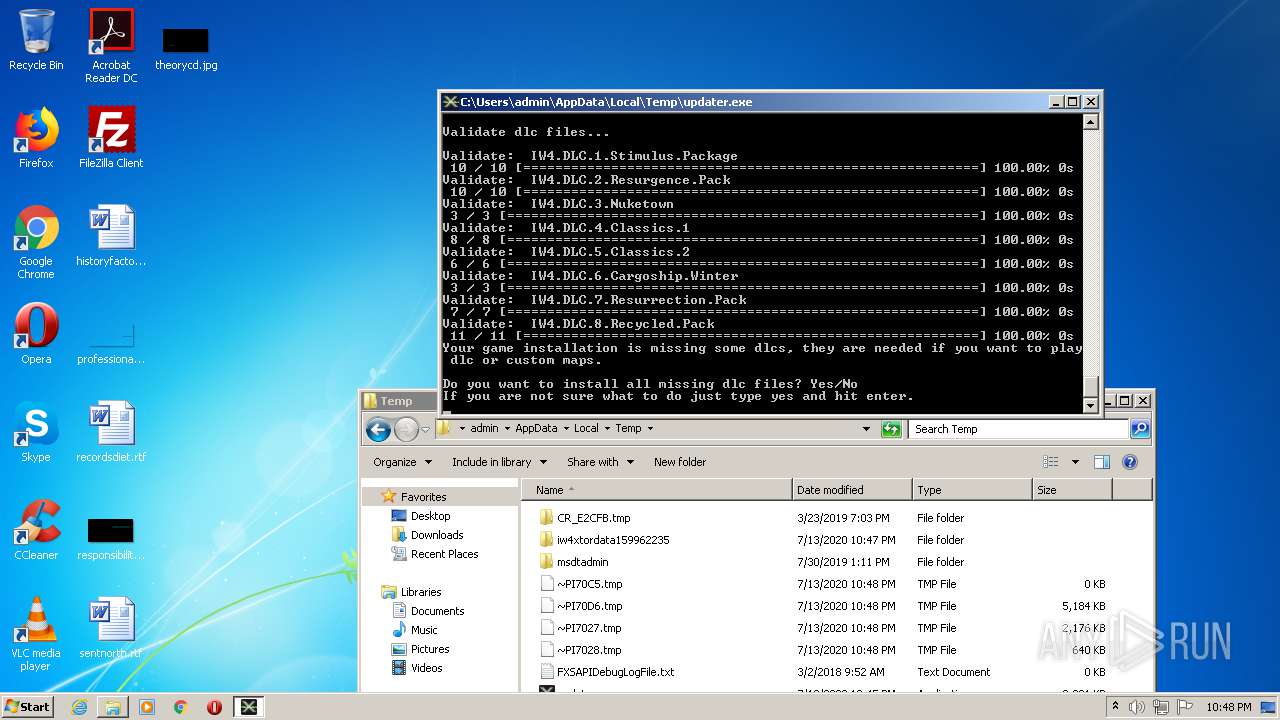
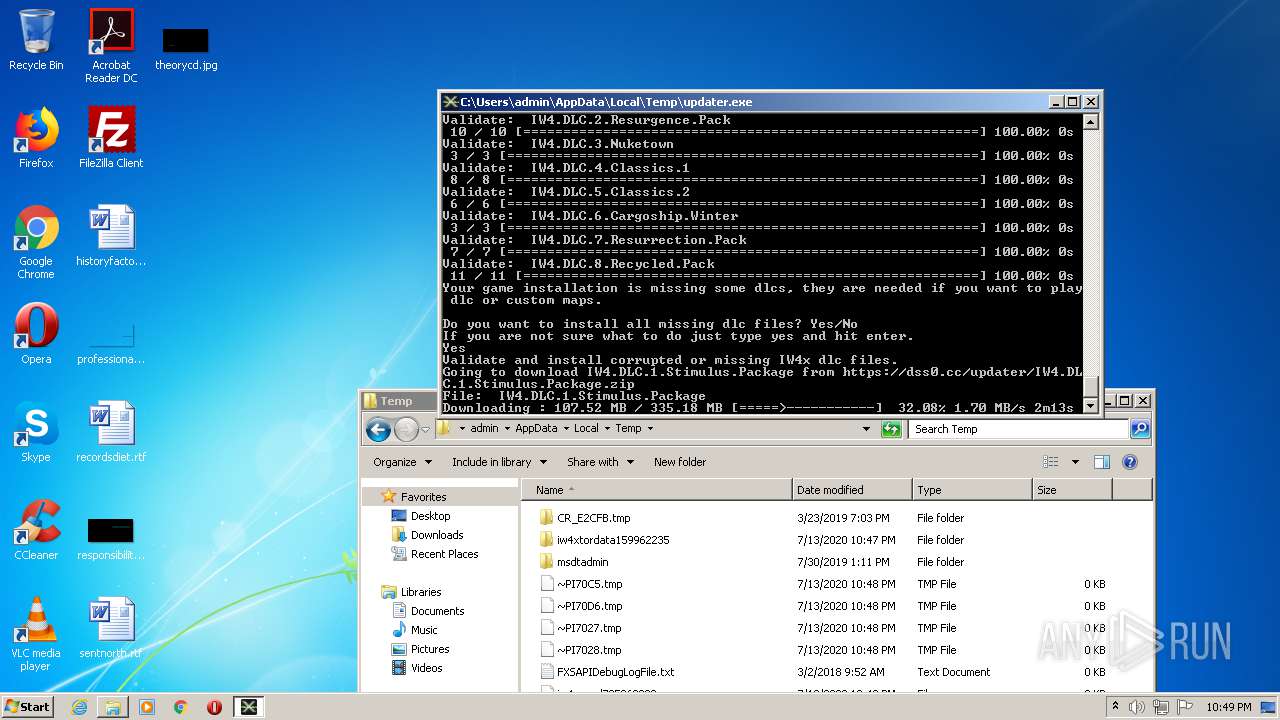
| File name: | updater.exe |
| Full analysis: | https://app.any.run/tasks/805bf04b-d5a7-434f-bbe4-29251ad52b22 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 21:45:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | 11DF9FD1A9FFC1DC72778B81D8BC609D |
| SHA1: | E5E661A346EAD9B932DC1BAE2A22F0FE074B0A7B |
| SHA256: | FB2A60A7181DEED228524F6853192F877241CE0C27F7B9584D56C246A81D9619 |
| SSDEEP: | 49152:GB90TPblJHJGhY0bibkguO51u228w3GL7AsKLac:GBiTDlJHJ2Y1AO51ubGL0s+a |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 4024)
INFO
Dropped object may contain Bitcoin addresses
- updater.exe (PID: 1872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:03 17:26:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2076672 |
| InitializedDataSize: | 364544 |
| UninitializedDataSize: | 5218304 |
| EntryPoint: | 0x6f49a0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.3.0.0 |
| ProductVersionNumber: | 0.3.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | IW4x Updater |
| FileDescription: | IW4x Updater |
| FileVersion: | 0.3.0.0 |
| InternalName: | iw4x-updater |
| OriginalFileName: | iw4x-updater.exe |
| PrivateBuild: | 1 |
| ProductName: | IW4x Updater |
| ProductVersion: | 0.3.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 03-Jul-2017 15:26:27 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Comments: | IW4x Updater |
| FileDescription: | IW4x Updater |
| FileVersion: | 0.3.0.0 |
| InternalName: | iw4x-updater |
| OriginalFilename: | iw4x-updater.exe |
| PrivateBuild: | 1 |
| ProductName: | IW4x Updater |
| ProductVersion: | 0.3.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 03-Jul-2017 15:26:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x004FA000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x004FB000 | 0x001FB000 | 0x001FA600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9999 |
.rsrc | 0x006F6000 | 0x00059000 | 0x00058A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.92455 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04134 | 554 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.7405 | 1128 | UNKNOWN | English - United States | RT_ICON |
3 | 5.84328 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.88064 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 5.90444 | 67624 | UNKNOWN | English - United States | RT_ICON |
6 | 5.87674 | 270376 | UNKNOWN | English - United States | RT_ICON |
7 | 2.69468 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
WINMM.DLL |
WS2_32.dll |
msvcrt.dll |
ntdll.dll |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
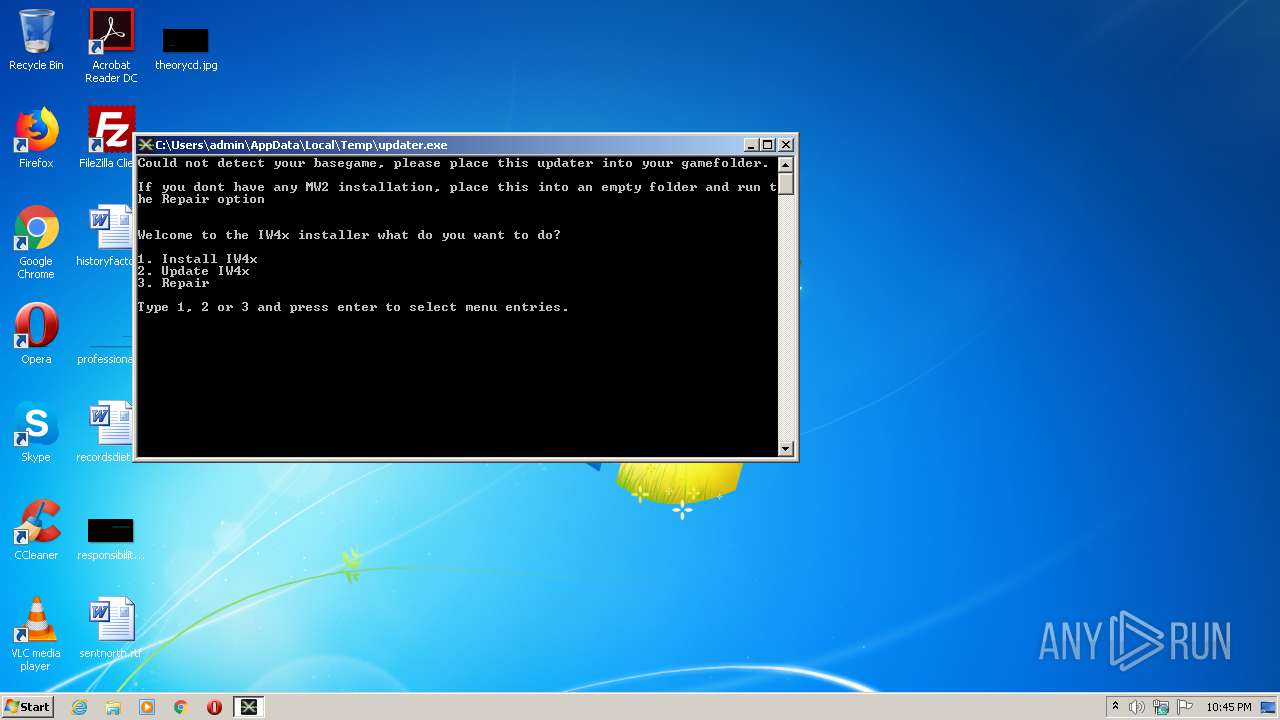
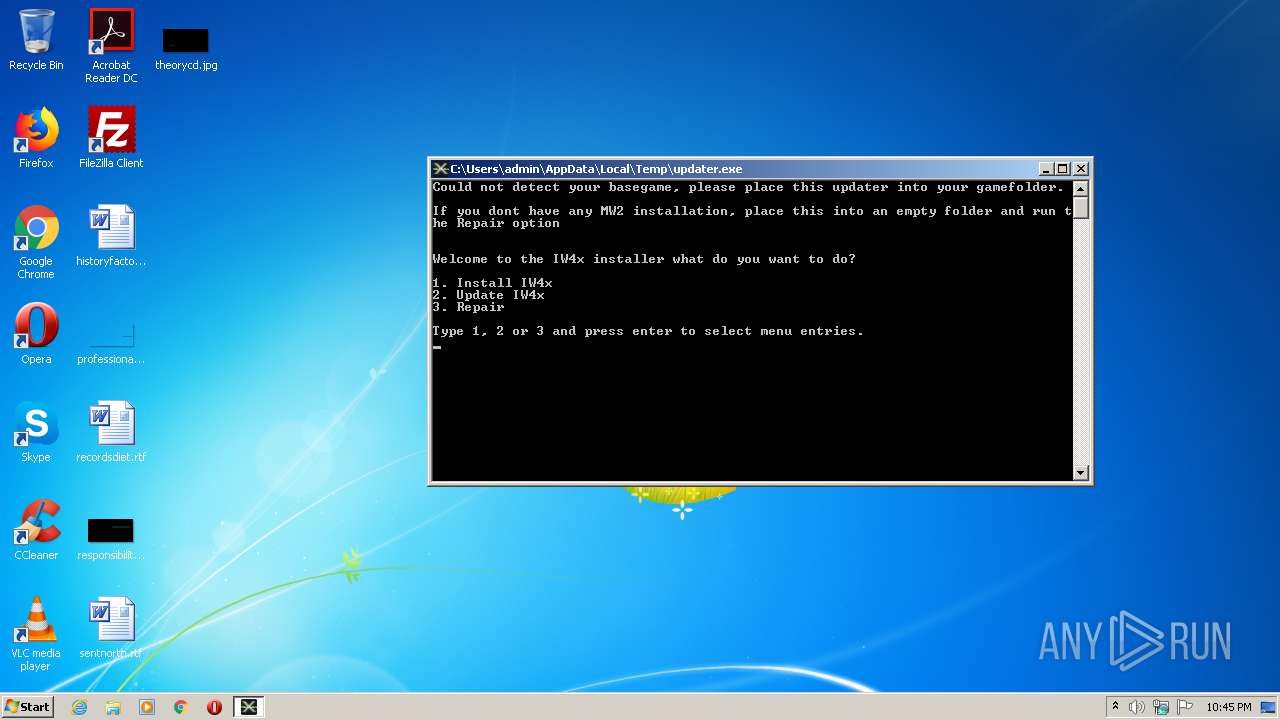
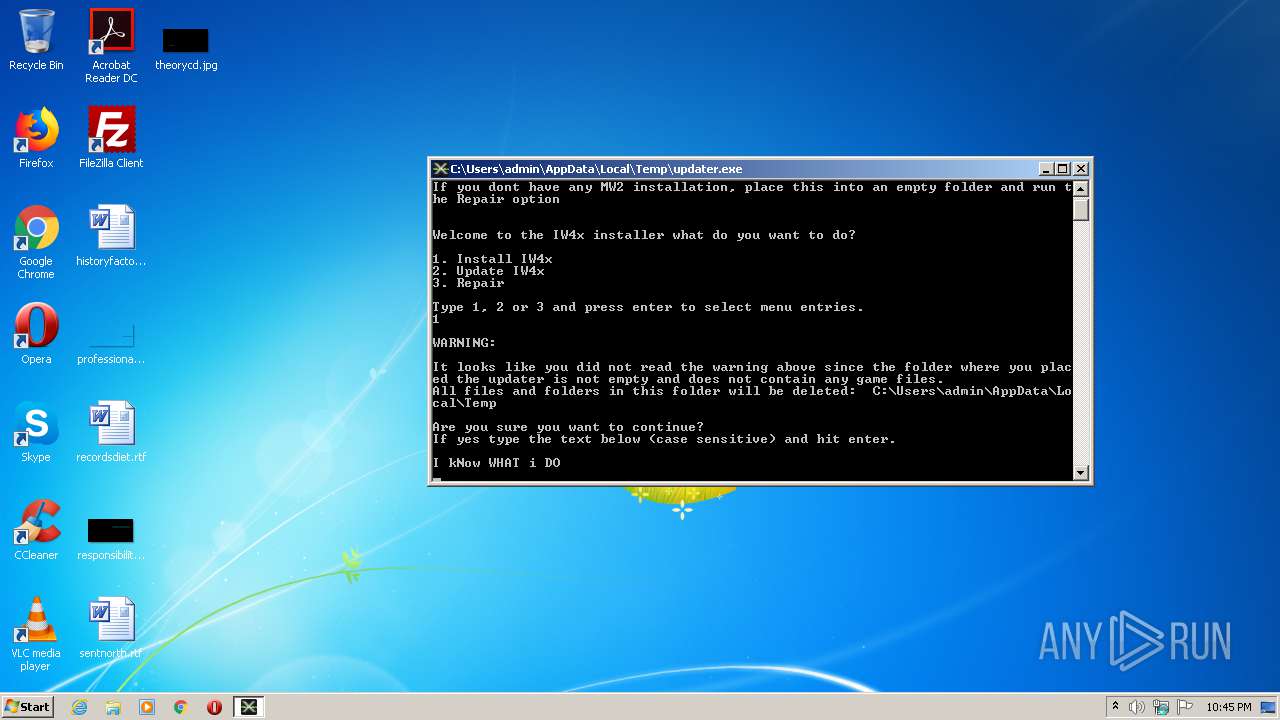
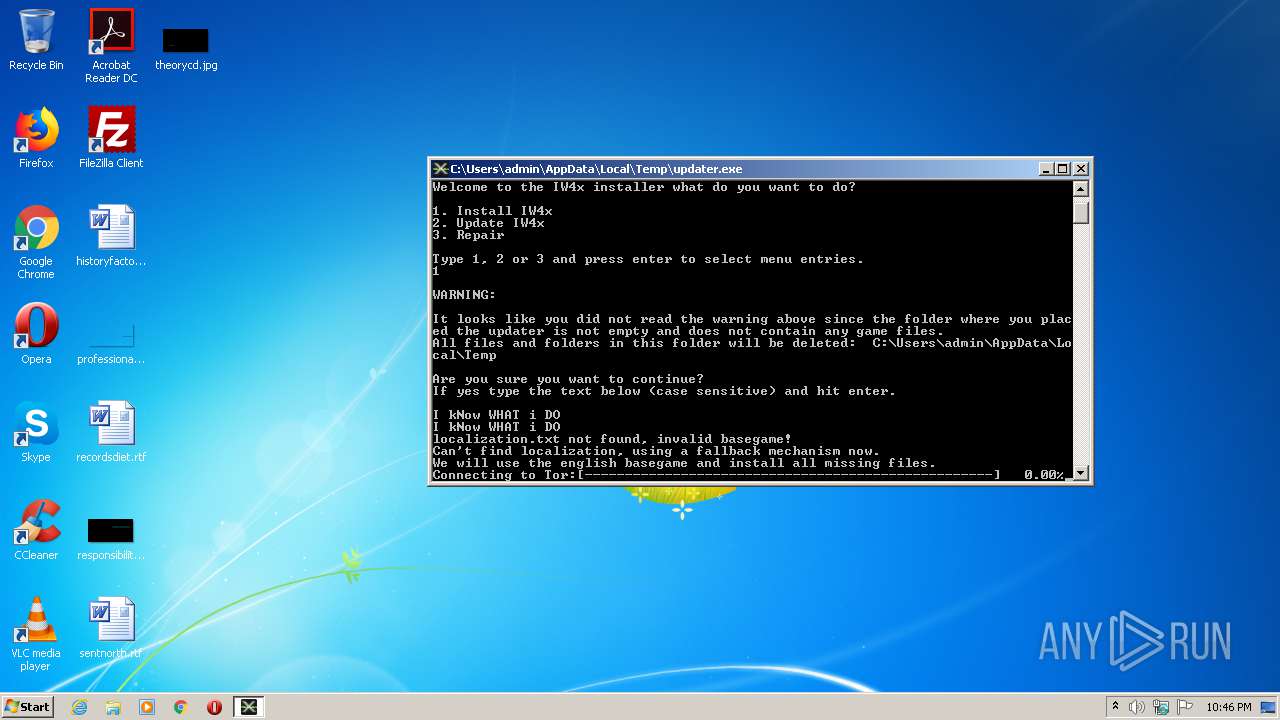
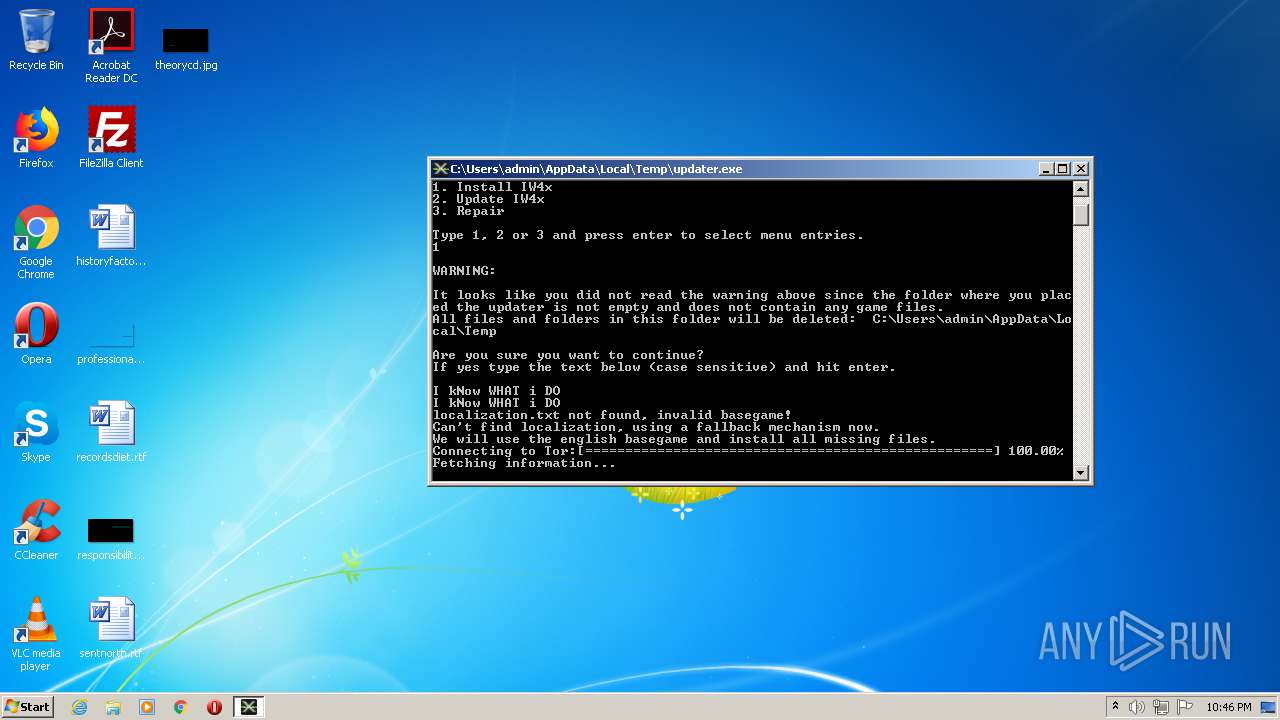
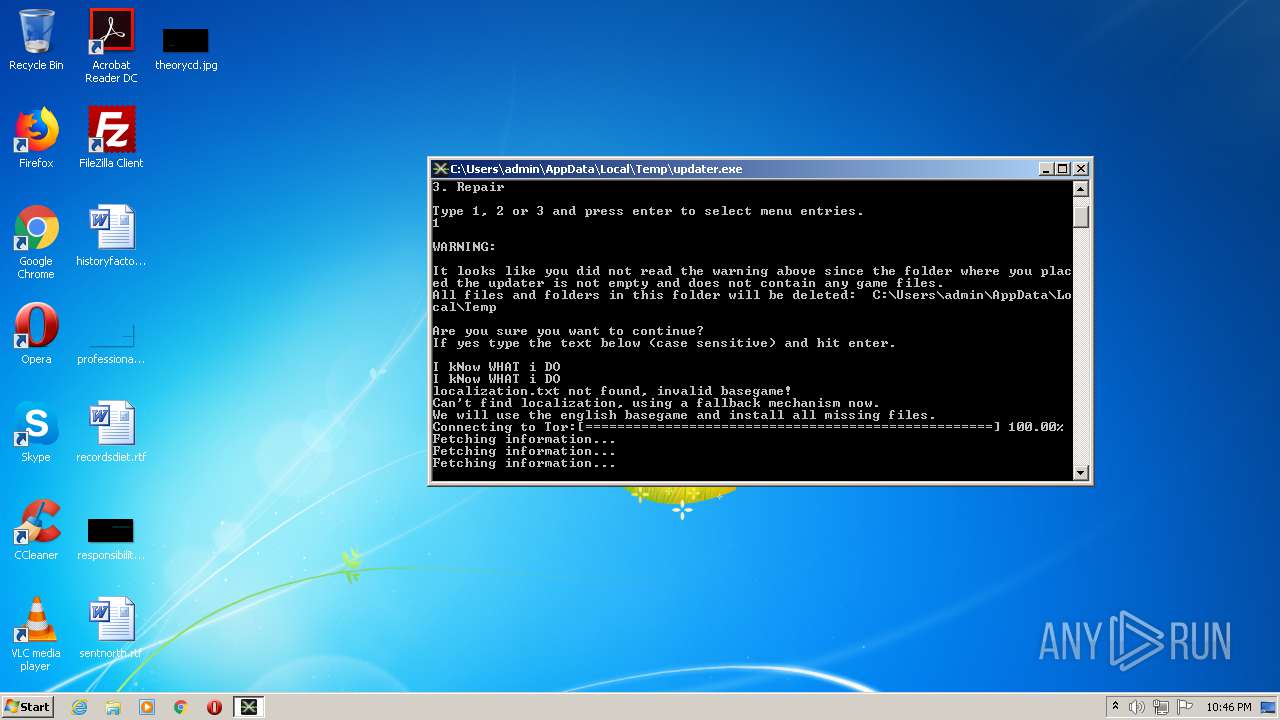
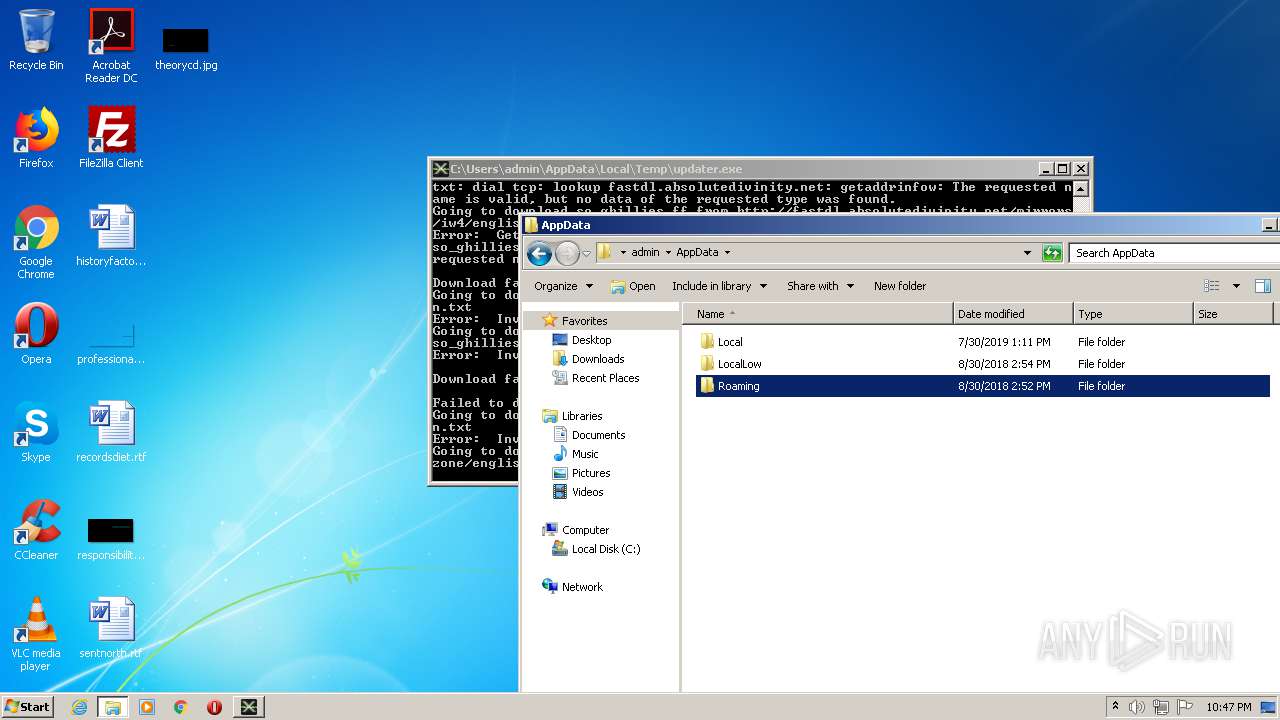
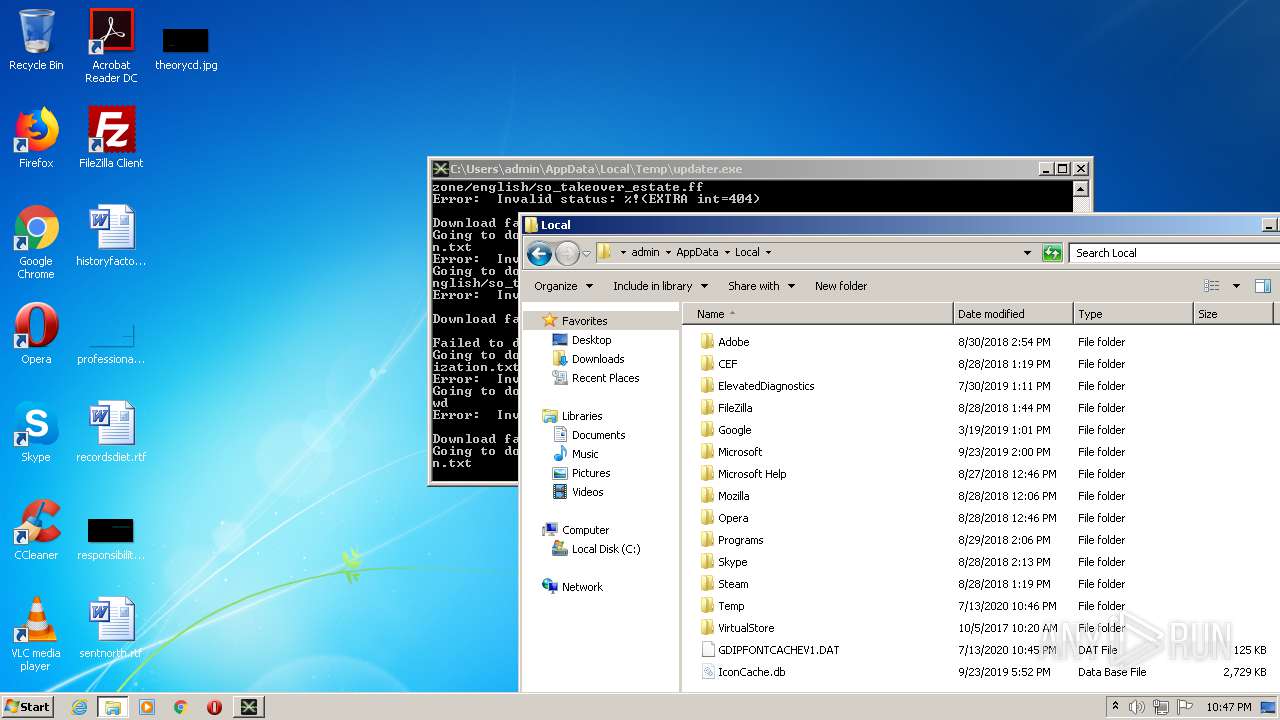
| 1872 | "C:\Users\admin\AppData\Local\Temp\updater.exe" | C:\Users\admin\AppData\Local\Temp\updater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: IW4x Updater Exit code: 0 Version: 0.3.0.0 Modules
| |||||||||||||||
| 4024 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
73
Read events
56
Write events
17
Delete events
0
Modification events
| (PID) Process: | (4024) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (4024) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (1872) updater.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1872) updater.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (1872) updater.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (1872) updater.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (1872) updater.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (1872) updater.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
Executable files
0
Suspicious files
0
Text files
12
Unknown types
0
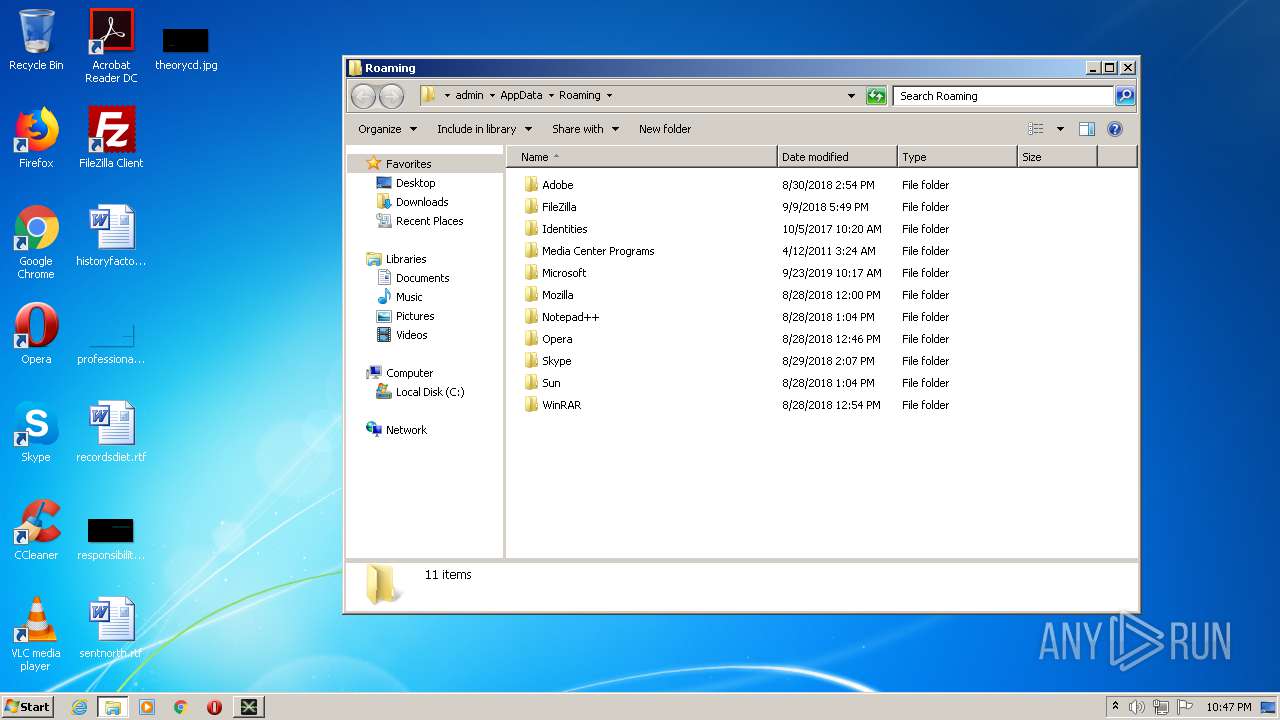
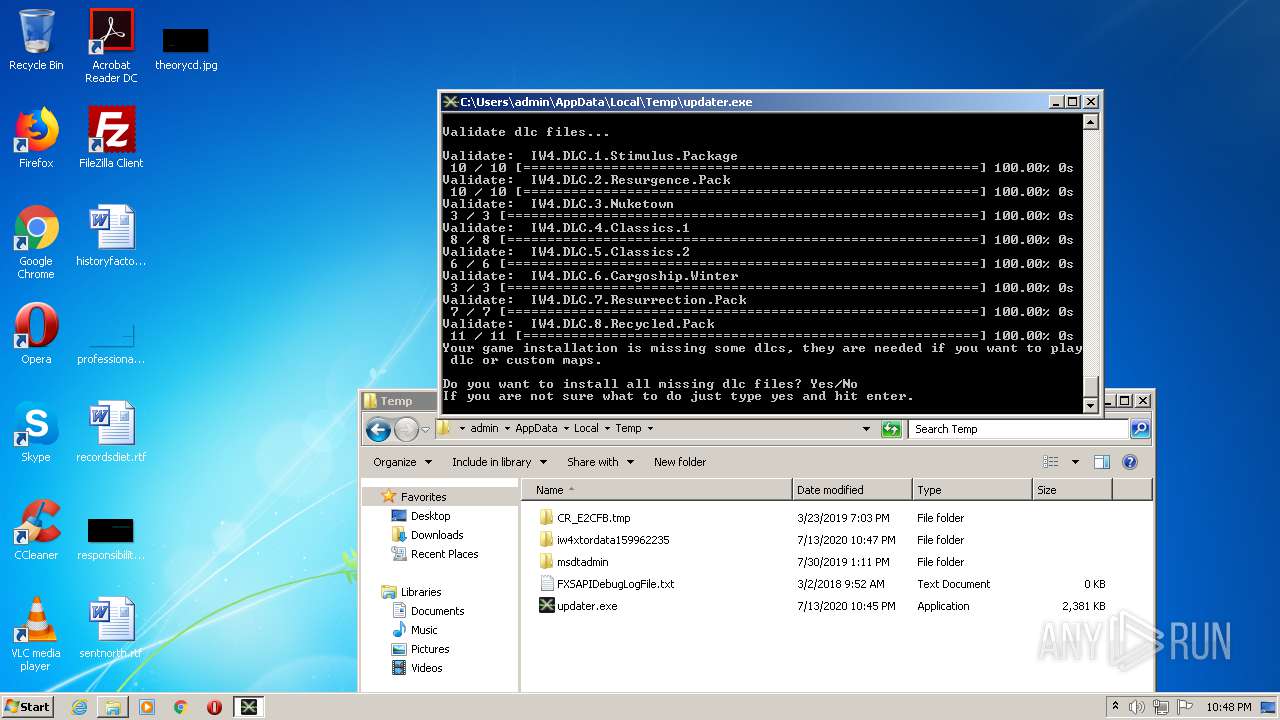
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
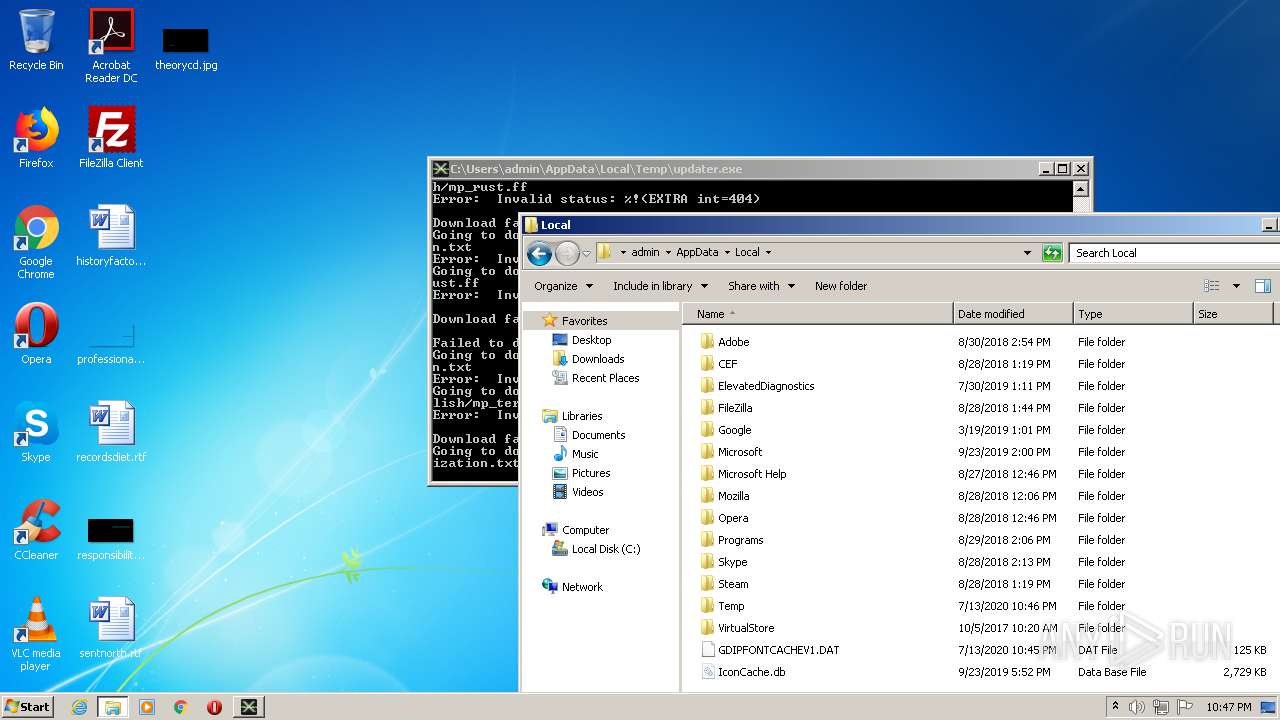
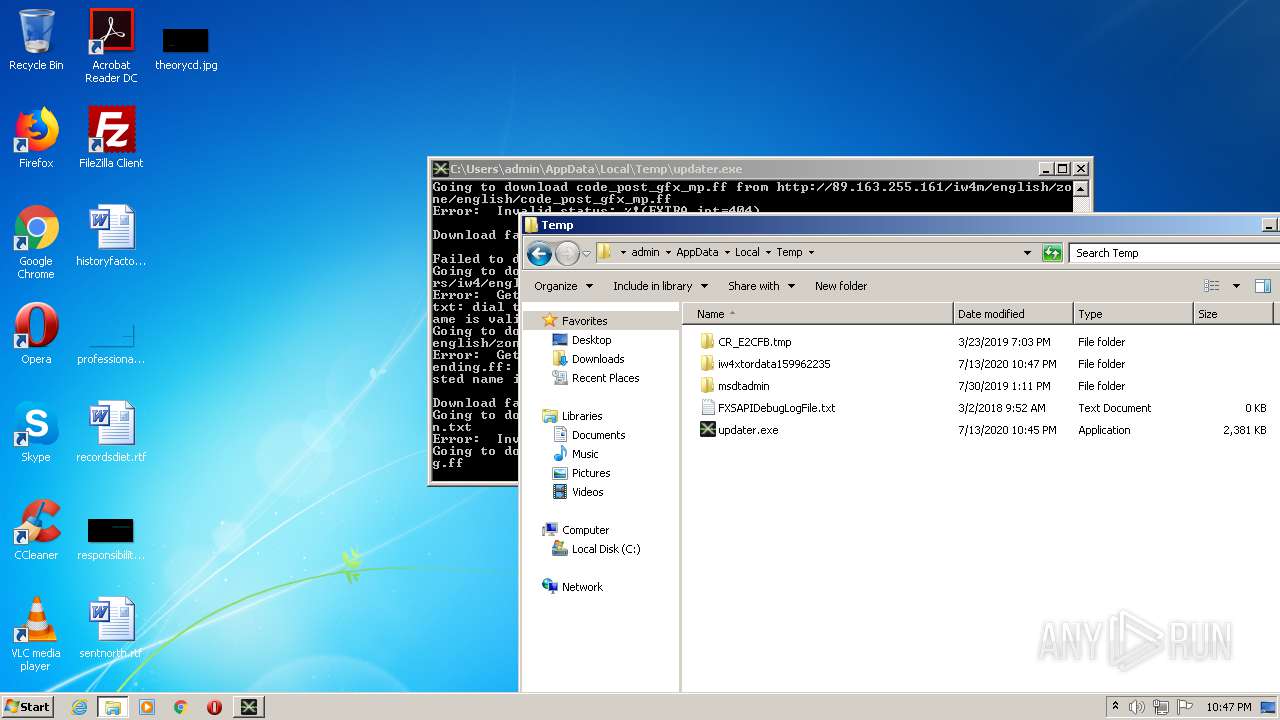
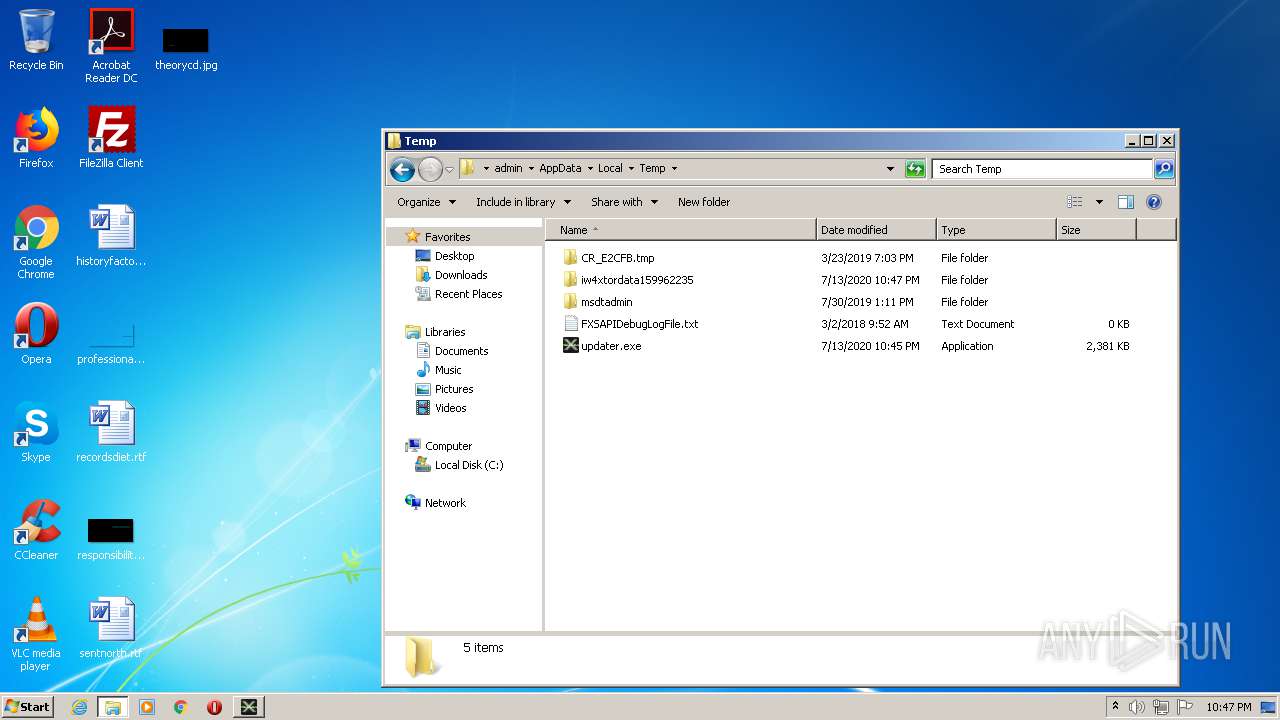
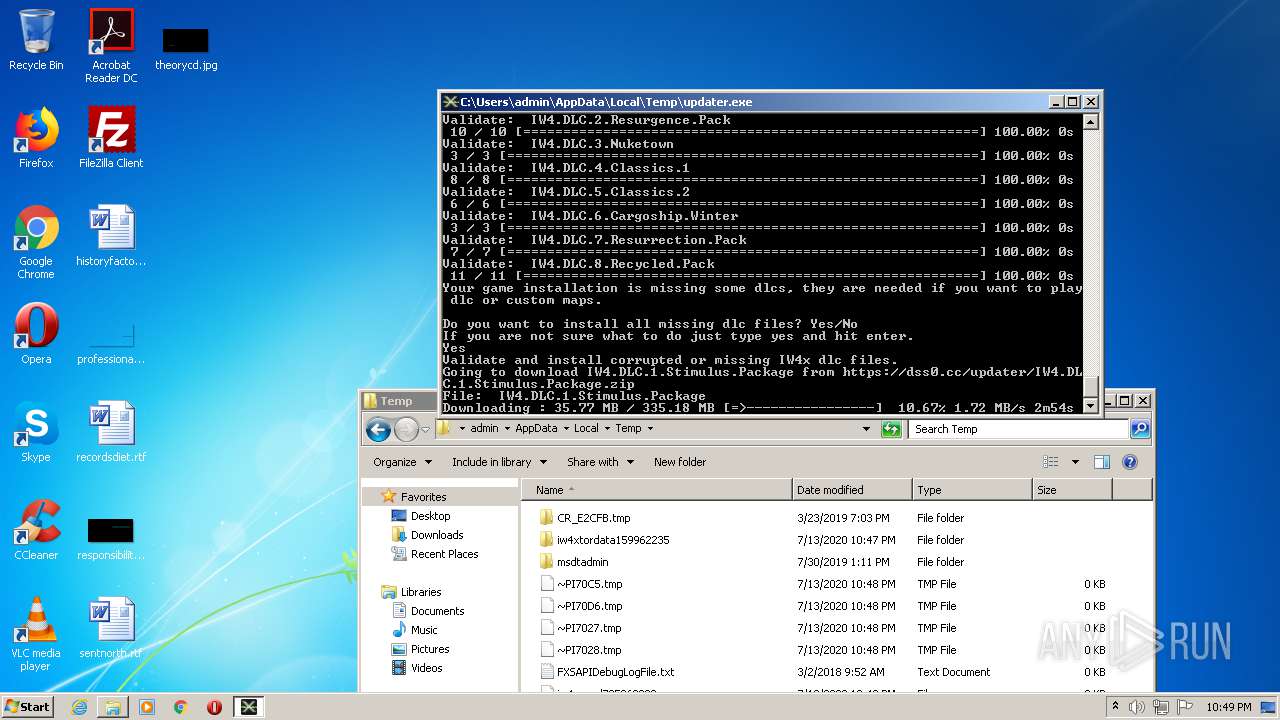
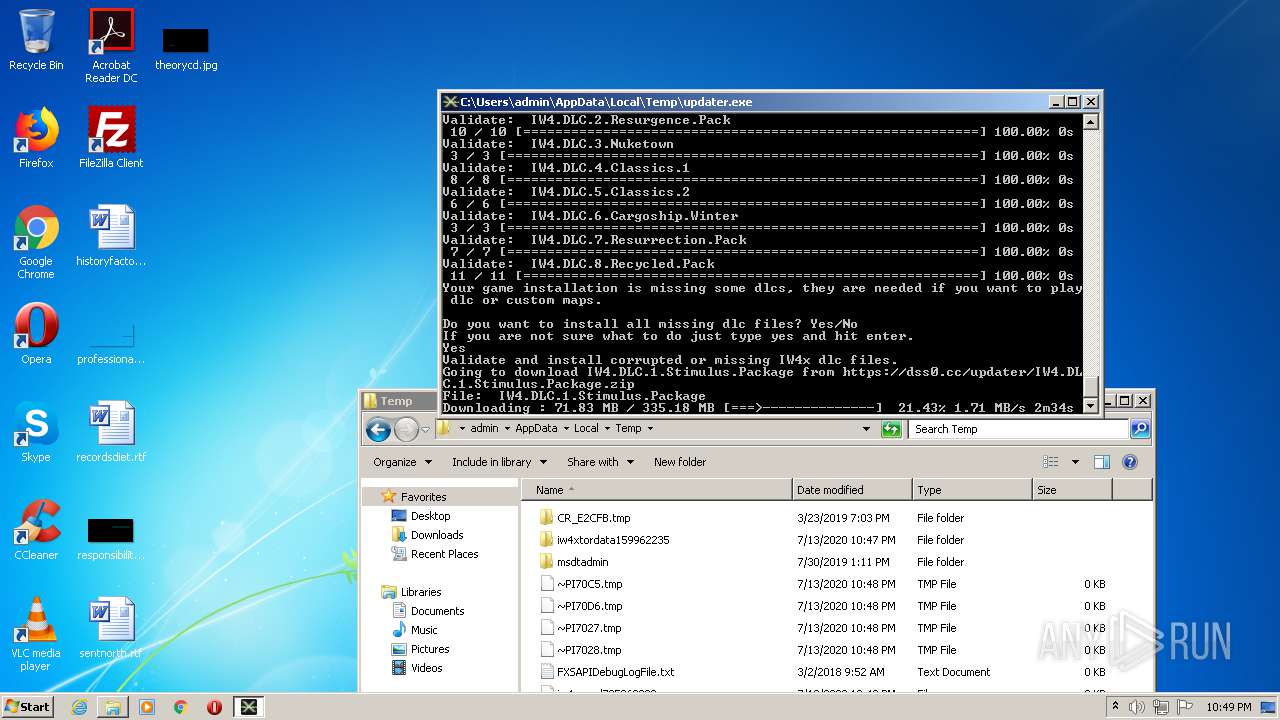
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\controlport.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\state.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\control_auth_cookie.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\unverified-microdesc-consensus.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\cached-certs.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\cached-microdesc-consensus.tmp | — | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\cached-microdescs.new | text | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\state | text | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\unverified-microdesc-consensus | text | |
MD5:— | SHA256:— | |||
| 1872 | updater.exe | C:\Users\admin\AppData\Local\Temp\iw4xtordata159962235\cached-microdesc-consensus | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
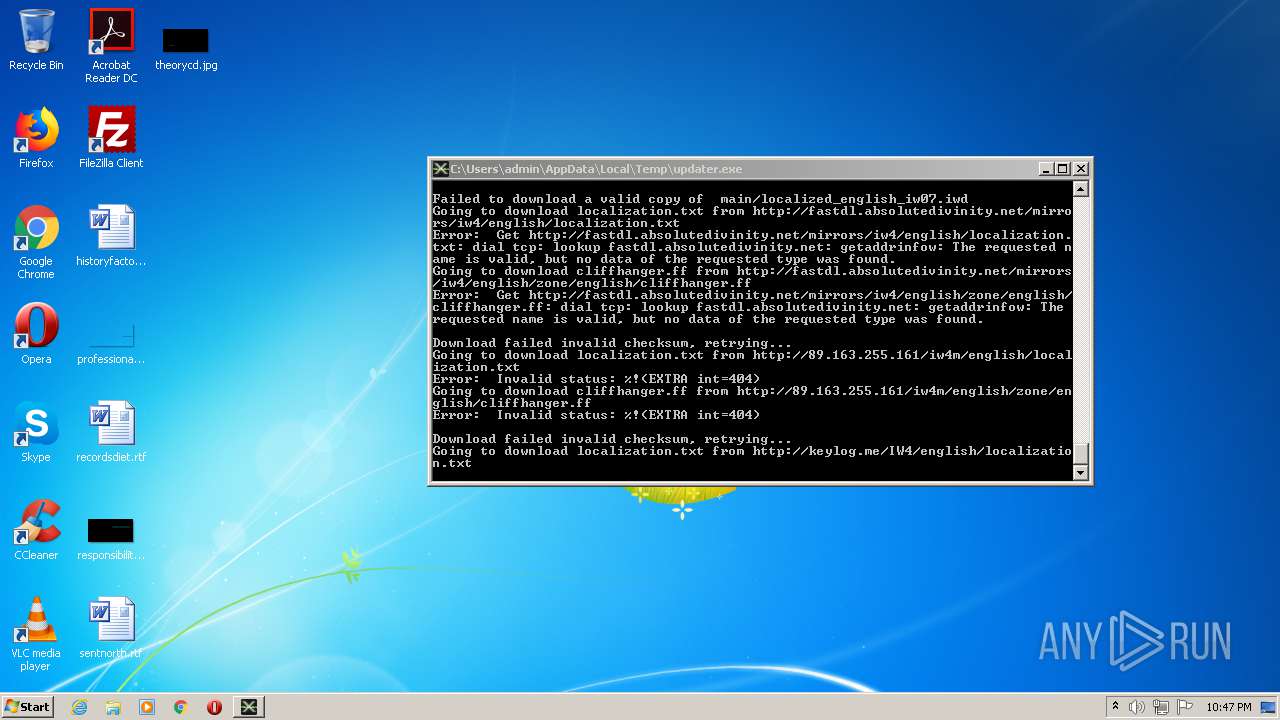
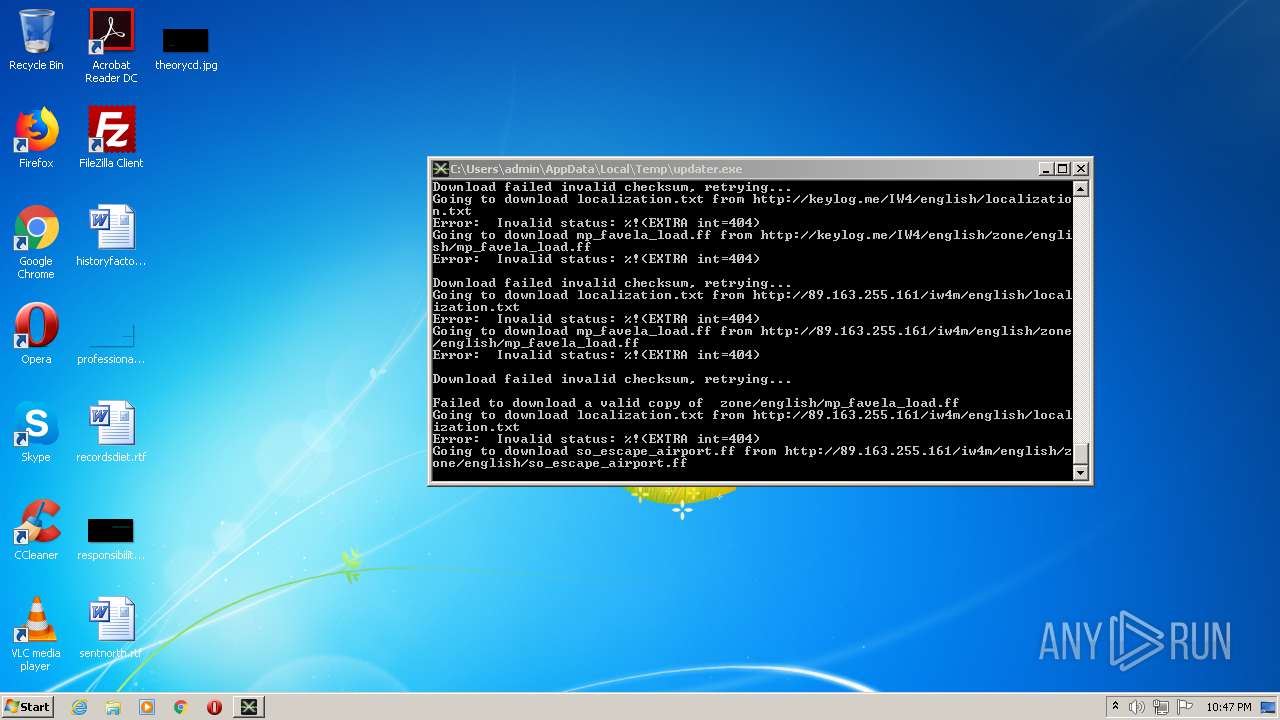
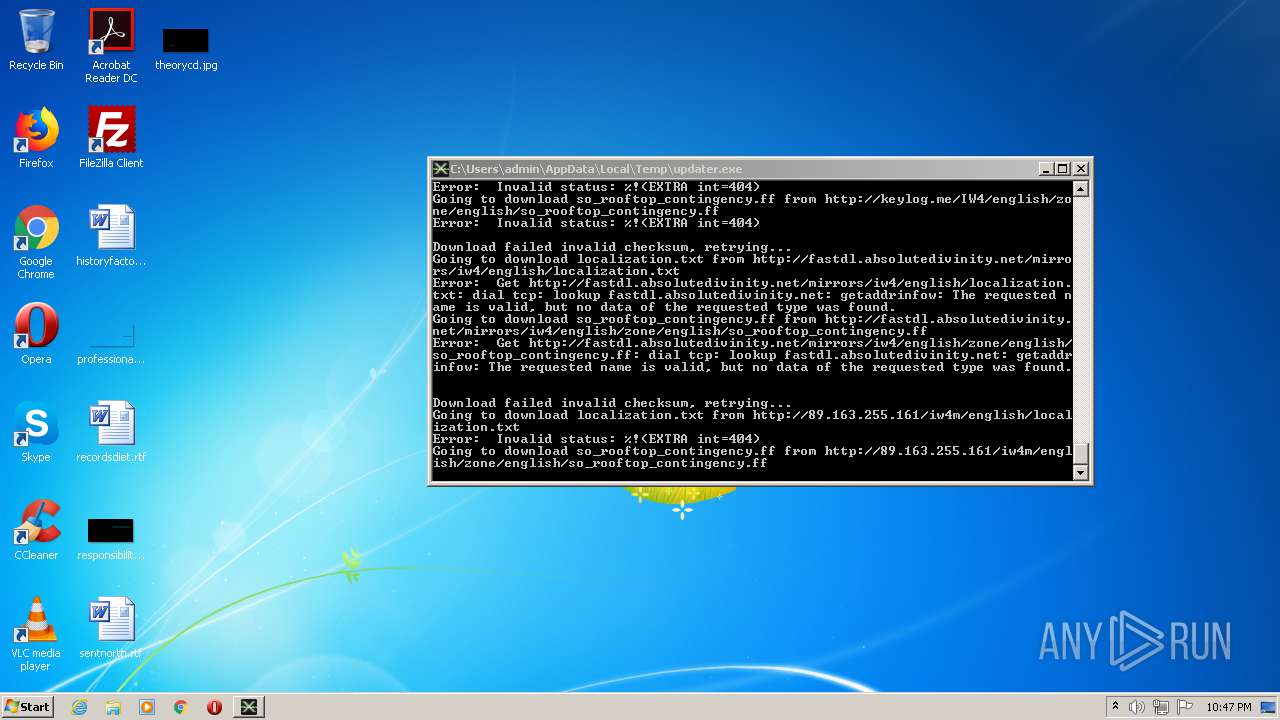
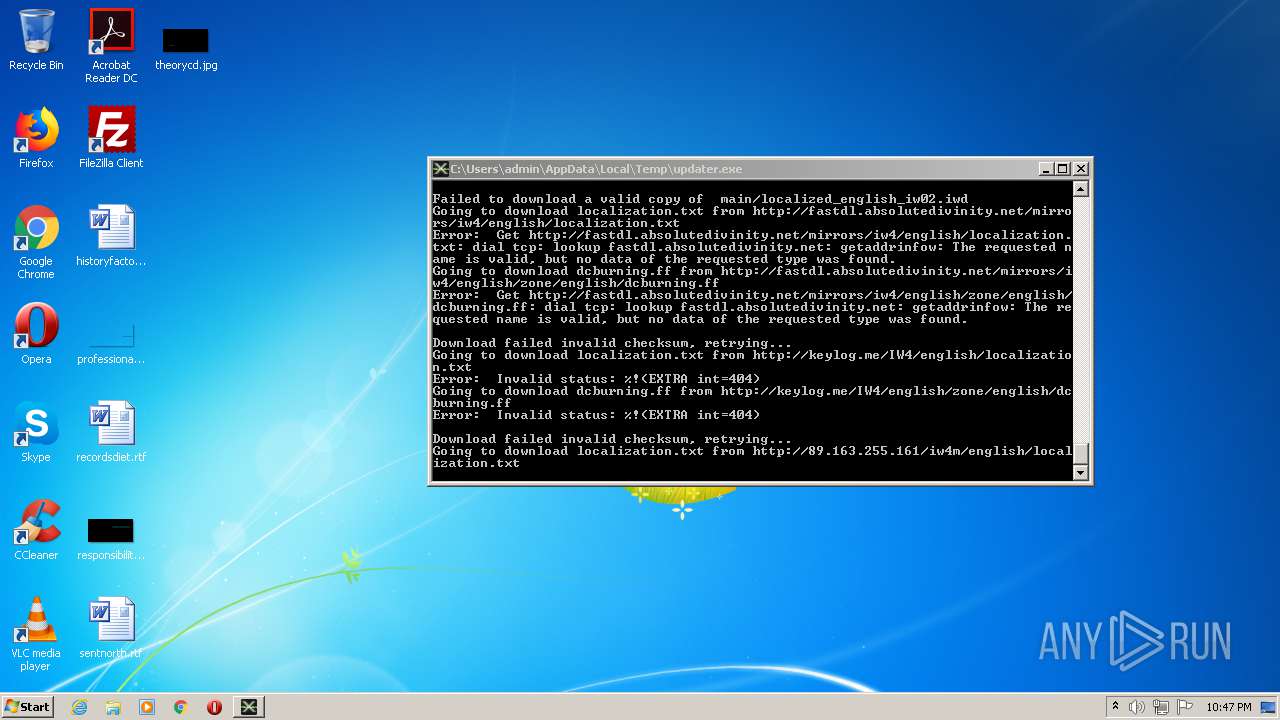
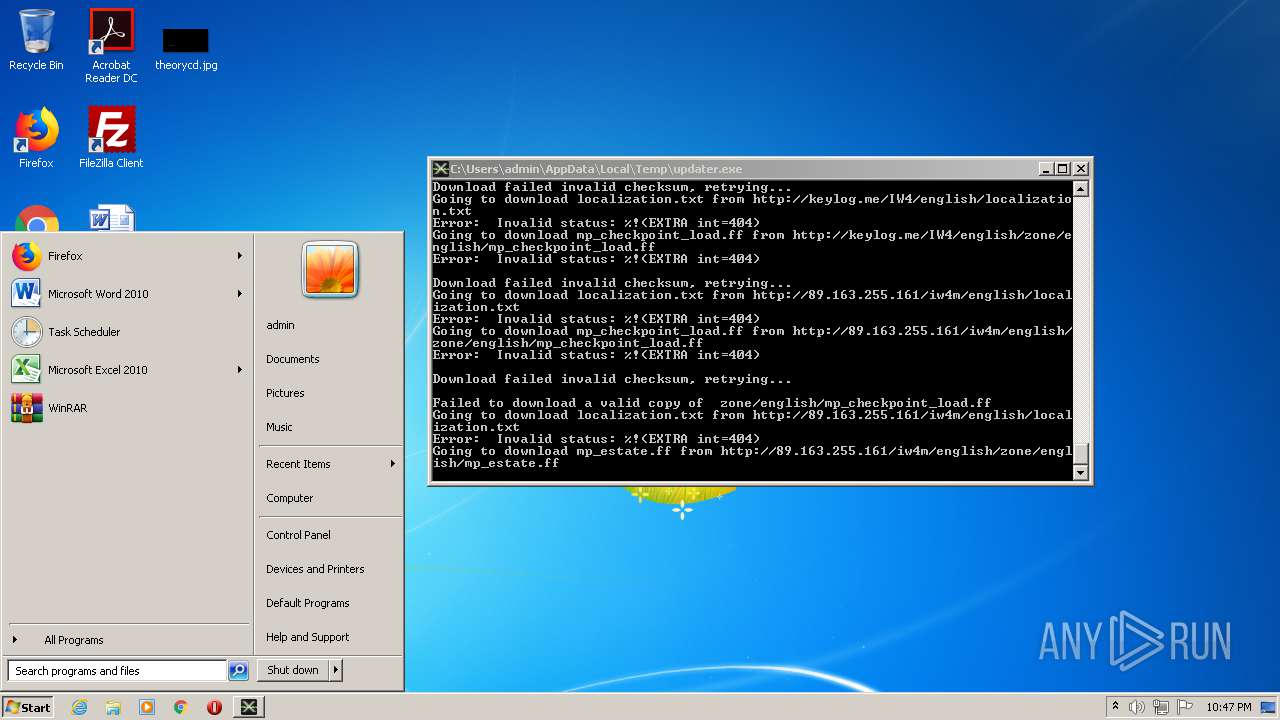
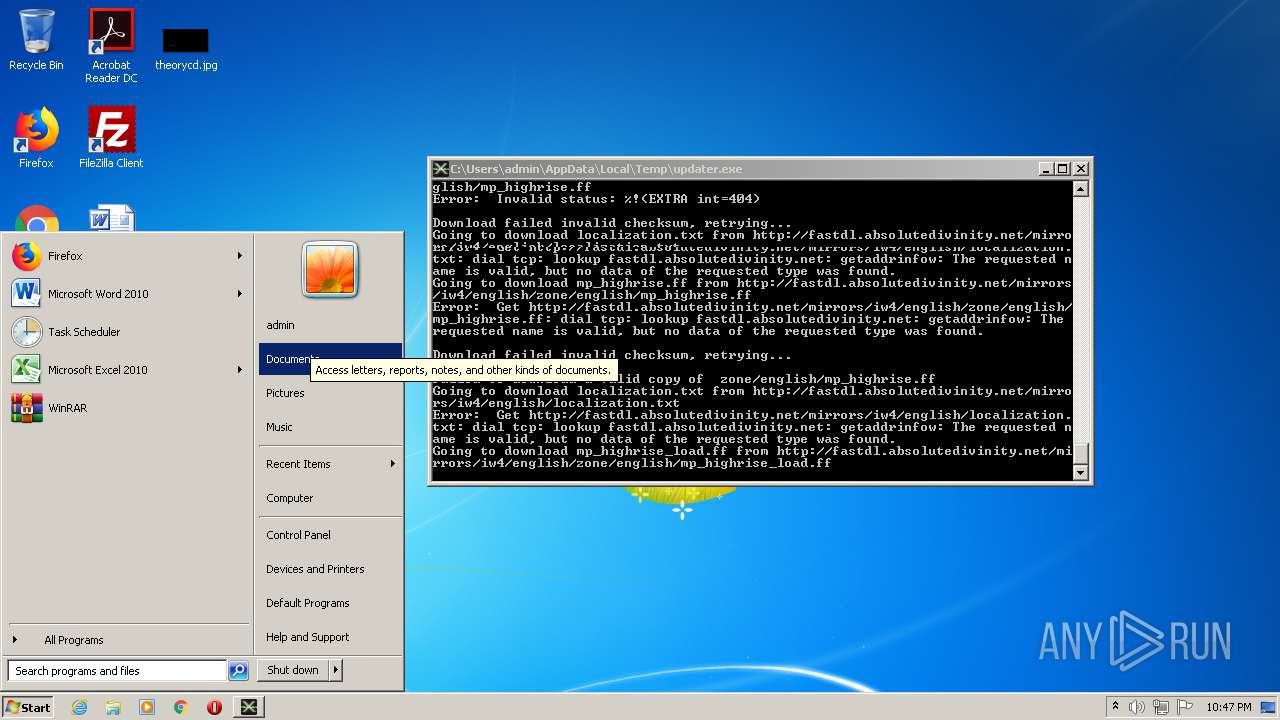
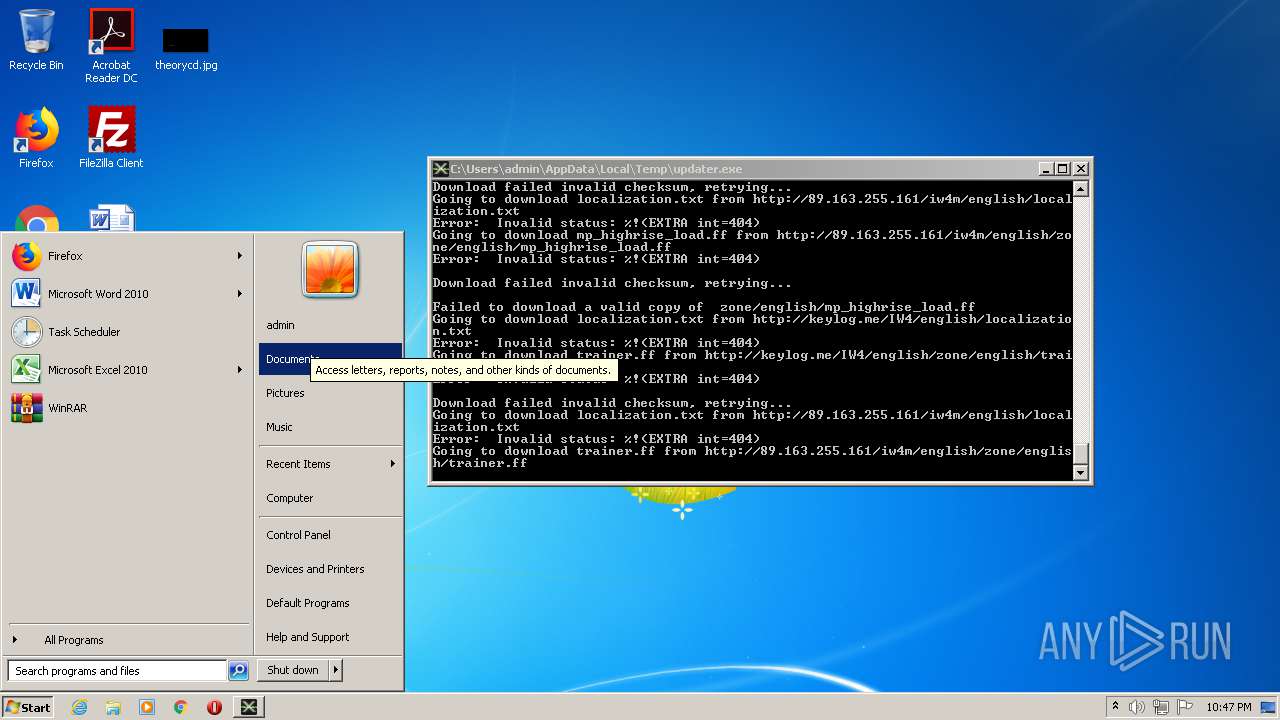
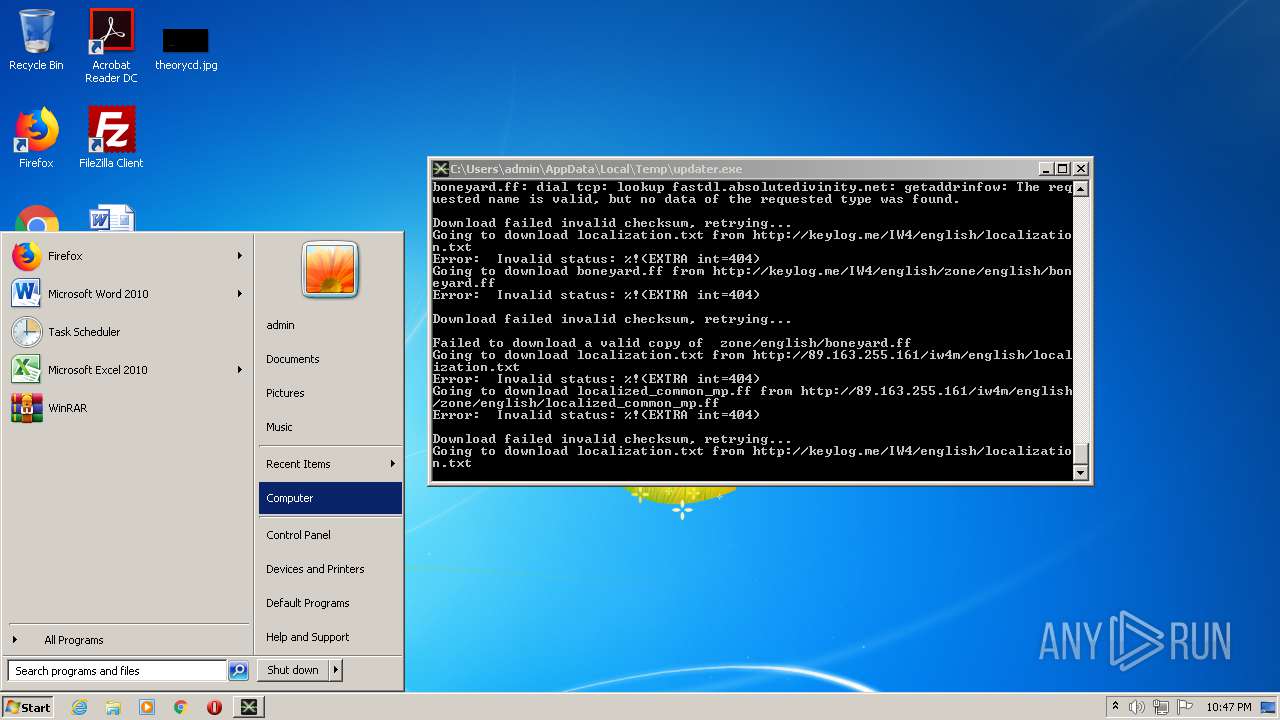
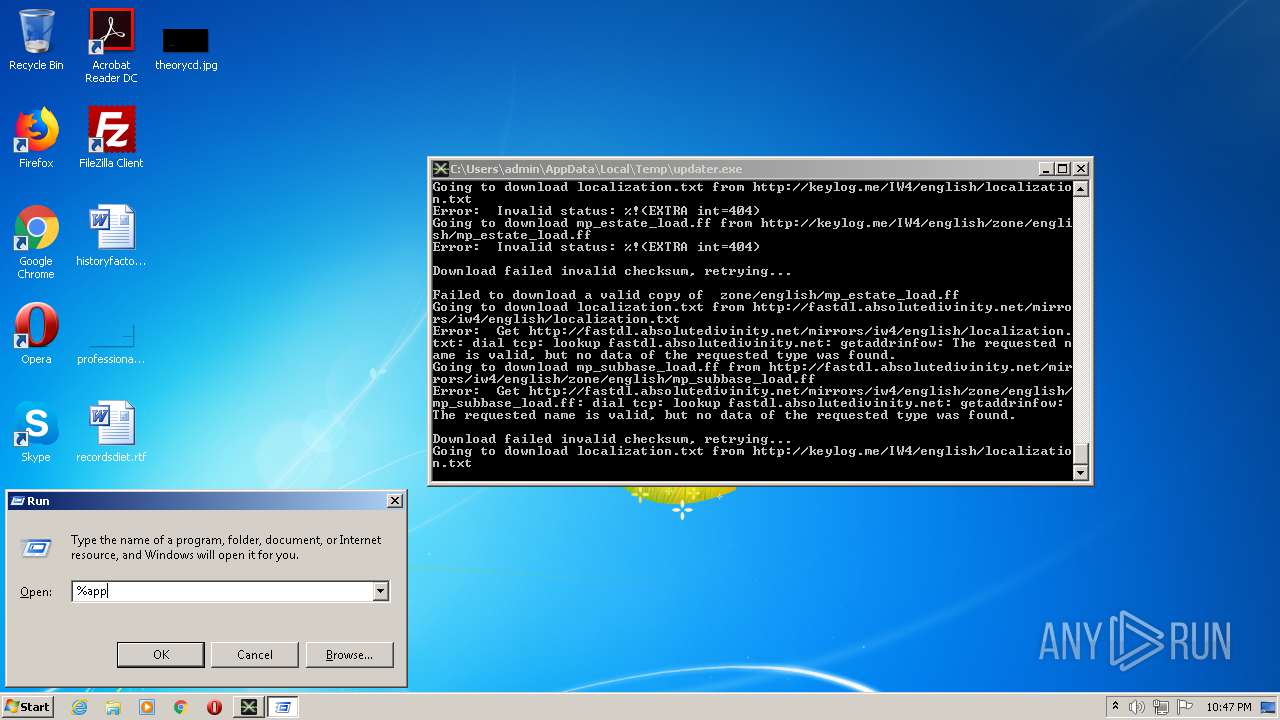
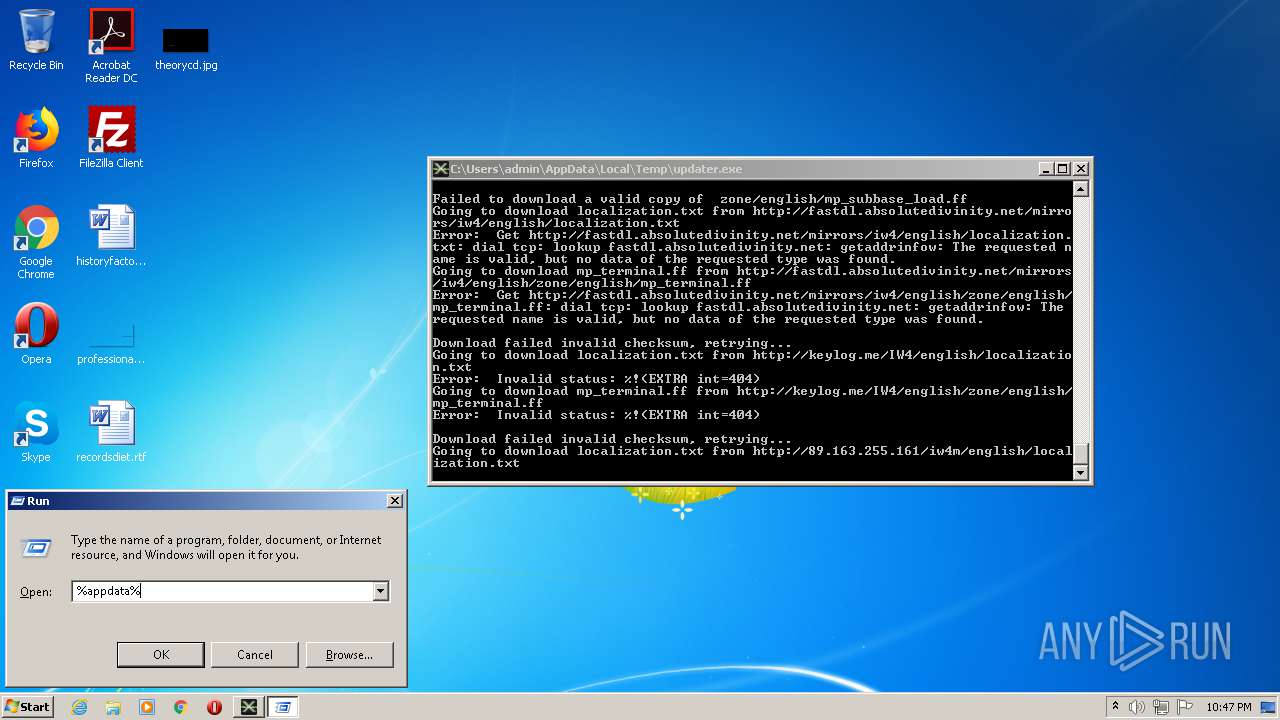
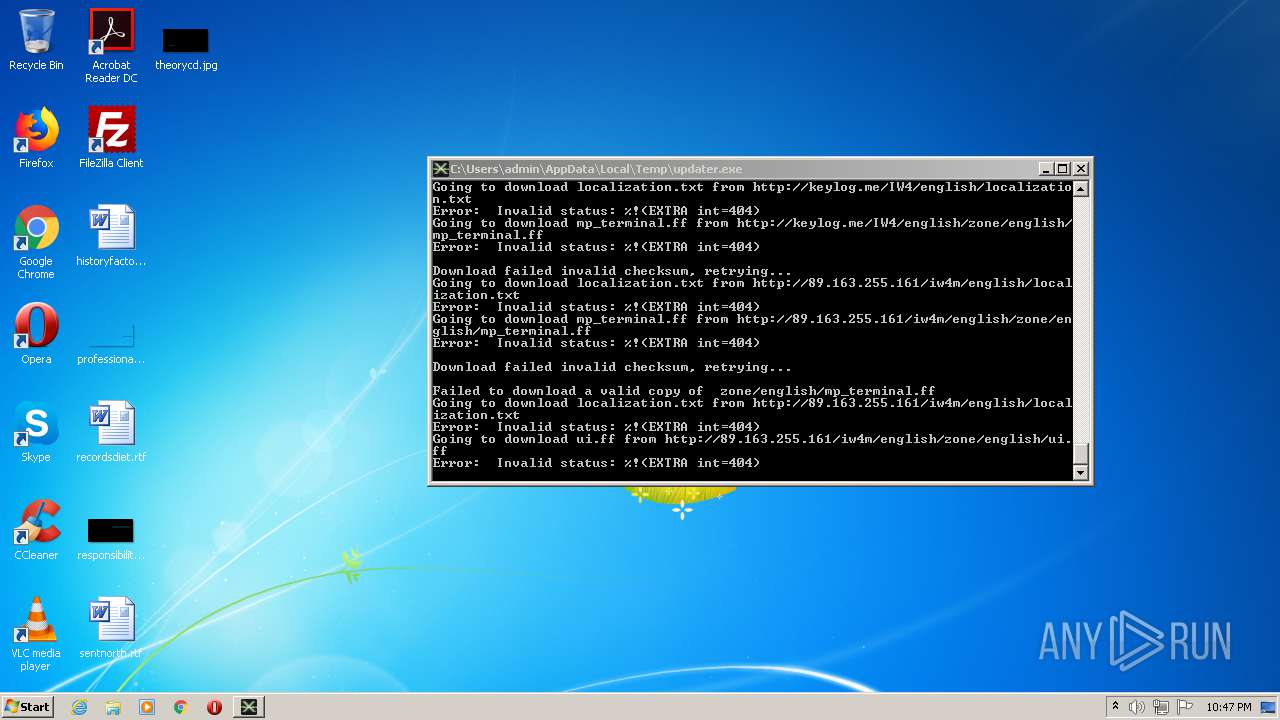
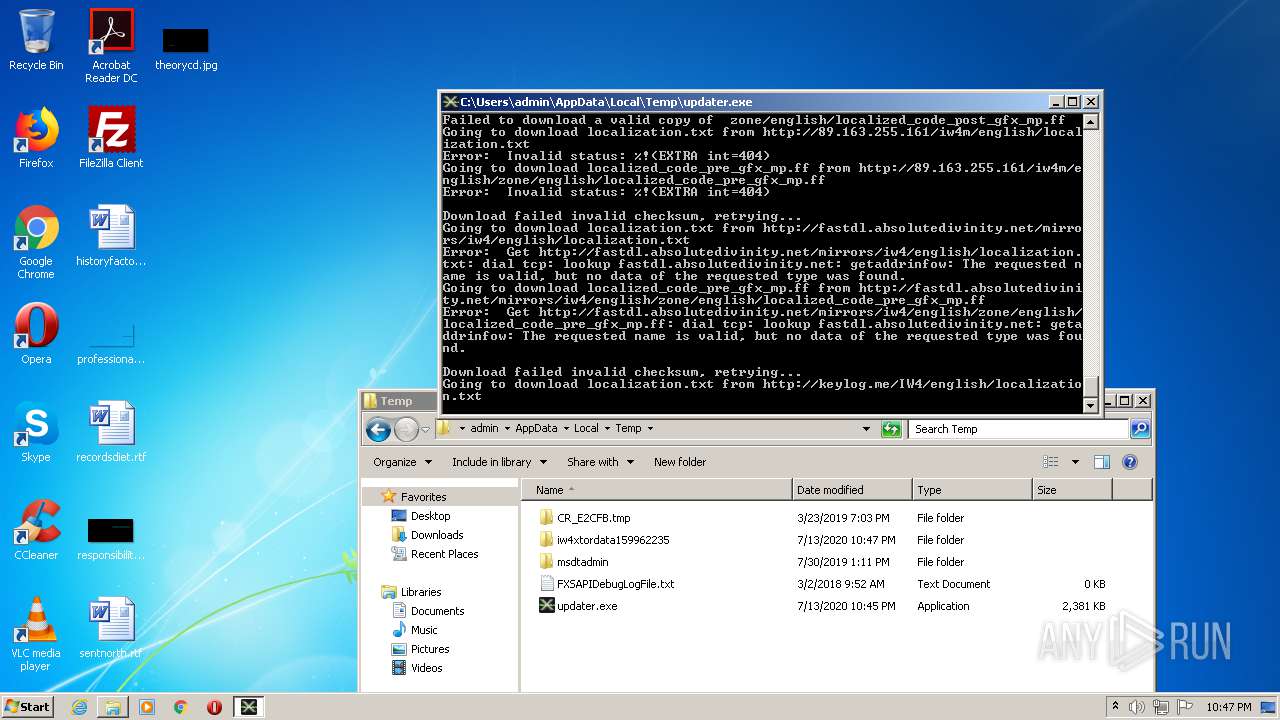
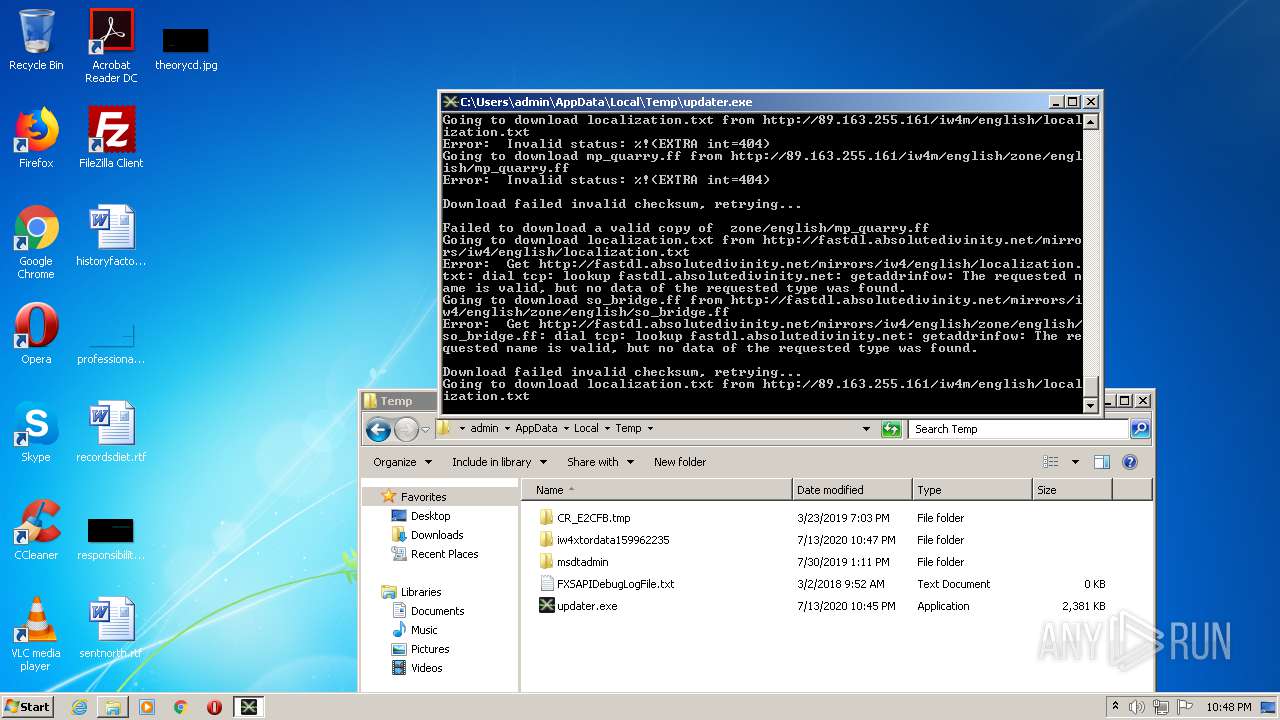
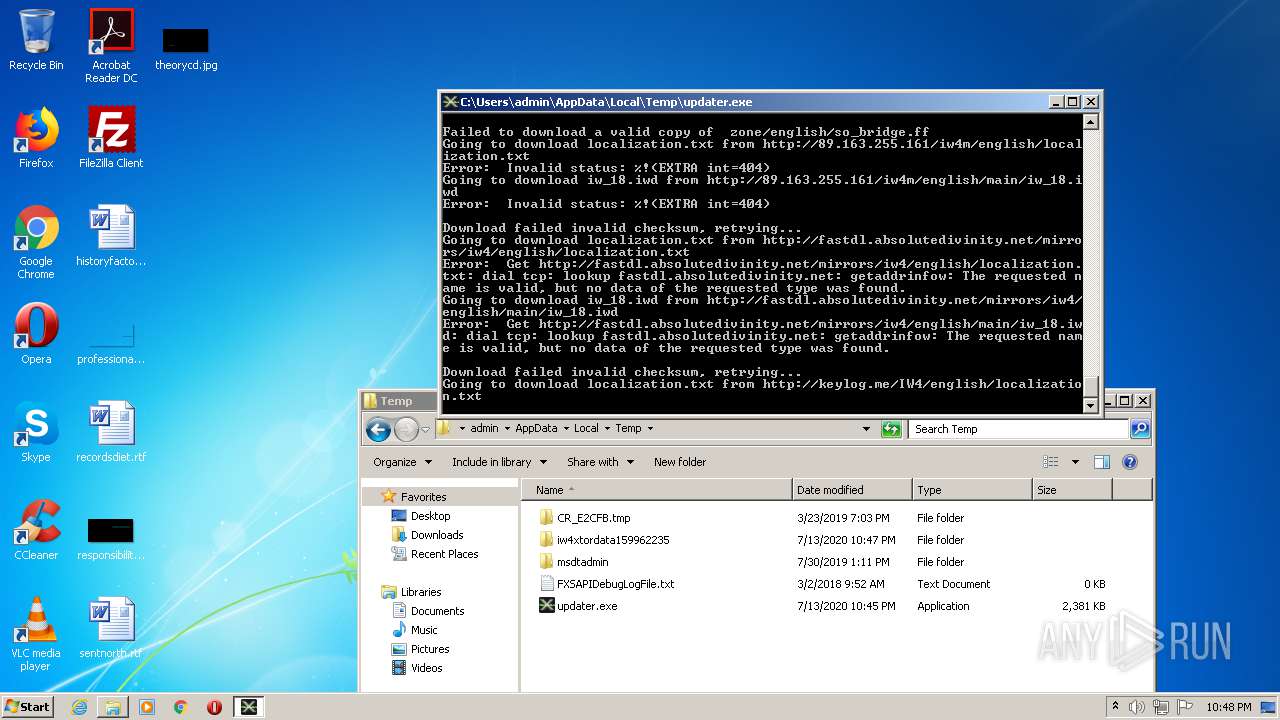
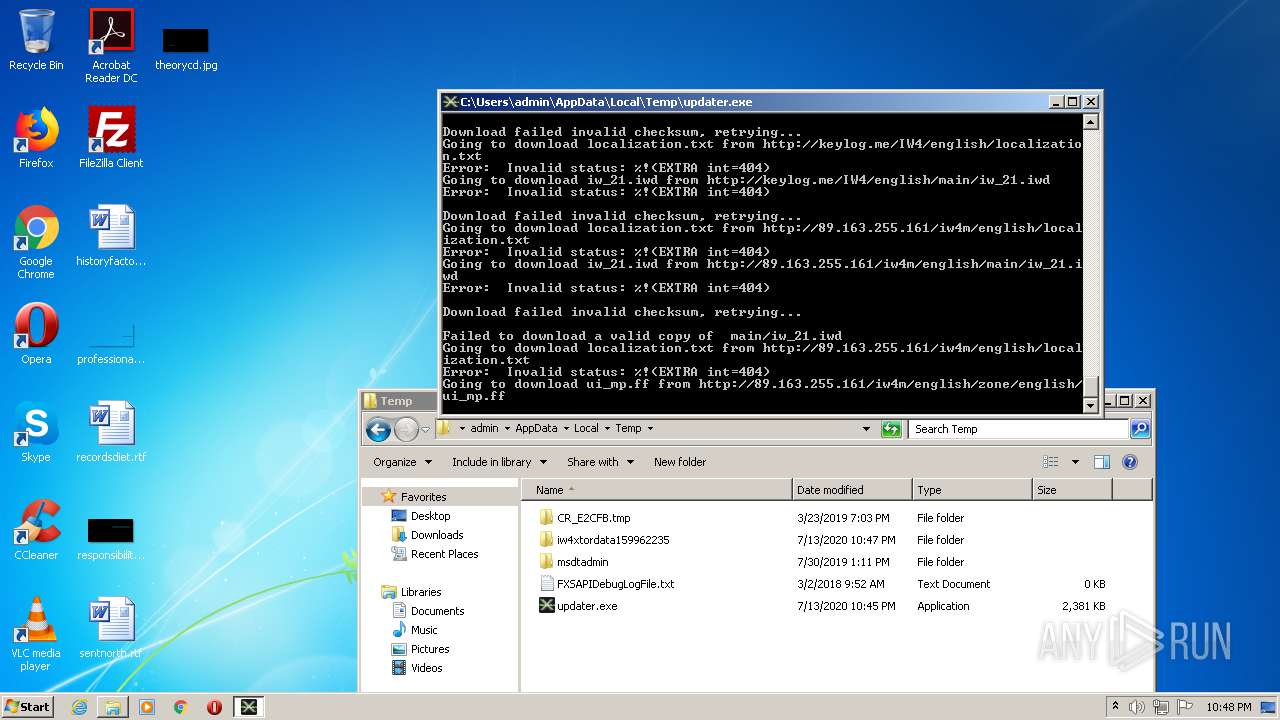
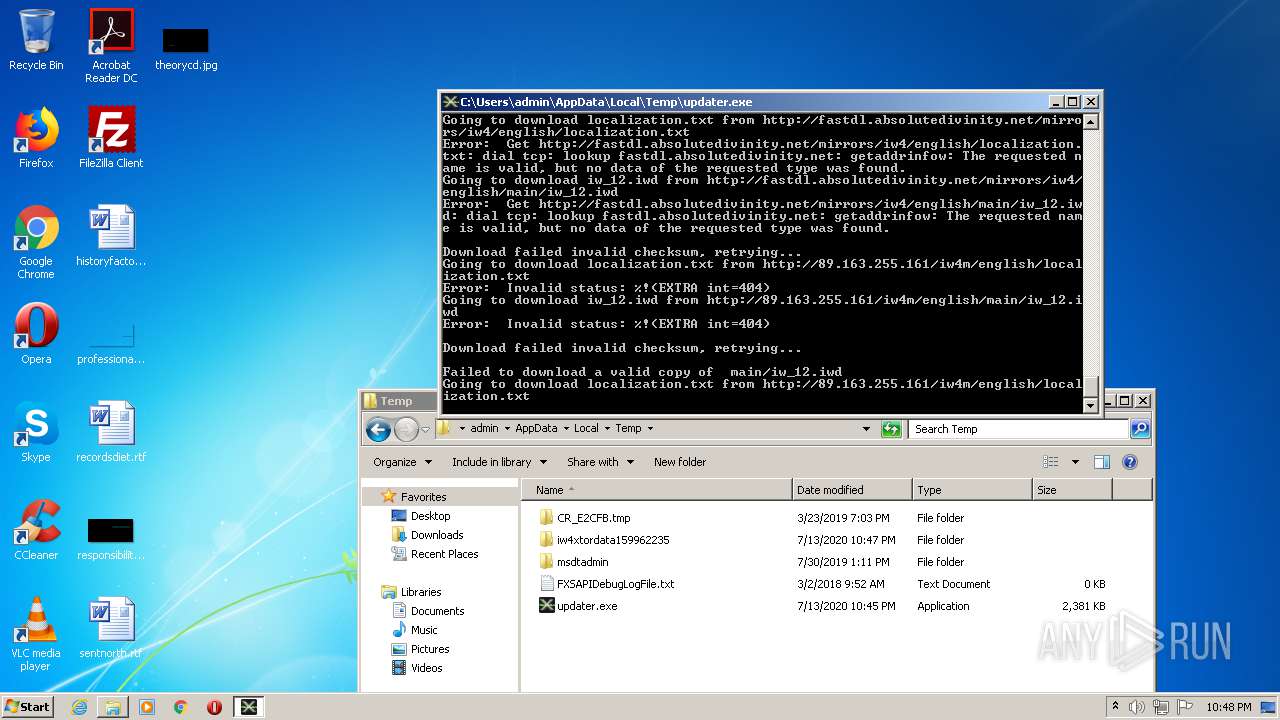
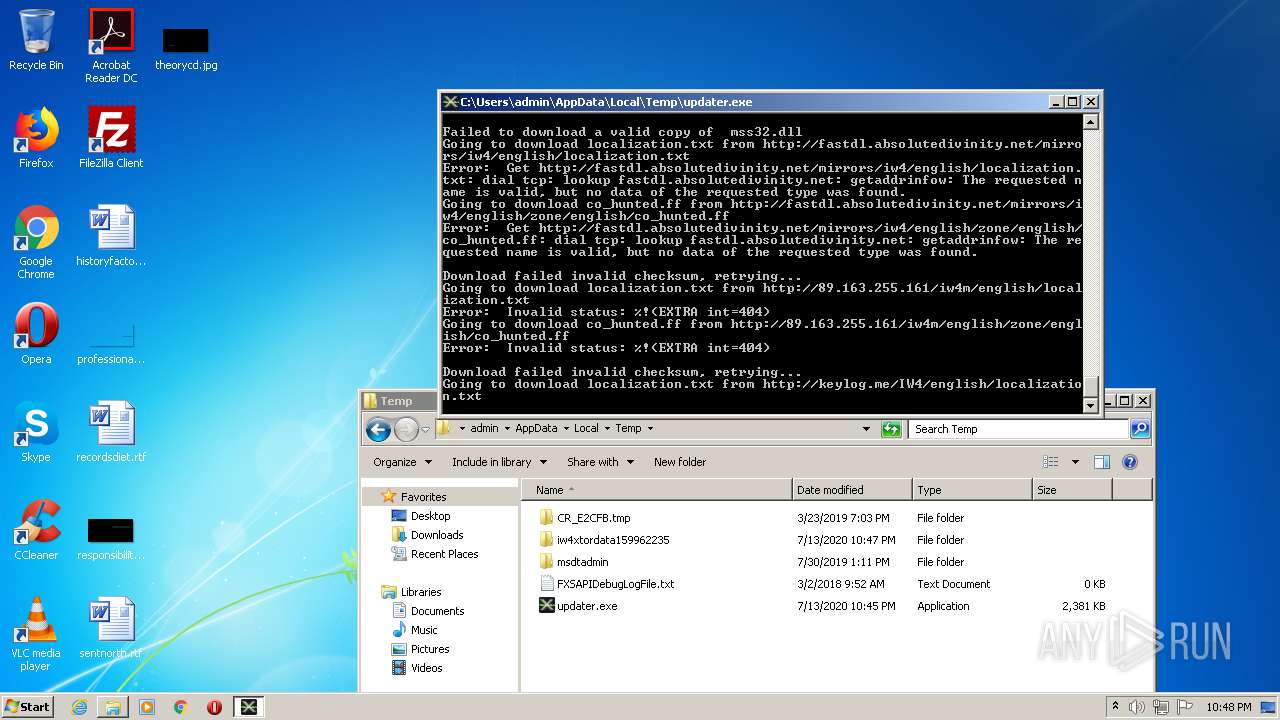
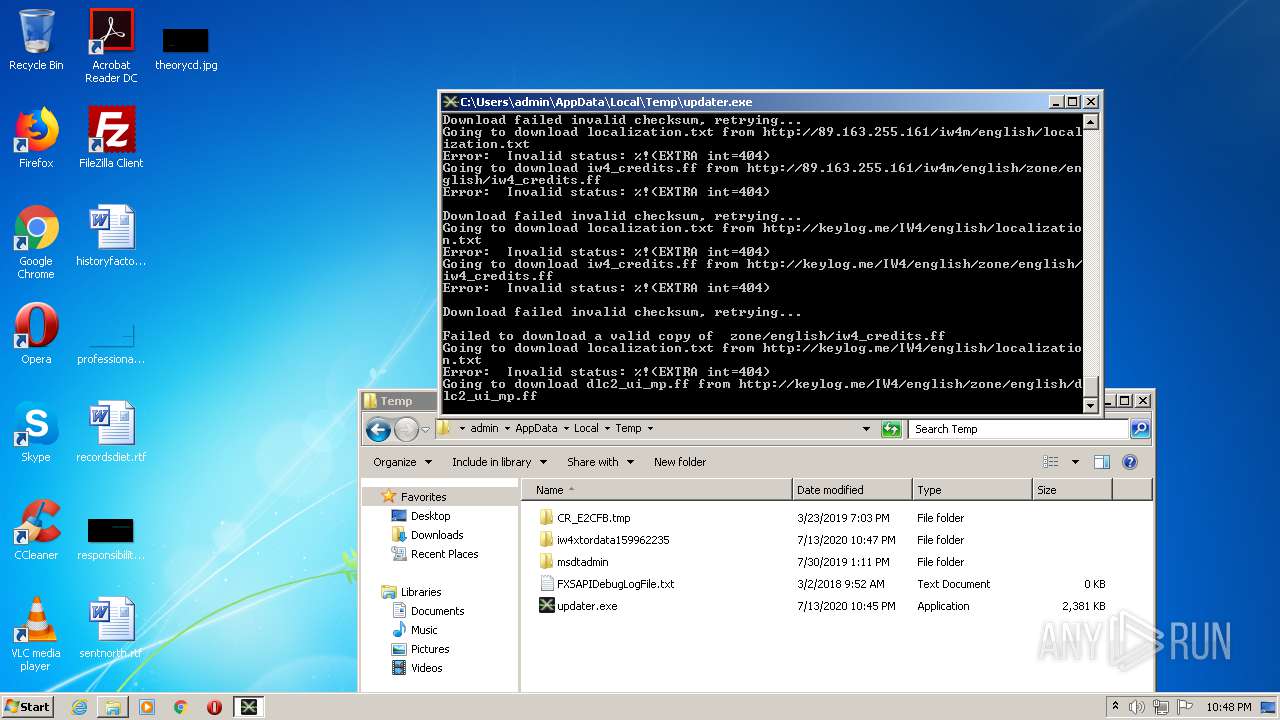
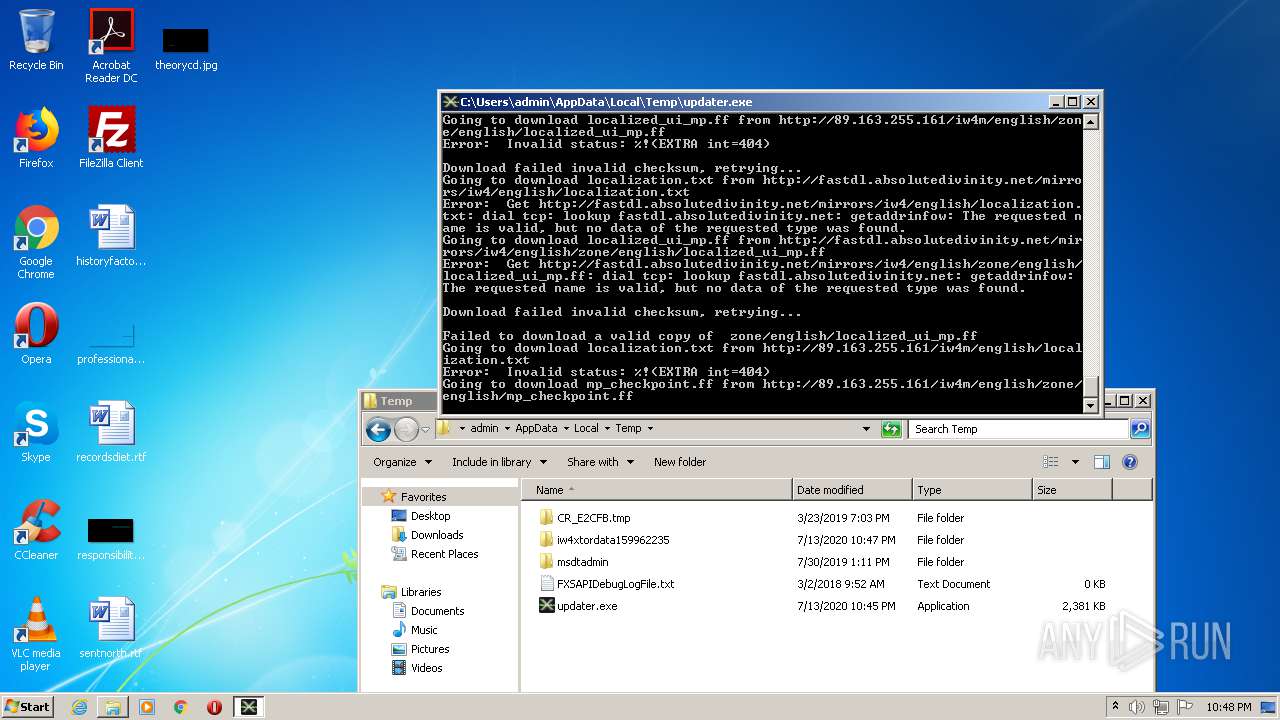
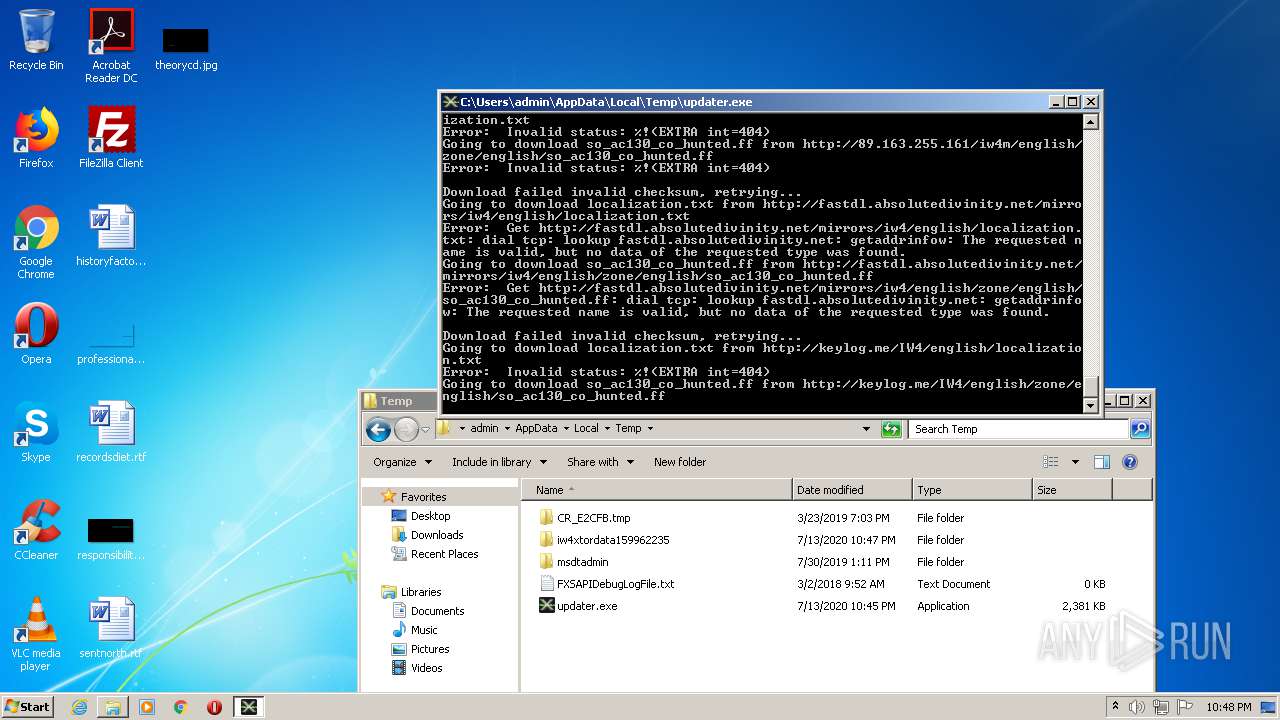
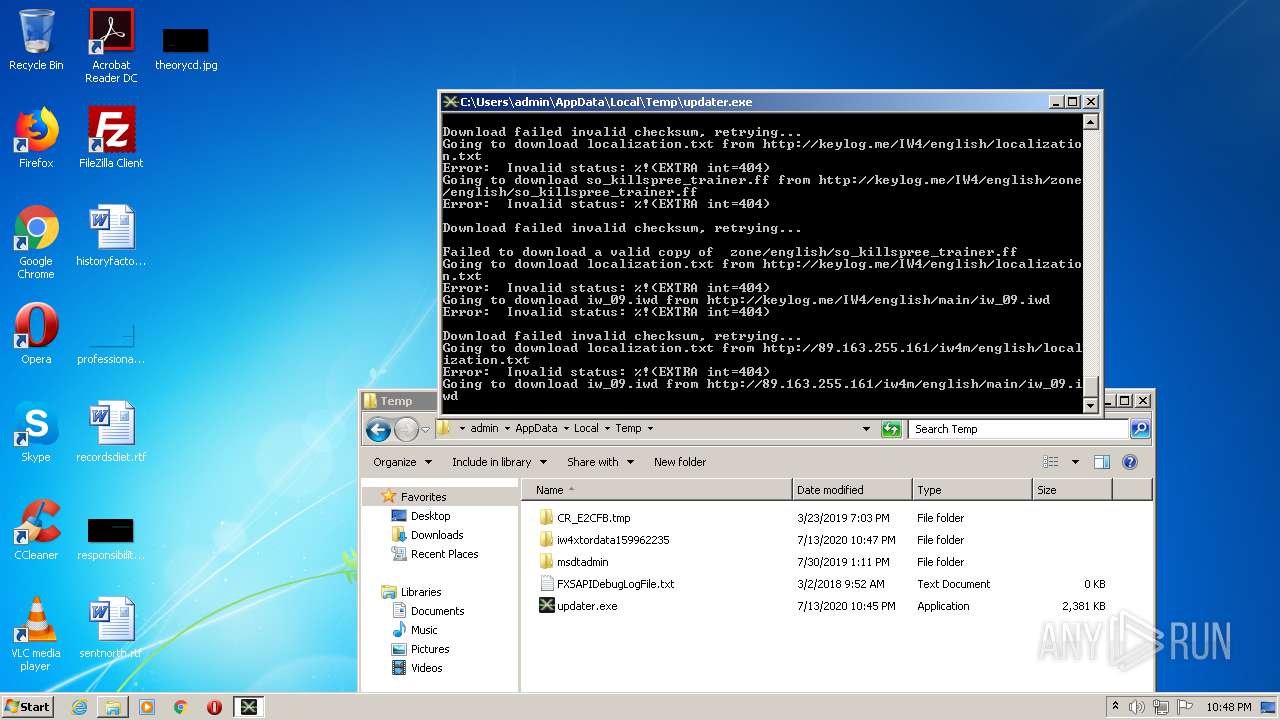
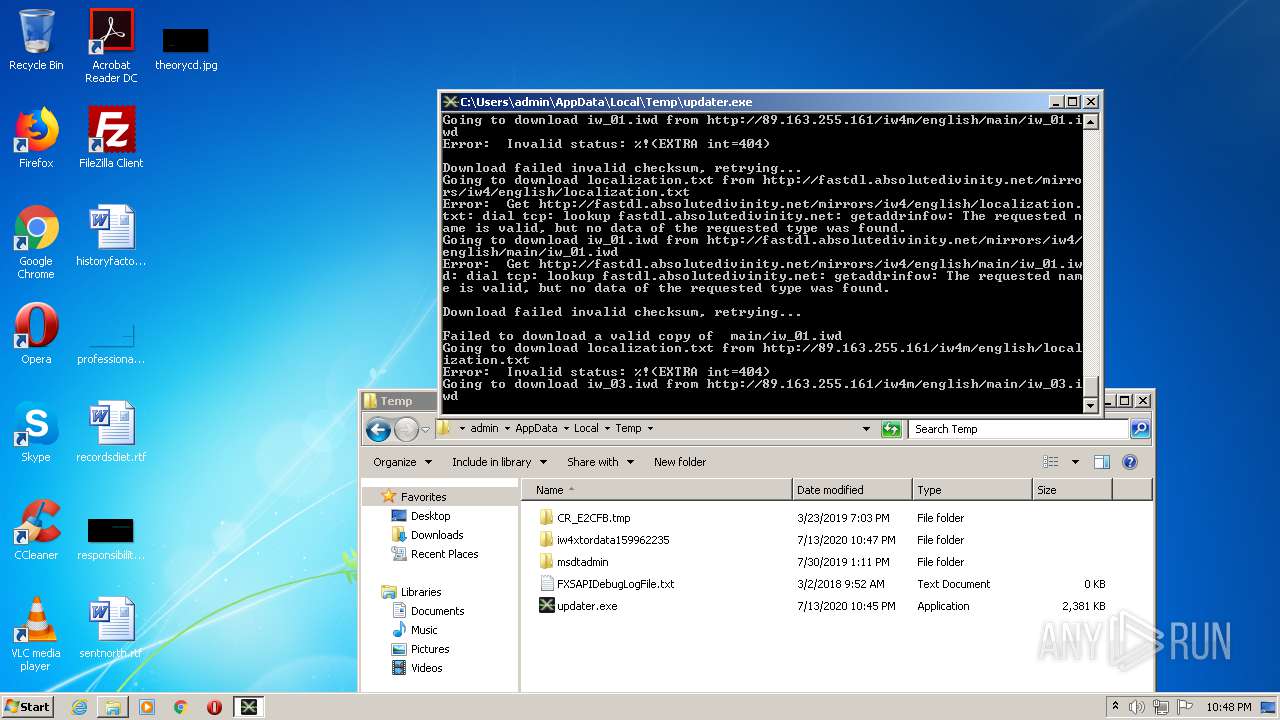
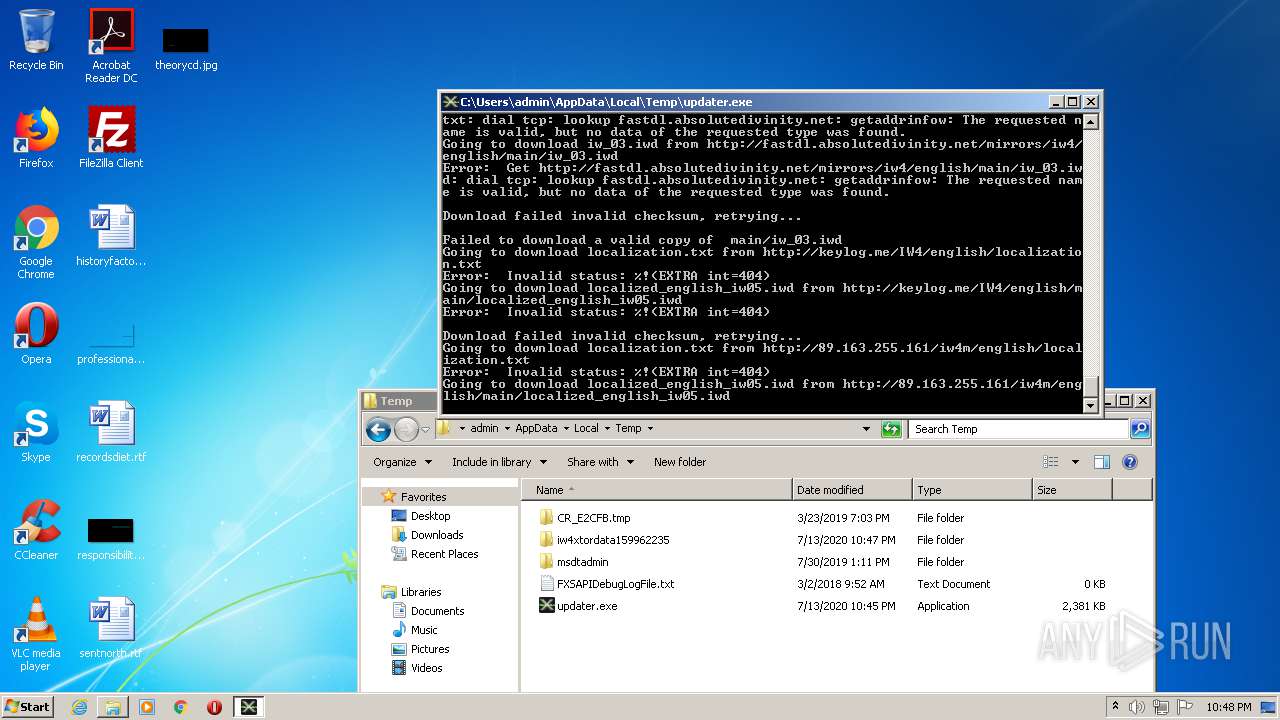
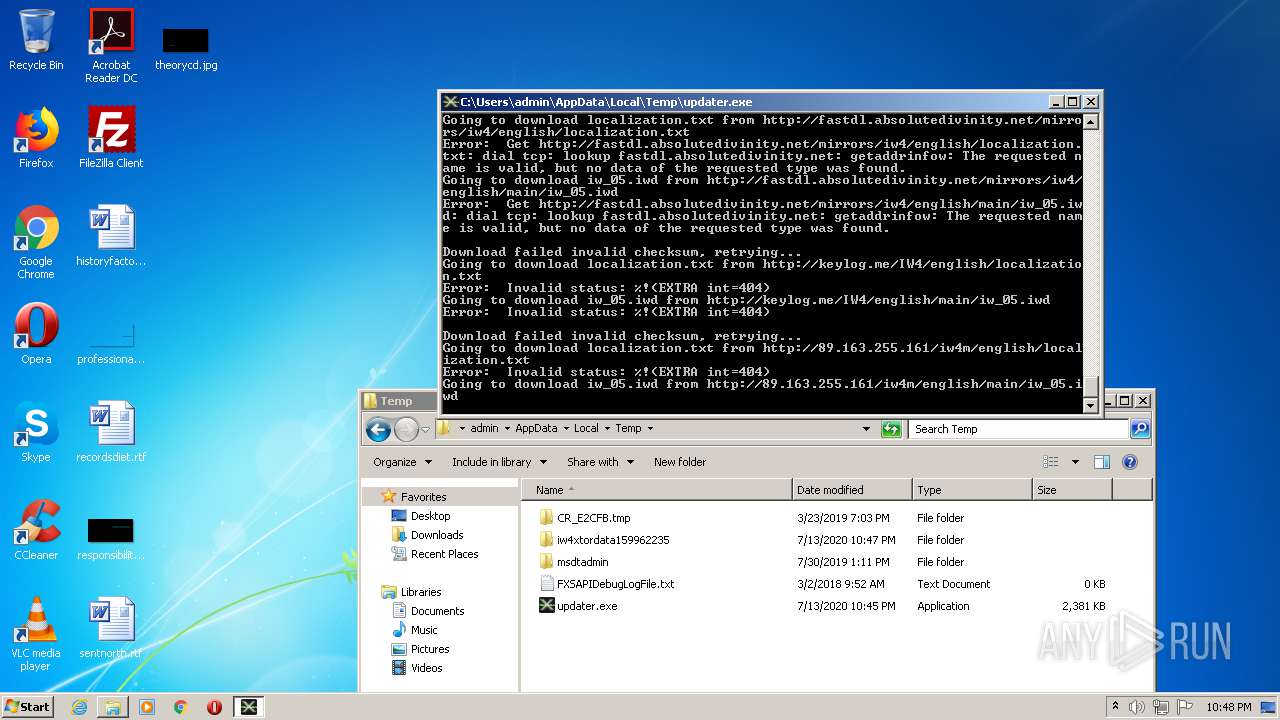
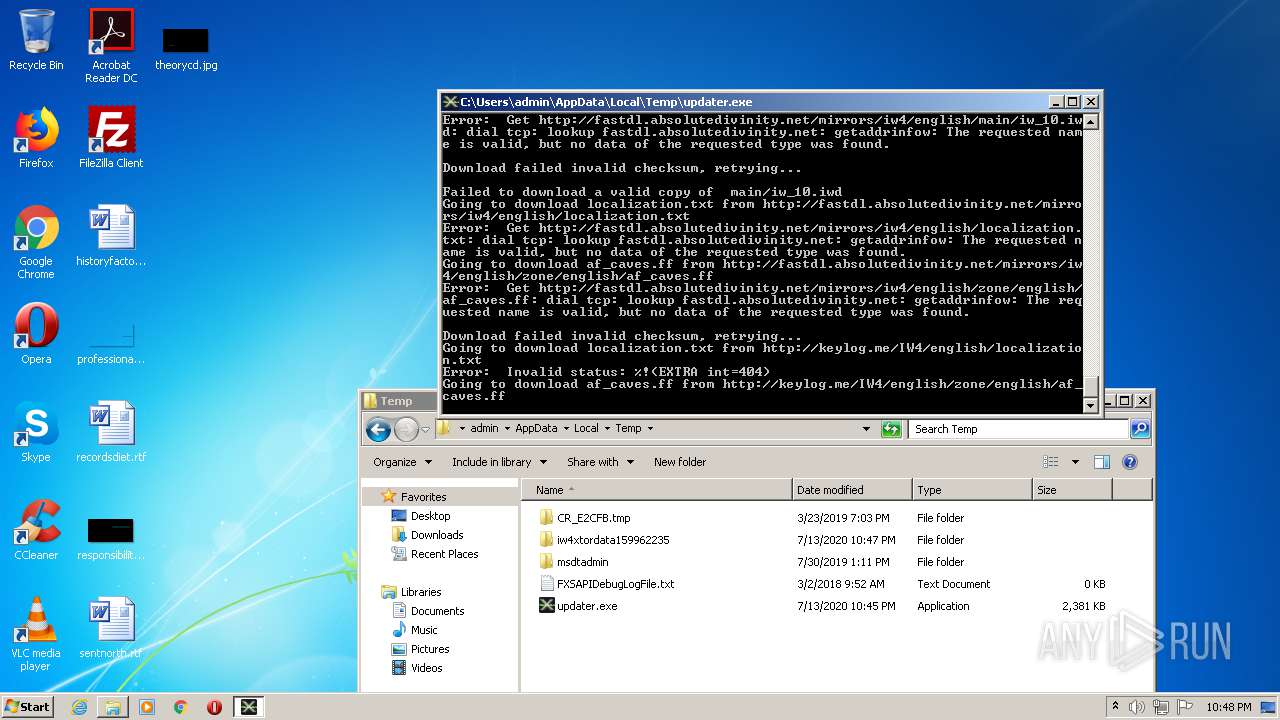
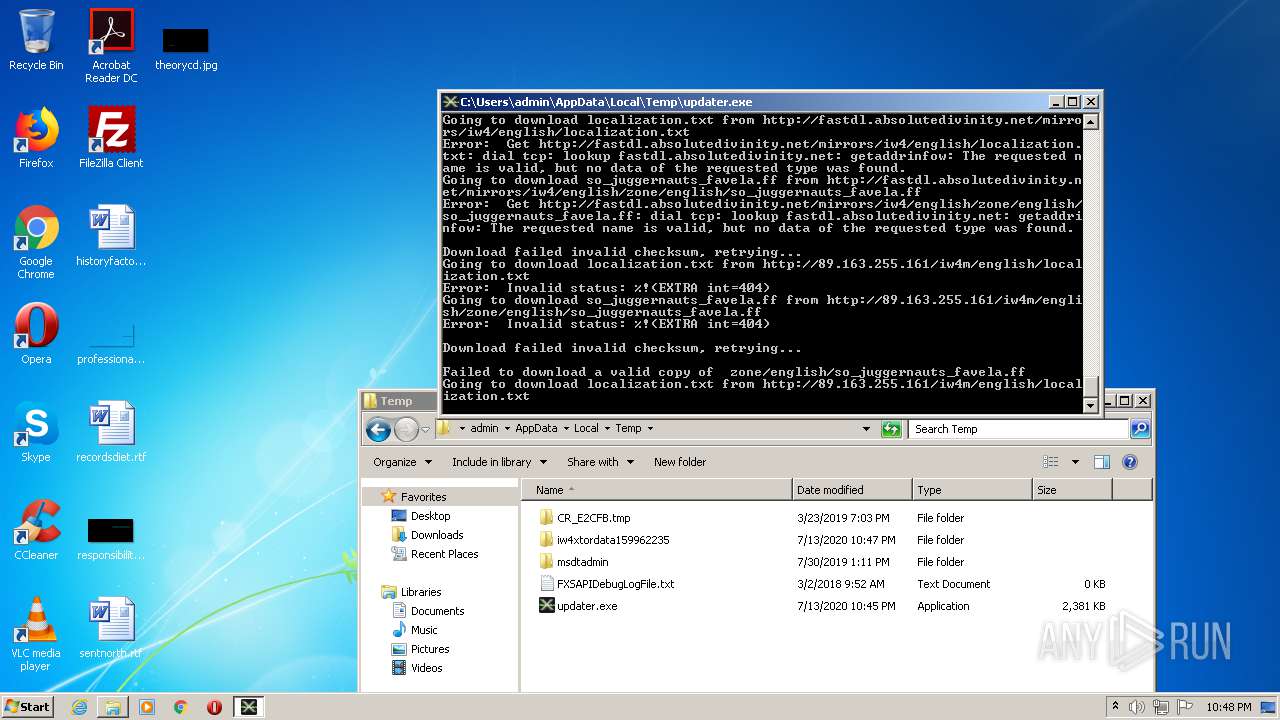
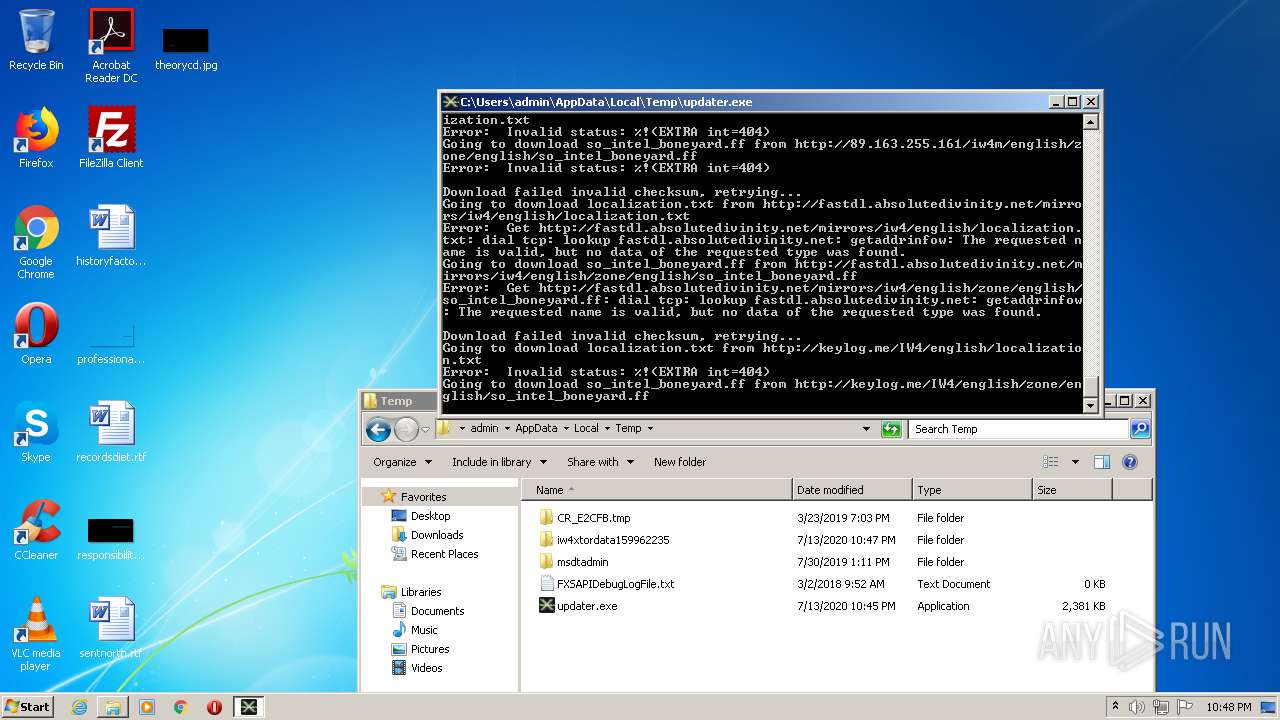
HTTP(S) requests
537
TCP/UDP connections
553
DNS requests
3
Threats
556
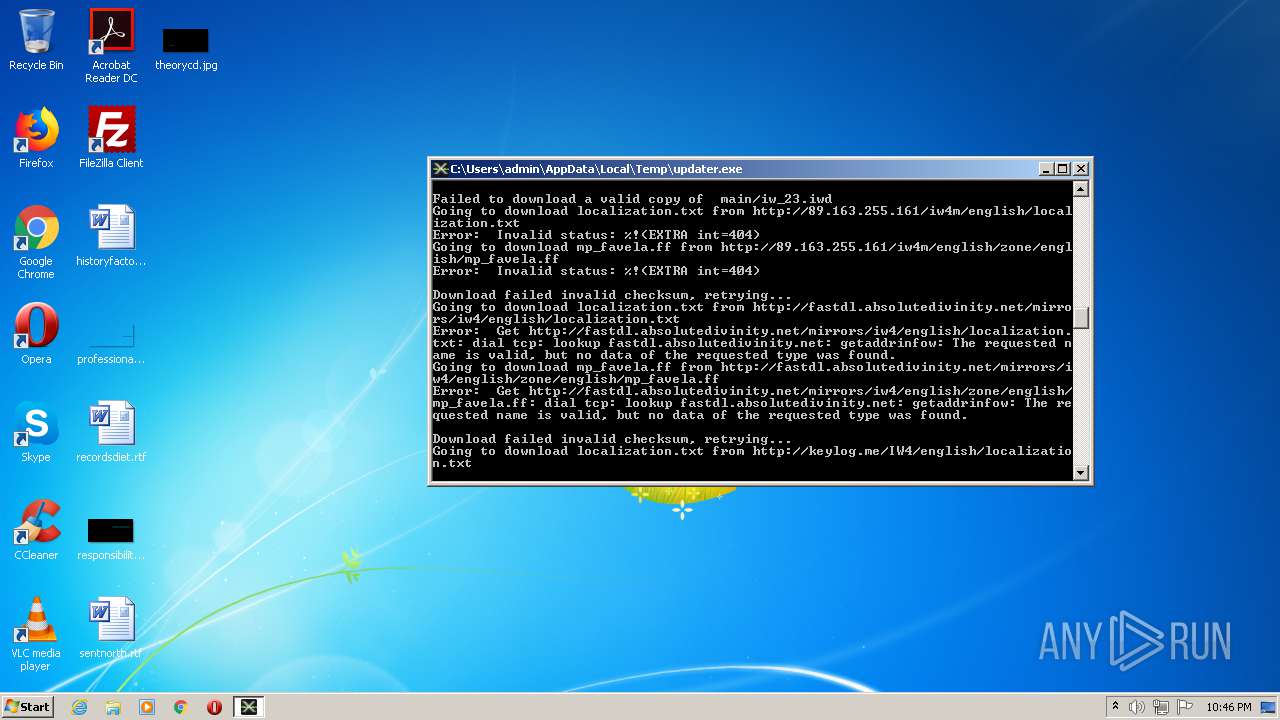
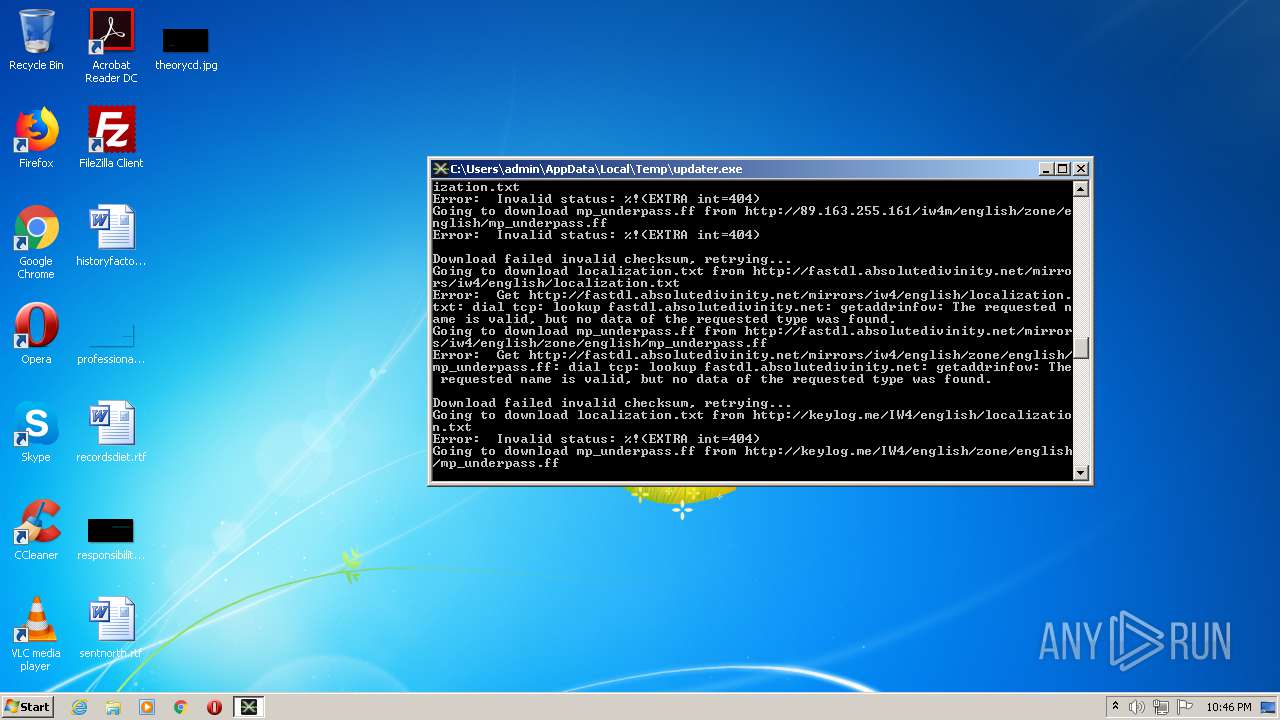
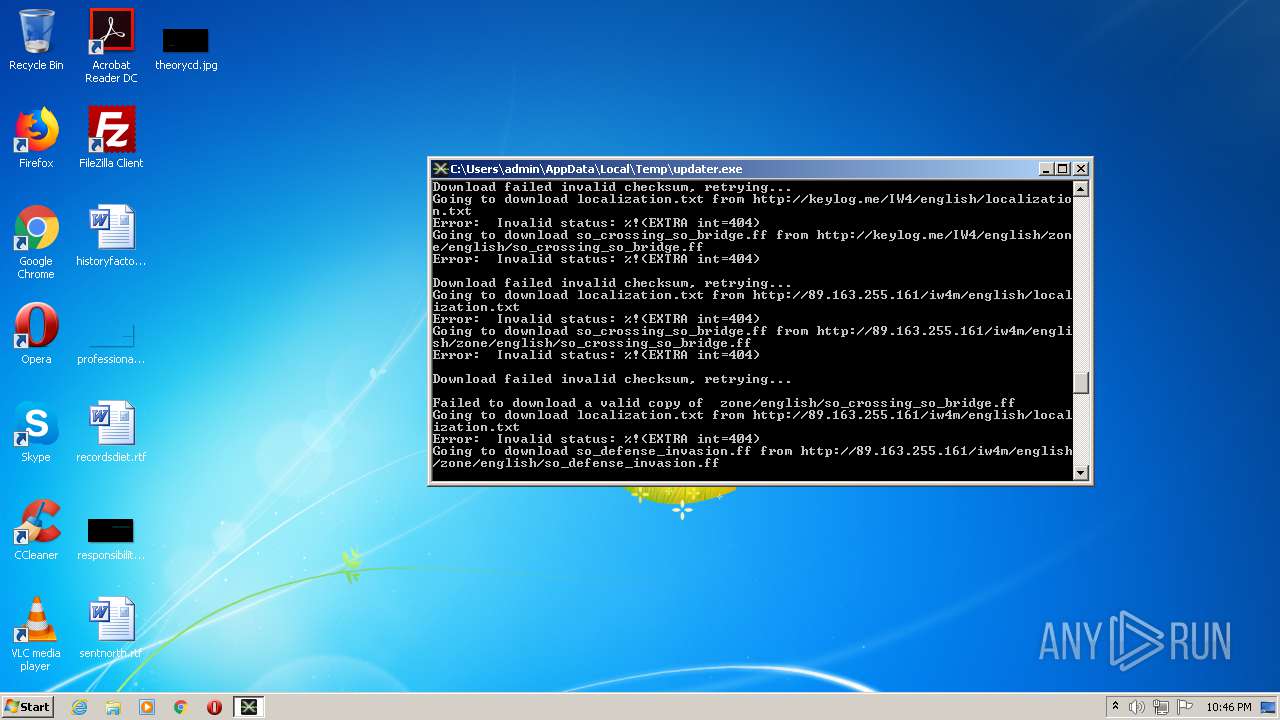
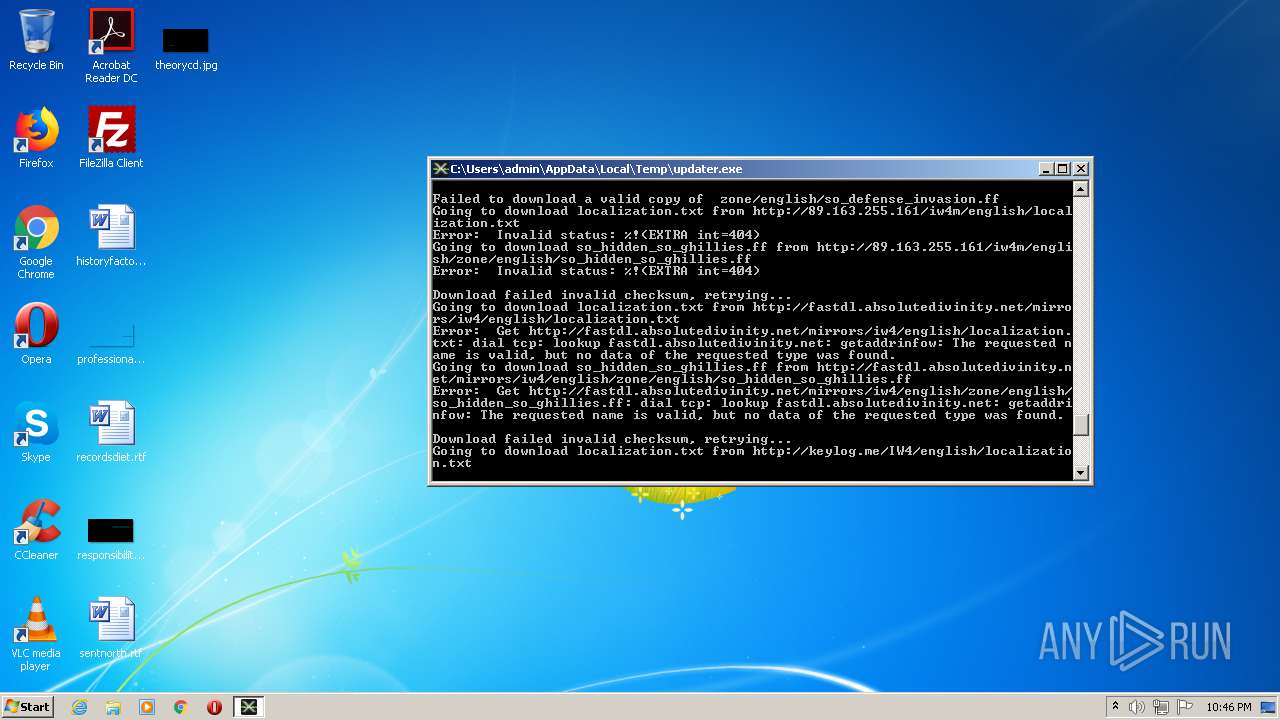
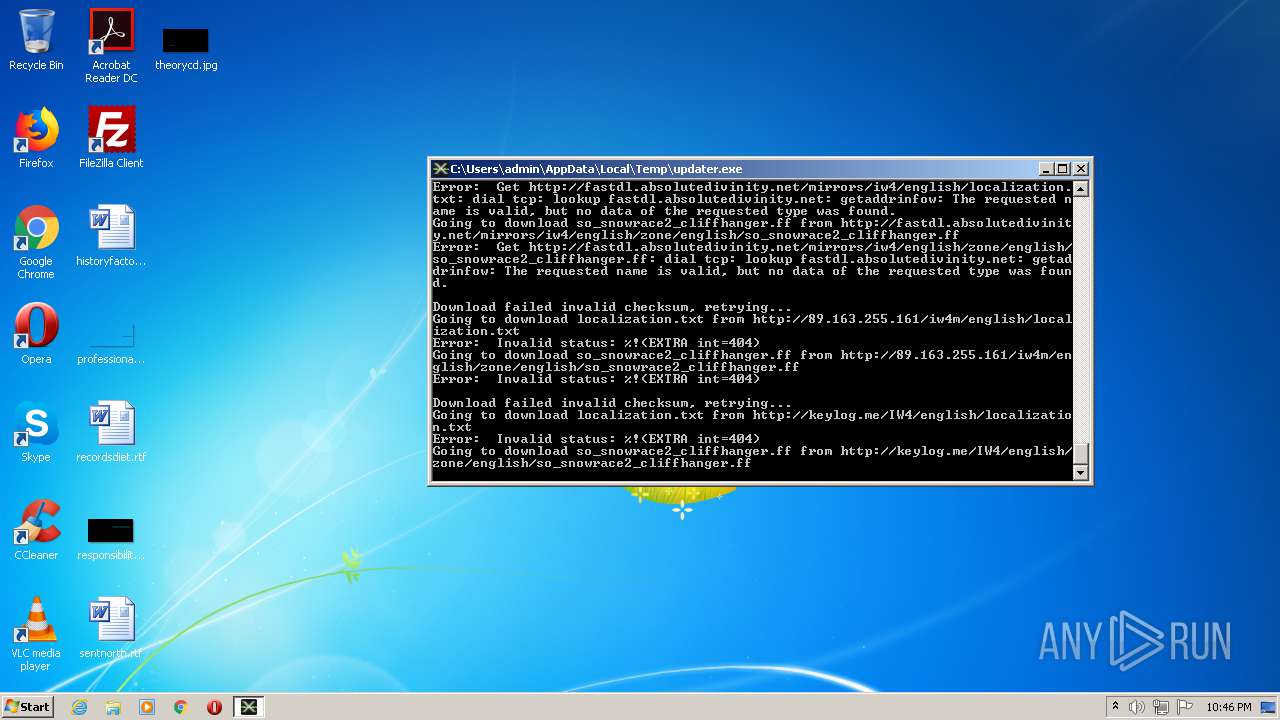
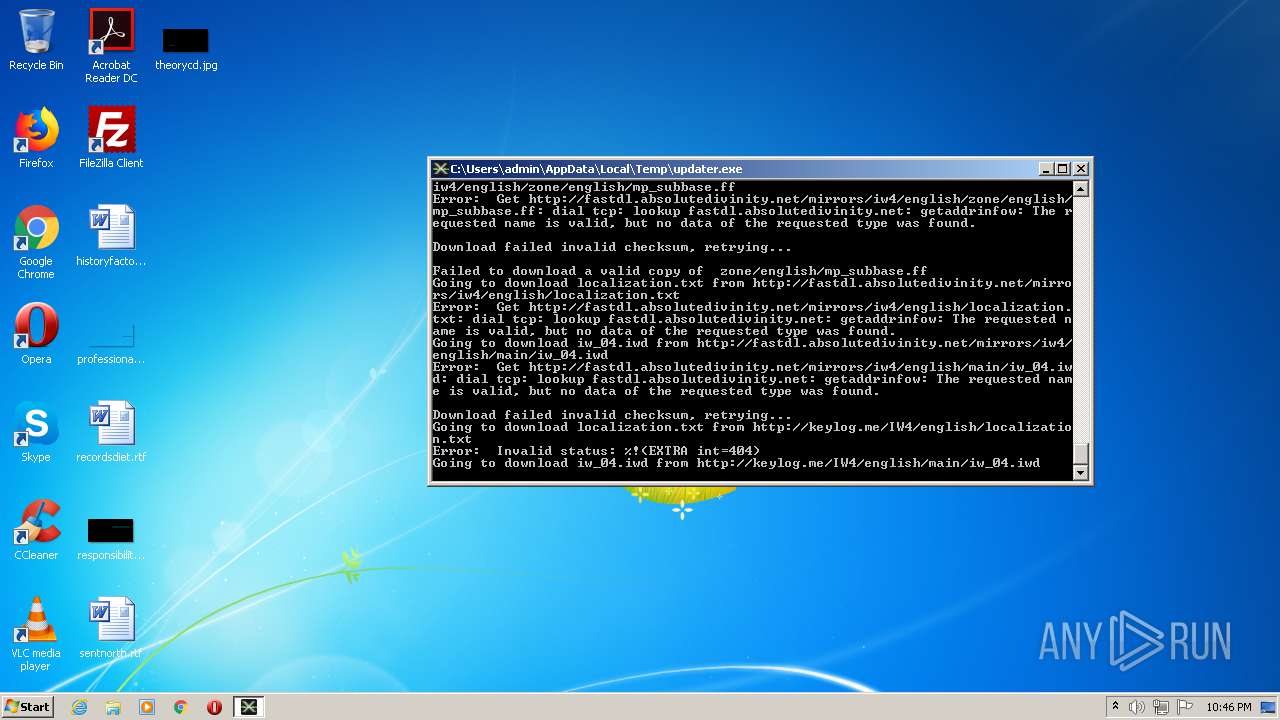
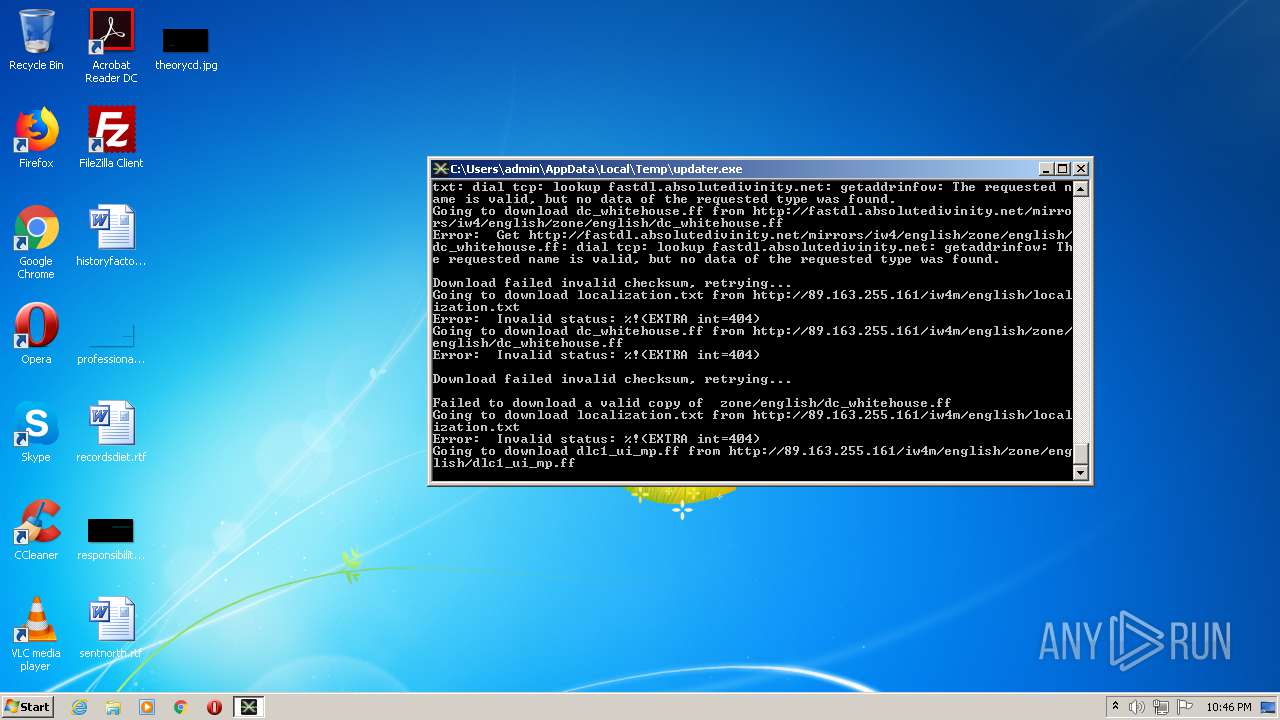
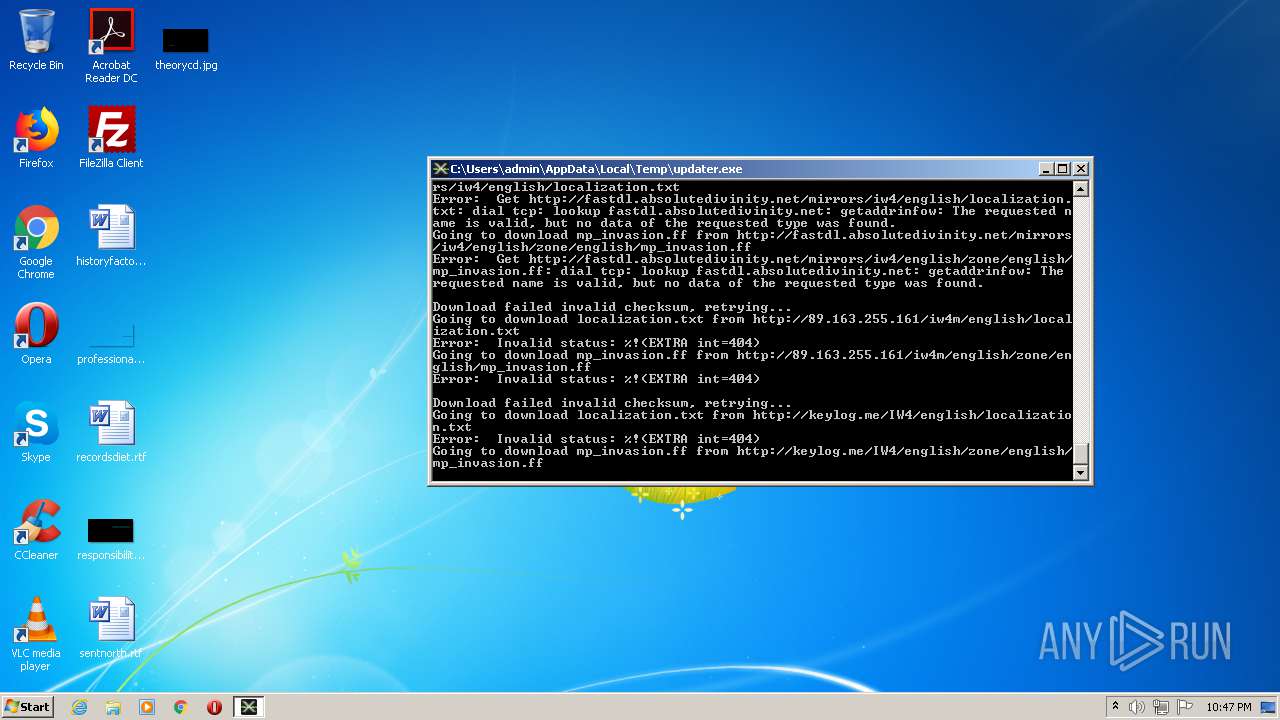
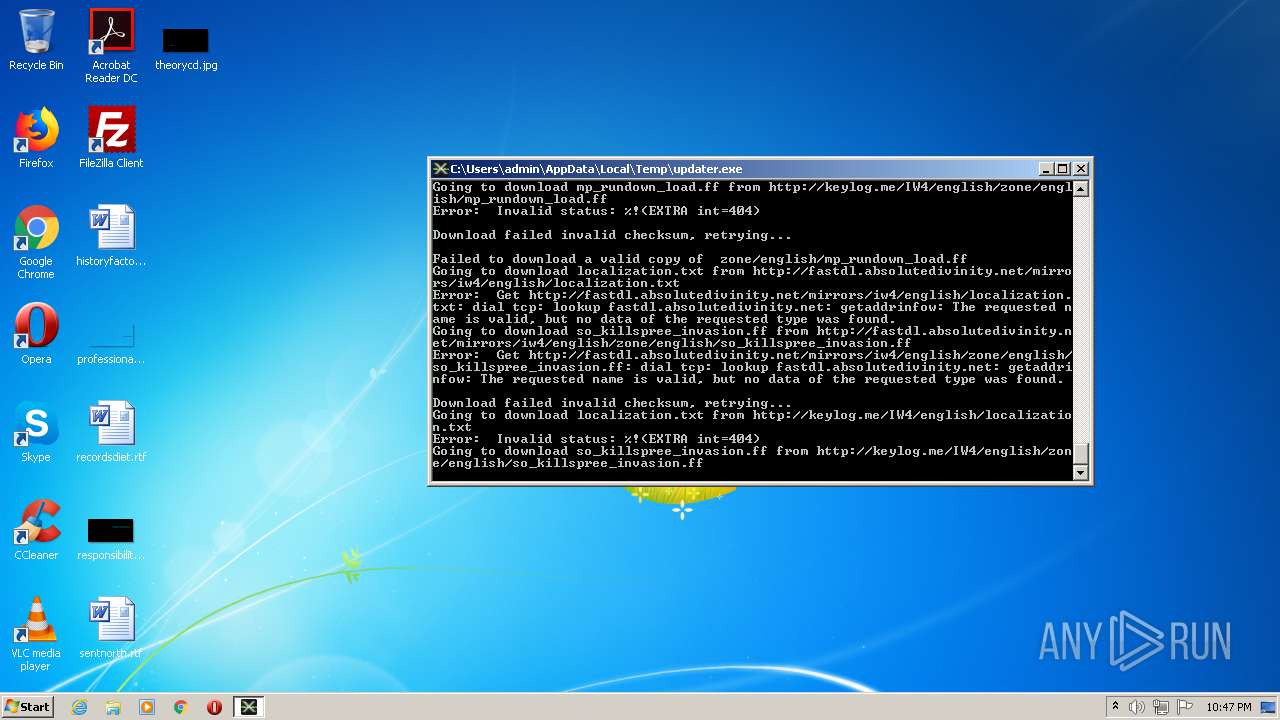
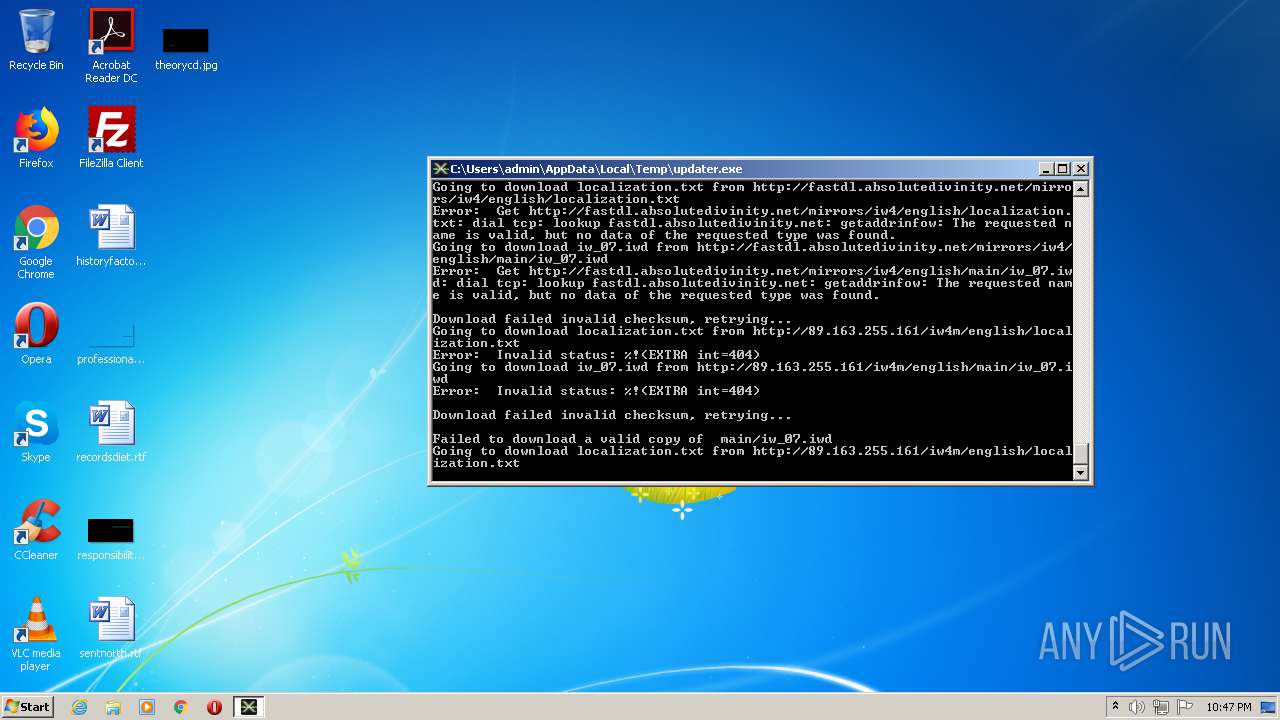
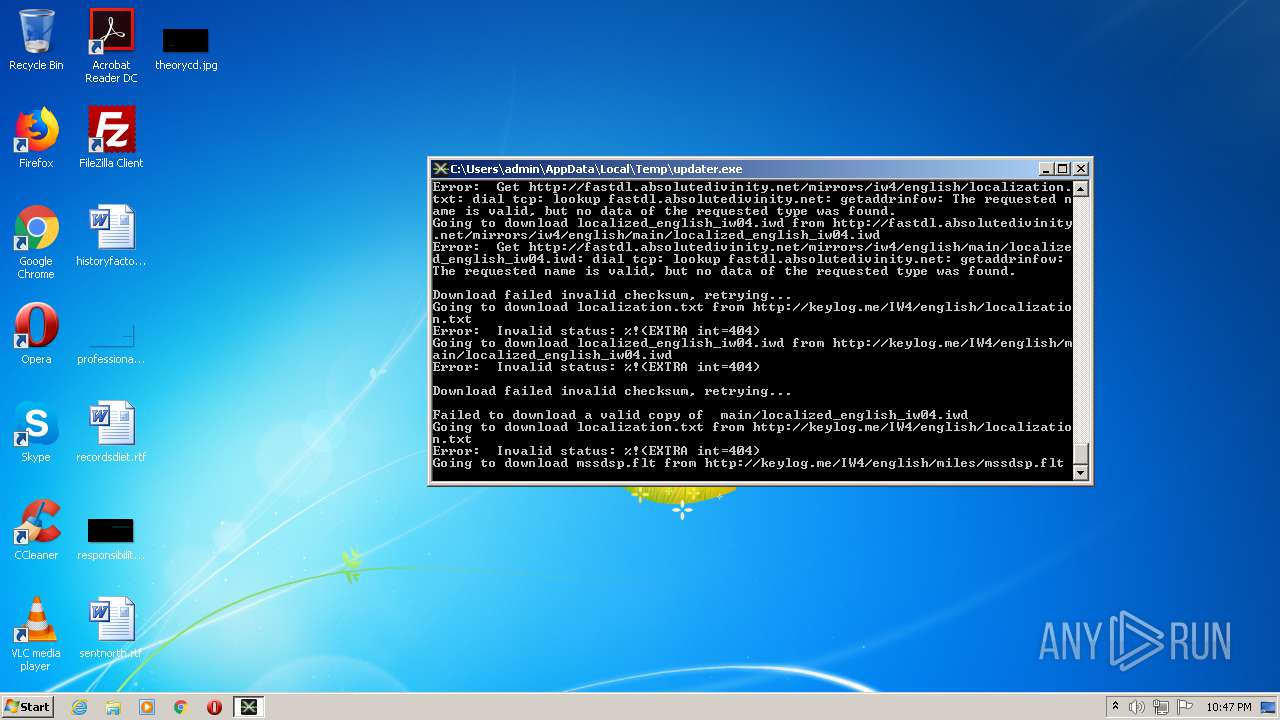
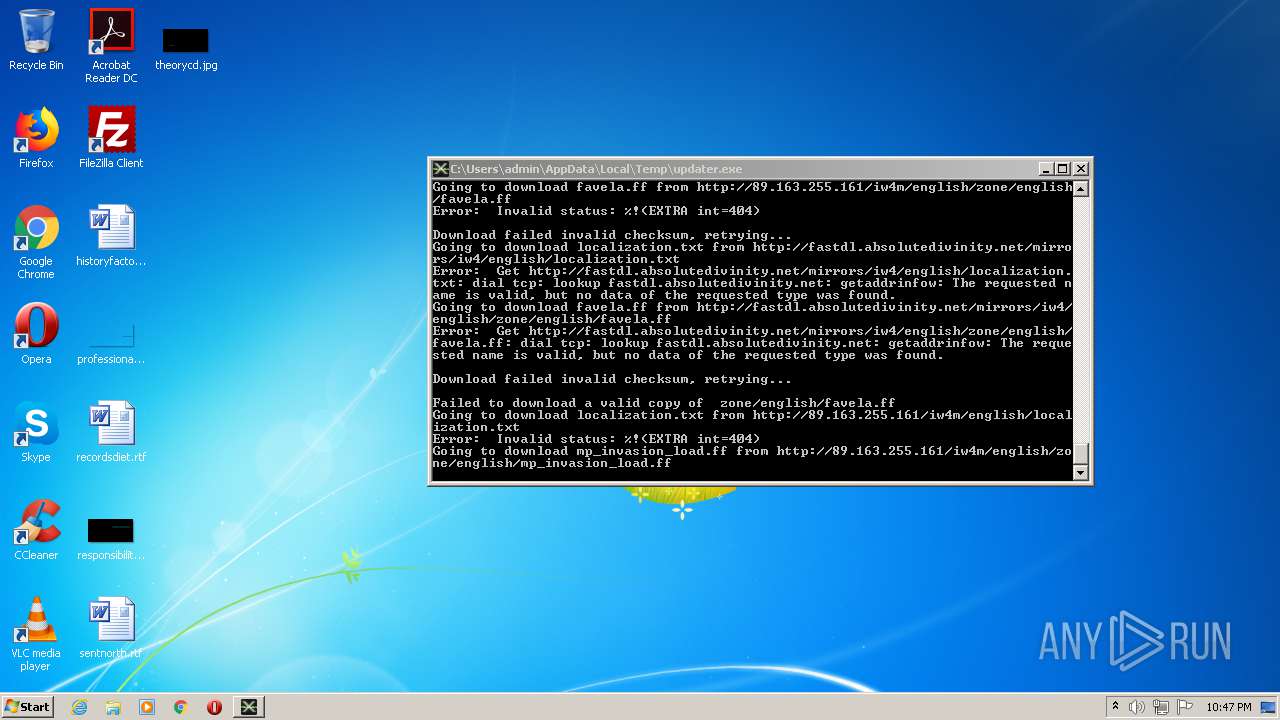
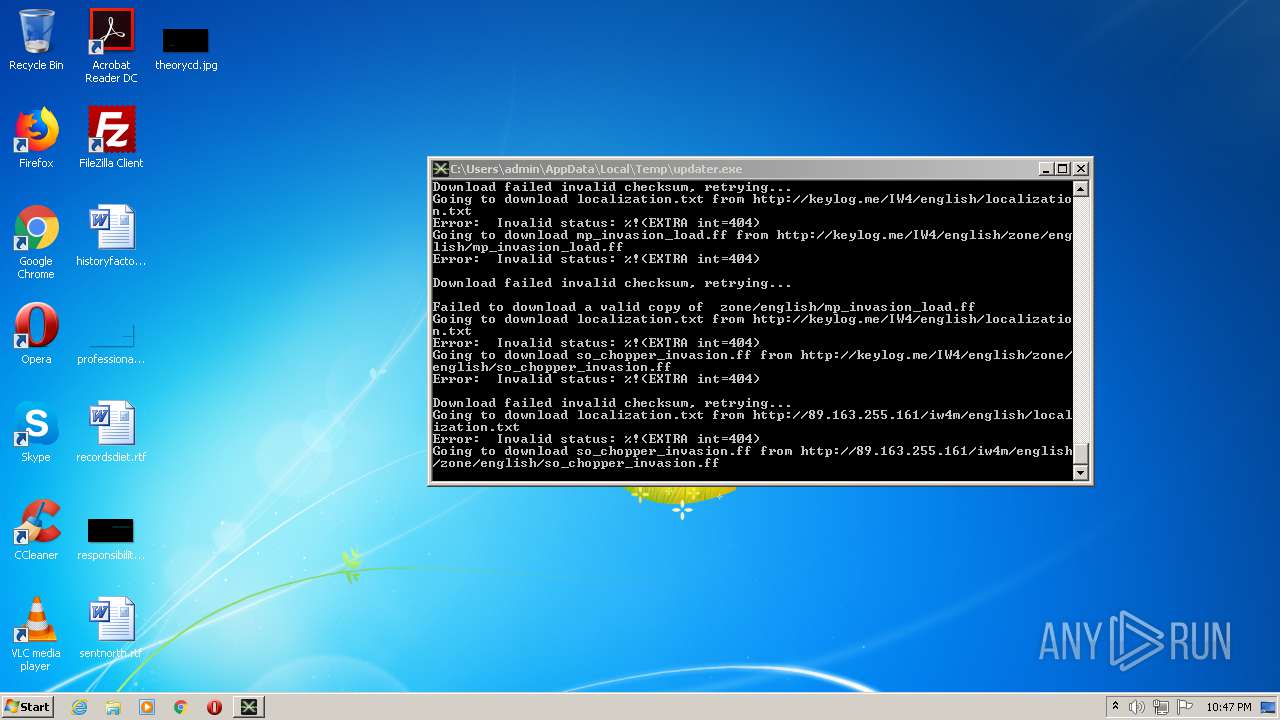
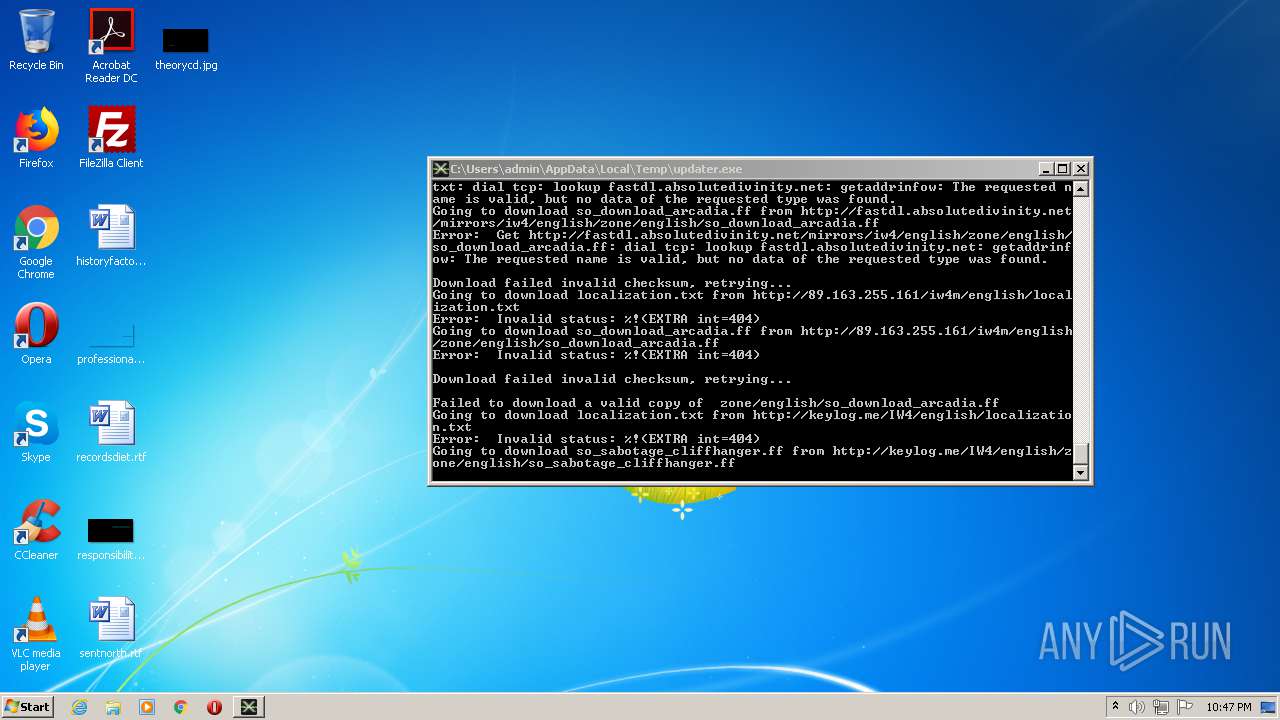
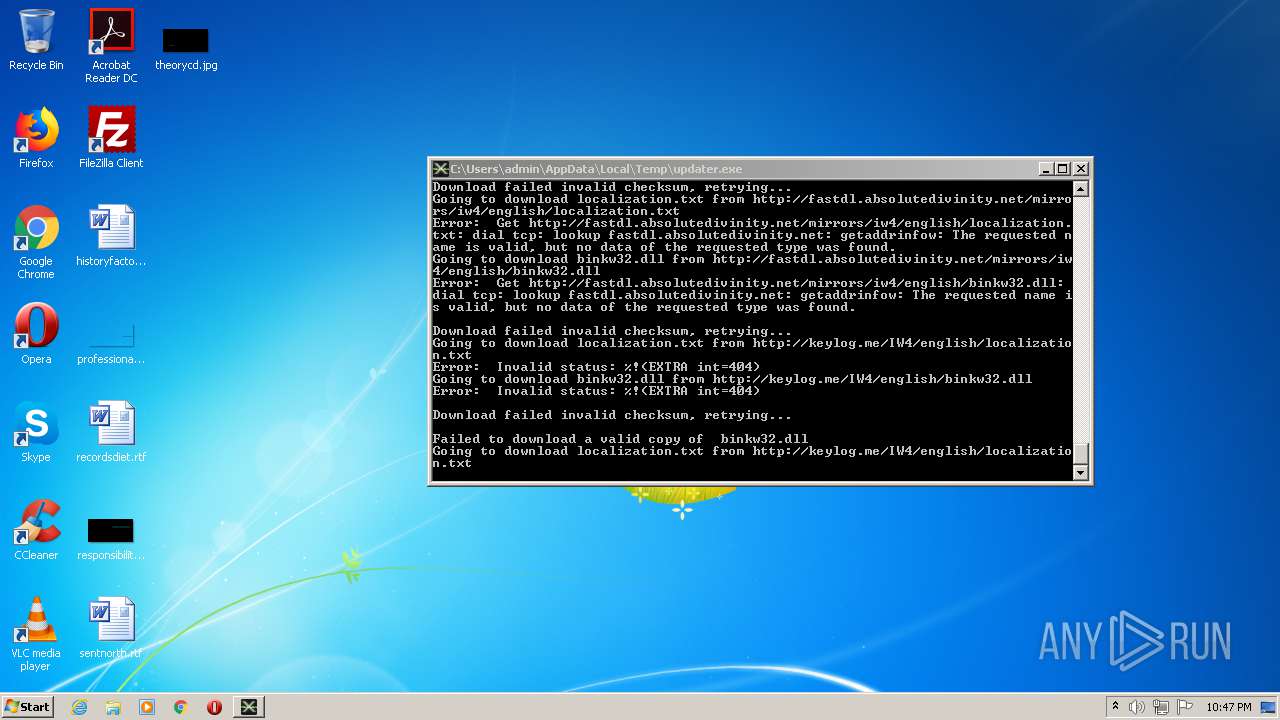
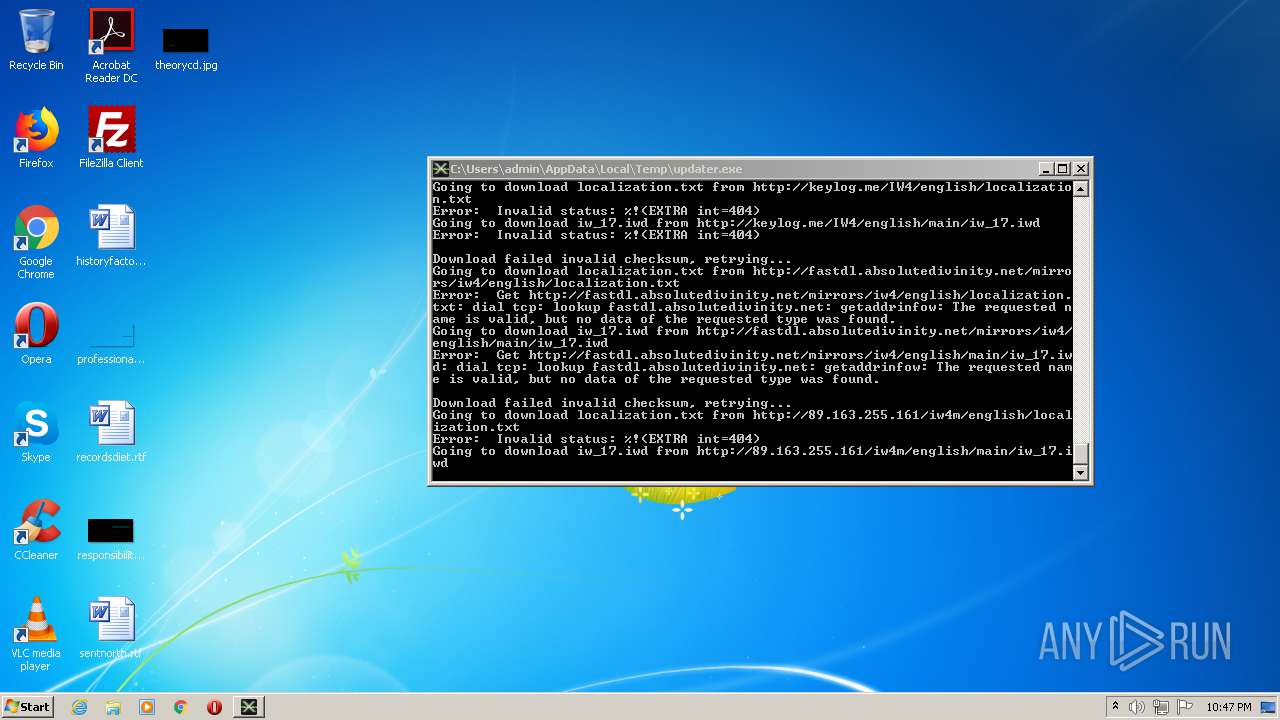
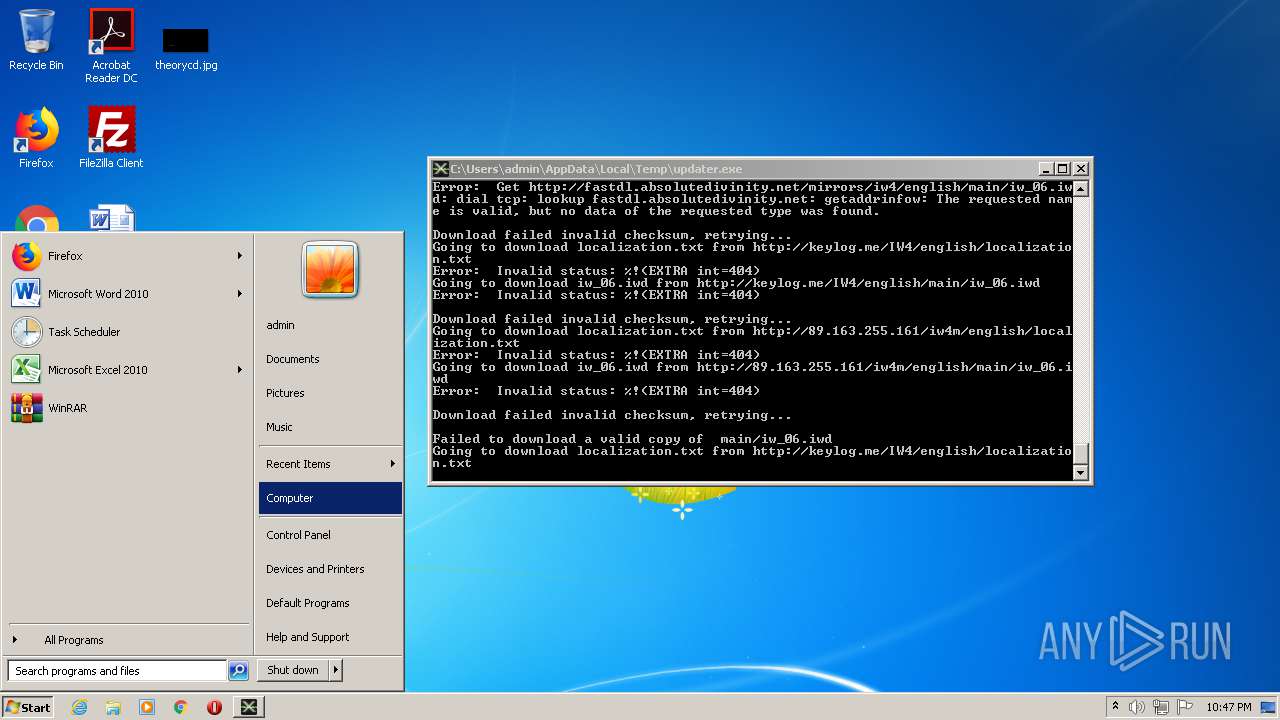
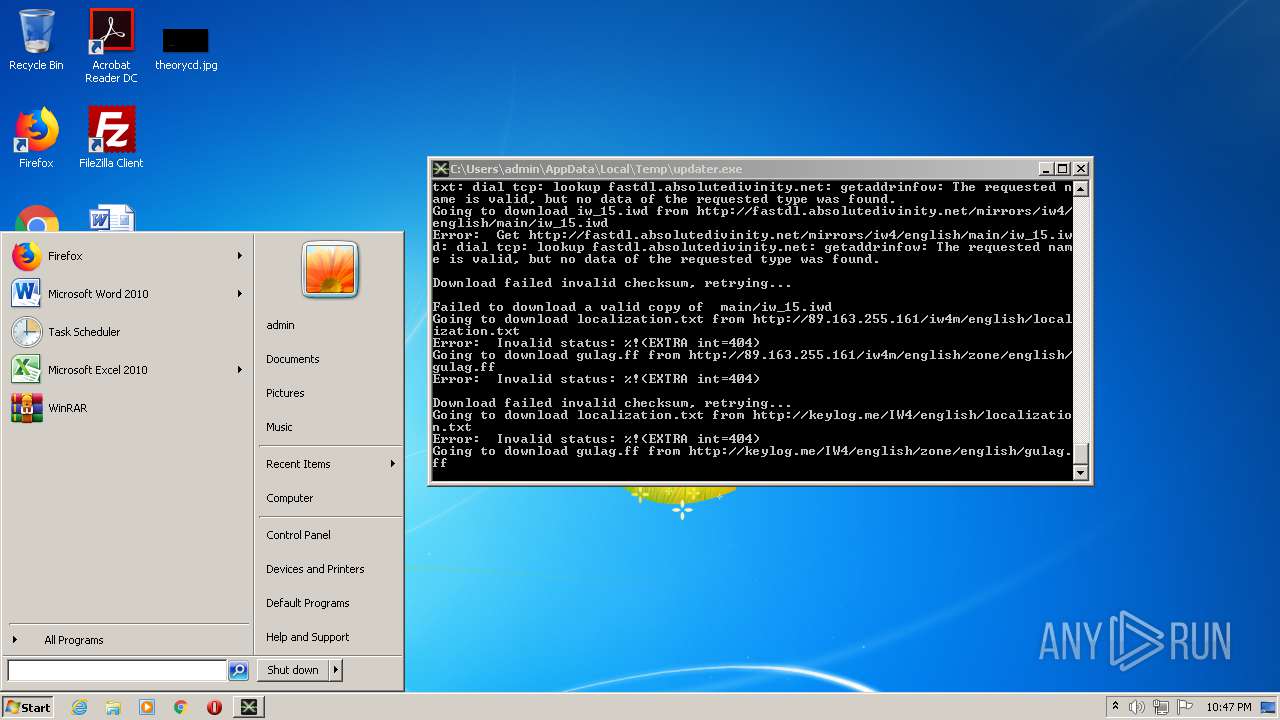
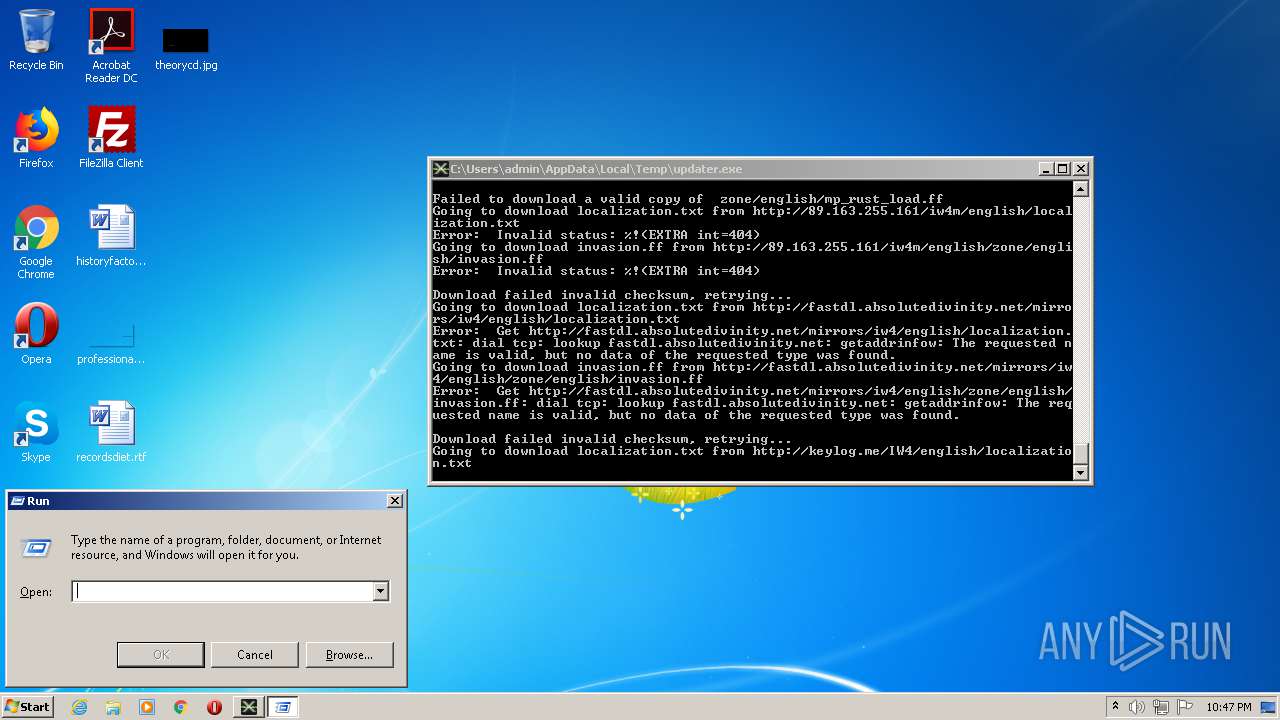
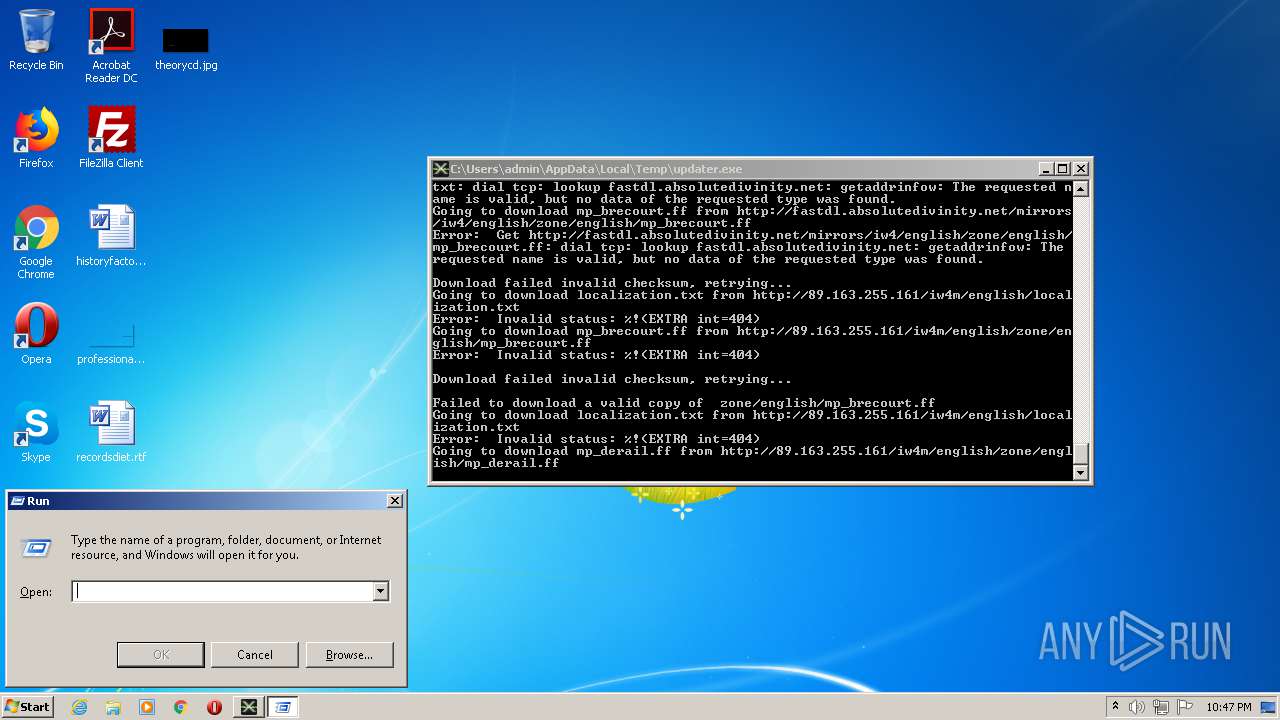
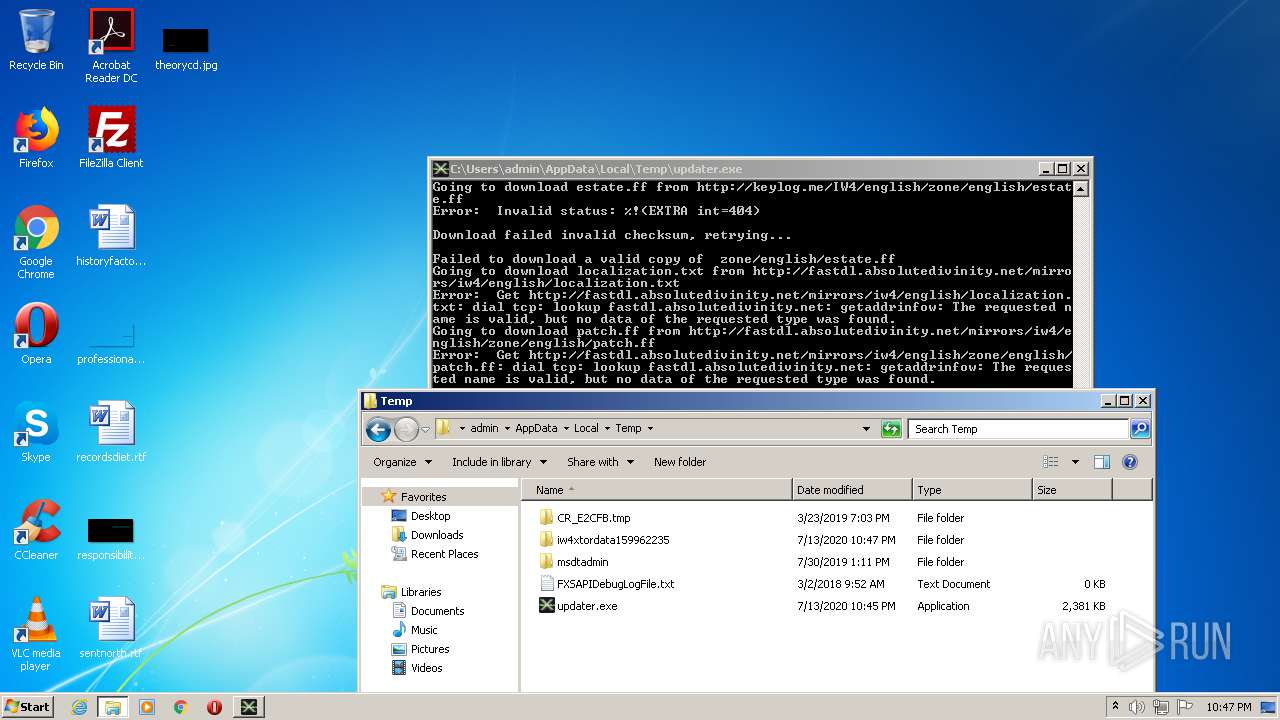
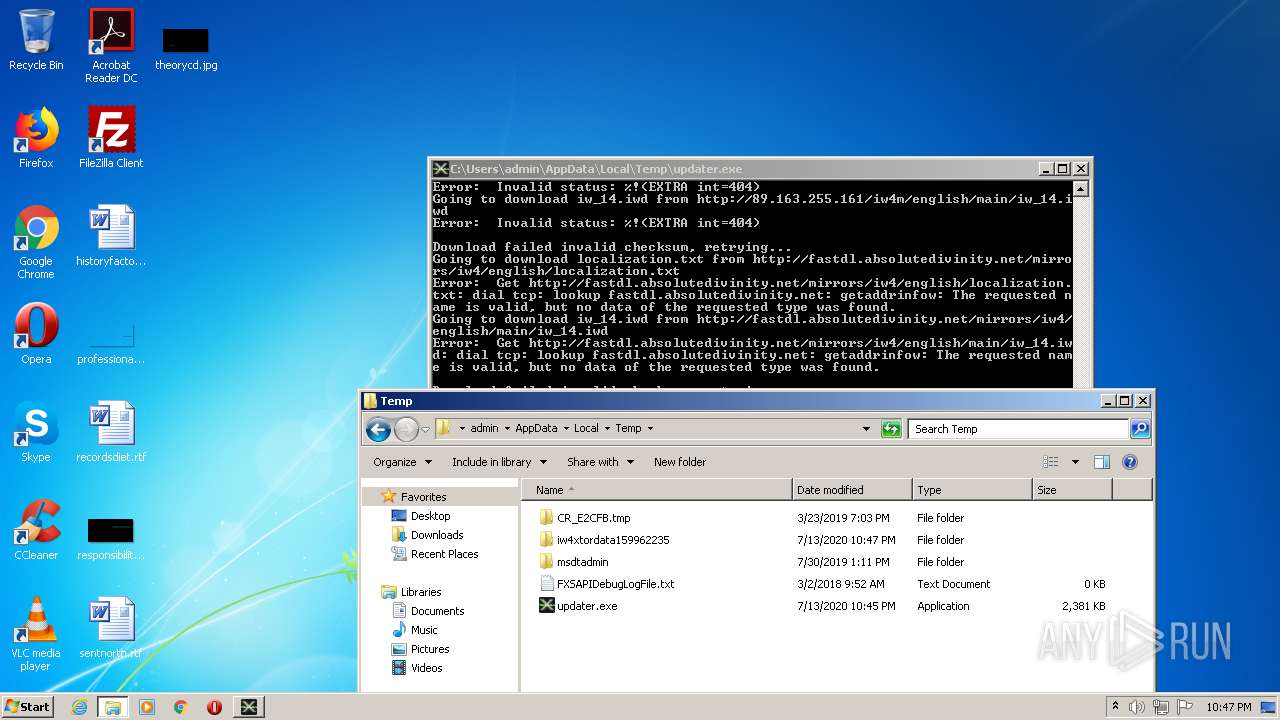
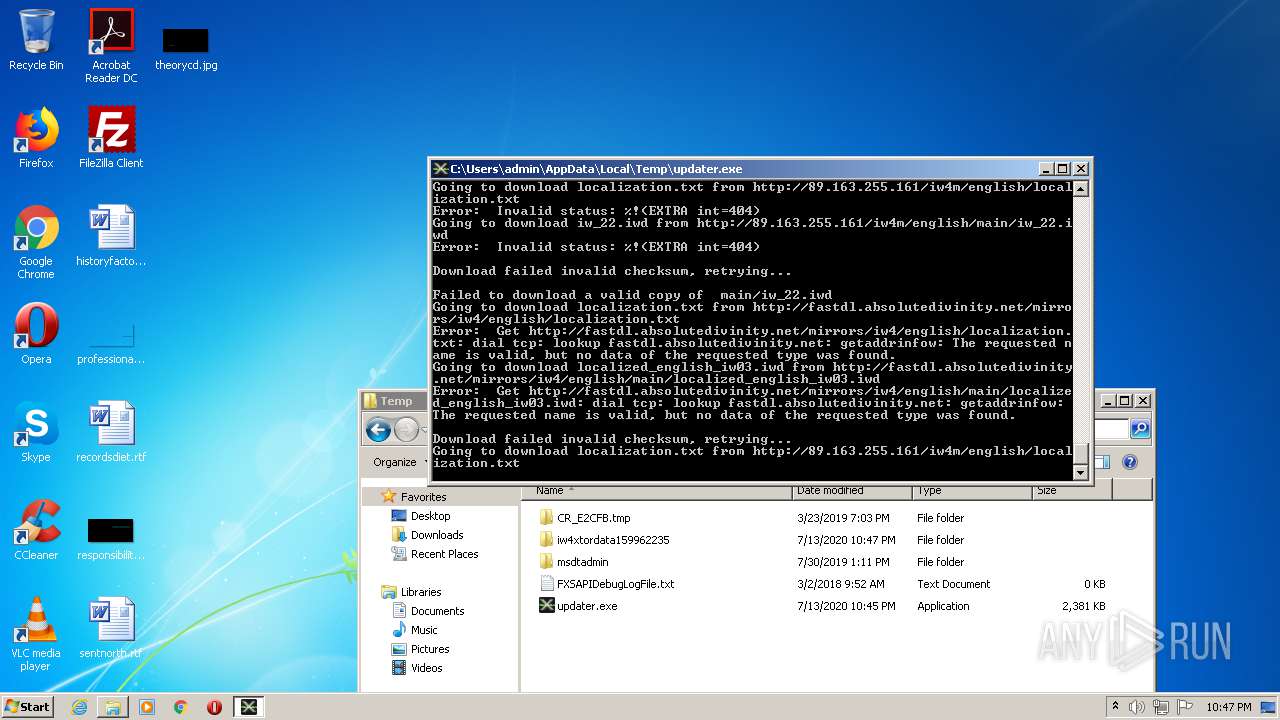
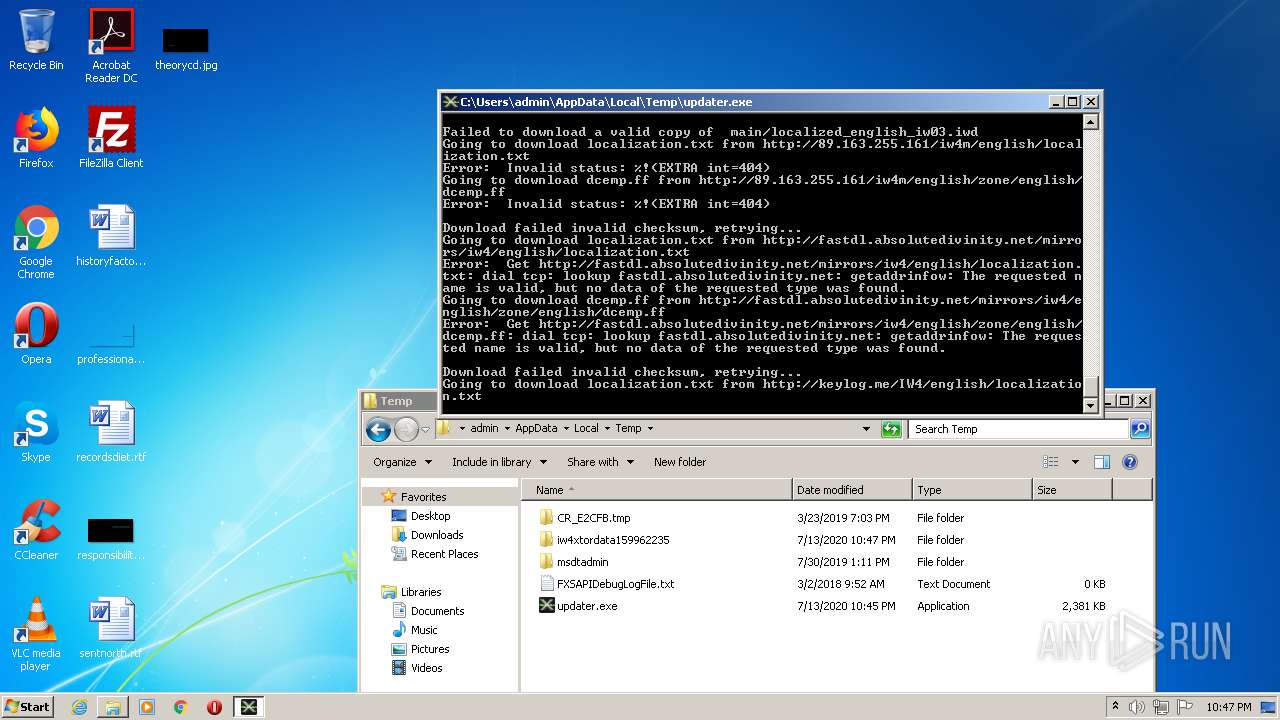
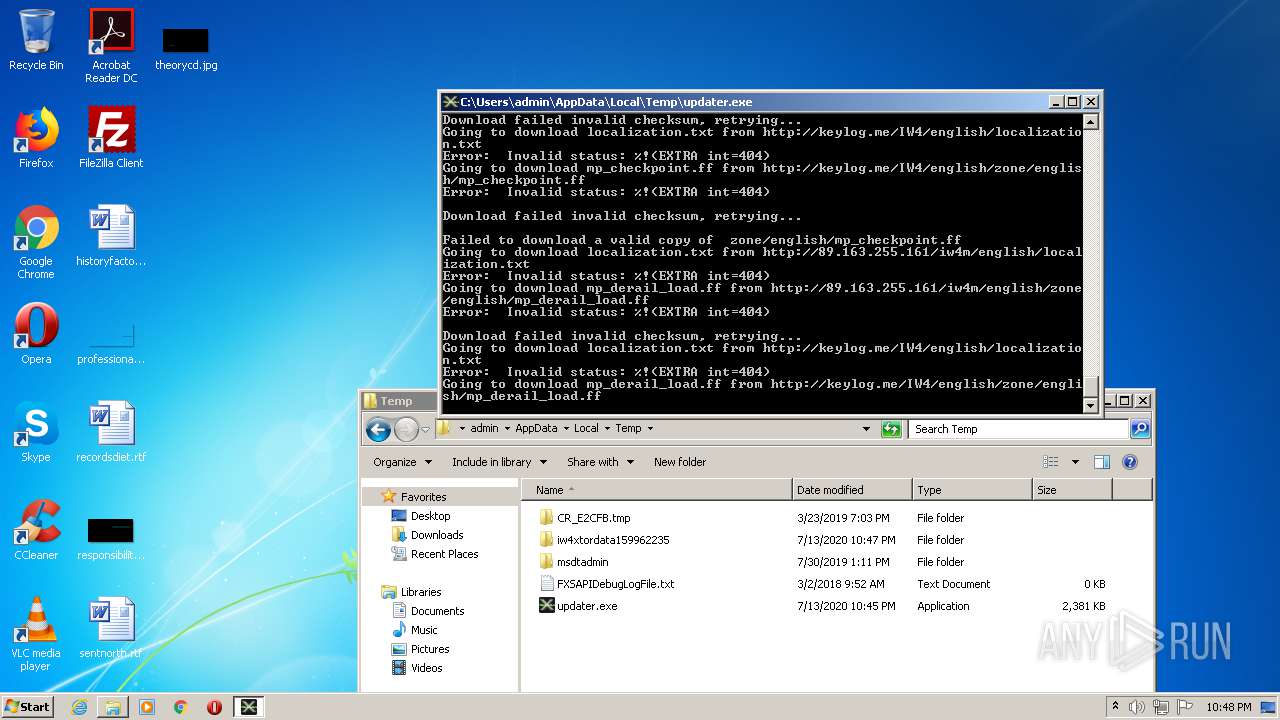
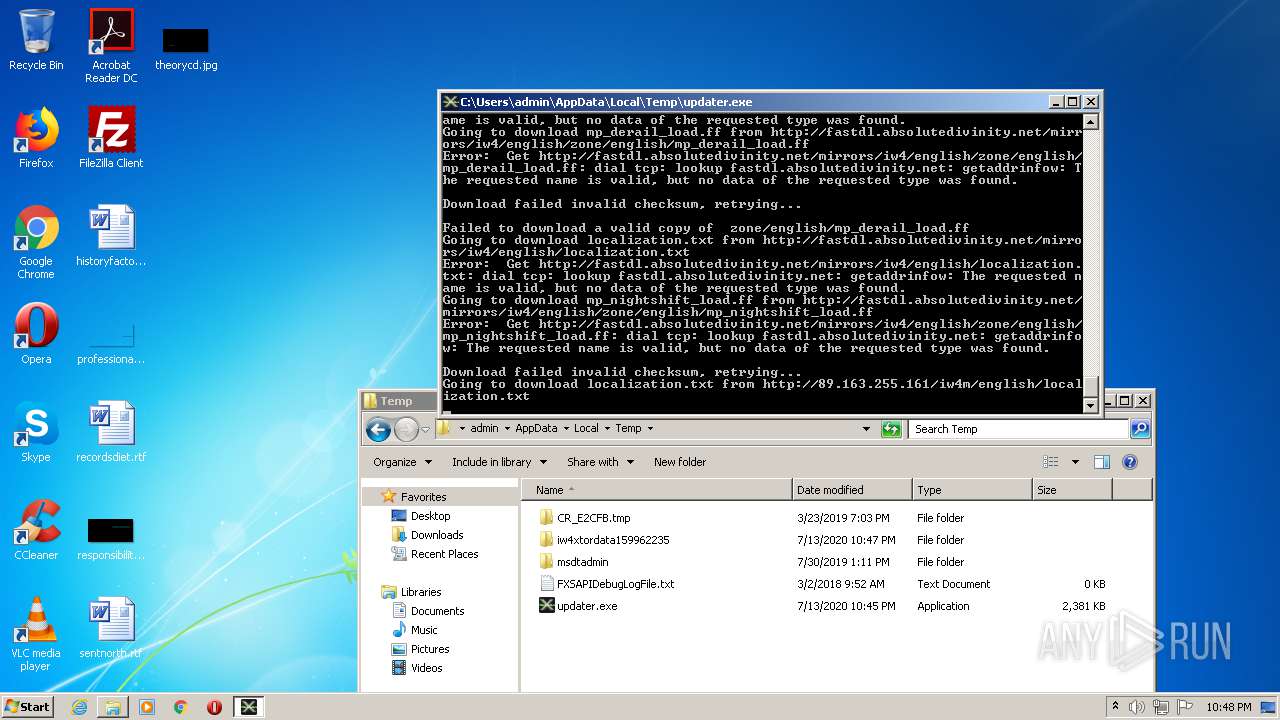
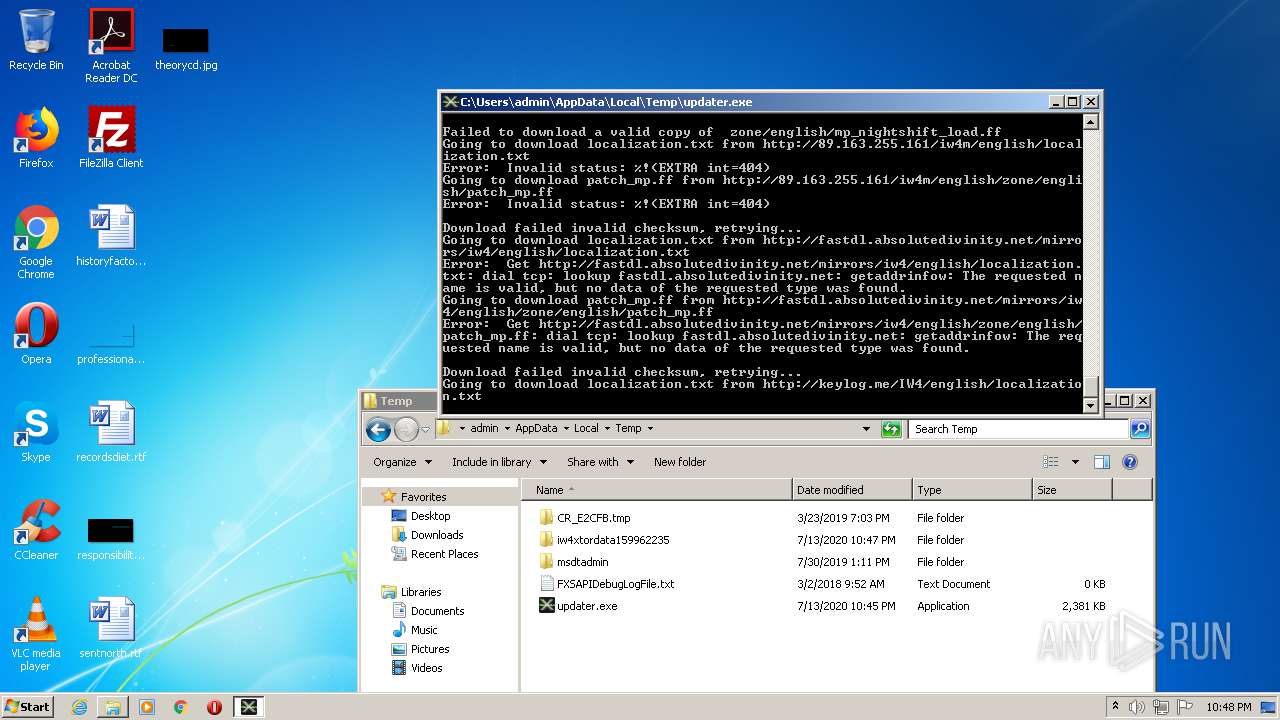
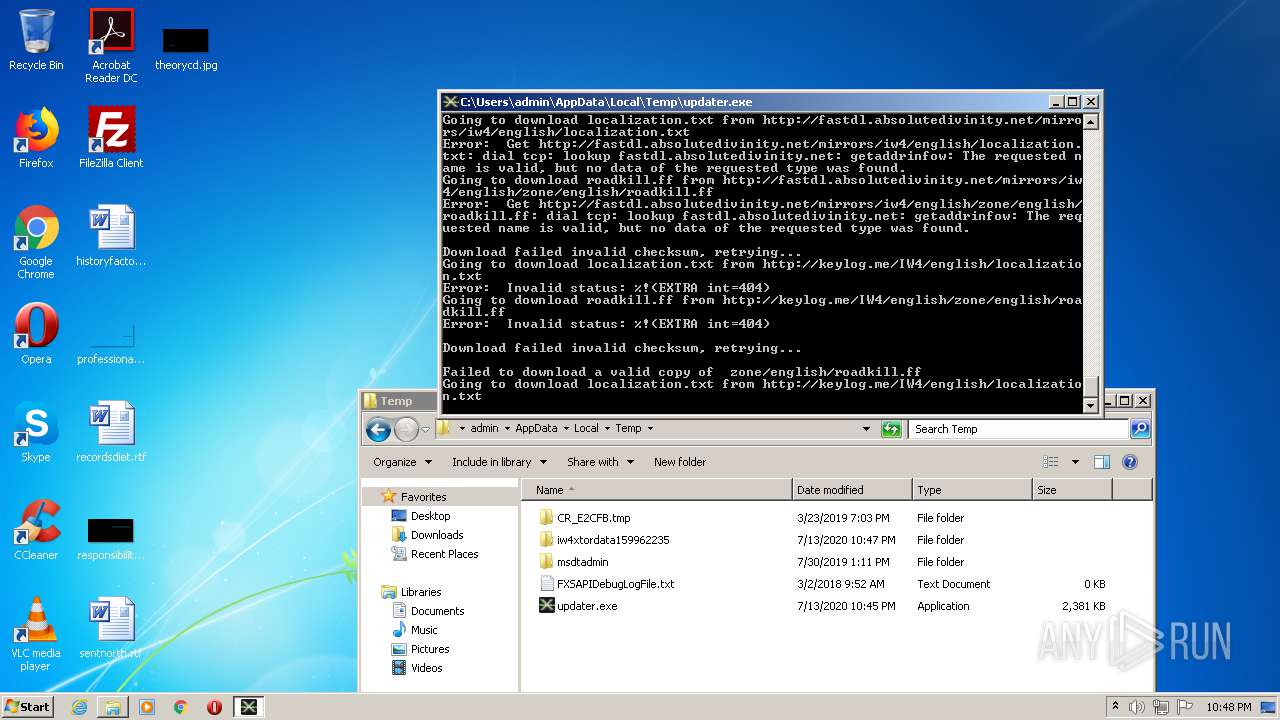
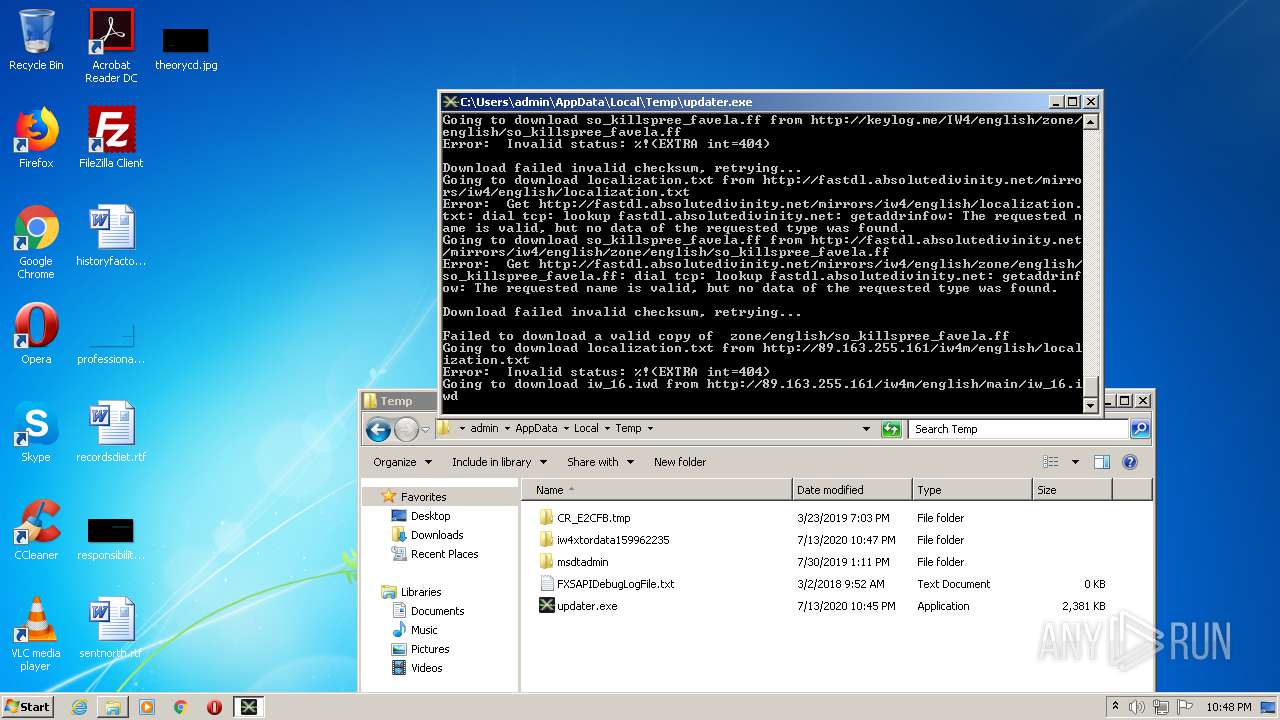
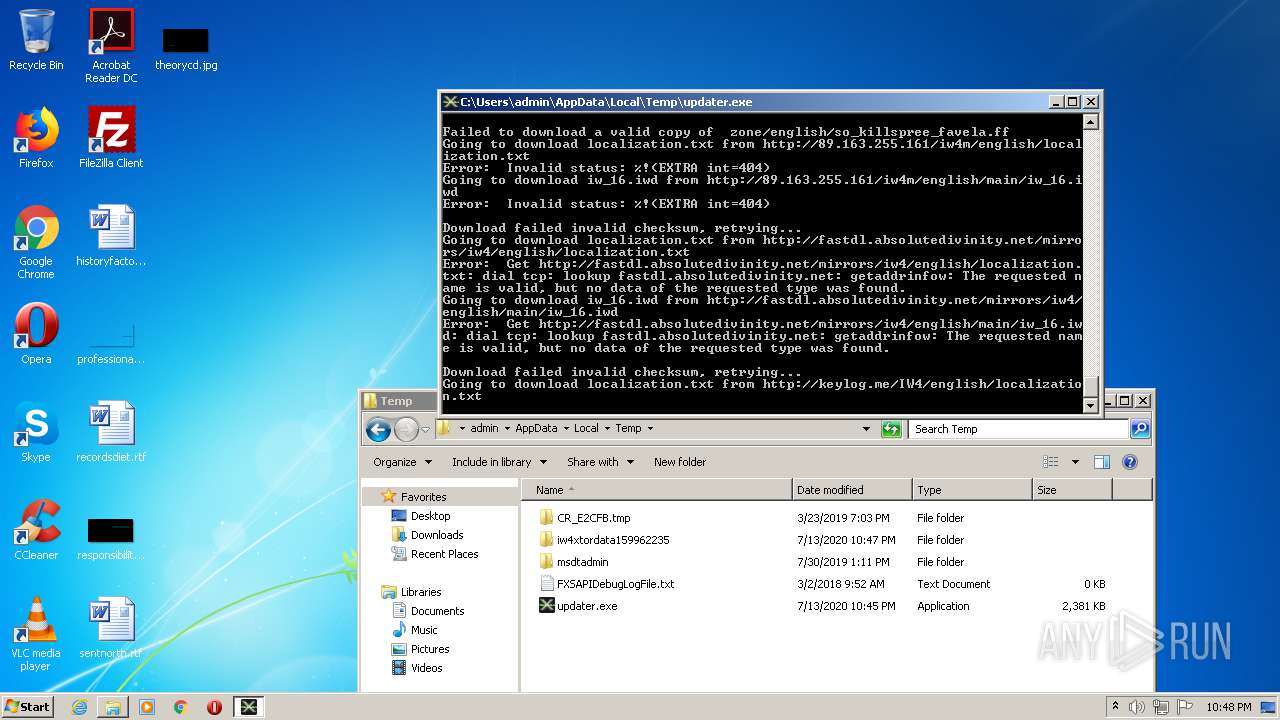
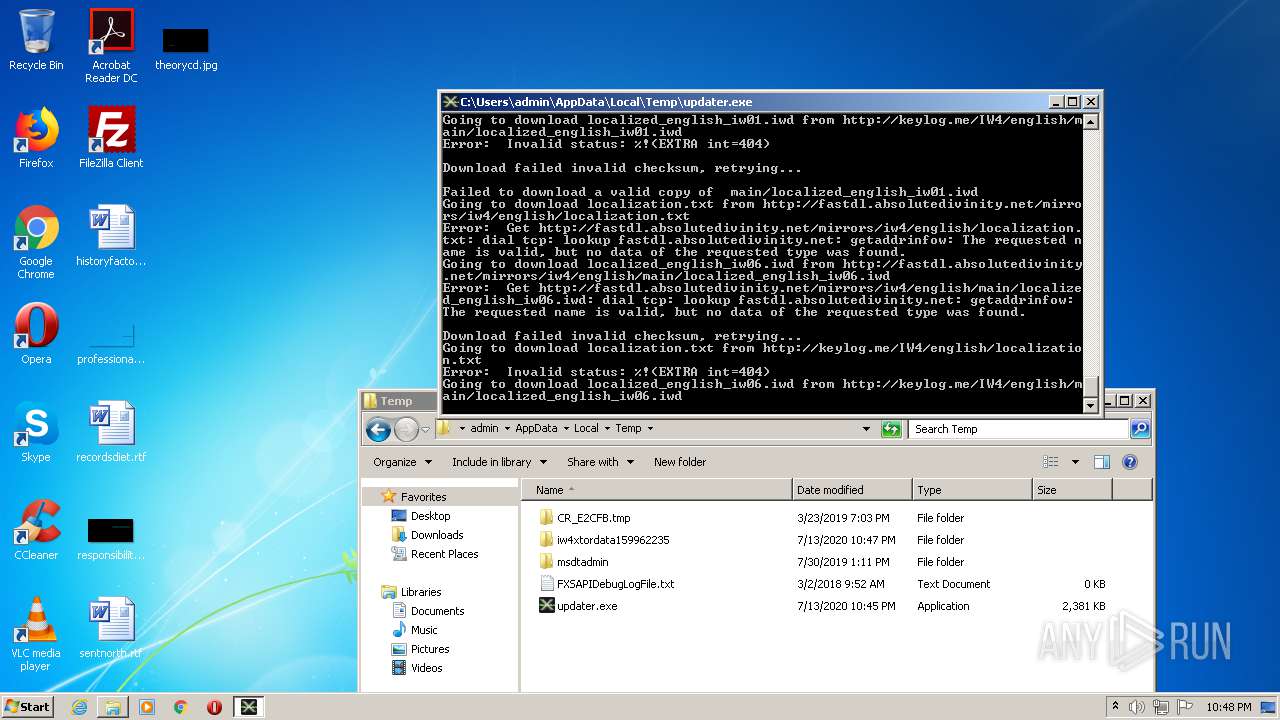
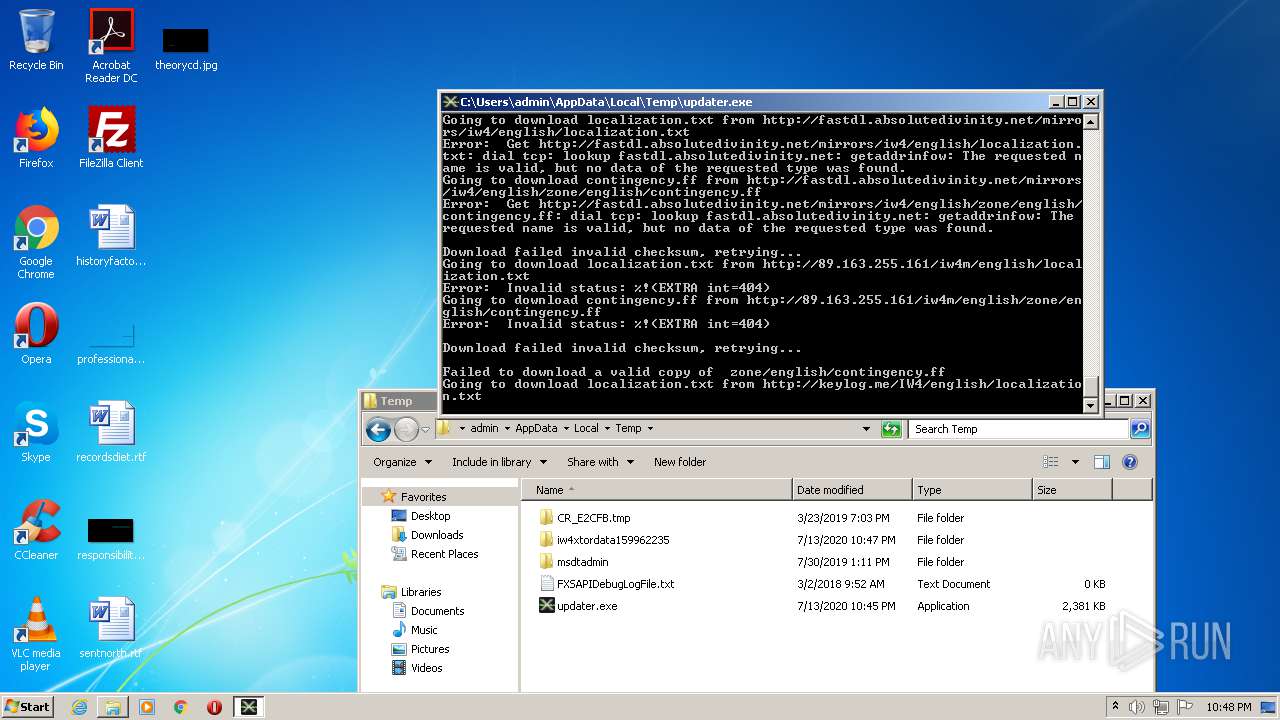
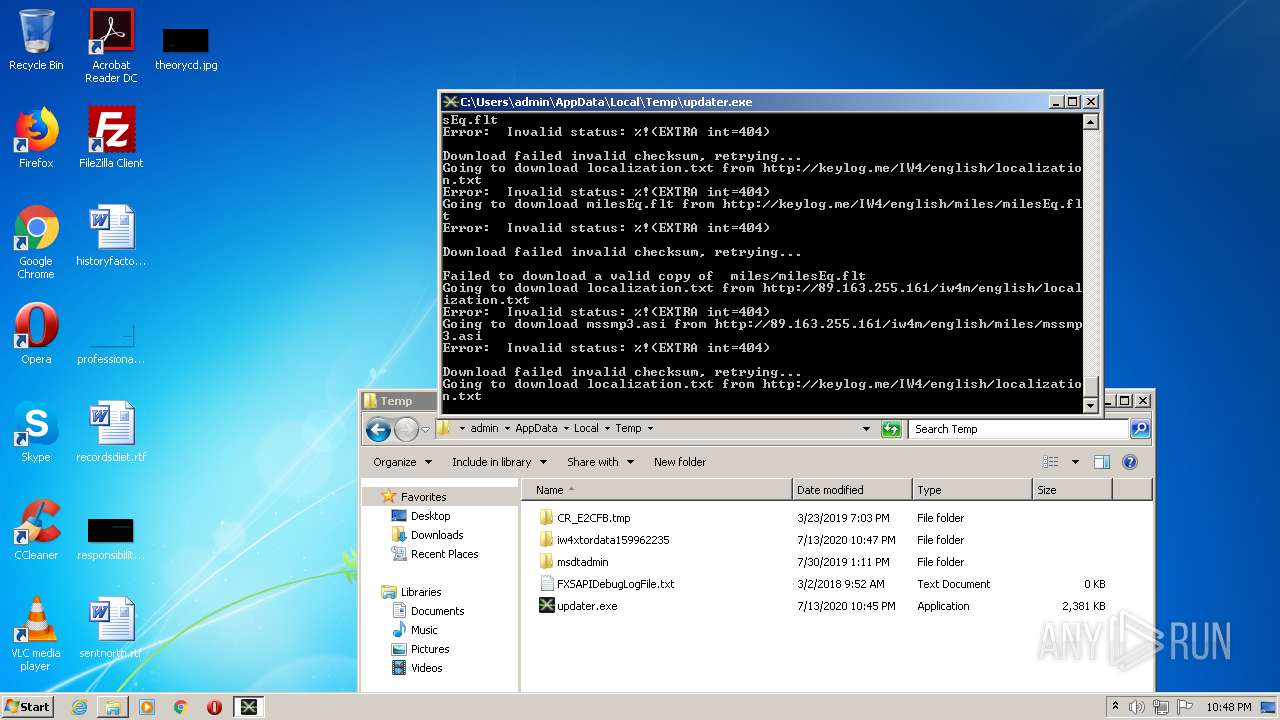
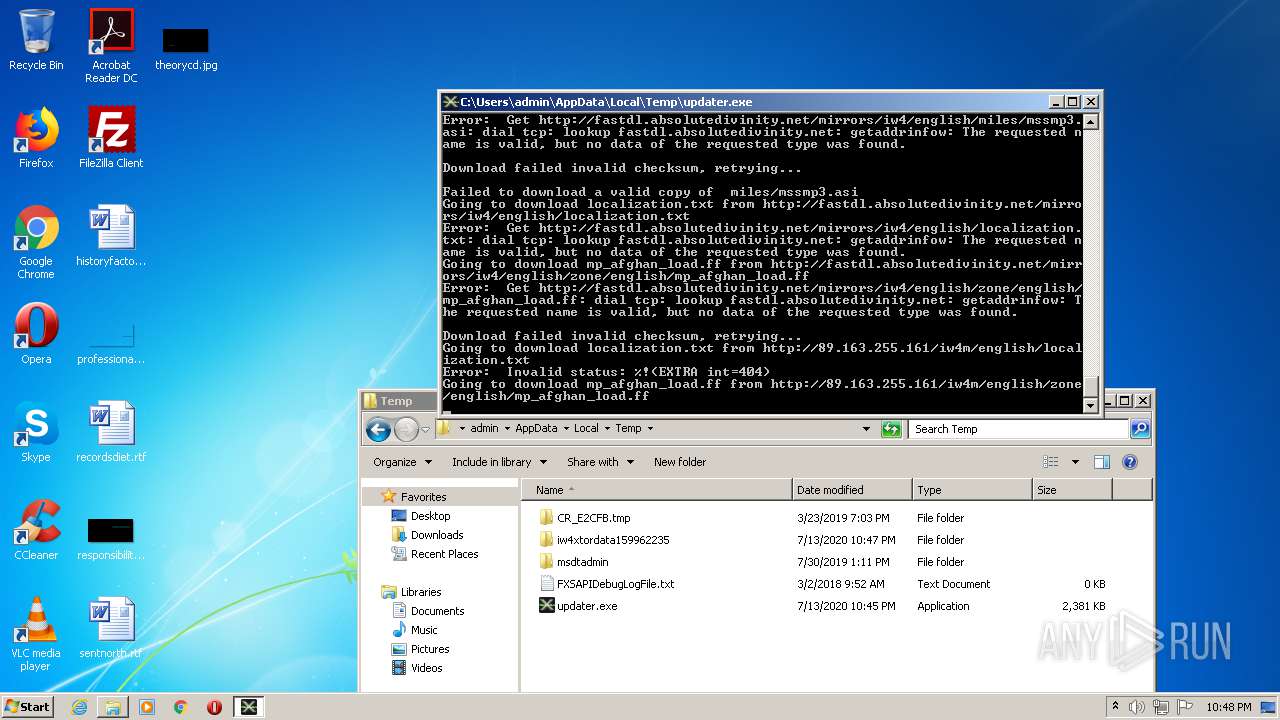
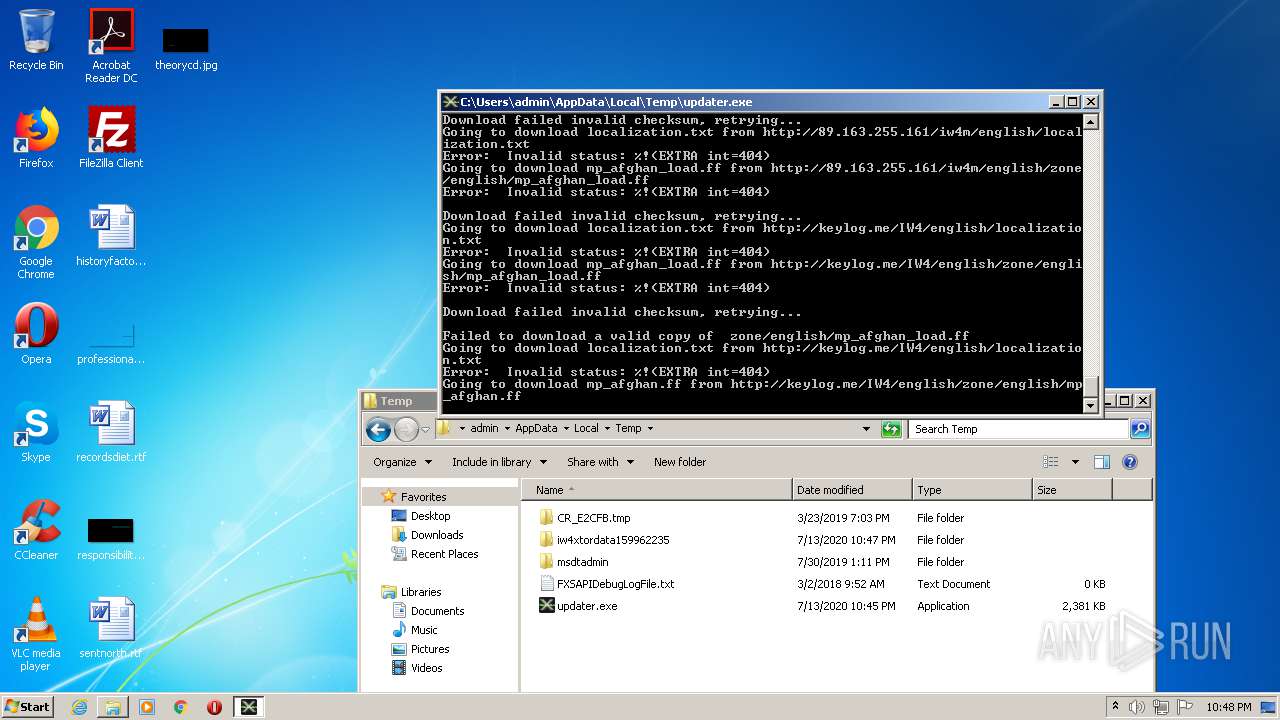
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
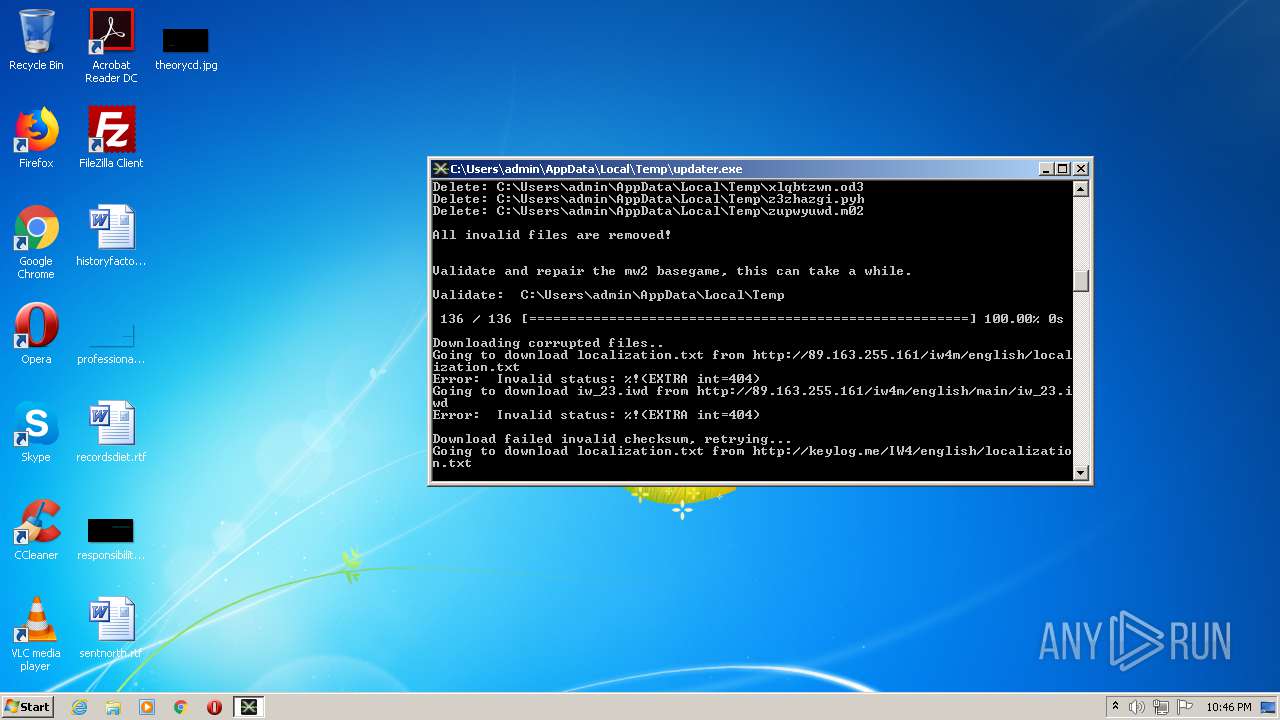
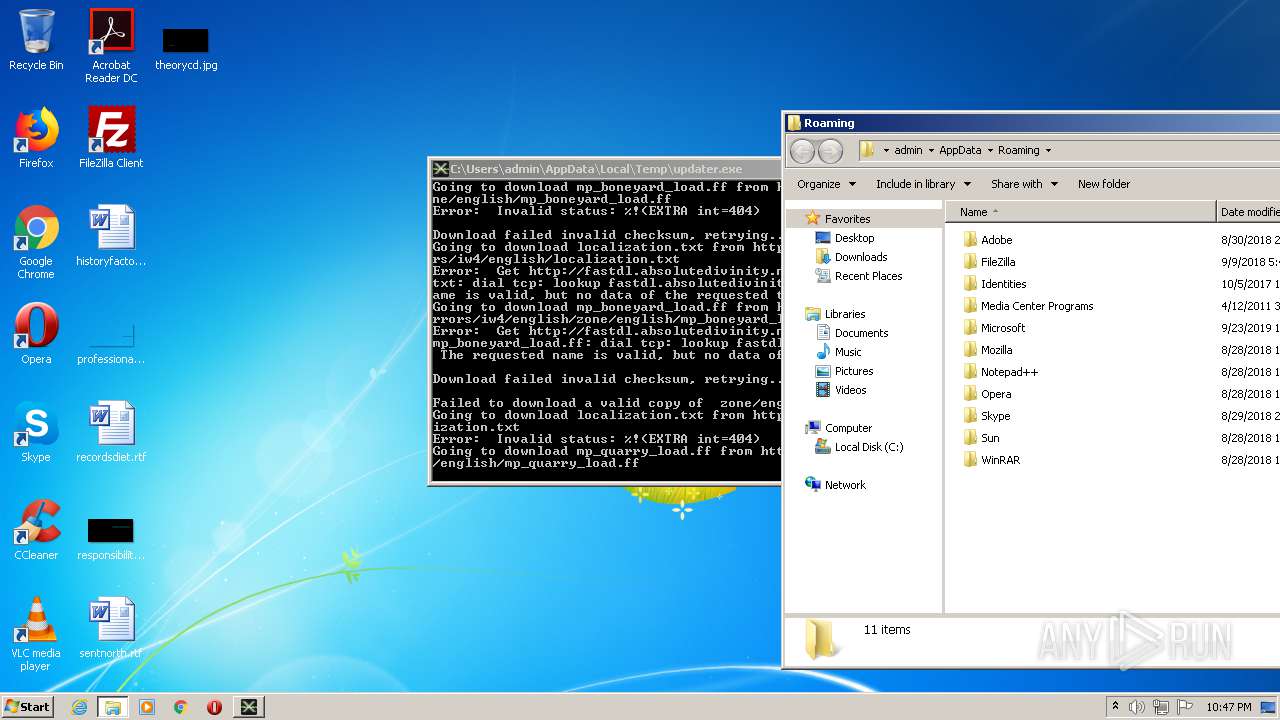
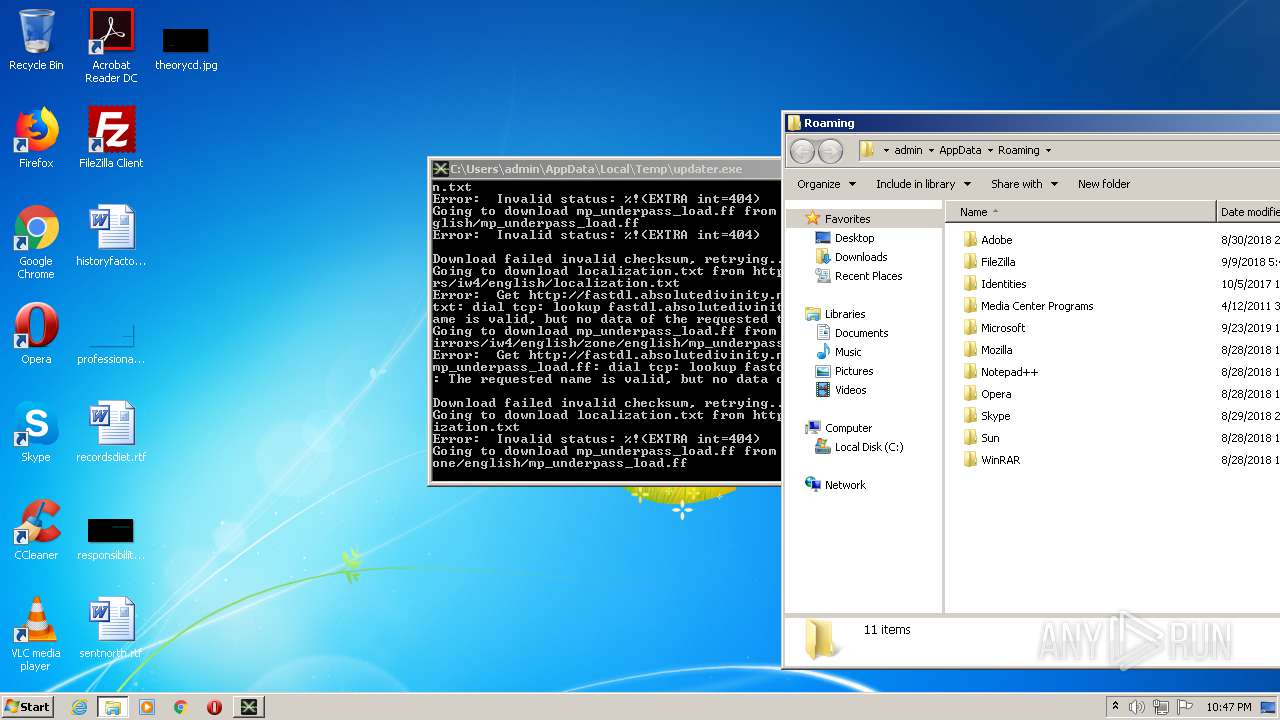
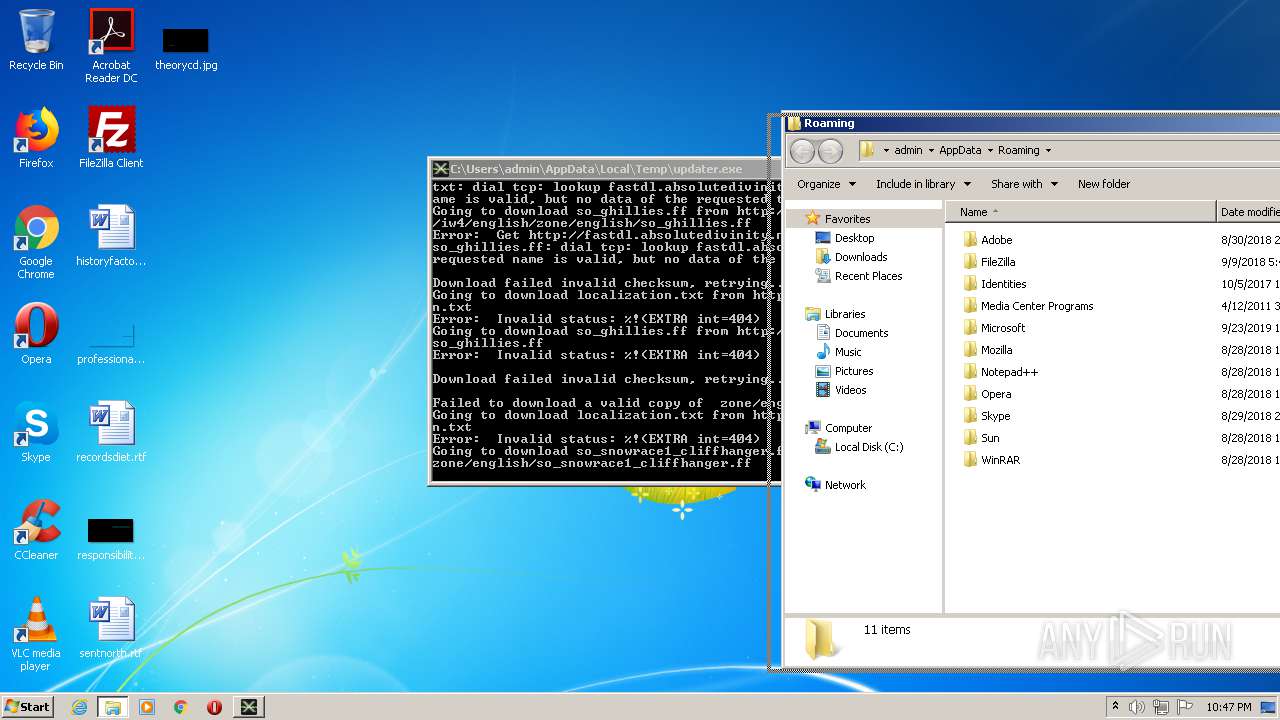
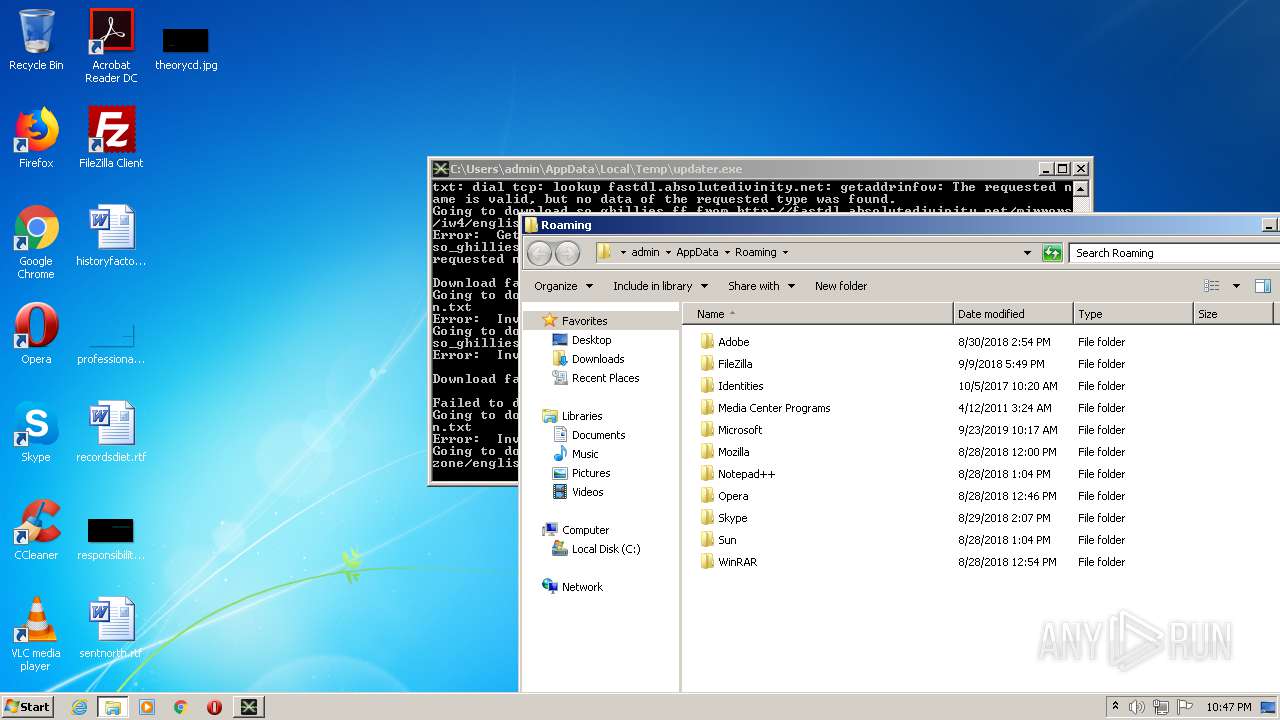
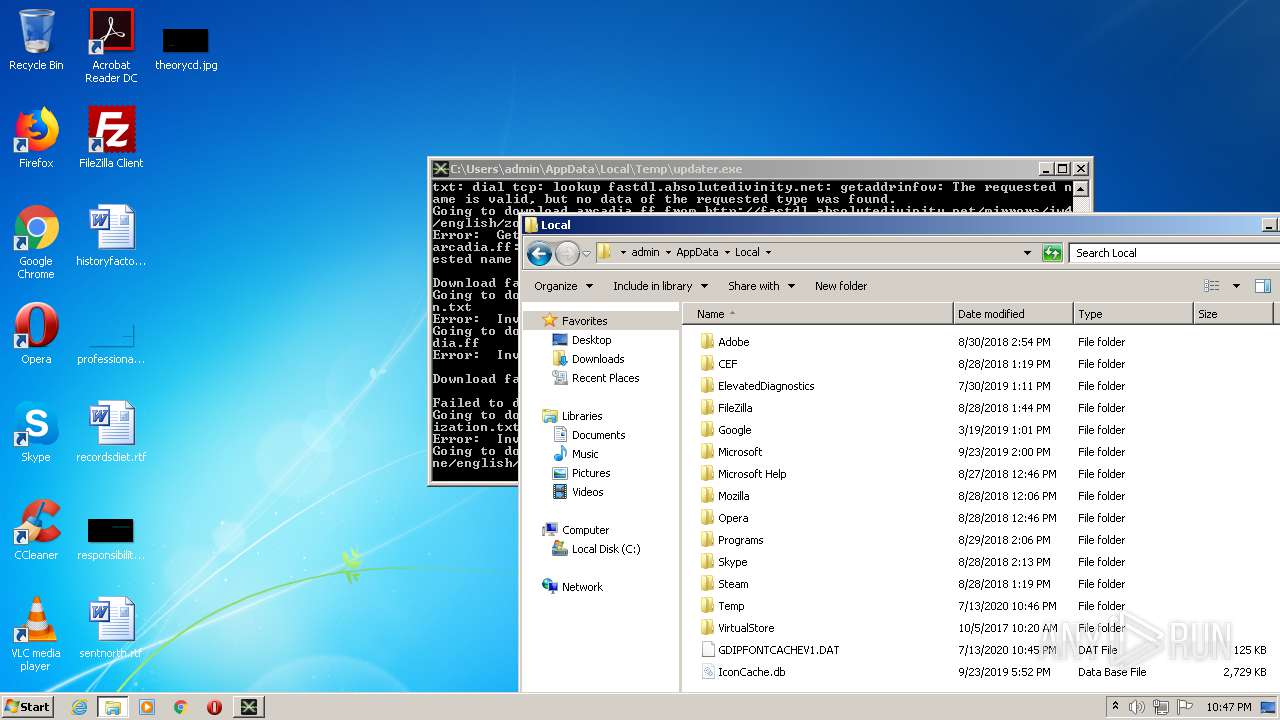
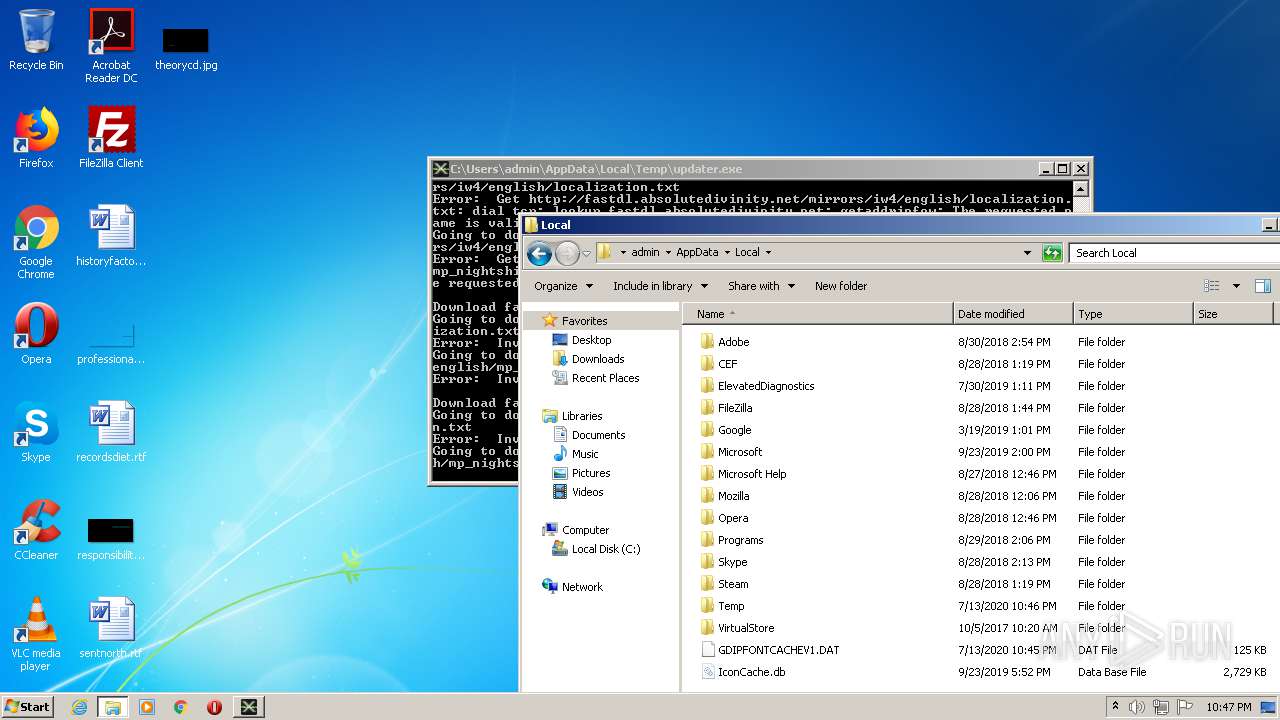
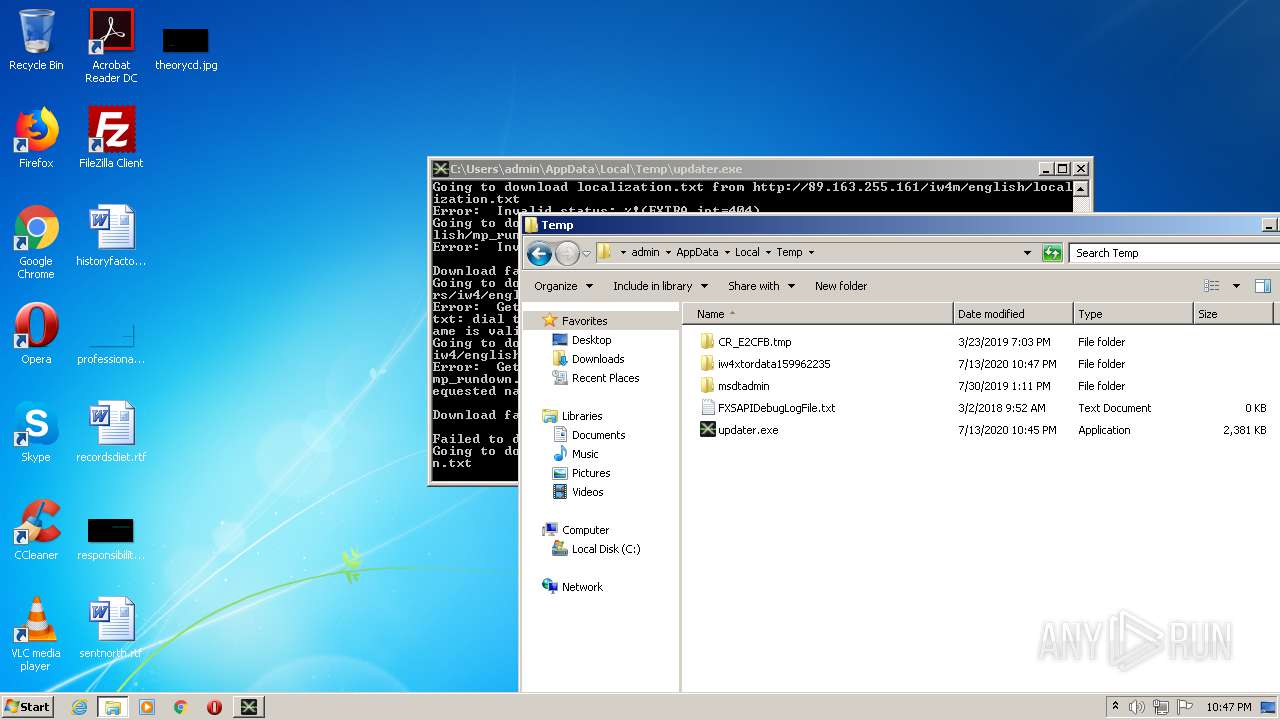
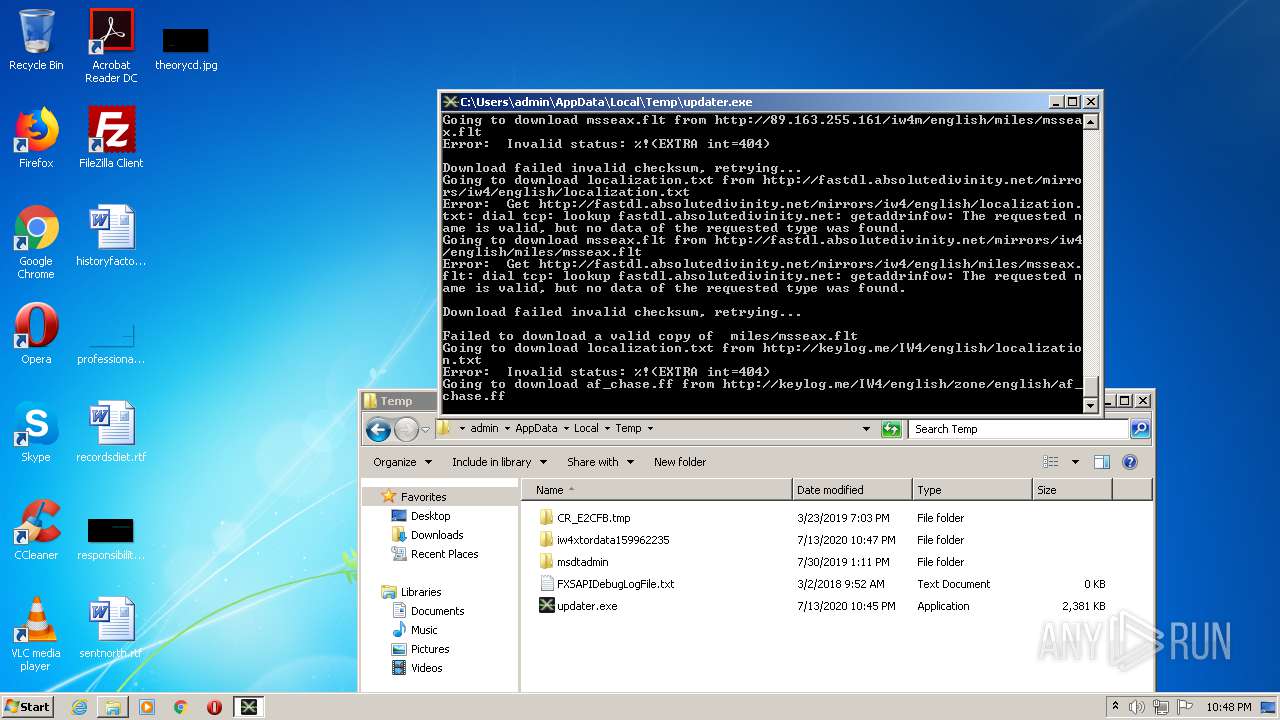
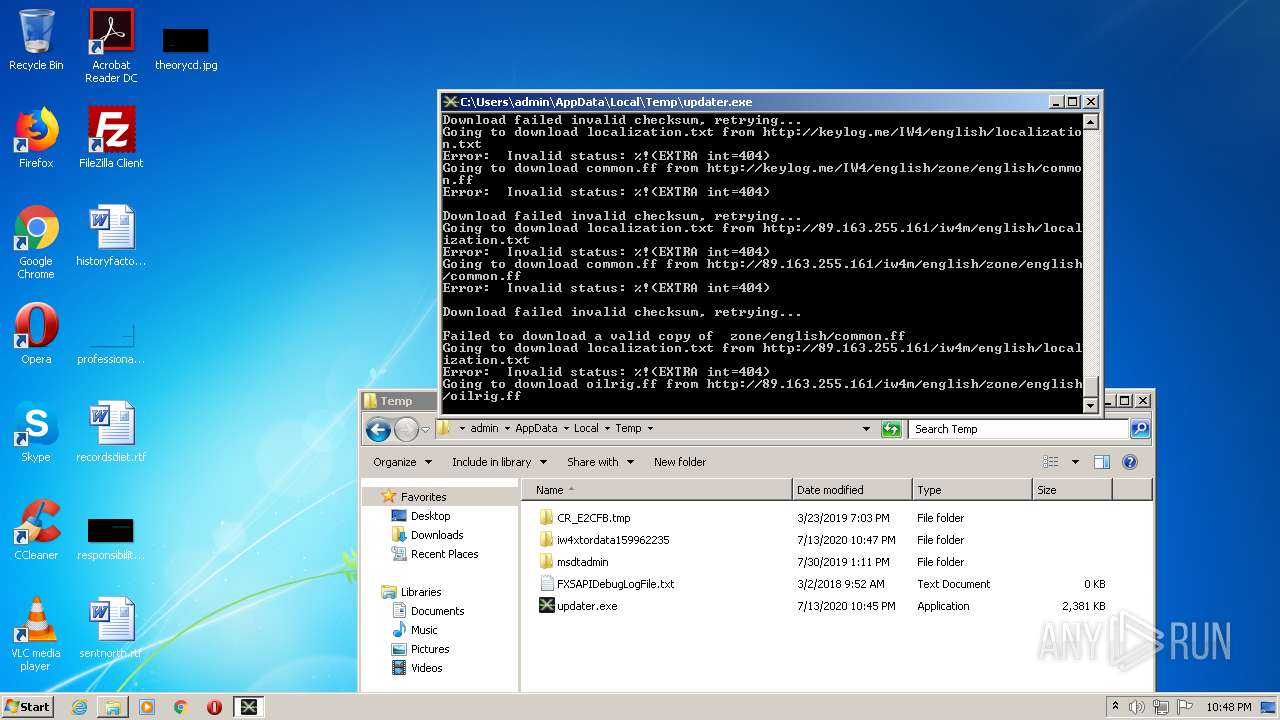
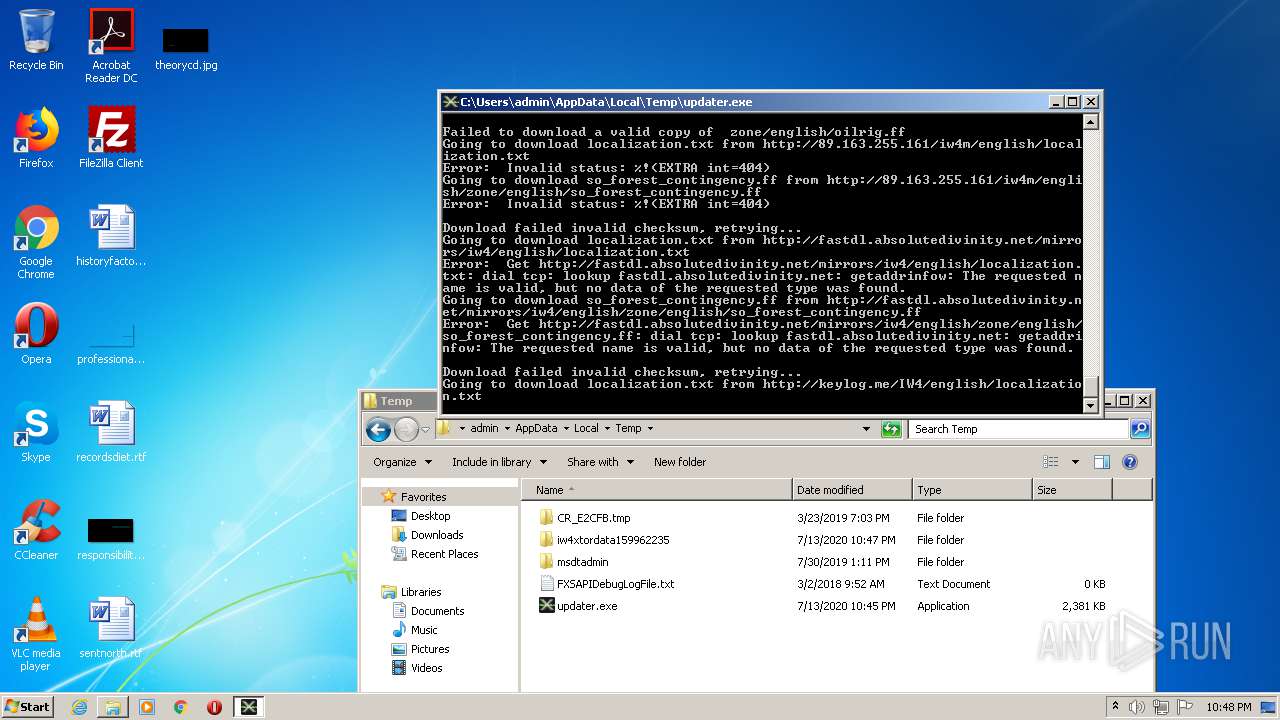
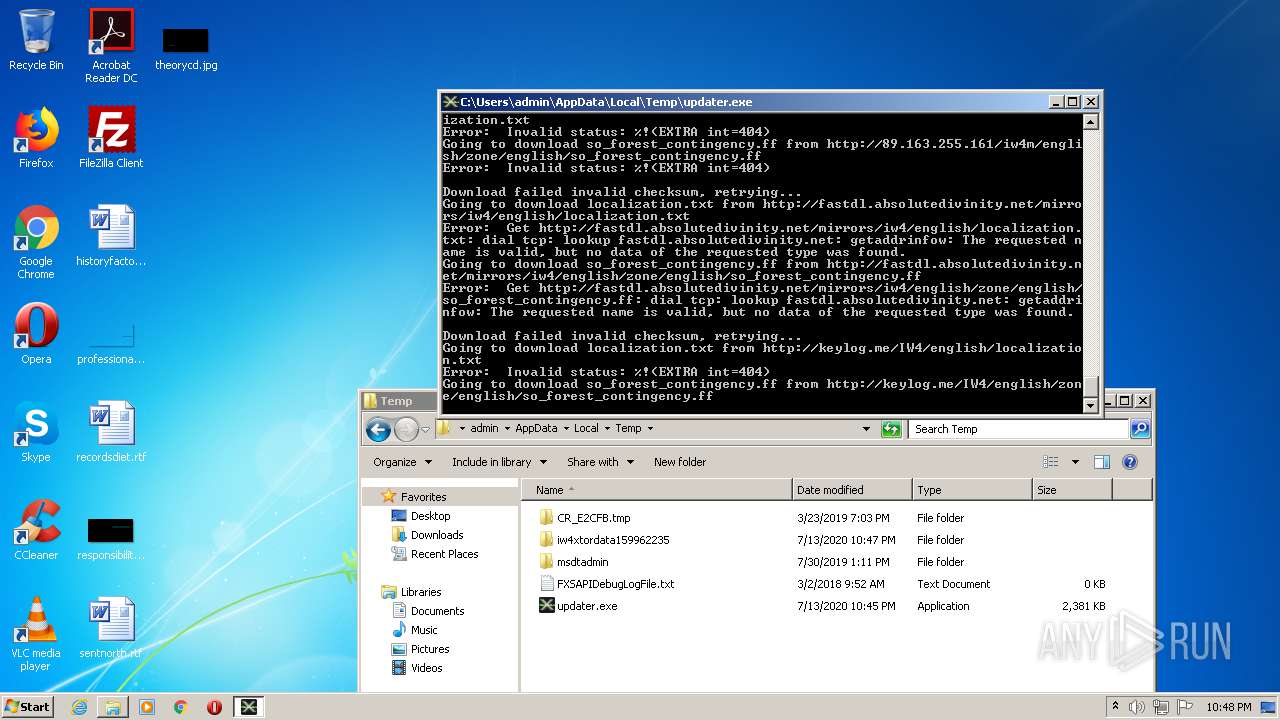
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/main/iw_23.iwd | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/localization.txt | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/zone/english/mp_favela.ff | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/localization.txt | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/zone/english/mp_underpass.ff | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/localization.txt | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/localization.txt | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/zone/english/so_crossing_so_bridge.ff | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/localization.txt | DE | html | 260 b | suspicious |
1872 | updater.exe | GET | 404 | 89.163.255.161:80 | http://89.163.255.161/iw4m/english/zone/english/so_defense_invasion.ff | DE | html | 260 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1872 | updater.exe | 85.235.250.88:443 | — | Telia Company AB | DK | suspicious |
1872 | updater.exe | 171.25.193.9:80 | — | Foreningen for digitala fri- och rattigheter | SE | malicious |
1872 | updater.exe | 37.187.22.87:9001 | — | OVH SAS | FR | suspicious |
1872 | updater.exe | 66.111.2.20:9001 | — | The New York Internet Company | US | suspicious |
1872 | updater.exe | 154.35.175.225:443 | — | Rethem Hosting LLC | US | malicious |
1872 | updater.exe | 137.226.59.108:9001 | — | RWTH Aachen University | DE | suspicious |
1872 | updater.exe | 144.76.5.242:9001 | — | Hetzner Online GmbH | DE | suspicious |
1872 | updater.exe | 185.165.240.126:443 | — | Inovare-Prim SRL | MD | suspicious |
1872 | updater.exe | 89.163.255.161:80 | — | myLoc managed IT AG | DE | suspicious |
1872 | updater.exe | 104.28.15.170:80 | keylog.me | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
keylog.me |
| suspicious |
fastdl.absolutedivinity.net |
| unknown |
dss0.cc |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
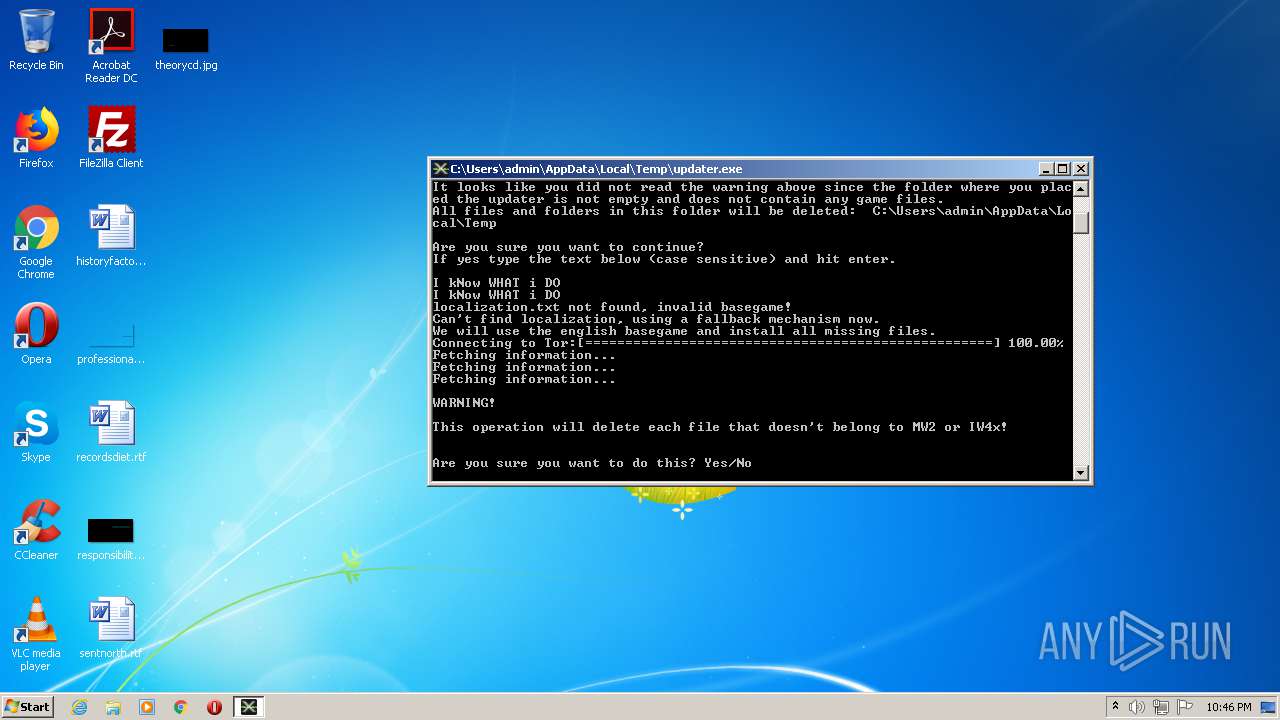
1872 | updater.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 687 |
1872 | updater.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
1872 | updater.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 252 |
1872 | updater.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TOR SSL connection |
1872 | updater.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 323 |
1872 | updater.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 218 |
1872 | updater.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 239 |
1872 | updater.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
1872 | updater.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
1872 | updater.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |