| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/36a68ada-cc1b-4ed9-813f-817547278e74 |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2020, 11:53:08 |
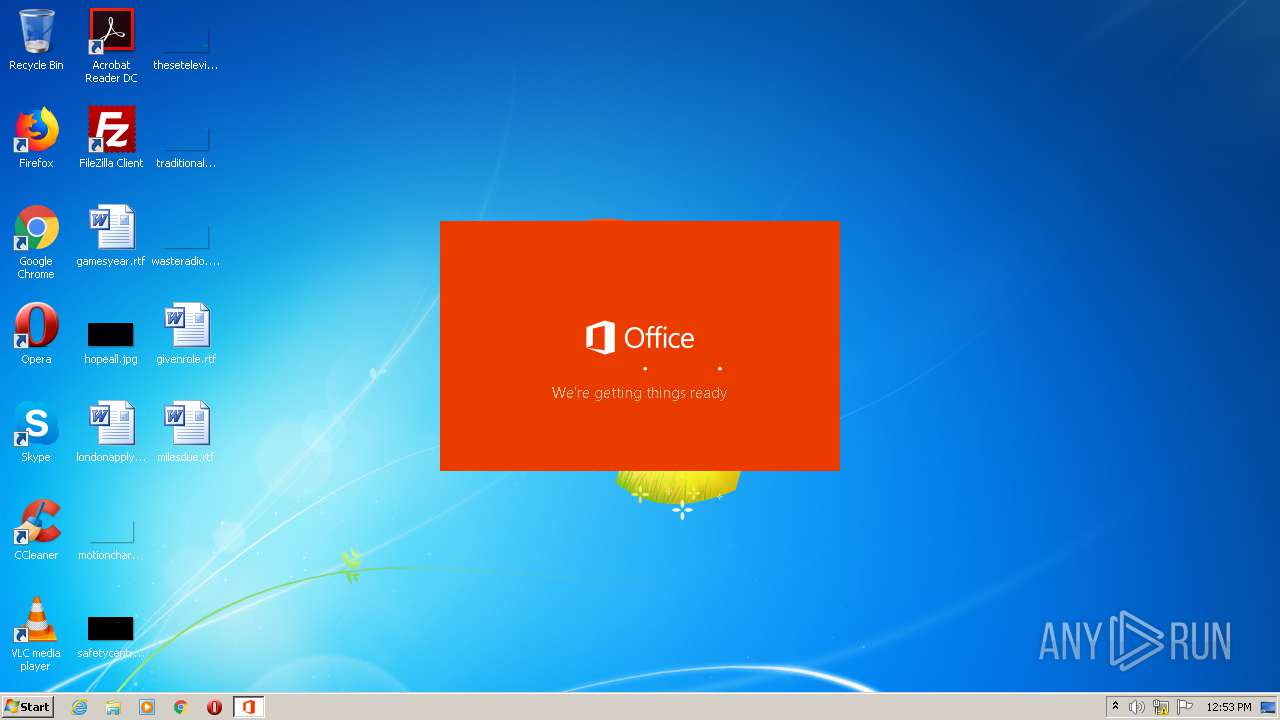
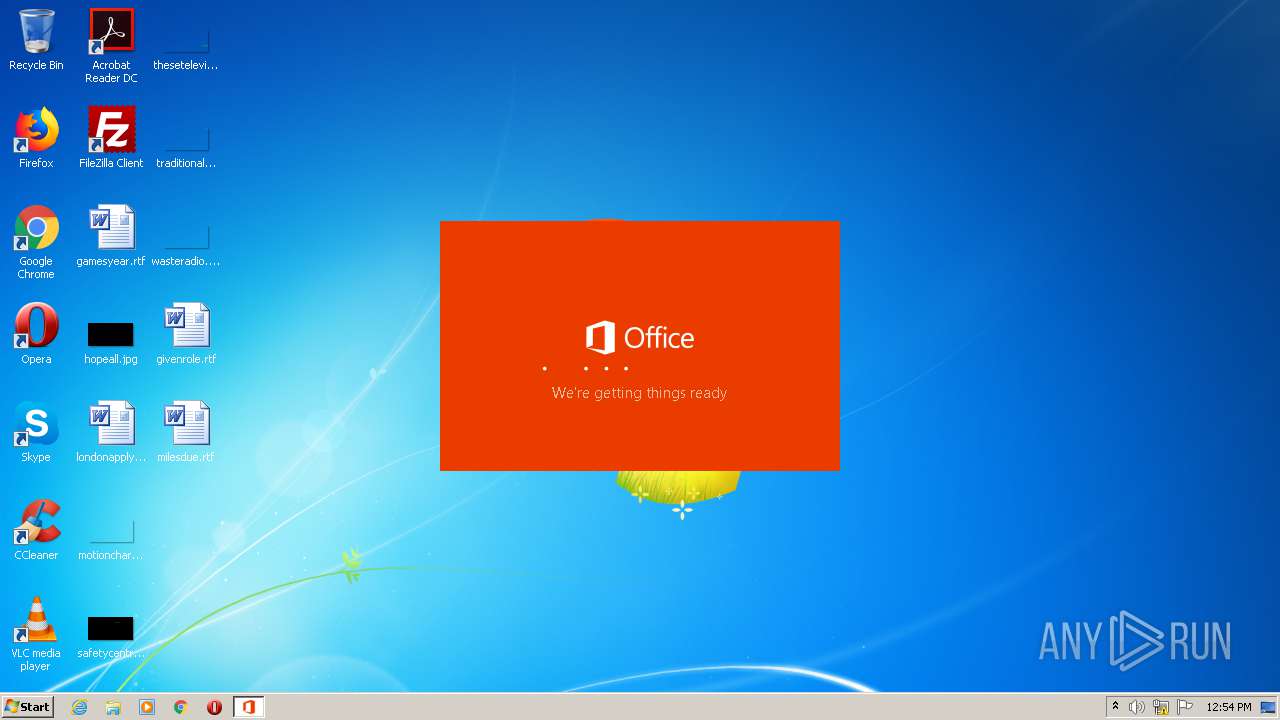
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AF0EF2667EAA9D3B0E7C2F5CA5169448 |
| SHA1: | 026DC556A52F8BE713C12524632A7E1CF6CBC631 |
| SHA256: | FB6B98597EE0B72FBFC4248D838244065C294009FA6266F2F1B8451538C1010C |
| SSDEEP: | 196608:0JywEbBMyCC4TNW3D7HPZAkZ28Z+1XaNpb8HT8aIexjwpLy:0kwsBMyCFZW3D7v9fZ+1opHKwFy |
MALICIOUS
Application was dropped or rewritten from another process
- KMSS.exe (PID: 3824)
- kmss.dat (PID: 3688)
- files.dat (PID: 2592)
- wget_oinstall.exe (PID: 3008)
- wget_oinstall.exe (PID: 3296)
- mkisofs.exe (PID: 292)
- wget_oinstall.exe (PID: 1732)
- Setup16.exe (PID: 4056)
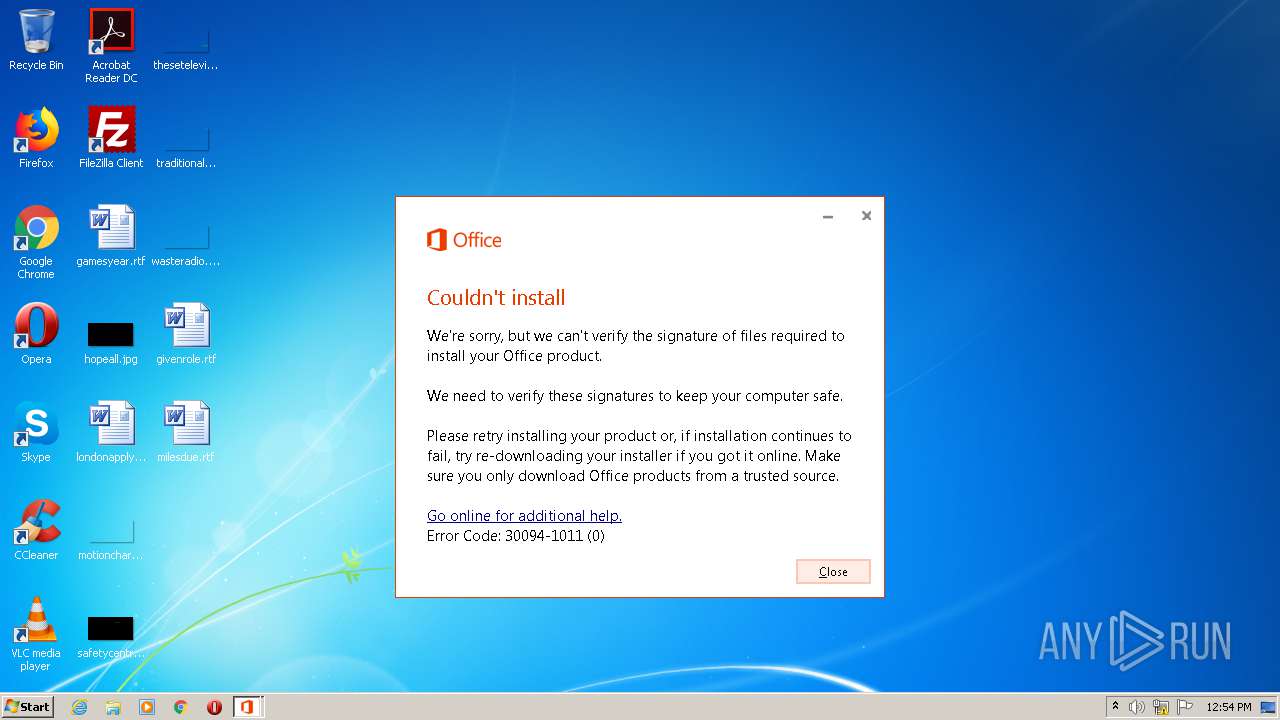
Changes settings of System certificates
- Setup16.exe (PID: 4056)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Setup.exe (PID: 4000)
Starts application with an unusual extension
- cmd.exe (PID: 2044)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 2560)
Executable content was dropped or overwritten
- kmss.dat (PID: 3688)
- Setup.exe (PID: 4000)
- aes.dat (PID: 3388)
- files.dat (PID: 2592)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2672)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 3932)
Executes scripts
- cmd.exe (PID: 948)
- cmd.exe (PID: 3084)
Uses TASKKILL.EXE to kill process
- Setup.exe (PID: 4000)
Adds / modifies Windows certificates
- Setup16.exe (PID: 4056)
Reads Internet Cache Settings
- Setup16.exe (PID: 4056)
INFO
Reads settings of System Certificates
- Setup16.exe (PID: 4056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:09:16 10:00:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 718848 |
| InitializedDataSize: | 11596800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
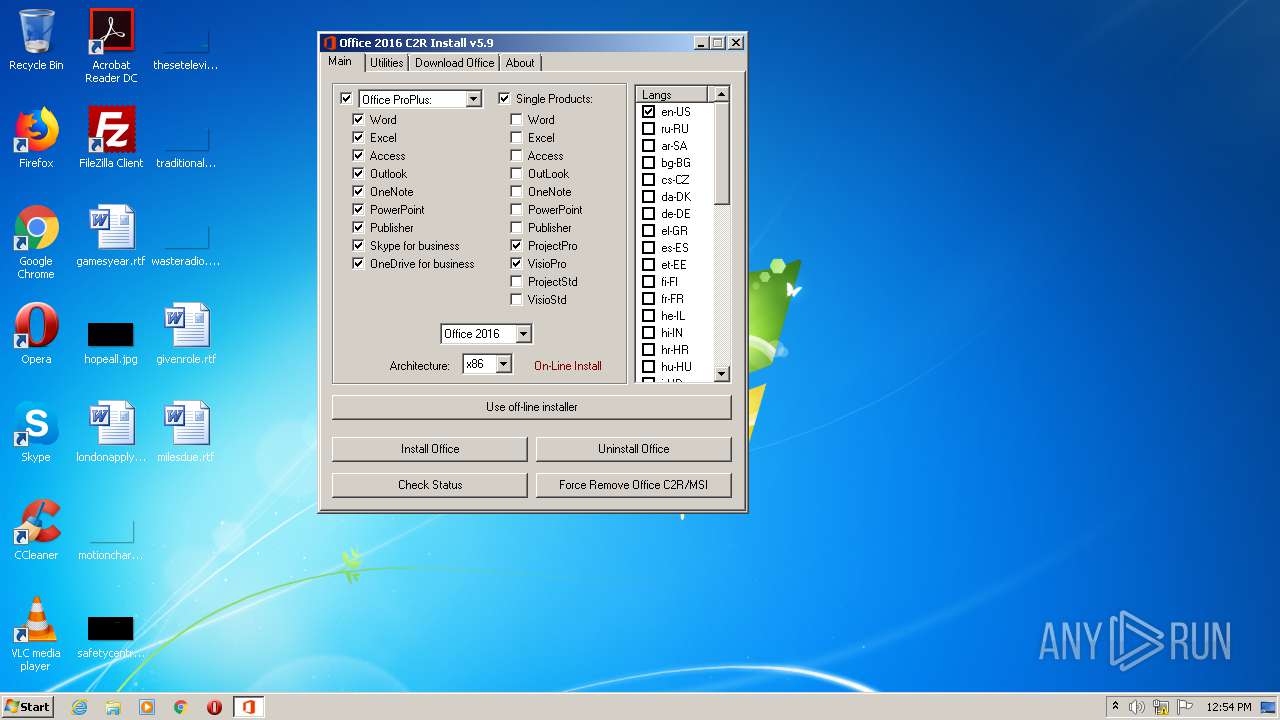
| FileVersionNumber: | 5.9.0.0 |
| ProductVersionNumber: | 5.9.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
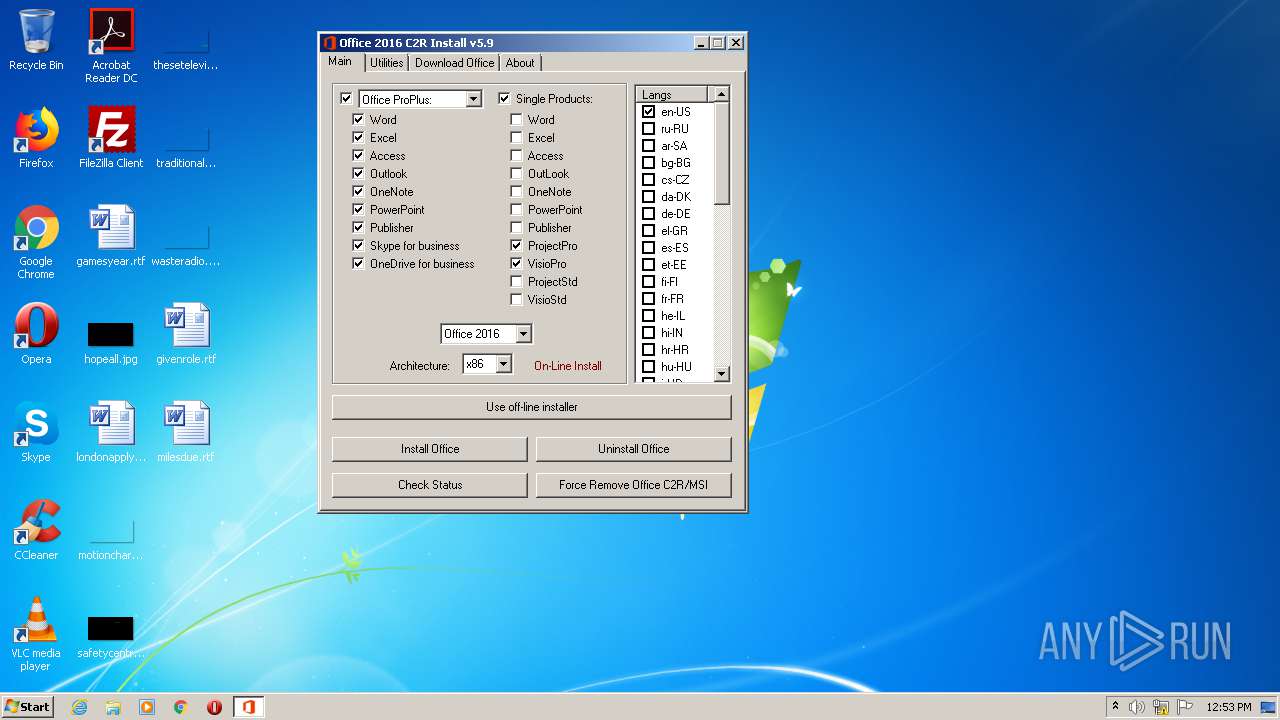
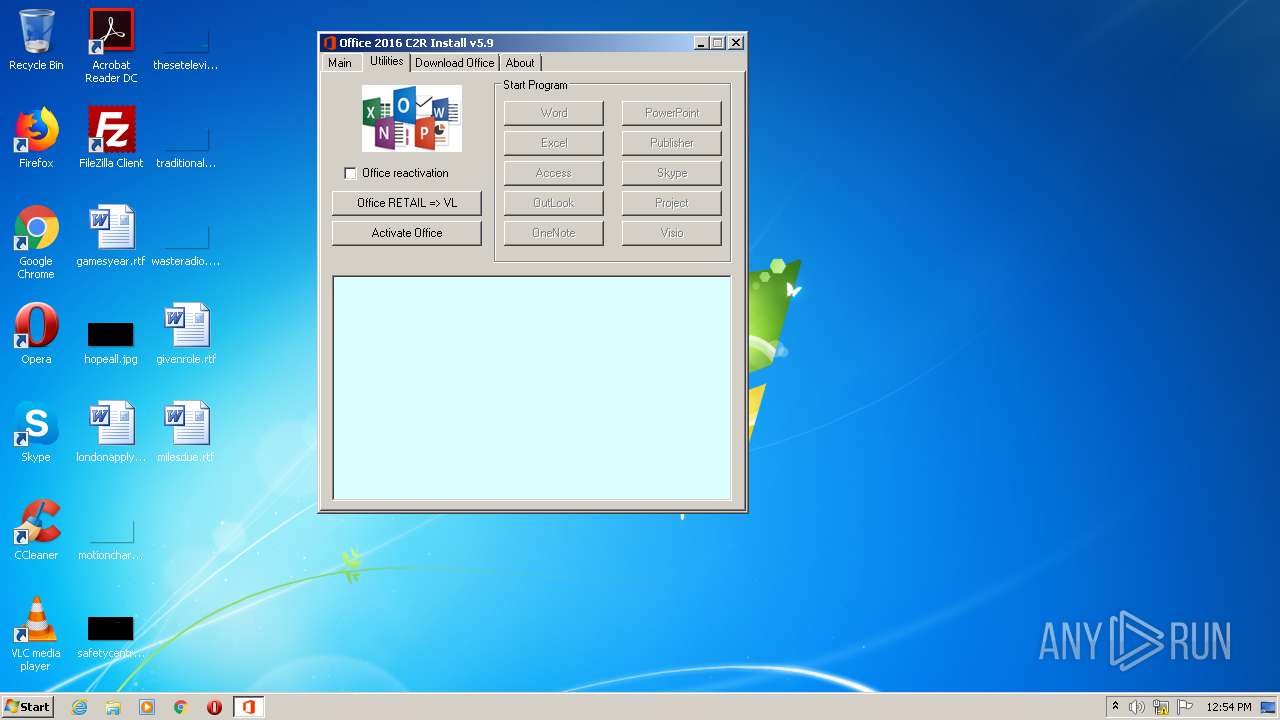
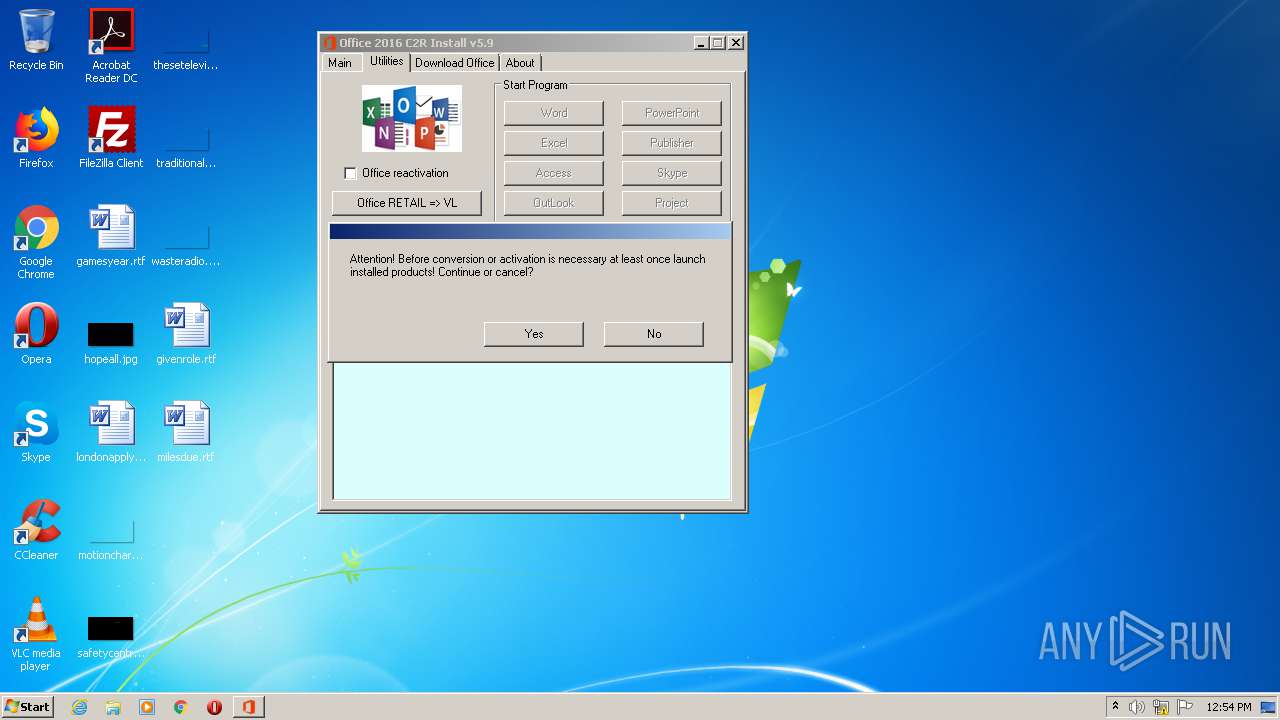
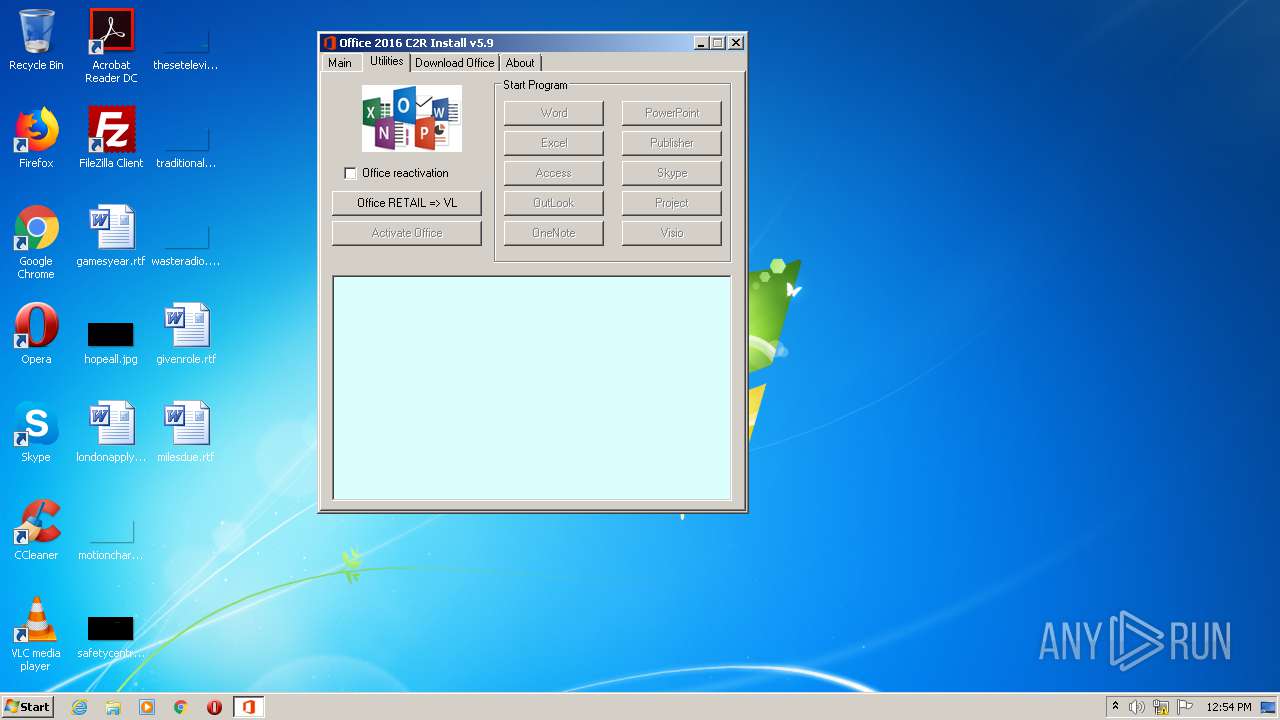
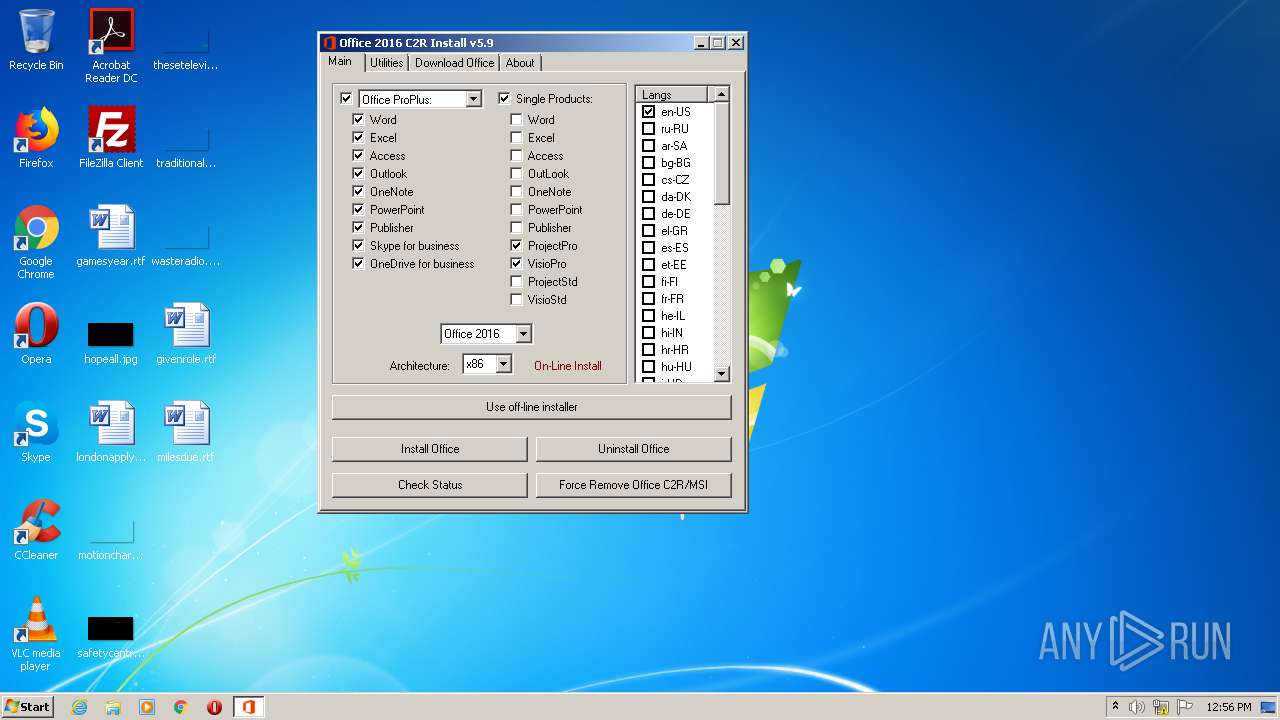
| ProductName: | Office 2013-2016 C2R Install |
| FileDescription: | Office 2013-2016 C2R Install |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Sep-2016 08:00:16 |
| Detected languages: |
|
| ProductName: | Office 2013-2016 C2R Install |
| FileDescription: | Office 2013-2016 C2R Install |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 16-Sep-2016 08:00:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0001F067 | 0x0001F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.99089 |
.text | 0x00021000 | 0x00090441 | 0x00090600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58484 |
.rdata | 0x000B2000 | 0x0001C6B0 | 0x0001C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.81585 |
.data | 0x000CF000 | 0x00ADE130 | 0x00A64400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.62634 |
.rsrc | 0x00BAE000 | 0x000149E8 | 0x00014A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86189 |
.modplug | 0x00BC3000 | 0x00005000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8674 | 874 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.20562 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.87138 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.dll |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
99
Monitored processes
35
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
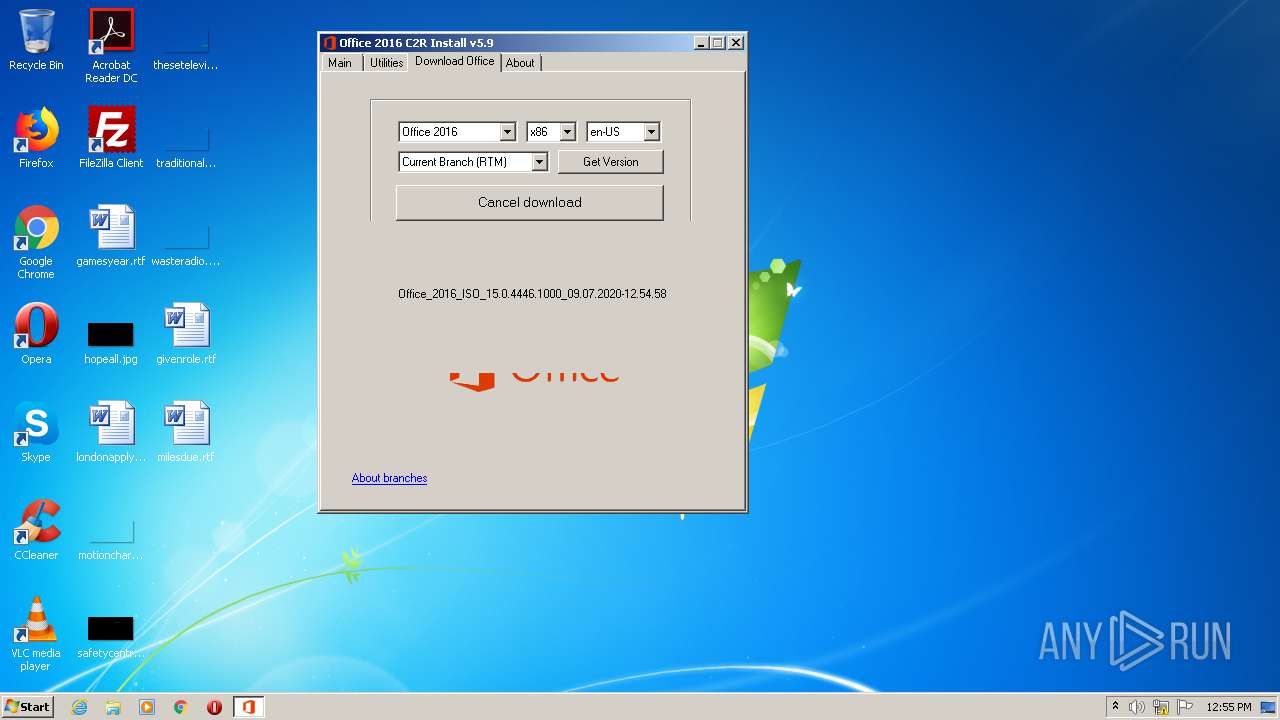
| 292 | "C:\Users\admin\AppData\Local\Temp\files\mkisofs.exe" -udf -log-file log.txt -volid 15.0.4446.1000 -o "C:\Users\admin\AppData\Local\Temp\Office_2016_15.0.4446.1000.iso" "C:\Users\admin\AppData\Local\Temp\Office_2016_ISO_15.0.4446.1000_09.07.2020-12.54.58" | C:\Users\admin\AppData\Local\Temp\files\mkisofs.exe | — | Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
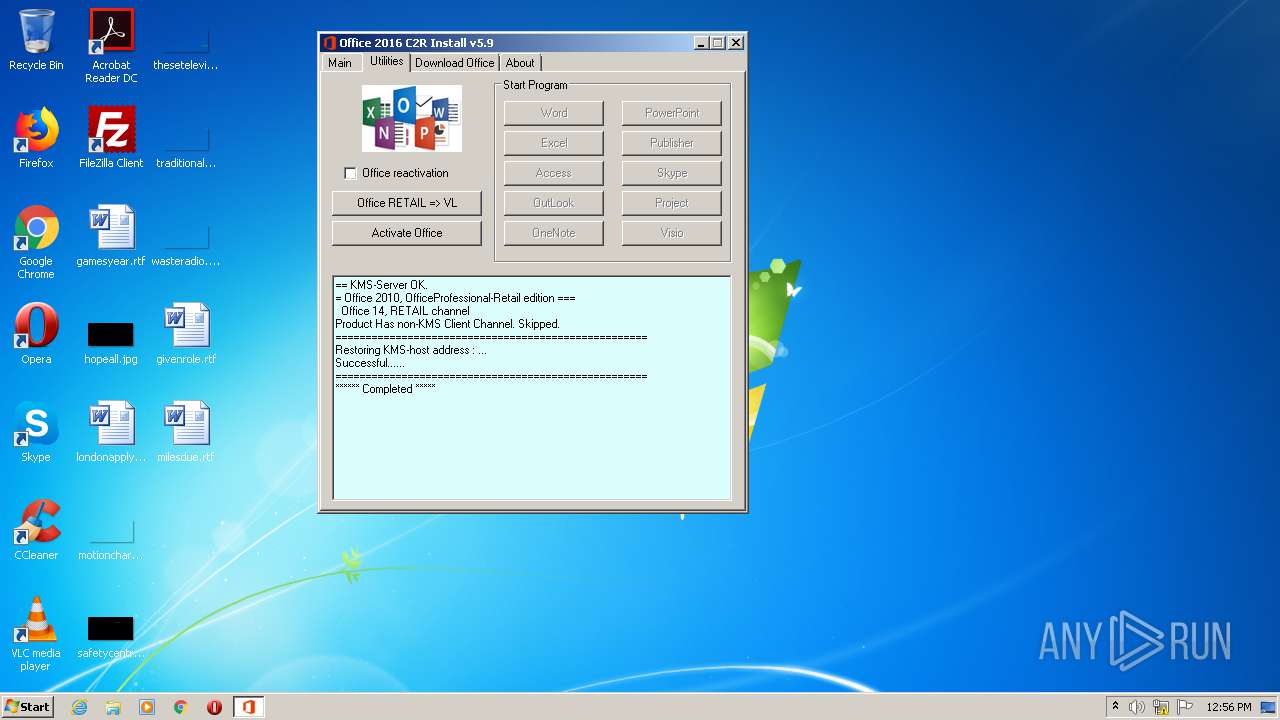
| 948 | "C:\Windows\System32\cmd.exe" /D /c cscript.exe ospp.vbs //NoLogo /ADR:127.0.0.2 /PRT:1688 /P10:1688 /P13:1688 /ACT:OFSRES | C:\Windows\System32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
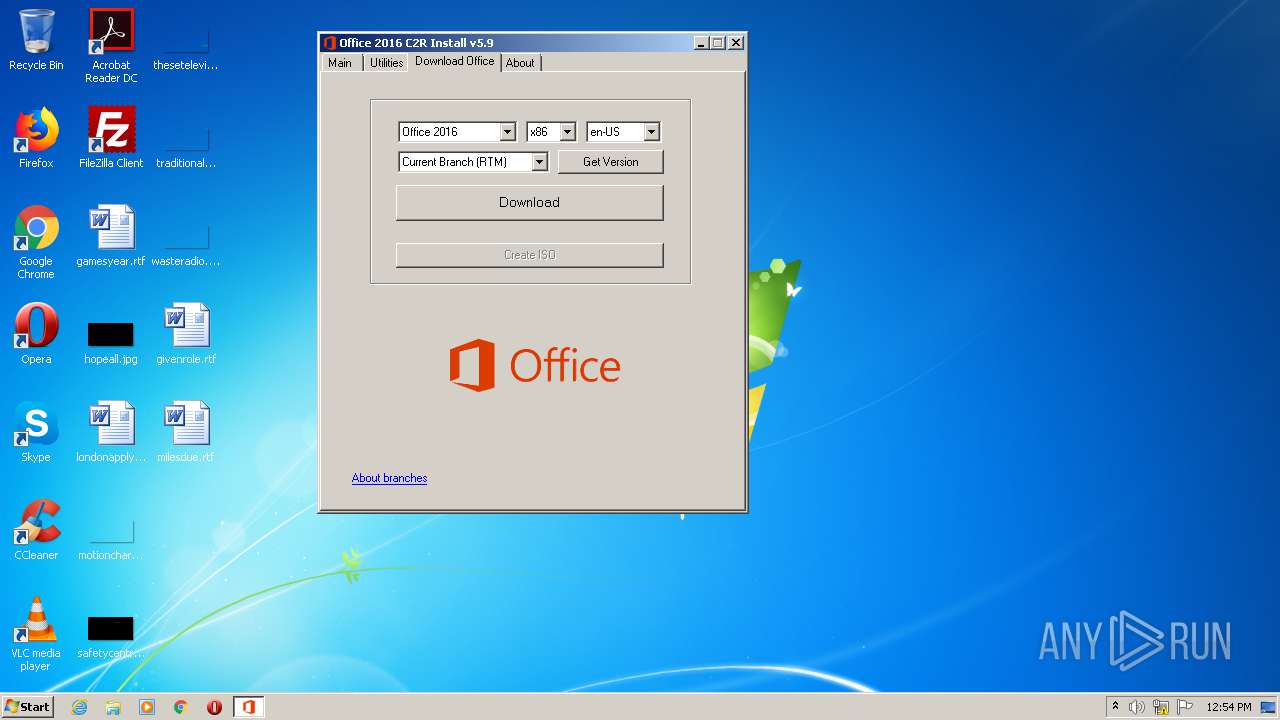
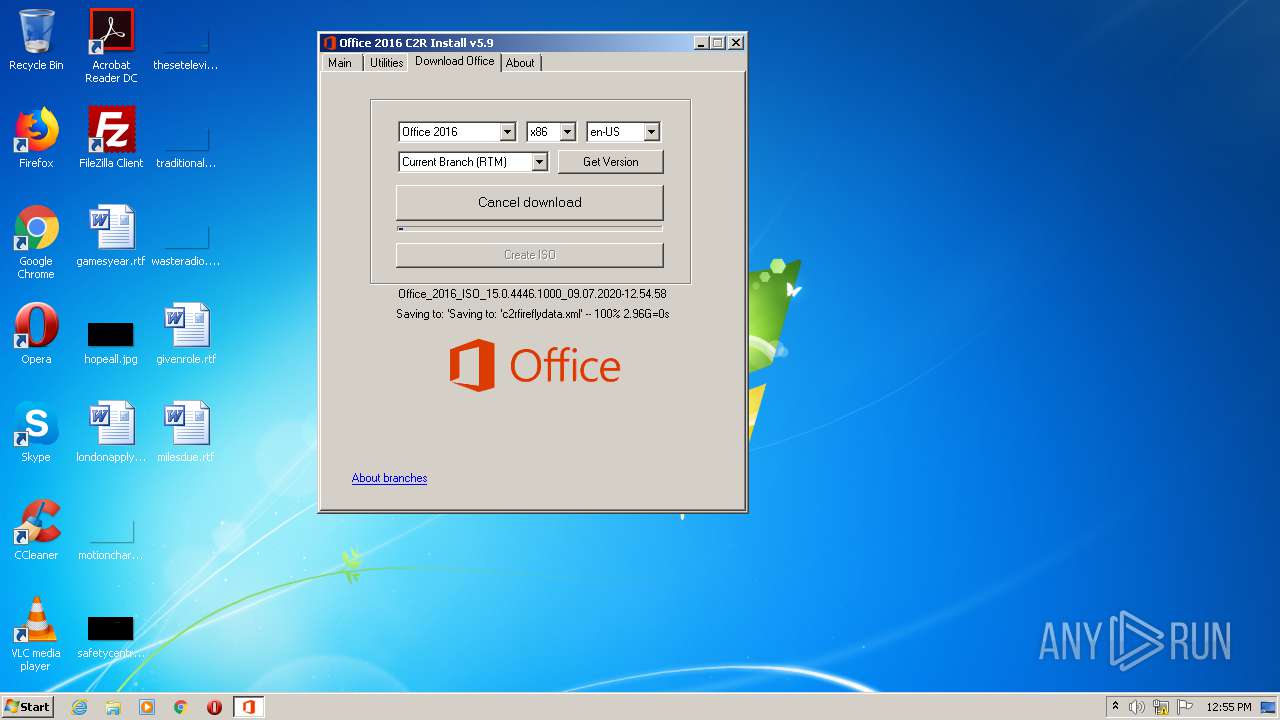
| 1732 | C:\Users\admin\AppData\Local\Temp\files\wget_oinstall.exe --continue --tries=0 --timestamping --force-directories --no-host-directories --cut-dirs=2 http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/c2rfireflydata.xml http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_15.0.4446.1000.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/fre.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/i320.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/i640.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/s320.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/stream.x86.en-us.dat http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/i321033.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/i641033.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/s321033.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/stream.x86.x-none.dat http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/stream.x86.x-none.dat.cobra http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/e320.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/e321033.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/r320.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/r321033.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/ui320.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/ui321033.cab http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/15.0.4446.1000/workaround.cab | C:\Users\admin\AppData\Local\Temp\files\wget_oinstall.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 8 Modules
| |||||||||||||||
| 2044 | "C:\Windows\System32\cmd.exe" /D /c files.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2060 | cscript.exe ospp.vbs //NoLogo | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2176 | Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2280 | "C:\Windows\System32\cmd.exe" /D /c Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS dir=in action=allow protocol=TCP localport= | C:\Windows\System32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2432 | "C:\Windows\System32\cmd.exe" /D /c "C:\Users\admin\AppData\Local\Temp\files\wget_oinstall.exe" --continue --tries=0 --timestamping --force-directories --no-host-directories --cut-dirs=2 http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab | C:\Windows\System32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2488 | "taskkill.exe" /t /f /IM wget_oinstall.exe | C:\Windows\system32\taskkill.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2560 | "C:\Windows\System32\cmd.exe" /D /c kmss.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
930
Read events
686
Write events
242
Delete events
2
Modification events
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\Experiment\officeclicktorun |
| Operation: | write | Name: | EdgeRequestPending |
Value: 0 | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\Experiment\officeclicktorun |
| Operation: | write | Name: | EcsRequestPending |
Value: 0 | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common |
| Operation: | write | Name: | UID |
Value: 00341D03873C6145B3F580624FDF039C | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\139\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Registration\USER-PC |
| Operation: | write | Name: | none.AttemptGetKey |
Value: 1 | |||
| (PID) Process: | (4056) Setup16.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\ClickToRun\Configuration |
| Operation: | write | Name: | ClientVersionToReport |
Value: | |||
Executable files
19
Suspicious files
14
Text files
11
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4056 | Setup16.exe | C:\Users\admin\AppData\Local\Temp\CabC049.tmp | — | |
MD5:— | SHA256:— | |||
| 4056 | Setup16.exe | C:\Users\admin\AppData\Local\Temp\TarC04A.tmp | — | |
MD5:— | SHA256:— | |||
| 4056 | Setup16.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\696F3DE637E6DE85B458996D49D759AD | der | |
MD5:— | SHA256:— | |||
| 4056 | Setup16.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:— | SHA256:— | |||
| 4056 | Setup16.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R9DABB2B8-5B3D-4F72-B508-25E7D2510E3E\v32.cab | compressed | |
MD5:— | SHA256:— | |||
| 4056 | Setup16.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7396C420A8E1BC1DA97F1AF0D10BAD21 | binary | |
MD5:— | SHA256:— | |||
| 4000 | Setup.exe | C:\Users\admin\AppData\Local\Temp\files\kmss.dat.aes | — | |
MD5:— | SHA256:— | |||
| 4000 | Setup.exe | C:\Users\admin\AppData\Local\Temp\files\aes.dat | — | |
MD5:— | SHA256:— | |||
| 4056 | Setup16.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F90F18257CBB4D84216AC1E1F3BB2C76 | der | |
MD5:— | SHA256:— | |||
| 4056 | Setup16.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A583E2A51BFBDC1E492A57B7C8325850 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
81
TCP/UDP connections
53
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4056 | Setup16.exe | GET | — | 184.86.251.136:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab | US | — | — | whitelisted |
4056 | Setup16.exe | HEAD | 403 | 104.108.144.60:80 | http://officecdn.microsoft.com/sg/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/MRO.cab | US | html | 368 b | whitelisted |
4056 | Setup16.exe | GET | 403 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/MRO.cab | US | html | 368 b | whitelisted |
4056 | Setup16.exe | GET | 403 | 104.108.144.60:80 | http://officecdn.microsoft.com/db/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/MRO.cab | US | html | 368 b | whitelisted |
4056 | Setup16.exe | HEAD | 403 | 104.108.144.60:80 | http://officecdn.microsoft.com/db/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/MRO.cab | US | html | 368 b | whitelisted |
4056 | Setup16.exe | GET | 403 | 104.108.144.60:80 | http://officecdn.microsoft.com/db/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/MRO.cab | US | html | 368 b | whitelisted |
4056 | Setup16.exe | GET | 403 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/MRO.cab | US | html | 368 b | whitelisted |
4056 | Setup16.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
4056 | Setup16.exe | HEAD | 301 | 104.108.144.60:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32.cab | US | html | 368 b | whitelisted |
4056 | Setup16.exe | GET | 403 | 104.108.144.60:80 | http://officecdn.microsoft.com/sg/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/MRO.cab | US | html | 368 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | Setup16.exe | 13.107.13.88:443 | ocos-office365-s2s.msedge.net | Microsoft Corporation | US | whitelisted |
4056 | Setup16.exe | 104.108.144.60:80 | officecdn.microsoft.com | TOT Public Company Limited | US | unknown |
4056 | Setup16.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3008 | wget_oinstall.exe | 104.108.144.60:80 | officecdn.microsoft.com | TOT Public Company Limited | US | unknown |
3296 | wget_oinstall.exe | 104.108.144.60:80 | officecdn.microsoft.com | TOT Public Company Limited | US | unknown |
3008 | wget_oinstall.exe | 184.86.251.154:80 | officecdn.microsoft.com.edgesuite.net | Comcast Cable Communications, LLC | US | suspicious |
4056 | Setup16.exe | 184.86.251.136:80 | officecdn.microsoft.com.edgesuite.net | Comcast Cable Communications, LLC | US | suspicious |
1732 | wget_oinstall.exe | 184.86.251.154:80 | officecdn.microsoft.com.edgesuite.net | Comcast Cable Communications, LLC | US | suspicious |
4056 | Setup16.exe | 13.107.42.23:443 | config.edge.skype.com | Microsoft Corporation | US | suspicious |
3296 | wget_oinstall.exe | 184.86.251.154:80 | officecdn.microsoft.com.edgesuite.net | Comcast Cable Communications, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officecdn.microsoft.com |
| whitelisted |
ocos-office365-s2s.msedge.net |
| whitelisted |
config.edge.skype.com |
| malicious |
officecdn.microsoft.com.edgesuite.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |