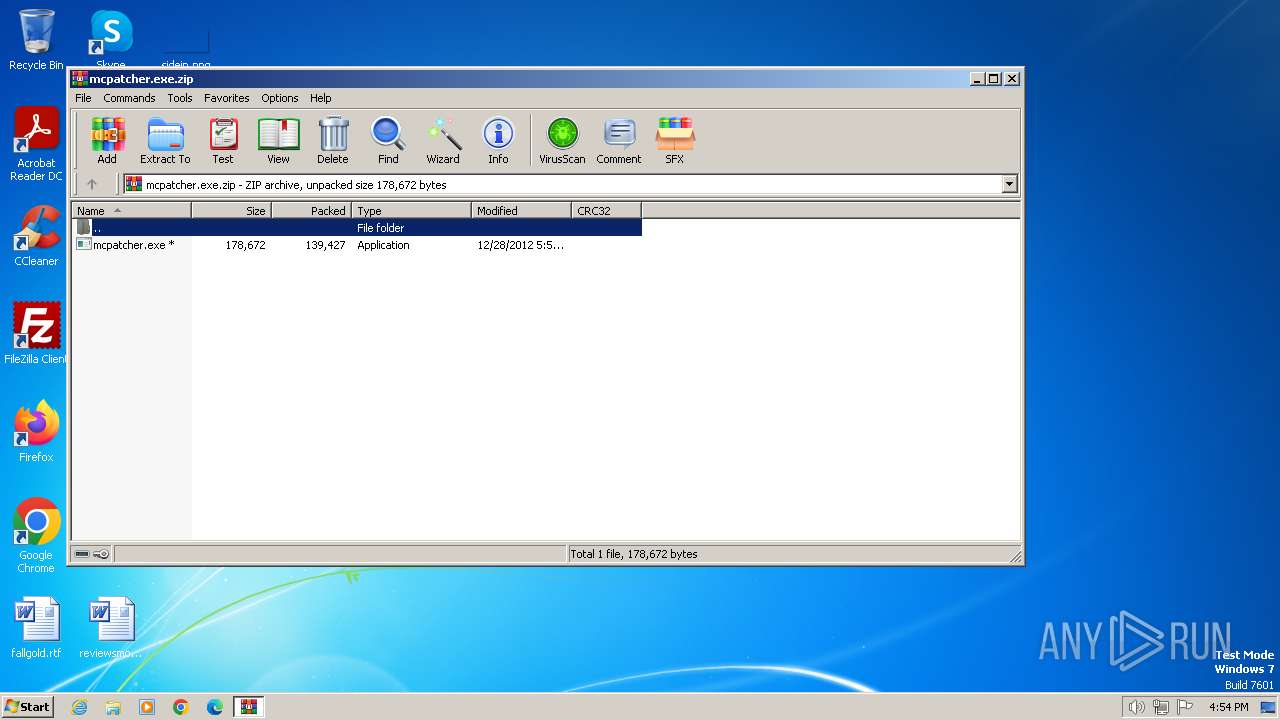
| File name: | mcpatcher.exe.zip |
| Full analysis: | https://app.any.run/tasks/71cda047-192d-48a6-ba62-0530b29c6347 |
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2024, 16:53:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
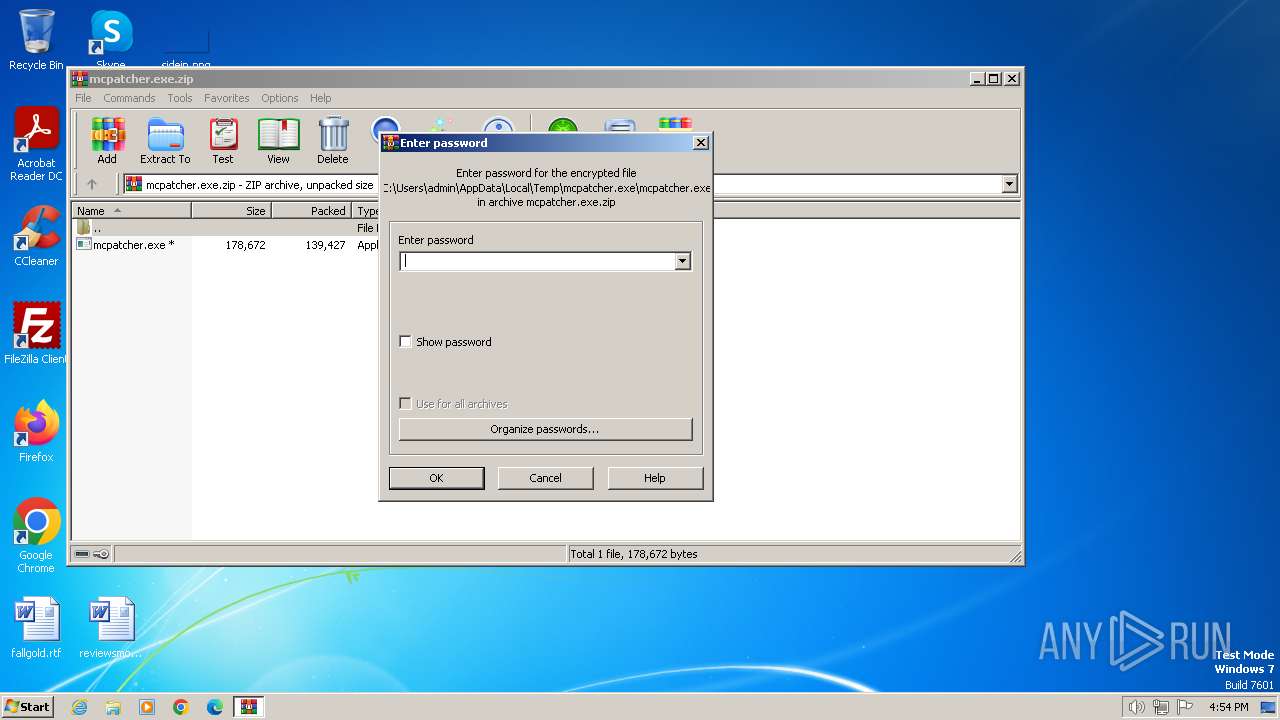
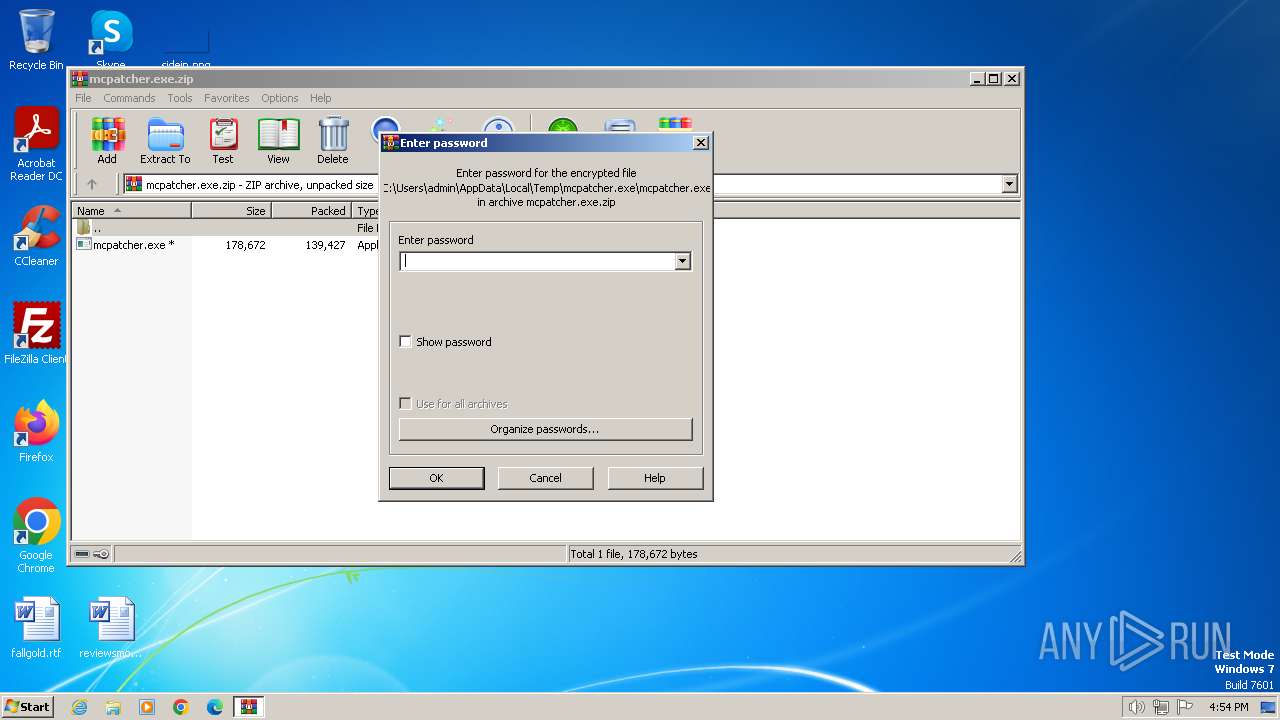
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | CAF2F13745ED7E02F6BCFEF51348664A |
| SHA1: | 0839A799AE179079F9DEE7508945BAE50619C01D |
| SHA256: | FBEF51562863B1BAB41388A1F1DD421E44B17EA40261DDB85D343CEDCAA761B8 |
| SSDEEP: | 6144:7ONZSexs44PQmW8mFY7IokmXV3PcbSNNnkBbZt:7O2exv47udIlfFx4Vt |
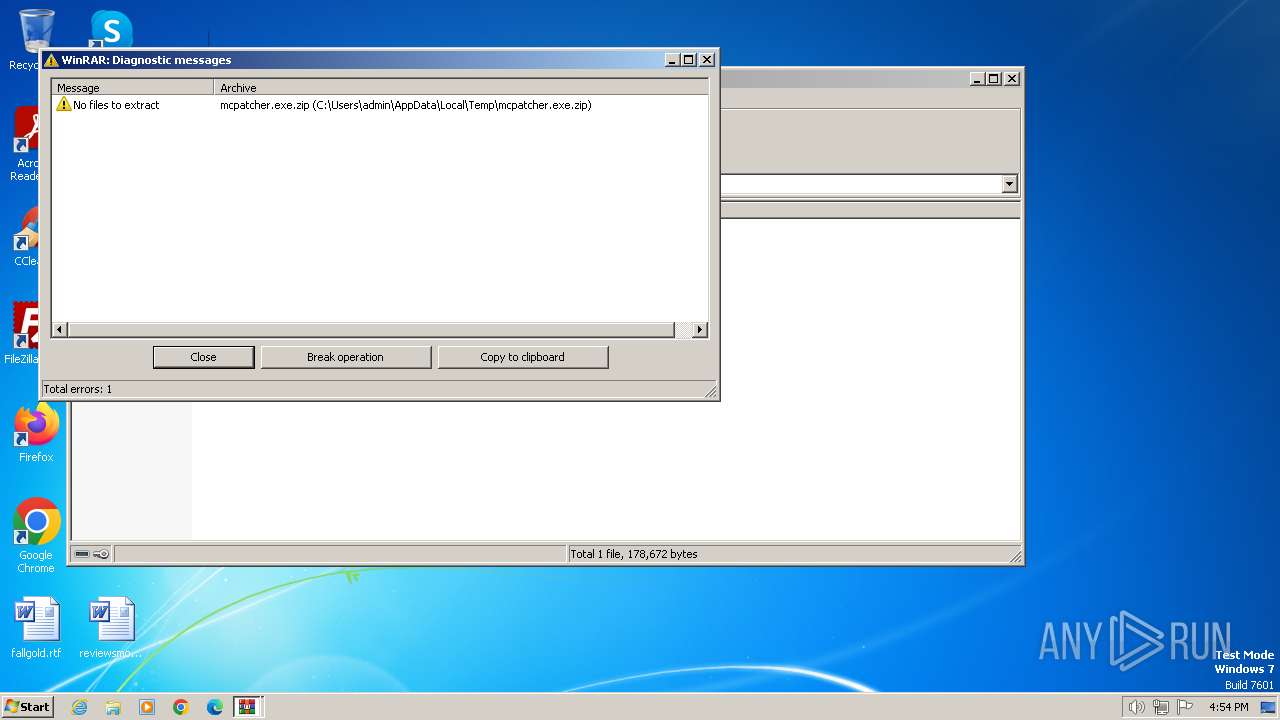
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4052)
- mcpatcher.exe (PID: 120)
- mcpatcher.exe (PID: 1656)
SUSPICIOUS
Executable content was dropped or overwritten
- mcpatcher.exe (PID: 120)
- mcpatcher.exe (PID: 1656)
The process creates files with name similar to system file names
- mcpatcher.exe (PID: 120)
- mcpatcher.exe (PID: 1656)
Malware-specific behavior (creating "System.dll" in Temp)
- mcpatcher.exe (PID: 120)
- mcpatcher.exe (PID: 1656)
Reads security settings of Internet Explorer
- northstar.exe (PID: 2120)
- northstar.exe (PID: 1976)
Checks Windows Trust Settings
- northstar.exe (PID: 2120)
- northstar.exe (PID: 1976)
Reads settings of System Certificates
- northstar.exe (PID: 2120)
- northstar.exe (PID: 1976)
INFO
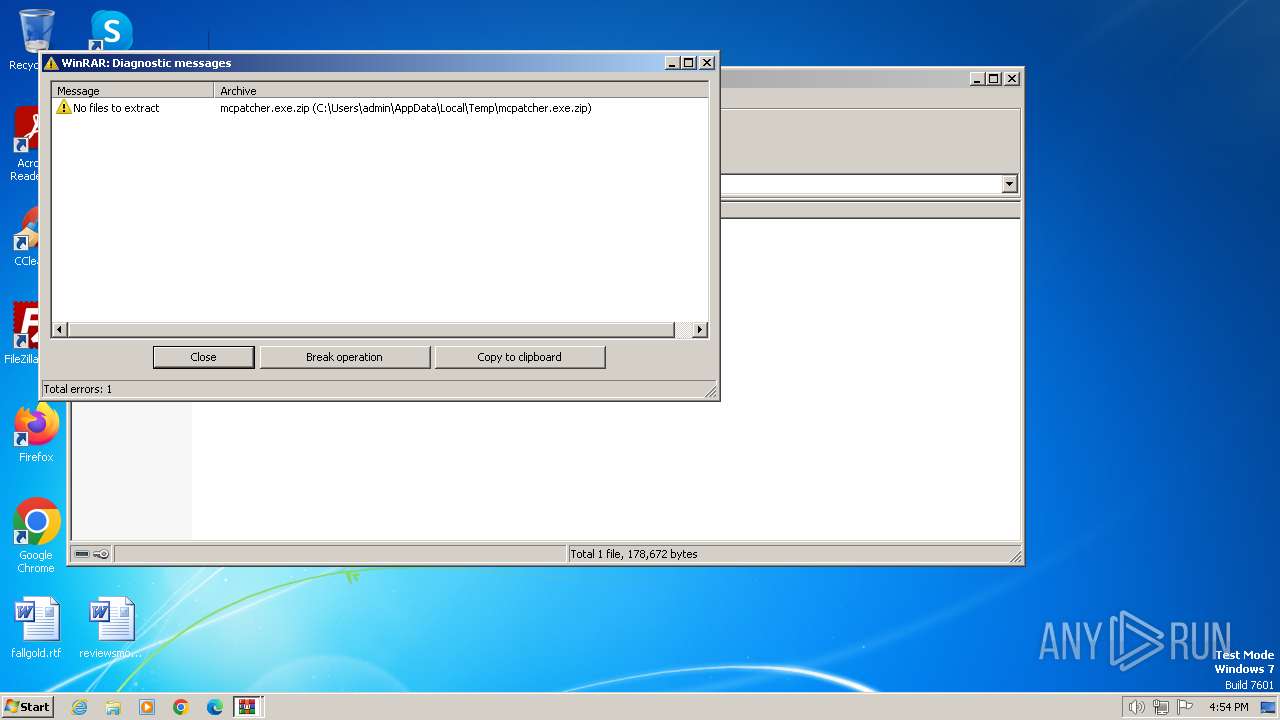
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4052)
Checks supported languages
- mcpatcher.exe (PID: 120)
- northstar.exe (PID: 2120)
- mcpatcher.exe (PID: 1656)
- northstar.exe (PID: 1976)
Reads the computer name
- mcpatcher.exe (PID: 120)
- northstar.exe (PID: 2120)
- mcpatcher.exe (PID: 1656)
- northstar.exe (PID: 1976)
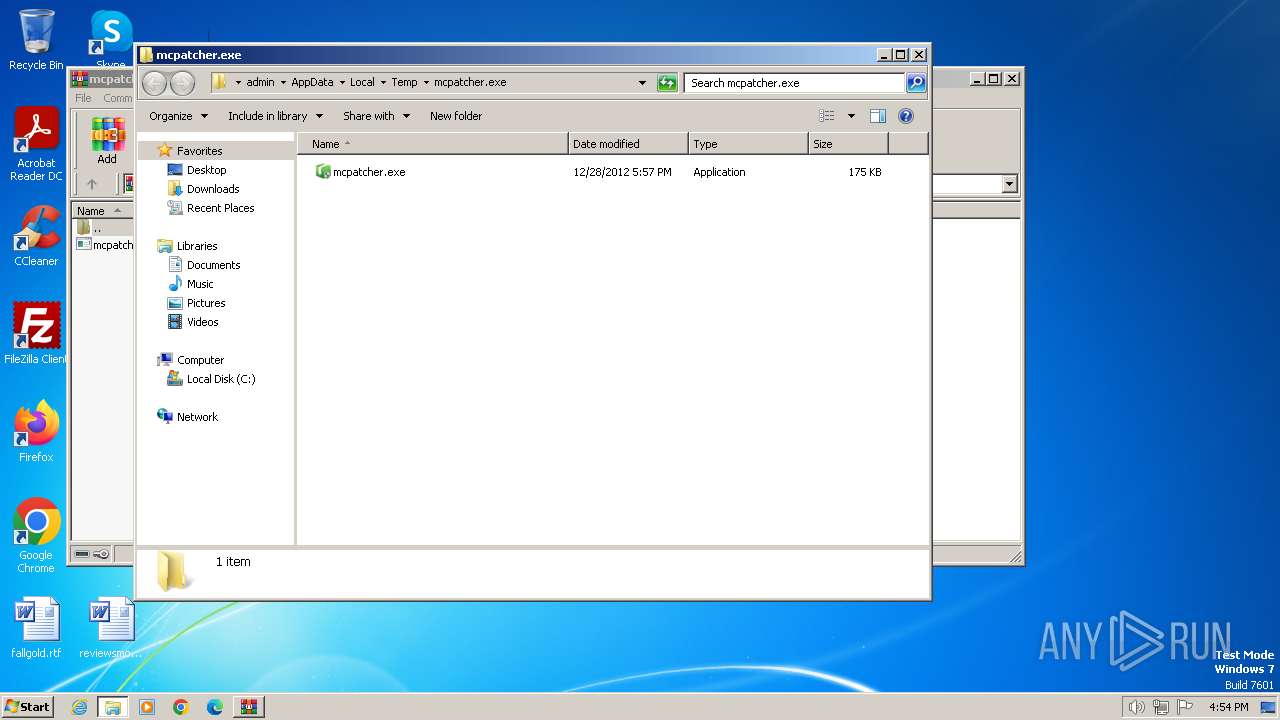
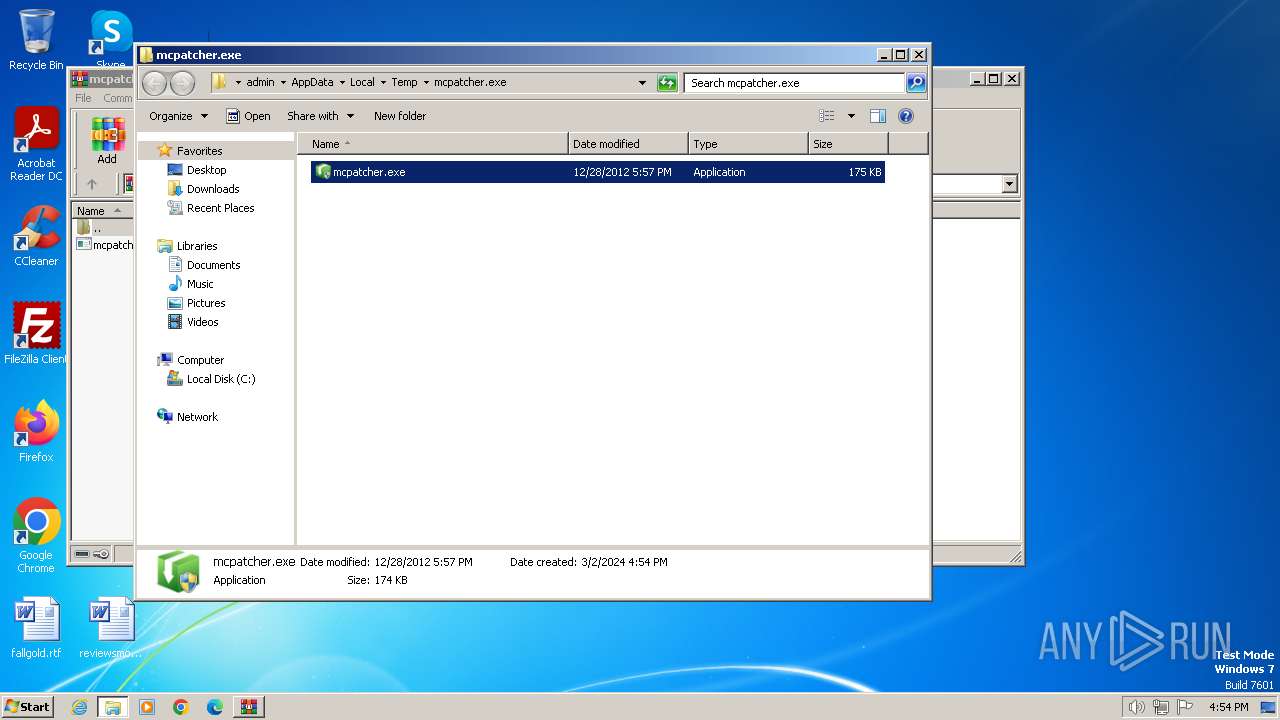
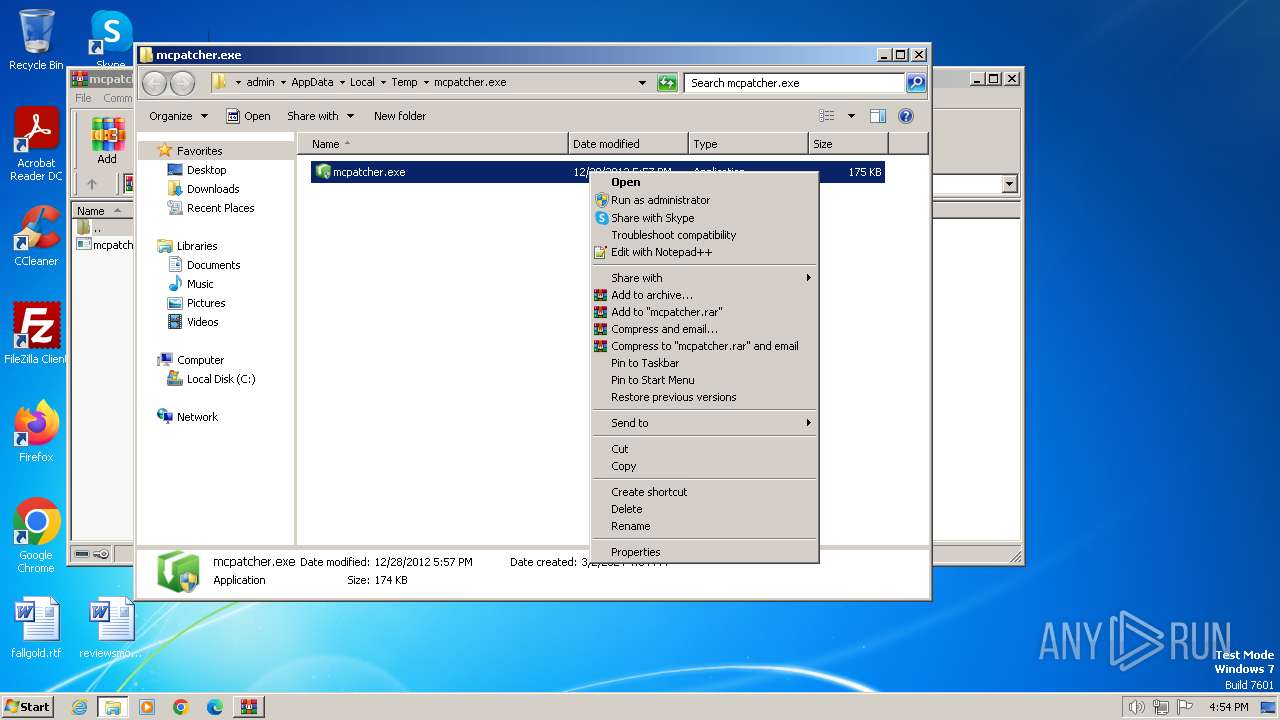
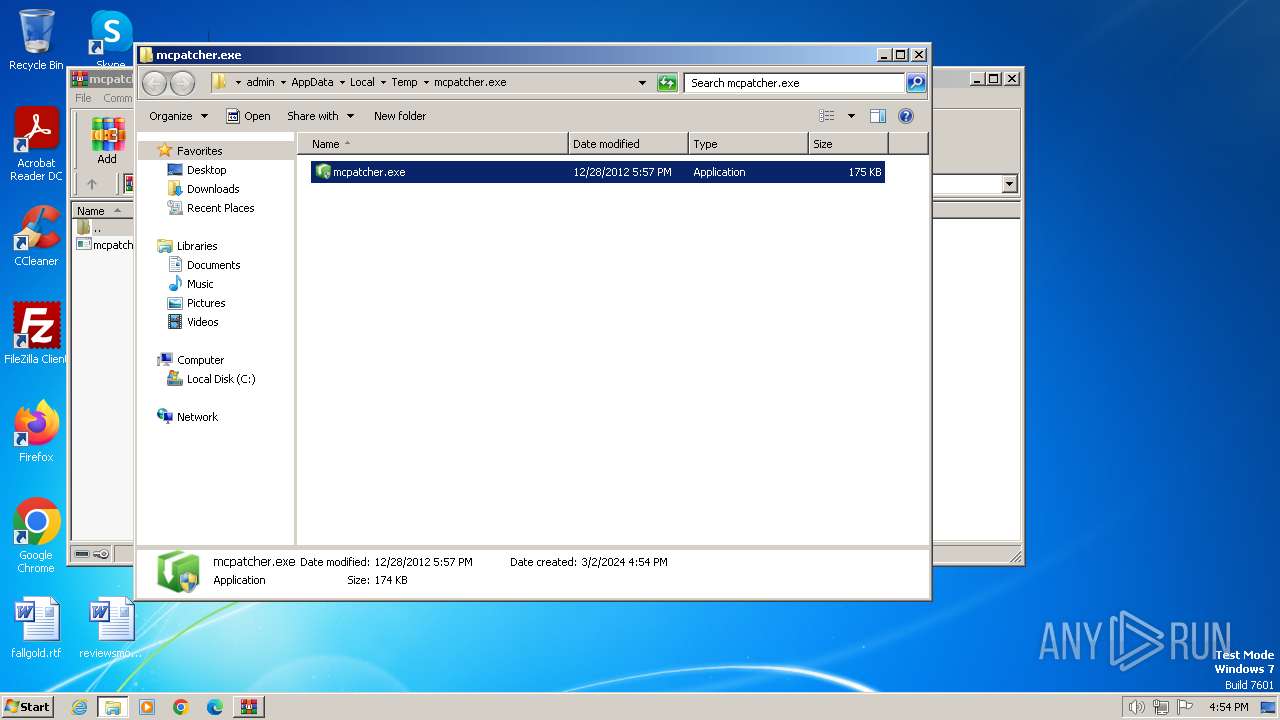
Manual execution by a user
- mcpatcher.exe (PID: 2852)
- mcpatcher.exe (PID: 120)
- mcpatcher.exe (PID: 1656)
Create files in a temporary directory
- mcpatcher.exe (PID: 120)
- mcpatcher.exe (PID: 1656)
Reads the machine GUID from the registry
- northstar.exe (PID: 2120)
- northstar.exe (PID: 1976)
Reads the software policy settings
- northstar.exe (PID: 2120)
- northstar.exe (PID: 1976)
Reads Environment values
- northstar.exe (PID: 2120)
- northstar.exe (PID: 1976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
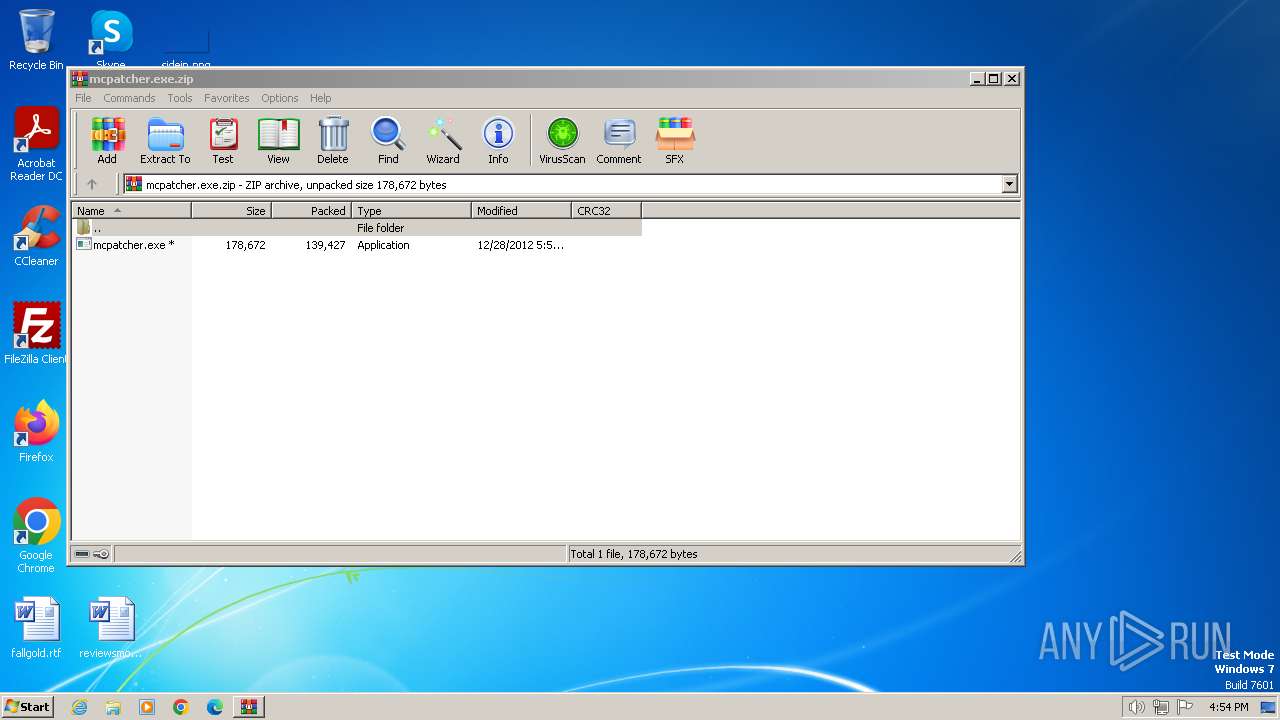
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 819 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2012:12:28 17:57:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 139427 |
| ZipUncompressedSize: | 178672 |
| ZipFileName: | mcpatcher.exe |
Total processes
48
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
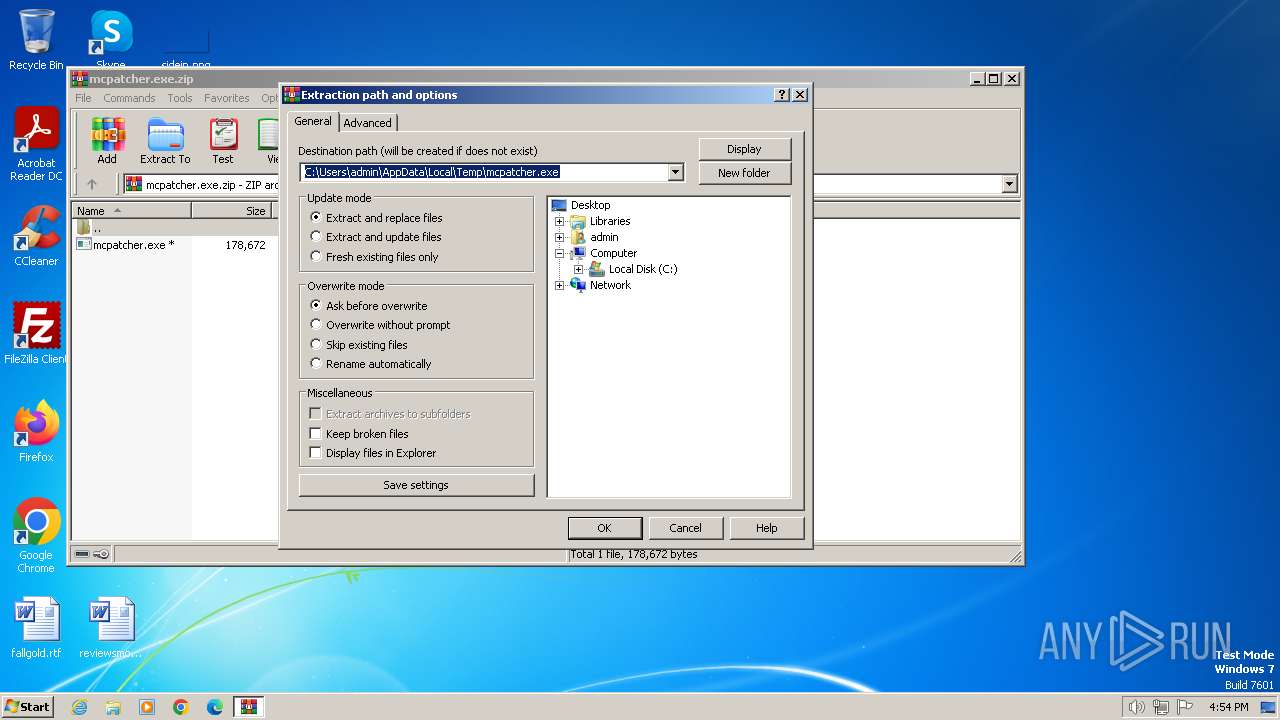
| 120 | "C:\Users\admin\AppData\Local\Temp\mcpatcher.exe\mcpatcher.exe" | C:\Users\admin\AppData\Local\Temp\mcpatcher.exe\mcpatcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: mcpatcher Exit code: 0 Version: 2.2.49.0 Modules
| |||||||||||||||
| 1656 | "C:\Users\admin\AppData\Local\Temp\mcpatcher.exe\mcpatcher.exe" | C:\Users\admin\AppData\Local\Temp\mcpatcher.exe\mcpatcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: mcpatcher Exit code: 0 Version: 2.2.49.0 Modules
| |||||||||||||||
| 1976 | C:\Users\admin\AppData\Local\Temp\nsf7F01.tmp\northstar.exe /u50b892e5-d96c-476b-834e-555c5bc06f2f /e5174922 /dT201212281757 | C:\Users\admin\AppData\Local\Temp\nsf7F01.tmp\northstar.exe | — | mcpatcher.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 2.2.49 Modules
| |||||||||||||||
| 2120 | C:\Users\admin\AppData\Local\Temp\nsq6714.tmp\northstar.exe /u50b892e5-d96c-476b-834e-555c5bc06f2f /e5174922 /dT201212281757 | C:\Users\admin\AppData\Local\Temp\nsq6714.tmp\northstar.exe | — | mcpatcher.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 23 Version: 2.2.49 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\mcpatcher.exe\mcpatcher.exe" | C:\Users\admin\AppData\Local\Temp\mcpatcher.exe\mcpatcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: mcpatcher Exit code: 3221226540 Version: 2.2.49.0 Modules
| |||||||||||||||
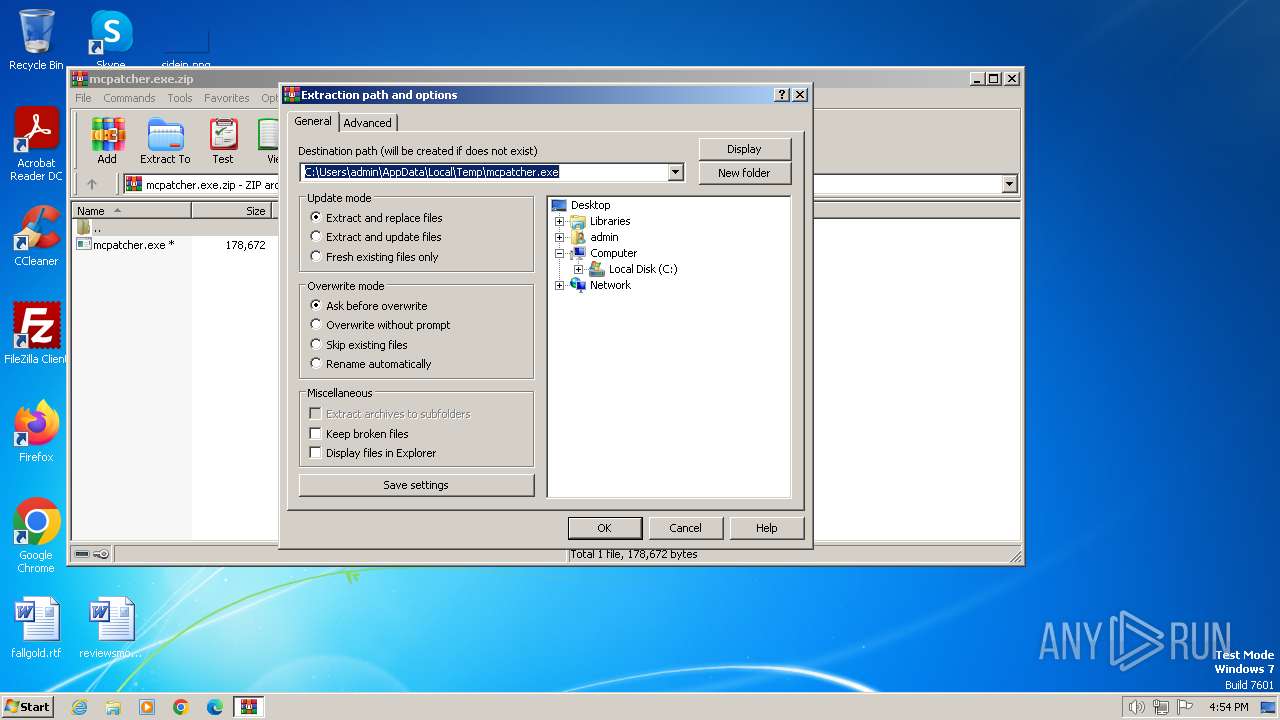
| 4052 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\mcpatcher.exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
15 547
Read events
15 496
Write events
48
Delete events
3
Modification events
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\mcpatcher.exe.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
5
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 120 | mcpatcher.exe | C:\Users\admin\AppData\Local\Temp\nsq6714.tmp\System.dll | executable | |
MD5:5EBC73650256E9C8DDBCDA231DB829A1 | SHA256:1EAA543842DF7795404184E8892A1654B0773DBC9BD8B54C7FDB9E68F4355493 | |||
| 120 | mcpatcher.exe | C:\Users\admin\AppData\Local\Temp\nsq6714.tmp\northstar.exe | executable | |
MD5:A1E2472DB630C7043C2FB486A17300BC | SHA256:0E990E290A6C3B4B3A3AC7495BFC197B698799AE840A06586EB5D5CBE74A1BD7 | |||
| 1656 | mcpatcher.exe | C:\Users\admin\AppData\Local\Temp\nsf7F01.tmp\northstar.exe | executable | |
MD5:A1E2472DB630C7043C2FB486A17300BC | SHA256:0E990E290A6C3B4B3A3AC7495BFC197B698799AE840A06586EB5D5CBE74A1BD7 | |||
| 4052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\mcpatcher.exe\mcpatcher.exe | executable | |
MD5:FEFBE2912C3A7203B24315333D9B63BF | SHA256:D9B8890CE626D1238D2D50536CC7A699347C01EE4D9567C1A0994E7FAD3EC973 | |||
| 1656 | mcpatcher.exe | C:\Users\admin\AppData\Local\Temp\nsf7F01.tmp\System.dll | executable | |
MD5:5EBC73650256E9C8DDBCDA231DB829A1 | SHA256:1EAA543842DF7795404184E8892A1654B0773DBC9BD8B54C7FDB9E68F4355493 | |||
| 120 | mcpatcher.exe | C:\Users\admin\AppData\Local\Temp\nsq6713.tmp | binary | |
MD5:227E587E19681A0A52849BD3B53BD6E7 | SHA256:C8AE03F72636B9D2D0DCE8730770B9F53BF6F6BA5C3D4281345DCE42A8D1AFC9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
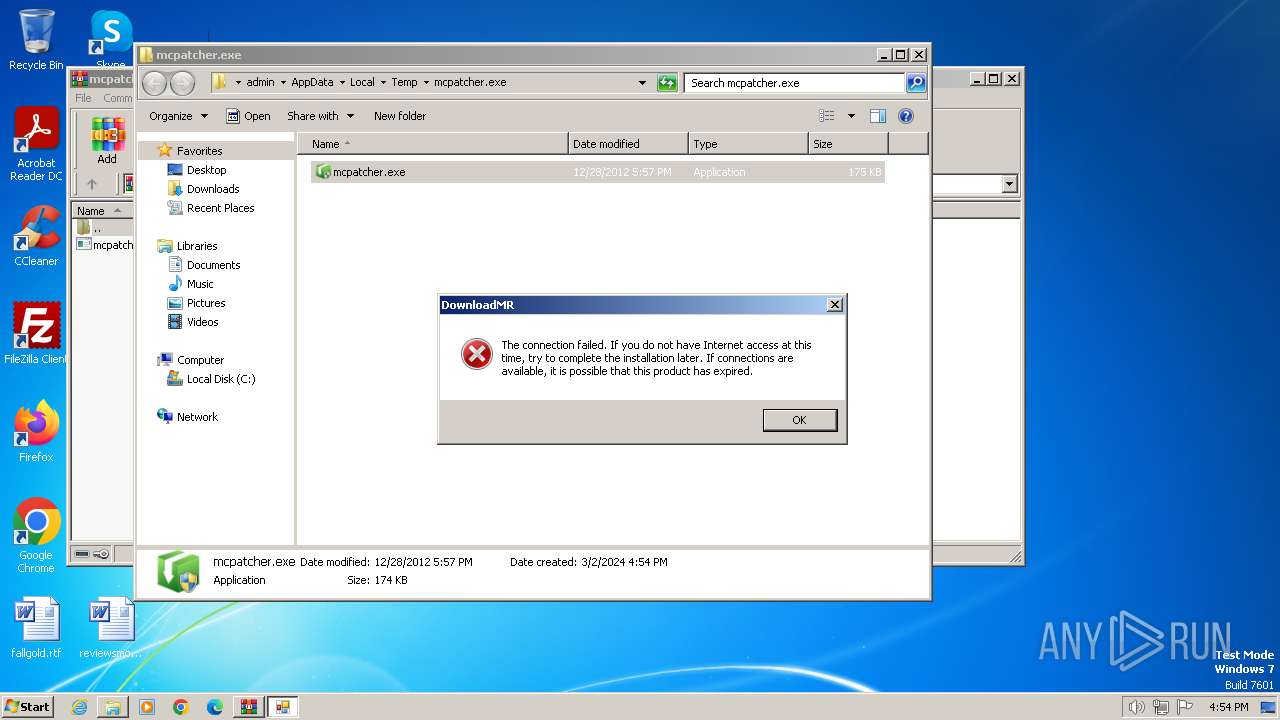
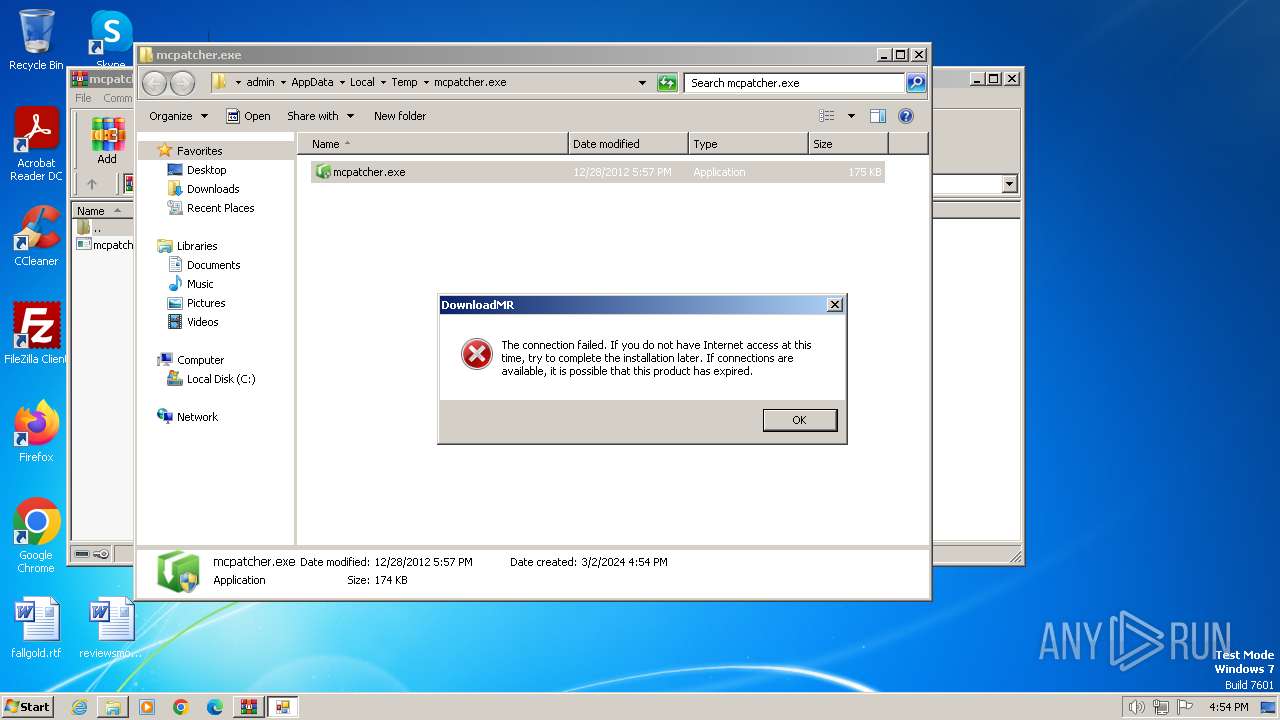
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.downloadmr.com |
| unknown |