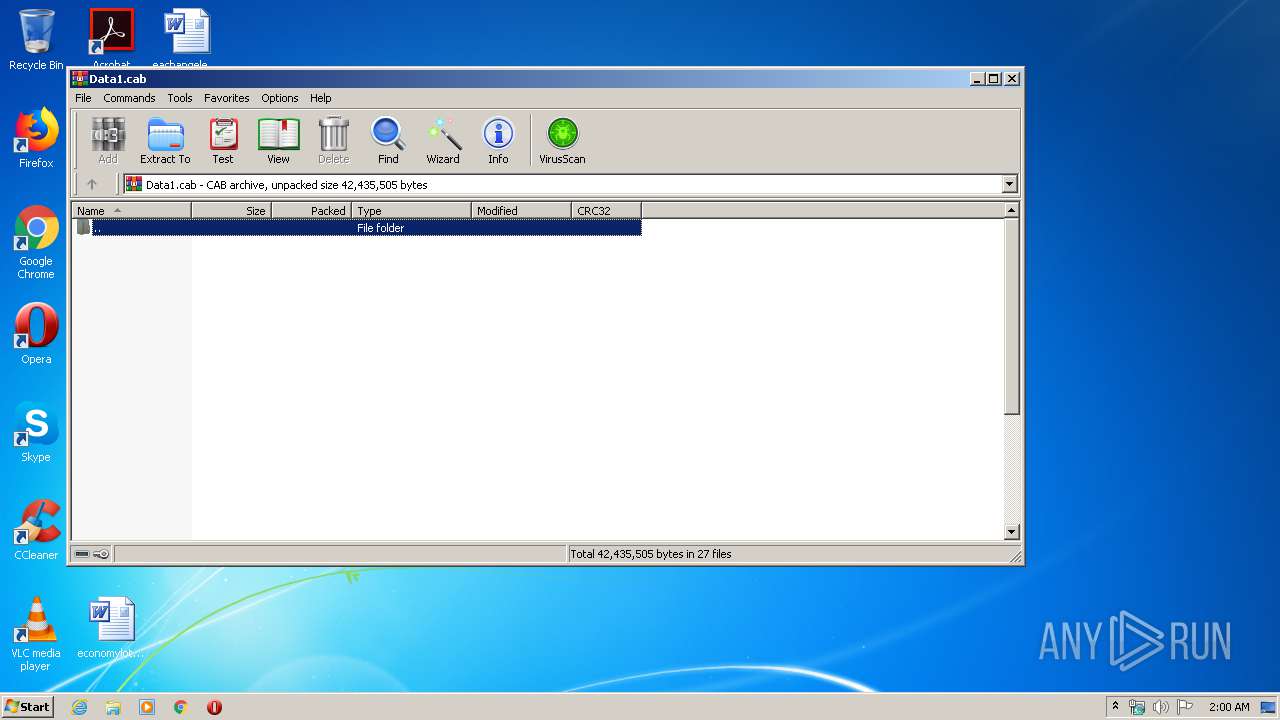
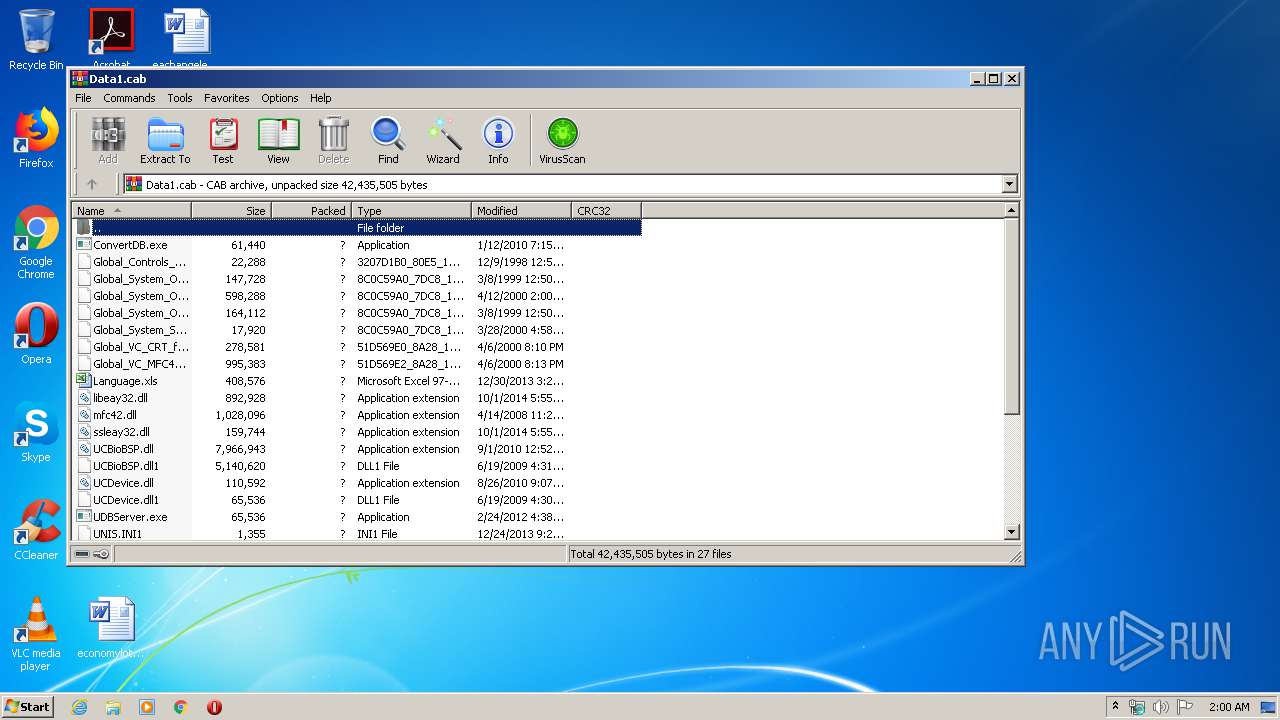
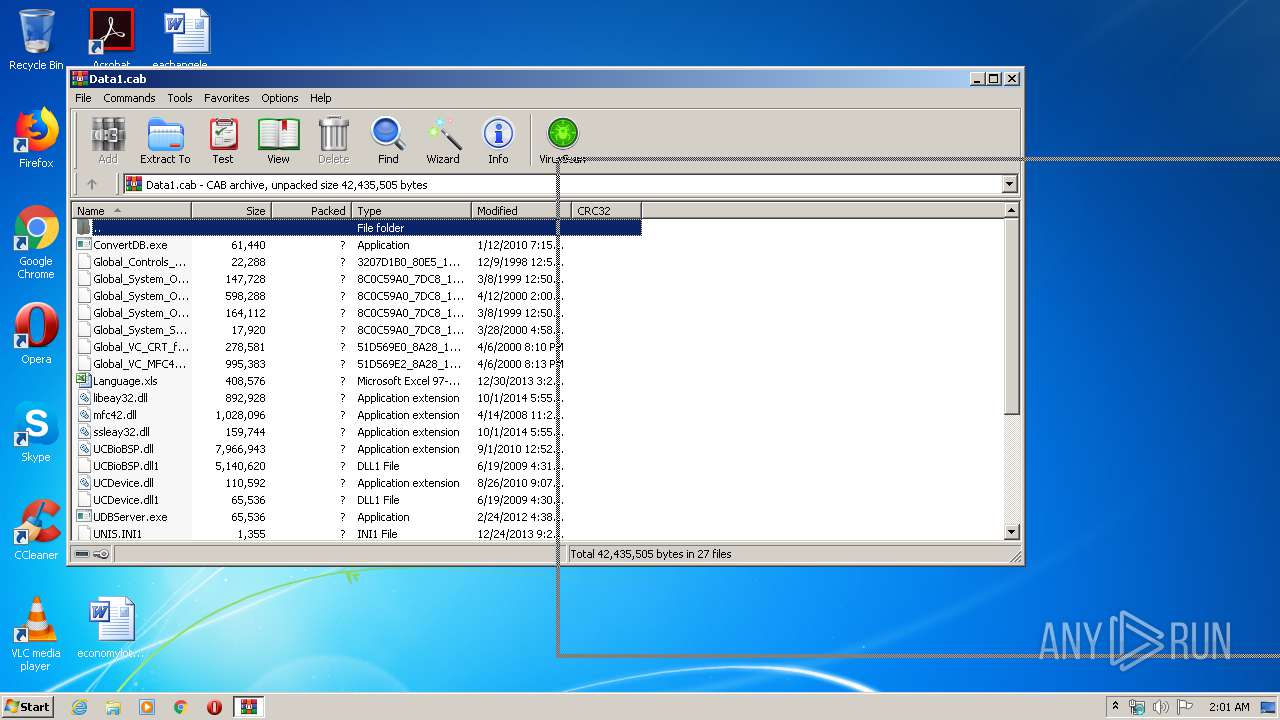
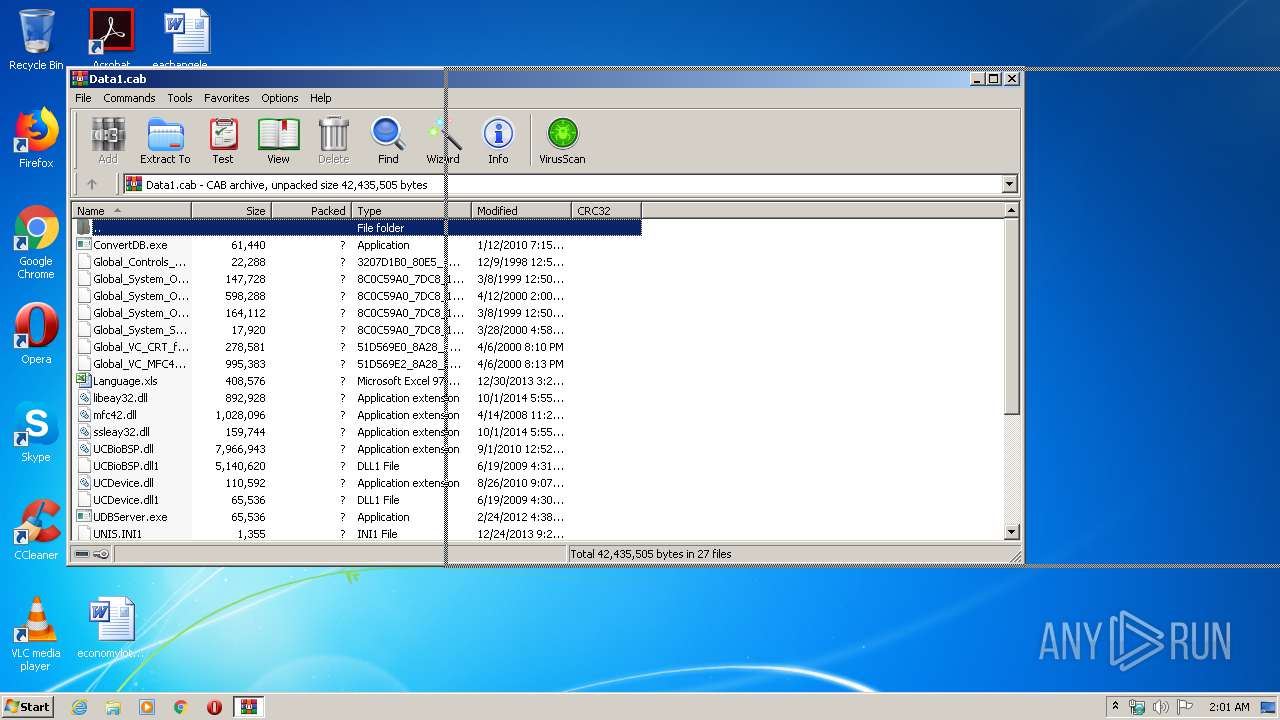
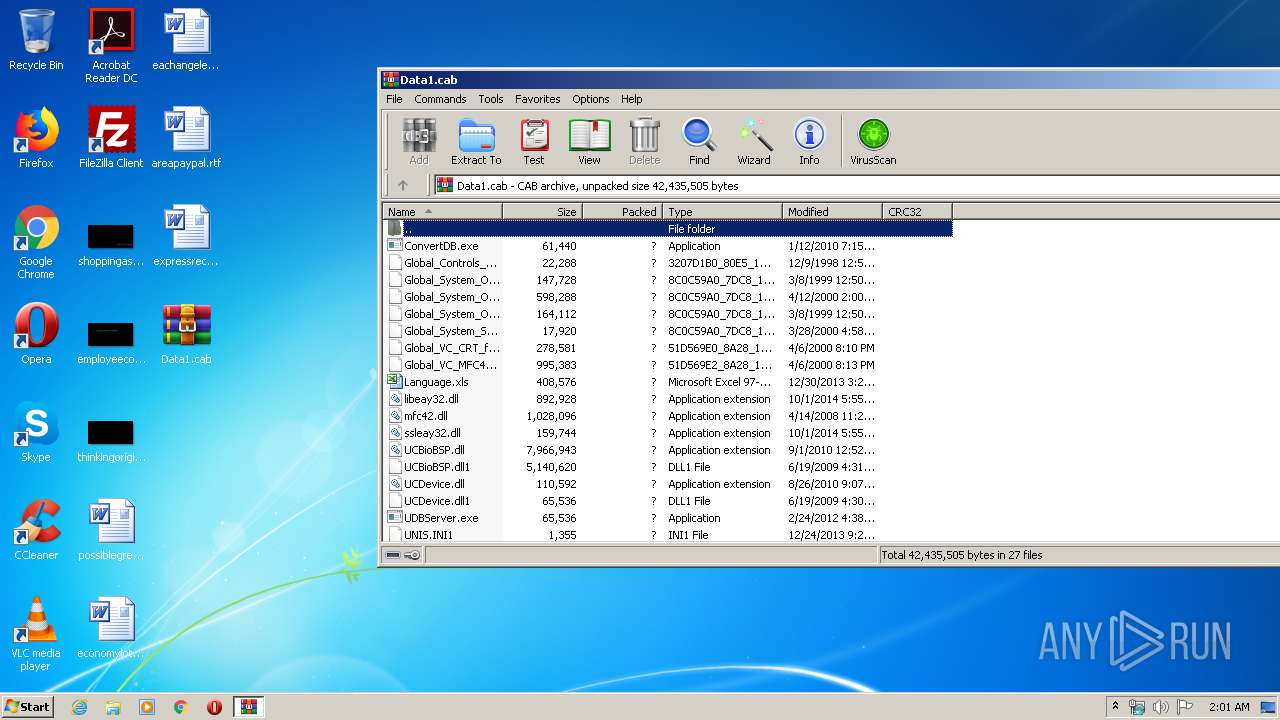
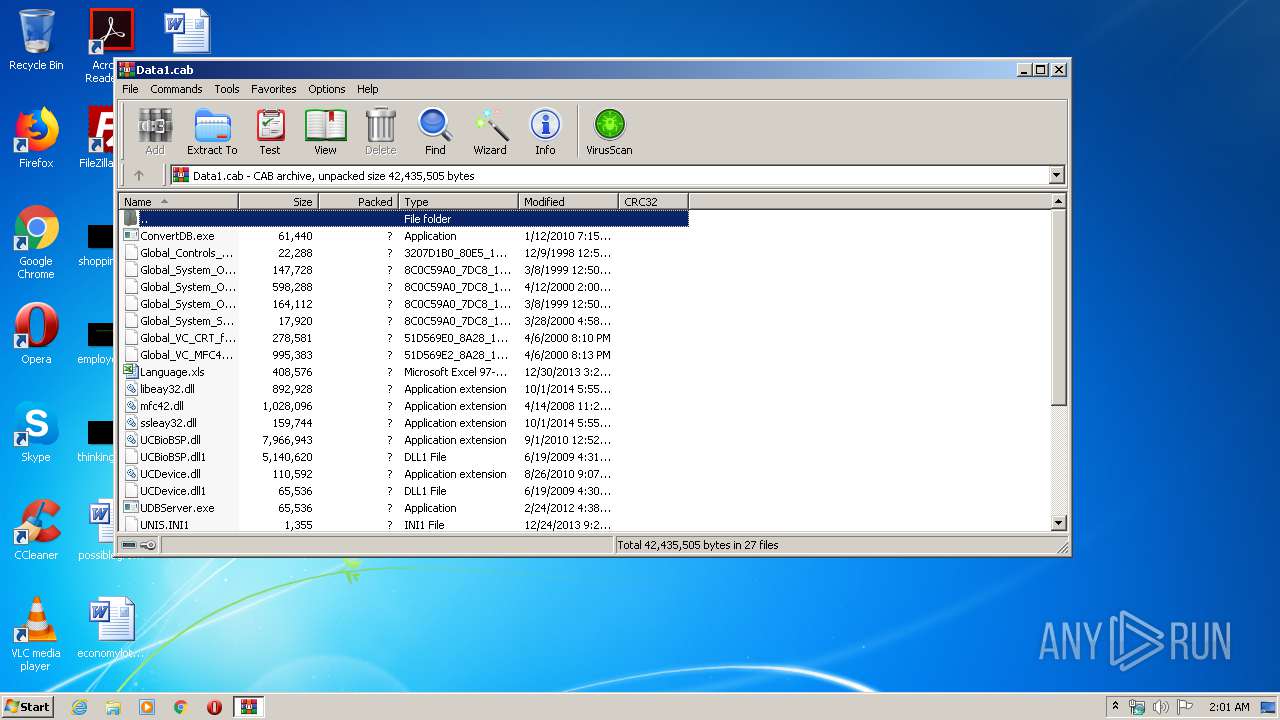
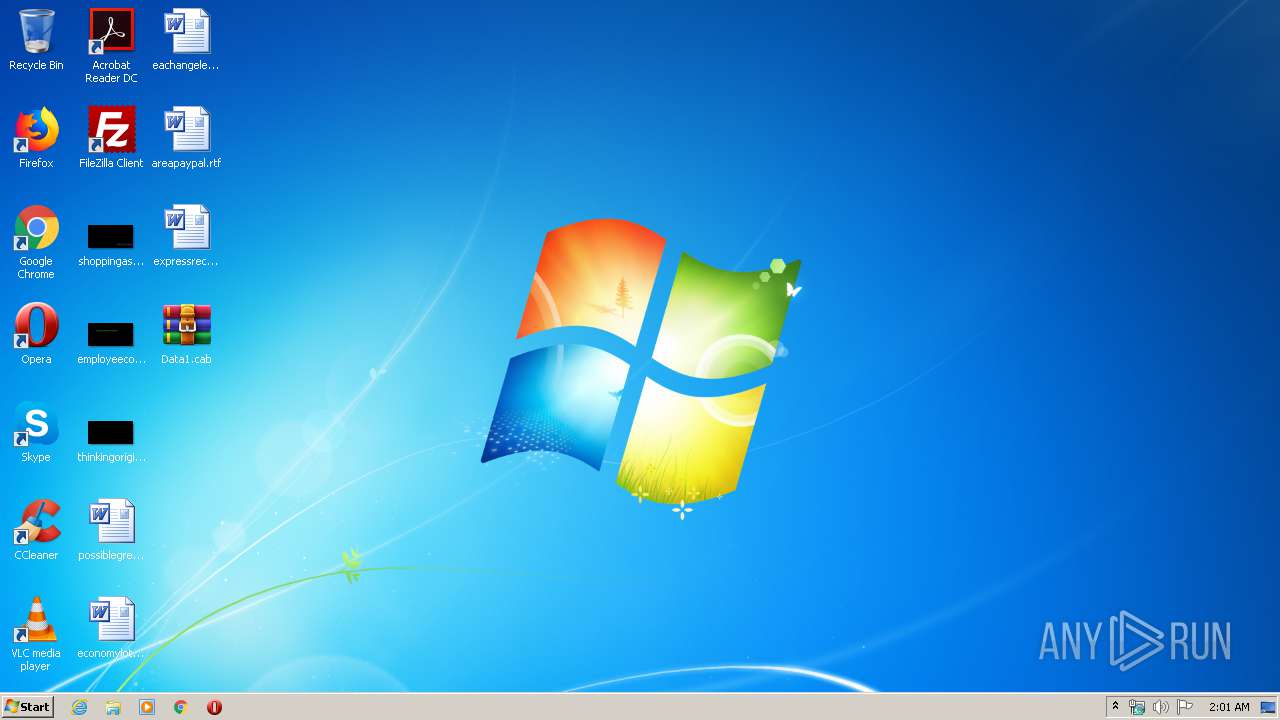
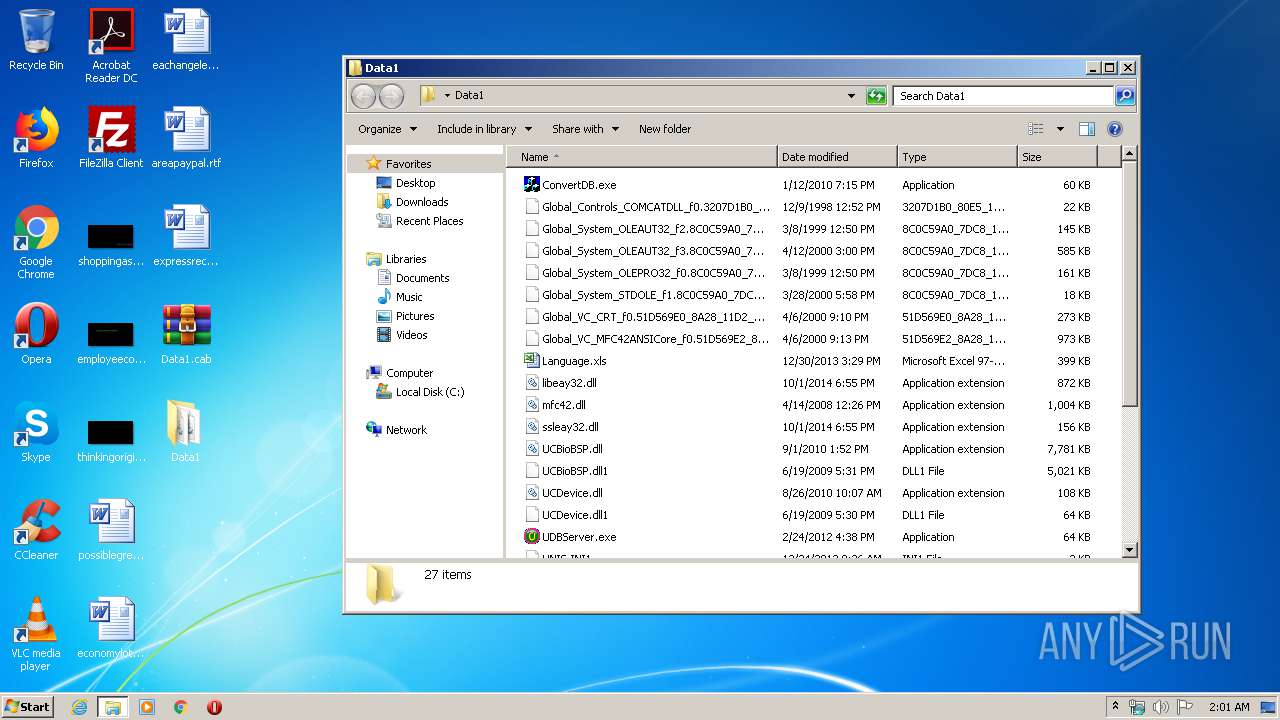
| File name: | Data1.cab |
| Full analysis: | https://app.any.run/tasks/71299ac0-54f5-4735-822a-7929ca21f418 |
| Verdict: | Malicious activity |
| Analysis date: | March 03, 2020, 02:00:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-cab-compressed |
| File info: | Microsoft Cabinet archive data, 9355040 bytes, 27 files |
| MD5: | 02F84FB230A0BAA14014F1C31FAFFE12 |
| SHA1: | 1614EC853B62B0BF4C011579D5AA551D01918793 |
| SHA256: | FBDB5F090AAD92FE825F165032EEE60FB1B0B245556B3EB16F3DF937C4C0E1E4 |
| SSDEEP: | 196608:mMfZDBSsSulYLWb/+9nqDkV9lyRqouxrVEzgjCYoBoeosak:miZTOqDknlcqZrizg2Zoeohk |
