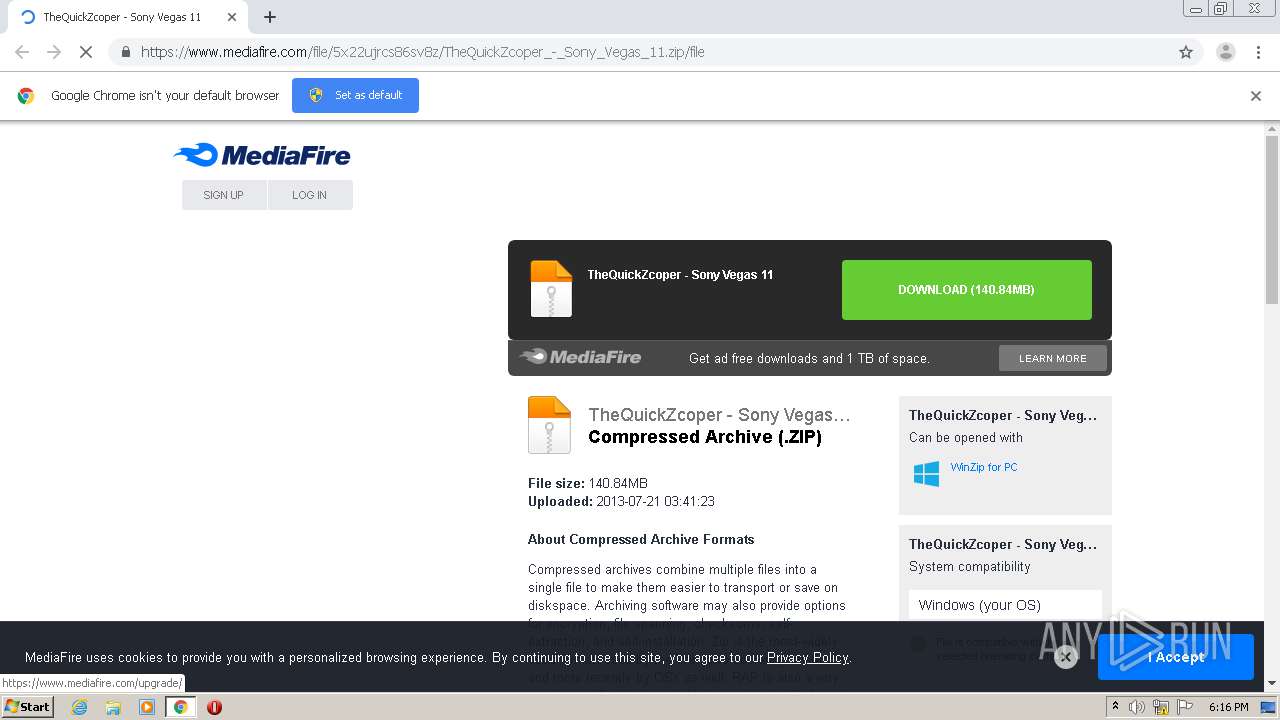
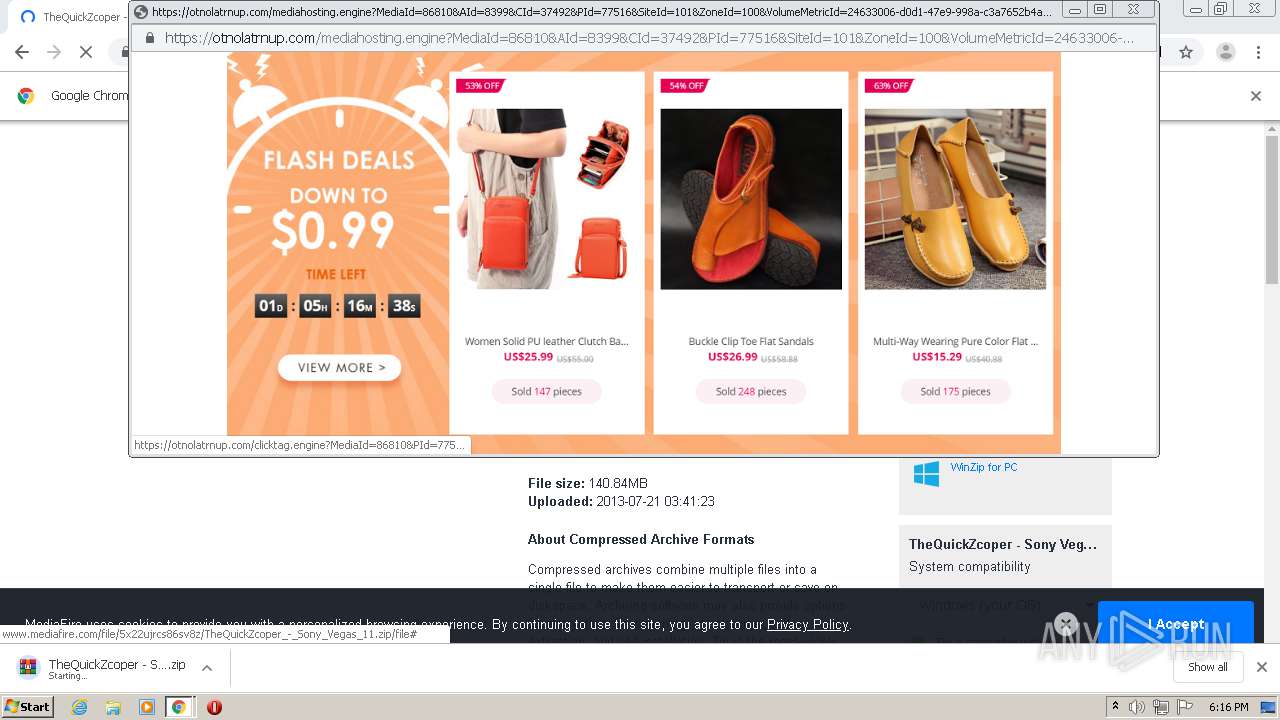
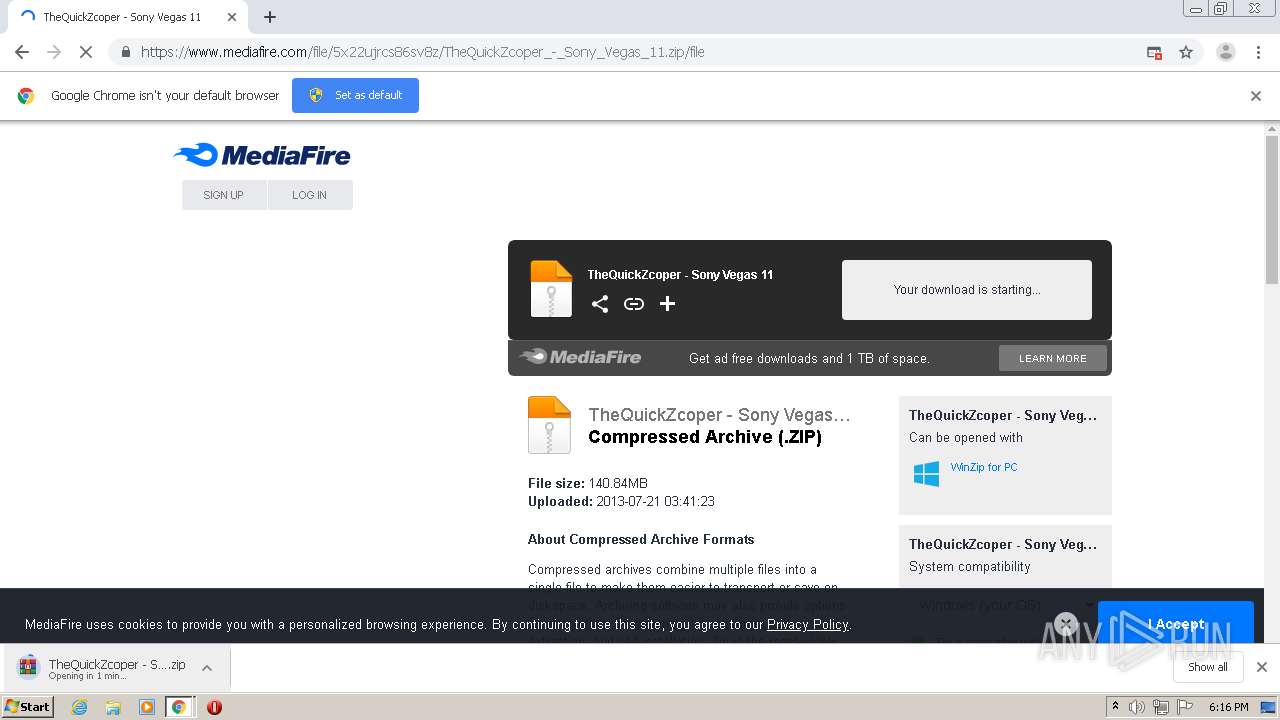
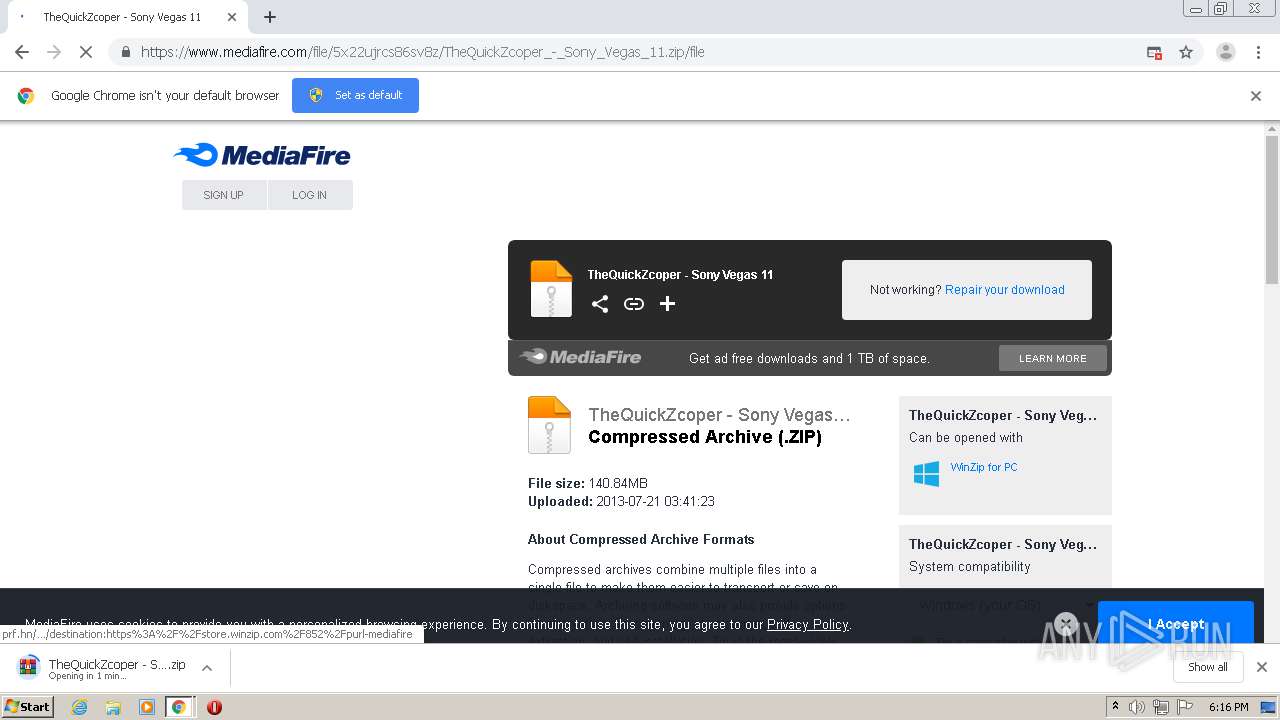
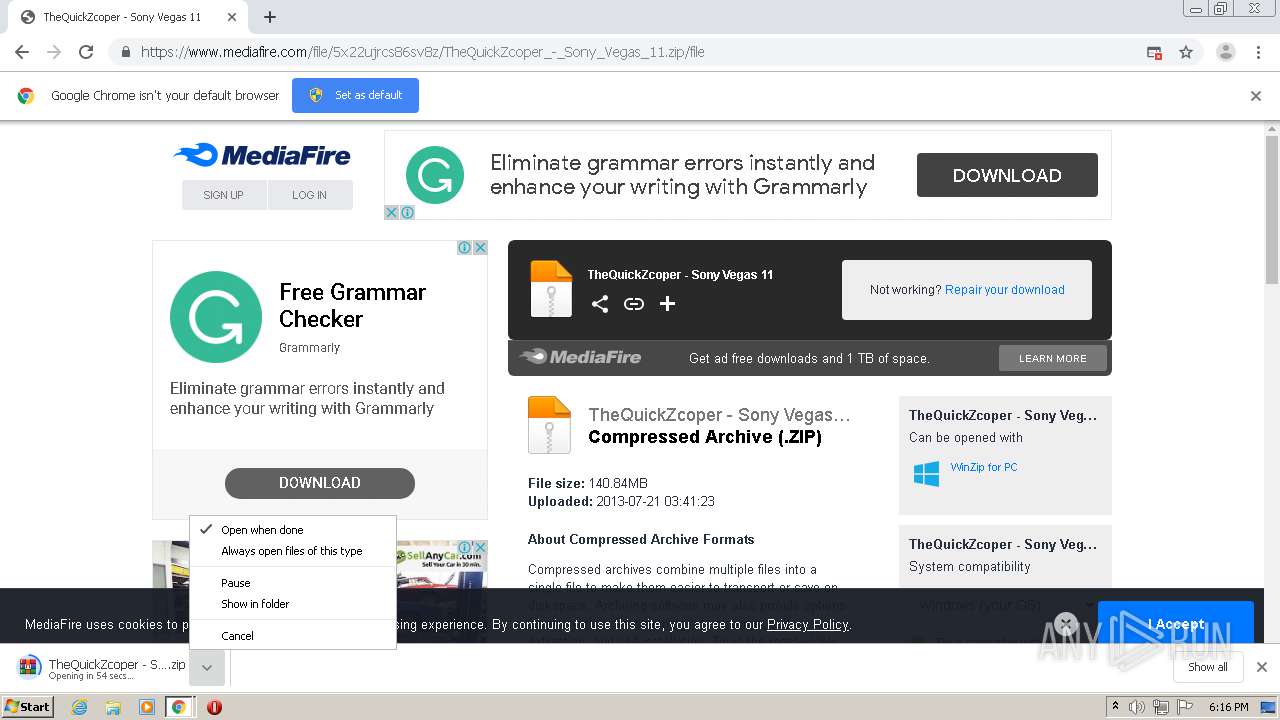
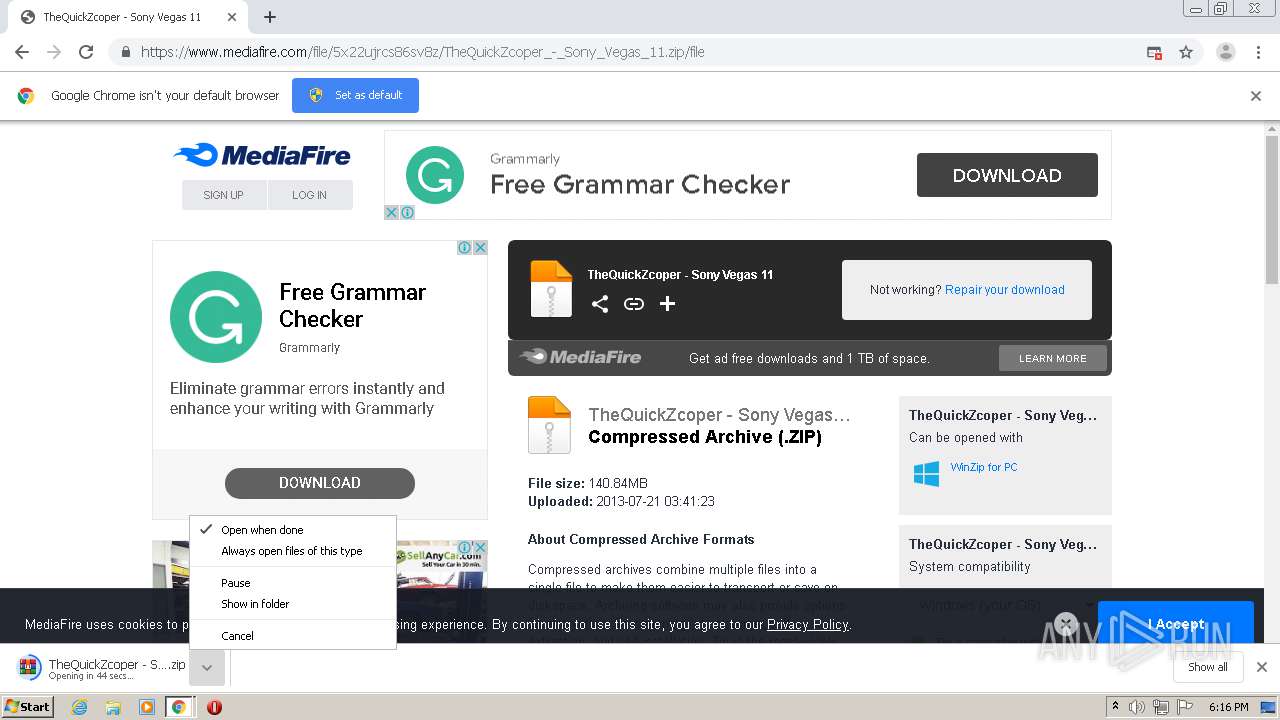
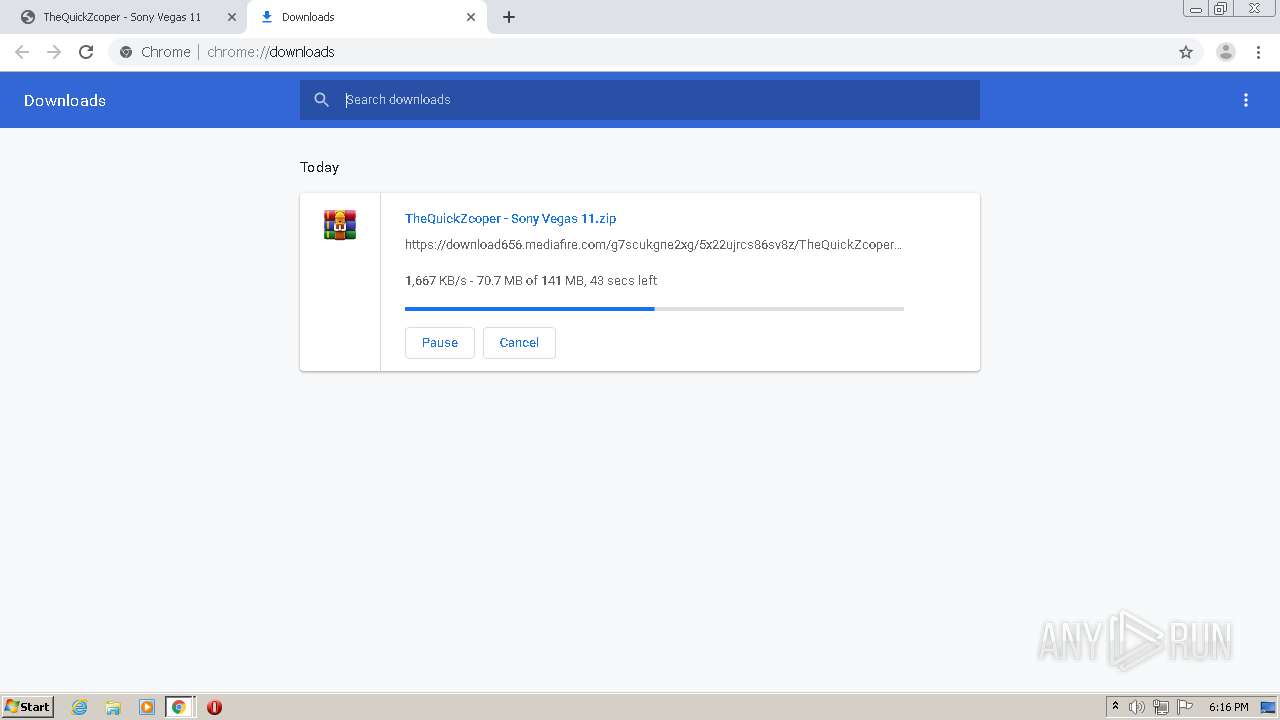
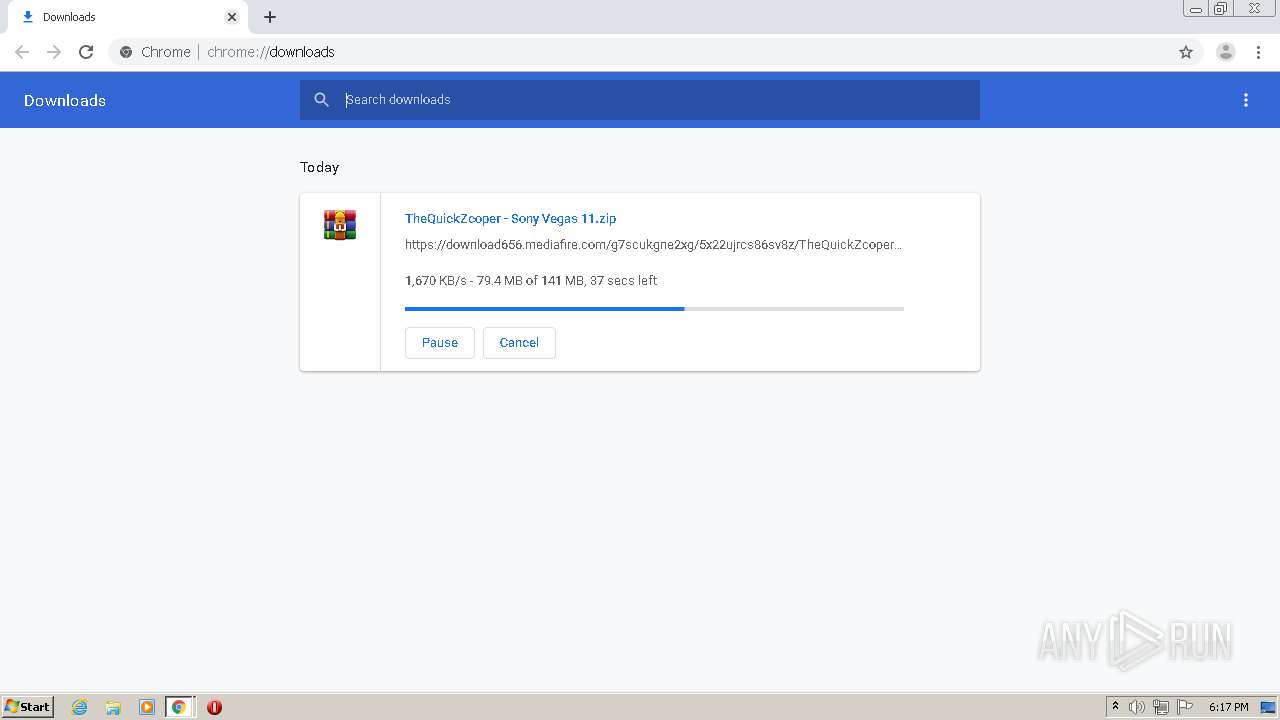
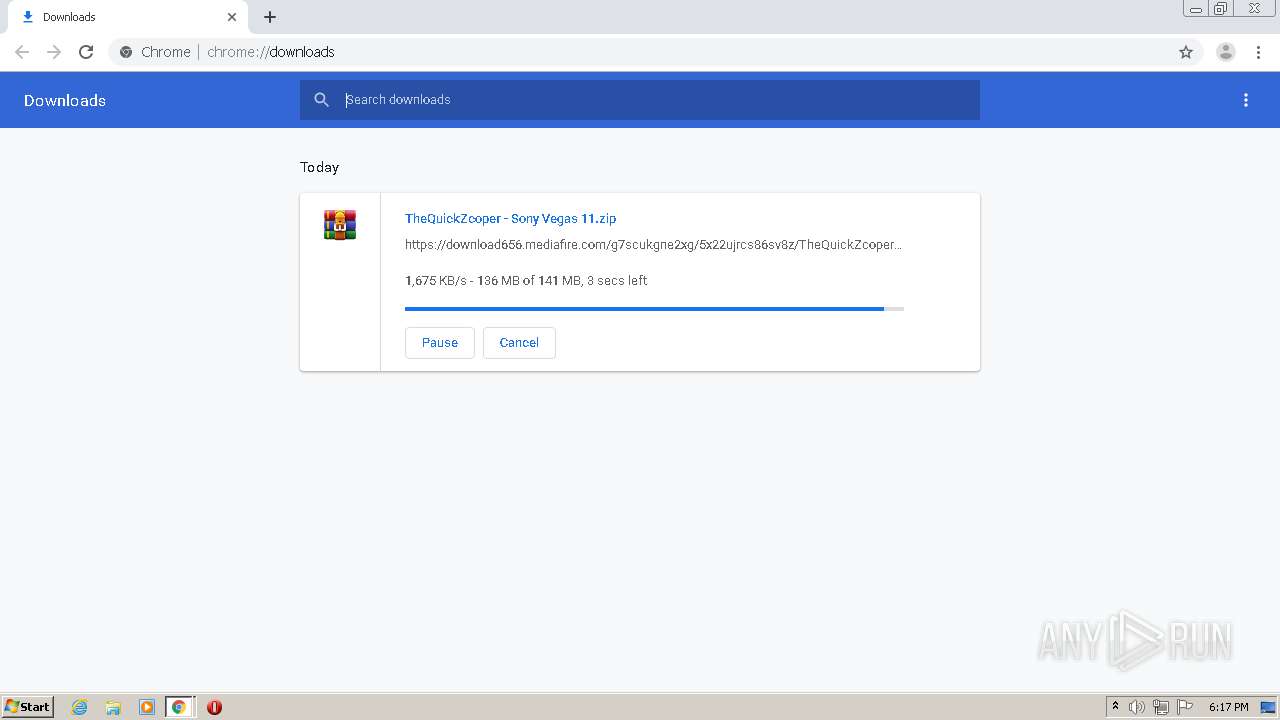
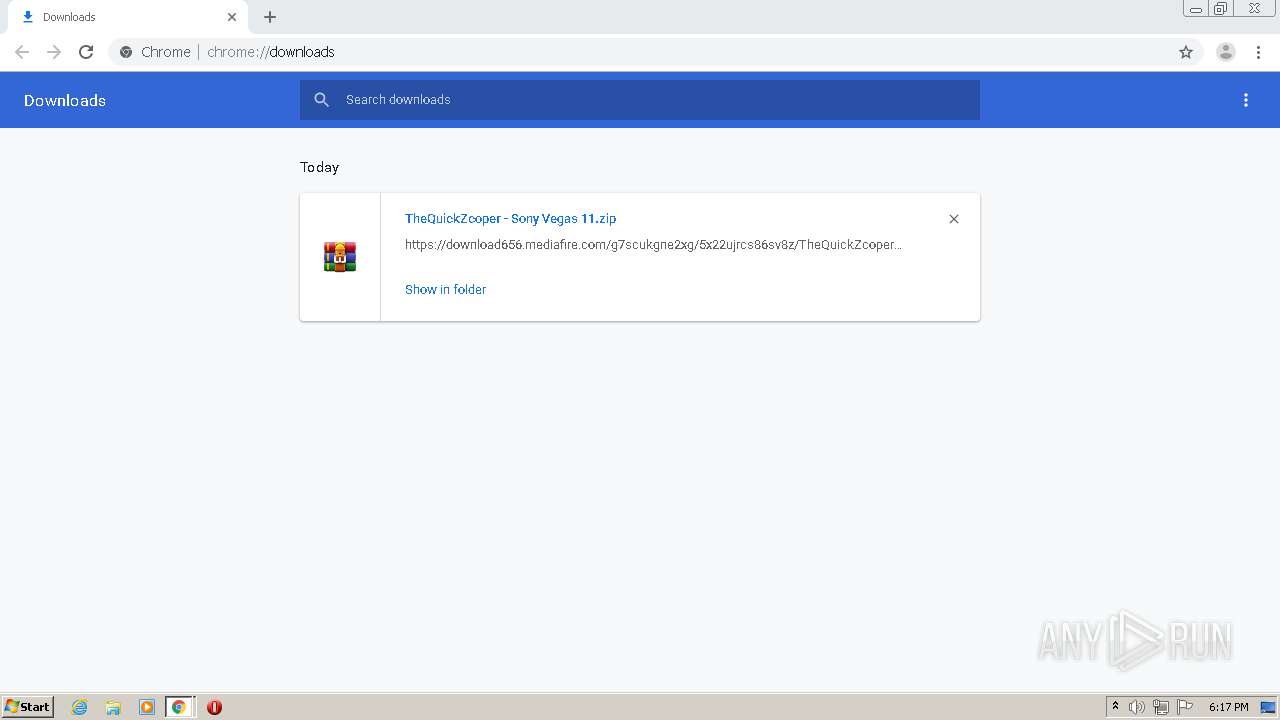
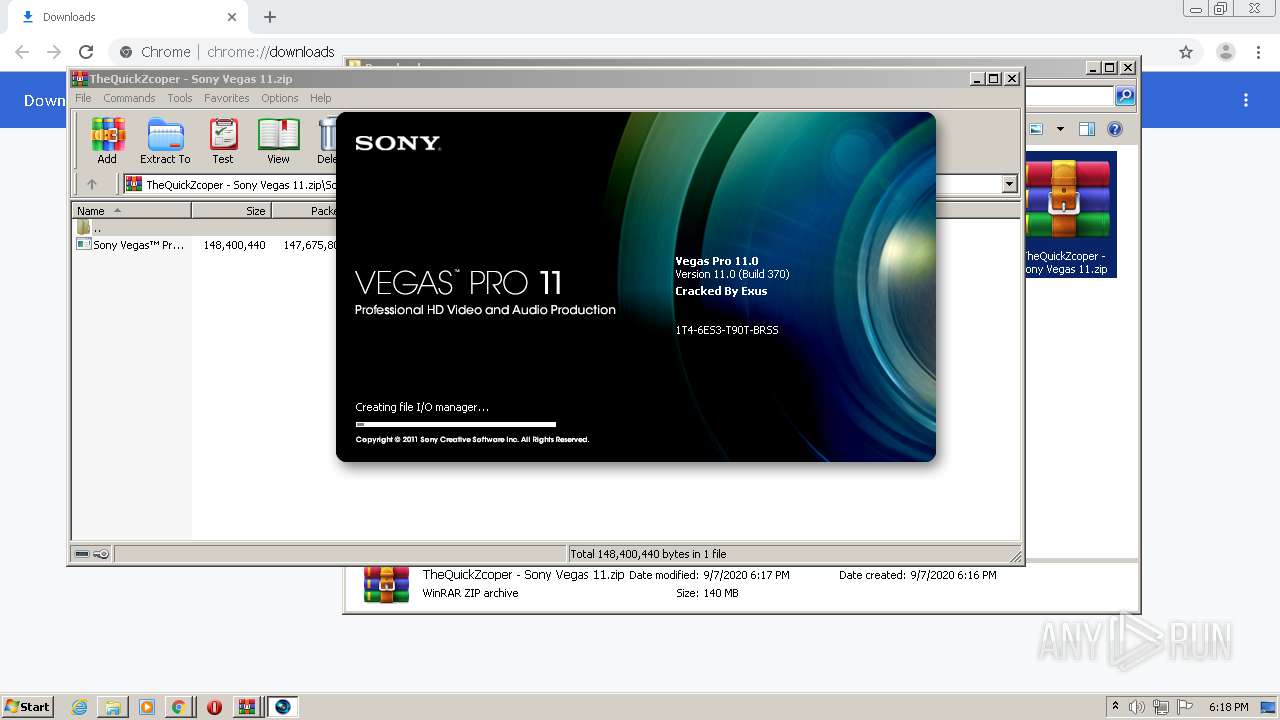
| URL: | https://www.mediafire.com/file/5x22ujrcs86sv8z/TheQuickZcoper_-_Sony_Vegas_11.zip/file |
| Full analysis: | https://app.any.run/tasks/8fa72262-b03b-47e9-bef8-edaaf696849e |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2020, 17:15:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D33D906ABD8C397E6937D00708FB5059 |
| SHA1: | A63EB3B61982D59076EE8180E7AB756A21C2ED14 |
| SHA256: | FAE47EA41184A6BFCC5642E564702F36A373AE352188AA8C0ED314376390EC52 |
| SSDEEP: | 3:N8DSLw3eGUoQVATYd22w9C6eaVo:2OLw3eGeNpw8vay |
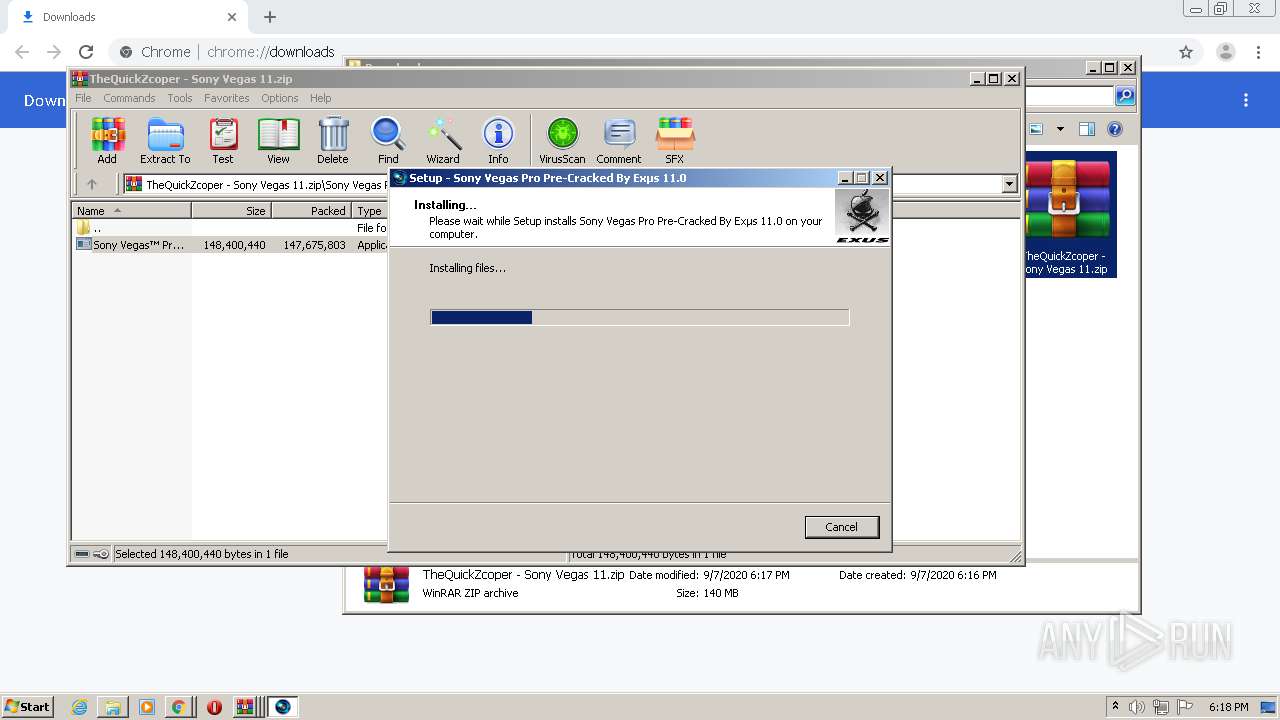
MALICIOUS
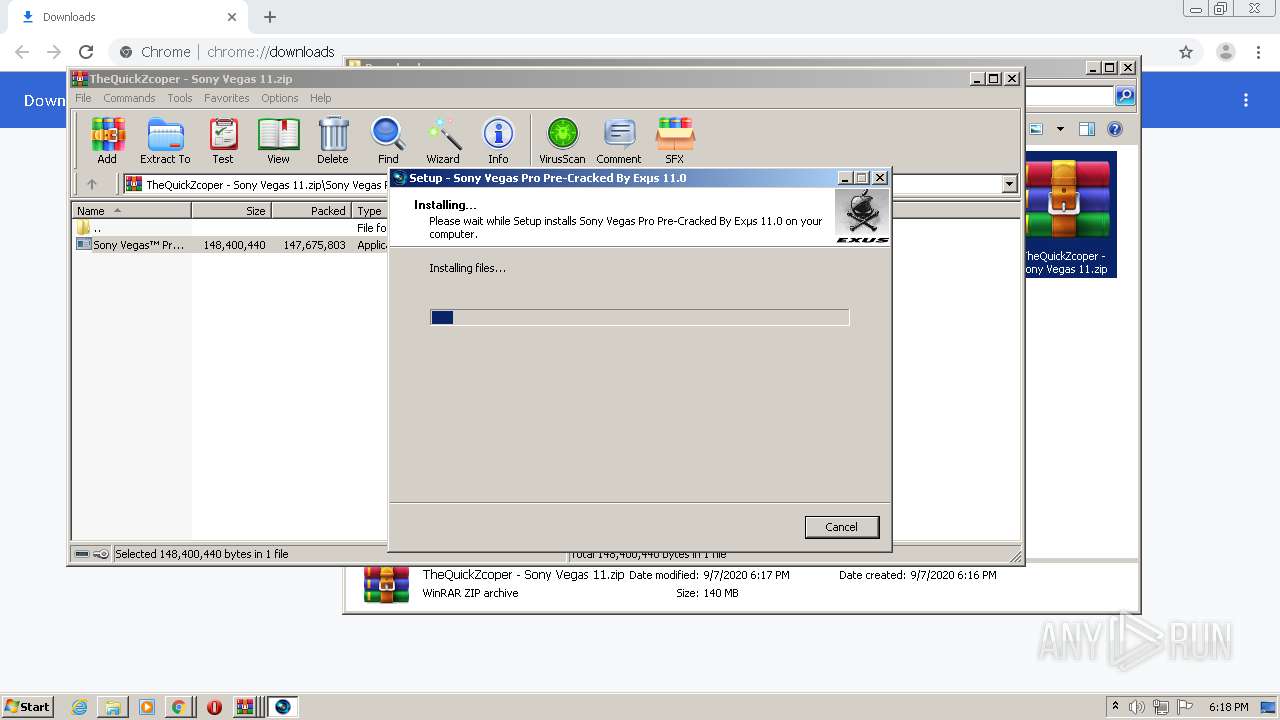
Loads dropped or rewritten executable
- FileIOSurrogate.exe (PID: 2064)
- FileIOSurrogate.exe (PID: 2108)
- vegas110.exe (PID: 3448)
- FileIOSurrogate.exe (PID: 2772)
Application was dropped or rewritten from another process
- ErrorReportLauncher.exe (PID: 2388)
- vegas110.exe (PID: 3448)
- FileIOSurrogate.exe (PID: 2108)
- FileIOSurrogate.exe (PID: 2064)
- FileIOSurrogate.exe (PID: 2772)
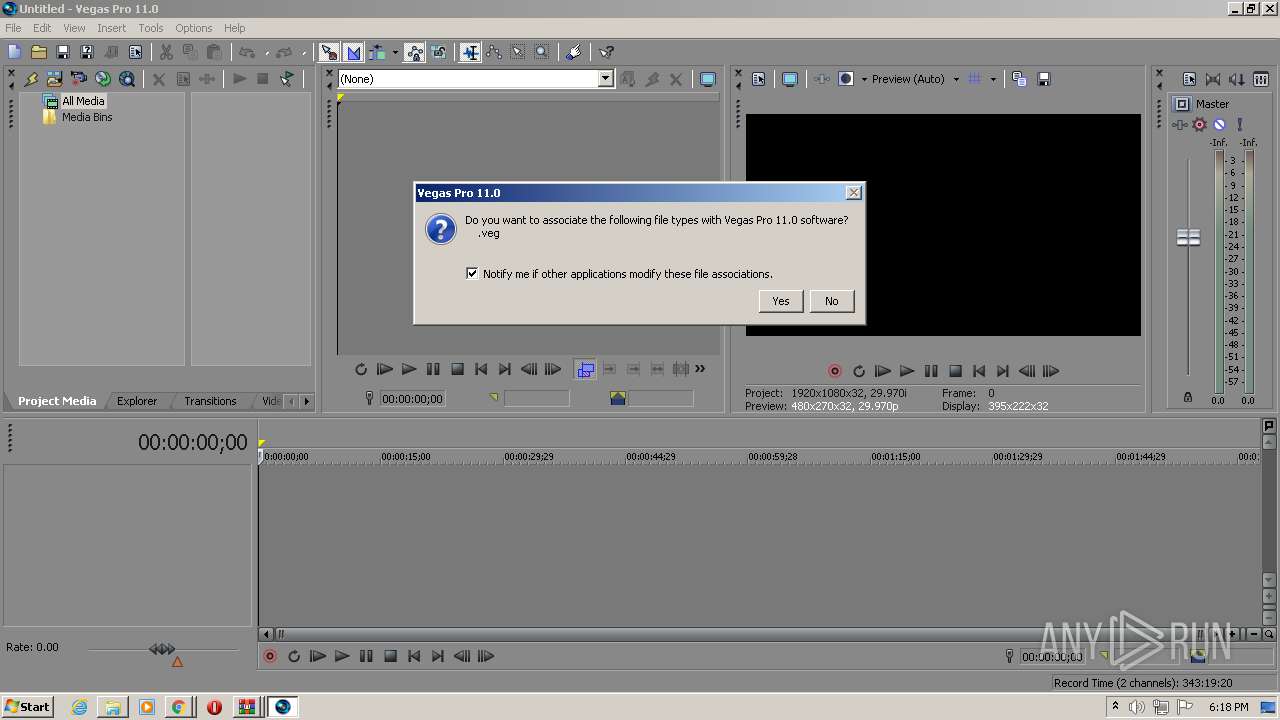
SUSPICIOUS
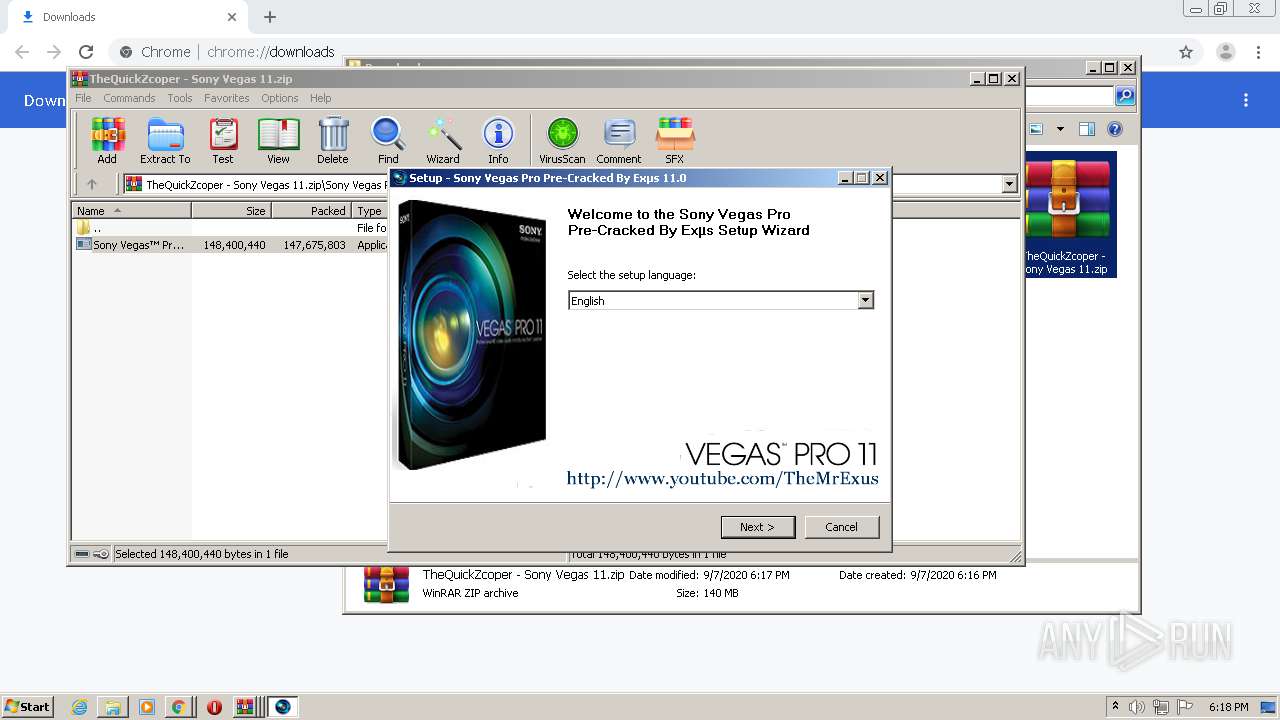
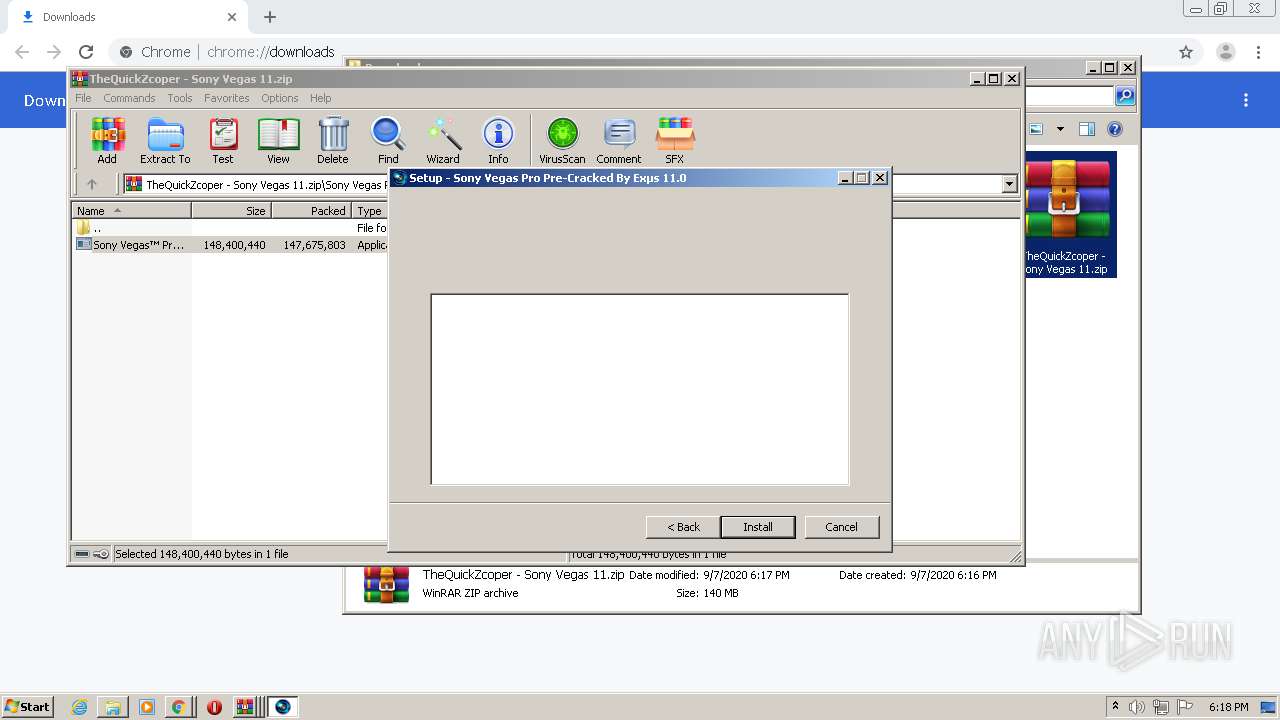
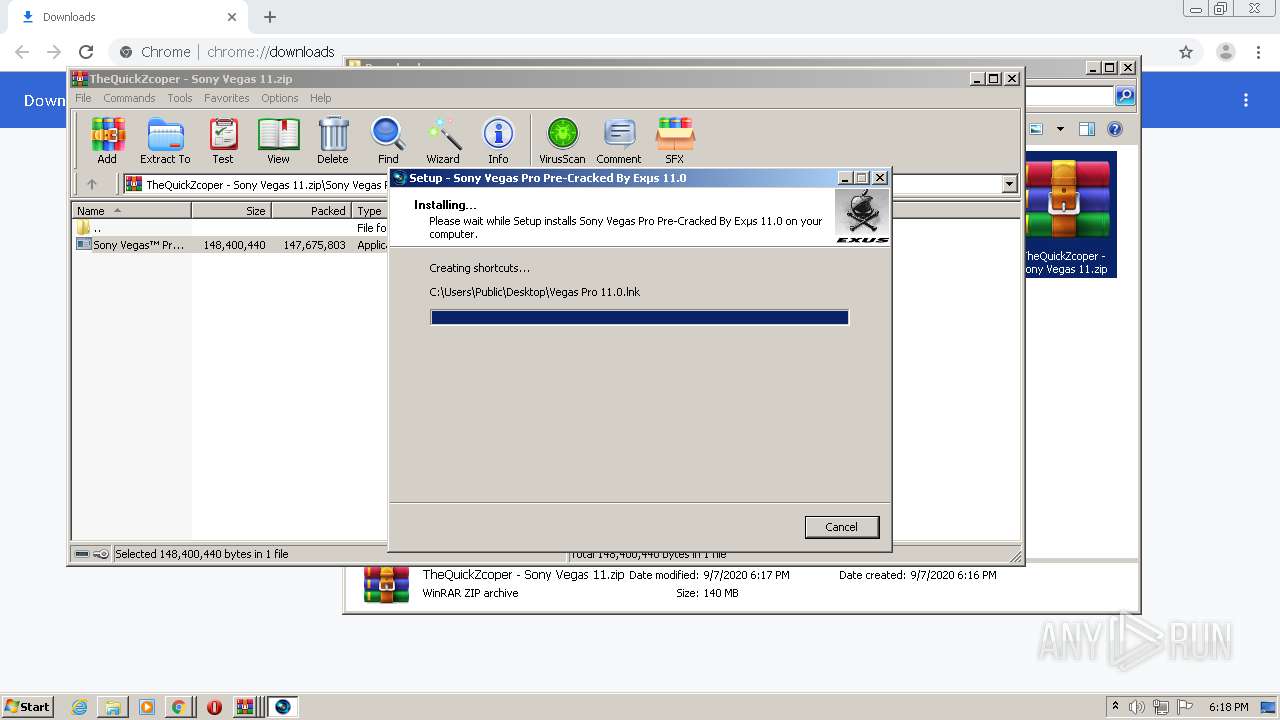
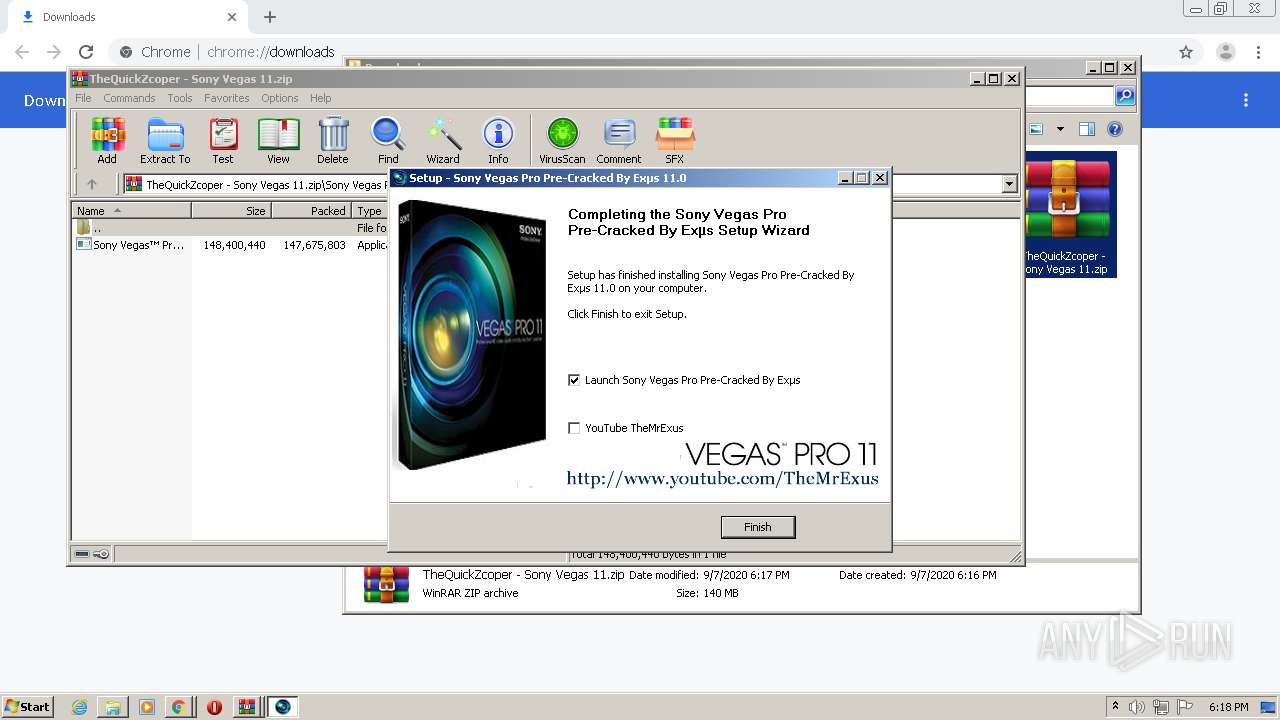
Creates a software uninstall entry
- Sony Vegas™ Pro 11 SetUp.exe (PID: 3252)
Creates files in the user directory
- vegas110.exe (PID: 3448)
Executed as Windows Service
- PresentationFontCache.exe (PID: 3948)
Modifies the open verb of a shell class
- vegas110.exe (PID: 3448)
Reads Internet Cache Settings
- vegas110.exe (PID: 3448)
Executable content was dropped or overwritten
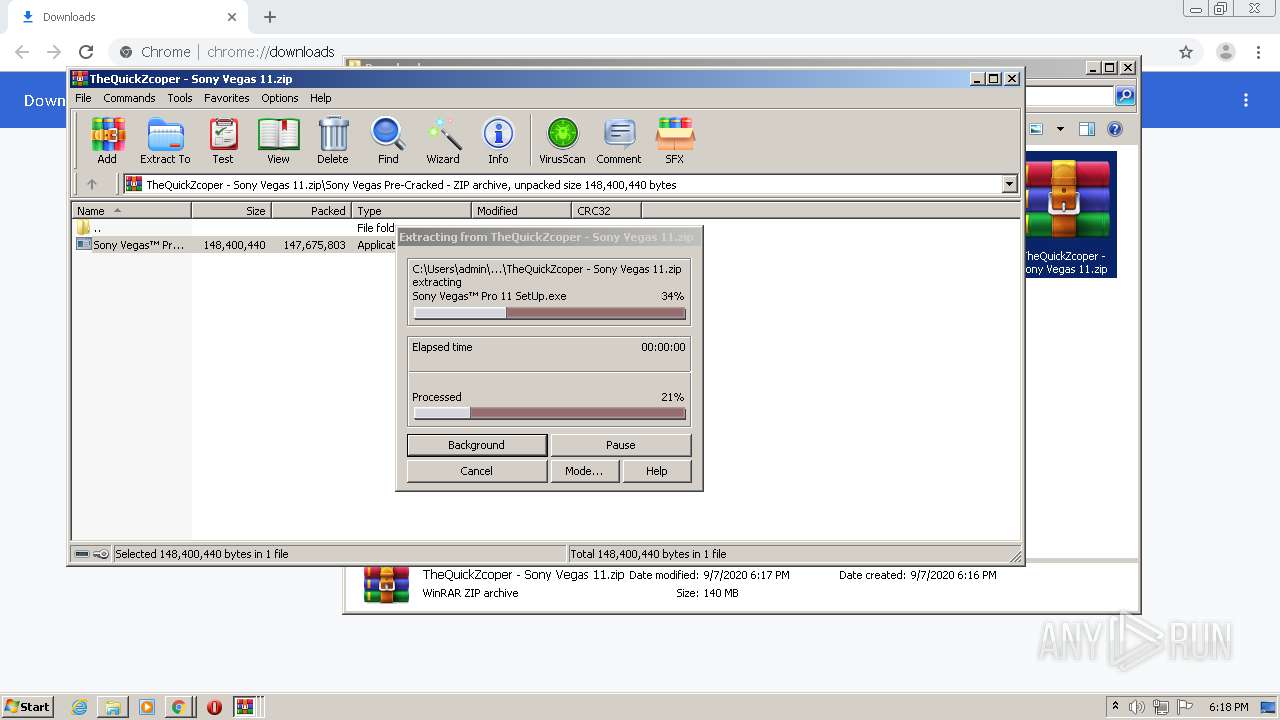
- Sony Vegas™ Pro 11 SetUp.exe (PID: 3252)
Creates files in the program directory
- Sony Vegas™ Pro 11 SetUp.exe (PID: 3252)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 1900)
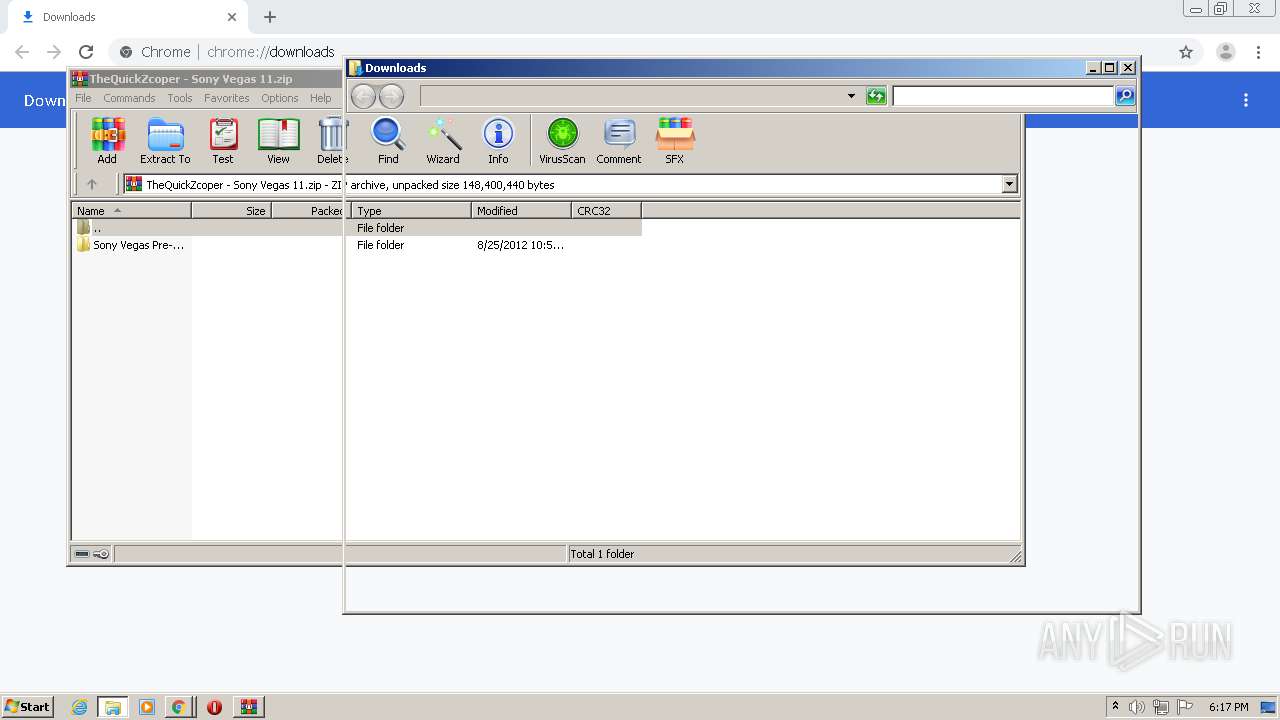
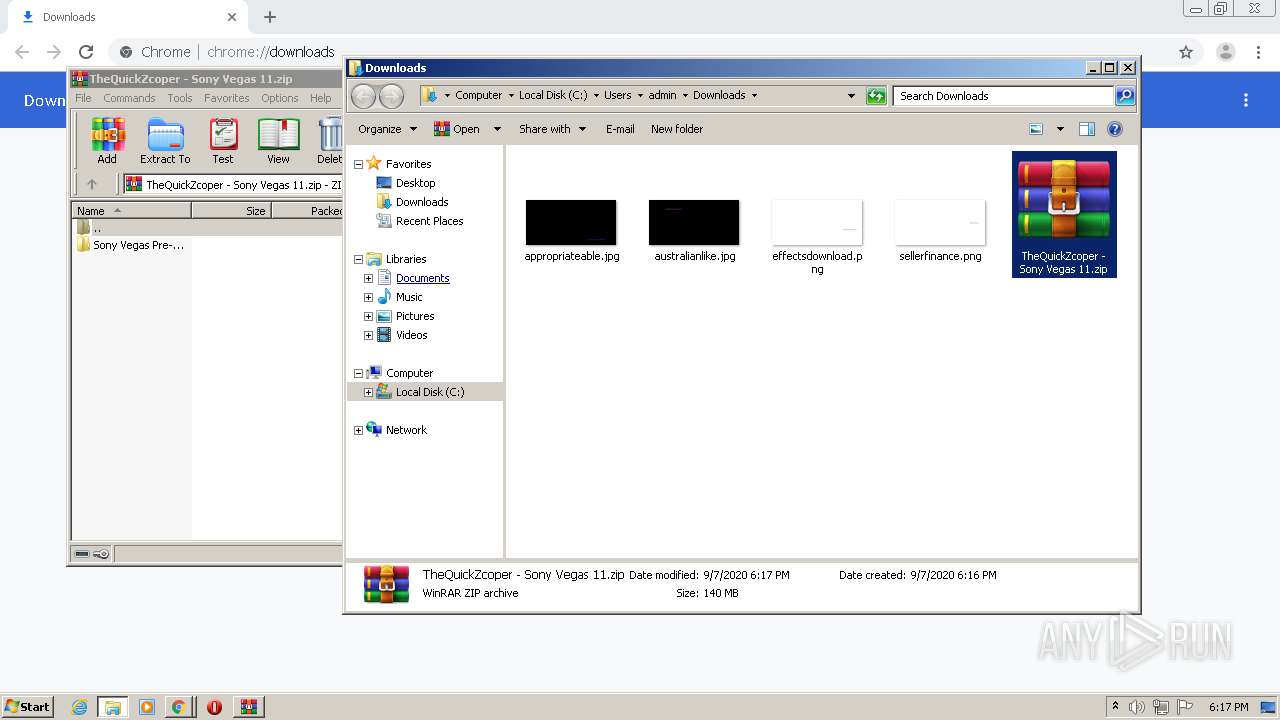
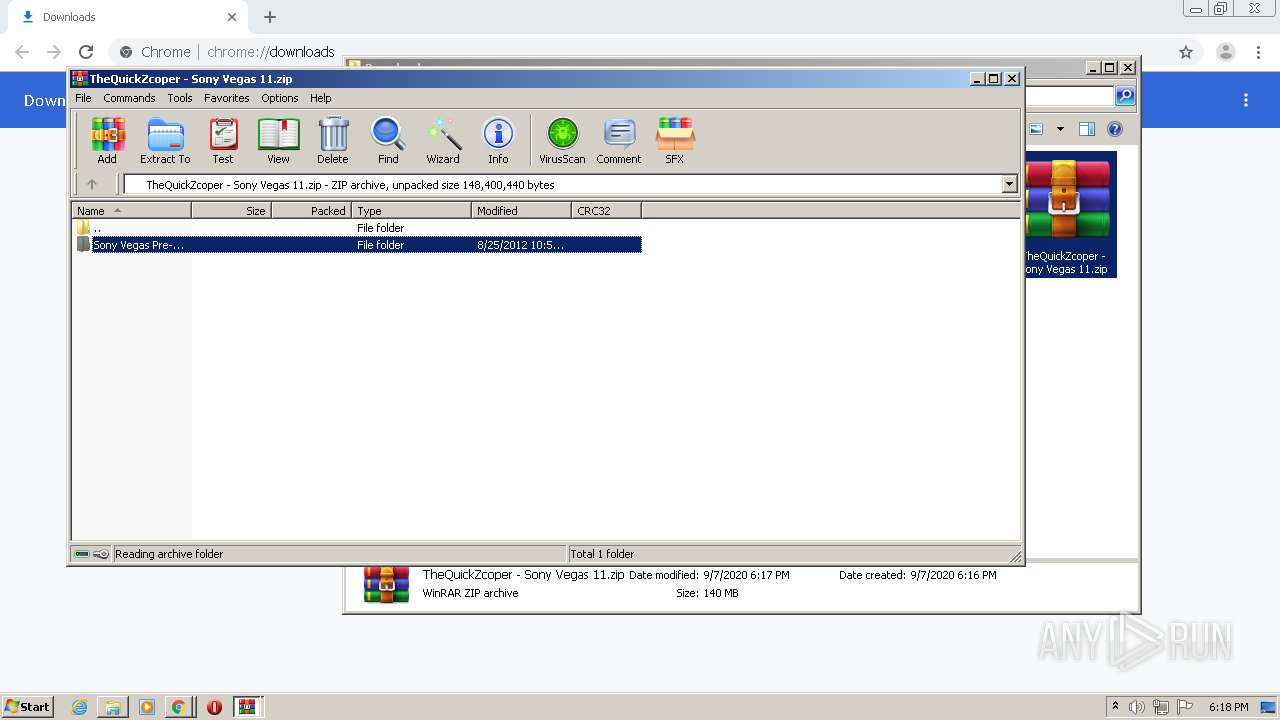
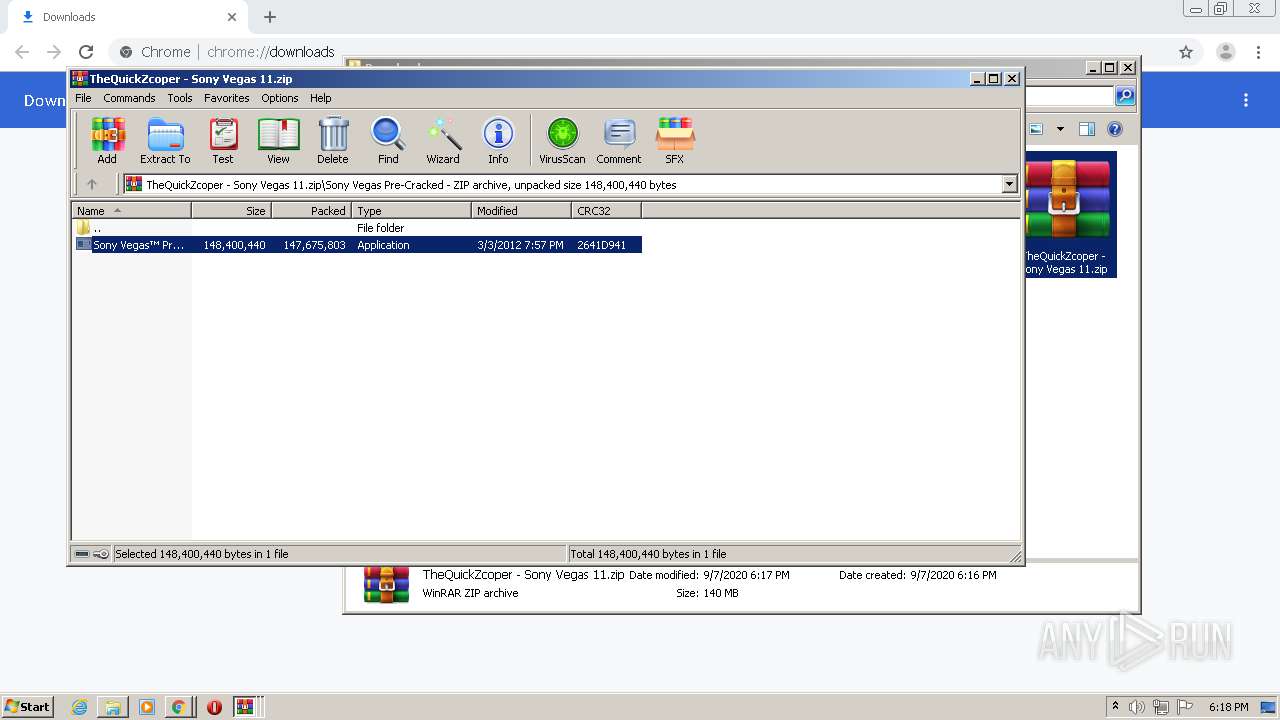
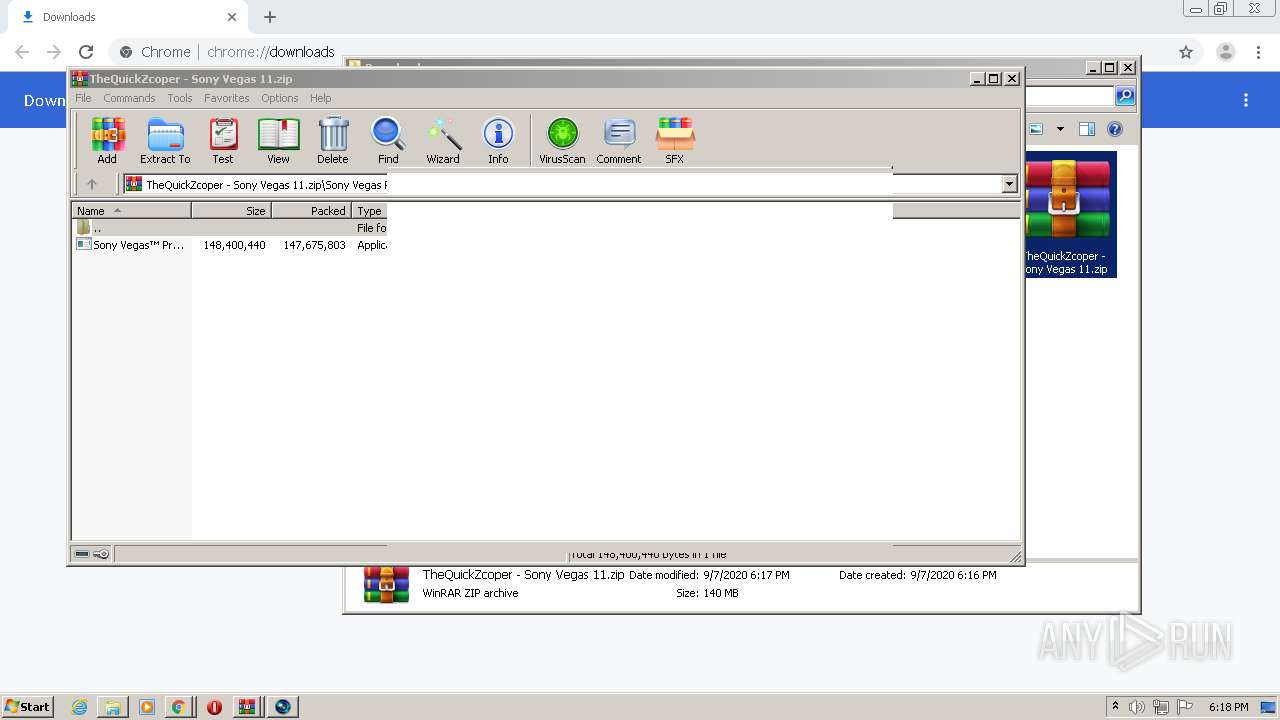
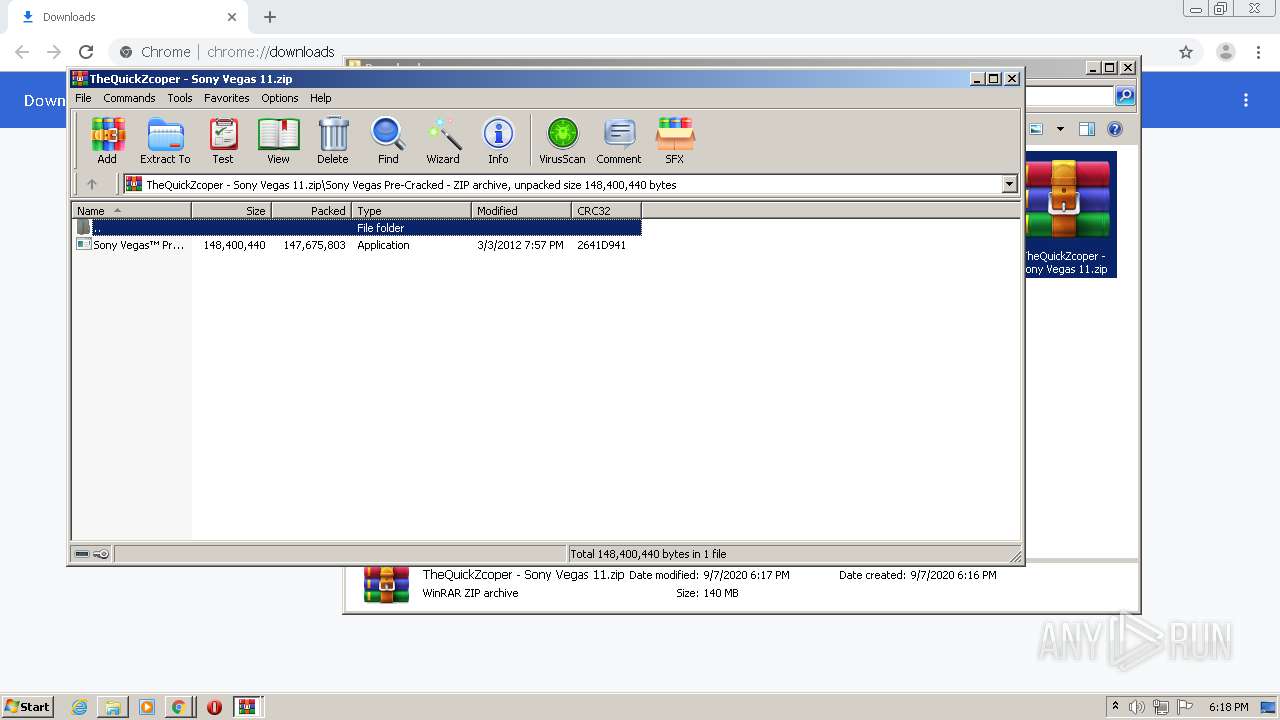
Manual execution by user
- WinRAR.exe (PID: 3228)
- WinRAR.exe (PID: 3352)
Application launched itself
- chrome.exe (PID: 1900)
Reads the hosts file
- chrome.exe (PID: 1900)
- chrome.exe (PID: 472)
Dropped object may contain Bitcoin addresses
- Sony Vegas™ Pro 11 SetUp.exe (PID: 3252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
41
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14259613323774056836,9287226493824954122,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2359003921860249430 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14259613323774056836,9287226493824954122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4754793965592098353 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,14259613323774056836,9287226493824954122,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3958884065226318682 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14259613323774056836,9287226493824954122,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3590891677416624019 --mojo-platform-channel-handle=3612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.mediafire.com/file/5x22ujrcs86sv8z/TheQuickZcoper_-_Sony_Vegas_11.zip/file" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14259613323774056836,9287226493824954122,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11937578220095013733 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
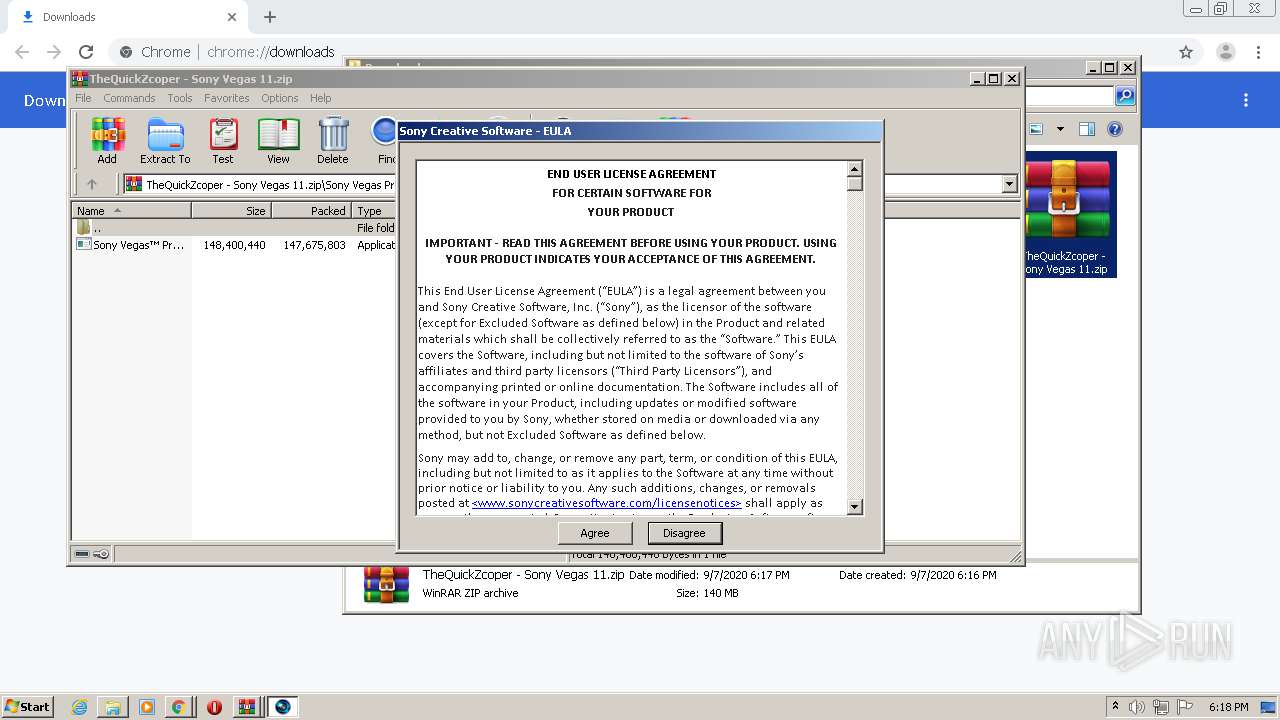
| 2036 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3228.41925\Sony Vegas Pre-Cracked\Sony Vegas™ Pro 11 SetUp.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3228.41925\Sony Vegas Pre-Cracked\Sony Vegas™ Pro 11 SetUp.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Softeza Development Integrity Level: MEDIUM Description: Actual Installer Setup Program Exit code: 3221226540 Version: 3.8 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Sony\Vegas Pro 11.0\FileIOSurrogate.exe" 1033 | C:\Program Files\Sony\Vegas Pro 11.0\FileIOSurrogate.exe | — | vegas110.exe | |||||||||||
User: admin Company: Sony Creative Software Inc. Integrity Level: HIGH Description: File I/O surrogate (not visible) Exit code: 0 Version: Version 11.0 (Build 370) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,14259613323774056836,9287226493824954122,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4770975362485105213 --mojo-platform-channel-handle=5092 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Sony\Vegas Pro 11.0\FileIOSurrogate.exe" 1033 | C:\Program Files\Sony\Vegas Pro 11.0\FileIOSurrogate.exe | — | vegas110.exe | |||||||||||
User: admin Company: Sony Creative Software Inc. Integrity Level: HIGH Description: File I/O surrogate (not visible) Exit code: 0 Version: Version 11.0 (Build 370) Modules
| |||||||||||||||
Total events
3 931
Read events
3 332
Write events
589
Delete events
10
Modification events
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1900-13243972566802375 |
Value: 259 | |||
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1900) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
349
Suspicious files
124
Text files
259
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f39ae62f-0b60-4d84-8bc1-196b635efa8c.tmp | — | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15d0f6.TMP | text | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF15d144.TMP | text | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15d28c.TMP | — | |
MD5:— | SHA256:— | |||
| 1900 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
112
DNS requests
82
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
472 | chrome.exe | GET | 304 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
472 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
472 | chrome.exe | GET | 304 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
472 | chrome.exe | GET | 304 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.200.116.90:3478 | huanpbv8a7af.s.adsco.re | M247 Ltd | SG | malicious |
472 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
472 | chrome.exe | 104.16.202.237:443 | www.mediafire.com | Cloudflare Inc | US | unknown |
472 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
472 | chrome.exe | 216.58.205.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
472 | chrome.exe | 95.100.73.102:443 | c.aaxads.com | Akamai Technologies, Inc. | — | unknown |
472 | chrome.exe | 216.58.205.226:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
472 | chrome.exe | 216.58.210.14:443 | translate.google.com | Google Inc. | US | whitelisted |
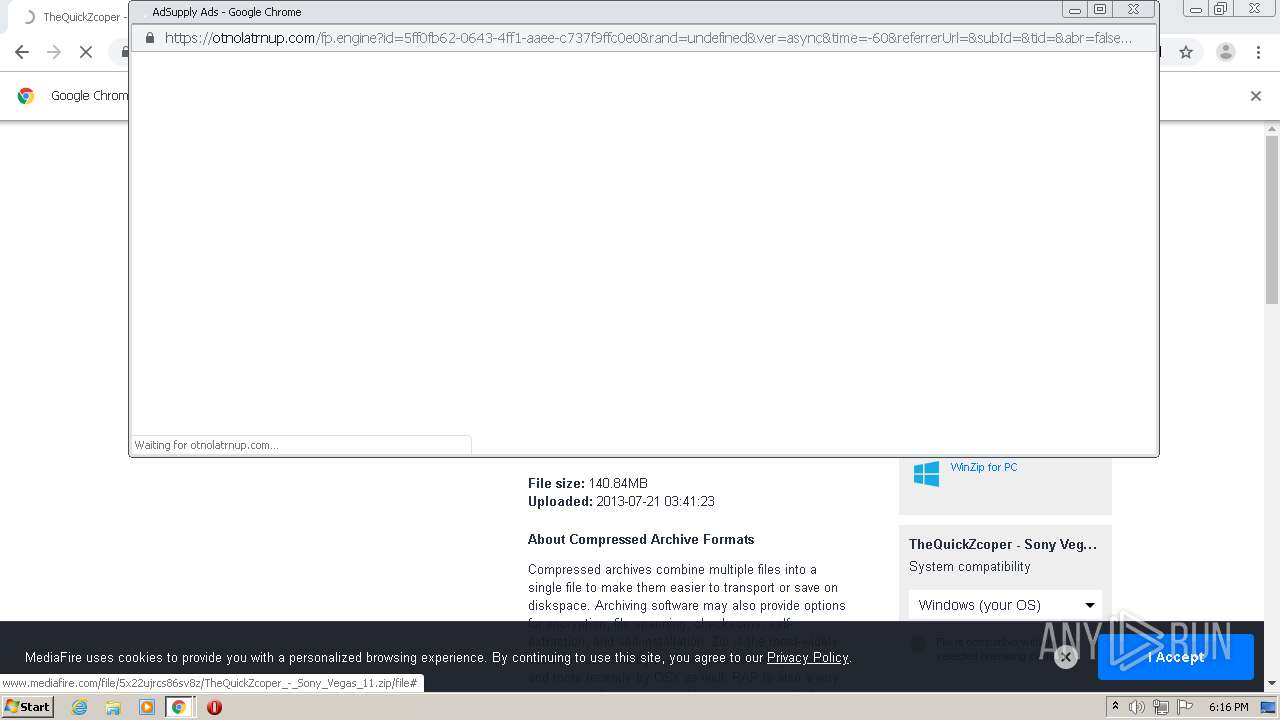
472 | chrome.exe | 104.19.214.37:443 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
472 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
static.mediafire.com |
| shared |
translate.google.com |
| whitelisted |
cdn.otnolatrnup.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
472 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |