| File name: | fb3f2b0636c7f9e8913fb5ff593c38ed261473bc1a2f8fb0860dce82ecaf5e06.msi |
| Full analysis: | https://app.any.run/tasks/0273e93d-555a-4399-95f2-c2d8ad39d6d7 |
| Verdict: | Malicious activity |
| Analysis date: | April 30, 2023, 12:21:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Installer, Author: Installer, Keywords: Installer, Comments: Installer Package, Template: Intel;1033, Revision Number: {45F7917A-AAA7-4834-B69B-DBFD6CBD2AD1}, Create Time/Date: Sat Apr 30 14:13:22 2022, Last Saved Time/Date: Sat Apr 30 14:13:22 2022, Number of Pages: 200, Number of Words: 10, Name of Creating Application: Windows Installer XML Toolset (3.13.3.1364), Security: 2 |
| MD5: | 2EB29D721FBEE14EDBF2AD8F60336EBF |
| SHA1: | E1AADA3863D929F9674597EBB595DC84BAC7263E |
| SHA256: | FB3F2B0636C7F9E8913FB5FF593C38ED261473BC1A2F8FB0860DCE82ECAF5E06 |
| SSDEEP: | 1536:3RGjMkF2VAv21tCHDca26KfpD15sy7o/D6Ds0Ds7d:QJAAvatCHDaF515V7iDL |
MALICIOUS
Application was injected by another process
- explorer.exe (PID: 860)
- svchost.exe (PID: 4136)
- StartMenuExperienceHost.exe (PID: 4556)
- dllhost.exe (PID: 4924)
- sihost.exe (PID: 3688)
- svchost.exe (PID: 3712)
- SearchApp.exe (PID: 4736)
- ApplicationFrameHost.exe (PID: 5704)
- svchost.exe (PID: 3760)
- RuntimeBroker.exe (PID: 4620)
- RuntimeBroker.exe (PID: 4904)
- TextInputHost.exe (PID: 5156)
- UserOOBEBroker.exe (PID: 5140)
- dllhost.exe (PID: 624)
- svchost.exe (PID: 1656)
- ShellExperienceHost.exe (PID: 3412)
- RuntimeBroker.exe (PID: 4248)
- RuntimeBroker.exe (PID: 6664)
Registers / Runs the DLL via REGSVR32.EXE
- svchost.exe (PID: 3712)
- RuntimeBroker.exe (PID: 4620)
- explorer.exe (PID: 860)
- svchost.exe (PID: 4136)
- svchost.exe (PID: 3760)
- svchost.exe (PID: 1656)
- RuntimeBroker.exe (PID: 4904)
- ApplicationFrameHost.exe (PID: 5704)
- UserOOBEBroker.exe (PID: 5140)
- TextInputHost.exe (PID: 5156)
- StartMenuExperienceHost.exe (PID: 4556)
- sihost.exe (PID: 3688)
- RuntimeBroker.exe (PID: 4248)
- msiexec.exe (PID: 1536)
- RuntimeBroker.exe (PID: 6664)
- fodhelper.exe (PID: 6296)
- fodhelper.exe (PID: 8204)
Runs injected code in another process
- msiexec.exe (PID: 4580)
Using BCDEDIT.EXE to modify recovery options
- regsvr32.exe (PID: 7232)
- regsvr32.exe (PID: 324)
Deletes shadow copies
- regsvr32.exe (PID: 7232)
- regsvr32.exe (PID: 324)
SUSPICIOUS
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1536)
Reads settings of System Certificates
- msiexec.exe (PID: 1536)
Executes as Windows Service
- VSSVC.exe (PID: 6888)
- wbengine.exe (PID: 8596)
- vds.exe (PID: 9472)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6392)
Starts CMD.EXE for commands execution
- StartMenuExperienceHost.exe (PID: 4556)
- RuntimeBroker.exe (PID: 4620)
- TextInputHost.exe (PID: 5156)
- svchost.exe (PID: 4136)
- explorer.exe (PID: 860)
- RuntimeBroker.exe (PID: 4904)
- UserOOBEBroker.exe (PID: 5140)
- svchost.exe (PID: 3760)
- ApplicationFrameHost.exe (PID: 5704)
- svchost.exe (PID: 1656)
- RuntimeBroker.exe (PID: 6664)
- RuntimeBroker.exe (PID: 4248)
- sihost.exe (PID: 3688)
- svchost.exe (PID: 3712)
Executes application which crashes
- dllhost.exe (PID: 624)
- dllhost.exe (PID: 4924)
INFO
The process checks LSA protection
- msiexec.exe (PID: 1536)
- msiexec.exe (PID: 6392)
- VSSVC.exe (PID: 6888)
Reads the computer name
- msiexec.exe (PID: 6392)
Checks supported languages
- msiexec.exe (PID: 6392)
Application launched itself
- msiexec.exe (PID: 6392)
Manual execution by a user
- regsvr32.exe (PID: 6768)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 7784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Installer (100) |
|---|
EXIF
FlashPix
| Security: | Read-only recommended |
|---|---|
| Software: | Windows Installer XML Toolset (3.13.3.1364) |
| Words: | 10 |
| Pages: | 200 |
| ModifyDate: | 2022:05:31 14:13:22 |
| CreateDate: | 2022:05:31 14:13:22 |
| RevisionNumber: | {45F7917A-AAA7-4834-B69B-DBFD6CBD2AD1} |
| Template: | Intel;1033 |
| Comments: | Installer Package |
| Keywords: | Installer |
| Author: | Installer |
| Subject: | Installer |
| Title: | Installation Database |
| CodePage: | Windows Latin 1 (Western European) |
Total processes
618
Monitored processes
62
Malicious processes
10
Suspicious processes
0
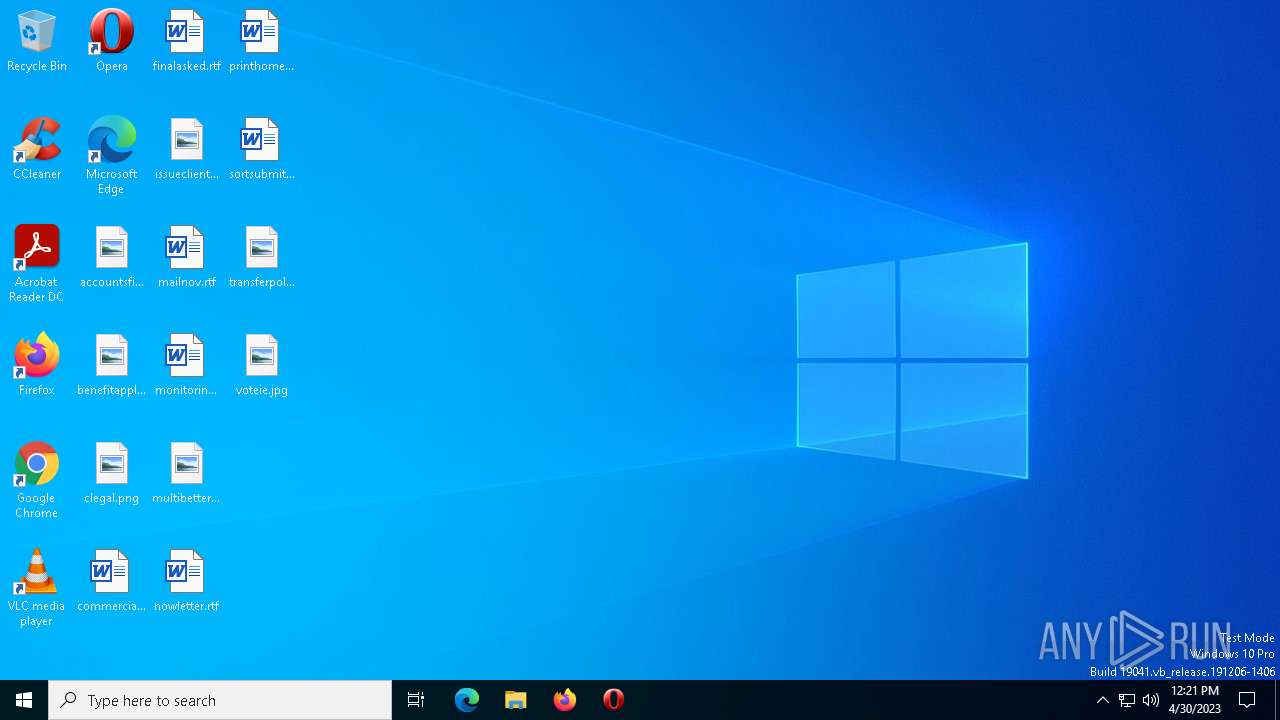
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "regsvr32.exe" scrobj.dll /s /u /n /i:../../../Users/Public/kq1k2a | C:\Windows\System32\regsvr32.exe | — | fodhelper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 624 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 3221225477 Version: 10.0.19041.546 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 860 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 10.0.19041.1023 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | bcdedit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1108 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:2 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 2147942421 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\fb3f2b0636c7f9e8913fb5ff593c38ed261473bc1a2f8fb0860dce82ecaf5e06.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1656 | C:\WINDOWS\system32\svchost.exe -k UnistackSvcGroup | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wbadmin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2264 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 200
Read events
23 928
Write events
196
Delete events
76
Modification events
| (PID) Process: | (6392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000FEDD345EB5CCD801FC0E00005C100000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000002BF41169B5CCD801D81100000C150000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6888) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6888) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Description |
| Operation: | write | Name: | FirmwareModified |
Value: 1 | |||
| (PID) Process: | (6888) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6888) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6888) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6888) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Description |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6888) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Elements\24000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6888) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Elements\25000004 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
2
Suspicious files
164
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6392 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6392 | msiexec.exe | C:\WINDOWS\Installer\434b99.msi | — | |
MD5:— | SHA256:— | |||
| 3712 | svchost.exe | C:\Users\Public\kq1k2a | — | |
MD5:— | SHA256:— | |||
| 6392 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:A9BE8F6403929E6D2C186D10B7B3CE89 | SHA256:AC7DF8DEBCECEA79B191B3D2709D31D8DA013AE06EB5C7BC2143341CCF2EE90A | |||
| 3688 | sihost.exe | C:\Users\admin\Desktop\finalasked.rtf.rpmdzlml | binary | |
MD5:6B471F032CC9AE4C89CE67D0DF34C3A2 | SHA256:69C3FC928D522C3793F5A2306B37B3A281ED67E0713E7D1D5730AFBDB4C910BD | |||
| 3688 | sihost.exe | C:\Users\admin\Desktop\finalasked.rtf | binary | |
MD5:6B471F032CC9AE4C89CE67D0DF34C3A2 | SHA256:69C3FC928D522C3793F5A2306B37B3A281ED67E0713E7D1D5730AFBDB4C910BD | |||
| 3688 | sihost.exe | C:\Users\admin\Desktop\mailnov.rtf.rpmdzlml | binary | |
MD5:8FA93EED888E28435DBF21AE07657E86 | SHA256:3614AEDF97DE1E2FC901CD8BAB9B5031E762EB24761CE82A1363299509782EF6 | |||
| 3688 | sihost.exe | C:\Users\admin\Desktop\mailnov.rtf | binary | |
MD5:8FA93EED888E28435DBF21AE07657E86 | SHA256:3614AEDF97DE1E2FC901CD8BAB9B5031E762EB24761CE82A1363299509782EF6 | |||
| 3712 | svchost.exe | C:\Users\Public\zlujw06rvtx | binary | |
MD5:7476BBE5C57E420729394717137ADCF5 | SHA256:0F0D7322F036357ECBFBD923A9D5101F1499CB806DFB6300044C68D37D7BAF2E | |||
| 3688 | sihost.exe | C:\Users\admin\Desktop\monitoringbook.rtf | binary | |
MD5:5849626E346E14021288A5FD414AB674 | SHA256:5D1329F074373E6DE640E71F33EF4E5C28AD8C4B1F1EFE5E6A12DEE0080F7540 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
38
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | SIHClient.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | der | 409 b | whitelisted |
7236 | WerFault.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | binary | 1.11 Kb | whitelisted |
7236 | WerFault.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | binary | 814 b | whitelisted |
3820 | SIHClient.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | der | 418 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5756 | svchost.exe | 20.190.159.64:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7236 | WerFault.exe | 20.189.173.21:443 | umwatson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
7236 | WerFault.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | suspicious |
7236 | WerFault.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5952 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3488 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5896 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7052 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6372 | WerFault.exe | 104.208.16.94:443 | umwatson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
3820 | SIHClient.exe | 2.18.233.62:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
umwatson.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|
wbadmin.exe | Invalid parameter passed to C runtime function.
|