MALICIOUS
Application was dropped or rewritten from another process
- UWorkServer.exe (PID: 2236)
- UNIS_Access.exe (PID: 3840)
- wmPlayer.exe (PID: 3800)
- wmPlayer.exe (PID: 3440)
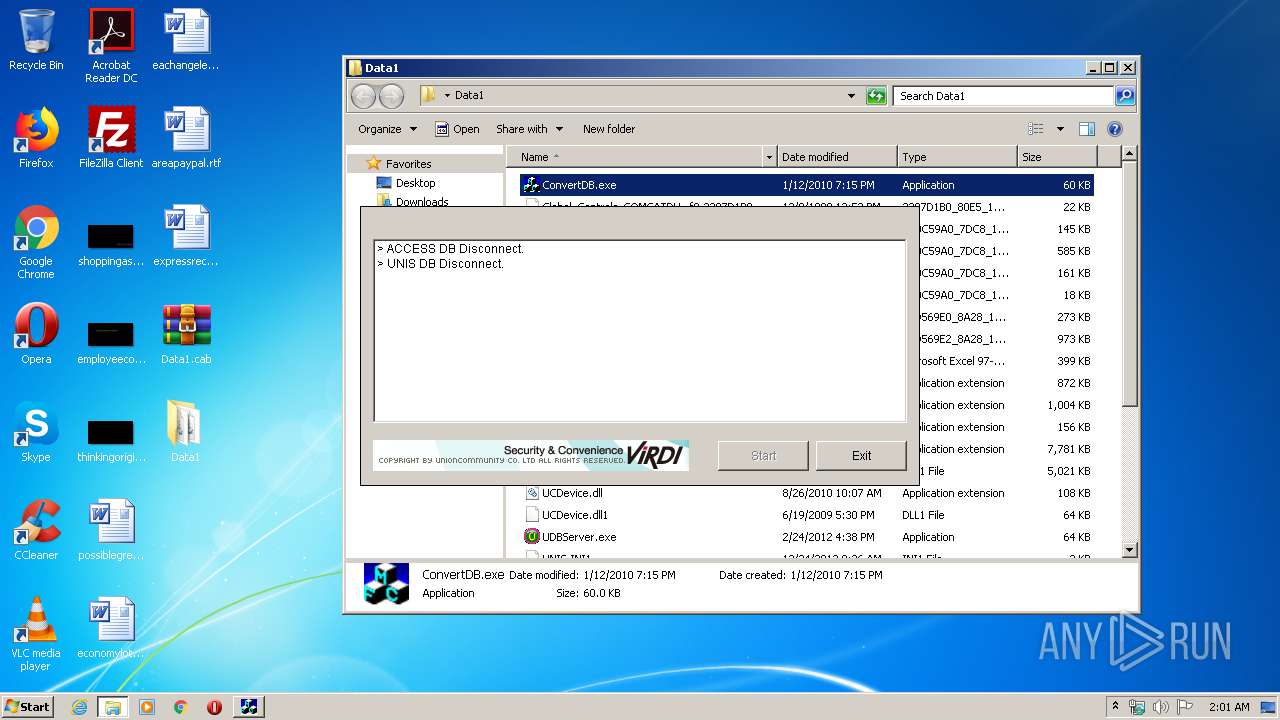
- ConvertDB.exe (PID: 3556)
- UDBServer.exe (PID: 2564)
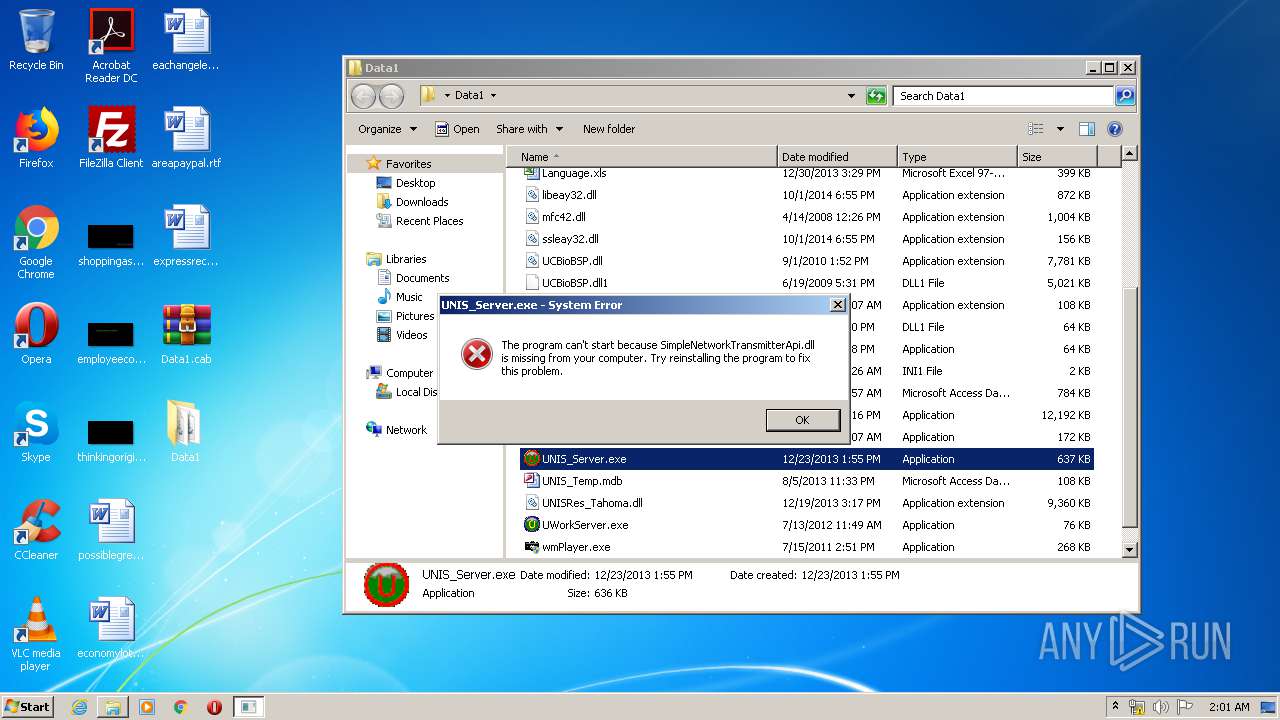
- UNIS_Server.exe (PID: 4056)
- UDBServer.exe (PID: 3144)
- UWorkServer.exe (PID: 1092)
- UNIS_Access.exe (PID: 2052)
Loads dropped or rewritten executable
- UWorkServer.exe (PID: 2236)
- ConvertDB.exe (PID: 3556)
- SearchProtocolHost.exe (PID: 3548)
- UDBServer.exe (PID: 2564)
- UWorkServer.exe (PID: 1092)
- explorer.exe (PID: 372)
- UDBServer.exe (PID: 3144)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 372)
- wmplayer.exe (PID: 536)
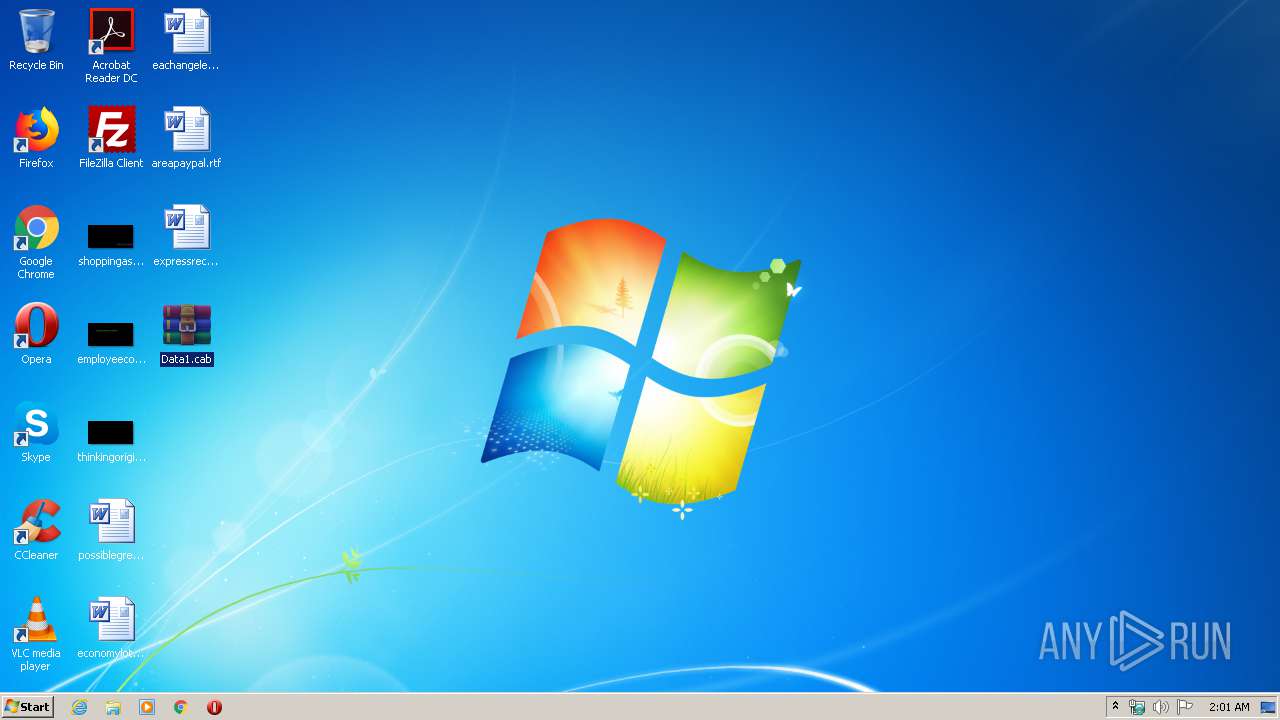
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2436)
Reads Internet Cache Settings
- wmplayer.exe (PID: 536)
INFO
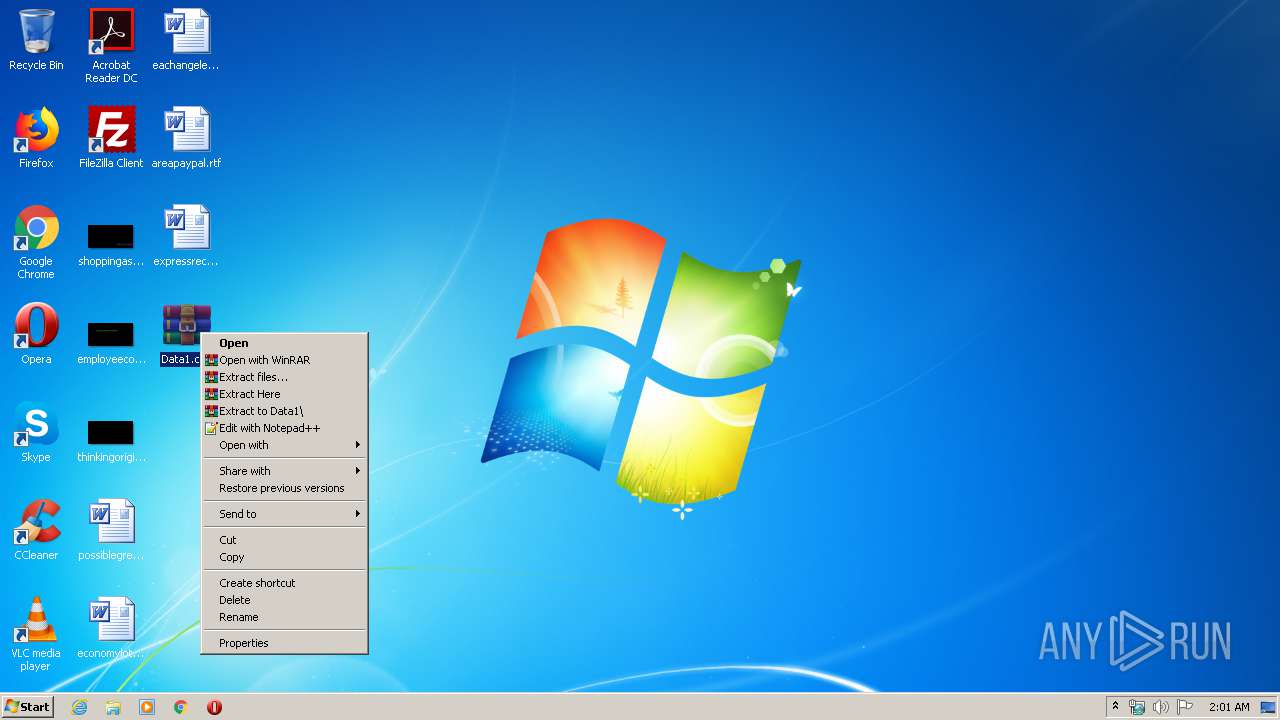
Manual execution by user
- WinRAR.exe (PID: 2436)
- ConvertDB.exe (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .cab | | | Microsoft Cabinet Archive (100) |
|---|
Total processes
58
Monitored processes
15
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
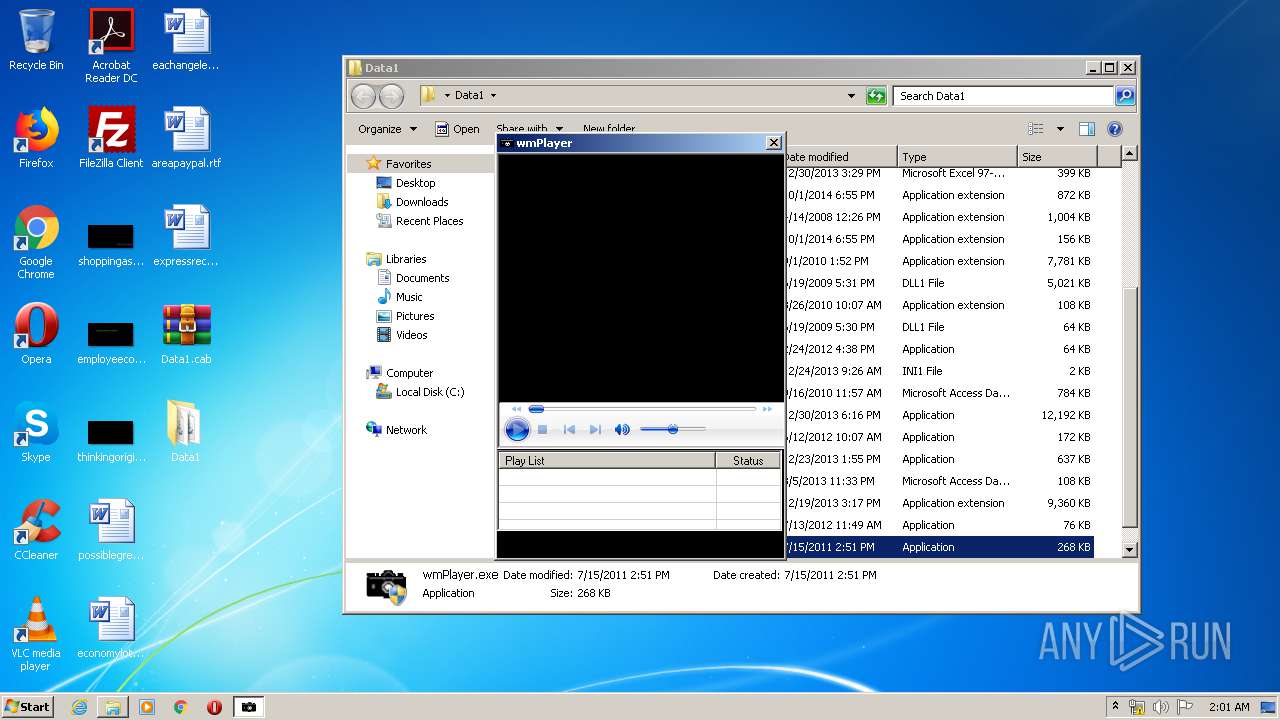
| 536 | "C:\Program Files\Windows Media Player\wmplayer.exe" /SkipFUE /RemoteOCXLaunch | C:\Program Files\Windows Media Player\wmplayer.exe | wmPlayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Player Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
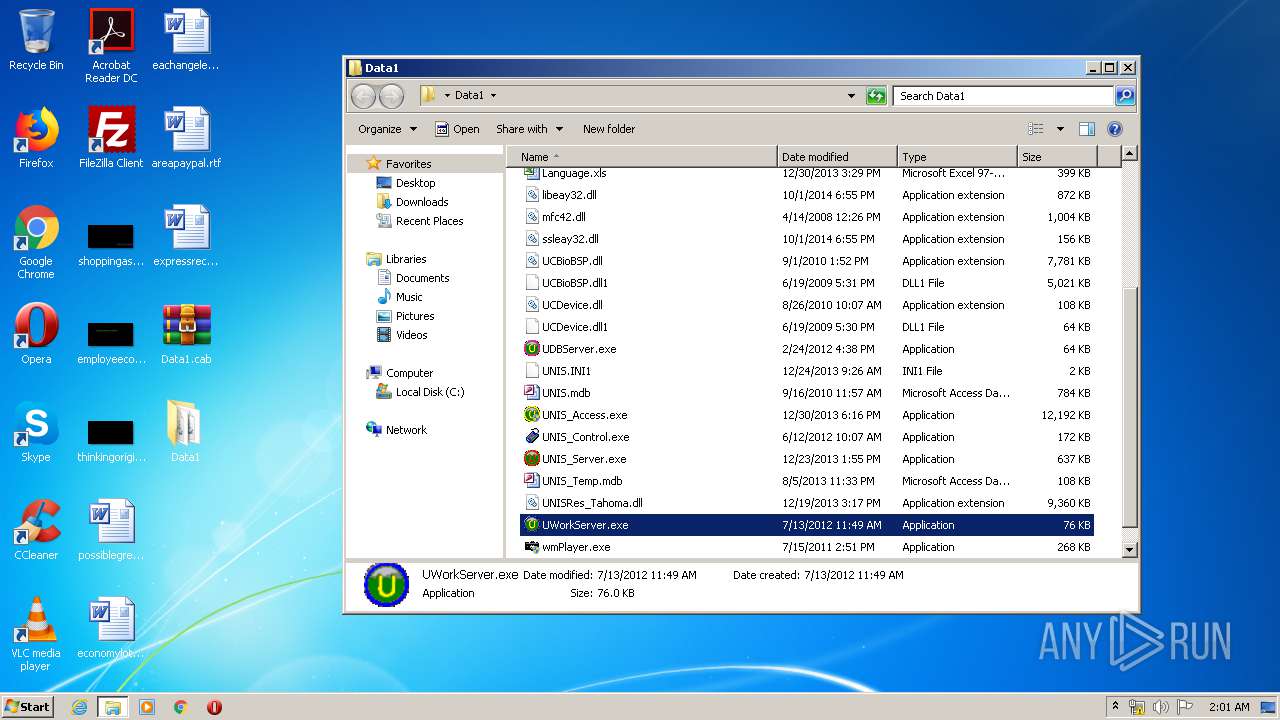
| 1092 | "C:\Users\admin\Desktop\Data1\UWorkServer.exe" | C:\Users\admin\Desktop\Data1\UWorkServer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: UWorkServer MFC for UNIS Exit code: 0 Version: 2, 7, 8, 0 Modules
| |||||||||||||||
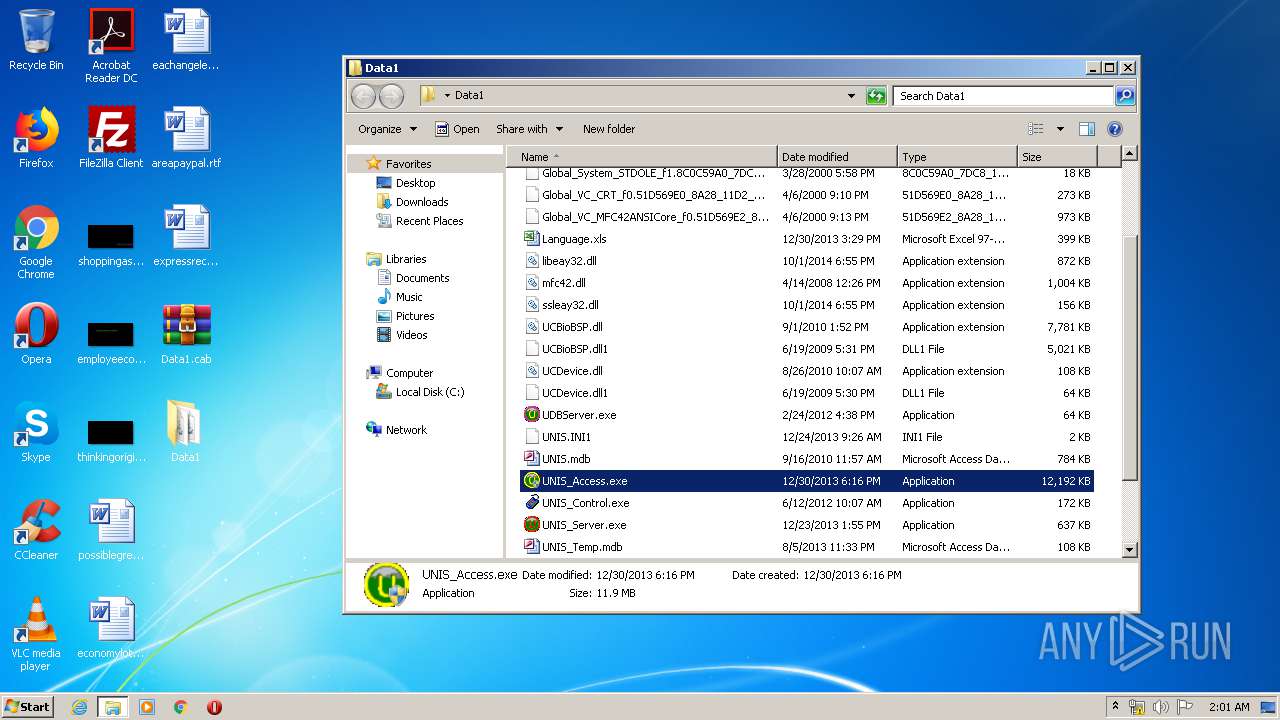
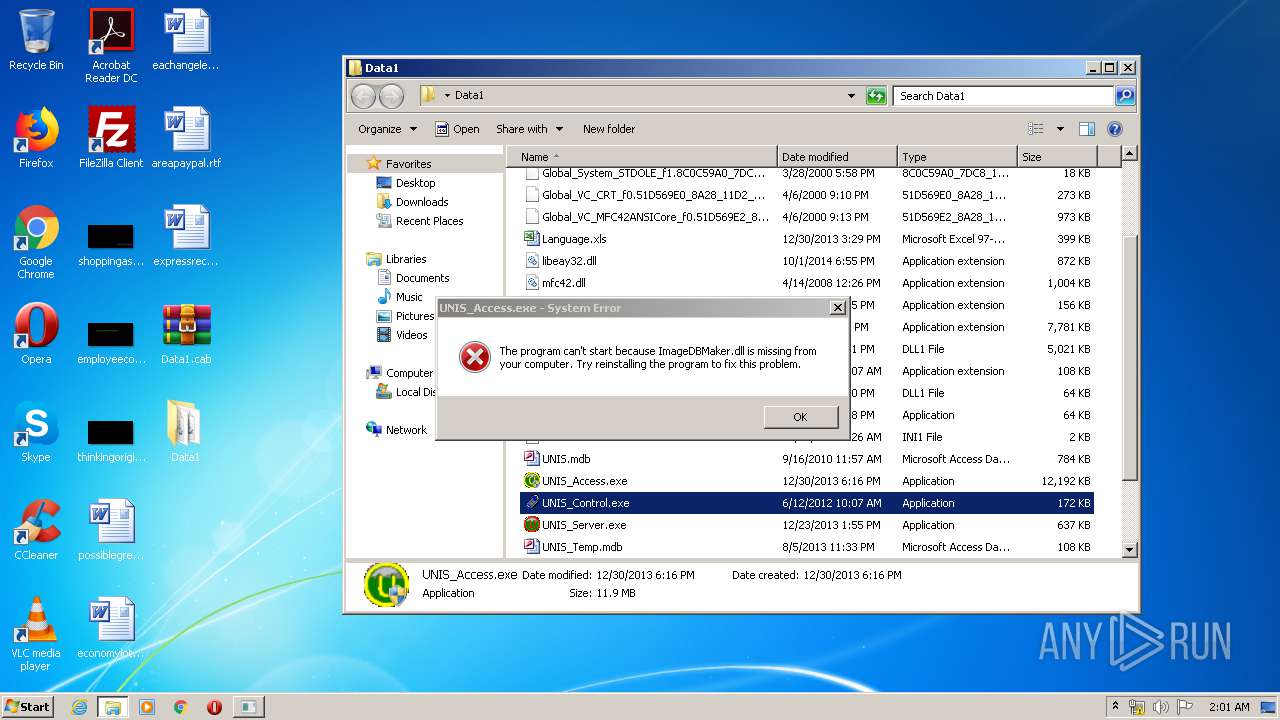
| 2052 | "C:\Users\admin\Desktop\Data1\UNIS_Access.exe" | C:\Users\admin\Desktop\Data1\UNIS_Access.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Remote Manager for UNIS Exit code: 3221226540 Version: 3, 1, 0, 0 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\Desktop\Data1\UWorkServer.exe" | C:\Users\admin\Desktop\Data1\UWorkServer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: UWorkServer MFC for UNIS Exit code: 0 Version: 2, 7, 8, 0 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Data1.cab" C:\Users\admin\Desktop\Data1\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2564 | "C:\Users\admin\Desktop\Data1\UDBServer.exe" | C:\Users\admin\Desktop\Data1\UDBServer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: UDBServer Application Exit code: 0 Version: 2, 5, 3, 0 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\Desktop\Data1\UDBServer.exe" | C:\Users\admin\Desktop\Data1\UDBServer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: UDBServer Application Exit code: 0 Version: 2, 5, 3, 0 Modules
| |||||||||||||||
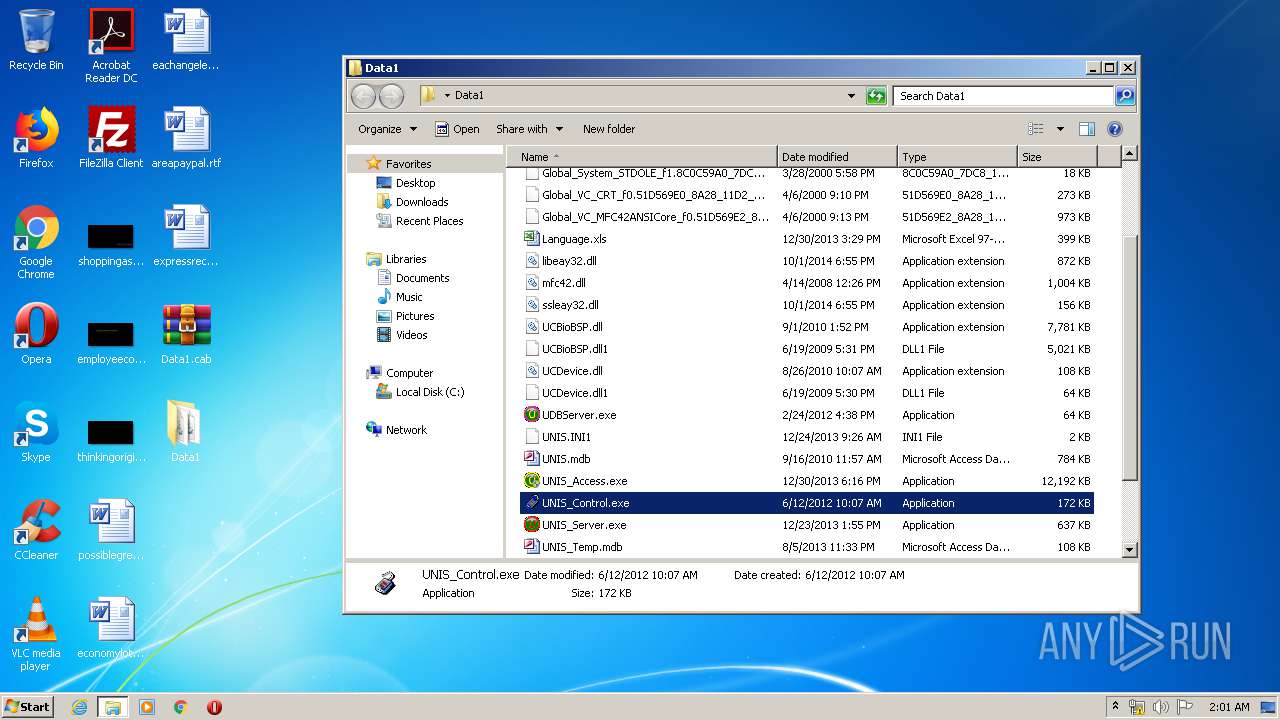
| 3440 | "C:\Users\admin\Desktop\Data1\wmPlayer.exe" | C:\Users\admin\Desktop\Data1\wmPlayer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: wmPlayer MFC Application Exit code: 2 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 848
Read events
5 576
Write events
270
Delete events
2
Modification events
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Data1.cab | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.cab\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.cab\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
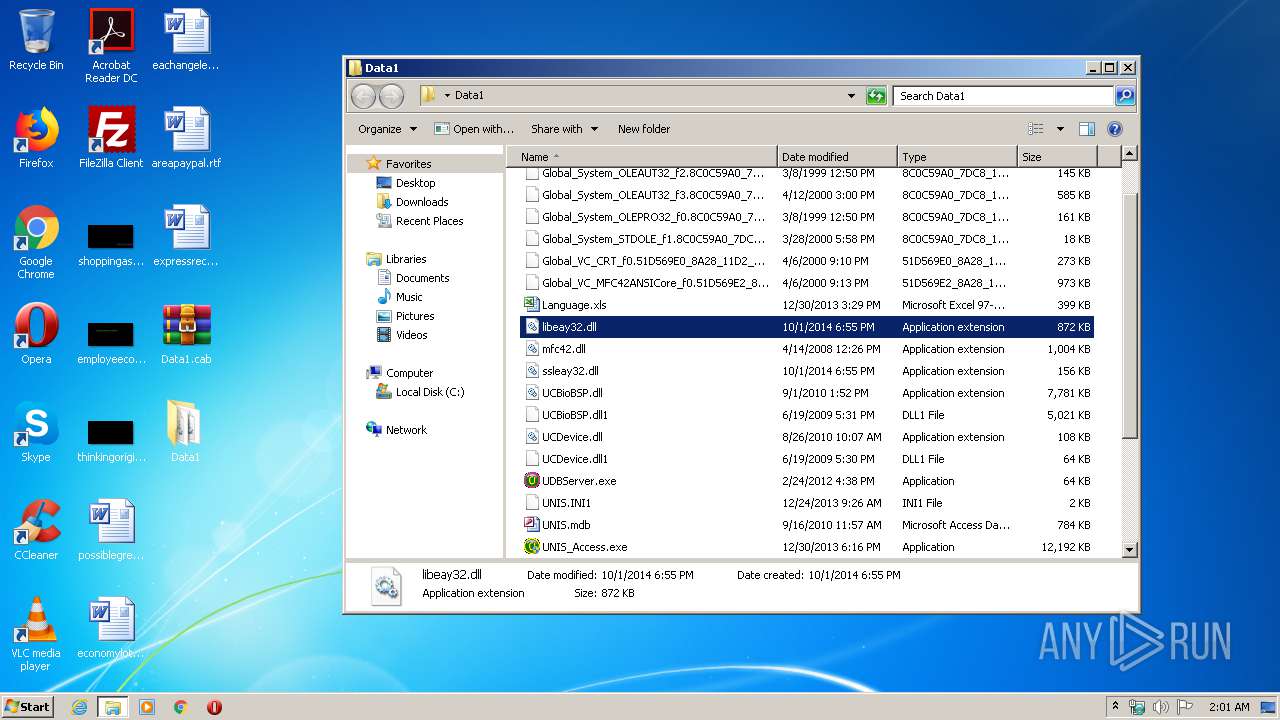
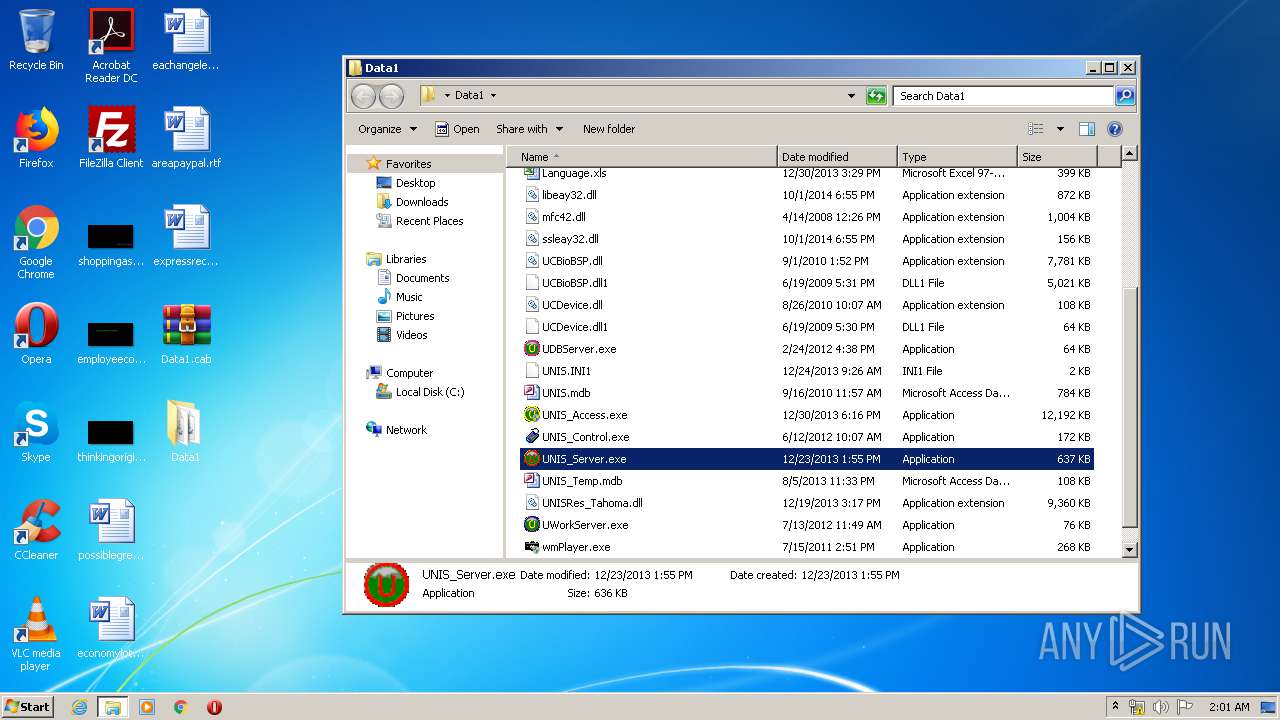
Executable files
23
Suspicious files
5
Text files
11
Unknown types
5
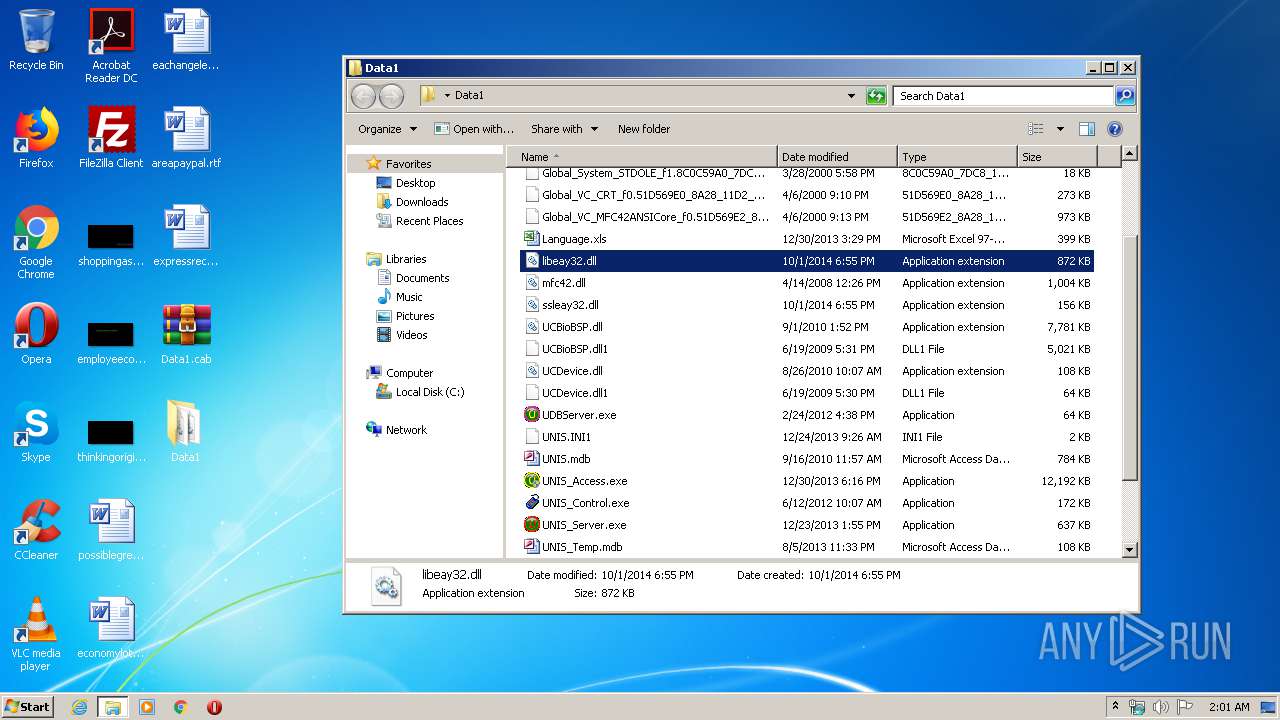
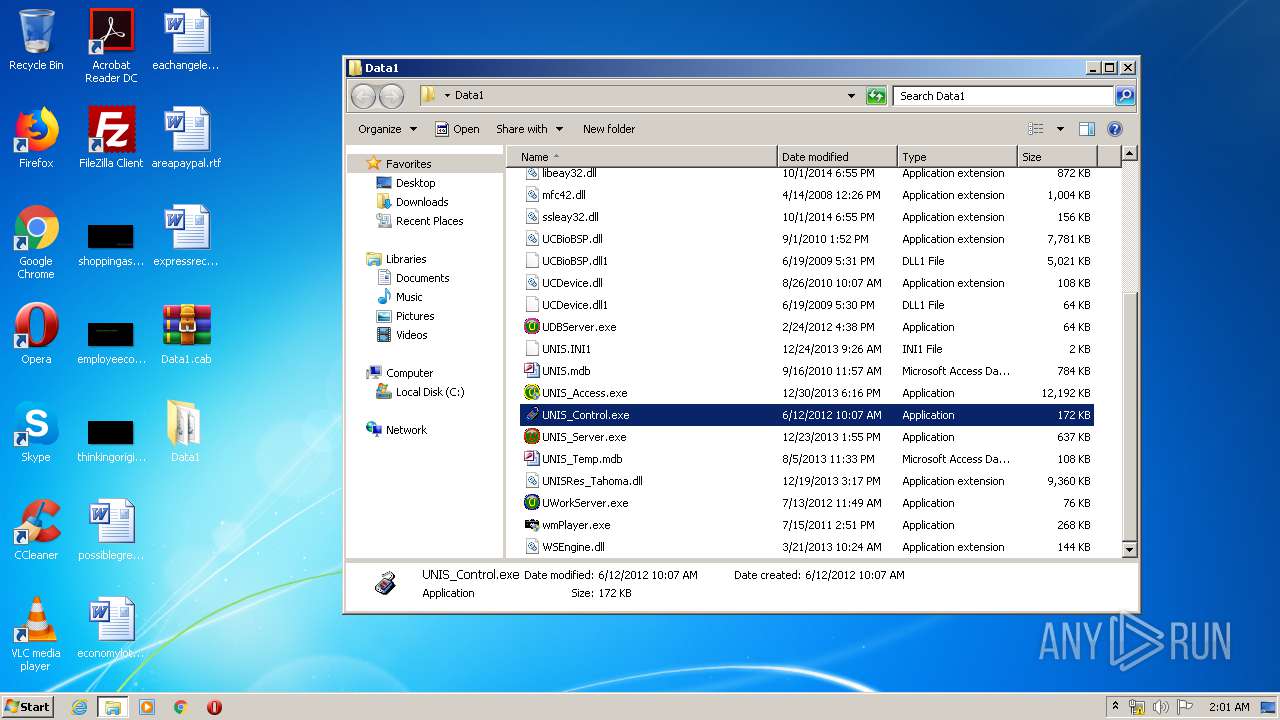
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Data1.cab.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\Data1\UDBServer.exe | executable | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\Data1\WSEngine.dll | executable | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\Data1\UNIS_Server.exe | executable | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\Data1\UWorkServer.exe | executable | |
MD5:— | SHA256:— | |||
| 372 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
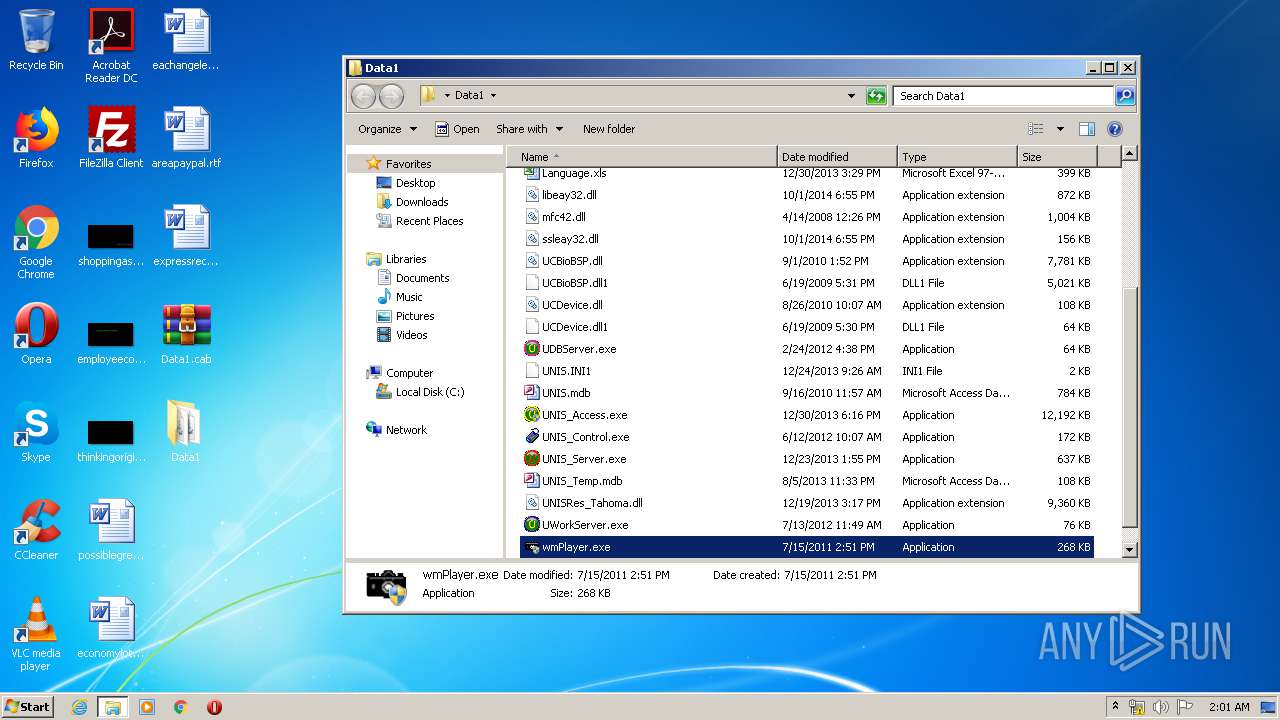
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\Data1\wmPlayer.exe | executable | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\Data1\Language.xls | document | |
MD5:— | SHA256:— | |||
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\Data1\UCDevice.dll | executable | |
MD5:— | SHA256:— | |||
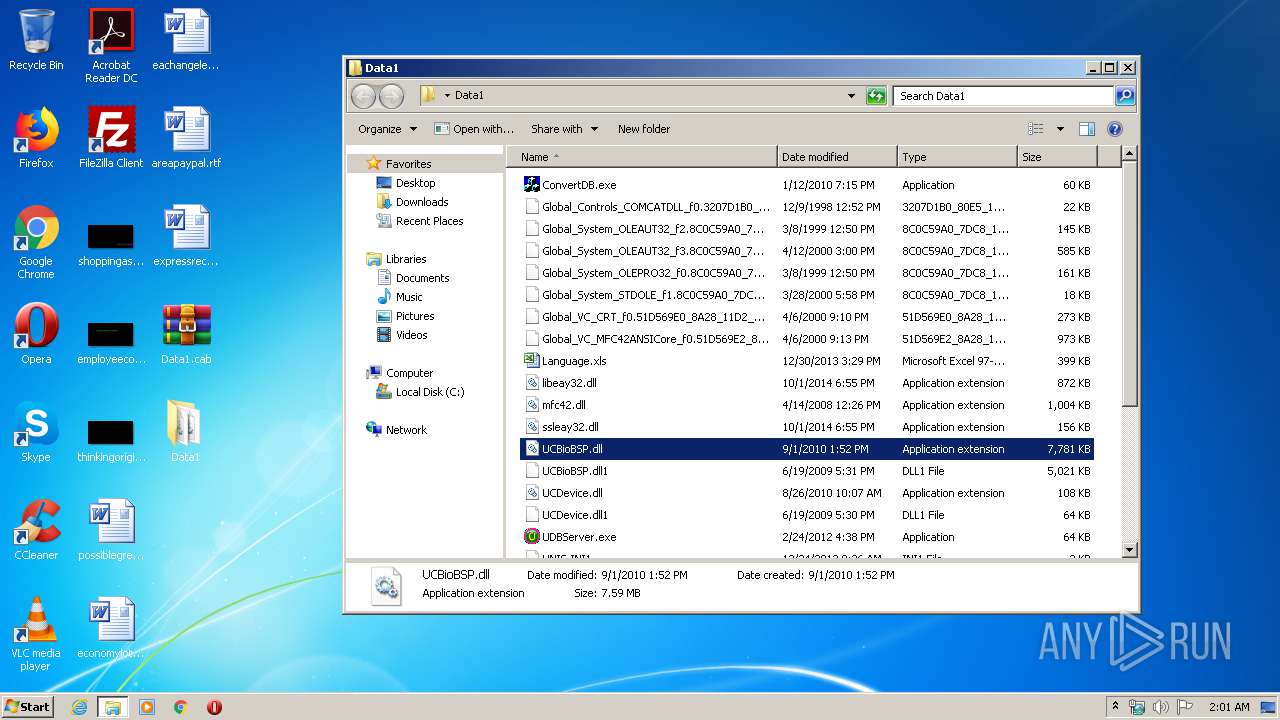
| 2436 | WinRAR.exe | C:\Users\admin\Desktop\Data1\UCBioBSP.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
536 | wmplayer.exe | GET | 302 | 2.16.186.11:80 | http://redir.metaservices.microsoft.com/redir/allservices/?sv=5&locale=409&geoid=f4&version=12.0.7601.17514&userlocale=409 | unknown | — | — | whitelisted |
536 | wmplayer.exe | GET | 200 | 2.16.186.64:80 | http://images.windowsmedia.com/svcswitch/media_guide_16x16.png | unknown | image | 897 b | whitelisted |
536 | wmplayer.exe | GET | 200 | 2.16.186.98:80 | http://onlinestores.metaservices.microsoft.com/bing/bing.xml?locale=409&geoid=f4&version=12.0.7601.17514&userlocale=409 | unknown | text | 523 b | whitelisted |
536 | wmplayer.exe | GET | 200 | 2.16.186.64:80 | http://images.windowsmedia.com/svcswitch/mg4_wmp12_30x30_2.png | unknown | image | 2.00 Kb | whitelisted |
536 | wmplayer.exe | GET | 200 | 2.16.186.98:80 | http://onlinestores.metaservices.microsoft.com/serviceswitching/AllServices.aspx?sv=5&locale=409&geoid=f4&version=12.0.7601.17514&userlocale=409 | unknown | xml | 546 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
536 | wmplayer.exe | 2.16.186.11:80 | redir.metaservices.microsoft.com | Akamai International B.V. | — | whitelisted |
536 | wmplayer.exe | 2.16.186.98:80 | onlinestores.metaservices.microsoft.com | Akamai International B.V. | — | whitelisted |
536 | wmplayer.exe | 2.16.186.64:80 | images.windowsmedia.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
redir.metaservices.microsoft.com |
| whitelisted |
onlinestores.metaservices.microsoft.com |
| whitelisted |
images.windowsmedia.com |
| whitelisted |