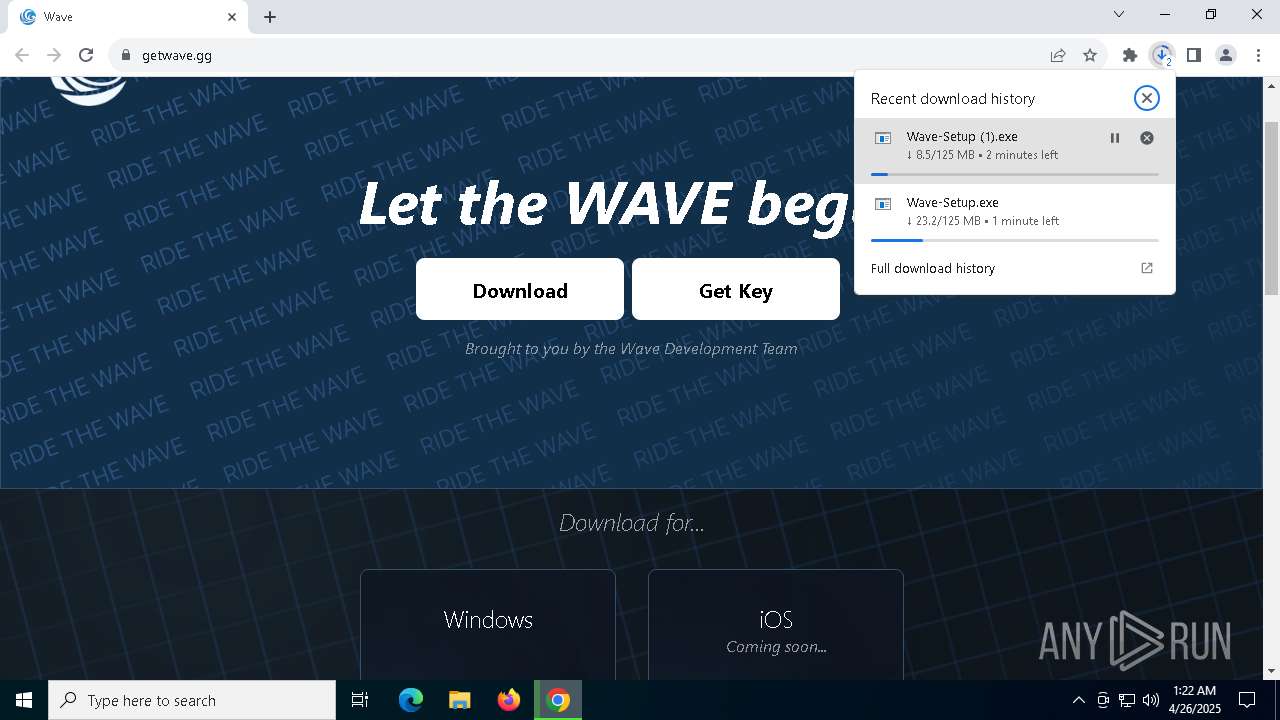
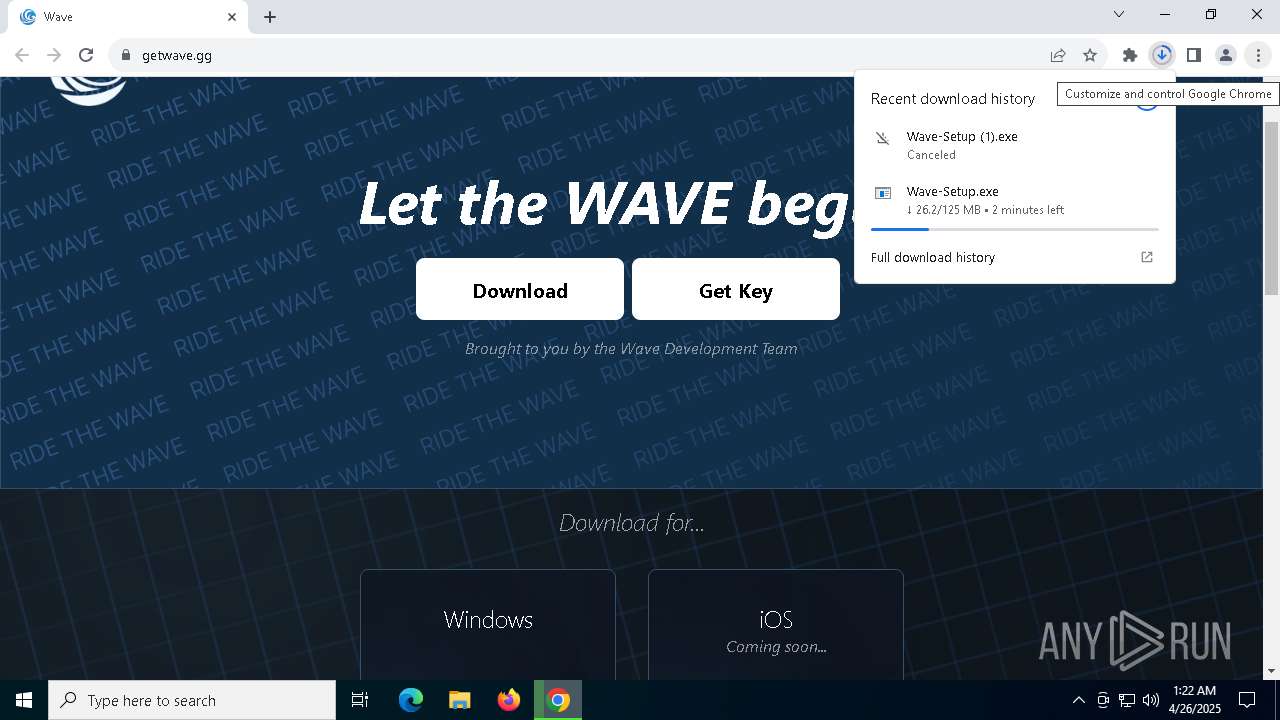
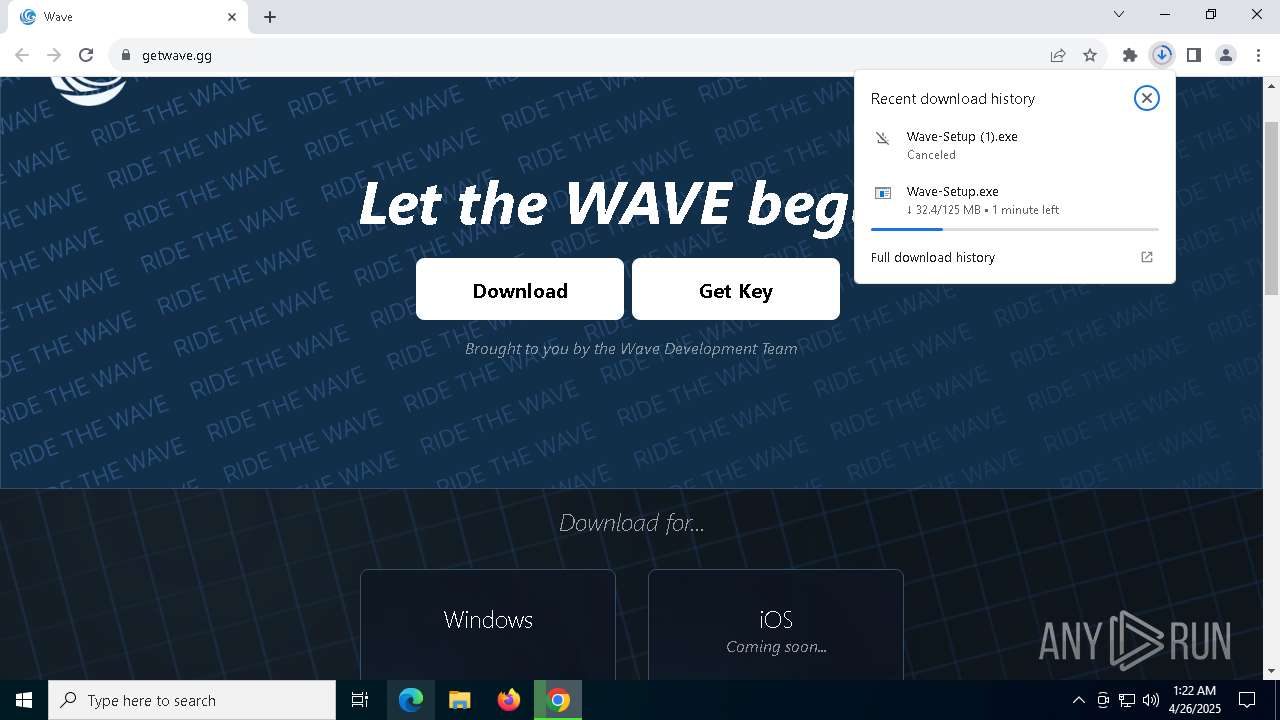
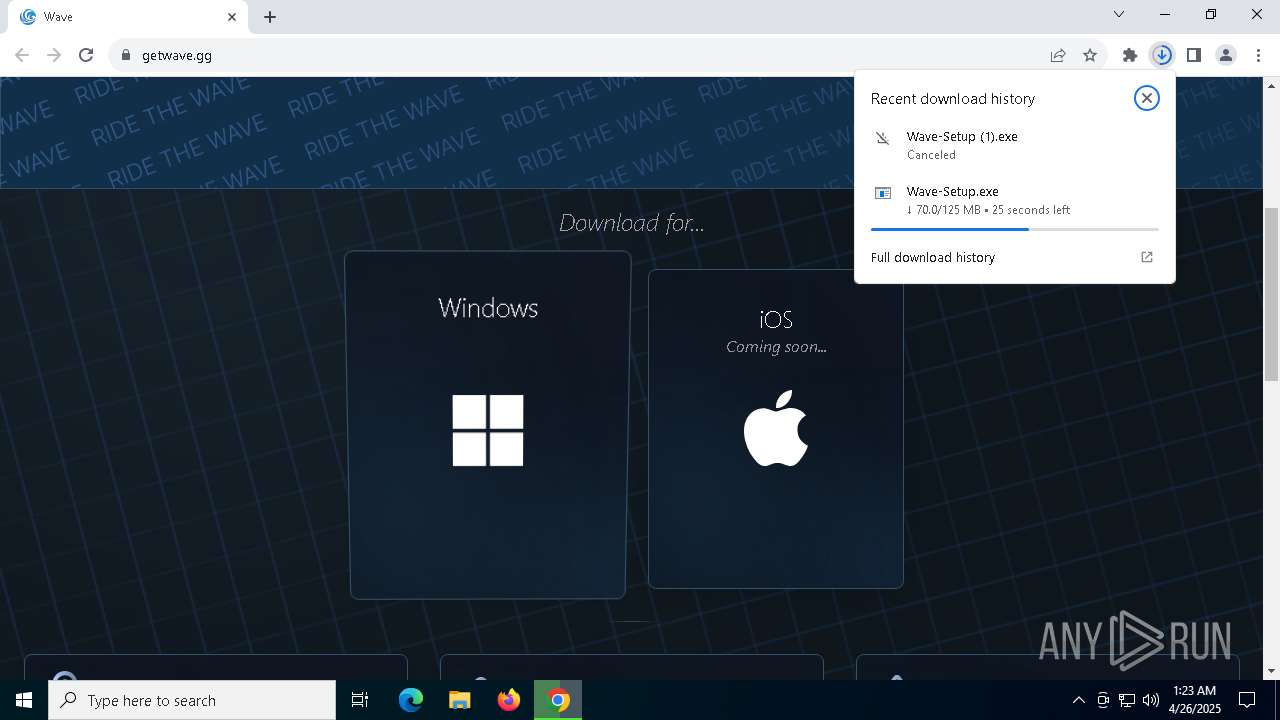
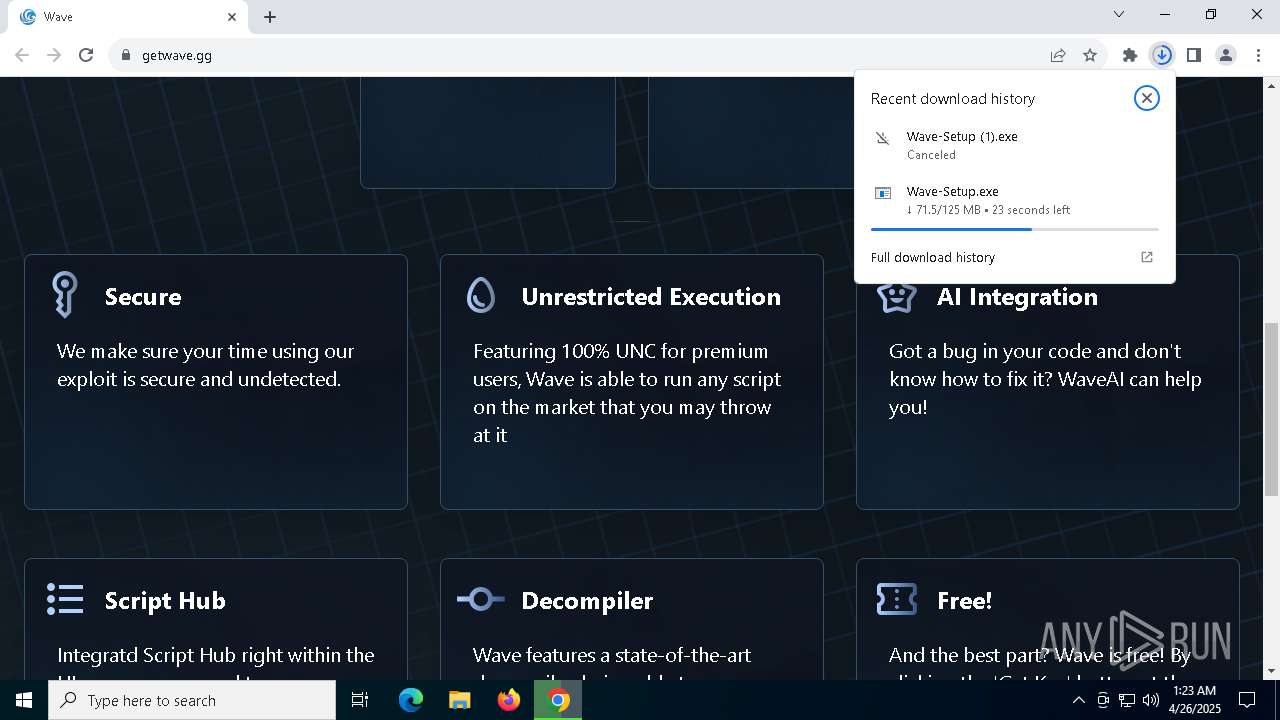
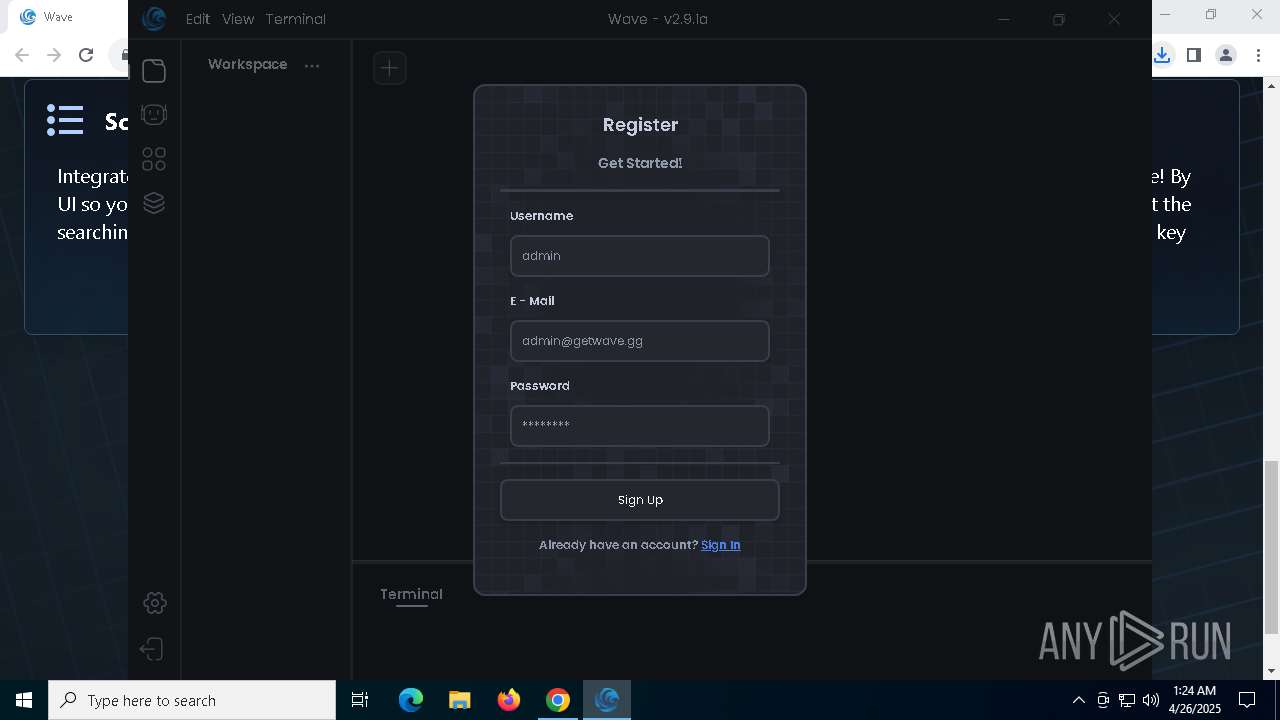
| URL: | getwave.gg |
| Full analysis: | https://app.any.run/tasks/11140e0d-d0c1-4e35-a370-fc6259e9debf |
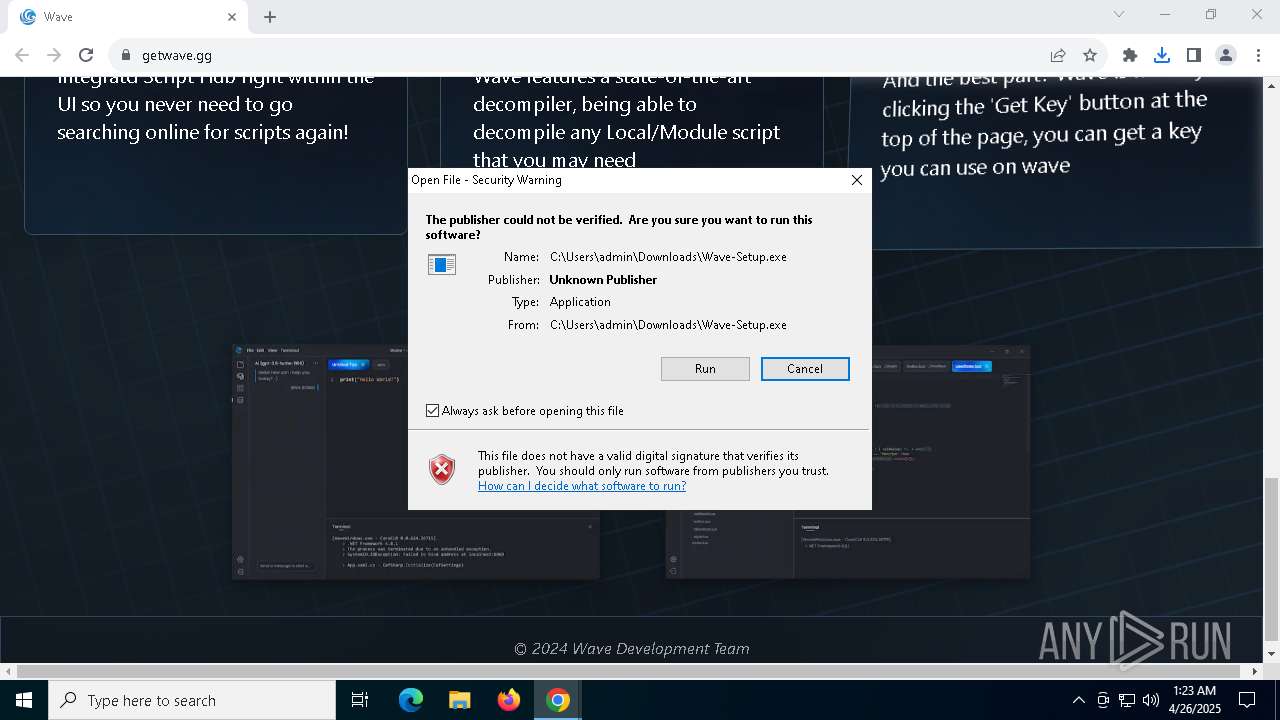
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2025, 01:22:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 202F69B2289A178BCD14236916381FFB |
| SHA1: | 28073053F3DBF82D5C9F937F0EF4F1BF031F2684 |
| SHA256: | FACBDC7E98918B1945BCB35C008DB51DA06A7CF6315CE7AB3E94D7B0F346205E |
| SSDEEP: | 3:hM2C:hMl |
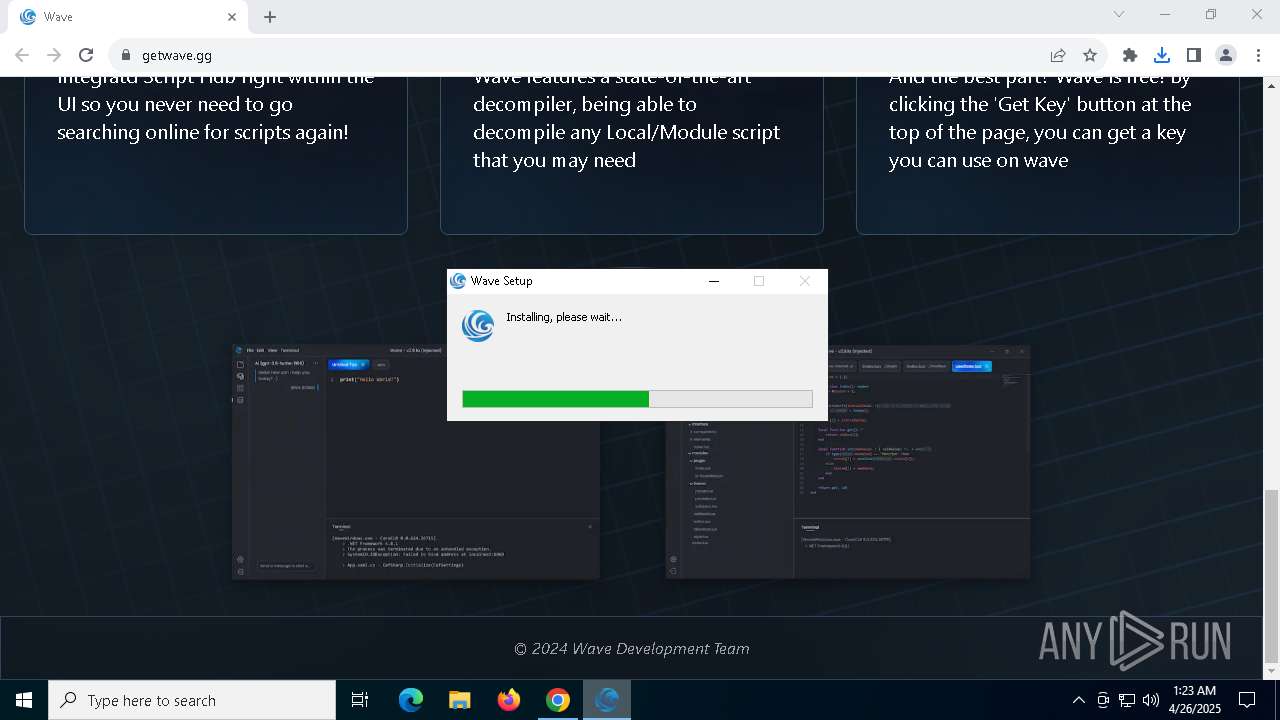
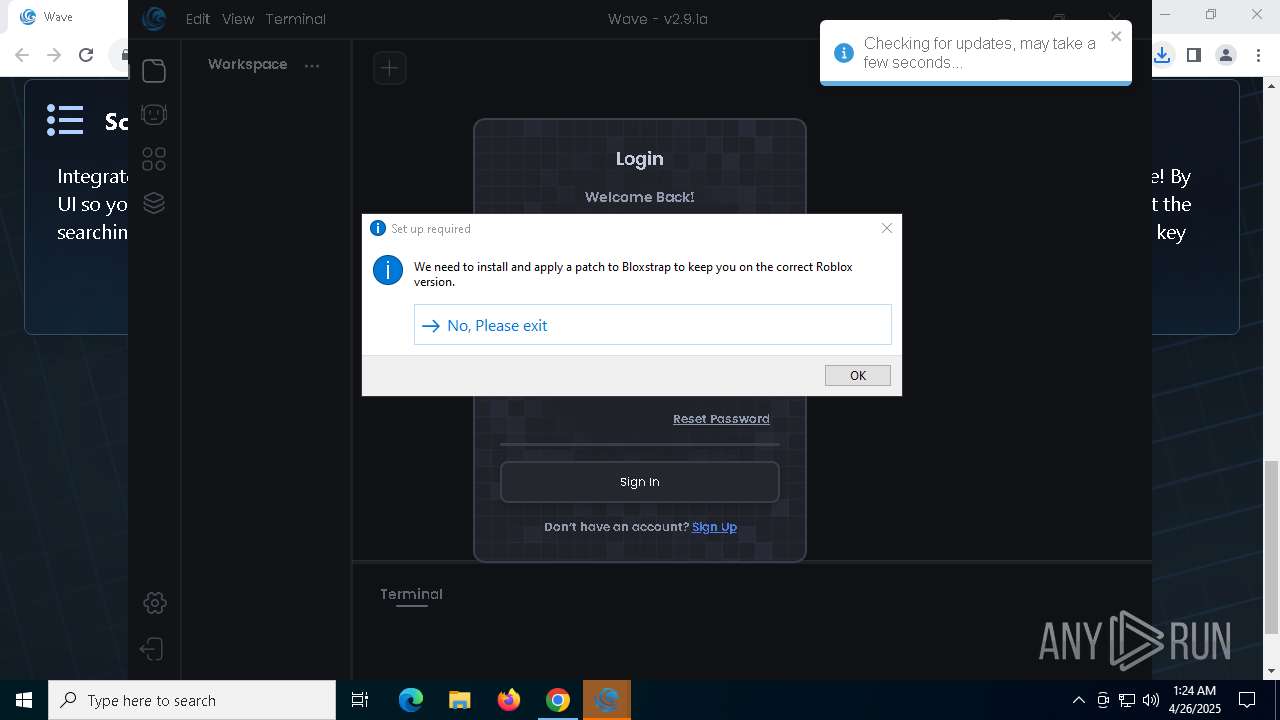
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 5428)
SUSPICIOUS
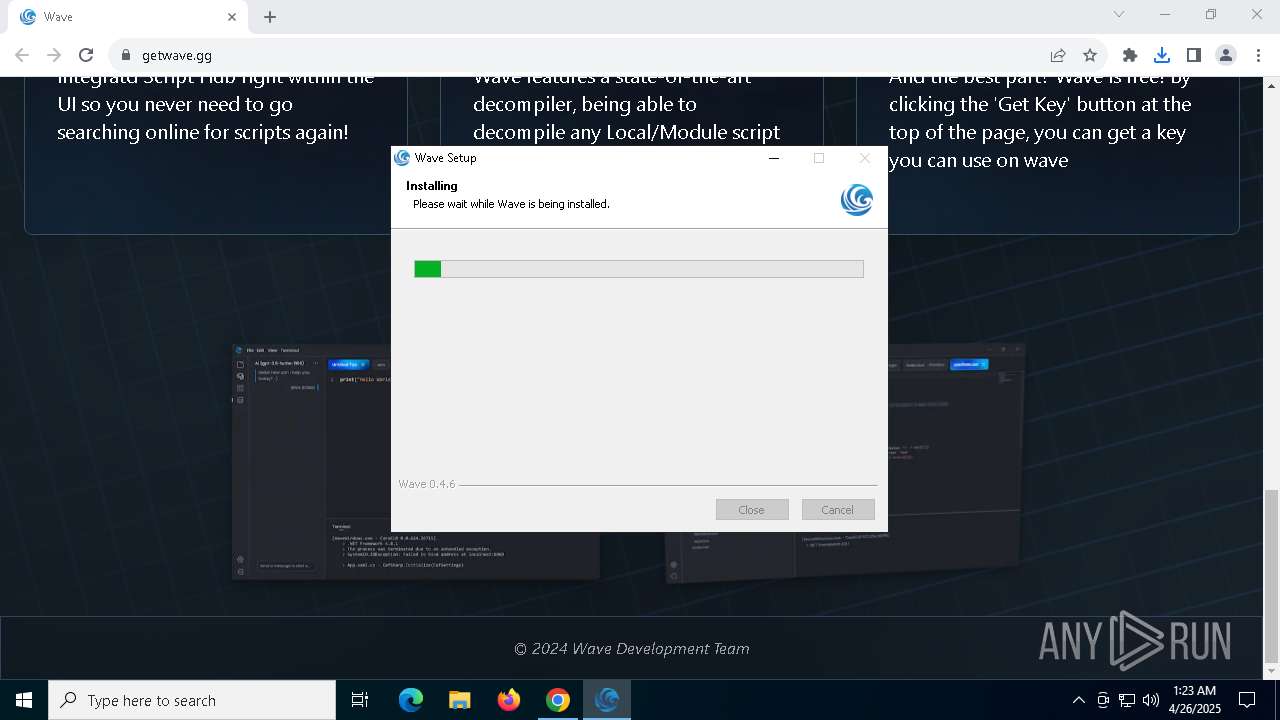
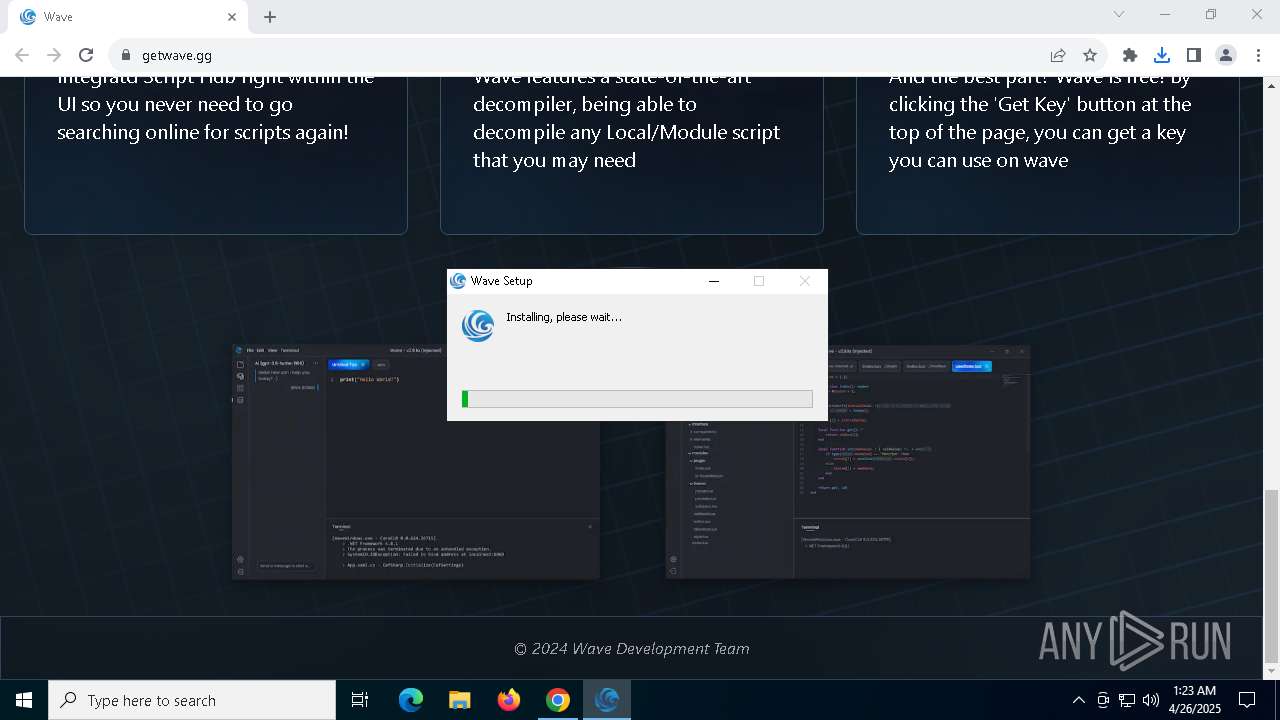
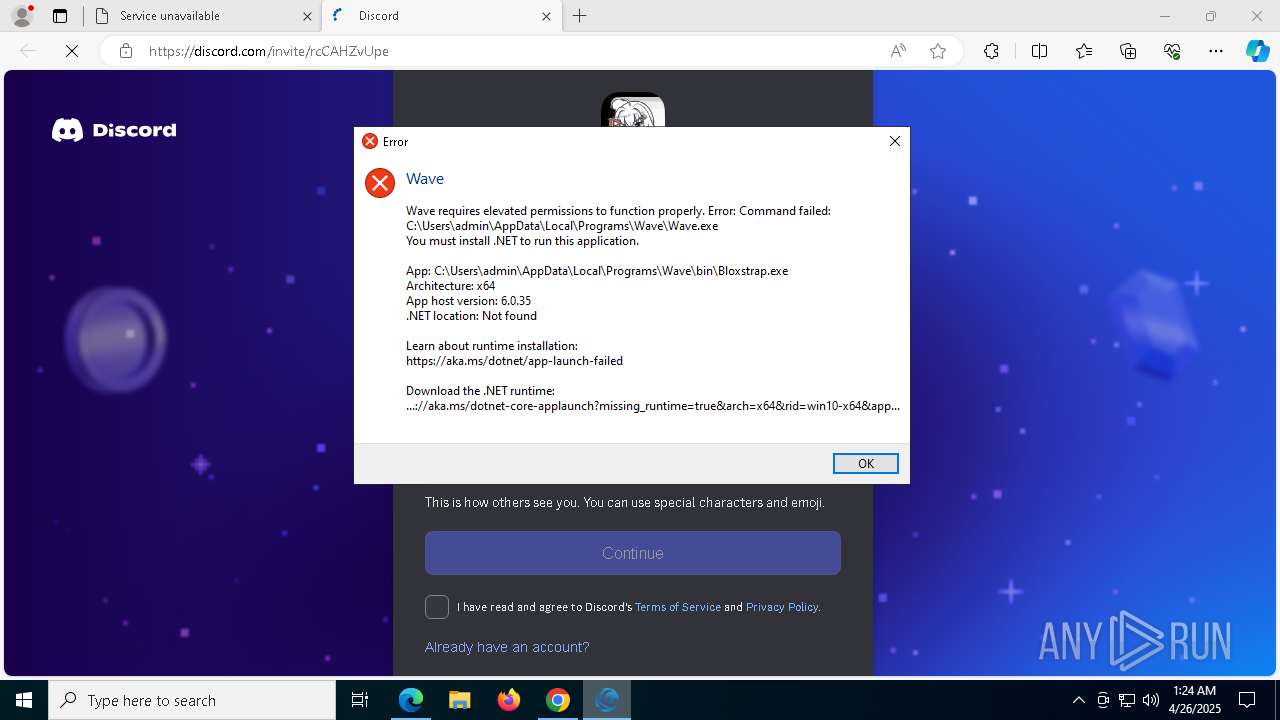
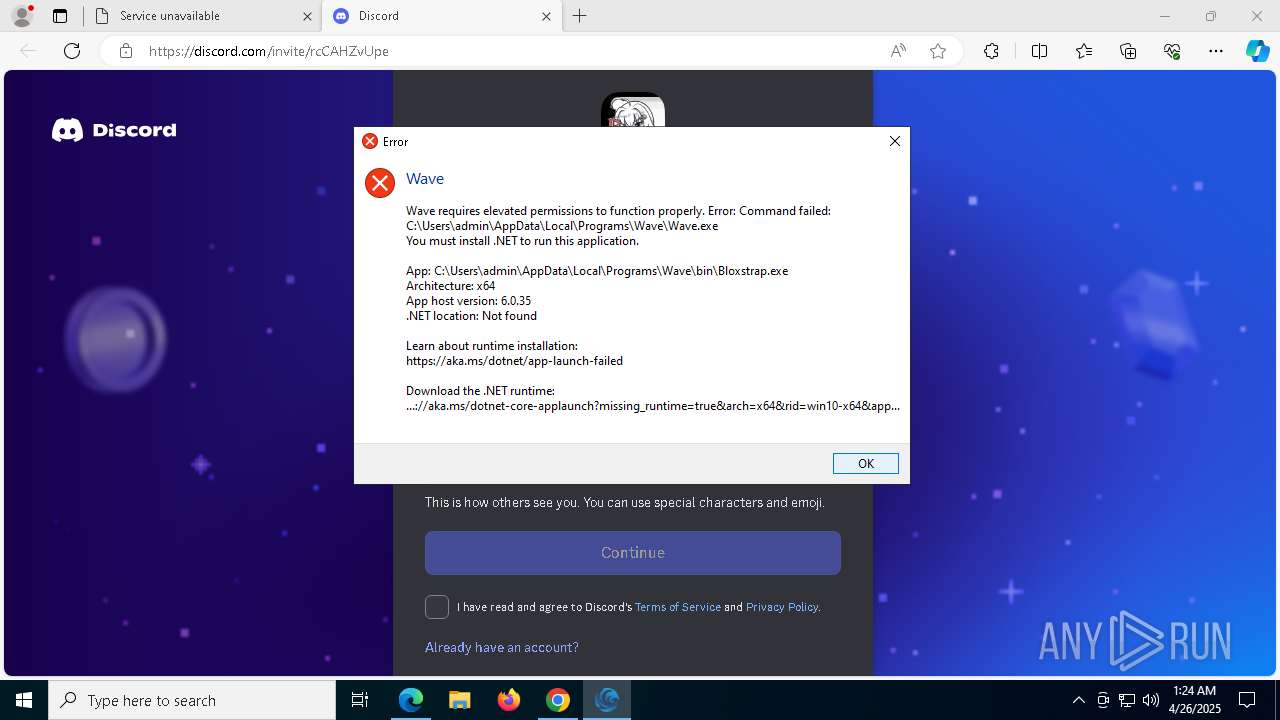
Malware-specific behavior (creating "System.dll" in Temp)
- Wave-Setup.exe (PID: 6108)
The process creates files with name similar to system file names
- Wave-Setup.exe (PID: 6108)
Executable content was dropped or overwritten
- Wave-Setup.exe (PID: 6108)
- Wave.exe (PID: 5452)
Starts CMD.EXE for commands execution
- Wave-Setup.exe (PID: 6108)
- Wave.exe (PID: 4628)
- powershell.exe (PID: 5428)
- Wave.exe (PID: 5452)
Get information on the list of running processes
- Wave-Setup.exe (PID: 6108)
- cmd.exe (PID: 6620)
Reads security settings of Internet Explorer
- Wave-Setup.exe (PID: 6108)
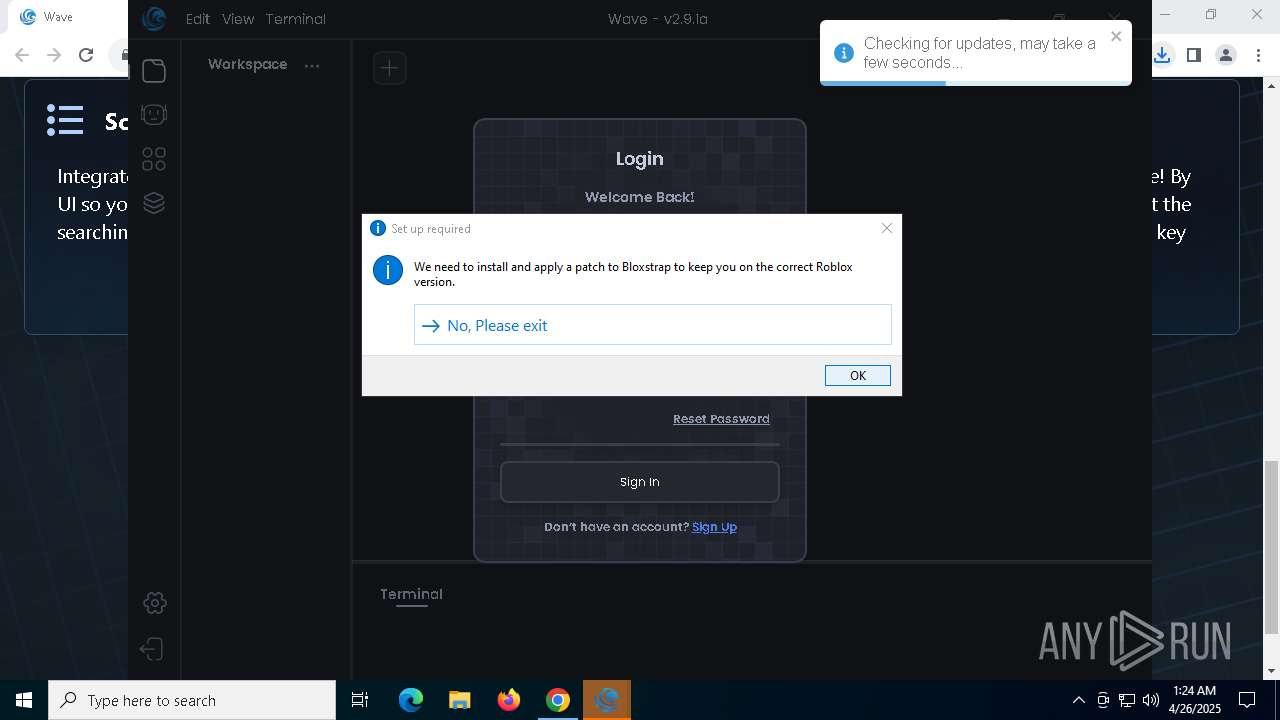
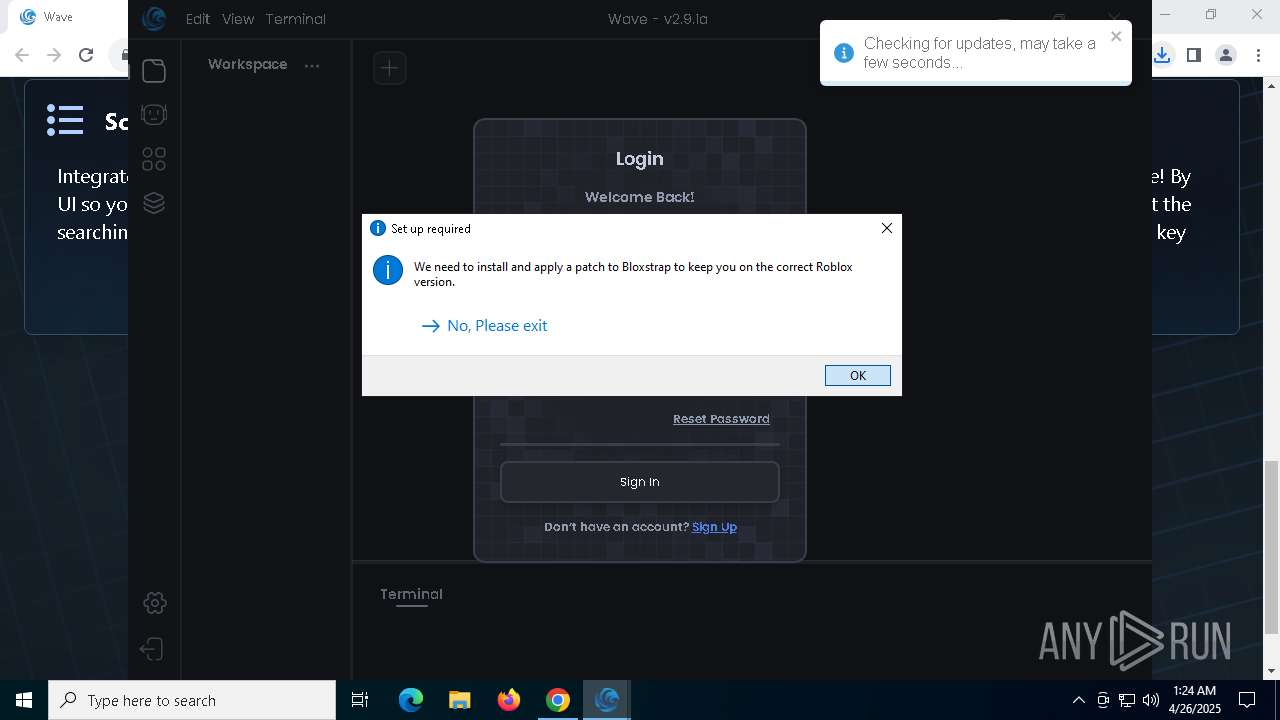
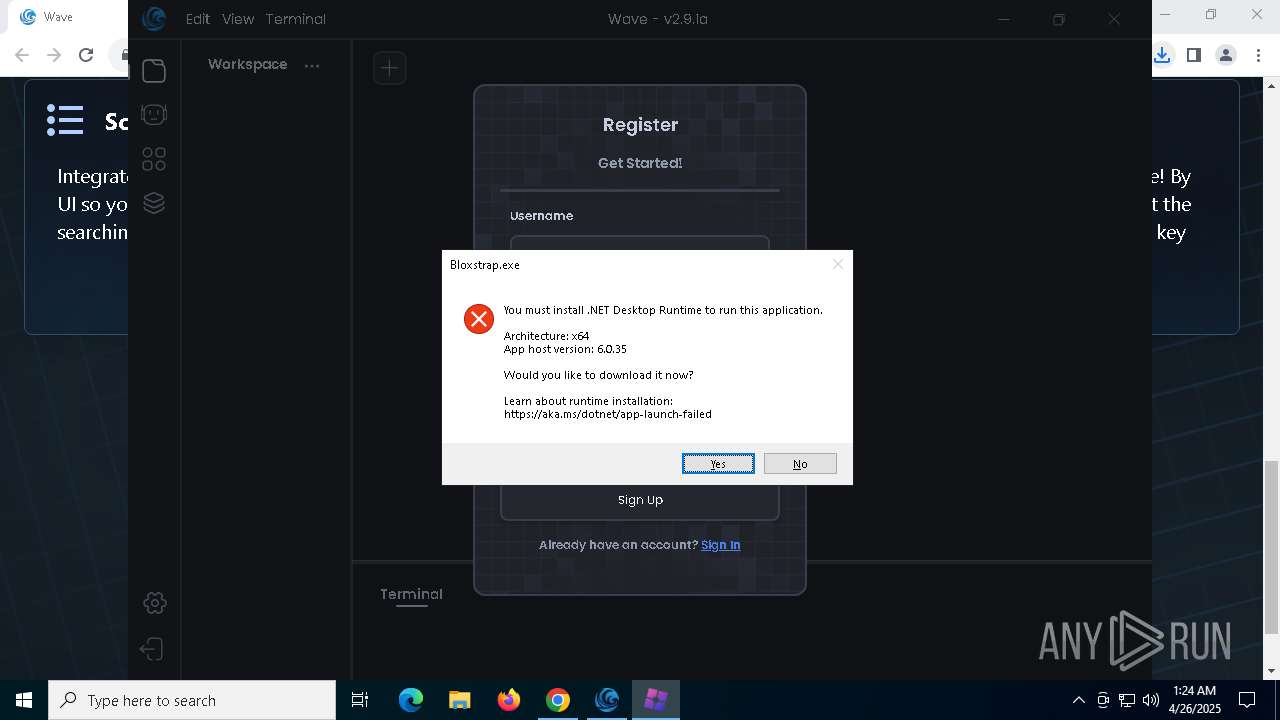
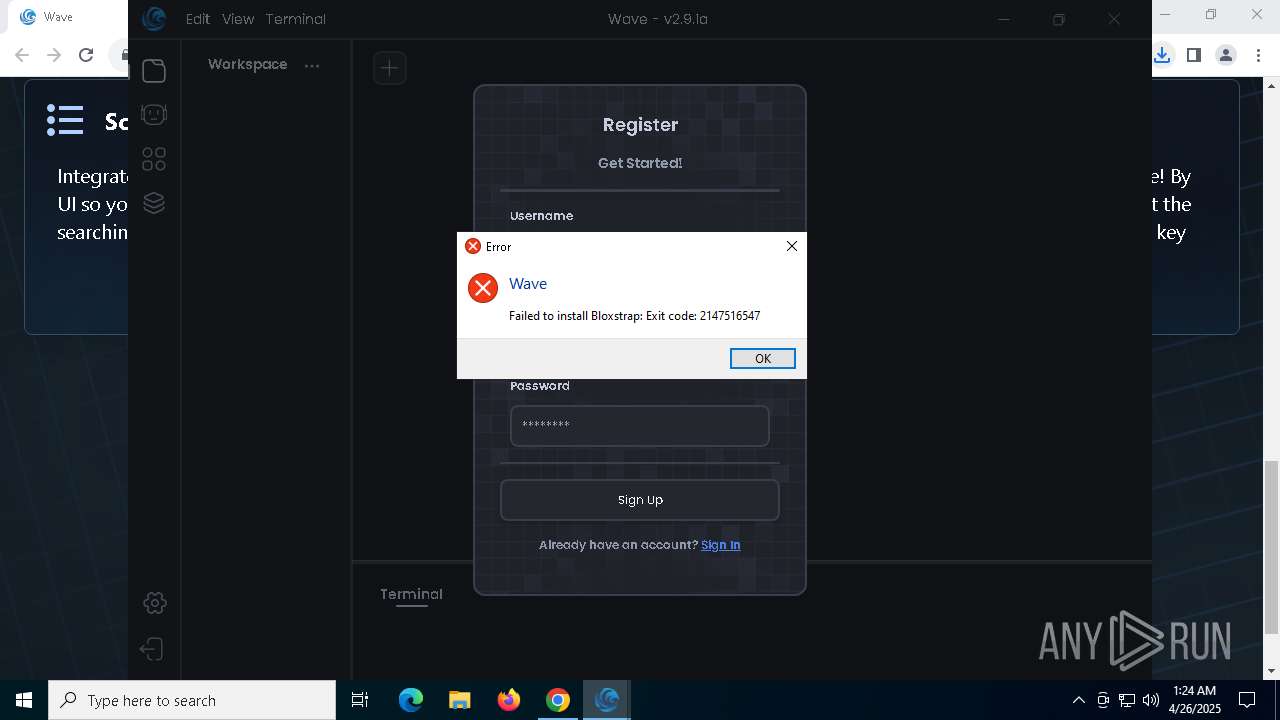
- Bloxstrap.exe (PID: 232)
Drops 7-zip archiver for unpacking
- Wave-Setup.exe (PID: 6108)
Process drops legitimate windows executable
- Wave-Setup.exe (PID: 6108)
Creates a software uninstall entry
- Wave-Setup.exe (PID: 6108)
Application launched itself
- Wave.exe (PID: 4628)
- Wave.exe (PID: 5452)
Starts process via Powershell
- powershell.exe (PID: 5428)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1324)
Executing commands from a ".bat" file
- Wave.exe (PID: 4628)
- powershell.exe (PID: 5428)
Starts application with an unusual extension
- cmd.exe (PID: 8040)
The executable file from the user directory is run by the CMD process
- Wave.exe (PID: 5452)
Detected use of alternative data streams (AltDS)
- wave-luau.exe (PID: 4012)
The process deletes folder without confirmation
- Wave.exe (PID: 4628)
INFO
Application launched itself
- chrome.exe (PID: 7332)
- msedge.exe (PID: 6808)
- msedge.exe (PID: 6700)
Reads the software policy settings
- slui.exe (PID: 7888)
Executable content was dropped or overwritten
- chrome.exe (PID: 7332)
Checks supported languages
- Wave-Setup.exe (PID: 6108)
- Wave.exe (PID: 1052)
- chcp.com (PID: 4932)
- Wave.exe (PID: 516)
- Wave.exe (PID: 5188)
- Wave.exe (PID: 5172)
- Wave.exe (PID: 5452)
- Wave.exe (PID: 4188)
- wave-luau.exe (PID: 4012)
- Bloxstrap.exe (PID: 232)
- Wave.exe (PID: 4628)
Create files in a temporary directory
- Wave-Setup.exe (PID: 6108)
- Wave.exe (PID: 4628)
- Wave.exe (PID: 5452)
The sample compiled with english language support
- Wave-Setup.exe (PID: 6108)
Reads the computer name
- Wave-Setup.exe (PID: 6108)
- Wave.exe (PID: 516)
- Wave.exe (PID: 4628)
- Wave.exe (PID: 1052)
- Wave.exe (PID: 5452)
- Wave.exe (PID: 5188)
- Wave.exe (PID: 5172)
- Bloxstrap.exe (PID: 232)
Reads Environment values
- Wave.exe (PID: 4628)
- Wave.exe (PID: 5452)
Checks proxy server information
- Wave.exe (PID: 4628)
- Wave.exe (PID: 5452)
Reads product name
- Wave.exe (PID: 4628)
- Wave.exe (PID: 5452)
Reads the machine GUID from the registry
- Wave.exe (PID: 4628)
- Wave.exe (PID: 5452)
Drops encrypted JS script (Microsoft Script Encoder)
- Wave.exe (PID: 4628)
- Wave.exe (PID: 5452)
Changes the display of characters in the console
- cmd.exe (PID: 8040)
Process checks computer location settings
- Wave.exe (PID: 5452)
- Wave.exe (PID: 4188)
Creates files or folders in the user directory
- Wave.exe (PID: 5452)
- Wave.exe (PID: 5172)
- Wave.exe (PID: 4628)
- Wave-Setup.exe (PID: 6108)
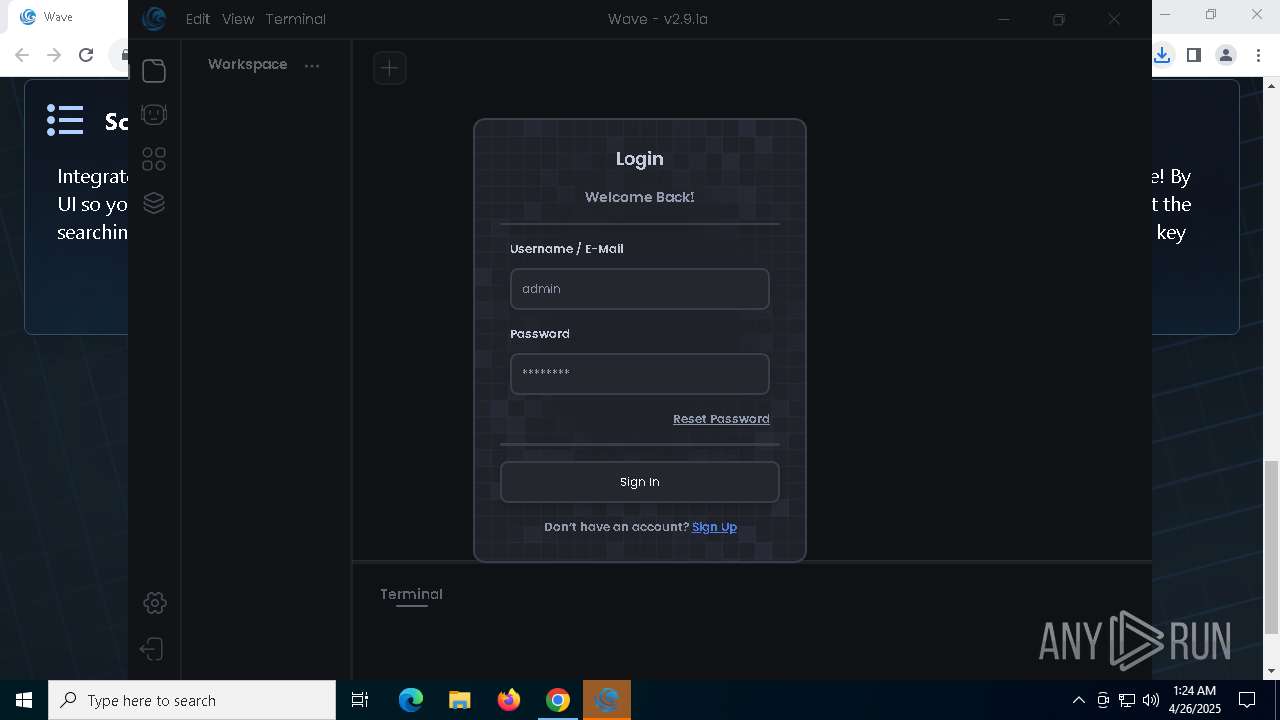
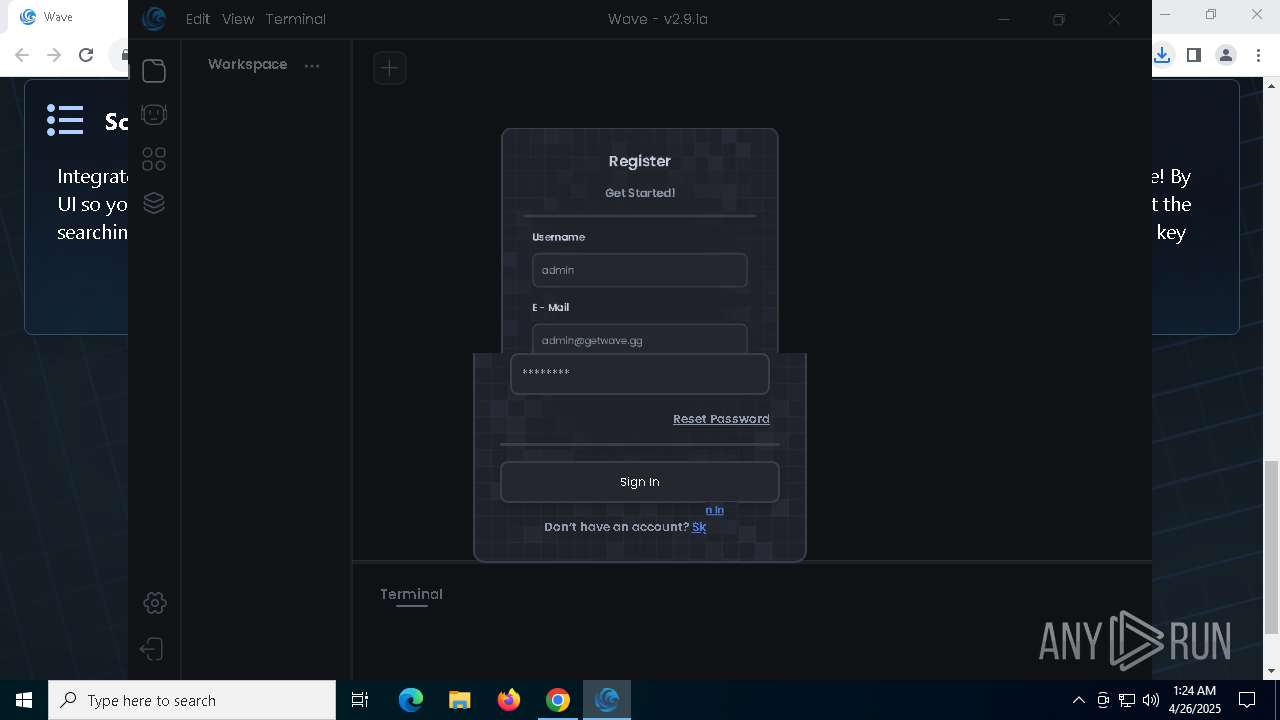
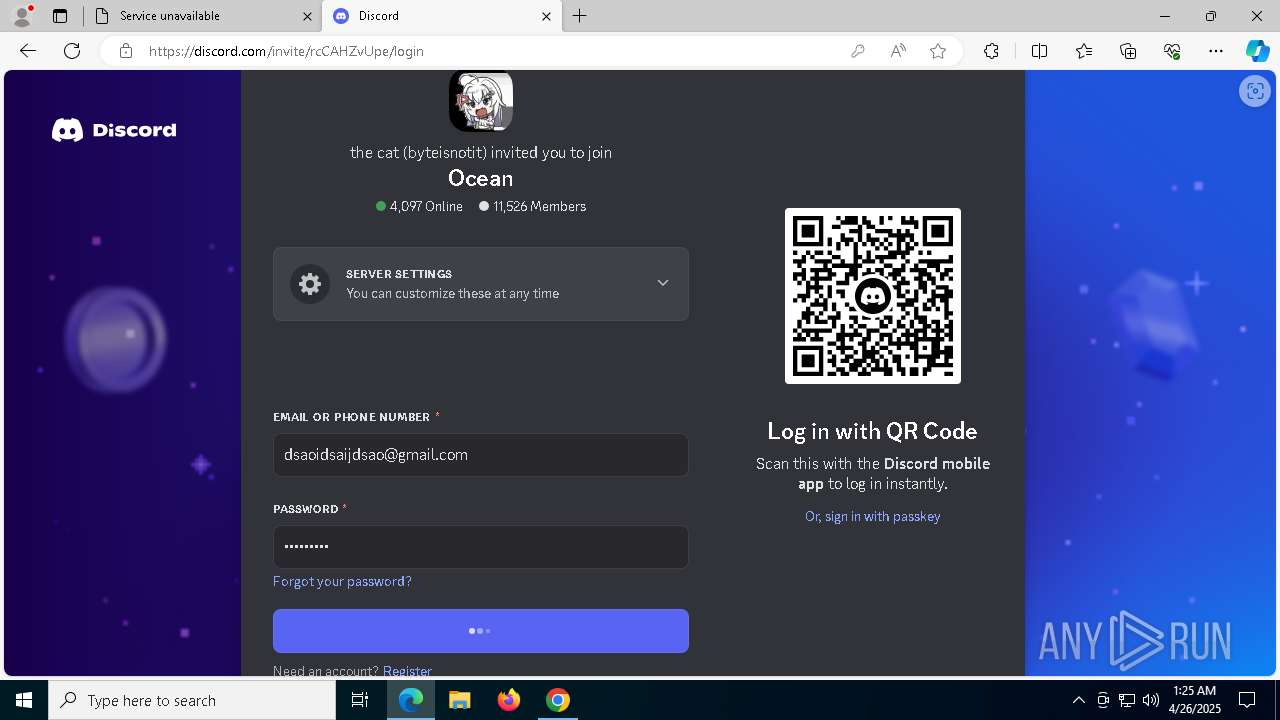
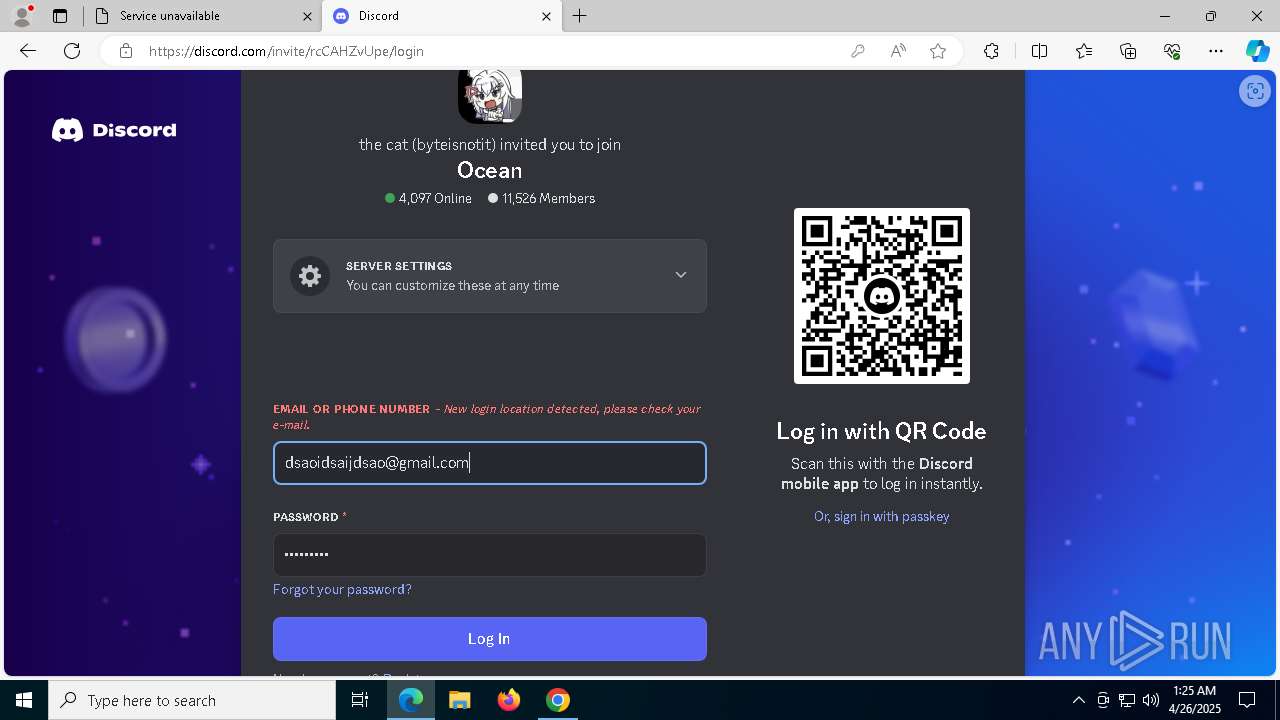
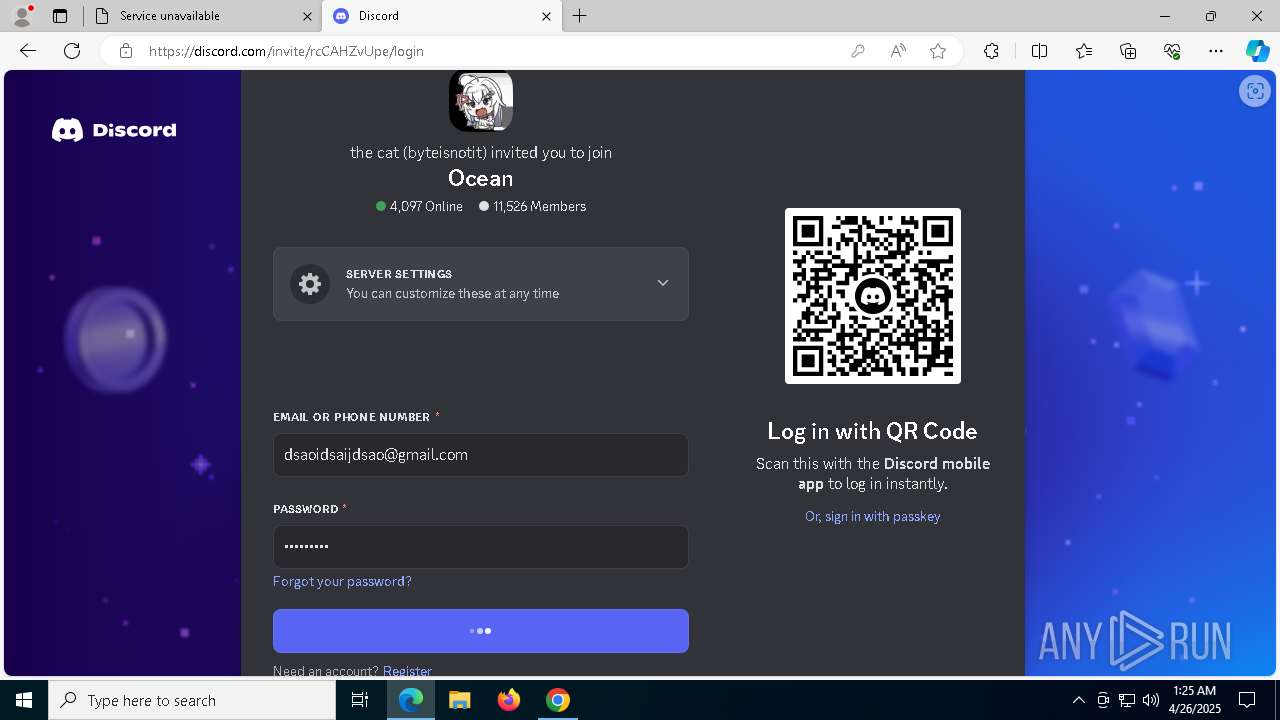
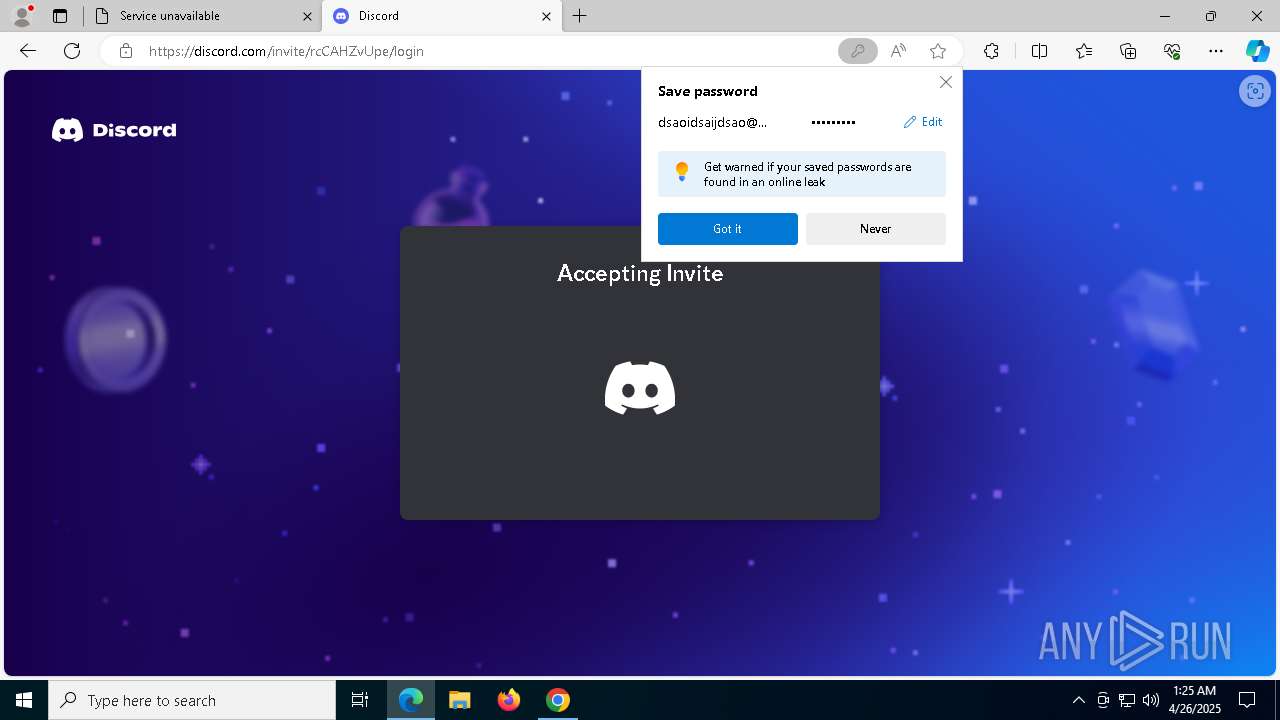
Manual execution by a user
- msedge.exe (PID: 6700)
- Wave.exe (PID: 4628)
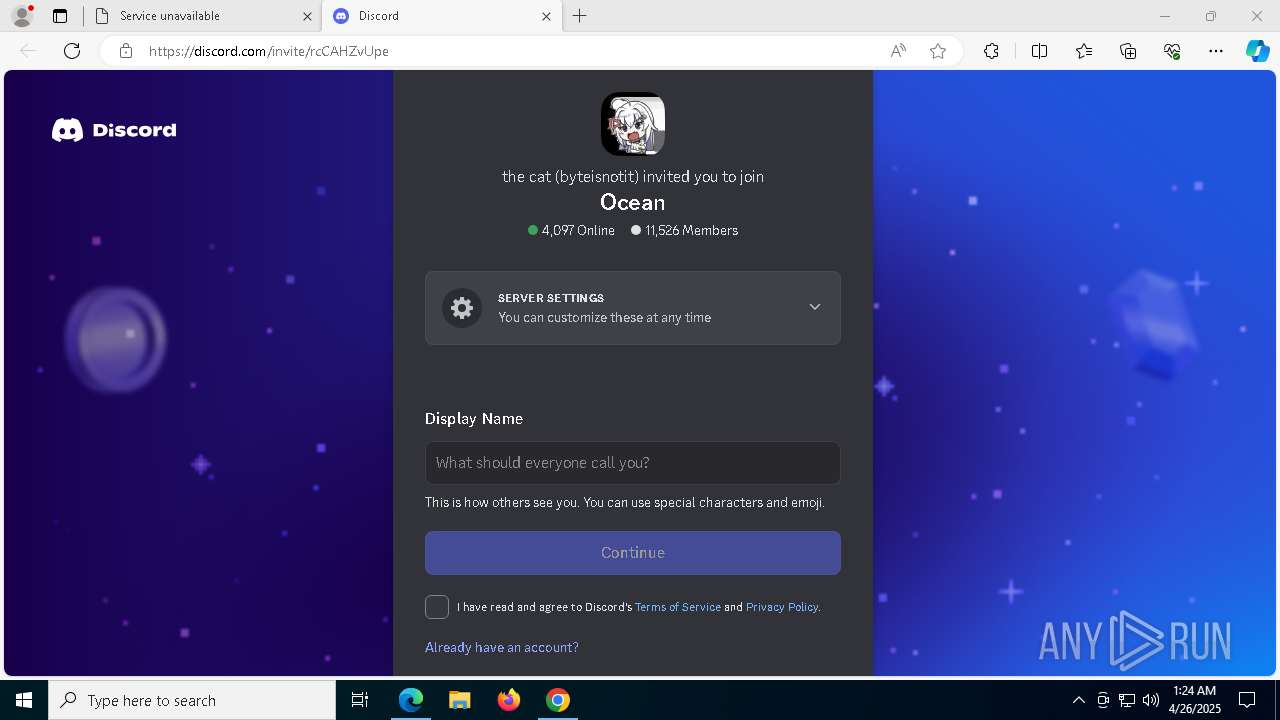
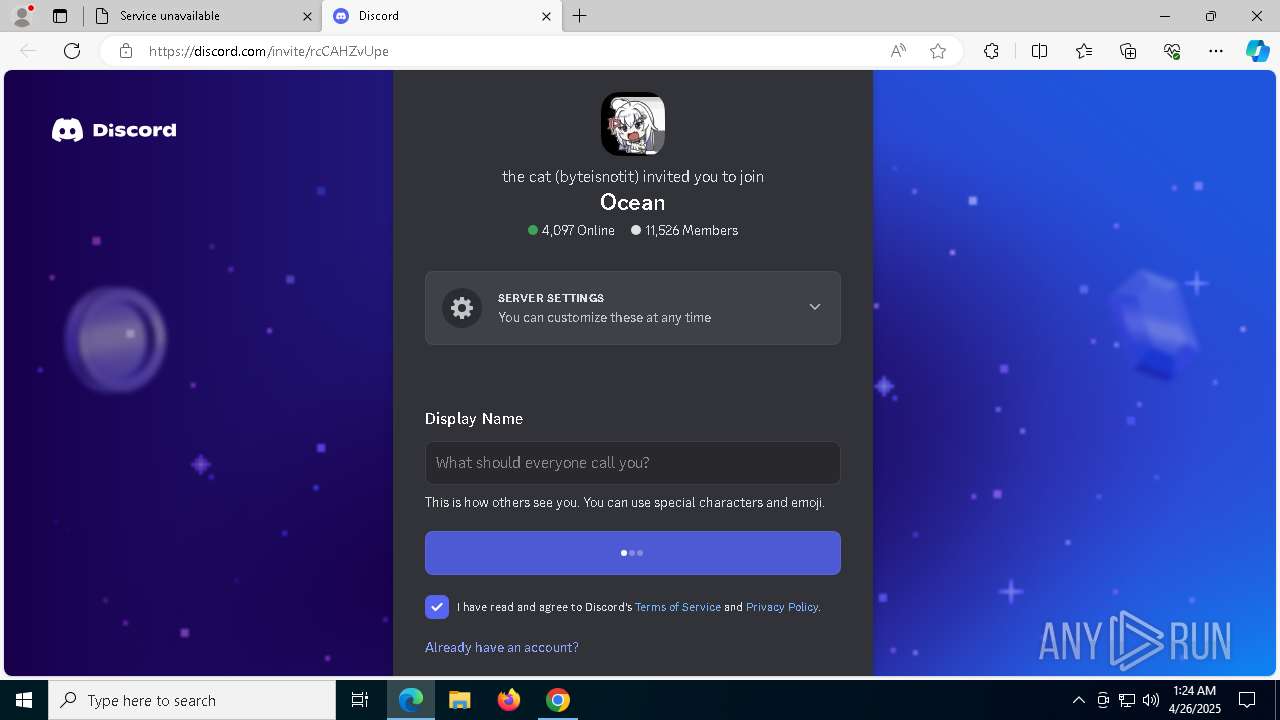
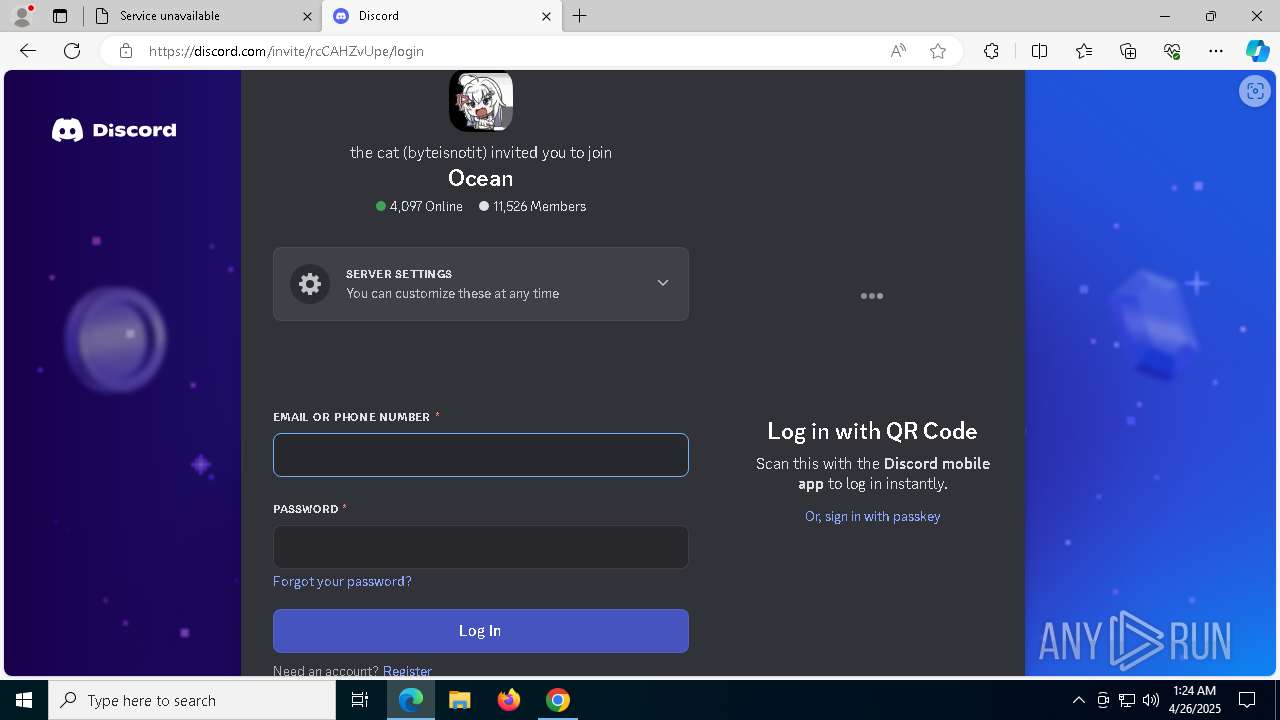
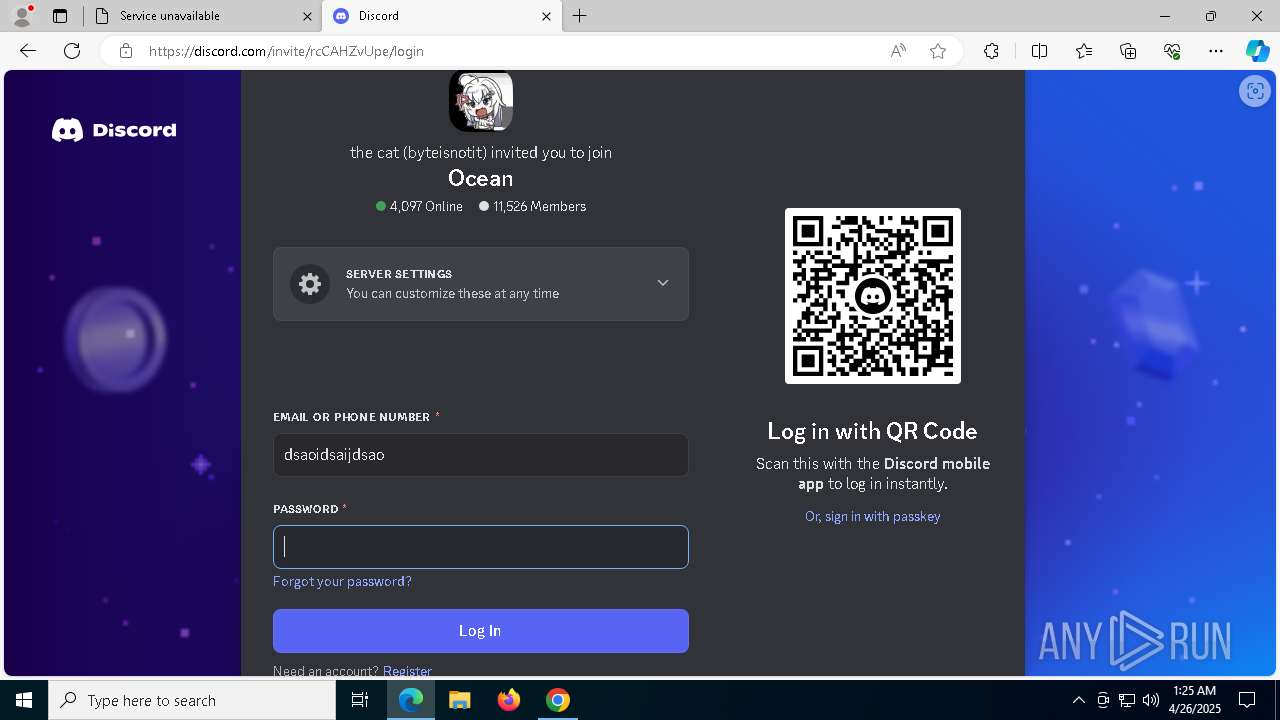
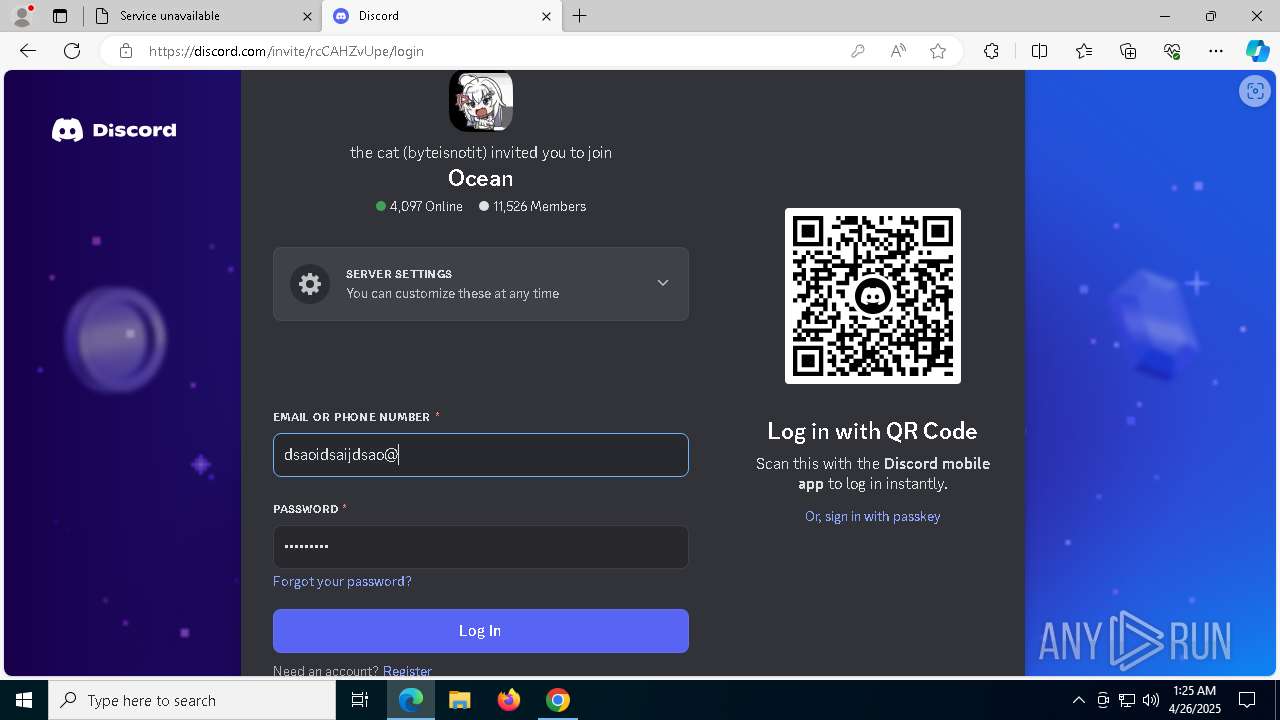
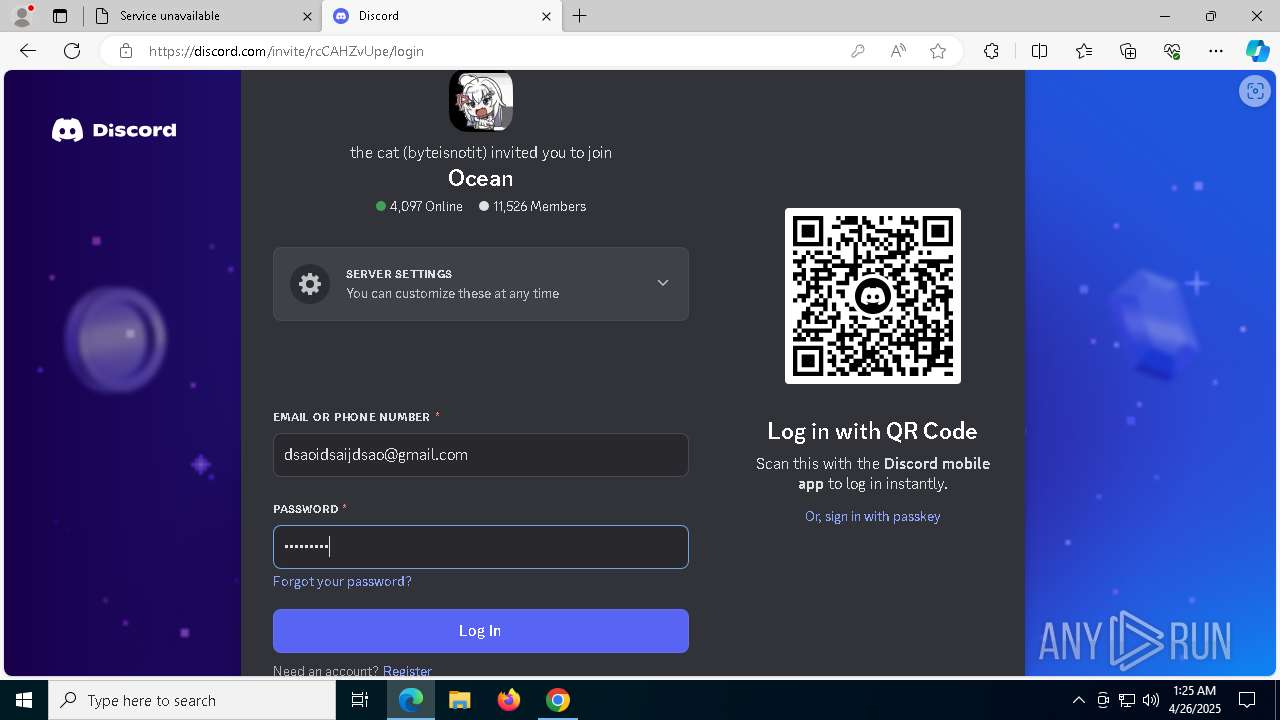
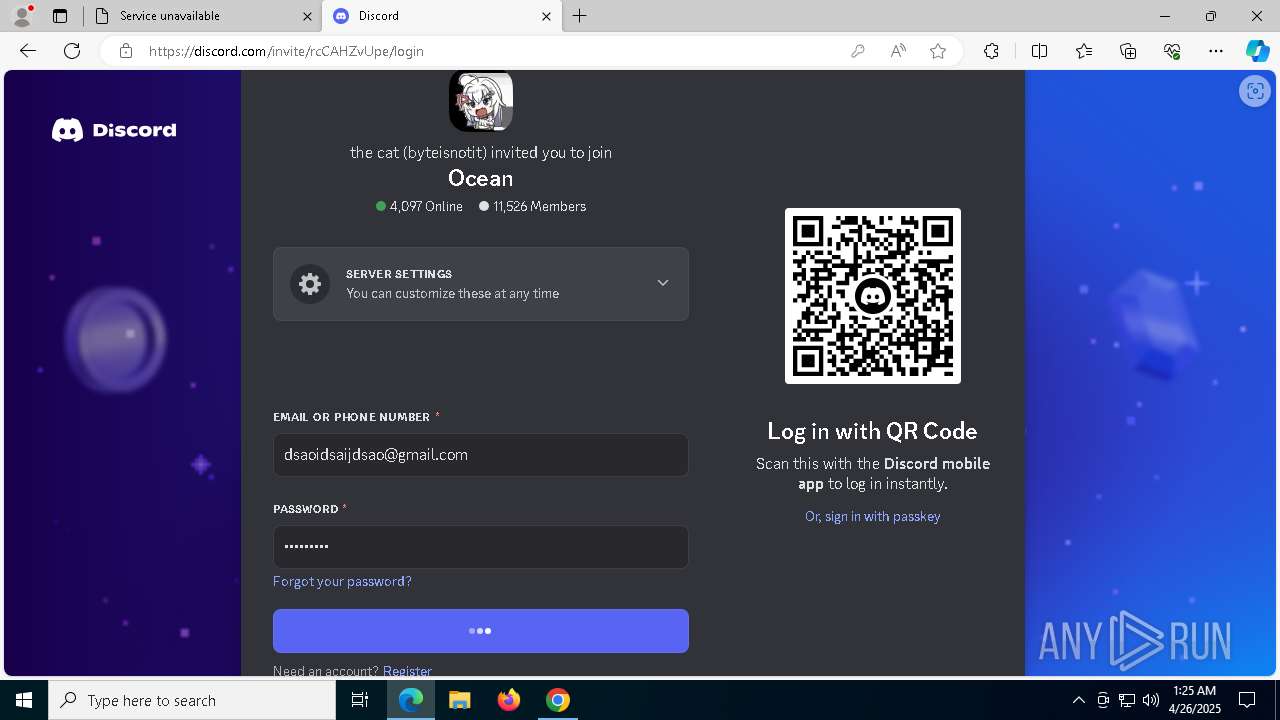
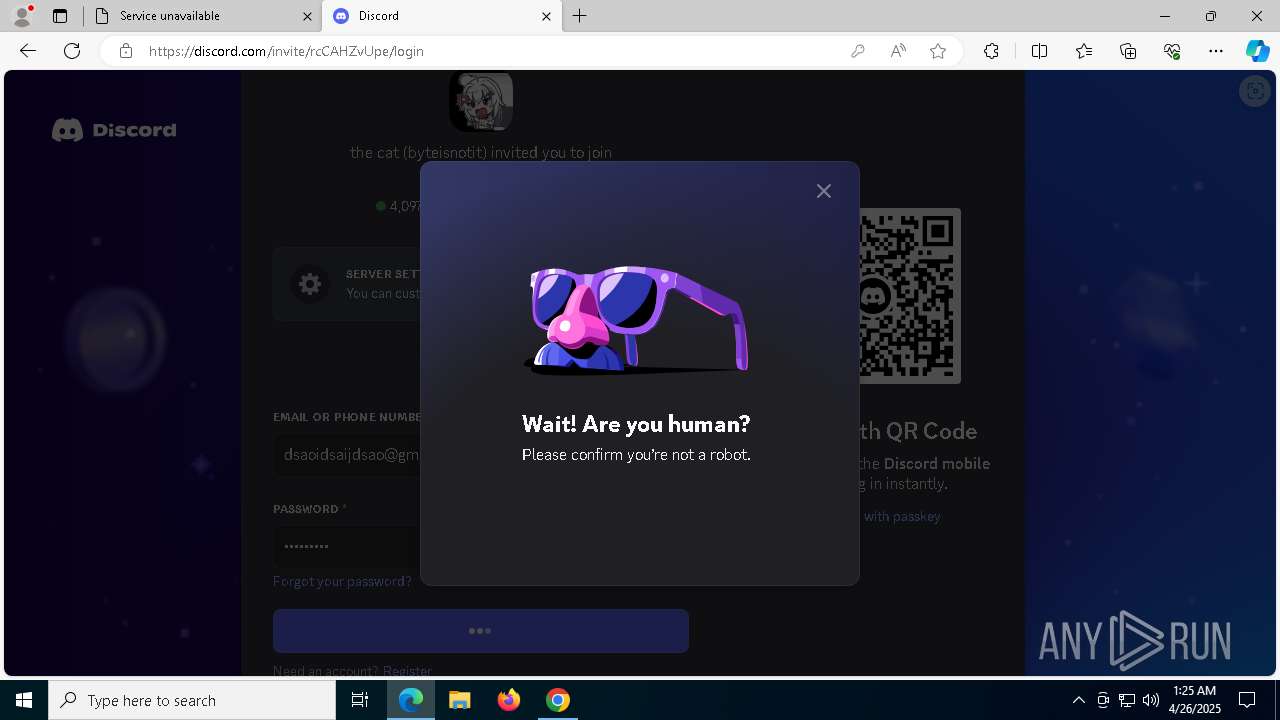
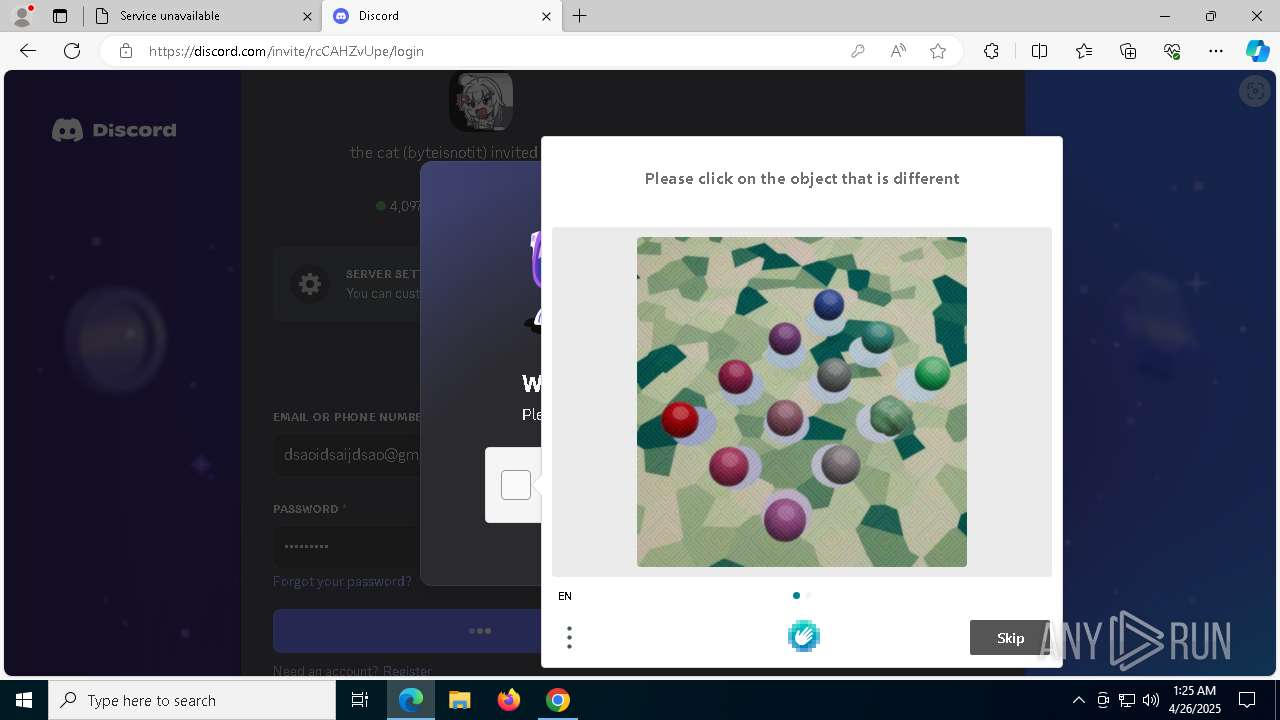
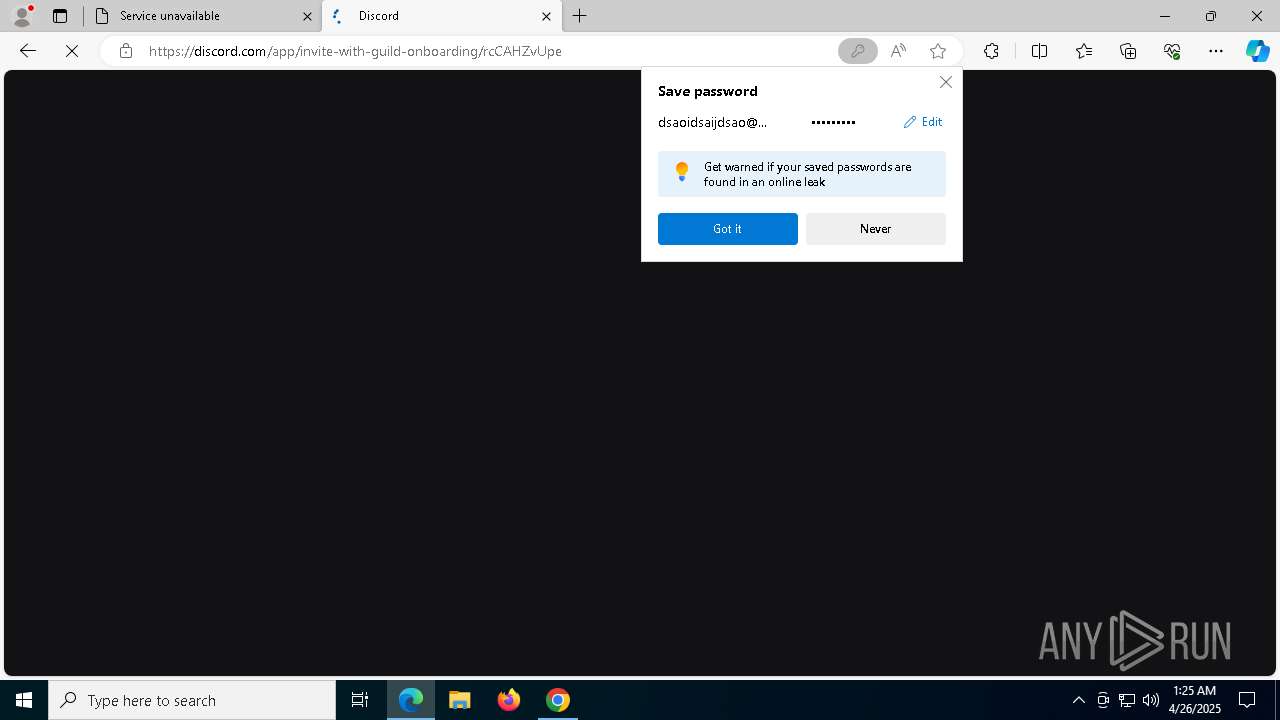
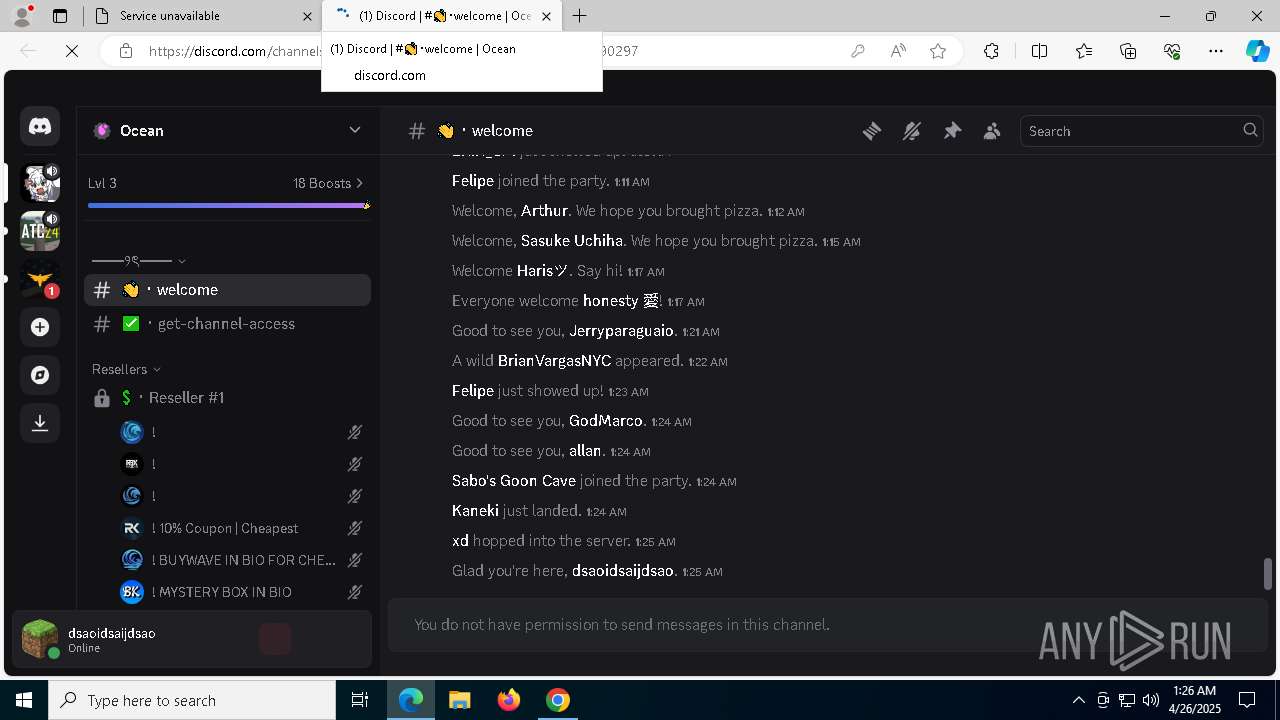
Attempting to use instant messaging service
- msedge.exe (PID: 736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
243
Monitored processes
102
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | C:\Users\admin\AppData\Local\Programs\Wave\bin\Bloxstrap.exe | C:\Users\admin\AppData\Local\Programs\Wave\bin\Bloxstrap.exe | — | Wave.exe | |||||||||||
User: admin Company: Bloxstrap Integrity Level: HIGH Description: Bloxstrap Exit code: 2147516547 Version: 4.2.1 Modules
| |||||||||||||||
| 516 | "C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Wave" --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAEAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --field-trial-handle=1808,i,12266441384618399038,315008063712946083,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=1796 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe | — | Wave.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: Wave Exit code: 0 Version: 0.4.6 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2456 --field-trial-handle=2352,i,5325905503952949546,6470372869517123497,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5644 --field-trial-handle=1784,i,1545960201631501287,55867322673334574,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6636 --field-trial-handle=2352,i,5325905503952949546,6470372869517123497,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5336 --field-trial-handle=1784,i,1545960201631501287,55867322673334574,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\Wave" --standard-schemes=app --secure-schemes=app --field-trial-handle=2036,i,12266441384618399038,315008063712946083,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2032 /prefetch:3 | C:\Users\admin\AppData\Local\Programs\Wave\Wave.exe | — | Wave.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Wave Exit code: 0 Version: 0.4.6 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x2f4,0x2f8,0x2fc,0x2ec,0x304,0x7ffc84505fd8,0x7ffc84505fe4,0x7ffc84505ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6248 --field-trial-handle=2352,i,5325905503952949546,6470372869517123497,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\system32\cmd.exe /d /s /c "powershell.exe Start-Process -FilePath "'C:\Users\admin\AppData\Local\Temp\6bd1b671fd3bbeb3aae79ba4d94671ba\execute.bat'" -WindowStyle hidden -Verb runAs" | C:\Windows\System32\cmd.exe | — | Wave.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 022
Read events
22 921
Write events
77
Delete events
24
Modification events
| (PID) Process: | (7332) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7332) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7332) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7332) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7332) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5988) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000E173B1D749B6DB01 | |||
| (PID) Process: | (6108) Wave-Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\66920116-fd5e-58eb-8cdb-b4525ae2cfc1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\Wave | |||
| (PID) Process: | (6108) Wave-Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\66920116-fd5e-58eb-8cdb-b4525ae2cfc1 |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (6108) Wave-Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\66920116-fd5e-58eb-8cdb-b4525ae2cfc1 |
| Operation: | write | Name: | ShortcutName |
Value: Wave | |||
| (PID) Process: | (6108) Wave-Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\66920116-fd5e-58eb-8cdb-b4525ae2cfc1 |
| Operation: | write | Name: | DisplayName |
Value: Wave 0.4.6 | |||
Executable files
45
Suspicious files
1 050
Text files
124
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c41d.TMP | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c42c.TMP | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c42c.TMP | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c43c.TMP | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c43c.TMP | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c43c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
122
DNS requests
151
Threats
62
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.206.251.73:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | IT | binary | 825 b | whitelisted |
2104 | svchost.exe | GET | 200 | 104.106.85.220:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | IT | binary | 868 b | whitelisted |
2104 | svchost.exe | GET | 200 | 23.206.251.73:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | IT | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 104.106.85.220:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | IT | binary | 868 b | whitelisted |
6544 | svchost.exe | GET | 200 | 23.52.56.216:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | NL | binary | 471 b | whitelisted |
1180 | SIHClient.exe | GET | 200 | 104.106.85.220:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | IT | binary | 419 b | whitelisted |
8092 | svchost.exe | HEAD | 200 | 142.250.186.78:80 | http://dl.google.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | US | — | — | whitelisted |
8092 | svchost.exe | GET | 206 | 142.250.186.78:80 | http://dl.google.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | US | binary | 2.47 Kb | whitelisted |
1180 | SIHClient.exe | GET | 200 | 104.106.85.220:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | IT | binary | 407 b | whitelisted |
8092 | svchost.exe | GET | 206 | 142.250.186.78:80 | http://dl.google.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | US | binary | 4.84 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5112 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.206.251.73:80 | crl.microsoft.com | Akamai International B.V. | IT | whitelisted |
2104 | svchost.exe | 23.206.251.73:80 | crl.microsoft.com | Akamai International B.V. | IT | whitelisted |
5496 | MoUsoCoreWorker.exe | 104.106.85.220:80 | www.microsoft.com | AKAMAI-AS | IT | whitelisted |
2104 | svchost.exe | 104.106.85.220:80 | www.microsoft.com | AKAMAI-AS | IT | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
getwave.gg |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn.getwave.gg |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7596 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7596 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7596 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
736 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
736 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
736 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
736 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
736 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
736 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
736 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |