| File name: | HELL_MAKER.exe |
| Full analysis: | https://app.any.run/tasks/b41eab2a-adfb-45ca-a16d-c11f978bbc25 |
| Verdict: | Malicious activity |
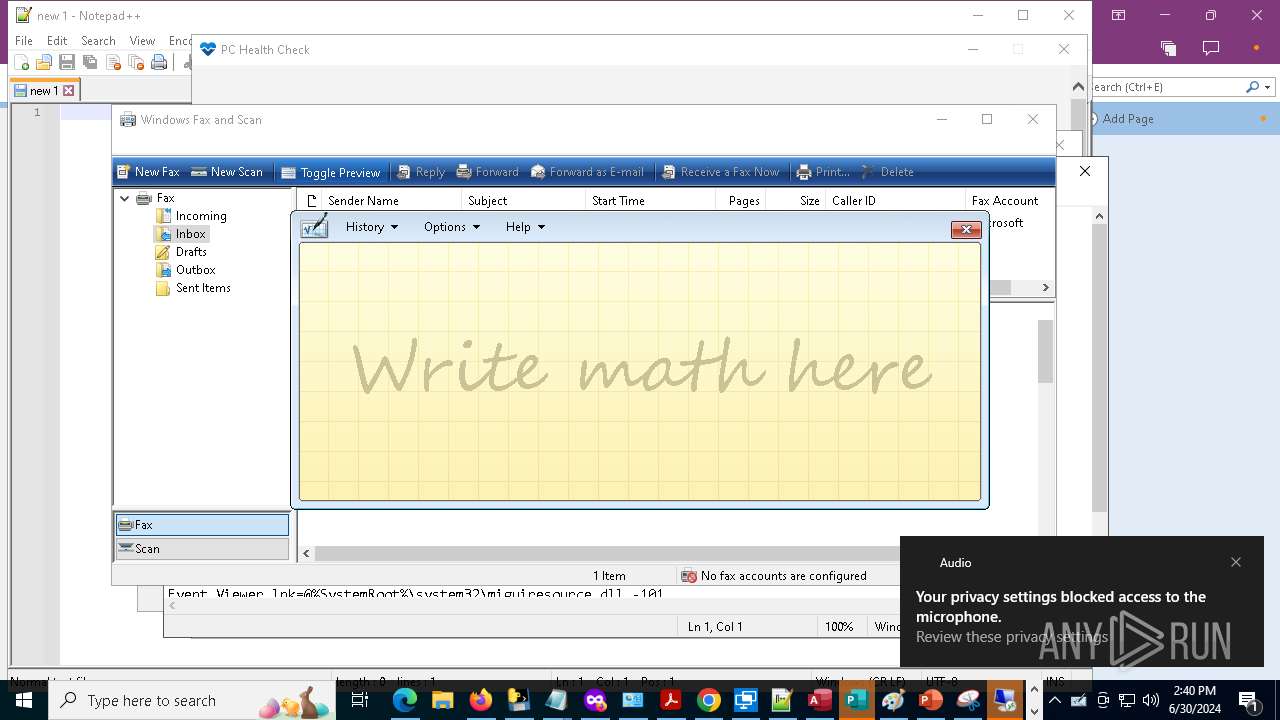
| Analysis date: | June 30, 2024, 14:40:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 4BEAE650D5D65F98C8E004A0CEF467D3 |
| SHA1: | 4E50D2D8BEA73728CE2F8212B6CAB73937B575F8 |
| SHA256: | FB0136A0EAA97B9B9FD3BEE54F602C1AA95A86A85485CFB73D9426108075D0AC |
| SSDEEP: | 98304:BXEBqsuDFqWXAz+SnzhAbYpB4RplQ94geo7HNR9dIofyxmxqMogIn/B25cQgDn28:sYYhji+yMrUz |
MALICIOUS
Drops the executable file immediately after the start
- HELL_MAKER.exe (PID: 4804)
- wv227C8.tmp (PID: 10944)
- MicrosoftEdgeUpdate.exe (PID: 11236)
Scans artifacts that could help determine the target
- MSPUB.EXE (PID: 6408)
SUSPICIOUS
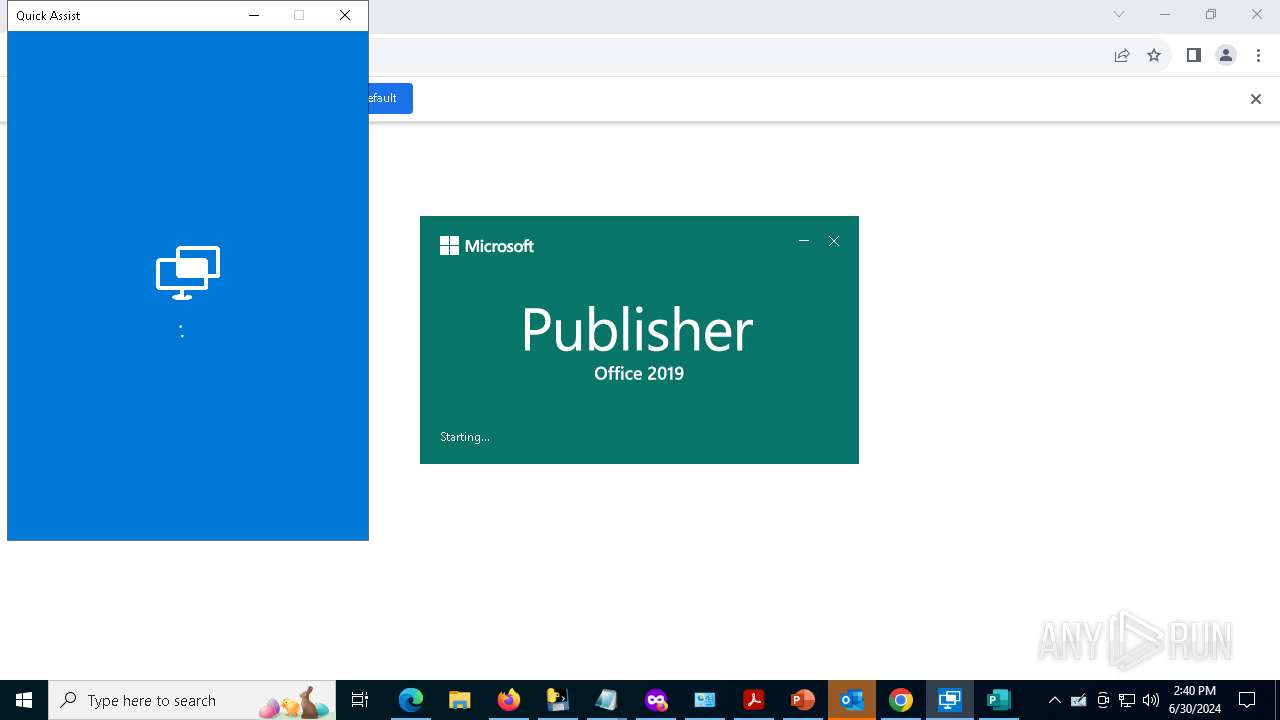
Process drops legitimate windows executable
- HELL_MAKER.exe (PID: 4804)
- quickassist.exe (PID: 9176)
- wv227C8.tmp (PID: 10944)
- MicrosoftEdgeUpdate.exe (PID: 11236)
Process drops python dynamic module
- HELL_MAKER.exe (PID: 4804)
The process drops C-runtime libraries
- HELL_MAKER.exe (PID: 4804)
Application launched itself
- HELL_MAKER.exe (PID: 4804)
Executable content was dropped or overwritten
- HELL_MAKER.exe (PID: 4804)
- quickassist.exe (PID: 9176)
- wv227C8.tmp (PID: 10944)
- MicrosoftEdgeUpdate.exe (PID: 11236)
Reads security settings of Internet Explorer
- HELL_MAKER.exe (PID: 4024)
- PCHealthCheck.exe (PID: 5908)
- MSPUB.EXE (PID: 6408)
- sapisvr.exe (PID: 7100)
- wmplayer.exe (PID: 9140)
Loads Python modules
- HELL_MAKER.exe (PID: 4024)
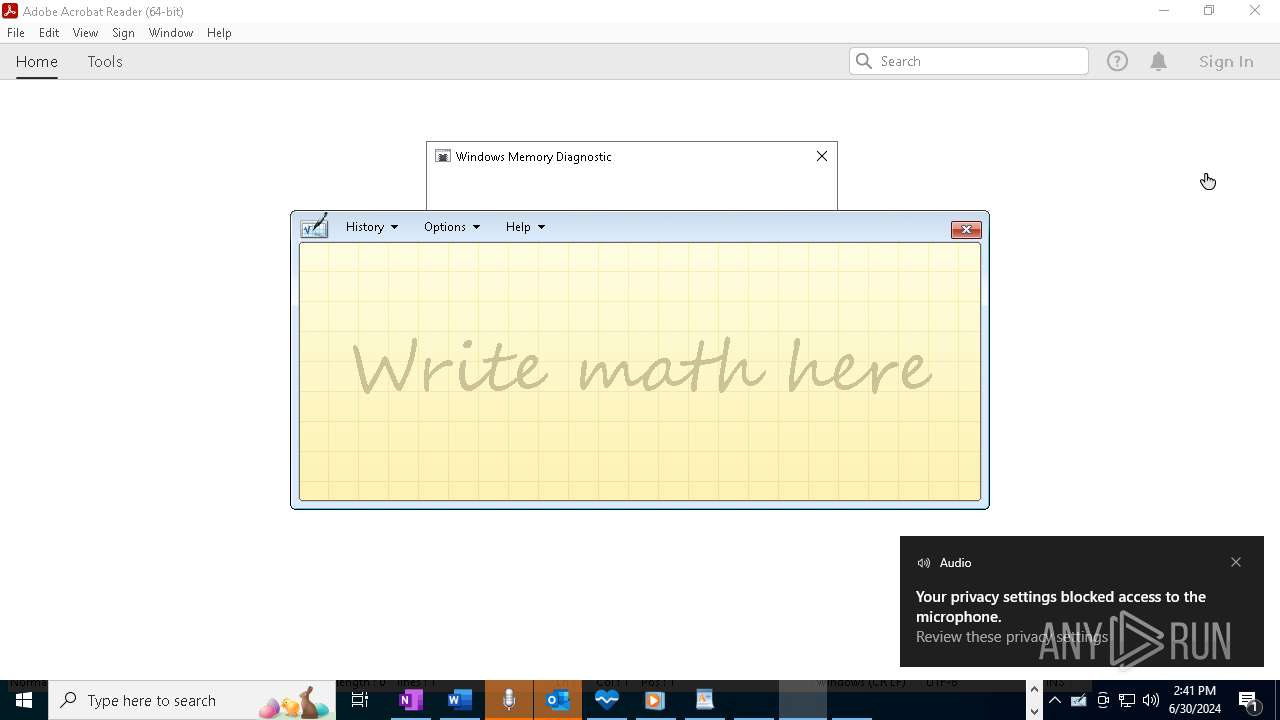
Reads the date of Windows installation
- HELL_MAKER.exe (PID: 4024)
- sapisvr.exe (PID: 7100)
- PCHealthCheck.exe (PID: 5908)
- wmplayer.exe (PID: 9140)
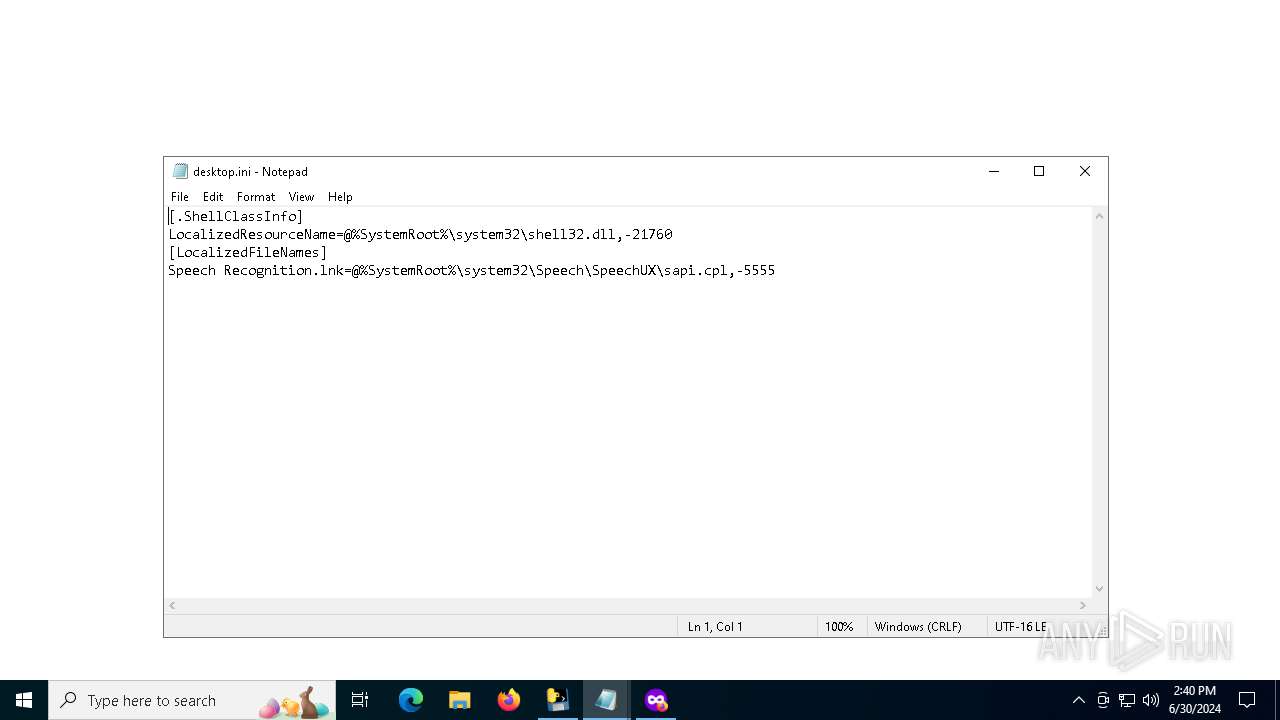
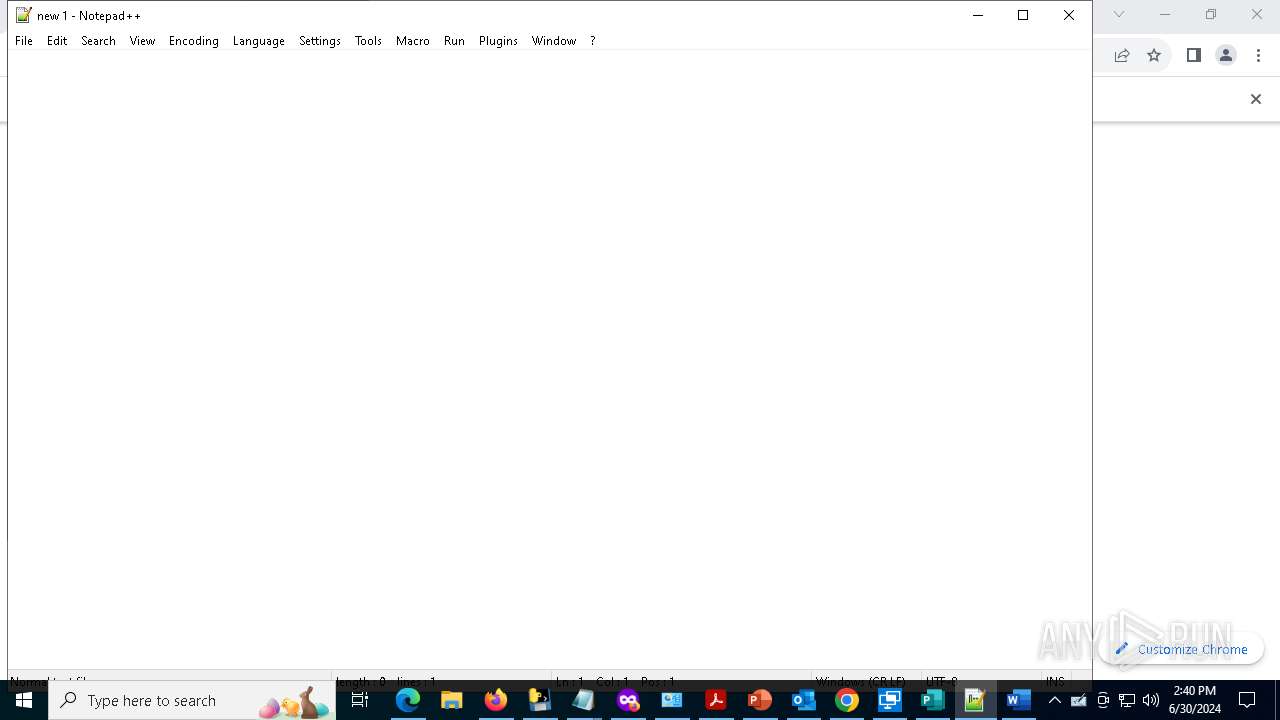
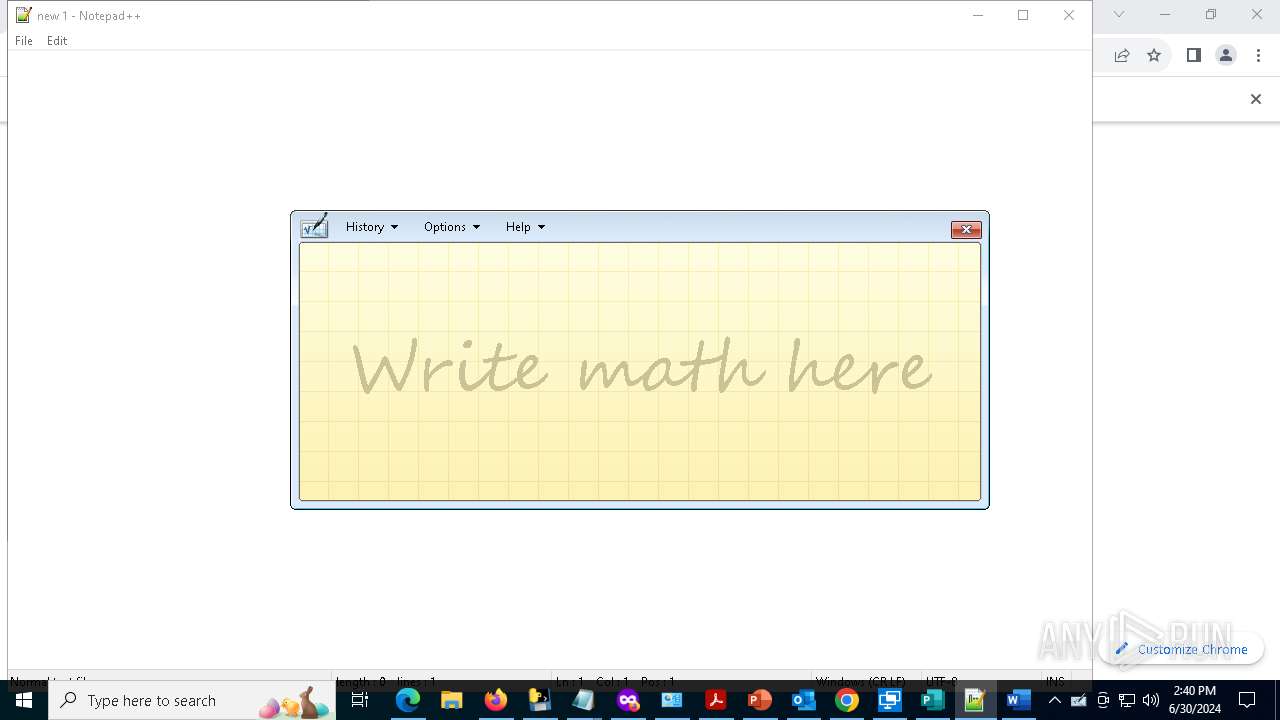
Start notepad (likely ransomware note)
- HELL_MAKER.exe (PID: 4024)
Loads DLL from Mozilla Firefox
- private_browsing.exe (PID: 5868)
Reads Microsoft Outlook installation path
- HELL_MAKER.exe (PID: 4024)
- PCHealthCheck.exe (PID: 5908)
Detected use of alternative data streams (AltDS)
- ONENOTE.EXE (PID: 3780)
- WFS.exe (PID: 10168)
Reads Internet Explorer settings
- PCHealthCheck.exe (PID: 5908)
Reads the history of recent RDP connections
- mstsc.exe (PID: 9336)
Write to the desktop.ini file (may be used to cloak folders)
- WFS.exe (PID: 10168)
Starts a Microsoft application from unusual location
- wv227C8.tmp (PID: 10944)
- MicrosoftEdgeUpdate.exe (PID: 11236)
Starts application with an unusual extension
- quickassist.exe (PID: 9176)
Executes as Windows Service
- FXSSVC.exe (PID: 11100)
- dllhost.exe (PID: 12520)
- msdtc.exe (PID: 12960)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 11236)
INFO
Checks supported languages
- HELL_MAKER.exe (PID: 4804)
- HELL_MAKER.exe (PID: 4024)
- private_browsing.exe (PID: 5868)
- PCHealthCheck.exe (PID: 5908)
- MSPUB.EXE (PID: 6408)
- sapisvr.exe (PID: 7100)
- mip.exe (PID: 6440)
- wmplayer.exe (PID: 9140)
- wordpad.exe (PID: 7444)
- TextInputHost.exe (PID: 8184)
- setup_wm.exe (PID: 10288)
Reads the computer name
- HELL_MAKER.exe (PID: 4804)
- HELL_MAKER.exe (PID: 4024)
- PCHealthCheck.exe (PID: 5908)
- MSPUB.EXE (PID: 6408)
- sapisvr.exe (PID: 7100)
- mip.exe (PID: 6440)
- TextInputHost.exe (PID: 8184)
- wordpad.exe (PID: 7444)
- setup_wm.exe (PID: 10288)
- wmplayer.exe (PID: 9140)
Create files in a temporary directory
- HELL_MAKER.exe (PID: 4804)
- MSPUB.EXE (PID: 6408)
- quickassist.exe (PID: 9176)
- WFS.exe (PID: 10168)
- setup_wm.exe (PID: 10288)
Process checks computer location settings
- HELL_MAKER.exe (PID: 4024)
- sapisvr.exe (PID: 7100)
- MSPUB.EXE (PID: 6408)
- wmplayer.exe (PID: 9140)
- setup_wm.exe (PID: 10288)
Reads Microsoft Office registry keys
- HELL_MAKER.exe (PID: 4024)
- msedge.exe (PID: 4852)
- MSPUB.EXE (PID: 6408)
- firefox.exe (PID: 2268)
- chrome.exe (PID: 2356)
Application launched itself
- Acrobat.exe (PID: 608)
- firefox.exe (PID: 6020)
- msedge.exe (PID: 4852)
- firefox.exe (PID: 4728)
- firefox.exe (PID: 2268)
- chrome.exe (PID: 2356)
- AcroCEF.exe (PID: 12852)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5124)
- notepad.exe (PID: 6632)
- notepad.exe (PID: 7164)
- quickassist.exe (PID: 9176)
- mstsc.exe (PID: 9336)
- unregmp2.exe (PID: 10368)
- notepad.exe (PID: 10108)
Reads the software policy settings
- PCHealthCheck.exe (PID: 5908)
- MSPUB.EXE (PID: 6408)
- quickassist.exe (PID: 9176)
Reads Environment values
- MSPUB.EXE (PID: 6408)
- PCHealthCheck.exe (PID: 5908)
- setup_wm.exe (PID: 10288)
Process checks Internet Explorer phishing filters
- PCHealthCheck.exe (PID: 5908)
Creates files or folders in the user directory
- sapisvr.exe (PID: 7100)
- MSPUB.EXE (PID: 6408)
- quickassist.exe (PID: 9176)
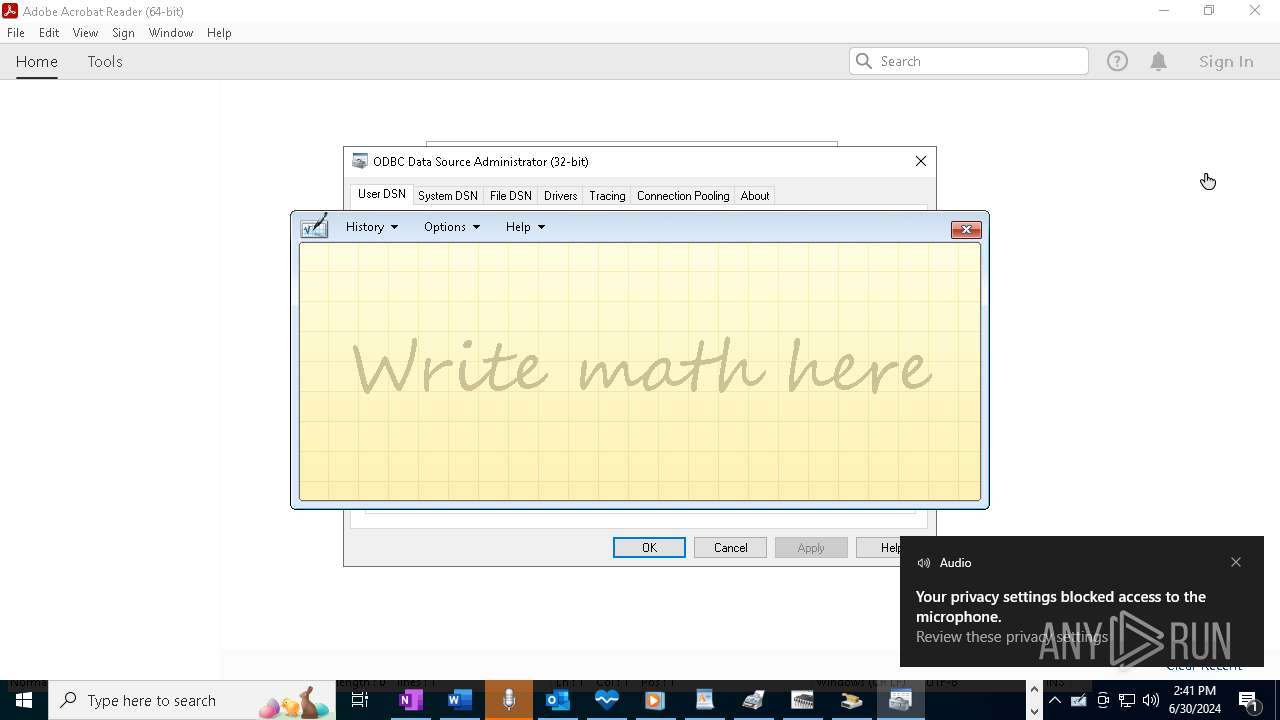
Checks proxy server information
- MSPUB.EXE (PID: 6408)
- PCHealthCheck.exe (PID: 5908)
- quickassist.exe (PID: 9176)
Reads the machine GUID from the registry
- MSPUB.EXE (PID: 6408)
Reads product name
- MSPUB.EXE (PID: 6408)
Reads CPU info
- MSPUB.EXE (PID: 6408)
Drops the executable file immediately after the start
- quickassist.exe (PID: 9176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:07:19 15:59:00+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.34 |
| CodeSize: | 166400 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa6a0 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
295
Monitored processes
142
Malicious processes
9
Suspicious processes
0
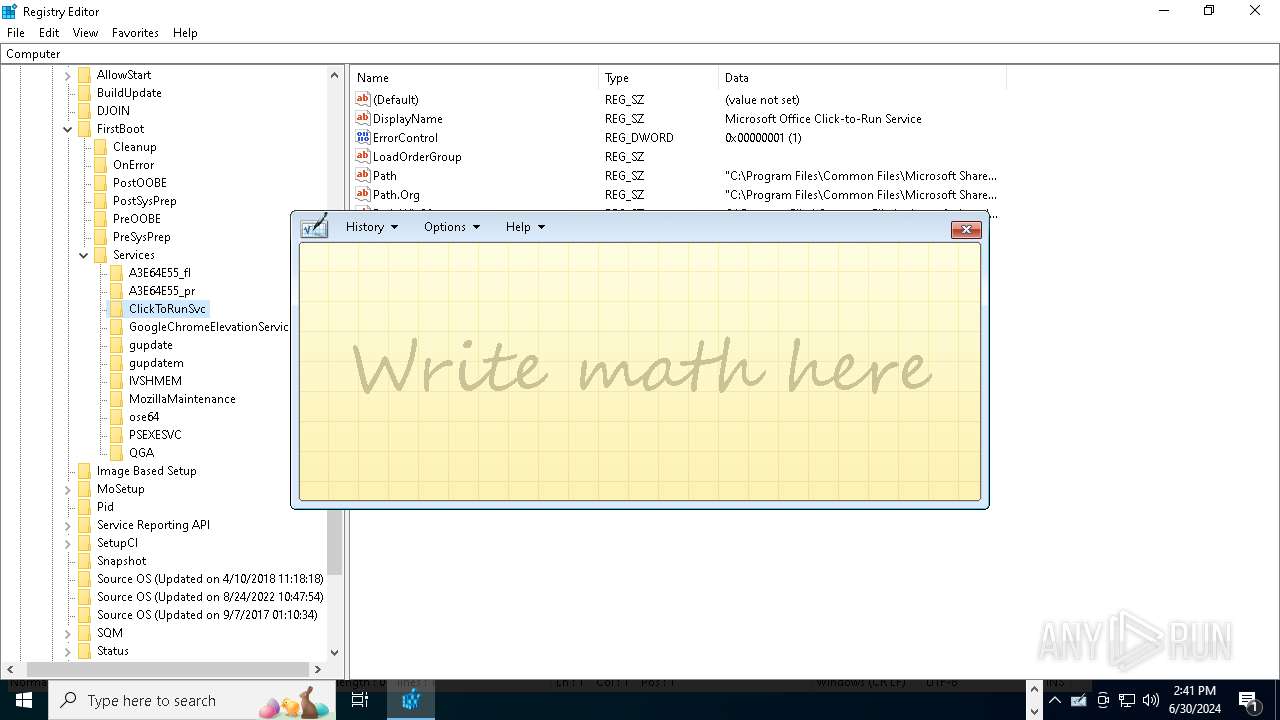
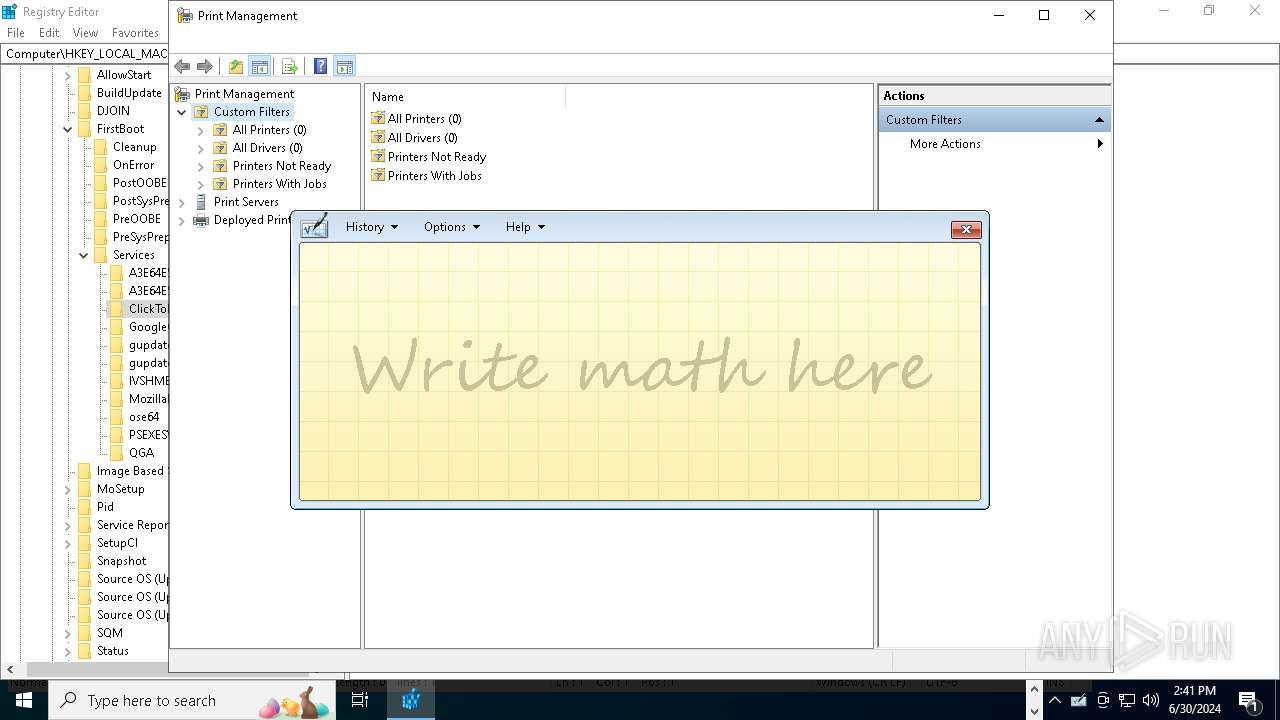
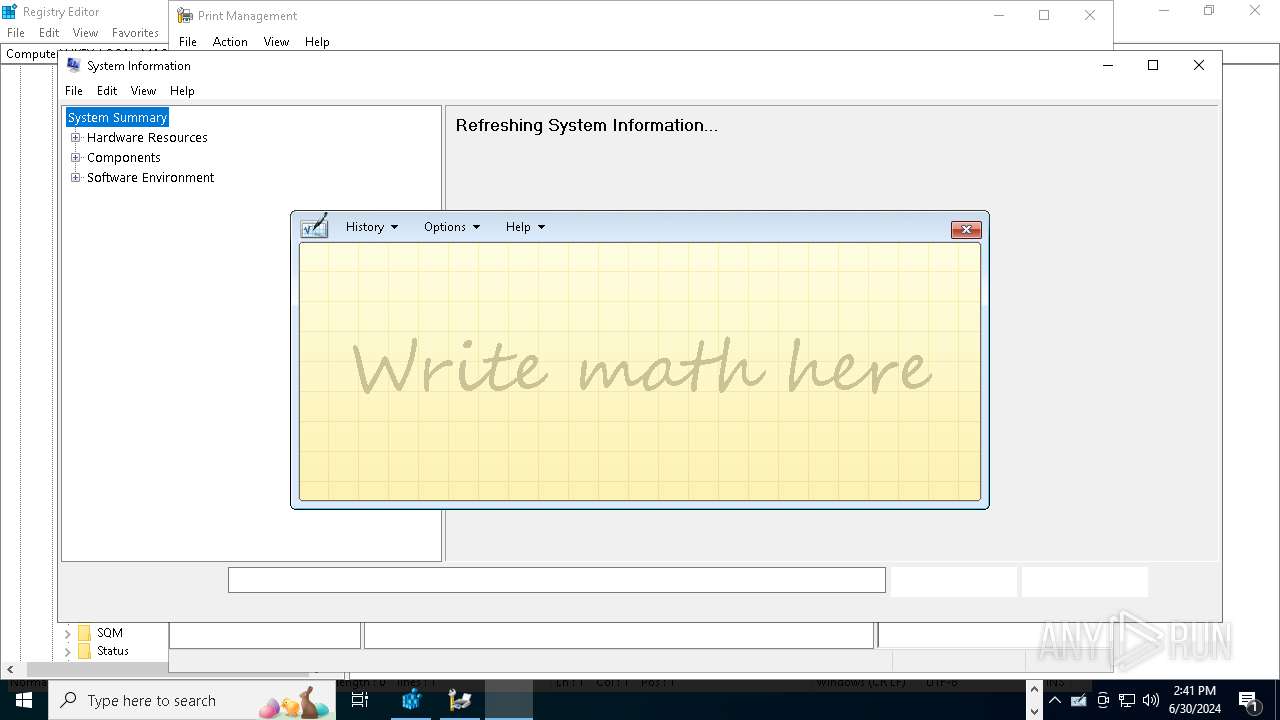
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | HELL_MAKER.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
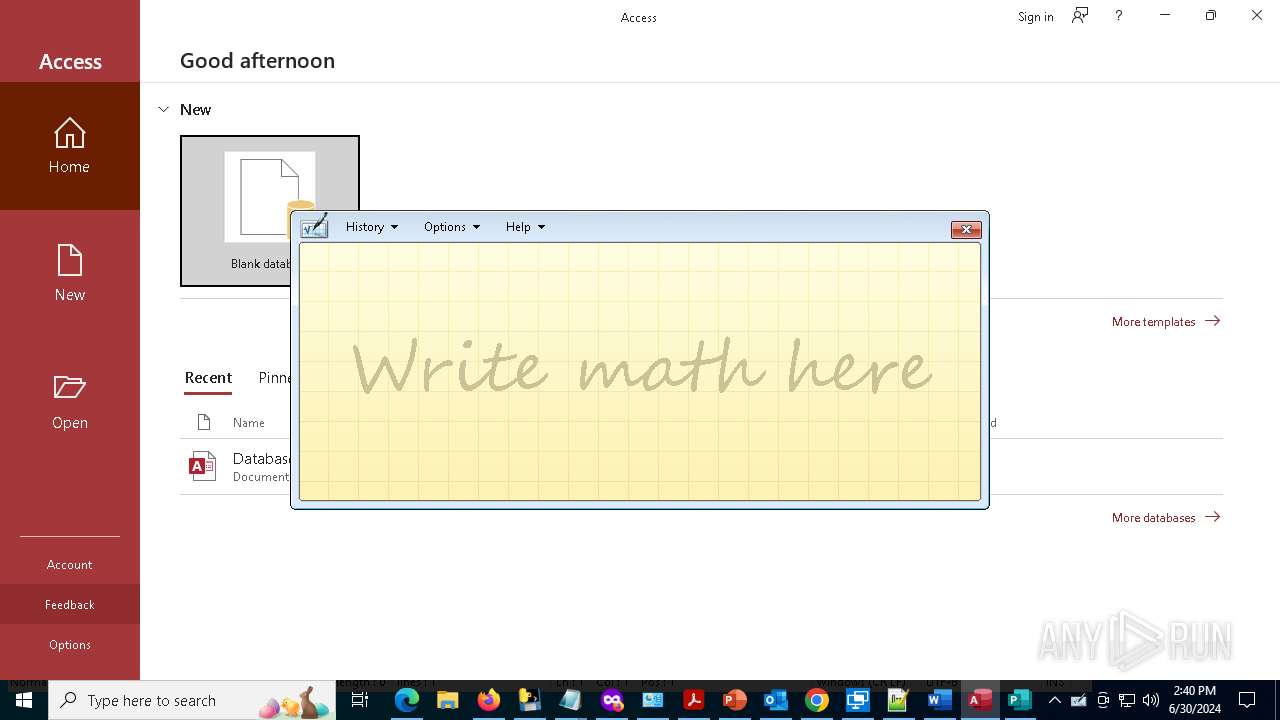
| 1112 | "C:\Program Files\Microsoft Office\root\Office16\MSACCESS.EXE" | C:\Program Files\Microsoft Office\root\Office16\MSACCESS.EXE | HELL_MAKER.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Access Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | — | HELL_MAKER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 16.0.16026.20146 Modules
| |||||||||||||||
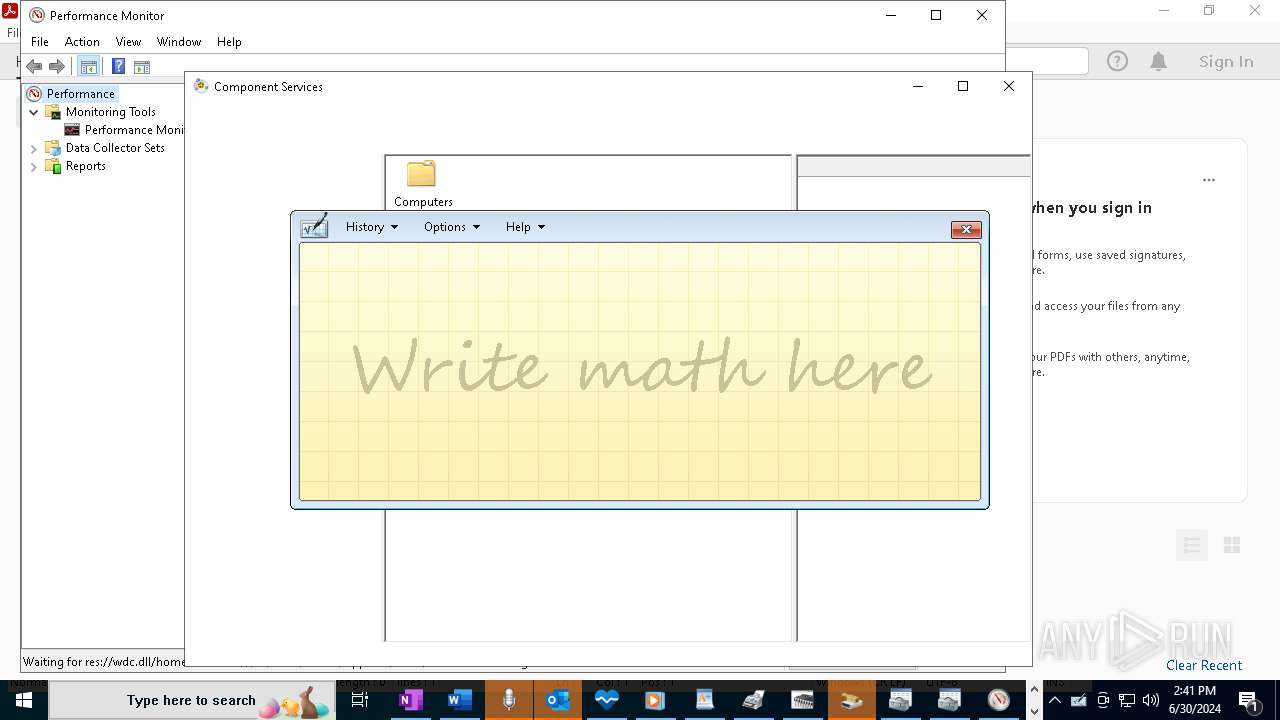
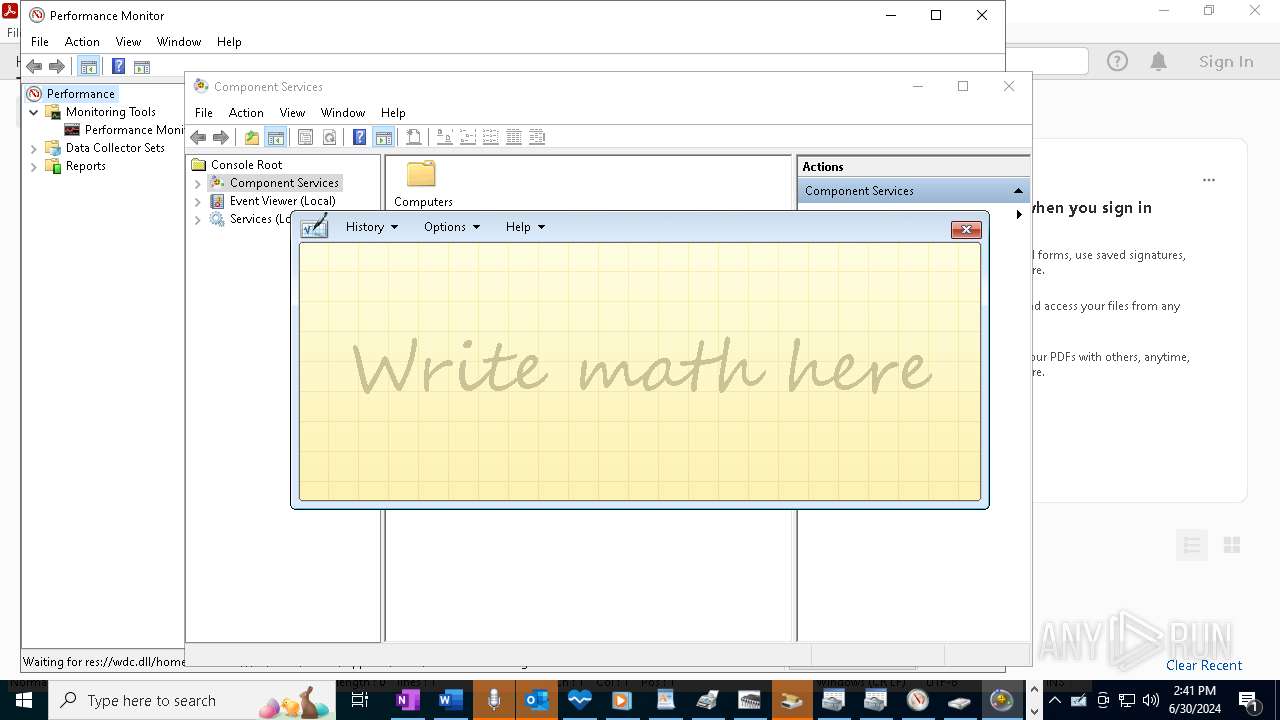
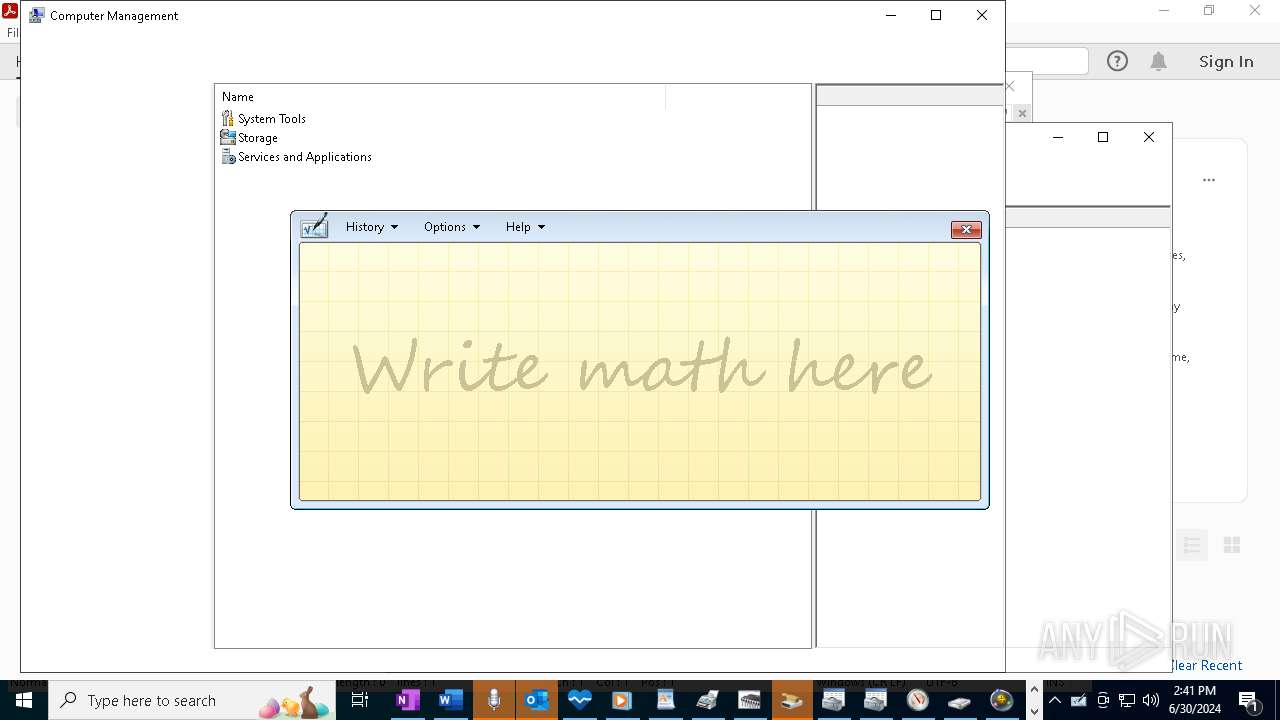
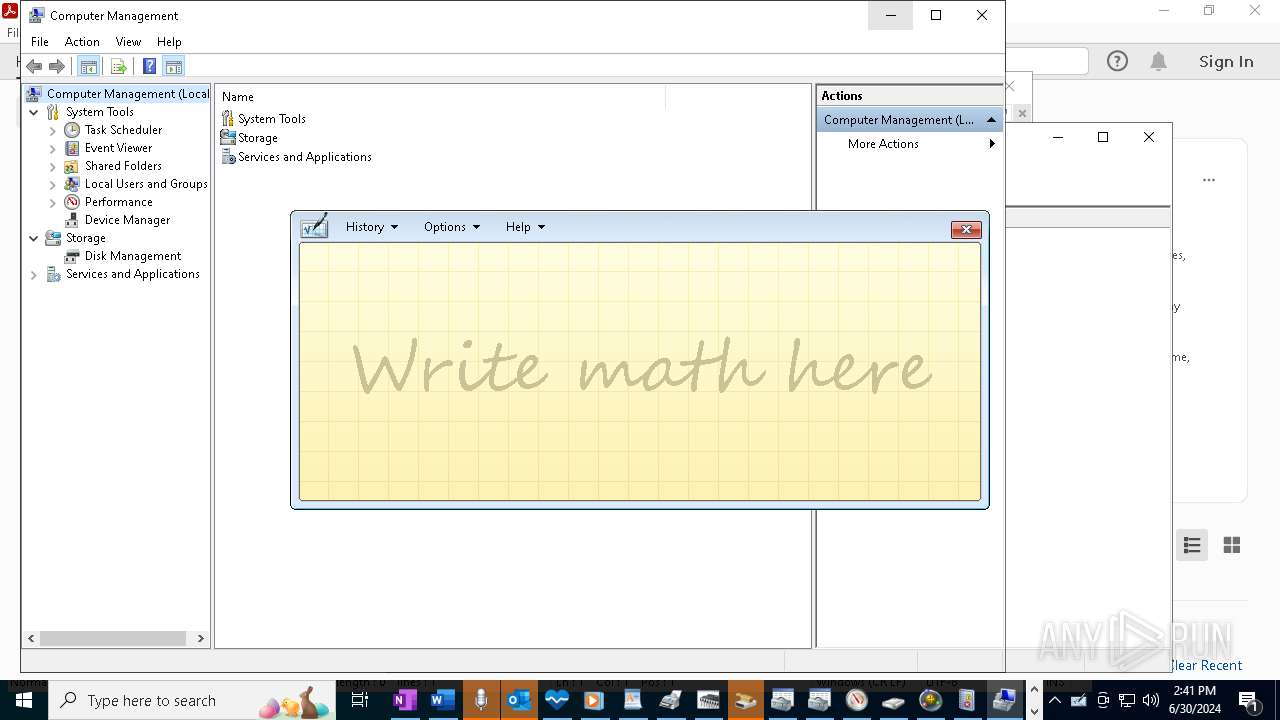
| 2100 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\perfmon.msc" /s | C:\Windows\System32\mmc.exe | HELL_MAKER.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2176 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2240 -parentBuildID 20240213221259 -prefsHandle 2236 -prefMapHandle 2224 -prefsLen 30537 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {60fb74d1-0ac2-4721-93ea-000f936167d0} 2268 "\\.\pipe\gecko-crash-server-pipe.2268" 221cf67fb10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -private-window | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | HELL_MAKER.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2416 | "C:\WINDOWS\System32\Control.exe" | C:\Windows\System32\control.exe | — | HELL_MAKER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | HELL_MAKER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3152 | "C:\Program Files\Notepad++\notepad++.exe" | C:\Program Files\Notepad++\notepad++.exe | HELL_MAKER.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
Total events
104 620
Read events
102 979
Write events
1 545
Delete events
96
Modification events
| (PID) Process: | (4024) HELL_MAKER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (4024) HELL_MAKER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C000000000000046FA0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (4024) HELL_MAKER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4024) HELL_MAKER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4024) HELL_MAKER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4024) HELL_MAKER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4024) HELL_MAKER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.ini\OpenWithProgids |
| Operation: | write | Name: | inifile |
Value: | |||
| (PID) Process: | (608) Acrobat.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Mappings\S-1-15-2-2034283098-2252572593-1072577386-2659511007-3245387615-27016815-3920691934 |
| Operation: | write | Name: | DisplayName |
Value: Adobe Acrobat Reader Protected Mode | |||
| (PID) Process: | (6020) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 4B5DCE7801000000 | |||
| (PID) Process: | (5116) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 4B69D47801000000 | |||
Executable files
219
Suspicious files
377
Text files
171
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4804 | HELL_MAKER.exe | C:\Users\admin\AppData\Local\Temp\_MEI48042\_bz2.pyd | executable | |
MD5:A62207FC33140DE460444E191AE19B74 | SHA256:EBCAC51449F323AE3AE961A33843029C34B6A82138CCD9214CF99F98DD2148C2 | |||
| 4804 | HELL_MAKER.exe | C:\Users\admin\AppData\Local\Temp\_MEI48042\_ssl.pyd | executable | |
MD5:AB0E4FBFFB6977D0196C7D50BC76CF2D | SHA256:680AD2DE8A6CFF927822C1D7DD22112A3E8A824E82A7958EE409A7B9CE45EC70 | |||
| 4804 | HELL_MAKER.exe | C:\Users\admin\AppData\Local\Temp\_MEI48042\_hashlib.pyd | executable | |
MD5:787B82D4466F393366657B8F1BC5F1A9 | SHA256:241322647BA9F94BDC3AE387413FFB57AE14C8CF88BD564A31FE193C6CA43E37 | |||
| 4804 | HELL_MAKER.exe | C:\Users\admin\AppData\Local\Temp\_MEI48042\_lzma.pyd | executable | |
MD5:0C7EA68CA88C07AE6B0A725497067891 | SHA256:F74AAF0AA08CF90EB1EB23A474CCB7CB706B1EDE7F911DAF7AE68480765BDF11 | |||
| 4804 | HELL_MAKER.exe | C:\Users\admin\AppData\Local\Temp\_MEI48042\VCRUNTIME140.dll | executable | |
MD5:4585A96CC4EEF6AAFD5E27EA09147DC6 | SHA256:A8F950B4357EC12CFCCDDC9094CCA56A3D5244B95E09EA6E9A746489F2D58736 | |||
| 4804 | HELL_MAKER.exe | C:\Users\admin\AppData\Local\Temp\_MEI48042\_decimal.pyd | executable | |
MD5:692C751A1782CC4B54C203546F238B73 | SHA256:C70F05F6BC564FE400527B30C29461E9642FB973F66EEC719D282D3D0B402F93 | |||
| 2268 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 4852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF1af81d.TMP | binary | |
MD5:D38E65900351368940616574EEA58831 | SHA256:B185F10E1AFDF0EEC98946C2A838EF8A7D95F5C1CD8B43CD82430F908FFF069A | |||
| 4852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:C771BB0788EF16FBA5F4663F6E8C5583 | SHA256:64F3D26B391A3A0C23DD3755C90D2259B21ED071269A912DCA73A732C95DAE1B | |||
| 4852 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:C7E2197BAE099B13BBB3ADEB1433487D | SHA256:3460EEAF45D581DD43A6E4E17AF8102DDAFF5AEAA88B10099527CF85211629E9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
161
DNS requests
233
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 95.101.54.131:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
2268 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | unknown |
2268 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | unknown |
2268 | firefox.exe | POST | 200 | 2.16.202.120:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
2268 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
2268 | firefox.exe | POST | 200 | 2.16.202.120:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
2268 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
2268 | firefox.exe | POST | 200 | 2.16.202.121:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
2268 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
3172 | svchost.exe | 52.137.106.217:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3088 | RUXIMICS.exe | 52.137.106.217:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3516 | MoUsoCoreWorker.exe | 52.137.106.217:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5908 | PCHealthCheck.exe | 2.19.246.123:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
5908 | PCHealthCheck.exe | 23.213.161.214:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3040 | OfficeClickToRun.exe | 40.79.197.34:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | JP | unknown |
3040 | OfficeClickToRun.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
2268 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | unknown |
4852 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
quickassist.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
ONENOTE.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|