| File name: | config.ps1 |
| Full analysis: | https://app.any.run/tasks/027684c2-250e-4eb3-9a89-3a324daf107a |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 19:32:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with very long lines (447), with CRLF line terminators |
| MD5: | 1B155E9C3D9FFB95B0579E8B40B99B1B |
| SHA1: | 441547660A8119B2BD0847F378FEA847F080F3F5 |
| SHA256: | FAEC6F9DE09C51FDA25FAC4218756B38A42C34E48901C8676A45C8AA037BFA7A |
| SSDEEP: | 192:0k8lYYya+Eo7myQ0tudYVk8NkWZrj1qZ3dsq/dsJH47hWAlbWAb:zqPya+9myQ0odYqKkWZn1qxumuJY7hWg |
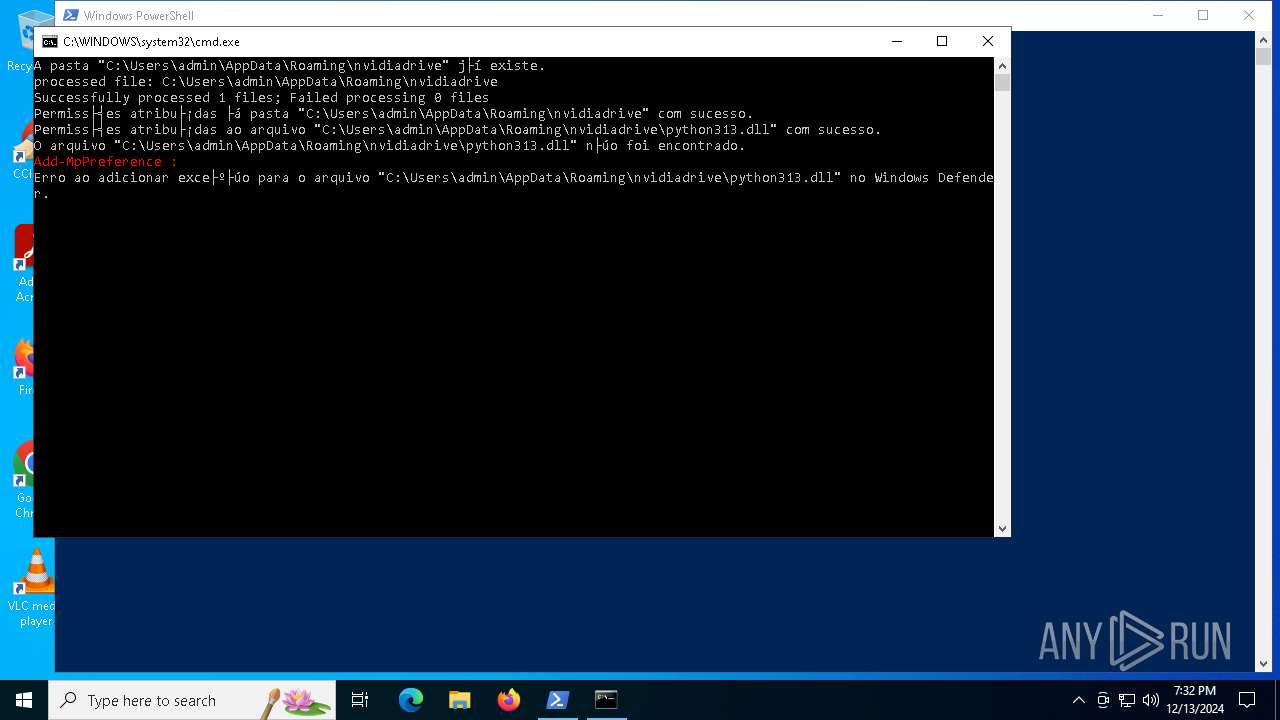
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5092)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 5092)
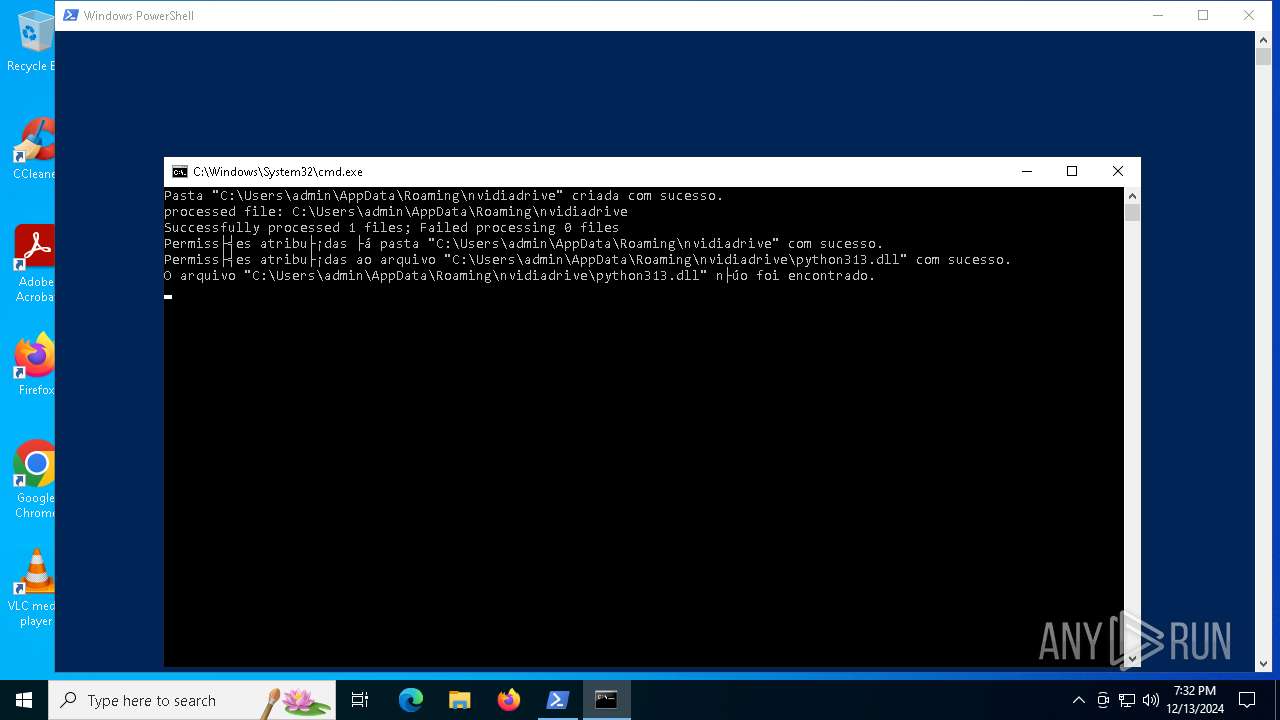
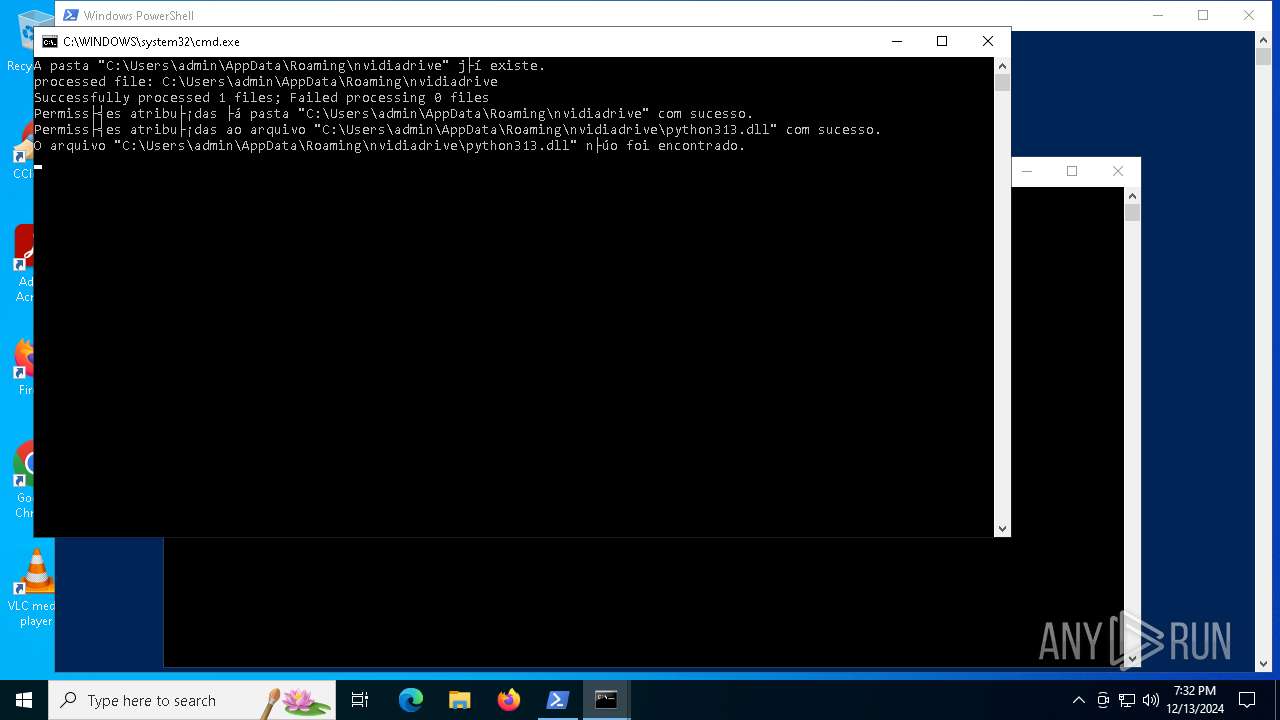
Adds process to the Windows Defender exclusion list
- cmd.exe (PID: 1200)
- cmd.exe (PID: 3620)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 1200)
- cmd.exe (PID: 3620)
Create files in the Startup directory
- powershell.exe (PID: 5092)
Changes the autorun value in the registry
- ©N03PZ.exe (PID: 5544)
SUSPICIOUS
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5092)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 5092)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5092)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 1200)
- cmd.exe (PID: 3620)
Script adds exclusion process to Windows Defender
- cmd.exe (PID: 3620)
- cmd.exe (PID: 1200)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 1200)
- cmd.exe (PID: 3620)
Executing commands from a ".bat" file
- powershell.exe (PID: 5092)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1200)
- cmd.exe (PID: 3620)
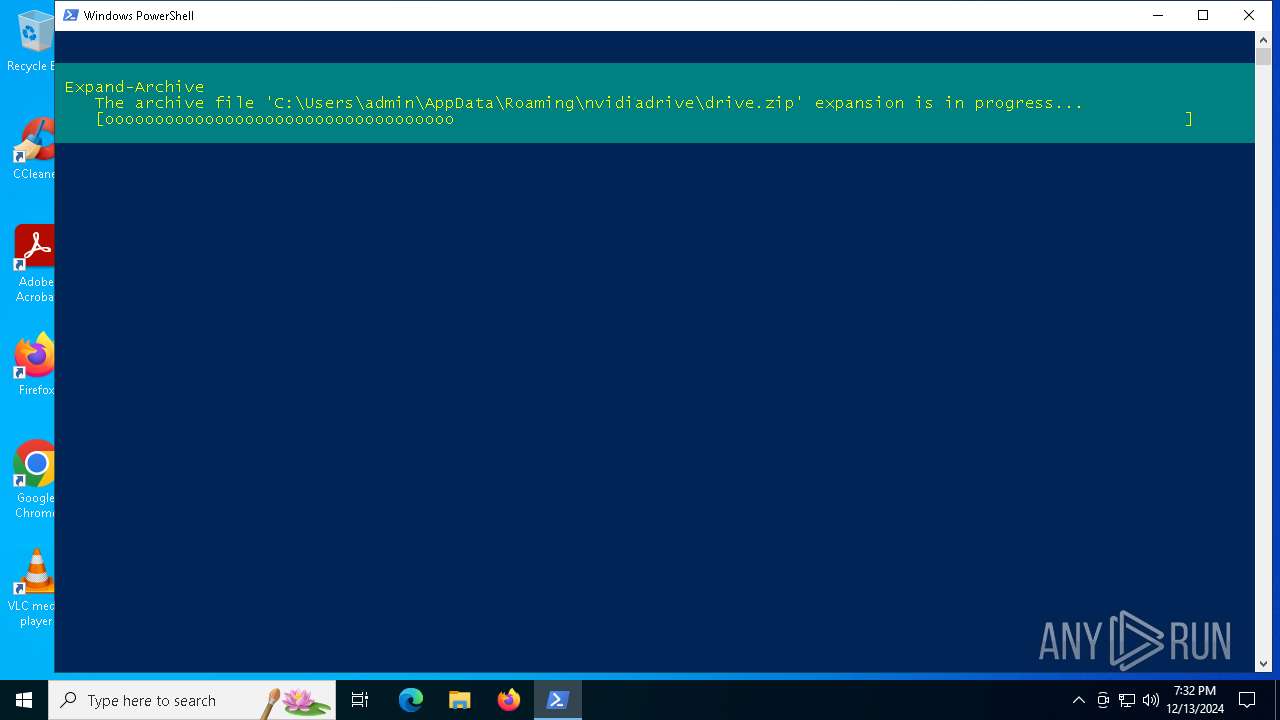
Executable content was dropped or overwritten
- powershell.exe (PID: 5092)
Process drops legitimate windows executable
- powershell.exe (PID: 5092)
The process drops C-runtime libraries
- powershell.exe (PID: 5092)
Loads Python modules
- ©N03PZ.exe (PID: 5544)
INFO
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5092)
- powershell.exe (PID: 1988)
- powershell.exe (PID: 2512)
- powershell.exe (PID: 904)
- powershell.exe (PID: 4556)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5092)
Disables trace logs
- powershell.exe (PID: 5092)
Checks proxy server information
- powershell.exe (PID: 5092)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5092)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1988)
- powershell.exe (PID: 2512)
- powershell.exe (PID: 4556)
- powershell.exe (PID: 904)
The process uses the downloaded file
- powershell.exe (PID: 5092)
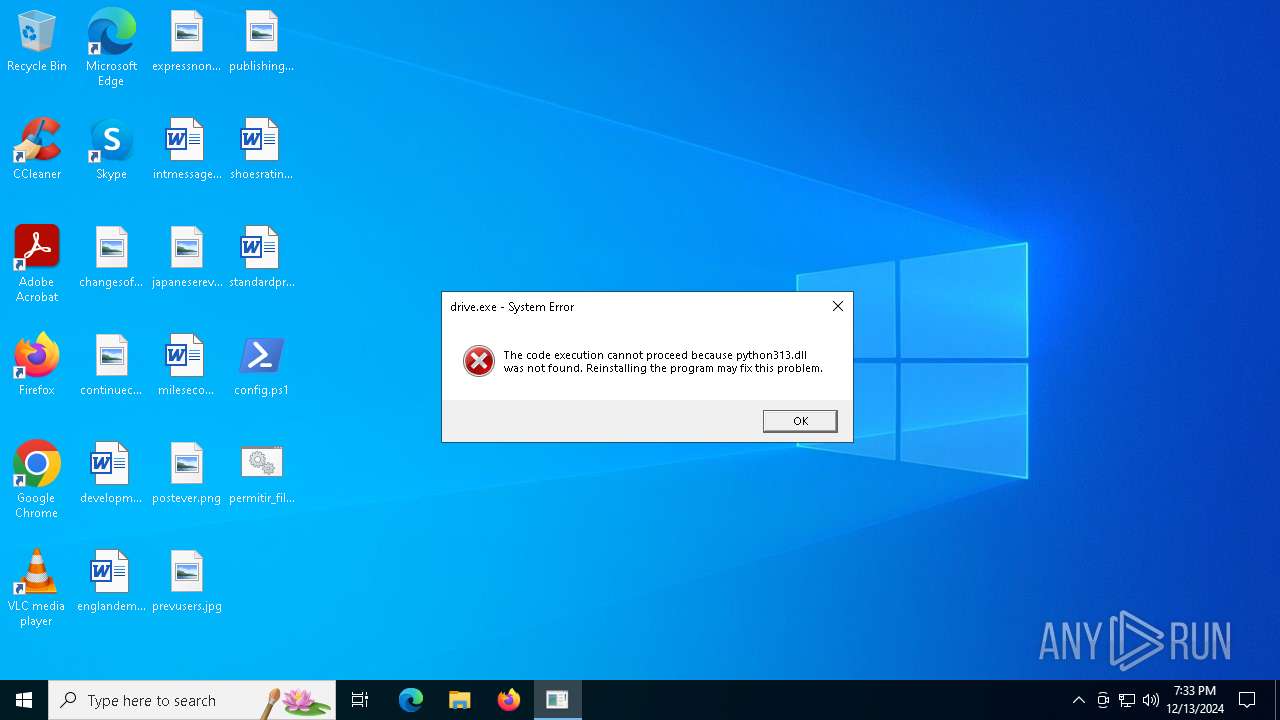
Manual execution by a user
- cmd.exe (PID: 3620)
- drive.exe (PID: 4704)
The sample compiled with english language support
- powershell.exe (PID: 5092)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5092)
The executable file from the user directory is run by the Powershell process
- ©N03PZ.exe (PID: 5544)
Python executable
- ©N03PZ.exe (PID: 5544)
- drive.exe (PID: 4704)
Reads the computer name
- ©N03PZ.exe (PID: 5544)
Reads the software policy settings
- ©N03PZ.exe (PID: 5544)
Reads the machine GUID from the registry
- ©N03PZ.exe (PID: 5544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
14
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming\nvidiadrive'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\DXFgJhmTlQ.bat | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1988 | powershell -Command "Add-MpPreference -ExclusionProcess 'C:\Users\admin\AppData\Roaming\nvidiadrive\python313.dll'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2512 | powershell -Command "Add-MpPreference -ExclusionProcess 'C:\Users\admin\AppData\Roaming\nvidiadrive\python313.dll'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2940 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3260 | icacls "C:\Users\admin\AppData\Roaming\nvidiadrive" /grant "admin":(F) /T | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\permitir_file.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4556 | powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming\nvidiadrive'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4704 | "C:\Users\admin\Desktop\drive.exe" | C:\Users\admin\Desktop\drive.exe | — | explorer.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 3221225781 Version: 3.13.0a5 Modules
| |||||||||||||||
| 5008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 134
Read events
31 133
Write events
1
Delete events
0
Modification events
| (PID) Process: | (5544) ©N03PZ.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ¡8Œ5G0w265Ø5 |
Value: C:\Users\admin\AppData\Roaming\nvidiadrive\©N03PZ.exe | |||
Executable files
4
Suspicious files
8
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5092 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_am3cky1c.x4o.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5092 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BZX57NOQMFL51HQTLU0W.temp | binary | |
MD5:1B9FE87FD349082FBFF8AB4D64D9A23F | SHA256:70970EEBEAD912ED11F7F293DF238A717CA704613D3365003751B17F3A2ABDB6 | |||
| 5092 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_regwhlqr.sug.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5092 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:1B9FE87FD349082FBFF8AB4D64D9A23F | SHA256:70970EEBEAD912ED11F7F293DF238A717CA704613D3365003751B17F3A2ABDB6 | |||
| 5092 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF13641c.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 5544 | ©N03PZ.exe | C:\Users\admin\AppData\Roaming\26B799FA | — | |
MD5:— | SHA256:— | |||
| 5092 | powershell.exe | C:\Users\admin\AppData\Local\Temp\permitir_file.zip | compressed | |
MD5:7DEEC11B21C0F7C89A3BB045031BFA8F | SHA256:5D1769AE751DA976E8E9EC27249CA4021B8A745556E352F55F2789E36BD5F9D5 | |||
| 4556 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5rig5m30.emn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5092 | powershell.exe | C:\Users\admin\AppData\Roaming\nvidiadrive\drive.zip | compressed | |
MD5:3F32D0DCE3F9F5EB354E3AED4CDC399E | SHA256:EC65C65D6D2B8383F919424BE9E0B9400F98DEBBA9A63305FF8B48846F404E67 | |||
| 1988 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fib1gqn5.lg5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
26
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.170:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.129:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.170:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
servicosfaturas.app |
| unknown |
servicespc.app |
| unknown |
self.events.data.microsoft.com |
| whitelisted |