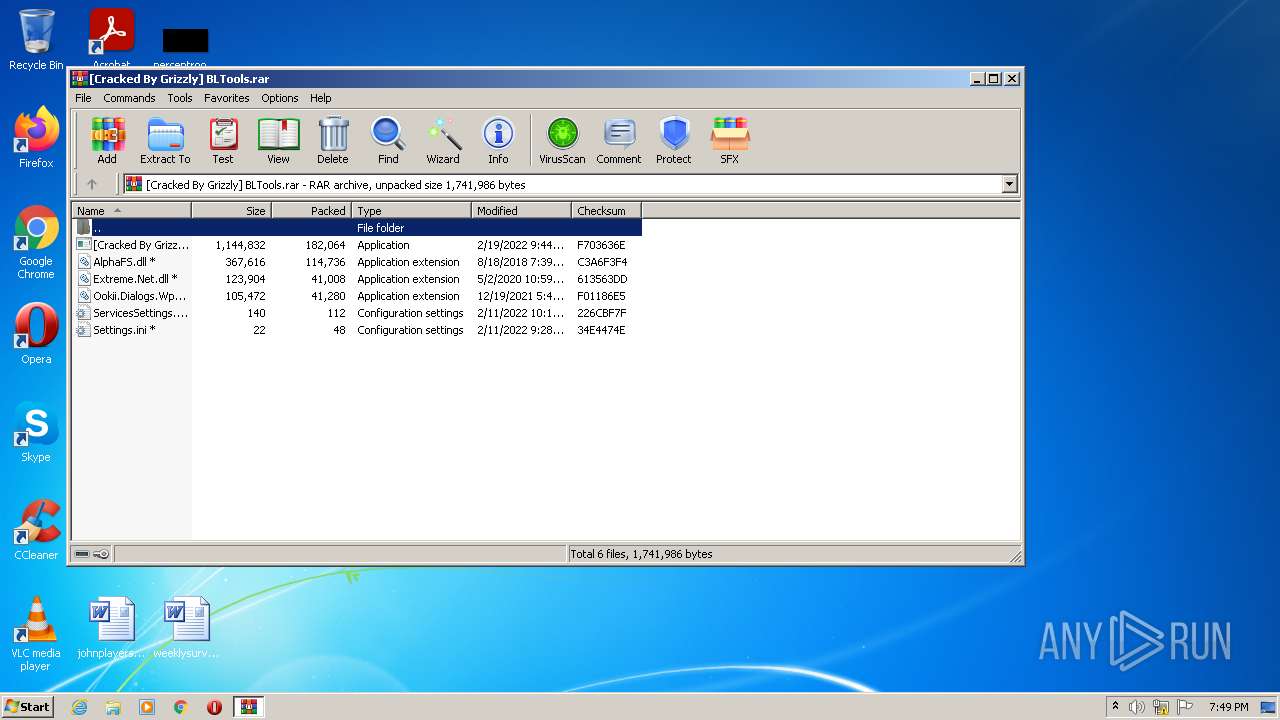
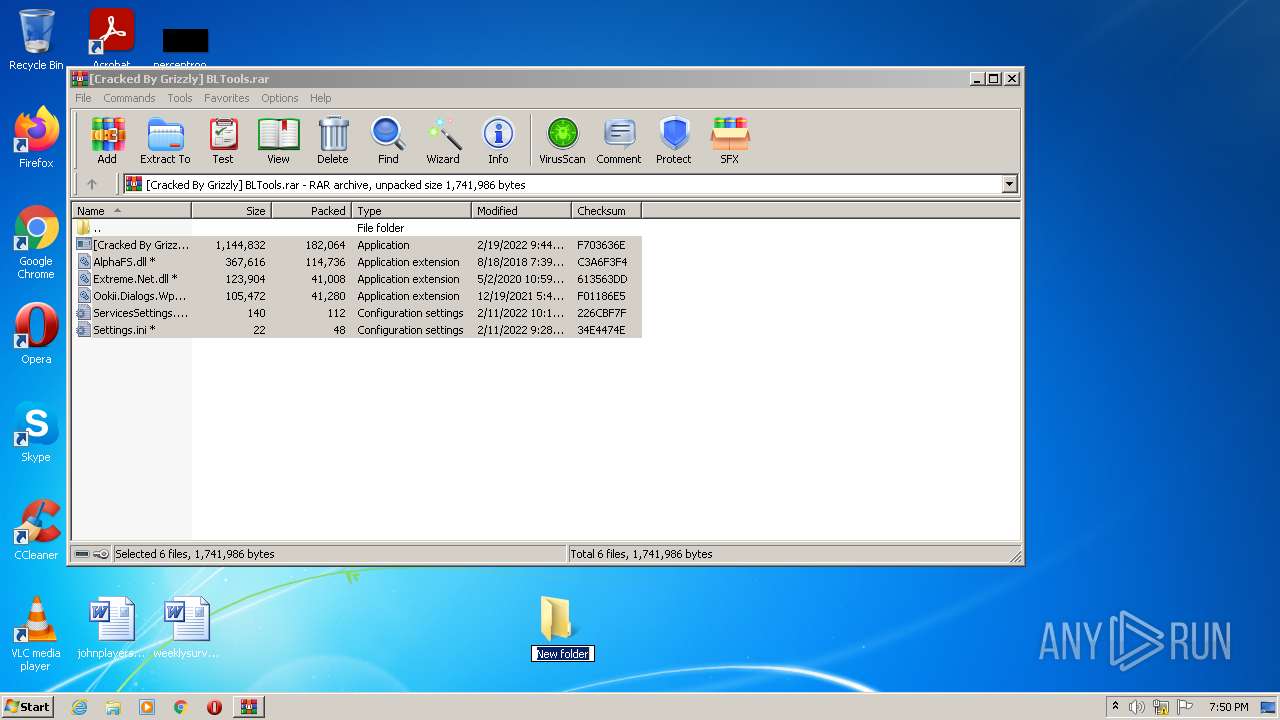
| File name: | [Cracked By Grizzly] BLTools.rar |
| Full analysis: | https://app.any.run/tasks/07b2ada7-f14a-4446-ad53-2cce8fc50ff6 |
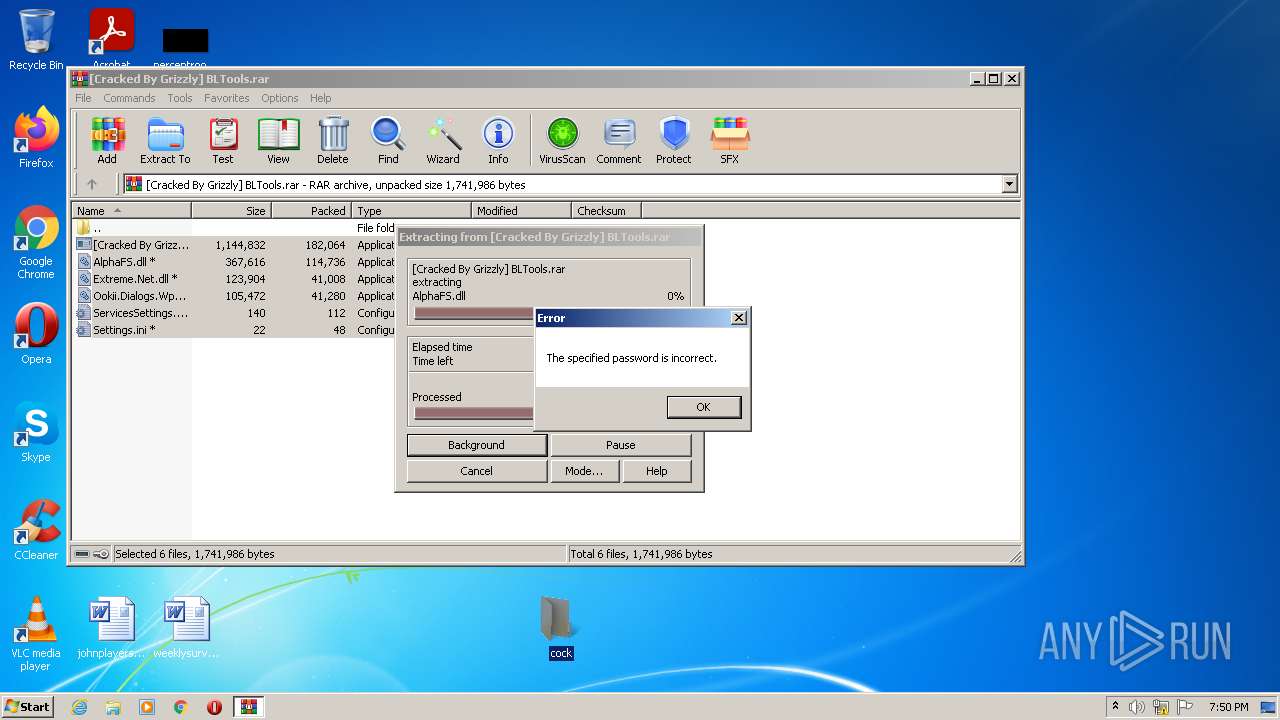
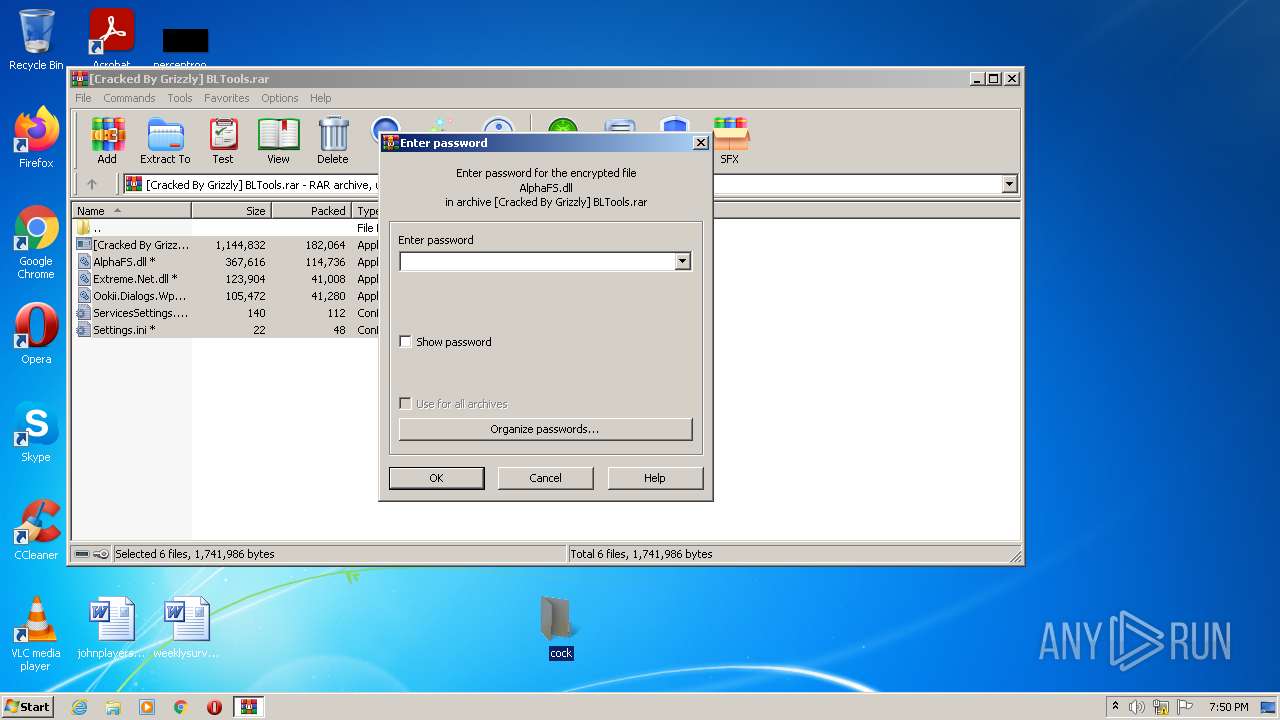
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2022, 18:49:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | F0A286AE48FE423684AAA955C25476C4 |
| SHA1: | 2E482F763864FCD87441FEADC3B5D9F5F3D13C09 |
| SHA256: | FB2DFA9B69728B234643346A9E9250ABD916E771ABC29745D1A7936B952E6F37 |
| SSDEEP: | 6144:WRS3wUP6ScVmRfj+ht0aIP9roletG8bA/eEfGKzevUgx+bZx1JteaffkGBt+dC1M:V3zP6ScyfKmV4etG8bQeEfGKWrOEaffK |
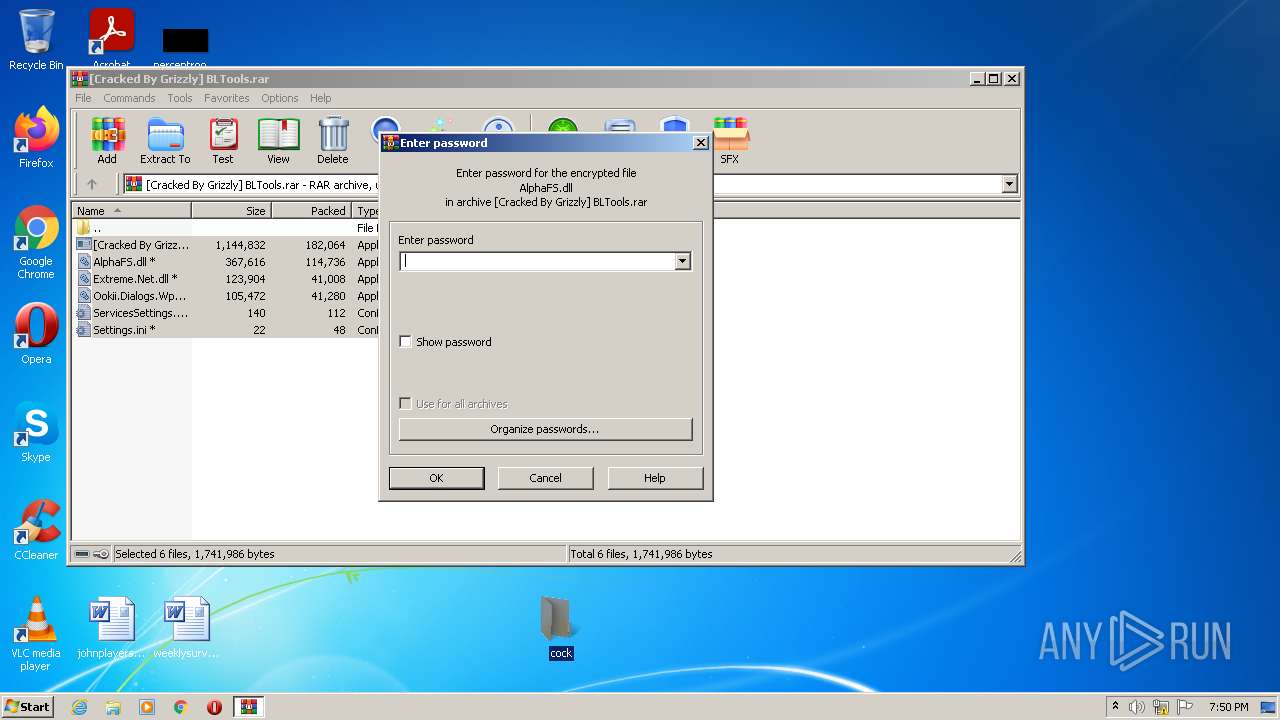
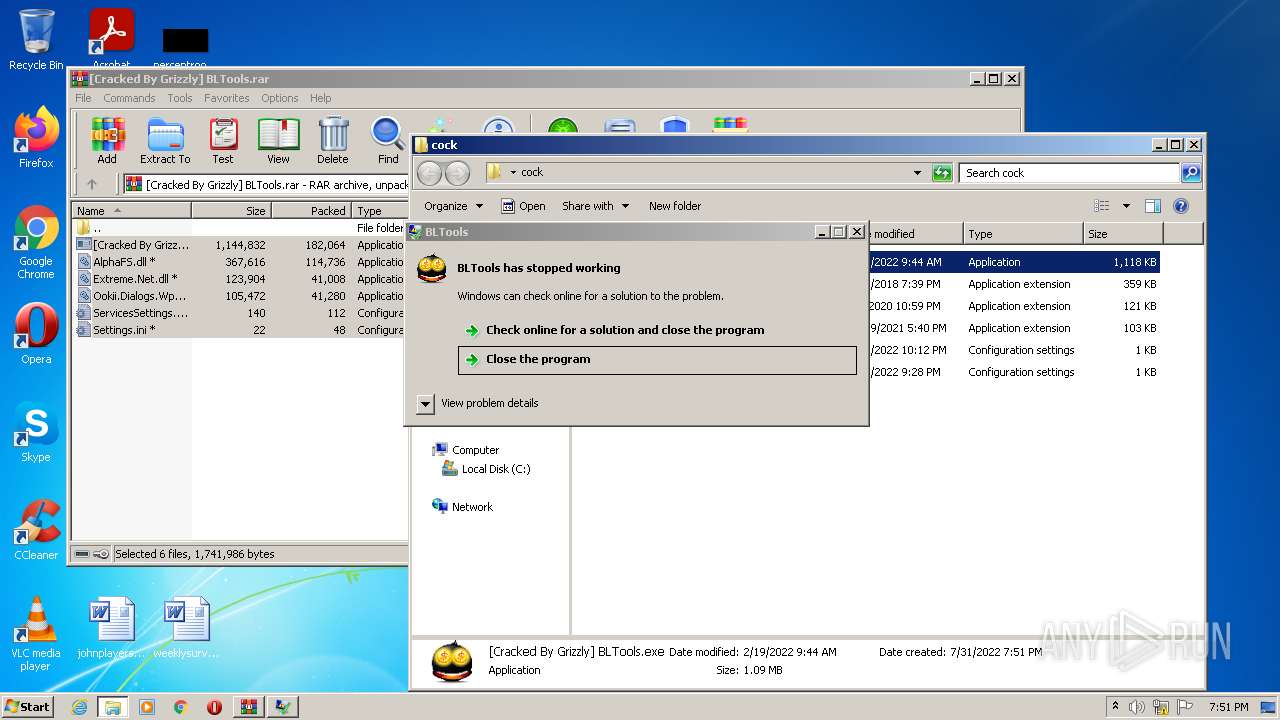
MALICIOUS
Application was dropped or rewritten from another process
- [Cracked By Grizzly] BLTools.exe (PID: 3928)
Drops executable file immediately after starts
- WinRAR.exe (PID: 2944)
Loads dropped or rewritten executable
- [Cracked By Grizzly] BLTools.exe (PID: 3928)
SUSPICIOUS
Reads the computer name
- [Cracked By Grizzly] BLTools.exe (PID: 3928)
- WinRAR.exe (PID: 2944)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2944)
Checks supported languages
- WinRAR.exe (PID: 2944)
- [Cracked By Grizzly] BLTools.exe (PID: 3928)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2944)
INFO
Manual execution by user
- [Cracked By Grizzly] BLTools.exe (PID: 3928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
39
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
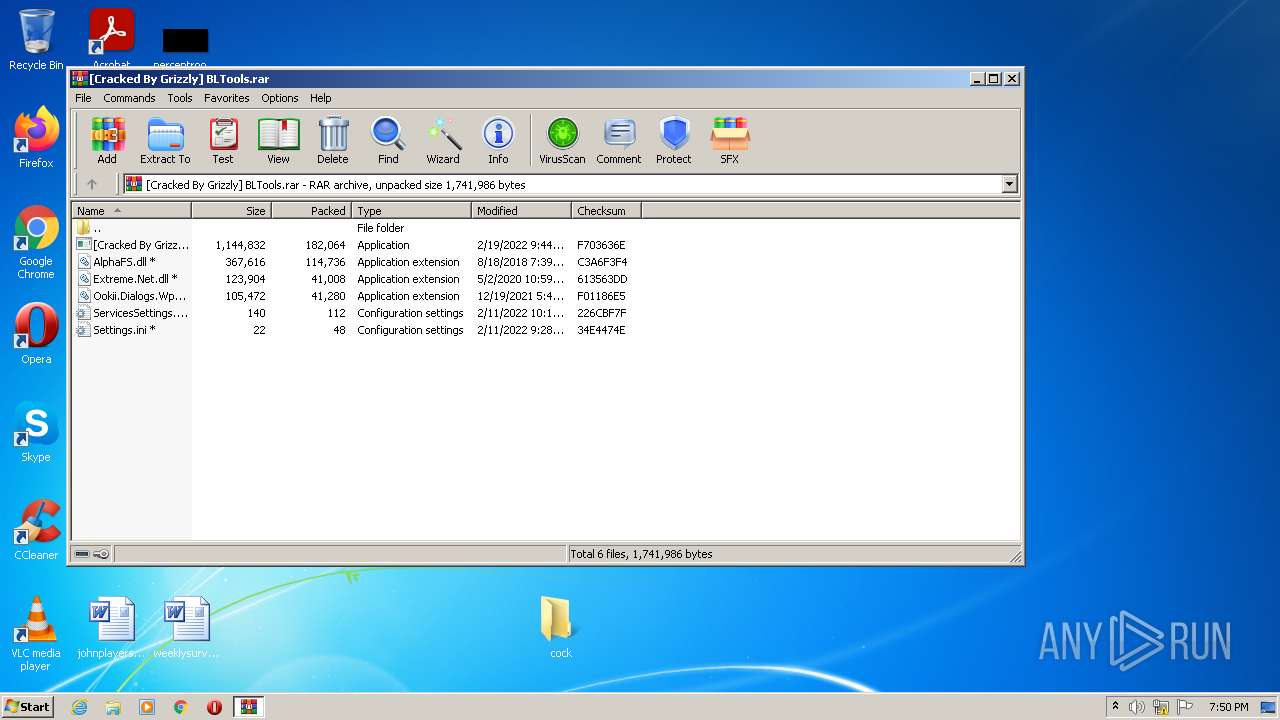
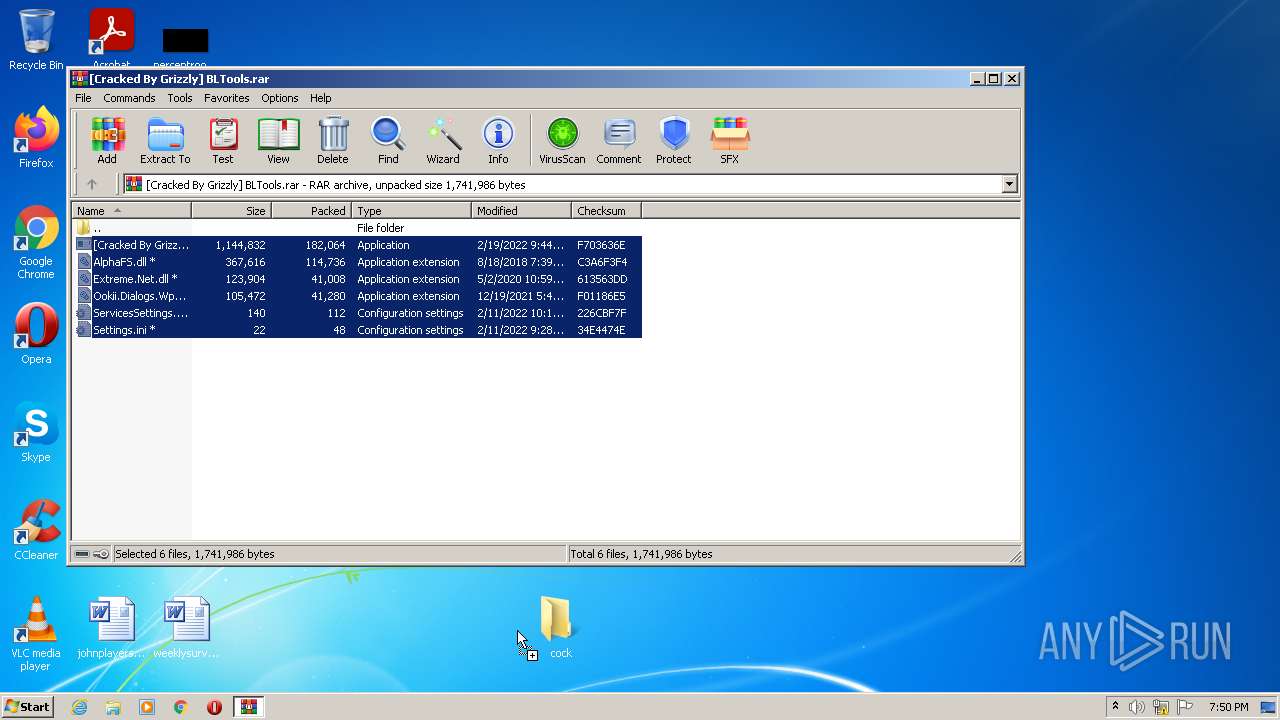
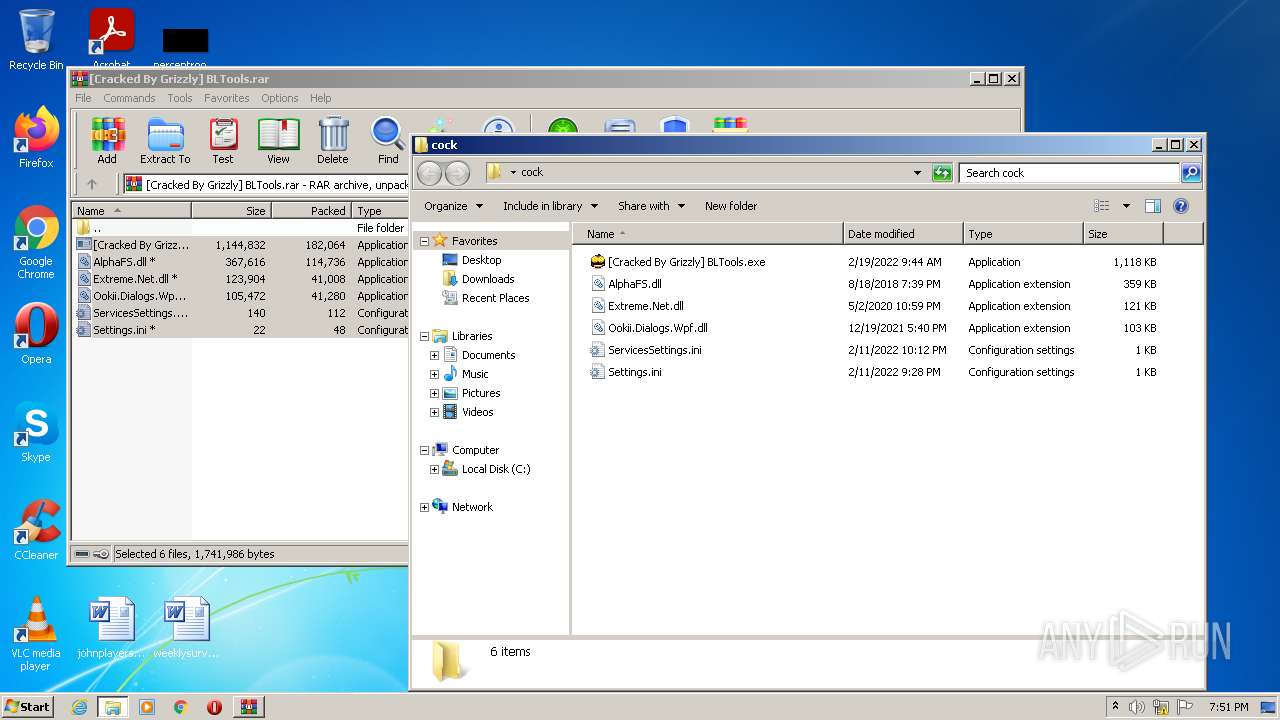
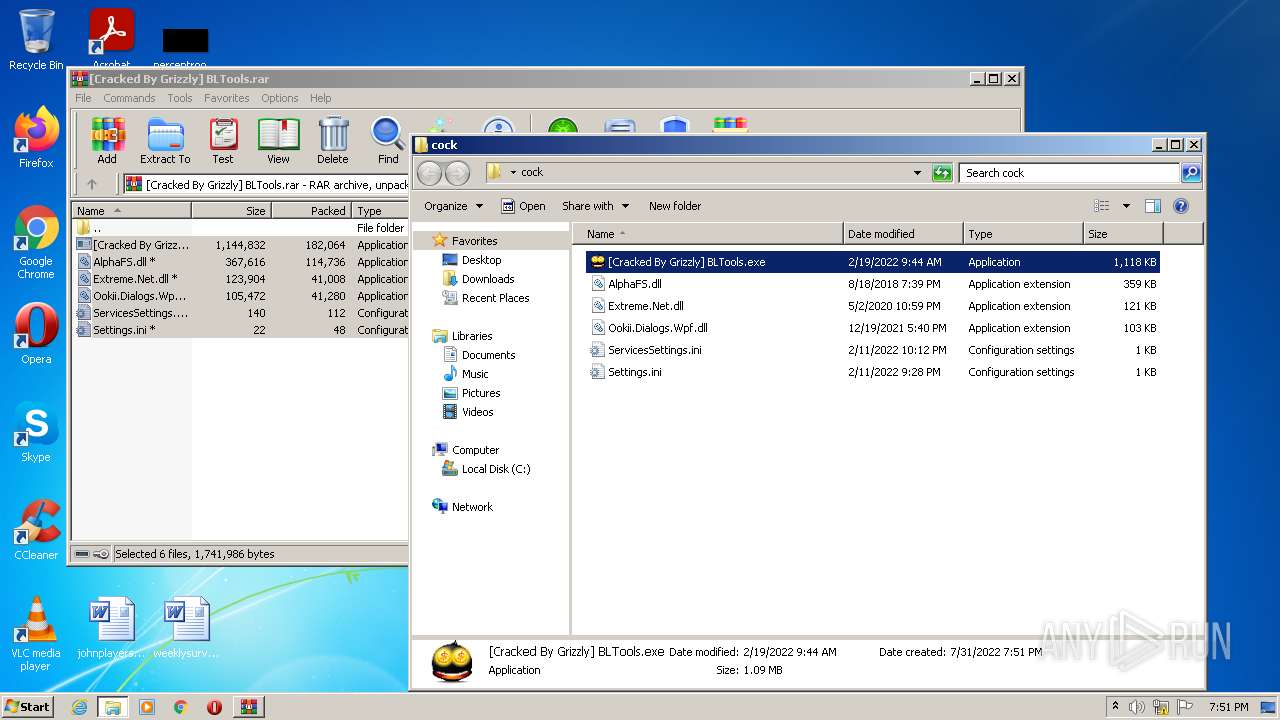
| 2944 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\[Cracked By Grizzly] BLTools.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3928 | "C:\Users\admin\Desktop\cock\[Cracked By Grizzly] BLTools.exe" | C:\Users\admin\Desktop\cock\[Cracked By Grizzly] BLTools.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: BLTools Exit code: 3762504530 Version: 1.5.2.0 Modules
| |||||||||||||||
Total events
1 227
Read events
1 214
Write events
13
Delete events
0
Modification events
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\[Cracked By Grizzly] BLTools.rar | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2944) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
0
Text files
2
Unknown types
0
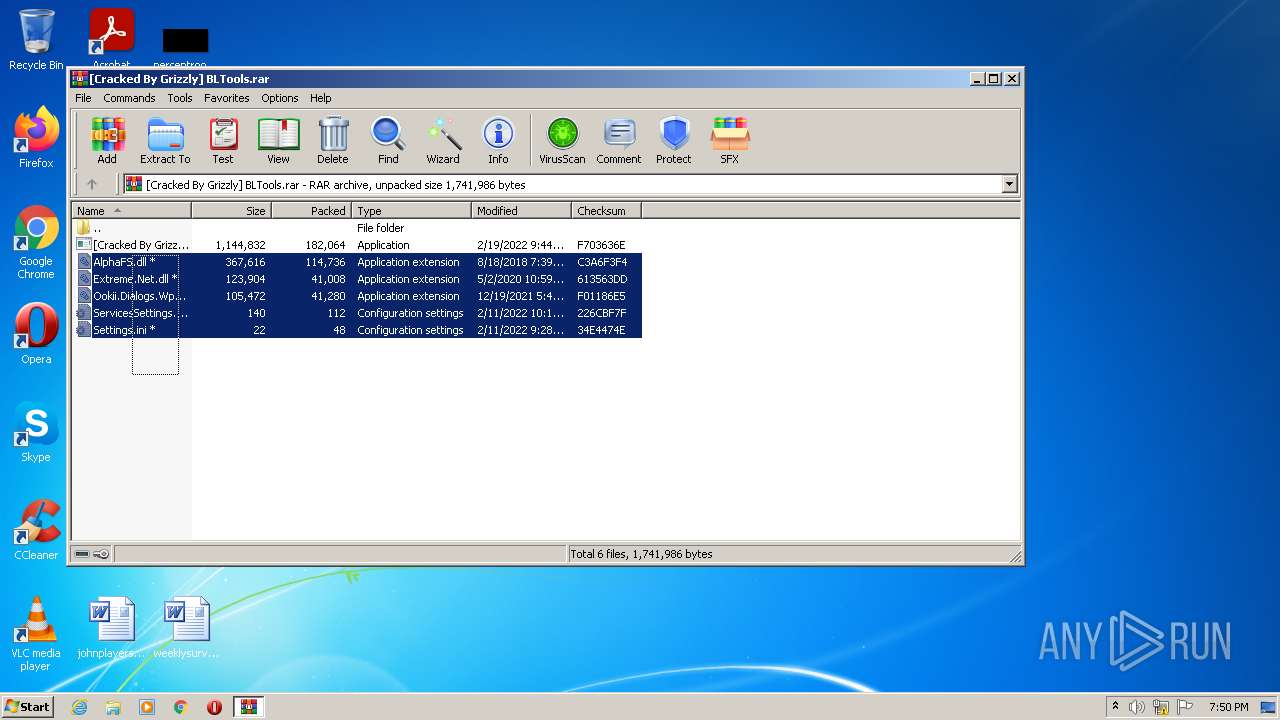
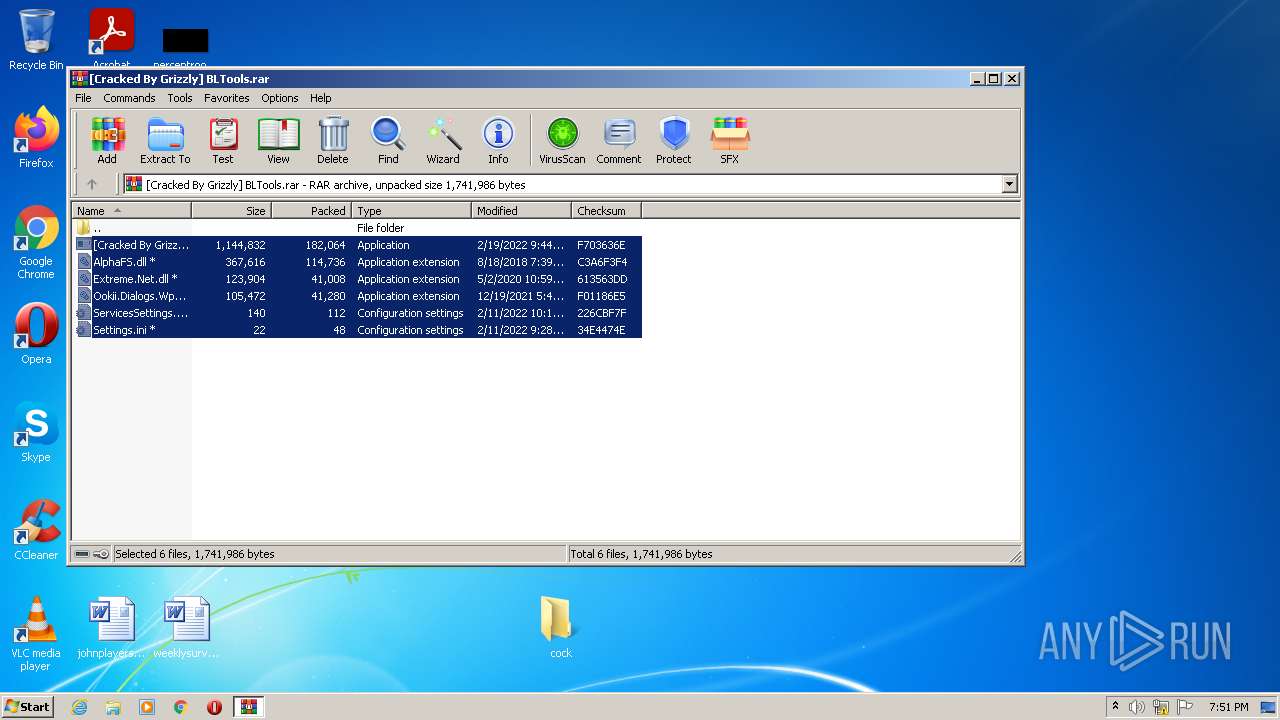
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2944.6497\Ookii.Dialogs.Wpf.dll | executable | |
MD5:932EBB3F9E7113071C6A17818342B7CC | SHA256:285AA8225732DDBCF211B1158BD6CFF8BF3ACBEEAB69617F4BE85862B7105AB5 | |||
| 2944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2944.6497\AlphaFS.dll | executable | |
MD5:F2F6F6798D306D6D7DF4267434B5C5F9 | SHA256:837F2CEAB6BBD9BC4BF076F1CB90B3158191888C3055DD2B78A1E23F1C3AAFDD | |||
| 2944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2944.6497\ServicesSettings.ini | text | |
MD5:B4E59BFE8C3B8976879A8650437874F9 | SHA256:6FB6F51FCD89497E2756B3040B75EE7D92052387AD9EFFCE4C0BA5C92B24BBA0 | |||
| 2944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2944.6497\[Cracked By Grizzly] BLTools.exe | executable | |
MD5:ADBE188BDEB56E9DE21EB22840CB1ECC | SHA256:30634E675EDDB8A0B953DAC342B0B93958809BDAF3577F85A46C4D5D4E3EA539 | |||
| 2944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2944.6497\Extreme.Net.dll | executable | |
MD5:F79F0E3A0361CAC000E2D3553753CD68 | SHA256:8A6518AB7419FBEC3AC9875BAA3AFB410AD1398C7AA622A09CD9084EC6CADFCD | |||
| 2944 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2944.6497\Settings.ini | text | |
MD5:3C3B53B6194B6C168FB40D517FFCBC69 | SHA256:696FCE0BDC97879F25A45F34EE095E1942E291DF40EF419D47E0BD7972531657 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report