| File name: | 549c23278d248e811ccb8487b27ab635d0a71cf2a9eab95e656eb9dc9e64557a.zip |
| Full analysis: | https://app.any.run/tasks/d3b3fa1a-44fb-47c7-86f9-4a9677192d2d |
| Verdict: | Malicious activity |
| Threats: | MassLogger is a credential stealer and keylogger first identified in April 2020. It has been actively used in cyber campaigns to exfiltrate sensitive information from compromised systems. It is designed for easy use by less tech-savvy actors and is prominent for the capability of spreading via USB drives. It targets both individuals and organizations in various industries, mostly in Europe and the USA. |
| Analysis date: | September 30, 2020, 08:30:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
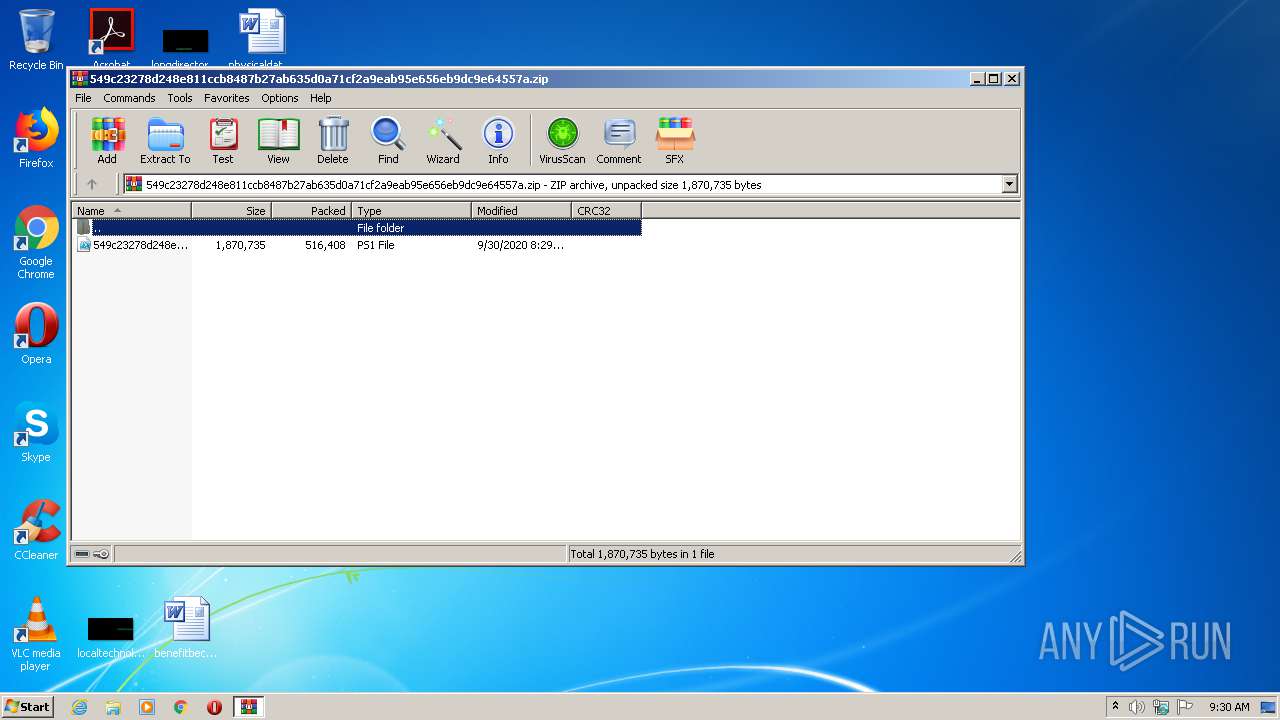
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D6A1F2C087E6ED0E18C7EA491FC70A01 |
| SHA1: | EB2273CBFC4853CBB6C7AAA0C54BFC886B54B500 |
| SHA256: | FB160A8E640553DA22EB9CF50CFAE7E69151FA40EF1DD14FC96B5CEC6E80964C |
| SSDEEP: | 12288:bOiy5hJ1640W2/CfePKRftOlBsWyMDZe/A820q6WxVym:ij4W2/CfPLfW9kc9 |
MALICIOUS
MASSLOGGER was detected
- InstallUtil.exe (PID: 2988)
Stealing of credential data
- InstallUtil.exe (PID: 2988)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 2988)
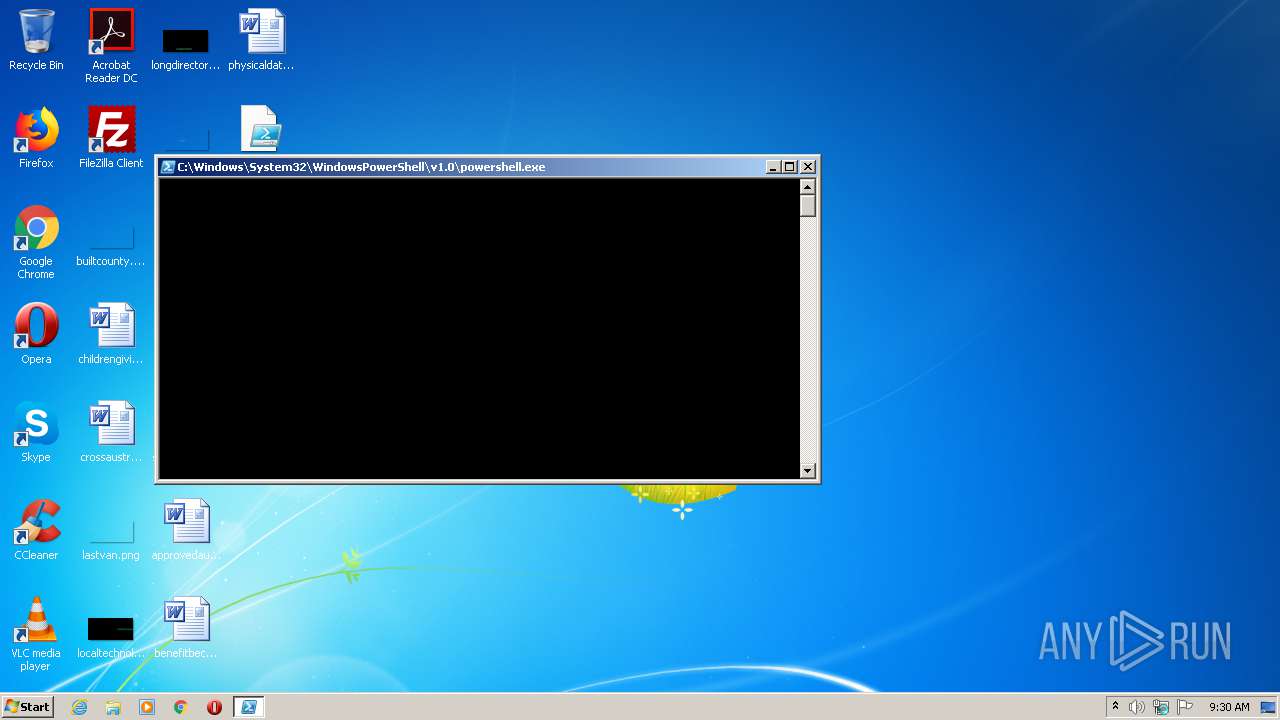
Executes PowerShell scripts
- cmd.exe (PID: 2112)
SUSPICIOUS
Checks for external IP
- InstallUtil.exe (PID: 2988)
Checks supported languages
- InstallUtil.exe (PID: 2988)
Reads Environment values
- InstallUtil.exe (PID: 2988)
Creates files in the user directory
- powershell.exe (PID: 2740)
- powershell.exe (PID: 3308)
PowerShell script executed
- powershell.exe (PID: 2740)
Starts CMD.EXE for commands execution
- InstallUtil.exe (PID: 2988)
INFO
Manual execution by user
- powershell.exe (PID: 2740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:30 08:29:19 |
| ZipCRC: | 0xc25d831c |
| ZipCompressedSize: | 516408 |
| ZipUncompressedSize: | 1870735 |
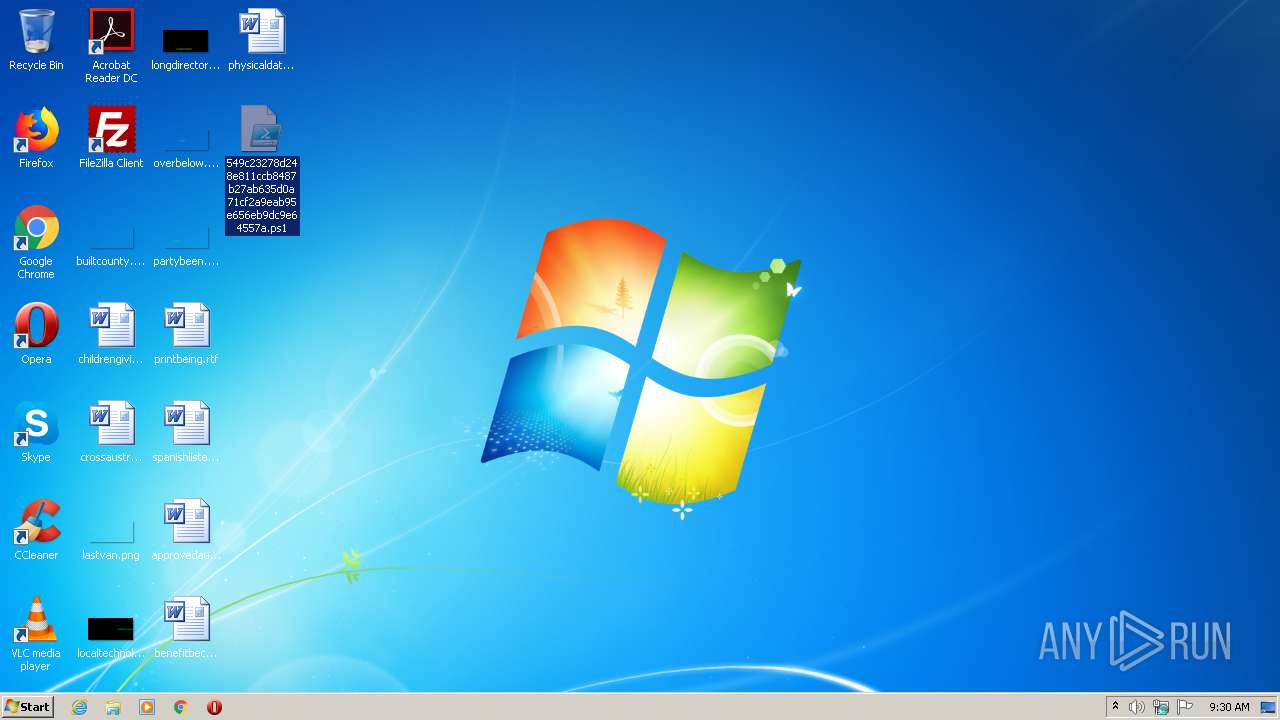
| ZipFileName: | 549c23278d248e811ccb8487b27ab635d0a71cf2a9eab95e656eb9dc9e64557a.ps1 |
Total processes
42
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2112 | "cmd" /c start /b powershell Start-Sleep -Seconds 2; Remove-Item -path 'C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe' & exit | C:\Windows\system32\cmd.exe | — | InstallUtil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
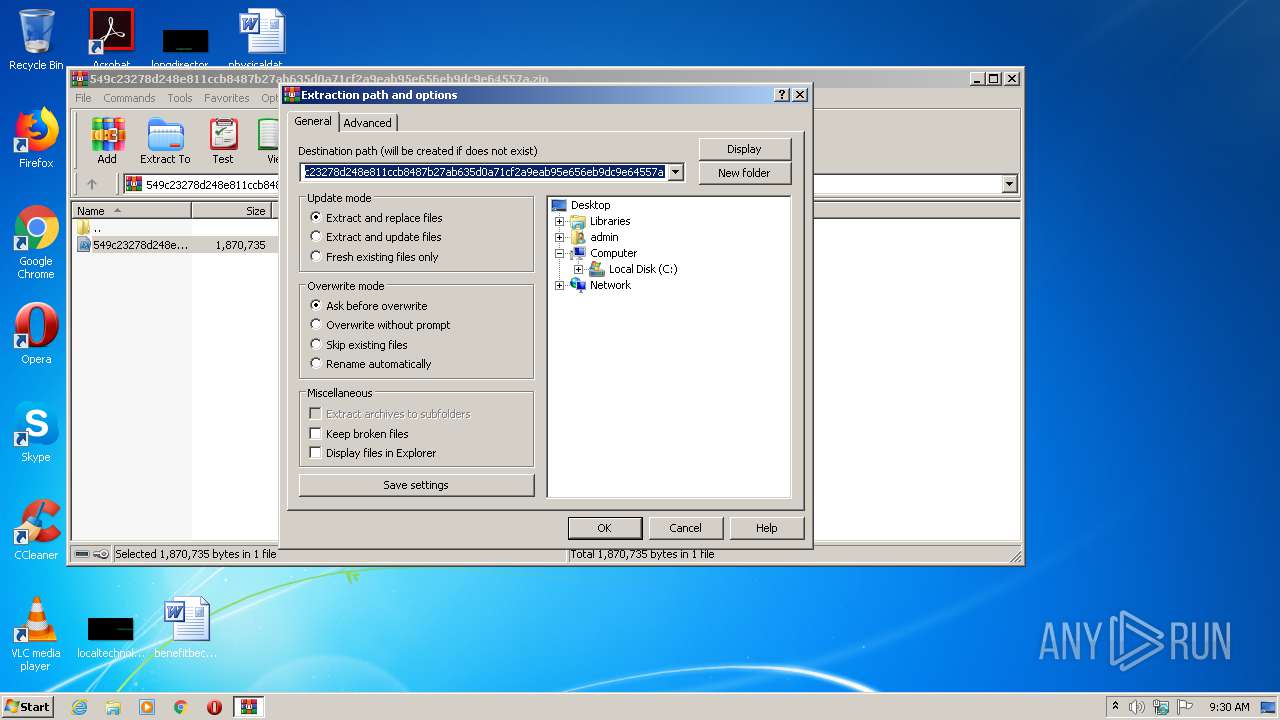
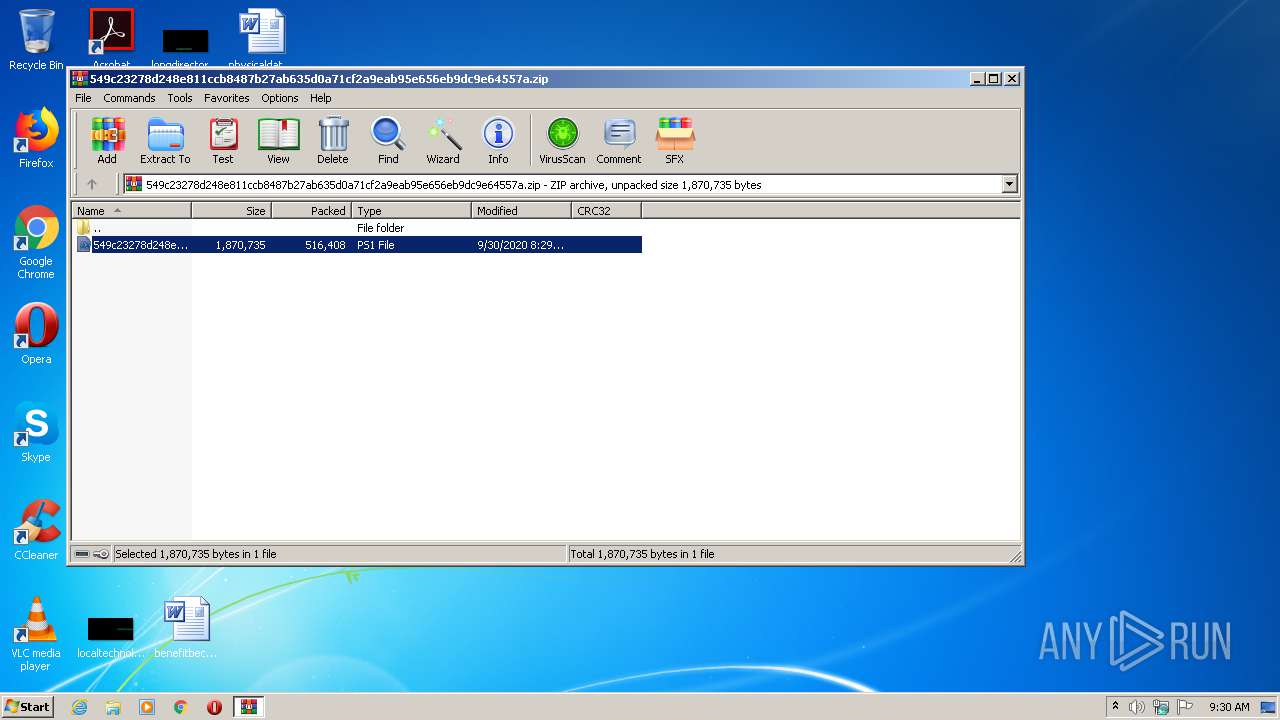
| 2552 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\549c23278d248e811ccb8487b27ab635d0a71cf2a9eab95e656eb9dc9e64557a.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2740 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\549c23278d248e811ccb8487b27ab635d0a71cf2a9eab95e656eb9dc9e64557a.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2988 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3308 | powershell Start-Sleep -Seconds 2; Remove-Item -path 'C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 027
Read events
869
Write events
158
Delete events
0
Modification events
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\549c23278d248e811ccb8487b27ab635d0a71cf2a9eab95e656eb9dc9e64557a.zip | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
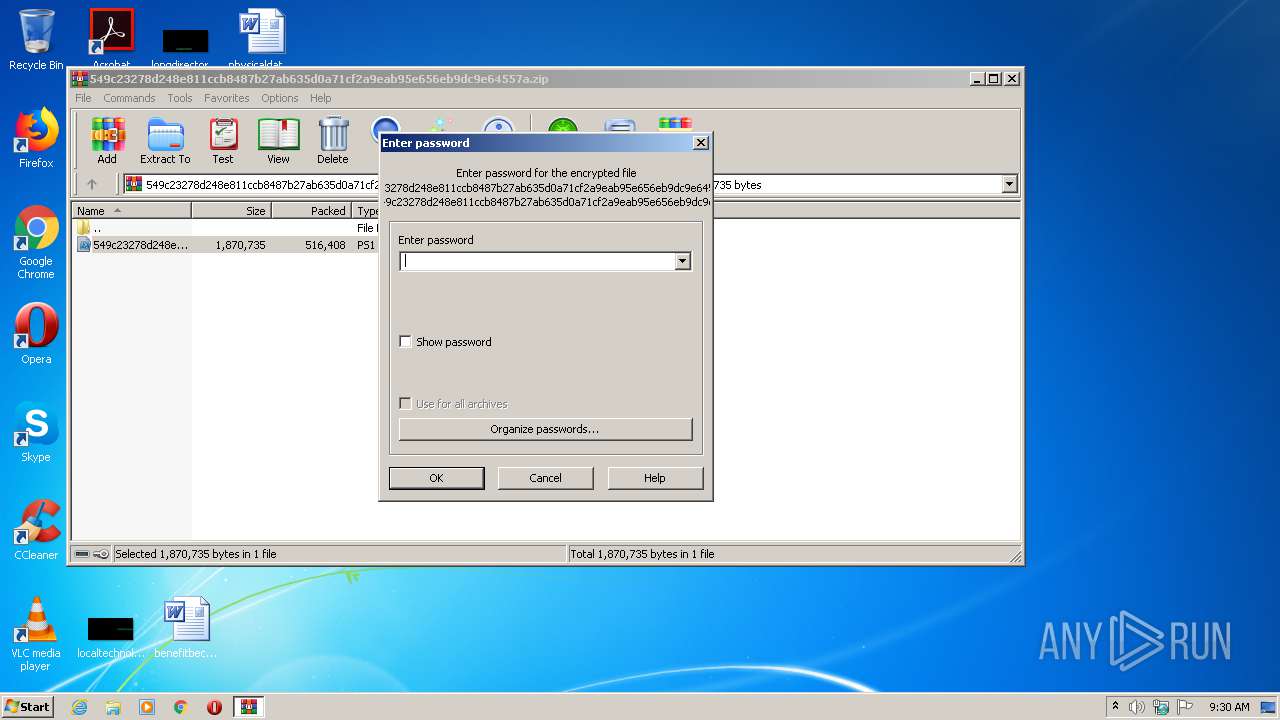
| (PID) Process: | (2552) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OM9YEJFOOJQQEV21P2C4.temp | — | |
MD5:— | SHA256:— | |||
| 2988 | InstallUtil.exe | C:\Users\admin\AppData\Local\D04F4D4D0D\DotNetZip-gqrxvcwf.tmp | — | |
MD5:— | SHA256:— | |||
| 3308 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\89XCPFJDRRYGC99M5VSR.temp | — | |
MD5:— | SHA256:— | |||
| 2552 | WinRAR.exe | C:\Users\admin\Desktop\549c23278d248e811ccb8487b27ab635d0a71cf2a9eab95e656eb9dc9e64557a.ps1 | text | |
MD5:— | SHA256:— | |||
| 2988 | InstallUtil.exe | C:\Users\admin\AppData\Local\D04F4D4D0D\Log.txt | text | |
MD5:— | SHA256:— | |||
| 2740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF22d0c7.TMP | binary | |
MD5:— | SHA256:— | |||
| 3308 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF231f55.TMP | binary | |
MD5:— | SHA256:— | |||
| 3308 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2988 | InstallUtil.exe | C:\Users\admin\AppData\Local\D04F4D4D0D\admin_United States_D04F4D4D0D_09-30-2020 9.30.56.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2988 | InstallUtil.exe | GET | 200 | 54.235.83.248:80 | http://api.ipify.org/ | US | text | 14 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2988 | InstallUtil.exe | 94.127.7.174:21 | milebgd.mycpanel.rs | Serbia BroadBand-Srpske Kablovske mreze d.o.o. | RS | malicious |
2988 | InstallUtil.exe | 64.233.184.108:587 | smtp.gmail.com | Google Inc. | US | whitelisted |
2988 | InstallUtil.exe | 54.235.83.248:80 | api.ipify.org | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
milebgd.mycpanel.rs |
| malicious |
smtp.gmail.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2988 | InstallUtil.exe | Misc activity | SUSPICIOUS [PTsecurity] External IP Lookup (possible MassLogger) |
2988 | InstallUtil.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
2988 | InstallUtil.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2988 | InstallUtil.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |