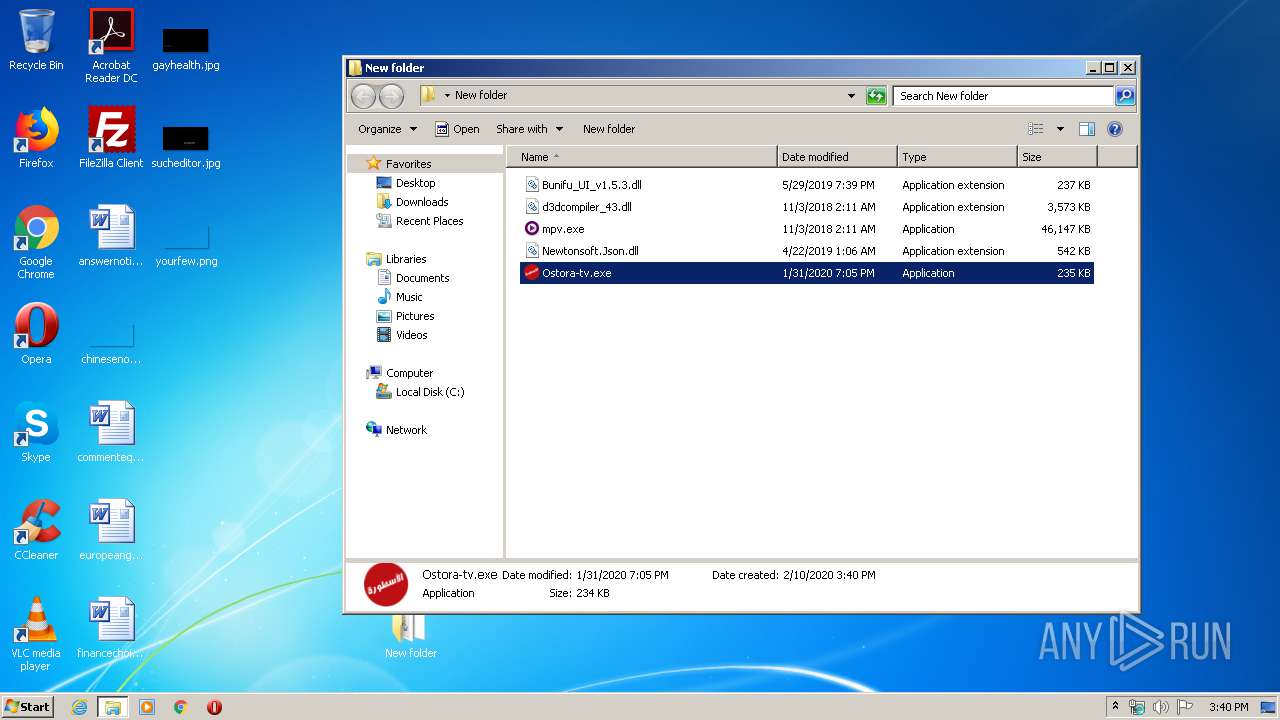
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2116 | WinRAR.exe | C:\Users\admin\Desktop\New folder\mpv.exe | — | |
MD5:— | SHA256:— | |||
| 2116 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Ostora-tv.exe | executable | |
MD5:— | SHA256:— | |||
| 2116 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Newtonsoft.Json.dll | executable | |
MD5:9DE86CDF74A30602D6BAA7AFFC8C4A0F | SHA256:56032ADE45CCF8F4C259A2E57487124CF448A90BCA2EEB430DA2722D9E109583 | |||
| 2116 | WinRAR.exe | C:\Users\admin\Desktop\New folder\Bunifu_UI_v1.5.3.dll | executable | |
MD5:2ECB51AB00C5F340380ECF849291DBCF | SHA256:F1B3E0F2750A9103E46A6A4A34F1CF9D17779725F98042CC2475EC66484801CF | |||
| 2116 | WinRAR.exe | C:\Users\admin\Desktop\New folder\d3dcompiler_43.dll | executable | |
MD5:587A415CD5AC2069813ADEF5F7685021 | SHA256:2AD0D4987FC4624566B190E747C9D95038443956ED816ABFD1E2D389B5EC0851 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
39
DNS requests
10
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | mpv.exe | GET | 302 | 104.27.188.106:80 | http://www.ostora-tv.com/api/vKz.m3u8?o=ZFyegfH0TQgpJzdPKHP9MP0vQwDbe9IzWsLVw0skcGsnCF-r_o2j1R2T2BNmBXMXS2wal0QhtxQ4mPRnr_tqsu1JrNZzhScK4PC2nVVNHTo=&h=20445099 | US | — | — | shared |
3872 | mpv.exe | GET | — | 89.38.97.161:1935 | http://lbv2.kora.video:1935/redirect/win1/alaula-win_240p?scheme=m3u8&knendtime=1581385310710&knstarttime=1530949310&knhash=1-3iV1qKpGVoLl-3hliy59th3_2duL2o03_8Acf1bFQ= | NL | — | — | unknown |
2708 | mpv.exe | GET | 200 | 104.27.183.175:80 | http://www.galaxi.pw/images/349252/25_00386012.jpg | US | ts | 865 Kb | suspicious |
2708 | mpv.exe | GET | 200 | 104.27.179.189:80 | http://www.hala-me.pw/images/349262/25_00386013.jpg | US | ts | 766 Kb | suspicious |
2708 | mpv.exe | GET | 200 | 104.27.183.175:80 | http://www.galaxi.pw/images/349282/25_00386015.jpg | US | ts | 804 Kb | suspicious |
2708 | mpv.exe | GET | 200 | 104.18.33.174:80 | http://www.dndsh.pw/images/349303/25_00386017.jpg | US | ts | 756 Kb | suspicious |
2708 | mpv.exe | GET | 200 | 104.27.179.189:80 | http://www.hala-me.pw/images/349292/25_00386016.jpg | US | ts | 716 Kb | suspicious |
3872 | mpv.exe | GET | 302 | 104.27.188.106:80 | http://www.ostora-tv.com/api/vKz.m3u8?o=ZFyegfH0TQgpJzdPKHP9MP0vQwDbe9IzWsLVw0skcGsnCF-r_o2j1R2T2BNmBXMXS2wal0QhtxQ4mPRnr_tqsu1JrNZzhScK4PC2nVVNHTo=&h=20445099 | US | — | — | shared |
3872 | mpv.exe | GET | — | 89.38.97.161:1935 | http://lbv2.kora.video:1935/redirect/win1/alaula-win_240p?scheme=m3u8&knendtime=1581385311812&knstarttime=1530949311&knhash=BnIl8EU6VEqpshG5291gQs8BGSkdf2Smfq9mdUVPA0k= | NL | — | — | unknown |
2708 | mpv.exe | GET | 200 | 104.18.33.174:80 | http://www.dndsh.pw/images/349272/25_00386014.jpg | US | ts | 743 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3312 | Ostora-tv.exe | 104.27.188.106:443 | www.ostora-tv.com | Cloudflare Inc | US | shared |
3312 | Ostora-tv.exe | 163.171.140.202:443 | demo.cloudimg.io | — | US | unknown |
2708 | mpv.exe | 104.27.188.106:443 | www.ostora-tv.com | Cloudflare Inc | US | shared |
3312 | Ostora-tv.exe | 163.171.133.152:443 | demo.cloudimg.io | — | US | malicious |
2708 | mpv.exe | 104.31.9.180:443 | cdn102.ost-cdn.xyz | Cloudflare Inc | US | unknown |
2708 | mpv.exe | 104.31.8.180:443 | cdn102.ost-cdn.xyz | Cloudflare Inc | US | unknown |
2708 | mpv.exe | 104.27.183.175:80 | www.galaxi.pw | Cloudflare Inc | US | shared |
2708 | mpv.exe | 104.27.179.189:80 | www.hala-me.pw | Cloudflare Inc | US | suspicious |
2708 | mpv.exe | 104.18.33.174:80 | www.dndsh.pw | Cloudflare Inc | US | shared |
3616 | mpv.exe | 104.27.188.106:443 | www.ostora-tv.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ostora-tv.com |
| unknown |
demo.cloudimg.io |
| malicious |
cdn102.ost-cdn.xyz |
| unknown |
cdn160.ost-cdn.xyz |
| unknown |
www.galaxi.pw |
| suspicious |
www.hala-me.pw |
| suspicious |
www.dndsh.pw |
| suspicious |
aflamuna.com |
| unknown |
lbv2.kora.video |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2708 | mpv.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2708 | mpv.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2708 | mpv.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2708 | mpv.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2708 | mpv.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2708 | mpv.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |
2708 | mpv.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |