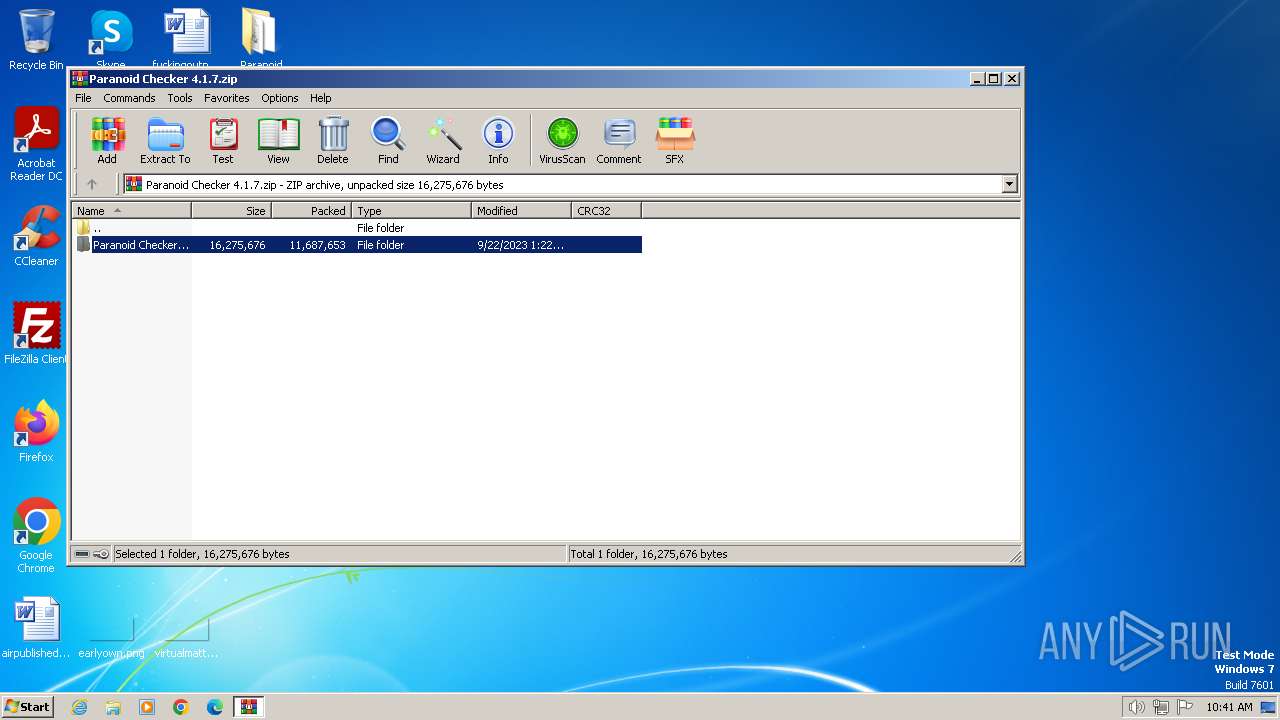
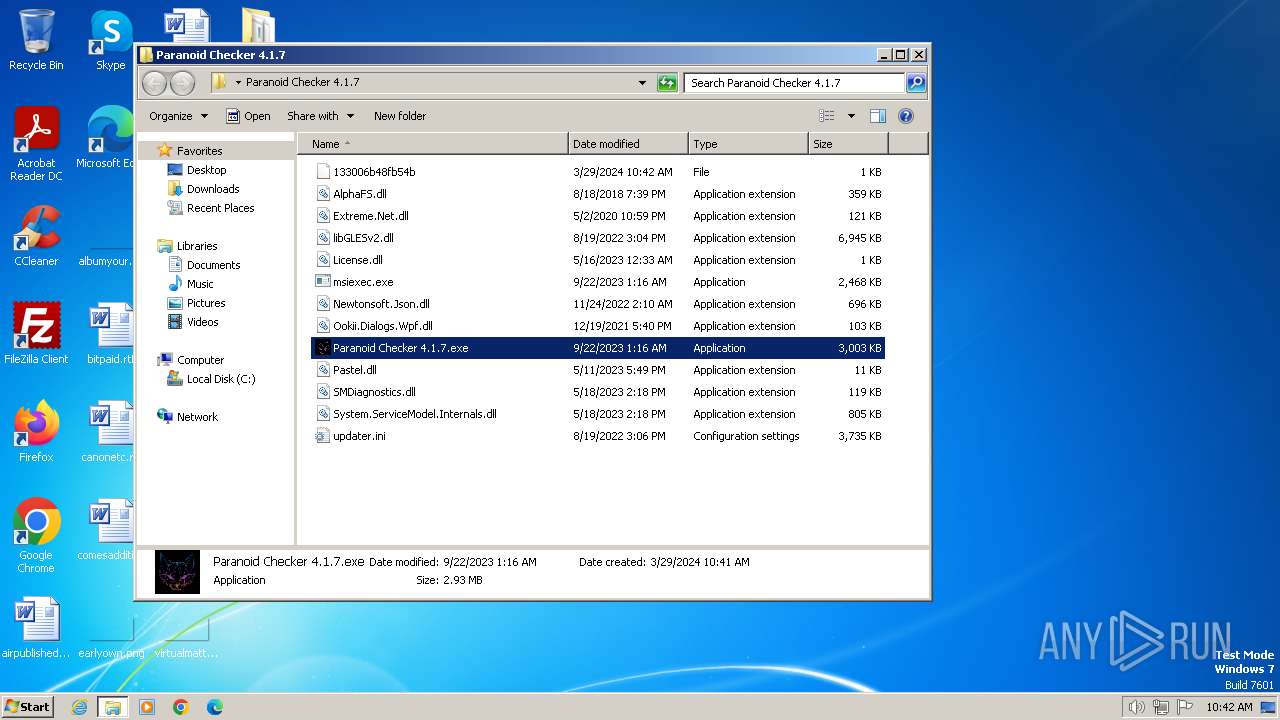
| File name: | Paranoid Checker 4.1.7.zip |
| Full analysis: | https://app.any.run/tasks/b451f34e-d303-4800-93b3-f4ff9e585e1e |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | March 29, 2024, 10:40:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
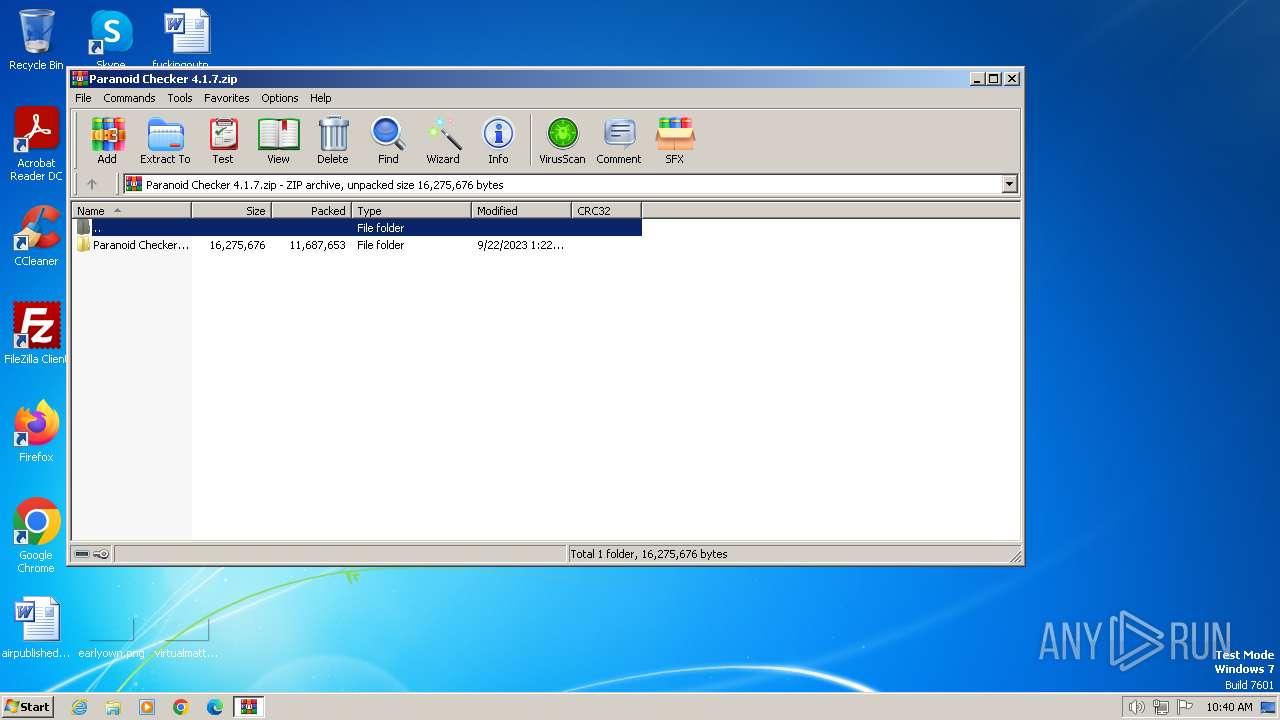
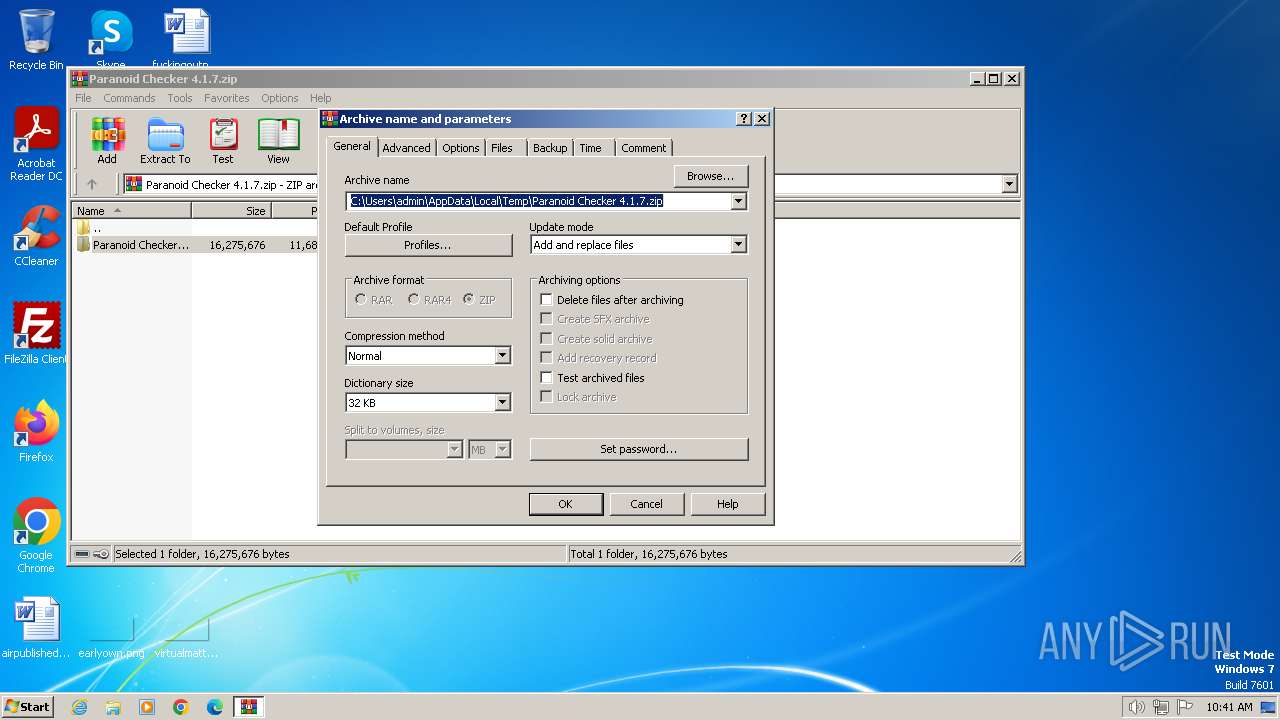
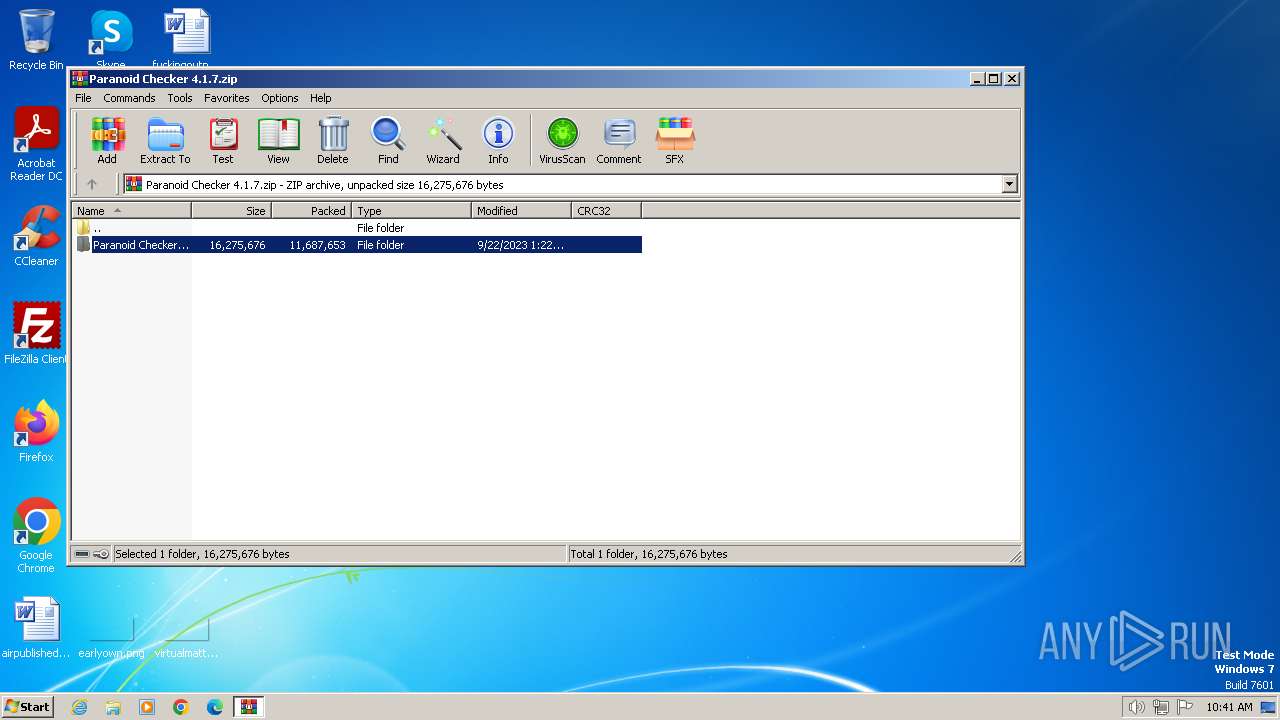
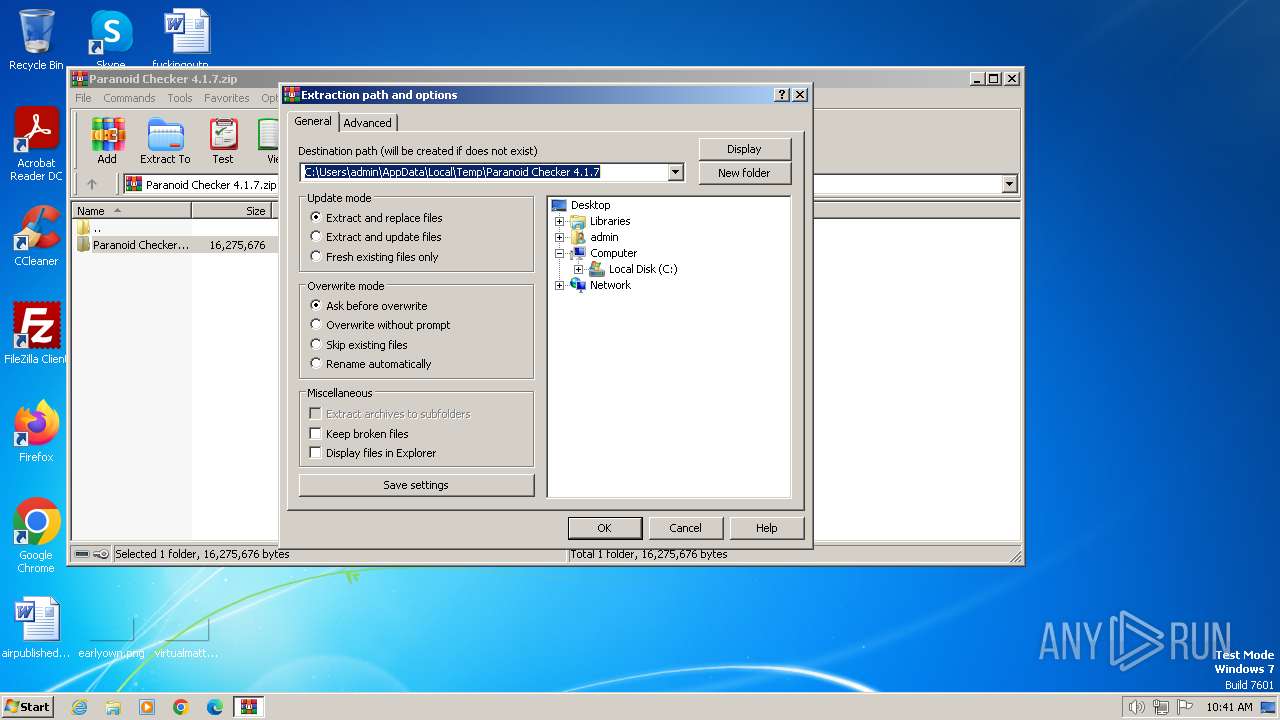
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 604ADFEACE617392A885BAE5BA91DEF9 |
| SHA1: | 75F6FB6DD88F2057850D4DBE6038D22BB068223B |
| SHA256: | FB63A03E752329D09522C7813CB212331AF2D18430B8CD2E9DB937CB555C382D |
| SSDEEP: | 98304:OadcEE9a2ur1GbsJrEjhPT9tQYqKOtPBLRQBdfhRk9f3OwLb4k/N8GDEEIJt0qUr:FrXTmrt86rraVGvJItBhUgX9eXZOYQ |
MALICIOUS
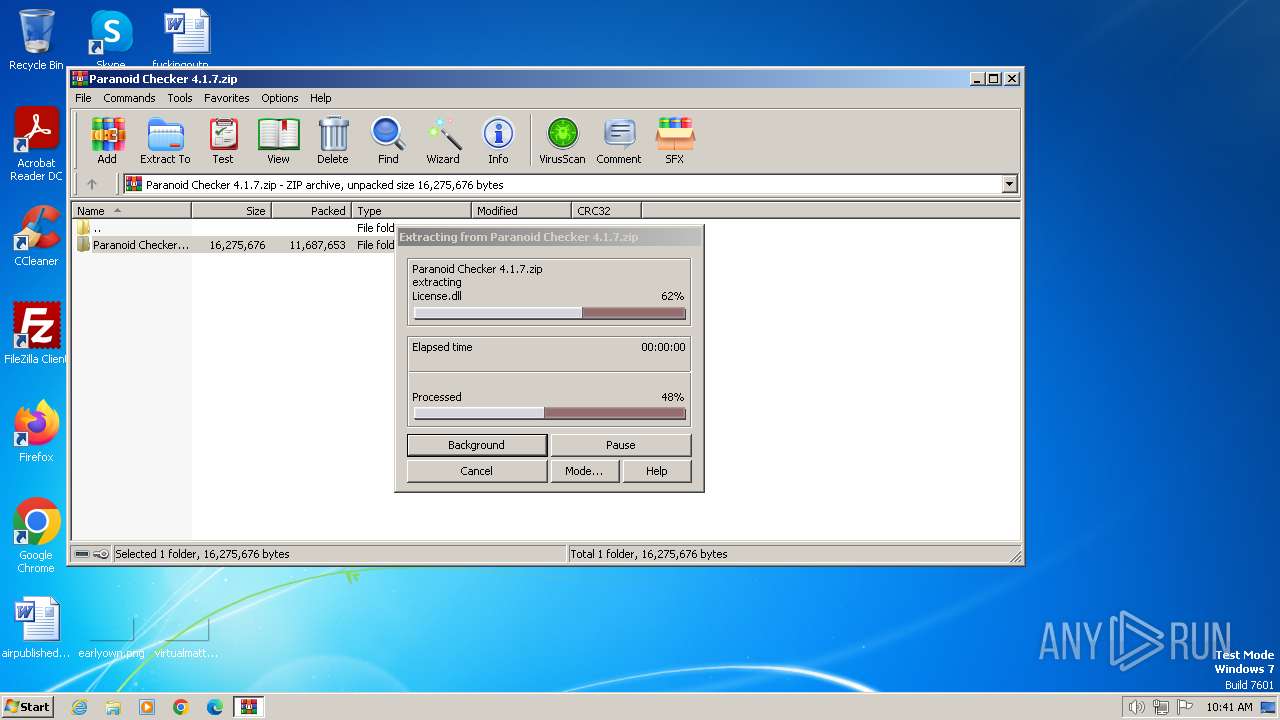
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1696)
- Paranoid Checker 4.1.7.exe (PID: 1496)
- msComponentsaves.exe (PID: 3400)
- System.exe (PID: 3520)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2364)
- wscript.exe (PID: 748)
- wscript.exe (PID: 3292)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 908)
- wscript.exe (PID: 3480)
- wscript.exe (PID: 3828)
- wscript.exe (PID: 3844)
- wscript.exe (PID: 2208)
- wscript.exe (PID: 2888)
- wscript.exe (PID: 2320)
- wscript.exe (PID: 1408)
- wscript.exe (PID: 2308)
- wscript.exe (PID: 1936)
- wscript.exe (PID: 2768)
DCRAT has been detected (YARA)
- System.exe (PID: 3520)
- System.exe (PID: 1536)
- System.exe (PID: 3304)
- System.exe (PID: 3488)
- System.exe (PID: 1900)
Deletes a file (SCRIPT)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 3844)
- wscript.exe (PID: 2320)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 1696)
Reads security settings of Internet Explorer
- Paranoid Checker 4.1.7.exe (PID: 1496)
- Paranoid Checker 4.1.7.exe (PID: 3684)
- msComponentsaves.exe (PID: 3400)
- System.exe (PID: 3520)
- System.exe (PID: 1536)
- Paranoid Checker 4.1.7.exe (PID: 3568)
- System.exe (PID: 3304)
- Paranoid Checker 4.1.7.exe (PID: 2648)
- System.exe (PID: 3488)
- Paranoid Checker 4.1.7.exe (PID: 3820)
- System.exe (PID: 1900)
Reads the Internet Settings
- Paranoid Checker 4.1.7.exe (PID: 1496)
- Paranoid Checker 4.1.7.exe (PID: 3684)
- wscript.exe (PID: 2364)
- msComponentsaves.exe (PID: 3400)
- System.exe (PID: 3520)
- wscript.exe (PID: 748)
- System.exe (PID: 1536)
- Paranoid Checker 4.1.7.exe (PID: 3568)
- wscript.exe (PID: 3480)
- System.exe (PID: 3304)
- Paranoid Checker 4.1.7.exe (PID: 2648)
- wscript.exe (PID: 2208)
- System.exe (PID: 3488)
- Paranoid Checker 4.1.7.exe (PID: 3820)
- wscript.exe (PID: 1408)
- System.exe (PID: 1900)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2364)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 748)
- wscript.exe (PID: 3480)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 2208)
- wscript.exe (PID: 3844)
- wscript.exe (PID: 2320)
- wscript.exe (PID: 1408)
Executing commands from a ".bat" file
- wscript.exe (PID: 2364)
- wscript.exe (PID: 748)
- wscript.exe (PID: 3480)
- wscript.exe (PID: 2208)
- wscript.exe (PID: 1408)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2364)
- wscript.exe (PID: 748)
- wscript.exe (PID: 3480)
- wscript.exe (PID: 2208)
- wscript.exe (PID: 1408)
The process creates files with name similar to system file names
- msComponentsaves.exe (PID: 3400)
Executed via WMI
- schtasks.exe (PID: 2888)
- schtasks.exe (PID: 2484)
- schtasks.exe (PID: 2384)
- schtasks.exe (PID: 880)
- schtasks.exe (PID: 680)
- schtasks.exe (PID: 1772)
- schtasks.exe (PID: 1848)
- schtasks.exe (PID: 2972)
- schtasks.exe (PID: 3028)
- schtasks.exe (PID: 1780)
- schtasks.exe (PID: 1404)
- schtasks.exe (PID: 3088)
- schtasks.exe (PID: 2040)
- schtasks.exe (PID: 3616)
- schtasks.exe (PID: 1540)
- schtasks.exe (PID: 2772)
- schtasks.exe (PID: 2172)
- schtasks.exe (PID: 1596)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3912)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 2924)
- cmd.exe (PID: 2044)
- cmd.exe (PID: 2384)
Starts itself from another location
- msComponentsaves.exe (PID: 3400)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 3292)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 908)
- wscript.exe (PID: 3844)
- wscript.exe (PID: 3828)
- wscript.exe (PID: 2320)
- wscript.exe (PID: 2888)
- wscript.exe (PID: 1936)
- wscript.exe (PID: 2308)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 3844)
- wscript.exe (PID: 2320)
- wscript.exe (PID: 1936)
Reads settings of System Certificates
- System.exe (PID: 3520)
- System.exe (PID: 1536)
- System.exe (PID: 3304)
- System.exe (PID: 3488)
- System.exe (PID: 1900)
The process executes VB scripts
- System.exe (PID: 3520)
- System.exe (PID: 1536)
- System.exe (PID: 3304)
- System.exe (PID: 3488)
- System.exe (PID: 1900)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 3844)
- wscript.exe (PID: 2320)
- wscript.exe (PID: 1936)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 3292)
- wscript.exe (PID: 908)
- wscript.exe (PID: 3828)
- wscript.exe (PID: 2888)
- wscript.exe (PID: 2308)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 3844)
- wscript.exe (PID: 2320)
INFO
Checks supported languages
- Paranoid Checker 4.1.7.exe (PID: 1496)
- Paranoid Checker 4.1.7.exe (PID: 3684)
- msComponentsaves.exe (PID: 3400)
- System.exe (PID: 3520)
- System.exe (PID: 1536)
- msComponentsaves.exe (PID: 1264)
- Paranoid Checker 4.1.7.exe (PID: 3568)
- msComponentsaves.exe (PID: 4028)
- System.exe (PID: 3304)
- Paranoid Checker 4.1.7.exe (PID: 2648)
- msComponentsaves.exe (PID: 3772)
- Paranoid Checker 4.1.7.exe (PID: 3820)
- System.exe (PID: 3488)
- msComponentsaves.exe (PID: 2668)
- System.exe (PID: 1900)
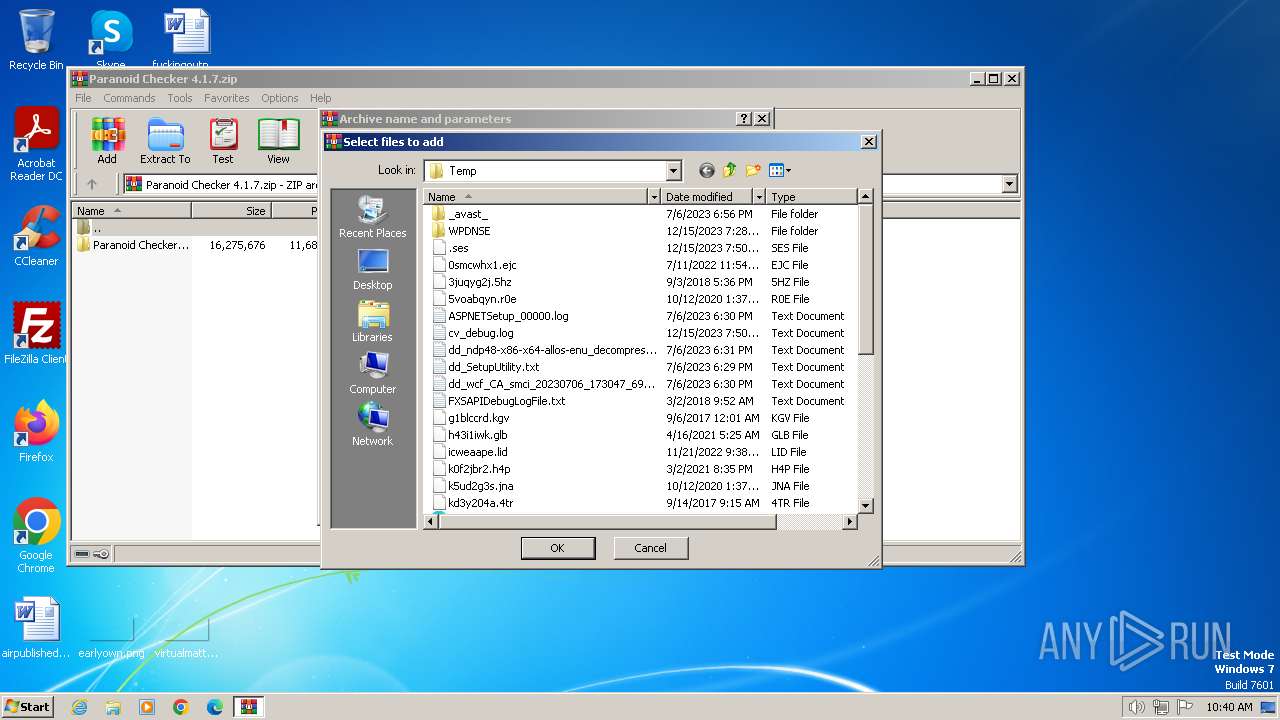
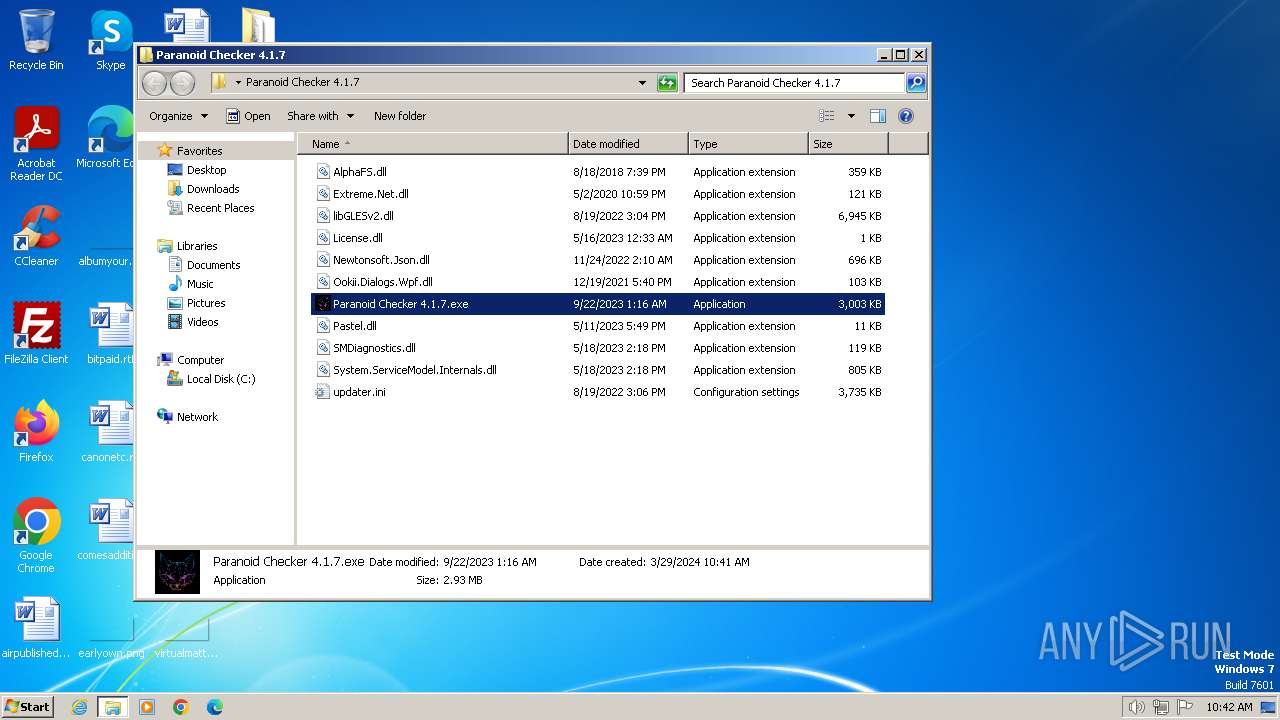
Manual execution by a user
- Paranoid Checker 4.1.7.exe (PID: 1496)
- Paranoid Checker 4.1.7.exe (PID: 3684)
- Paranoid Checker 4.1.7.exe (PID: 3568)
- Paranoid Checker 4.1.7.exe (PID: 2648)
- Paranoid Checker 4.1.7.exe (PID: 3820)
Reads the computer name
- Paranoid Checker 4.1.7.exe (PID: 1496)
- Paranoid Checker 4.1.7.exe (PID: 3684)
- msComponentsaves.exe (PID: 3400)
- System.exe (PID: 3520)
- System.exe (PID: 1536)
- msComponentsaves.exe (PID: 1264)
- Paranoid Checker 4.1.7.exe (PID: 3568)
- msComponentsaves.exe (PID: 4028)
- System.exe (PID: 3304)
- Paranoid Checker 4.1.7.exe (PID: 2648)
- msComponentsaves.exe (PID: 3772)
- System.exe (PID: 3488)
- Paranoid Checker 4.1.7.exe (PID: 3820)
- System.exe (PID: 1900)
- msComponentsaves.exe (PID: 2668)
Reads Environment values
- msComponentsaves.exe (PID: 3400)
- System.exe (PID: 3520)
- msComponentsaves.exe (PID: 1264)
- System.exe (PID: 1536)
- msComponentsaves.exe (PID: 4028)
- System.exe (PID: 3304)
- msComponentsaves.exe (PID: 3772)
- System.exe (PID: 3488)
- msComponentsaves.exe (PID: 2668)
- System.exe (PID: 1900)
Reads the machine GUID from the registry
- msComponentsaves.exe (PID: 3400)
- System.exe (PID: 3520)
- msComponentsaves.exe (PID: 1264)
- System.exe (PID: 1536)
- System.exe (PID: 3304)
- msComponentsaves.exe (PID: 4028)
- msComponentsaves.exe (PID: 3772)
- System.exe (PID: 3488)
- msComponentsaves.exe (PID: 2668)
- System.exe (PID: 1900)
Reads product name
- msComponentsaves.exe (PID: 3400)
- System.exe (PID: 3520)
- msComponentsaves.exe (PID: 1264)
- System.exe (PID: 1536)
- System.exe (PID: 3304)
- msComponentsaves.exe (PID: 4028)
- System.exe (PID: 3488)
- msComponentsaves.exe (PID: 3772)
- msComponentsaves.exe (PID: 2668)
- System.exe (PID: 1900)
Reads the software policy settings
- System.exe (PID: 3520)
- System.exe (PID: 1536)
- System.exe (PID: 3304)
- System.exe (PID: 3488)
- System.exe (PID: 1900)
Create files in a temporary directory
- System.exe (PID: 3520)
- System.exe (PID: 1536)
- System.exe (PID: 3304)
- System.exe (PID: 3488)
- System.exe (PID: 1900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(3520) System.exe
C2 (1)https://pastebin.com/raw/Gbnj27pi
Options
MutexDCR_MUTEX-P1ZqoYzVZVLOM11zKbBJ
savebrowsersdatatosinglefilefalse
ignorepartiallyemptydatafalse
cookiestrue
passwordstrue
formstrue
cctrue
historyfalse
telegramtrue
steamtrue
discordtrue
filezillatrue
screenshottrue
clipboardtrue
sysinfotrue
searchpath%UsersFolder% - Fast
Targetru
(PID) Process(1536) System.exe
C2 (1)https://pastebin.com/raw/Gbnj27pi
Options
MutexDCR_MUTEX-P1ZqoYzVZVLOM11zKbBJ
savebrowsersdatatosinglefilefalse
ignorepartiallyemptydatafalse
cookiestrue
passwordstrue
formstrue
cctrue
historyfalse
telegramtrue
steamtrue
discordtrue
filezillatrue
screenshottrue
clipboardtrue
sysinfotrue
searchpath%UsersFolder% - Fast
Targetru
(PID) Process(3304) System.exe
C2 (1)https://pastebin.com/raw/Gbnj27pi
Options
MutexDCR_MUTEX-P1ZqoYzVZVLOM11zKbBJ
savebrowsersdatatosinglefilefalse
ignorepartiallyemptydatafalse
cookiestrue
passwordstrue
formstrue
cctrue
historyfalse
telegramtrue
steamtrue
discordtrue
filezillatrue
screenshottrue
clipboardtrue
sysinfotrue
searchpath%UsersFolder% - Fast
Targetru
(PID) Process(3488) System.exe
C2 (1)https://pastebin.com/raw/Gbnj27pi
Options
MutexDCR_MUTEX-P1ZqoYzVZVLOM11zKbBJ
savebrowsersdatatosinglefilefalse
ignorepartiallyemptydatafalse
cookiestrue
passwordstrue
formstrue
cctrue
historyfalse
telegramtrue
steamtrue
discordtrue
filezillatrue
screenshottrue
clipboardtrue
sysinfotrue
searchpath%UsersFolder% - Fast
Targetru
(PID) Process(1900) System.exe
C2 (1)https://pastebin.com/raw/Gbnj27pi
Options
MutexDCR_MUTEX-P1ZqoYzVZVLOM11zKbBJ
savebrowsersdatatosinglefilefalse
ignorepartiallyemptydatafalse
cookiestrue
passwordstrue
formstrue
cctrue
historyfalse
telegramtrue
steamtrue
discordtrue
filezillatrue
screenshottrue
clipboardtrue
sysinfotrue
searchpath%UsersFolder% - Fast
Targetru
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2023:09:22 03:22:54 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Paranoid Checker 4.1.7/ |
Total processes
102
Monitored processes
59
Malicious processes
23
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | schtasks.exe /create /tn "lsml" /sc MINUTE /mo 12 /tr "'C:\ServerwebRefmonitorDhcp\lsm.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Windows\System32\WScript.exe" "C:\ServerwebRefmonitorDhcp\Oj1Ch.vbe" | C:\Windows\System32\wscript.exe | — | Paranoid Checker 4.1.7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 880 | schtasks.exe /create /tn "ctfmonc" /sc MINUTE /mo 14 /tr "'C:\MSOCache\All Users\{90140000-0017-0412-0000-0000000FF1CE}-C\ctfmon.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\3b6aeb52-5329-4b63-beb0-a465a3e0dcfd.vbs" | C:\Windows\System32\wscript.exe | — | System.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1264 | "C:\ServerwebRefmonitorDhcp\msComponentsaves.exe" | C:\ServerwebRefmonitorDhcp\msComponentsaves.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 1404 | schtasks.exe /create /tn "winlogonw" /sc MINUTE /mo 9 /tr "'C:\Users\admin\Pictures\winlogon.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1408 | "C:\Windows\System32\WScript.exe" "C:\ServerwebRefmonitorDhcp\Oj1Ch.vbe" | C:\Windows\System32\wscript.exe | — | Paranoid Checker 4.1.7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1496 | "C:\Users\admin\Desktop\Paranoid Checker 4.1.7\Paranoid Checker 4.1.7.exe" | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\Paranoid Checker 4.1.7.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1536 | "C:\MSOCache\All Users\{90140000-0019-0C0A-0000-0000000FF1CE}-C\System.exe" | C:\MSOCache\All Users\{90140000-0019-0C0A-0000-0000000FF1CE}-C\System.exe | wscript.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
DcRat(PID) Process(1536) System.exe C2 (1)https://pastebin.com/raw/Gbnj27pi Options MutexDCR_MUTEX-P1ZqoYzVZVLOM11zKbBJ savebrowsersdatatosinglefilefalse ignorepartiallyemptydatafalse cookiestrue passwordstrue formstrue cctrue historyfalse telegramtrue steamtrue discordtrue filezillatrue screenshottrue clipboardtrue sysinfotrue searchpath%UsersFolder% - Fast Targetru | |||||||||||||||
| 1540 | schtasks.exe /create /tn "explorer" /sc ONLOGON /tr "'C:\MSOCache\All Users\{90140000-0015-0410-0000-0000000FF1CE}-C\explorer.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
54 947
Read events
54 532
Write events
342
Delete events
73
Modification events
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Paranoid Checker 4.1.7.zip | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1696) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
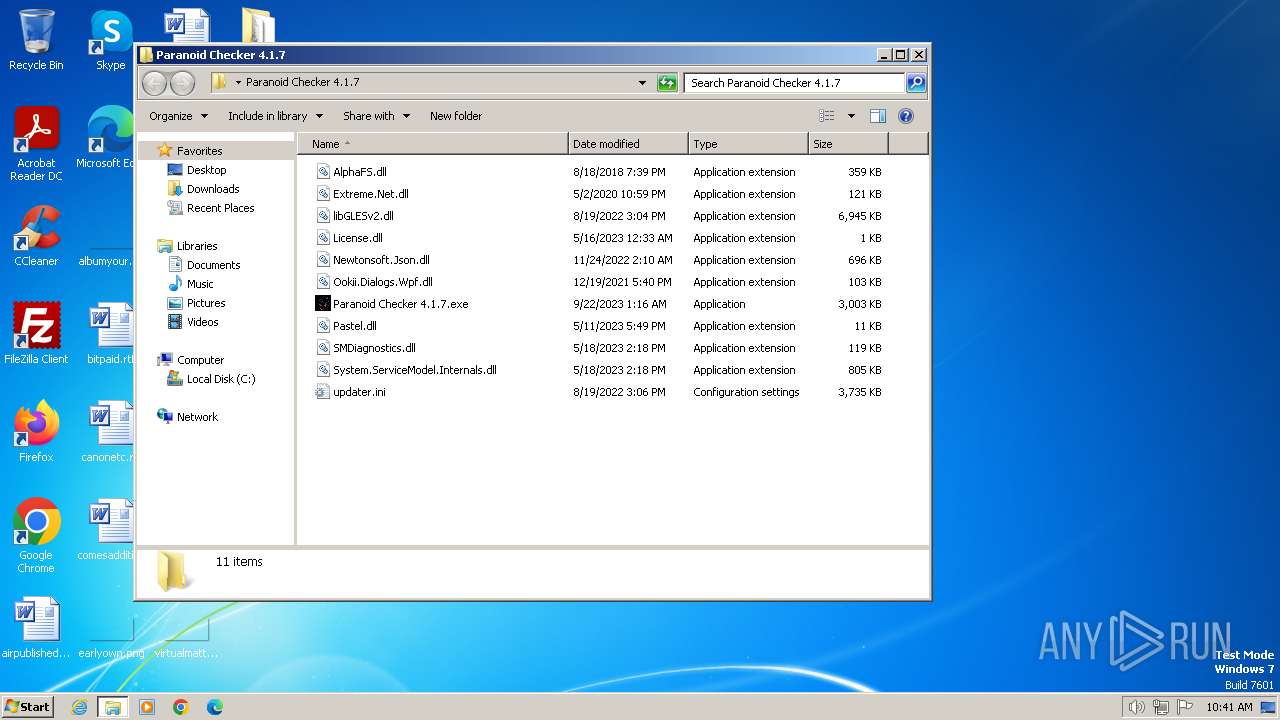
Executable files
16
Suspicious files
1
Text files
18
Unknown types
1
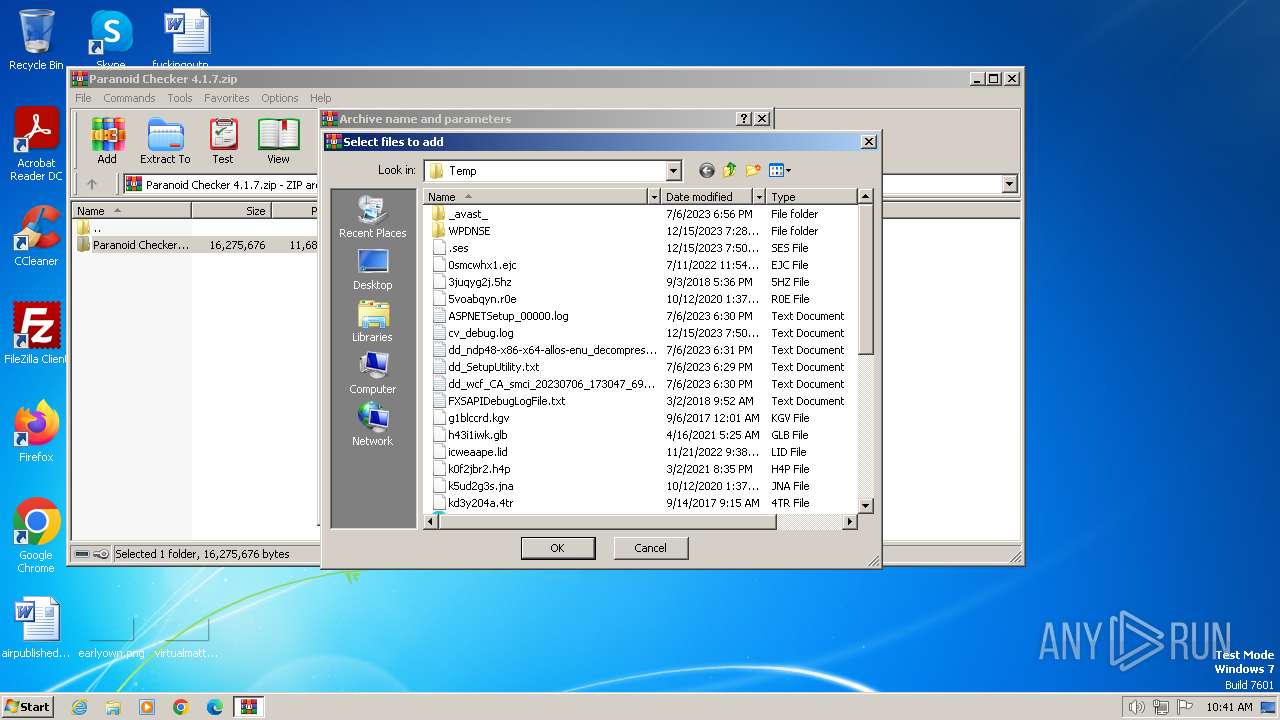
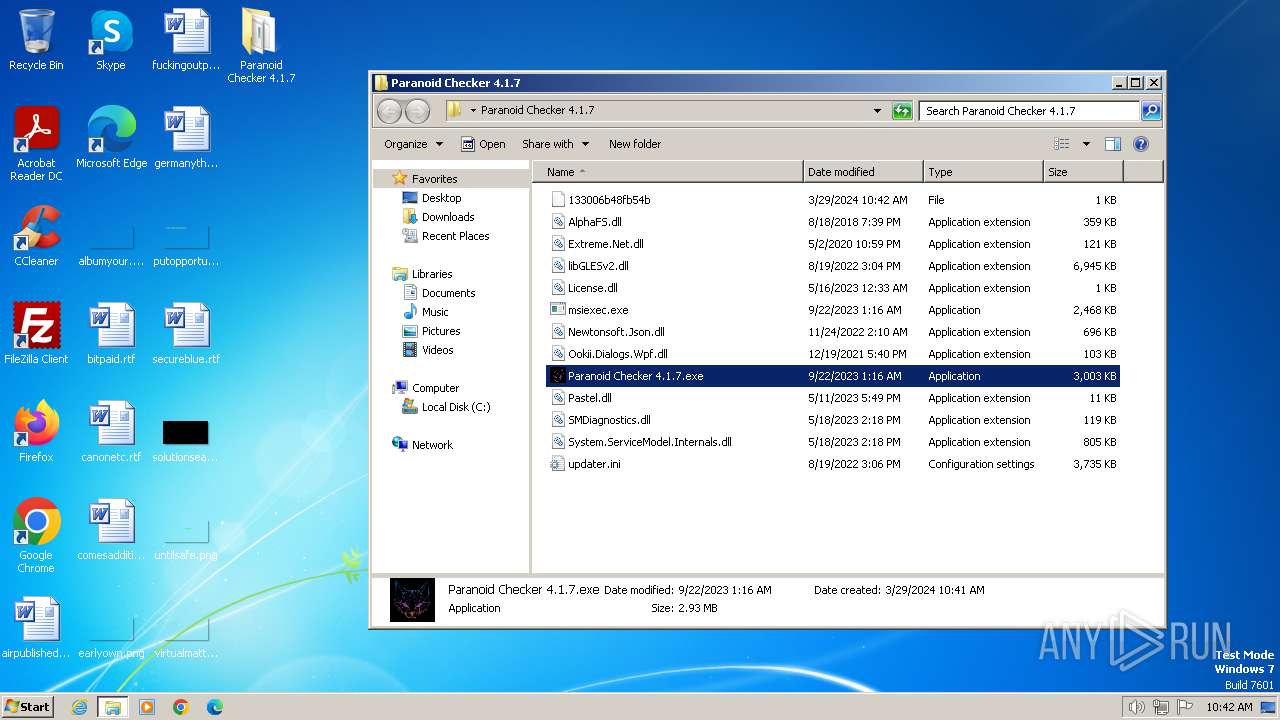
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\AlphaFS.dll | executable | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\Extreme.Net.dll | executable | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\libGLESv2.dll | — | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\License.dll | text | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\Newtonsoft.Json.dll | executable | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\Ookii.Dialogs.Wpf.dll | executable | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\Paranoid Checker 4.1.7.exe | executable | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\Pastel.dll | executable | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\SMDiagnostics.dll | executable | |
MD5:— | SHA256:— | |||
| 1696 | WinRAR.exe | C:\Users\admin\Desktop\Paranoid Checker 4.1.7\System.ServiceModel.Internals.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
18
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3520 | System.exe | 104.20.68.143:443 | pastebin.com | CLOUDFLARENET | — | unknown |
3520 | System.exe | 49.13.77.253:80 | cw08653.tw1.ru | Hetzner Online GmbH | DE | unknown |
1536 | System.exe | 104.20.68.143:443 | pastebin.com | CLOUDFLARENET | — | unknown |
1536 | System.exe | 49.13.77.253:80 | cw08653.tw1.ru | Hetzner Online GmbH | DE | unknown |
3304 | System.exe | 104.20.68.143:443 | pastebin.com | CLOUDFLARENET | — | unknown |
3304 | System.exe | 49.13.77.253:80 | cw08653.tw1.ru | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| shared |
cw08653.tw1.ru |
| unknown |
dns.msftncsi.com |
| shared |