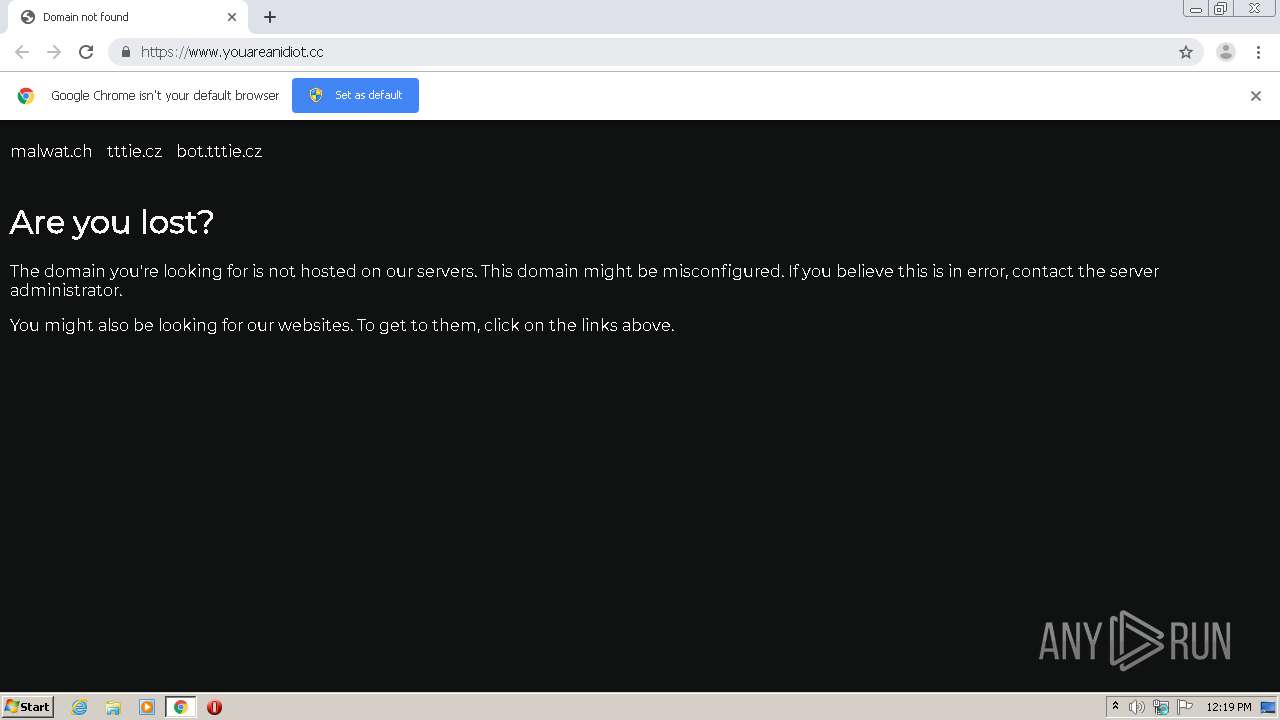
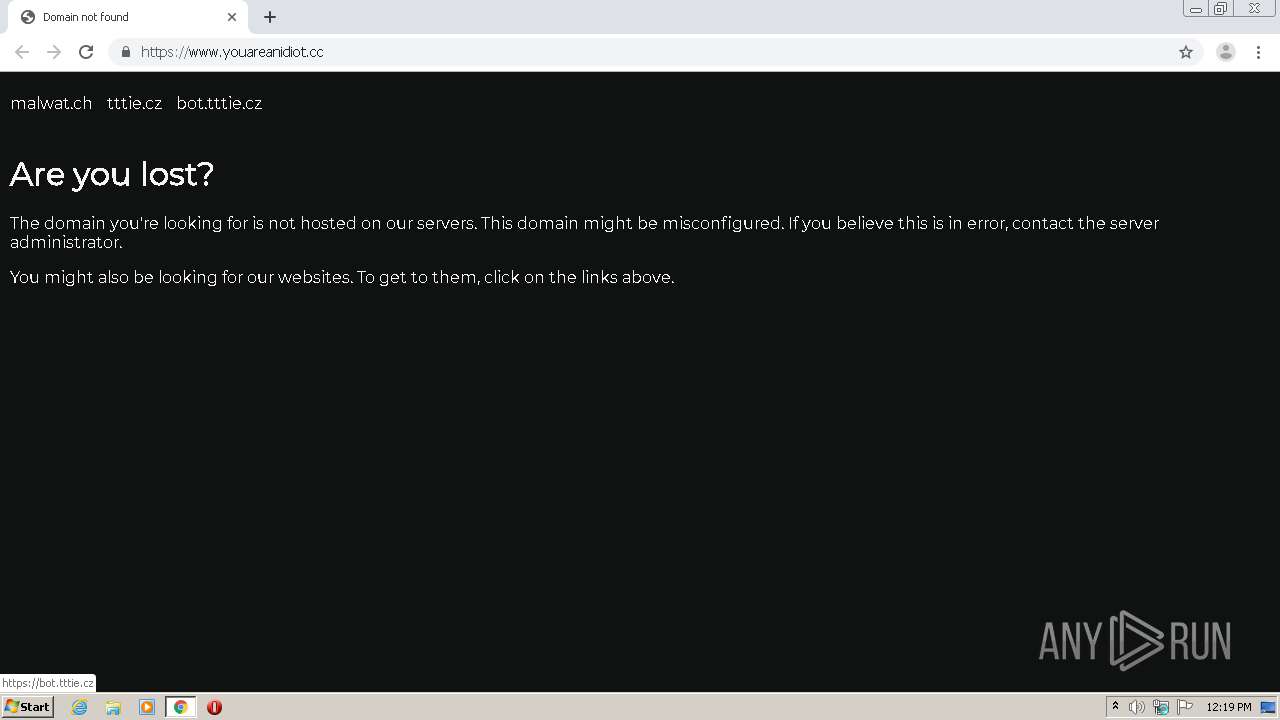
| URL: | http://www.youareanidiot.cc |
| Full analysis: | https://app.any.run/tasks/21835965-4b55-4272-8cf5-c1ae4f61b61b |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2020, 11:19:12 |
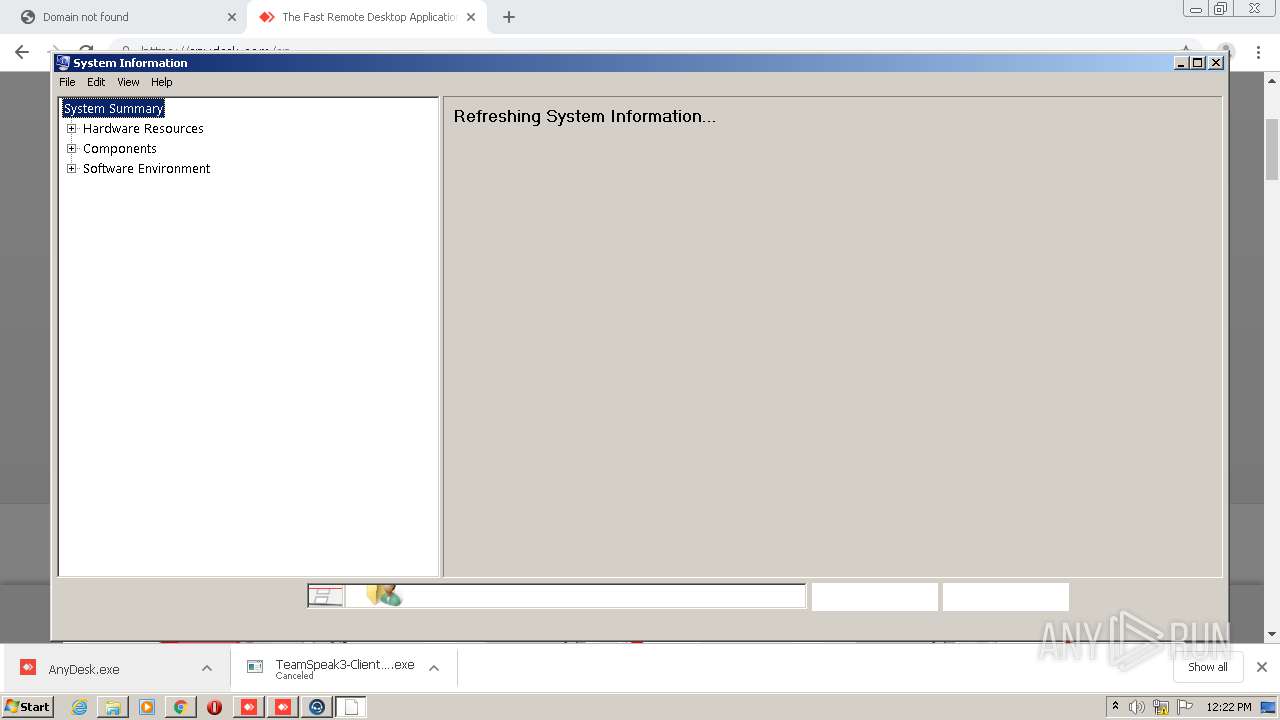
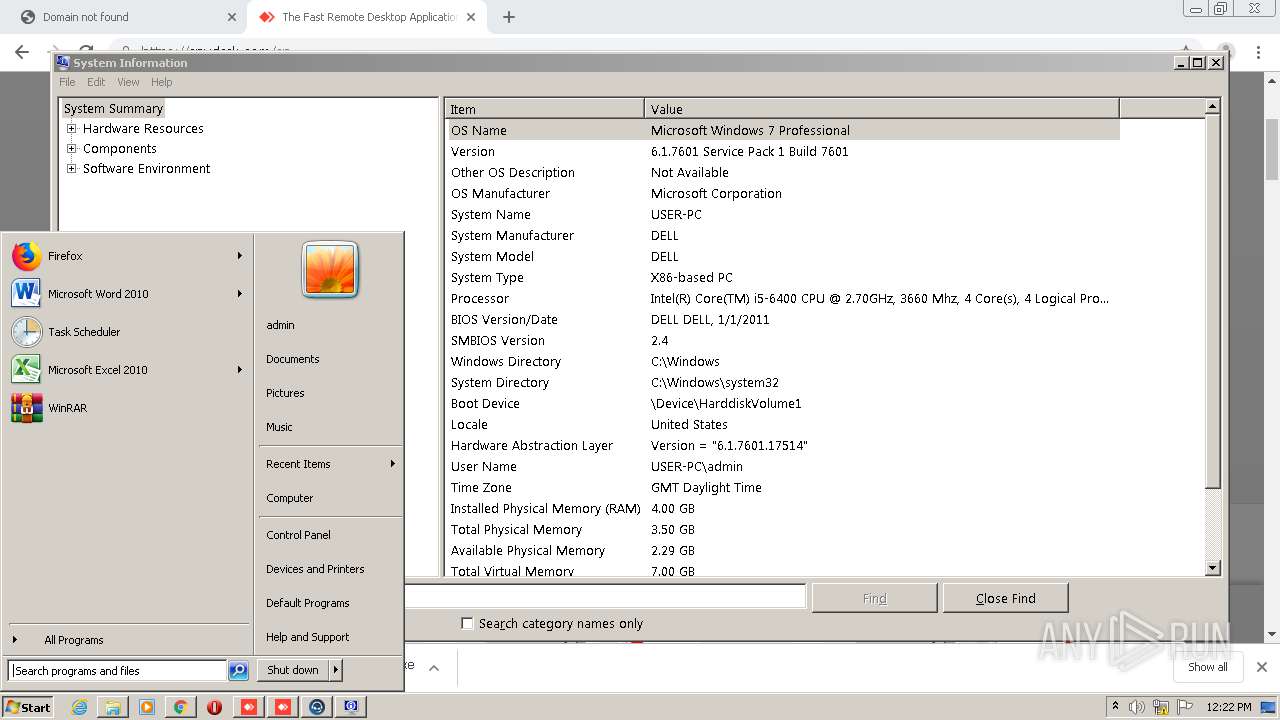
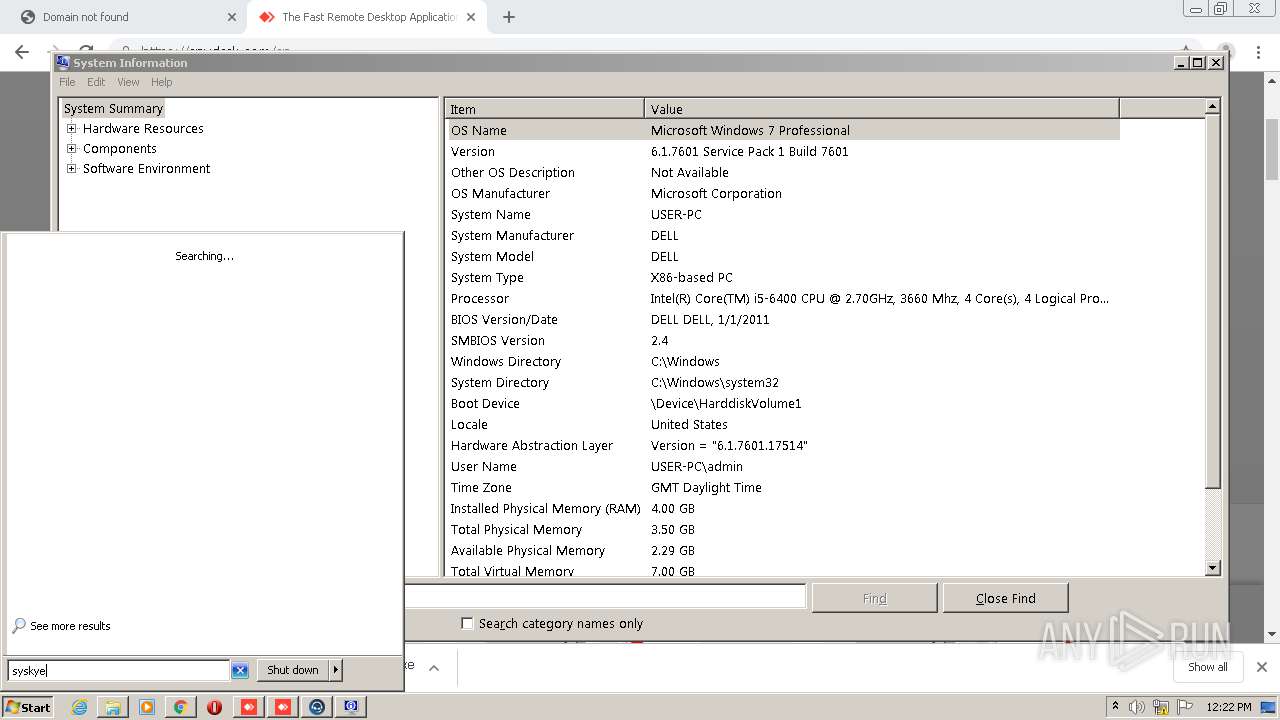
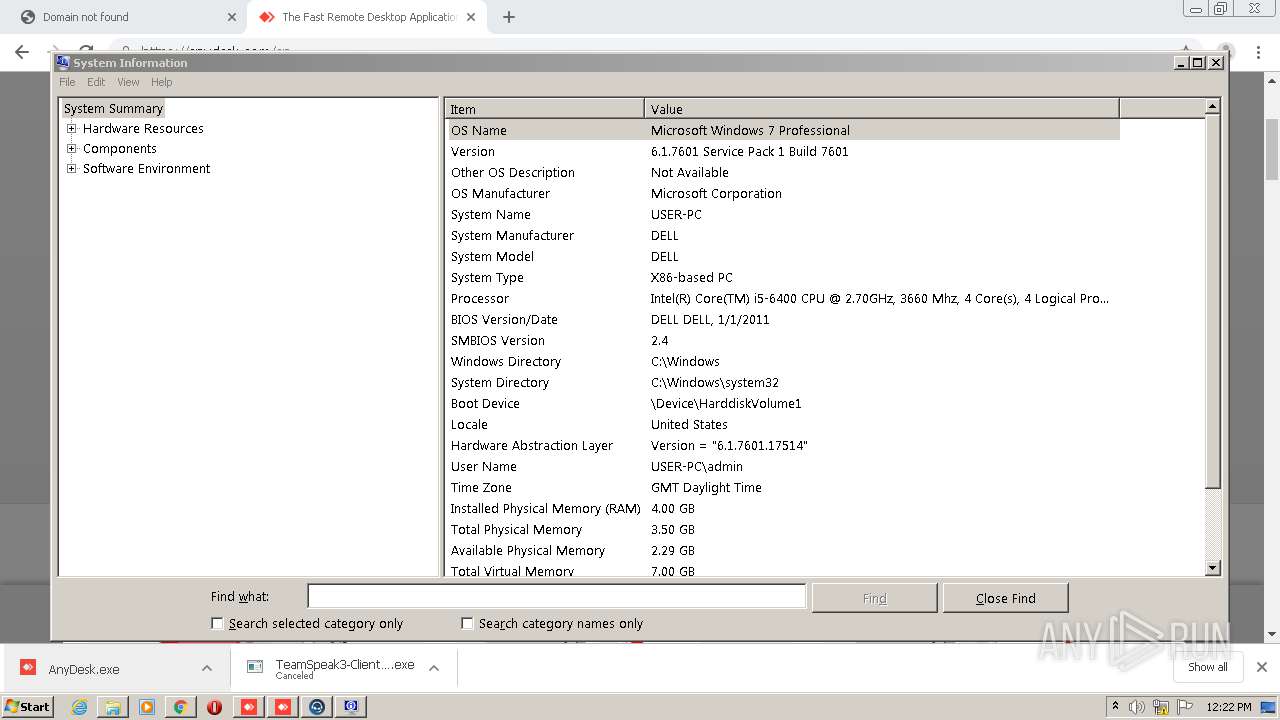
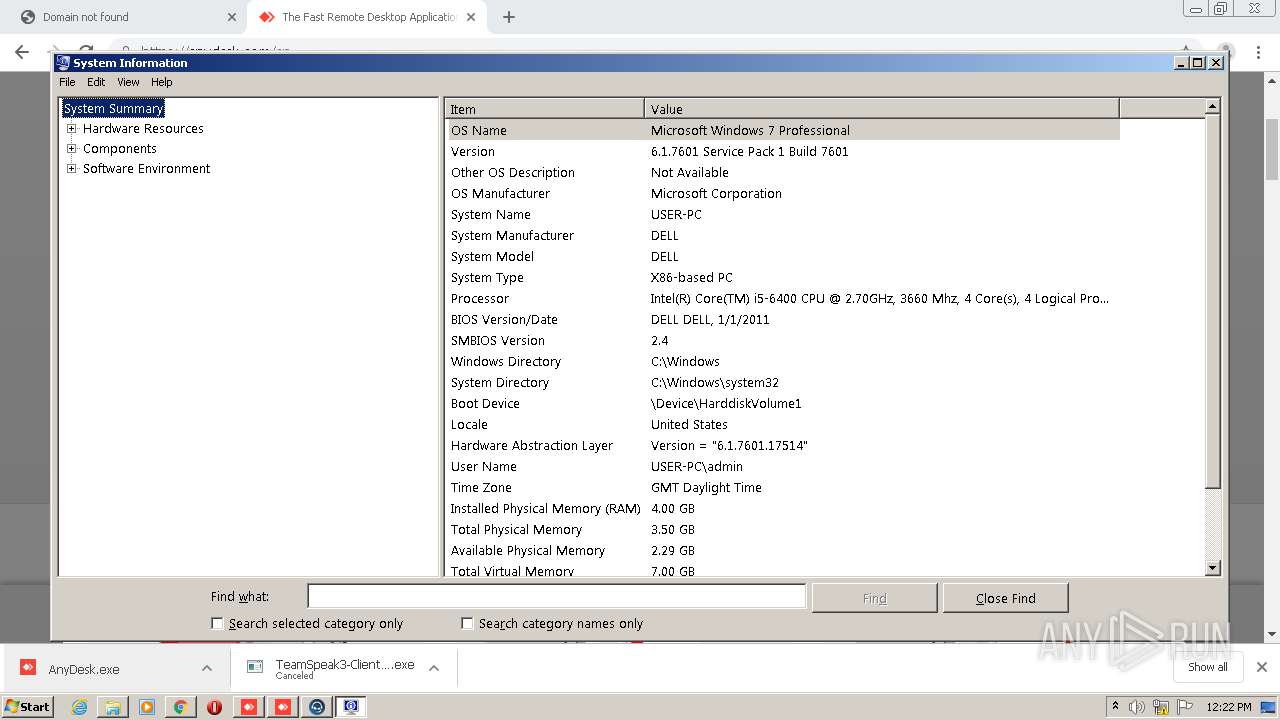
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6C9D4C63700588929A530ADF9C0A8C2B |
| SHA1: | D97FFE98647590498EDE0316136EAFC317340F88 |
| SHA256: | FAC981BC82C58005B2AE2A3D16769365F6A78584382557DEA11AAA0FC160291A |
| SSDEEP: | 3:N1KJS4U+dpQGG:Cc4Ul |
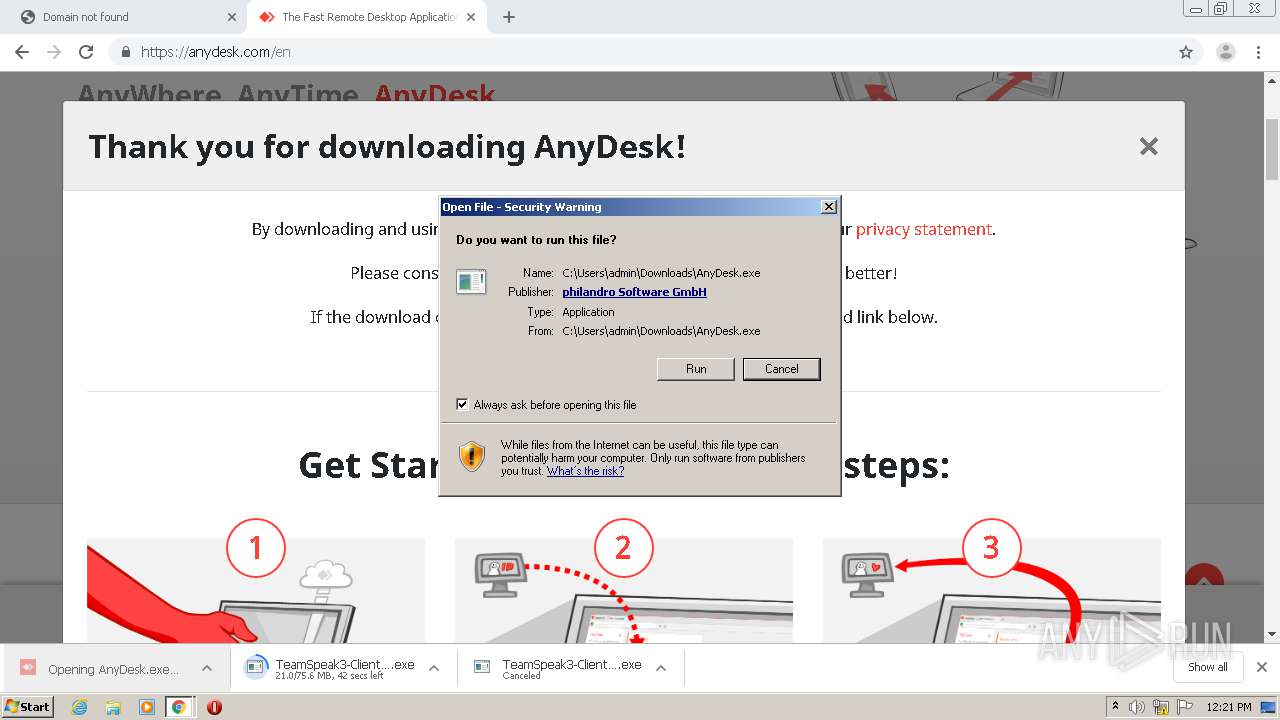
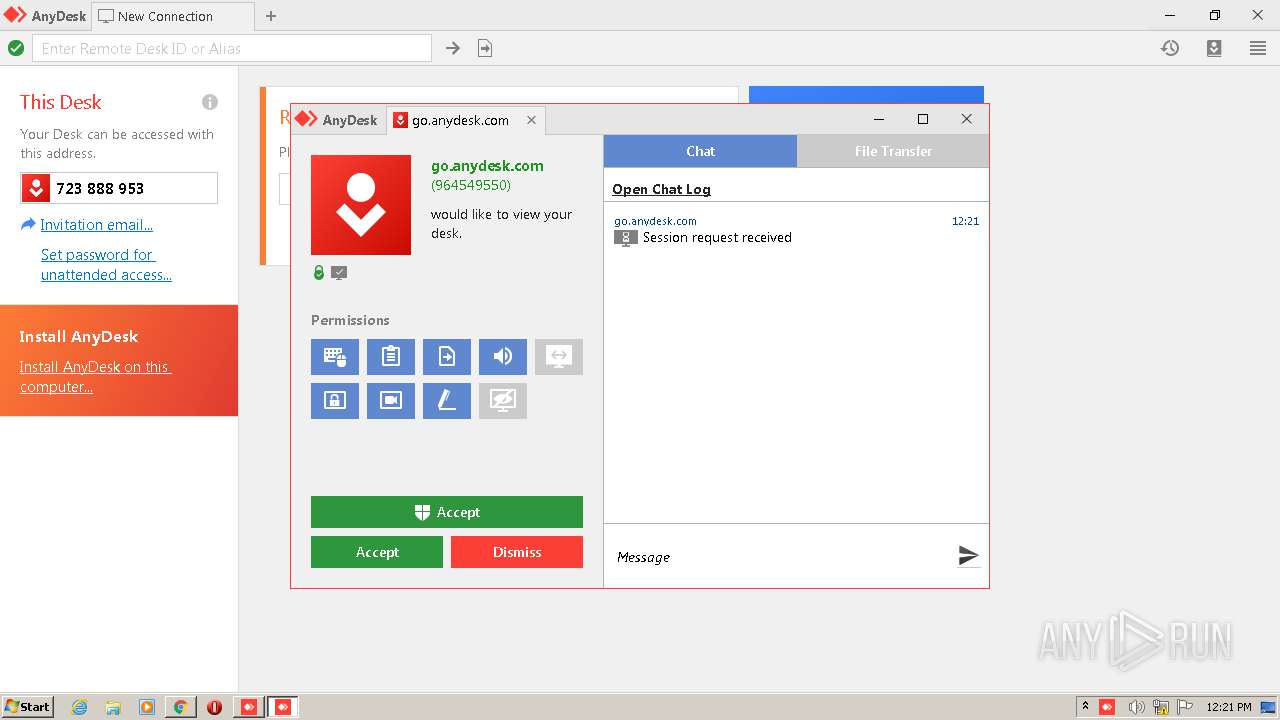
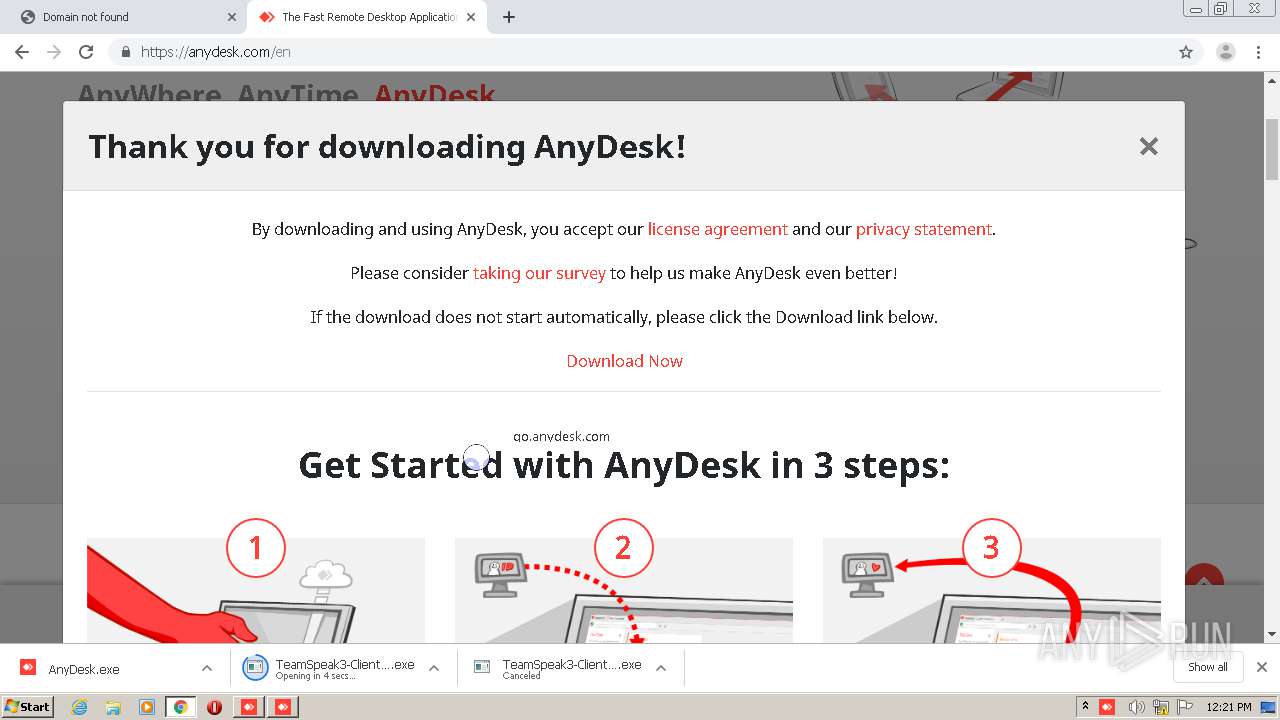
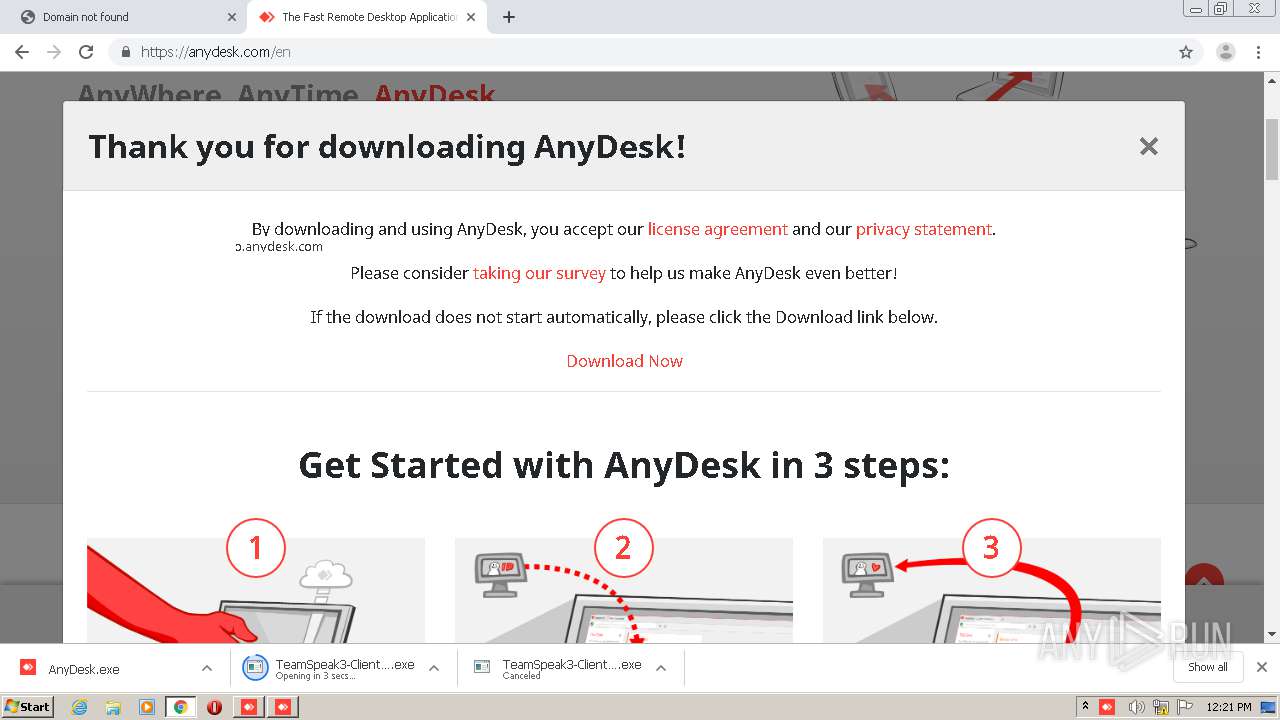
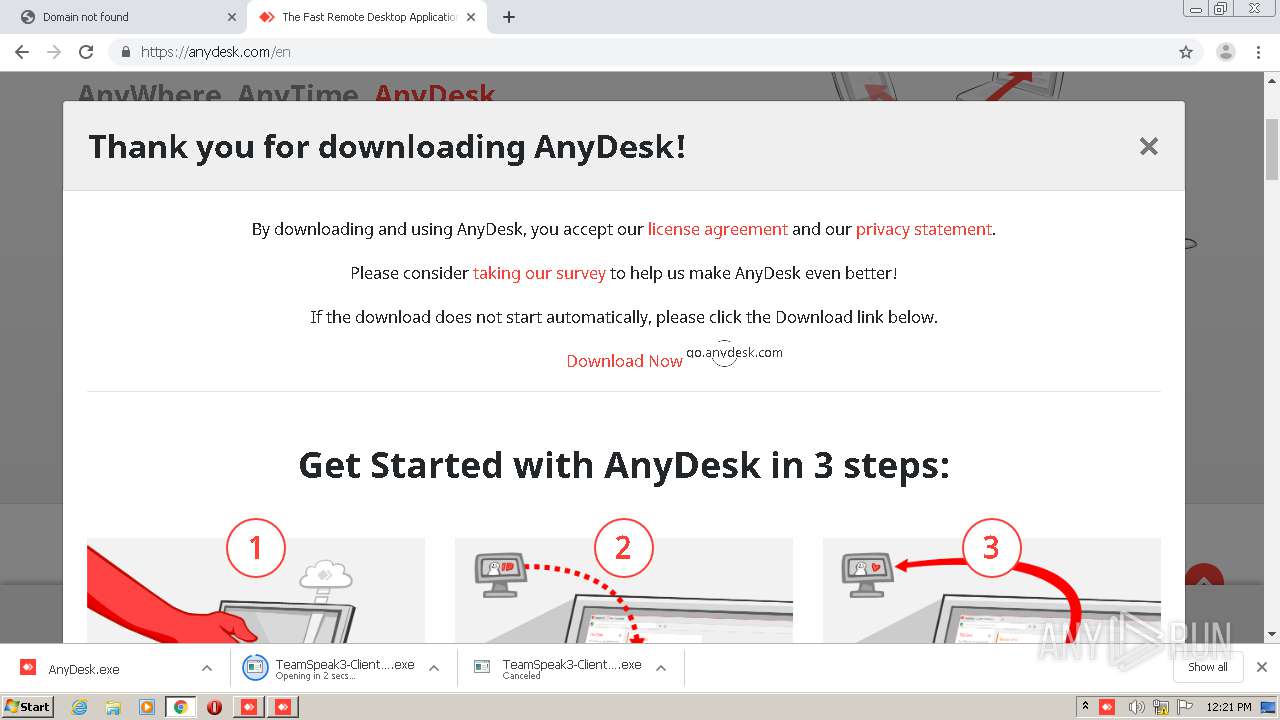
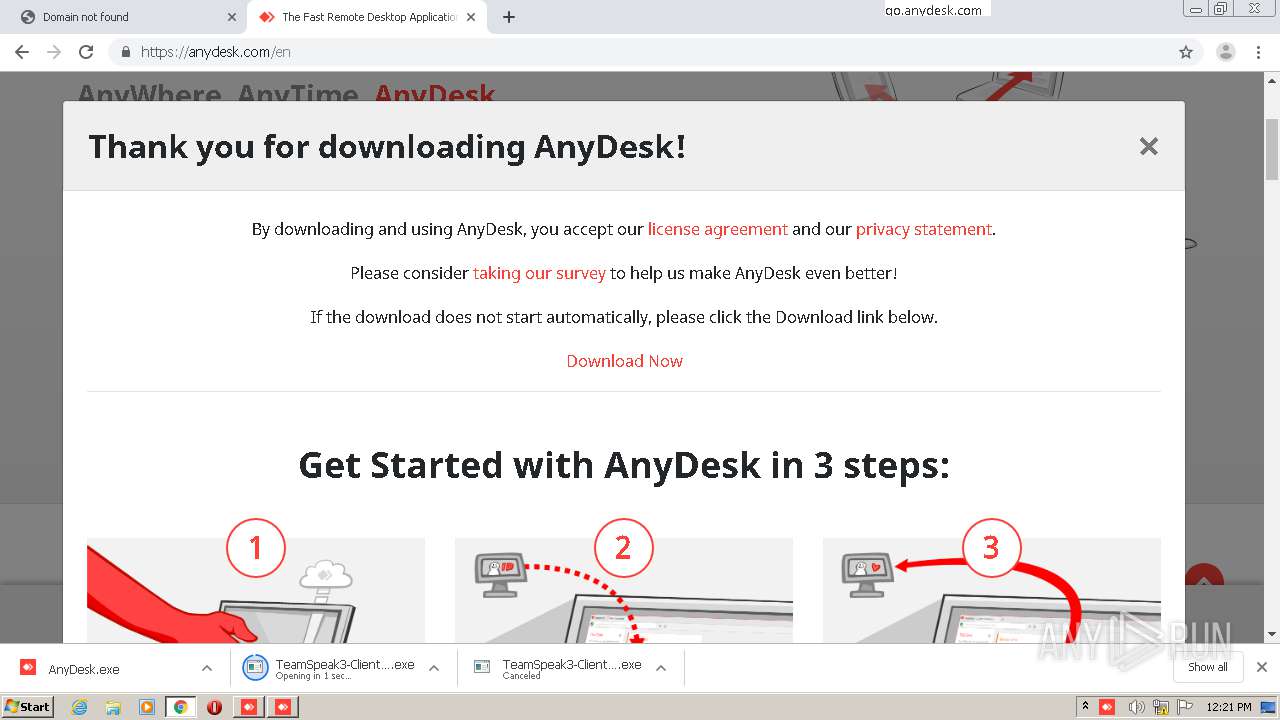
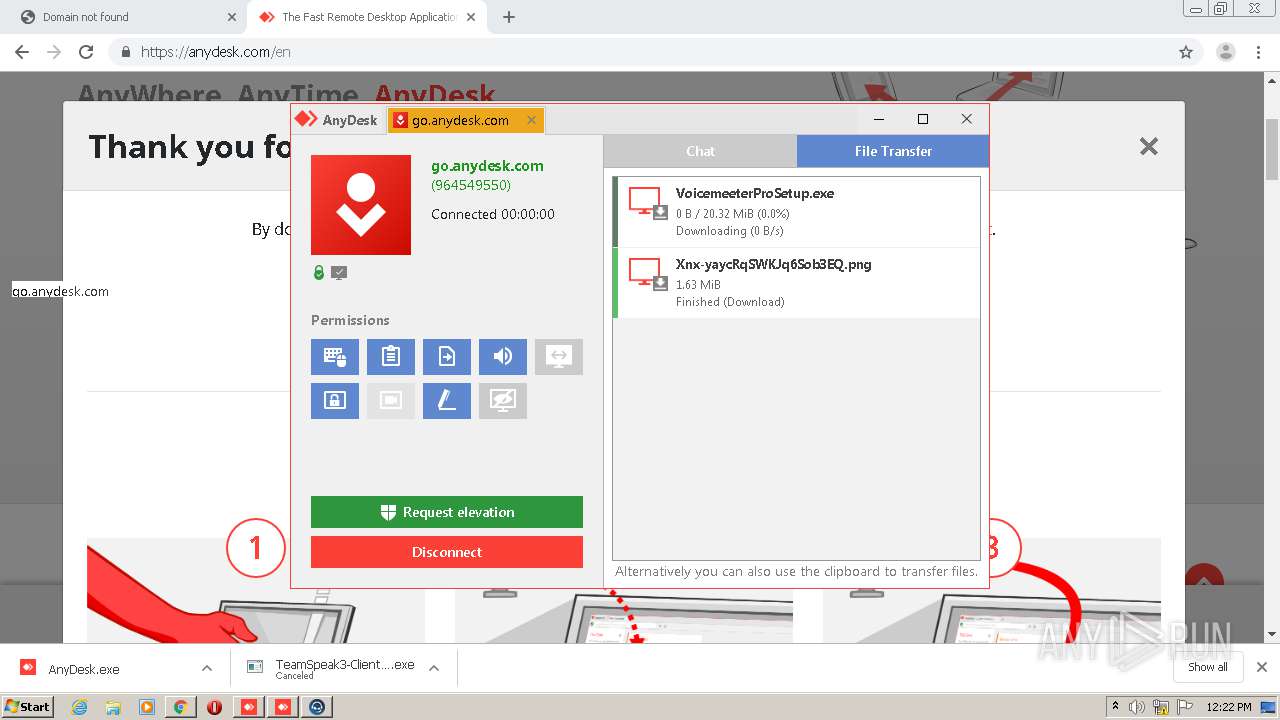
MALICIOUS
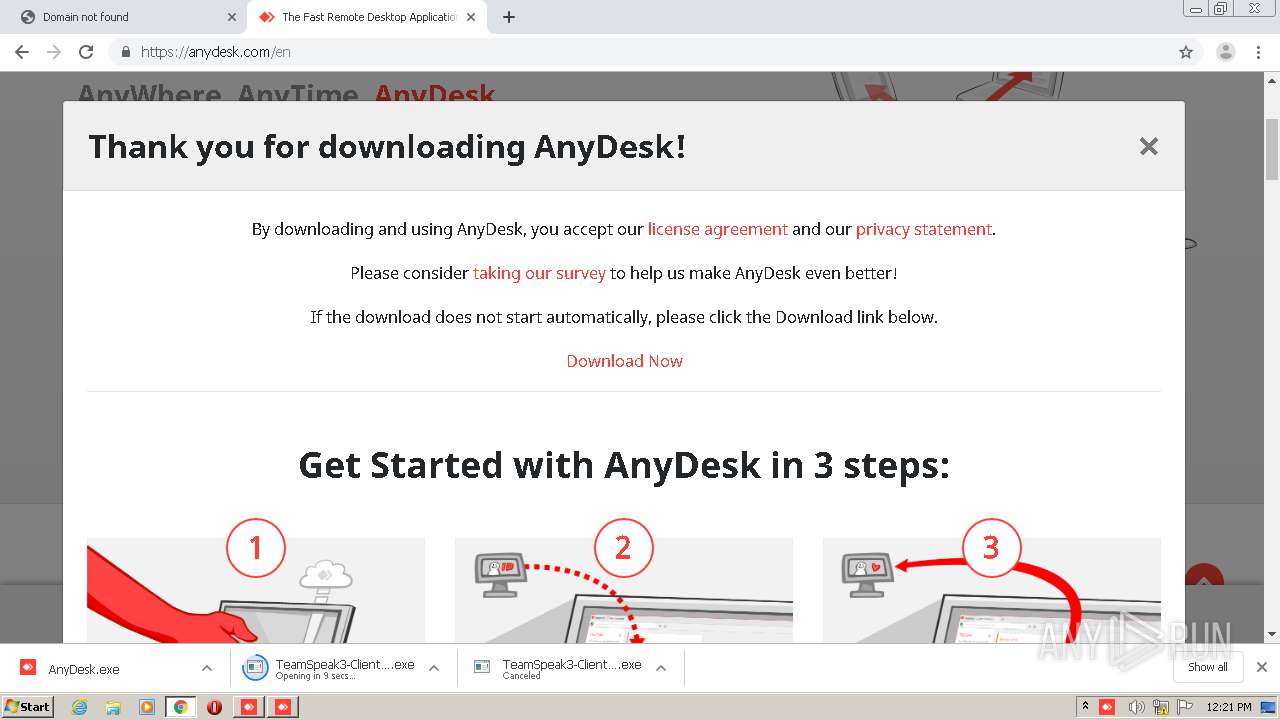
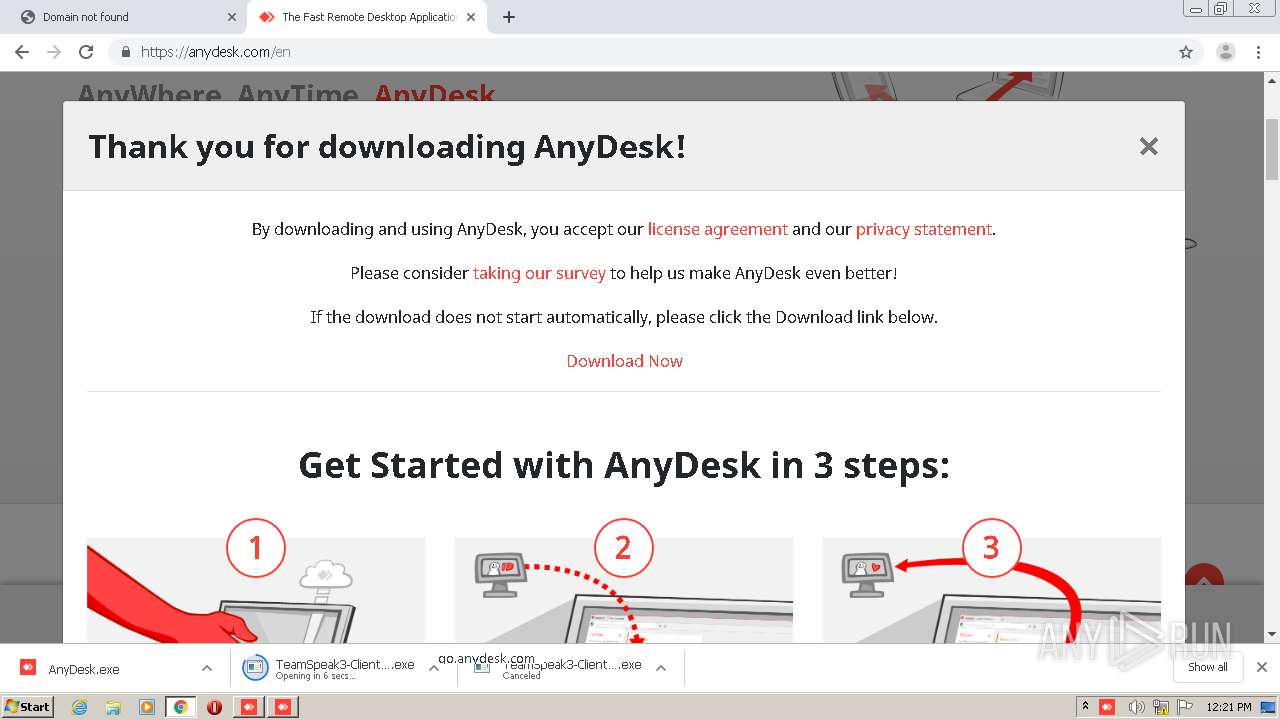
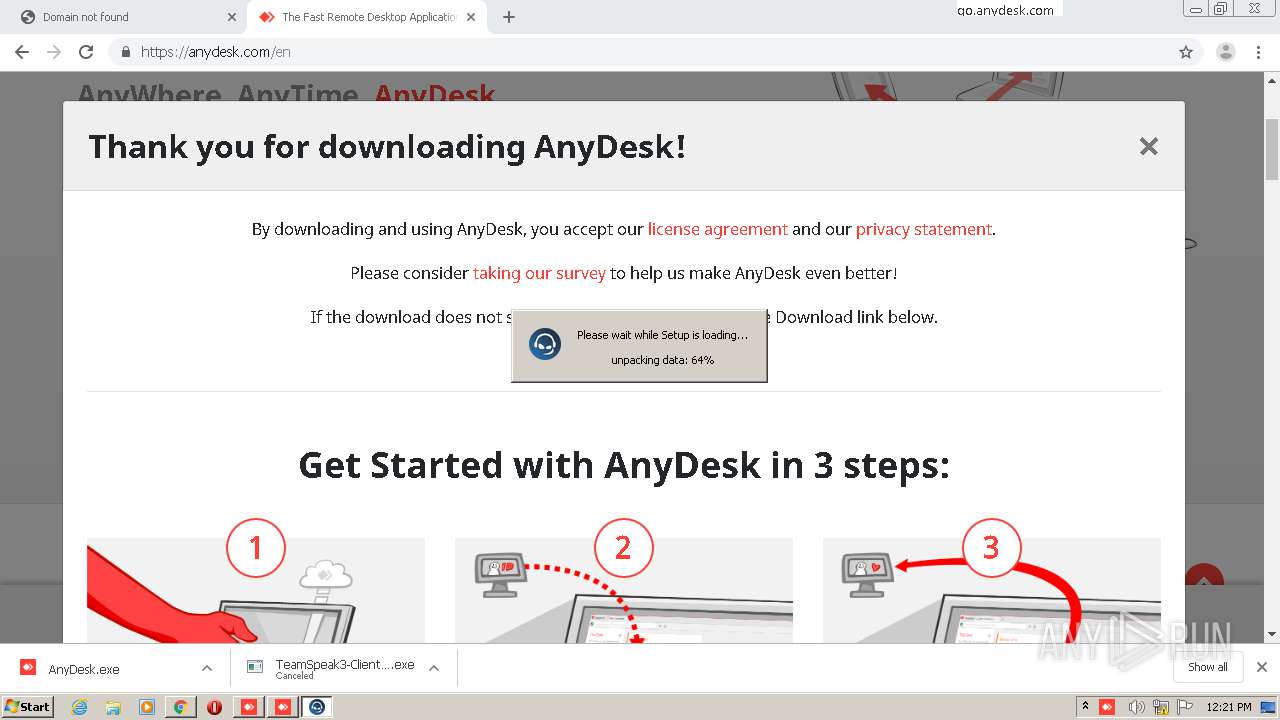
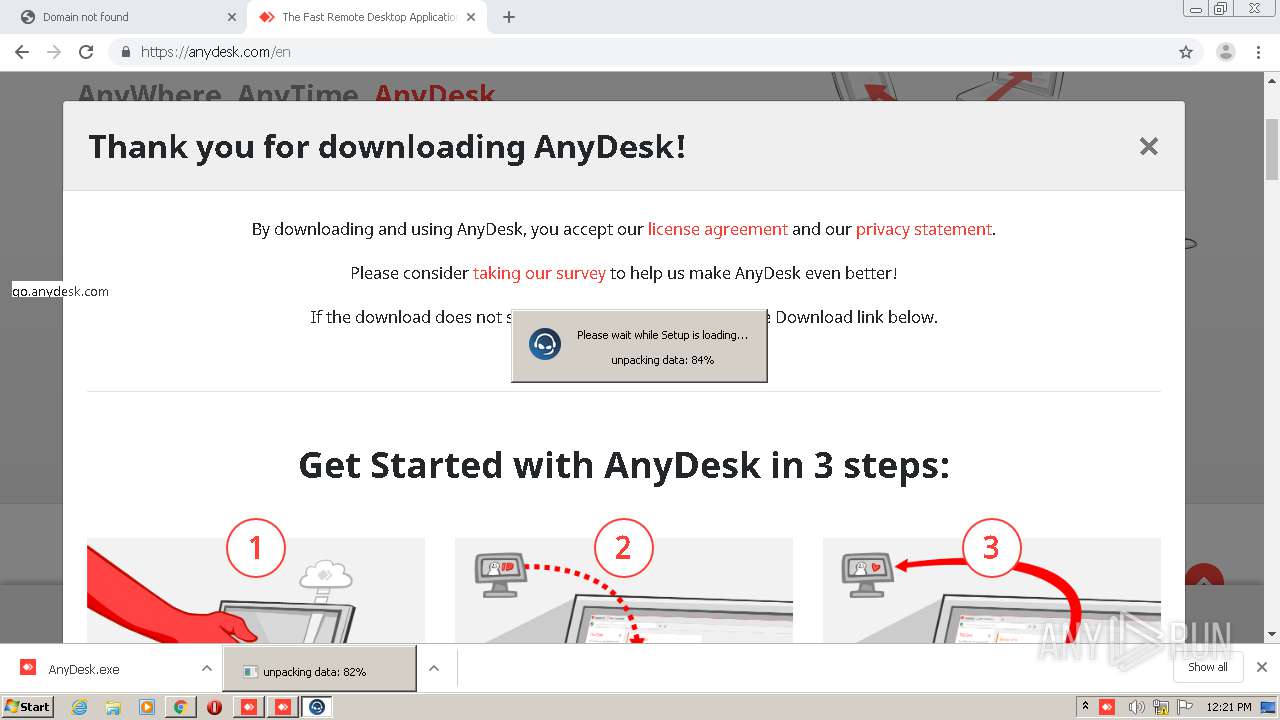
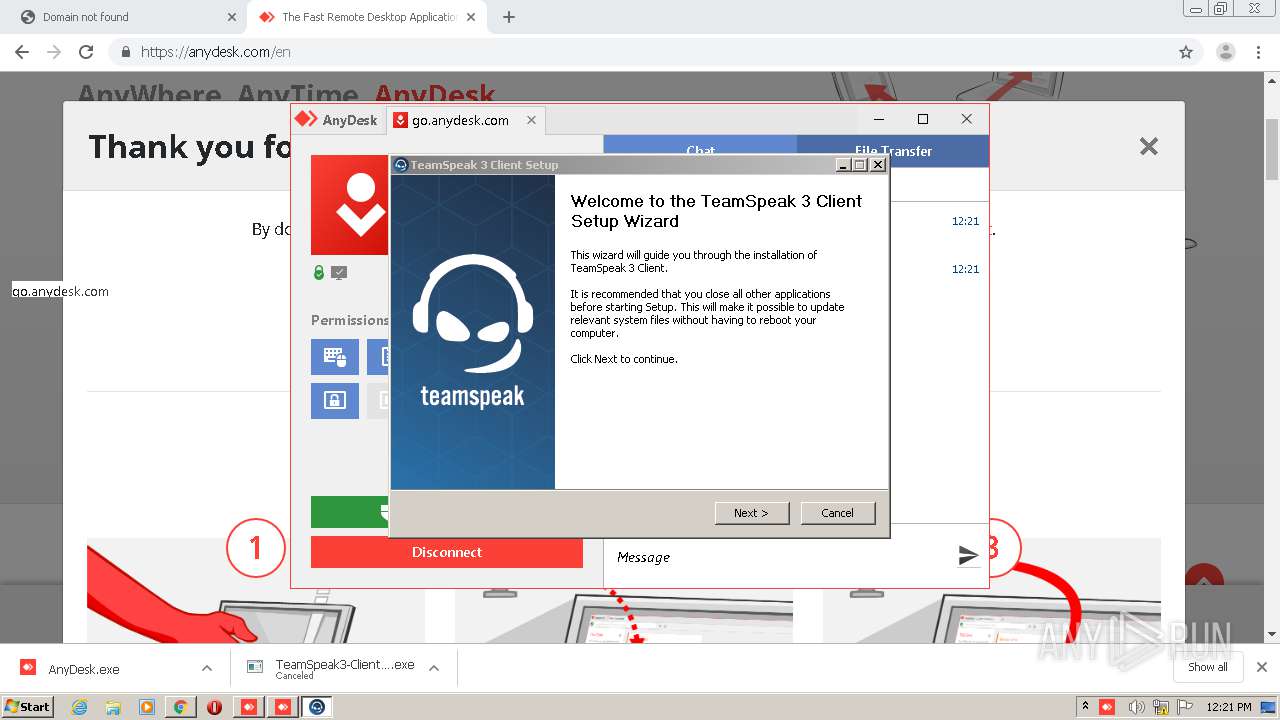
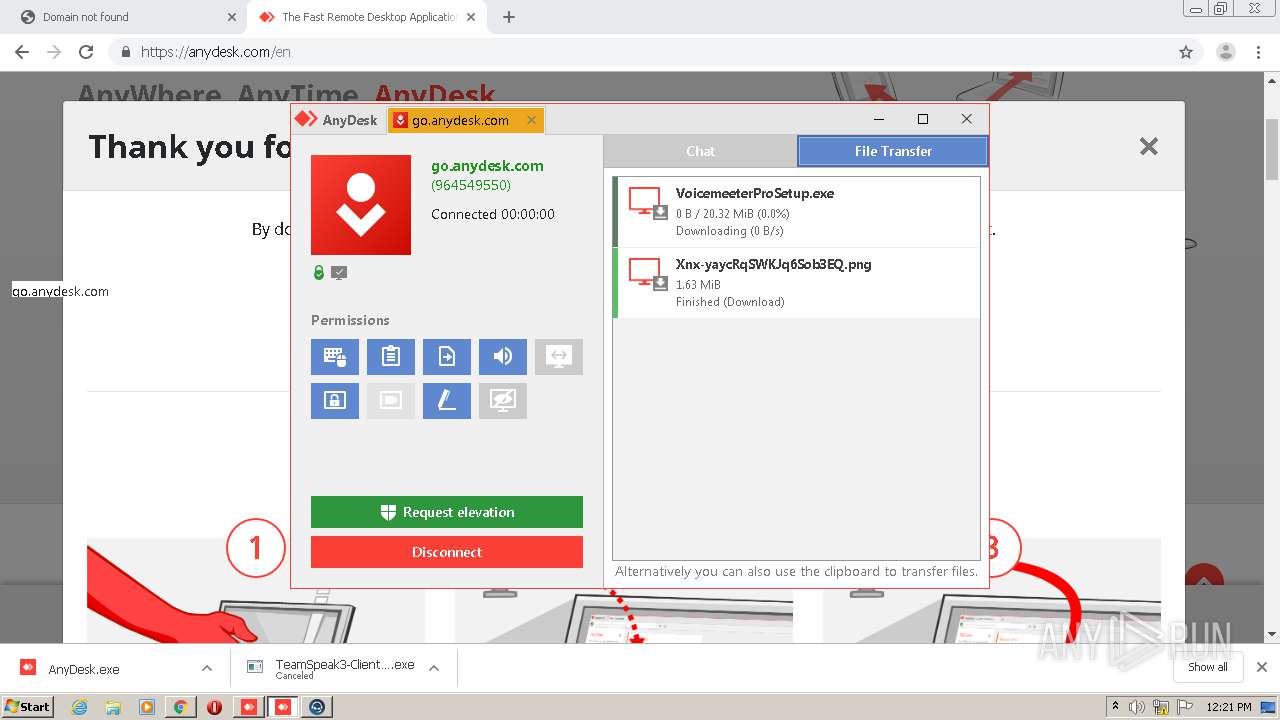
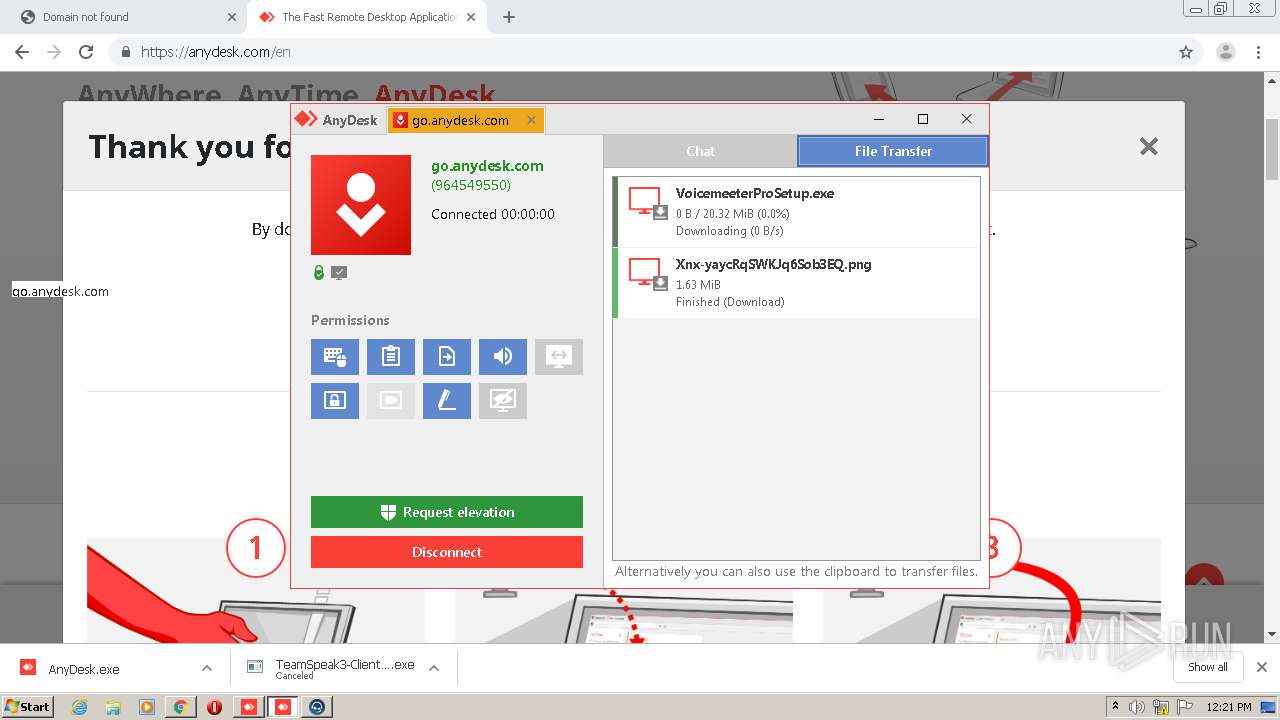
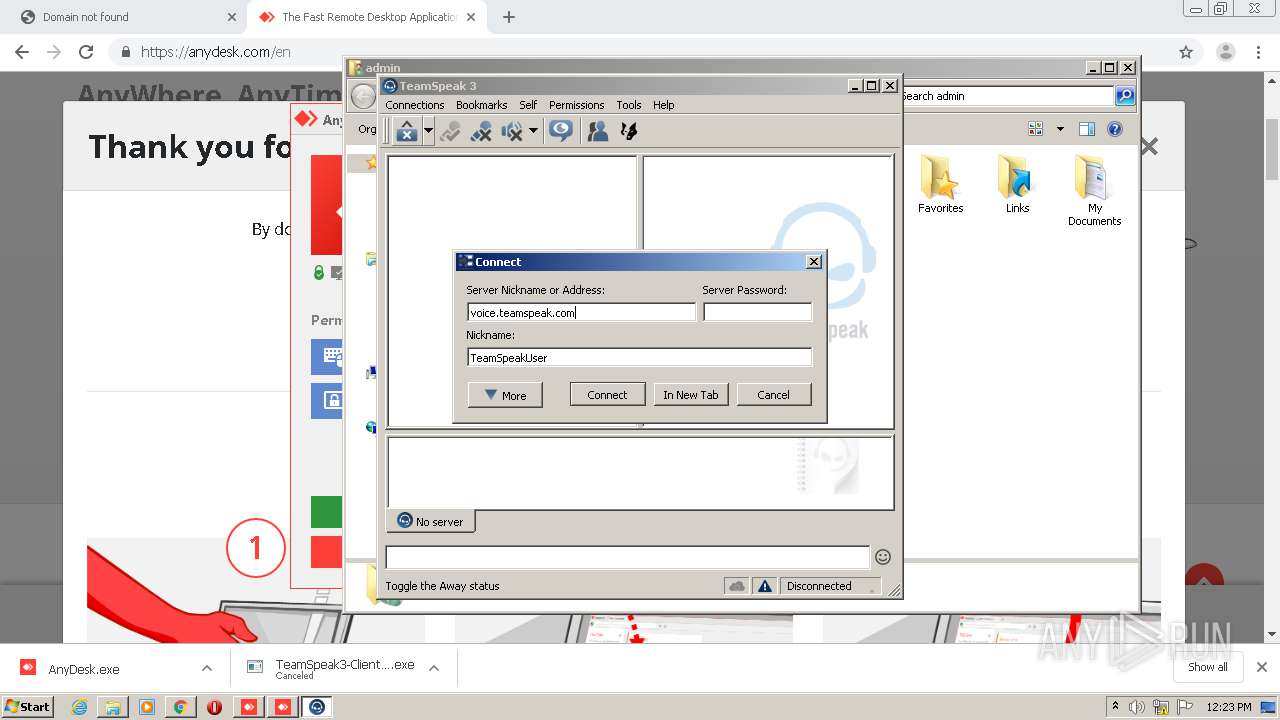
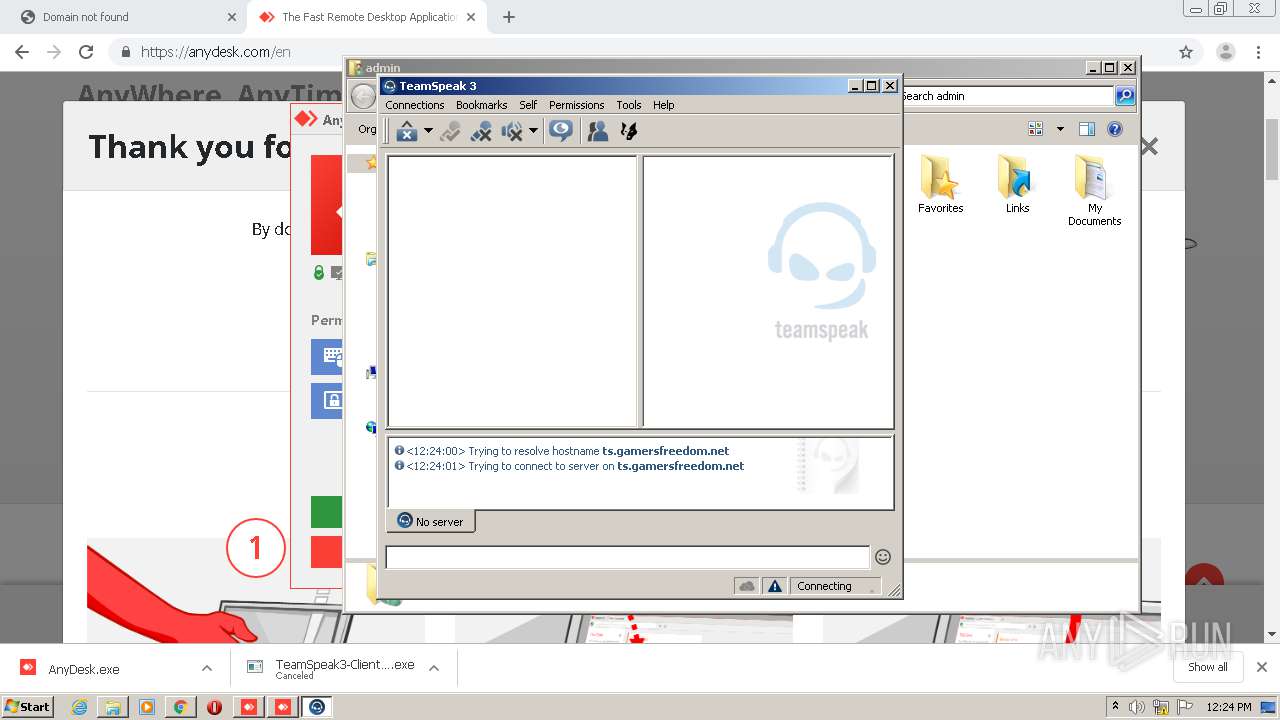
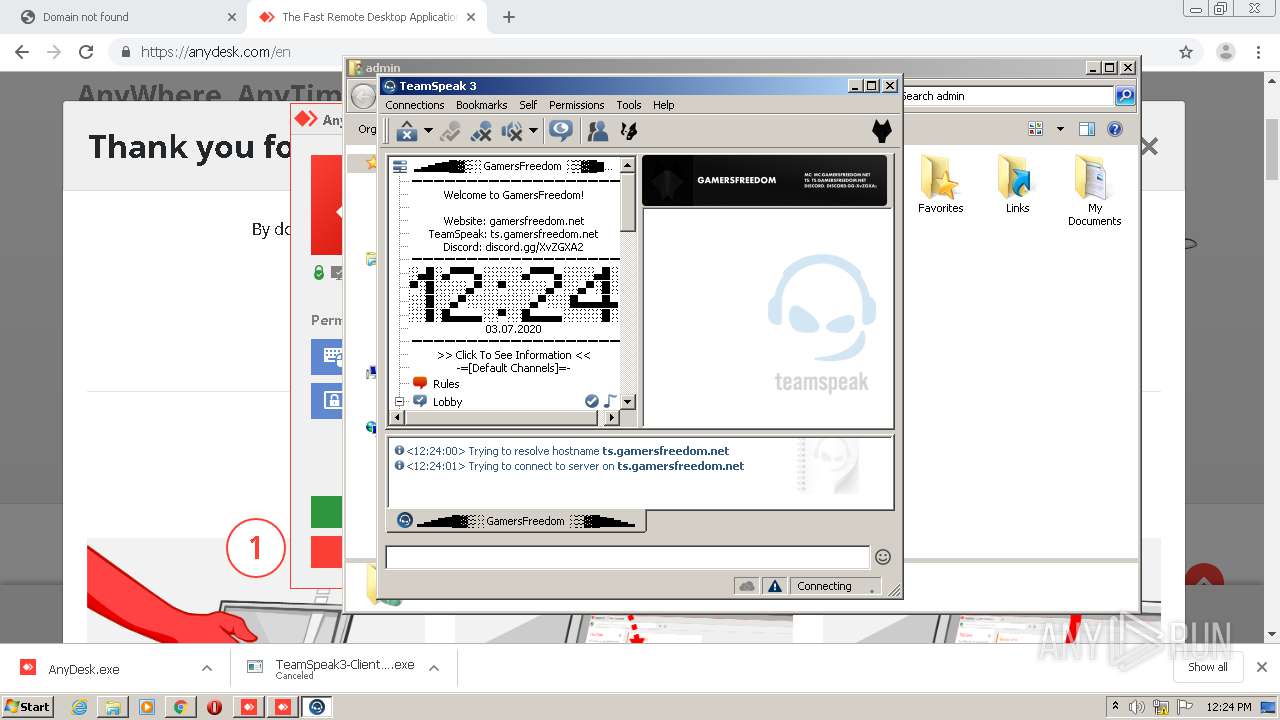
Application was dropped or rewritten from another process
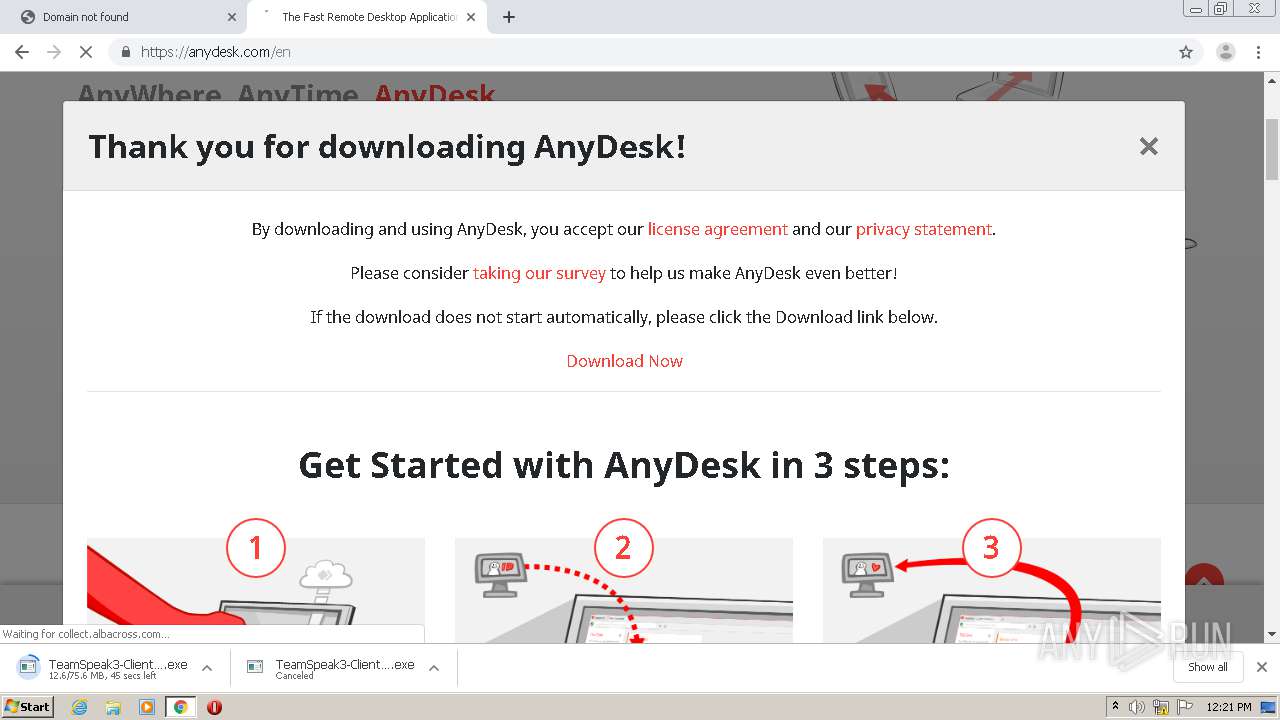
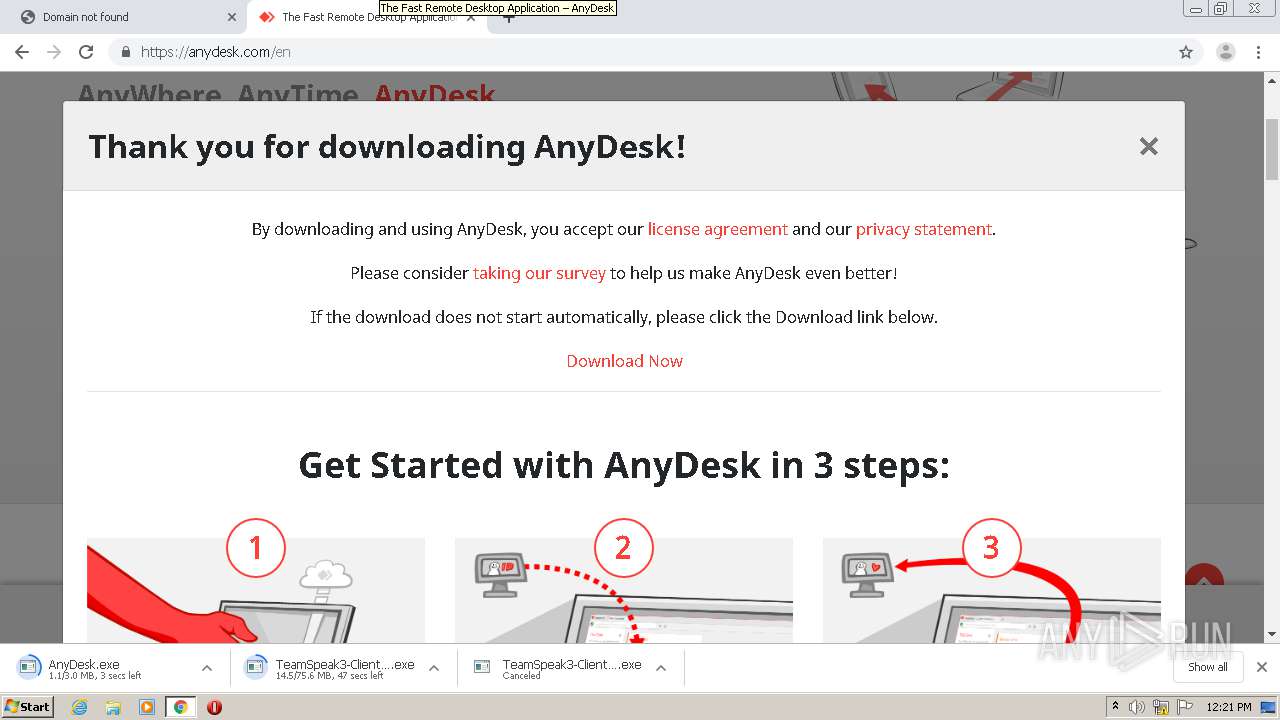
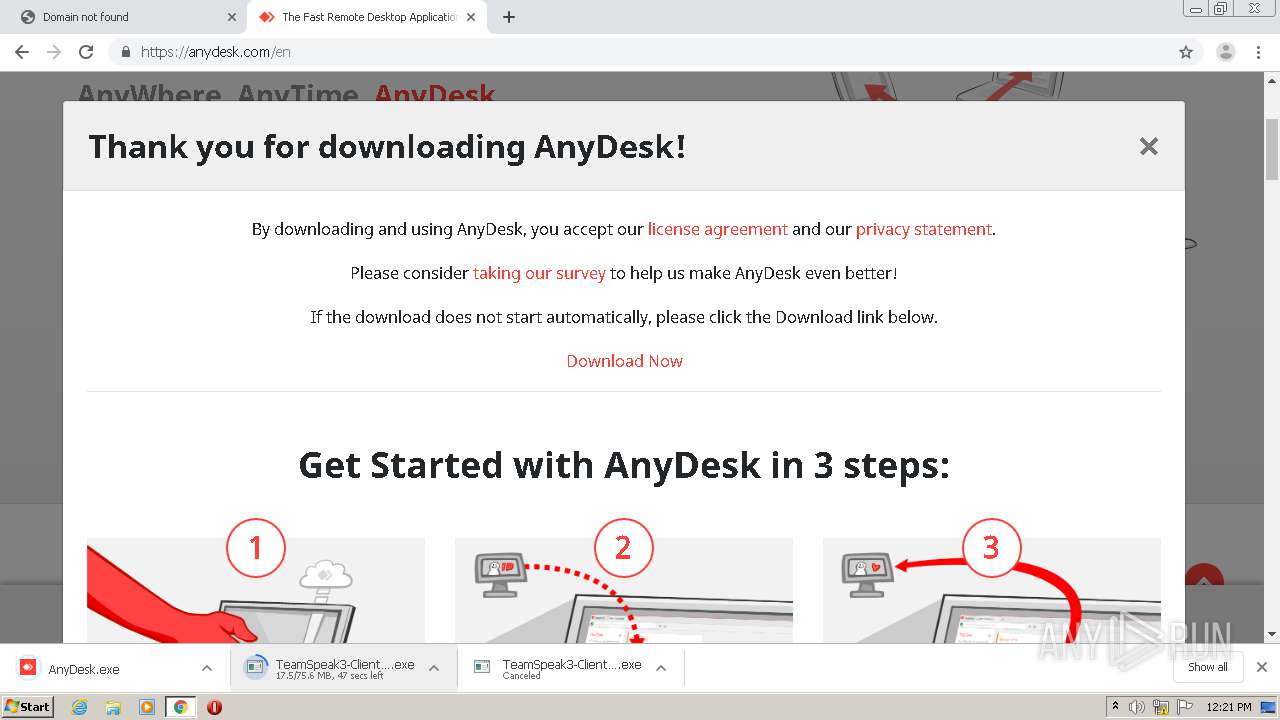
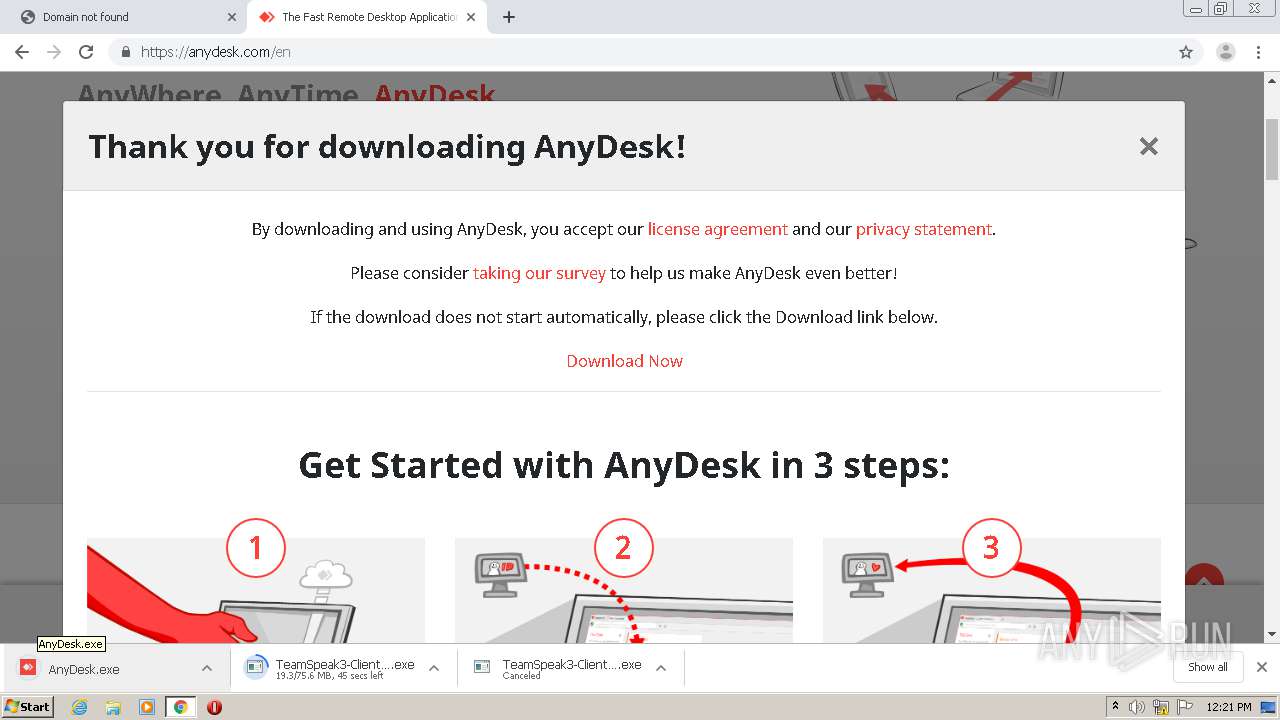
- AnyDesk.exe (PID: 1088)
- AnyDesk.exe (PID: 4060)
- AnyDesk.exe (PID: 2736)
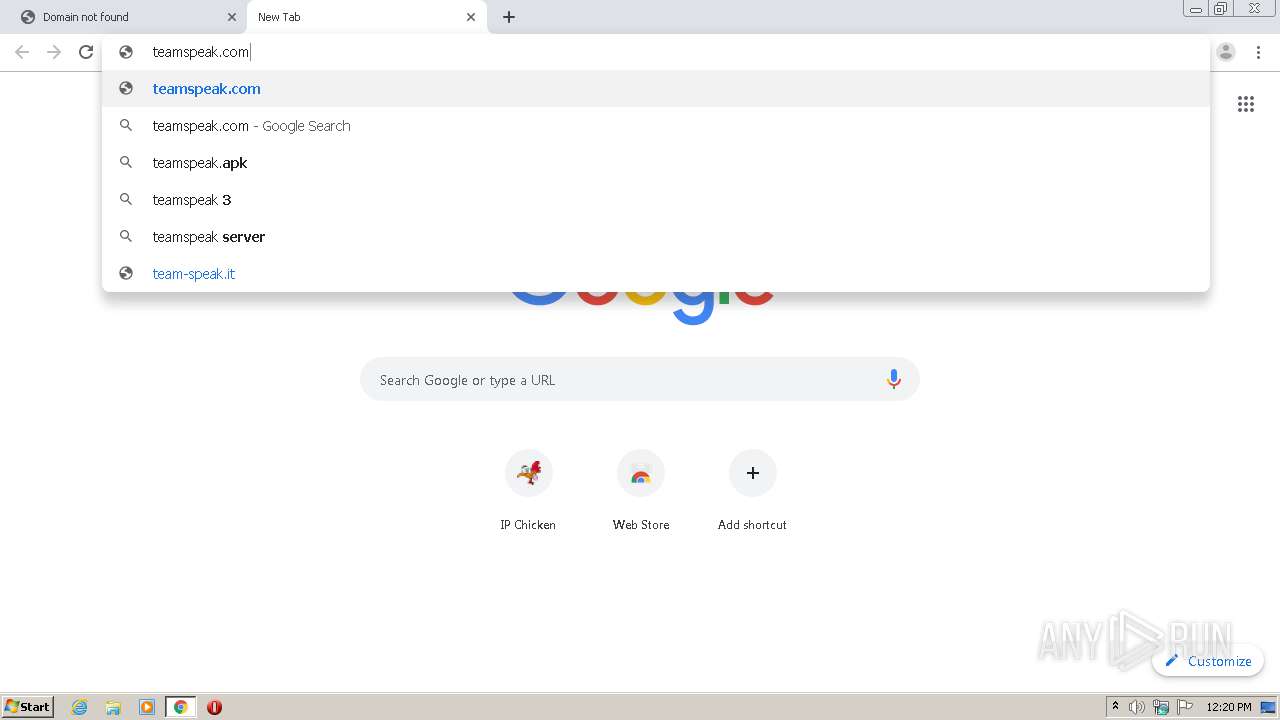
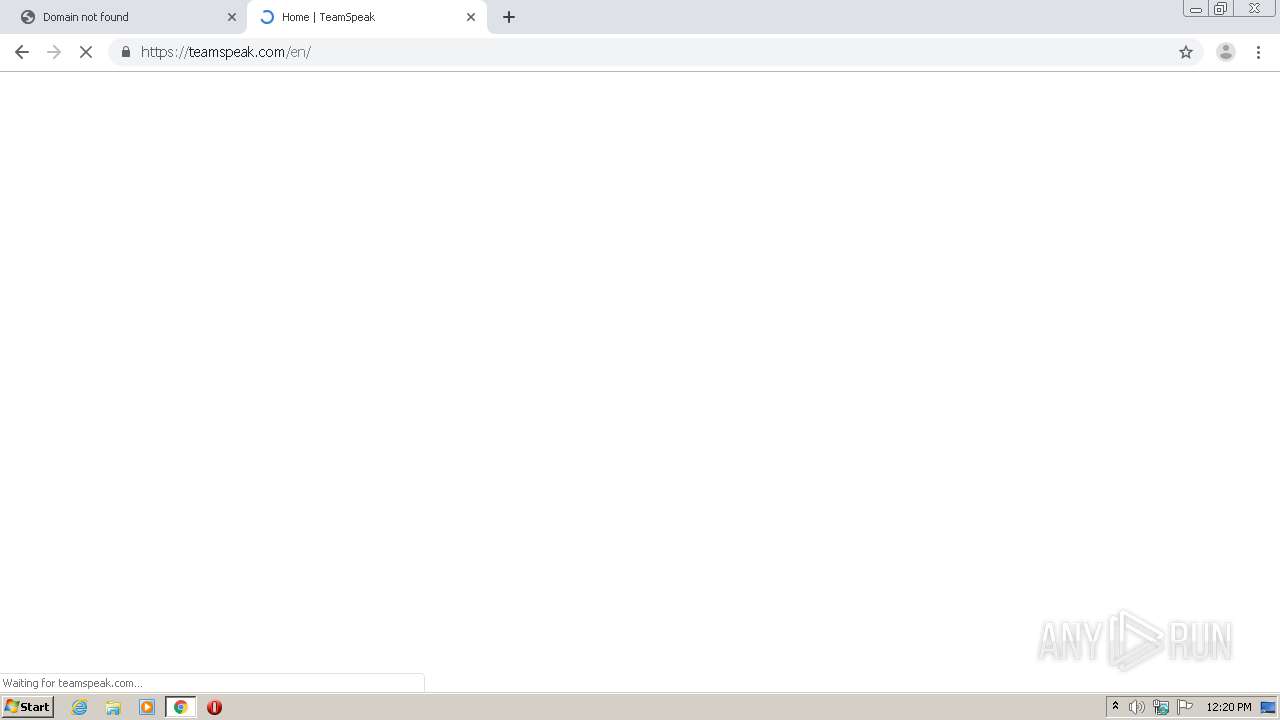
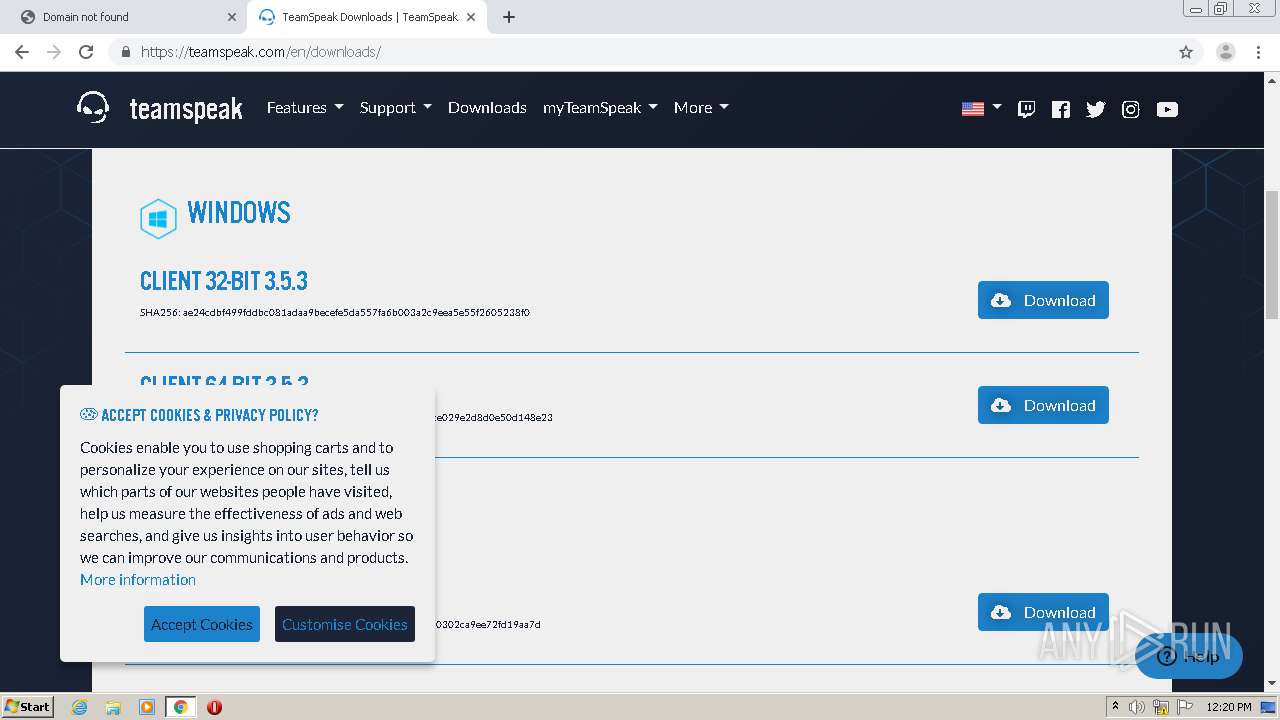
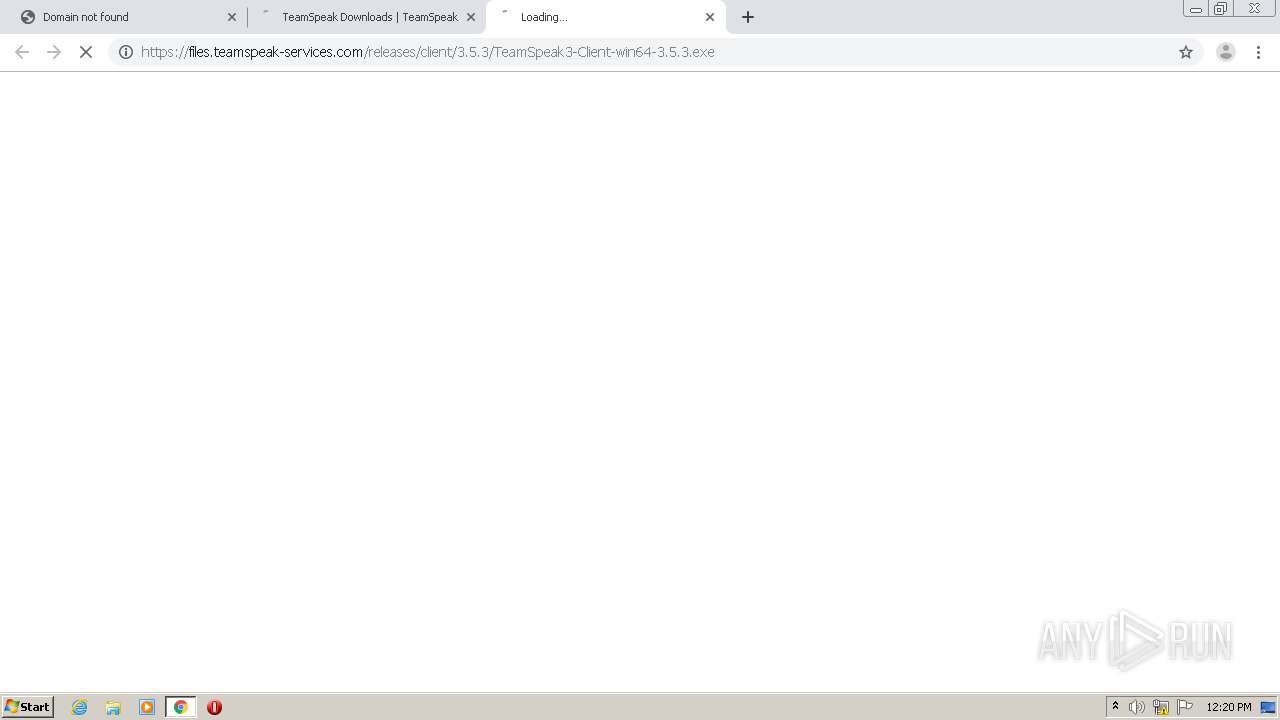
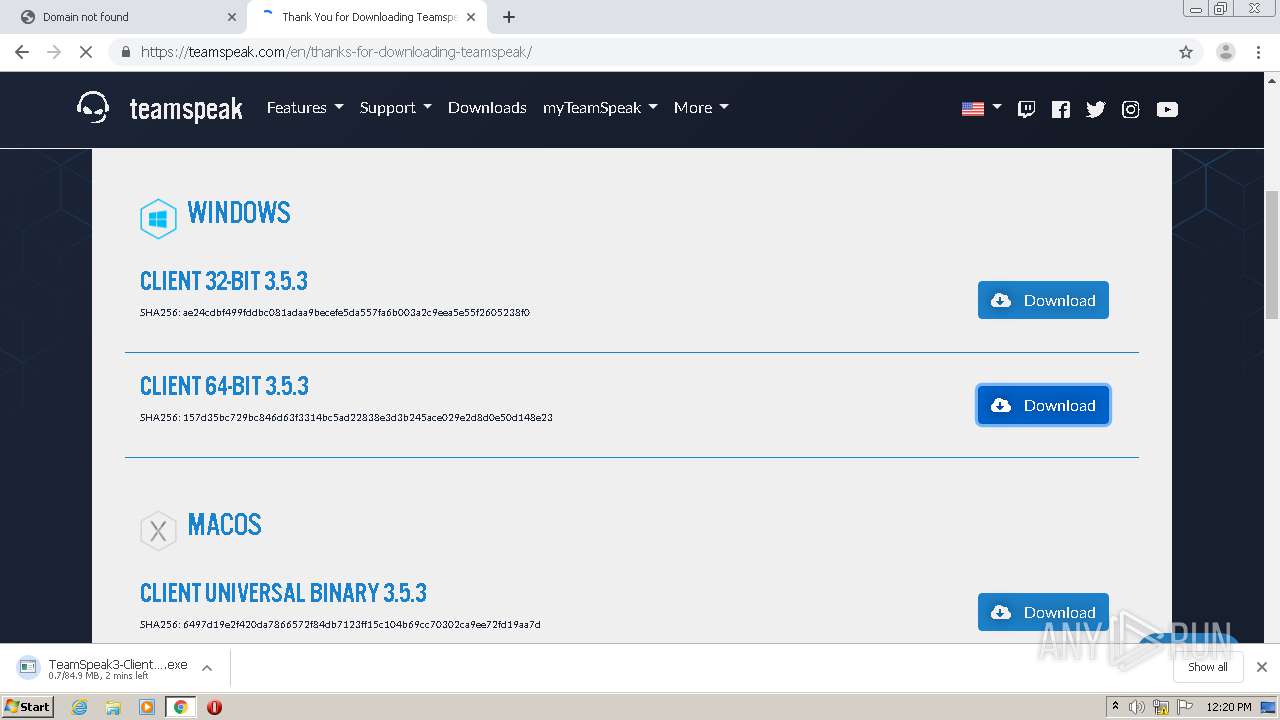
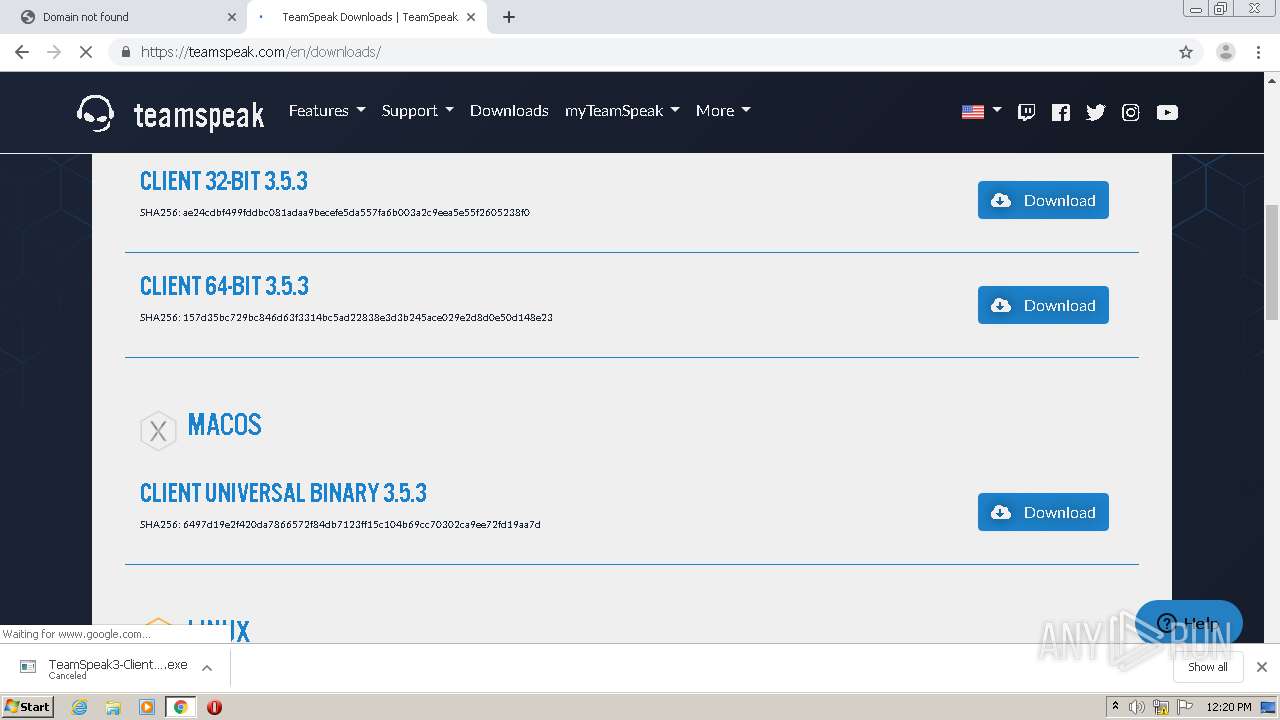
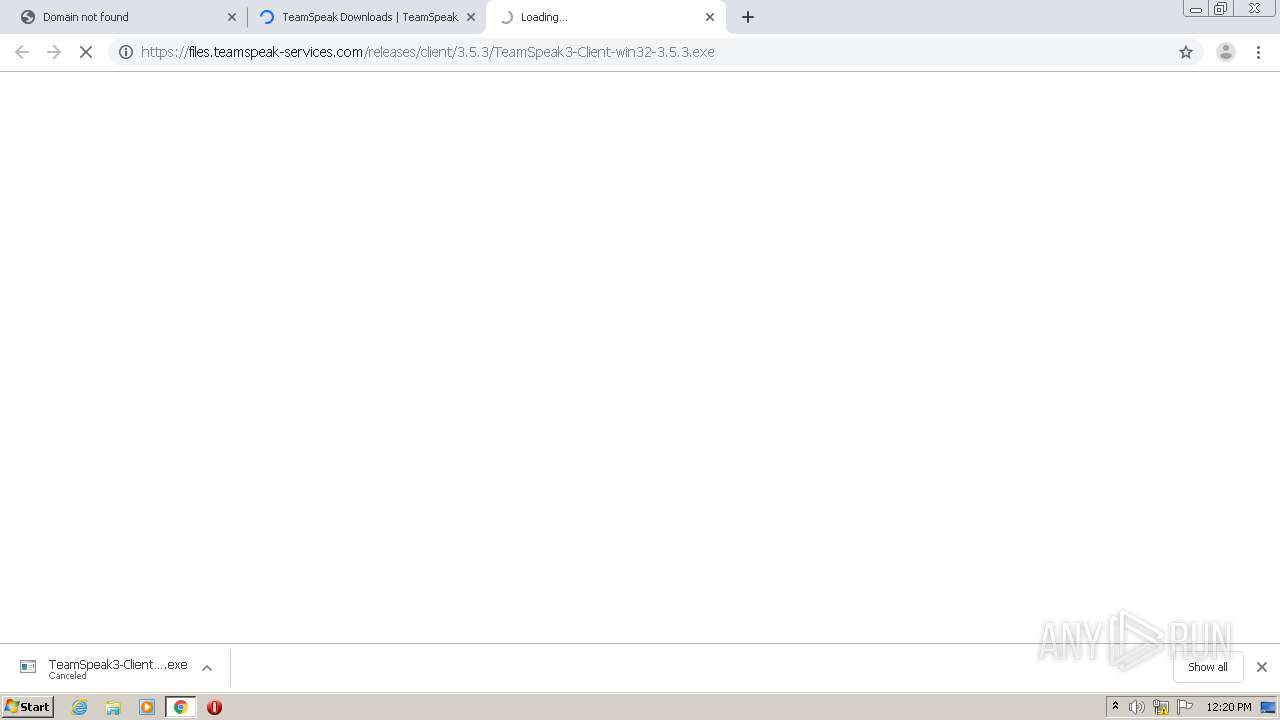
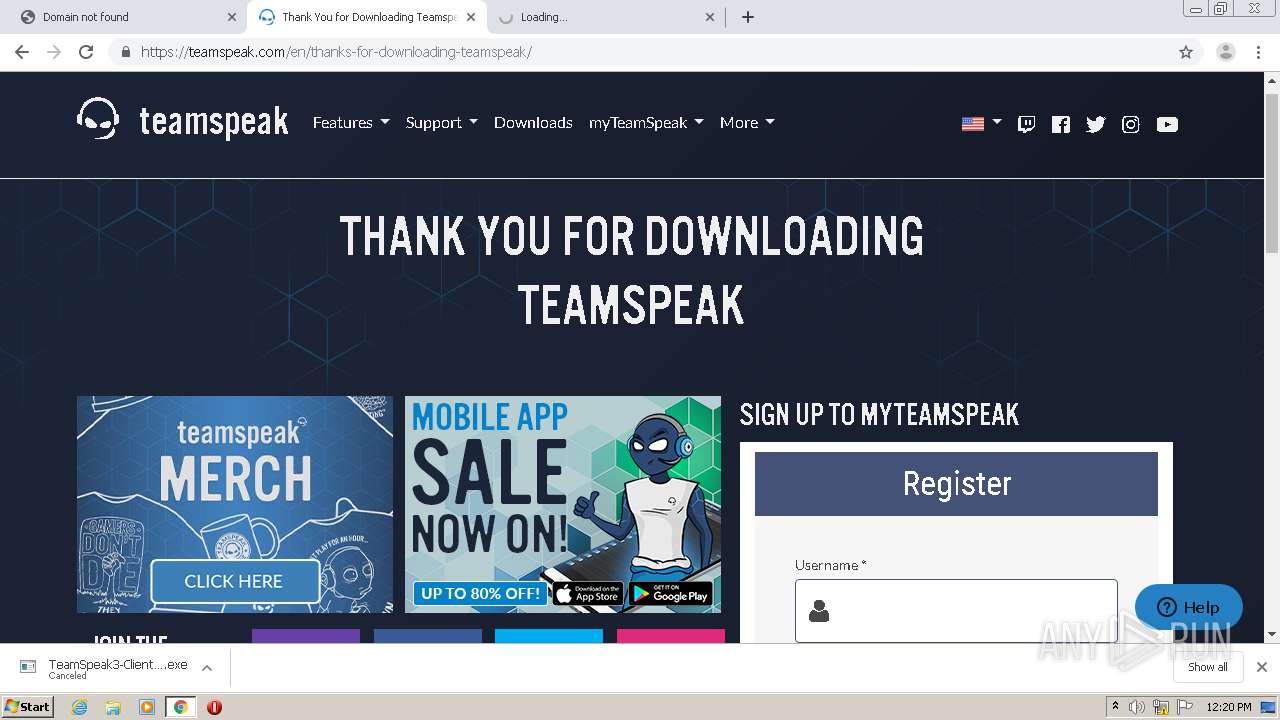
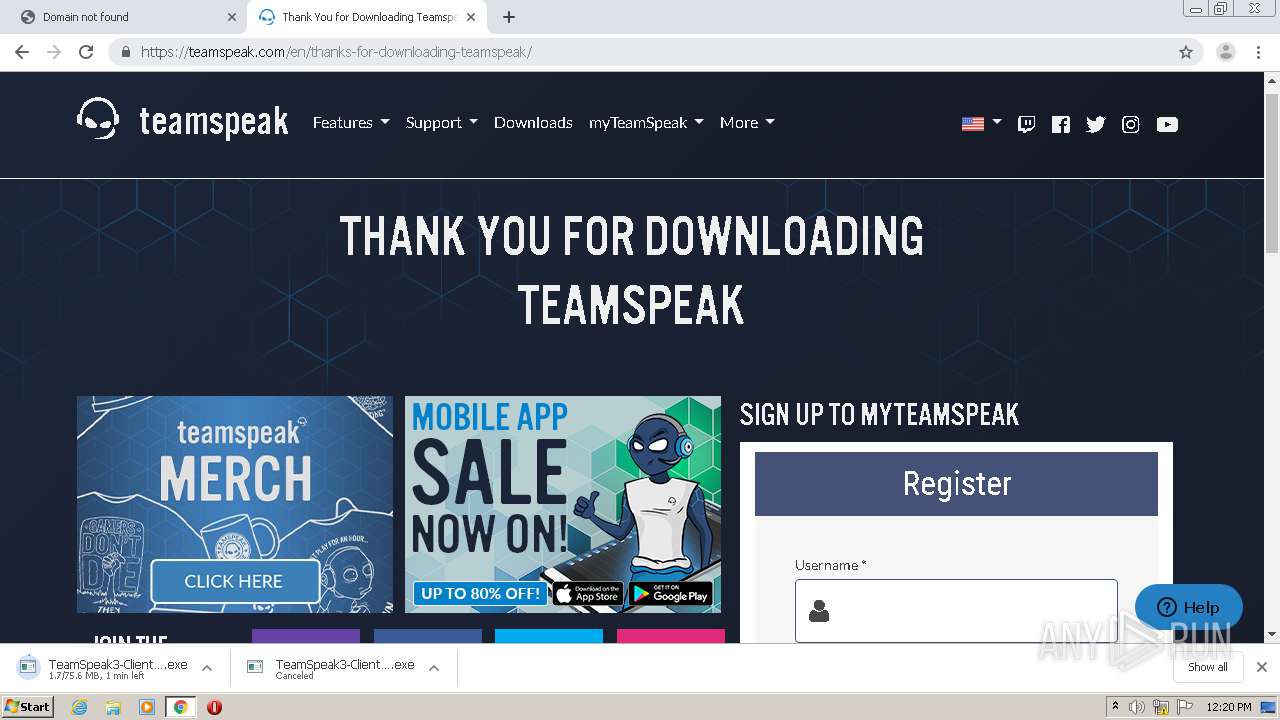
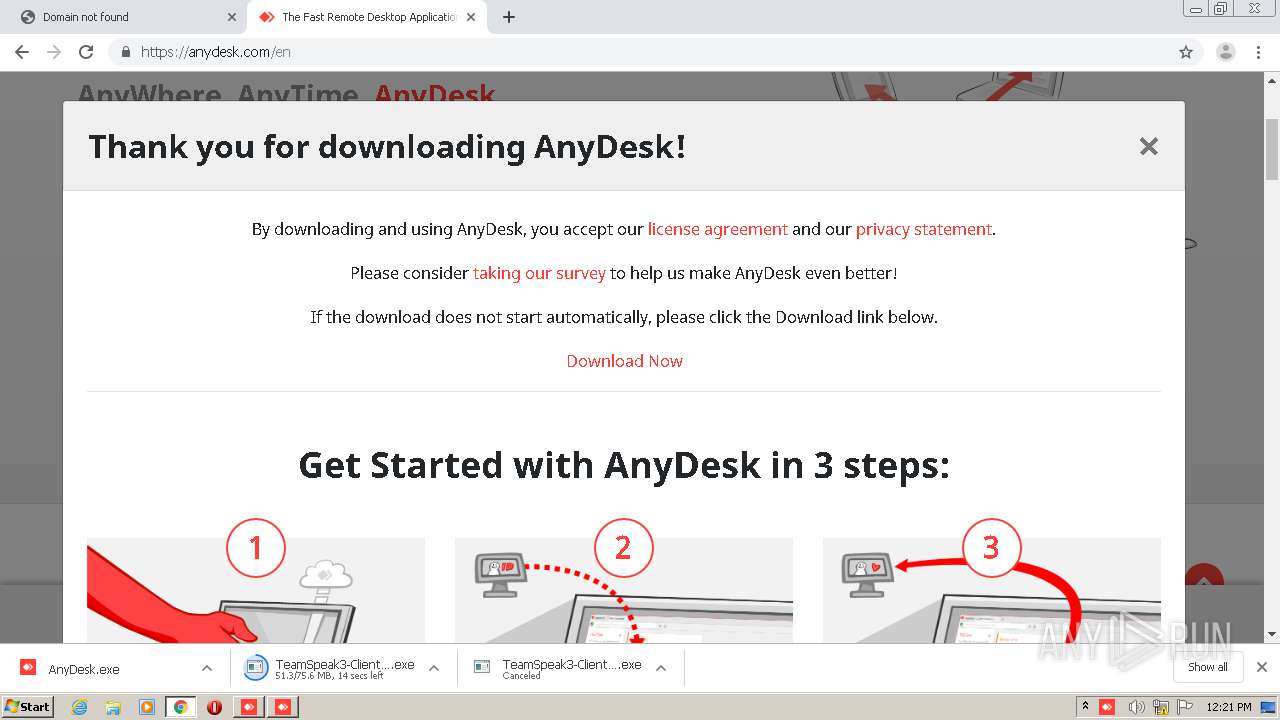
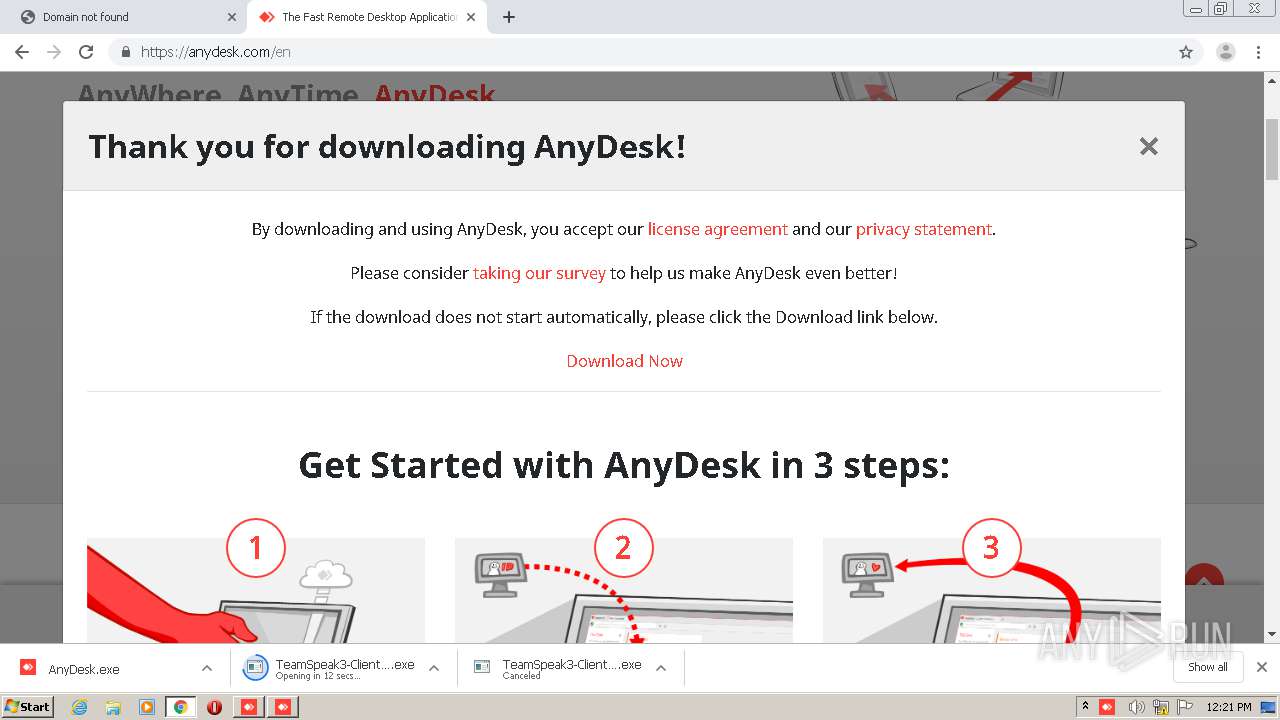
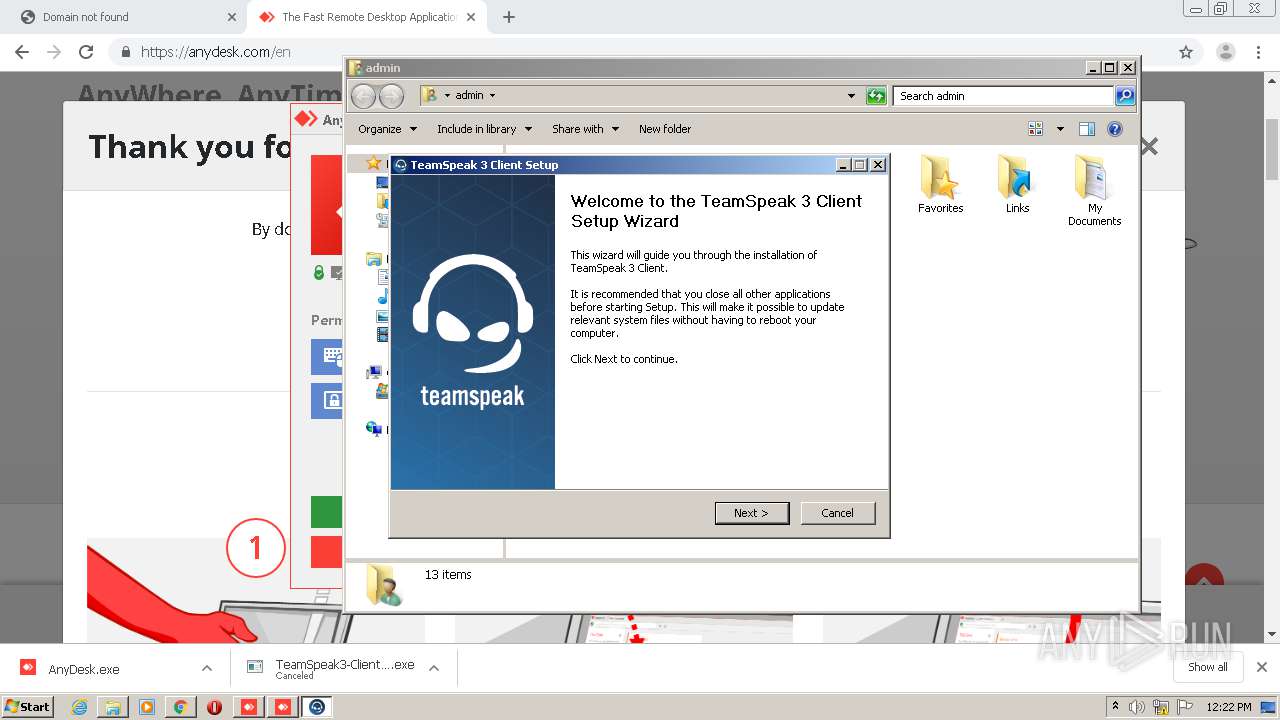
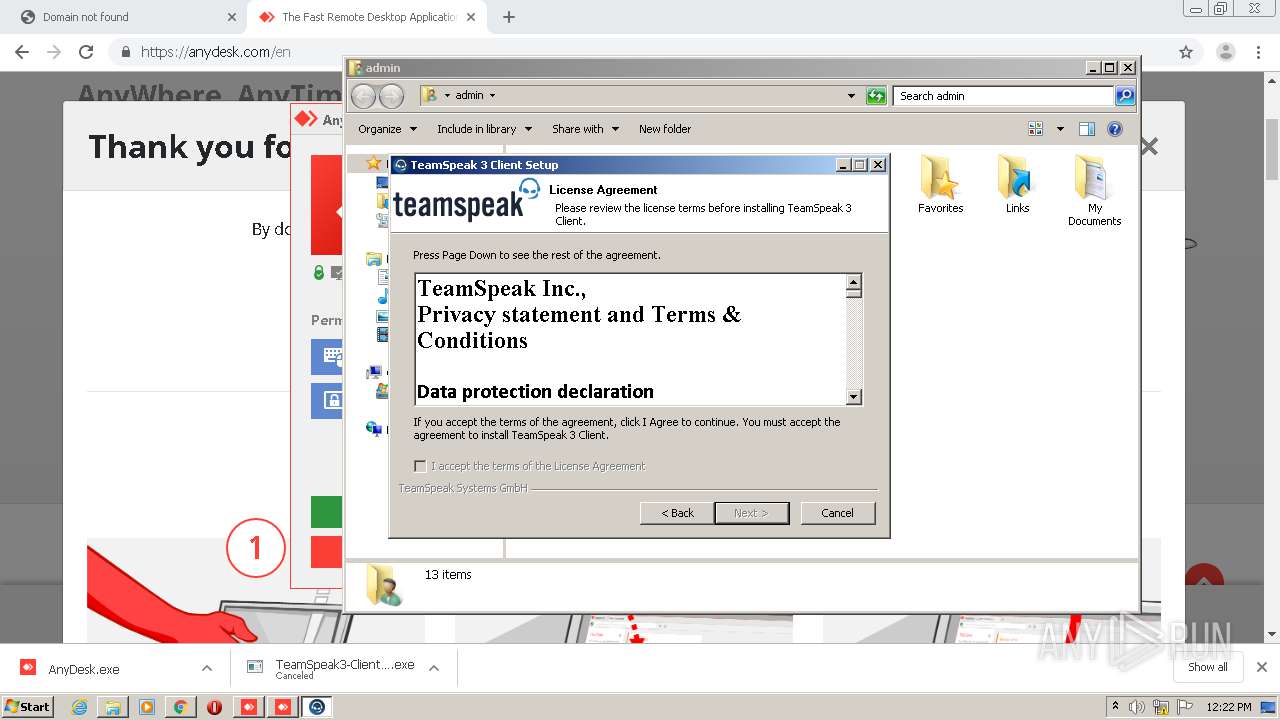
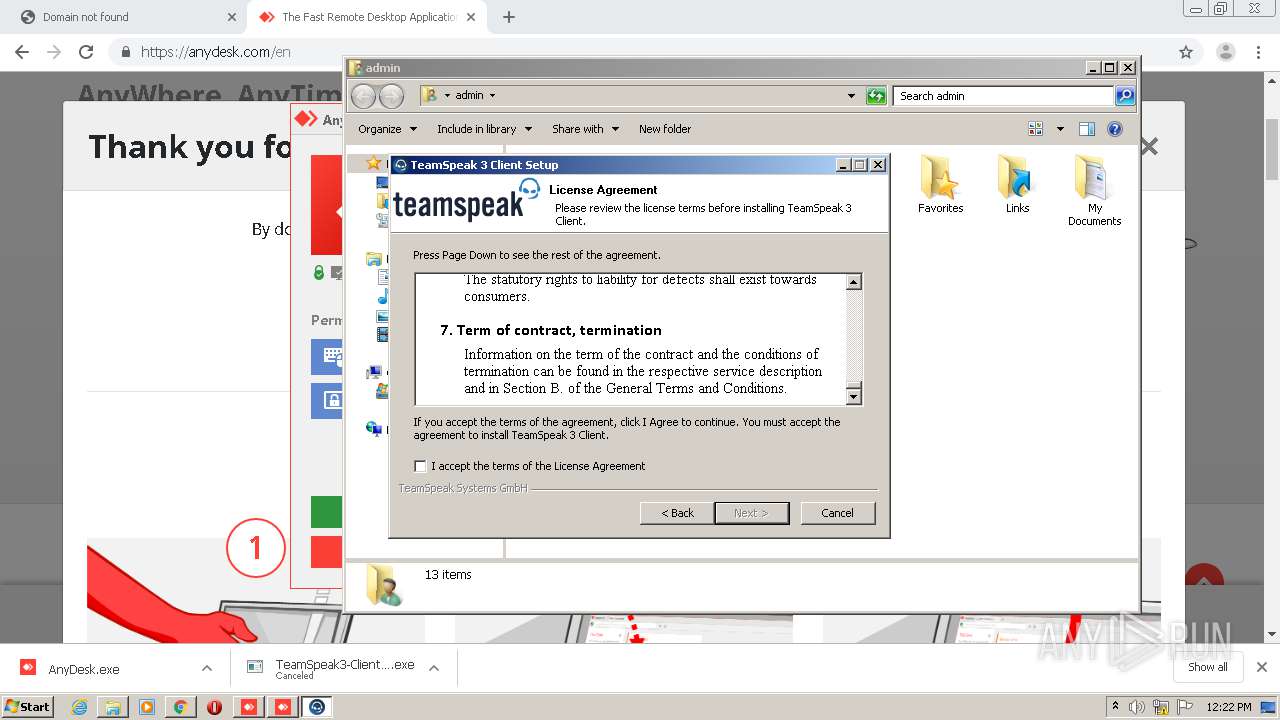
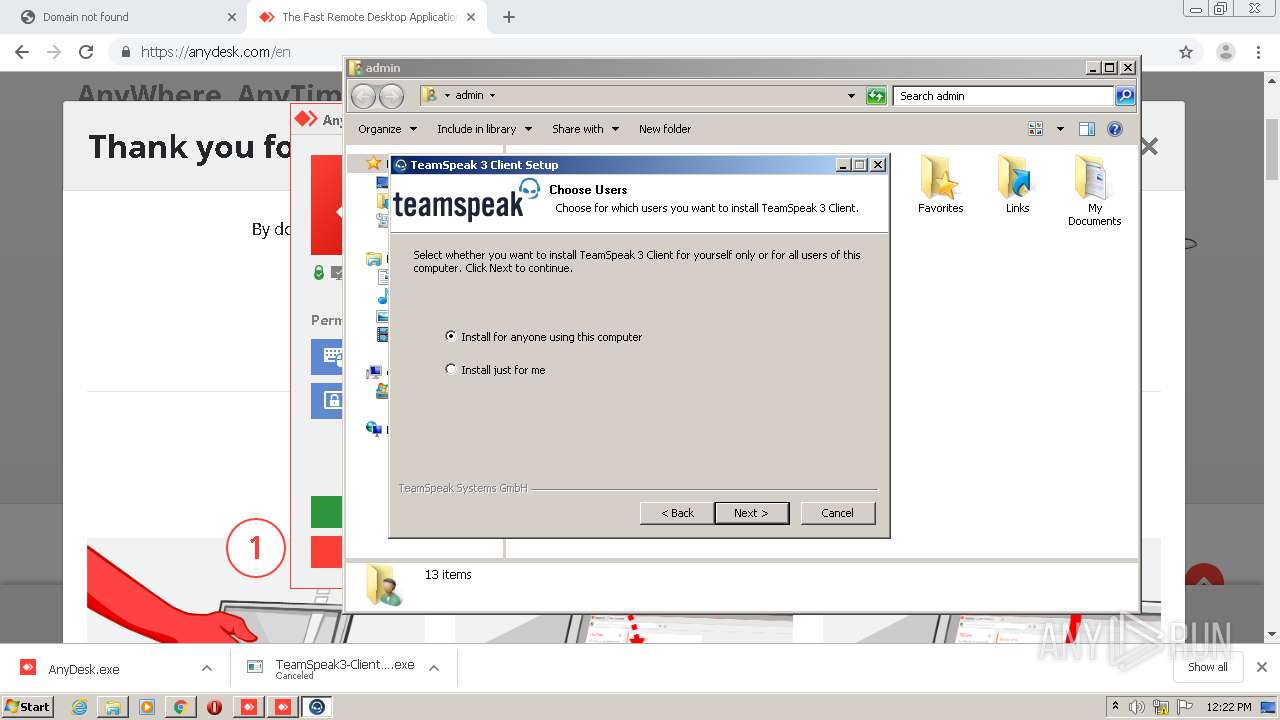
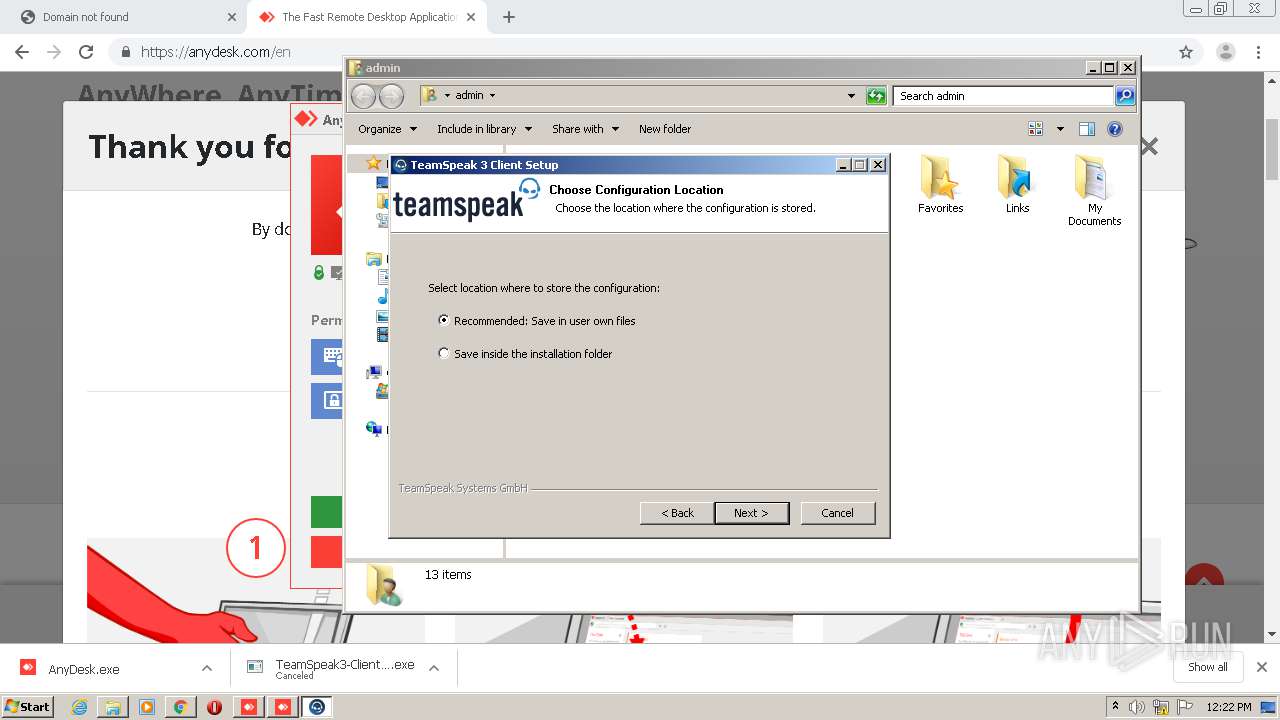
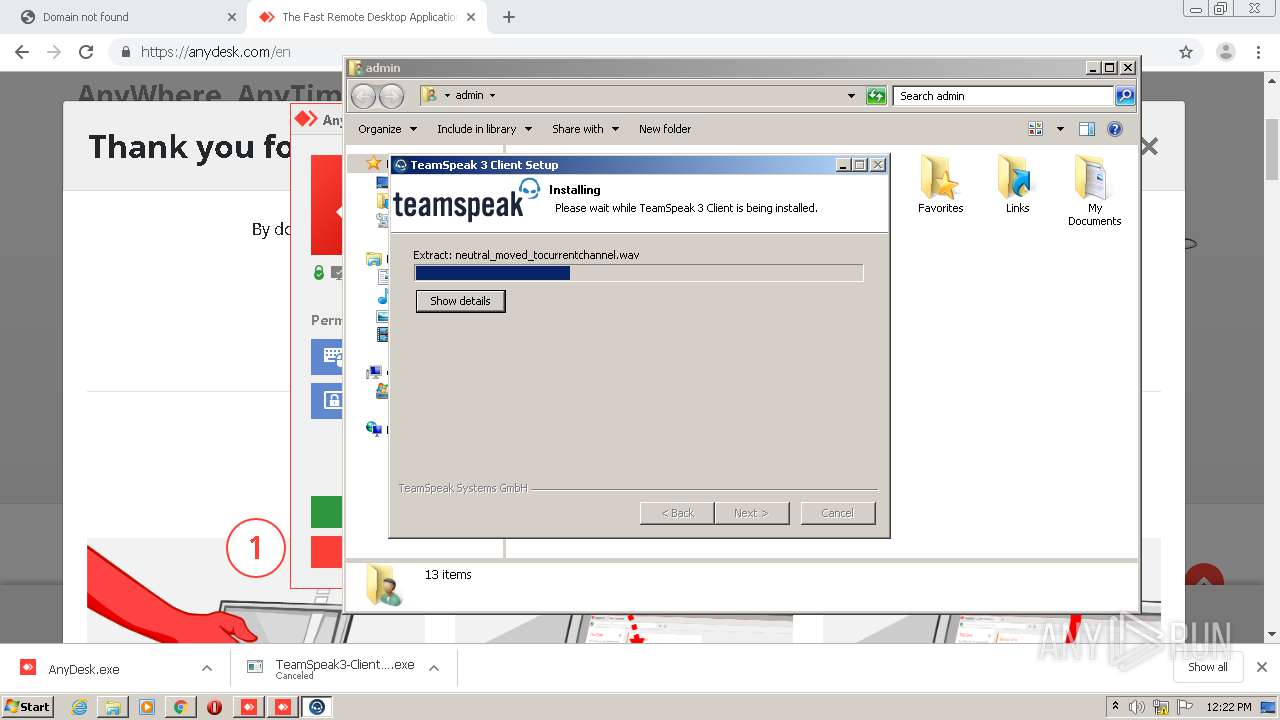
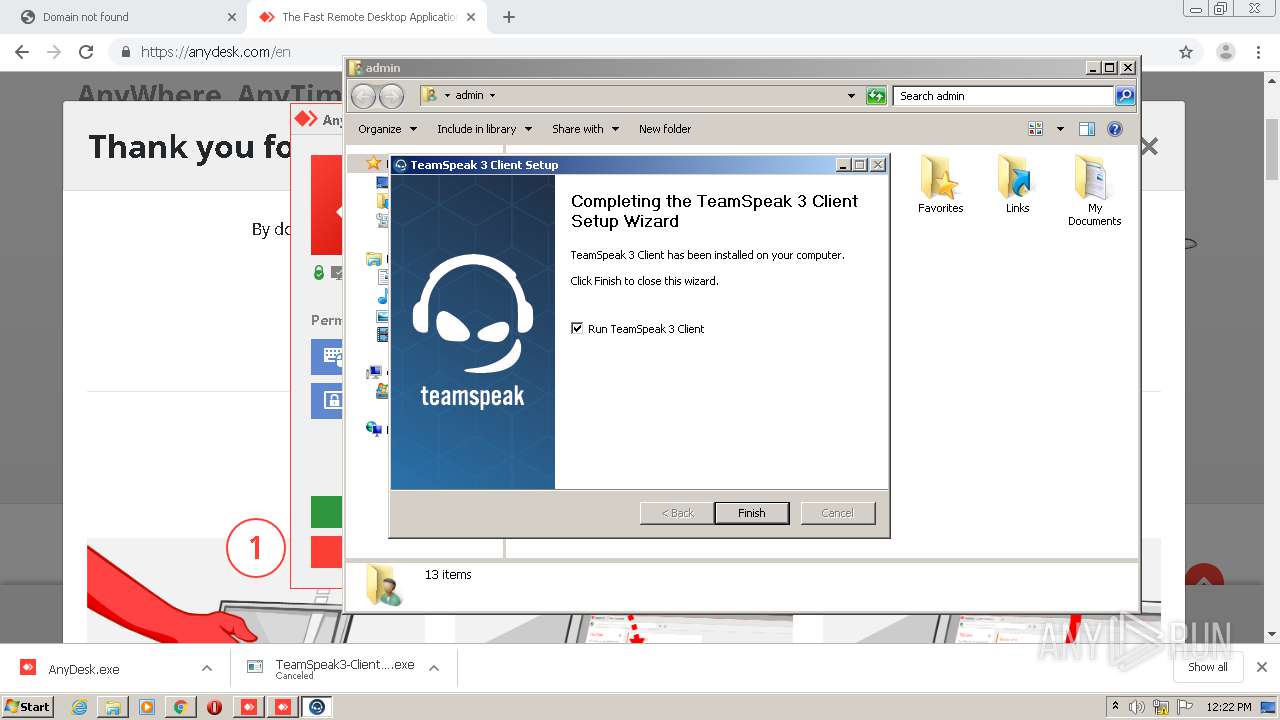
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 2552)
- AnyDesk.exe (PID: 3988)
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 3592)
- vcredist_x86.exe (PID: 280)
- vcredist_x86.exe (PID: 1836)
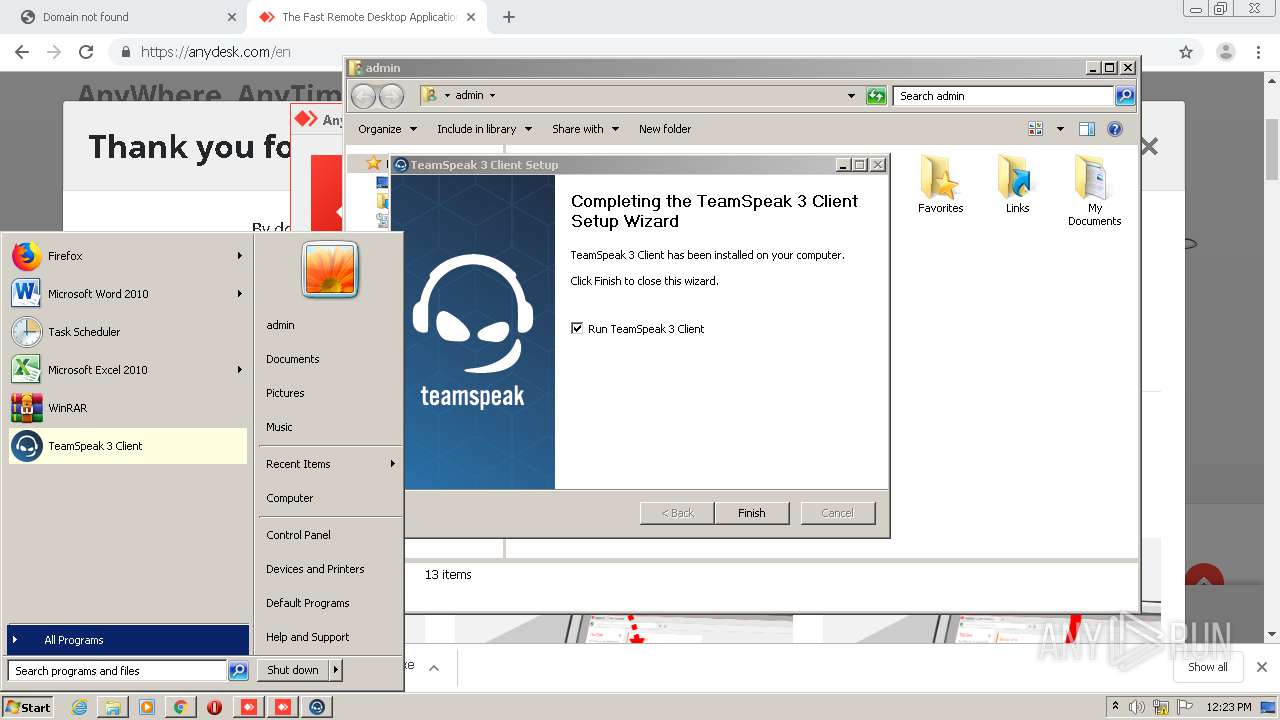
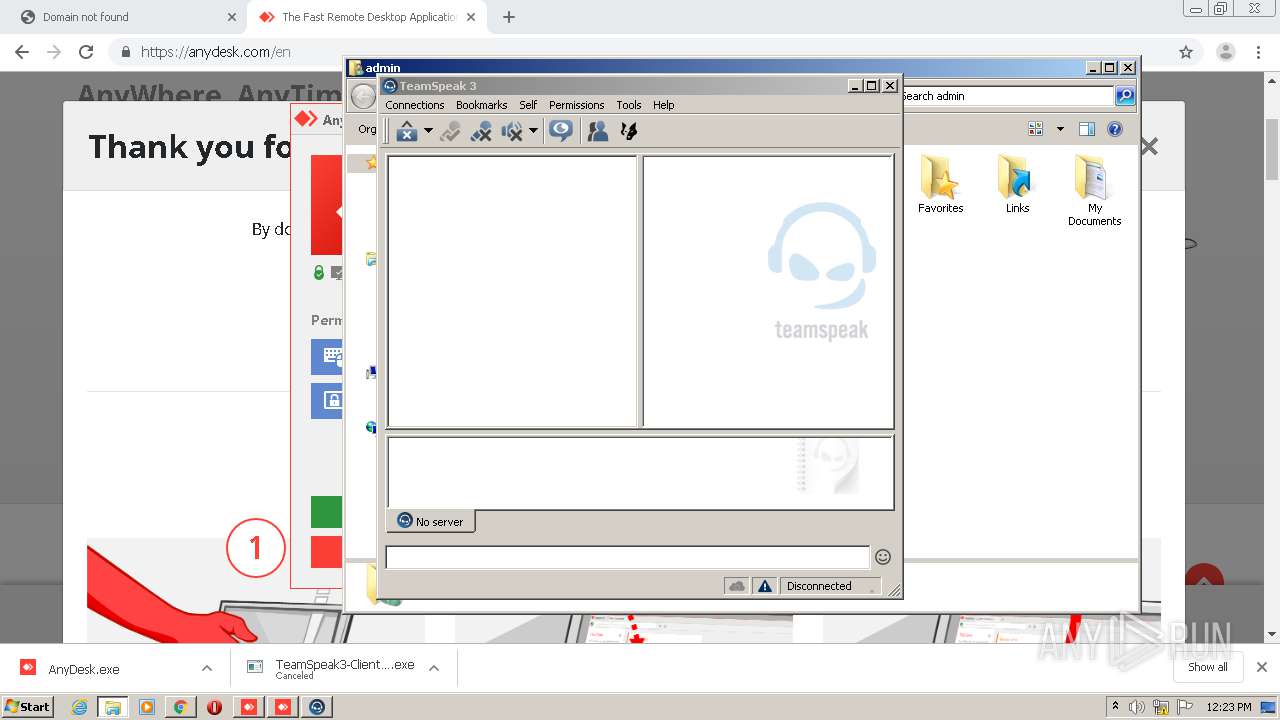
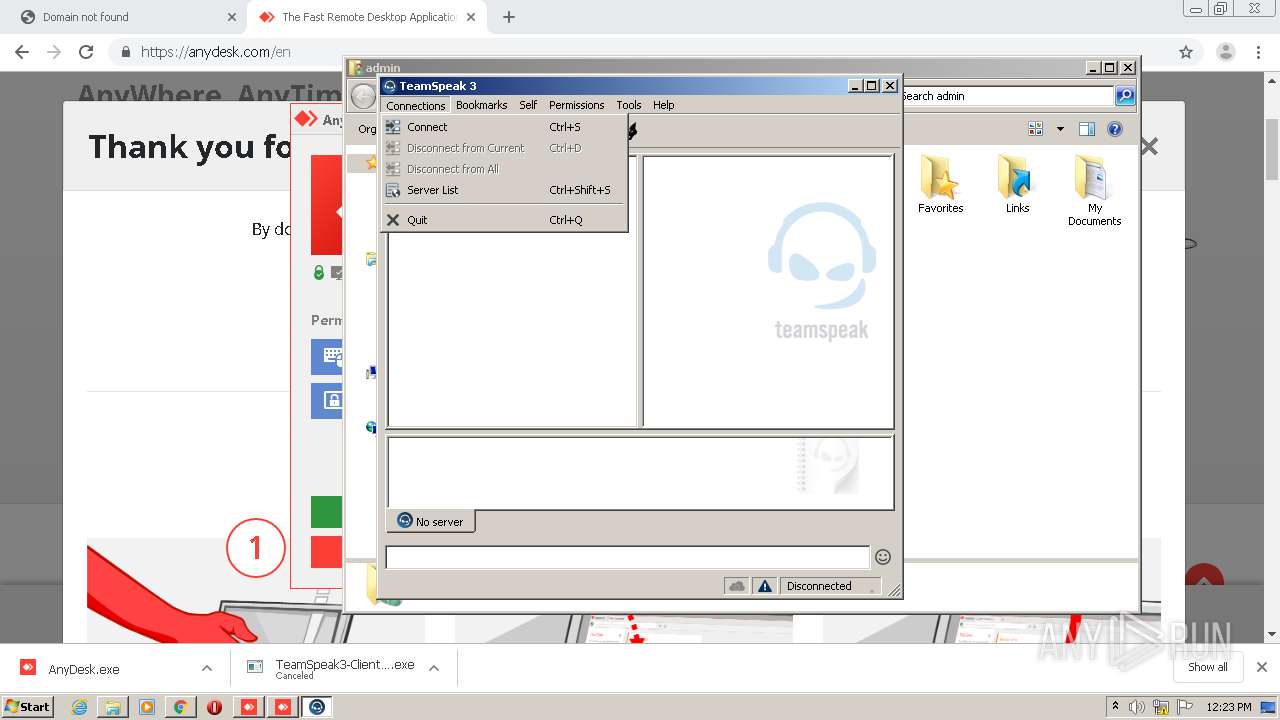
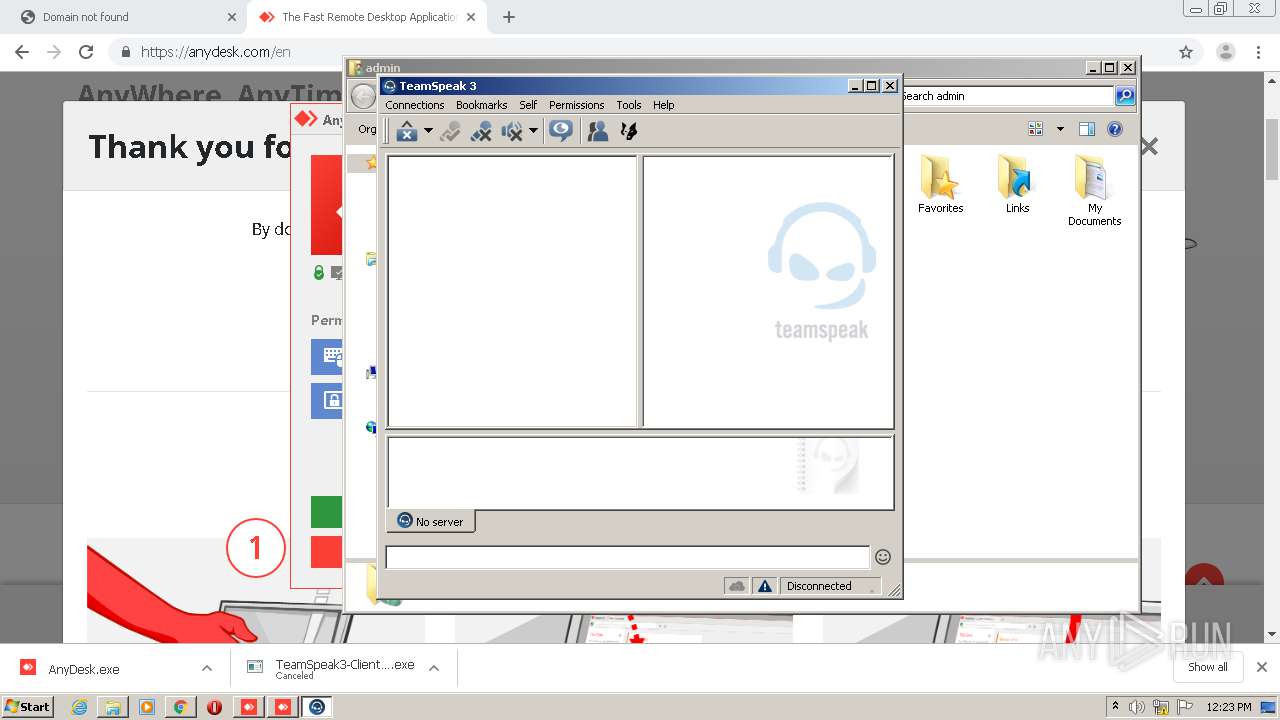
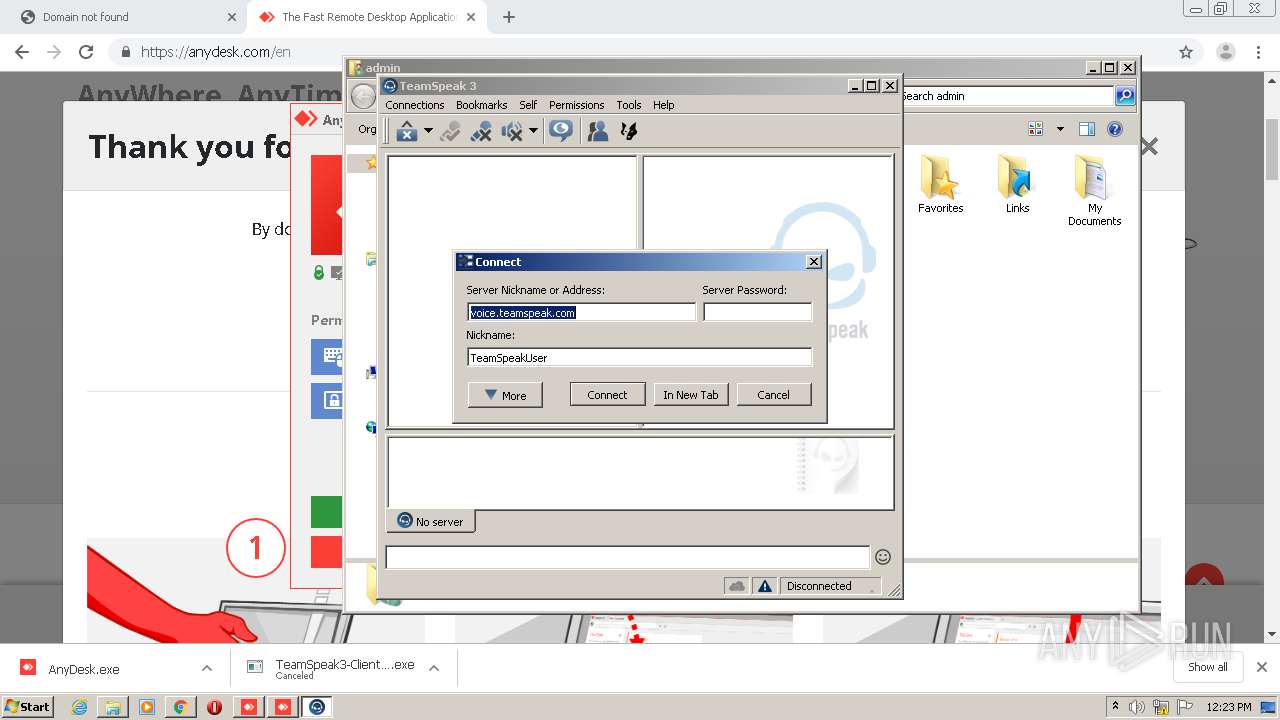
- ts3client_win32.exe (PID: 3616)
- ts3client_win32.exe (PID: 2248)
- package_inst.exe (PID: 620)
- package_inst.exe (PID: 1076)
- package_inst.exe (PID: 3196)
- QtWebEngineProcess.exe (PID: 3952)
- ts3client_win32.exe (PID: 2884)
- ts3client_win32.exe (PID: 2472)
Loads dropped or rewritten executable
- AnyDesk.exe (PID: 4060)
- AnyDesk.exe (PID: 2736)
- SearchProtocolHost.exe (PID: 3956)
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 3592)
- ts3client_win32.exe (PID: 3616)
- package_inst.exe (PID: 620)
- vcredist_x86.exe (PID: 1836)
- package_inst.exe (PID: 1076)
- package_inst.exe (PID: 3196)
- QtWebEngineProcess.exe (PID: 3952)
- ts3client_win32.exe (PID: 2472)
SUSPICIOUS
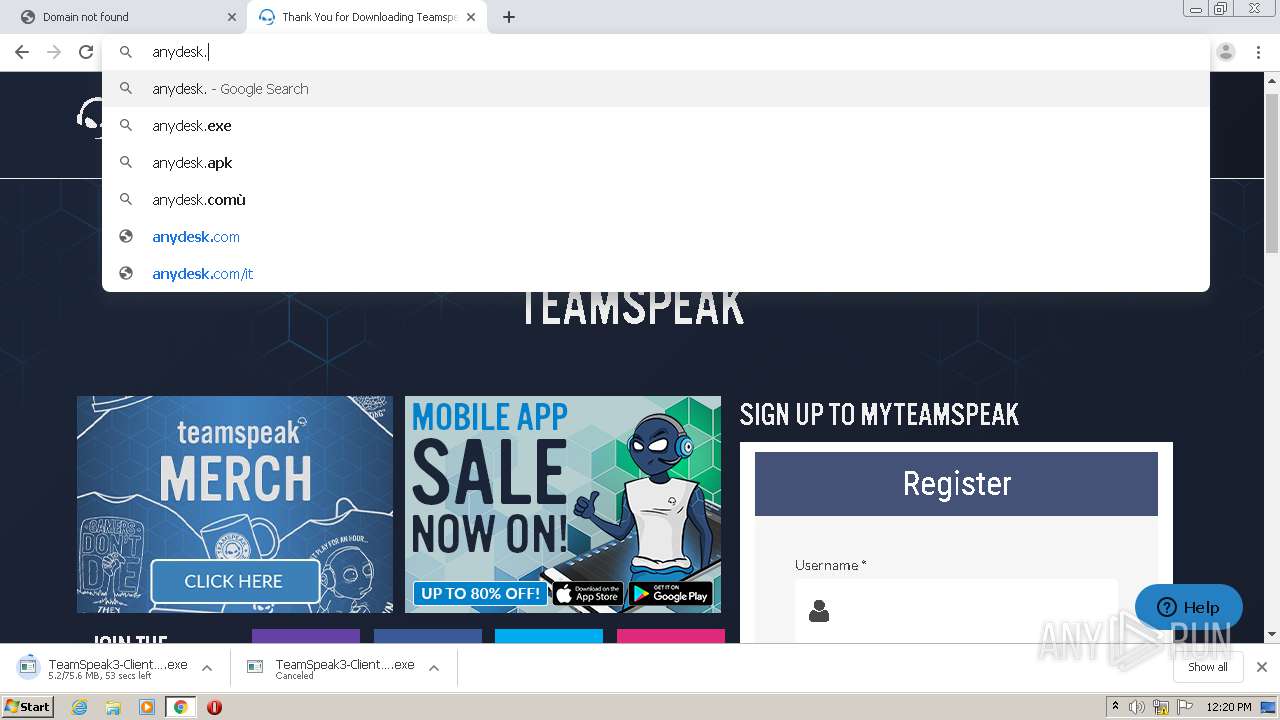
Modifies files in Chrome extension folder
- chrome.exe (PID: 952)
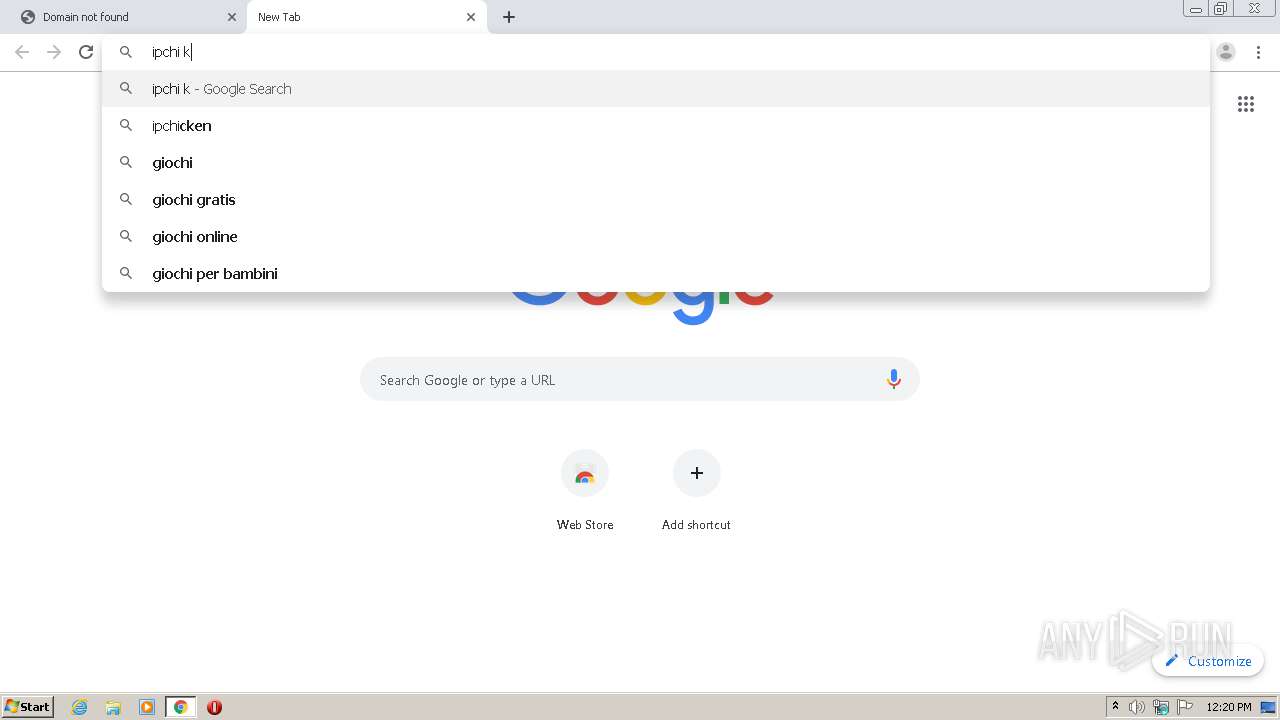
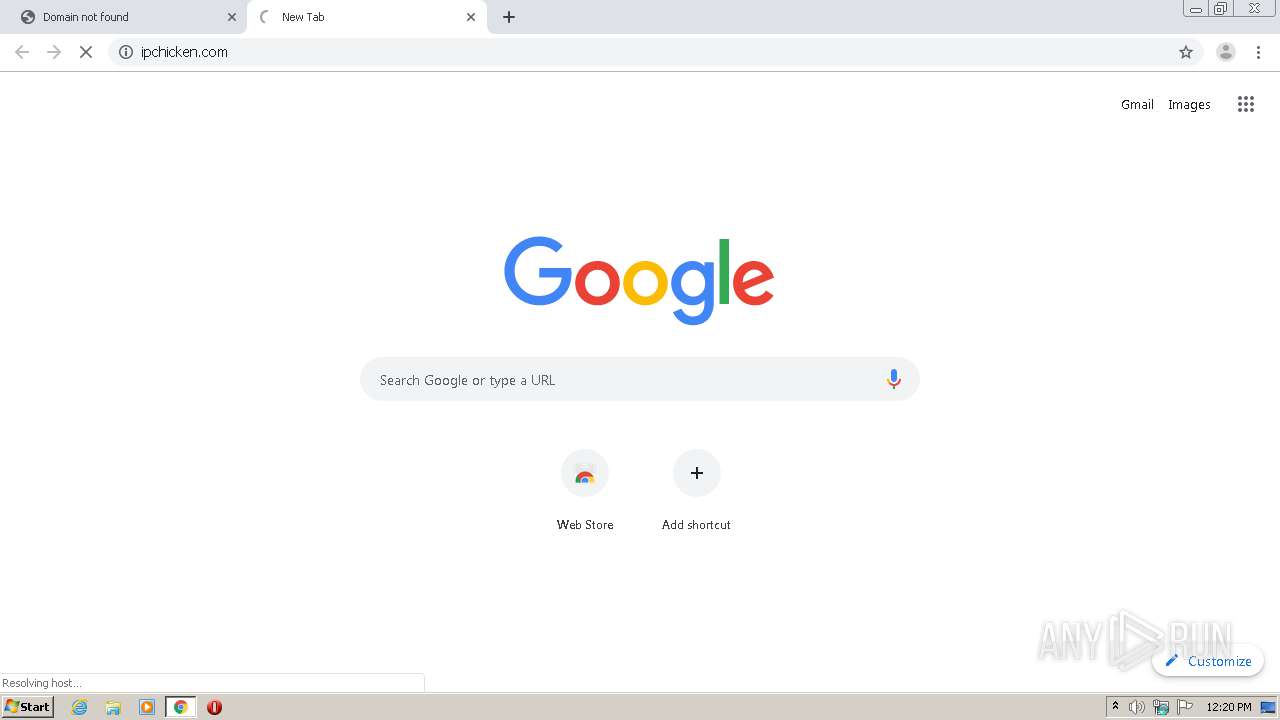
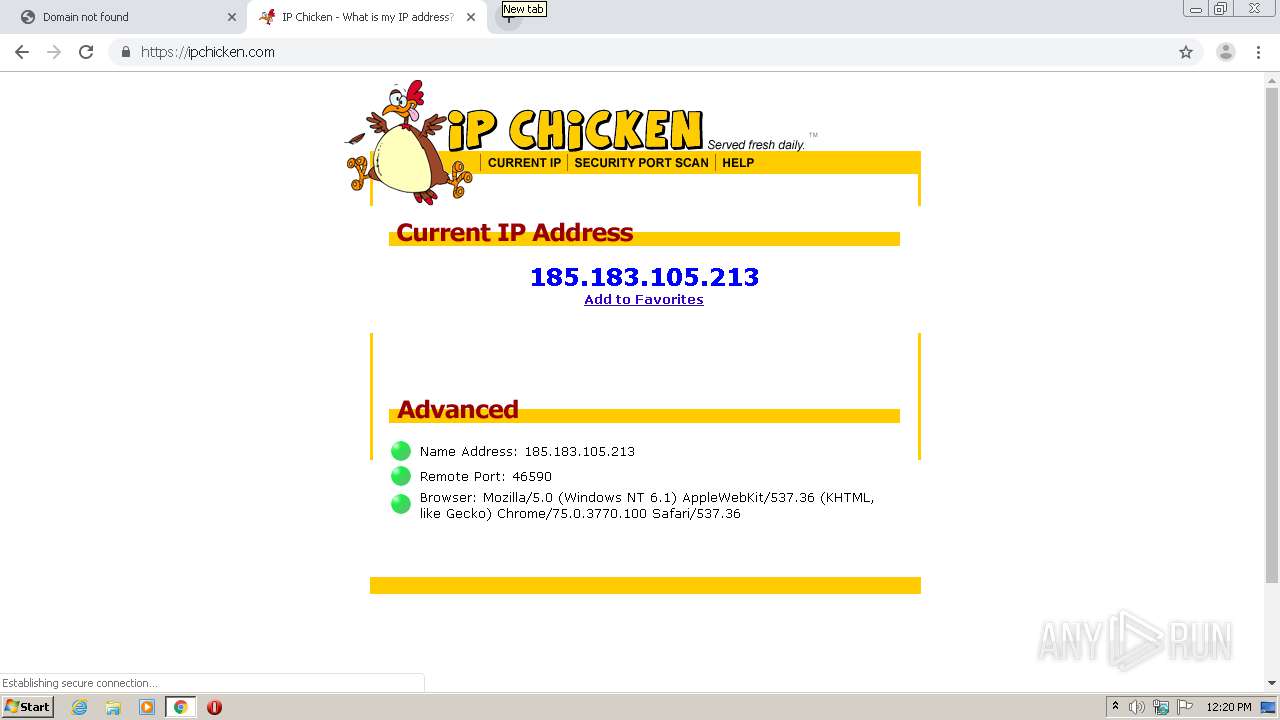
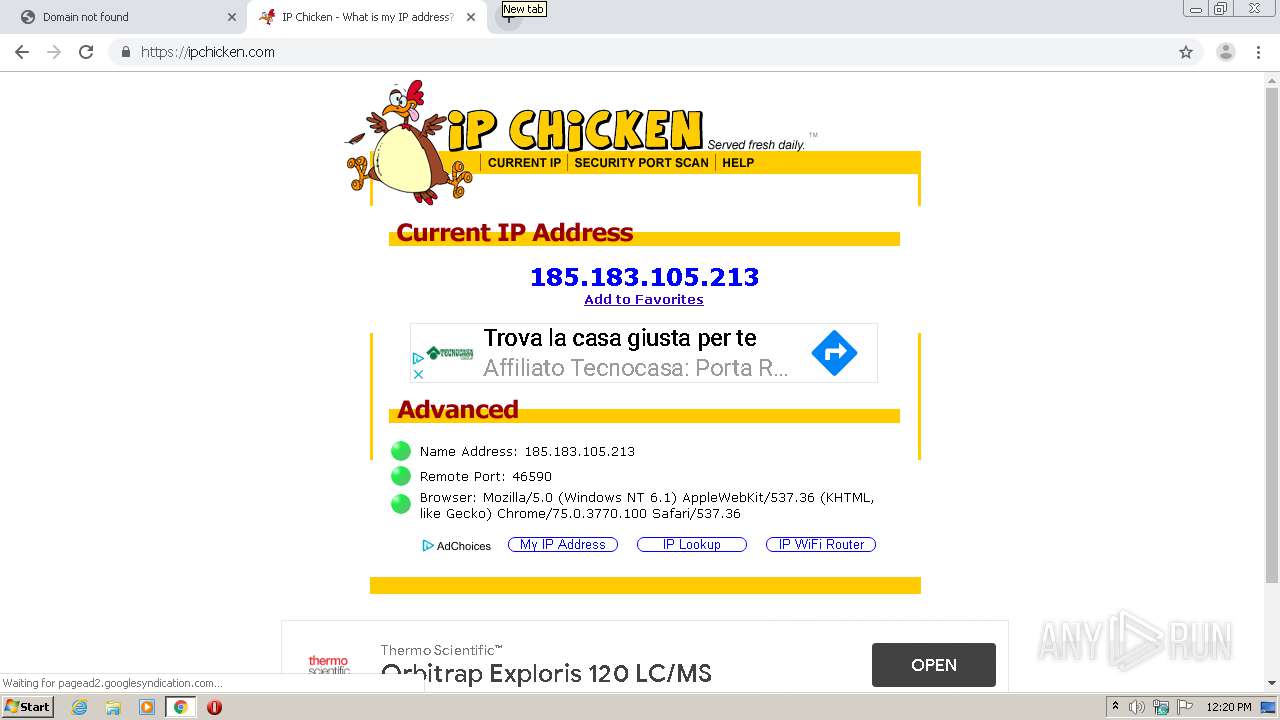
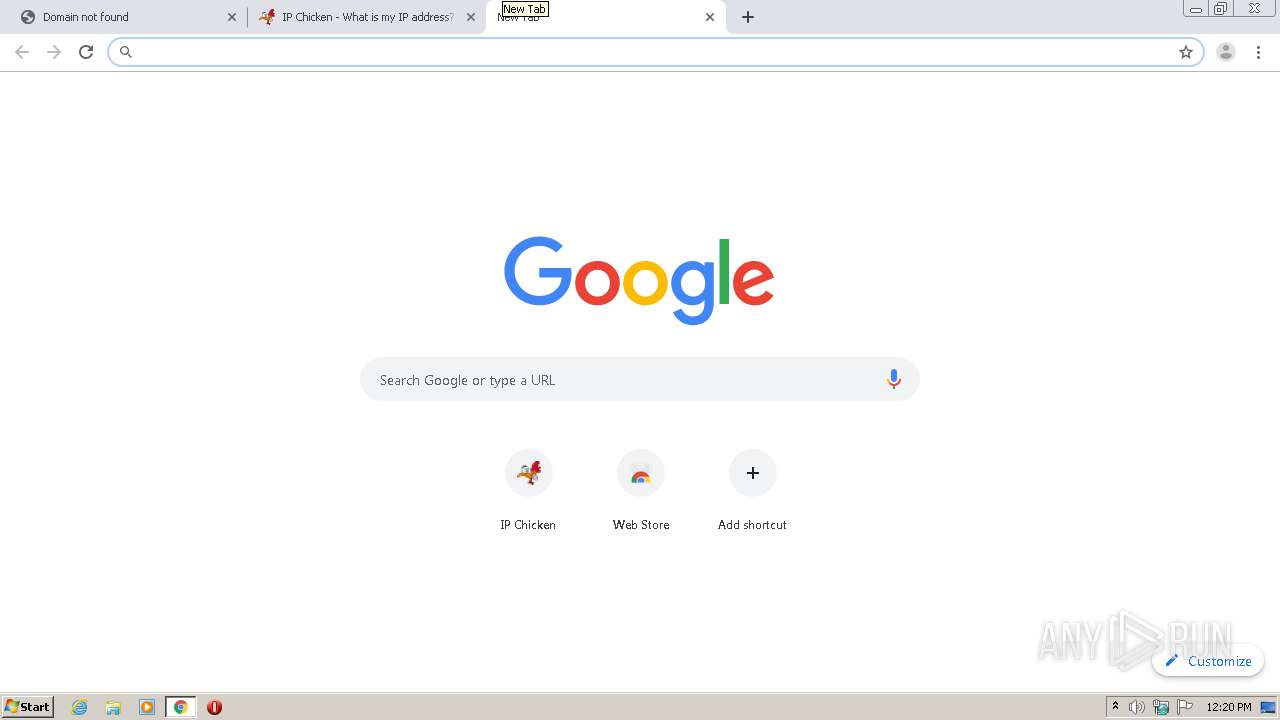
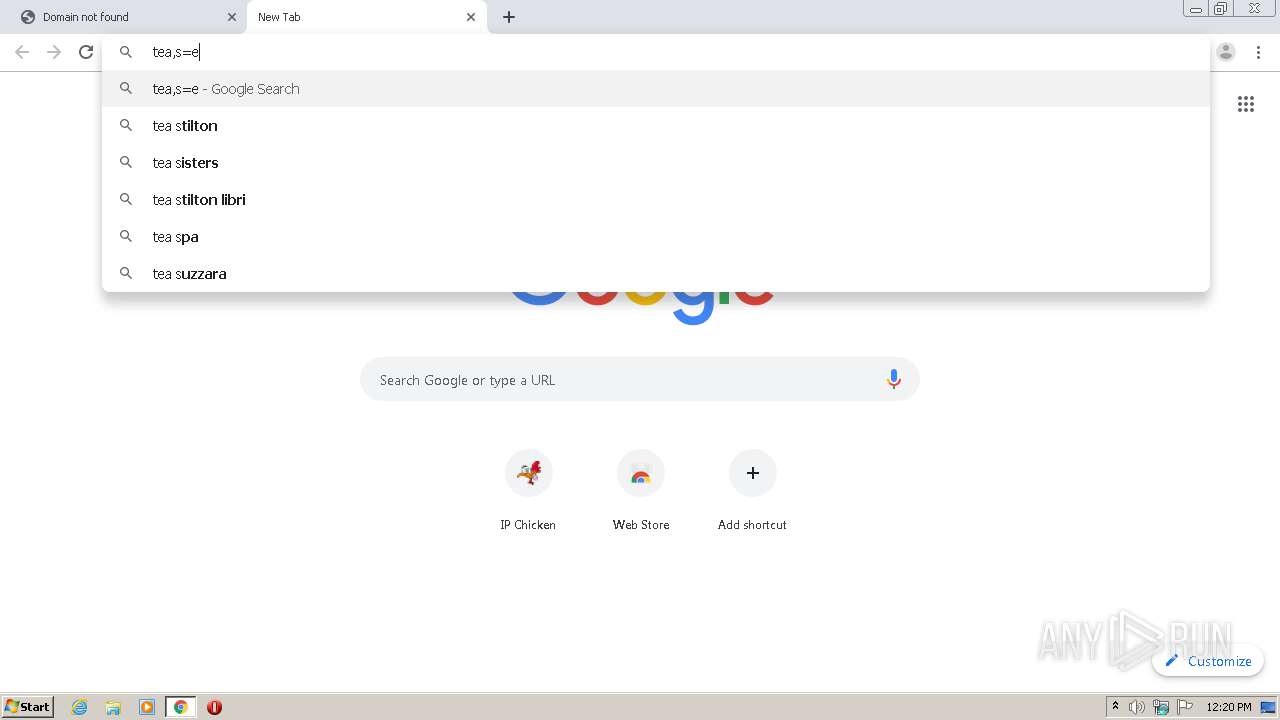
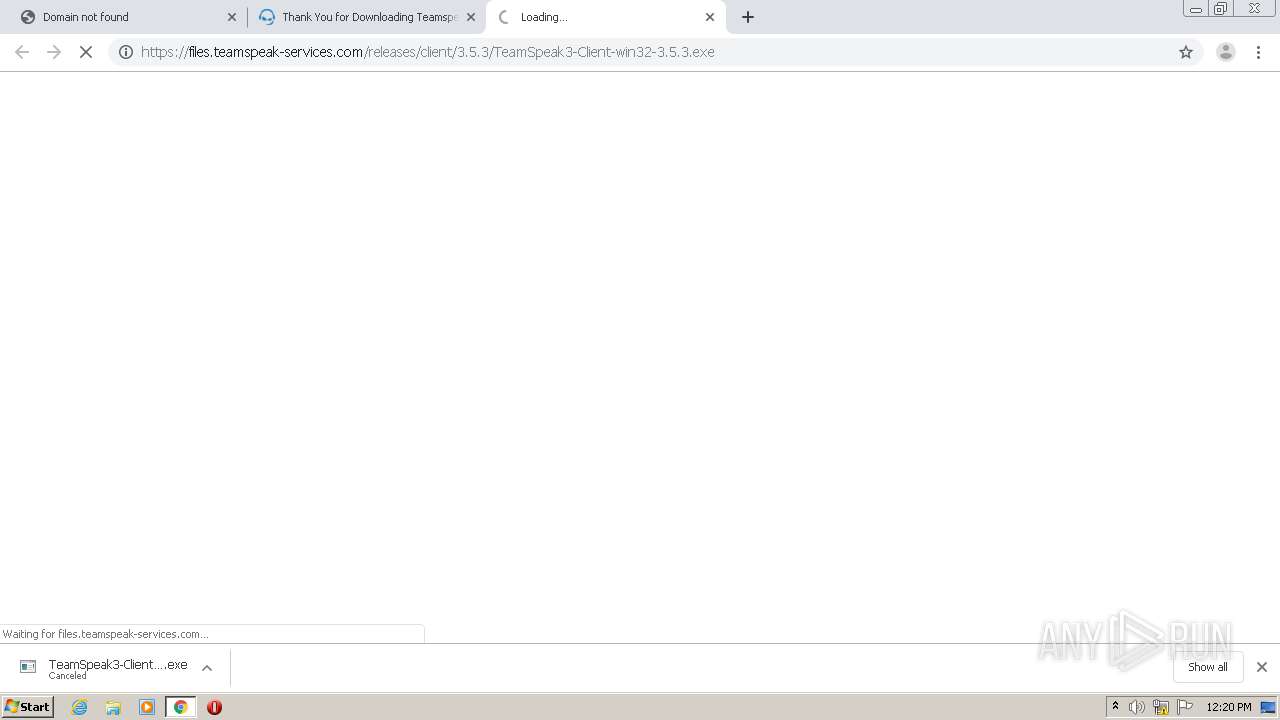
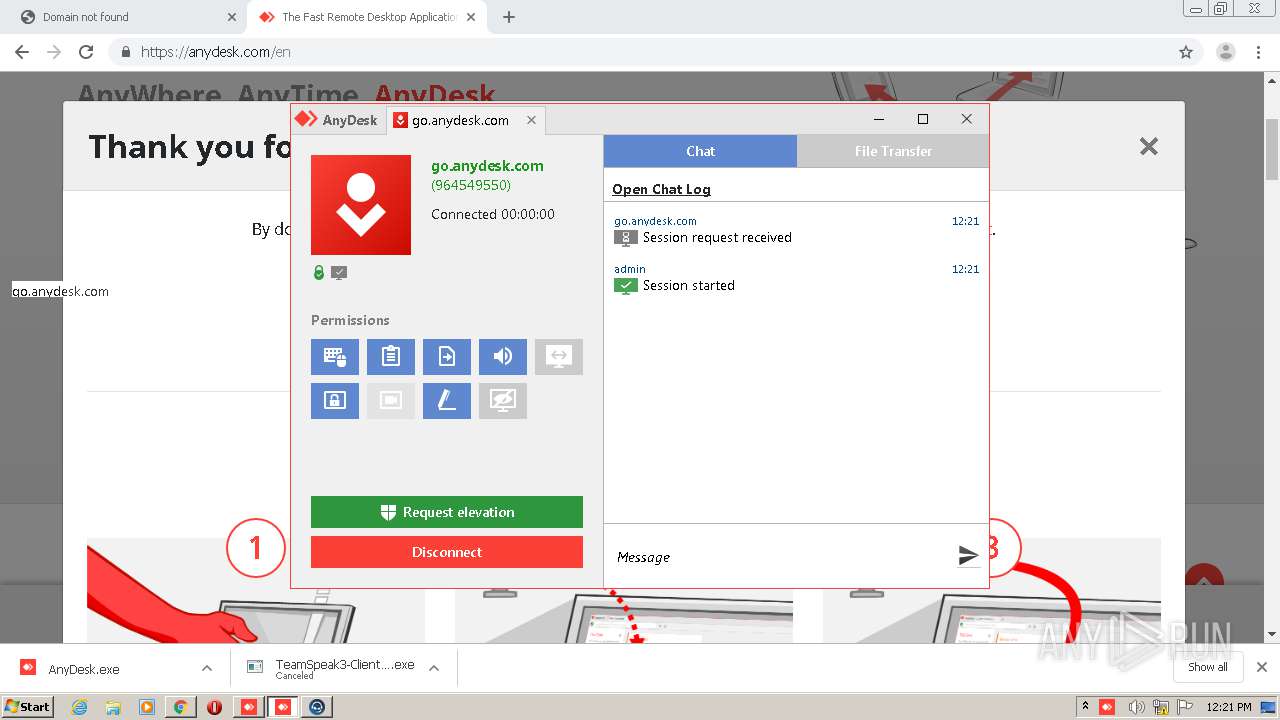
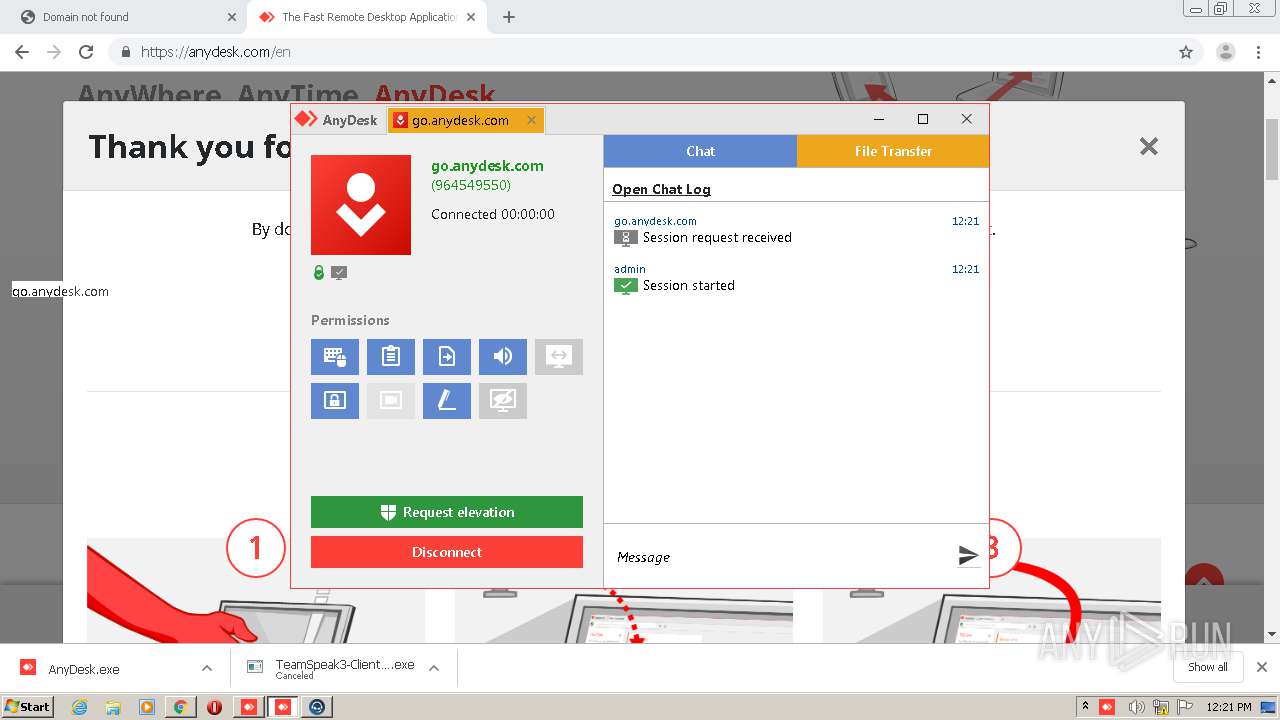
Checks for external IP
- chrome.exe (PID: 3708)
Cleans NTFS data-stream (Zone Identifier)
- AnyDesk.exe (PID: 1088)
Executable content was dropped or overwritten
- chrome.exe (PID: 3708)
- chrome.exe (PID: 952)
- AnyDesk.exe (PID: 4060)
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 3592)
- AnyDesk.exe (PID: 2736)
- vcredist_x86.exe (PID: 1836)
- package_inst.exe (PID: 620)
- package_inst.exe (PID: 3196)
- package_inst.exe (PID: 1076)
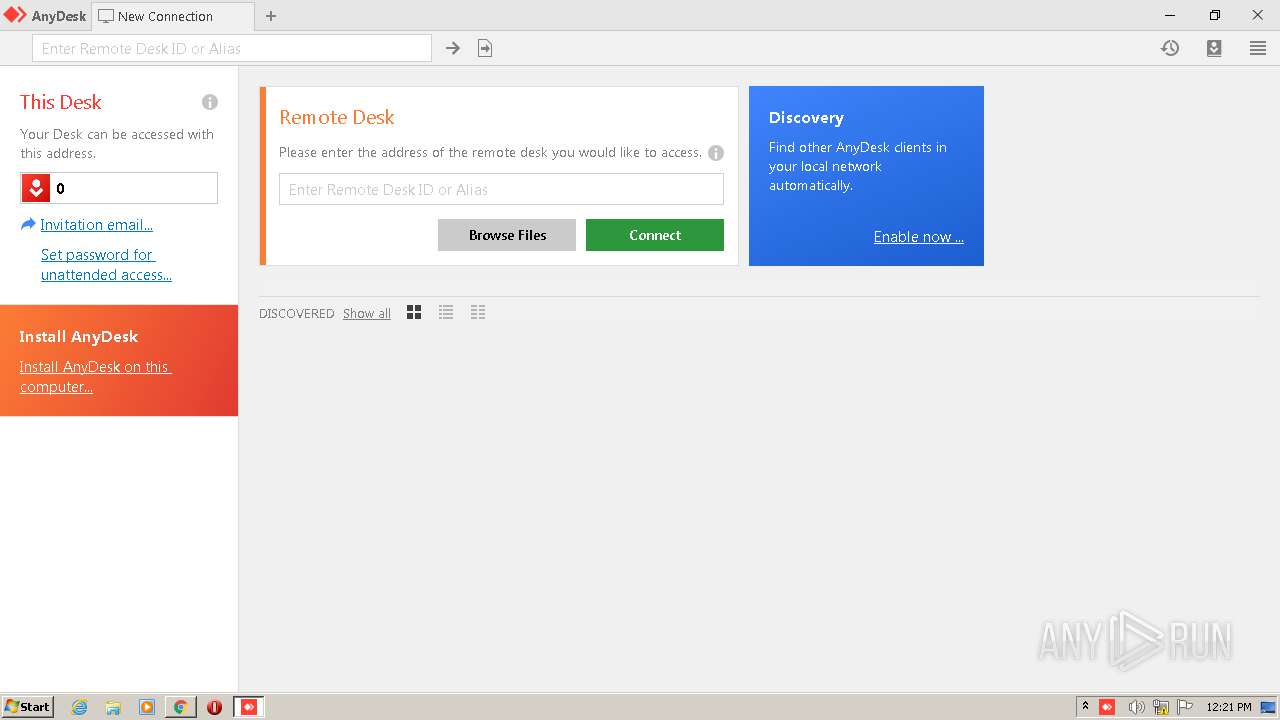
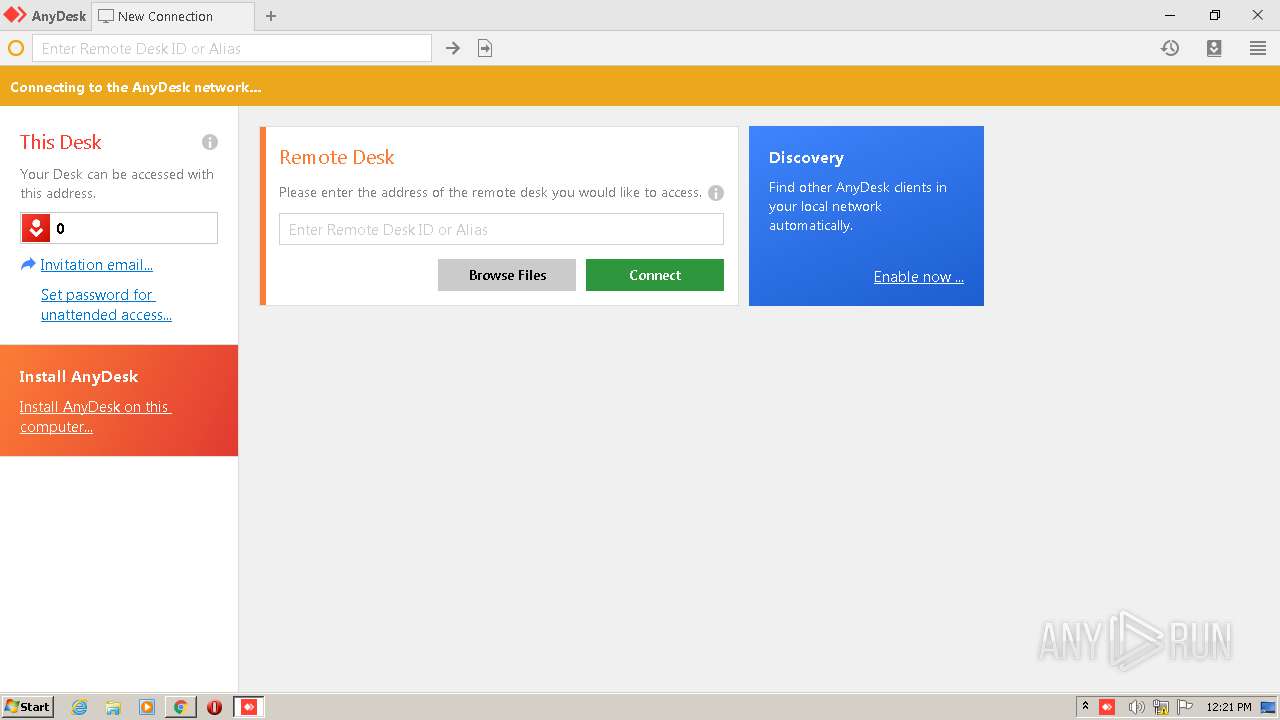
Application launched itself
- AnyDesk.exe (PID: 1088)
- AnyDesk.exe (PID: 4060)
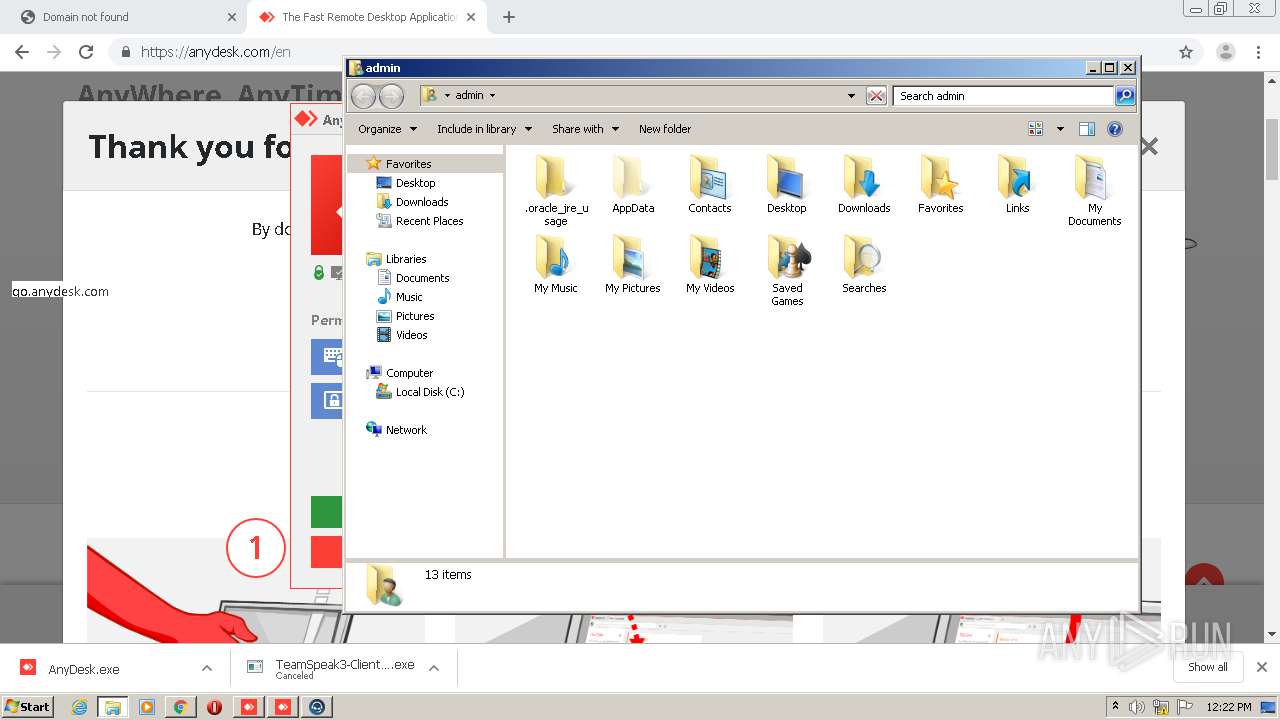
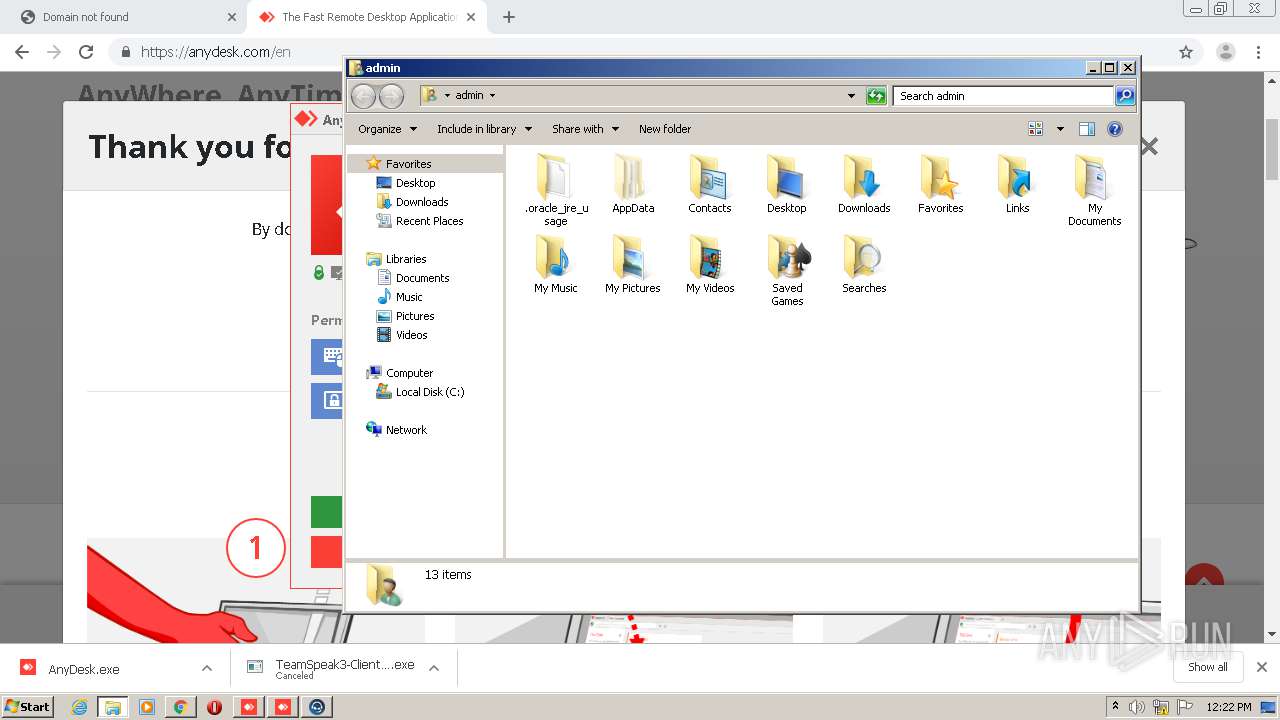
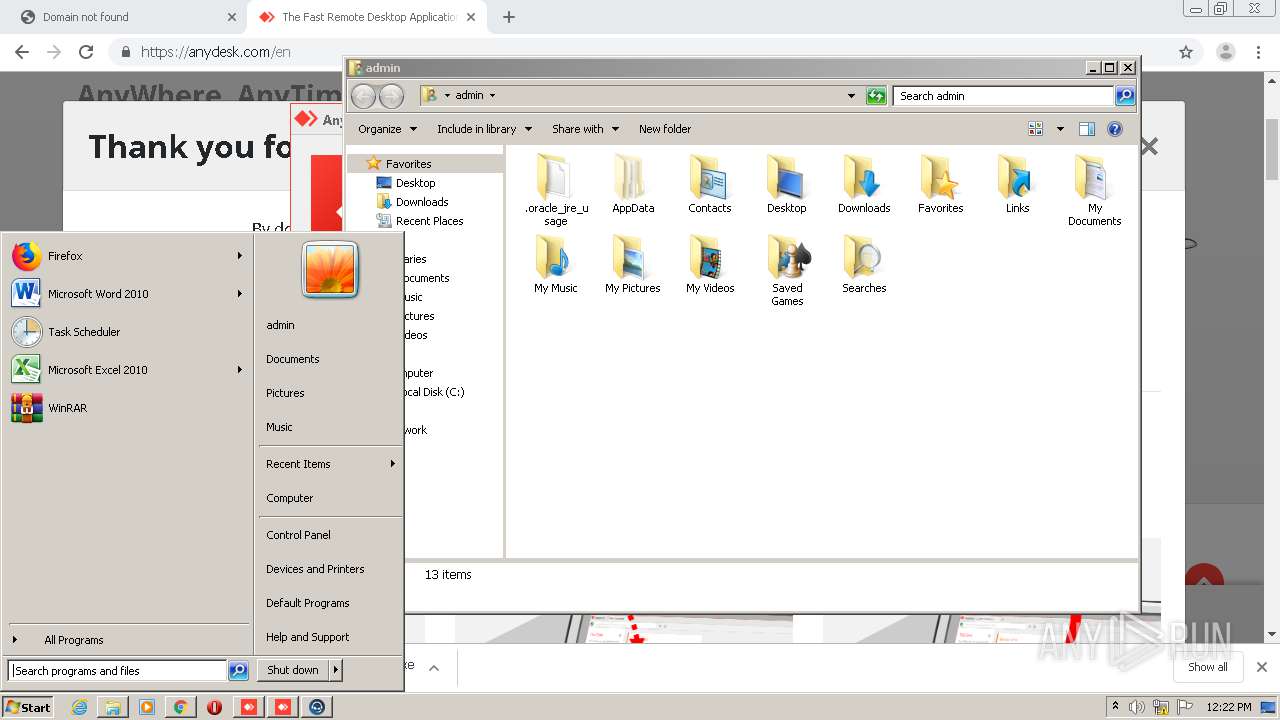
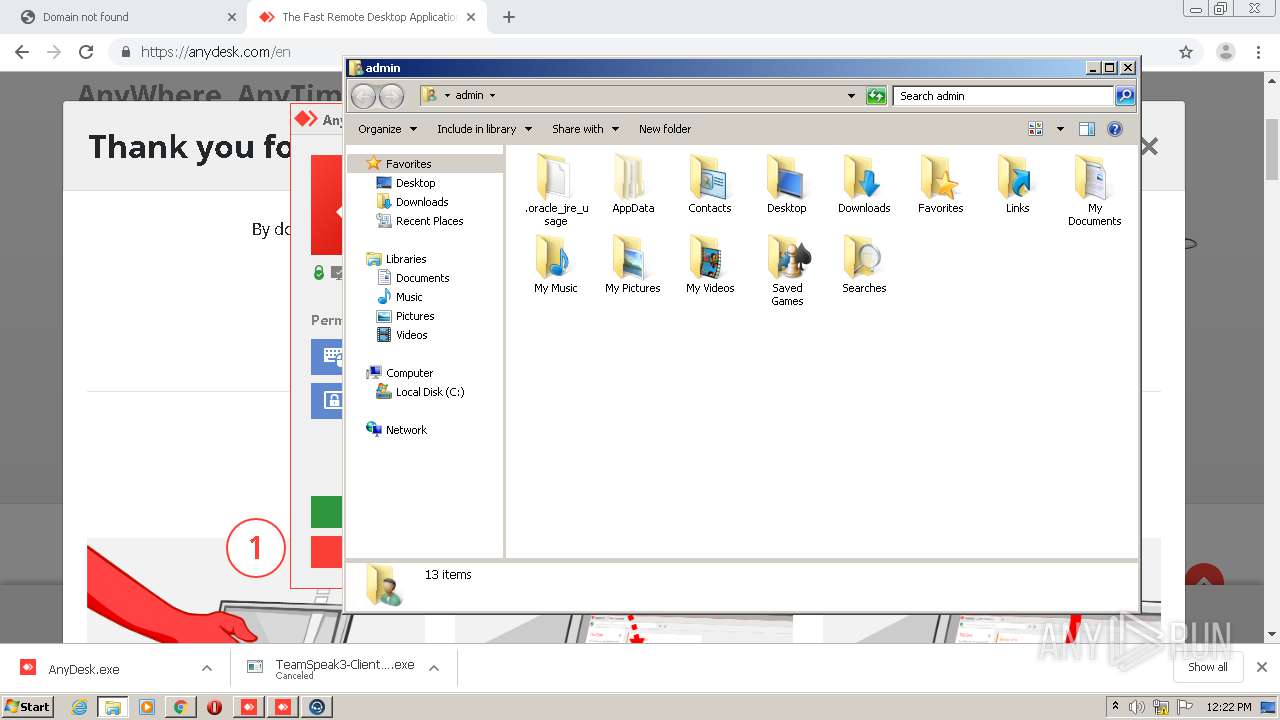
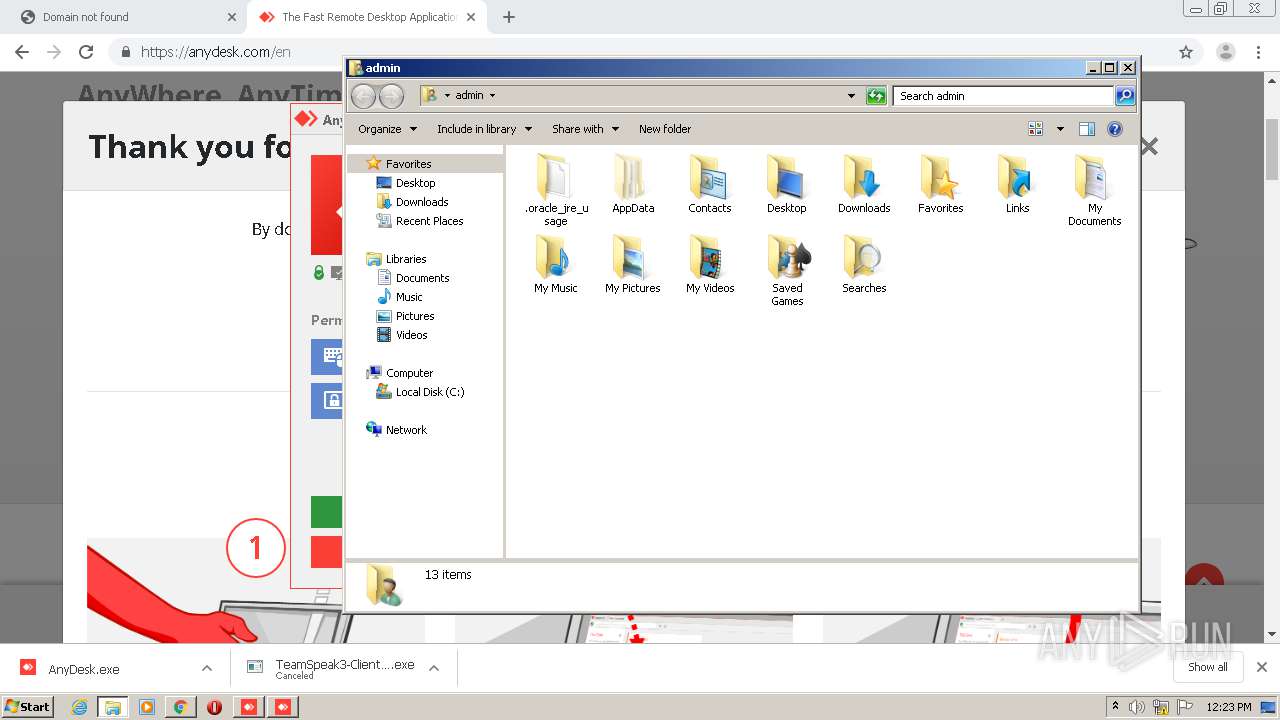
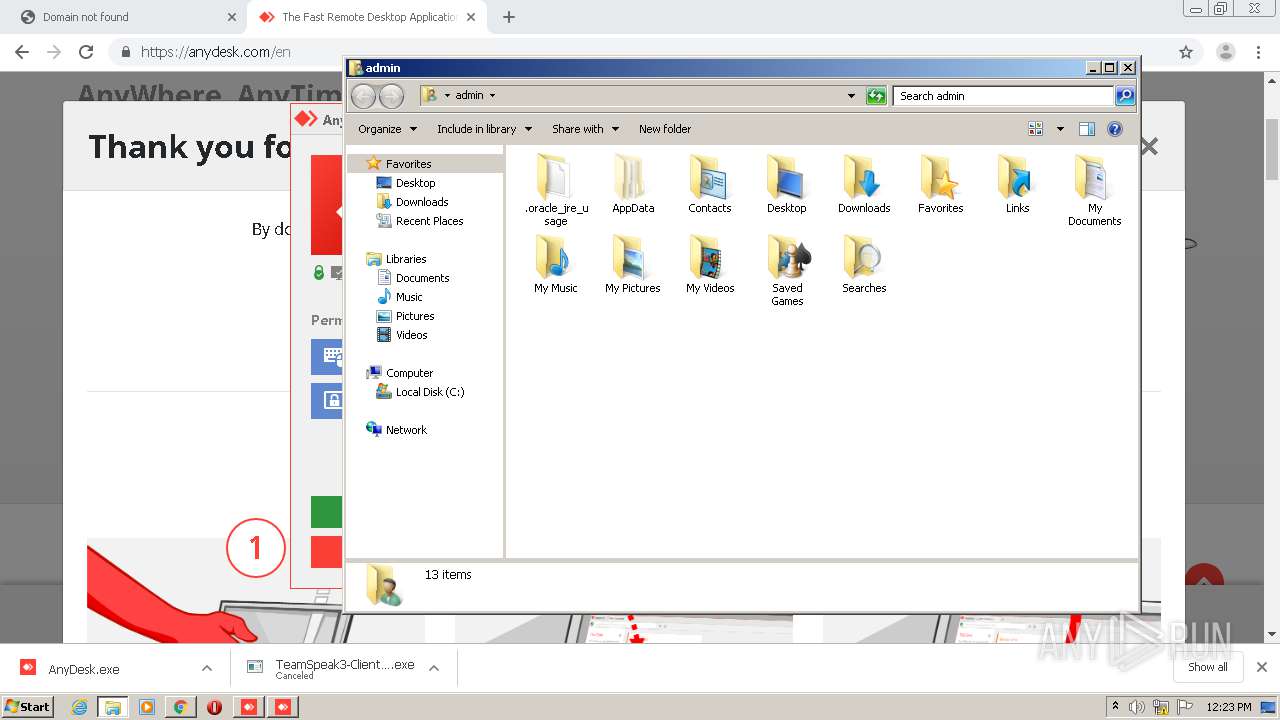
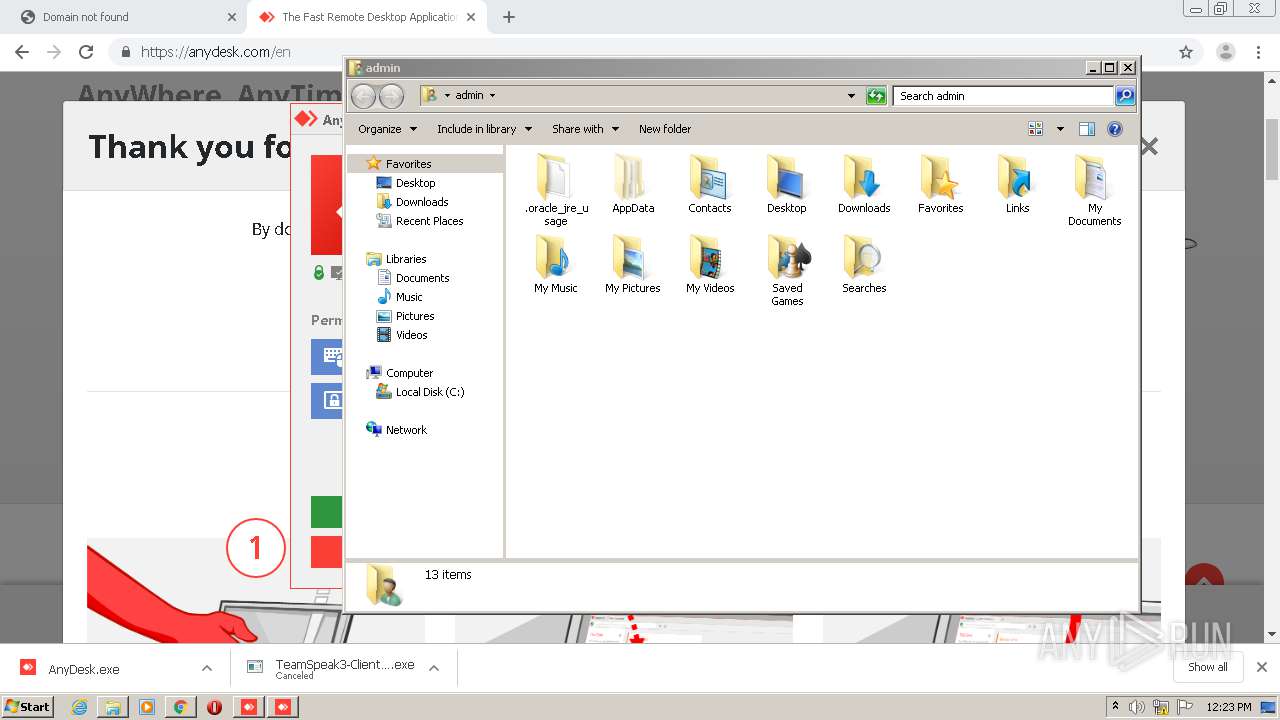
Creates files in the user directory
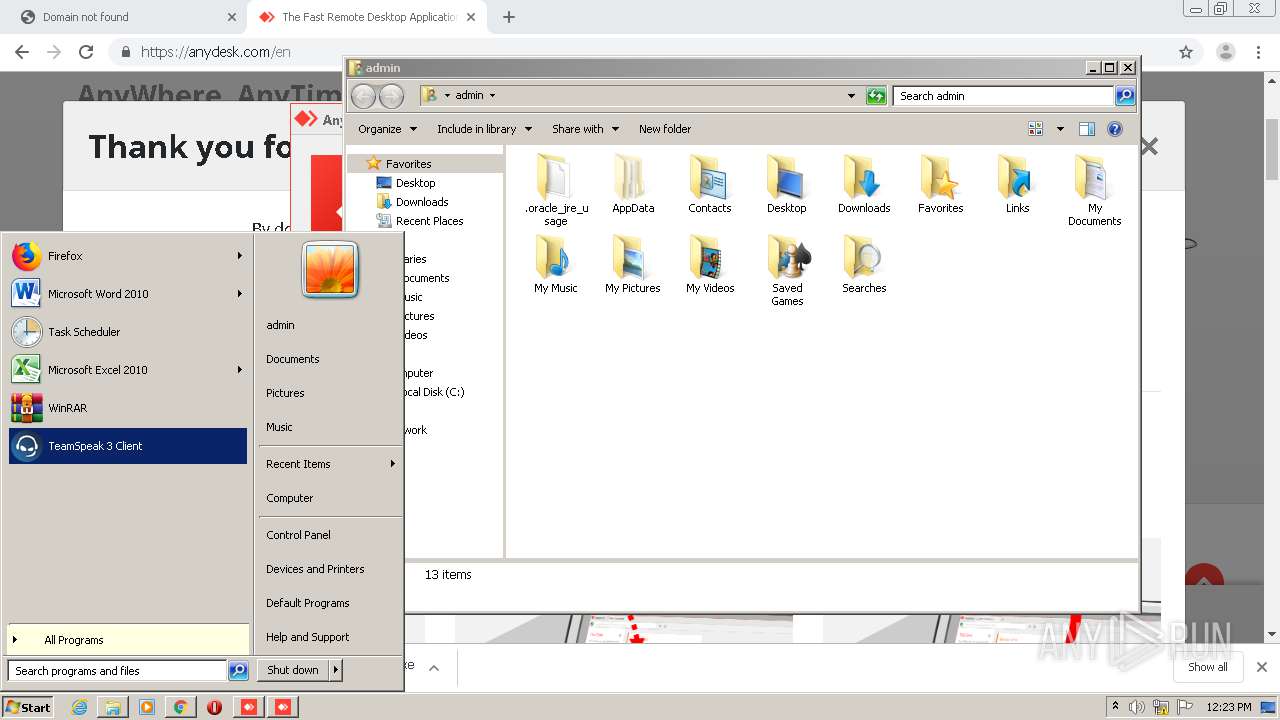
- AnyDesk.exe (PID: 1088)
- AnyDesk.exe (PID: 4060)
- ts3client_win32.exe (PID: 3616)
- package_inst.exe (PID: 620)
- package_inst.exe (PID: 3196)
- ts3client_win32.exe (PID: 2472)
- package_inst.exe (PID: 1076)
Reads Internet Cache Settings
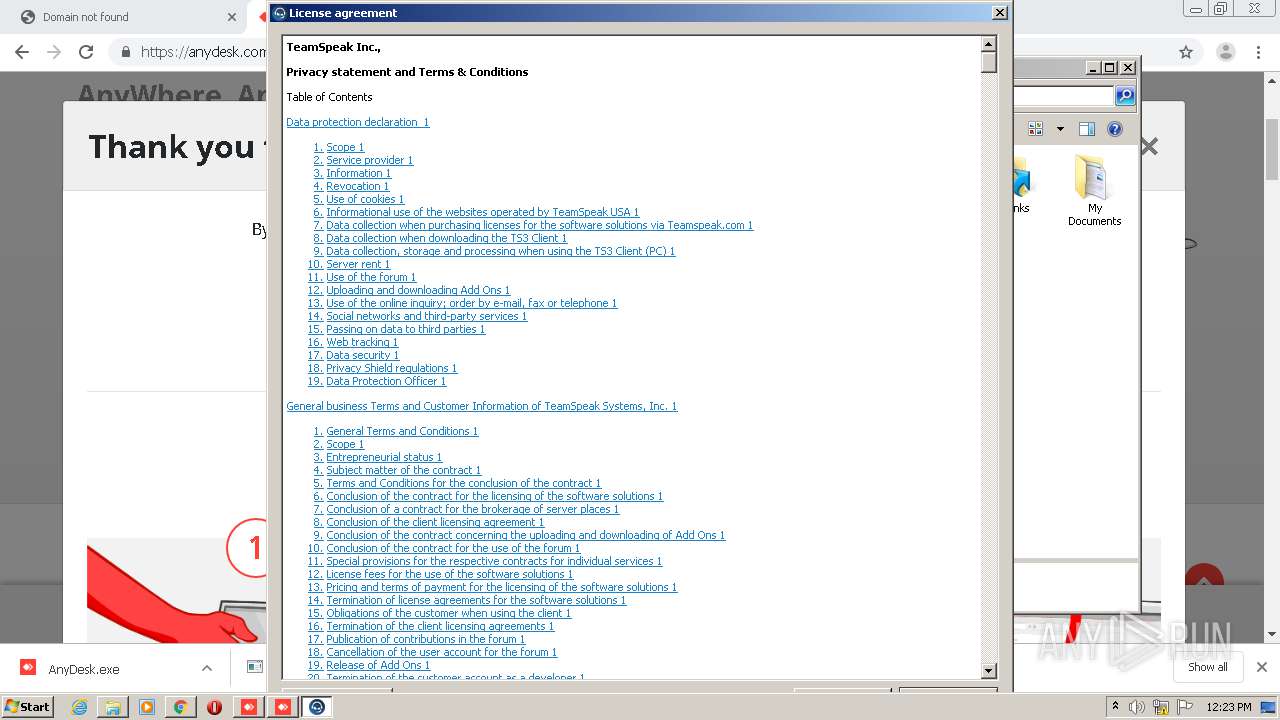
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 3592)
Modifies the open verb of a shell class
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 3592)
Creates a software uninstall entry
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 3592)
Searches for installed software
- vcredist_x86.exe (PID: 1836)
Creates files in the program directory
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 3592)
INFO
Reads the hosts file
- chrome.exe (PID: 952)
- chrome.exe (PID: 3708)
- ts3client_win32.exe (PID: 3616)
Reads settings of System Certificates
- chrome.exe (PID: 952)
- chrome.exe (PID: 3708)
- ts3client_win32.exe (PID: 3616)
Reads Internet Cache Settings
- chrome.exe (PID: 952)
Application launched itself
- chrome.exe (PID: 952)
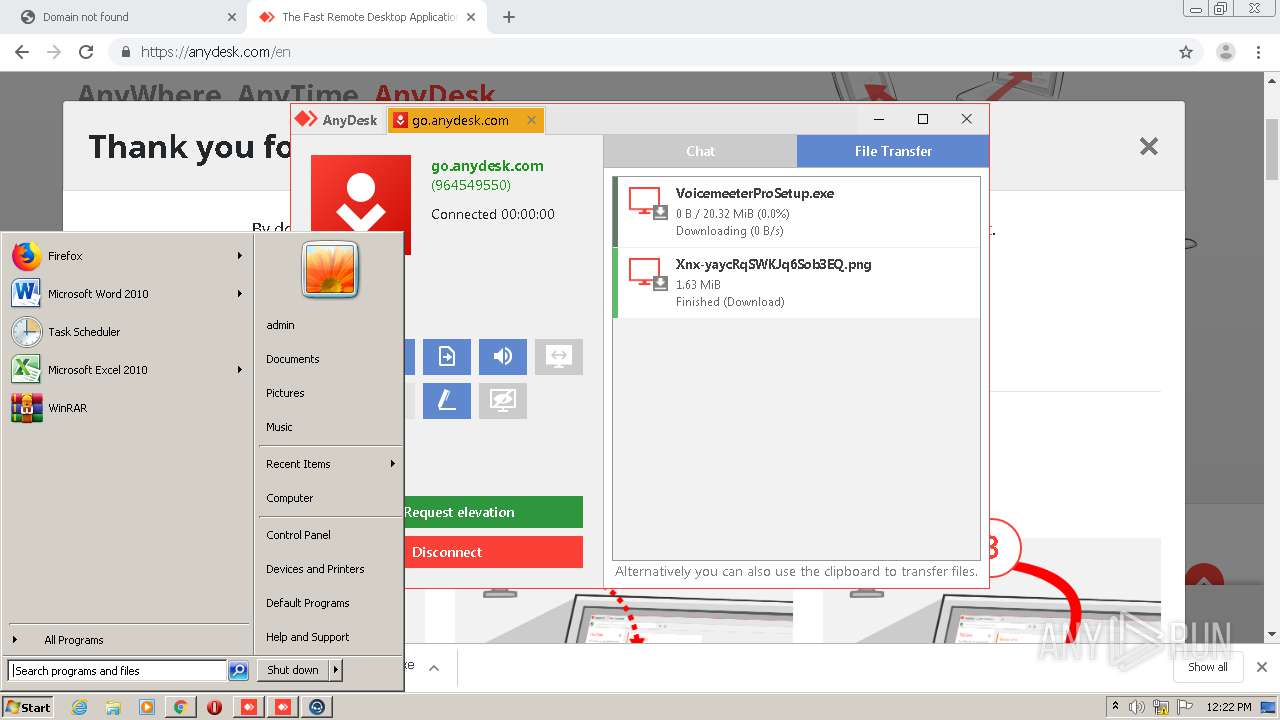
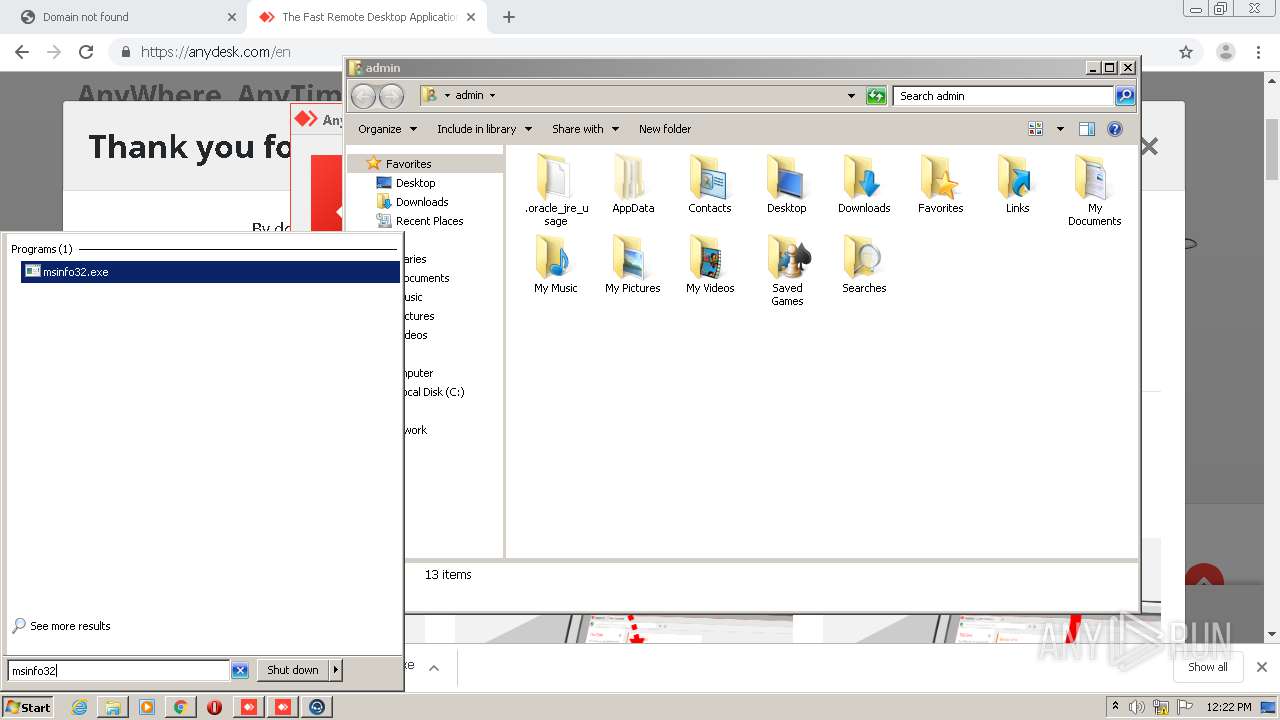
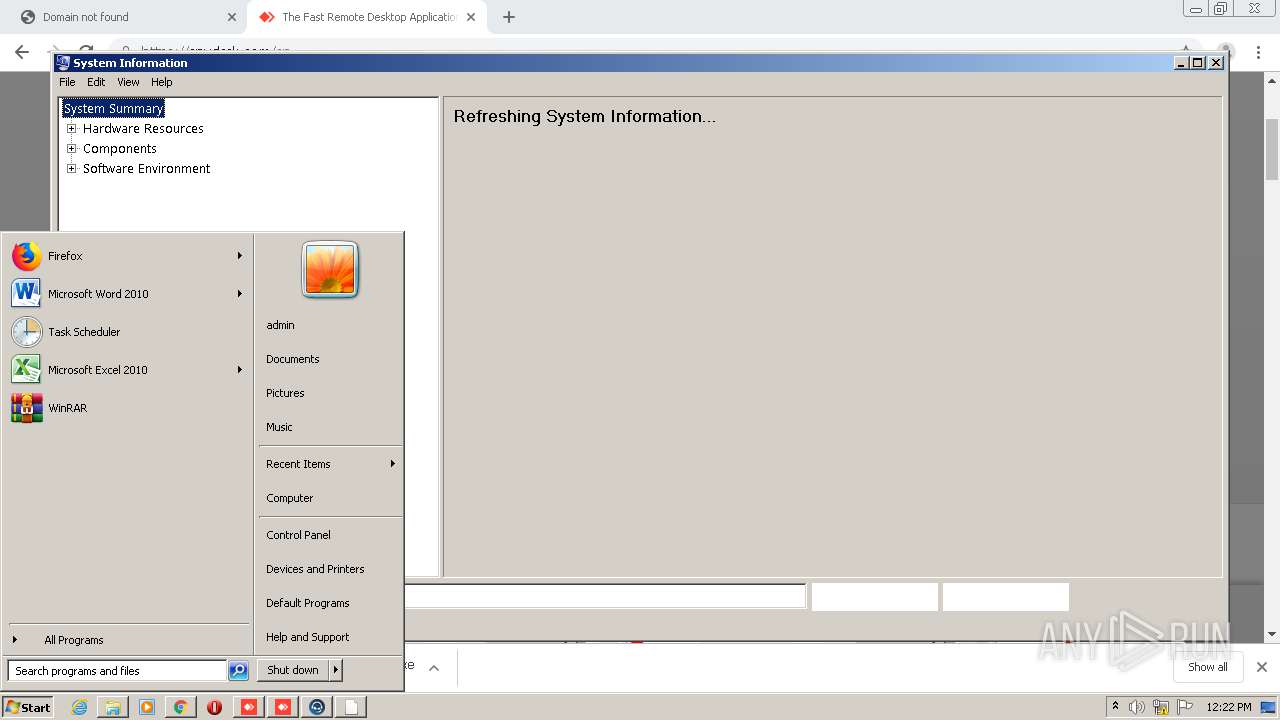
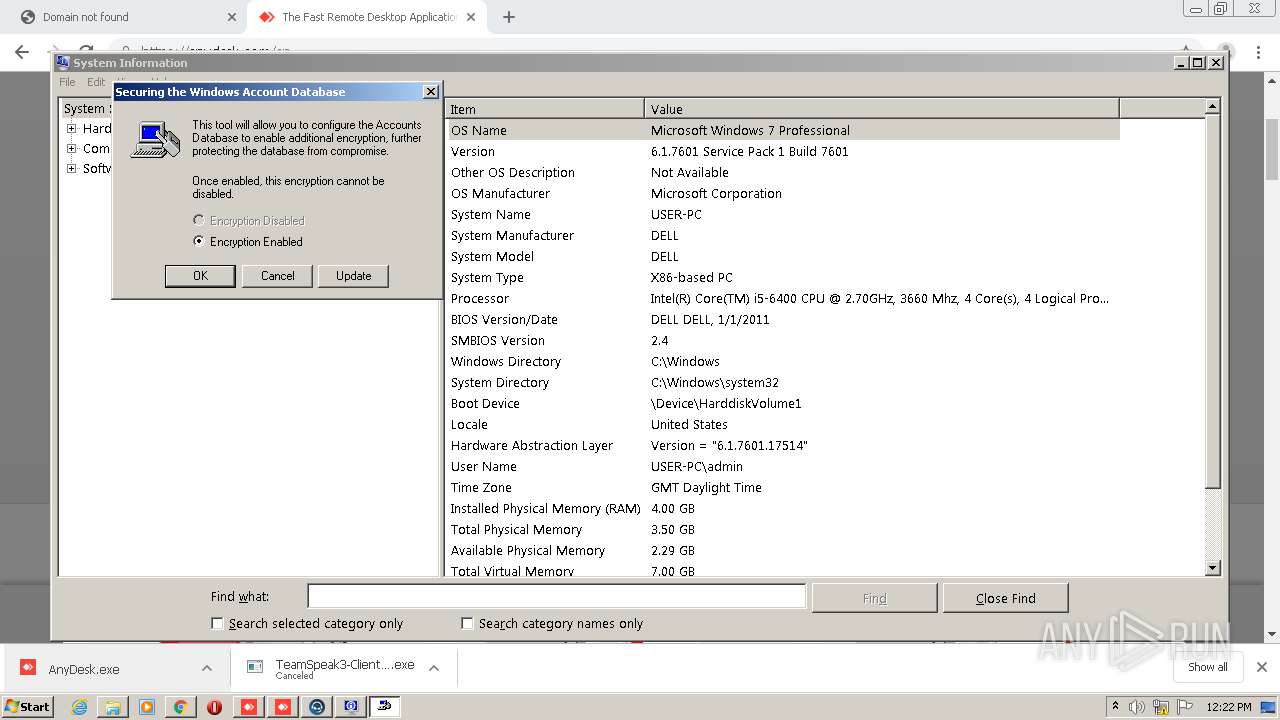
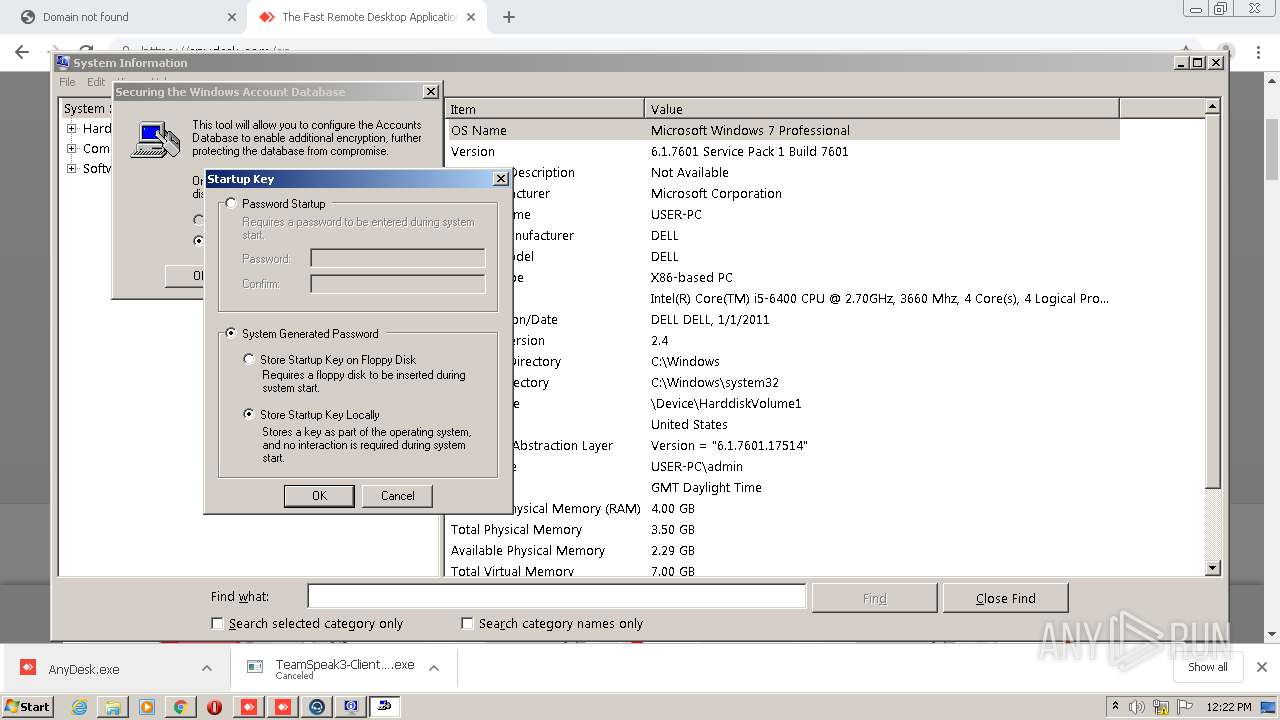
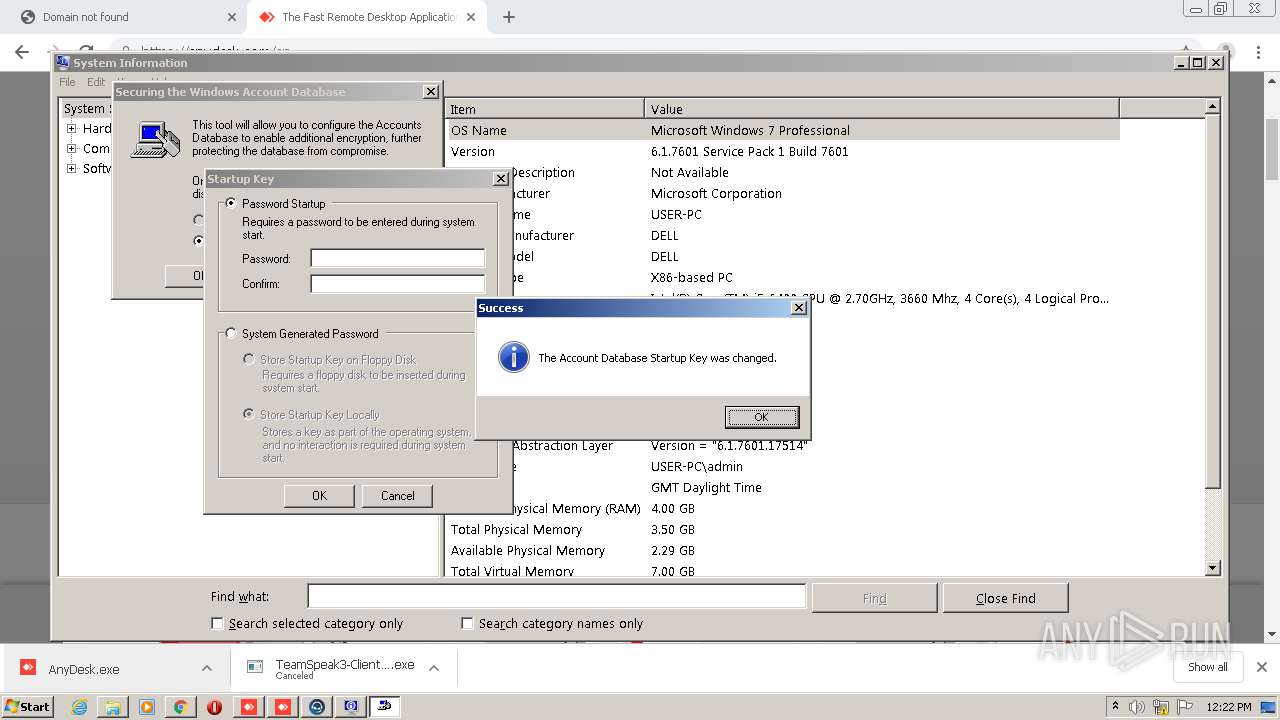
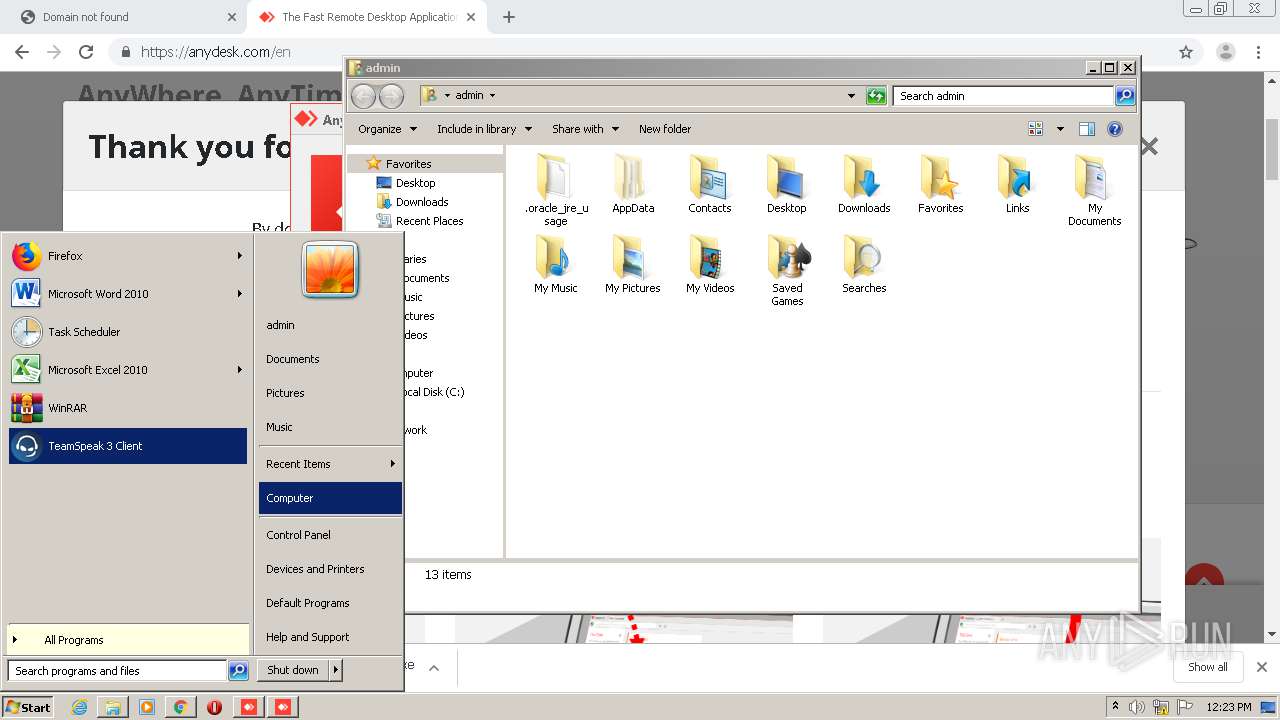
Manual execution by user
- msinfo32.exe (PID: 2464)
- syskey.exe (PID: 3768)
- syskey.exe (PID: 1292)
- ts3client_win32.exe (PID: 2884)
- ts3client_win32.exe (PID: 2472)
Dropped object may contain Bitcoin addresses
- TeamSpeak3-Client-win32-3.5.3.exe (PID: 3592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
123
Monitored processes
72
Malicious processes
12
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | C:\Users\admin\AppData\Local\Temp\nswB734.tmp\vcredist_x86.exe /passive /norestart | C:\Users\admin\AppData\Local\Temp\nswB734.tmp\vcredist_x86.exe | — | TeamSpeak3-Client-win32-3.5.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.24215 Exit code: 1638 Version: 14.0.24215.1 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,11850066860908188605,7375806783511130639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13876375777657937691 --mojo-platform-channel-handle=4556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11850066860908188605,7375806783511130639,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8346325143490015704 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\TeamSpeak 3 Client\package_inst.exe" -silent C:/Users/admin/AppData/Local/Temp/control-13win32_5d002c29ac868.ts3_plugin | C:\Program Files\TeamSpeak 3 Client\package_inst.exe | ts3client_win32.exe | ||||||||||||
User: admin Company: TeamSpeak Systems GmbH Integrity Level: HIGH Description: TeamSpeak 3 Package Installer Exit code: 0 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,11850066860908188605,7375806783511130639,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=906409022190013947 --mojo-platform-channel-handle=4016 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.youareanidiot.cc" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,11850066860908188605,7375806783511130639,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8046028435920085560 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\TeamSpeak 3 Client\package_inst.exe" -silent C:/Users/admin/AppData/Local/Temp/clientquerypluginwin32_5d2d9a74714fb.ts3_plugin | C:\Program Files\TeamSpeak 3 Client\package_inst.exe | ts3client_win32.exe | ||||||||||||
User: admin Company: TeamSpeak Systems GmbH Integrity Level: HIGH Description: TeamSpeak 3 Package Installer Exit code: 0 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
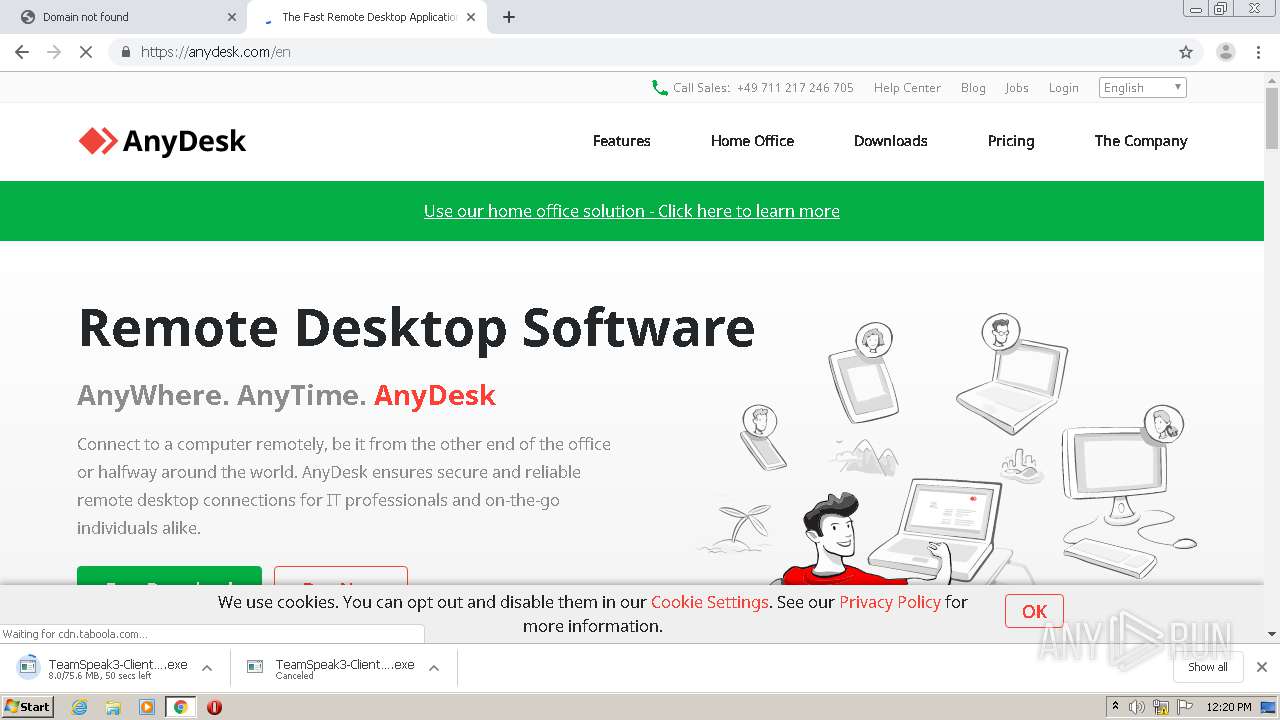
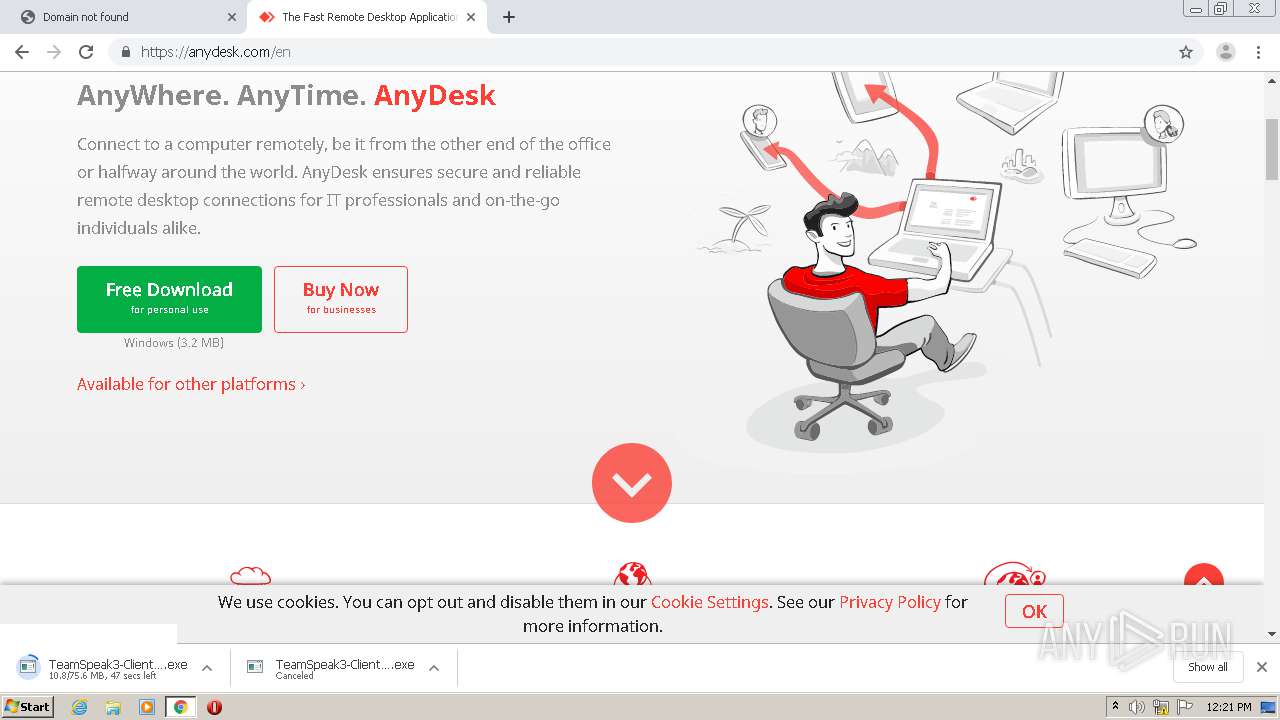
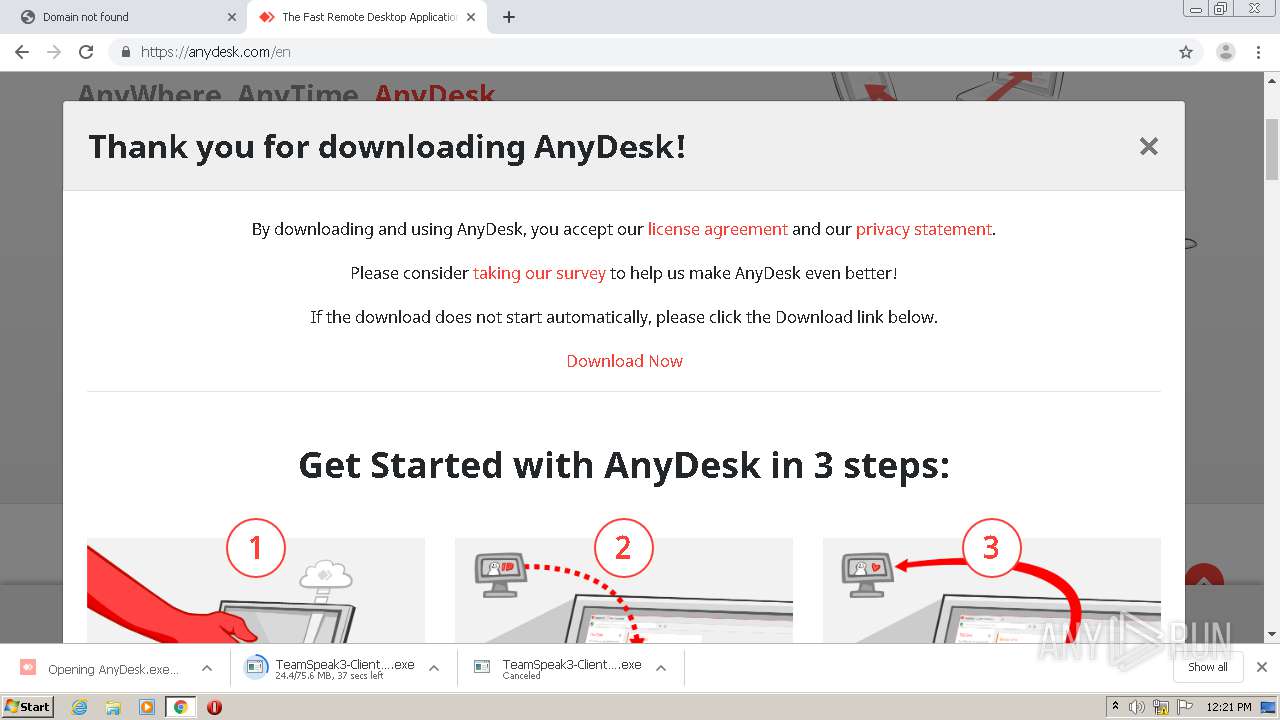
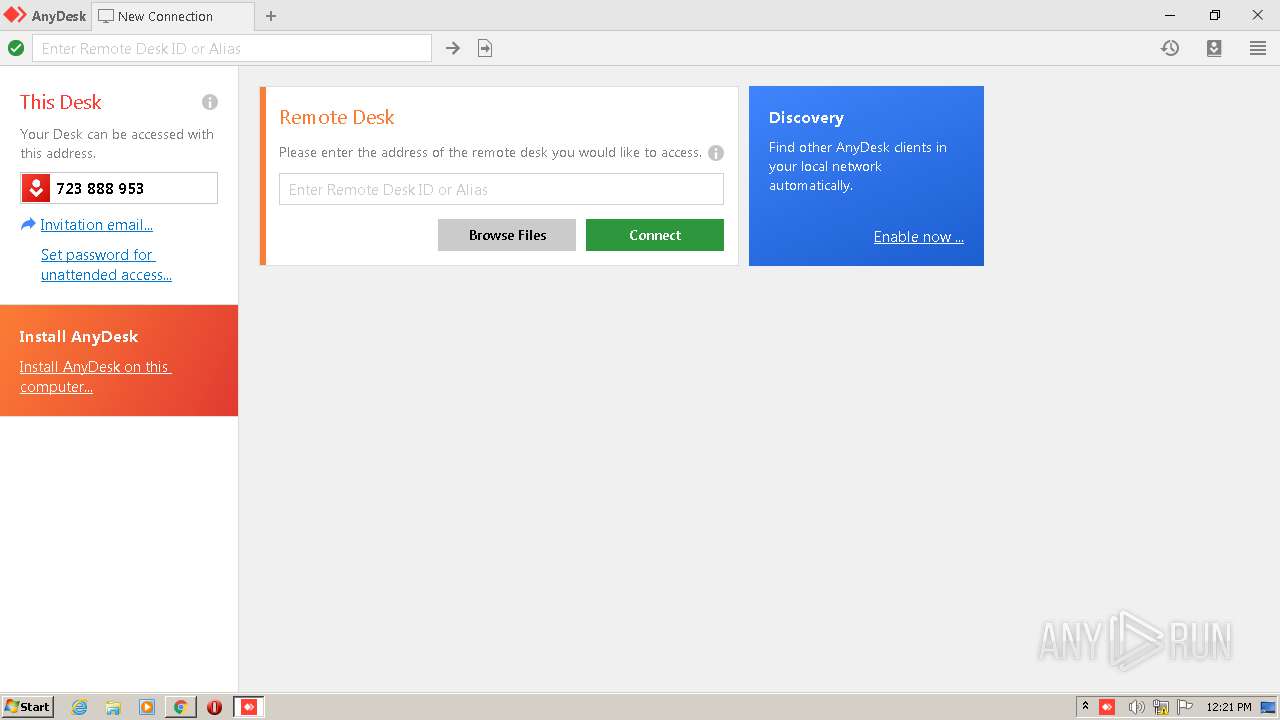
| 1088 | "C:\Users\admin\Downloads\AnyDesk.exe" | C:\Users\admin\Downloads\AnyDesk.exe | — | chrome.exe | |||||||||||
User: admin Company: philandro Software GmbH Integrity Level: MEDIUM Description: AnyDesk Exit code: 0 Version: 5.5.3.0 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,11850066860908188605,7375806783511130639,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17443964083541306268 --mojo-platform-channel-handle=3684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 617
Read events
3 440
Write events
168
Delete events
9
Modification events
| (PID) Process: | (952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2528) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 952-13238248767004750 |
Value: 259 | |||
| (PID) Process: | (952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (952) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
66
Suspicious files
256
Text files
542
Unknown types
235
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EFF143F-3B8.pma | — | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a0be85ee-a9cd-4f7c-b2a1-6ffe9a013b26.tmp | — | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF109d1c.TMP | text | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF109ed2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
121
DNS requests
80
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3708 | chrome.exe | GET | 301 | 172.67.183.93:80 | http://www.youareanidiot.cc/ | US | — | — | malicious |
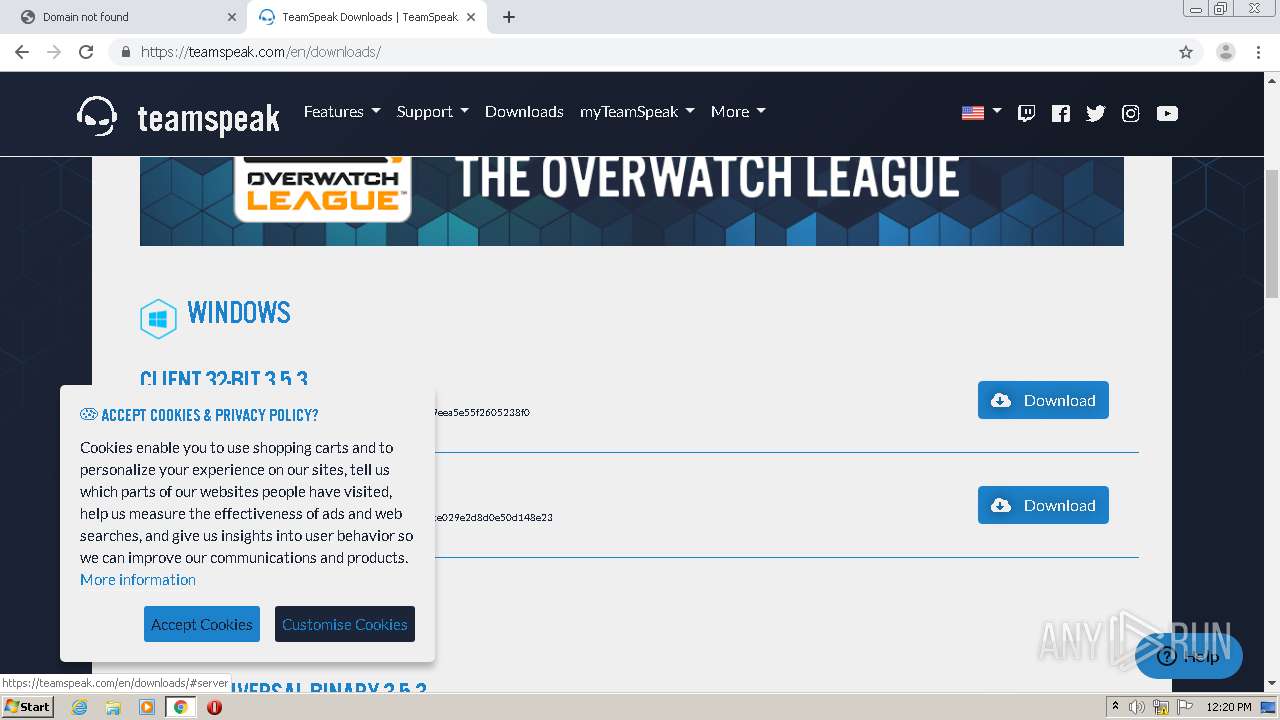
3708 | chrome.exe | GET | 301 | 104.22.26.164:80 | http://teamspeak.com/ | US | — | — | whitelisted |
3708 | chrome.exe | GET | 301 | 172.67.73.20:80 | http://ipchicken.com/ | US | — | — | suspicious |
3592 | TeamSpeak3-Client-win32-3.5.3.exe | GET | 404 | 69.16.175.10:80 | http://install.overwolf.com/partner/teamspeak/shouldoptout | US | xml | 301 b | malicious |
3708 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 526 b | whitelisted |
3708 | chrome.exe | GET | 200 | 173.194.182.136:80 | http://r3---sn-hpa7znsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.183.105.213&mm=28&mn=sn-hpa7znsz&ms=nvh&mt=1593775092&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
3708 | chrome.exe | GET | 302 | 172.217.21.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
4060 | AnyDesk.exe | POST | — | 18.202.151.176:80 | http://api.playanext.com/httpapi | US | — | — | whitelisted |
3708 | chrome.exe | GET | 200 | 173.194.182.136:80 | http://r3---sn-hpa7znsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.183.105.213&mm=28&mn=sn-hpa7znsz&ms=nvh&mt=1593775092&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3708 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3708 | chrome.exe | 172.217.22.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
3708 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3708 | chrome.exe | 172.67.183.93:80 | www.youareanidiot.cc | — | US | suspicious |
3708 | chrome.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3708 | chrome.exe | 172.67.183.93:443 | www.youareanidiot.cc | — | US | suspicious |
3708 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3708 | chrome.exe | 173.194.182.136:80 | r3---sn-hpa7znsz.gvt1.com | Google Inc. | US | whitelisted |
3708 | chrome.exe | 172.217.23.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3708 | chrome.exe | 172.217.21.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youareanidiot.cc |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-hpa7znsz.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1044 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY ipchicken .com DNS Lookup |
1044 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY ipchicken .com DNS Lookup |
3708 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup (ipchicken .com) |
4060 | AnyDesk.exe | Potential Corporate Privacy Violation | ET POLICY SSL/TLS Certificate Observed (AnyDesk Remote Desktop Software) |
3592 | TeamSpeak3-Client-win32-3.5.3.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
3592 | TeamSpeak3-Client-win32-3.5.3.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |
Process | Message |
|---|---|
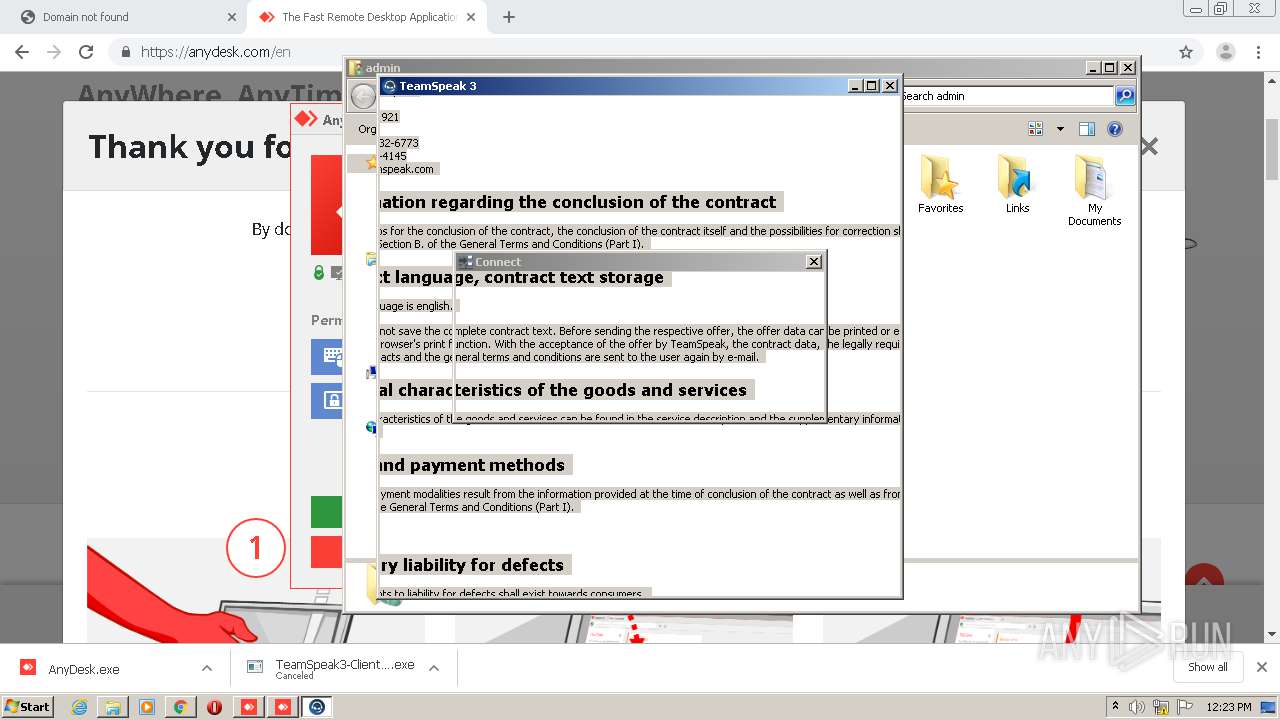
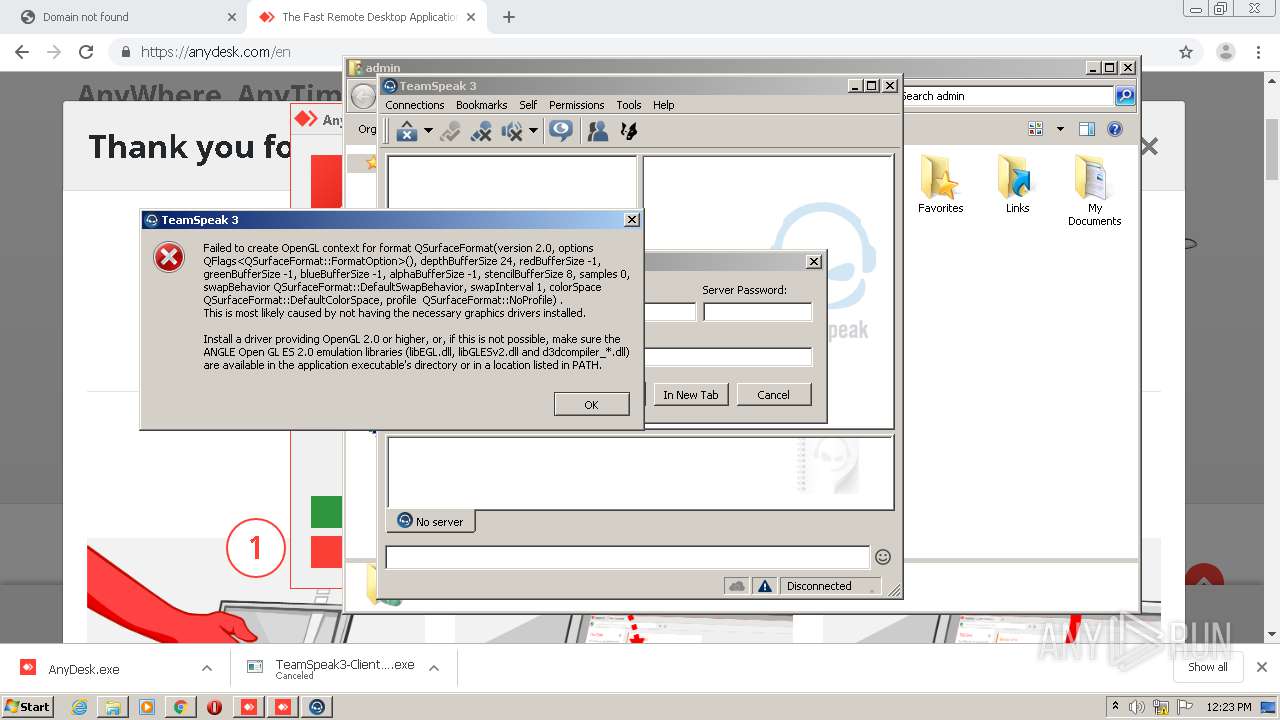
ts3client_win32.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll isÐ |
ts3client_win32.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
ts3client_win32.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll isÐ |
ts3client_win32.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
ts3client_win32.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
ts3client_win32.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
ts3client_win32.exe | WebEngineContext used before QtWebEngine::initialize() or OpenGL context creation failed.
|
ts3client_win32.exe | Qt WebEngine ICU data not found at C:/Qt/Qt5.12.3/5.12.3/msvc2017. Trying application directory...
|
ts3client_win32.exe | Qt WebEngine ICU data not found at C:/Qt/Qt5.12.3/5.12.3/msvc2017/resources. Trying parent directory...
|
ts3client_win32.exe | Installed Qt WebEngine locales directory not found at location C:/Qt/Qt5.12.3/5.12.3/msvc2017/translations\qtwebengine_locales. Trying application directory...
|