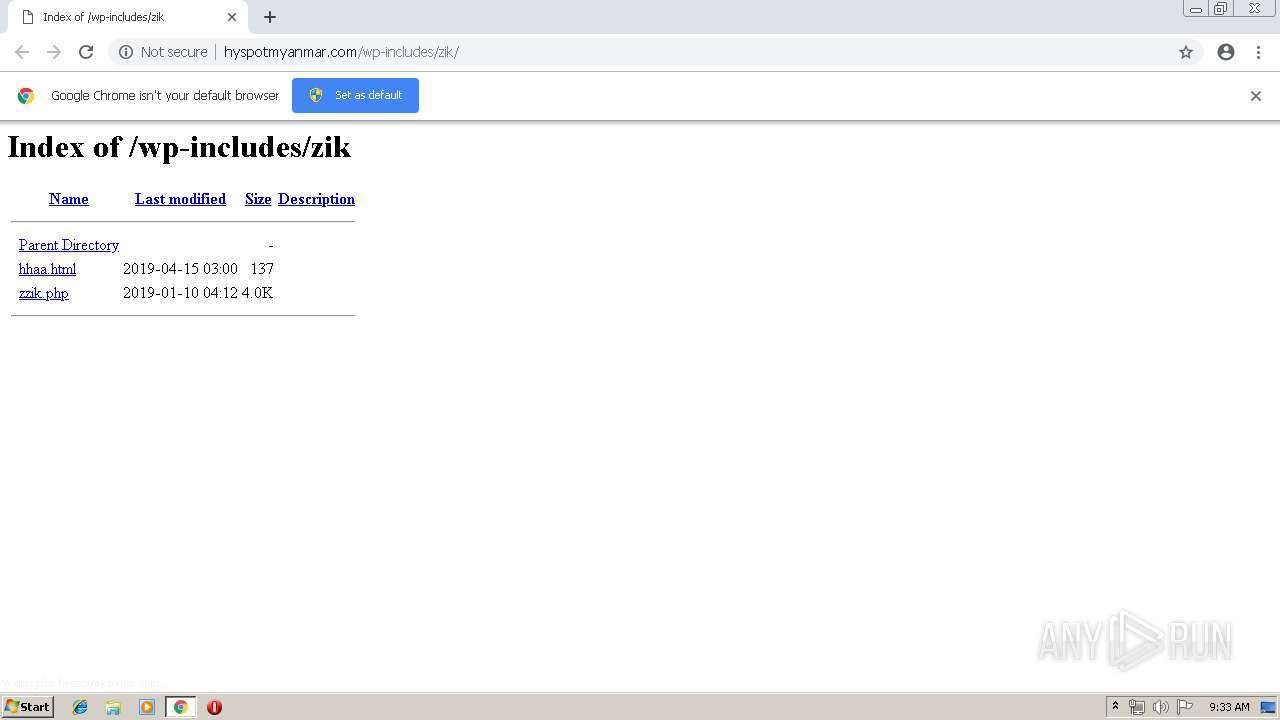
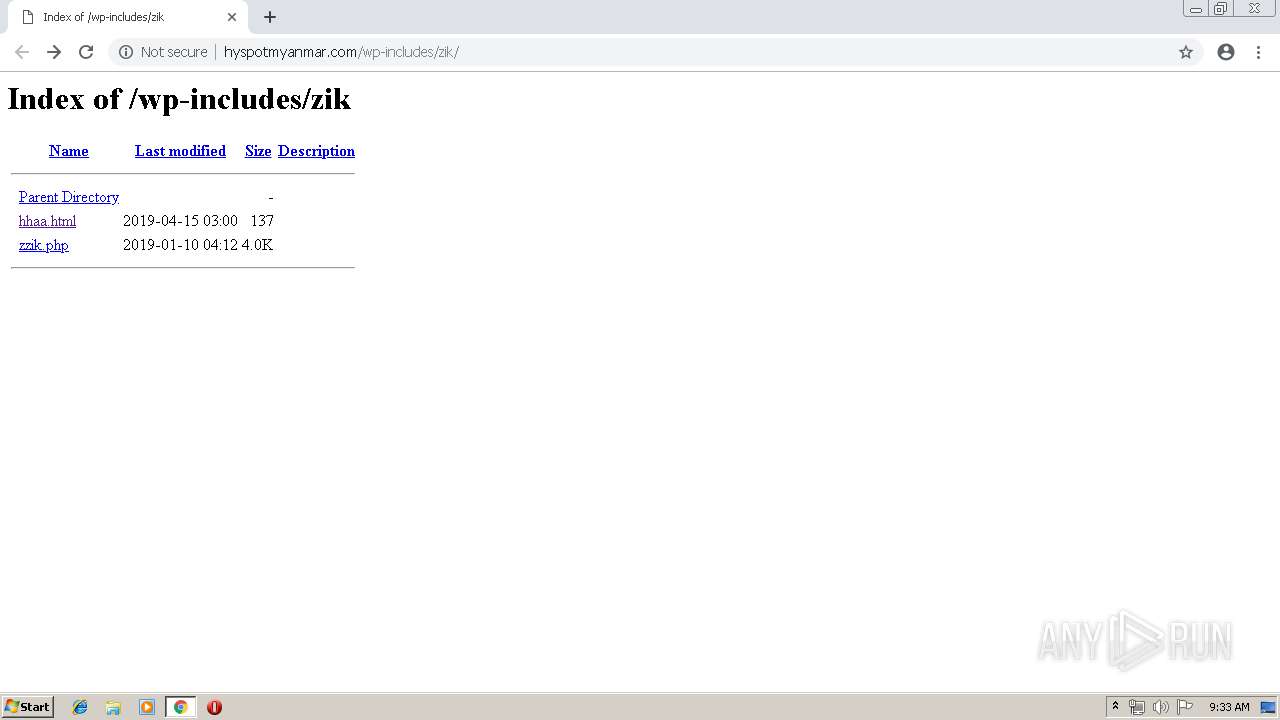
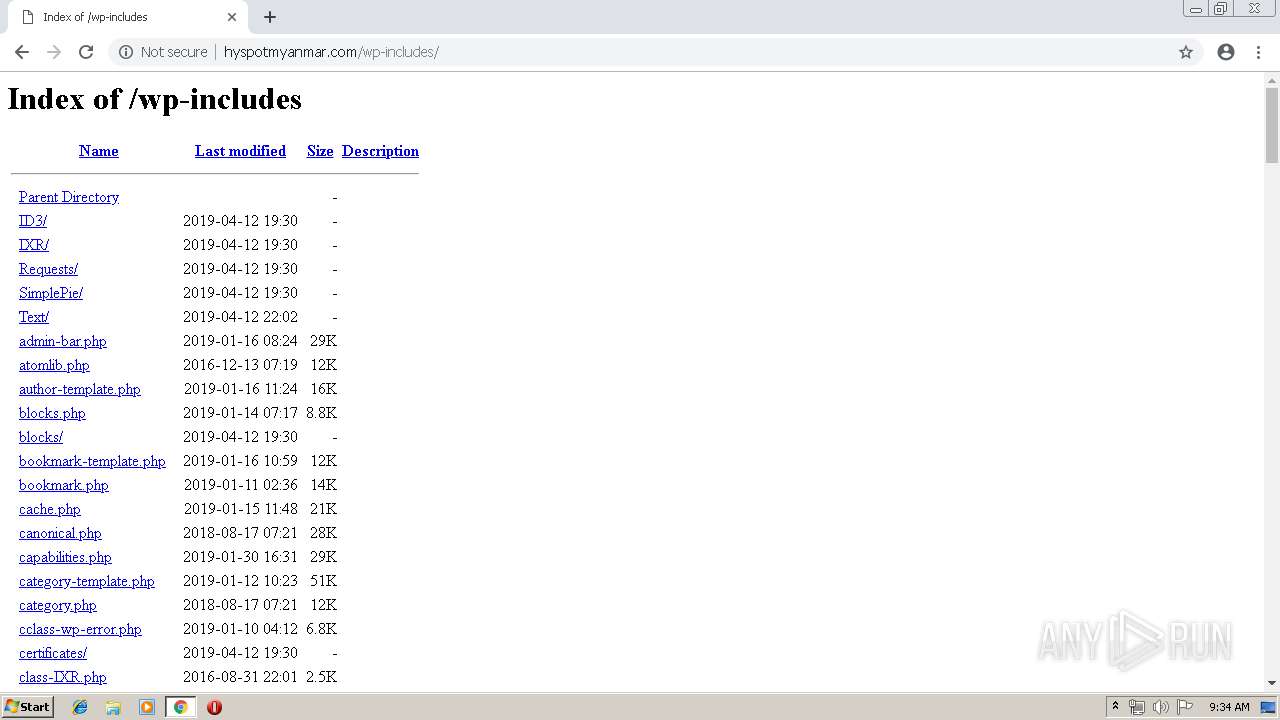
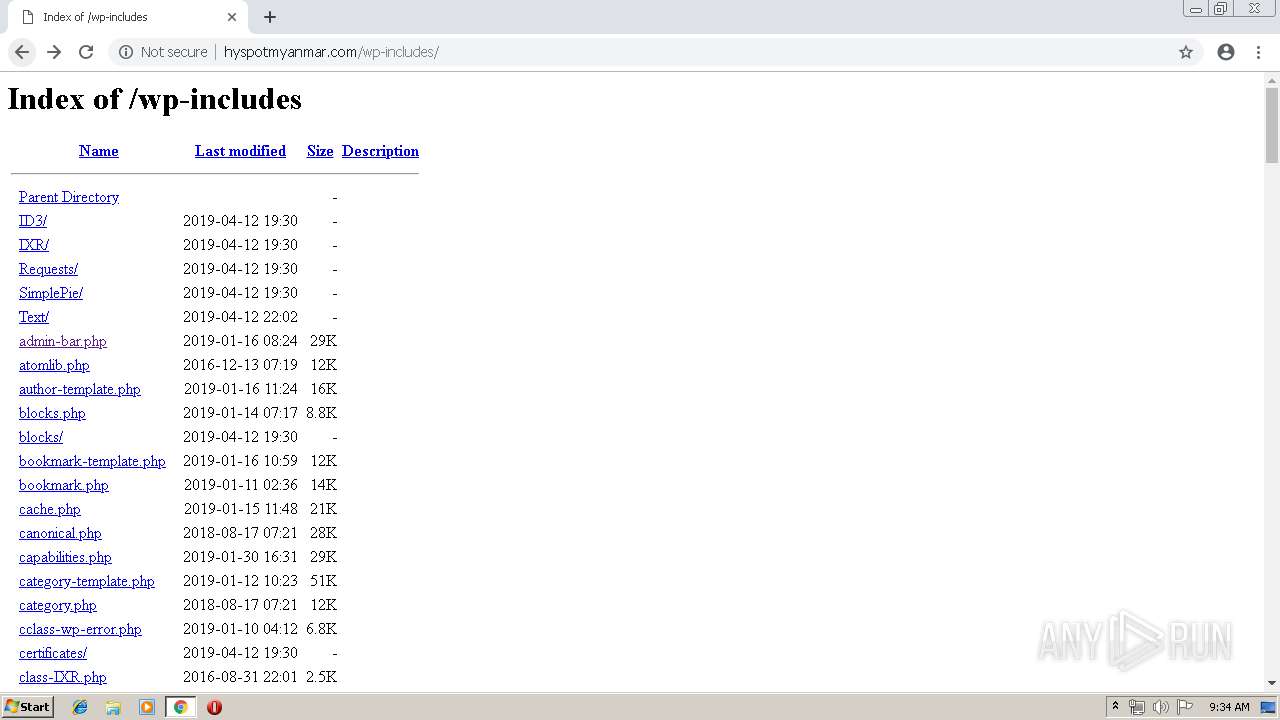
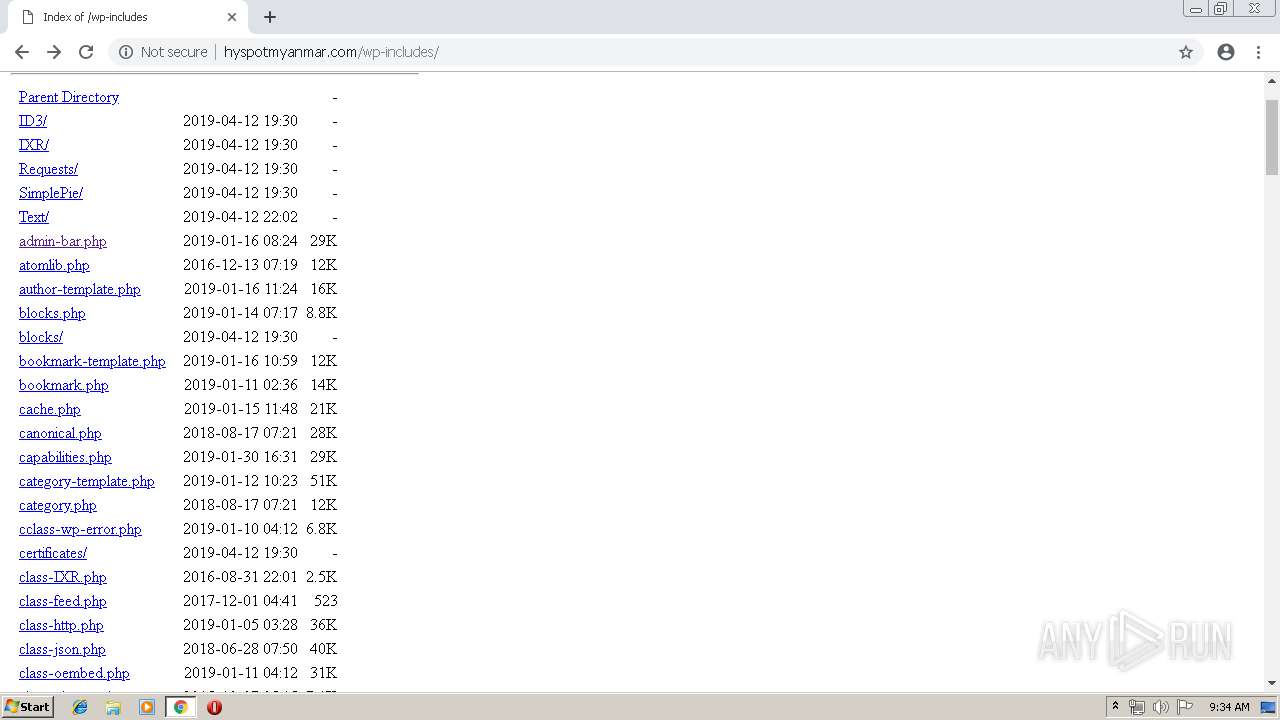
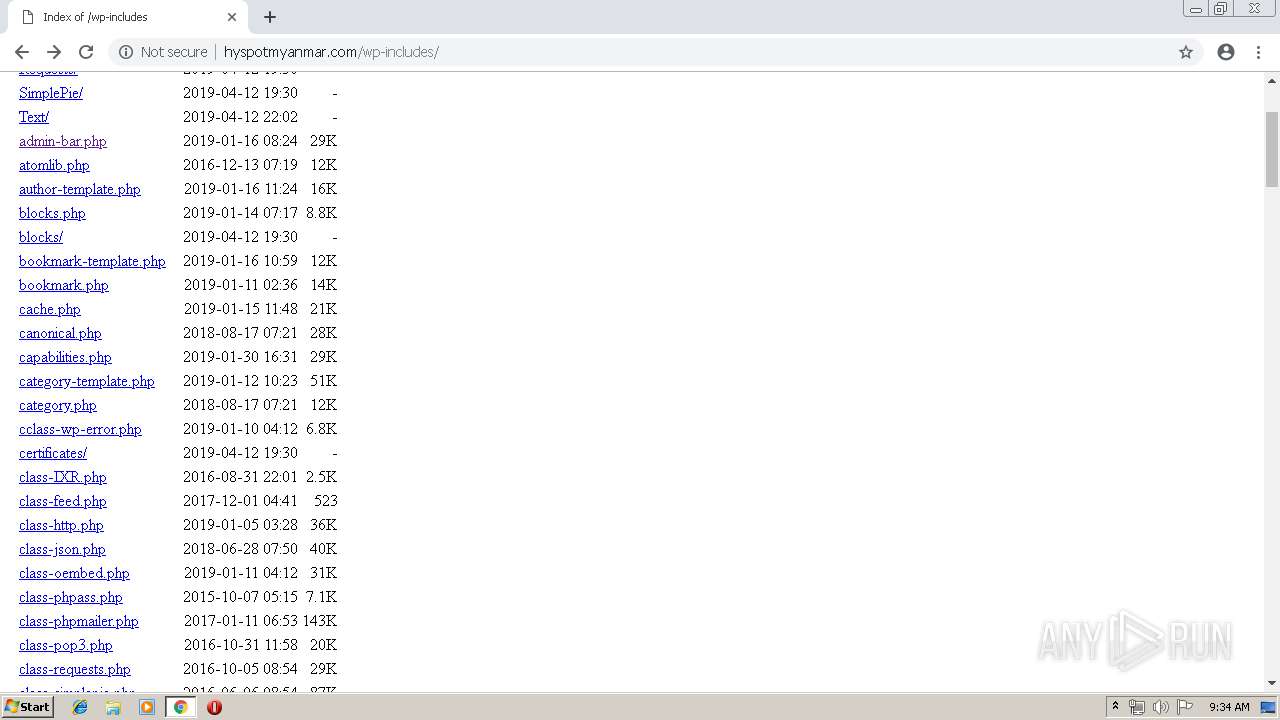
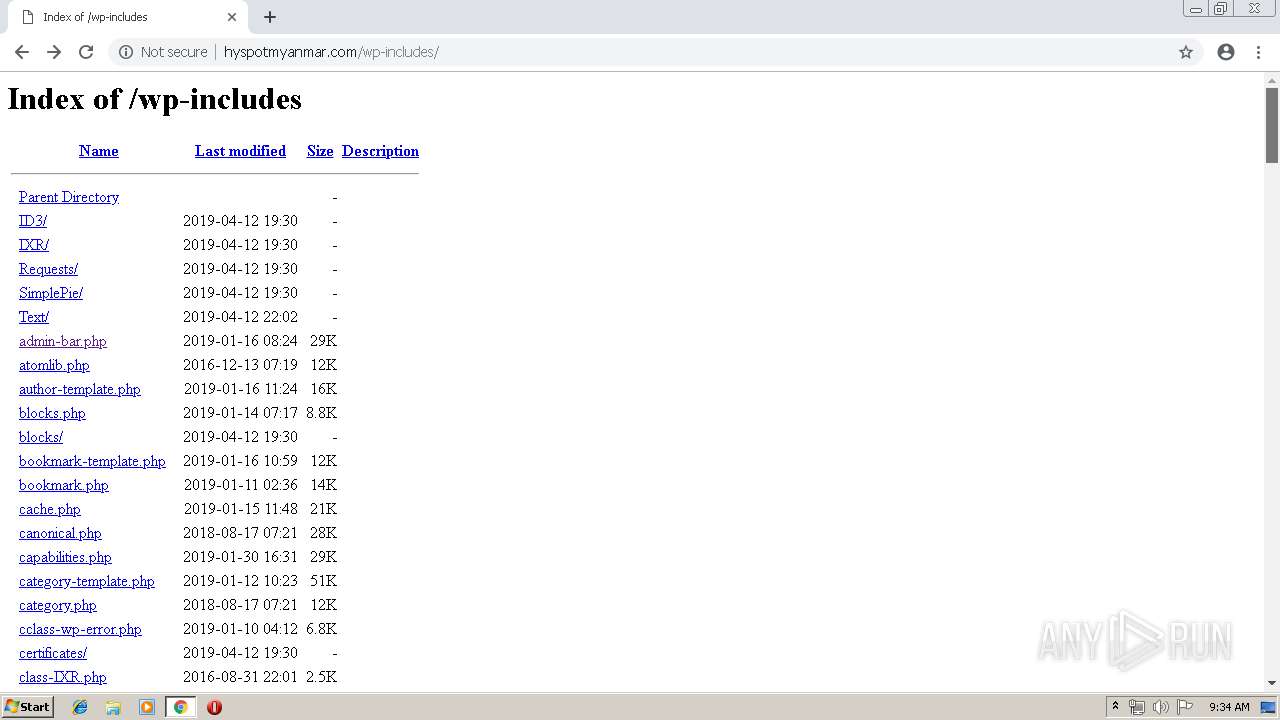
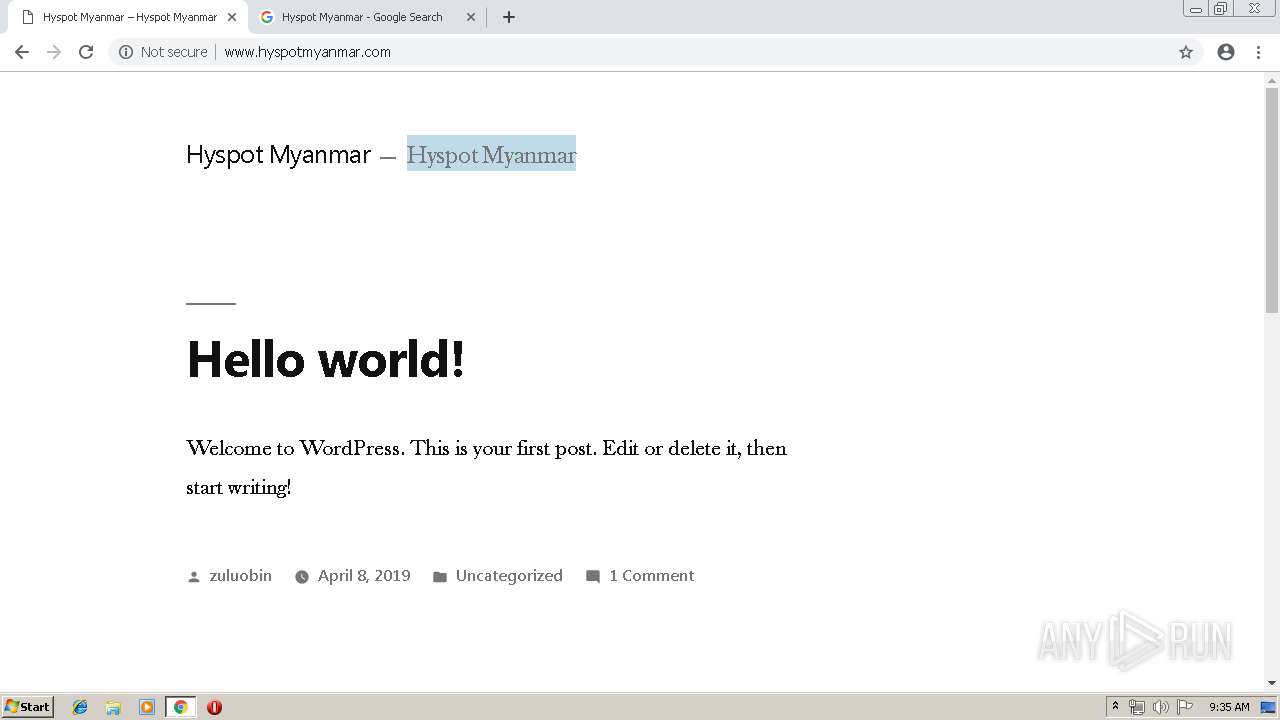
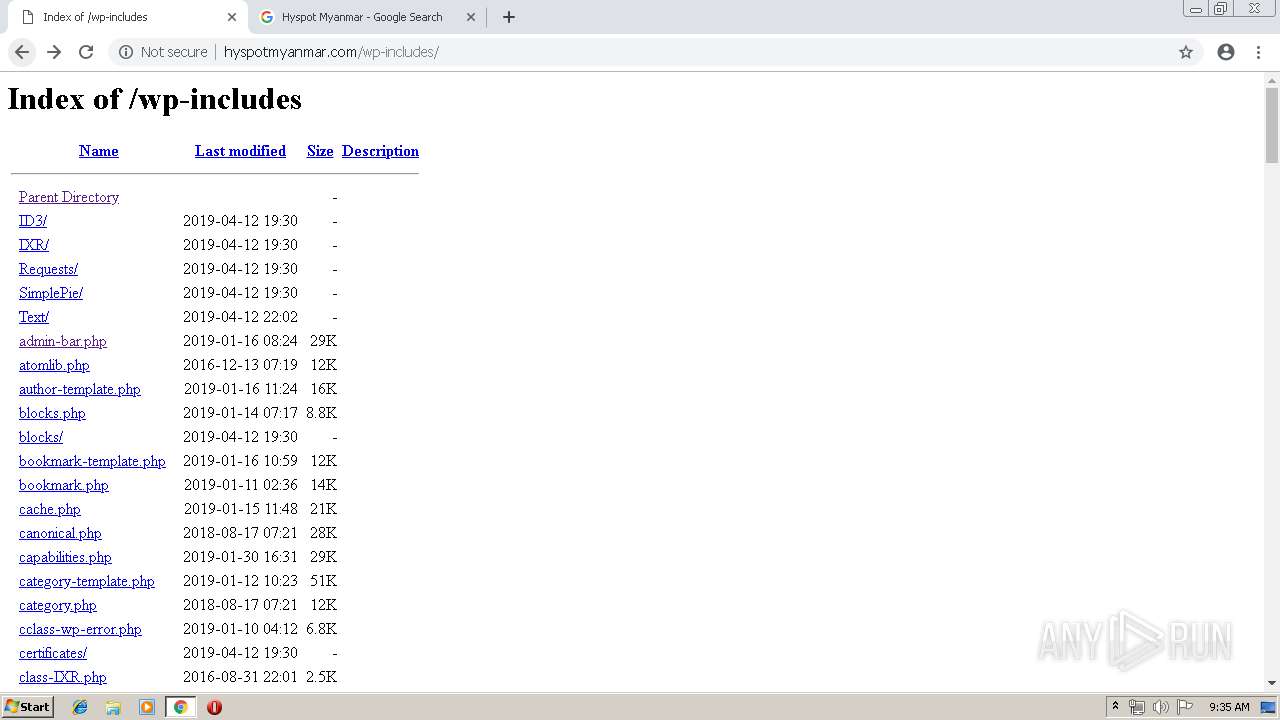
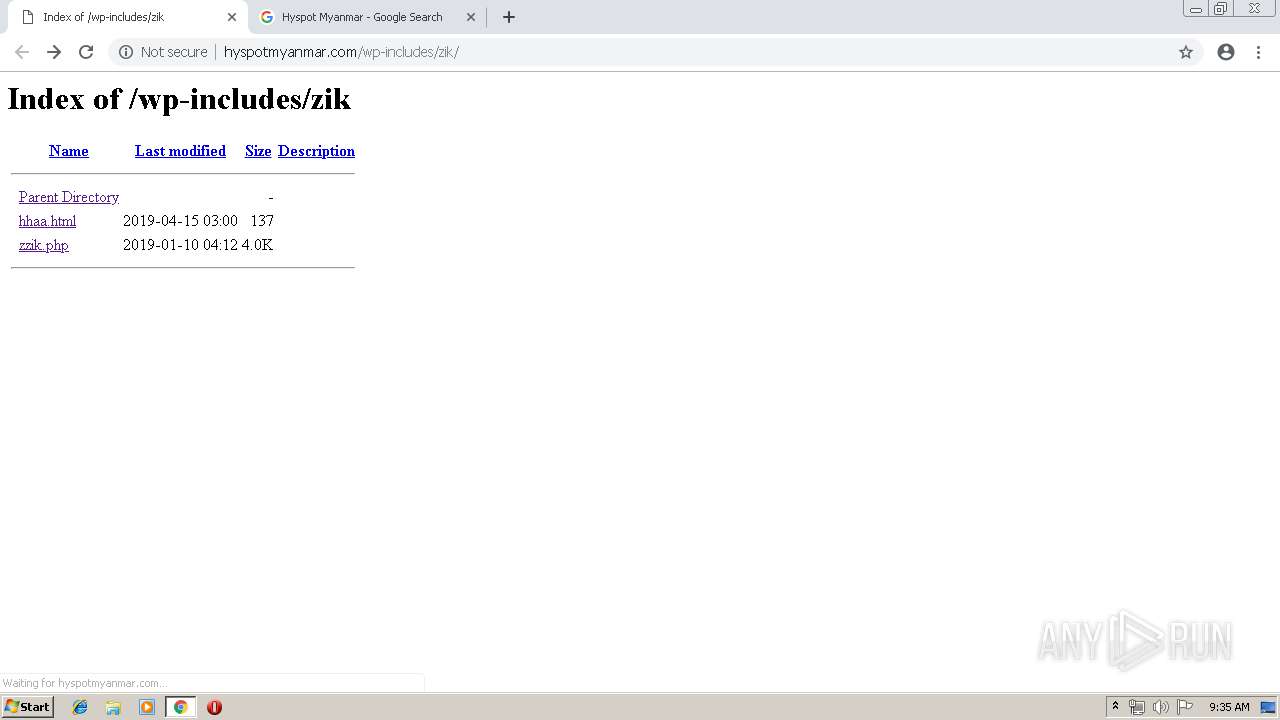
| URL: | http://hyspotmyanmar.com/wp-includes/zik |
| Full analysis: | https://app.any.run/tasks/b88e7a59-735c-43a0-8679-31b3679903c8 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 08:33:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F5290EF86DA4F7BD3221185EC29249E5 |
| SHA1: | 164C16A193F223CBEE4D9BBA6F9B0EAF59C5F406 |
| SHA256: | FB97D428AAE93936A99E6C237C13C6000B2ADE9C974D74430E0E1825C7A10A9B |
| SSDEEP: | 3:N1KWc5u7gUe2R:CWg/UfR |
MALICIOUS
No malicious indicators.SUSPICIOUS
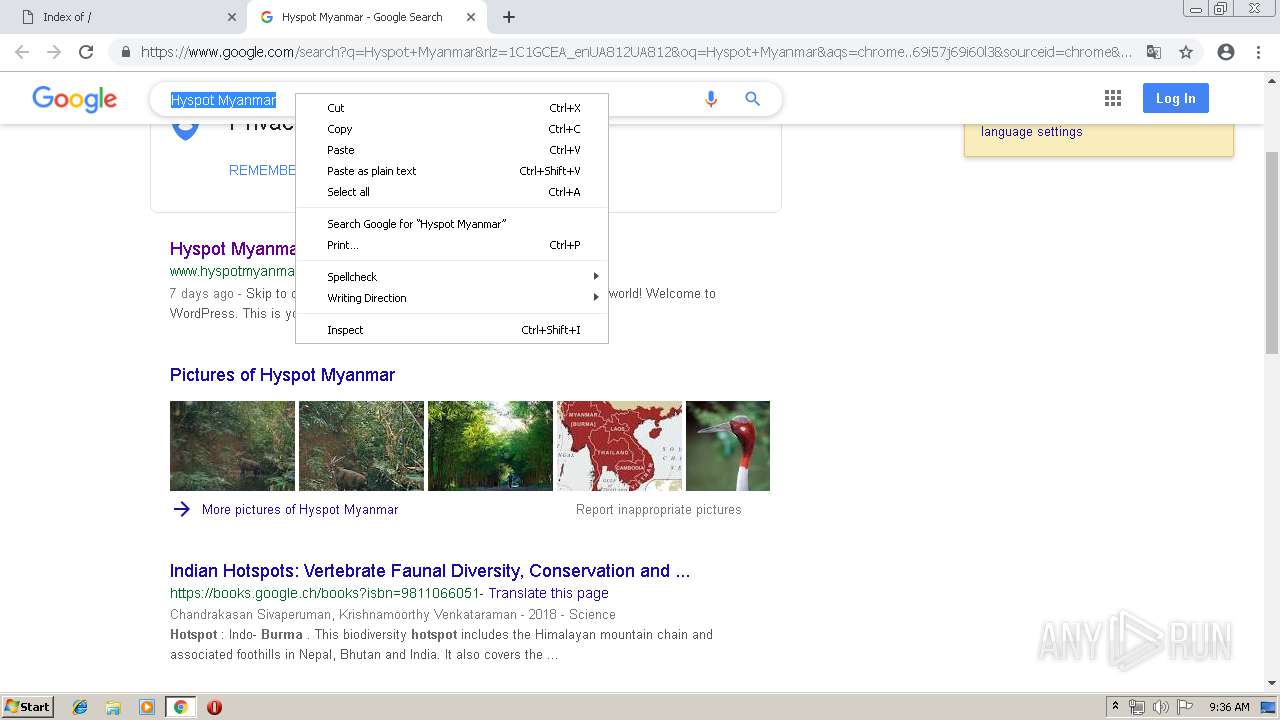
Modifies files in Chrome extension folder
- chrome.exe (PID: 3912)
INFO
Application launched itself
- chrome.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10233624464519313068 --mojo-platform-channel-handle=1508 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10890422505050834990 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10890422505050834990 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=511693891433612147 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=511693891433612147 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12972846307878433203 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12972846307878433203 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12768803790020574164 --mojo-platform-channel-handle=2868 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=770670942843634410 --mojo-platform-channel-handle=3328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17126367039334391711 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17126367039334391711 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3920 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7114342407721008412 --mojo-platform-channel-handle=3244 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,8681400434083708809,201876131481113161,131072 --enable-features=PasswordImport --service-pipe-token=3843540505654937781 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3843540505654937781 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
592
Read events
486
Write events
101
Delete events
5
Modification events
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2180) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3912-13199790802313125 |
Value: 259 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3912-13199790802313125 |
Value: 259 | |||
Executable files
0
Suspicious files
71
Text files
254
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\32957eb3-cf17-4621-ad93-1ef6134b95b8.tmp | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
72
DNS requests
28
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
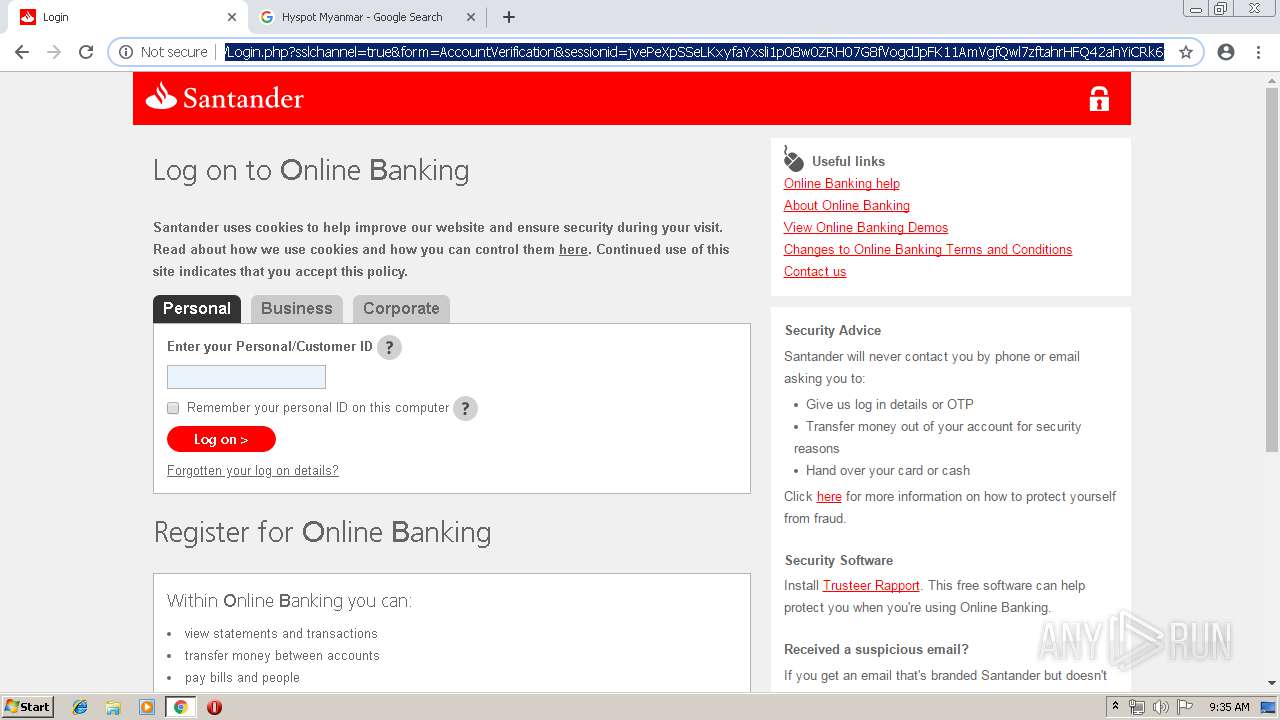
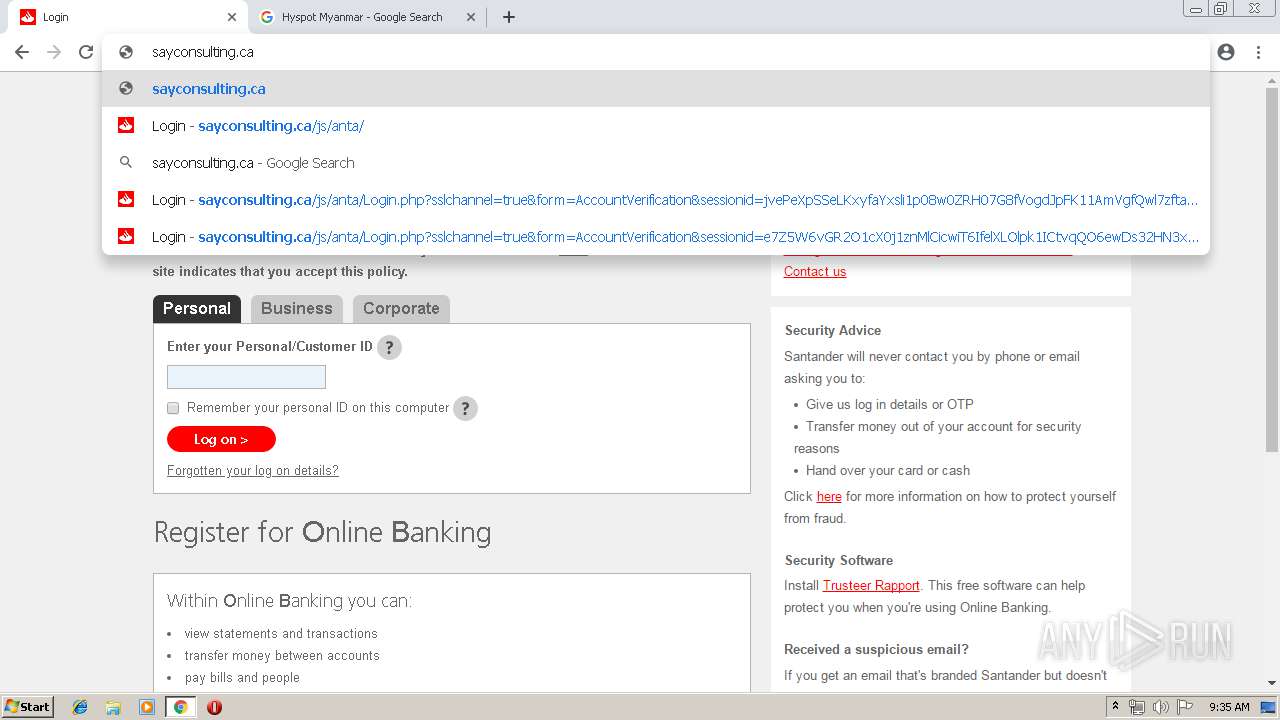
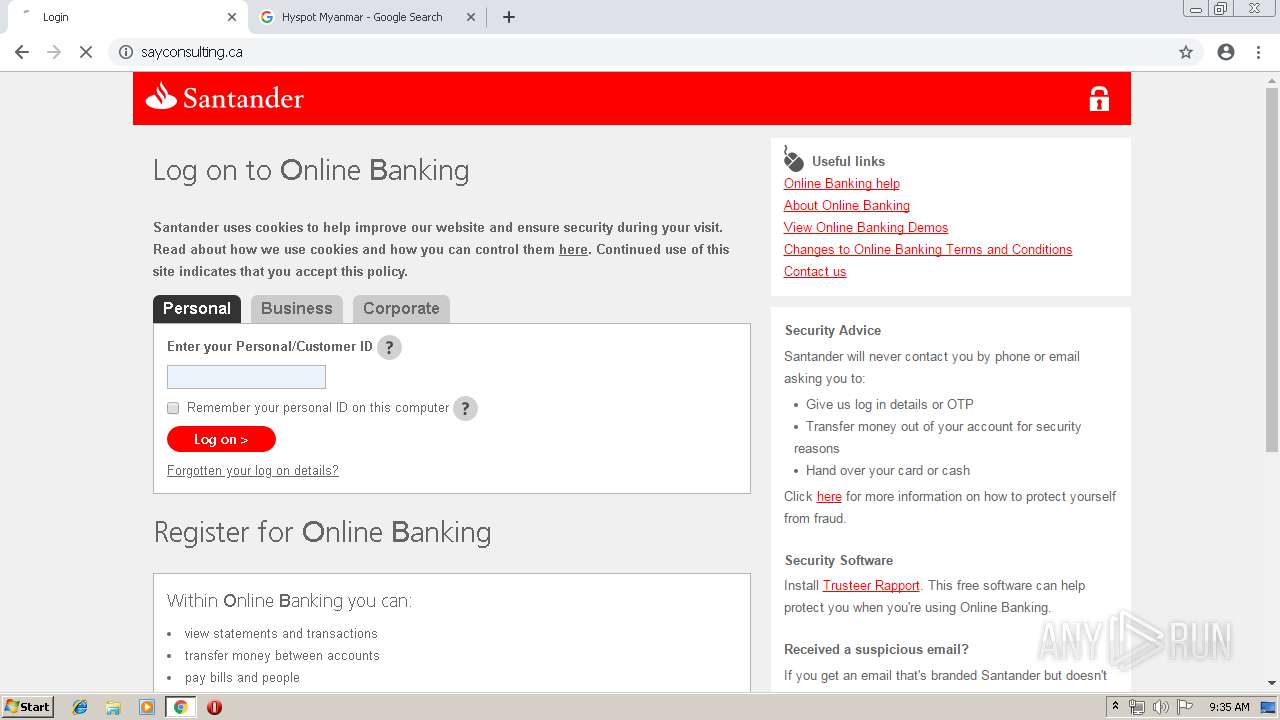
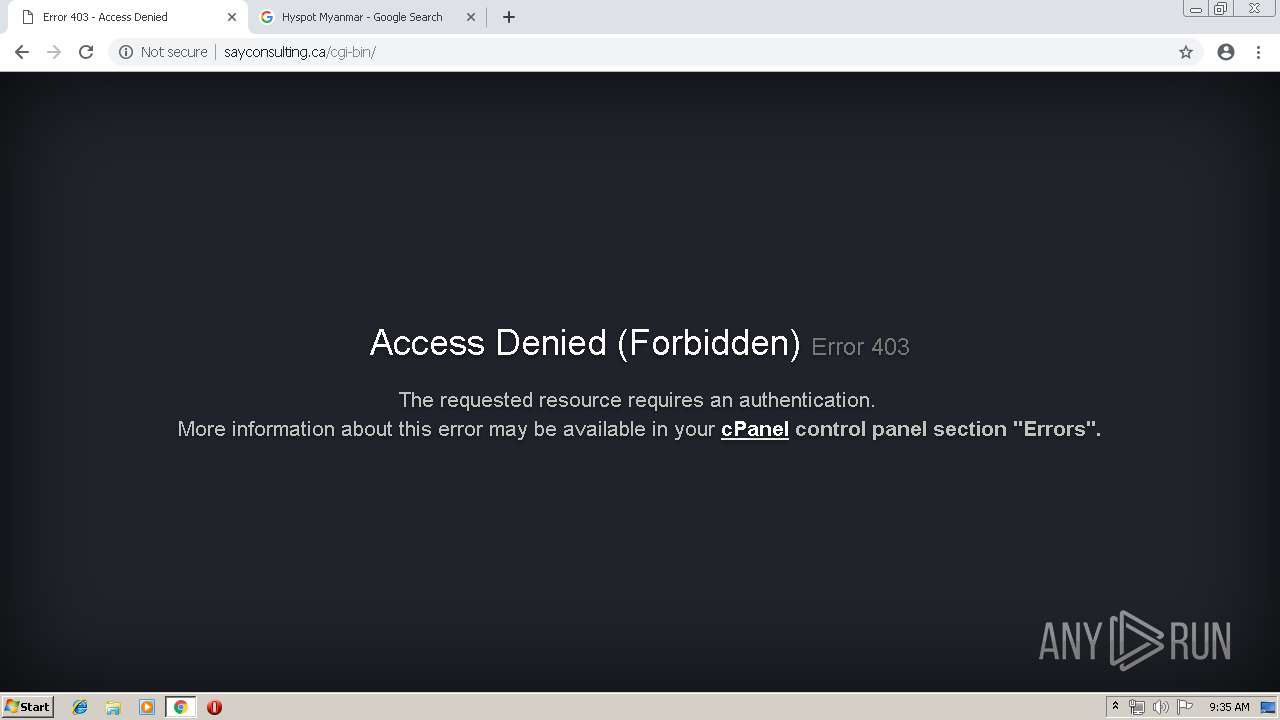
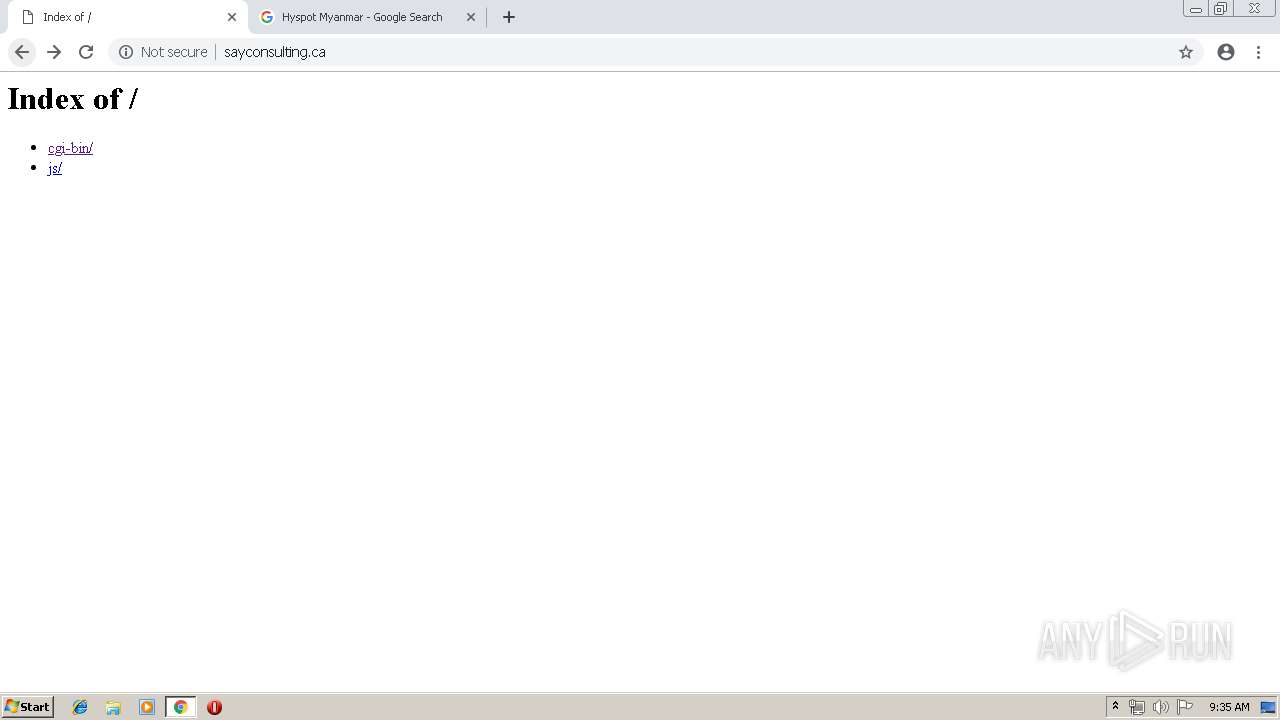
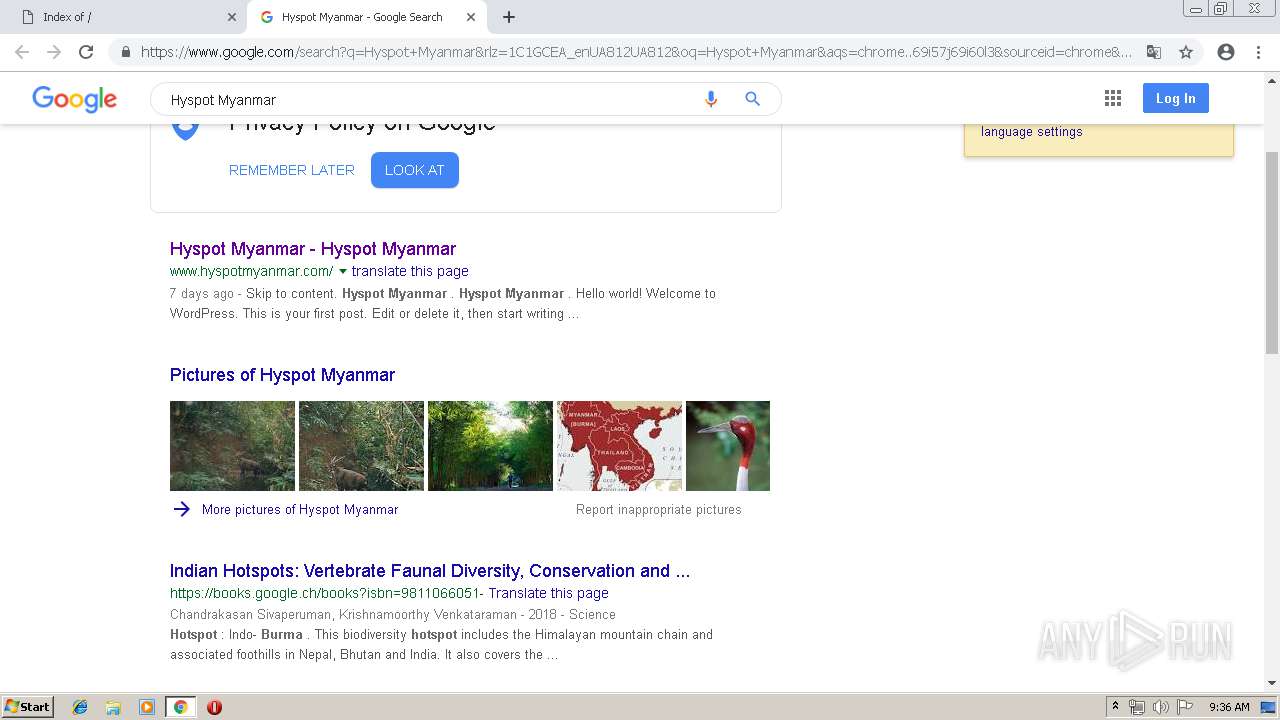
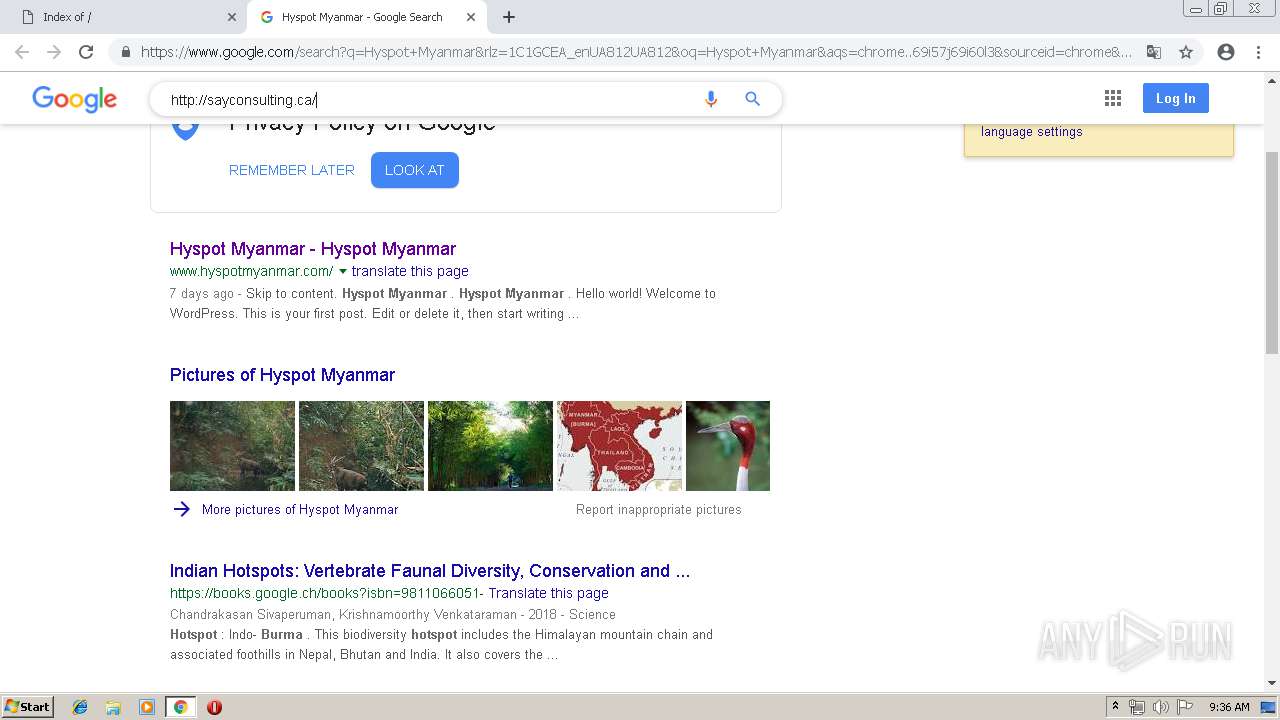
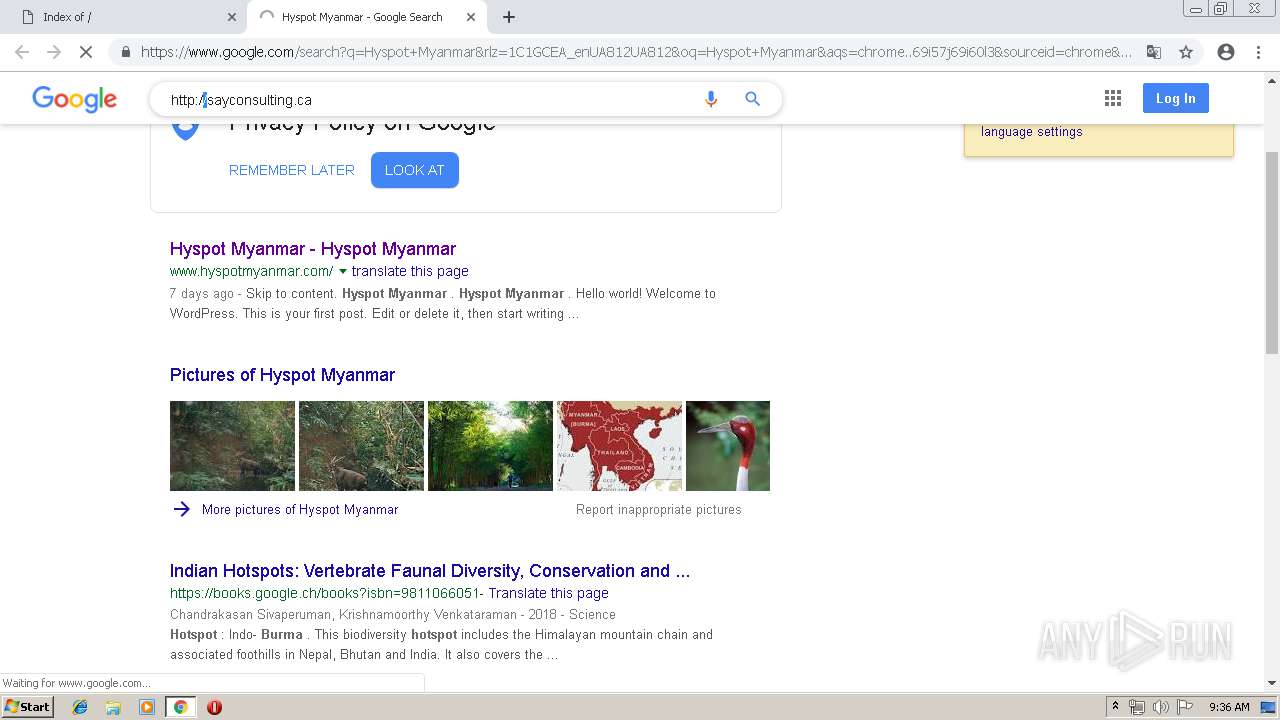
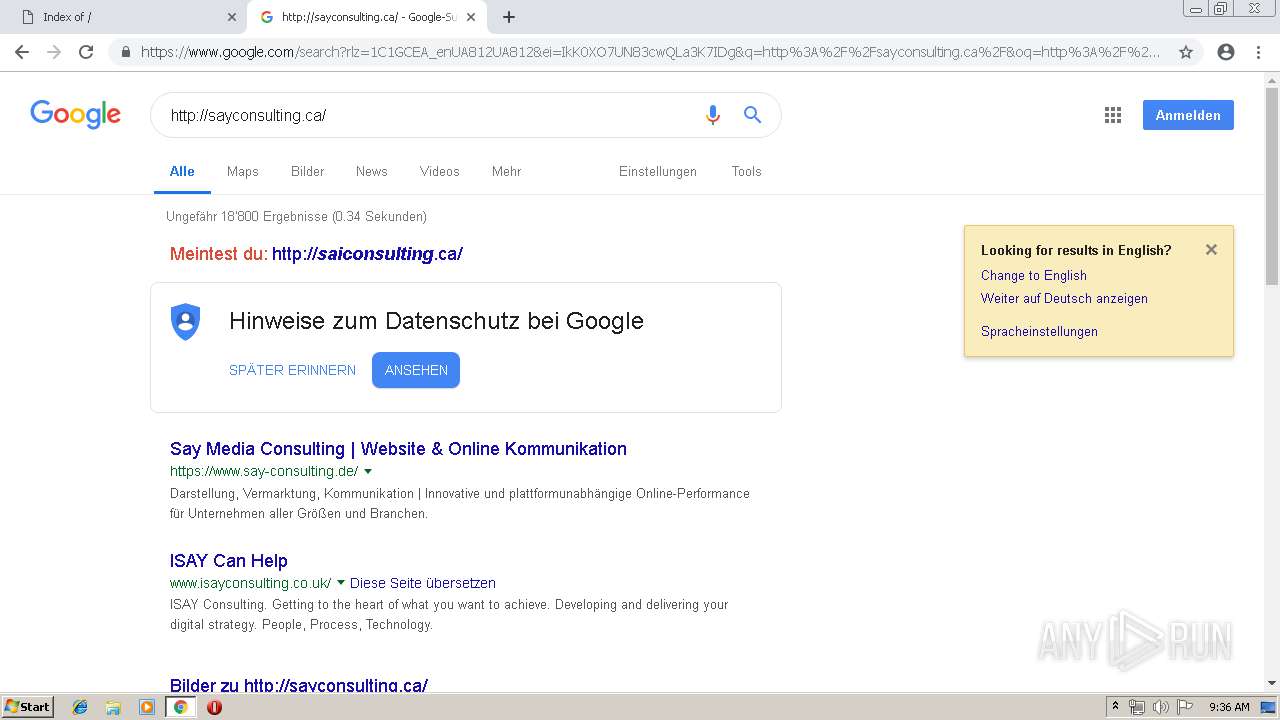
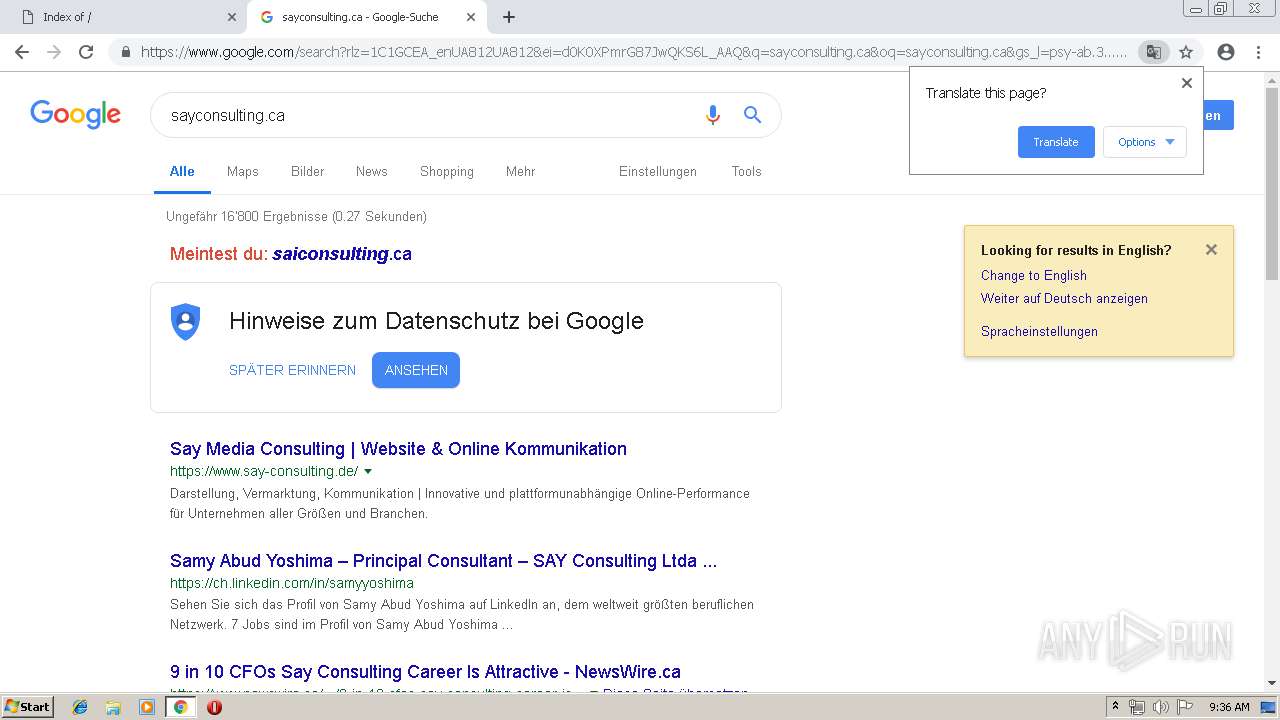
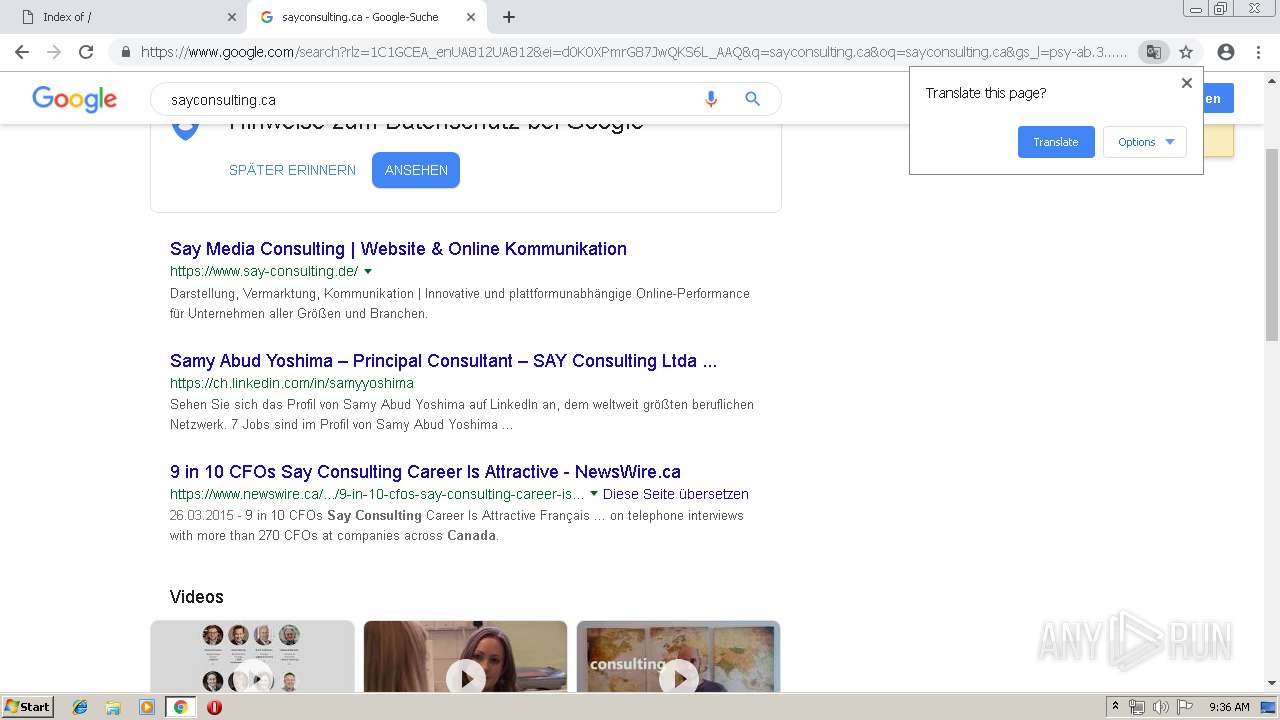
736 | chrome.exe | GET | 200 | 204.93.178.22:80 | http://hyspotmyanmar.com/favicon.ico | US | html | 137 b | malicious |
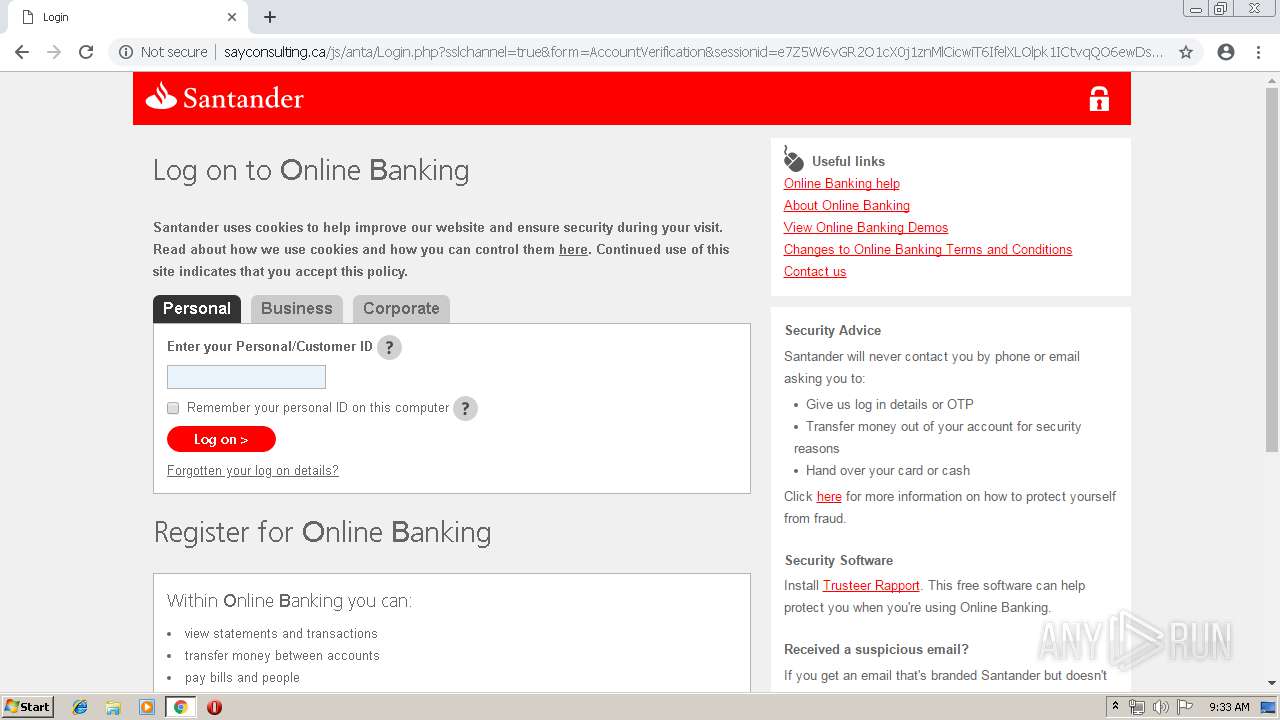
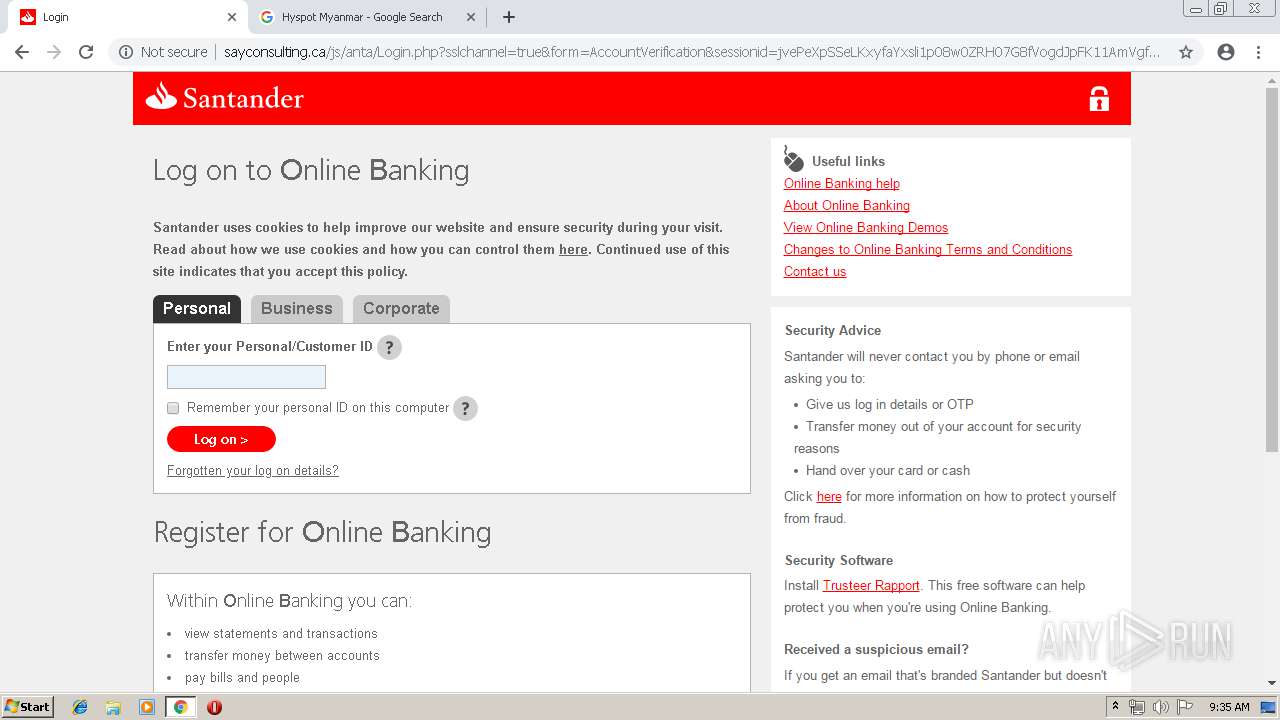
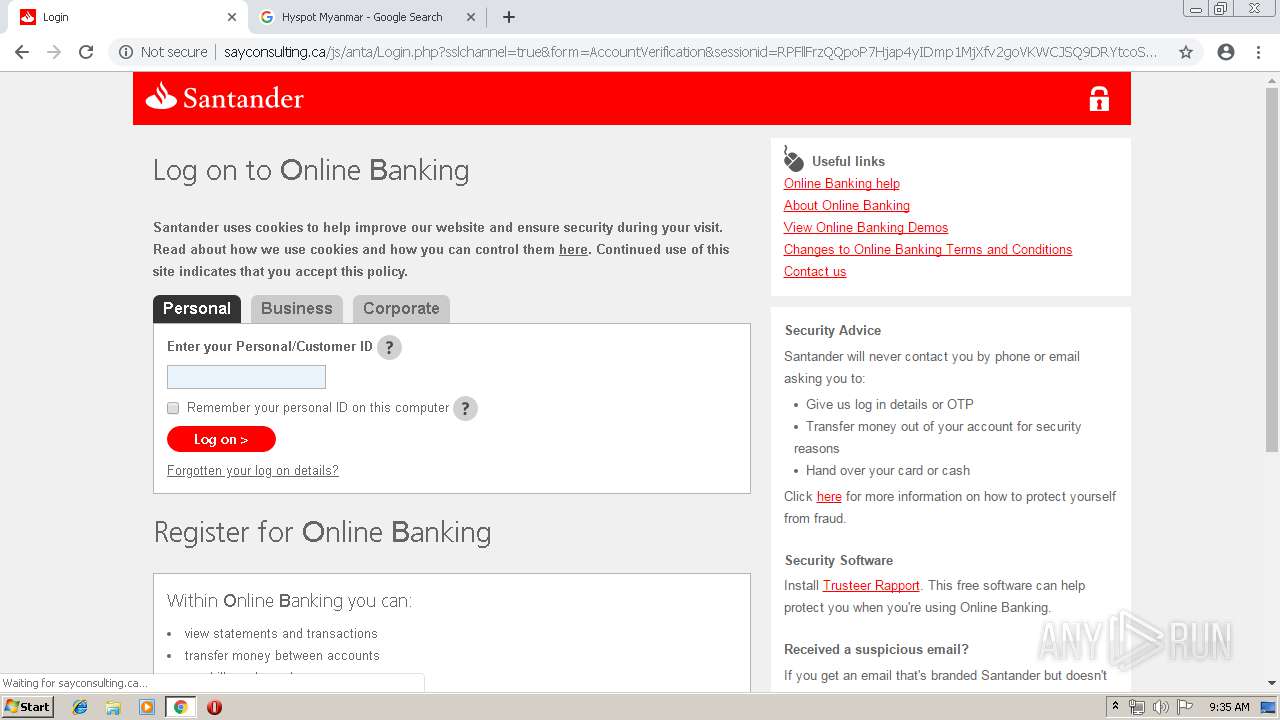
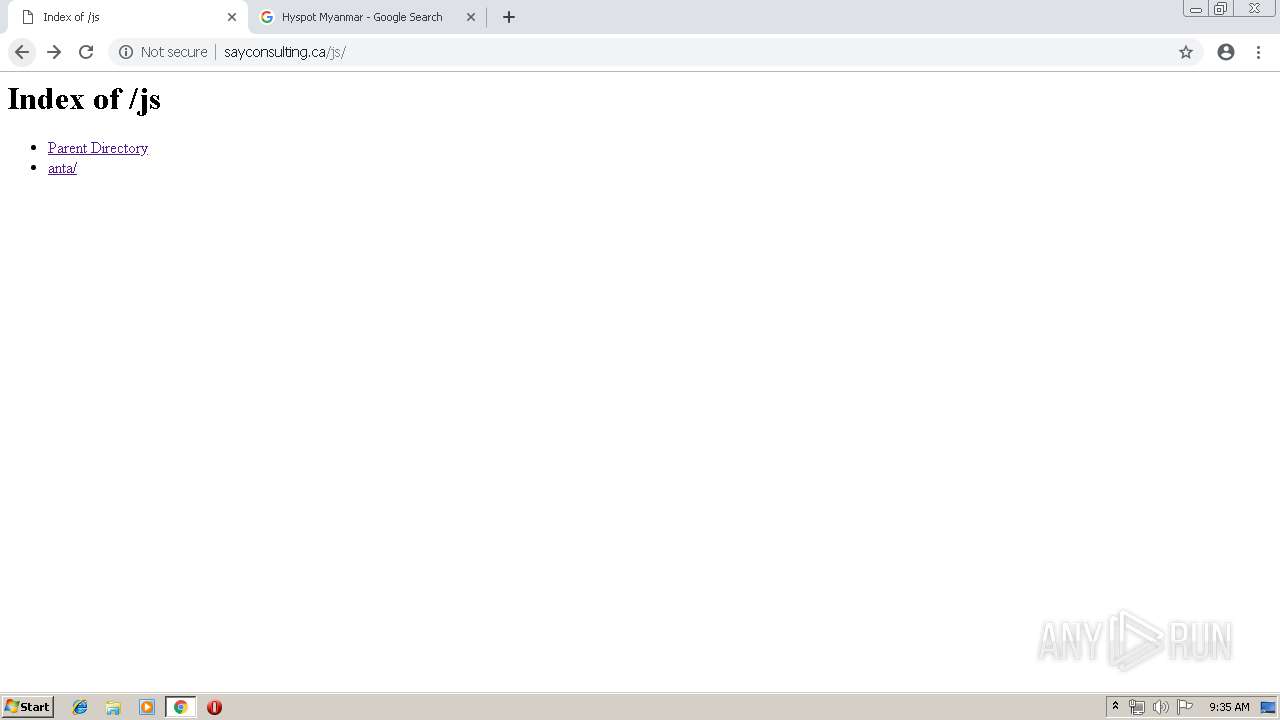
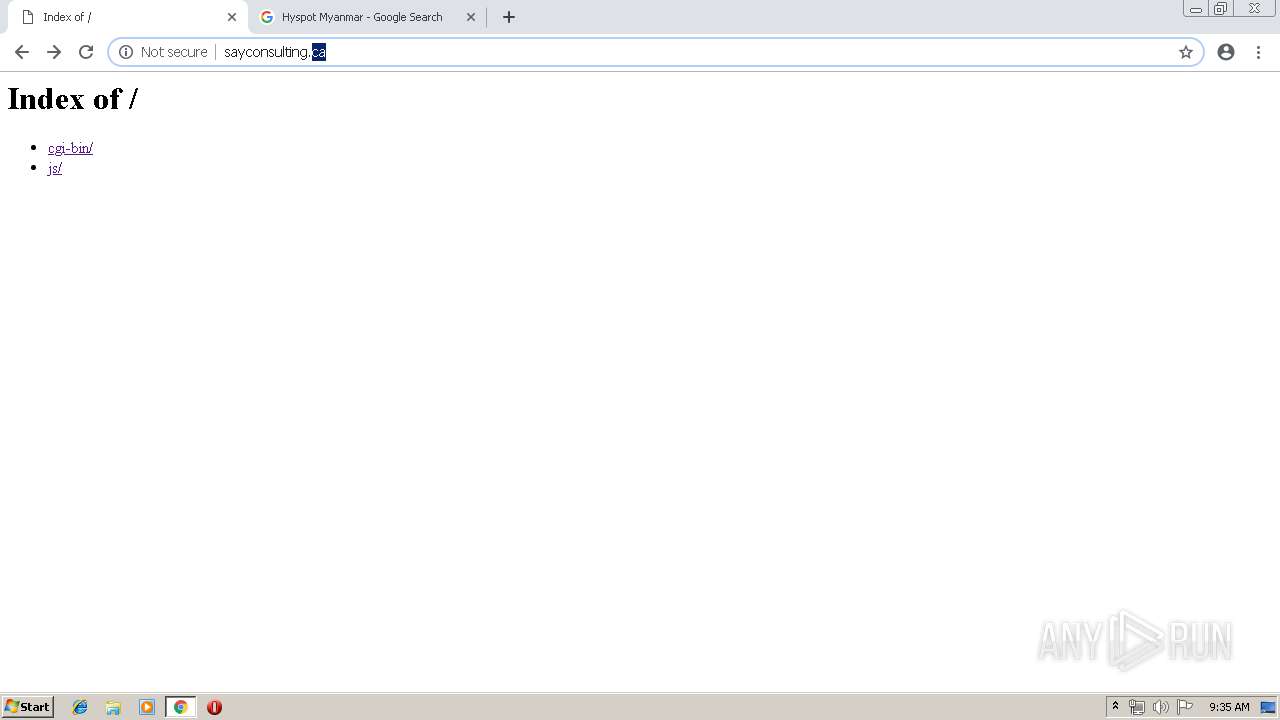
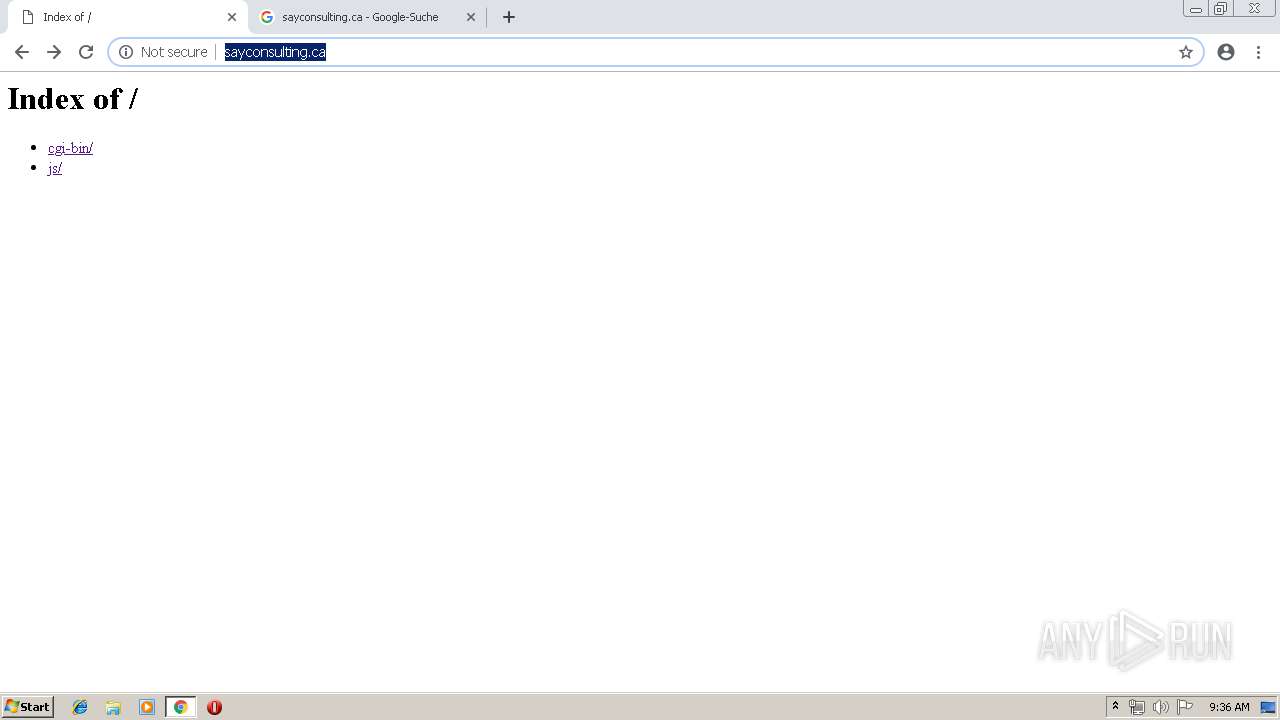
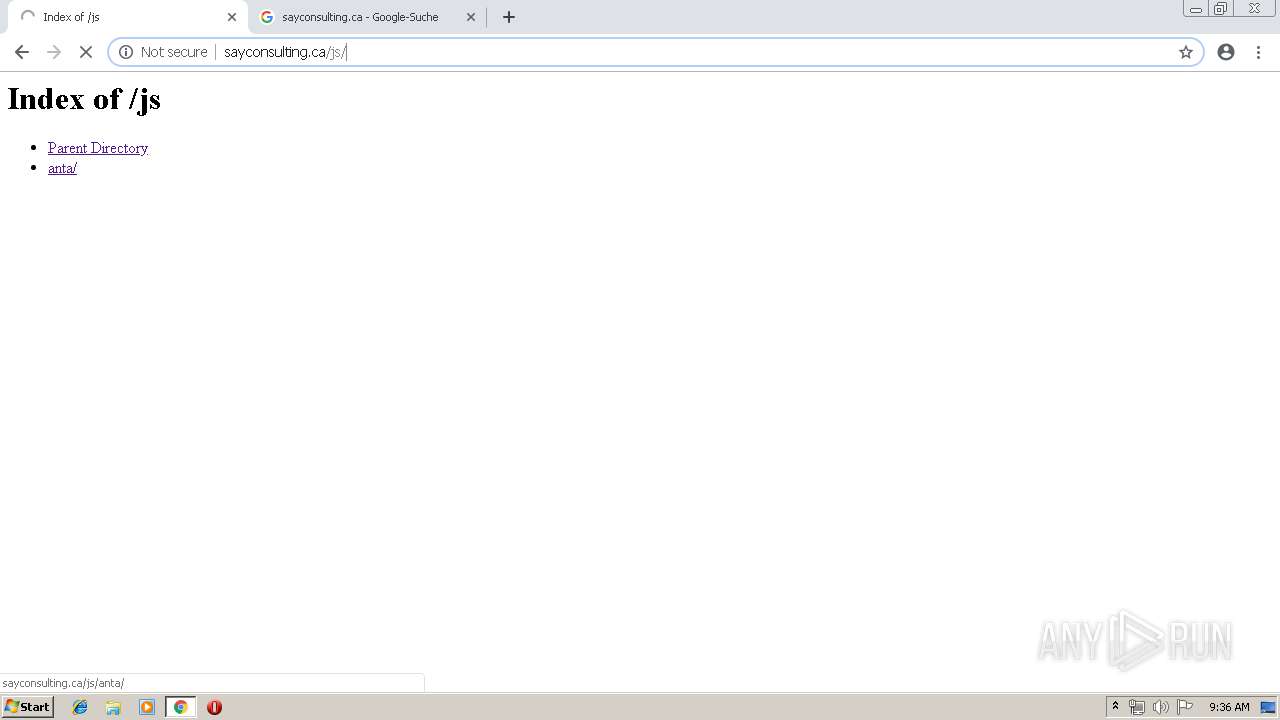
736 | chrome.exe | GET | 200 | 204.93.167.45:80 | http://sayconsulting.ca/js/anta/Login.php?sslchannel=true&form=AccountVerification&sessionid=e7Z5W6vGR2O1cX0j1znMlCicwiT6IfelXLOlpk1ICtvqQO6ewDs32HN3xK7uoLJu6oYjzUN0ti4s9xUs | US | html | 40.6 Kb | malicious |
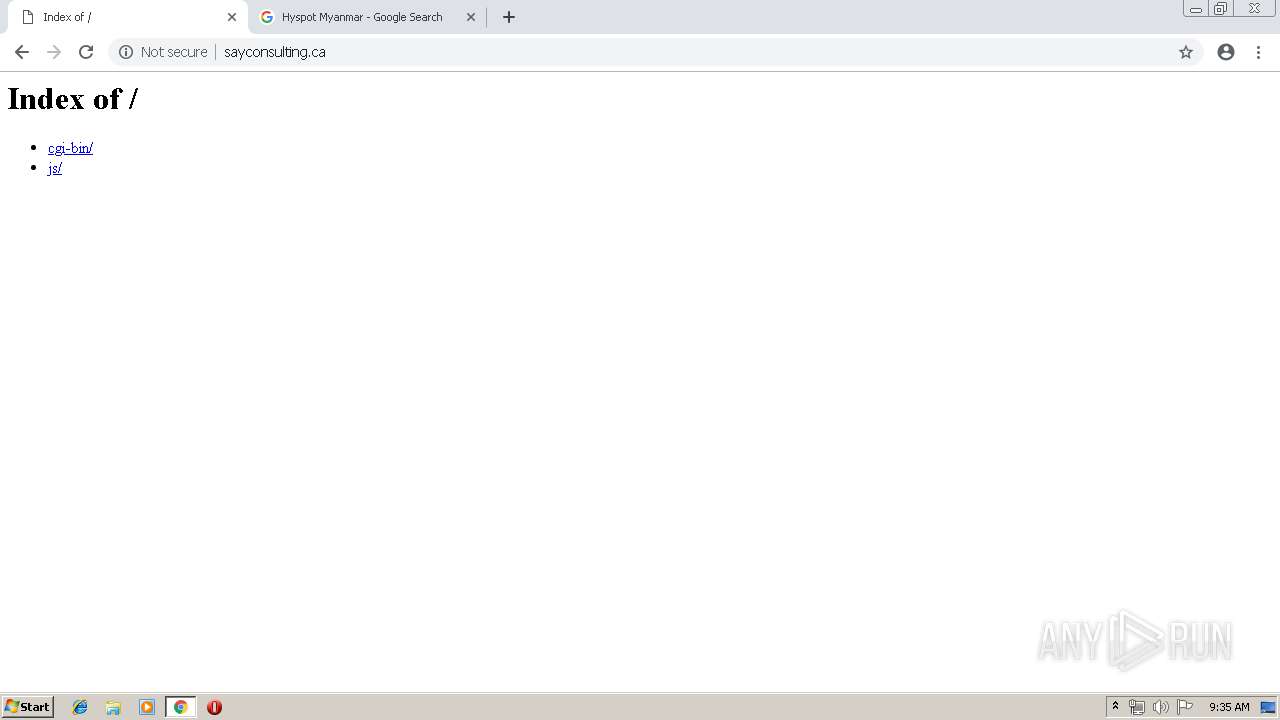
736 | chrome.exe | GET | 200 | 204.93.167.45:80 | http://sayconsulting.ca/js/anta/ | US | html | 229 b | malicious |
736 | chrome.exe | GET | 302 | 172.217.17.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
736 | chrome.exe | GET | 200 | 204.93.178.22:80 | http://hyspotmyanmar.com/wp-includes/zik/zzik.php | US | html | 137 b | malicious |
736 | chrome.exe | GET | 200 | 204.93.167.45:80 | http://sayconsulting.ca/js/anta/assets/img/ico_help.svg | US | image | 1.93 Kb | malicious |
736 | chrome.exe | GET | 200 | 217.146.165.206:80 | http://r3---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.156&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1555317141&mv=m&pl=25&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
736 | chrome.exe | GET | 200 | 204.93.178.22:80 | http://hyspotmyanmar.com/favicon.ico | US | html | 985 b | malicious |
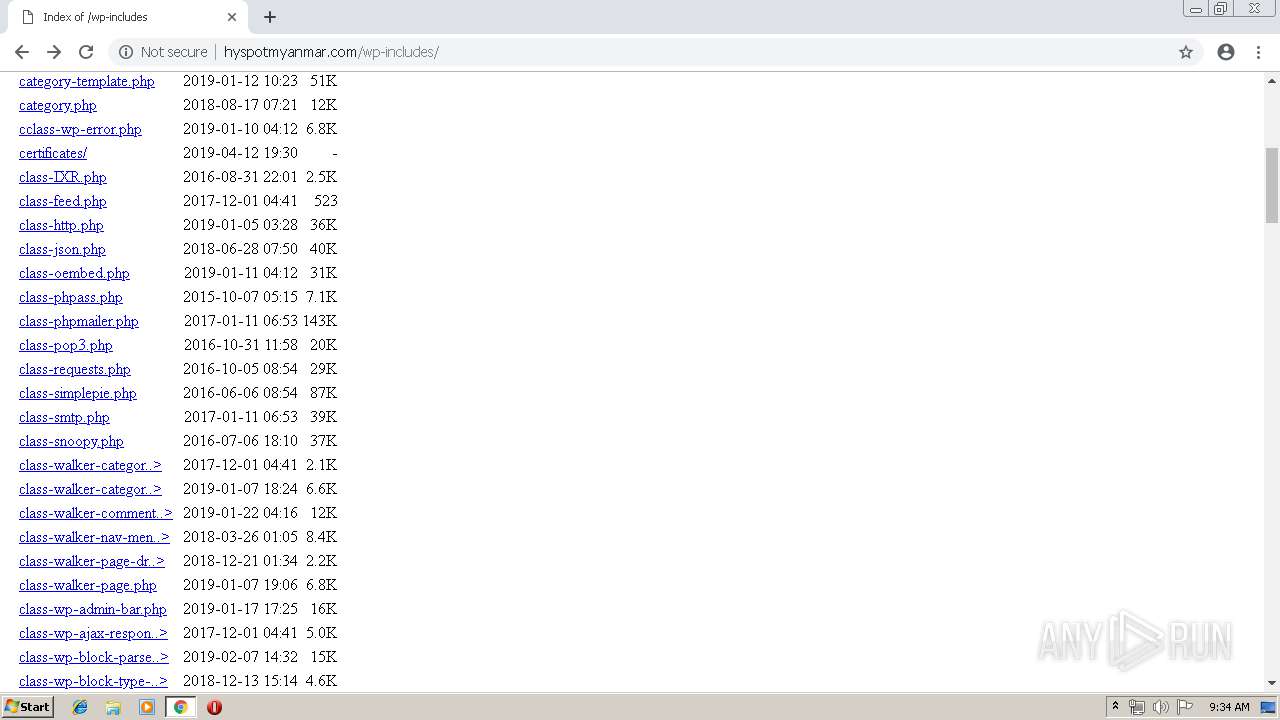
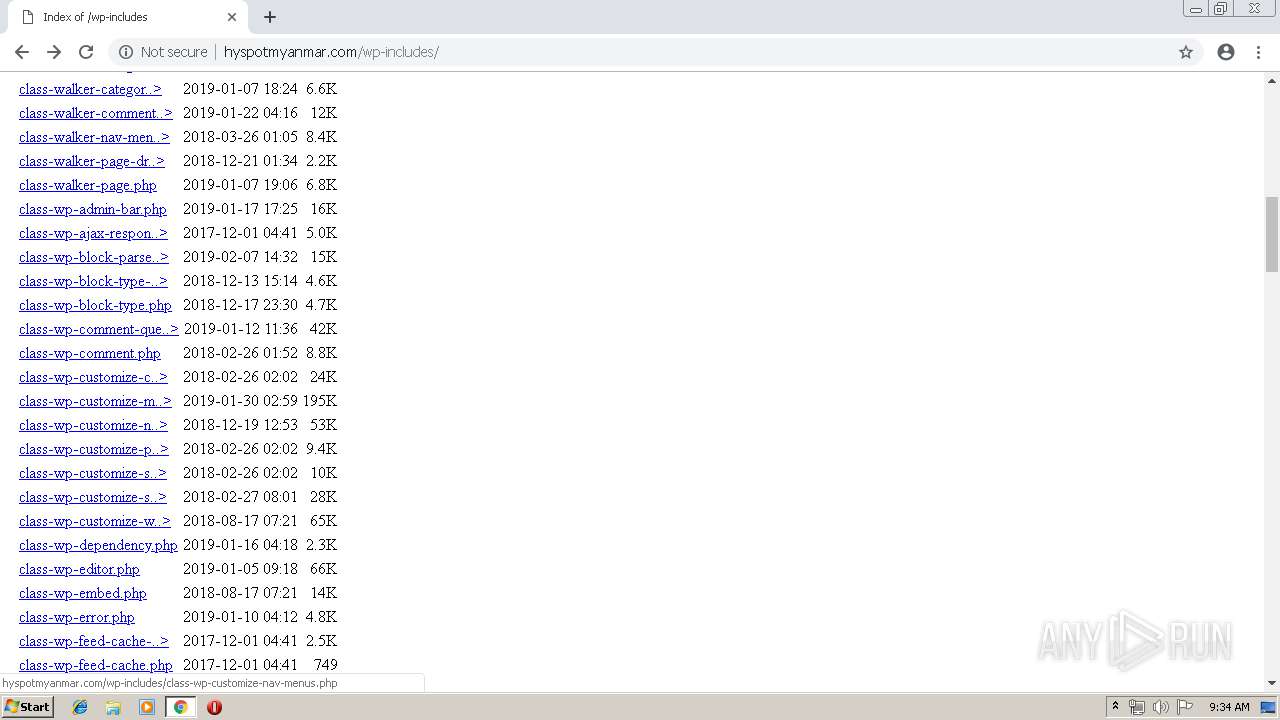
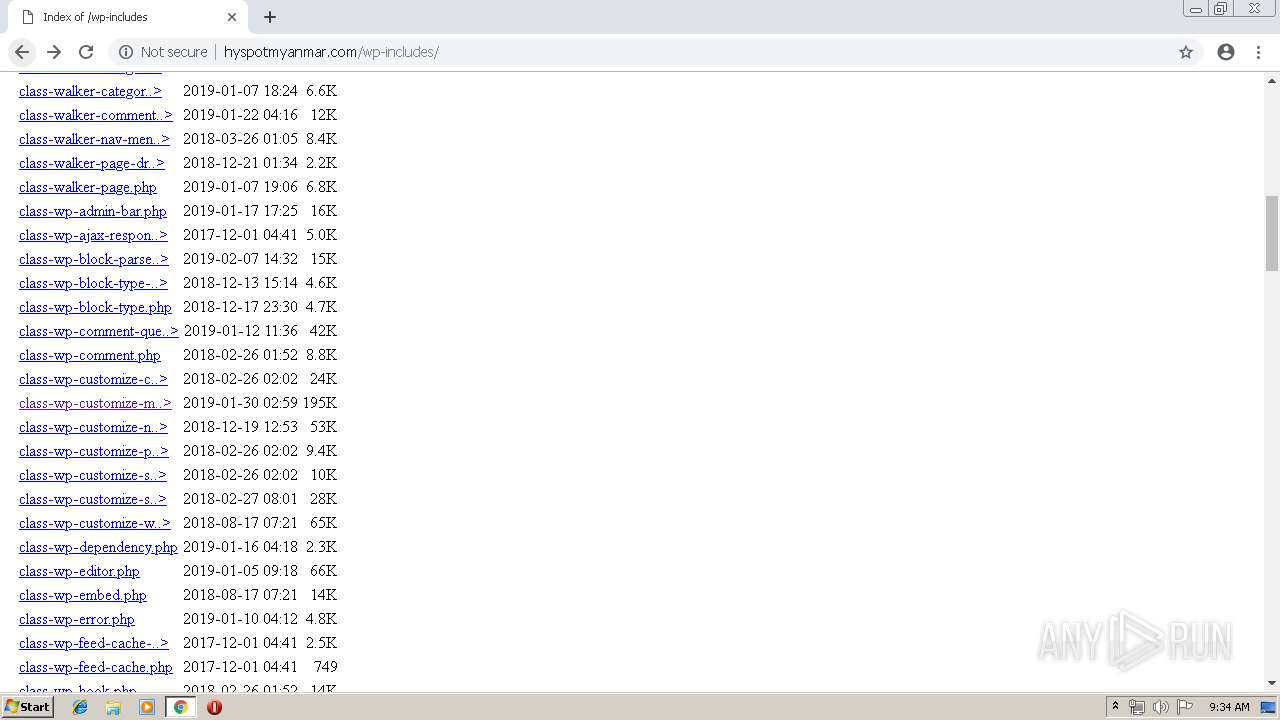
736 | chrome.exe | GET | 200 | 204.93.178.22:80 | http://hyspotmyanmar.com/wp-includes/zik/ | US | html | 985 b | malicious |
736 | chrome.exe | GET | 200 | 204.93.167.45:80 | http://sayconsulting.ca/js/anta/assets/img/ico_help.gif | US | image | 834 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
736 | chrome.exe | 204.93.178.22:80 | hyspotmyanmar.com | Server Central Network | US | malicious |
736 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
736 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
— | — | 172.217.17.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
736 | chrome.exe | 204.93.167.45:80 | sayconsulting.ca | Server Central Network | US | malicious |
— | — | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
736 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
736 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
736 | chrome.exe | 217.146.165.206:80 | r3---sn-oun-1gie.gvt1.com | NTS workspace AG | CH | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
hyspotmyanmar.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-oun-1gie.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
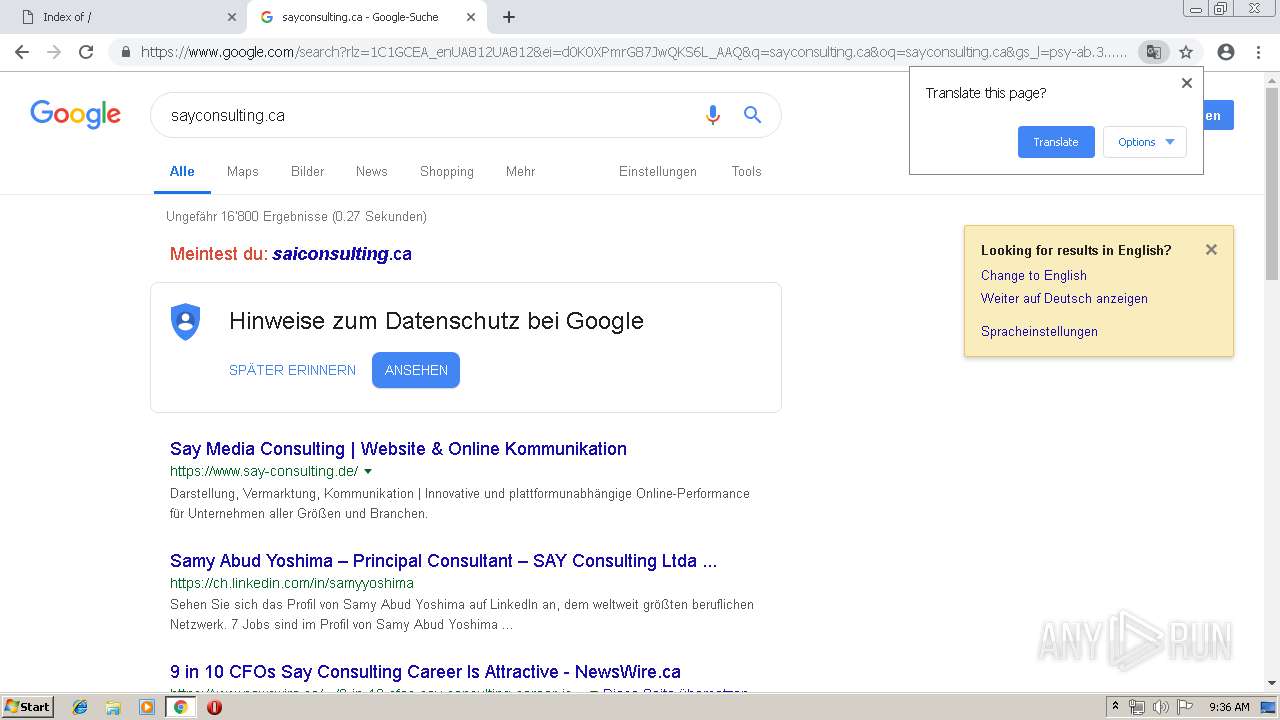
sayconsulting.ca |
| malicious |
clients1.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
3 ETPRO signatures available at the full report