| File name: | american.express.03.30.2020.pdf |
| Full analysis: | https://app.any.run/tasks/3e53afda-3516-41e8-91e8-b10b26a44c09 |
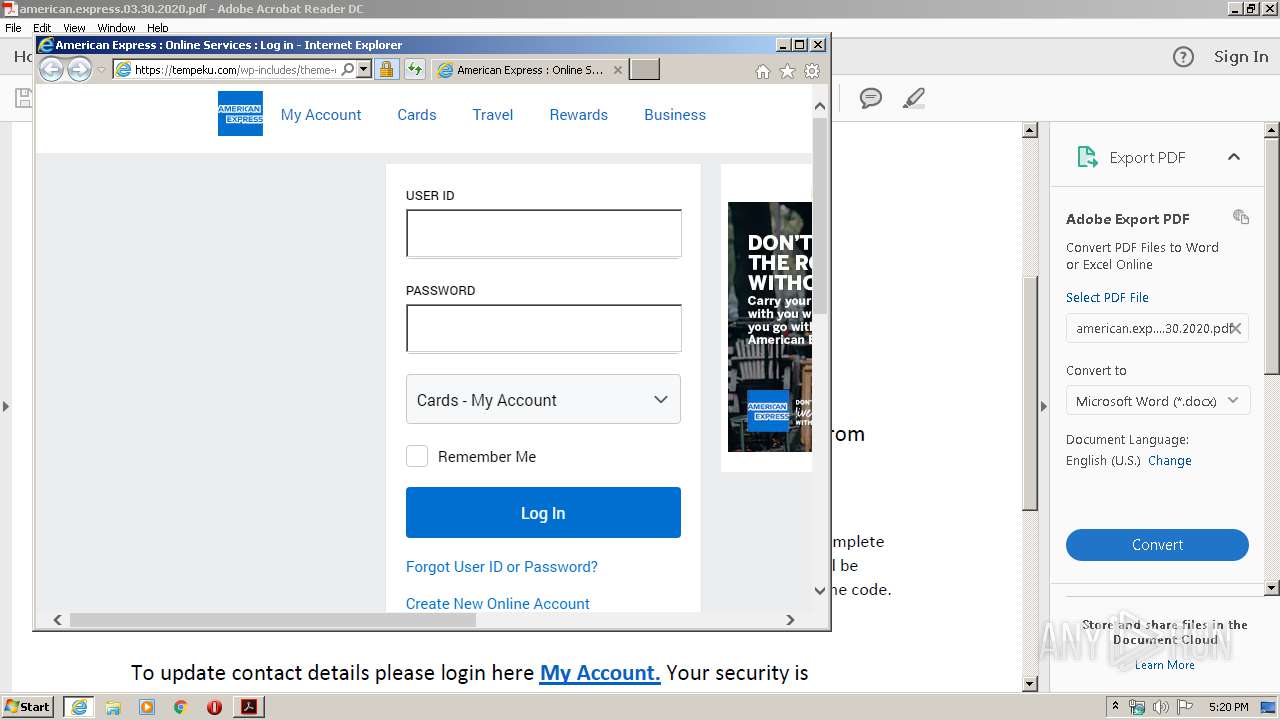
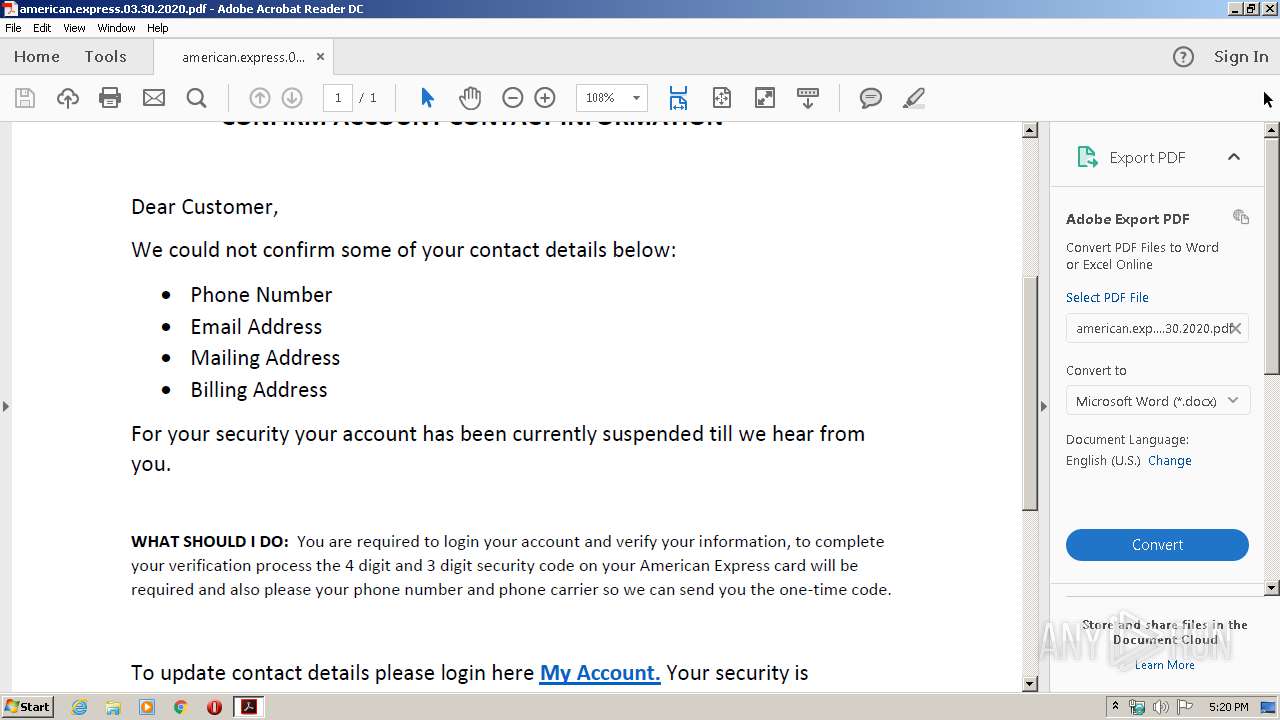
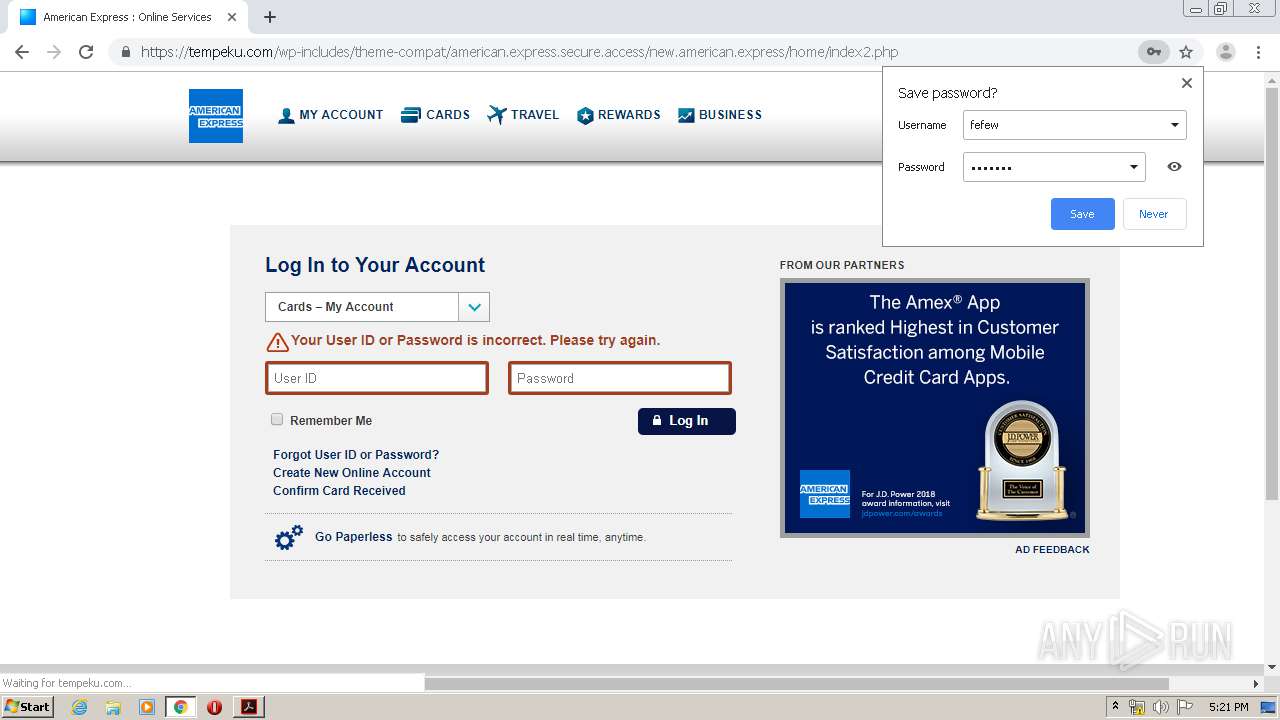
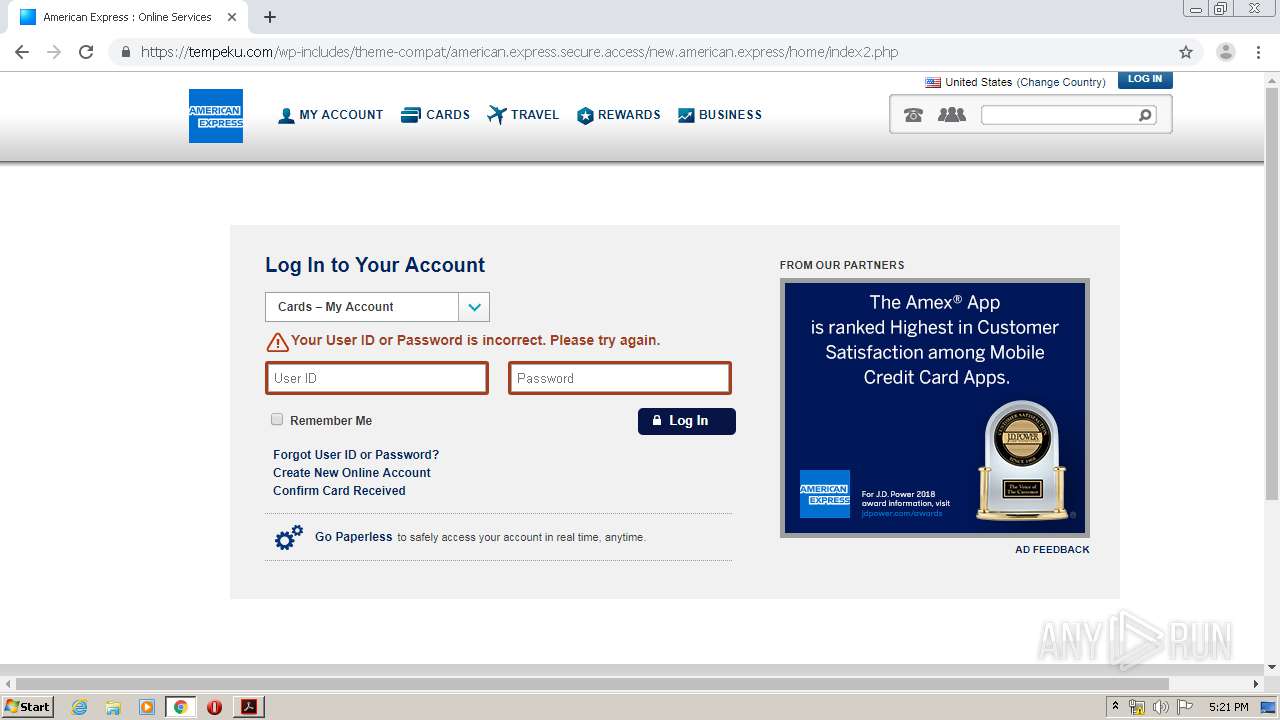
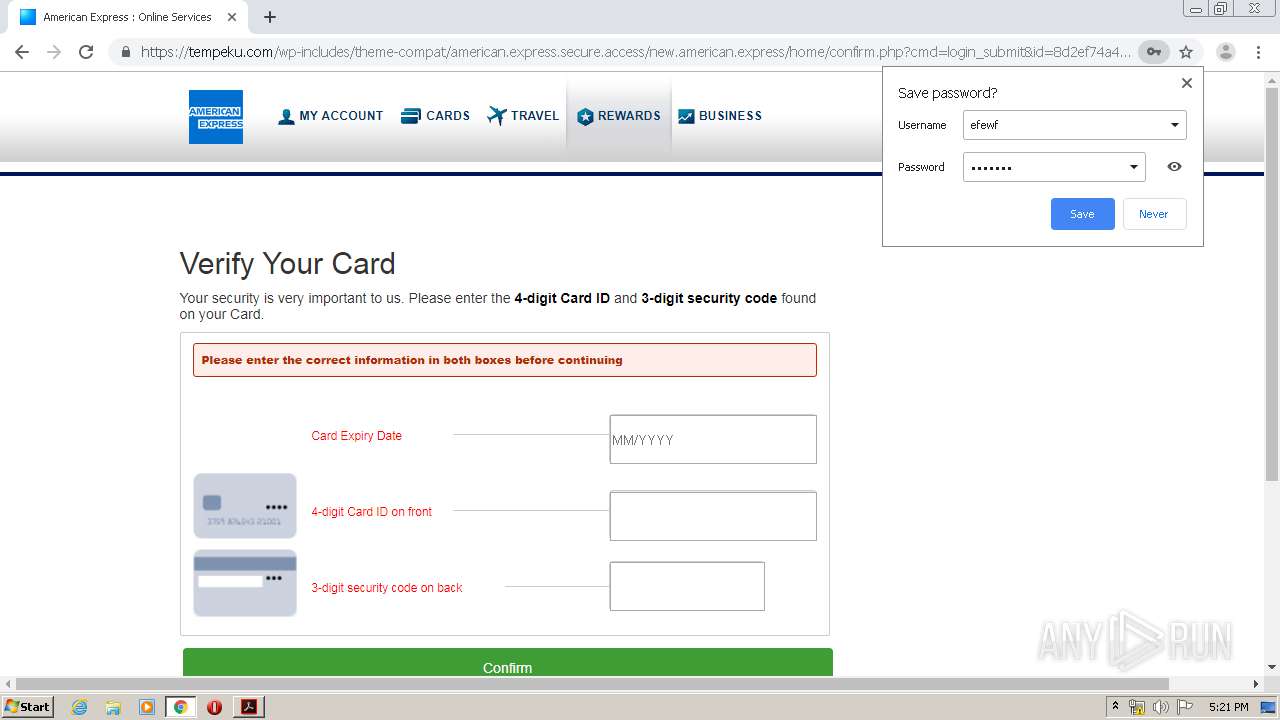
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 16:20:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.7 |
| MD5: | ADE8B2CC4616FF60BE3397BE6599BE60 |
| SHA1: | 32CFCAC382EA01BECED030AF1C858A2A07DD0458 |
| SHA256: | FAEFFB5AAFFD01CB0E9BF8CC35BFA1BD8A5855C92D349040701400C035894C1E |
| SSDEEP: | 3072:QbzKUyR4xw7OclsFE4vU8GUWRY86CcMQ8onw4VwNT:QbzKUI7Oc5431Ccr7nw4yNT |
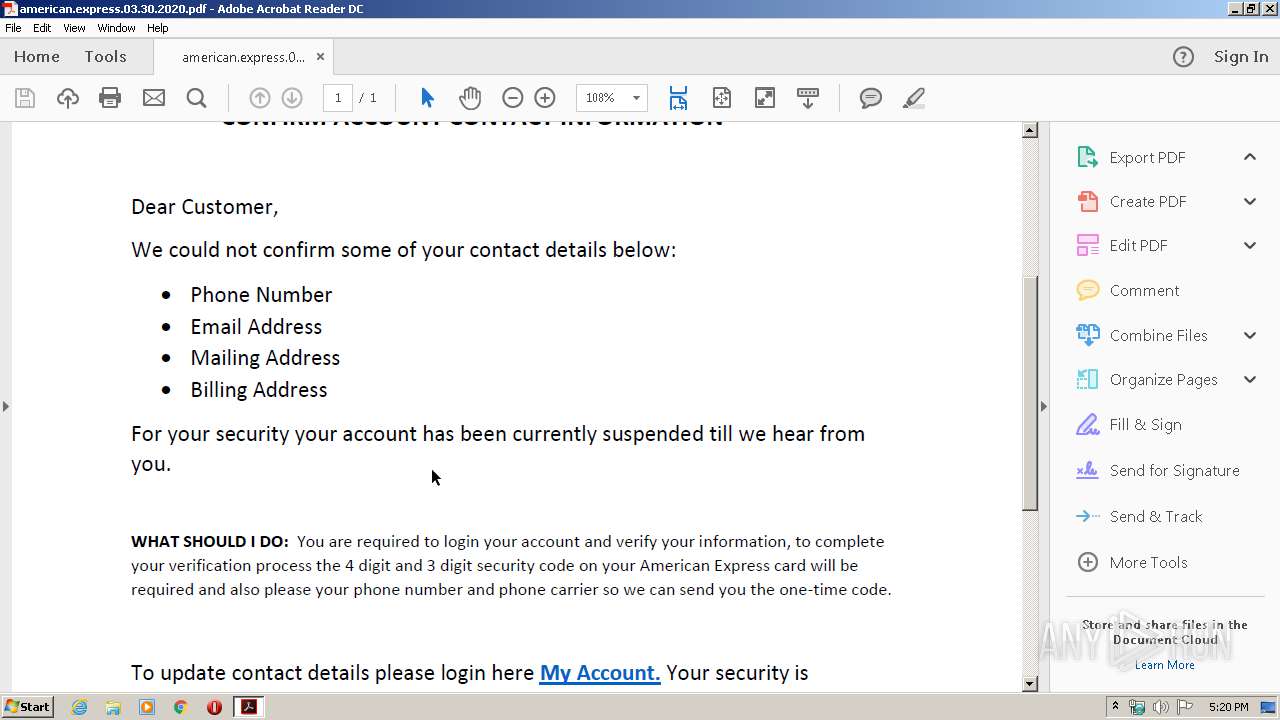
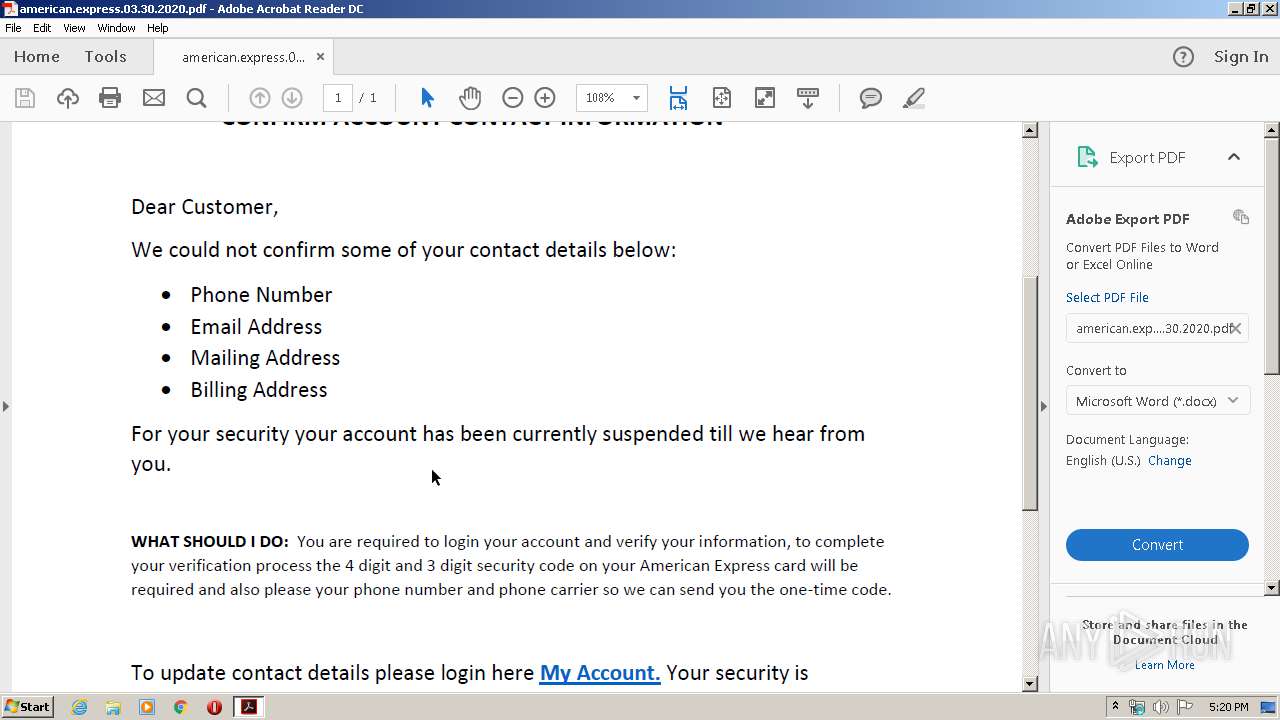
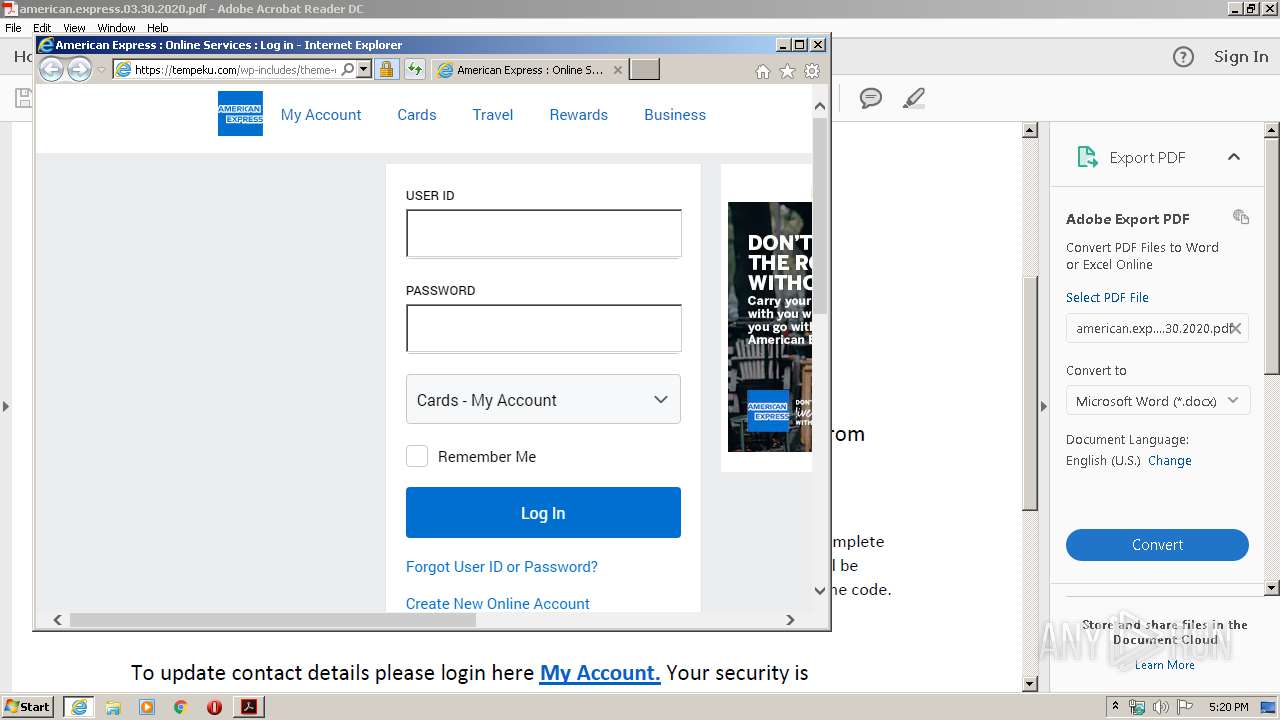
MALICIOUS
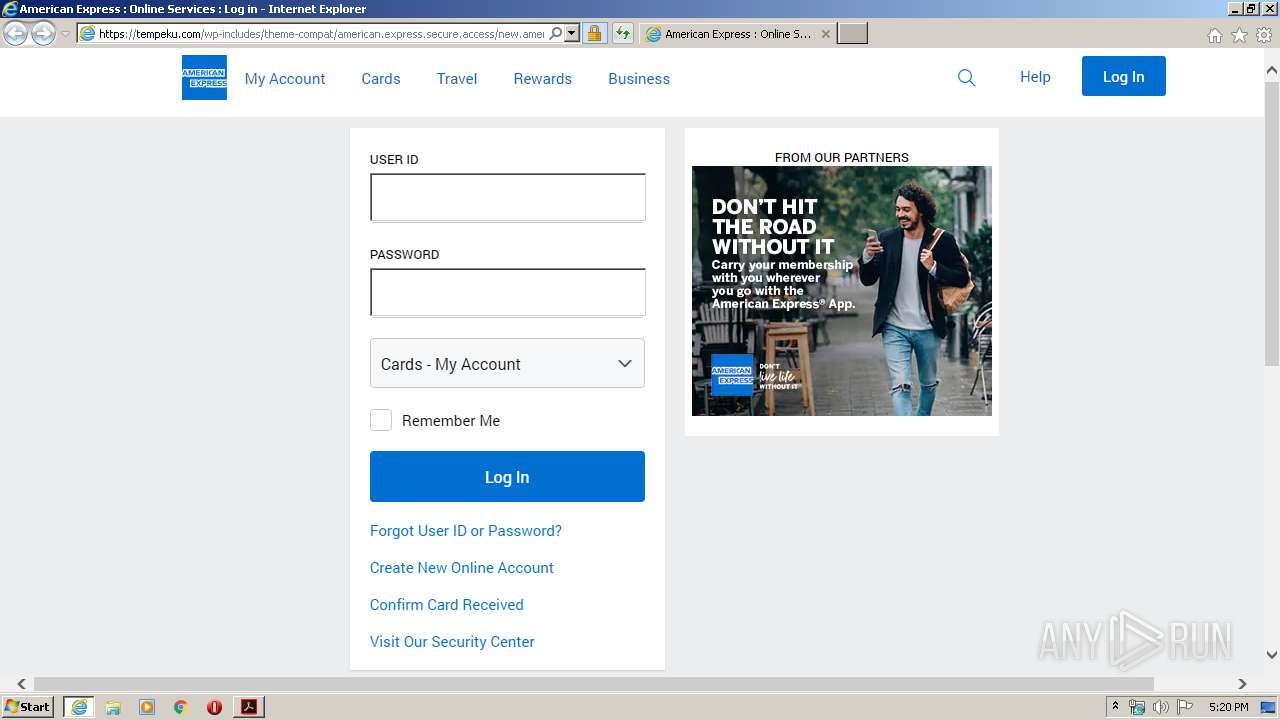
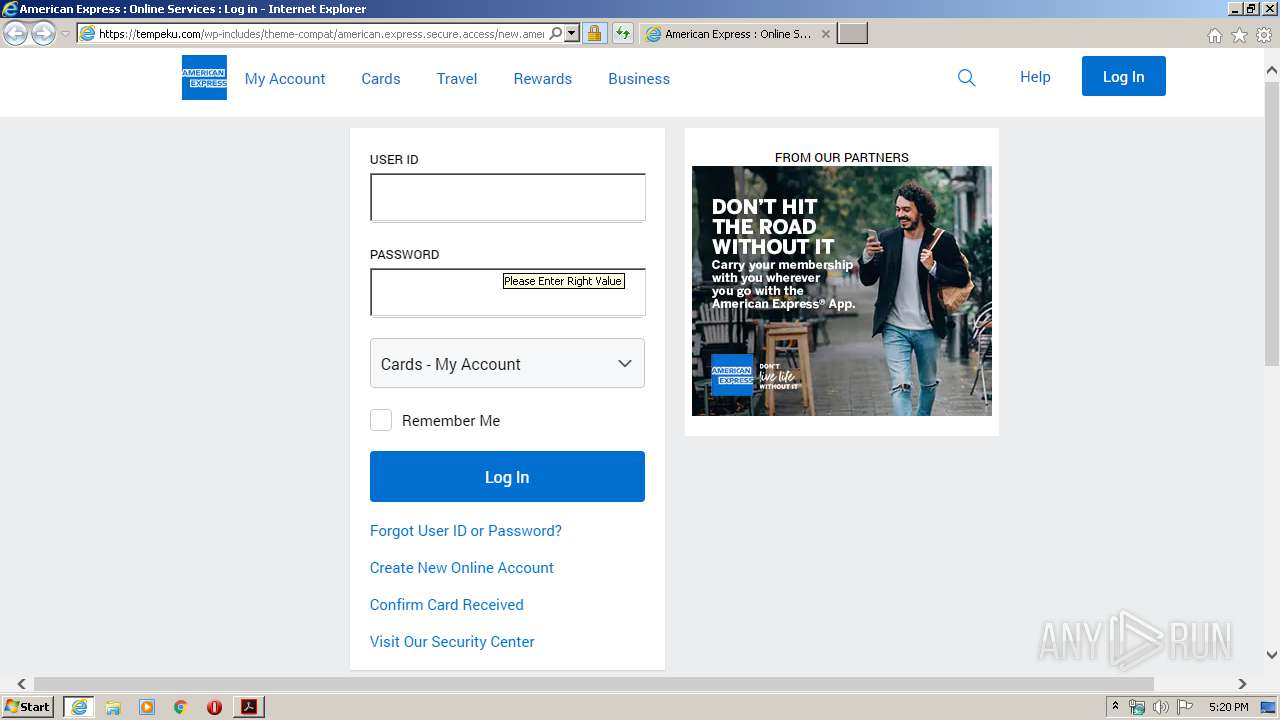
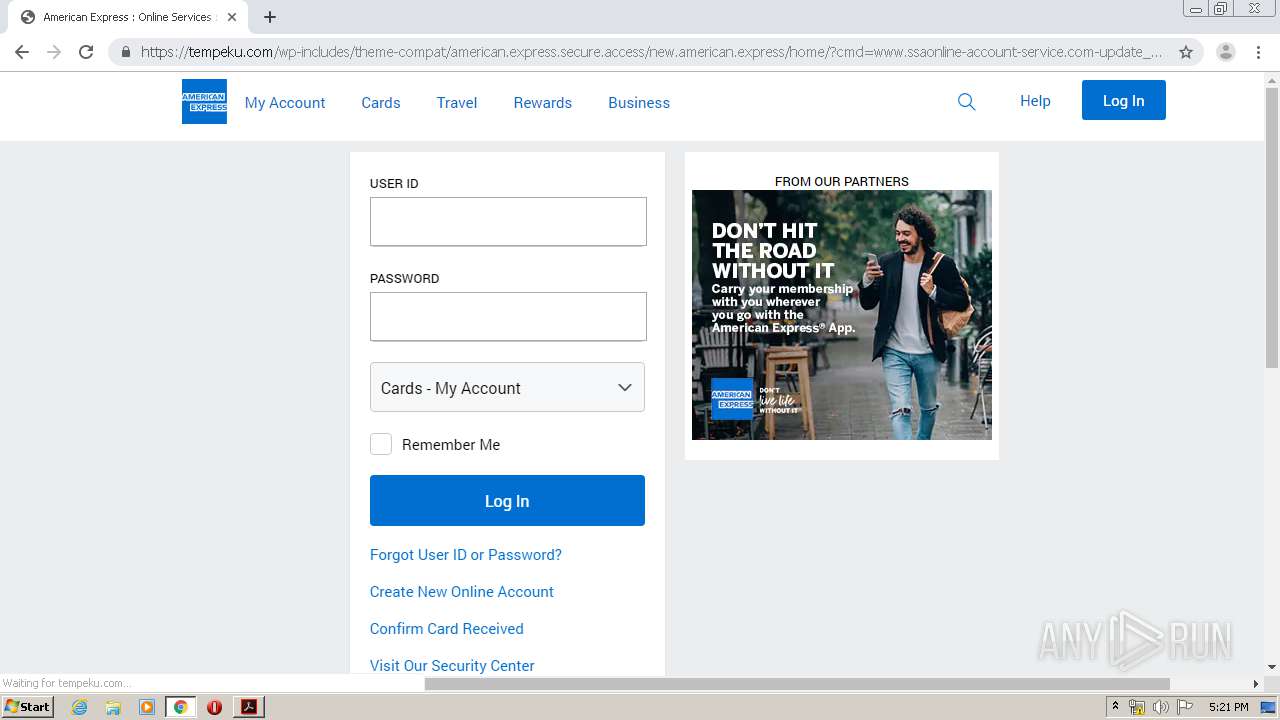
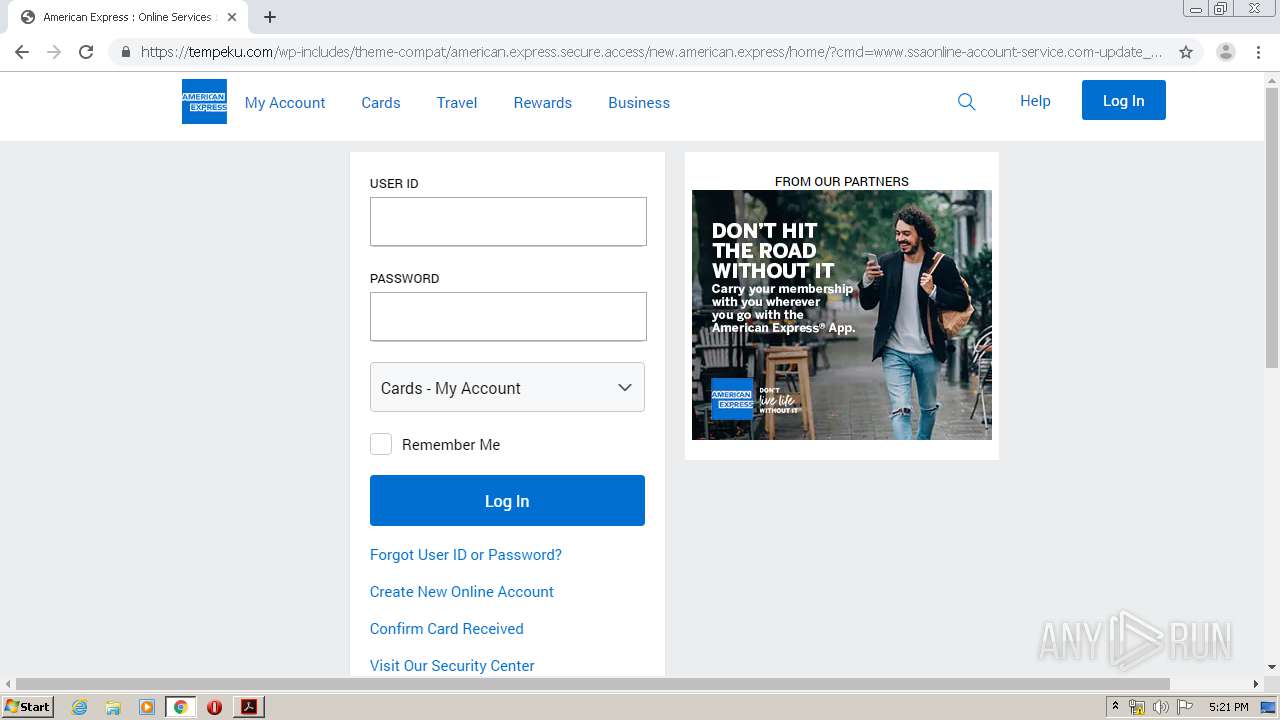
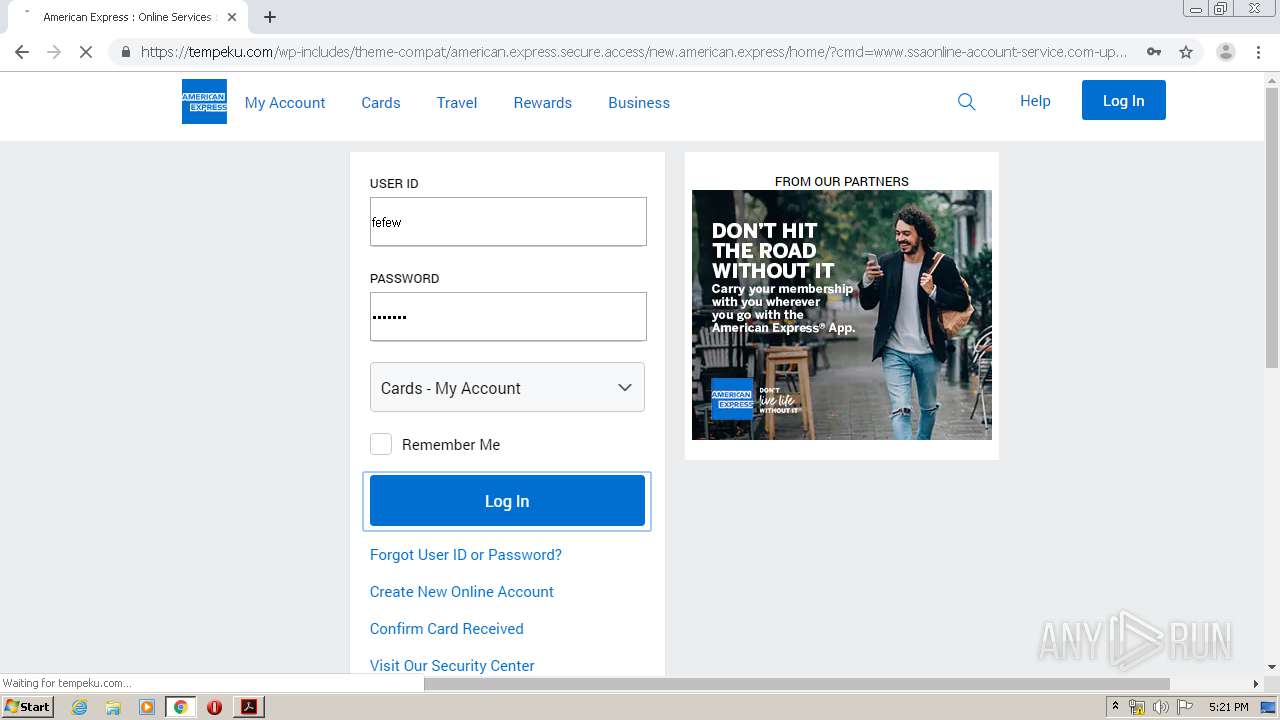
Outlook phishing page detected
- iexplore.exe (PID: 2892)
- chrome.exe (PID: 2192)
SUSPICIOUS
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 2856)
Starts Internet Explorer
- AcroRd32.exe (PID: 2856)
Creates files in the program directory
- AdobeARM.exe (PID: 2572)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2716)
INFO
Reads Internet Cache Settings
- AcroRd32.exe (PID: 1008)
- iexplore.exe (PID: 540)
- iexplore.exe (PID: 2480)
- iexplore.exe (PID: 2892)
- AcroRd32.exe (PID: 2856)
- iexplore.exe (PID: 2436)
Reads settings of System Certificates
- AcroRd32.exe (PID: 2856)
- chrome.exe (PID: 2192)
- iexplore.exe (PID: 2892)
- iexplore.exe (PID: 540)
Application launched itself
- iexplore.exe (PID: 540)
- RdrCEF.exe (PID: 2944)
- iexplore.exe (PID: 2480)
- chrome.exe (PID: 2716)
Creates files in the user directory
- iexplore.exe (PID: 2892)
- iexplore.exe (PID: 540)
Reads the hosts file
- RdrCEF.exe (PID: 2944)
- chrome.exe (PID: 2192)
- chrome.exe (PID: 2716)
Changes internet zones settings
- iexplore.exe (PID: 540)
- iexplore.exe (PID: 2480)
Reads internet explorer settings
- iexplore.exe (PID: 2892)
Manual execution by user
- chrome.exe (PID: 2716)
Changes settings of System certificates
- iexplore.exe (PID: 540)
Adds / modifies Windows certificates
- iexplore.exe (PID: 540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.7 |
|---|---|
| Linearized: | No |
| PageCount: | 1 |
| Language: | en-US |
| TaggedPDF: | Yes |
| Author: | Rohan Poddar |
| Creator: | Microsoft Word |
| CreateDate: | 2020:03:30 08:52:26-07:00 |
| ModifyDate: | 2020:03:30 08:52:26-07:00 |
XMP
| XMPToolkit: | 3.1-701 |
|---|---|
| Creator: | Rohan Poddar |
| CreatorTool: | Microsoft Word |
| CreateDate: | 2020:03:30 08:52:26-07:00 |
| ModifyDate: | 2020:03:30 08:52:26-07:00 |
| DocumentID: | uuid:43DAAAE8-E3AA-45EB-8BEE-7034FD14A3D7 |
| InstanceID: | uuid:43DAAAE8-E3AA-45EB-8BEE-7034FD14A3D7 |
Total processes
80
Monitored processes
43
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
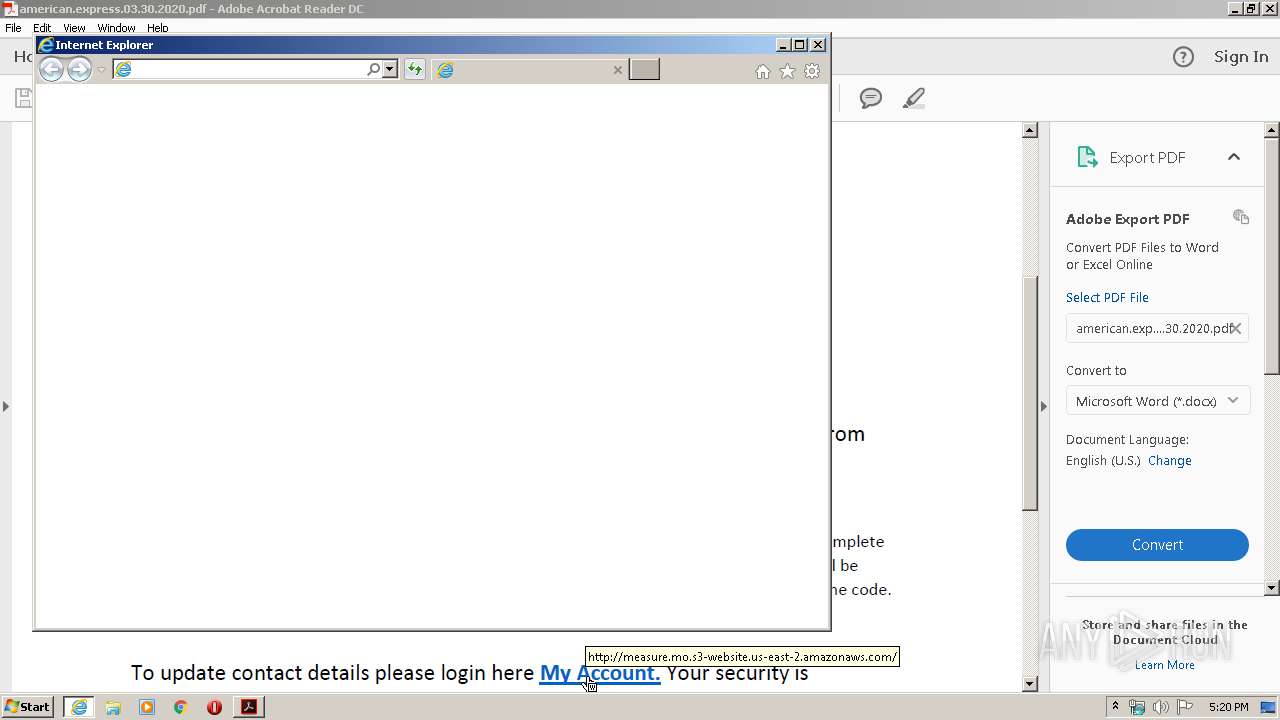
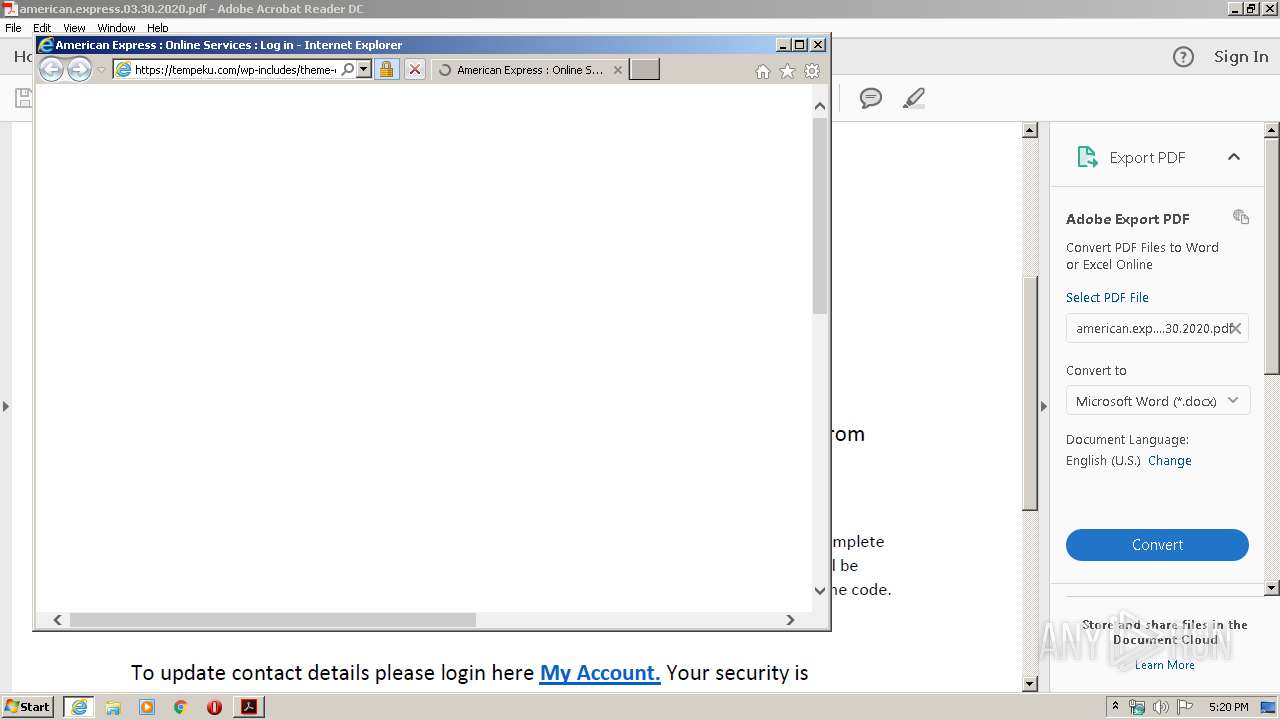
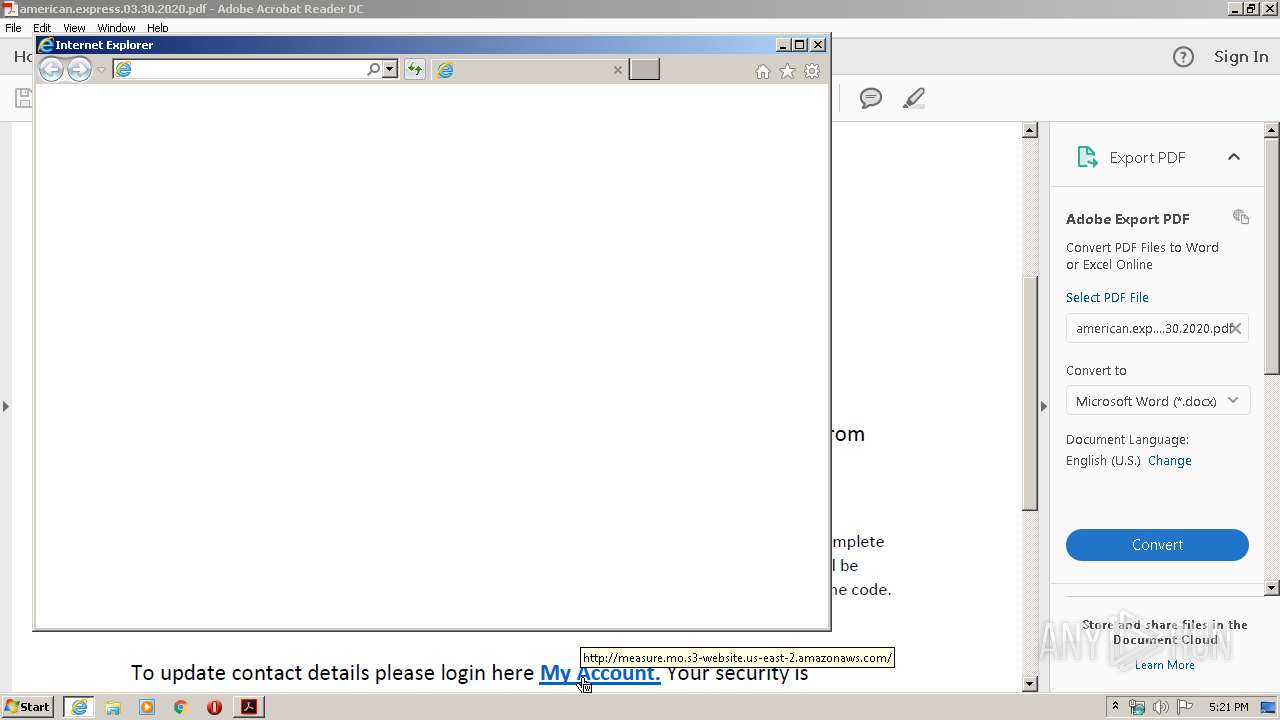
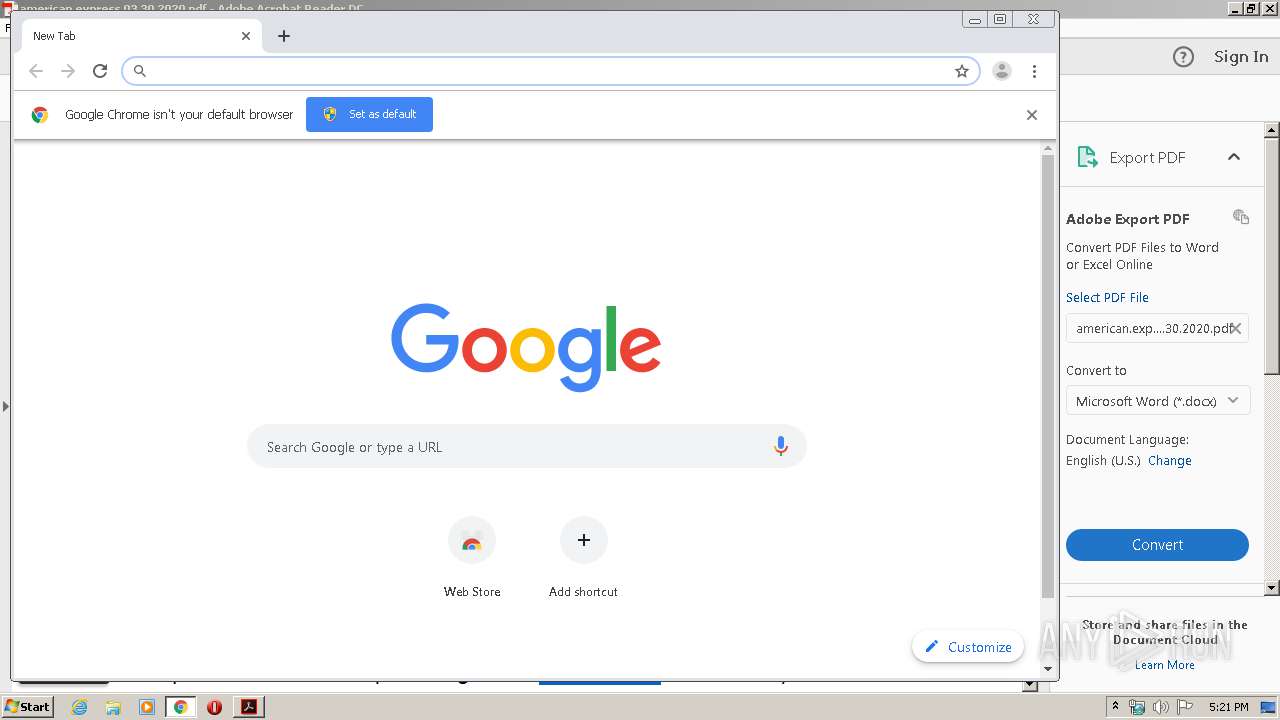
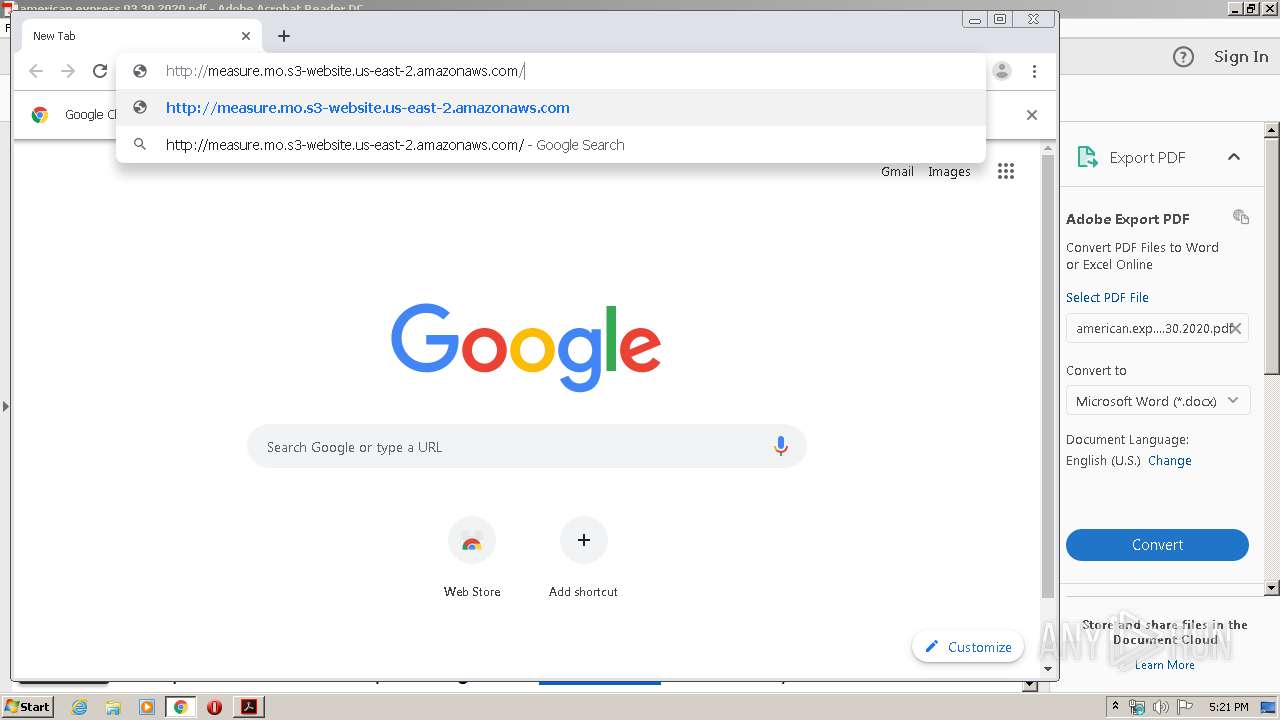
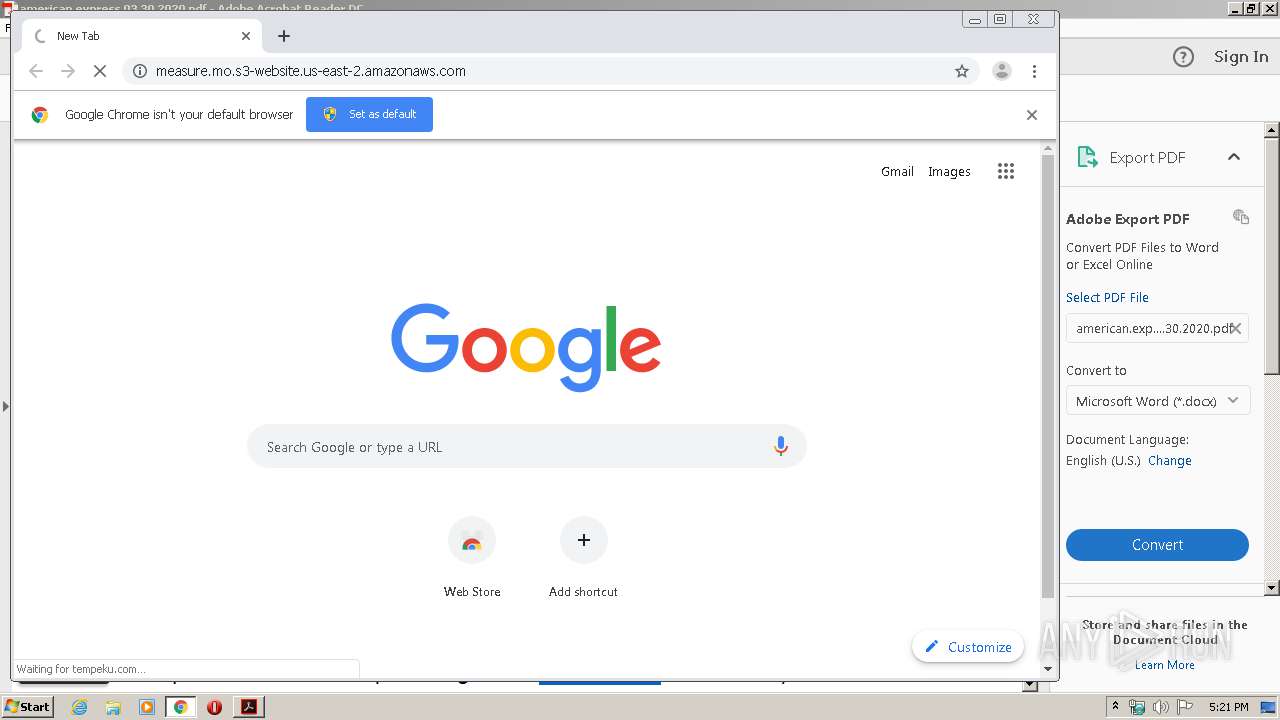
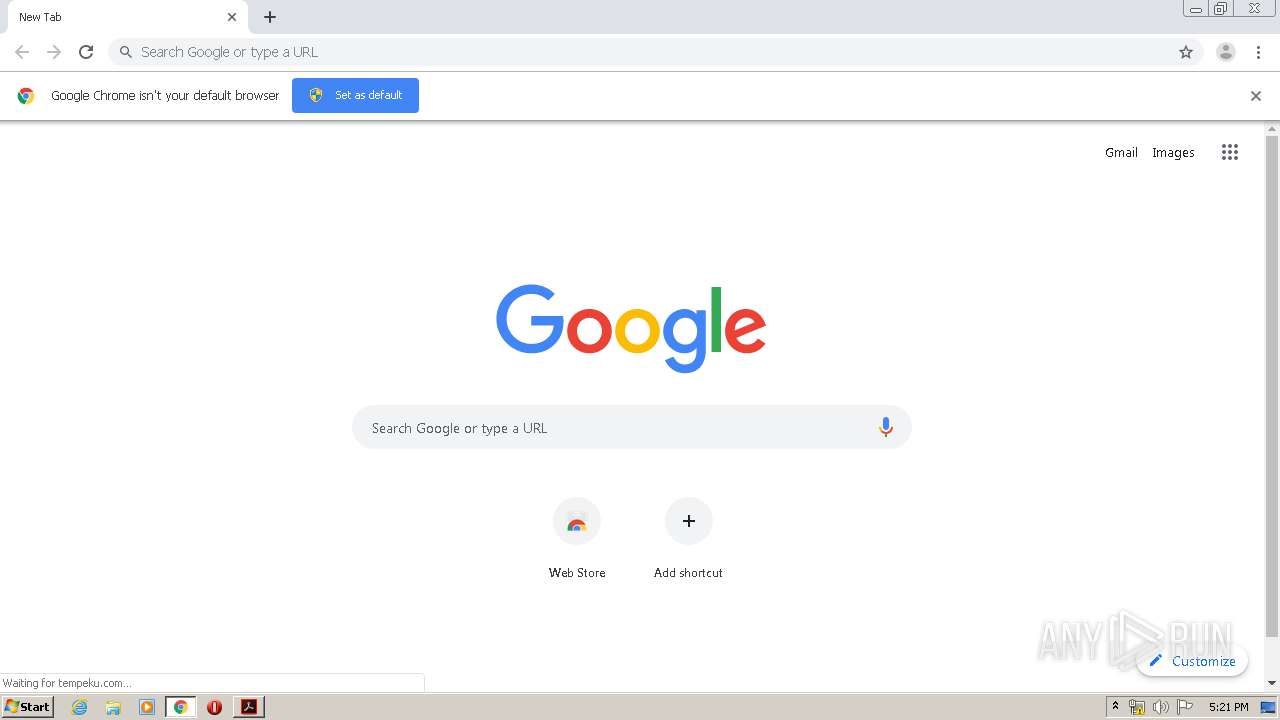
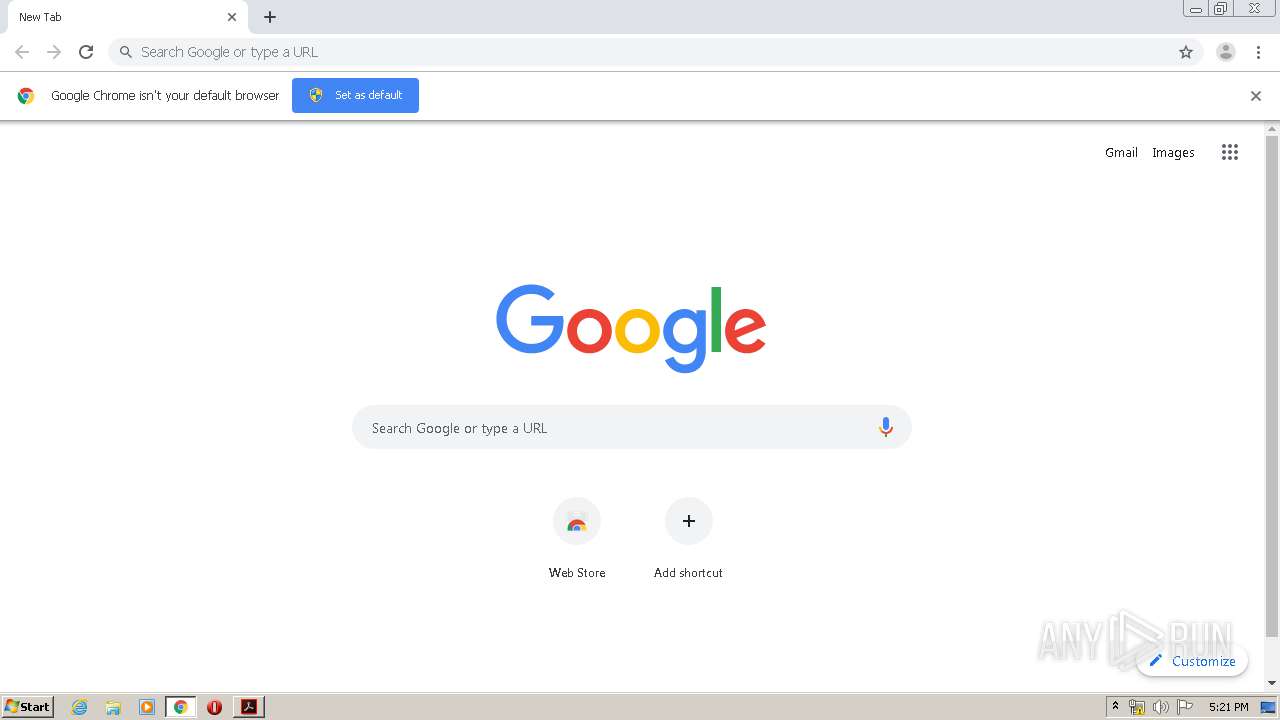
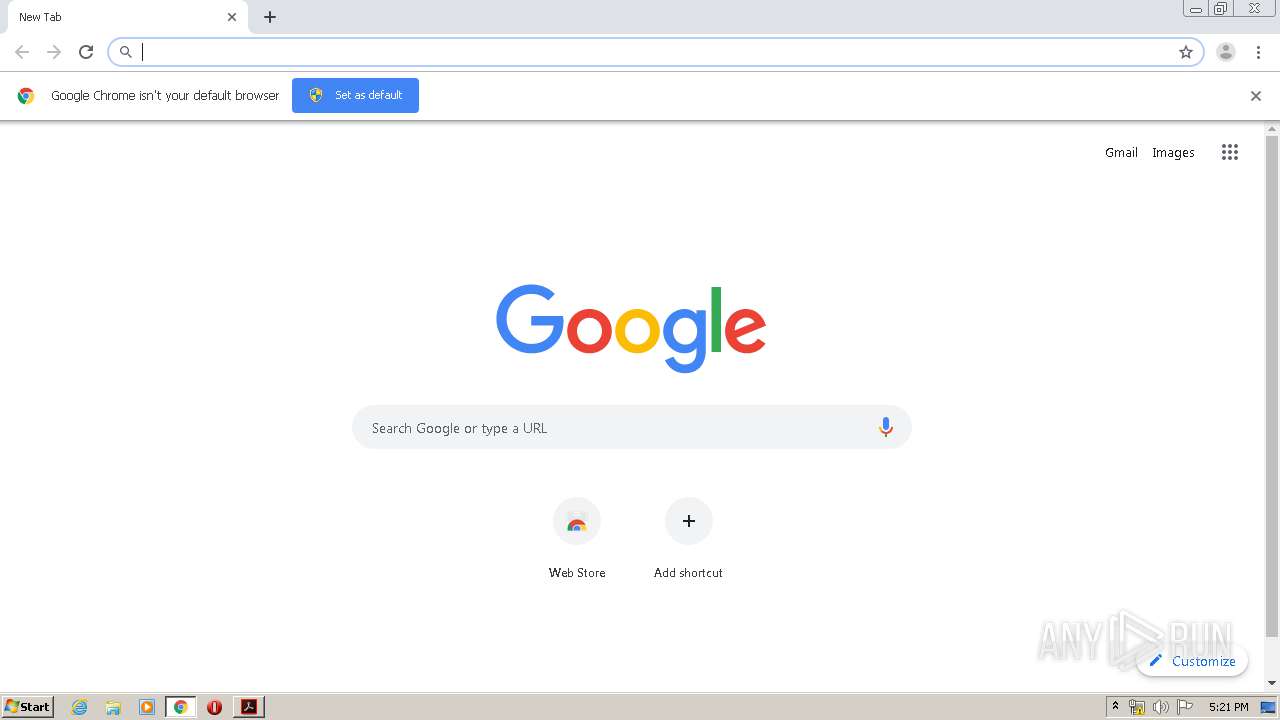
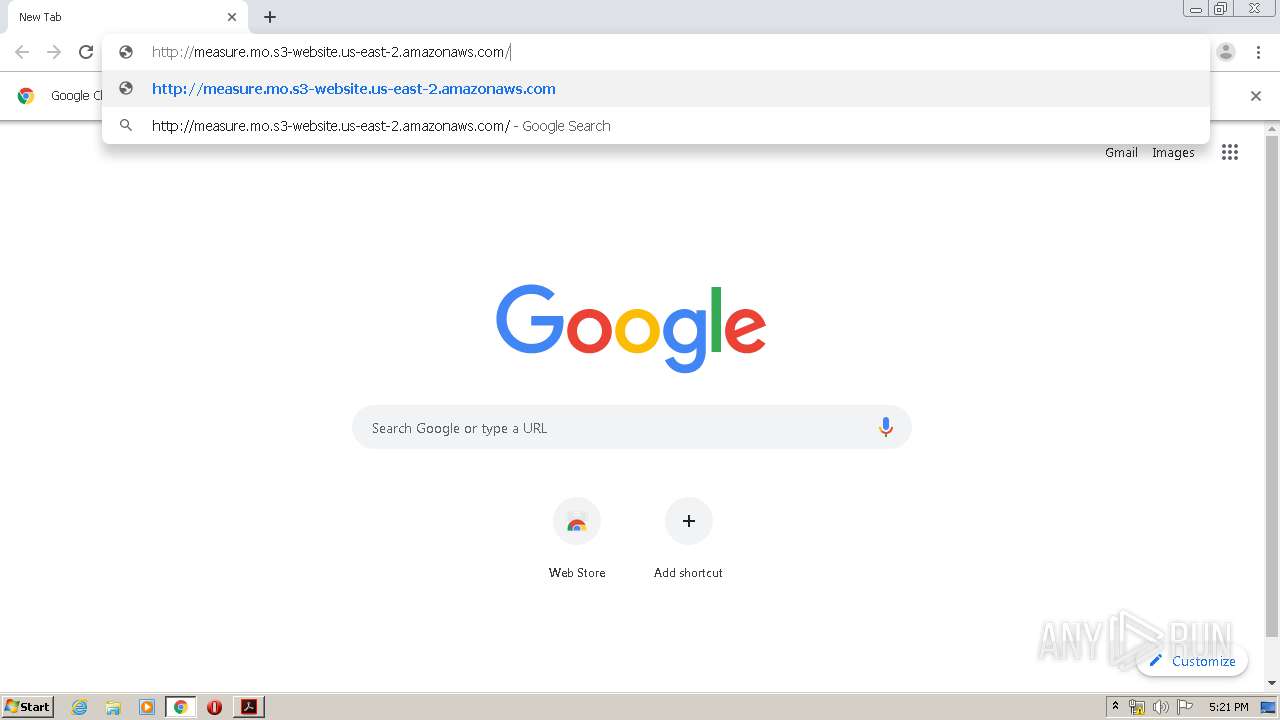
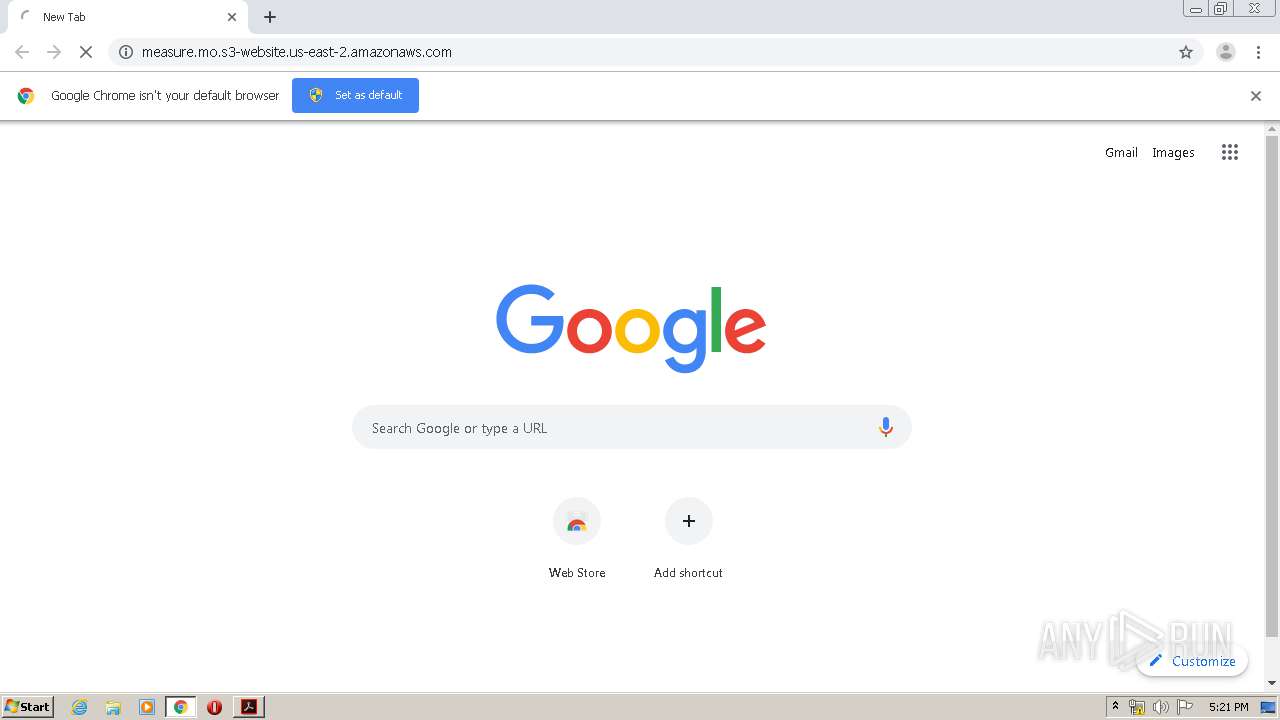
| 540 | "C:\Program Files\Internet Explorer\iexplore.exe" http://measure.mo.s3-website.us-east-2.amazonaws.com/ | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1213902477193442026,2250117146329812324,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11895109519205033475 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\american.express.03.30.2020.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1213902477193442026,2250117146329812324,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15685346483616589780 --mojo-platform-channel-handle=3508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1213902477193442026,2250117146329812324,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4167430185050226556 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1213902477193442026,2250117146329812324,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17316771383083025753 --mojo-platform-channel-handle=4120 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1213902477193442026,2250117146329812324,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10133478086696258886 --mojo-platform-channel-handle=2744 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4048 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1213902477193442026,2250117146329812324,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4018366828904603820 --mojo-platform-channel-handle=4212 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1213902477193442026,2250117146329812324,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6112458215745386160 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
7 159
Read events
1 798
Write events
3 635
Delete events
1 726
Modification events
| (PID) Process: | (1008) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (1008) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (1008) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (2856) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AcroRd32.exe |
Value: 10001 | |||
| (PID) Process: | (2856) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 01000000000000002DF30524AF06D601 | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 905697834 | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803631 | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
36
Text files
329
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1008 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab90FD.tmp | — | |
MD5:— | SHA256:— | |||
| 2892 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar90FE.tmp | — | |
MD5:— | SHA256:— | |||
| 540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1008 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1bknitk_1gp02rl_s0.tmp | — | |
MD5:— | SHA256:— | |||
| 1008 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rfppx84_1gp02rn_s0.tmp | — | |
MD5:— | SHA256:— | |||
| 1008 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rerb9j2_1gp02ro_s0.tmp | — | |
MD5:— | SHA256:— | |||
| 2892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 2892 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
| 2856 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\CabBB59.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
53
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2856 | AcroRd32.exe | GET | 304 | 23.55.110.54:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | US | — | — | whitelisted |
2192 | chrome.exe | GET | 301 | 52.219.104.211:80 | http://measure.mo.s3-website.us-east-2.amazonaws.com/ | US | — | — | shared |
2856 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | US | — | — | whitelisted |
2856 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | US | — | — | whitelisted |
2892 | iexplore.exe | GET | 301 | 52.219.80.4:80 | http://measure.mo.s3-website.us-east-2.amazonaws.com/ | US | — | — | shared |
2856 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | US | — | — | whitelisted |
2192 | chrome.exe | GET | 302 | 172.217.16.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
2892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2892 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 5.23 Kb | whitelisted |
2856 | AcroRd32.exe | GET | 200 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | US | compressed | 9.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2892 | iexplore.exe | 52.219.80.4:80 | measure.mo.s3-website.us-east-2.amazonaws.com | Amazon.com, Inc. | US | shared |
540 | iexplore.exe | 104.27.157.167:443 | tempeku.com | Cloudflare Inc | US | unknown |
2856 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2892 | iexplore.exe | 104.27.157.167:443 | tempeku.com | Cloudflare Inc | US | unknown |
540 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2892 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2856 | AcroRd32.exe | 23.55.110.79:80 | acroipm2.adobe.com | NTT America, Inc. | US | suspicious |
2192 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2192 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
540 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
measure.mo.s3-website.us-east-2.amazonaws.com |
| shared |
tempeku.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |