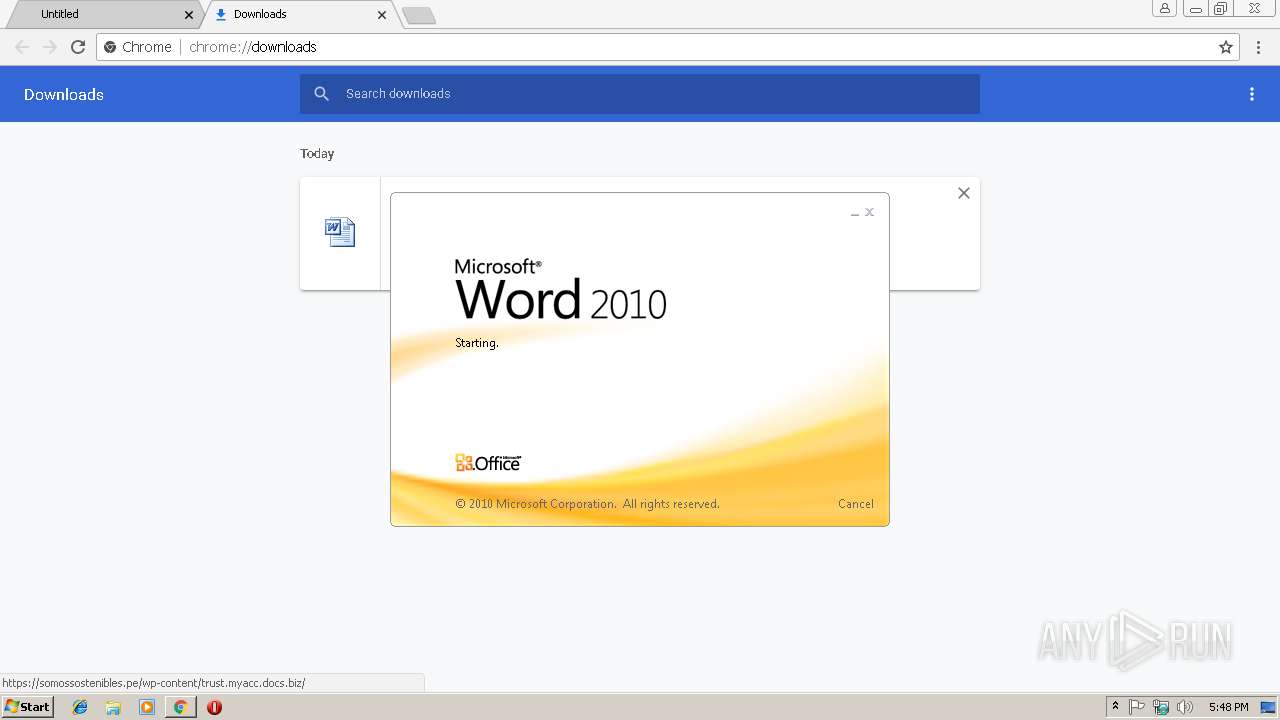
| URL: | http://somossostenibles.pe/wp-content/trust.myacc.docs.biz/ |
| Full analysis: | https://app.any.run/tasks/31da71e6-bc88-4281-9159-8426c9a9be12 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 14, 2019, 17:47:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A67FCF9774ED7539E4091FFA82001F09 |
| SHA1: | 022476DA7B0B7584E3598F22ACA9466078784622 |
| SHA256: | FB1FE69D17221AFC8E628F234A9D08C548CA47731D703B2119858F598DE7B658 |
| SSDEEP: | 3:N1KNK3W6hvmIGEAQxQWWGOMHeK:CYmQv3A+AGOGV |
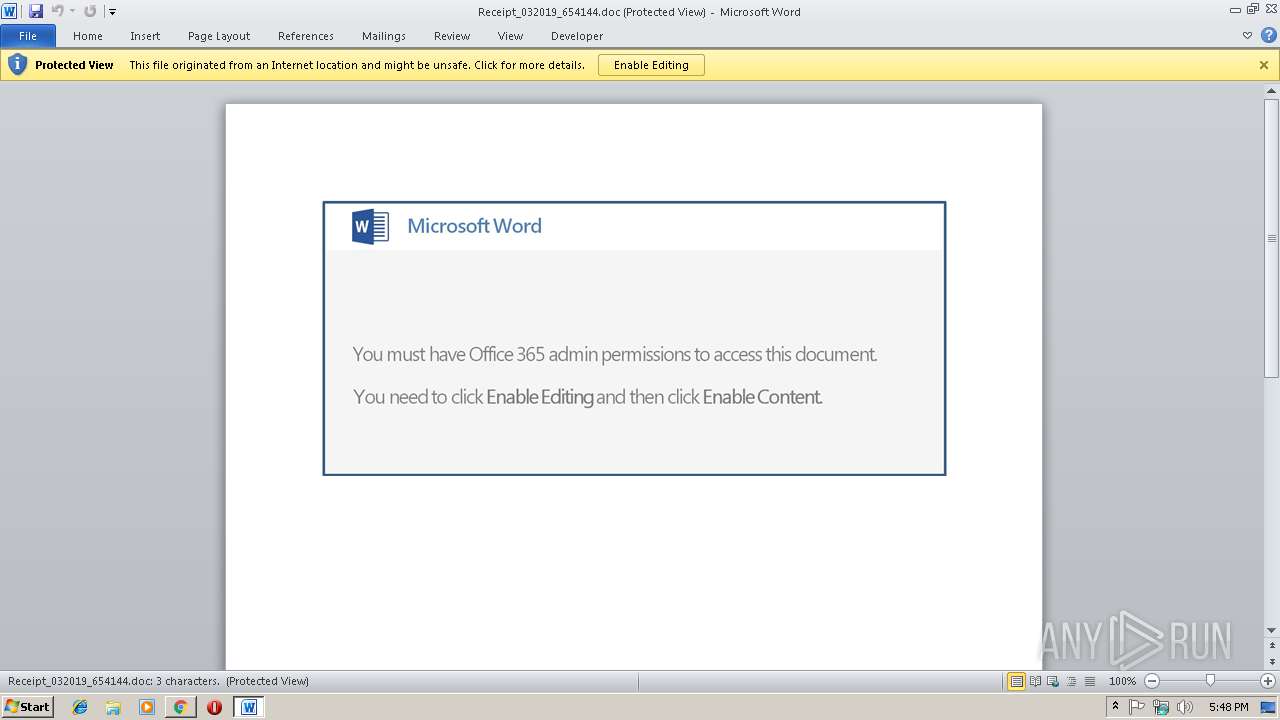
MALICIOUS
Application was dropped or rewritten from another process
- 509.exe (PID: 308)
- 509.exe (PID: 3956)
- wabmetagen.exe (PID: 676)
- wabmetagen.exe (PID: 3136)
Downloads executable files from the Internet
- powershell.exe (PID: 3328)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 3136)
EMOTET was detected
- wabmetagen.exe (PID: 3136)
Emotet process was detected
- wabmetagen.exe (PID: 676)
Connects to CnC server
- wabmetagen.exe (PID: 3136)
SUSPICIOUS
Application launched itself
- WINWORD.EXE (PID: 3568)
- 509.exe (PID: 3956)
- wabmetagen.exe (PID: 676)
Creates files in the user directory
- powershell.exe (PID: 3328)
Starts Microsoft Office Application
- chrome.exe (PID: 2884)
- WINWORD.EXE (PID: 3568)
Executable content was dropped or overwritten
- powershell.exe (PID: 3328)
- 509.exe (PID: 308)
Starts itself from another location
- 509.exe (PID: 308)
INFO
Application launched itself
- chrome.exe (PID: 2884)
Creates files in the user directory
- chrome.exe (PID: 2884)
- WINWORD.EXE (PID: 3568)
Reads Internet Cache Settings
- chrome.exe (PID: 2884)
Reads settings of System Certificates
- chrome.exe (PID: 2884)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3160)
- WINWORD.EXE (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Users\admin\509.exe" | C:\Users\admin\509.exe | 509.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 676 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 509.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=876,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=11BFF5CE3237868FC9DA1CE0606B0AEB --mojo-platform-channel-handle=932 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=876,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3A03051EF576BF44BBA7C46E412DD3FD --mojo-platform-channel-handle=2348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=876,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=EB4E79B81CEC48AA41F15913EA427D2F --mojo-platform-channel-handle=3148 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://somossostenibles.pe/wp-content/trust.myacc.docs.biz/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=876,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E986B084163D78931164E879EFB7BE67 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E986B084163D78931164E879EFB7BE67 --renderer-client-id=6 --mojo-platform-channel-handle=3764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2888 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=876,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --renderer-client-id=4 --mojo-platform-channel-handle=1880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3136 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 276
Read events
2 776
Write events
485
Delete events
15
Modification events
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2884-13197059279008000 |
Value: 259 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2884-13197059279008000 |
Value: 259 | |||
Executable files
2
Suspicious files
27
Text files
68
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c2f0bcfa-384e-46f5-8c3c-608b285273d7.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\92e897de-8dff-407f-a7a3-dcb31e907e52.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6f1d0437-fb23-467e-afa3-be66156b10e8.tmp | — | |
MD5:— | SHA256:— | |||
| 2884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e497.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
11
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
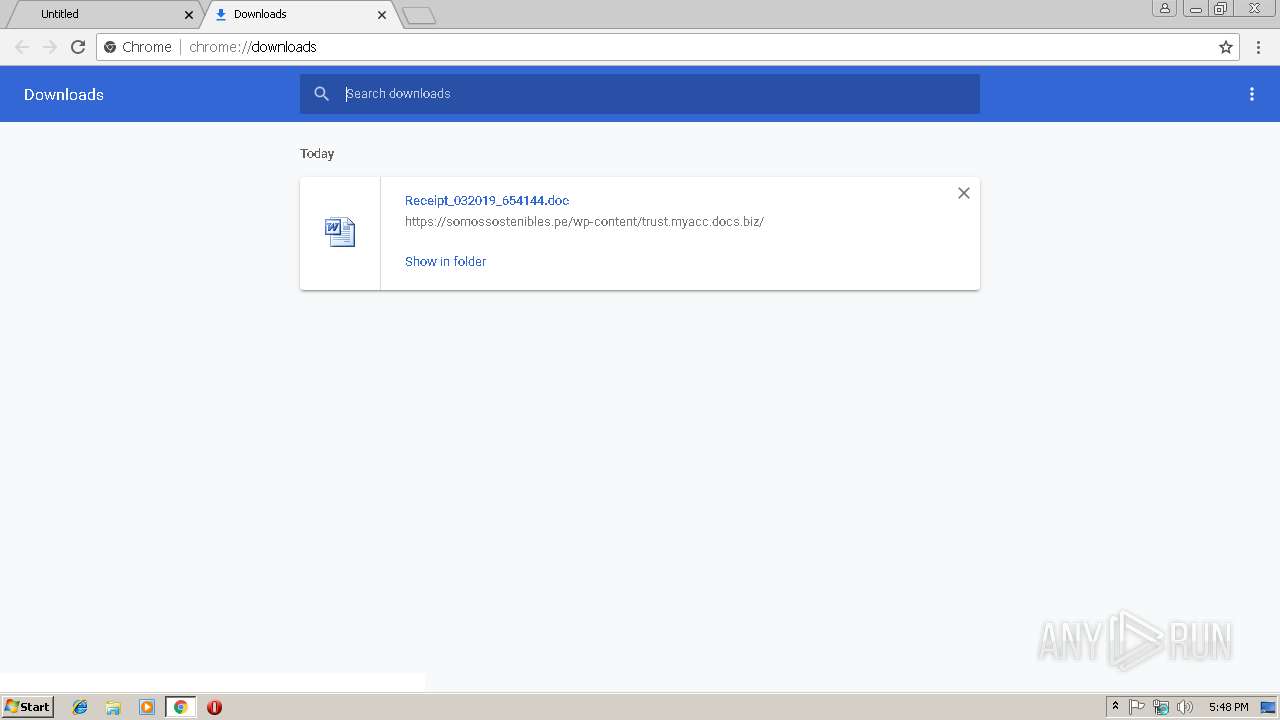
2884 | chrome.exe | GET | 301 | 104.27.173.26:80 | http://somossostenibles.pe/wp-content/trust.myacc.docs.biz/ | US | — | — | shared |
3328 | powershell.exe | GET | — | 178.210.177.101:80 | http://uzeyirpeygamber.com/wp-admin/nH4/ | TR | — | — | suspicious |
3136 | wabmetagen.exe | GET | — | 82.78.228.57:443 | http://82.78.228.57:443/ | RO | — | — | malicious |
3136 | wabmetagen.exe | GET | 200 | 187.207.188.248:443 | http://187.207.188.248:443/ | MX | binary | 132 b | malicious |
3328 | powershell.exe | GET | 200 | 139.99.156.119:80 | http://navewindre.xyz/wp2/wp-content/ktVWQ8/ | AU | executable | 359 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2884 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3328 | powershell.exe | 47.94.209.126:443 | www.yanjiaozhan.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2884 | chrome.exe | 172.217.22.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
3328 | powershell.exe | 178.210.177.101:80 | uzeyirpeygamber.com | Equinix Turkey Internet Hizmetleri Anonim Sirketi | TR | suspicious |
2884 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3328 | powershell.exe | 139.99.156.119:80 | navewindre.xyz | OVH SAS | AU | suspicious |
2884 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3136 | wabmetagen.exe | 82.78.228.57:443 | — | RCS & RDS | RO | malicious |
3136 | wabmetagen.exe | 187.207.188.248:443 | — | Uninet S.A. de C.V. | MX | malicious |
2884 | chrome.exe | 104.27.173.26:443 | somossostenibles.pe | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
somossostenibles.pe |
| unknown |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.yanjiaozhan.com |
| unknown |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
uzeyirpeygamber.com |
| suspicious |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2884 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3328 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3328 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3328 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3136 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3136 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2 ETPRO signatures available at the full report