| File name: | greet.ex_ |
| Full analysis: | https://app.any.run/tasks/891f6856-f601-494d-ac5c-022a2ee5fed3 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2019, 11:33:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 63C94D3096DEC9A0748515104518DB21 |
| SHA1: | 8A56A8D4A69872E8C011E893036AF4495F123B7F |
| SHA256: | FBC18D28F50F3235C6E4BCD0C1CAE58E2F6EEB34887859EE4DC38C25B7D8B8EE |
| SSDEEP: | 24576:TZB2PAmZ4Nj9KRpRoUWmmKKR+Pz3VZcwZ60PX0wS7fLIbgqOCpLa:TZYPNSNj4fWm/KUPDVZnZfPtEL+gmpW |
MALICIOUS
Changes the autorun value in the registry
- regedit.exe (PID: 3520)
Application was dropped or rewritten from another process
- spoolsv.exe (PID: 3688)
SUSPICIOUS
Modifies the open verb of a shell class
- spoolsv.exe (PID: 3688)
Executable content was dropped or overwritten
- greet.ex_.exe (PID: 3348)
Starts CMD.EXE for commands execution
- greet.ex_.exe (PID: 3348)
Creates files in the Windows directory
- greet.ex_.exe (PID: 3348)
- spoolsv.exe (PID: 3688)
Removes files from Windows directory
- spoolsv.exe (PID: 3688)
Creates a software uninstall entry
- spoolsv.exe (PID: 3688)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2876)
Connects to unusual port
- spoolsv.exe (PID: 3688)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (94.8) |
|---|---|---|
| .scr | | | Windows screen saver (2.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:08:05 07:34:26+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 77824 |
| InitializedDataSize: | 115200 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Aug-2006 05:34:26 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 05-Aug-2006 05:34:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00013000 | 0x00012E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46788 |
.data | 0x00014000 | 0x00007000 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.75622 |
.idata | 0x0001B000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05399 |
.rsrc | 0x0001C000 | 0x0001A6E8 | 0x0001A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.06138 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10885 | 531 | Latin 1 / Western European | Russian - Russia | RT_MANIFEST |
2 | 3.0402 | 744 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.14196 | 488 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 3.0945 | 296 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 3.43007 | 3752 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 3.49049 | 2216 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.24143 | 556 | Latin 1 / Western European | Russian - Russia | RT_STRING |
8 | 3.28574 | 946 | Latin 1 / Western European | Russian - Russia | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | Russian - Russia | RT_STRING |
10 | 3.15563 | 638 | Latin 1 / Western European | Russian - Russia | RT_STRING |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
41
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1104 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2584 | attrib +H +S C:\Windows\temp\spoolsv | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | cmd /c ""C:\Windows\temp\spoolsv\run.bat" " | C:\Windows\system32\cmd.exe | — | greet.ex_.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3080 | "C:\Users\admin\AppData\Local\Temp\greet.ex_.exe" | C:\Users\admin\AppData\Local\Temp\greet.ex_.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3348 | "C:\Users\admin\AppData\Local\Temp\greet.ex_.exe" | C:\Users\admin\AppData\Local\Temp\greet.ex_.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3520 | regedit /s C:\Windows\Temp\spoolsv\a.reg | C:\Windows\regedit.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3688 | C:\Windows\temp\spoolsv\spoolsv.exe | C:\Windows\temp\spoolsv\spoolsv.exe | cmd.exe | ||||||||||||
User: admin Company: mIRC Co. Ltd. Integrity Level: HIGH Description: mIRC Exit code: 0 Version: 6.03 Modules
| |||||||||||||||
Total events
171
Read events
134
Write events
37
Delete events
0
Modification events
| (PID) Process: | (3348) greet.ex_.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%Windows%temp%spoolsv% |
Value: C:\Windows\temp\spoolsv\ | |||
| (PID) Process: | (3348) greet.ex_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3348) greet.ex_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3520) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\svchost\Parameters |
| Operation: | write | Name: | Application |
Value: "C:\Windows\temp\spoolsv\spoolsv.exe" | |||
| (PID) Process: | (3520) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\svchost\Parameters |
| Operation: | write | Name: | AppDirectory |
Value: "C:\Windows\temp\spoolsv\spoolsv.exe" | |||
| (PID) Process: | (3520) regedit.exe | Key: | HKEY_CURRENT_USER\Software\mIRC\License |
| Operation: | write | Name: | |
Value: 5662-546732 | |||
| (PID) Process: | (3520) regedit.exe | Key: | HKEY_CURRENT_USER\Software\mIRC\LockOptions |
| Operation: | write | Name: | |
Value: 0,4096 | |||
| (PID) Process: | (3520) regedit.exe | Key: | HKEY_CURRENT_USER\Software\mIRC\UserName |
| Operation: | write | Name: | |
Value: WhiteHat | |||
| (PID) Process: | (3520) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | spoolsv |
Value: "C:\Windows\temp\spoolsv\spoolsv.exe" | |||
| (PID) Process: | (1104) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
Executable files
1
Suspicious files
1
Text files
85
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | spoolsv.exe | C:\Windows\temp\spoolsv\TMP1.$$ | — | |
MD5:— | SHA256:— | |||
| 3688 | spoolsv.exe | C:\Windows\temp\spoolsv\TMP2.$$ | — | |
MD5:— | SHA256:— | |||
| 3688 | spoolsv.exe | C:\Windows\temp\spoolsv\TMP3.$$ | — | |
MD5:— | SHA256:— | |||
| 3688 | spoolsv.exe | C:\Windows\temp\spoolsv\TMP4.$$ | — | |
MD5:— | SHA256:— | |||
| 3348 | greet.ex_.exe | C:\Windows\Temp\spoolsv\ident.txt | text | |
MD5:— | SHA256:— | |||
| 3688 | spoolsv.exe | C:\Windows\temp\spoolsv\remote.ini | ini | |
MD5:— | SHA256:— | |||
| 3348 | greet.ex_.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat | hiv | |
MD5:— | SHA256:— | |||
| 3348 | greet.ex_.exe | C:\Windows\Temp\spoolsv\servers.ini | text | |
MD5:— | SHA256:— | |||
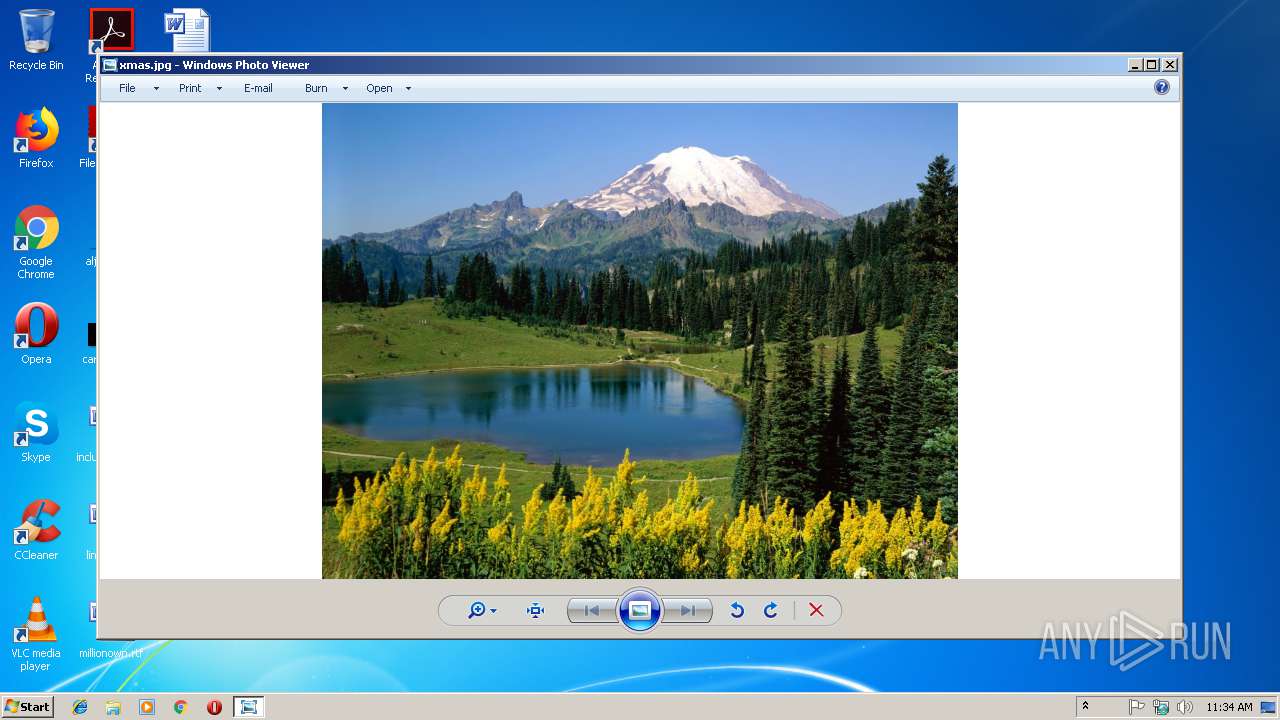
| 3348 | greet.ex_.exe | C:\Windows\Temp\spoolsv\xmas.jpg | image | |
MD5:— | SHA256:— | |||
| 3348 | greet.ex_.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
2
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3688 | spoolsv.exe | 154.35.136.18:6667 | Newyork.NY.US.Undernet.Org | Rethem Hosting LLC | US | unknown |
3688 | spoolsv.exe | 168.235.81.212:6667 | irc.indoirc.net | RamNode LLC | US | unknown |
— | — | 46.246.1.160:137 | — | Portlane AB | SE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
Newyork.NY.US.Undernet.Org |
| malicious |
irc.indoirc.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3688 | spoolsv.exe | Misc activity | ET CHAT IRC PONG response |
3688 | spoolsv.exe | Misc activity | ET CHAT IRC PONG response |
3688 | spoolsv.exe | Misc activity | ET CHAT IRC PING command |
3688 | spoolsv.exe | Misc activity | ET CHAT IRC PONG response |
3688 | spoolsv.exe | Misc activity | ET CHAT IRC PING command |