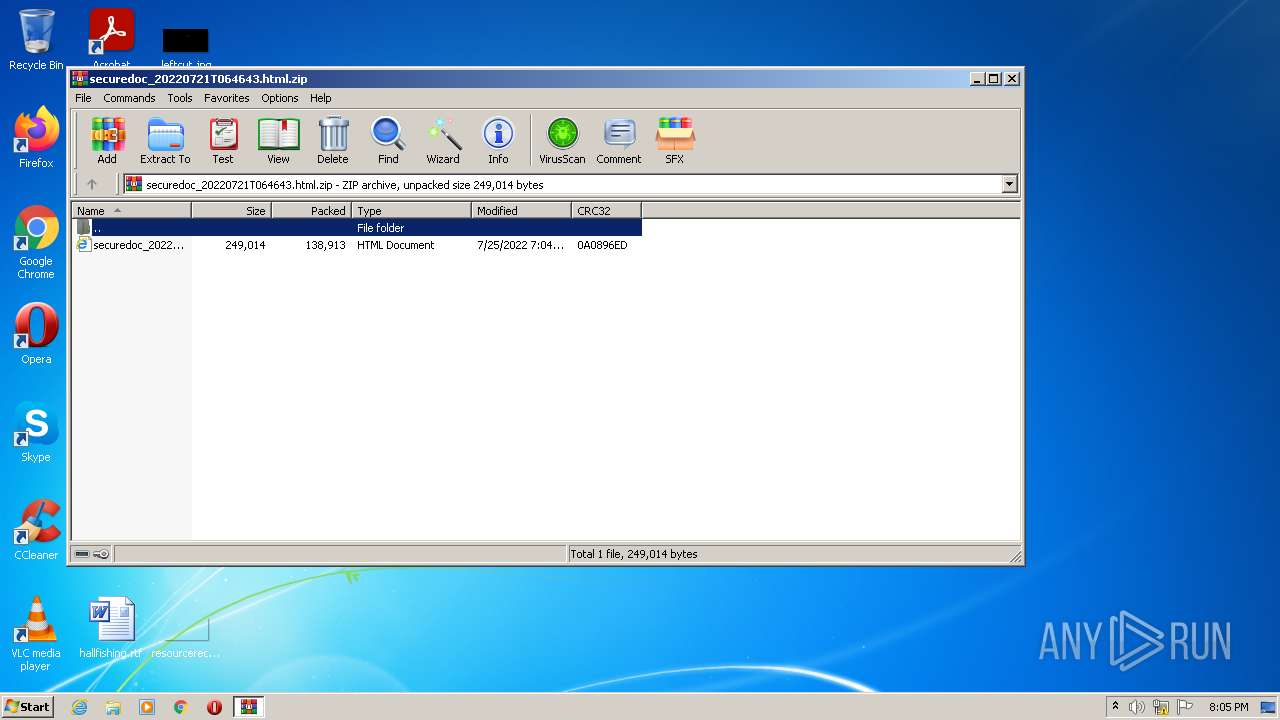
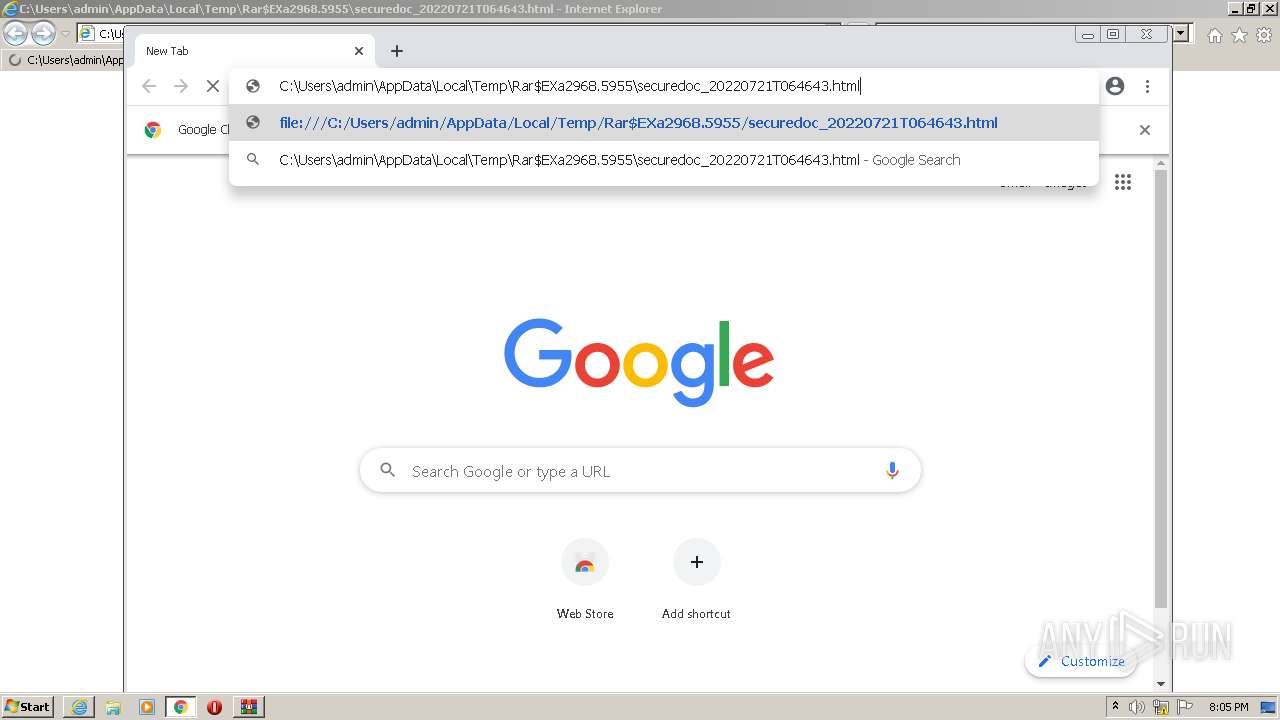
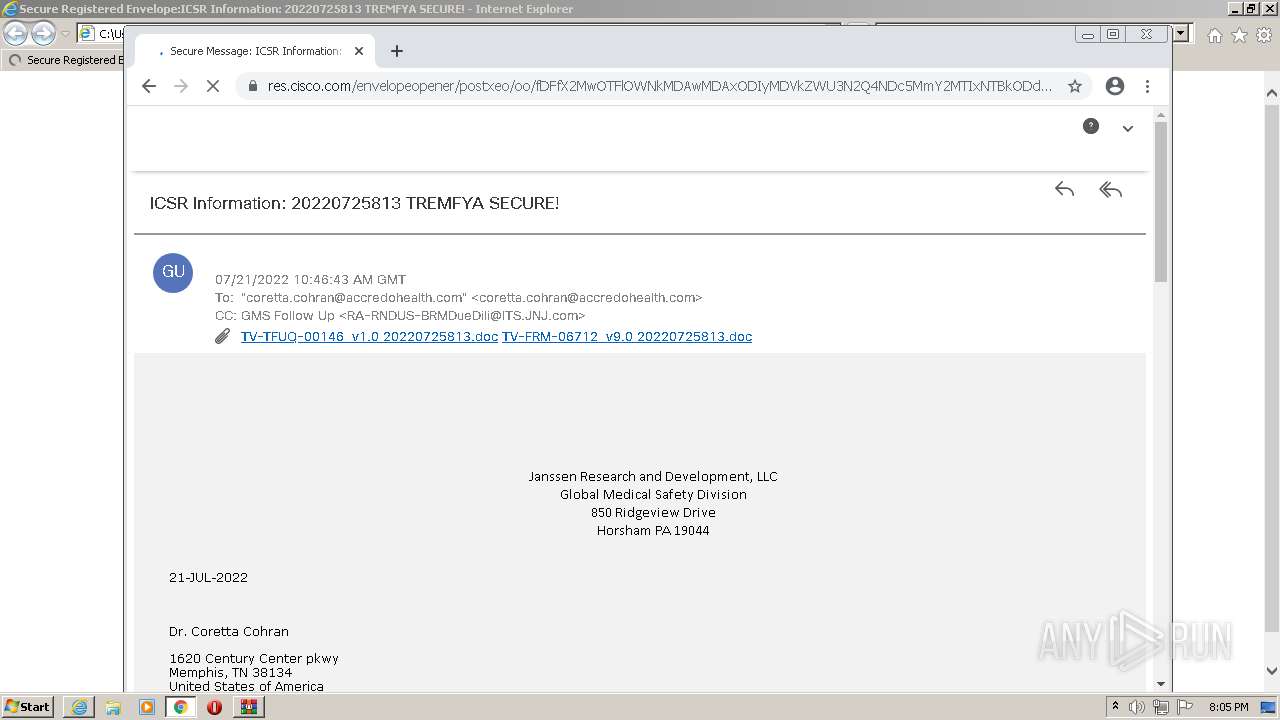
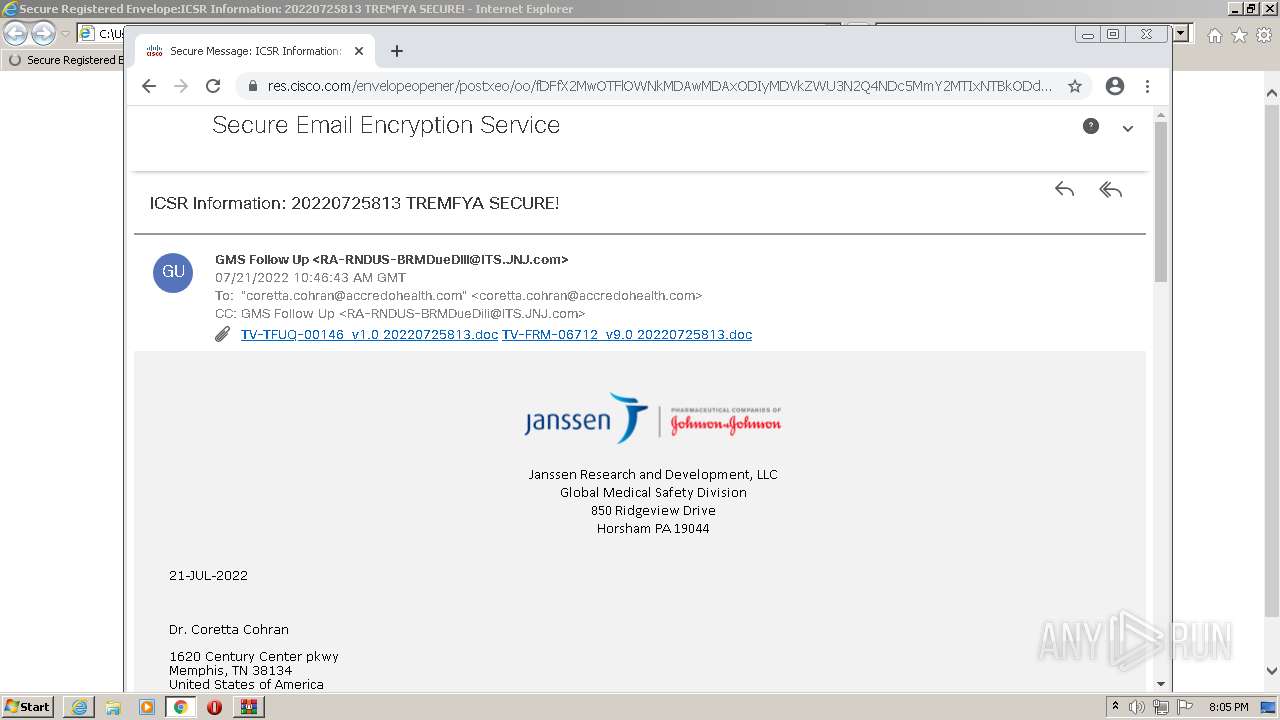
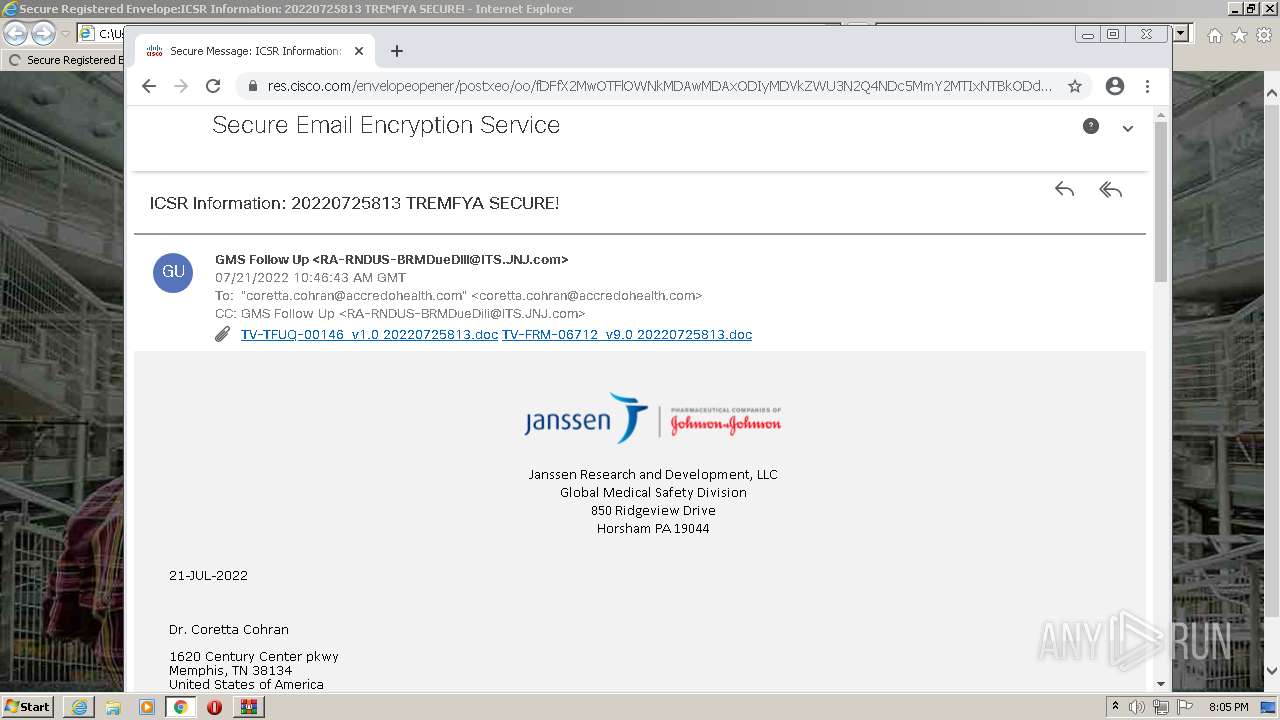
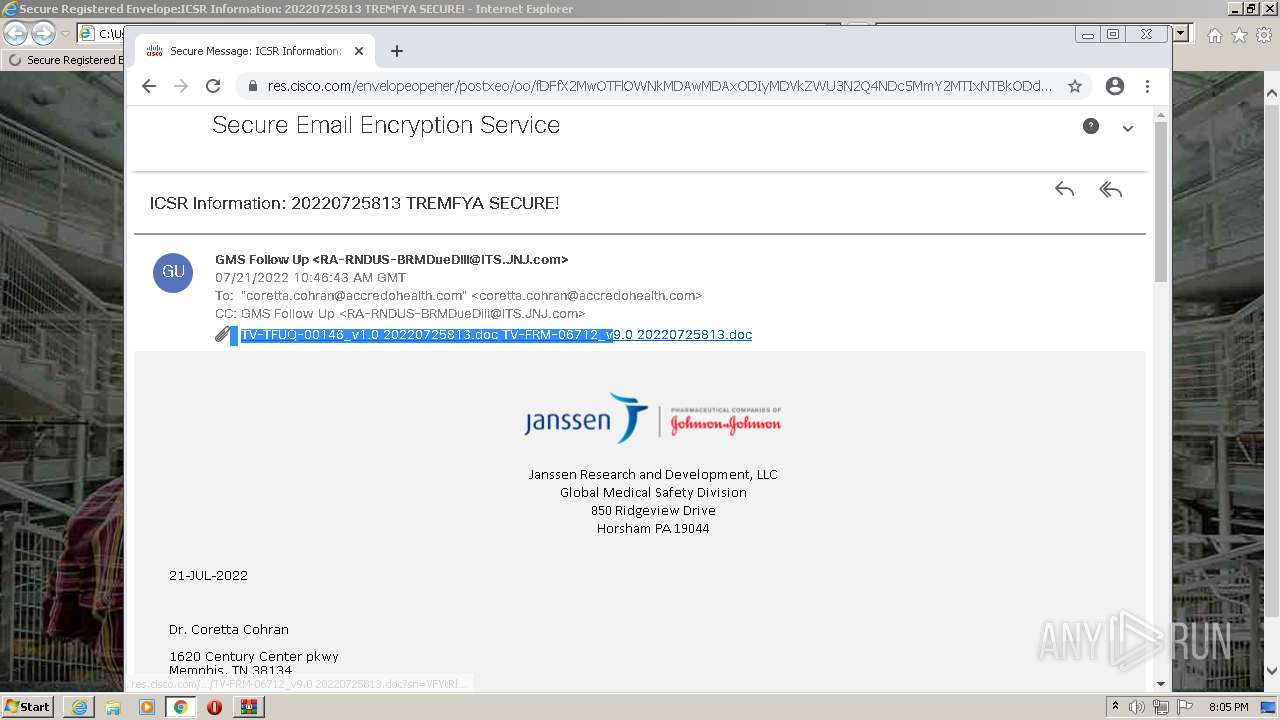
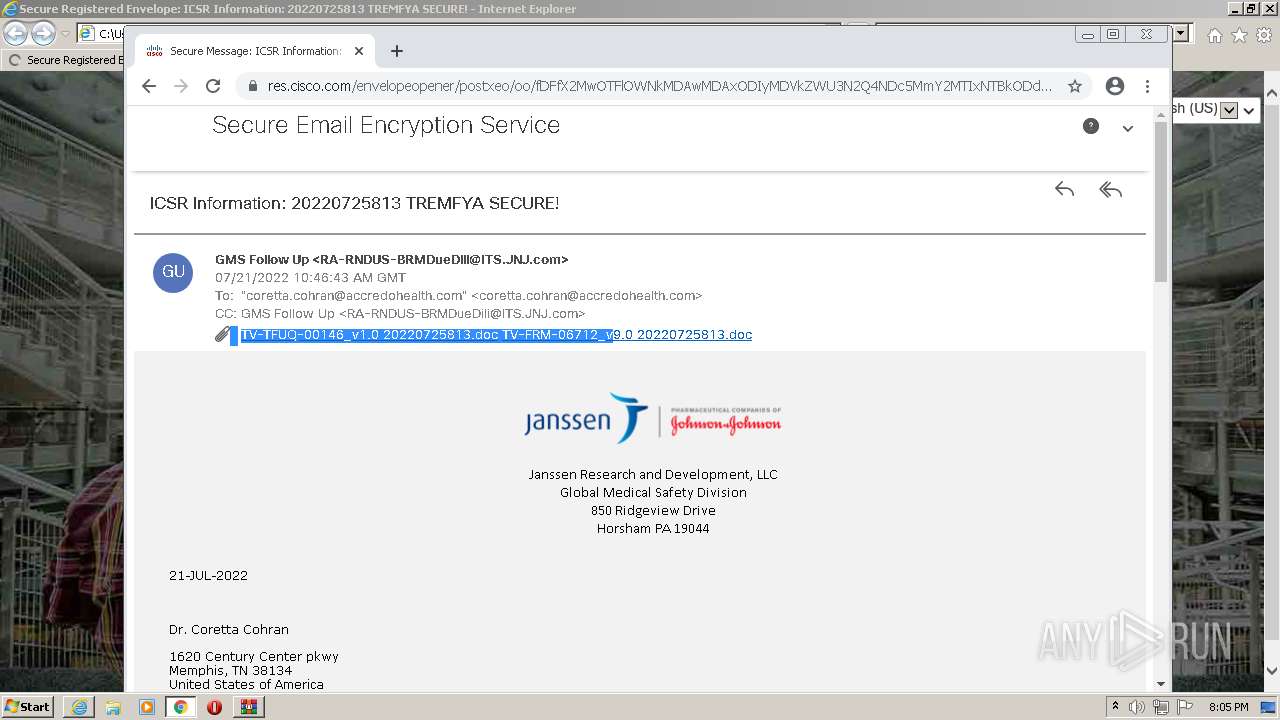
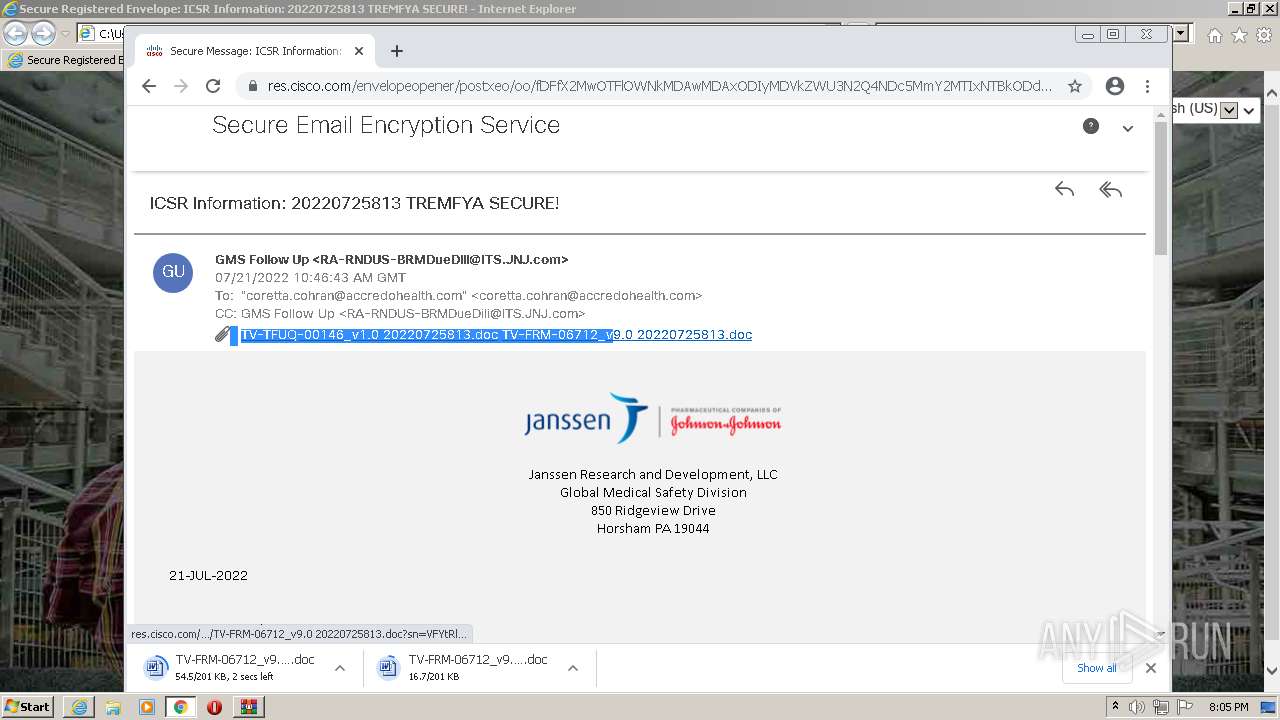
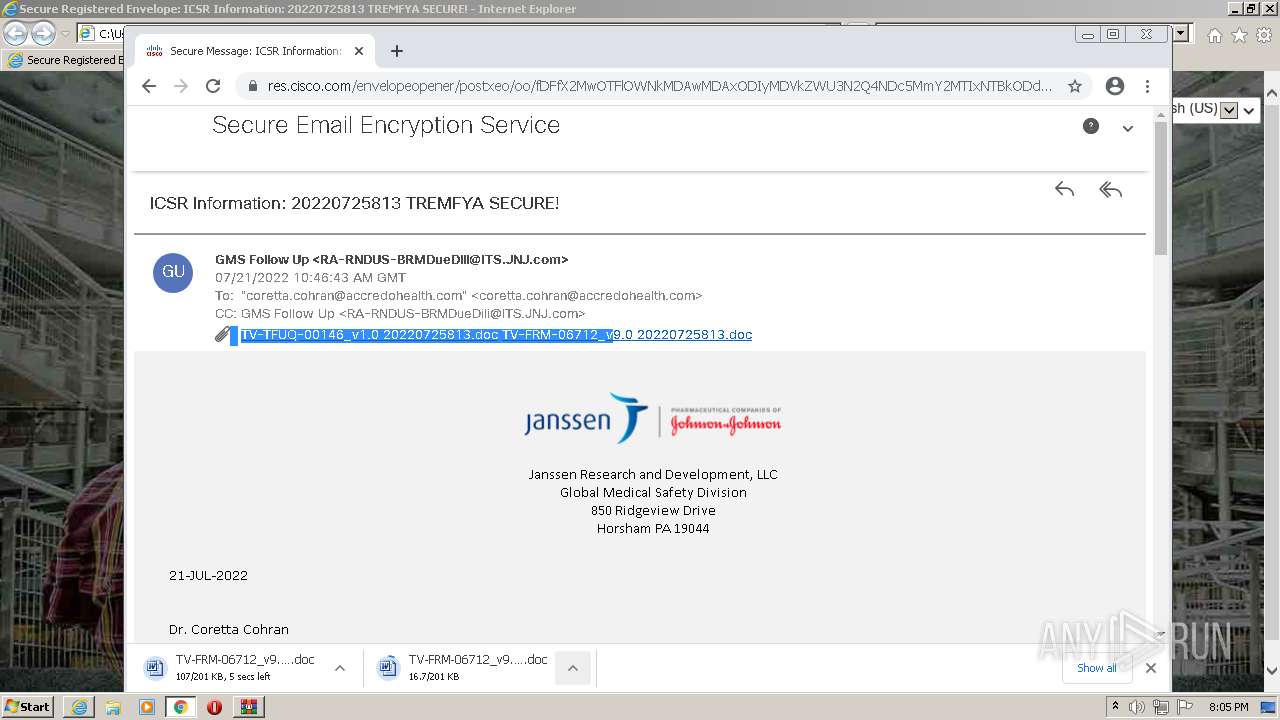
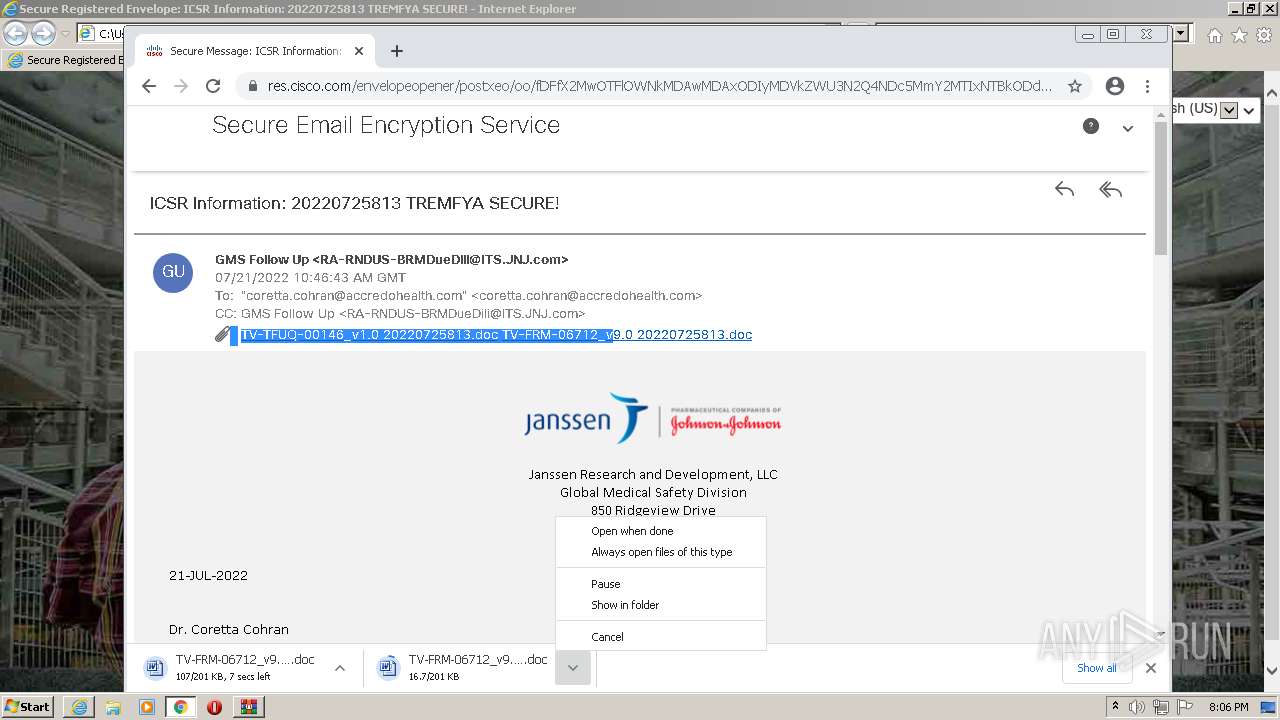
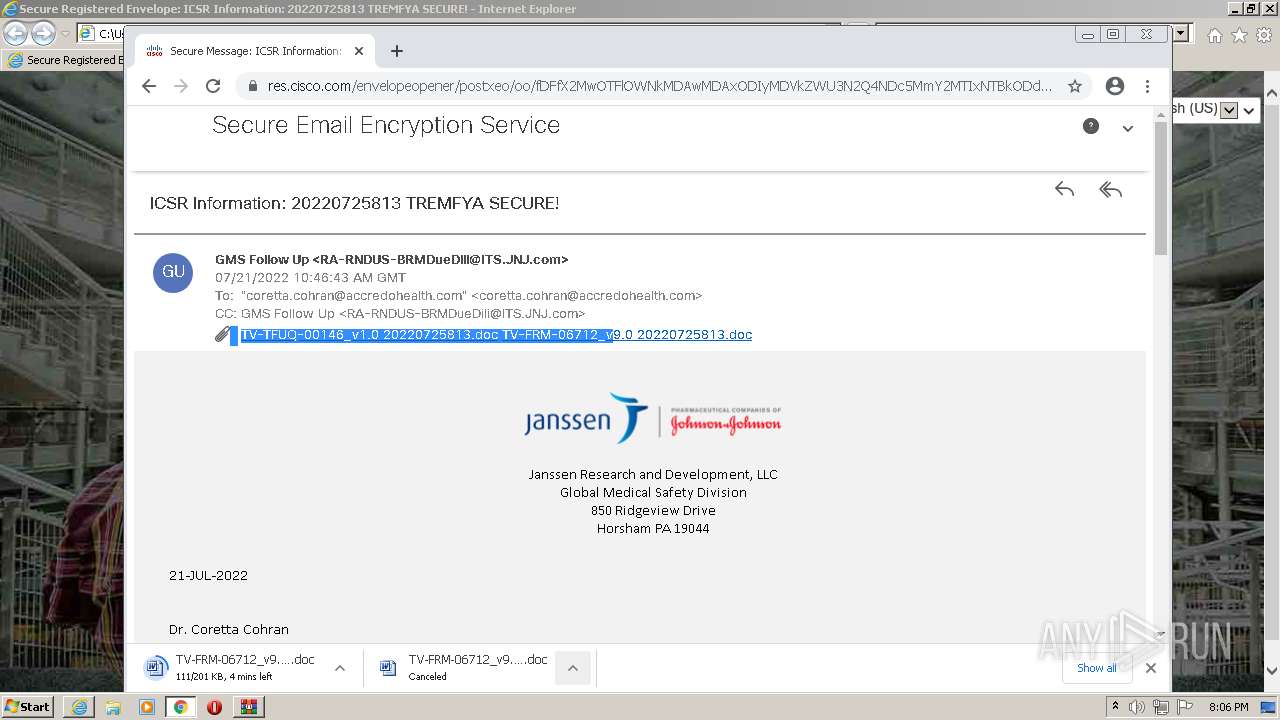
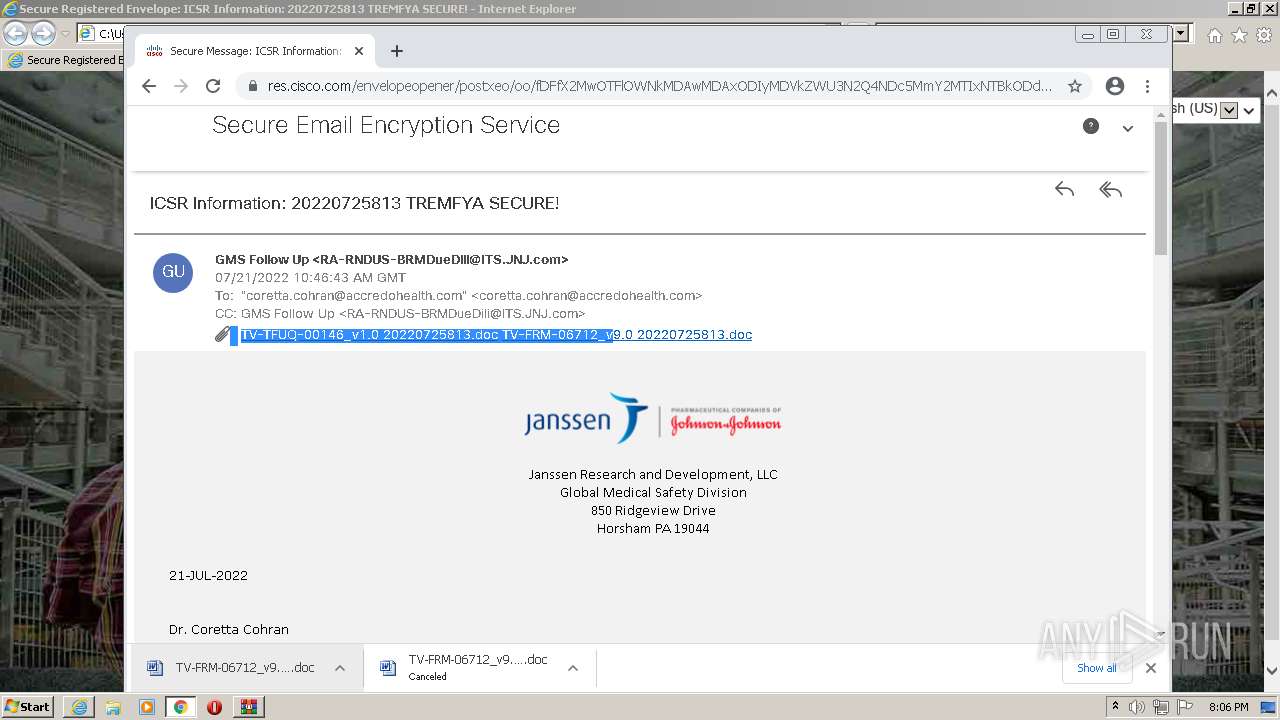
| File name: | securedoc_20220721T064643.html.zip |
| Full analysis: | https://app.any.run/tasks/9528b39b-651e-47de-ae52-d3fe08f7f0d9 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2022, 19:04:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2736B4547343F0E137210CC5DB84372D |
| SHA1: | B8B24DB4EB0190CA4D44DC6920D0FD69AC9826F3 |
| SHA256: | FBC75B043EDFFCE8A2A5D24A9B0DF60918775660417C66993701EA16BE5822F9 |
| SSDEEP: | 3072:R77nc49yYehyPIz02Q+TR59vTeAyUe8zryxarq9LbAcXmJXK:RXz0cIztvpPyxarqhbDXmtK |
MALICIOUS
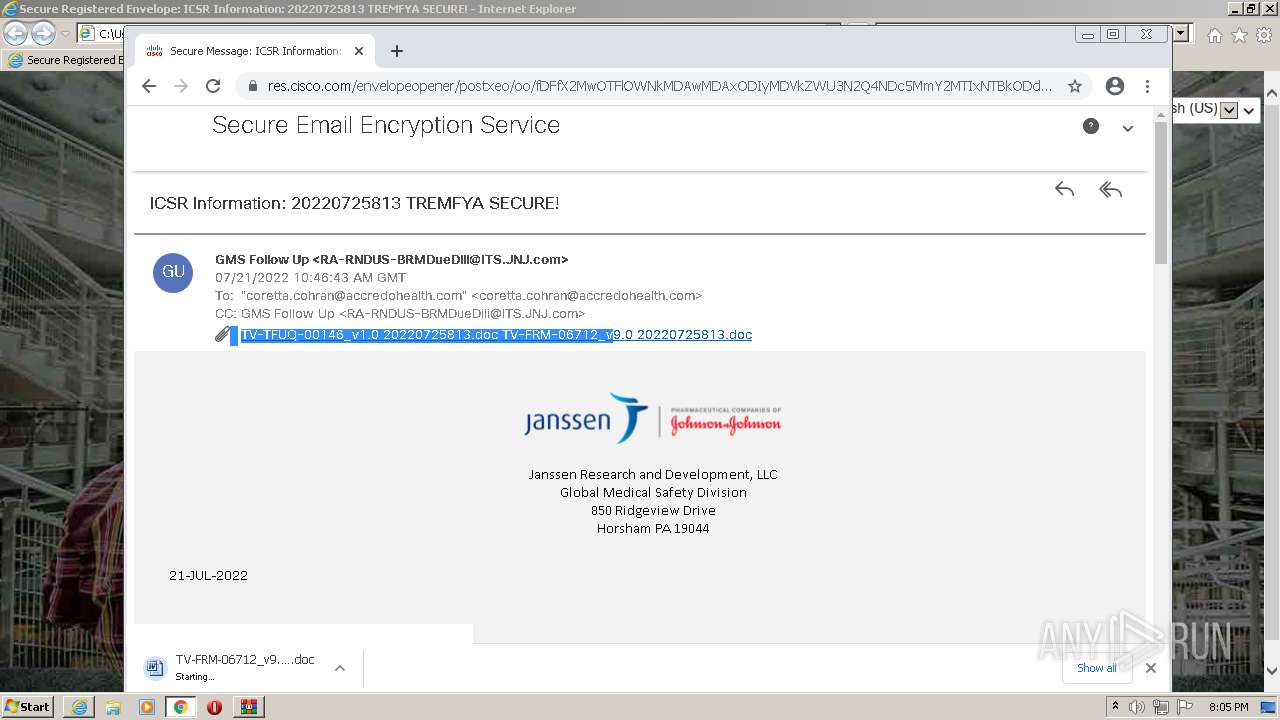
Drops executable file immediately after starts
- chrome.exe (PID: 880)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2968)
Checks supported languages
- WinRAR.exe (PID: 2968)
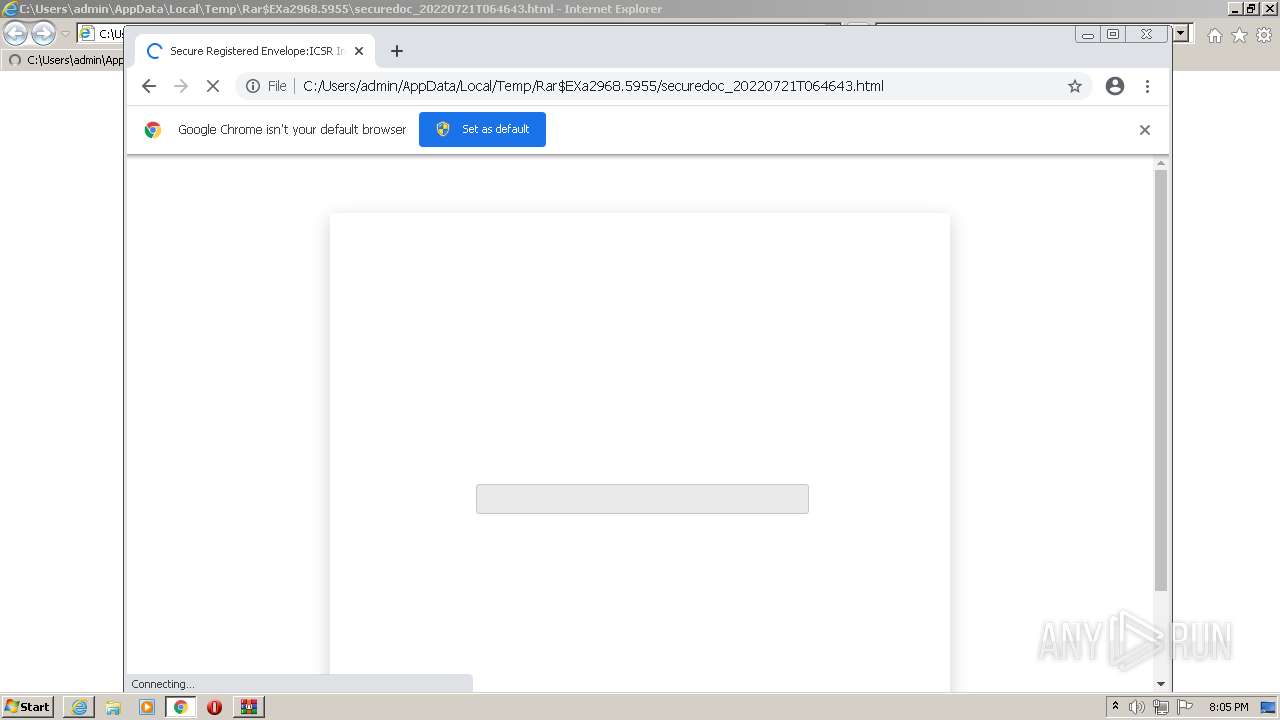
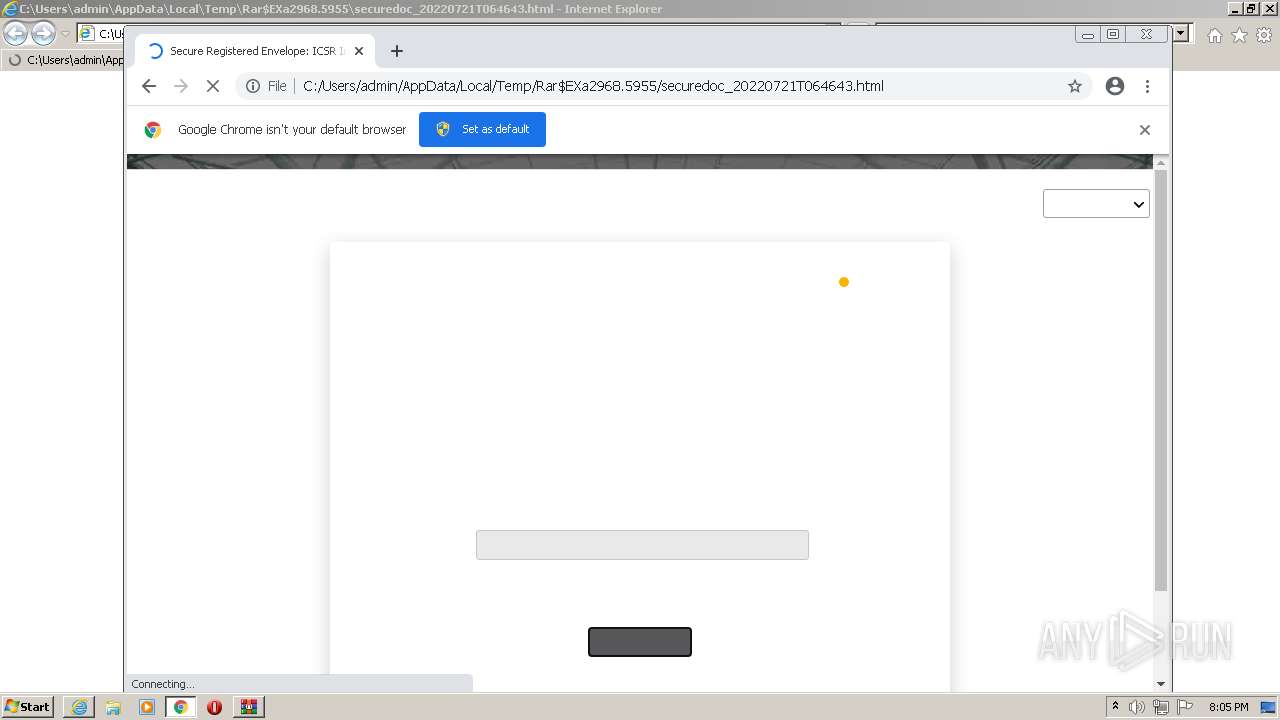
Starts Internet Explorer
- WinRAR.exe (PID: 2968)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3824)
Modifies files in Chrome extension folder
- chrome.exe (PID: 880)
Reads default file associations for system extensions
- chrome.exe (PID: 880)
- WINWORD.EXE (PID: 2596)
Drops a file with a compile date too recent
- chrome.exe (PID: 880)
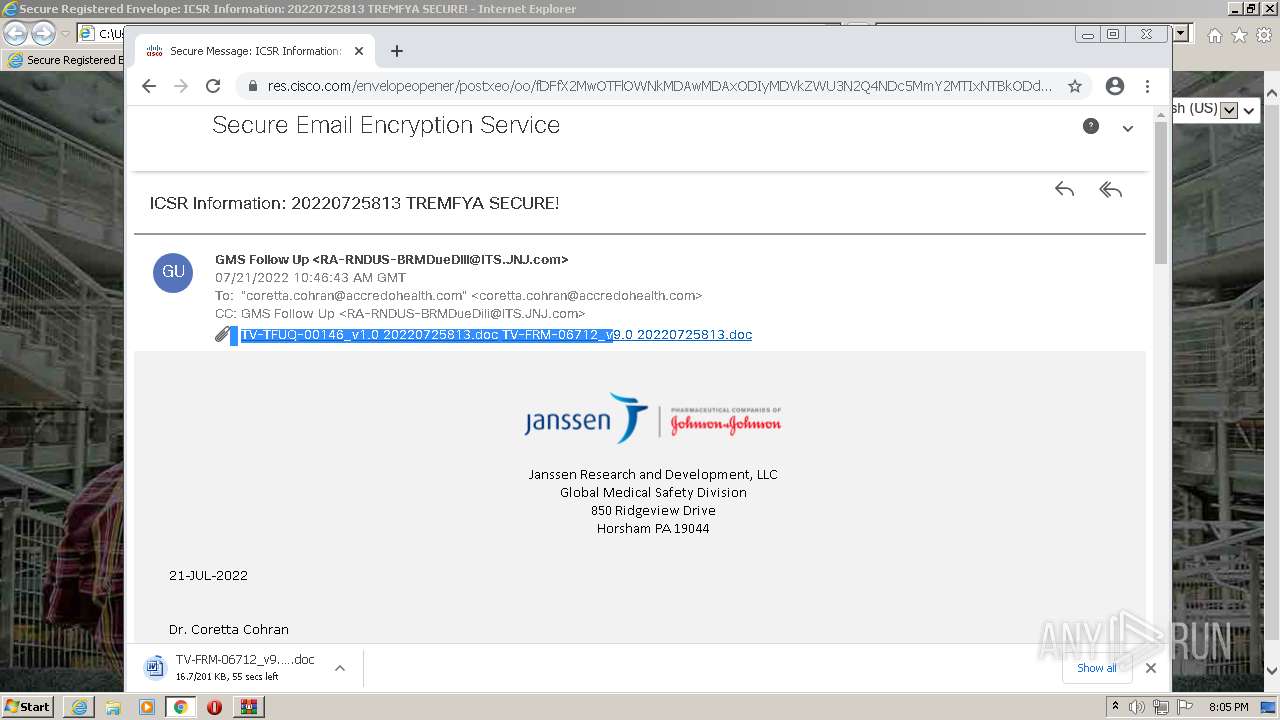
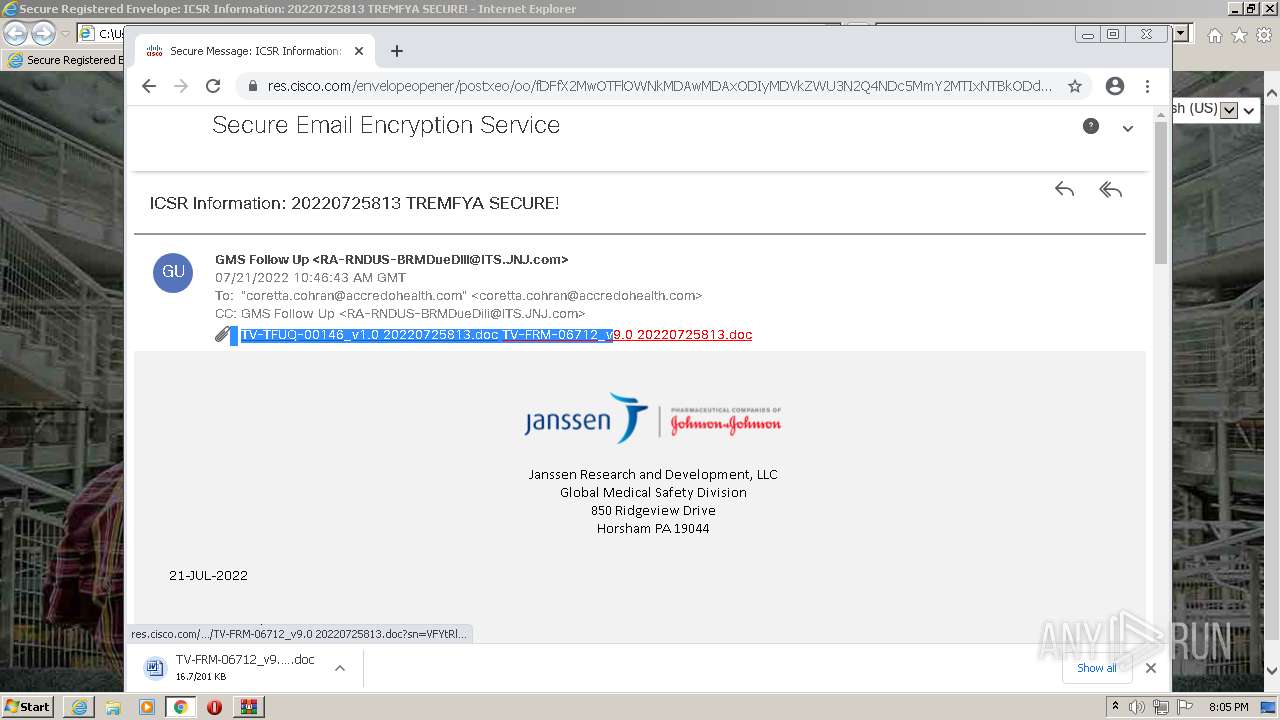
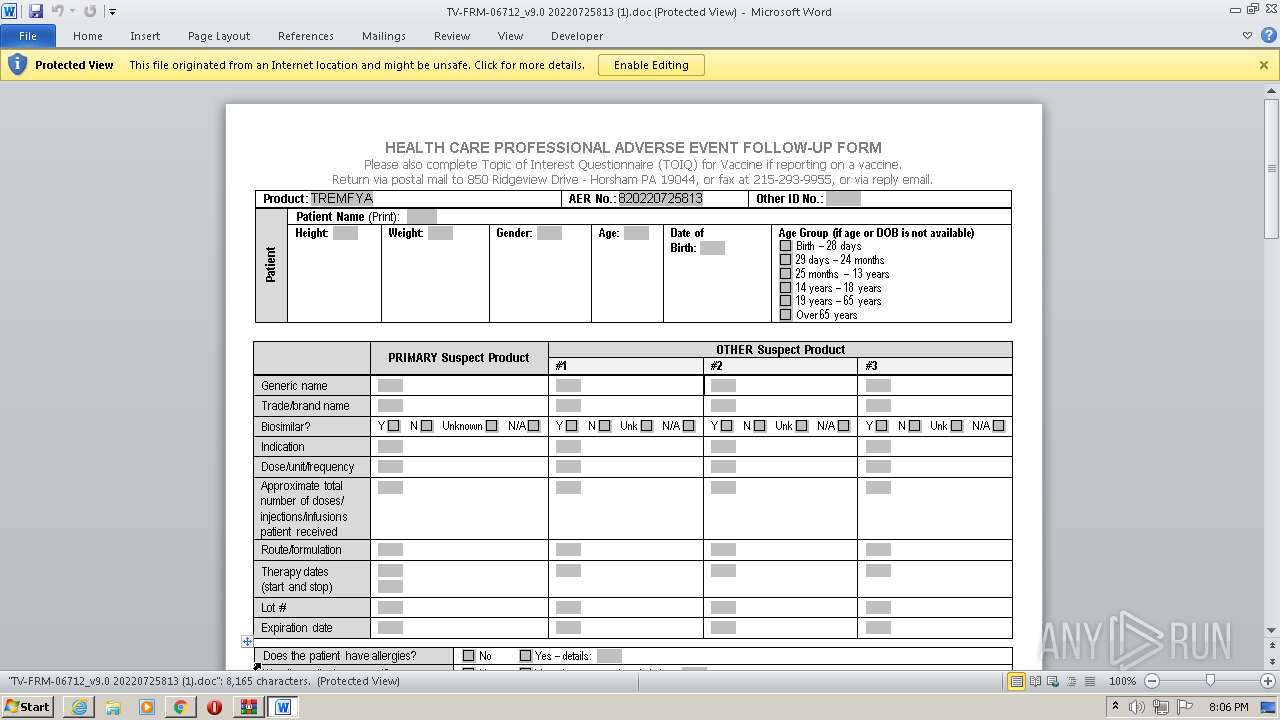
Starts Microsoft Office Application
- chrome.exe (PID: 880)
- WINWORD.EXE (PID: 2596)
Application launched itself
- WINWORD.EXE (PID: 2596)
INFO
Application launched itself
- iexplore.exe (PID: 1600)
- chrome.exe (PID: 880)
Checks Windows Trust Settings
- iexplore.exe (PID: 3824)
- iexplore.exe (PID: 1600)
Reads settings of System Certificates
- iexplore.exe (PID: 3824)
- iexplore.exe (PID: 1600)
- chrome.exe (PID: 1560)
Checks supported languages
- iexplore.exe (PID: 1600)
- chrome.exe (PID: 880)
- chrome.exe (PID: 1616)
- iexplore.exe (PID: 3824)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 1560)
- chrome.exe (PID: 1564)
- chrome.exe (PID: 120)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 1936)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 328)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 3772)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 1360)
- chrome.exe (PID: 3948)
- WINWORD.EXE (PID: 2596)
- WINWORD.EXE (PID: 3856)
- chrome.exe (PID: 4048)
Reads the computer name
- iexplore.exe (PID: 3824)
- iexplore.exe (PID: 1600)
- chrome.exe (PID: 880)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 1560)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 1360)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 3948)
- WINWORD.EXE (PID: 2596)
- WINWORD.EXE (PID: 3856)
Manual execution by user
- chrome.exe (PID: 880)
Reads internet explorer settings
- iexplore.exe (PID: 3824)
Changes internet zones settings
- iexplore.exe (PID: 1600)
Reads the hosts file
- chrome.exe (PID: 880)
- chrome.exe (PID: 1560)
Reads the date of Windows installation
- chrome.exe (PID: 2240)
Creates files in the user directory
- iexplore.exe (PID: 1600)
- WINWORD.EXE (PID: 2596)
Reads Microsoft Office registry keys
- chrome.exe (PID: 880)
- WINWORD.EXE (PID: 3856)
- WINWORD.EXE (PID: 2596)
Changes settings of System certificates
- iexplore.exe (PID: 1600)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | securedoc_20220721T064643.html |
|---|---|
| ZipUncompressedSize: | 249014 |
| ZipCompressedSize: | 138913 |
| ZipCRC: | 0x0a0896ed |
| ZipModifyDate: | 2022:07:25 19:04:21 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
67
Monitored processes
29
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,12852066379006432640,1918390741274434945,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,12852066379006432640,1918390741274434945,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1068,12852066379006432640,1918390741274434945,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1036 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1068,12852066379006432640,1918390741274434945,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1304 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,12852066379006432640,1918390741274434945,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
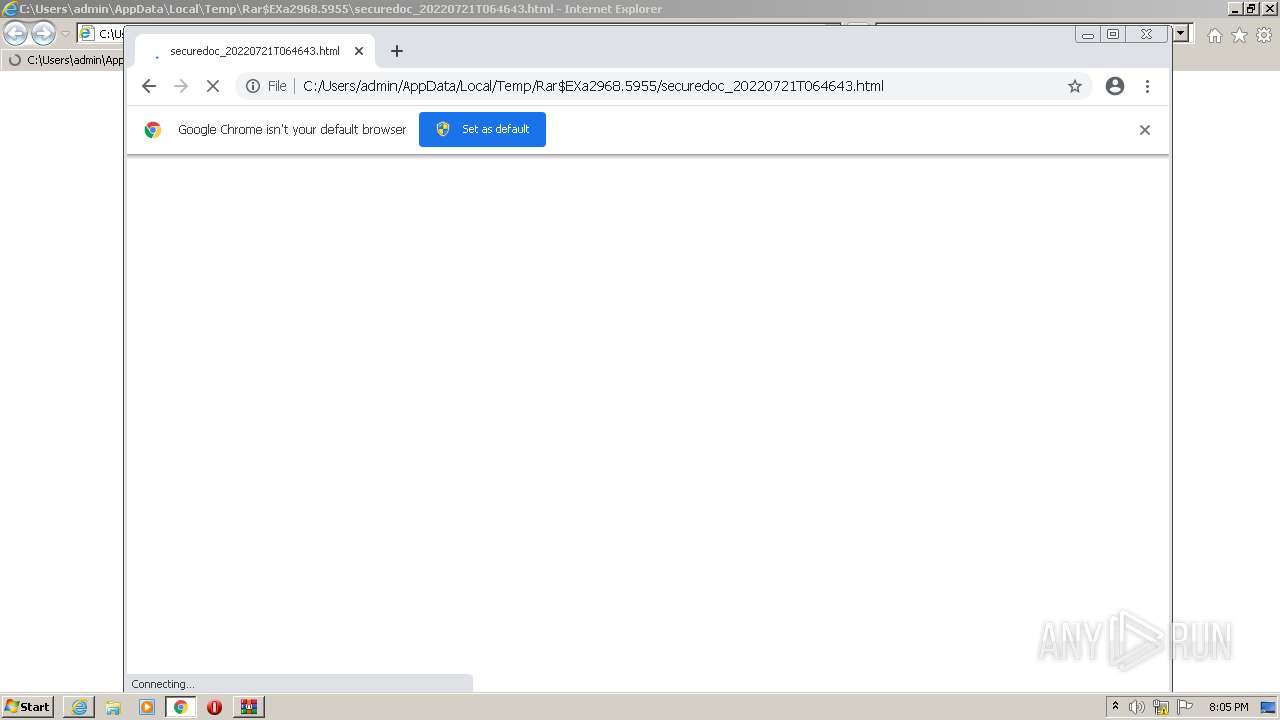
| 1600 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.5955\securedoc_20220721T064643.html | C:\Program Files\Internet Explorer\iexplore.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6b64d988,0x6b64d998,0x6b64d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,12852066379006432640,1918390741274434945,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1068,12852066379006432640,1918390741274434945,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
31 217
Read events
30 727
Write events
439
Delete events
51
Modification events
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\securedoc_20220721T064643.html.zip | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2968) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
155
Text files
152
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62DEE966-370.pma | — | |
MD5:— | SHA256:— | |||
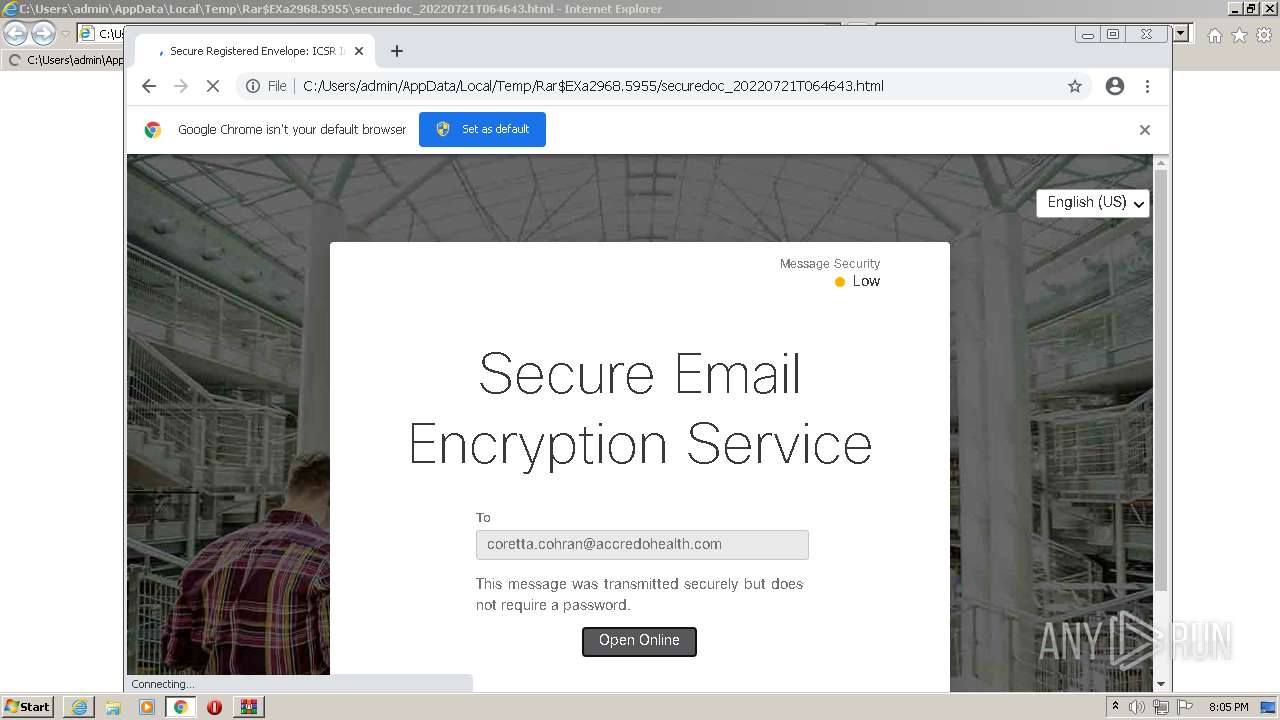
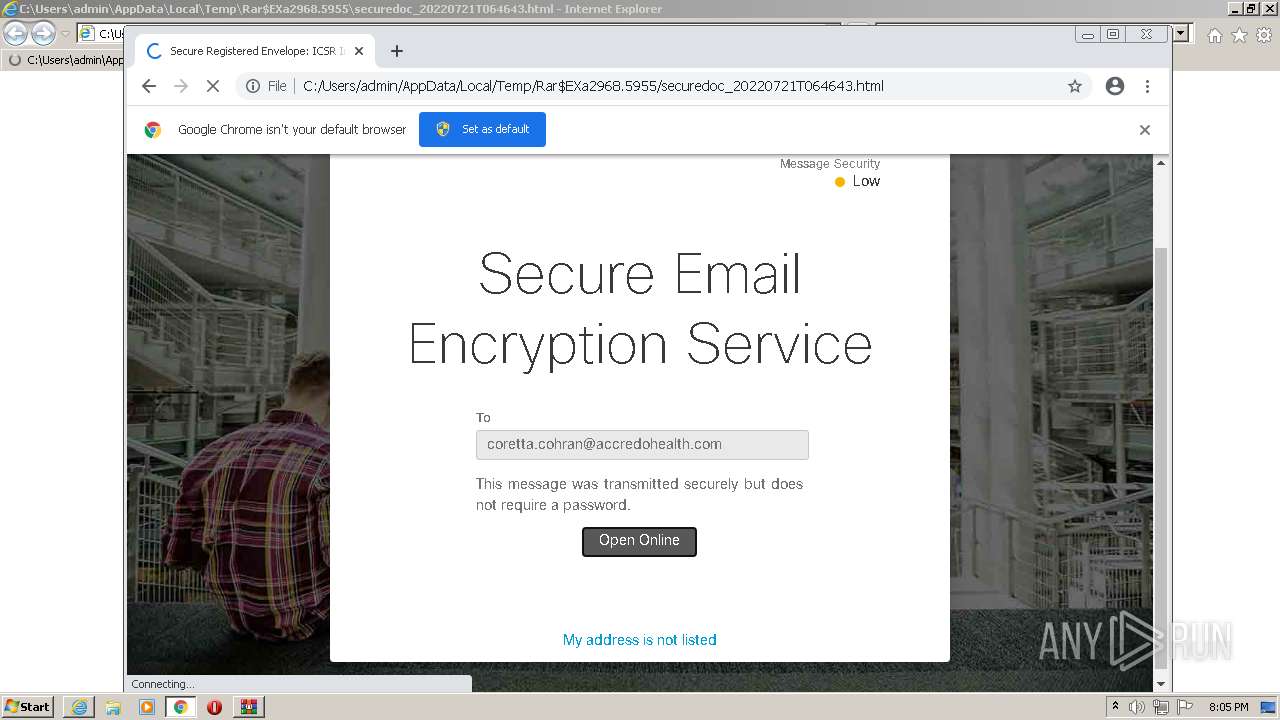
| 2968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2968.5955\securedoc_20220721T064643.html | html | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1616 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFffee8.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFffed9.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
101
DNS requests
41
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 74.125.110.137:80 | http://r4---sn-5goeen7y.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3?cms_redirect=yes&mh=VX&mip=196.244.192.6&mm=28&mn=sn-5goeen7y&ms=nvh&mt=1658775628&mv=m&mvi=4&pl=24&rmhost=r3---sn-5goeen7y.gvt1.com&shardbypass=sd&smhost=r1---sn-5goeenez.gvt1.com | US | — | — | whitelisted |
— | — | HEAD | 302 | 142.250.186.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
3824 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3824 | iexplore.exe | GET | 200 | 18.194.140.191:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBTyhcKR1A4XhQLFZRt5u%2BT8TDsYdQQUGoRivEhMMyUE1O7Q9gPEGUbRlGsCFHI7b%2BXCUnVNIYmwkVVSGjGHkW24 | DE | der | 1.71 Kb | whitelisted |
1600 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3824 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDqkhspY9VhihK0Rxq6O%2BRa | US | der | 472 b | whitelisted |
1560 | chrome.exe | GET | 302 | 142.250.186.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 592 b | whitelisted |
3824 | iexplore.exe | GET | 200 | 18.194.140.191:80 | http://ocsp.quovadisglobal.com/MFUwUzBRME8wTTAJBgUrDgMCGgUABBQKn47RTHY4CAiWs41NfwpqyKQFgAQUzKLzOK32xVQnMkbFOV9JchMTgHkCFEMXUL6dqdmPuedJ42e9ijTMmHho | DE | der | 1.75 Kb | whitelisted |
3824 | iexplore.exe | GET | 200 | 18.66.242.94:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3824 | iexplore.exe | GET | 200 | 52.222.250.185:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.250.186.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
— | — | 104.17.24.14:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3824 | iexplore.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
3824 | iexplore.exe | 142.250.186.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
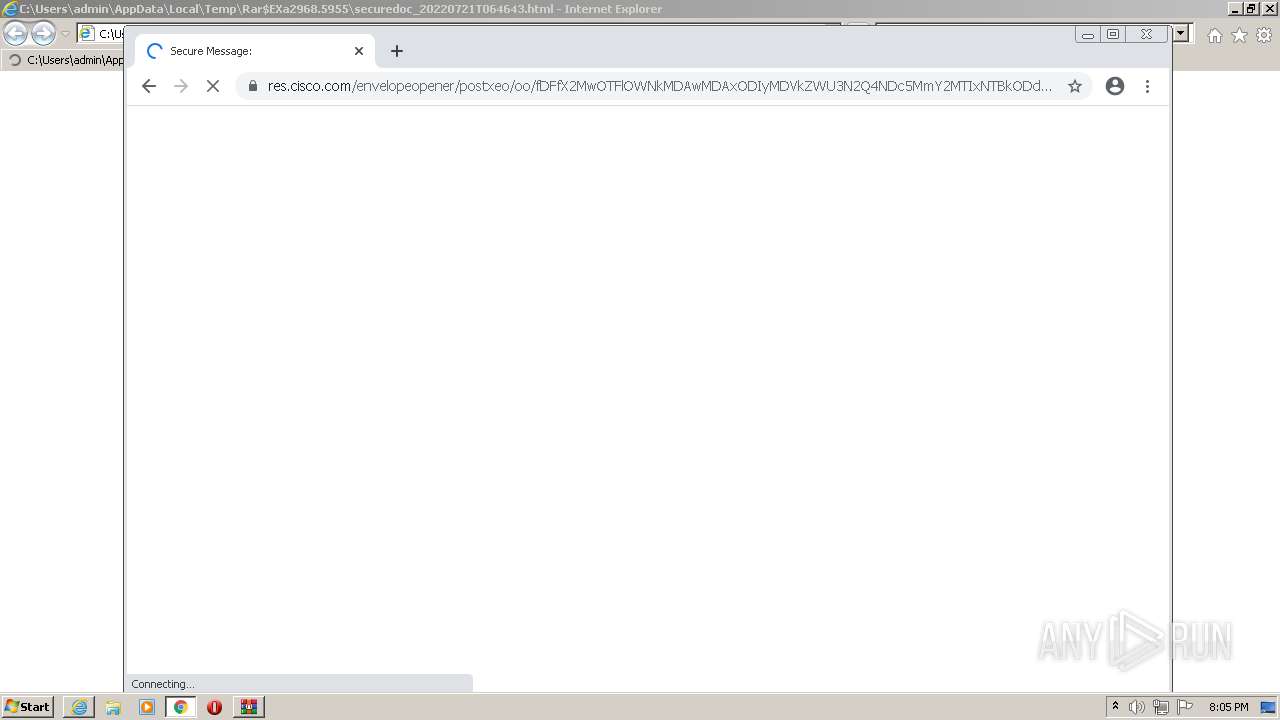
3824 | iexplore.exe | 184.94.241.74:443 | res.cisco.com | Cisco Systems Ironport Division | US | suspicious |
— | — | 184.94.241.74:443 | res.cisco.com | Cisco Systems Ironport Division | US | suspicious |
— | — | 184.94.241.74:80 | res.cisco.com | Cisco Systems Ironport Division | US | suspicious |
3824 | iexplore.exe | 92.123.195.28:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | suspicious |
1600 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1600 | iexplore.exe | 92.123.195.28:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
res.cisco.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1560 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
1560 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |