| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/cdd6c5aa-a073-4a4e-9c3f-c526f1b595ba |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | July 05, 2025, 23:24:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 3CB864B79656FF23B6B43315B1016AAF |
| SHA1: | 336AF4397618C0A7A014AA0BEF90702B8BF0EBB9 |
| SHA256: | FB3F40376CC7890EFA0138C46C4553EEED341F6700309F97B9779DAC411D4973 |
| SSDEEP: | 98304:/fLIQ/AcJl6ZrQym90T0kfROMkjn2PetSojhUw+Ye4Hk//njdtAMOFnUIqFnodaN:TEi9uCaA8KS5o2AAn |
MALICIOUS
DARKCRYSTAL has been detected (SURICATA)
- lithjmeaf.exe (PID: 3800)
Connects to the CnC server
- lithjmeaf.exe (PID: 3800)
Steals credentials from Web Browsers
- lithjmeaf.exe (PID: 3800)
Actions looks like stealing of personal data
- lithjmeaf.exe (PID: 3800)
SUSPICIOUS
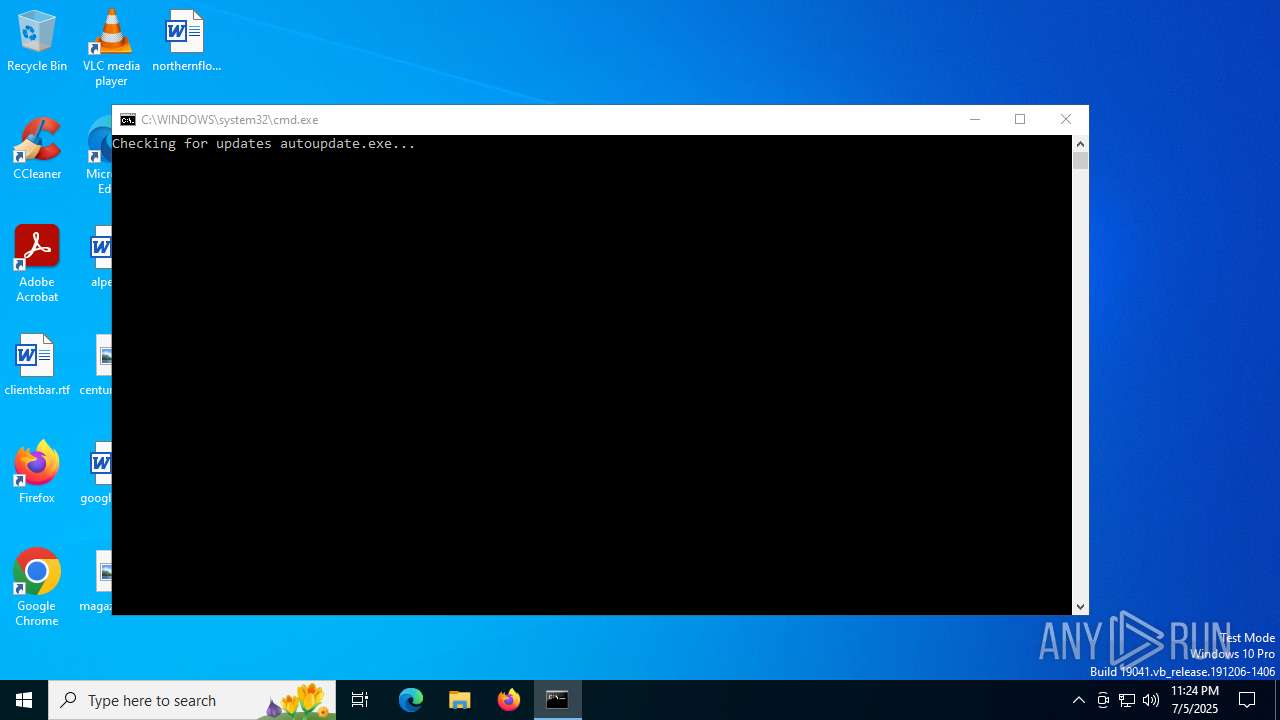
Executing commands from a ".bat" file
- AutoBuyGifts.exe (PID: 6124)
- 1.exe (PID: 1212)
- autoupdate.exe (PID: 4060)
The executable file from the user directory is run by the CMD process
- autoupdate.exe (PID: 4060)
- AutoBuyGifts.exe (PID: 6124)
- mixworld.exe (PID: 6336)
Executable content was dropped or overwritten
- 1.exe (PID: 1212)
- autoupdate.exe (PID: 4060)
- mixworld.exe (PID: 6336)
- lithjmeaf.exe (PID: 3800)
- AutoBuyGifts.exe (PID: 6124)
Reads security settings of Internet Explorer
- 1.exe (PID: 1212)
- autoupdate.exe (PID: 4060)
- mixworld.exe (PID: 6336)
- AutoBuyGifts.exe (PID: 6124)
Starts CMD.EXE for commands execution
- 1.exe (PID: 1212)
- autoupdate.exe (PID: 4060)
- AutoBuyGifts.exe (PID: 6124)
Reads the date of Windows installation
- autoupdate.exe (PID: 4060)
- mixworld.exe (PID: 6336)
Connects to the server without a host name
- lithjmeaf.exe (PID: 3800)
Loads DLL from Mozilla Firefox
- lithjmeaf.exe (PID: 3800)
INFO
Checks supported languages
- 1.exe (PID: 1212)
- autoupdate.exe (PID: 4060)
- mixworld.exe (PID: 6336)
- lithjmeaf.exe (PID: 3800)
- AutoBuyGifts.exe (PID: 6124)
Reads the computer name
- autoupdate.exe (PID: 4060)
- 1.exe (PID: 1212)
- AutoBuyGifts.exe (PID: 6124)
- mixworld.exe (PID: 6336)
- lithjmeaf.exe (PID: 3800)
Process checks computer location settings
- 1.exe (PID: 1212)
- autoupdate.exe (PID: 4060)
- mixworld.exe (PID: 6336)
- AutoBuyGifts.exe (PID: 6124)
Create files in a temporary directory
- 1.exe (PID: 1212)
- autoupdate.exe (PID: 4060)
- mixworld.exe (PID: 6336)
- lithjmeaf.exe (PID: 3800)
- AutoBuyGifts.exe (PID: 6124)
Reads the machine GUID from the registry
- lithjmeaf.exe (PID: 3800)
Reads Environment values
- lithjmeaf.exe (PID: 3800)
Disables trace logs
- lithjmeaf.exe (PID: 3800)
Checks proxy server information
- lithjmeaf.exe (PID: 3800)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:03 07:51:19+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 214528 |
| InitializedDataSize: | 137728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21d50 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
149
Monitored processes
13
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1296 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\run_my_app.bat" " | C:\Windows\SysWOW64\cmd.exe | — | AutoBuyGifts.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3400 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3800 | "C:\Users\admin\AppData\Local\Temp\RarSFX2\lithjmeaf.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX2\lithjmeaf.exe | mixworld.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 16.10.31418.88 Modules
| |||||||||||||||
| 4060 | autoupdate.exe | C:\Users\admin\AppData\Local\Temp\autoupdate.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6124 | AutoBuyGifts.exe -paLPakalokomortpoea | C:\Users\admin\AppData\Local\Temp\RarSFX0\AutoBuyGifts.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6336 | mixworld.exe -priverdD | C:\Users\admin\AppData\Local\Temp\RarSFX1\mixworld.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6360 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 325
Read events
5 309
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\56f4a74f9b0de1abf8e9277e39f0b116d9430d96 |
| Operation: | write | Name: | 087da62af53768ea17a2e4d5a48df3e8a85ee0d8 |
Value: H4sIAAAAAAAEAItWcraKiQktTi0qjolJTMnNzIuJcSwocEksSYyJ8clPTsyJiQlJzS2IiQlKLAp2izCKicnJLMnIyk1NTNNLrUhVigUAZ0HxIEIAAAA= | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASMANCS |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASMANCS |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3800) lithjmeaf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\lithjmeaf_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
11
Suspicious files
22
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1212 | 1.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\1.bat | text | |
MD5:B2337442A01A8763A0E00D19090D7530 | SHA256:DA7A97460FFD851334C5C45D6C3706713A30EEDDFE33CF0D61979D14F4350629 | |||
| 1212 | 1.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\AutoBuyGifts.exe | executable | |
MD5:78E404B7182FEA6FF85389F8DC7ACCCB | SHA256:A3E9B98A9B5840400C2839CF4AF9D140DB56054EA952F77BC648B7379F357FA2 | |||
| 6124 | AutoBuyGifts.exe | C:\Users\admin\AppData\Local\Temp\run_my_app.bat | text | |
MD5:6D5A572952A2EB69010A297258EC7732 | SHA256:940F7DC8CA76C30D02C8A98CE2560F194BA3D886BB923801D944CB011BA00F0D | |||
| 6124 | AutoBuyGifts.exe | C:\Users\admin\AppData\Local\Temp\data\json\info.json | binary | |
MD5:FFAFDADB871EAADAA159D3D7D3318030 | SHA256:EC2D77DE89A72D082823926ED248408D2930A000F286AE7C5561731D54E72066 | |||
| 6124 | AutoBuyGifts.exe | C:\Users\admin\AppData\Local\Temp\autoupdate.exe | executable | |
MD5:7441F901560595CC738FE44488F175CE | SHA256:22251C12F74004444BC4AD4F6E00B160BD6BA8D8898ADD2A7BB8946343DBBBEA | |||
| 6124 | AutoBuyGifts.exe | C:\Users\admin\AppData\Local\Temp\main.exe | executable | |
MD5:95080F2B0EC7C60C6BEEC677F83BA2D0 | SHA256:F7520C86937502CBBF6D0964FC68349490F10CE5D354BD1455A0B510D7B3CE9E | |||
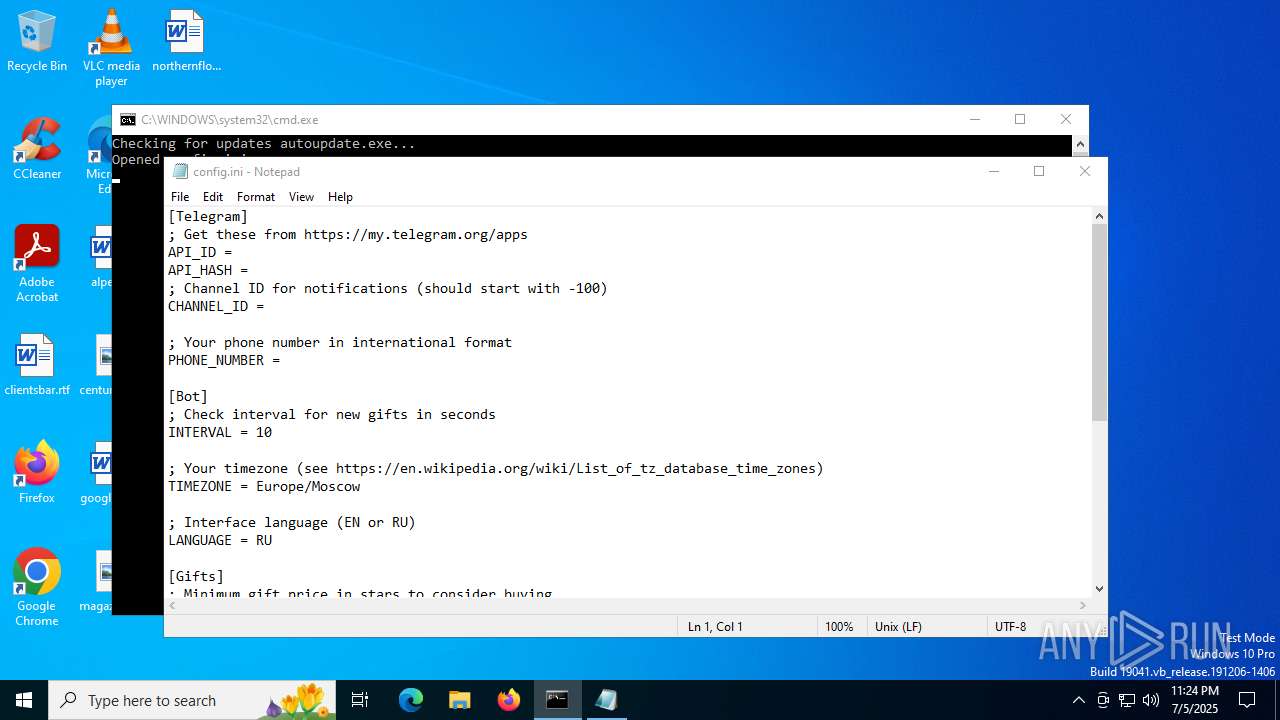
| 6124 | AutoBuyGifts.exe | C:\Users\admin\AppData\Local\Temp\data\config.py | text | |
MD5:2111769BDA005EF426BFF376A1A9F838 | SHA256:590CD4EDA57F88C0EC5FF8CF65D1CC922C54E9DB82A6435700EE0B3DDCFB810D | |||
| 3800 | lithjmeaf.exe | C:\Users\admin\Desktop\jSPllQGj.log | executable | |
MD5:5420053AF2D273C456FB46C2CDD68F64 | SHA256:A4DFD8B1735598699A410538B8B2ACE6C9A68631D2A26FBF8089D6537DBB30F2 | |||
| 3800 | lithjmeaf.exe | C:\Users\admin\Desktop\kXaLlzvk.log | executable | |
MD5:2D6975FD1CC3774916D8FF75C449EE7B | SHA256:75CE6EB6CDDD67D47FB7C5782F45FDC497232F87A883650BA98679F92708A986 | |||
| 3800 | lithjmeaf.exe | C:\Users\admin\AppData\Local\Temp\xVcIssUYPX | text | |
MD5:44481763A39DCEC4E344E3B36AD97DAB | SHA256:46FEBB00B6C83970C7603F386E2C75D3A3DD6F73BAC16DD55A20AC46EEFF21D7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
24
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3800 | lithjmeaf.exe | POST | 200 | 38.180.165.153:80 | http://38.180.165.153/7providerLinux/cdngenerator/JsPacketUpdateProcessorServerprotectTrafficTestdatalifeUploads.php | unknown | — | — | malicious |
3800 | lithjmeaf.exe | POST | 200 | 38.180.165.153:80 | http://38.180.165.153/7providerLinux/cdngenerator/JsPacketUpdateProcessorServerprotectTrafficTestdatalifeUploads.php | unknown | — | — | malicious |
3800 | lithjmeaf.exe | POST | 200 | 38.180.165.153:80 | http://38.180.165.153/7providerLinux/cdngenerator/JsPacketUpdateProcessorServerprotectTrafficTestdatalifeUploads.php | unknown | — | — | malicious |
3800 | lithjmeaf.exe | POST | 200 | 38.180.165.153:80 | http://38.180.165.153/7providerLinux/cdngenerator/JsPacketUpdateProcessorServerprotectTrafficTestdatalifeUploads.php | unknown | — | — | malicious |
3800 | lithjmeaf.exe | POST | 200 | 38.180.165.153:80 | http://38.180.165.153/7providerLinux/cdngenerator/JsPacketUpdateProcessorServerprotectTrafficTestdatalifeUploads.php | unknown | — | — | malicious |
1268 | svchost.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3800 | lithjmeaf.exe | POST | 200 | 38.180.165.153:80 | http://38.180.165.153/7providerLinux/cdngenerator/JsPacketUpdateProcessorServerprotectTrafficTestdatalifeUploads.php | unknown | — | — | malicious |
3800 | lithjmeaf.exe | POST | 200 | 38.180.165.153:80 | http://38.180.165.153/7providerLinux/cdngenerator/JsPacketUpdateProcessorServerprotectTrafficTestdatalifeUploads.php | unknown | — | — | malicious |
3800 | lithjmeaf.exe | POST | 200 | 38.180.165.153:80 | http://38.180.165.153/7providerLinux/cdngenerator/JsPacketUpdateProcessorServerprotectTrafficTestdatalifeUploads.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4372 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3800 | lithjmeaf.exe | 38.180.165.153:80 | — | COGENT-174 | US | malicious |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2520 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3800 | lithjmeaf.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
3800 | lithjmeaf.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |