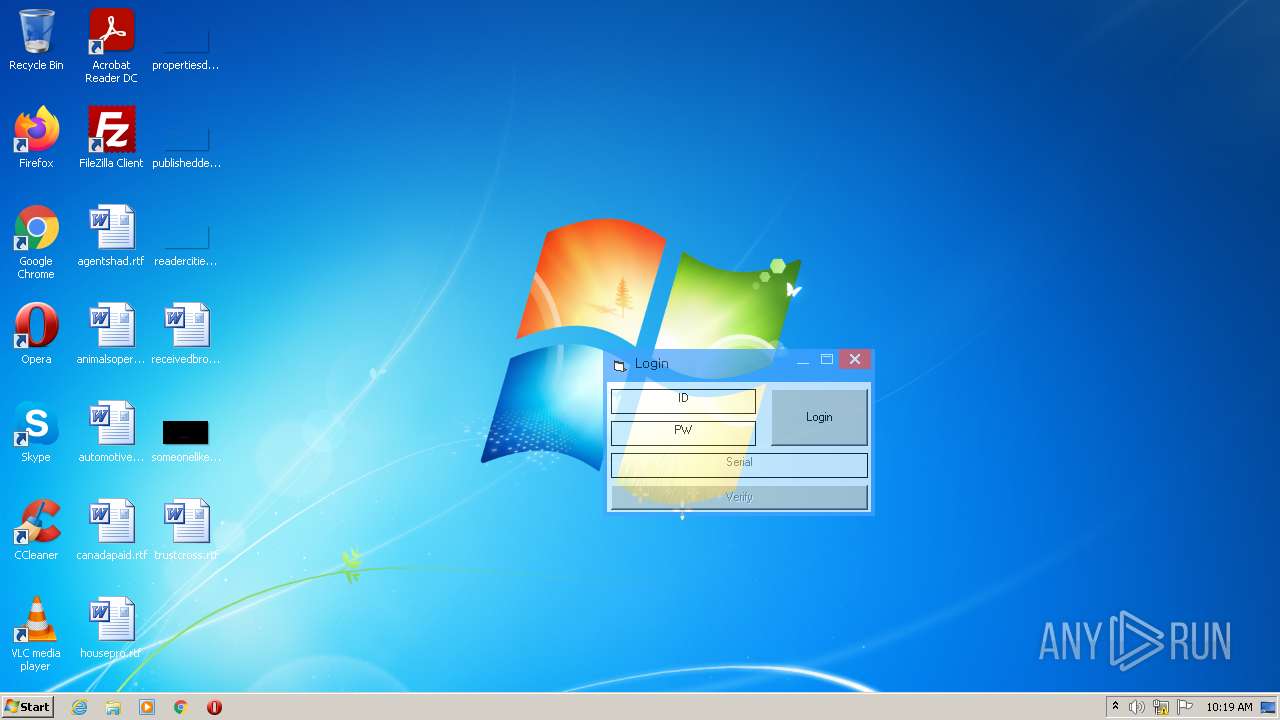
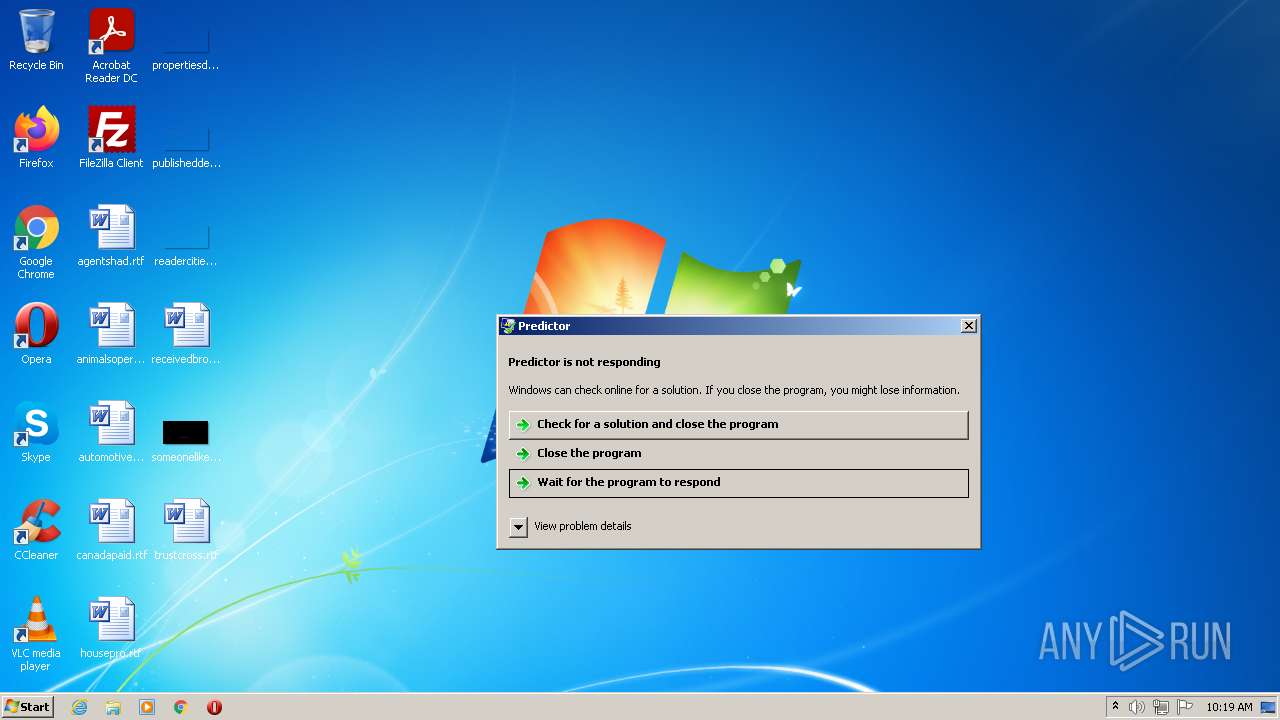
| File name: | Predictor.exe |
| Full analysis: | https://app.any.run/tasks/4352a3f9-c84d-4ce9-b270-06366a12a4c5 |
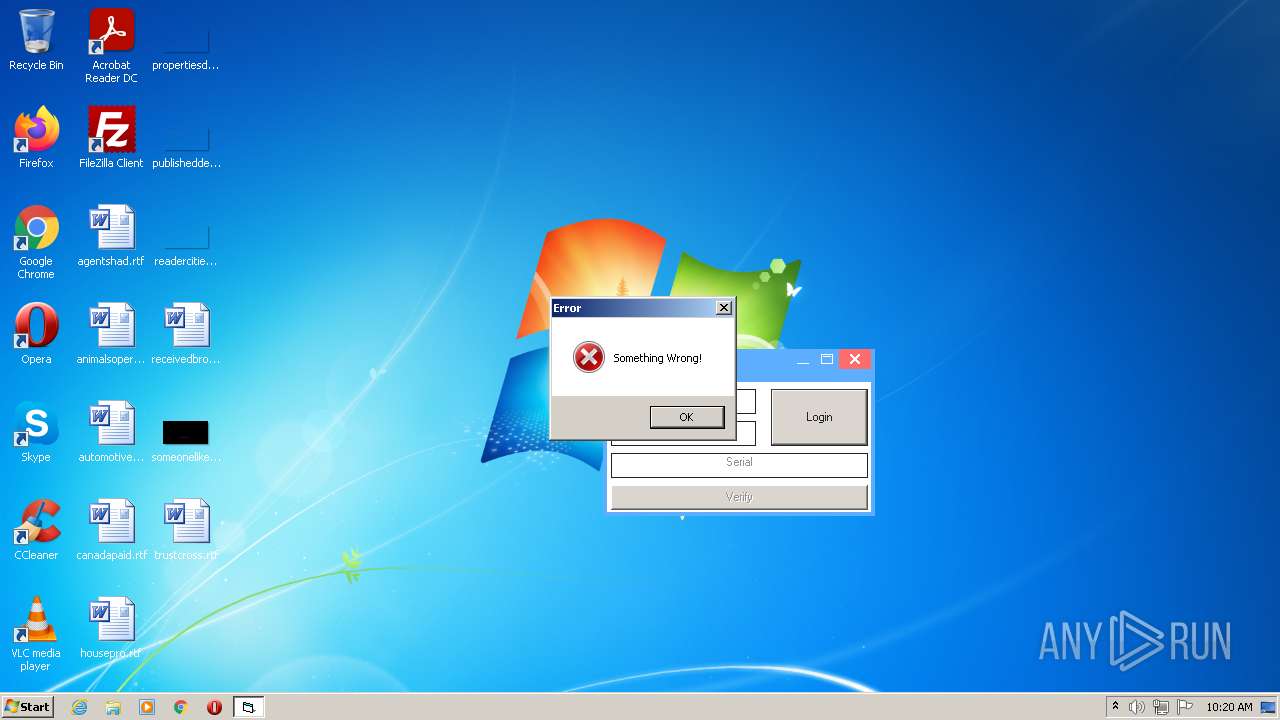
| Verdict: | Malicious activity |
| Analysis date: | June 26, 2022, 09:19:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BB7055CEBC335B6F627EBC9045B238CF |
| SHA1: | A2AD9BC8D795A020A5FB9CB7486A4B3F73A12512 |
| SHA256: | FB15506041438117E04A494886349F801230ABFAE1729412A916F1AD69A0290C |
| SSDEEP: | 768:HW8x2MH/HD8tB87EuwwI0L1+JqDVR3iaFA9qzDASl7ZsC0zEOVSggZ23AQlVh5br:f8MfjsB87EuwwIC1nDVRSZZw7Ztm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- Predictor.exe (PID: 2992)
Reads the computer name
- Predictor.exe (PID: 2992)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (90.6) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| OriginalFileName: | Predictor.exe |
|---|---|
| InternalName: | Predictor |
| ProductVersion: | 1.02.0007 |
| FileVersion: | 1.02.0007 |
| ProductName: | Predictor |
| CompanyName: | Telegram: @bustako7 |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.2.0.7 |
| FileVersionNumber: | 1.2.0.7 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1.2 |
| OSVersion: | 4 |
| EntryPoint: | 0x1734 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 12288 |
| CodeSize: | 73728 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2022:01:13 15:44:08+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jan-2022 14:44:08 |
| Detected languages: |
|
| CompanyName: | Telegram: @bustako7 |
| ProductName: | Predictor |
| FileVersion: | 1.02.0007 |
| ProductVersion: | 1.02.0007 |
| InternalName: | Predictor |
| OriginalFilename: | Predictor.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 13-Jan-2022 14:44:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00011994 | 0x00012000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.46135 |
.data | 0x00013000 | 0x00001C4C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00015000 | 0x000008FC | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.9824 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.29721 | 572 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 2.57965 | 304 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 1.76987 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 2.07177 | 296 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
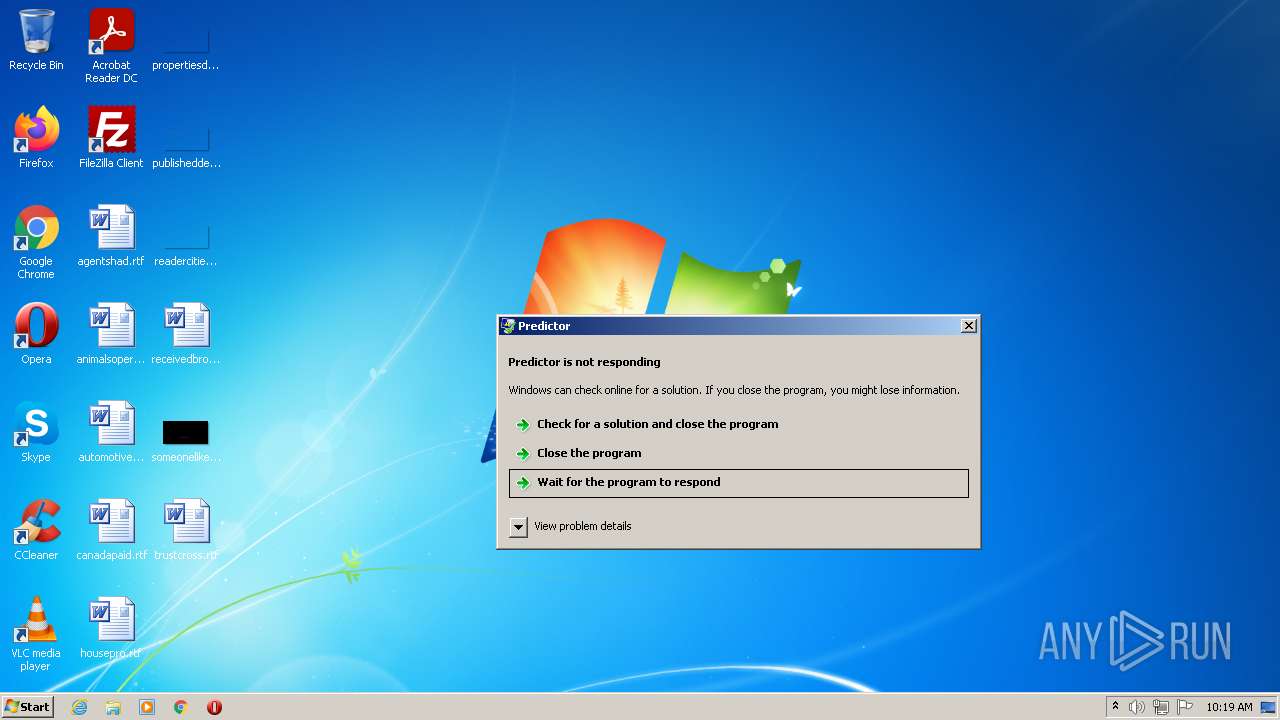
Total processes
36
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2992 | "C:\Users\admin\AppData\Local\Temp\Predictor.exe" | C:\Users\admin\AppData\Local\Temp\Predictor.exe | Explorer.EXE | ||||||||||||
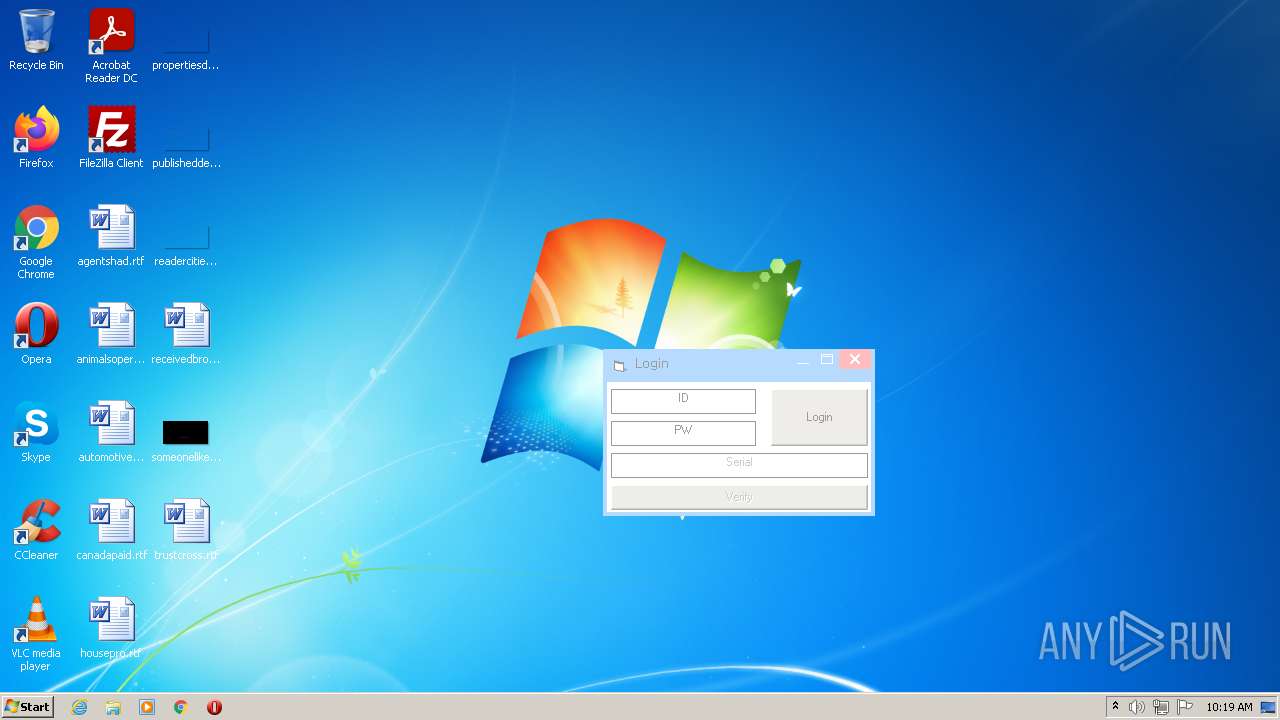
User: admin Company: Telegram: @bustako7 Integrity Level: MEDIUM Exit code: 0 Version: 1.02.0007 Modules
| |||||||||||||||
Total events
279
Read events
270
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionTime |
Value: 9832AAD03D89D801 | |||
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecision |
Value: 0 | |||
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadNetworkName |
Value: Network 4 | |||
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | write | Name: | WpadDecisionTime |
Value: 9832AAD03D89D801 | |||
| (PID) Process: | (2992) Predictor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\52-54-00-36-3e-ff |
| Operation: | write | Name: | WpadDecision |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | Predictor.exe | C:\Users\admin\AppData\Local\VirtualStore\info.ini | text | |
MD5:37E212CD25A63D81F56B41E0C4FBF81A | SHA256:78E0E0AA93273F1A40C0D50F59FD8DF2F675F18F07F5FCBC05A711F7D6E6DAAE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
17
DNS requests
1
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
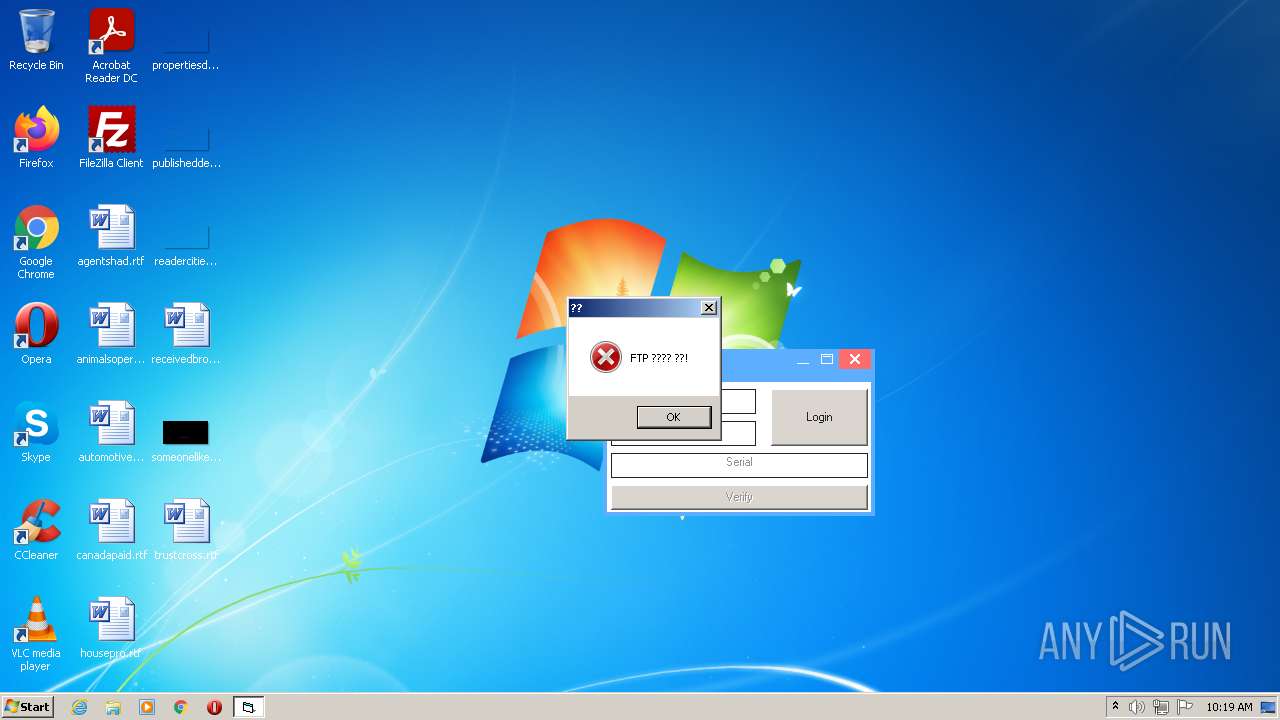
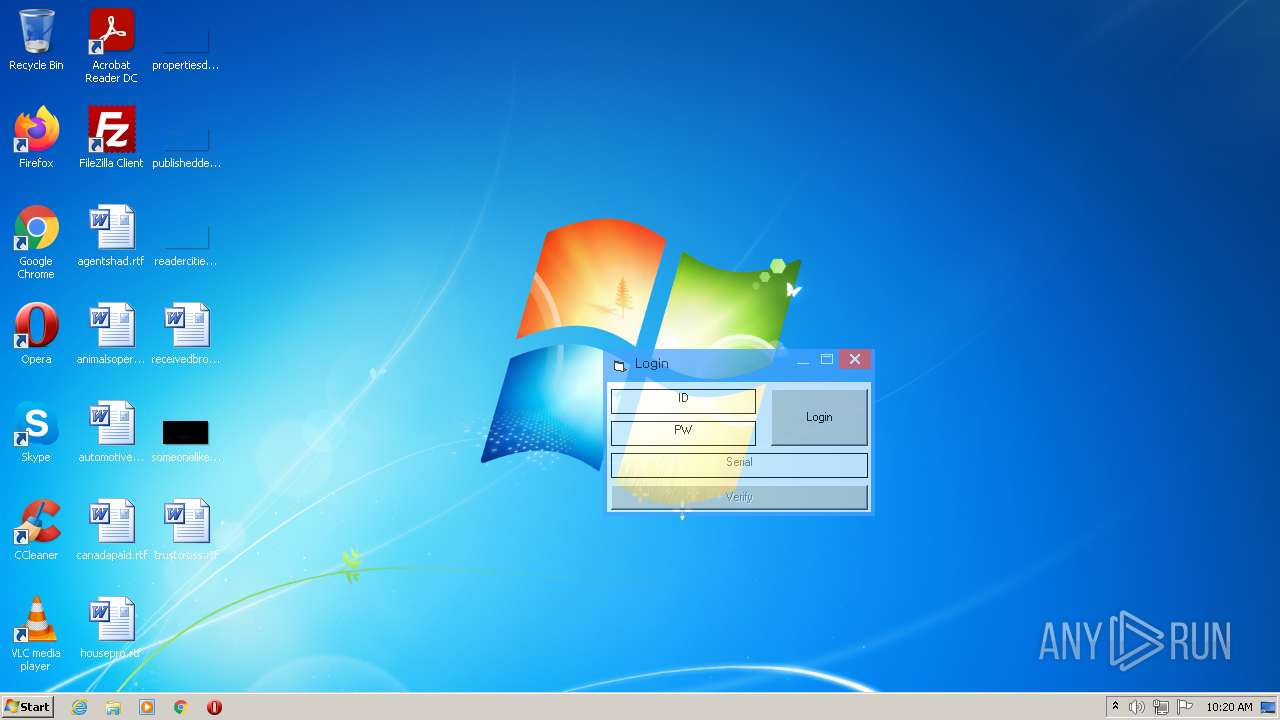
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/serial.txt | KR | text | 32 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
2992 | Predictor.exe | GET | 200 | 112.175.184.77:80 | http://bustabit.dothome.co.kr/bustabit.txt | KR | text | 3 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2992 | Predictor.exe | 112.175.184.77:80 | bustabit.dothome.co.kr | Korea Telecom | KR | malicious |
2992 | Predictor.exe | 112.175.184.77:21 | bustabit.dothome.co.kr | Korea Telecom | KR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bustabit.dothome.co.kr |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2992 | Predictor.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2992 | Predictor.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |