| File name: | 2023-03-07-Emotet-malspam-143908-UTC.eml |
| Full analysis: | https://app.any.run/tasks/2560254d-9dbf-4843-914a-a936ccde2ed9 |
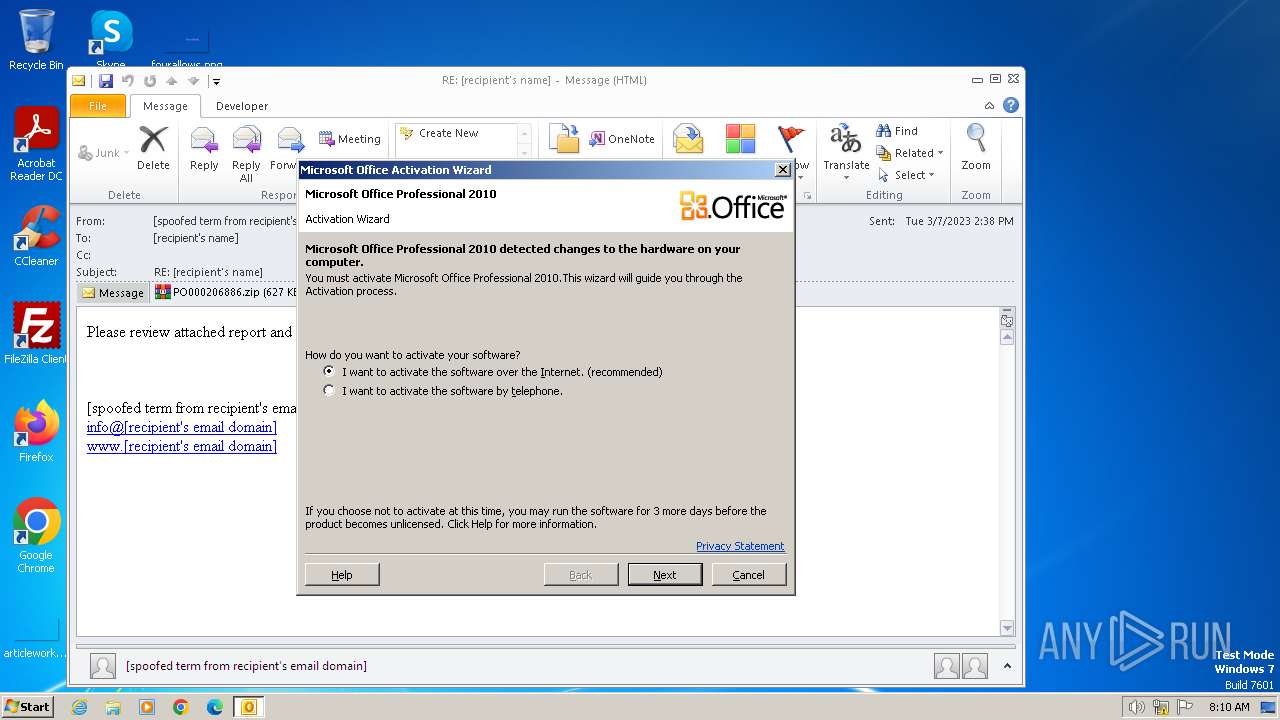
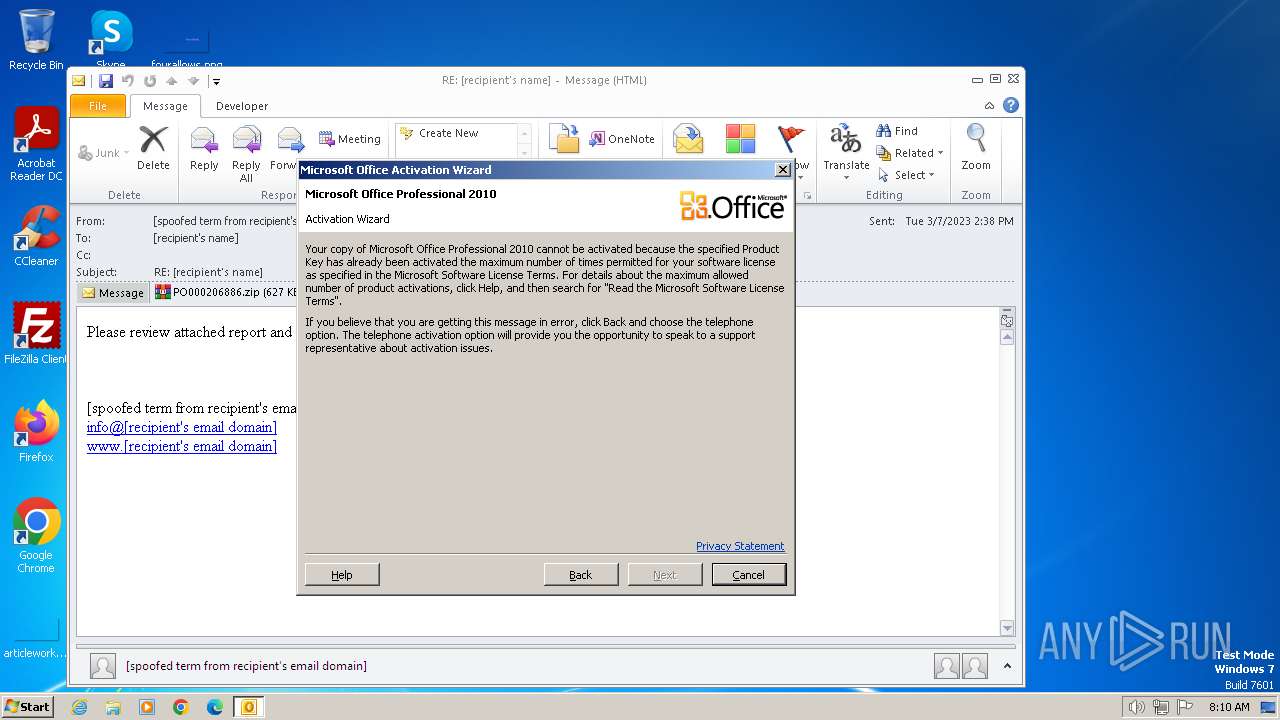
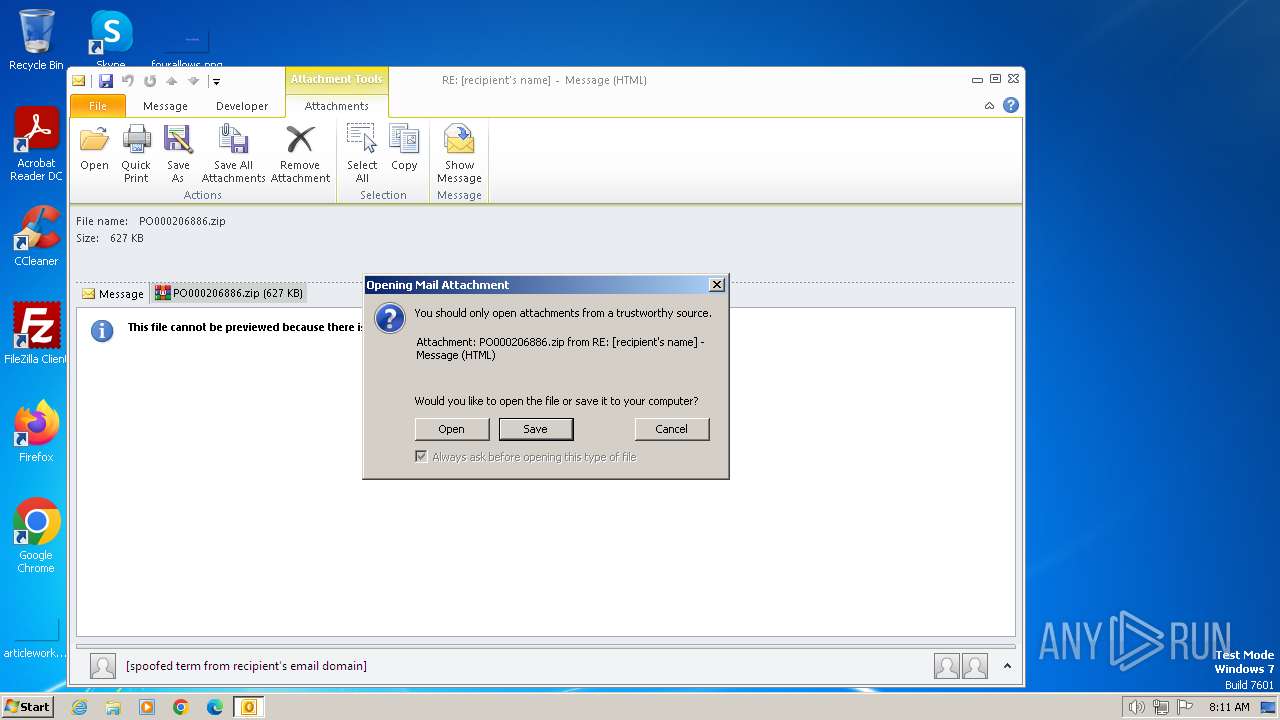
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 20, 2024, 07:10:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text, with CRLF line terminators |
| MD5: | B72A53C67A1B64BA6C73808744552F16 |
| SHA1: | 8CF1D2EAA5A585CE95456FDC3D11B258783E21F0 |
| SHA256: | FB64D3677A4413623FC21F81BB24B93943238BF626AA8AC14686FDF7AFDD08A0 |
| SSDEEP: | 3072:bR2Rnu7qK8PYvBecdx2xcV7g7rZYVk/YjILyyEol0/tn51haTNrghnJRP:eu70vgx2xcOHZxx3UT1qNrg7RP |
MALICIOUS
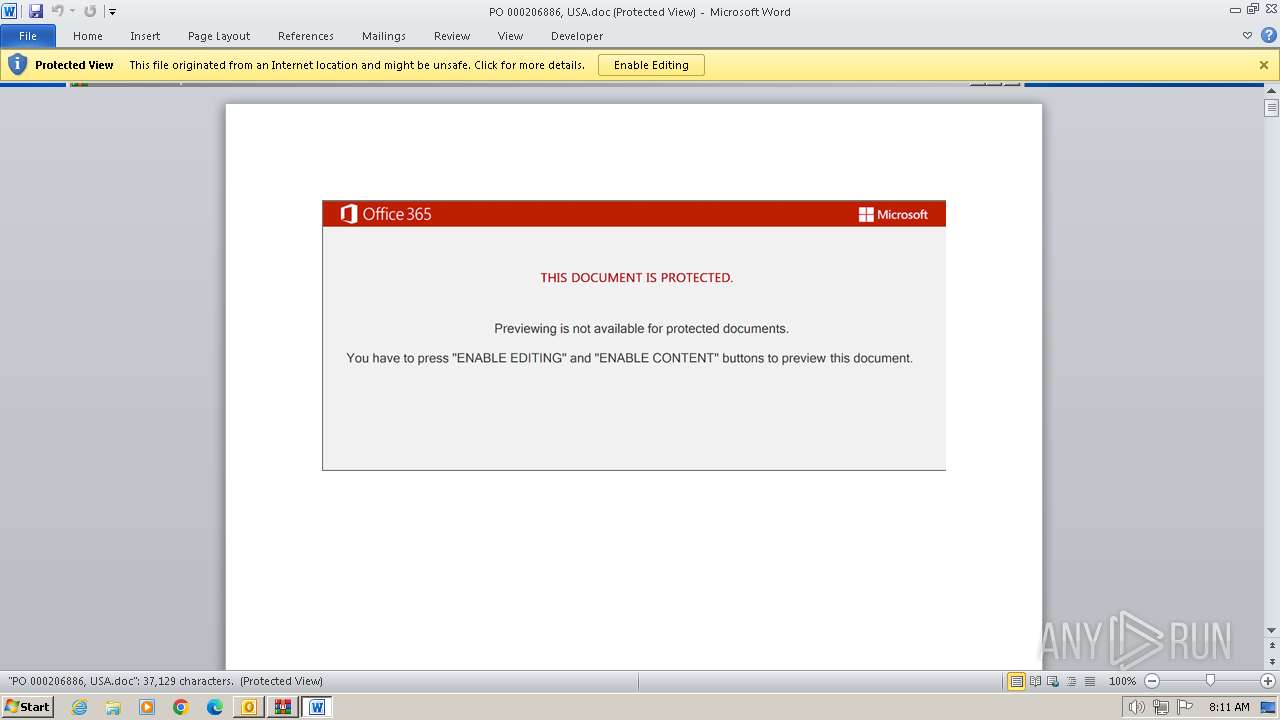
EMOTET has been detected (SURICATA)
- WINWORD.EXE (PID: 2812)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 2812)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2448)
Reads the computer name
- wmpnscfg.exe (PID: 2448)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2024)
The process uses the downloaded file
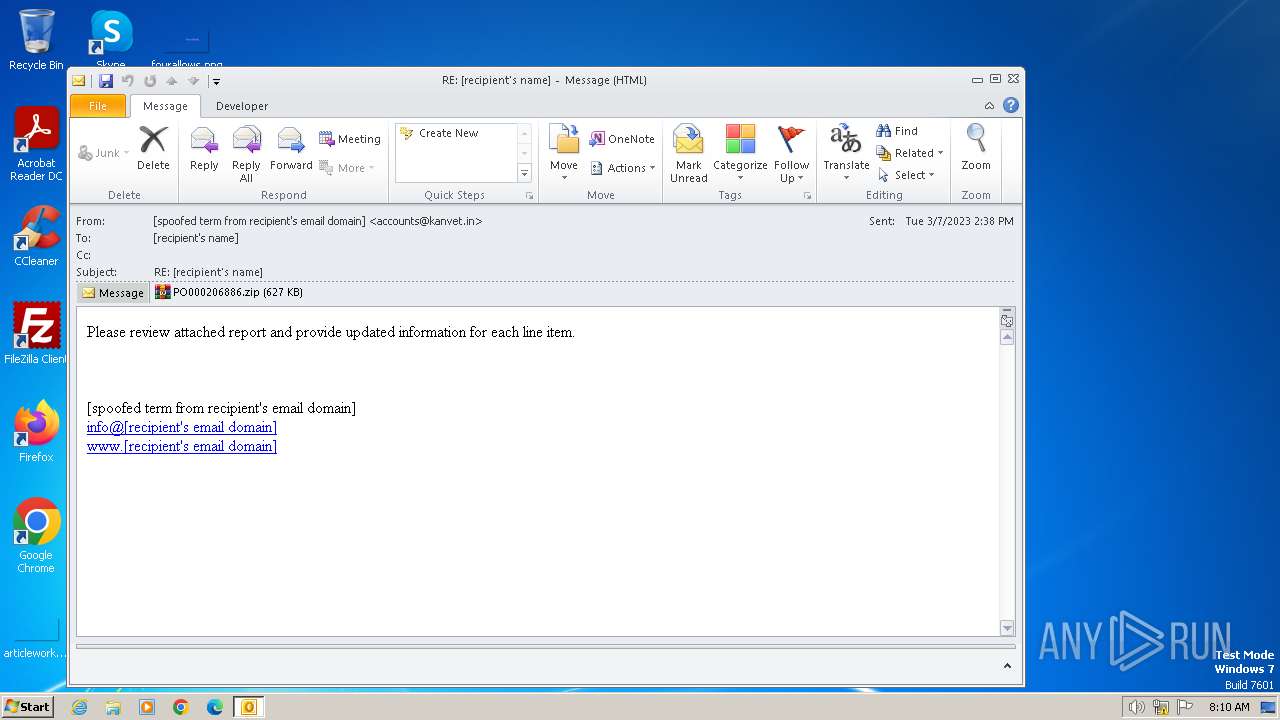
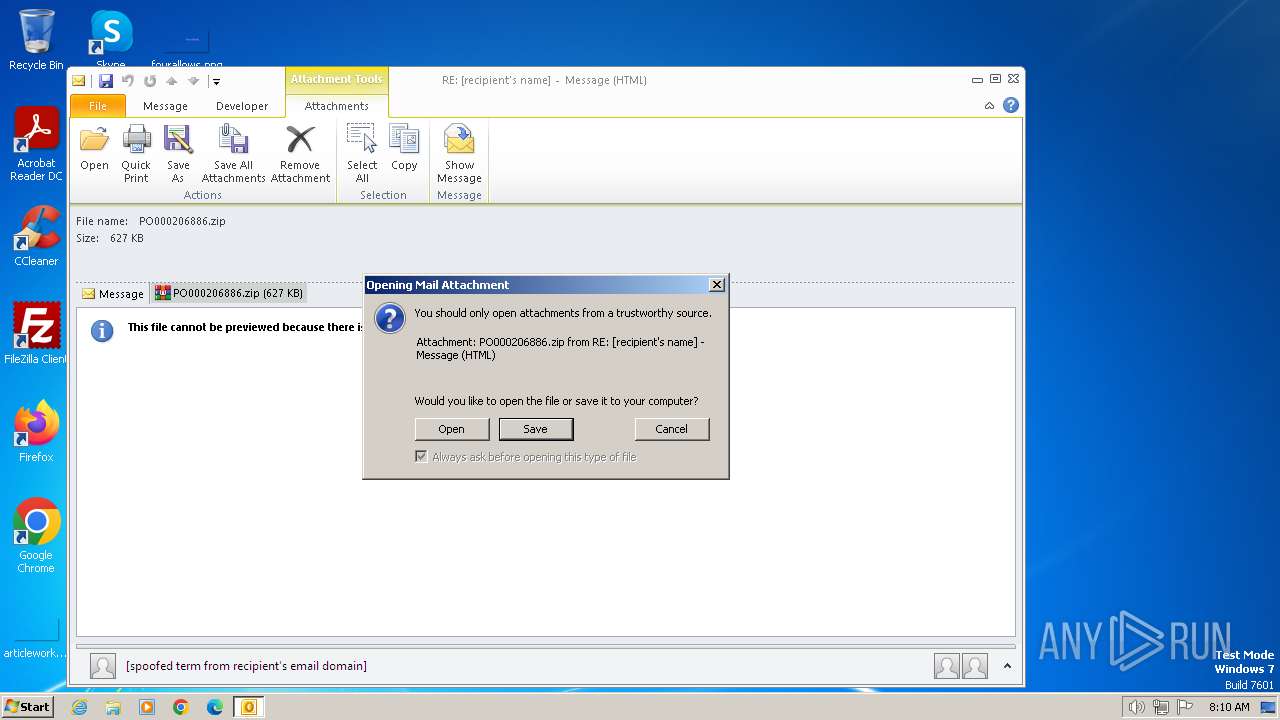
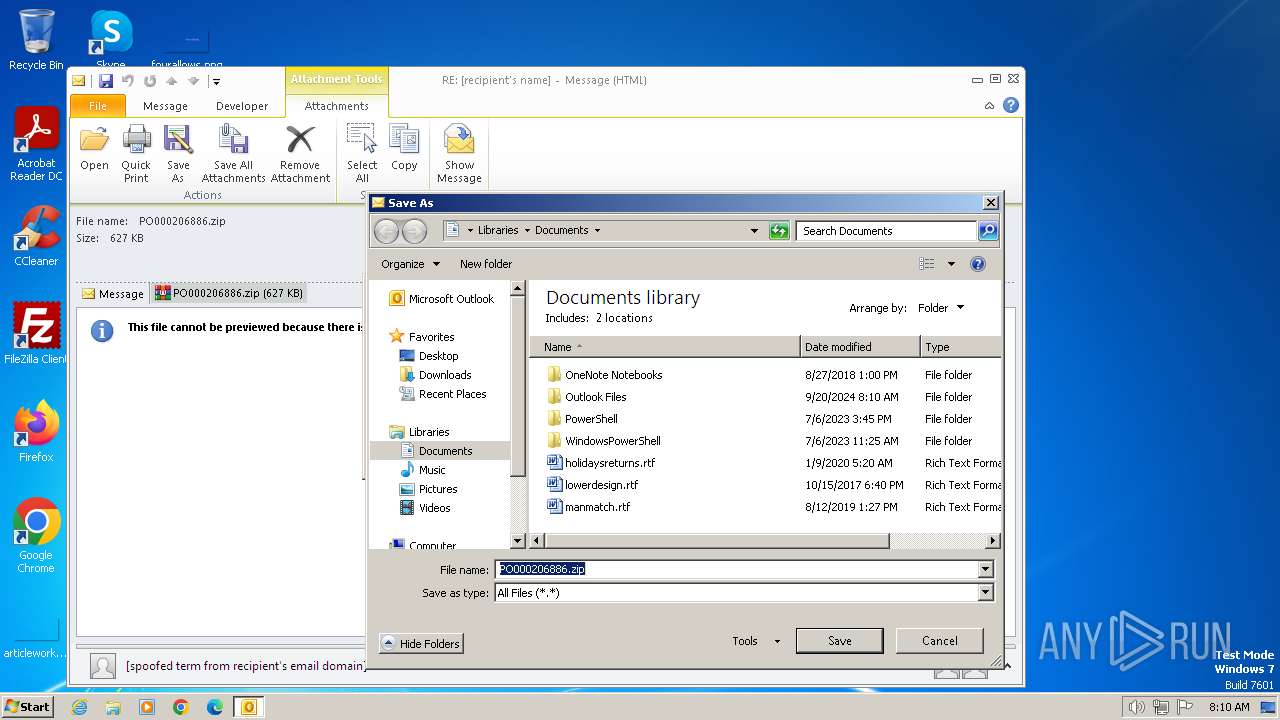
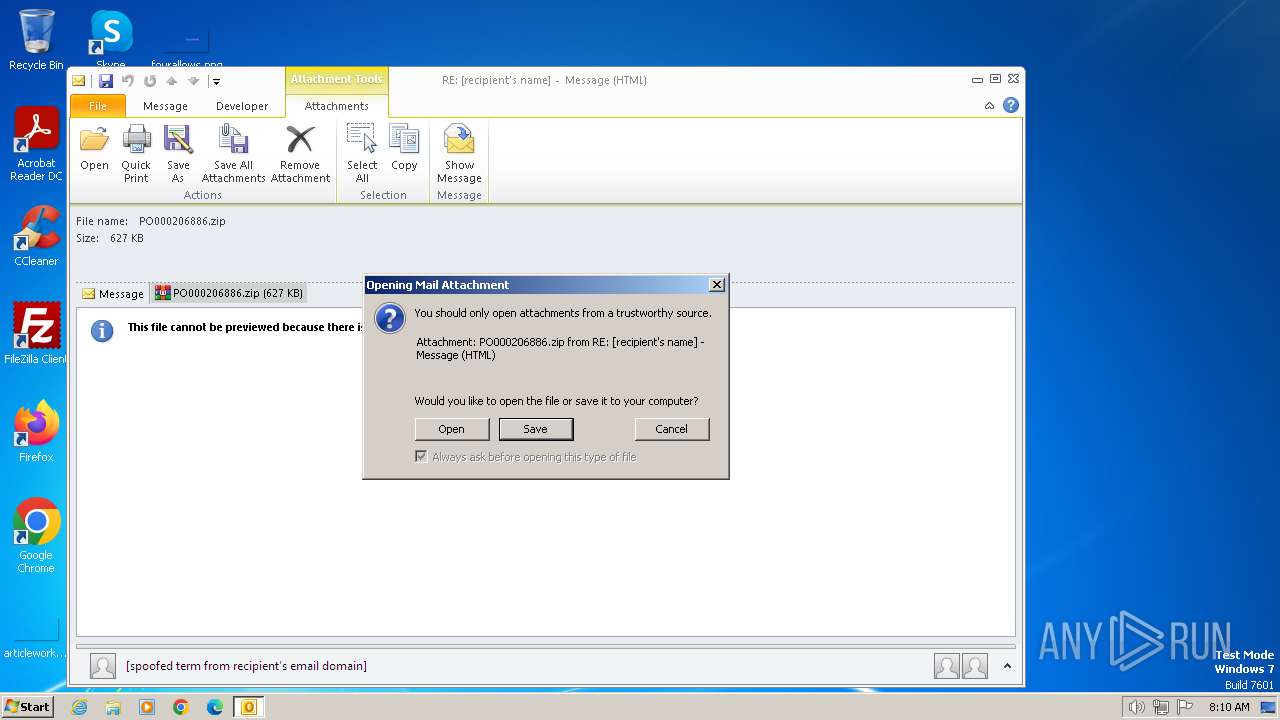
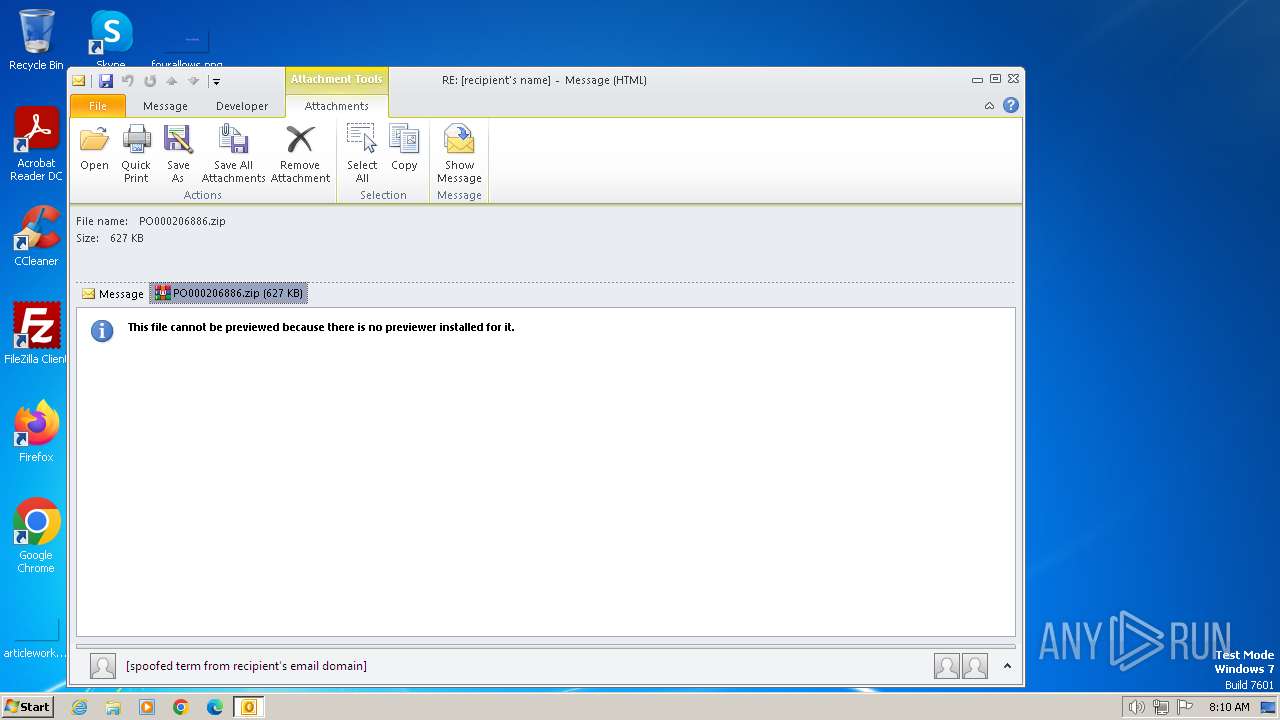
- OUTLOOK.EXE (PID: 2108)
- WinRAR.exe (PID: 2024)
Manual execution by a user
- wmpnscfg.exe (PID: 2448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 1) (100) |
|---|
Total processes
41
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
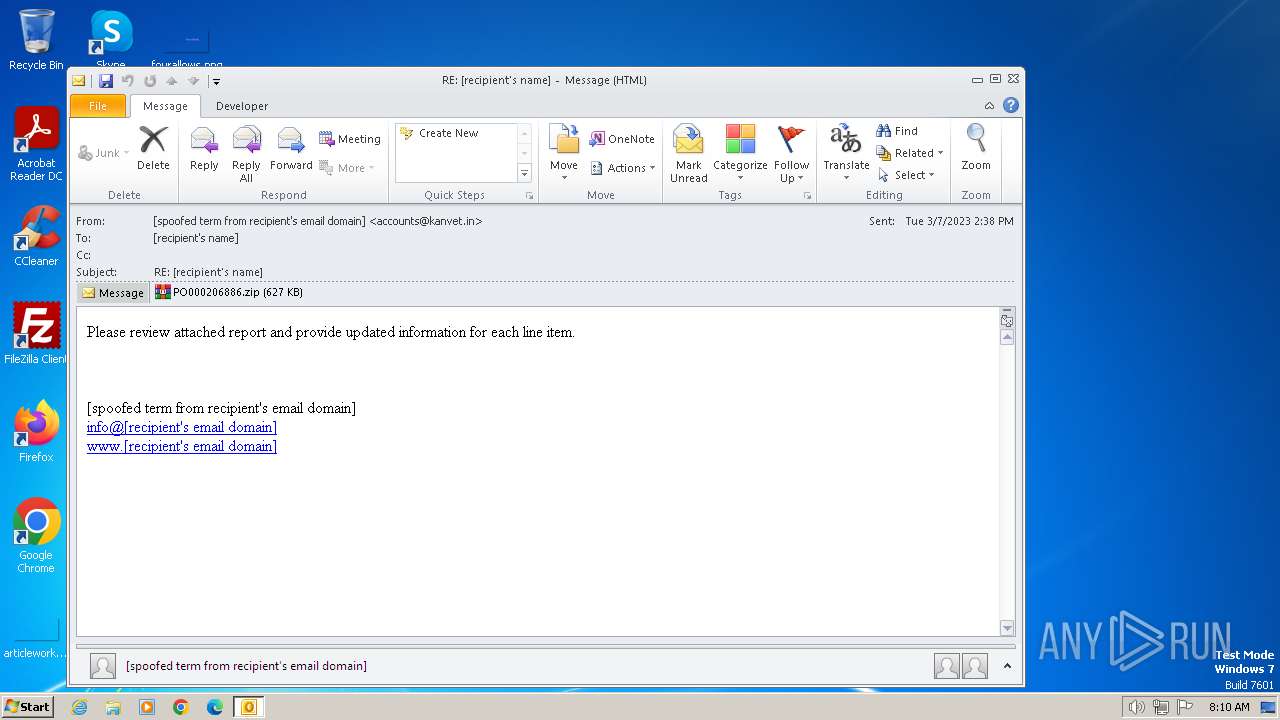
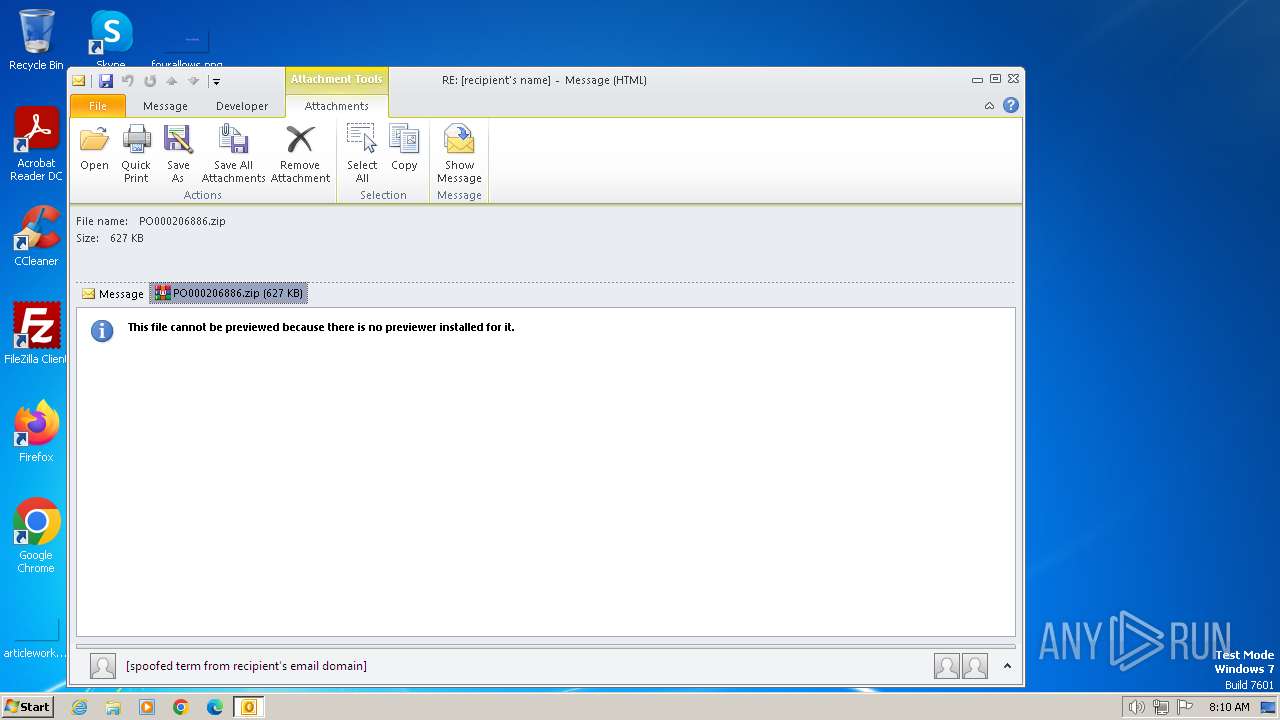
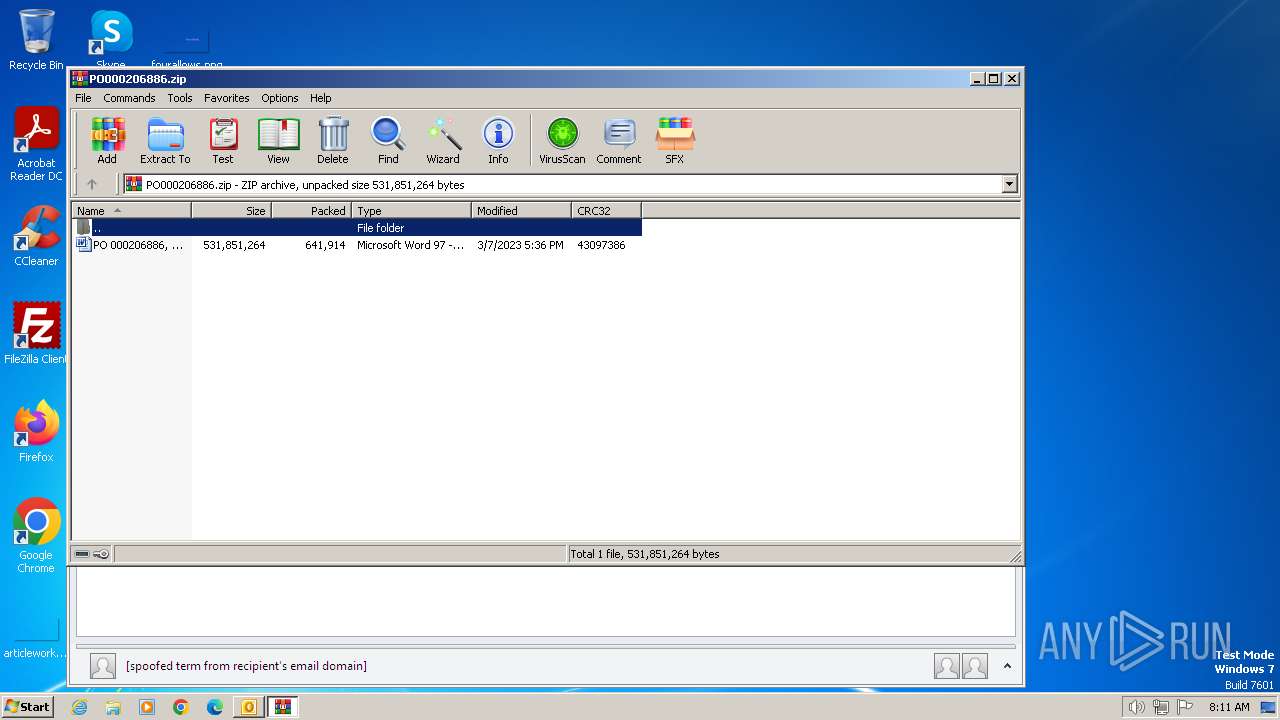
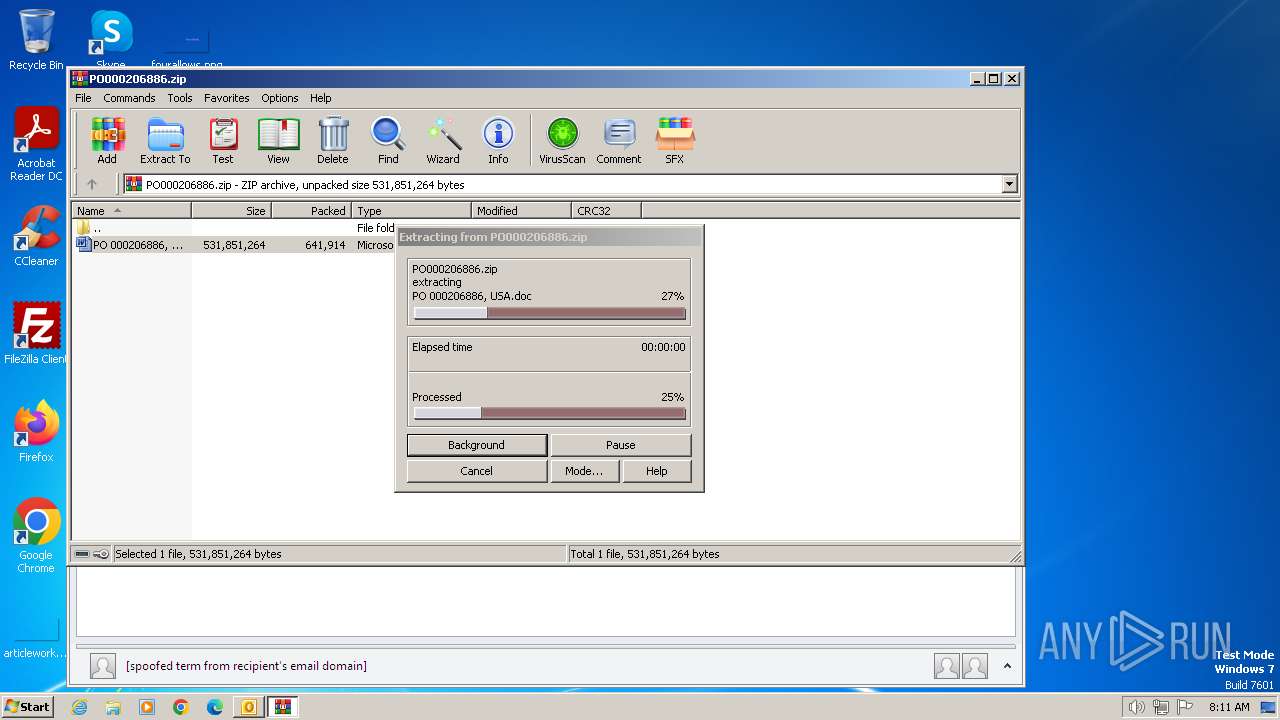
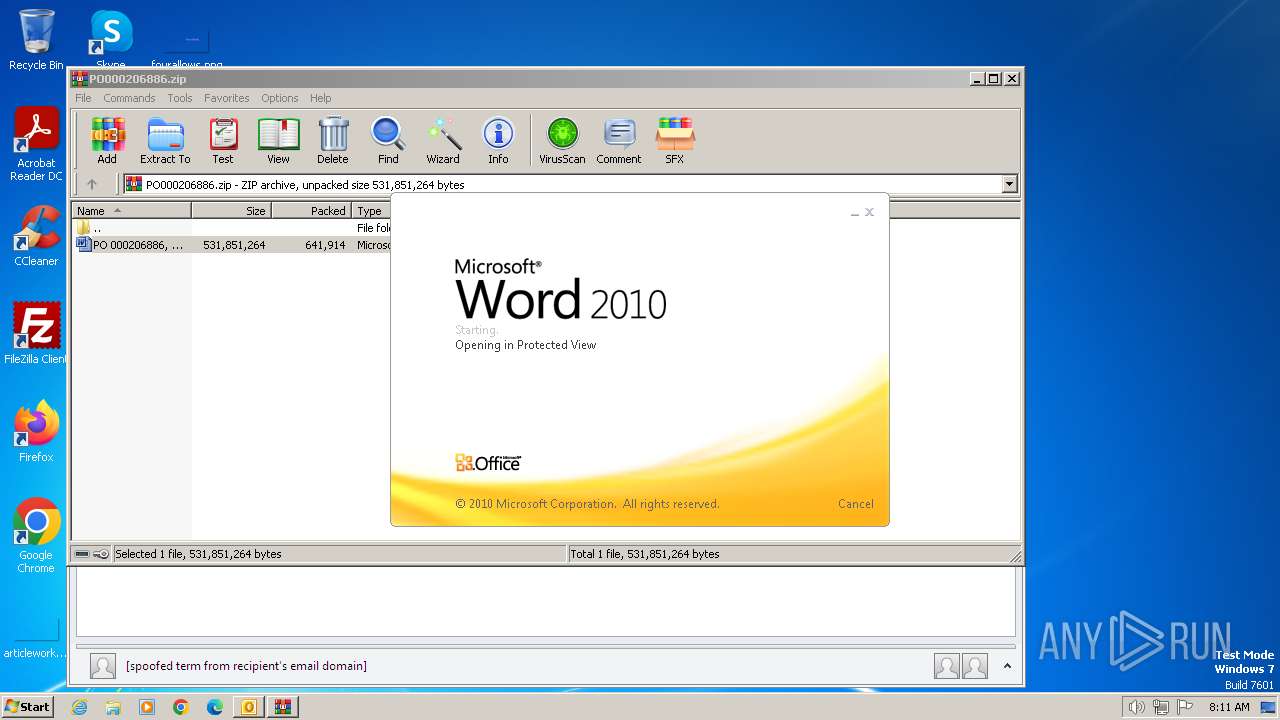
| 2024 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\G1KNUSE5\PO000206886.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2108 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml C:\Users\admin\AppData\Local\Temp\2023-03-07-Emotet-malspam-143908-UTC.eml | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
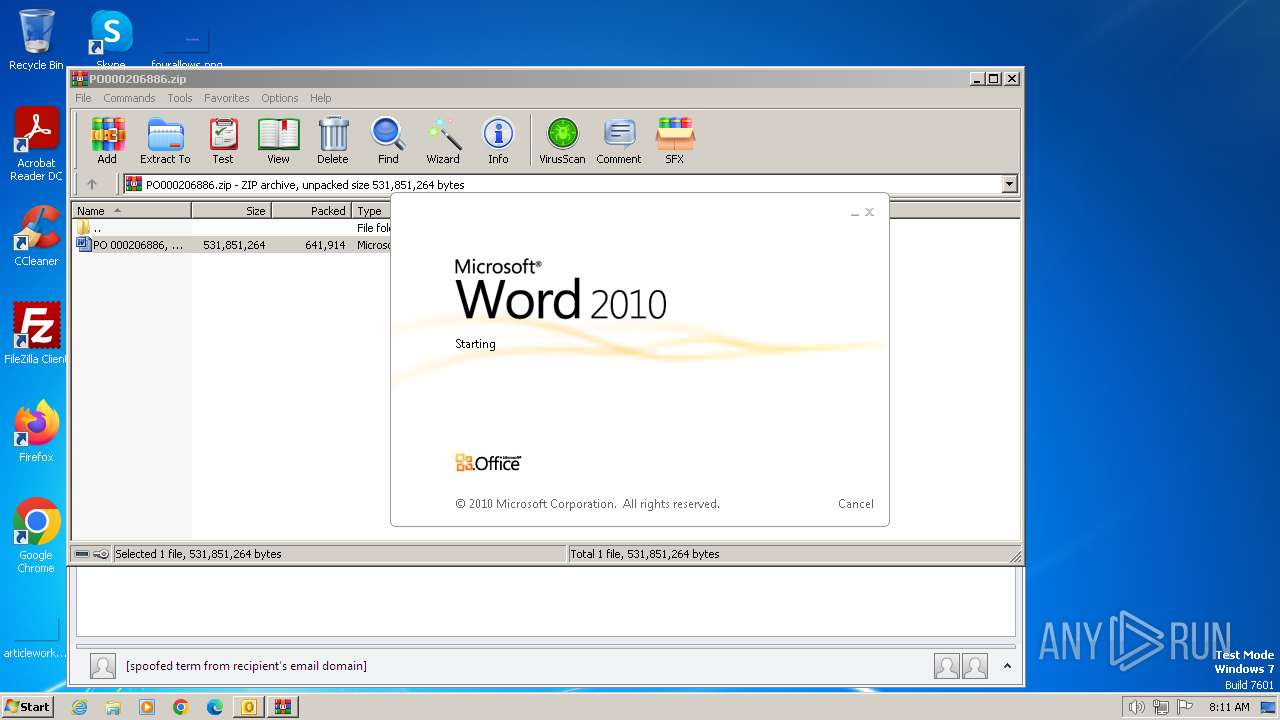
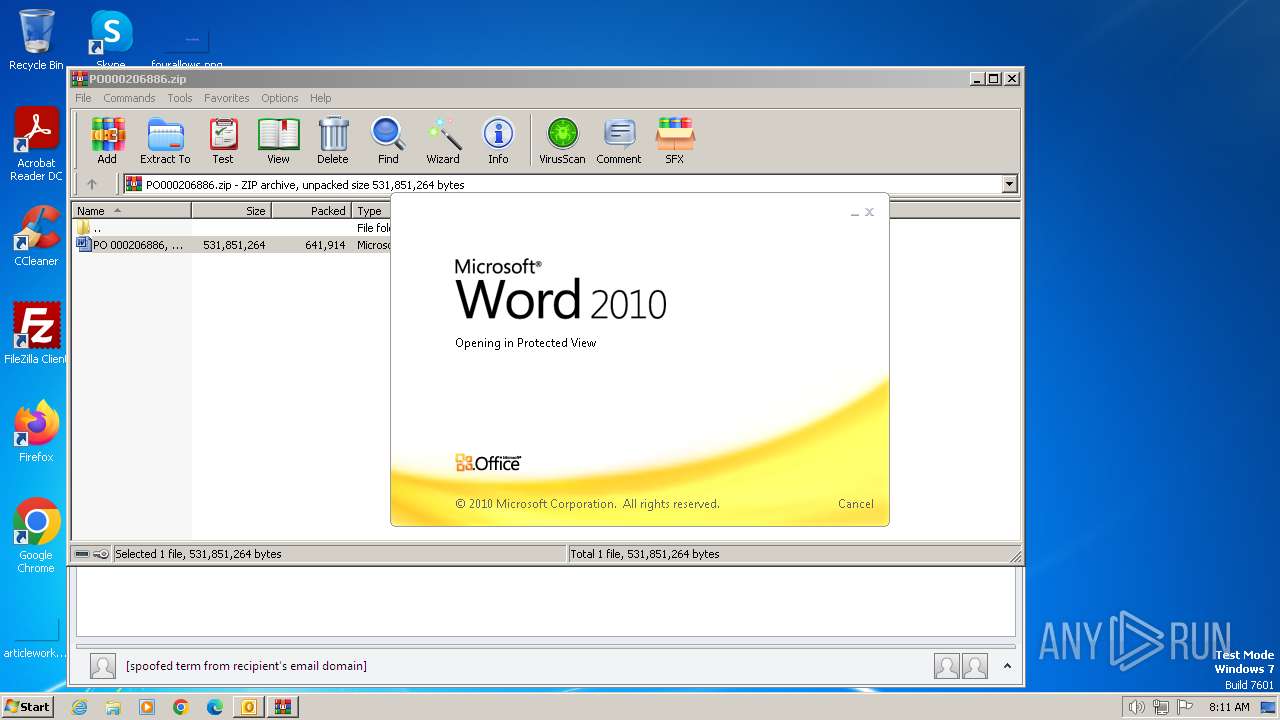
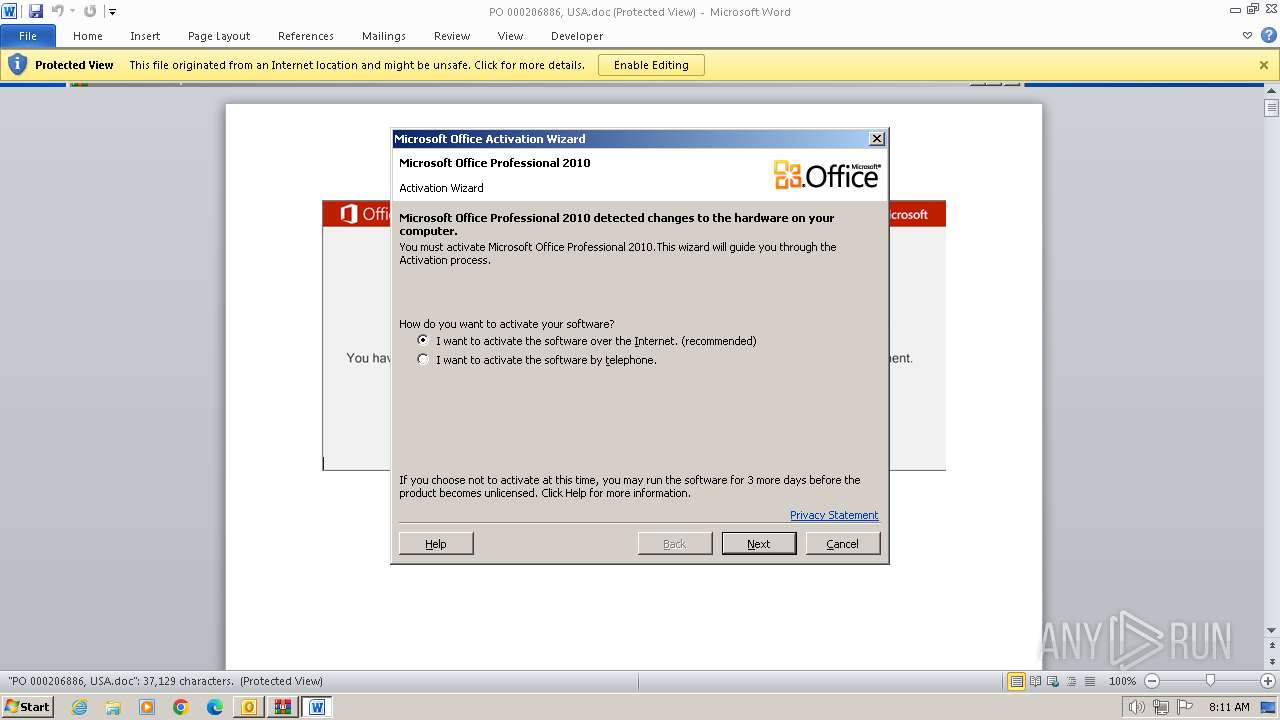
| 2812 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa2024.7702\PO 000206886, USA.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3720 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
19 230
Read events
18 013
Write events
1 044
Delete events
173
Modification events
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2108) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
7
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA364.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2108 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2024 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2024.7702\PO 000206886, USA.doc | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8D56.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2812 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_A1DF0F7B-6079-4B0A-BCCF-E53E0C65C3FB.0\71EC6CE7.doc | — | |
MD5:— | SHA256:— | |||
| 2108 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 2108 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\G1KNUSE5\PO000206886.zip | compressed | |
MD5:9118C9FCE73C1E93E50F01D5FEF6C476 | SHA256:AFBC2421CD177BF8CA5E42F8B51C0330F1A7BEC7B3214483CE653C691DBBB235 | |||
| 2108 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpA672.tmp | binary | |
MD5:71FCE4F48A62E815F8D2A652E1F13400 | SHA256:7DE9F97F043AFBA2EE760C07DDE50B29EDED57BD5A842A59394B66543DF97943 | |||
| 2108 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\G1KNUSE5\PO000206886.zip:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 2108 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{923FB72C-5F85-40C2-9168-18EB81552B24}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
12
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2108 | OUTLOOK.EXE | POST | 302 | 184.28.89.167:80 | http://go.microsoft.com/fwlink/?LinkID=120751 | unknown | — | — | whitelisted |
2108 | OUTLOOK.EXE | POST | 302 | 184.28.89.167:80 | http://go.microsoft.com/fwlink/?LinkID=120750 | unknown | — | — | whitelisted |
2108 | OUTLOOK.EXE | POST | 302 | 184.28.89.167:80 | http://go.microsoft.com/fwlink/?LinkID=120752 | unknown | — | — | whitelisted |
2812 | WINWORD.EXE | GET | 403 | 211.149.240.116:80 | http://www.189dom.com/xue80/C0aJr5tfI5Pvi8m/?081154 | unknown | — | — | unknown |
2812 | WINWORD.EXE | GET | 301 | 101.99.3.20:80 | http://mtp.evotek.vn/wp-content/L/?081147 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2108 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2108 | OUTLOOK.EXE | 184.28.89.167:80 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
2108 | OUTLOOK.EXE | 40.91.76.224:443 | activation.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2812 | WINWORD.EXE | 27.54.81.161:443 | midcoastsupplies.com.au | Dreamscape Networks Limited | AU | unknown |
2812 | WINWORD.EXE | 101.99.3.20:80 | mtp.evotek.vn | CMC Telecom Infrastructure Company | VN | malicious |
2812 | WINWORD.EXE | 101.99.3.20:443 | mtp.evotek.vn | CMC Telecom Infrastructure Company | VN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.messenger.msn.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |
midcoastsupplies.com.au |
| unknown |
mtp.evotek.vn |
| unknown |
achilles.com.vn |
| unknown |
www.189dom.com |
| unknown |
esentai-gourmet.kz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2812 | WINWORD.EXE | A Network Trojan was detected | ET MALWARE Observed Emotet Maldoc Retrieving Payload (2023-03-07) M1 |
2812 | WINWORD.EXE | A Network Trojan was detected | ET MALWARE Observed Emotet Maldoc Retrieving Payload (2023-03-07) M1 |