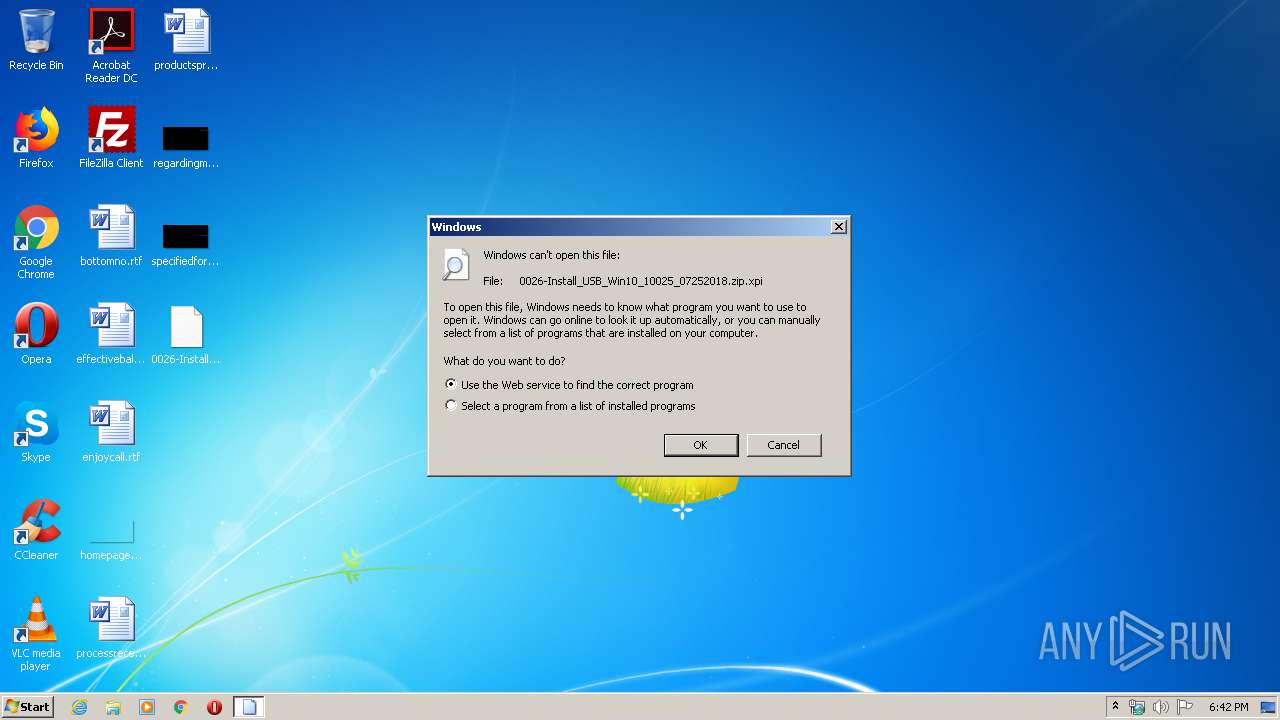
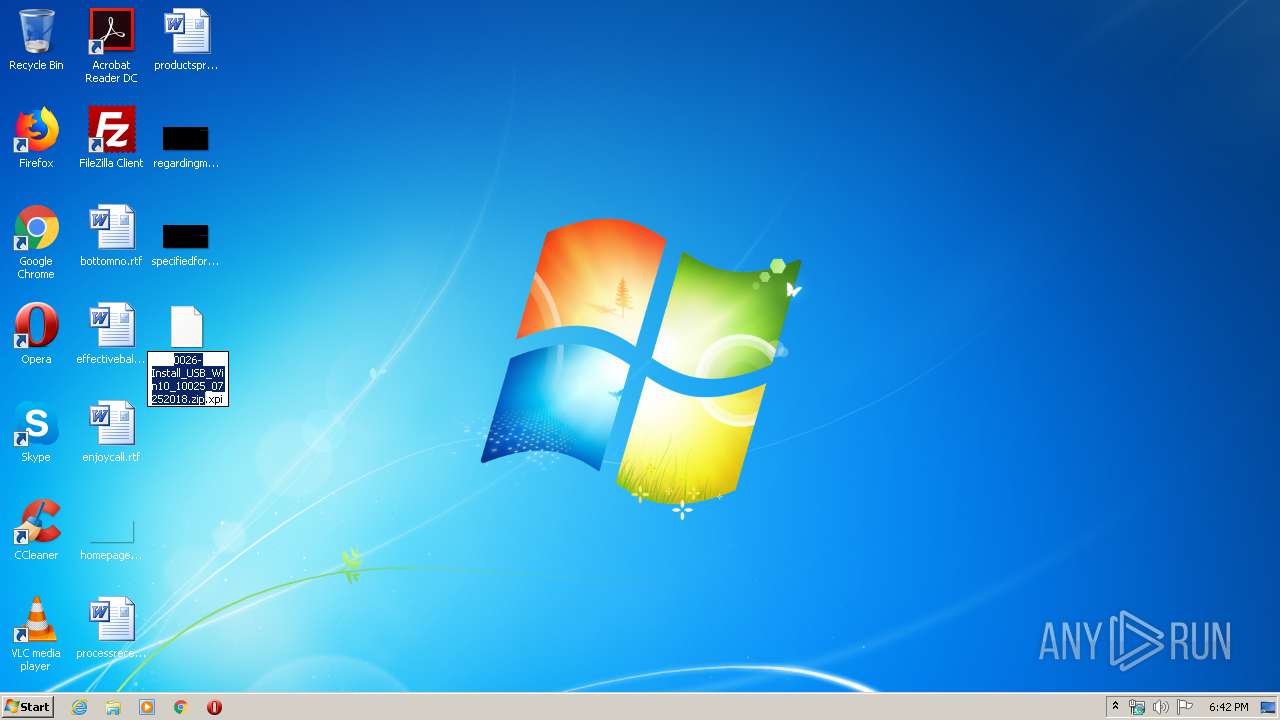
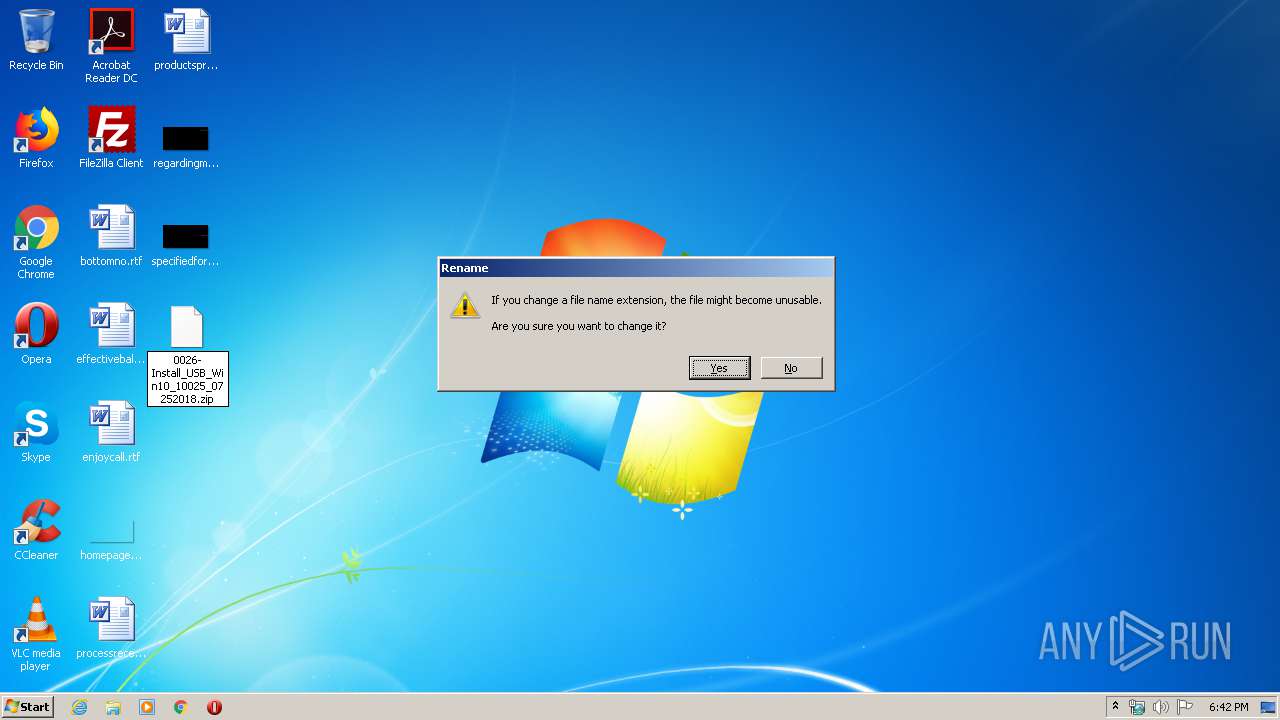
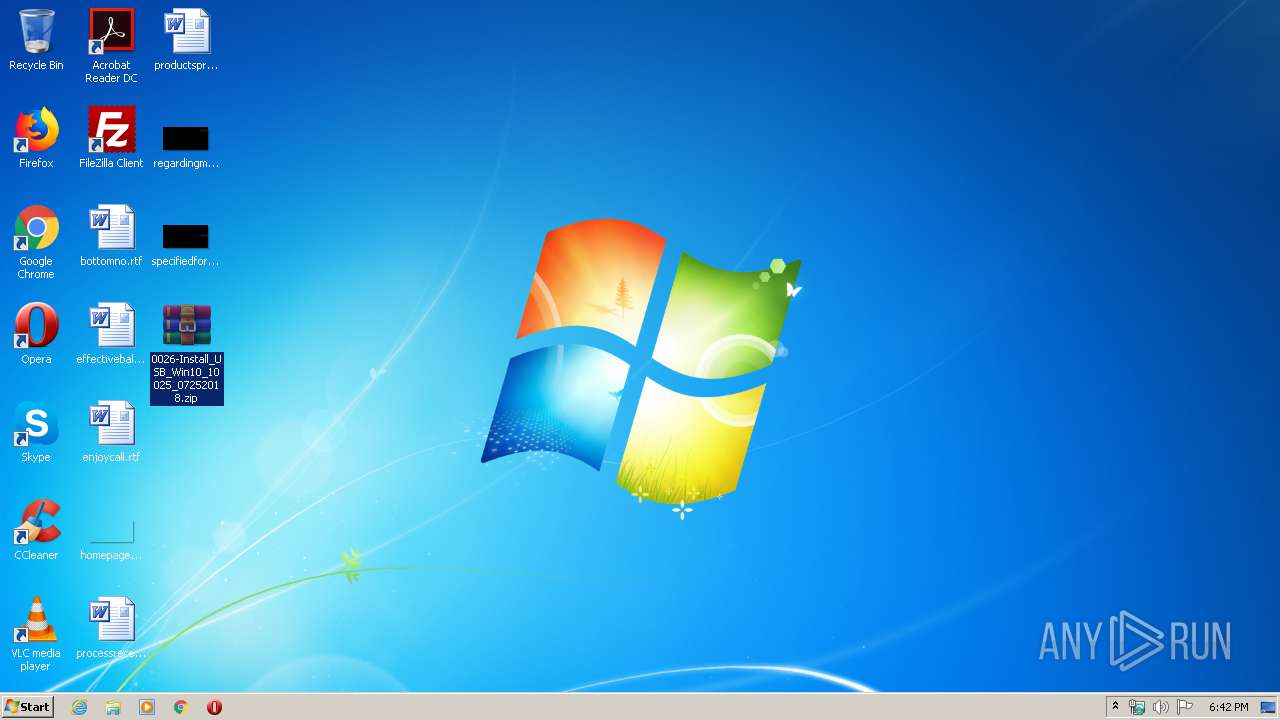
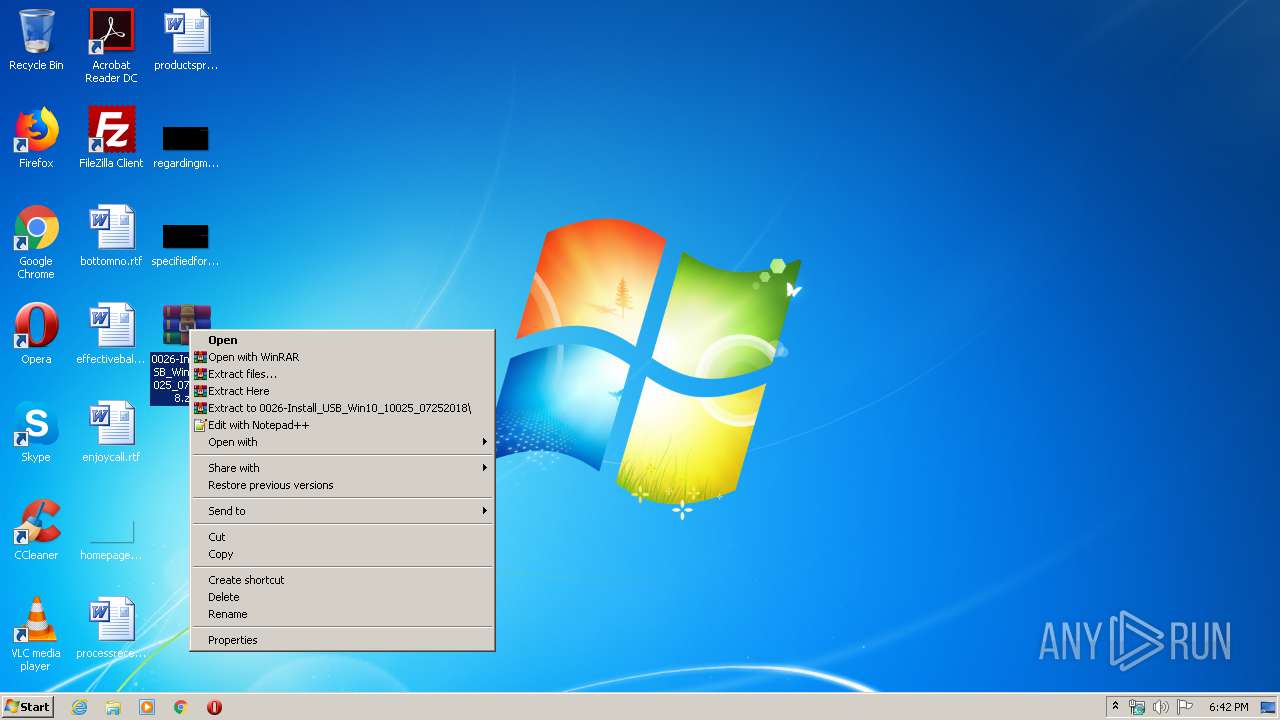
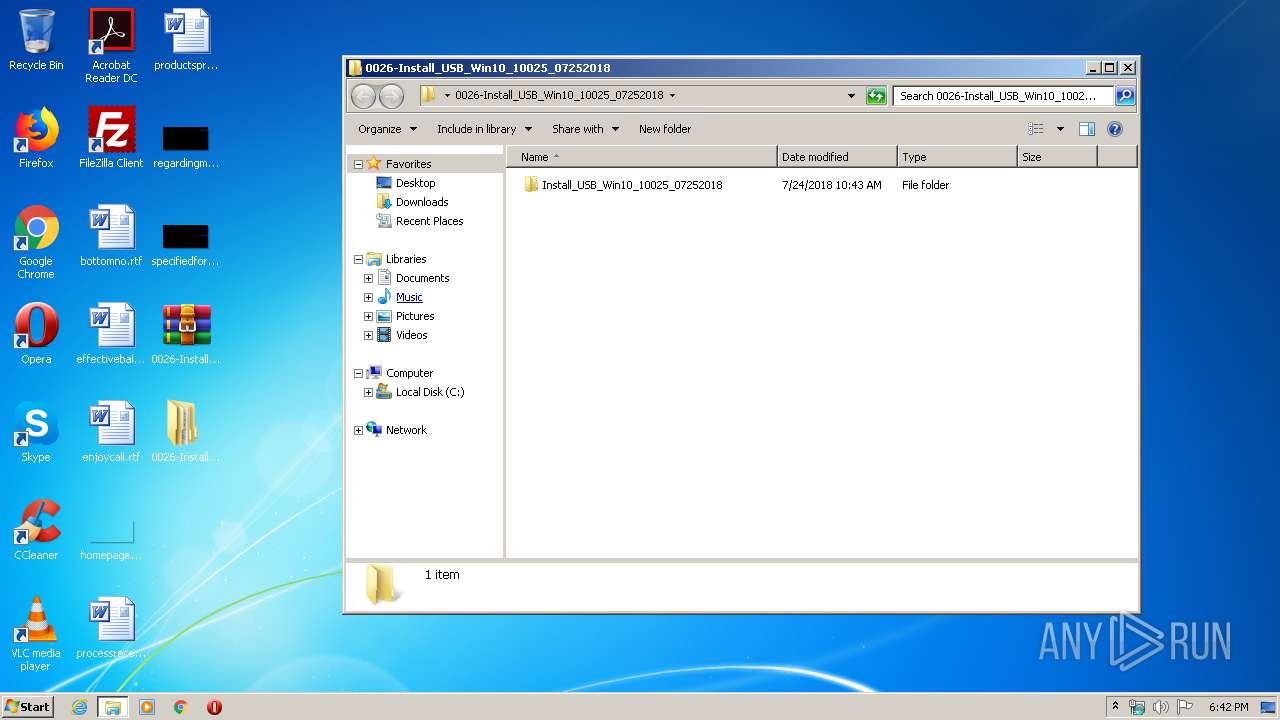
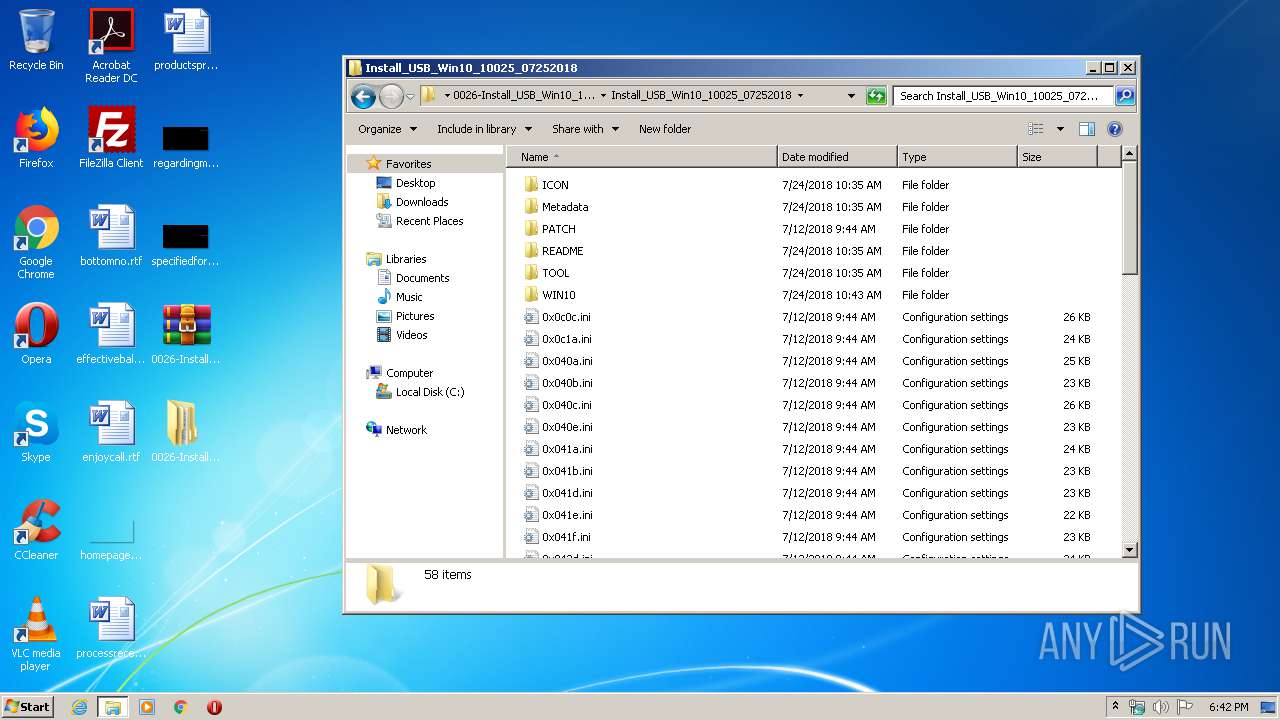
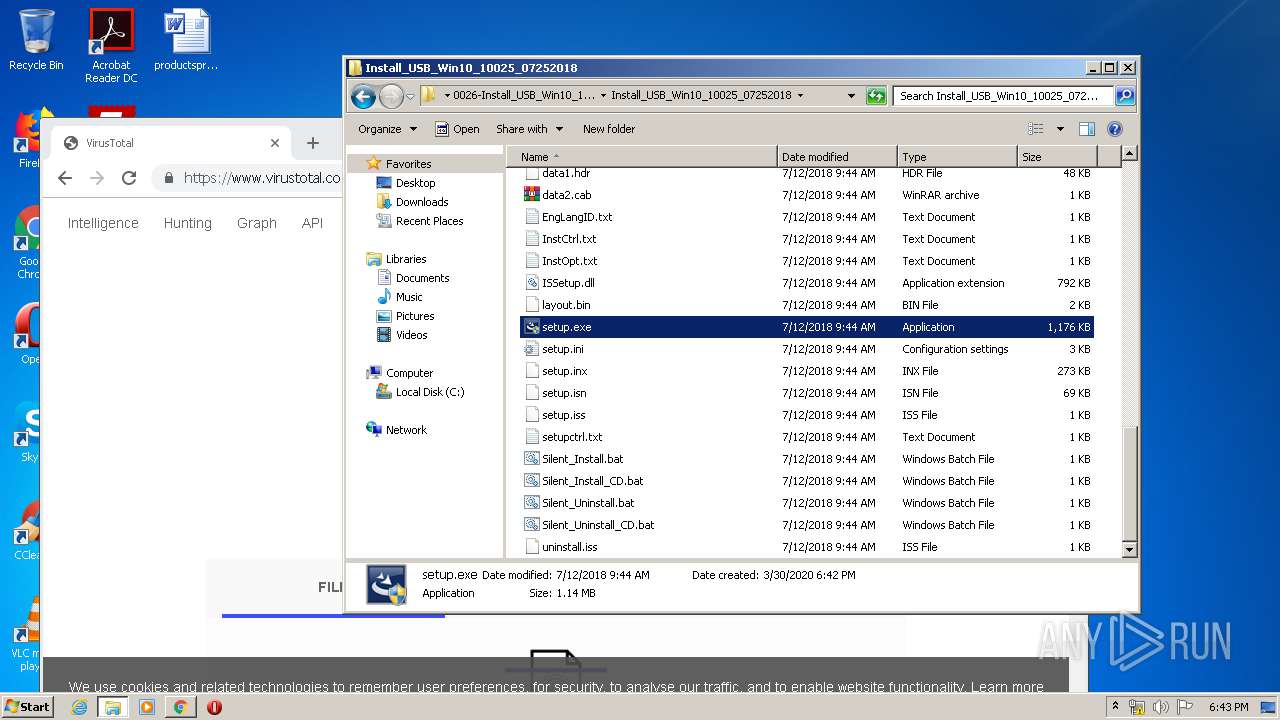
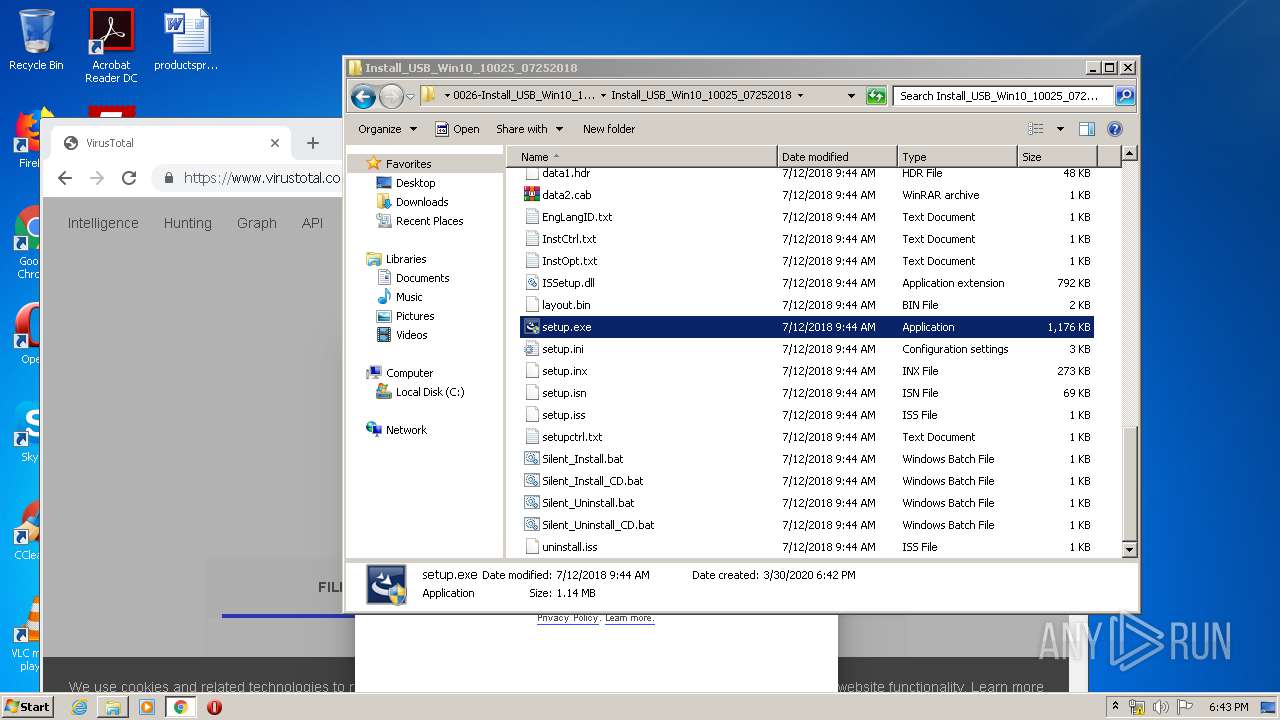
| download: | 0026-Install_USB_Win10_10025_07252018.zip |
| Full analysis: | https://app.any.run/tasks/ebf4a92f-c1f0-4098-9b40-5d12735d2f05 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 17:41:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9F9F539BD5ED654DB7FD2B2CC9B8A78D |
| SHA1: | 8D7B9F5F1B20287EF1D1D53996AA4109C6184D25 |
| SHA256: | FB04DE3316AB31E74250207DDCF4B6133733DA297573C88438F66CA022149D84 |
| SSDEEP: | 196608:NV6JCLCJbgQFKfXScvhh7oq0Ci5ua7tovRD43:NVUgQ2CcvvxhUv7ti43 |
MALICIOUS
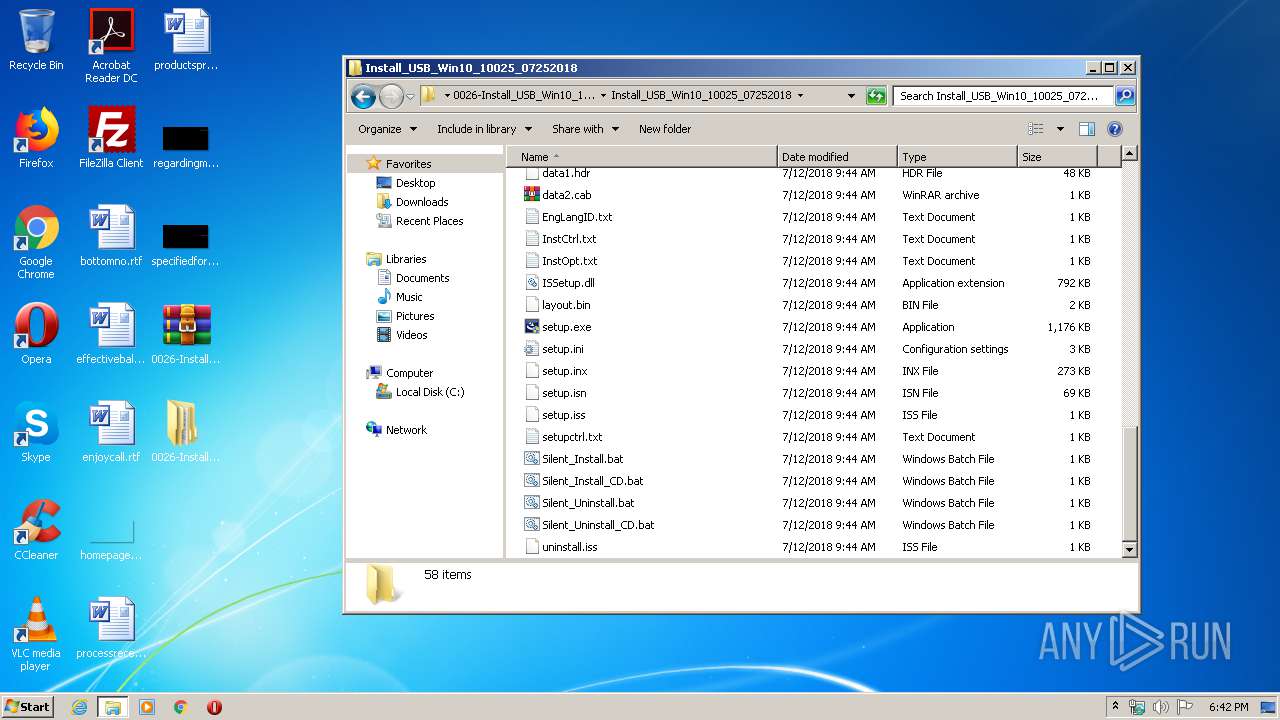
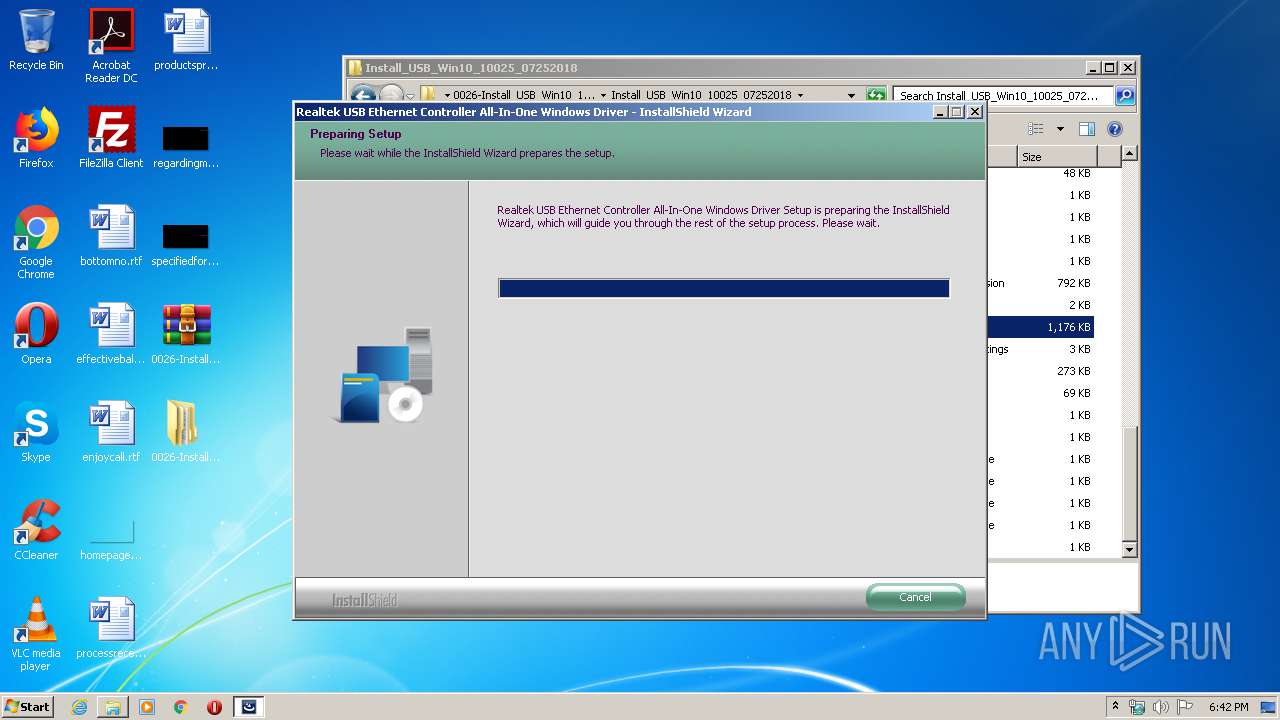
Loads dropped or rewritten executable
- setup.exe (PID: 1064)
- SearchProtocolHost.exe (PID: 3548)
Application was dropped or rewritten from another process
- setup.exe (PID: 1064)
- setup.exe (PID: 2456)
SUSPICIOUS
Starts Internet Explorer
- rundll32.exe (PID: 676)
Executed as Windows Service
- vssvc.exe (PID: 2628)
Executable content was dropped or overwritten
- setup.exe (PID: 1064)
- WinRAR.exe (PID: 3916)
Searches for installed software
- setup.exe (PID: 1064)
Creates files in the program directory
- setup.exe (PID: 1064)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3016)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2424)
- iexplore.exe (PID: 3872)
Changes internet zones settings
- iexplore.exe (PID: 2424)
Reads internet explorer settings
- iexplore.exe (PID: 3872)
Creates files in the user directory
- iexplore.exe (PID: 3872)
Reads settings of System Certificates
- iexplore.exe (PID: 2424)
- chrome.exe (PID: 2768)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2628)
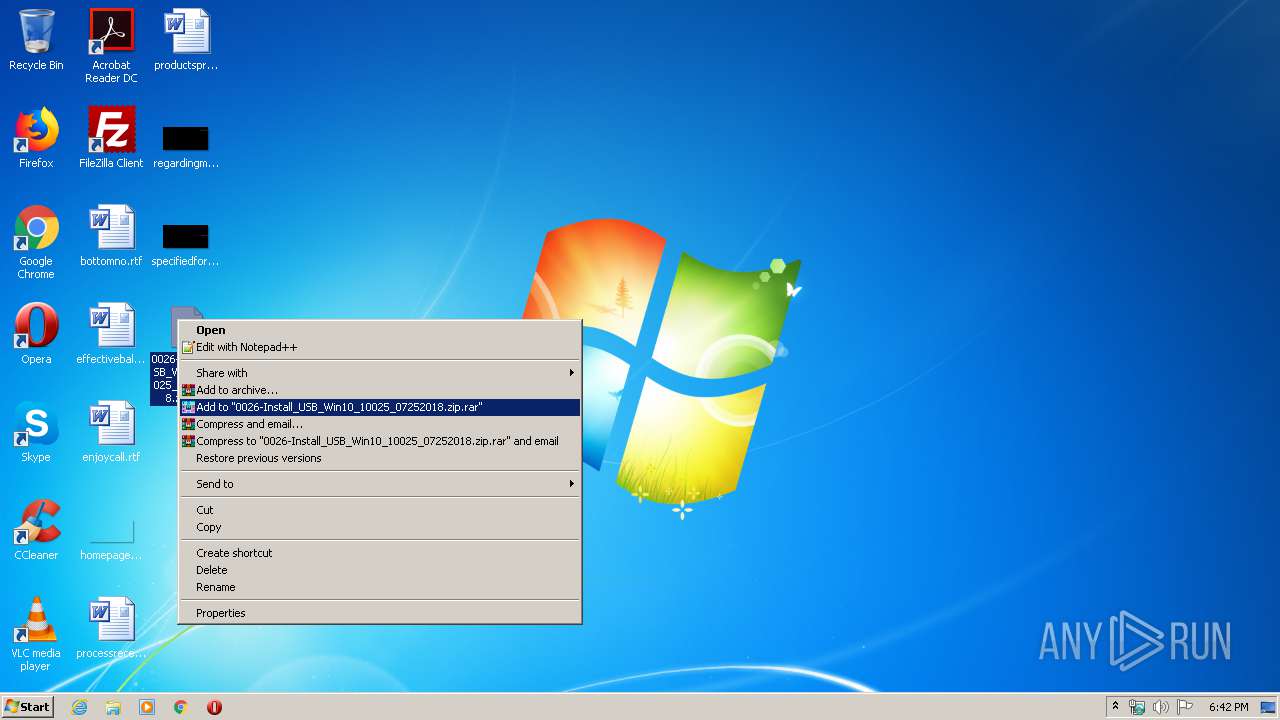
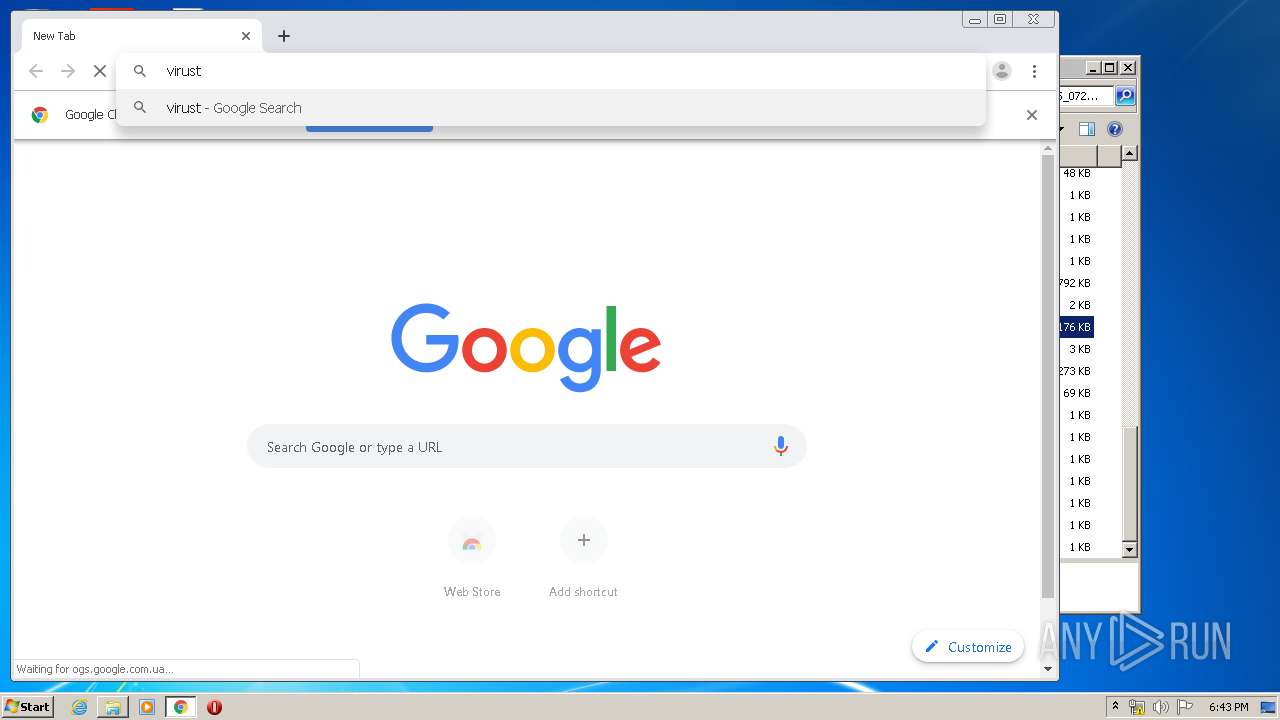
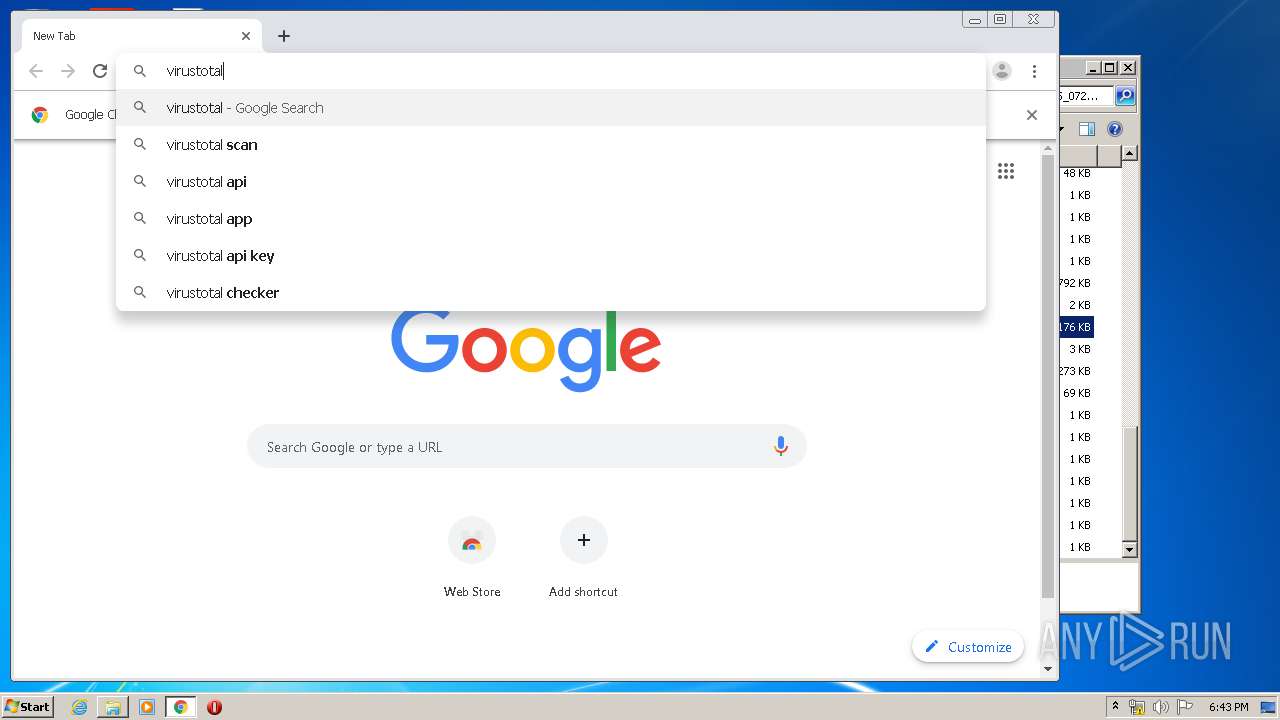
Manual execution by user
- chrome.exe (PID: 3016)
- WinRAR.exe (PID: 3916)
- setup.exe (PID: 1064)
- setup.exe (PID: 2456)
Reads the hosts file
- chrome.exe (PID: 2768)
- chrome.exe (PID: 3016)
Application launched itself
- chrome.exe (PID: 3016)
Changes settings of System certificates
- iexplore.exe (PID: 2424)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:07:24 17:43:02 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Install_USB_Win10_10025_07252018/ |
Total processes
86
Monitored processes
40
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8185848539738352251,17075428498448941858,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9194985572639021683 --mojo-platform-channel-handle=3704 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8185848539738352251,17075428498448941858,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3334890344511662001 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\0026-Install_USB_Win10_10025_07252018.zip.xpi | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
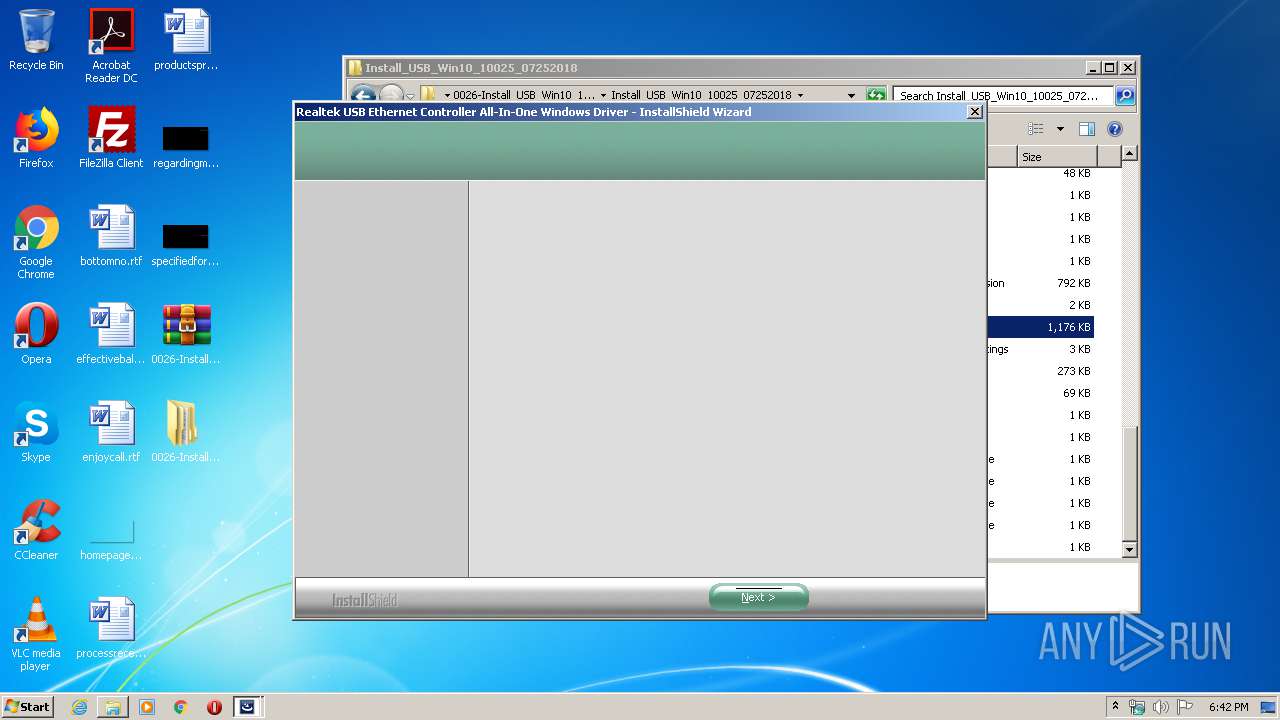
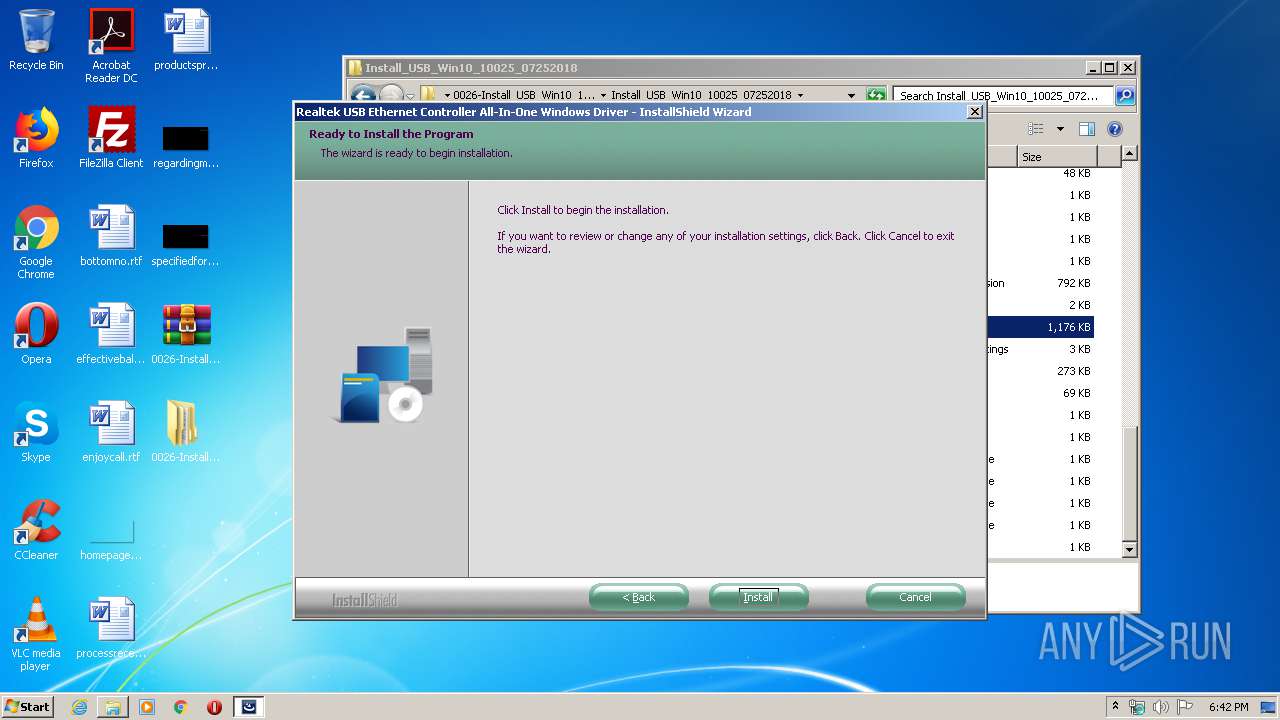
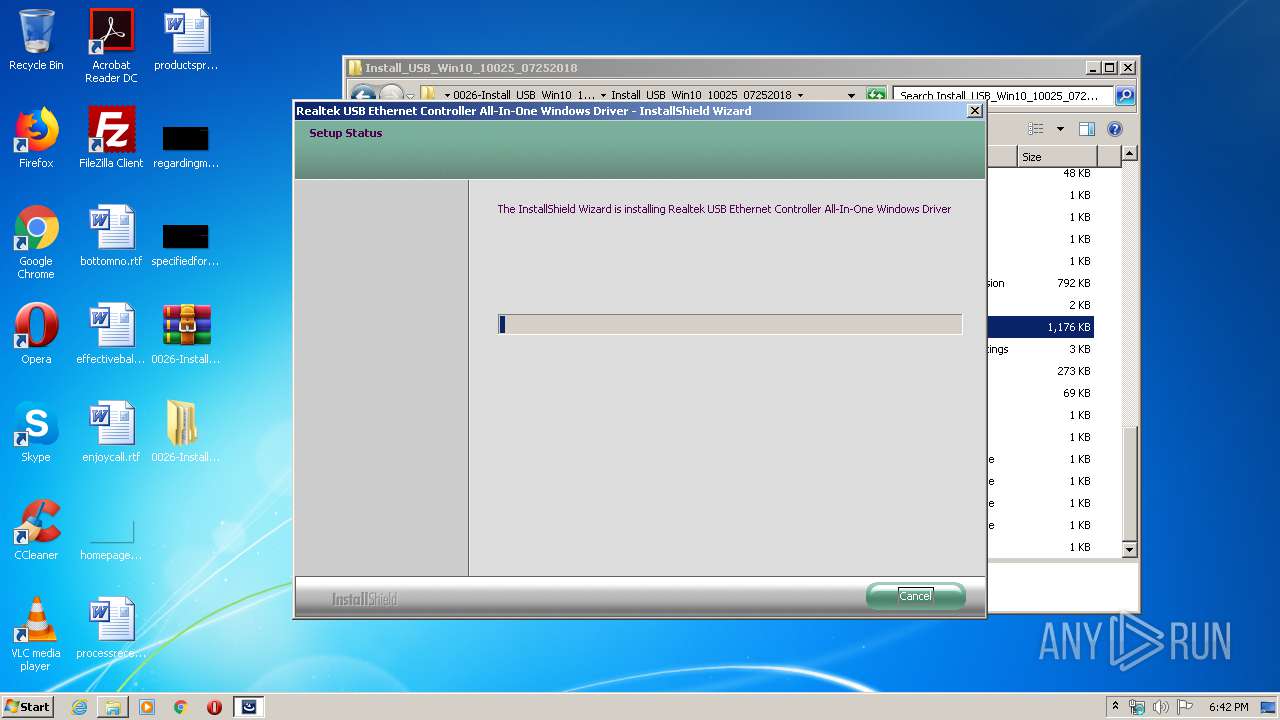
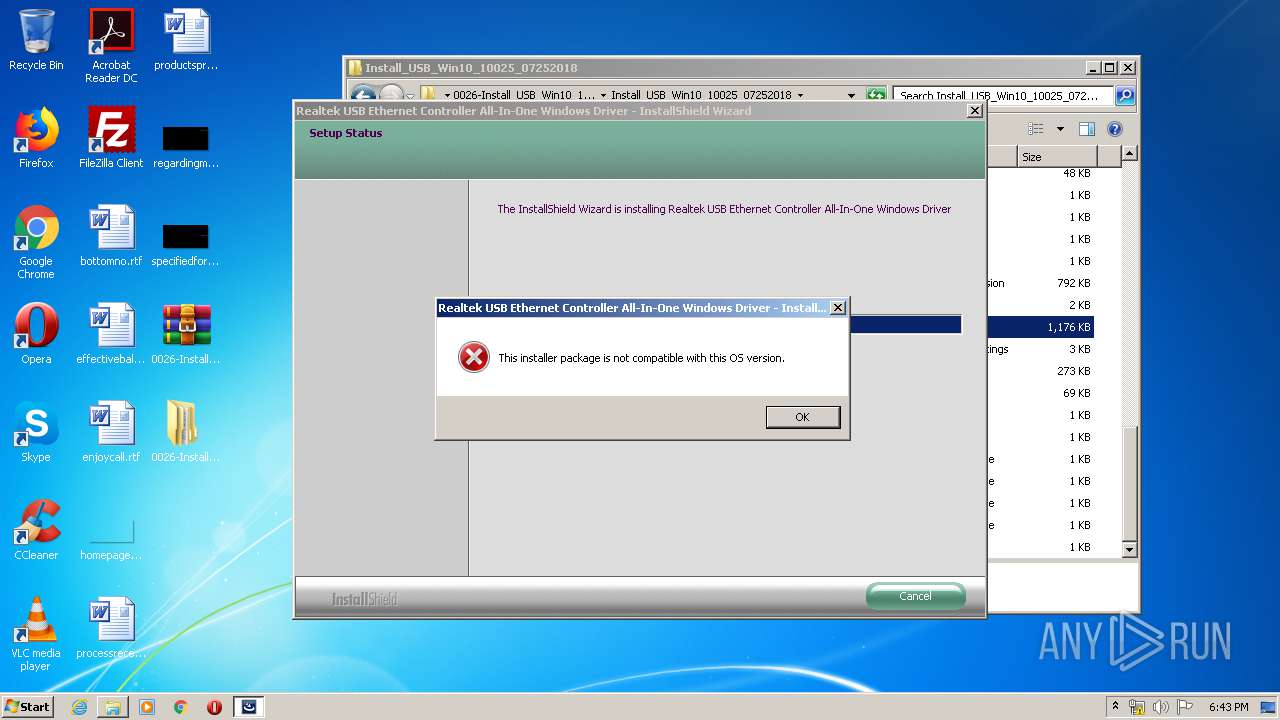
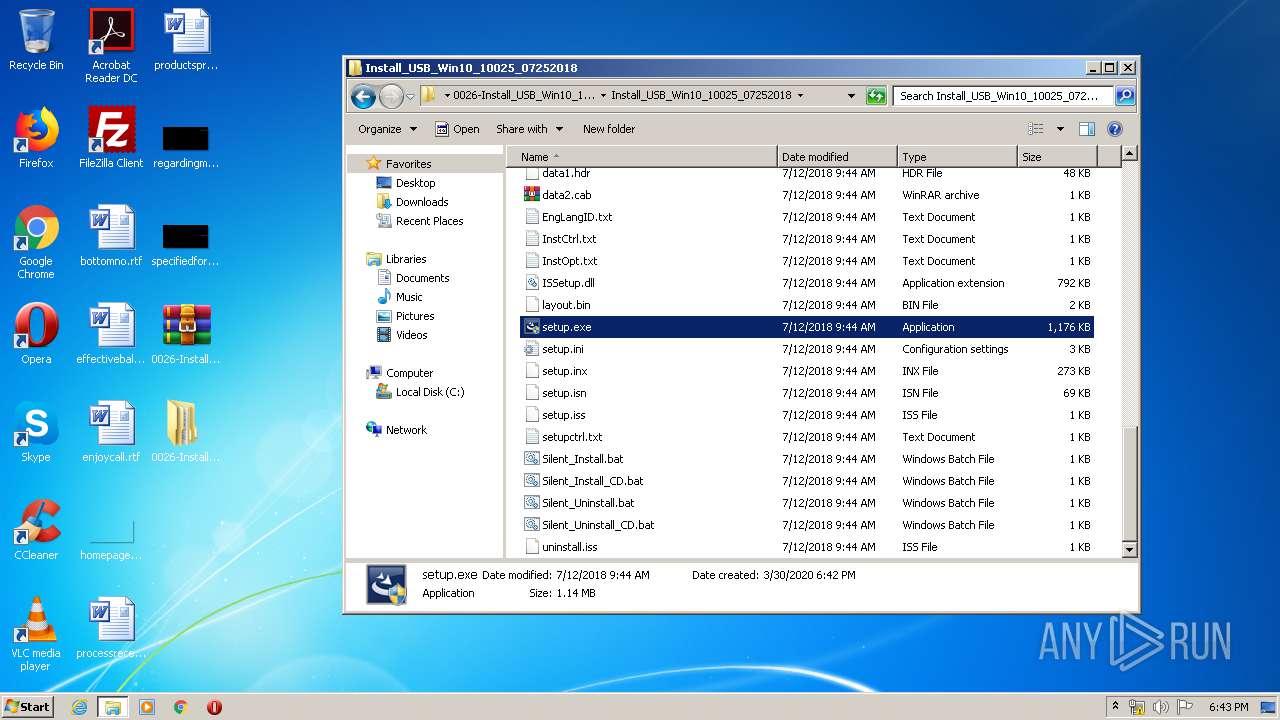
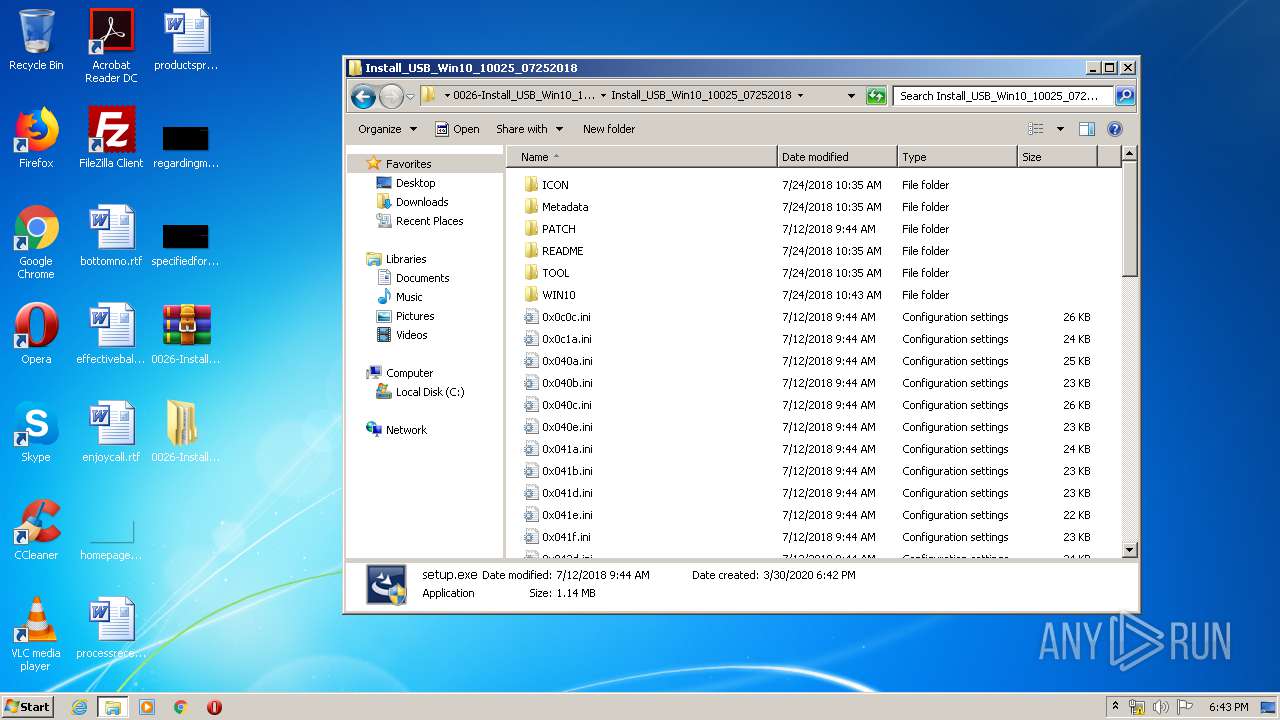
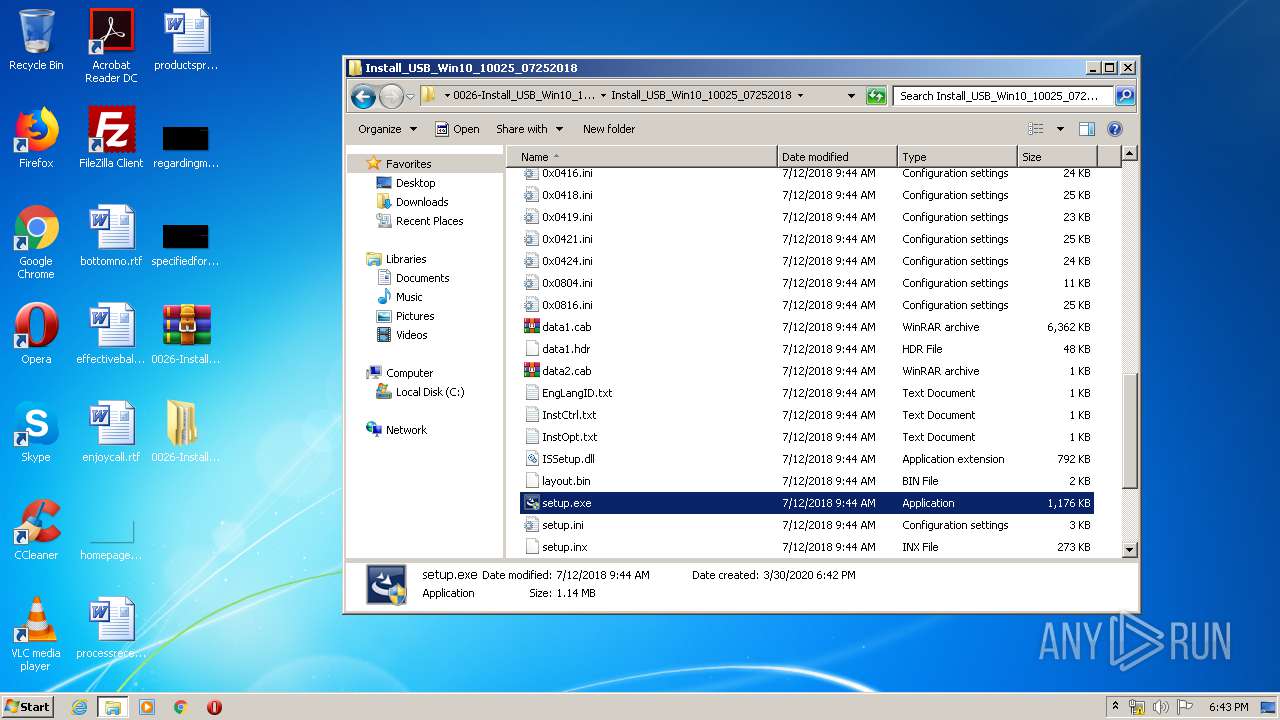
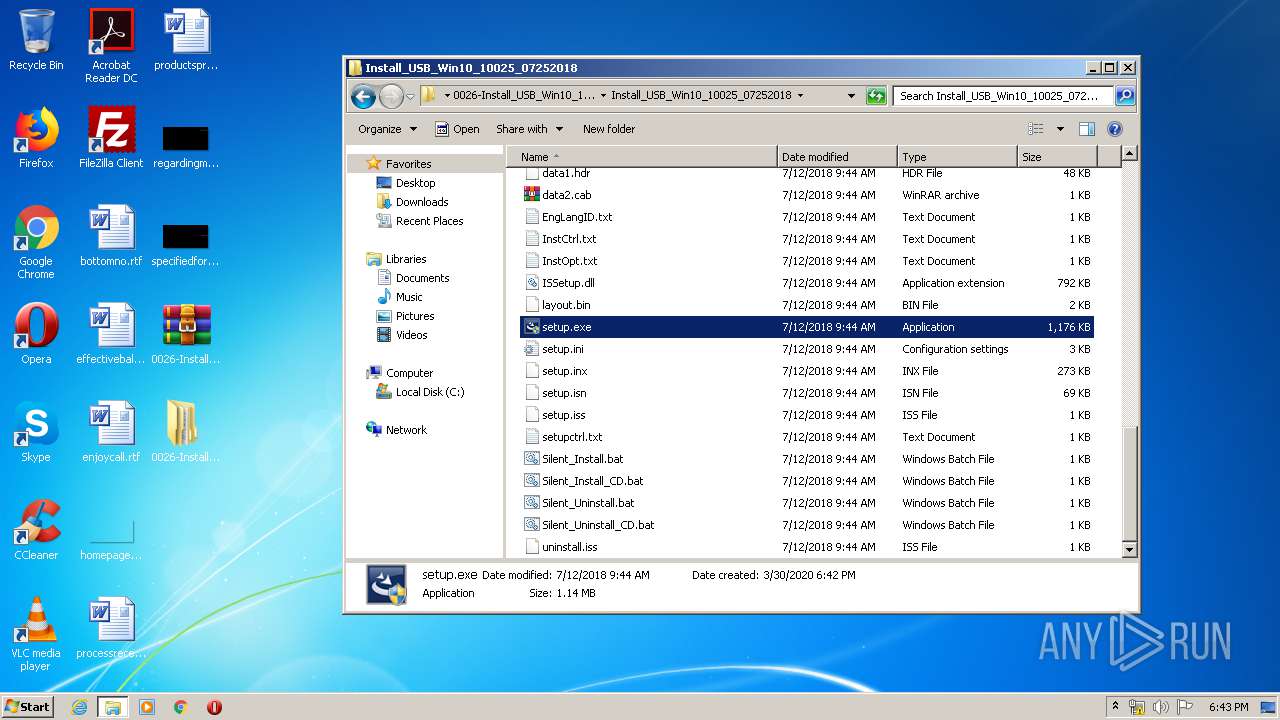
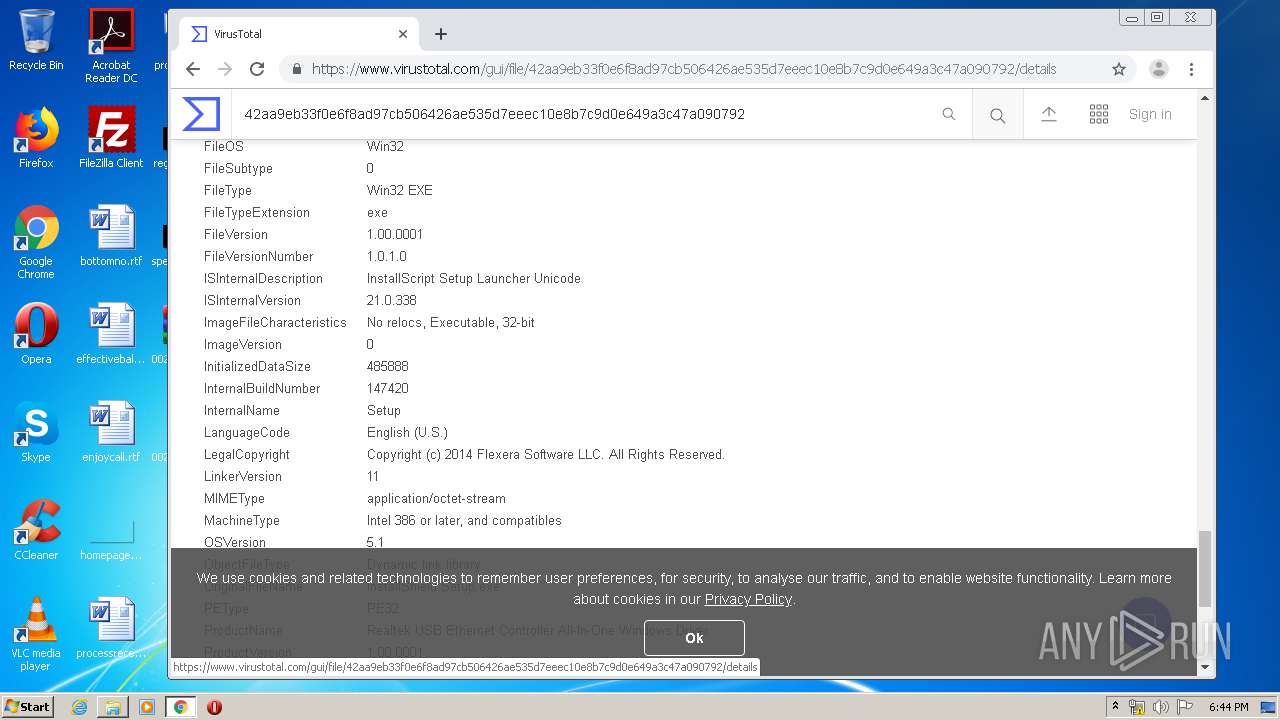
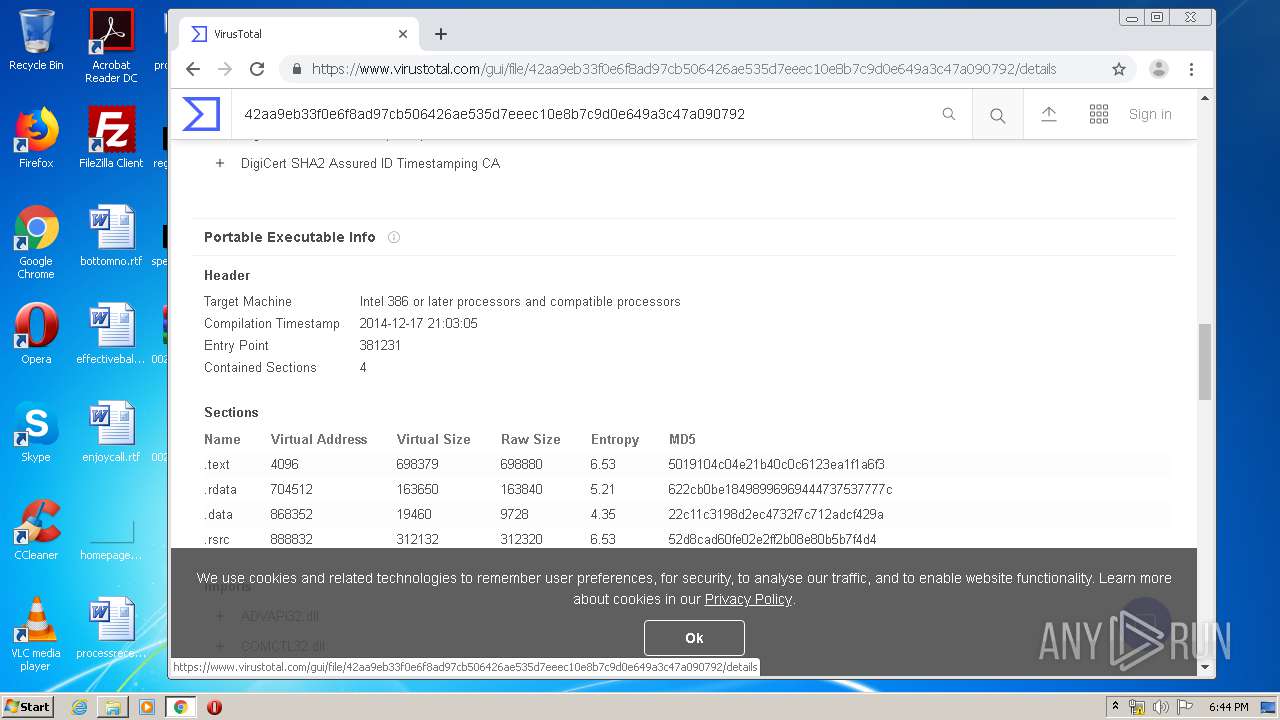
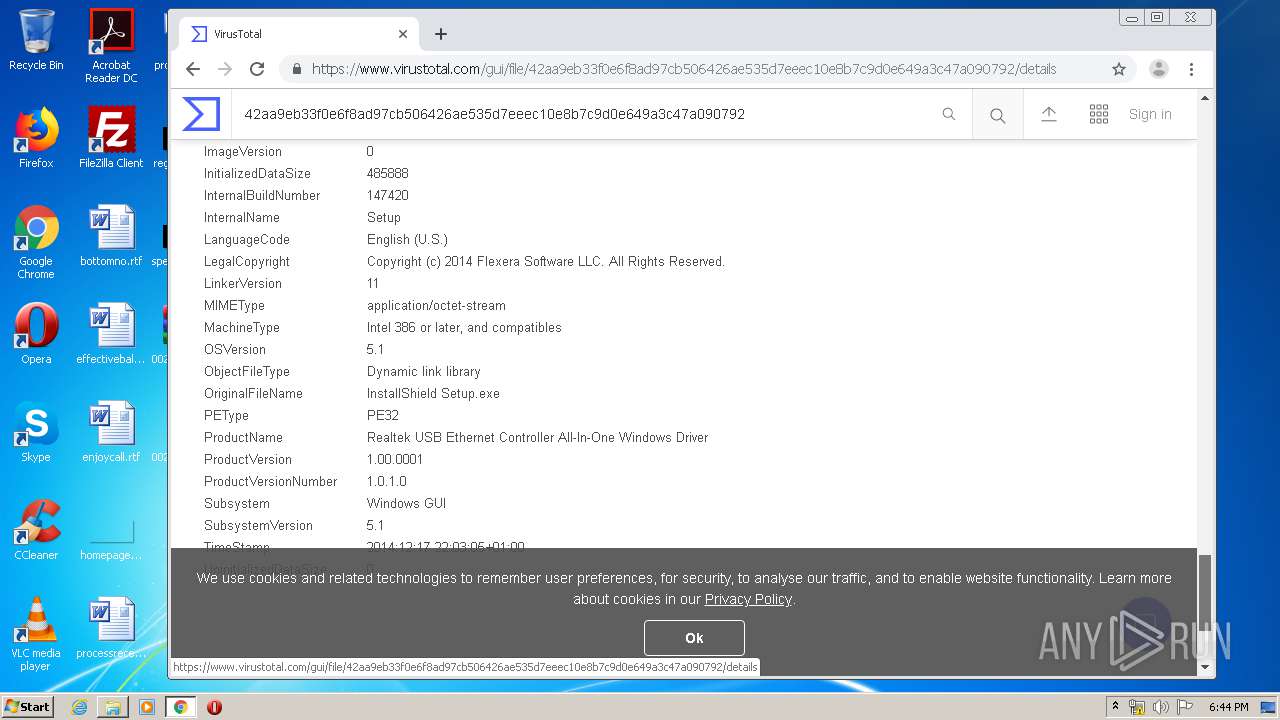
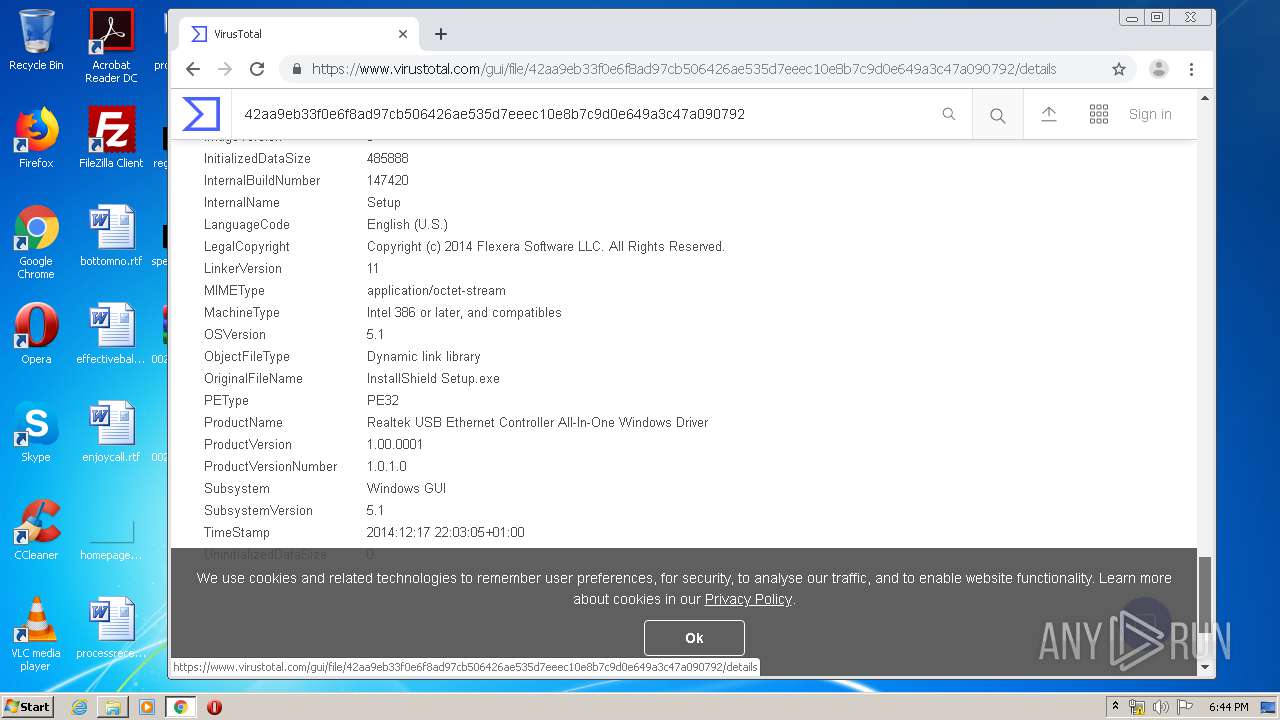
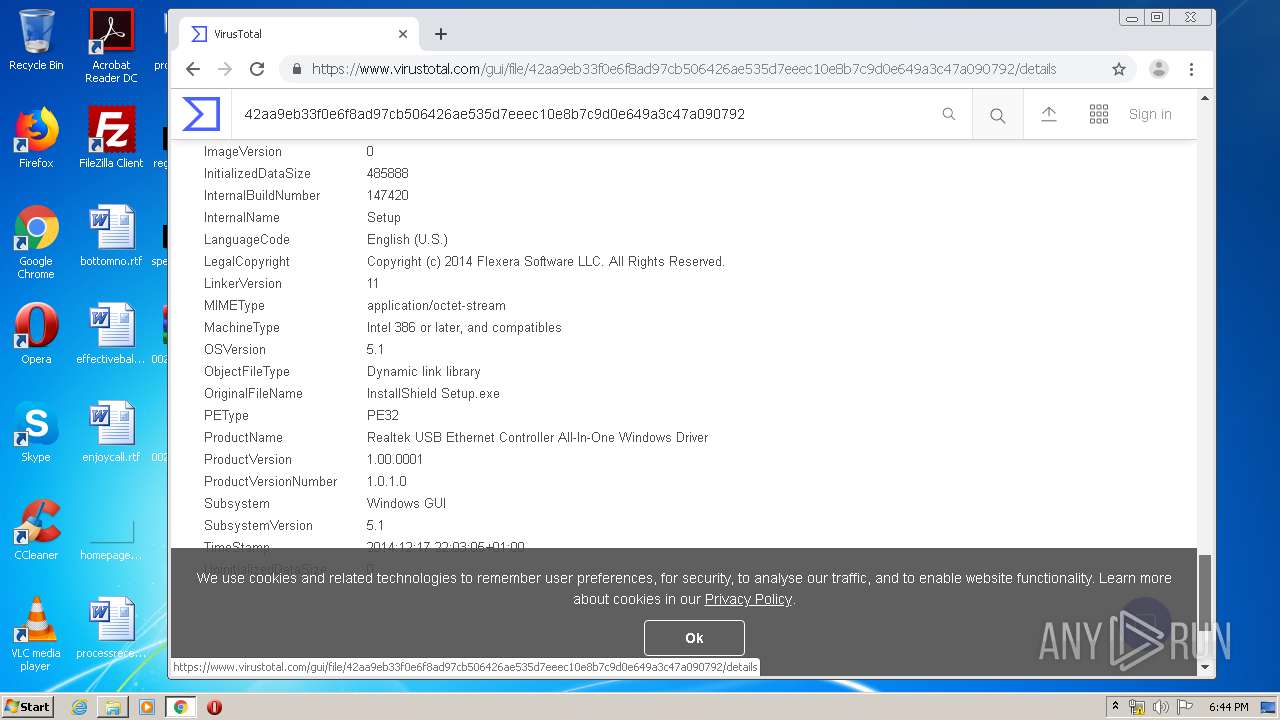
| 1064 | "C:\Users\admin\Desktop\0026-Install_USB_Win10_10025_07252018\Install_USB_Win10_10025_07252018\setup.exe" | C:\Users\admin\Desktop\0026-Install_USB_Win10_10025_07252018\Install_USB_Win10_10025_07252018\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Realtek Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Exit code: 2147753984 Version: 1.00.0001 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8185848539738352251,17075428498448941858,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9743326006581981989 --mojo-platform-channel-handle=3396 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8185848539738352251,17075428498448941858,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7829647344126060690 --mojo-platform-channel-handle=2596 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,8185848539738352251,17075428498448941858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3830732525254996730 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
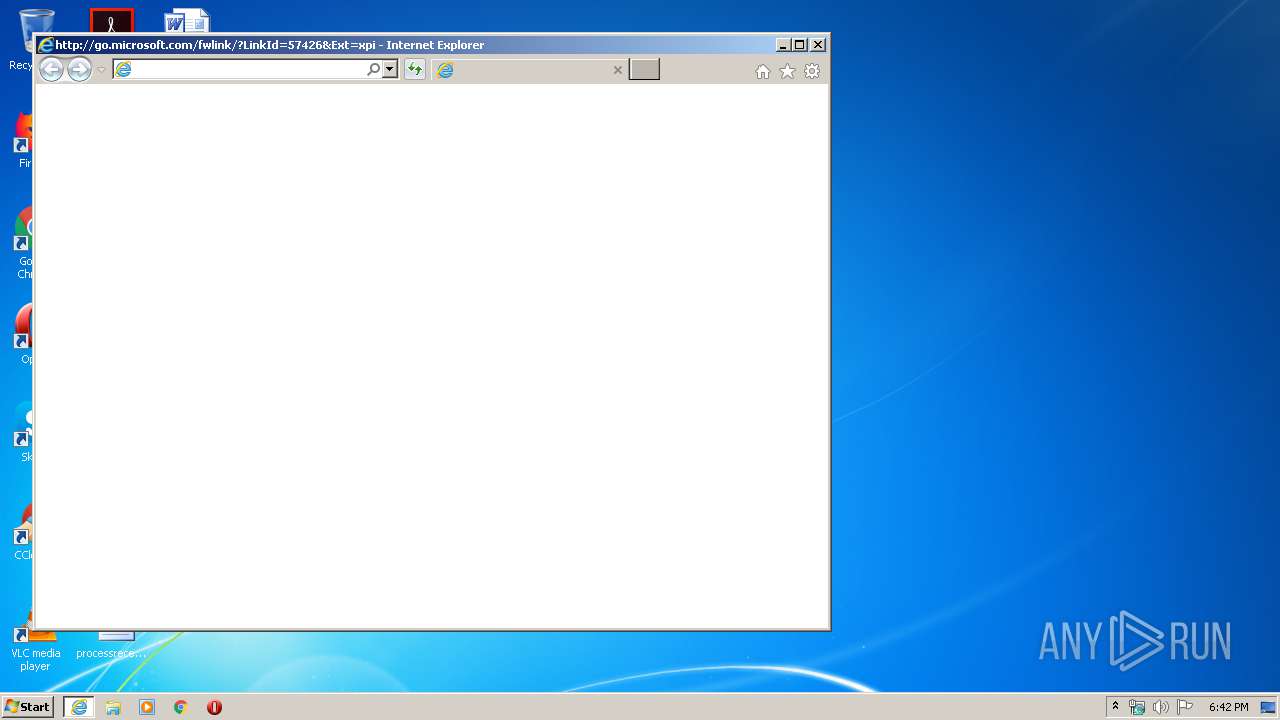
| 2424 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=xpi | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2456 | "C:\Users\admin\Desktop\0026-Install_USB_Win10_10025_07252018\Install_USB_Win10_10025_07252018\setup.exe" | C:\Users\admin\Desktop\0026-Install_USB_Win10_10025_07252018\Install_USB_Win10_10025_07252018\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Realtek Integrity Level: MEDIUM Description: InstallScript Setup Launcher Unicode Exit code: 3221226540 Version: 1.00.0001 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,8185848539738352251,17075428498448941858,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1890825346385372705 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
6 105
Read events
1 358
Write events
3 247
Delete events
1 500
Modification events
| (PID) Process: | (676) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000943AD987BA06D601 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2580254218 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803642 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2424) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
11
Suspicious files
105
Text files
323
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9013.tmp | — | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9014.tmp | — | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Q9SKI2QS.txt | — | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\517UAPU8.txt | — | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\LW7K8QWW.txt | — | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2U450B5J.txt | — | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6ZEQR2R1.txt | — | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\V9WXIBG0.txt | text | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\FWL830EZ.txt | text | |
MD5:— | SHA256:— | |||
| 3872 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_D9817BD5013875AD517DA73475345203 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
62
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | iexplore.exe | GET | 301 | 23.55.161.159:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=xpi | US | — | — | whitelisted |
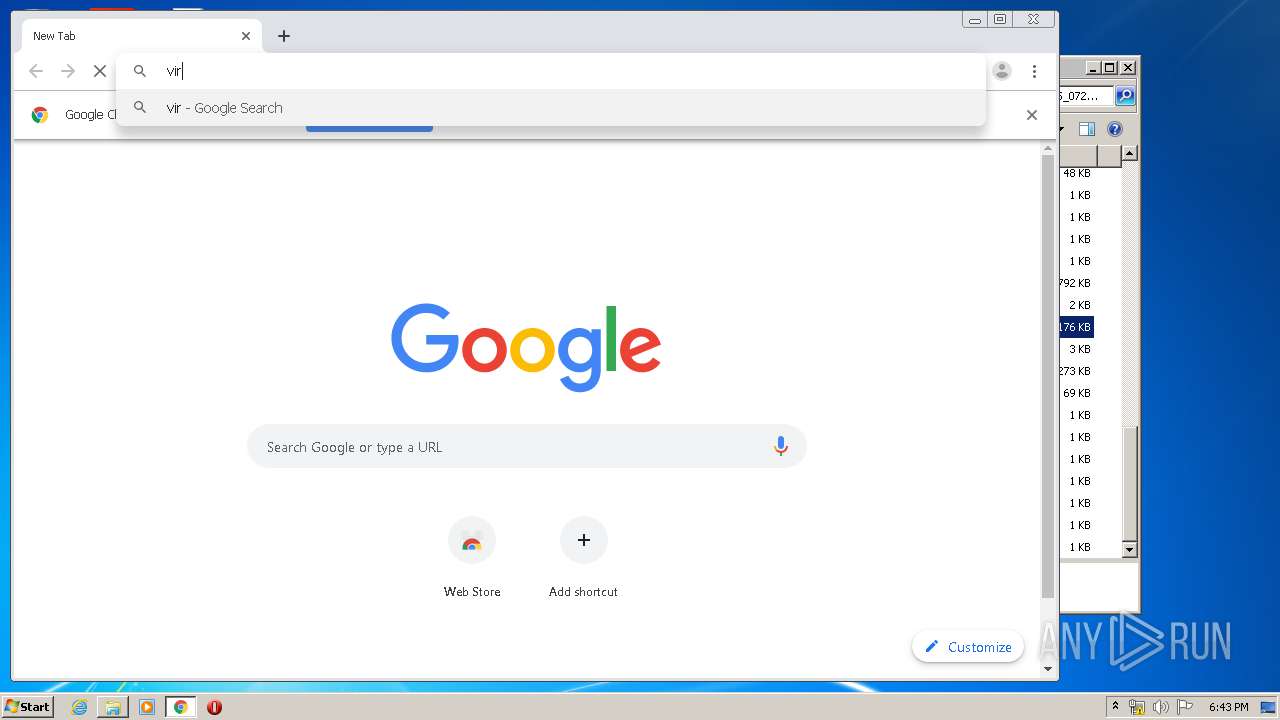
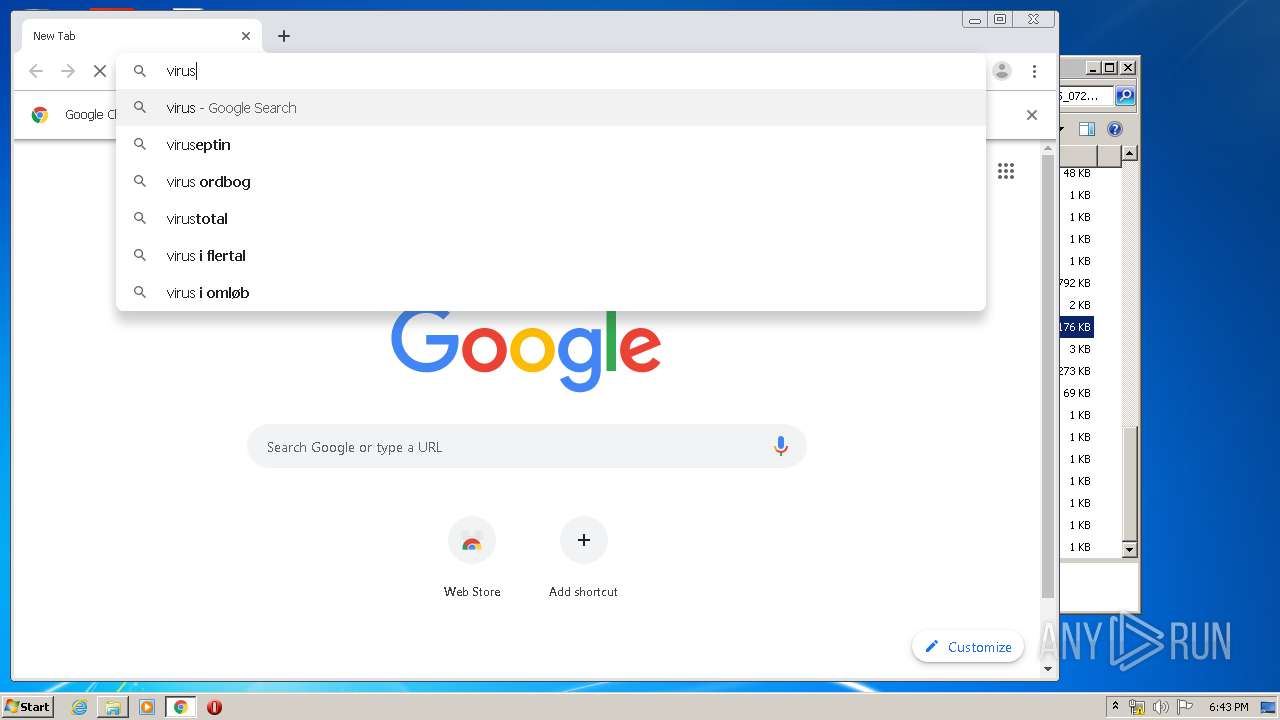
2768 | chrome.exe | GET | 302 | 216.239.38.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
3872 | iexplore.exe | GET | 302 | 104.96.146.202:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=xpi | NL | — | — | whitelisted |
3872 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
3872 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3872 | iexplore.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPC1vZt9qvn7bzY3Iidtbhla4mKQQUWIif1tycSCK3FD7%2FhIjo5oX%2F%2Bn0CE3sAAvTsRon4%2BRVzrdwAAAAC9Ow%3D | US | der | 1.79 Kb | whitelisted |
2768 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
2768 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
3872 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
3872 | iexplore.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPC1vZt9qvn7bzY3Iidtbhla4mKQQUWIif1tycSCK3FD7%2FhIjo5oX%2F%2Bn0CE3sAAvTsRon4%2BRVzrdwAAAAC9Ow%3D | US | der | 1.79 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3872 | iexplore.exe | 104.96.146.202:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
3872 | iexplore.exe | 23.55.161.159:80 | shell.windows.com | Akamai International B.V. | US | unknown |
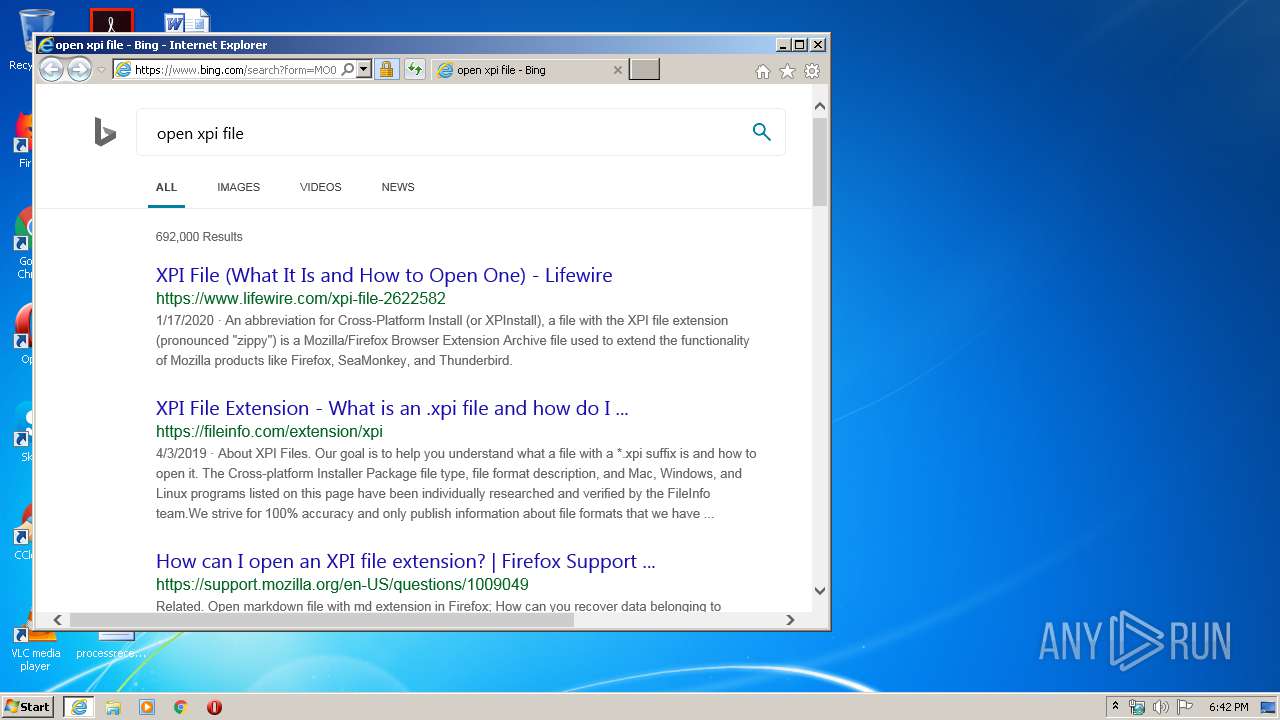
3872 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3872 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2424 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3872 | iexplore.exe | 20.190.129.130:443 | login.microsoftonline.com | Microsoft Corporation | US | malicious |
3872 | iexplore.exe | 104.18.25.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
3872 | iexplore.exe | 40.90.23.247:443 | login.live.com | Microsoft Corporation | US | unknown |
2424 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2768 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
api.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |