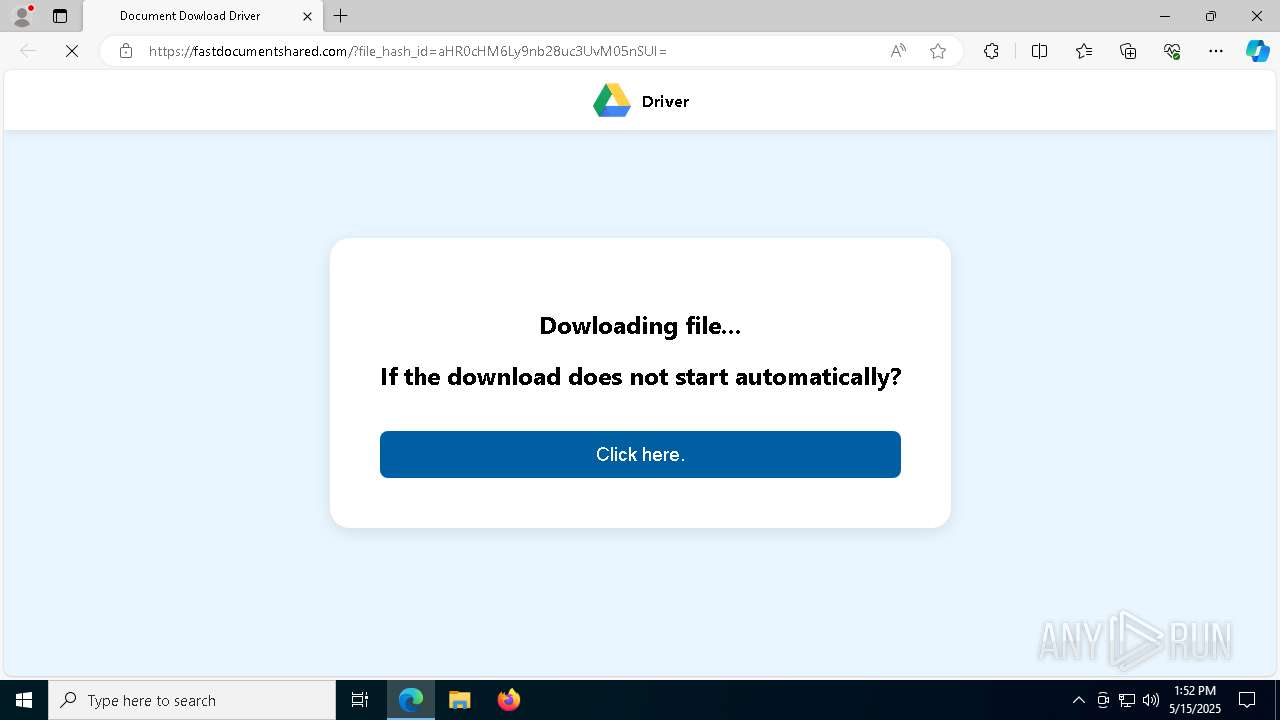
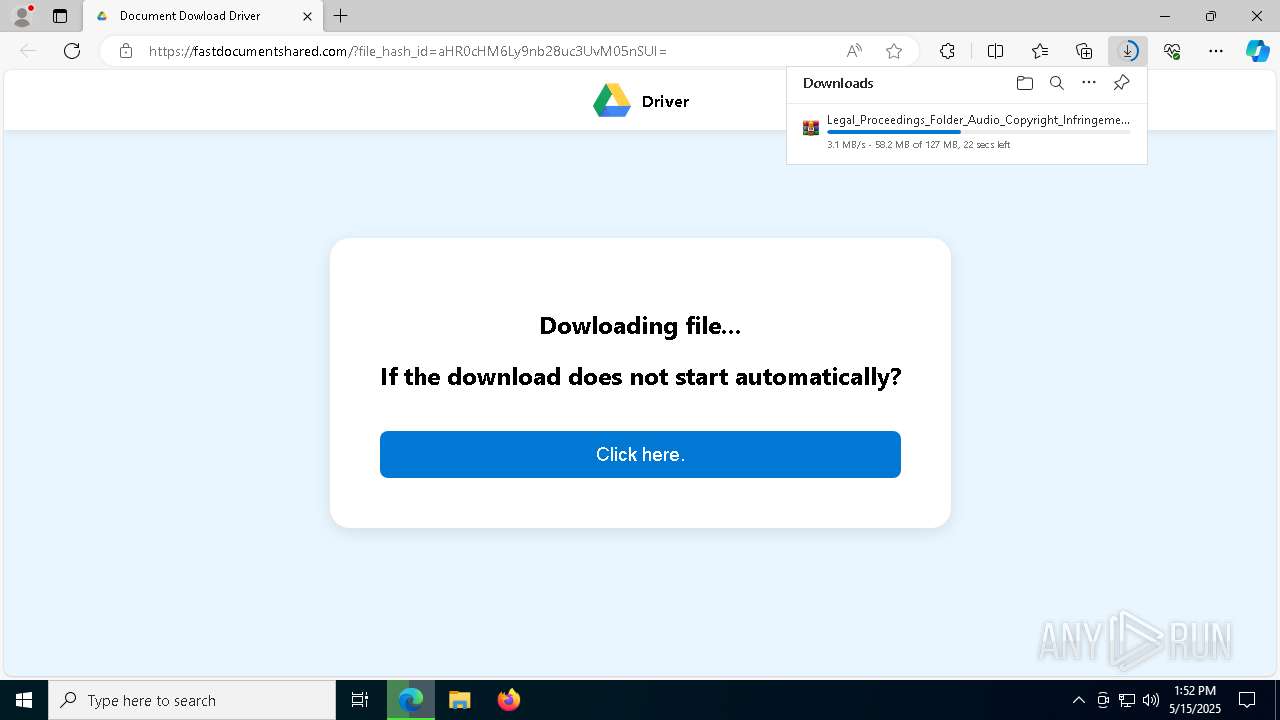
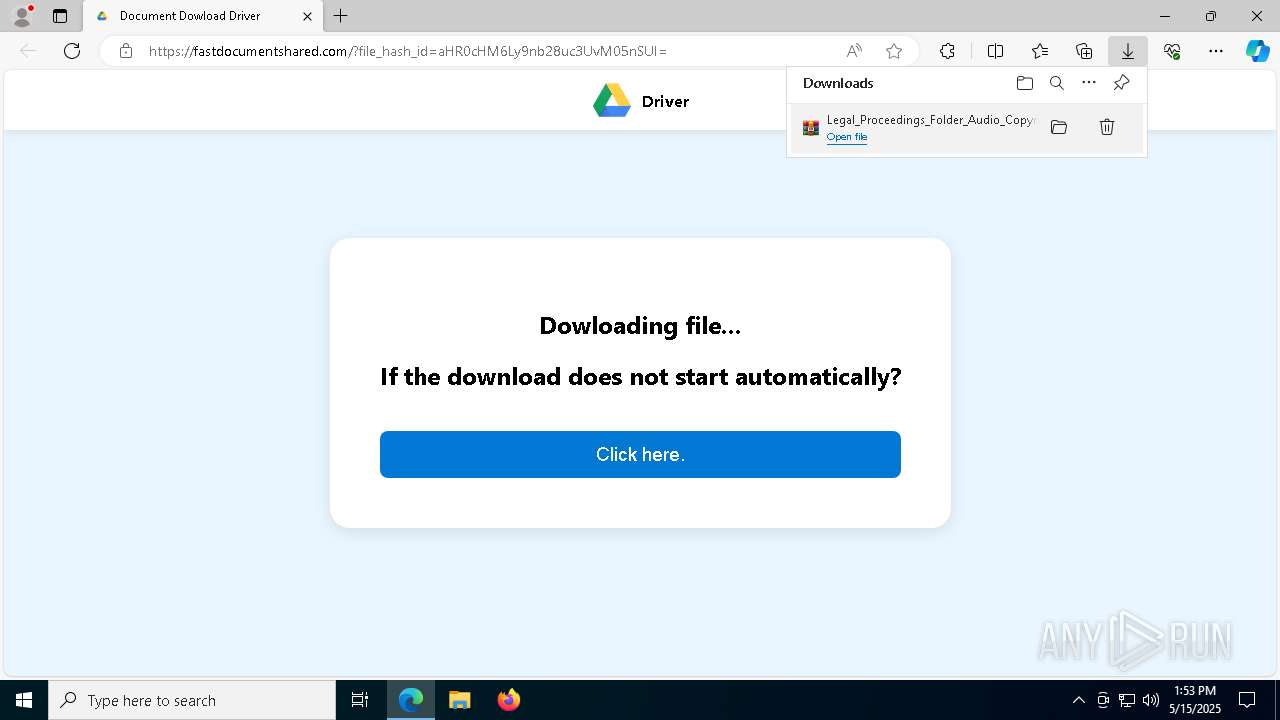
| URL: | https://goo.su/bzmQWd4 |
| Full analysis: | https://app.any.run/tasks/bfa4198c-9df7-4eaf-ac85-577bb24930ee |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
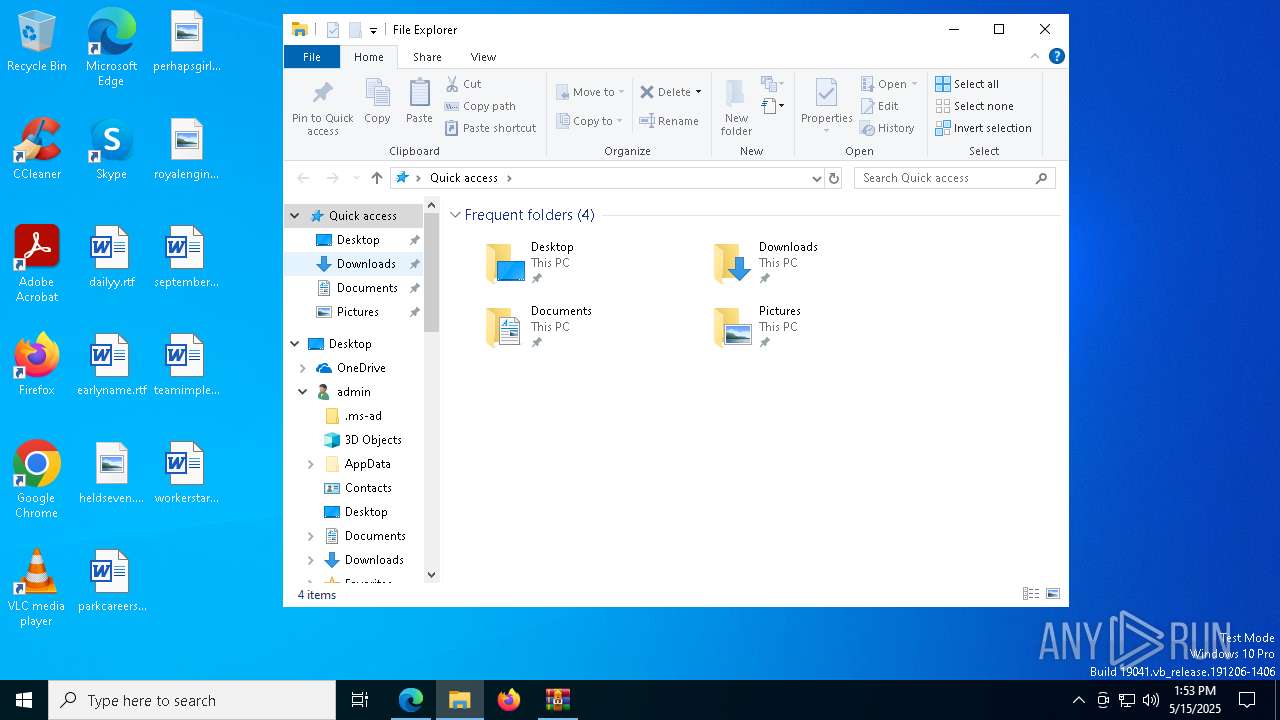
| Analysis date: | May 15, 2025, 13:52:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CE67A4B4ECF6EA74485659FF94AB4B7A |
| SHA1: | AD1784BF37807B325537A60E1CAED027A4E6404C |
| SHA256: | FB9CD14ECA2F77BAAAA403DF9D48E4671D2495AD2DB27092F9594D936ABA8FD8 |
| SSDEEP: | 3:N8rQXKHfE:2UaHfE |
MALICIOUS
Suspicious browser debugging (Possible cookie theft)
- msedge.exe (PID: 3896)
- chrome.exe (PID: 872)
SUSPICIOUS
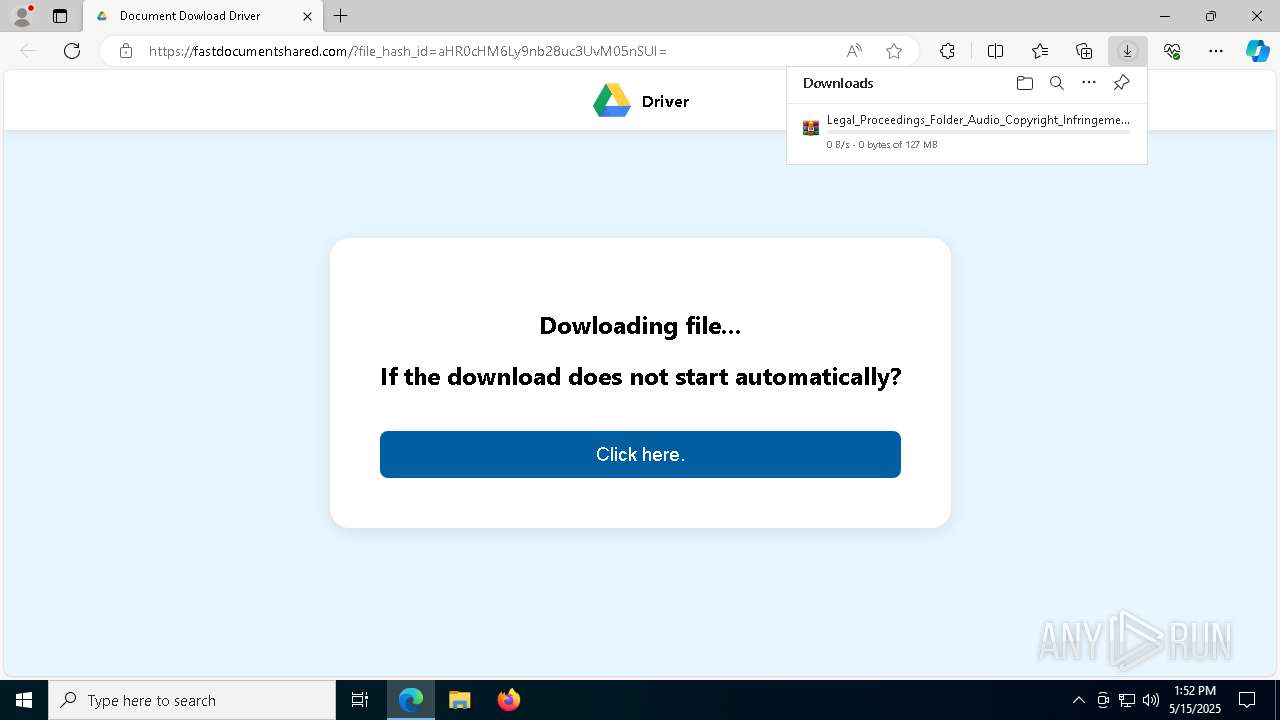
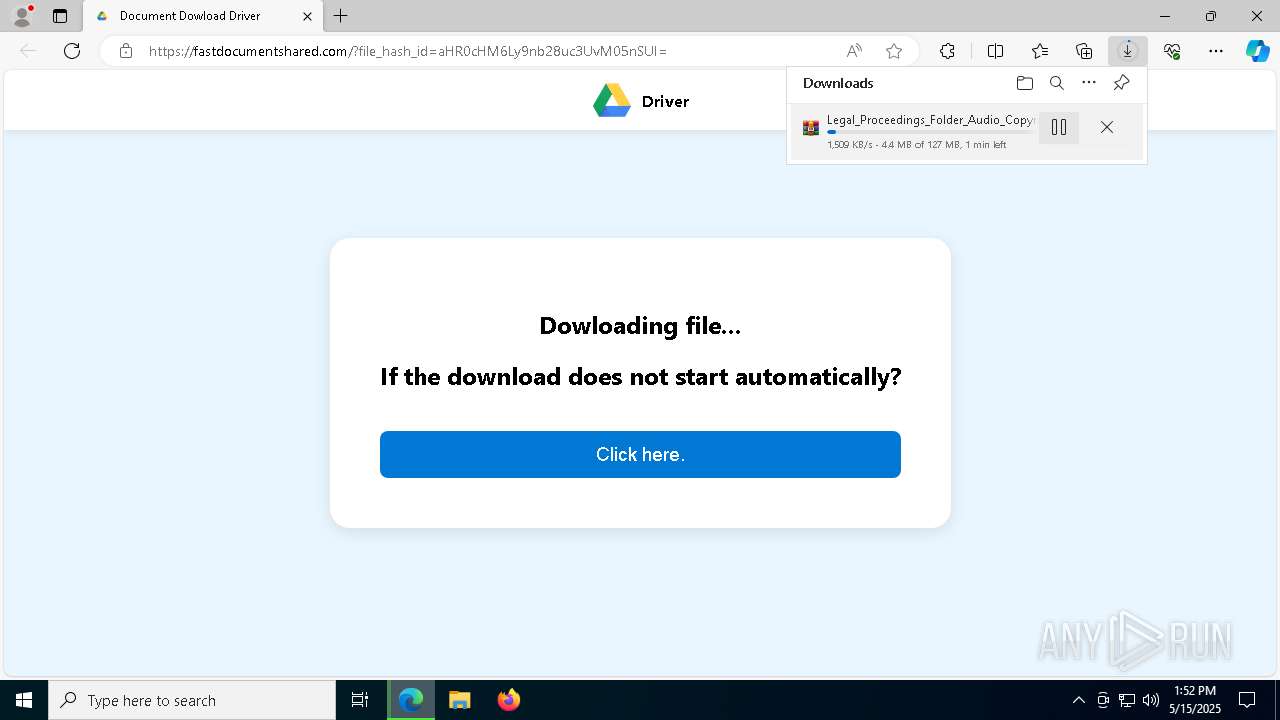
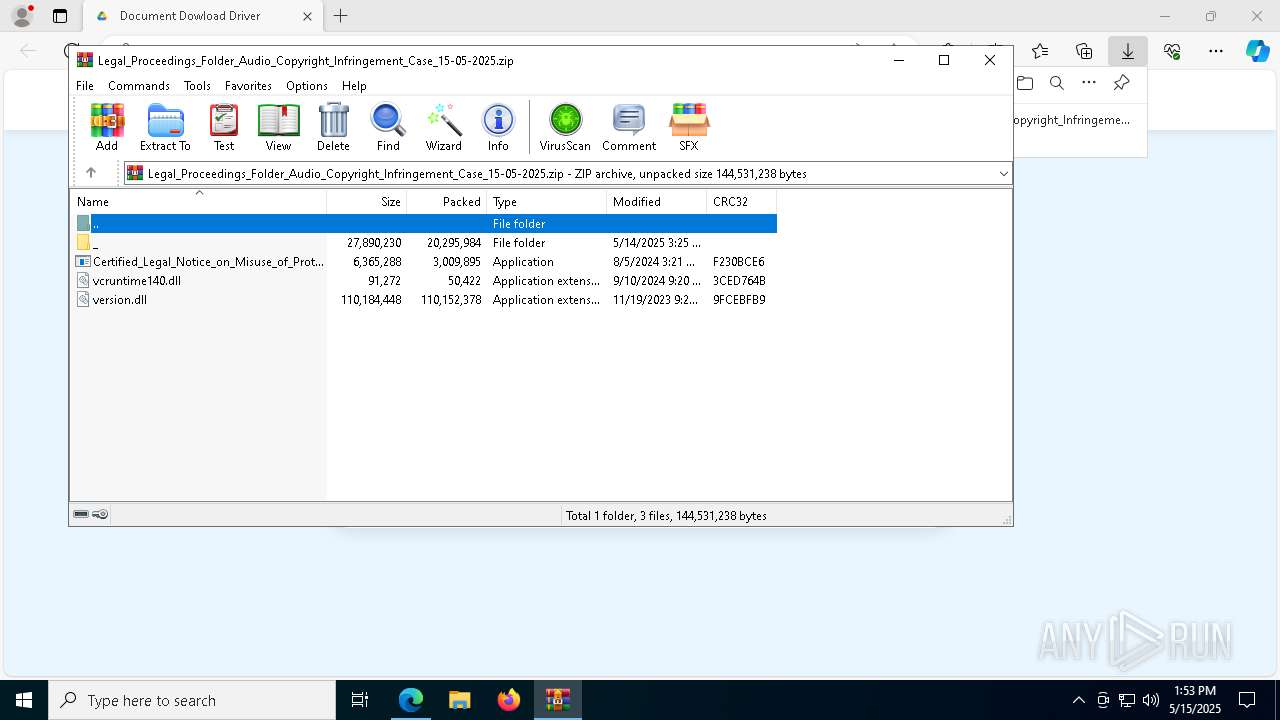
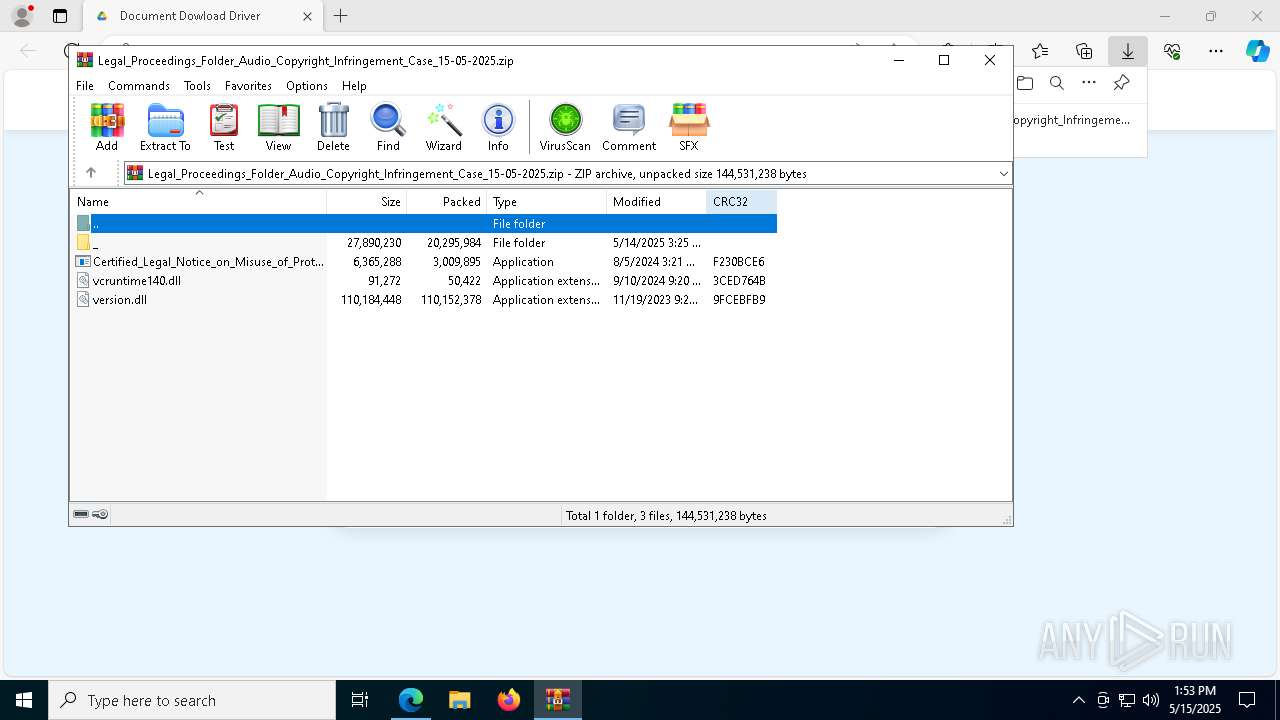
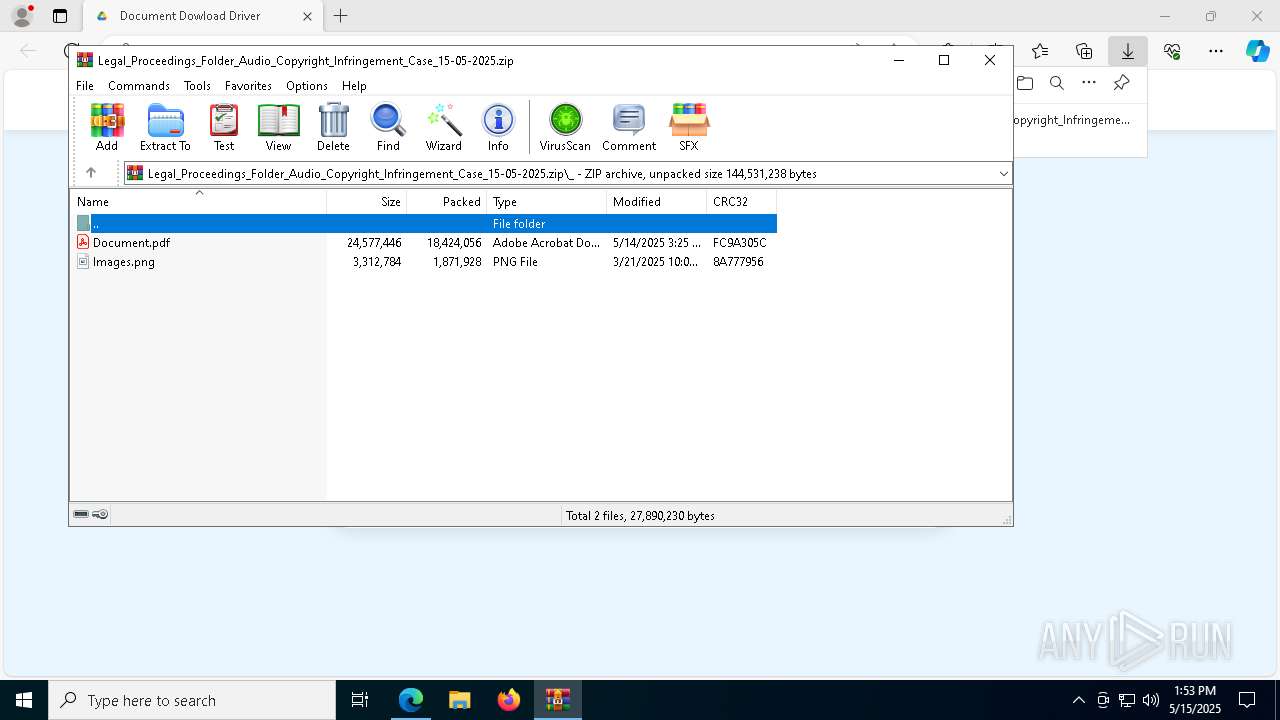
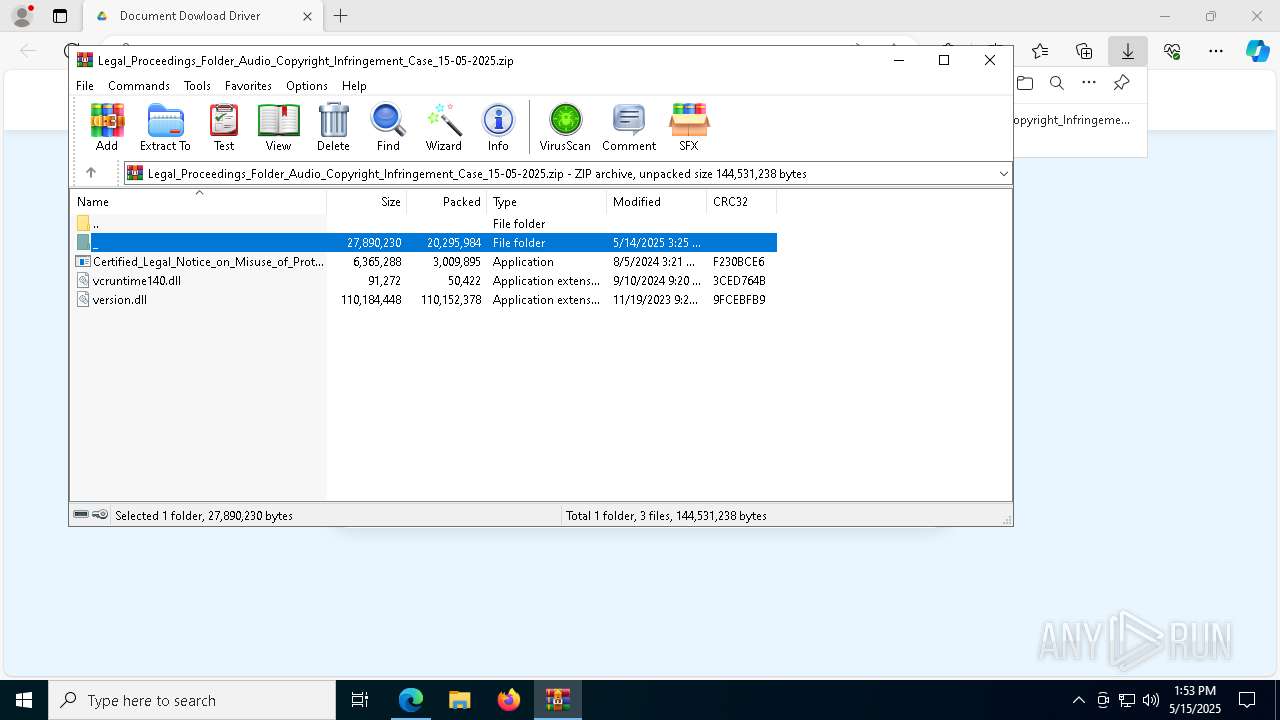
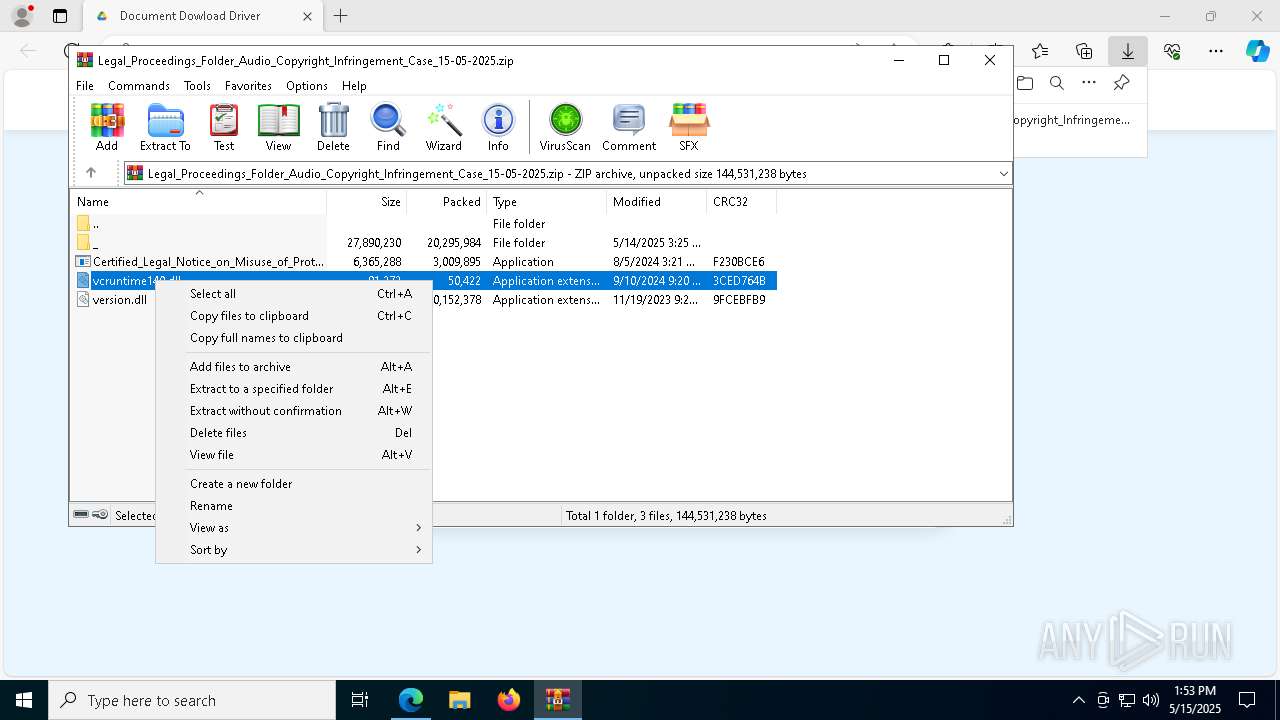
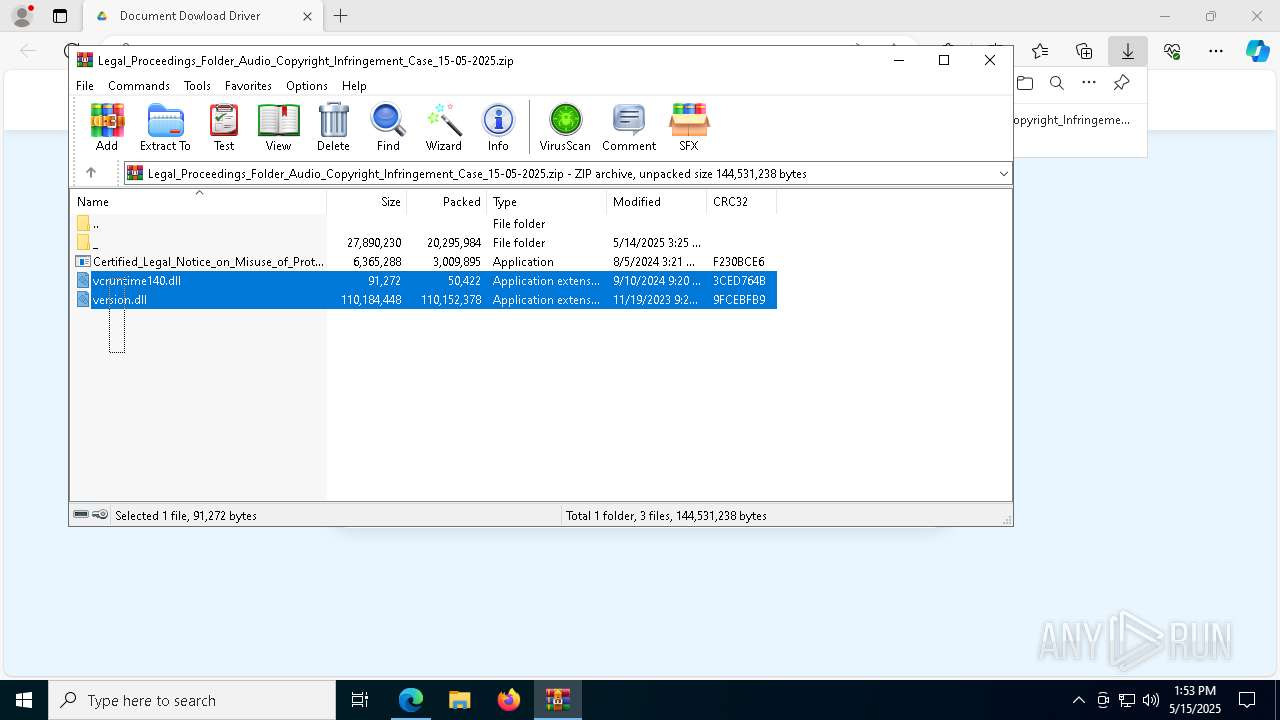
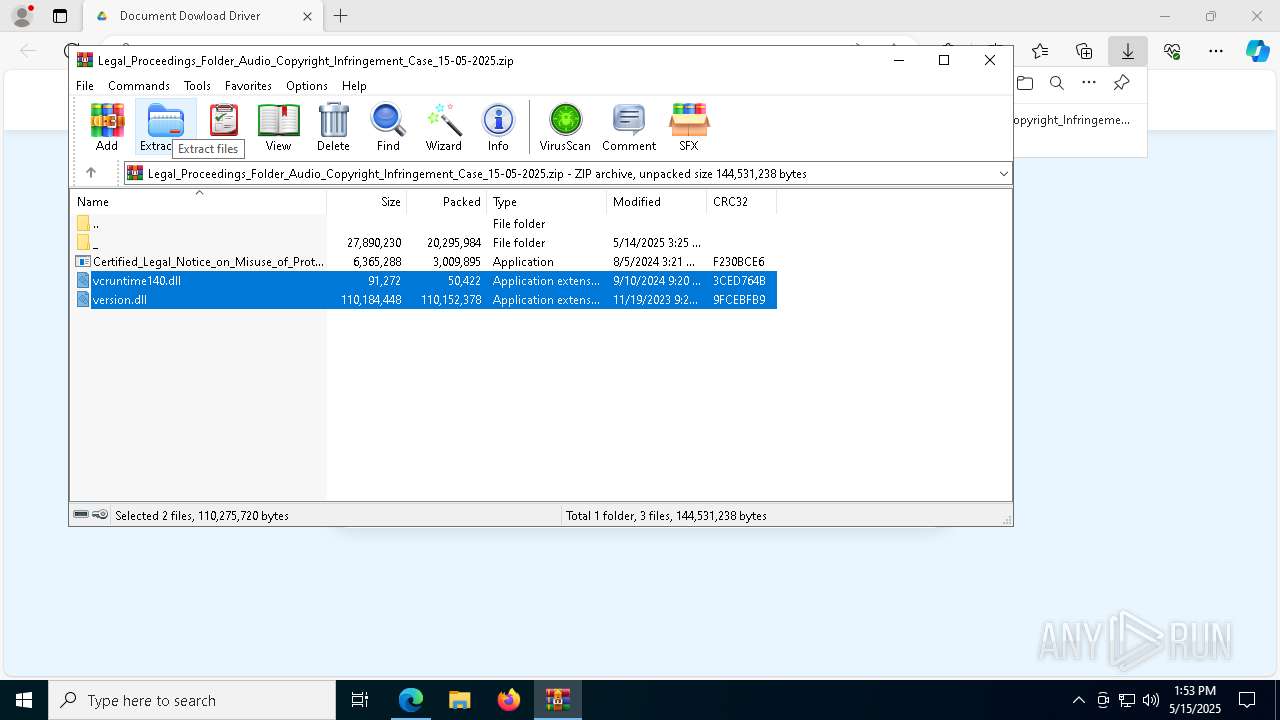
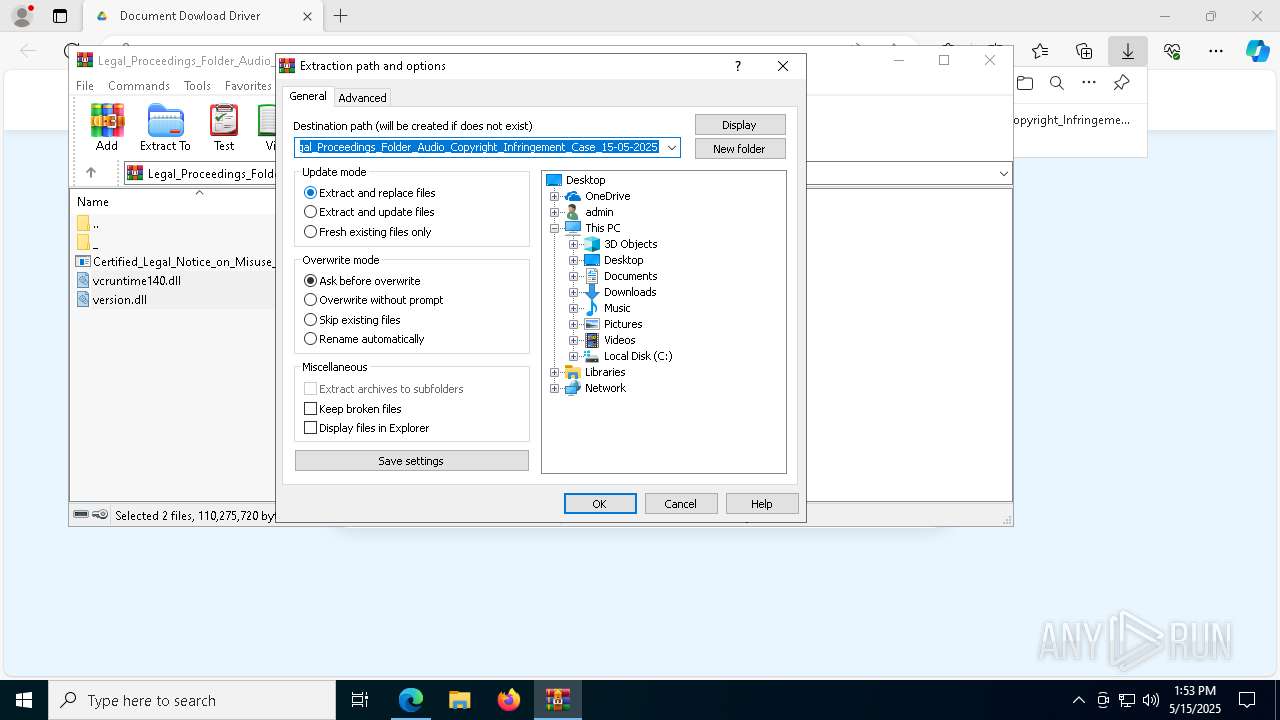
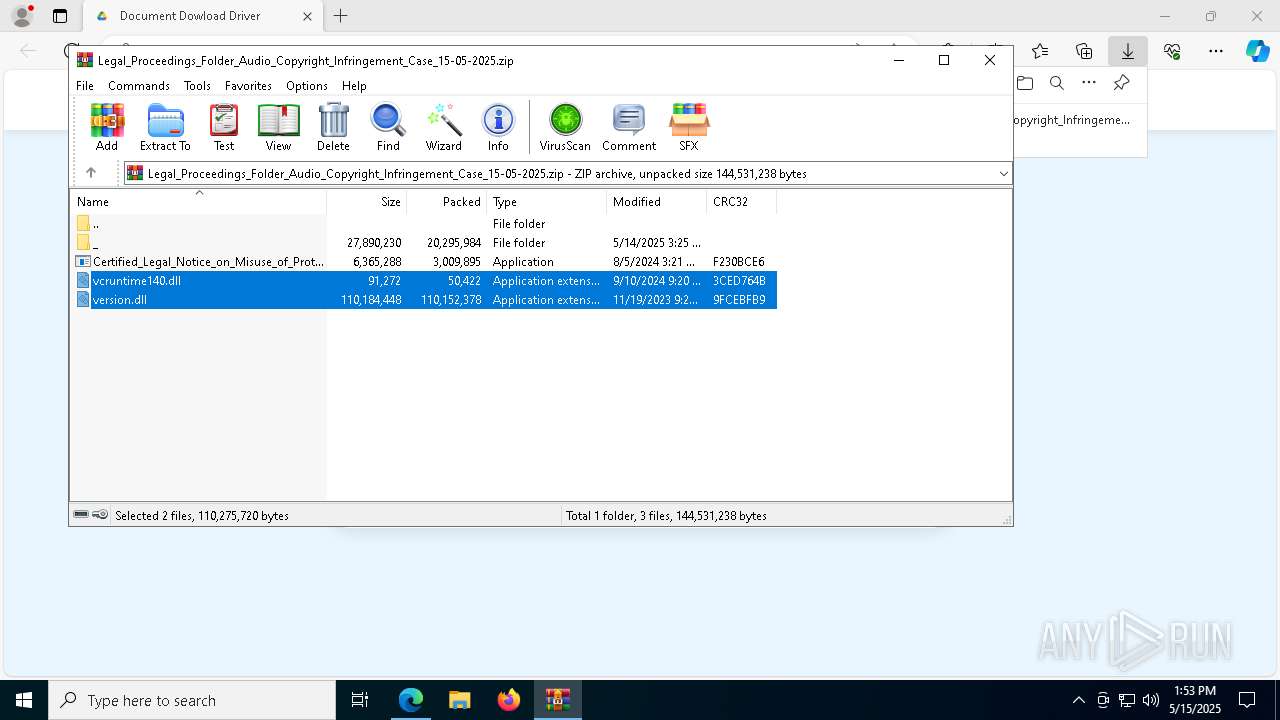
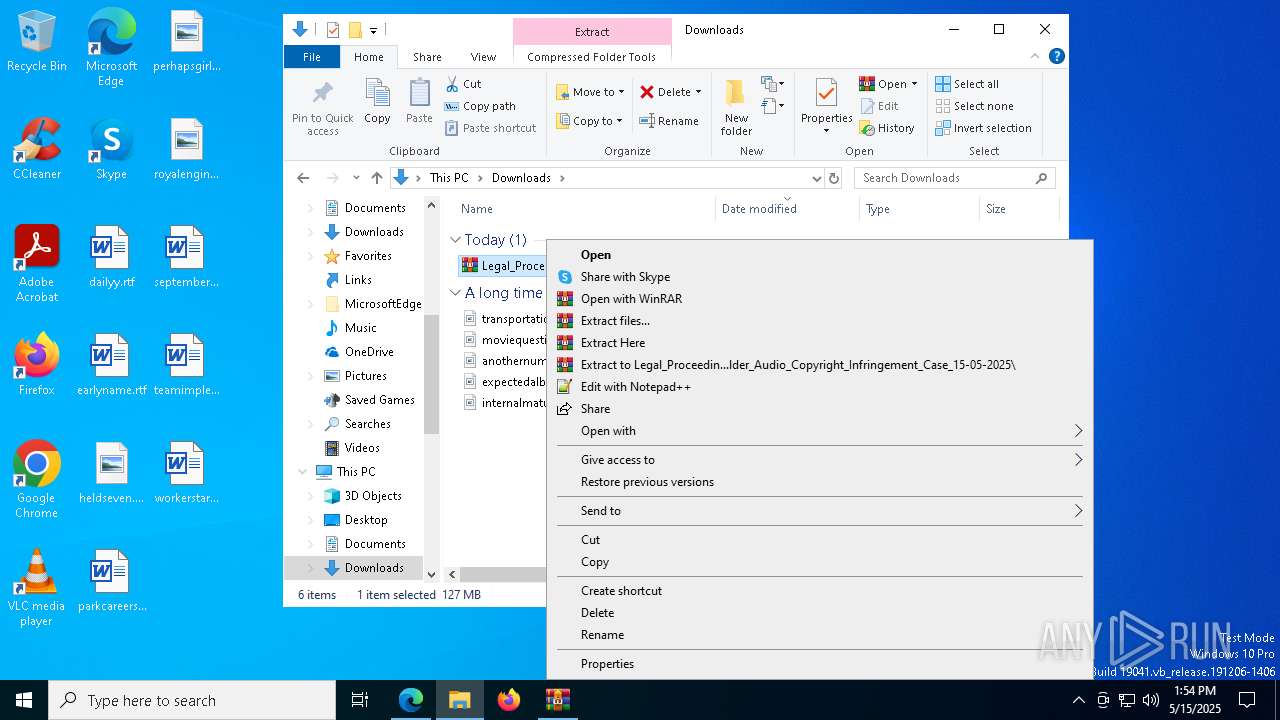
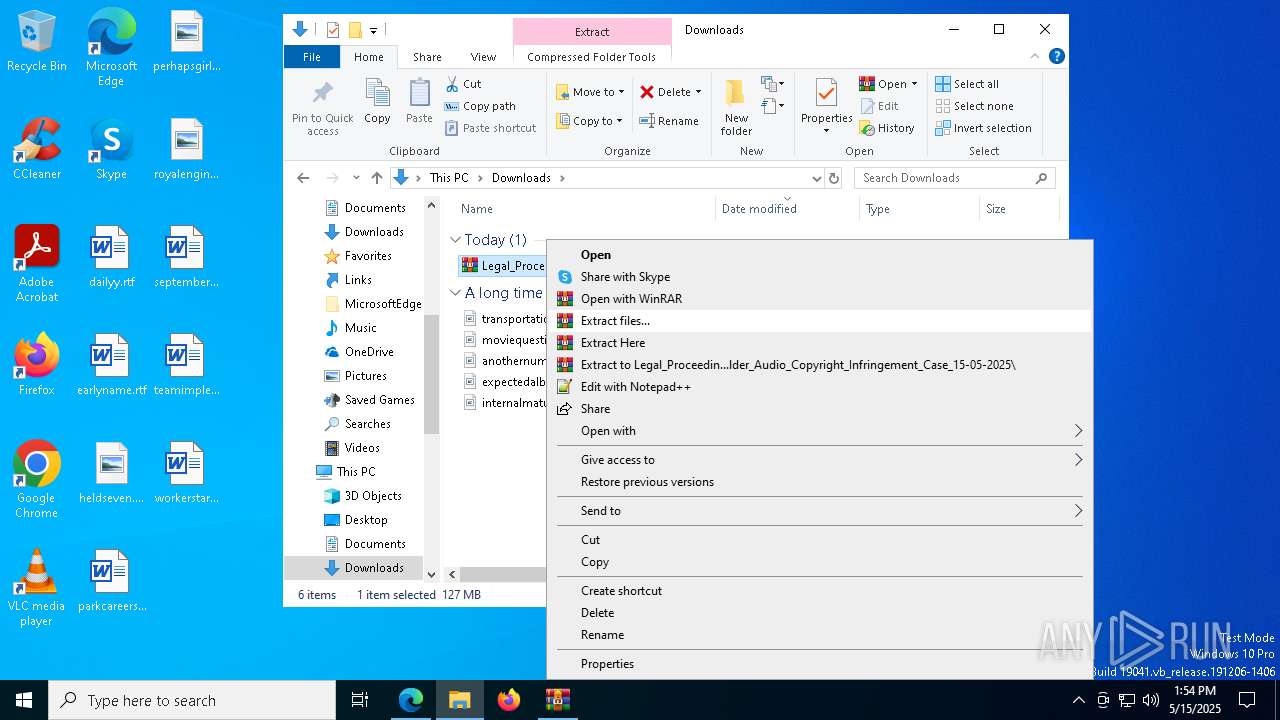
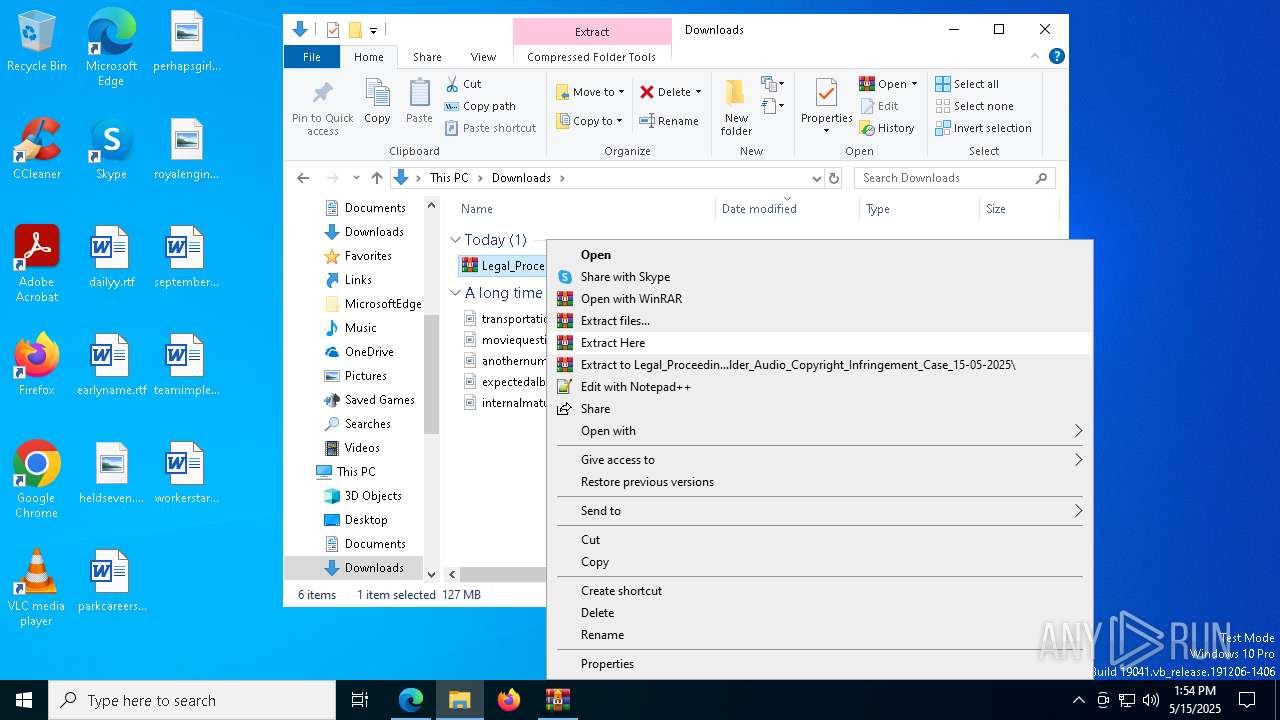
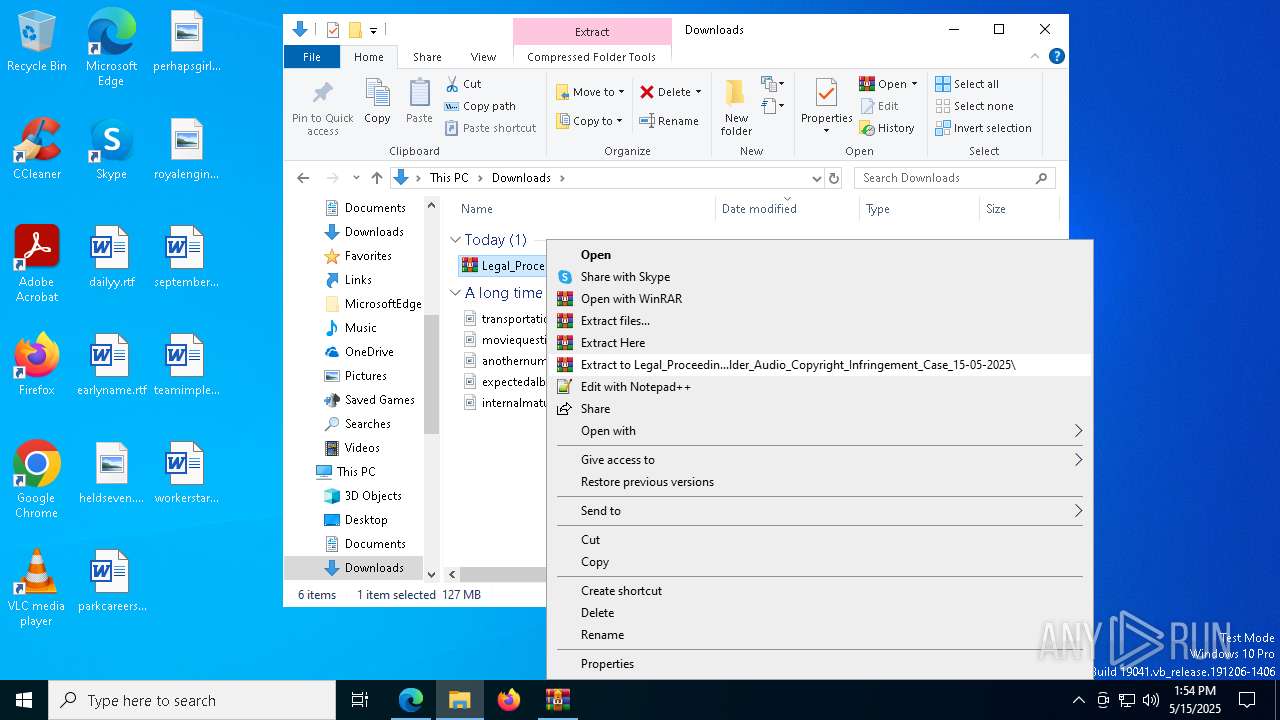
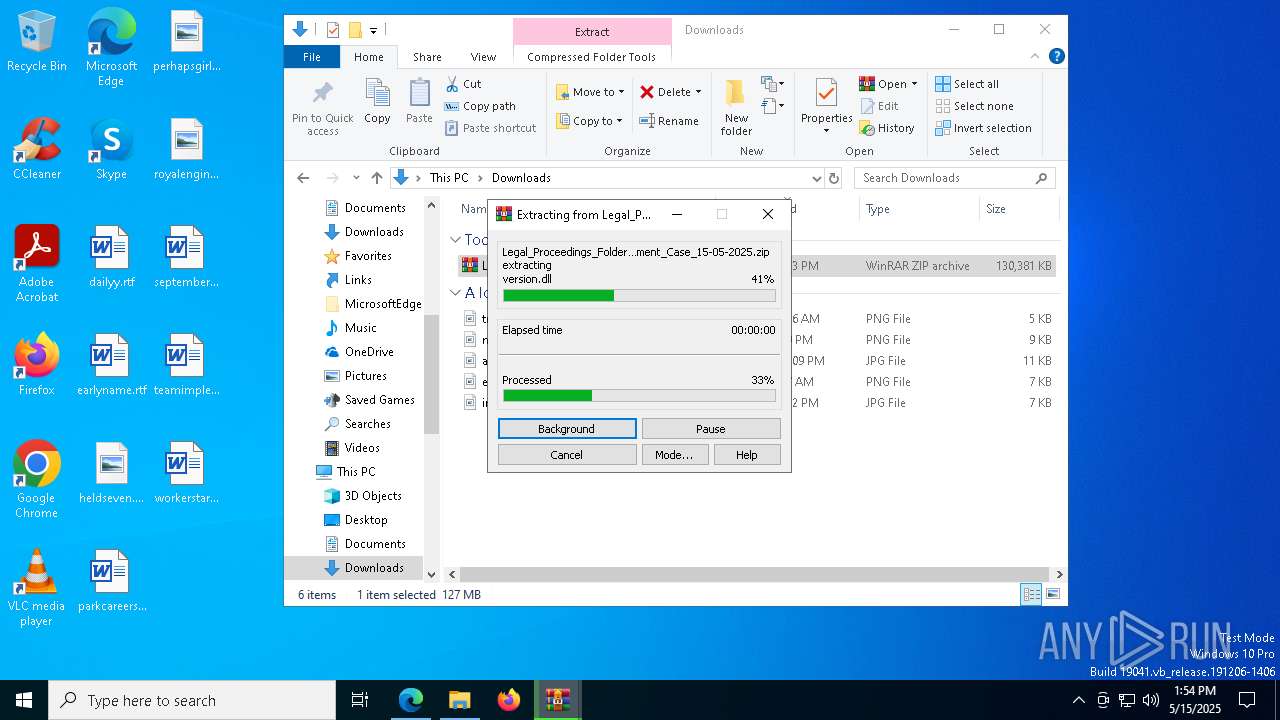
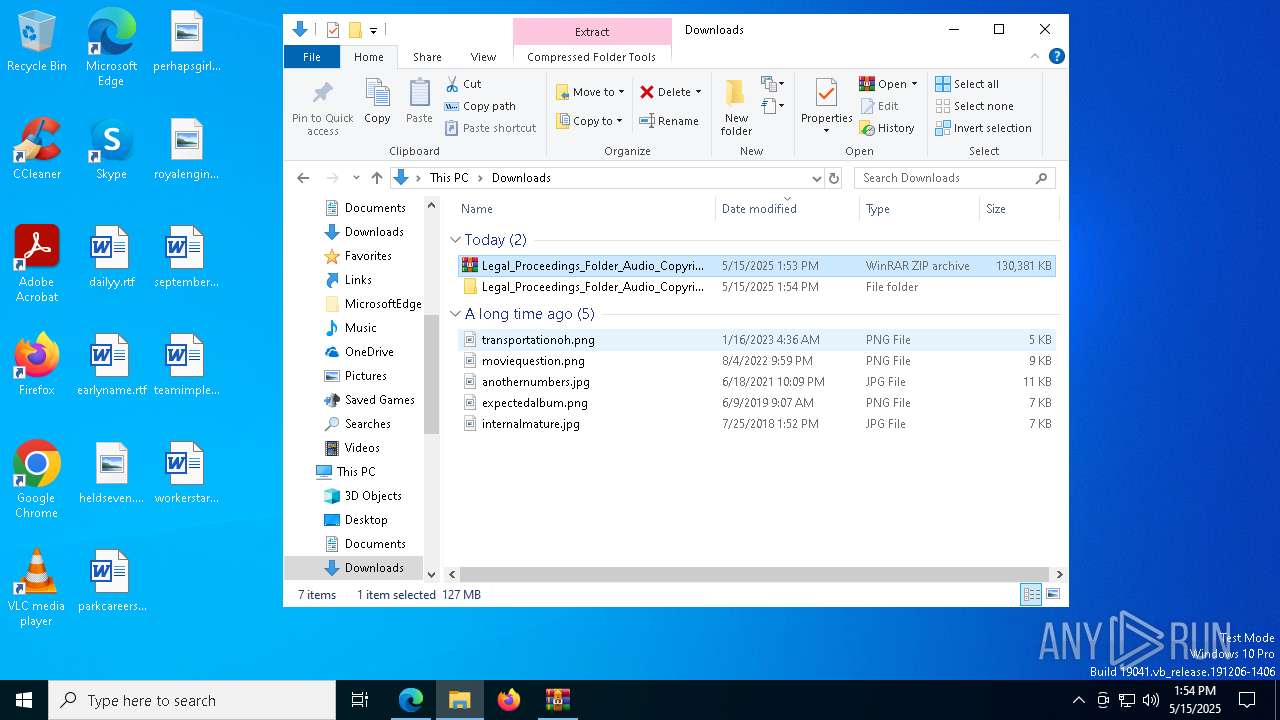
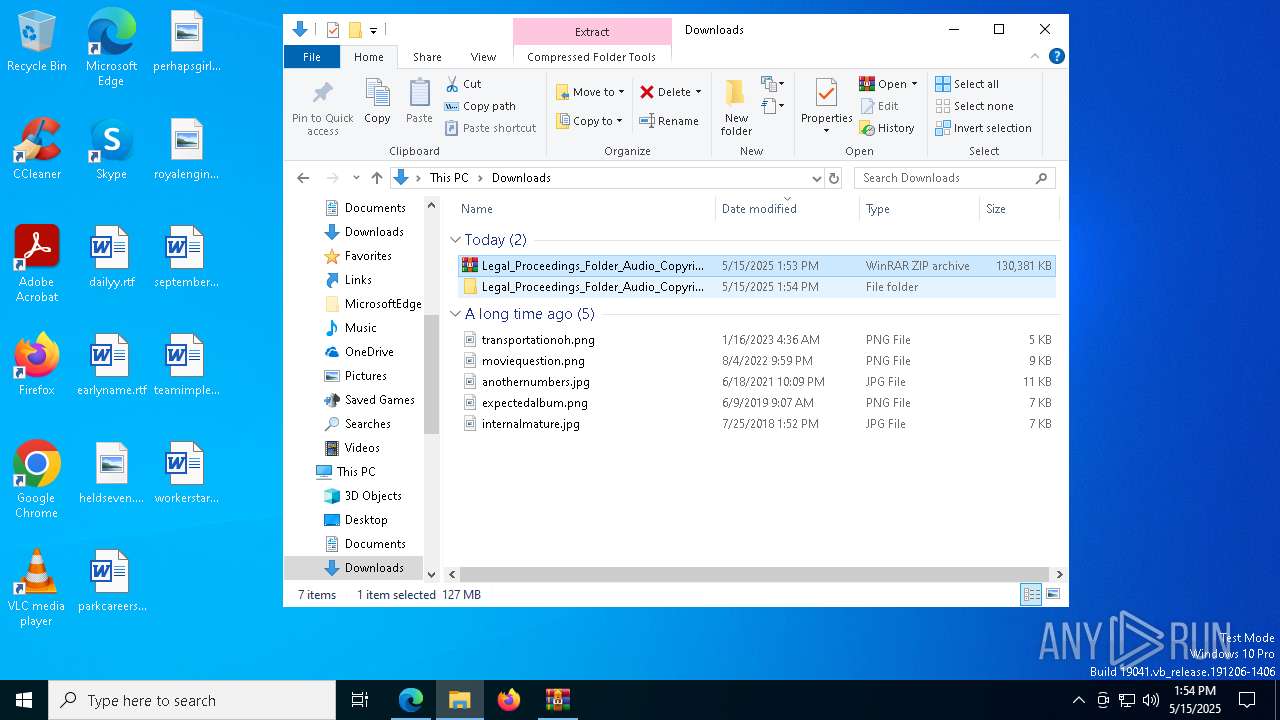
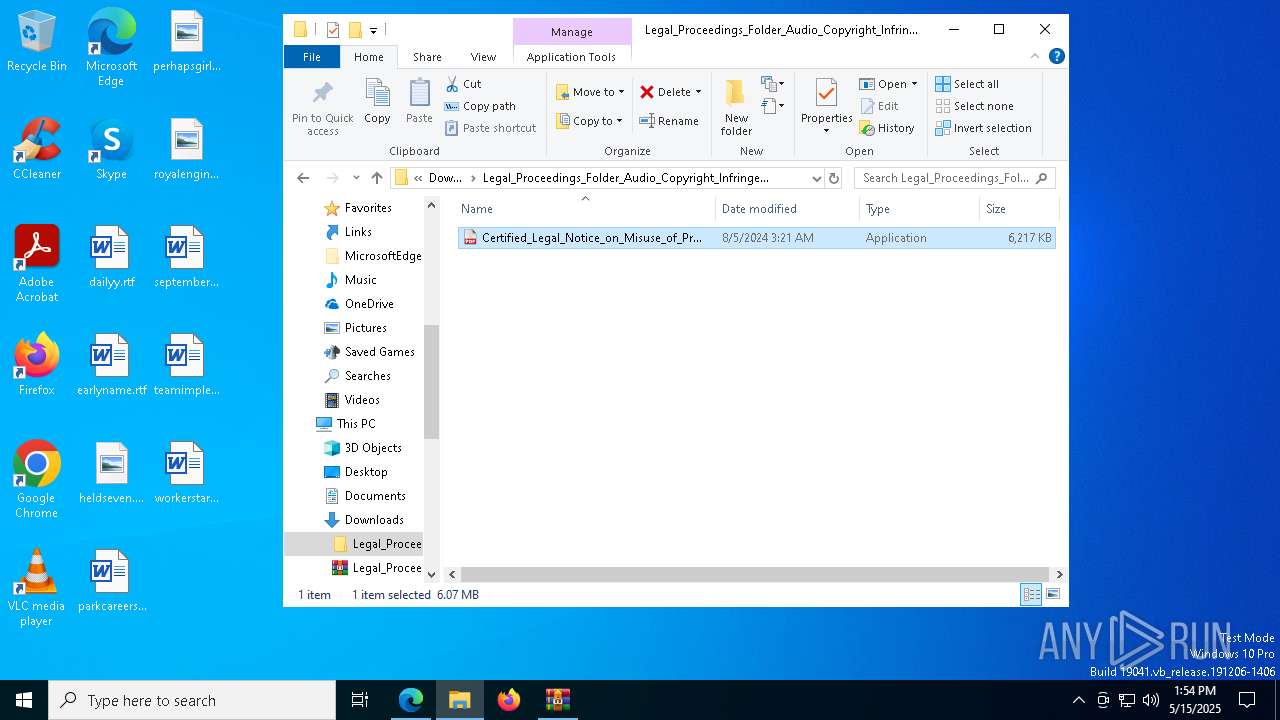
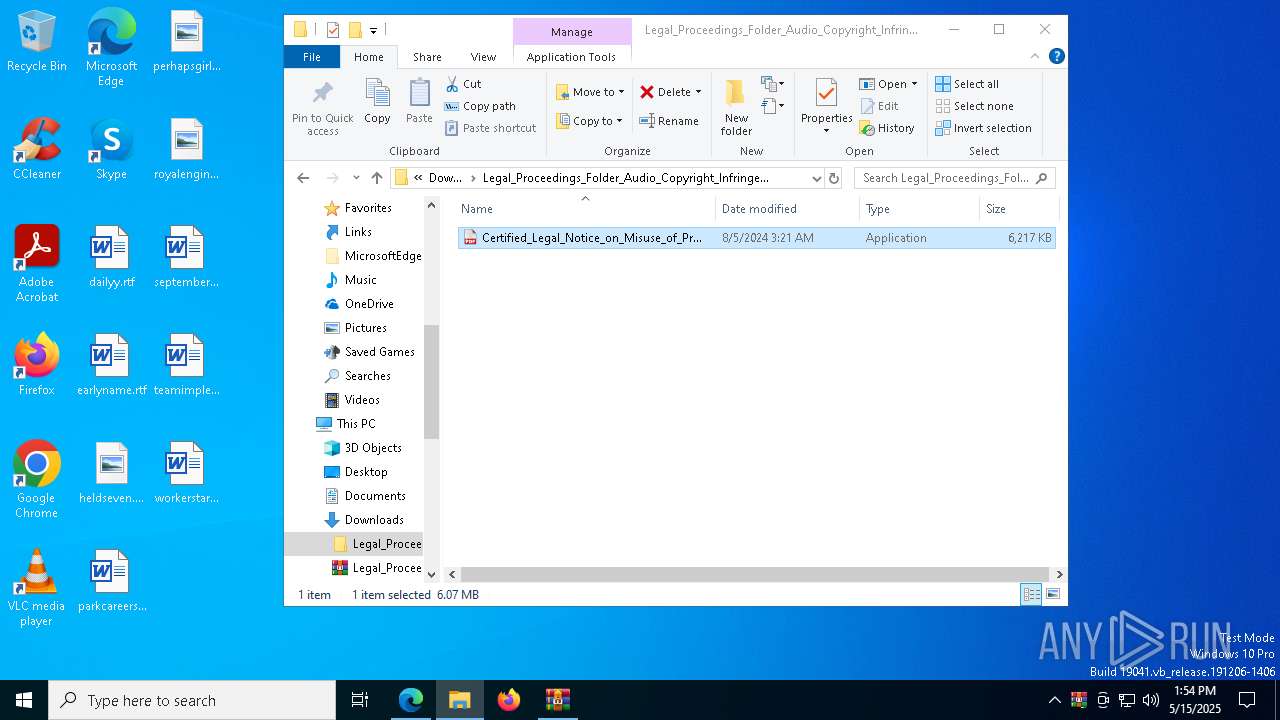
Process drops legitimate windows executable
- WinRAR.exe (PID: 6988)
- WinRAR.exe (PID: 7784)
- Images.png (PID: 6944)
Starts application with an unusual extension
- cmd.exe (PID: 1180)
Process drops python dynamic module
- Images.png (PID: 6944)
Executable content was dropped or overwritten
- Images.png (PID: 6944)
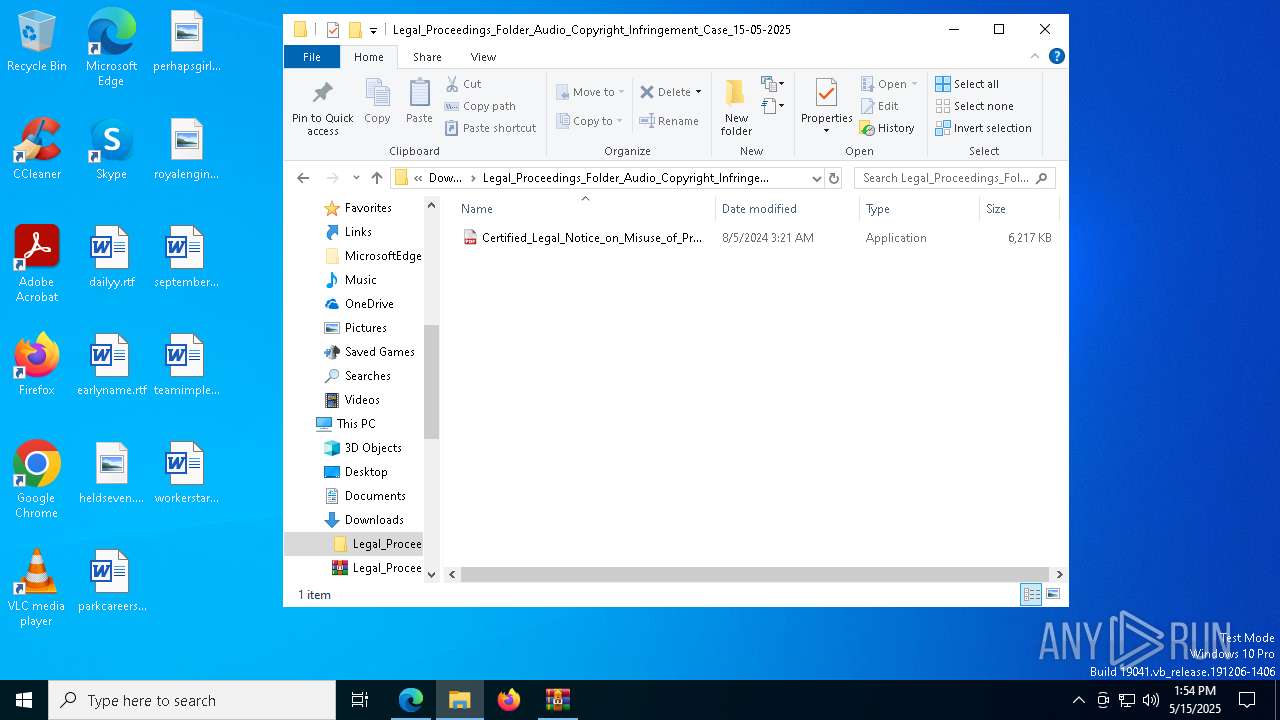
Starts CMD.EXE for commands execution
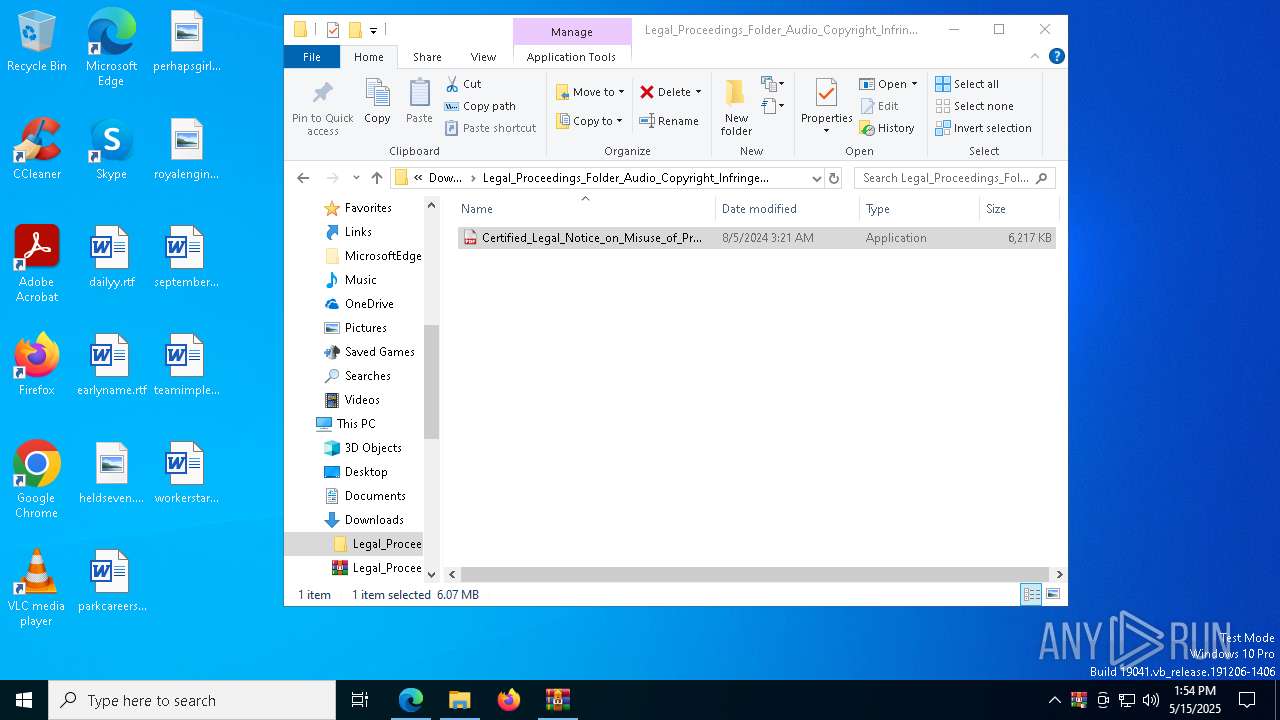
- Certified_Legal_Notice_on_Misuse_of_Protected_Audio_Work_15-05-2025.exe (PID: 3784)
- svchost.exe (PID: 8188)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 1180)
- svchost.exe (PID: 8188)
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 1180)
The executable file from the user directory is run by the CMD process
- Images.png (PID: 6944)
Possible usage of Discord/Telegram API has been detected (YARA)
- svchost.exe (PID: 8188)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 7884)
- cmd.exe (PID: 856)
There is functionality for taking screenshot (YARA)
- Images.png (PID: 6944)
The process drops C-runtime libraries
- Images.png (PID: 6944)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 8188)
Checks for external IP
- svchost.exe (PID: 2196)
INFO
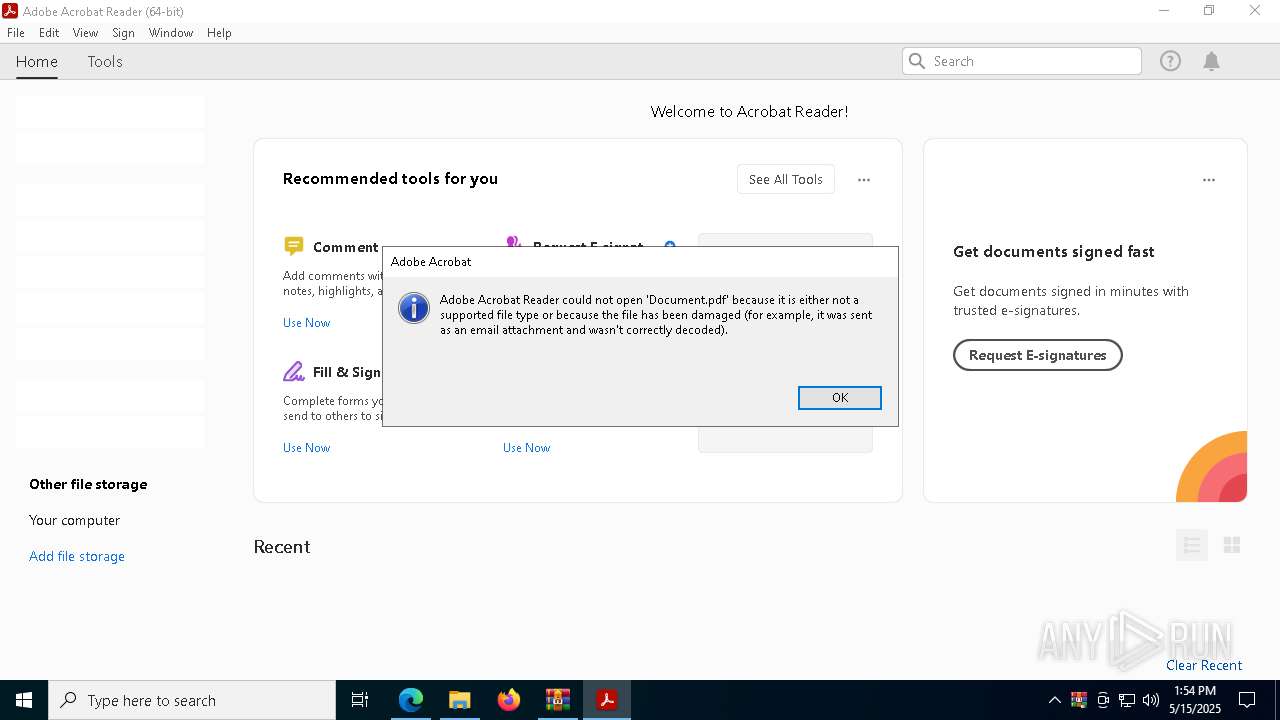
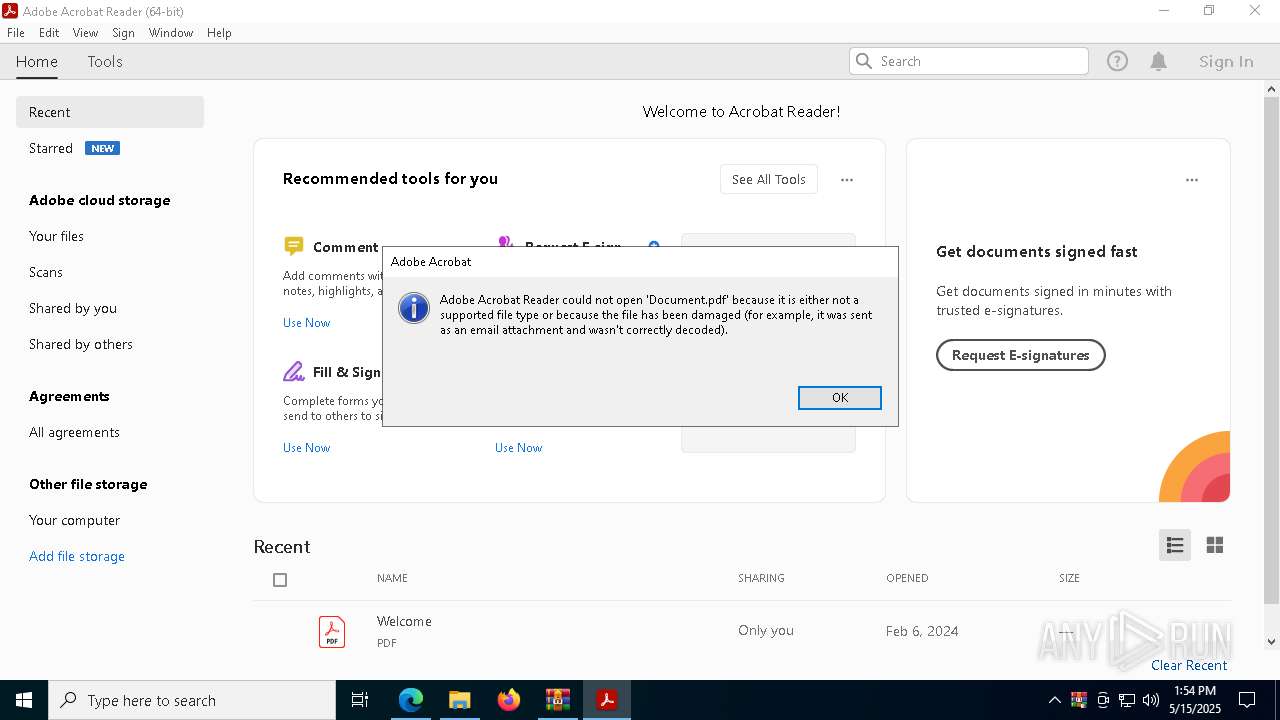
Application launched itself
- msedge.exe (PID: 3332)
- Acrobat.exe (PID: 2316)
- AcroCEF.exe (PID: 7848)
- msedge.exe (PID: 3896)
- chrome.exe (PID: 872)
Reads the computer name
- identity_helper.exe (PID: 1164)
Checks supported languages
- identity_helper.exe (PID: 1164)
- Certified_Legal_Notice_on_Misuse_of_Protected_Audio_Work_15-05-2025.exe (PID: 3784)
Reads Environment values
- identity_helper.exe (PID: 1164)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3332)
Reads the software policy settings
- slui.exe (PID: 4408)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6988)
- WinRAR.exe (PID: 7784)
- msedge.exe (PID: 8140)
The sample compiled with english language support
- WinRAR.exe (PID: 6988)
- WinRAR.exe (PID: 7784)
- Images.png (PID: 6944)
- msedge.exe (PID: 8140)
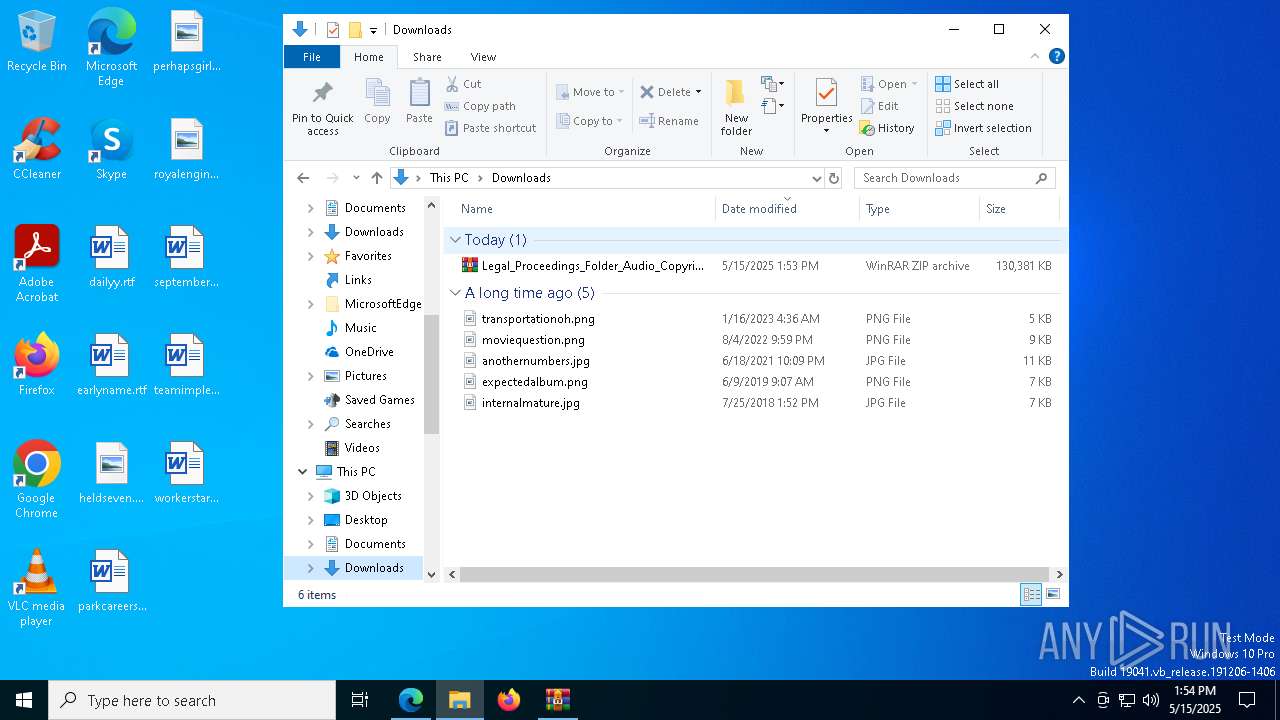
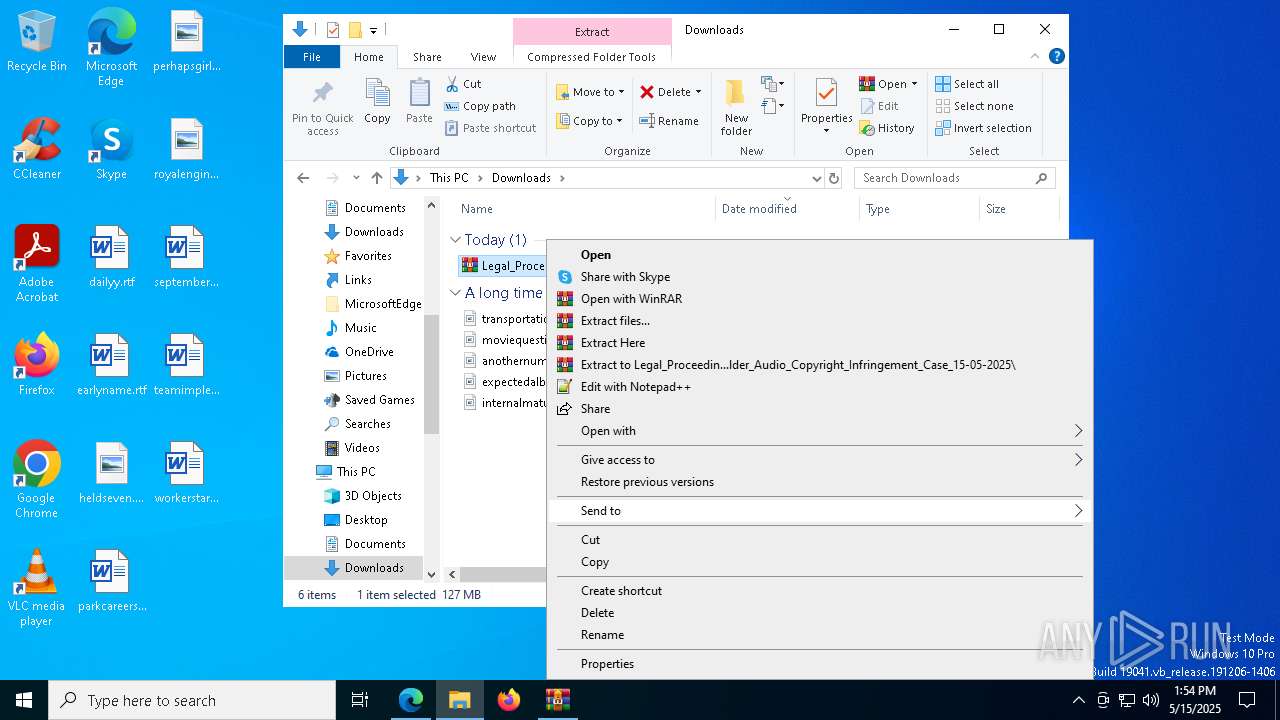
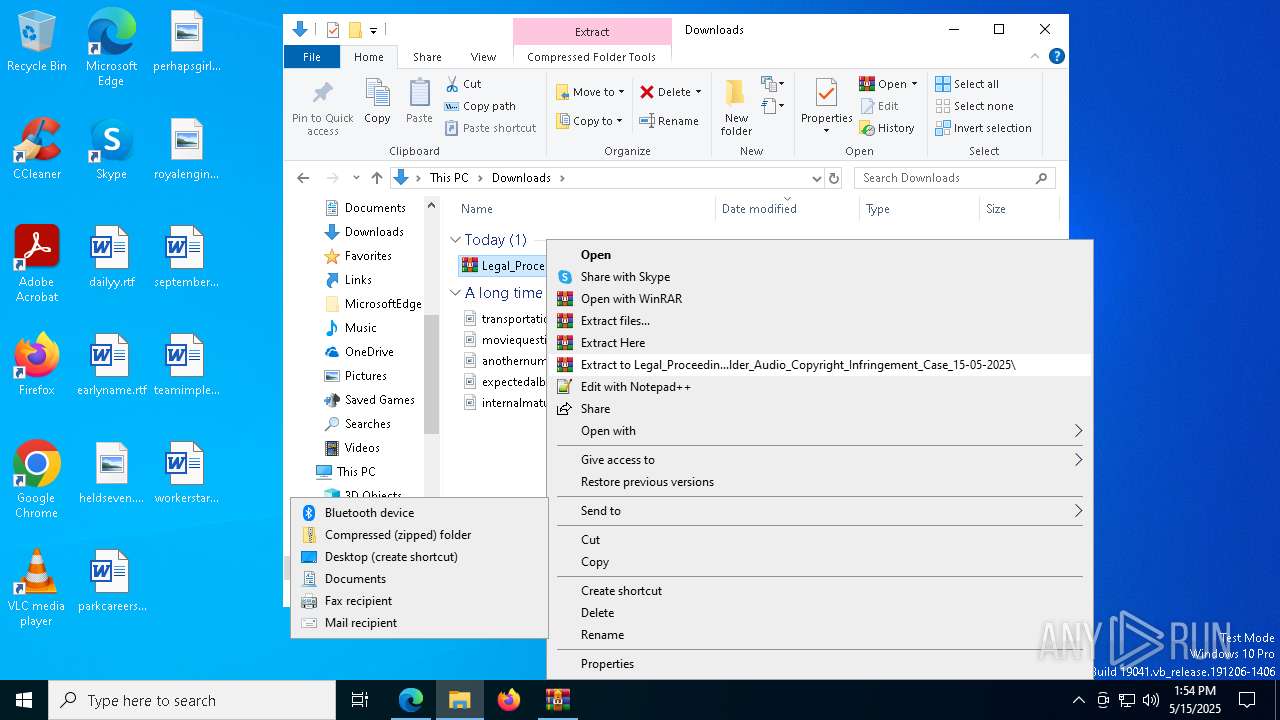
Manual execution by a user
- WinRAR.exe (PID: 7784)
- Certified_Legal_Notice_on_Misuse_of_Protected_Audio_Work_15-05-2025.exe (PID: 3784)
Python executable
- svchost.exe (PID: 8188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(8188) svchost.exe
Telegram-Tokens (1)7414494371:AAHsrQDkPrEVyz9z0RoiRS5fJKI-ihKJpzQ
Telegram-Info-Links
7414494371:AAHsrQDkPrEVyz9z0RoiRS5fJKI-ihKJpzQ
Get info about bothttps://api.telegram.org/bot7414494371:AAHsrQDkPrEVyz9z0RoiRS5fJKI-ihKJpzQ/getMe
Get incoming updateshttps://api.telegram.org/bot7414494371:AAHsrQDkPrEVyz9z0RoiRS5fJKI-ihKJpzQ/getUpdates
Get webhookhttps://api.telegram.org/bot7414494371:AAHsrQDkPrEVyz9z0RoiRS5fJKI-ihKJpzQ/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7414494371:AAHsrQDkPrEVyz9z0RoiRS5fJKI-ihKJpzQ/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7414494371:AAHsrQDkPrEVyz9z0RoiRS5fJKI-ihKJpzQ/deleteWebhook?drop_pending_updates=true
Total processes
225
Monitored processes
91
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6456 --field-trial-handle=2728,i,17440045612421881096,609314215613342806,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5132 --field-trial-handle=2728,i,17440045612421881096,609314215613342806,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1564 --field-trial-handle=1636,i,9777529324883011214,7588193948718974357,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5688 --field-trial-handle=2728,i,17440045612421881096,609314215613342806,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | C:\WINDOWS\system32\cmd.exe /c "taskkill /f /im chrome.exe" | C:\Windows\SysWOW64\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --remote-debugging-port=9909 "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --profile-directory=Default --remote-allow-origins=* --headless | C:\Program Files\Google\Chrome\Application\chrome.exe | — | svchost.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2172 --field-trial-handle=1636,i,9777529324883011214,7588193948718974357,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5776 --field-trial-handle=2728,i,17440045612421881096,609314215613342806,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --headless --use-angle=swiftshader-webgl --headless --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --use-gl=angle --mojo-platform-channel-handle=1476 --field-trial-handle=1480,i,10066204263525911104,458468103828306259,262144 --disable-features=PaintHolding --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5132 --field-trial-handle=2728,i,17440045612421881096,609314215613342806,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
20 439
Read events
20 224
Write events
192
Delete events
23
Modification events
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B18B8342C3932F00 | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 33D98C42C3932F00 | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D55ED528-BF50-4F20-827D-AFA0738F7344} | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4B935C92-A2BC-4537-B2AC-ECD6572FB3DB} | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2B60E2B9-895A-4480-8AE5-9743FA77B813} | |||
| (PID) Process: | (3332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D2105857-64DE-4884-B055-81A9BF172D26} | |||
Executable files
144
Suspicious files
1 042
Text files
1 489
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b6a0.TMP | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b6a0.TMP | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b6a0.TMP | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b6a0.TMP | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b6af.TMP | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
72
DNS requests
87
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8084 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747803061&P2=404&P3=2&P4=WBu4nx27ZM4ogtVPQT32PXDfYeZbXzNF3OGrR2hcH54QV0fEZRSEePiDmKuh1zxBTwbvnIpcmKo2qUSIF6JIww%3d%3d | unknown | — | — | whitelisted |
7652 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7652 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8084 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747803061&P2=404&P3=2&P4=WBu4nx27ZM4ogtVPQT32PXDfYeZbXzNF3OGrR2hcH54QV0fEZRSEePiDmKuh1zxBTwbvnIpcmKo2qUSIF6JIww%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1747803061&P2=404&P3=2&P4=WBu4nx27ZM4ogtVPQT32PXDfYeZbXzNF3OGrR2hcH54QV0fEZRSEePiDmKuh1zxBTwbvnIpcmKo2qUSIF6JIww%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747803060&P2=404&P3=2&P4=fCZdco5KzMeaWmWGCzlCC0%2fRnmc6TcCW28KK%2f1wqPTkdQo5NiWPglP6NIj6wzWsXL8a%2fPnAXSXj%2b0t8h%2fJMy%2fQ%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747803061&P2=404&P3=2&P4=Hx9Ti9uNAmmilkvGrDgKa6yADO5DRMkOshgWHsN3tRGzF0TgYaLdWBglkOjKdUwSfqkLApAdlOiwzqTn%2fEtC3g%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747803060&P2=404&P3=2&P4=fCZdco5KzMeaWmWGCzlCC0%2fRnmc6TcCW28KK%2f1wqPTkdQo5NiWPglP6NIj6wzWsXL8a%2fPnAXSXj%2b0t8h%2fJMy%2fQ%3d%3d | unknown | — | — | whitelisted |
8084 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747803061&P2=404&P3=2&P4=Hx9Ti9uNAmmilkvGrDgKa6yADO5DRMkOshgWHsN3tRGzF0TgYaLdWBglkOjKdUwSfqkLApAdlOiwzqTn%2fEtC3g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7340 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | msedge.exe | 150.171.29.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | msedge.exe | 104.26.2.56:443 | — | — | — | unknown |
3332 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7340 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
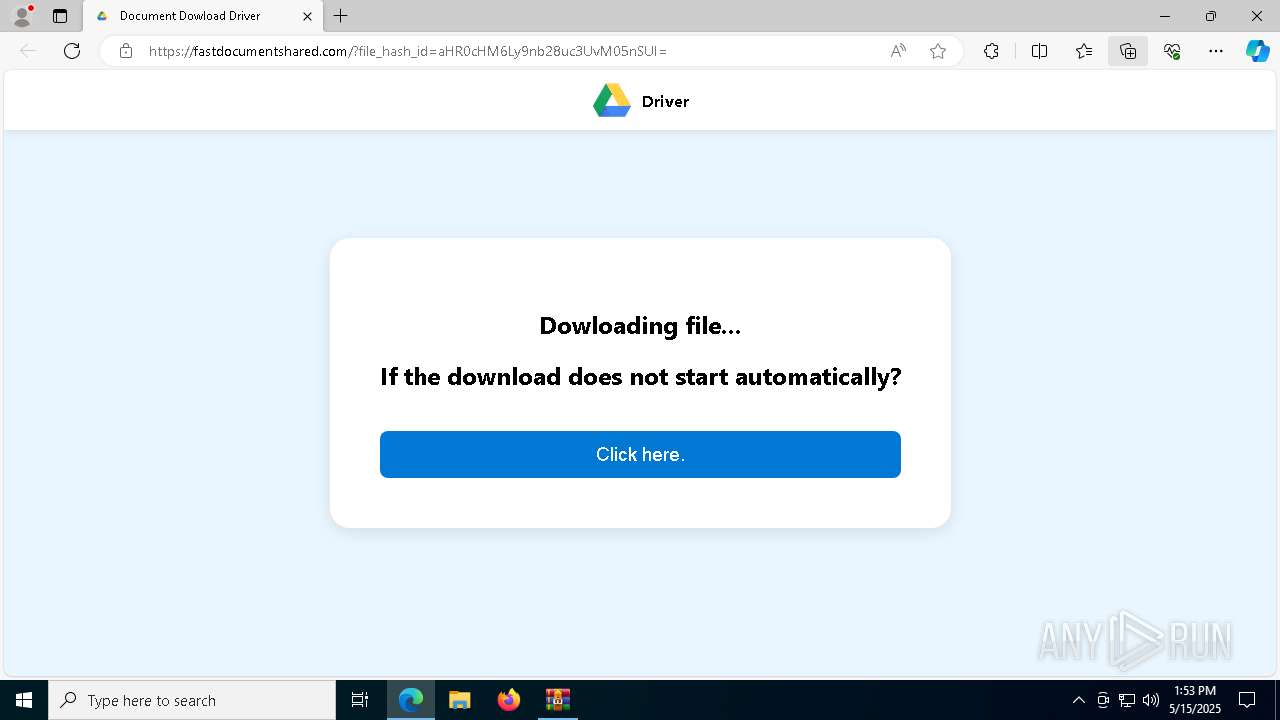
7340 | msedge.exe | 104.21.76.107:443 | fastdocumentshared.com | CLOUDFLARENET | — | unknown |
7340 | msedge.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
goo.su |
| unknown |
business.bing.com |
| whitelisted |
fastdocumentshared.com |
| unknown |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
upload.wikimedia.org |
| whitelisted |
region1.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7340 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
7340 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
7340 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
7340 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (goo .su) |
7340 | msedge.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (goo .su in TLS SNI) |
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |